| File name: | file |
| Full analysis: | https://app.any.run/tasks/92350a8e-55ca-4085-8998-24542fb455ce |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 06, 2022, 04:49:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | 0CA285F97845E33DE99B444E236051E5 |
| SHA1: | 5FFE1DA169061E7C05400CE881C6482083502ADF |
| SHA256: | 65A4E90524E4A2AB747A80DE50A1D965F17CE6286B62CD4632DC73B84772CB37 |
| SSDEEP: | 98304:60gBCqdVjTMMlI7ghfV00ClDpkQ+YObOq5r:U31G0Y8YObxF |
MALICIOUS
Drops the executable file immediately after the start
- is-MJCER.tmp (PID: 1232)
- PrintFolders.exe (PID: 3844)
- gntuud.exe (PID: 392)
Application was dropped or rewritten from another process
- GfL0MIF7f.exe (PID: 1304)
- gntuud.exe (PID: 392)
- 2BN3oyIUjp.exe (PID: 3976)
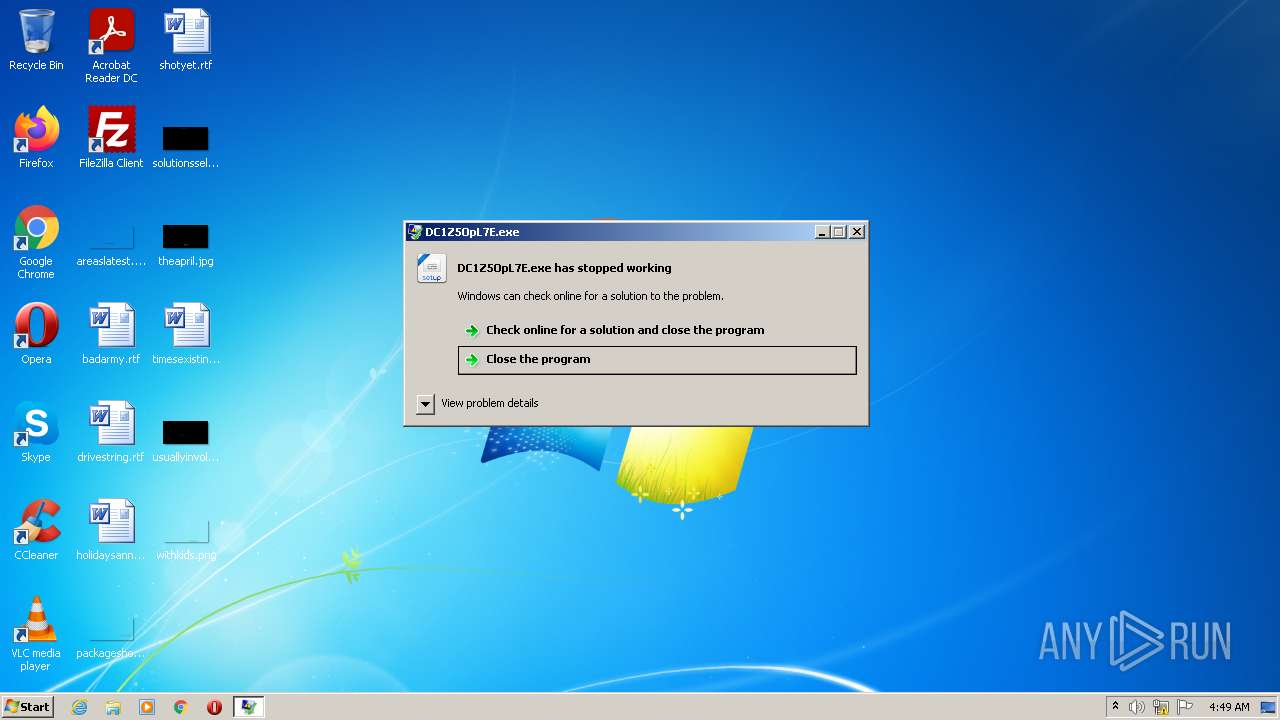
- DC1Z5OpL7E.exe (PID: 2532)
- w8s4VUV7DoZ.exe (PID: 276)
- gntuud.exe (PID: 3592)
- gntuud.exe (PID: 3552)
Changes the Startup folder
- gntuud.exe (PID: 392)
Uses Task Scheduler to run other applications
- gntuud.exe (PID: 392)
Changes the autorun value in the registry
- gntuud.exe (PID: 392)
G-cleaner network activity is detected
- PrintFolders.exe (PID: 3844)
AMADEY was detected
- gntuud.exe (PID: 392)
Connects to the CnC server
- gntuud.exe (PID: 392)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1396)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1264)
SUSPICIOUS
Creates a directory in Program Files
- is-MJCER.tmp (PID: 1232)
Executable content was dropped or overwritten
- is-MJCER.tmp (PID: 1232)
- PrintFolders.exe (PID: 3844)
- gntuud.exe (PID: 392)
Reads the Windows owner or organization settings
- is-MJCER.tmp (PID: 1232)
Drops a file with too old compile date
- is-MJCER.tmp (PID: 1232)
- gntuud.exe (PID: 392)
Reads Microsoft Outlook installation path
- PrintFolders.exe (PID: 3844)
Reads the Internet Settings
- 2BN3oyIUjp.exe (PID: 3976)
- gntuud.exe (PID: 392)
- PrintFolders.exe (PID: 3844)
Starts itself from another location
- 2BN3oyIUjp.exe (PID: 3976)
Connects to the server without a host name
- PrintFolders.exe (PID: 3844)
- gntuud.exe (PID: 392)
- rundll32.exe (PID: 1264)
Starts CMD.EXE for commands execution
- PrintFolders.exe (PID: 3844)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1308)
Uses TASKKILL.EXE to terminate process
- cmd.exe (PID: 1308)
Executes via Task Scheduler
- gntuud.exe (PID: 3592)
- gntuud.exe (PID: 3552)
Uses RUNDLL32.EXE to load library
- gntuud.exe (PID: 392)
Process requests binary or script from the Internet
- gntuud.exe (PID: 392)
INFO
Creates a file in a temporary directory
- file.exe (PID: 2208)
- is-MJCER.tmp (PID: 1232)
- 2BN3oyIUjp.exe (PID: 3976)
- gntuud.exe (PID: 392)
Checks supported languages
- file.exe (PID: 2208)
- is-MJCER.tmp (PID: 1232)
- PrintFolders.exe (PID: 3844)
- 2BN3oyIUjp.exe (PID: 3976)
- gntuud.exe (PID: 392)
- DC1Z5OpL7E.exe (PID: 2532)
- w8s4VUV7DoZ.exe (PID: 276)
- gntuud.exe (PID: 3592)
- gntuud.exe (PID: 3552)
- GfL0MIF7f.exe (PID: 1304)
Reads the computer name
- is-MJCER.tmp (PID: 1232)
- PrintFolders.exe (PID: 3844)
- 2BN3oyIUjp.exe (PID: 3976)
- gntuud.exe (PID: 392)
Drops a file that was compiled in debug mode
- is-MJCER.tmp (PID: 1232)
- PrintFolders.exe (PID: 3844)
Creates files in the program directory
- is-MJCER.tmp (PID: 1232)
Creates a software uninstall entry
- is-MJCER.tmp (PID: 1232)
Loads dropped or rewritten executable
- is-MJCER.tmp (PID: 1232)
Application was dropped or rewritten from another process
- is-MJCER.tmp (PID: 1232)
Checks proxy server information
- PrintFolders.exe (PID: 3844)
- gntuud.exe (PID: 392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 1992-Jun-19 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | - |
| FileDescription: | PrintFolders Setup |
| FileVersion: | - |
| InternalName: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 8 |
| TimeDateStamp: | 1992-Jun-19 22:22:17 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 4096 | 36352 | 36352 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60044 |
DATA | 40960 | 584 | 1024 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.72043 |
BSS | 45056 | 3684 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 49152 | 2248 | 2560 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.2508 |
.tls | 53248 | 8 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 57344 | 24 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 61440 | 2156 | 0 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | |
.rsrc | 65536 | 54688 | 54784 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.75782 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26485 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 5.20743 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.46677 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.74812 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56273 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.79202 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.82124 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.89108 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.13941 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 6.51874 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
advapi32.dll (#2) |
comctl32.dll |
kernel32.dll |
kernel32.dll (#2) |
oleaut32.dll |
user32.dll |
user32.dll (#2) |
Total processes
56
Monitored processes
15
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Users\admin\AppData\Roaming\GuqW04l\w8s4VUV7DoZ.exe" | C:\Users\admin\AppData\Roaming\GuqW04l\w8s4VUV7DoZ.exe | — | PrintFolders.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\ecaac49691\gntuud.exe" | C:\Users\admin\AppData\Local\Temp\ecaac49691\gntuud.exe | 2BN3oyIUjp.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Temp\is-HH50F.tmp\is-MJCER.tmp" /SL4 $30138 "C:\Users\admin\AppData\Local\Temp\file.exe" 3625704 96256 | C:\Users\admin\AppData\Local\Temp\is-HH50F.tmp\is-MJCER.tmp | file.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.42.0.0 Modules
| |||||||||||||||
| 1264 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\f49dfc5e4e2508\cred.dll, Main | C:\Windows\System32\rundll32.exe | gntuud.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1304 | C:\Users\admin\AppData\Roaming\{e29ac6c0-7037-11de-816d-806e6f6e6963}\GfL0MIF7f.exe | — | PrintFolders.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1308 | "C:\Windows\System32\cmd.exe" /c taskkill /im "PrintFolders.exe" /f & erase "C:\Program Files\PrintFolders\PrintFolders.exe" & exit | C:\Windows\System32\cmd.exe | — | PrintFolders.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | "C:\Windows\System32\schtasks.exe" /Create /SC MINUTE /MO 1 /TN gntuud.exe /TR "C:\Users\admin\AppData\Local\Temp\ecaac49691\gntuud.exe" /F | C:\Windows\System32\schtasks.exe | — | gntuud.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | Explorer.EXE | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: PrintFolders Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Roaming\OuT9rzTT\DC1Z5OpL7E.exe" | C:\Users\admin\AppData\Roaming\OuT9rzTT\DC1Z5OpL7E.exe | PrintFolders.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3068 | taskkill /im "PrintFolders.exe" /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 469
Read events
3 398
Write events
70
Delete events
1
Modification events
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_CURRENT_USER\Software\Auapoint Software\PrintFolders |
| Operation: | write | Name: | Language |
Value: eng | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.1.2-beta | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\PrintFolders | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\PrintFolders\ | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: PrintFolders | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | DisplayName |
Value: PrintFolders 3.101 | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\PrintFolders\PrintFolders.exe | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\PrintFolders\unins000.exe" | |||
| (PID) Process: | (1232) is-MJCER.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2483CD7A-78F2-476F-86FF-B2EA93461085}}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\PrintFolders\unins000.exe" /SILENT | |||
Executable files
19
Suspicious files
3
Text files
6
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\is-DM9VU.tmp | — | |
MD5:— | SHA256:— | |||
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\PrintFolders.exe | — | |
MD5:— | SHA256:— | |||
| 2208 | file.exe | C:\Users\admin\AppData\Local\Temp\is-HH50F.tmp\is-MJCER.tmp | executable | |
MD5:— | SHA256:— | |||
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\is-M7UQD.tmp | executable | |
MD5:— | SHA256:— | |||
| 1232 | is-MJCER.tmp | C:\Users\admin\AppData\Local\Temp\is-FTL83.tmp\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 1232 | is-MJCER.tmp | C:\Users\admin\AppData\Local\Temp\is-FTL83.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\is-NS569.tmp | chm | |
MD5:204A5BF160646F9A55ED70AB6E1A07A6 | SHA256:CACDD2C8BFA4BAE33A16A10ED609F4841AC5C4C2FE481ED0FD8CB04BC8016BBD | |||
| 3844 | PrintFolders.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\MIXTWO[1].file | executable | |
MD5:— | SHA256:— | |||
| 1232 | is-MJCER.tmp | C:\Program Files\PrintFolders\is-KSTIP.tmp | text | |
MD5:C8B211D81EB7D4F9EBB071A117444D51 | SHA256:AFD6FEA6A792B722E45A6587F70334F30051798017F4A278508C7ED3FEEA80CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
6
DNS requests
0
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
392 | gntuud.exe | POST | 200 | 77.73.133.72:80 | http://77.73.133.72/hfk3vK9/index.php?scr=1 | KZ | — | — | malicious |
3844 | PrintFolders.exe | GET | 200 | 107.182.129.235:80 | http://107.182.129.235/storage/ping.php | US | text | 17 b | malicious |
3844 | PrintFolders.exe | GET | 200 | 107.182.129.235:80 | http://107.182.129.235/storage/extension.php | US | binary | 92.0 Kb | malicious |
3844 | PrintFolders.exe | GET | 200 | 171.22.30.106:80 | http://171.22.30.106/library.php | GB | executable | 332 Kb | malicious |
3844 | PrintFolders.exe | GET | 200 | 171.22.30.106:80 | http://171.22.30.106/library.php | GB | executable | 3.78 Mb | malicious |
3844 | PrintFolders.exe | GET | 200 | 171.22.30.106:80 | http://171.22.30.106/library.php | GB | executable | 260 Kb | malicious |
1264 | rundll32.exe | POST | 200 | 77.73.133.72:80 | http://77.73.133.72/hfk3vK9/index.php | KZ | — | — | malicious |
392 | gntuud.exe | GET | 200 | 77.73.133.72:80 | http://77.73.133.72/hfk3vK9/Plugins/cred.dll | KZ | executable | 126 Kb | malicious |
3844 | PrintFolders.exe | GET | 200 | 45.139.105.171:80 | http://45.139.105.171/itsnotmalware/count.php?sub=NOSUB&stream=mixtwo&substream=mixinte | BG | binary | 1 b | malicious |
3844 | PrintFolders.exe | GET | 200 | 171.22.30.106:80 | http://171.22.30.106/library.php | GB | executable | 615 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3844 | PrintFolders.exe | 171.22.30.106:80 | — | Delis LLC | US | malicious |
392 | gntuud.exe | 77.73.133.72:80 | — | Partner LLC | KZ | malicious |
1264 | rundll32.exe | 77.73.133.72:80 | — | Partner LLC | KZ | malicious |
3844 | PrintFolders.exe | 45.139.105.171:80 | — | Xdeer Limited | BG | malicious |
3844 | PrintFolders.exe | 107.182.129.235:80 | — | Delis LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3844 | PrintFolders.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 9 |
3844 | PrintFolders.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3844 | PrintFolders.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3844 | PrintFolders.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3844 | PrintFolders.exe | Misc activity | ET INFO Packed Executable Download |
3844 | PrintFolders.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3844 | PrintFolders.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
392 | gntuud.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
392 | gntuud.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
392 | gntuud.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |