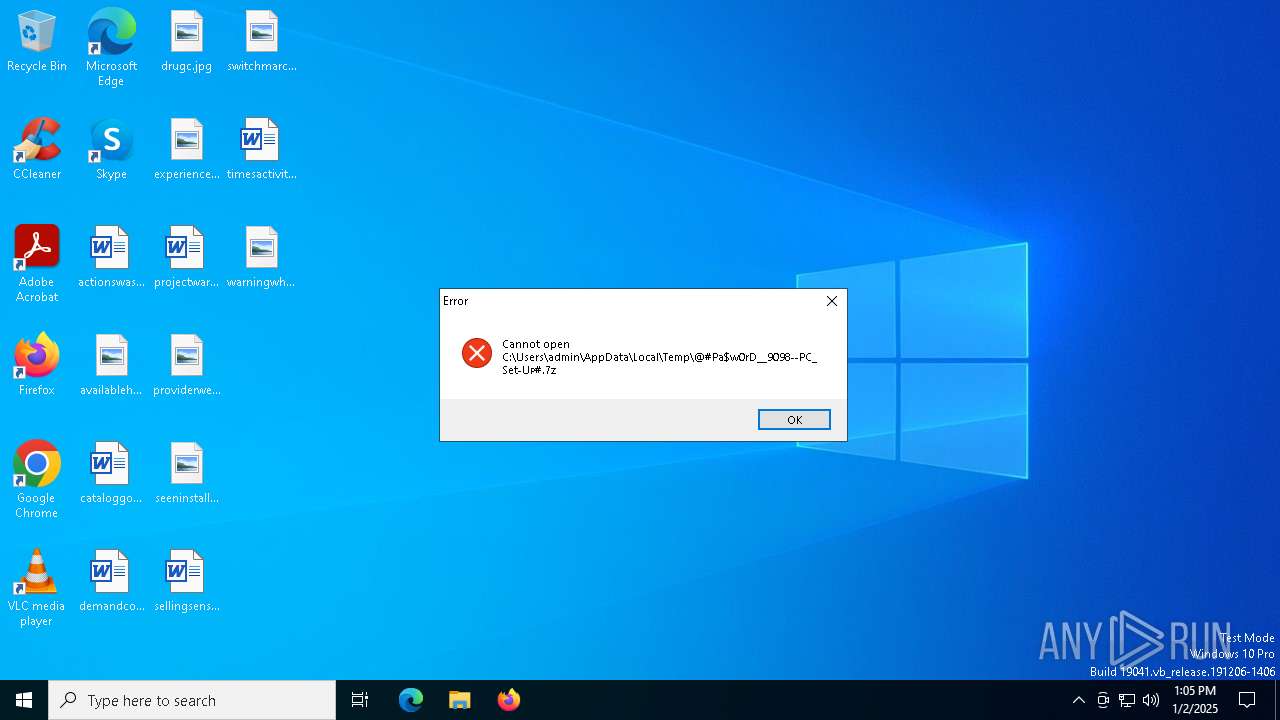
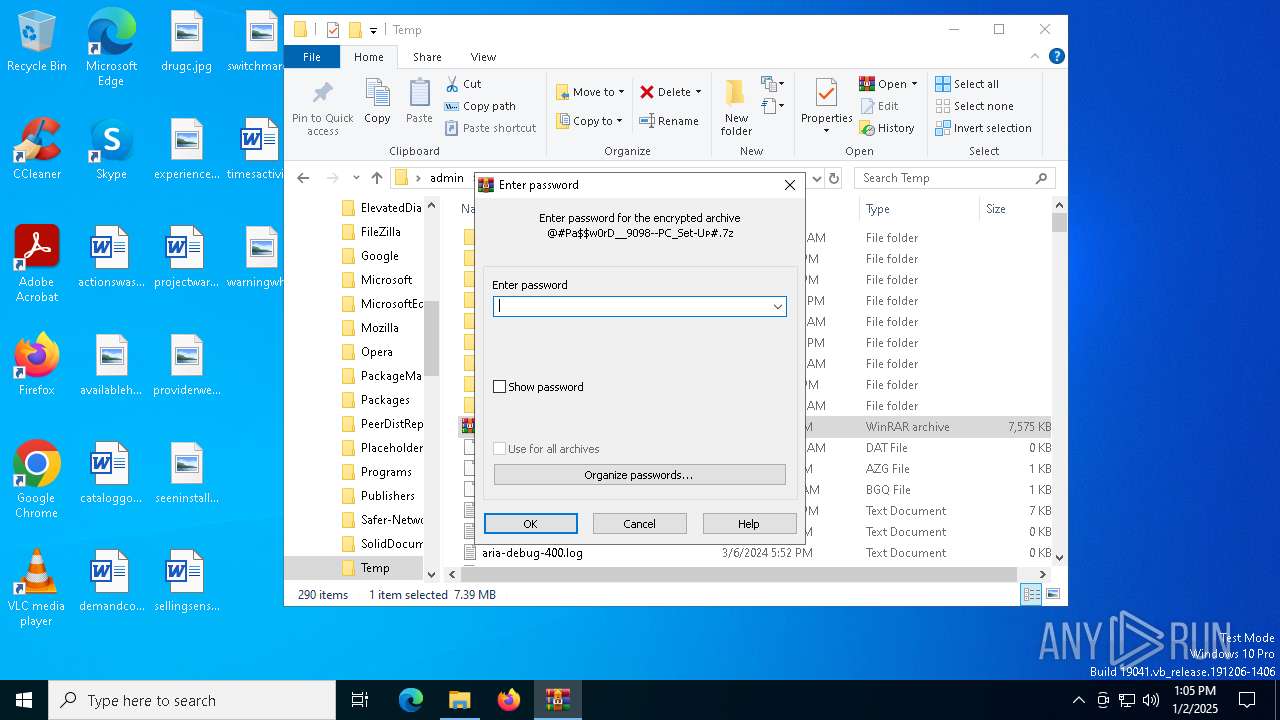
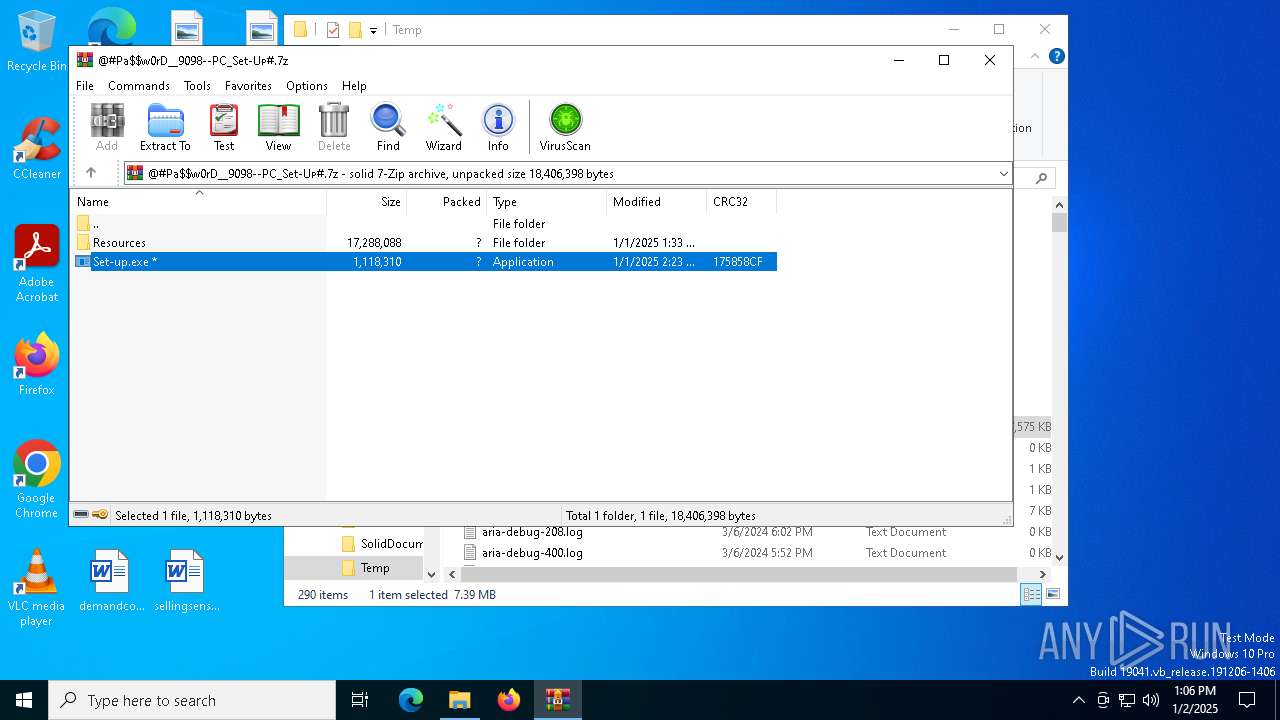
| File name: | @#Pa$w0rD__9098--PC_Set-Uᴘ#.7z |
| Full analysis: | https://app.any.run/tasks/ce96d014-dc37-49b8-9cbc-541d6a354c34 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 02, 2025, 13:05:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | BC6C215D3CB7AD0034B5205D049AB961 |
| SHA1: | 15408E82F63F0124E1F151E3B91B8638726767BE |
| SHA256: | 6532F999140742AD17B2D814AE35D109A9AC70F6BD26302BCECEF02EA1B47558 |
| SSDEEP: | 98304:nVI/NoPF9Lsyy3pZz4sahGfxy+zPjIJAore5iCpYnPtotPfKcAY7QUjePoRUoQWn:w47NSbrB3Wq6S |
MALICIOUS
Executing a file with an untrusted certificate
- Set-up.exe (PID: 7156)
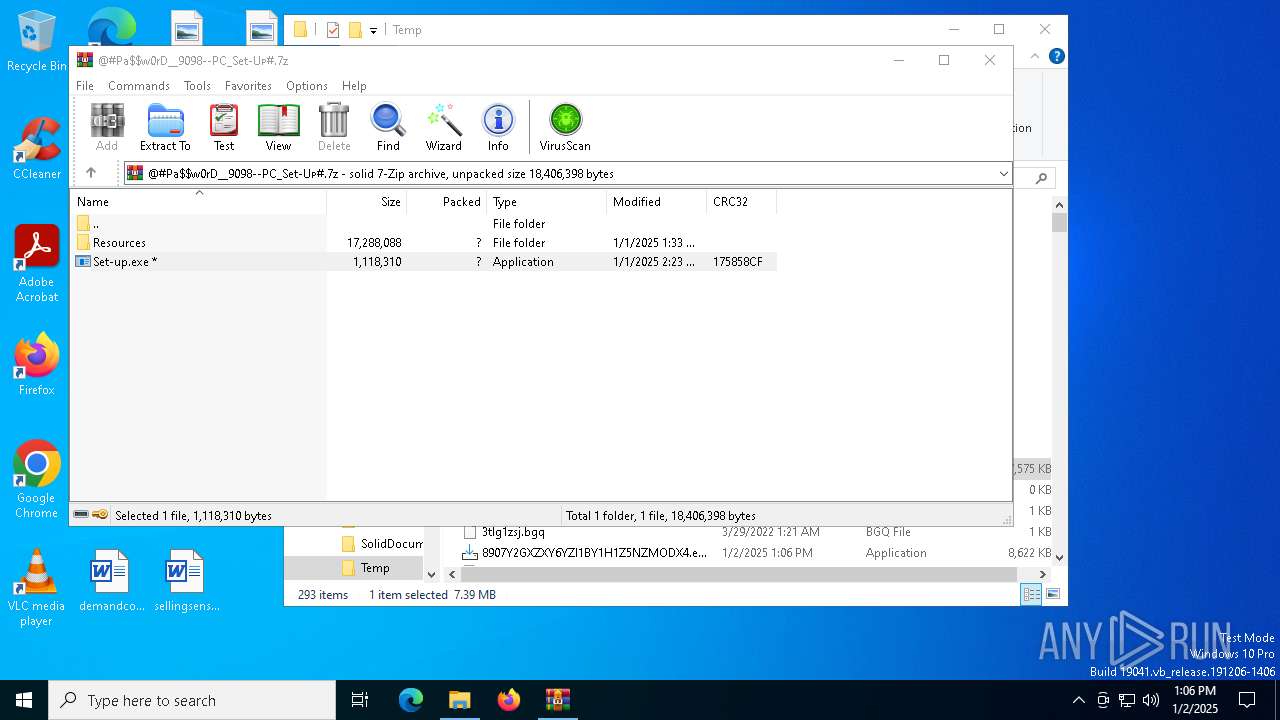
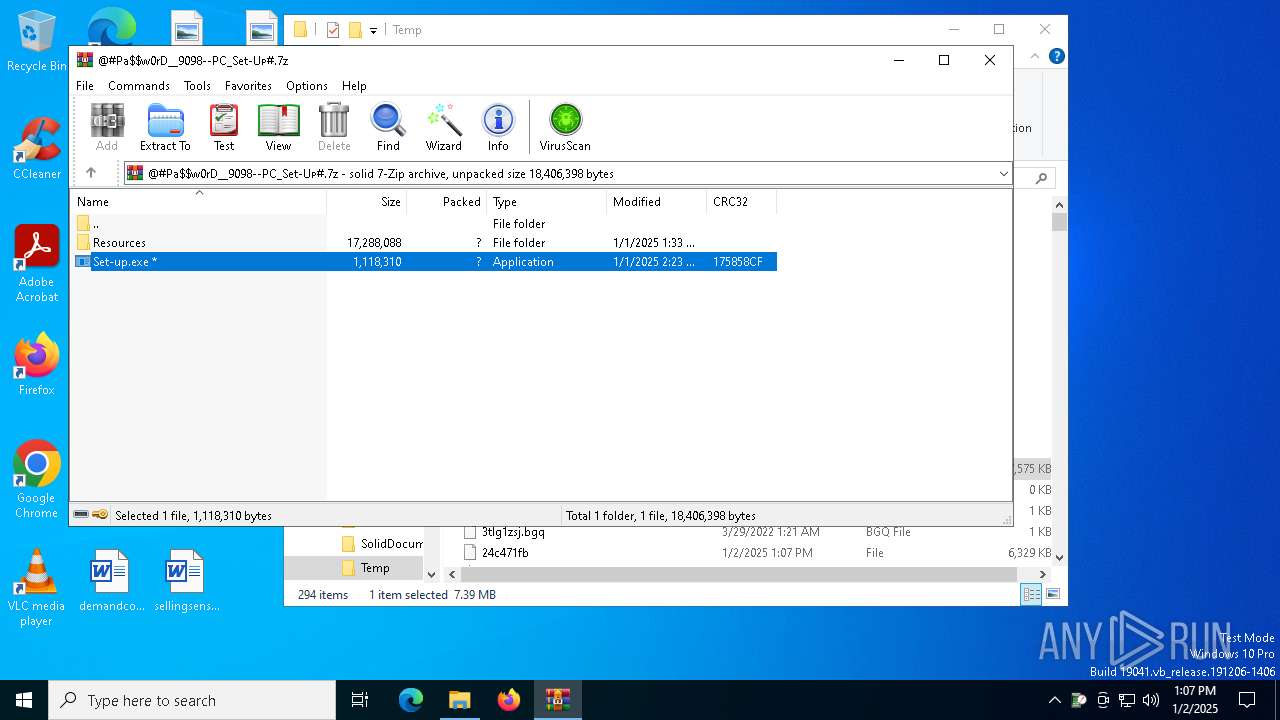
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 5432)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 4944)
Actions looks like stealing of personal data
- Temporary.com (PID: 3620)
AutoIt loader has been detected (YARA)
- Temporary.com (PID: 3620)
Steals credentials from Web Browsers
- Temporary.com (PID: 3620)
LUMMA mutex has been found
- Temporary.com (PID: 3620)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 6740)
- tasklist.exe (PID: 6680)
- cmd.exe (PID: 5080)
- find.exe (PID: 6772)
- tasklist.exe (PID: 6912)
- find.exe (PID: 5712)
- find.exe (PID: 1732)
- cmd.exe (PID: 1448)
- tasklist.exe (PID: 3608)
- cmd.exe (PID: 4740)
- find.exe (PID: 2132)
- cmd.exe (PID: 7100)
- tasklist.exe (PID: 6152)
- tasklist.exe (PID: 4504)
- find.exe (PID: 4548)
SUSPICIOUS
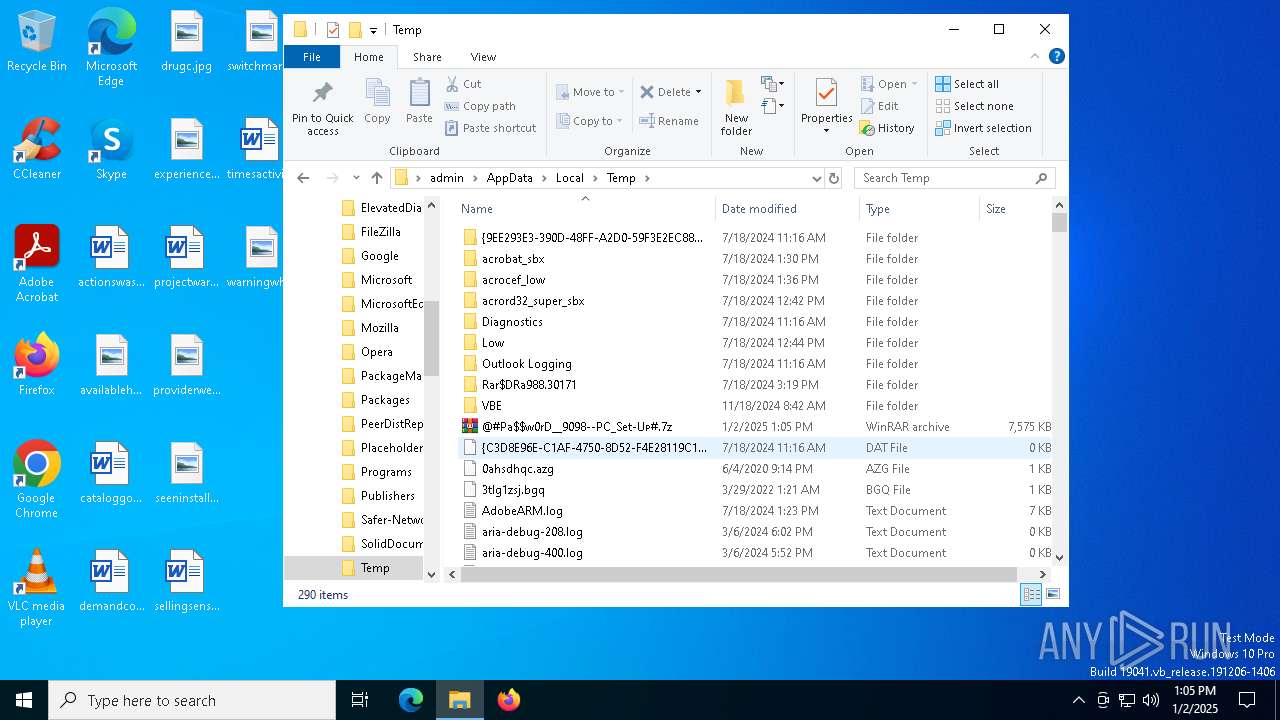
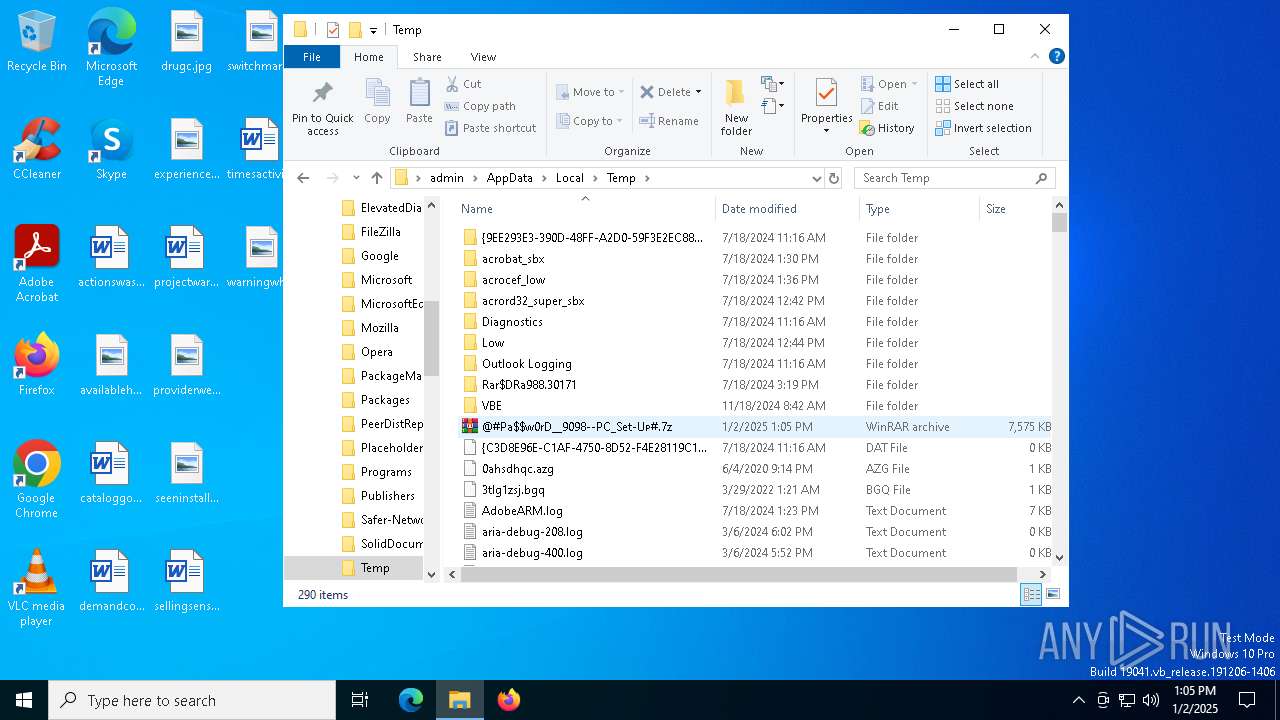
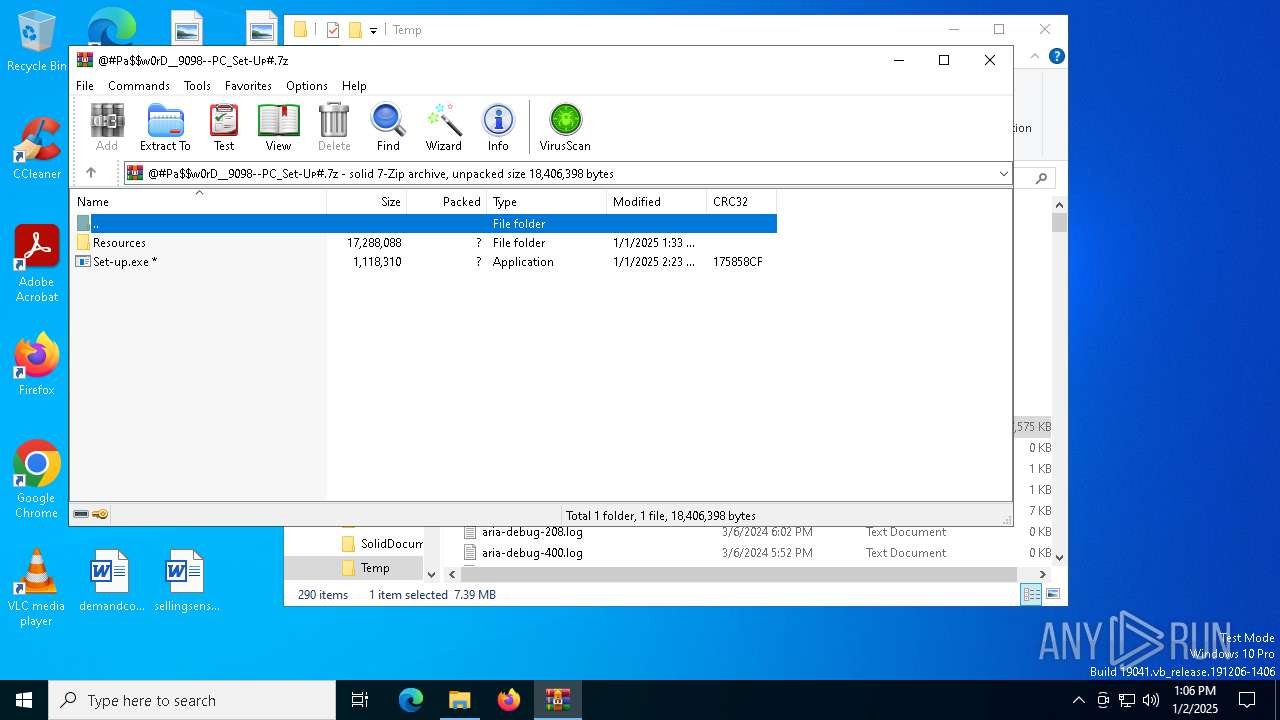
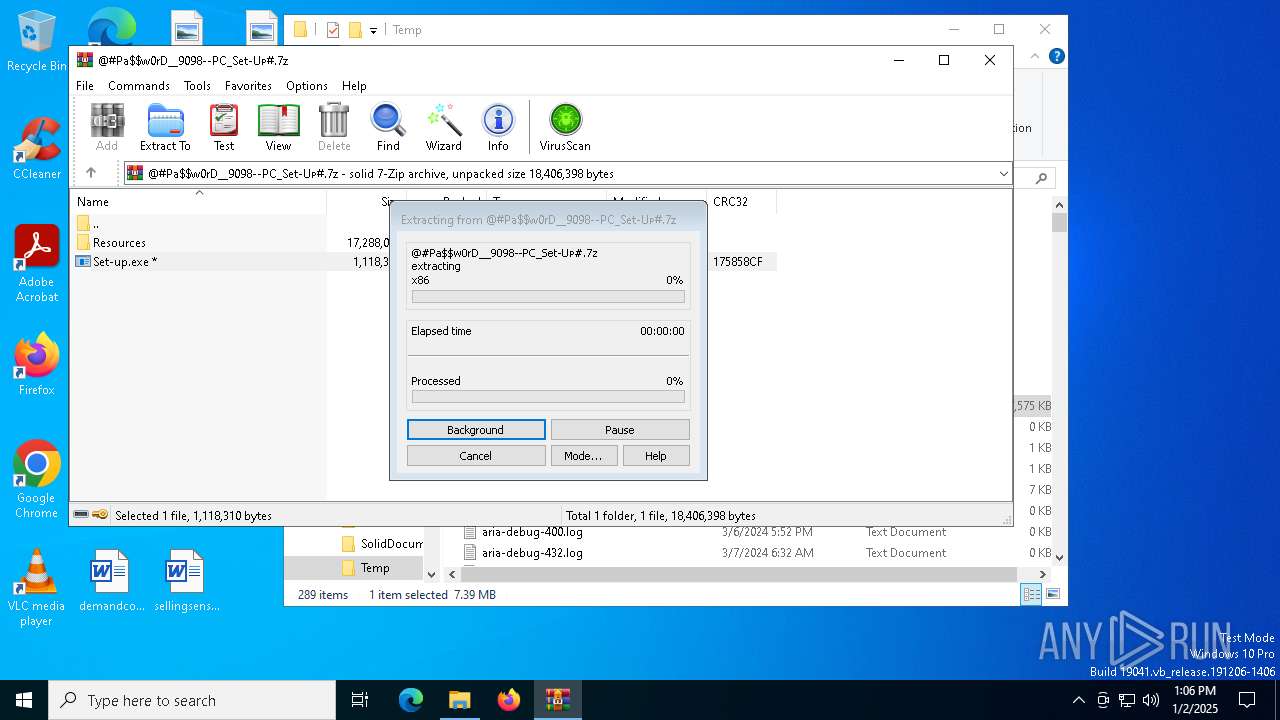
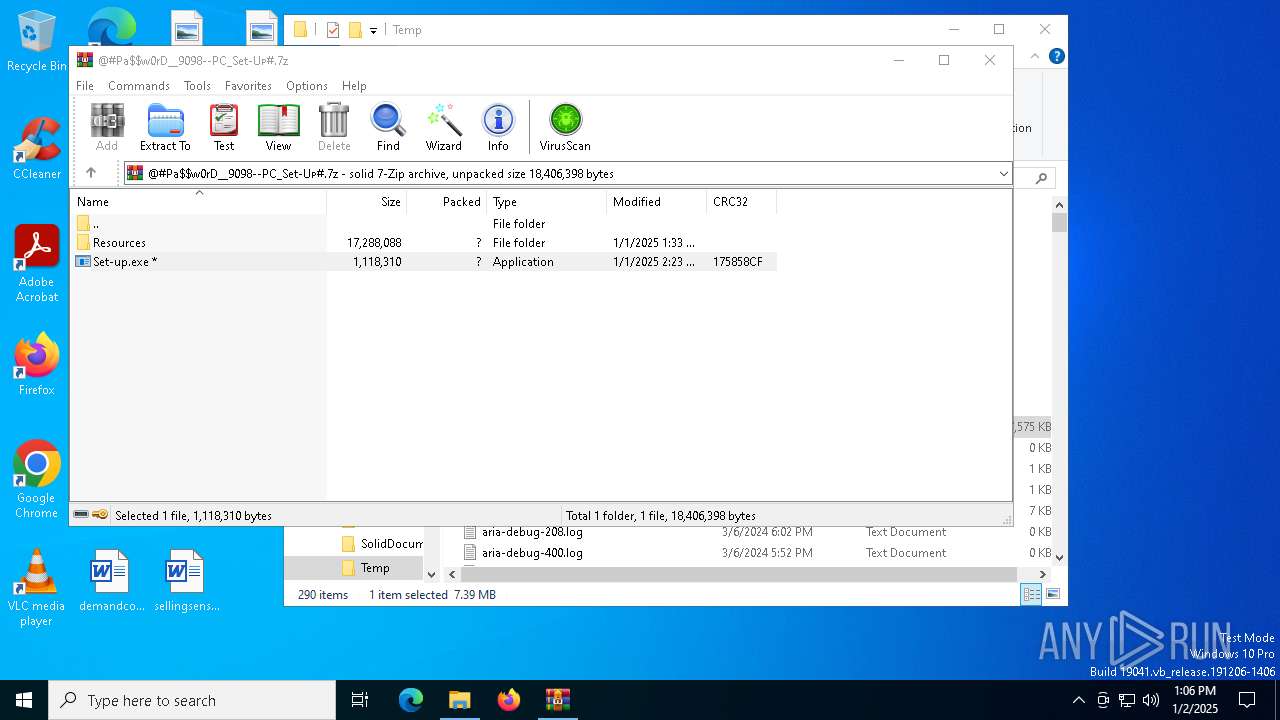
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7044)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7044)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7044)
- Set-up.exe (PID: 7156)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Starts CMD.EXE for commands execution
- Set-up.exe (PID: 7156)
- cmd.exe (PID: 3772)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Executing commands from ".cmd" file
- Set-up.exe (PID: 7156)
Get information on the list of running processes
- cmd.exe (PID: 3772)
- cmd.exe (PID: 5316)
- cmd.exe (PID: 6740)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 1448)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
- cmd.exe (PID: 7100)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3772)
Starts application with an unusual extension
- cmd.exe (PID: 3772)
Application launched itself
- cmd.exe (PID: 3772)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3772)
The executable file from the user directory is run by the CMD process
- Temporary.com (PID: 3620)
Executable content was dropped or overwritten
- Temporary.com (PID: 3620)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 5432)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 4944)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Reads the Windows owner or organization settings
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Uses TIMEOUT.EXE to delay execution
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7044)
The process uses the downloaded file
- WinRAR.exe (PID: 7044)
- Set-up.exe (PID: 7156)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
The sample compiled with english language support
- WinRAR.exe (PID: 7044)
Checks supported languages
- Set-up.exe (PID: 7156)
- Temporary.com (PID: 3620)
- extrac32.exe (PID: 4136)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 5432)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 4944)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
- ColorForgeLib.exe (PID: 3540)
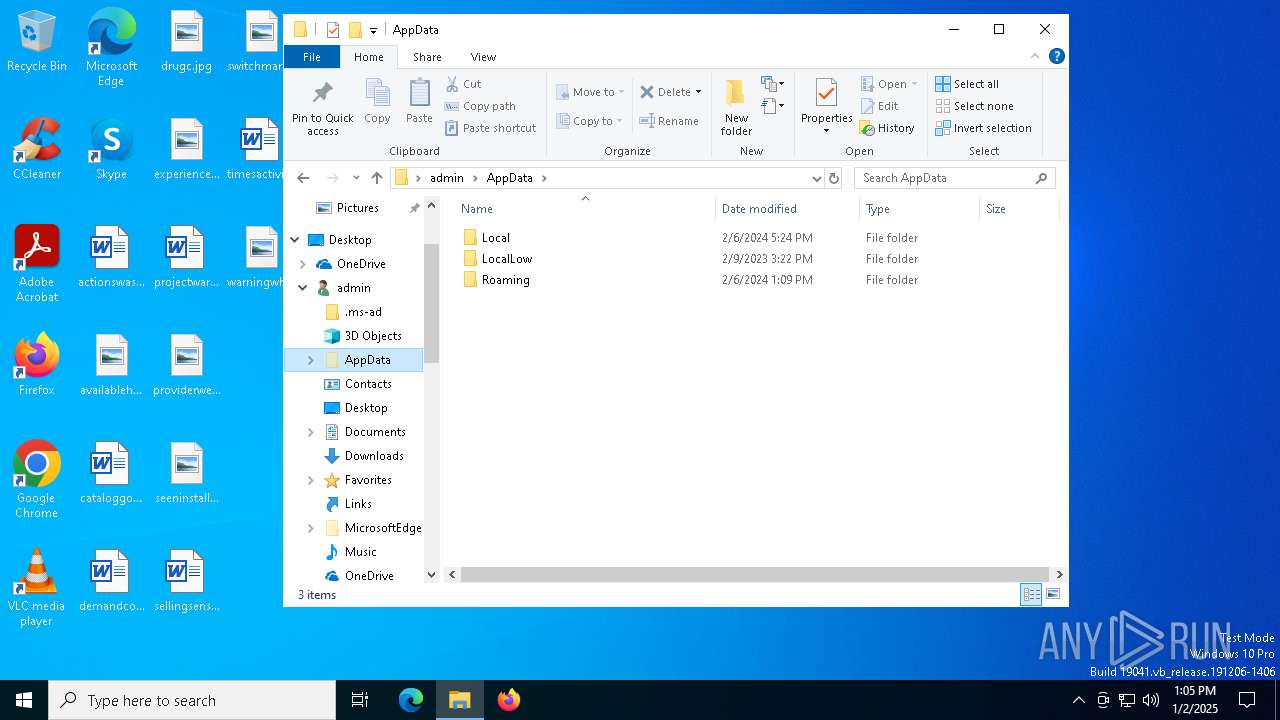
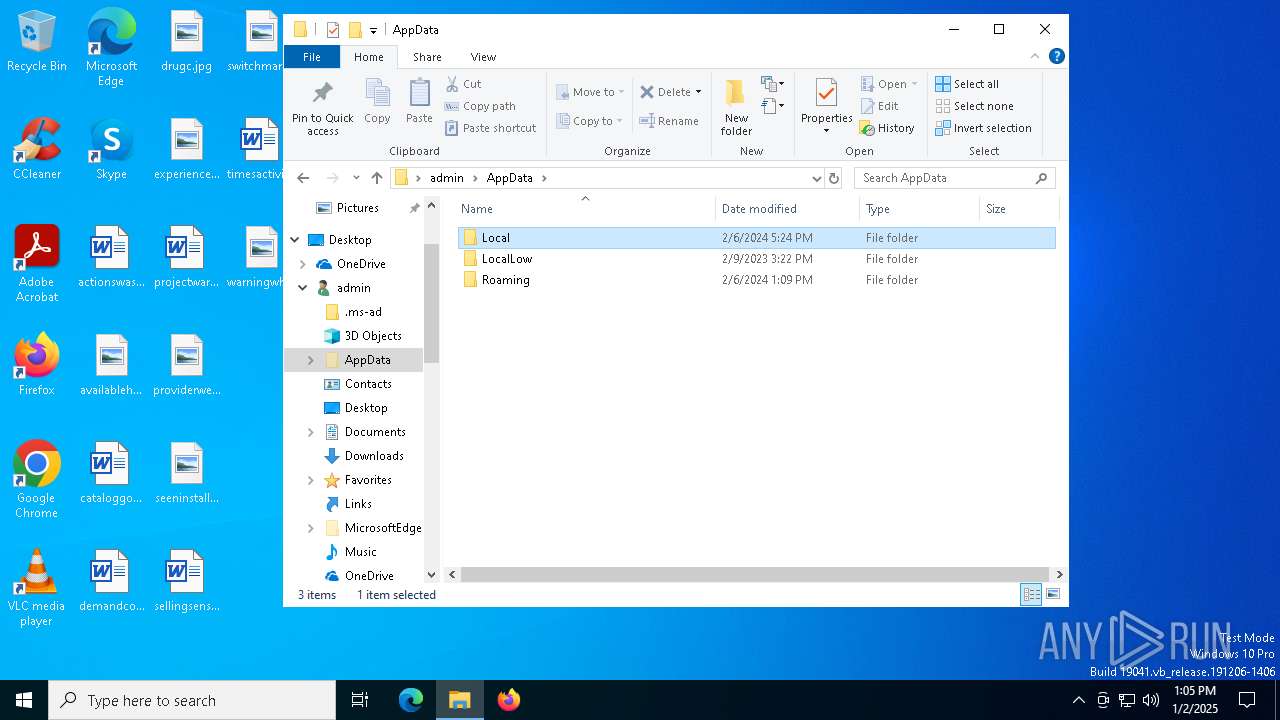
Creates files or folders in the user directory
- Set-up.exe (PID: 7156)
- extrac32.exe (PID: 4136)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Process checks computer location settings
- Set-up.exe (PID: 7156)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
Reads the computer name
- Set-up.exe (PID: 7156)
- extrac32.exe (PID: 4136)
- Temporary.com (PID: 3620)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
- ColorForgeLib.exe (PID: 3540)
Manual execution by a user
- WinRAR.exe (PID: 7044)
Creates a new folder
- cmd.exe (PID: 3296)
Reads mouse settings
- Temporary.com (PID: 3620)
Reads the software policy settings
- Temporary.com (PID: 3620)
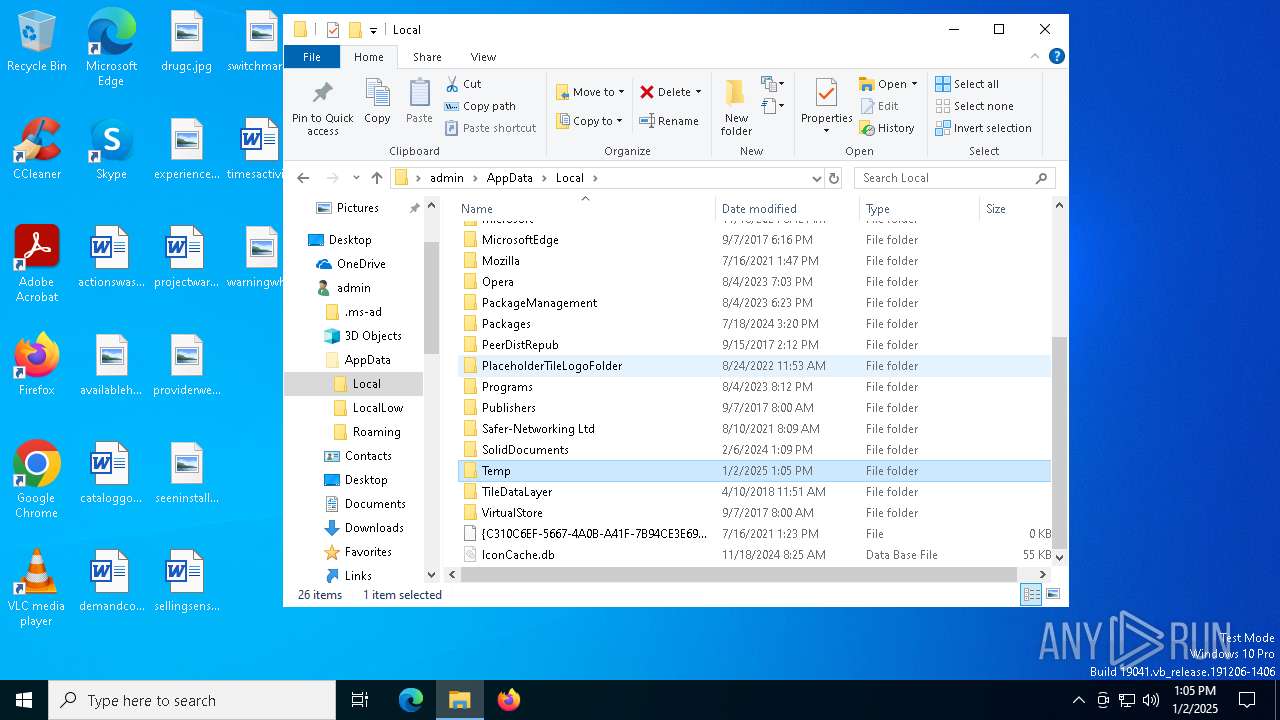
Create files in a temporary directory
- Temporary.com (PID: 3620)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 5432)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.exe (PID: 4944)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6444)
- 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp (PID: 6584)
- ColorForgeLib.exe (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
172
Monitored processes
48
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "cmd.exe" /C tasklist /FI "IMAGENAME eq nswscsvc.exe" /FO CSV /NH | find /I "nswscsvc.exe" | C:\Windows\System32\cmd.exe | — | 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | find /I "avgui.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | find /I "nswscsvc.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | findstr /V "Ny" Metropolitan | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | cmd /c md 87928 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | "C:\Users\admin\AppData\Roaming\ColorStreamLib\ColorForgeLib.exe" | C:\Users\admin\AppData\Roaming\ColorStreamLib\ColorForgeLib.exe | — | 8907Y2GXZXY6YZI1BY1H1Z5NZMODX4.tmp | |||||||||||
User: admin Company: Michael Uno Integrity Level: MEDIUM Description: Notifies process activities Exit code: 0 Version: 0.0.0.4 Modules
| |||||||||||||||
| 3568 | find /I "opssvc.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | tasklist /FI "IMAGENAME eq nswscsvc.exe" /FO CSV /NH | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | Temporary.com w | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\87928\Temporary.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
Total events
5 795
Read events
5 786
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
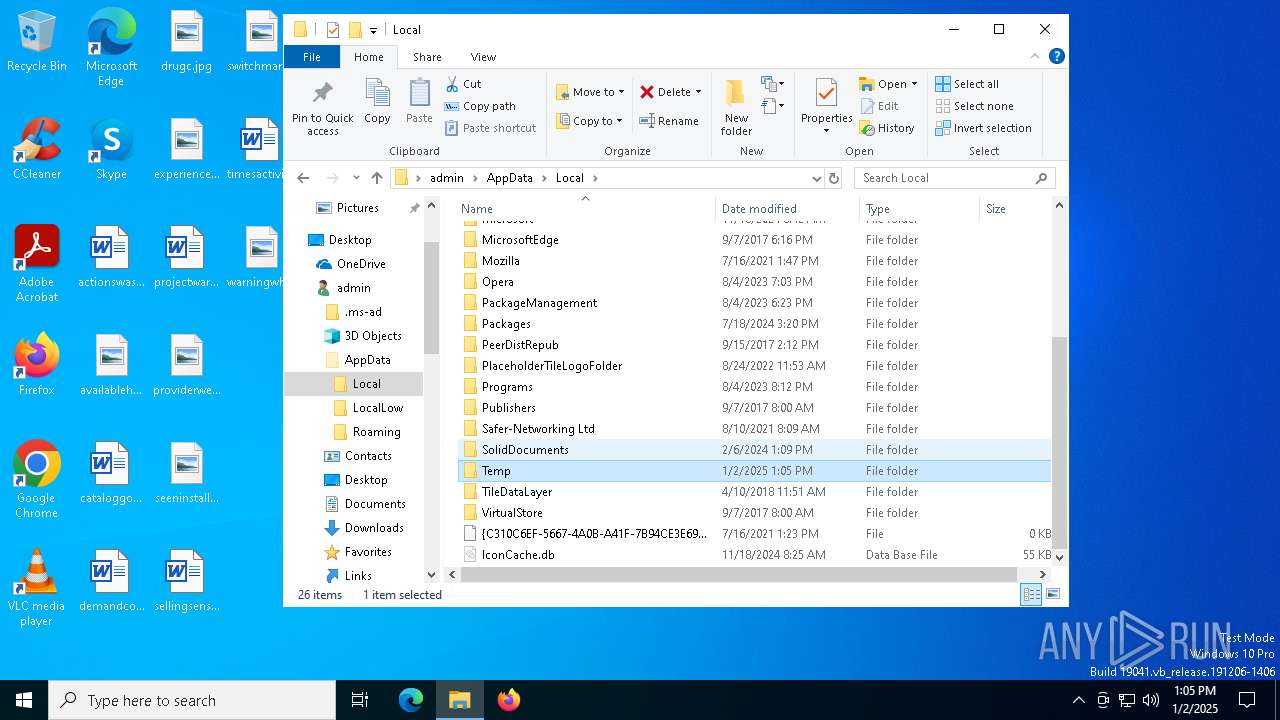
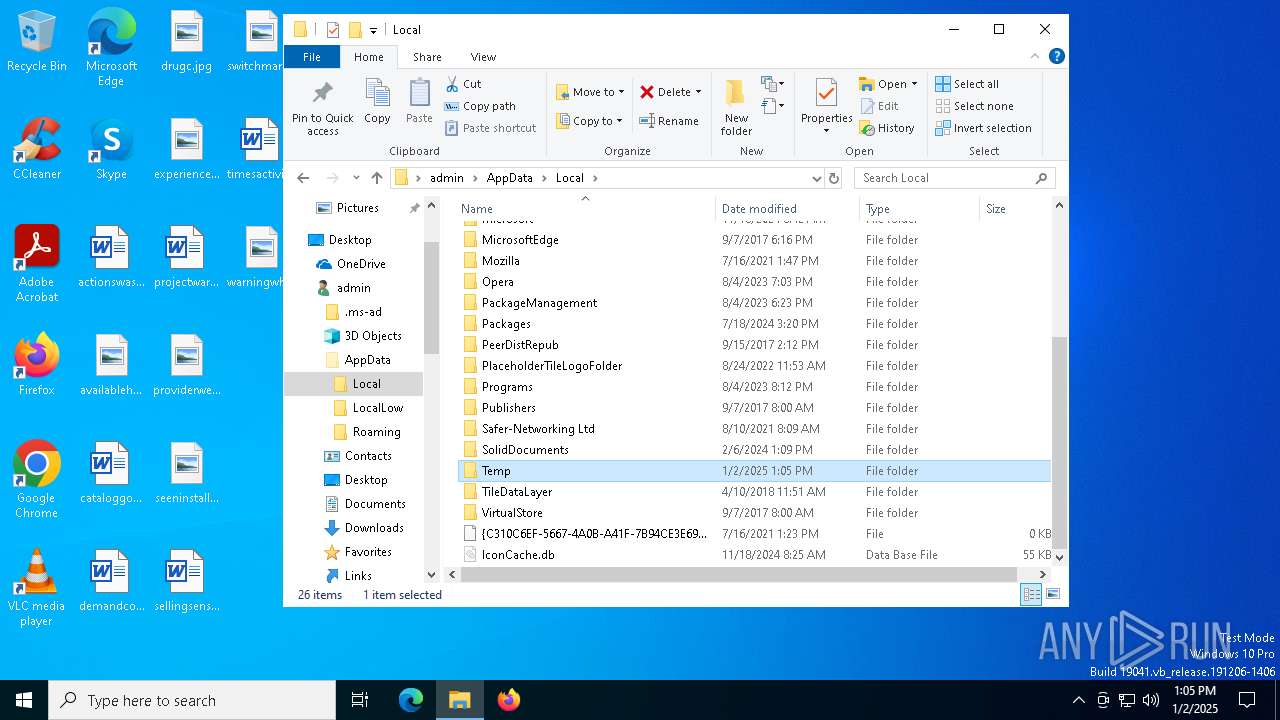
Value: C:\Users\admin\AppData\Local\Temp\@#Pa$w0rD__9098--PC_Set-Uᴘ#.7z | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
20
Suspicious files
41
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\add_007.phpt | text | |
MD5:7B7BD886DB62B3CA4D25E7DF4639F1A5 | SHA256:0FD0F08E8D608BB3C46C3D242E5758BEA99EA0C8EB7C19C87EA598A0475D6E29 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\custom-hg-hello.txt | text | |
MD5:9716121C5042516CA7388FD526B81DF2 | SHA256:1058A99BD62D4B686C2F4602ACB85EAE6A5B6B05C2202150585A6E98CB1B2797 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\code6.txt | text | |
MD5:B9BABB266F182C22A4E2E80680B07B72 | SHA256:51FAB753A2F49BAB7B3D0745E27771DD9D58D5A5DD60C81390AE878FA95E094E | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\todo.txt | text | |
MD5:007FCD32BBF72F6D0DB5C437574D3159 | SHA256:14FF2B92D86CF32A4ACE3930F7871E12E3B4089297E2B0F5D8FA190D5E354765 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\work_use_issue55952.txt | text | |
MD5:A6D8767473FC6131646148BDD488B3B4 | SHA256:CCE99E4949E725F7CC51553E24A1F68D78F6D7260F4F8885EAF128EE30D75C73 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\const.h | text | |
MD5:156515CAFA17466909E97CC290B5BB4E | SHA256:E693FB91A653562E13A09EC404A80C76DBC2E674EC933BC63D751181032A9928 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\example.com_noroot_v1.0.1.txt | text | |
MD5:7288D609B53D947433D19929DC8A30F0 | SHA256:595975BC53A4F9094BB2793DD82BF51E80EBAF2D6B4C31D56FE77C0D9DB7533C | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\test_vendor.txt | text | |
MD5:80AEC646E662ECDB8F7677B93F39AAB7 | SHA256:5912F1BA252BAC927720D0342E63B16A7E273B63E097BB3D1C8E68F9B0703742 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\msg_30.txt | binary | |
MD5:C045EE85A52D1967D69DE8A9614085BD | SHA256:C35DA53F1C5BF7639417AECDE7052DB57700828FCFF4600A81751AE13BAC03A8 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7044.47302\Resources\Data\Config\mod_run_issue52331.txt | text | |
MD5:DE6B86D9A5E674079E7AC7E77010B52D | SHA256:D84B2FFA9261A15CA009C8E24DD7919D554811A03277F92A182450CD423DAC95 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
42
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
732 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
2600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
732 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
732 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
732 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
— | — | 104.126.37.147:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| unknown |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |