| File name: | Ghostbruter.exe |
| Full analysis: | https://app.any.run/tasks/2c9becc7-80d7-49a6-a90a-5e91c4a206cc |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | November 29, 2020, 20:52:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 41DE32D3BC50E4E40A837B37188ADCD0 |
| SHA1: | D9FAB719964092AB7F48CC95EF0A89264CE4F8DE |
| SHA256: | 64F8FF1AA337FD27A4560929BC5CC76CB0C43AAAD4DD771427C742FBC5531CAE |
| SSDEEP: | 24576:rz1qxlLkCi4+syh3o1un9KpIVjEtEBH2qa5vvc4HpMy:f0bLkCR+TYuSIVj/v03c4p |
MALICIOUS
Drops executable file immediately after starts
- Ghostbruter.exe (PID: 2936)
ORCUS was detected
- fsg.exe (PID: 2820)
- Orcus.exe (PID: 3164)
- Orcus.exe (PID: 3220)
- WindowsWatchdog.exe (PID: 3648)
Application was dropped or rewritten from another process
- fsg.exe (PID: 2820)
- WindowsInput.exe (PID: 3176)
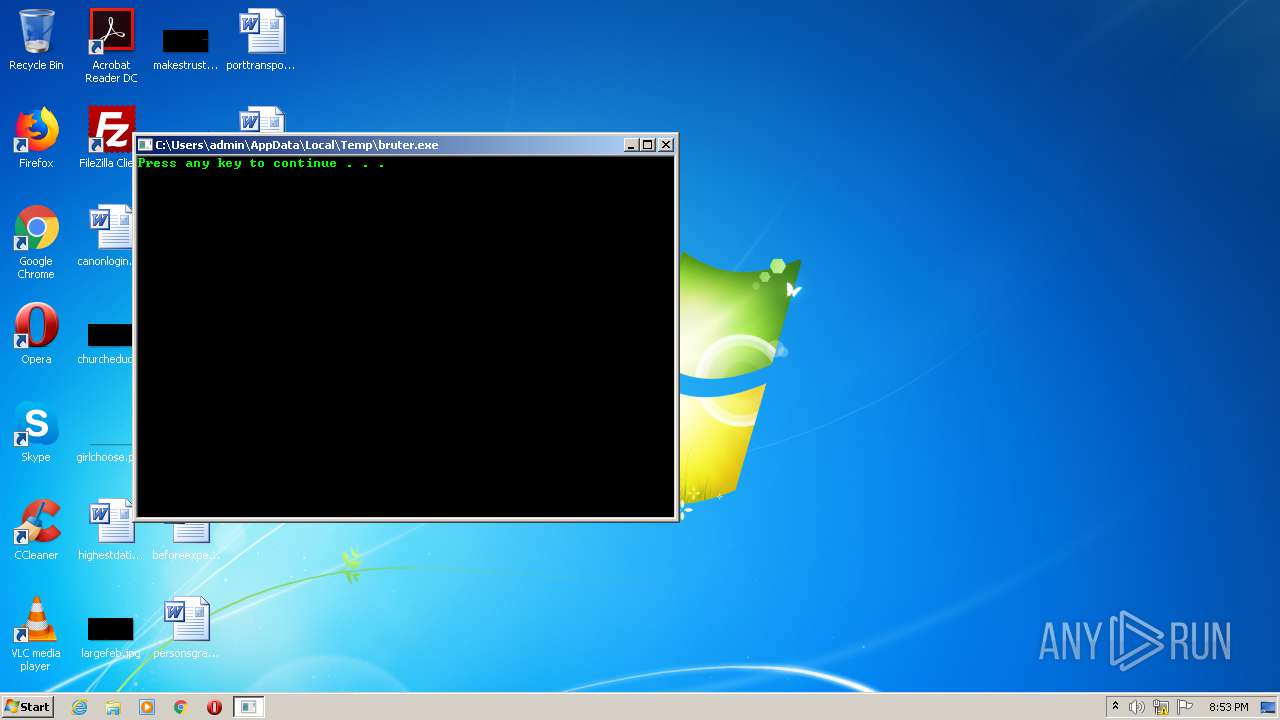
- bruter.exe (PID: 2996)
- WindowsInput.exe (PID: 3328)
- Orcus.exe (PID: 3220)
- WindowsWatchdog.exe (PID: 3648)
- WindowsWatchdog.exe (PID: 2548)
- Orcus.exe (PID: 3164)
Changes the autorun value in the registry
- Orcus.exe (PID: 3164)
Loads the Task Scheduler COM API
- Orcus.exe (PID: 3164)
Changes settings of System certificates
- Orcus.exe (PID: 3164)
SUSPICIOUS
Starts CMD.EXE for commands execution
- bruter.exe (PID: 2996)
Executable content was dropped or overwritten
- Ghostbruter.exe (PID: 2936)
- Orcus.exe (PID: 3164)
- fsg.exe (PID: 2820)
Drops a file with a compile date too recent
- Ghostbruter.exe (PID: 2936)
- fsg.exe (PID: 2820)
Creates files in the Windows directory
- fsg.exe (PID: 2820)
- WindowsInput.exe (PID: 3328)
Creates files in the program directory
- fsg.exe (PID: 2820)
Creates a directory in Program Files
- fsg.exe (PID: 2820)
Starts itself from another location
- fsg.exe (PID: 2820)
Executed via Task Scheduler
- Orcus.exe (PID: 3220)
Executed as Windows Service
- WindowsInput.exe (PID: 3176)
Drops a file that was compiled in debug mode
- Orcus.exe (PID: 3164)
- fsg.exe (PID: 2820)
Reads Environment values
- Orcus.exe (PID: 3164)
Application launched itself
- WindowsWatchdog.exe (PID: 3648)
Creates files in the user directory
- Orcus.exe (PID: 3164)
INFO
Reads settings of System Certificates
- Orcus.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:31 17:09:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x315d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2007 15:09:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Mar-2007 15:09:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005BBA | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47701 |
.rdata | 0x00007000 | 0x000011F0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27568 |
.data | 0x00009000 | 0x000260D4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15843 |
.ndata | 0x00030000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x000215C8 | 0x00021600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.19967 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.97858 | 35745 | UNKNOWN | English - United States | RT_ICON |
2 | 4.95014 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 5.11372 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 5.23371 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.42345 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.75083 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
51
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1596 | mode con: cols=67 lines=30 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Roaming\WindowsWatchdog.exe" /watchProcess "C:\Program Files\Orcus\Orcus.exe" 3164 "/protectFile" | C:\Users\admin\AppData\Roaming\WindowsWatchdog.exe | — | WindowsWatchdog.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\Ghostbruter.exe" | C:\Users\admin\AppData\Local\Temp\Ghostbruter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\AppData\Local\Temp\fsg.exe" | C:\Users\admin\AppData\Local\Temp\fsg.exe | Ghostbruter.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Temp\Ghostbruter.exe" | C:\Users\admin\AppData\Local\Temp\Ghostbruter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\bruter.exe" | C:\Users\admin\AppData\Local\Temp\bruter.exe | — | Ghostbruter.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Orcus\Orcus.exe" | C:\Program Files\Orcus\Orcus.exe | fsg.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3176 | "C:\Windows\system32\WindowsInput.exe" | C:\Windows\system32\WindowsInput.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Integrity Level: SYSTEM Description: Windows Input Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Orcus\Orcus.exe" | C:\Program Files\Orcus\Orcus.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3328 | "C:\Windows\system32\WindowsInput.exe" --install | C:\Windows\system32\WindowsInput.exe | — | fsg.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Windows Input Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
Total events
1 217
Read events
1 183
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2936) Ghostbruter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2936) Ghostbruter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3328) WindowsInput.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application |
| Operation: | write | Name: | AutoBackupLogFiles |
Value: 0 | |||
| (PID) Process: | (3328) WindowsInput.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\WindowsInput |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework\v4.0.30319\EventLogMessages.dll | |||
| (PID) Process: | (3328) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3328) WindowsInput.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2820) fsg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2820) fsg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3164) Orcus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | important |
Value: "C:\Program Files\Orcus\Orcus.exe" | |||
| (PID) Process: | (3164) Orcus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
4
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\CabBADD.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\TarBADE.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\CabBAFF.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\TarBB00.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\CabBC49.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\TarBC4A.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\CabBD06.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\TarBD07.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\CabBD18.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\TarBD19.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | Orcus.exe | GET | 304 | 67.27.235.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3164 | Orcus.exe | GET | 200 | 67.27.235.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | Orcus.exe | 67.27.235.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3164 | Orcus.exe | 193.161.193.99:39894 | skid81-39894.portmap.io | OOO Bitree Networks | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
skid81-39894.portmap.io |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
3164 | Orcus.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 392 |
3164 | Orcus.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) |
1 ETPRO signatures available at the full report