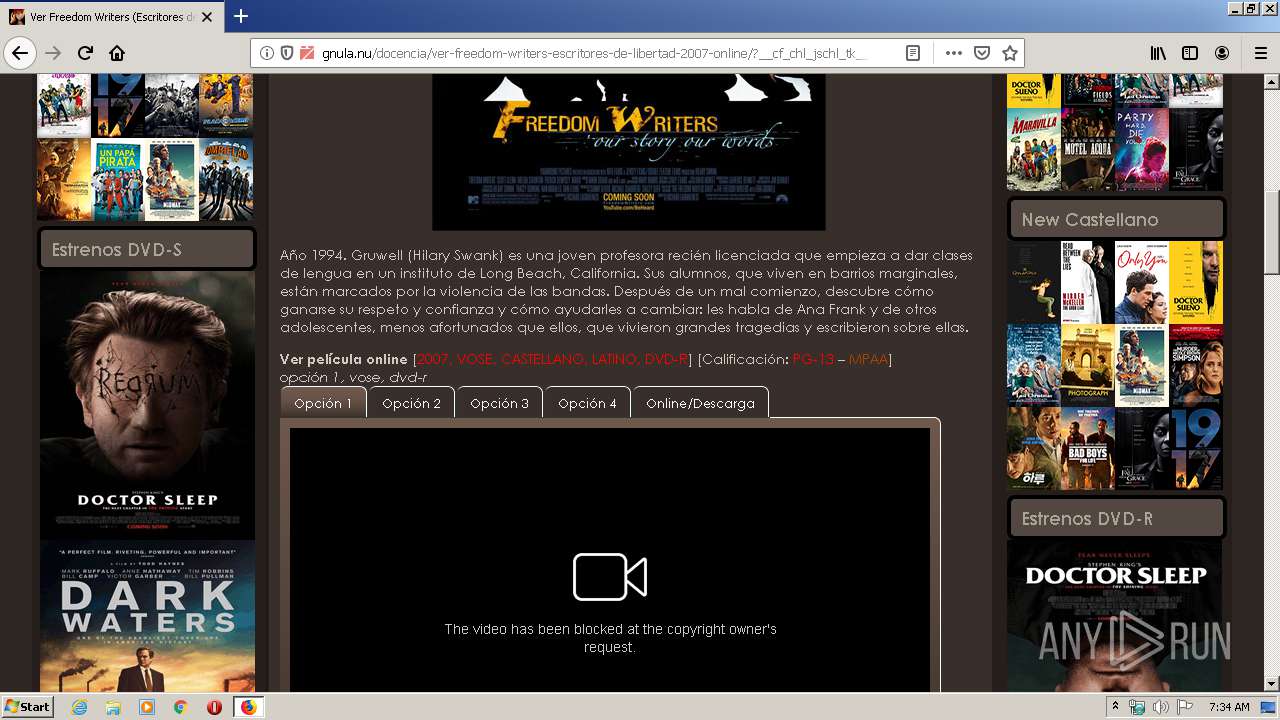
| URL: | http://gnula.nu/docencia/ver-freedom-writers-escritores-de-libertad-2007-online/ |
| Full analysis: | https://app.any.run/tasks/76a48d06-386f-4f96-b1fd-87eb2c07380e |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | January 27, 2020, 07:34:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AA758F4CF4DE8D200090782C6EF0C2BF |
| SHA1: | 66138E83D7DEA9AB99005F44355DA406BE7F4429 |
| SHA256: | 64E44AD1184F1858E0A7F9EA5EE92F0F6CAEC4E273350E718A012A92903ABA0B |
| SSDEEP: | 3:N1KZL9QBnANy0QMAW87XyBIX/B:C4qNy0QMA5WBe |
MALICIOUS
COINMINER was detected
- firefox.exe (PID: 2640)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2640)
INFO
Reads CPU info
- firefox.exe (PID: 2640)
Reads Internet Cache Settings
- firefox.exe (PID: 2640)
- firefox.exe (PID: 2636)
Application launched itself
- firefox.exe (PID: 2640)
Creates files in the user directory
- firefox.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://gnula.nu/docencia/ver-freedom-writers-escritores-de-libertad-2007-online/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.13.1641941694\370028539" -childID 2 -isForBrowser -prefsHandle 2856 -prefMapHandle 2860 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 2864 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.3.702834255\710548357" -childID 1 -isForBrowser -prefsHandle 1724 -prefMapHandle 1720 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 1744 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://gnula.nu/docencia/ver-freedom-writers-escritores-de-libertad-2007-online/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.20.703282185\2132112935" -childID 3 -isForBrowser -prefsHandle 3720 -prefMapHandle 3724 -prefsLen 7129 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 3736 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3872 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2640.0.1341437325\876402343" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2640 "\\.\pipe\gecko-crash-server-pipe.2640" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
2 376
Read events
2 371
Write events
5
Delete events
0
Modification events
| (PID) Process: | (660) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 1B8DB8ED08000000 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 61A7BBED08000000 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2640) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
390
Text files
126
Unknown types
210
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2640 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
168
TCP/UDP connections
230
DNS requests
414
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | firefox.exe | GET | — | 104.26.0.198:80 | http://gnula.nu/.well-known/http-opportunistic | US | — | — | whitelisted |
2640 | firefox.exe | GET | — | 104.26.0.198:80 | http://gnula.nu/docencia/ver-freedom-writers-escritores-de-libertad-2007-online/ | US | — | — | whitelisted |
2640 | firefox.exe | GET | — | 104.26.0.198:80 | http://gnula.nu/.well-known/http-opportunistic | US | — | — | whitelisted |
2640 | firefox.exe | GET | 200 | 104.26.0.198:80 | http://gnula.nu/favicon.ico | US | — | — | whitelisted |
2640 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2640 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2640 | firefox.exe | GET | 302 | 172.217.22.35:80 | http://www.google.es/cse/brand?form=cse-search-box&lang=es | US | html | 260 b | whitelisted |
2640 | firefox.exe | GET | 200 | 104.26.0.198:80 | http://gnula.nu/wp-content/themes/charcoal2/scroller.js | US | binary | 826 b | whitelisted |
2640 | firefox.exe | POST | 200 | 104.26.0.198:80 | http://gnula.nu/docencia/ver-freedom-writers-escritores-de-libertad-2007-online/?__cf_chl_jschl_tk__=ca4d4d39f3c2901574d587edc3ac4526a8e2ce31-1580110460-0-AdVW7VT4iL1L9brQ90ZoqF3ZZeCH8CUoHjPCQDuiu4YBVRFZGtQzXD1AL2mcJjDy7KiOflmfe95q-zwLe6L6U6FGuMKPtXjjVOnR1Nd_EUhB5VkIAvUPgNKmnlPnNuinIyFZF1Nfe9eMiBSQQiZyZLnxoqEifpVPEN5vV9cqqxcxt5azC8gS8VBgx4NEi7bkUIX6QGWTZcEqrhJb59kjHJF5UhtfFGn5IJC2o06jnwzQHgHp6k4mJgd9jcibDi2QxLeaNJVT0A2JLE4wKc5Gag1RAdOx1KAYCVJmWhbXYPVR4qD4k5NAJGg43Z80PSTetO9O7UJy7-Qgf27DdpN21RFX_hfJNgpWqhCsCtmX-GgZ | US | html | 27.7 Kb | whitelisted |
2640 | firefox.exe | GET | 200 | 104.26.0.198:80 | http://gnula.nu/wp-content/themes/charcoal2/style.css | US | text | 5.85 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | firefox.exe | 104.26.0.198:80 | gnula.nu | Cloudflare Inc | US | suspicious |
2640 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2640 | firefox.exe | 35.164.109.147:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2640 | firefox.exe | 52.33.18.205:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2640 | firefox.exe | 13.226.145.99:443 | snippets.cdn.mozilla.net | — | US | unknown |
2640 | firefox.exe | 104.26.0.198:443 | gnula.nu | Cloudflare Inc | US | suspicious |
2640 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2640 | firefox.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2640 | firefox.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2640 | firefox.exe | 13.226.145.45:443 | firefox.settings.services.mozilla.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gnula.nu |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
www.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2640 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
3 ETPRO signatures available at the full report