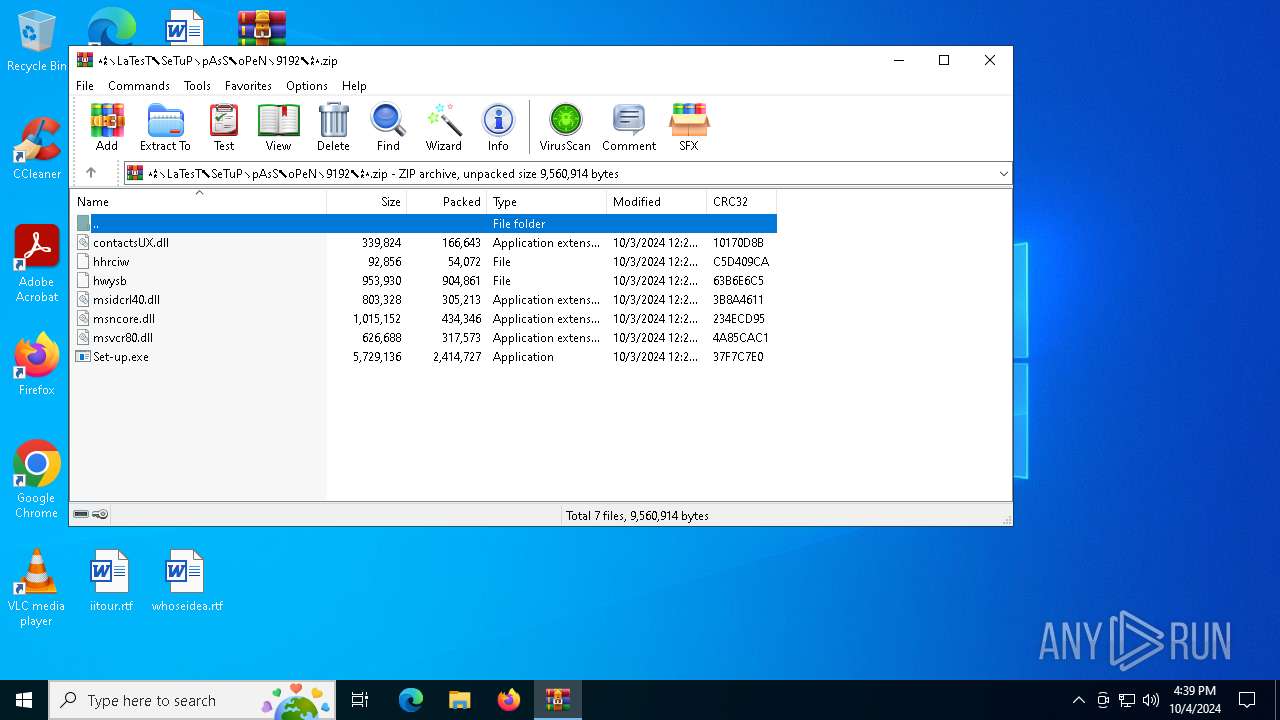
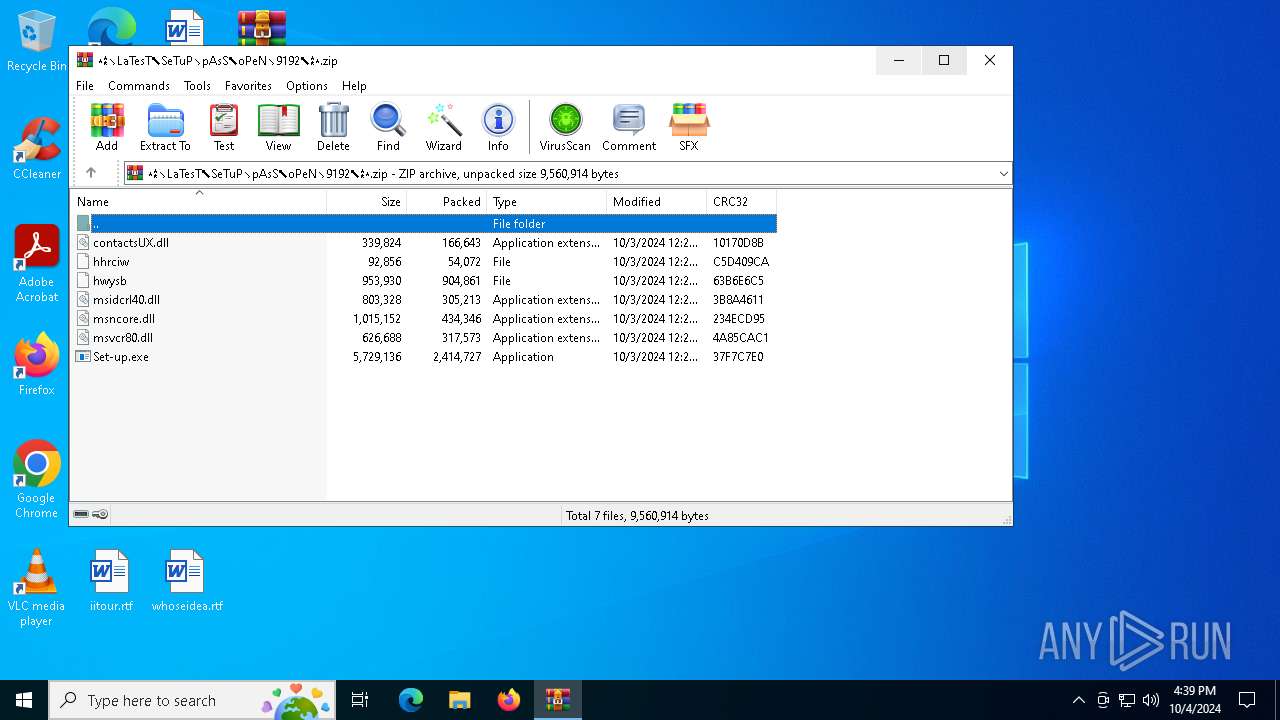
| File name: | ⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎.zip |
| Full analysis: | https://app.any.run/tasks/0b2fc2cb-c89f-4bd3-b6ac-3e90bf4ec7ab |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 04, 2024, 16:39:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 018AD89A6DC634E4F8F682AD12086176 |
| SHA1: | 31ACAEBFBAB52C3FCD30850C2F74094EAD1FAACC |
| SHA256: | 64E3037899D9970270F908FFB95FA36D8EDFFCFF5DFEAD259EDCDEFFE7E15674 |
| SSDEEP: | 98304:qI74jiMKxKdo4Z15qhCjjOhBn7XGcuu6wN8gNQP2t0fSfZuDaB7yNvKOaSDzw6eH:5JtGfu1 |
MALICIOUS
Stealers network behavior
- SearchIndexer.exe (PID: 2028)
LUMMA has been detected (SURICATA)
- SearchIndexer.exe (PID: 2028)
SUSPICIOUS
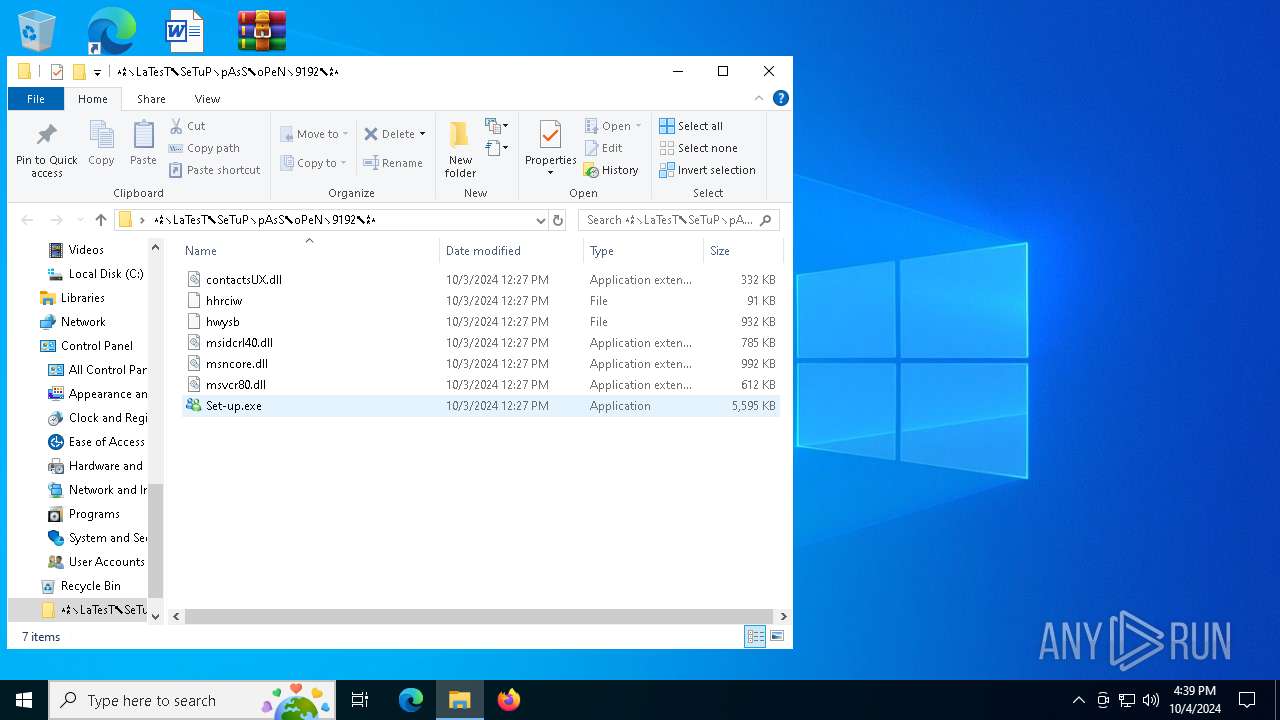
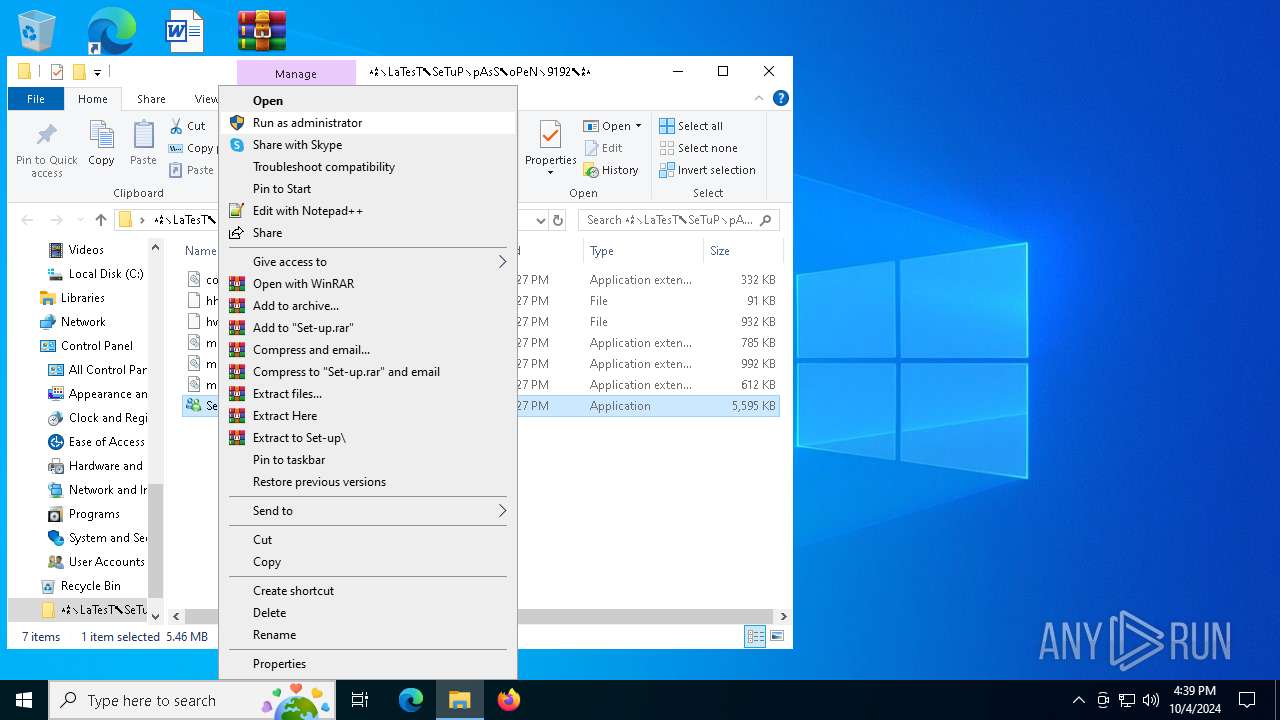
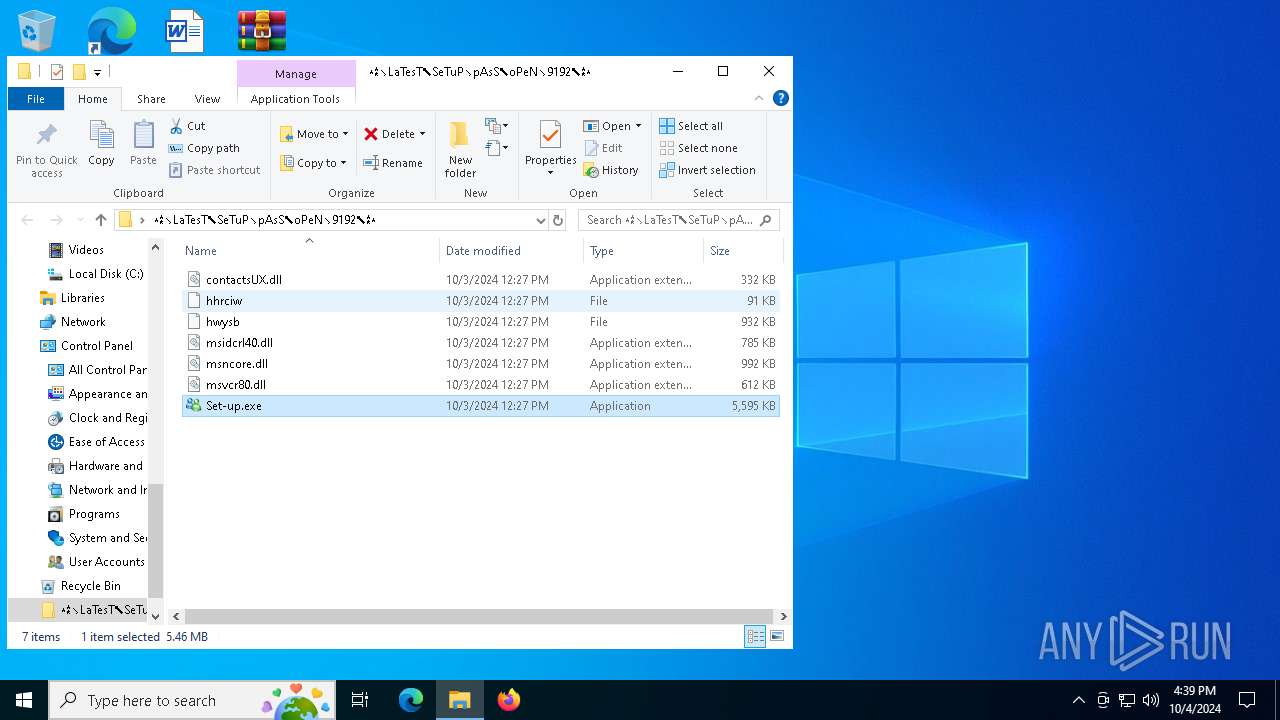
Starts a Microsoft application from unusual location
- Set-up.exe (PID: 6056)
Process drops legitimate windows executable
- Set-up.exe (PID: 6056)
- WinRAR.exe (PID: 5028)
Executable content was dropped or overwritten
- Set-up.exe (PID: 6056)
Starts application with an unusual extension
- Set-up.exe (PID: 6056)
The process drops C-runtime libraries
- Set-up.exe (PID: 6056)
INFO
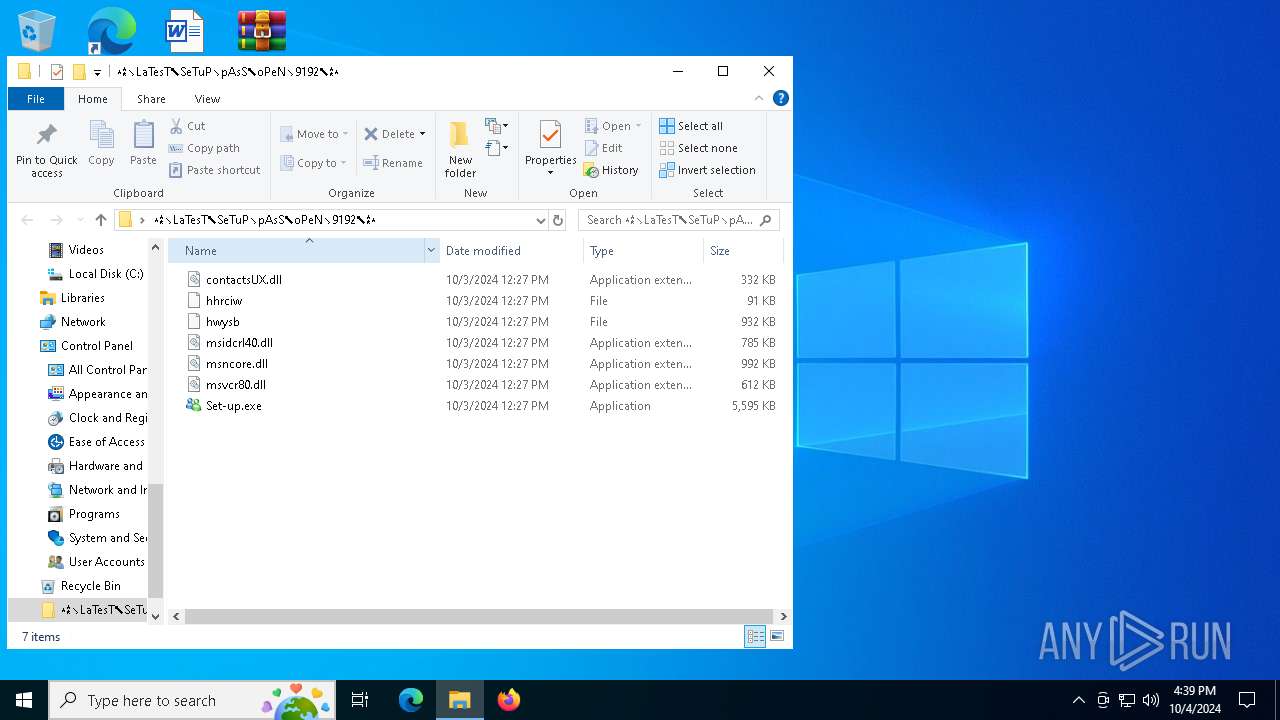
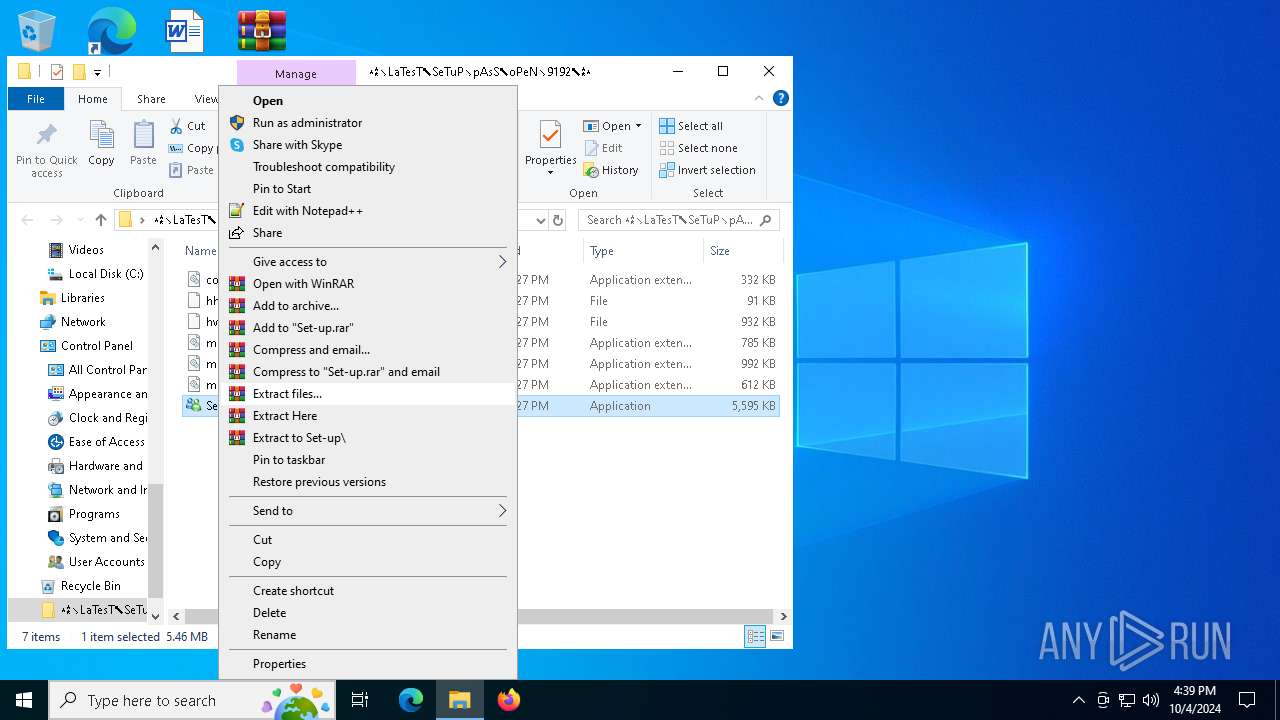
Manual execution by a user
- Set-up.exe (PID: 6056)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5028)
The process uses the downloaded file
- WinRAR.exe (PID: 5028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:03 14:27:54 |
| ZipCRC: | 0x37f7c7e0 |
| ZipCompressedSize: | 2414727 |
| ZipUncompressedSize: | 5729136 |
| ZipFileName: | Set-up.exe |
Total processes
136
Monitored processes
6
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2028 | C:\WINDOWS\SysWOW64\SearchIndexer.exe | C:\Windows\SysWOW64\SearchIndexer.exe | more.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3808 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | Set-up.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
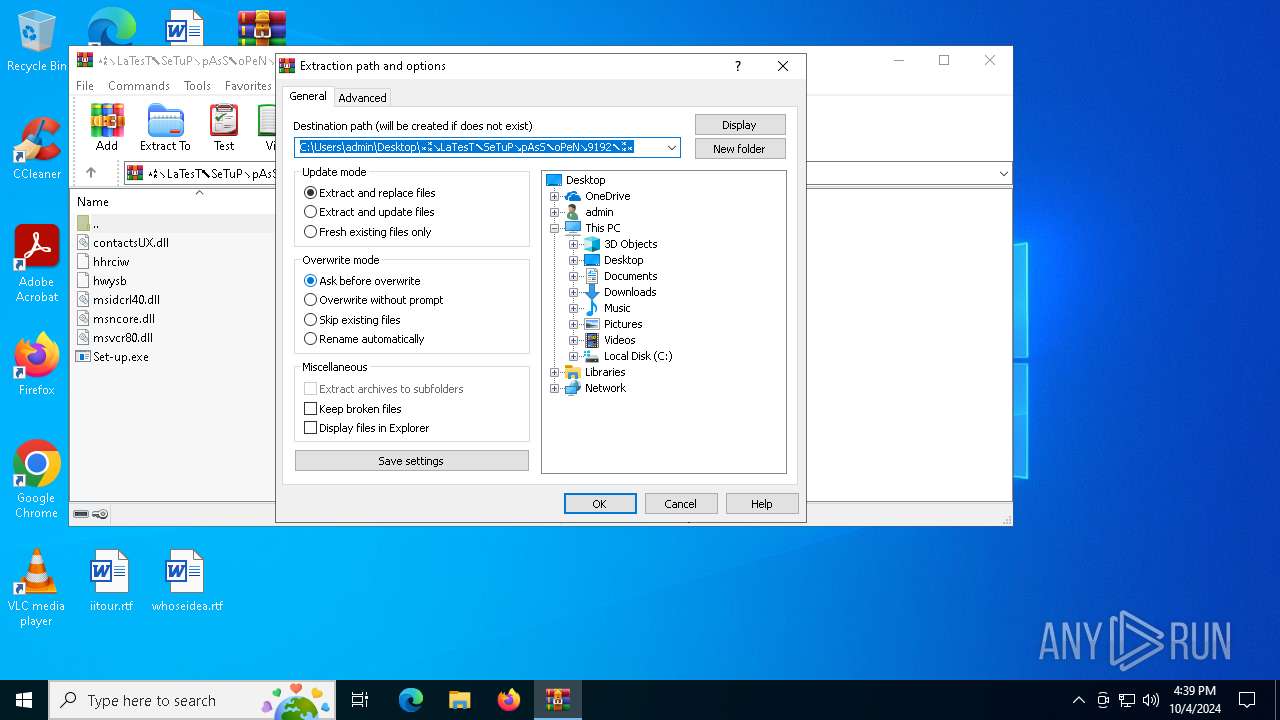
| 5028 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5920 | C:\Users\admin\AppData\Roaming\load\MHAUDZXRPVFMPPDWRGZSEDU\StrCmp.exe | C:\Users\admin\AppData\Roaming\load\MHAUDZXRPVFMPPDWRGZSEDU\StrCmp.exe | — | Set-up.exe | |||||||||||
User: admin Company: aaa Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6056 | "C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\Set-up.exe" | C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\Set-up.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Live Messenger Exit code: 1 Version: 8.5.1235.0517 Modules
| |||||||||||||||
Total events
2 114
Read events
2 077
Write events
23
Delete events
14
Modification events
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎.zip | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (5028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
10
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3808 | more.com | C:\Users\admin\AppData\Local\Temp\ofkwegigwigeym | — | |
MD5:— | SHA256:— | |||
| 5028 | WinRAR.exe | C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\msncore.dll | executable | |
MD5:DEAA38A71C85D2F9D4BA71343D1603DA | SHA256:1DC120F34B294E964EEE949C4D1EBD9C271715D46B38AE082FEC2F1D505E8D65 | |||
| 6056 | Set-up.exe | C:\Users\admin\AppData\Roaming\load\hhrciw | binary | |
MD5:49A2C569B16ACB07EC1E784A4E9D19C9 | SHA256:01D544C81180F4EA226E2D93841D246355B9DA0F9EF76A232D7934FF085844AD | |||
| 6056 | Set-up.exe | C:\Users\admin\AppData\Roaming\load\msidcrl40.dll | executable | |
MD5:93DFF0021CEFCB11A18BA7DE2EDFCAC9 | SHA256:22B7EC38D88C7B7CBF0618452313D3B24DCD0D3C4185FA7841E758636BDFC350 | |||
| 5028 | WinRAR.exe | C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\hhrciw | binary | |
MD5:49A2C569B16ACB07EC1E784A4E9D19C9 | SHA256:01D544C81180F4EA226E2D93841D246355B9DA0F9EF76A232D7934FF085844AD | |||
| 5028 | WinRAR.exe | C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\msvcr80.dll | executable | |
MD5:43143ABB001D4211FAB627C136124A44 | SHA256:CB8928FF2FAF2921B1EDDC267DCE1BB64E6FEE4D15B68CD32588E0F3BE116B03 | |||
| 6056 | Set-up.exe | C:\Users\admin\AppData\Roaming\load\msvcr80.dll | executable | |
MD5:43143ABB001D4211FAB627C136124A44 | SHA256:CB8928FF2FAF2921B1EDDC267DCE1BB64E6FEE4D15B68CD32588E0F3BE116B03 | |||
| 5028 | WinRAR.exe | C:\Users\admin\Desktop\⁎⁑↘LaTesT⬉SeTuP↘pAsS⬉oPeN↘9192⬉⁑⁎\msidcrl40.dll | executable | |
MD5:93DFF0021CEFCB11A18BA7DE2EDFCAC9 | SHA256:22B7EC38D88C7B7CBF0618452313D3B24DCD0D3C4185FA7841E758636BDFC350 | |||
| 6056 | Set-up.exe | C:\Users\admin\AppData\Roaming\load\MHAUDZXRPVFMPPDWRGZSEDU\StrCmp.exe | executable | |
MD5:916D7425A559AAA77F640710A65F9182 | SHA256:118DE01FB498E81EAB4ADE980A621AF43B52265A9FCBAE5DEDC492CDF8889F35 | |||
| 6056 | Set-up.exe | C:\Users\admin\AppData\Roaming\load\msncore.dll | executable | |
MD5:DEAA38A71C85D2F9D4BA71343D1603DA | SHA256:1DC120F34B294E964EEE949C4D1EBD9C271715D46B38AE082FEC2F1D505E8D65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
47
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4820 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2980 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2980 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7108 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7108 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4820 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4820 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2028 | SearchIndexer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |