| File name: | Confirm!!.exe |
| Full analysis: | https://app.any.run/tasks/1e9de9d8-407c-45fa-ac1f-b2be67164a9b |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 23, 2023, 16:23:02 |
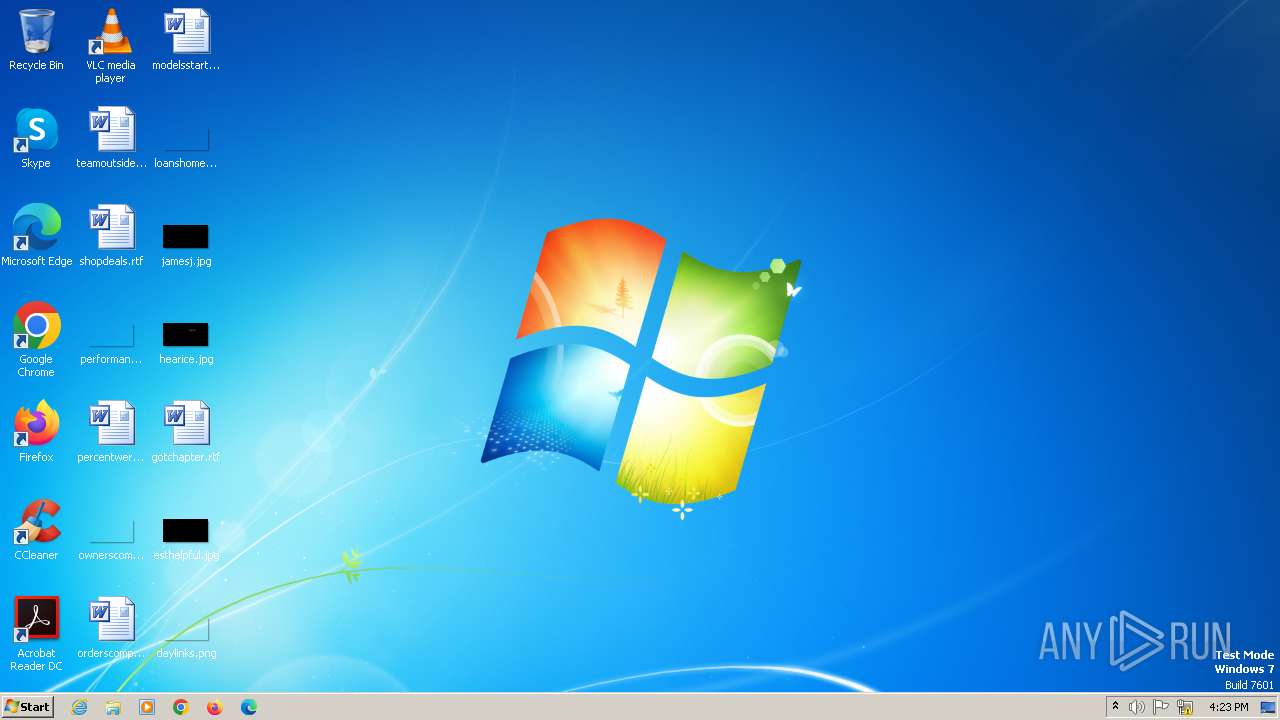
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A5D8E292694BEAC904AD6E84BC98BA32 |
| SHA1: | 3594D799F68699420E21EF12769872C4DD8721AC |
| SHA256: | 64D39C5CA1ACFEE70E9E783AE33212A0F271BA323077A7C2B0A135706E3E37C0 |
| SSDEEP: | 24576:LmSZuCOpcC9pnmW3G+44+xwID1qJ43Cx2ugO3+IlzTt0WyTTb:SSZuCOpcC9pnmW3G+43LD1qJ4302ugOa |
MALICIOUS
FORMBOOK has been detected (YARA)
- NAPSTAT.EXE (PID: 1088)
SUSPICIOUS
Starts CMD.EXE for commands execution
- NAPSTAT.EXE (PID: 1088)
Application launched itself
- Confirm!!.exe (PID: 2336)
INFO
Checks supported languages
- Confirm!!.exe (PID: 2336)
- Confirm!!.exe (PID: 712)
Reads the computer name
- Confirm!!.exe (PID: 2336)
- Confirm!!.exe (PID: 712)
Manual execution by a user
- NAPSTAT.EXE (PID: 1088)
Reads the machine GUID from the registry
- Confirm!!.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(1088) NAPSTAT.EXE
C2www.qfs-capital.com/he2a/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)connectioncompass.store
zekicharge.com
dp77.shop
guninfo.guru
mamaeconomics.net
narcisme.coach
redtopassociates.com
ezezn.com
theoregondog.com
pagosmultired.online
emsculptcenterofne.com
meet-friends.online
pf326.com
wealthjigsaw.xyz
arsajib.com
kickassholdings.online
avaturre.biz
dtslogs.com
lb92.tech
pittalam.com
cyberlegion.group
24eu-ru-startup.xyz
theaustralianbrisketboard.com
bavrnimn.site
xn--groupe-gorg-lbb.com
hg08139.com
myjbtest.net
cyg8wm3zfb.xyz
mimi2023.monster
ruixiangg.com
smokintires.net
out-boundlabs.net
matrix-promotions.com
botfolk.com
6o20r.beauty
cpohlelaw.com
zamupoi.fun
eletrobrasilvendas.com
desire-dating.com
678ap.com
bioprost.club
hfaer4.xyz
yuwangjing.com
359brigham.com
misstamar.mobi
lucasbrownviolinstudio.com
mybet668.com
giuila.online
mathews.buzz
dcmdot.com
epeople.store
totneshotdesk.com
jaehub.com
notbokin.online
trongiv.xyz
adept-expert-comptable.net
4tvaccounting.com
saledotfate.live
canadiantrafficmanagement.net
oktravelhi.com
taylorranchtrail.com
tempahwebsites.com
b-store.shop
paintellensburg.com
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2082:01:13 10:31:31+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 755200 |
| InitializedDataSize: | 95232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xba496 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GUI |
| FileVersion: | 1.0.0.0 |
| InternalName: | WCz.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | WCz.exe |
| ProductName: | GUI |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
36
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | "C:\Users\admin\AppData\Local\Temp\Confirm!!.exe" | C:\Users\admin\AppData\Local\Temp\Confirm!!.exe | — | Confirm!!.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1088 | "C:\Windows\SysWOW64\NAPSTAT.EXE" | C:\Windows\SysWOW64\NAPSTAT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Access Protection Client UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(1088) NAPSTAT.EXE C2www.qfs-capital.com/he2a/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)connectioncompass.store zekicharge.com dp77.shop guninfo.guru mamaeconomics.net narcisme.coach redtopassociates.com ezezn.com theoregondog.com pagosmultired.online emsculptcenterofne.com meet-friends.online pf326.com wealthjigsaw.xyz arsajib.com kickassholdings.online avaturre.biz dtslogs.com lb92.tech pittalam.com cyberlegion.group 24eu-ru-startup.xyz theaustralianbrisketboard.com bavrnimn.site xn--groupe-gorg-lbb.com hg08139.com myjbtest.net cyg8wm3zfb.xyz mimi2023.monster ruixiangg.com smokintires.net out-boundlabs.net matrix-promotions.com botfolk.com 6o20r.beauty cpohlelaw.com zamupoi.fun eletrobrasilvendas.com desire-dating.com 678ap.com bioprost.club hfaer4.xyz yuwangjing.com 359brigham.com misstamar.mobi lucasbrownviolinstudio.com mybet668.com giuila.online mathews.buzz dcmdot.com epeople.store totneshotdesk.com jaehub.com notbokin.online trongiv.xyz adept-expert-comptable.net 4tvaccounting.com saledotfate.live canadiantrafficmanagement.net oktravelhi.com taylorranchtrail.com tempahwebsites.com b-store.shop paintellensburg.com | |||||||||||||||
| 1696 | /c del "C:\Users\admin\AppData\Local\Temp\Confirm!!.exe" | C:\Windows\SysWOW64\cmd.exe | — | NAPSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\AppData\Local\Temp\Confirm!!.exe" | C:\Users\admin\AppData\Local\Temp\Confirm!!.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
69
Read events
69
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.narcisme.coach |
| unknown |
www.trongiv.xyz |
| unknown |
www.24eu-ru-startup.xyz |
| unknown |