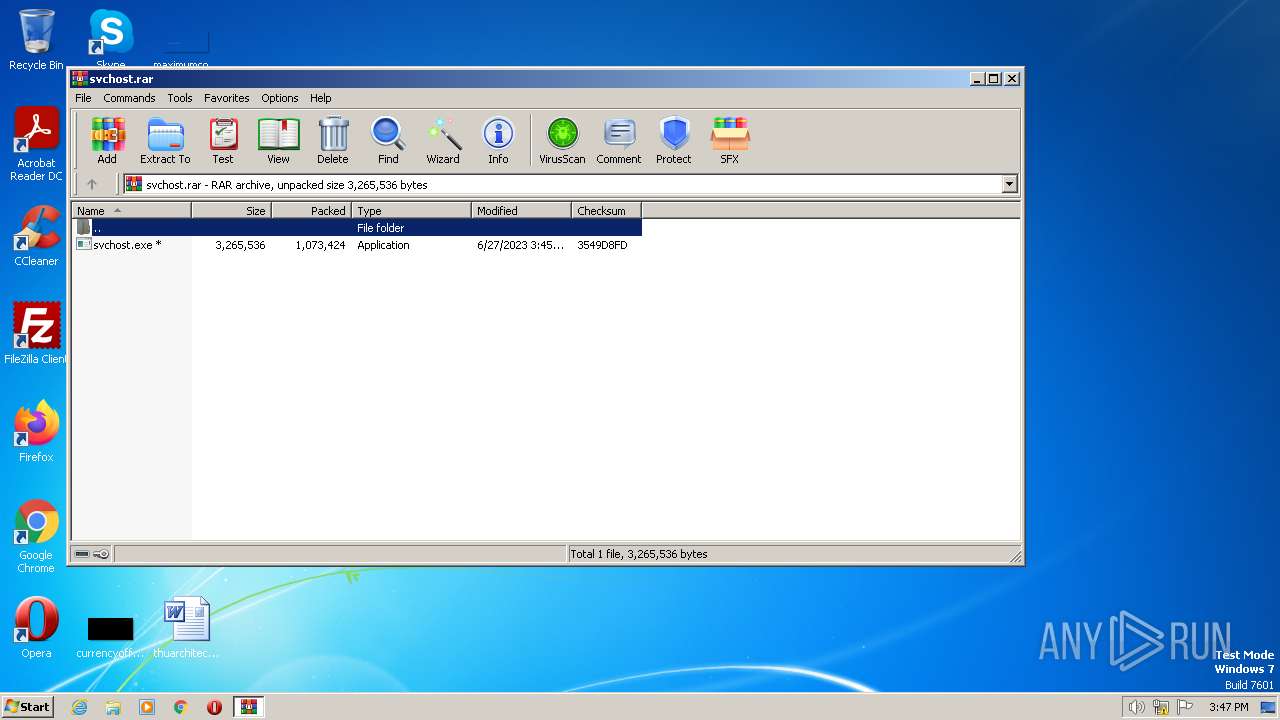
| File name: | svchost.rar |
| Full analysis: | https://app.any.run/tasks/71a39de2-813b-4084-904c-2692644c14f1 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
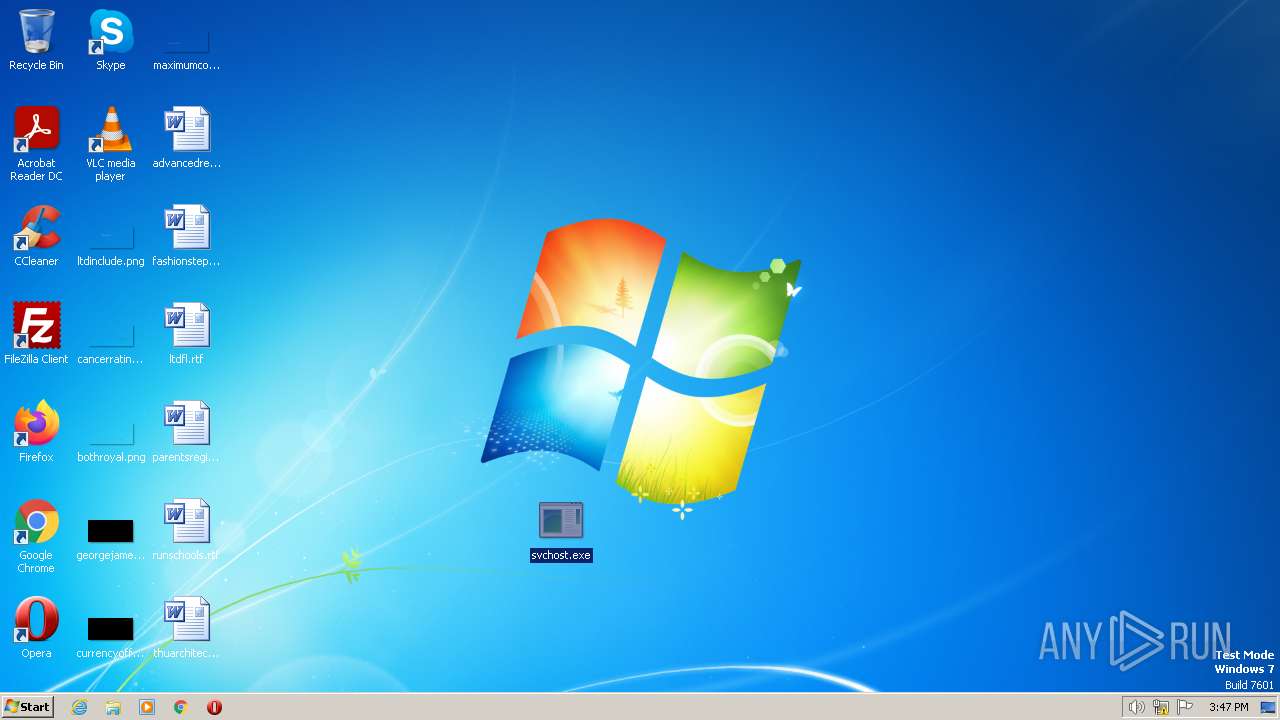
| Analysis date: | June 27, 2023, 14:46:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 834667FEDC73607C4E458E5DD7F57559 |
| SHA1: | 7A0D4BEDB15F85327753A1BDE4998E5D2D6F3FE3 |
| SHA256: | 638EC4E7BC15739C299081526DE6D759C7869BF062887AD3895EA52FDBCFAD53 |
| SSDEEP: | 24576:S/njHLXaqkOvgZFp6rsj+4DXr73wNHtDYQx3P3Wry3+jnvXE:S/jrKqkukiru+4DX4t5x3PGryyv0 |
MALICIOUS
QUASAR detected by memory dumps
- svchost.exe (PID: 3896)
Application was dropped or rewritten from another process
- svchost.exe (PID: 3896)
SUSPICIOUS
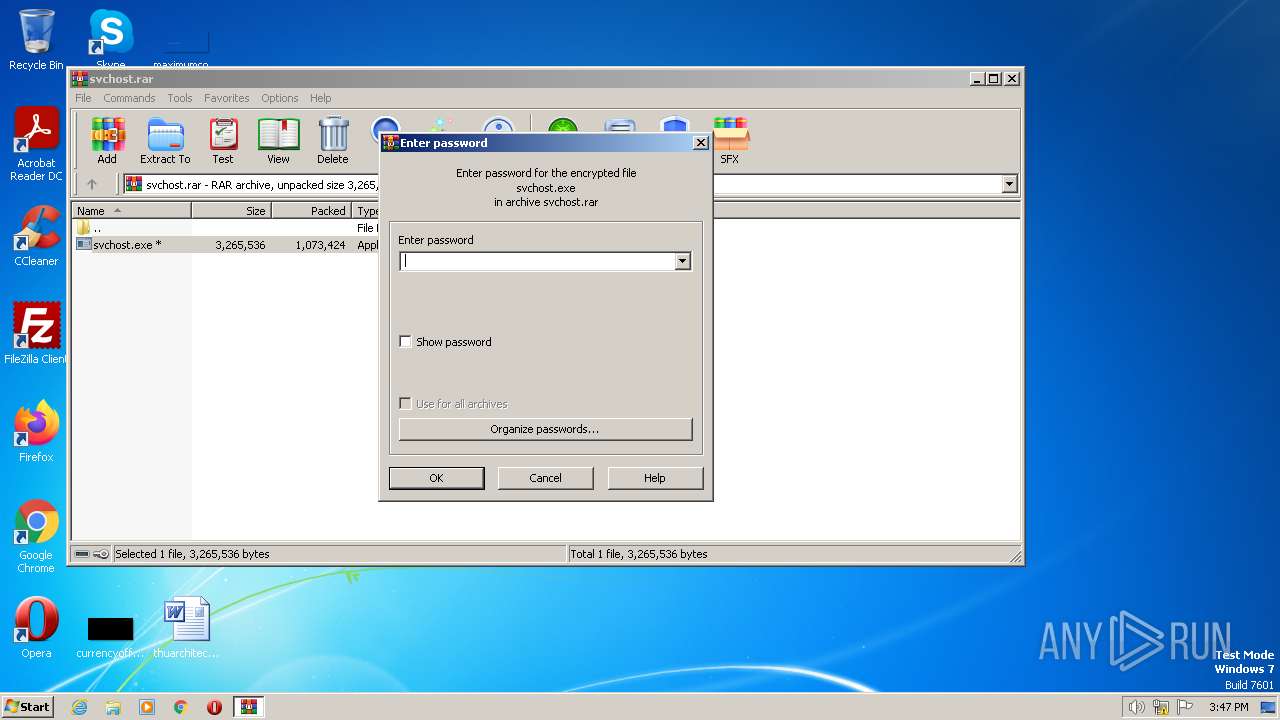
Creates executable files that already exist in Windows
- WinRAR.exe (PID: 2952)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 2952)
Reads settings of System Certificates
- svchost.exe (PID: 3896)
Reads the Internet Settings
- svchost.exe (PID: 3896)
Connects to unusual port
- svchost.exe (PID: 3896)
INFO
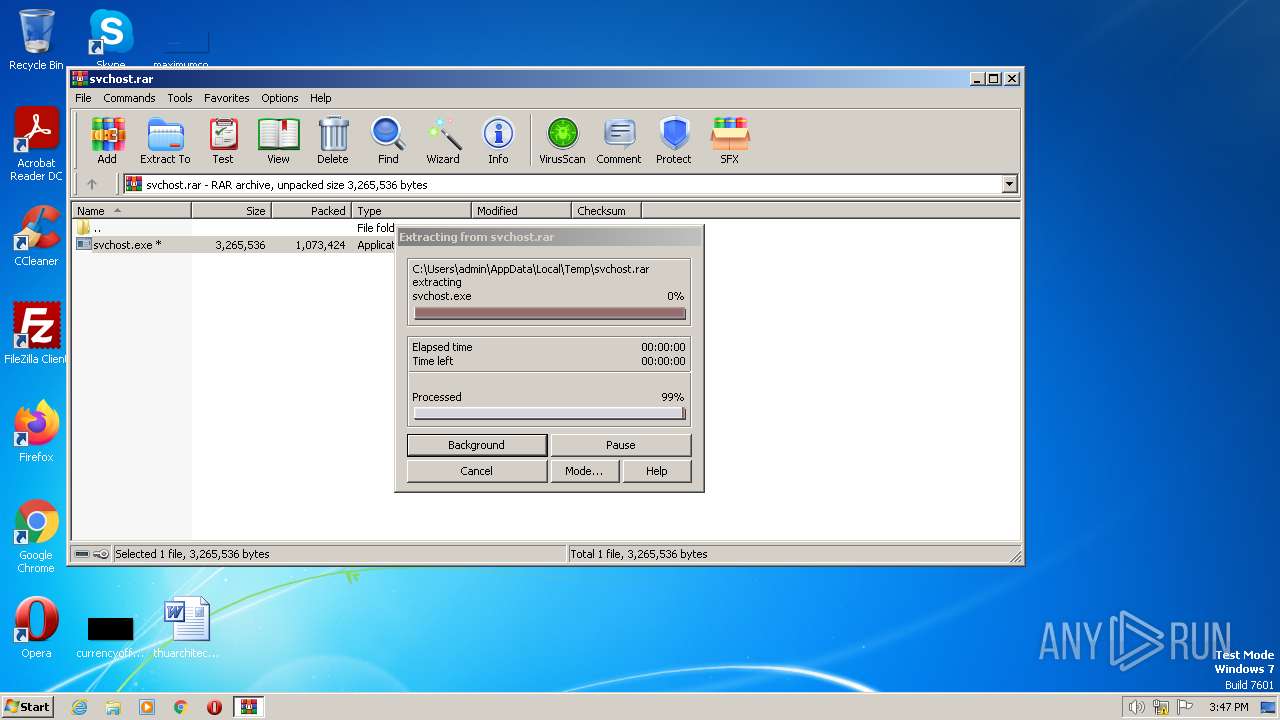
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2952)
Manual execution by a user
- svchost.exe (PID: 3896)
Create files in a temporary directory
- svchost.exe (PID: 3896)
Checks supported languages
- svchost.exe (PID: 3896)
Reads the computer name
- svchost.exe (PID: 3896)
The process checks LSA protection
- svchost.exe (PID: 3896)
Reads Environment values
- svchost.exe (PID: 3896)
Reads the machine GUID from the registry
- svchost.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
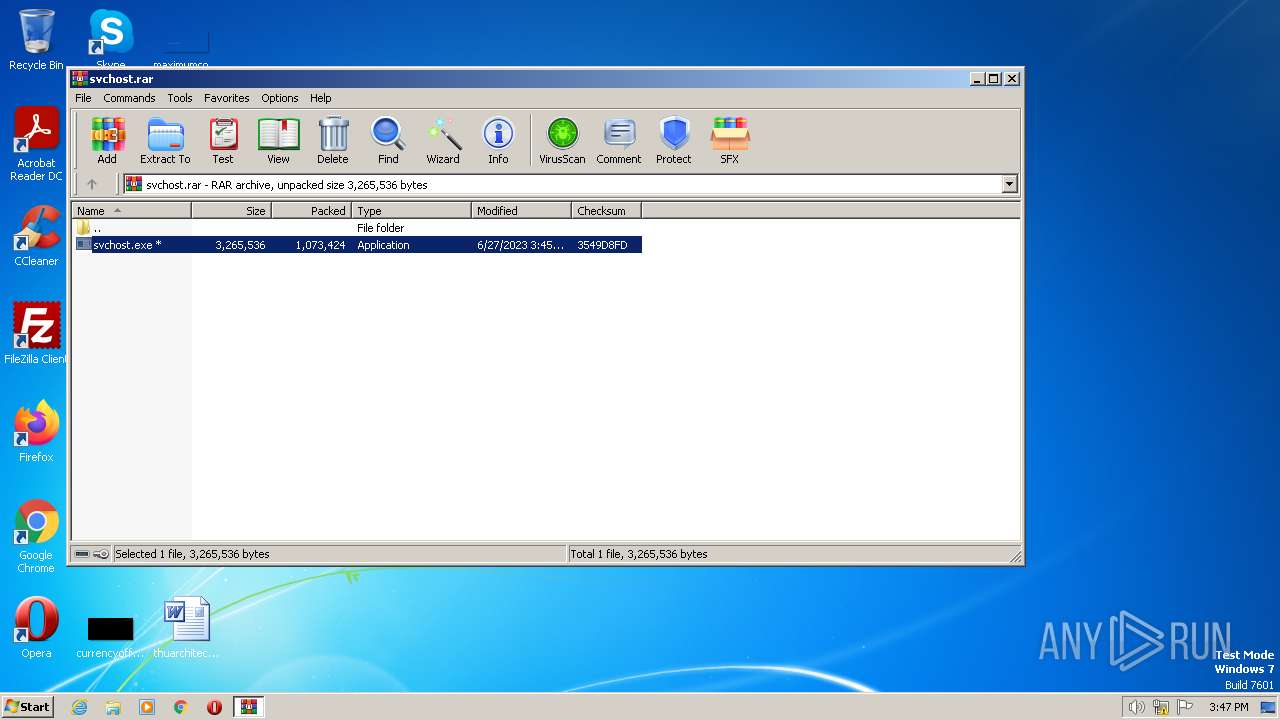
Quasar
(PID) Process(3896) svchost.exe
Version1.4.1
C2 (2)hi-world.duckdns.org:8846
Sub_Dir
Install_Namesvchost.exe
MutexMe
StartupJava Updater
TagMe
LogDirLogs
SignatureJxnlkuQ9PHKePwJOzhcqEMwmMXMZ7PI2IHPA38A3Vvh9rIwJY81Je7fXDHQfCFugWBxdz0oWjtncRb9kuq9yWQzWDlaopn1zOgAaM2WPLngou0lDOg0/8jlGxNs01rAycMQAYRA3Agpz3P8KfMbfIQf8q2+4fmgOrY0p4Y047wIzl2KhpuQpnHkFxijq4vHNa0msrGqKbb0bwdWZfNBYr1iEHk0GmPcnMbPvnGpBsdEYeSvl1VqTR0MfZfP61PVsWAACMO4hVTcAEaV1etucNfwzRG176JgPVshnmHiYZw3c...
CertificateMIIE9DCCAtygAwIBAgIQAJseDBewnuIm6EgNTdVsGTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMDYyNTE0MzMyM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAoKPSR9VHimamS7gx7FPP83gbu+rAJP9C5yoNyyNnQmFp/OI9LEy9mp74doA7fuH4zGUbKU22...
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\svchost.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\Desktop\svchost.exe" | C:\Users\admin\Desktop\svchost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 0 Version: 1.4.1 Modules
Quasar(PID) Process(3896) svchost.exe Version1.4.1 C2 (2)hi-world.duckdns.org:8846 Sub_Dir Install_Namesvchost.exe MutexMe StartupJava Updater TagMe LogDirLogs SignatureJxnlkuQ9PHKePwJOzhcqEMwmMXMZ7PI2IHPA38A3Vvh9rIwJY81Je7fXDHQfCFugWBxdz0oWjtncRb9kuq9yWQzWDlaopn1zOgAaM2WPLngou0lDOg0/8jlGxNs01rAycMQAYRA3Agpz3P8KfMbfIQf8q2+4fmgOrY0p4Y047wIzl2KhpuQpnHkFxijq4vHNa0msrGqKbb0bwdWZfNBYr1iEHk0GmPcnMbPvnGpBsdEYeSvl1VqTR0MfZfP61PVsWAACMO4hVTcAEaV1etucNfwzRG176JgPVshnmHiYZw3c... CertificateMIIE9DCCAtygAwIBAgIQAJseDBewnuIm6EgNTdVsGTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMDYyNTE0MzMyM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAoKPSR9VHimamS7gx7FPP83gbu+rAJP9C5yoNyyNnQmFp/OI9LEy9mp74doA7fuH4zGUbKU22... | |||||||||||||||
Total events
5 475
Read events
5 442
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | svchost.exe | C:\Users\admin\AppData\Local\Temp\CabEF7D.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3896 | svchost.exe | C:\Users\admin\AppData\Local\Temp\TarEF7E.tmp | binary | |
MD5:4FF65AD929CD9A367680E0E5B1C08166 | SHA256:C8733C93CC5AAF5CA206D06AF22EE8DBDEC764FB5085019A6A9181FEB9DFDEE6 | |||
| 3896 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:A4BC6328EB666B80F9E9F296D39CC165 | SHA256:C373FE151628887018E113E839C7E67916F8F59A17954981DF0FFAC9D2488E5E | |||
| 3896 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 2952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2952.20919\svchost.exe | executable | |
MD5:1A7C14DD1ADA80FB86781A0C26ACE3EC | SHA256:839AED22CE38A500F4C17AE2BDD1A26D4E31CDD14C685F00BC669AAF5B94EF72 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | svchost.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?789597aadd00daf7 | US | compressed | 62.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3896 | svchost.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3896 | svchost.exe | 109.108.78.4:8846 | hi-world.duckdns.org | Kyiv Optic Networks ltd | UA | malicious |
3896 | svchost.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hi-world.duckdns.org |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ipwho.is |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1076 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1076 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1076 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |