| File name: | Letter(05-02).exe.bin |
| Full analysis: | https://app.any.run/tasks/65600d53-2ece-4084-a41c-b6dc63e2cd22 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 31, 2020, 06:15:28 |
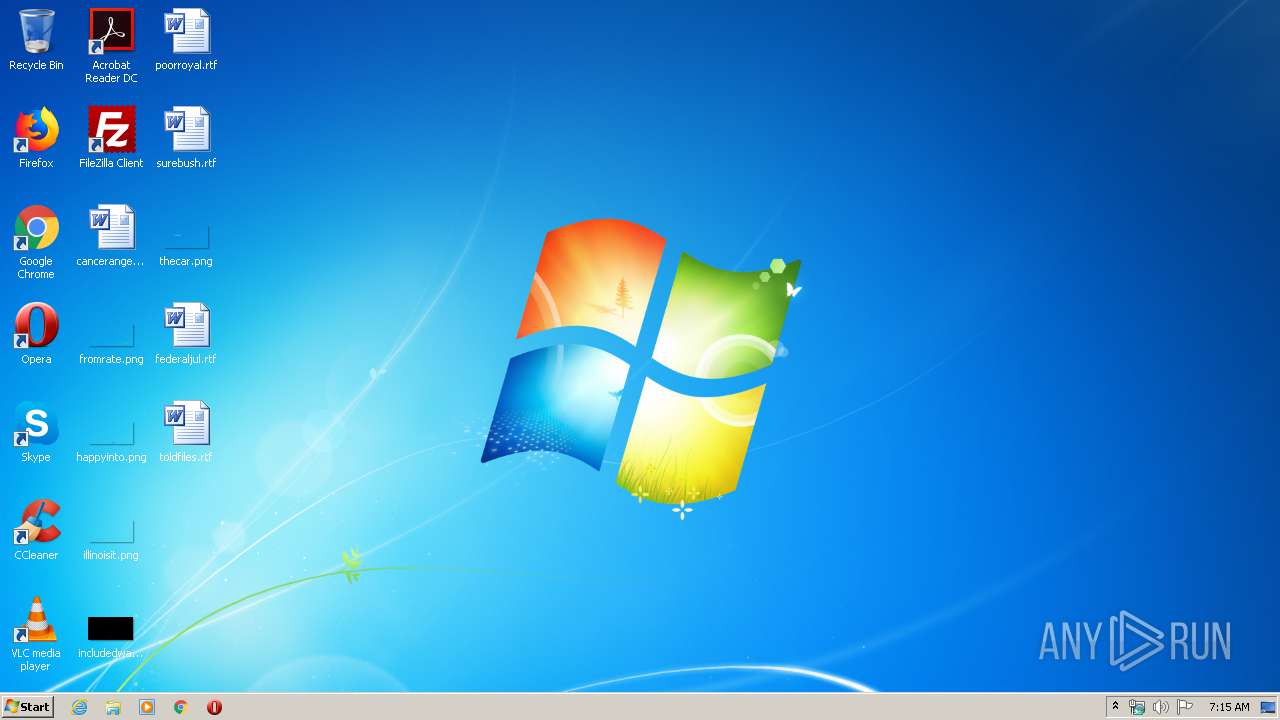
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1414BCB24C26EF6751929A9E7AAB11AA |
| SHA1: | 0ED9DE8C288C3E7CD4078B02AE1B7C4DD103ED5C |
| SHA256: | 637ED1175F23DC26A15A04745613C8091A30C070C4427AE9E1221D141FCBBFCF |
| SSDEEP: | 6144:nK6g8ITNR76Q7hN0wjXLCpYRFTBXccEdUc8kBtLpVuqv2q/YgfcVkliOG:nKNsQ7FjGpkcDec8kBdpVuGIkliX |
MALICIOUS
AGENTTESLA detected
- RegAsm.exe (PID: 3448)
Starts Visual C# compiler
- lnCAENRgjxLzOUQnma5.exe (PID: 1460)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 3448)
Application was dropped or rewritten from another process
- lnCAENRgjxLzOUQnma5.exe (PID: 1460)
SUSPICIOUS
Executable content was dropped or overwritten
- Letter(05-02).exe.bin.exe (PID: 3964)
Reads Environment values
- RegAsm.exe (PID: 3448)
INFO
Reads the hosts file
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2352)
Manual execution by user
- chrome.exe (PID: 3088)
Application launched itself
- chrome.exe (PID: 3088)
Reads settings of System Certificates
- chrome.exe (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:10:31 04:28:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 27136 |
| InitializedDataSize: | 367104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69d0 |
| OSVersion: | 6.3 |
| ImageVersion: | 6.3 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Oct-2014 03:28:47 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Oct-2014 03:28:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006964 | 0x00006A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35038 |
.data | 0x00008000 | 0x00001A8C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17593 |
.idata | 0x0000A000 | 0x0000107C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04714 |
.rsrc | 0x0000C000 | 0x00057854 | 0x00057A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.91235 |
.reloc | 0x00064000 | 0x000008C0 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.37329 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.37086 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
1 | 5.05393 | 1511 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.05105 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.2674 | 1312 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.29977 | 1484 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.2912 | 1098 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.13591 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
2001 | 3.25575 | 754 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
74
Monitored processes
36
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6960177152057713348 --mojo-platform-channel-handle=4336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13781122116418433842 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15220070870874605212 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15820207063763490516 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17506566245192375405 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1460 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\lnCAENRgjxLzOUQnma5.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\lnCAENRgjxLzOUQnma5.exe | — | Letter(05-02).exe.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14010571575689472595 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1774637562027419270 --mojo-platform-channel-handle=3324 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5627458215611453942 --mojo-platform-channel-handle=3756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,443066288486389983,6572744401096453216,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6762822284009174807 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
412
Read events
327
Write events
80
Delete events
5
Modification events
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3088-13230108952026250 |
Value: 259 | |||
Executable files
1
Suspicious files
40
Text files
246
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCA7A50323E9D46669676C884B51596C7.TMP | — | |
MD5:— | SHA256:— | |||
| 2608 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES6CAC.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | csc.exe | C:\Users\admin\AppData\Local\Temp\d0ranuu4.dll | — | |
MD5:— | SHA256:— | |||
| 3852 | csc.exe | C:\Users\admin\AppData\Local\Temp\d0ranuu4.out | — | |
MD5:— | SHA256:— | |||
| 1460 | lnCAENRgjxLzOUQnma5.exe | C:\Users\admin\AppData\Local\Temp\wguxfaqx.0.cs | — | |
MD5:— | SHA256:— | |||
| 1460 | lnCAENRgjxLzOUQnma5.exe | C:\Users\admin\AppData\Local\Temp\wguxfaqx.cmdline | — | |
MD5:— | SHA256:— | |||
| 3620 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC121B22BB5D34DBA9FB9A4C8738C88DD.TMP | — | |
MD5:— | SHA256:— | |||
| 2376 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES6E14.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | csc.exe | C:\Users\admin\AppData\Local\Temp\wguxfaqx.dll | — | |
MD5:— | SHA256:— | |||
| 3620 | csc.exe | C:\Users\admin\AppData\Local\Temp\wguxfaqx.out | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
23
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2352 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
2352 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
2352 | chrome.exe | GET | 200 | 74.125.168.7:80 | http://r2---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=81.17.242.238&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1585634849&mv=u&mvi=1&pl=20&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2352 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 173.194.129.232:80 | r3---sn-q0c7rn76.gvt1.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.22.67:443 | www.google.ie | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3448 | RegAsm.exe | 208.91.199.224:587 | us2.smtp.mailhostbox.com | PDR | US | shared |
2352 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3448 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |