| File name: | SUPPLIER_PURCHASE_ORDER.IMG |
| Full analysis: | https://app.any.run/tasks/91679b7b-cba2-43a5-981e-f8a7009fd755 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | February 21, 2020, 19:00:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
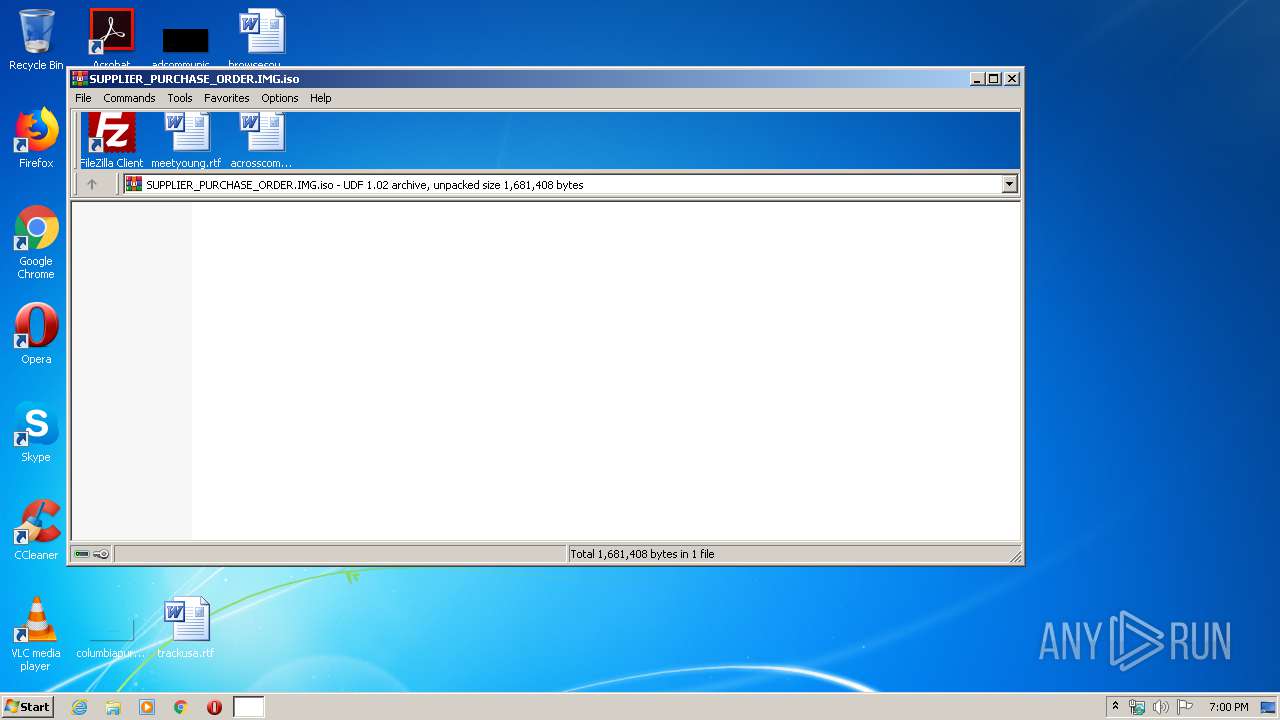
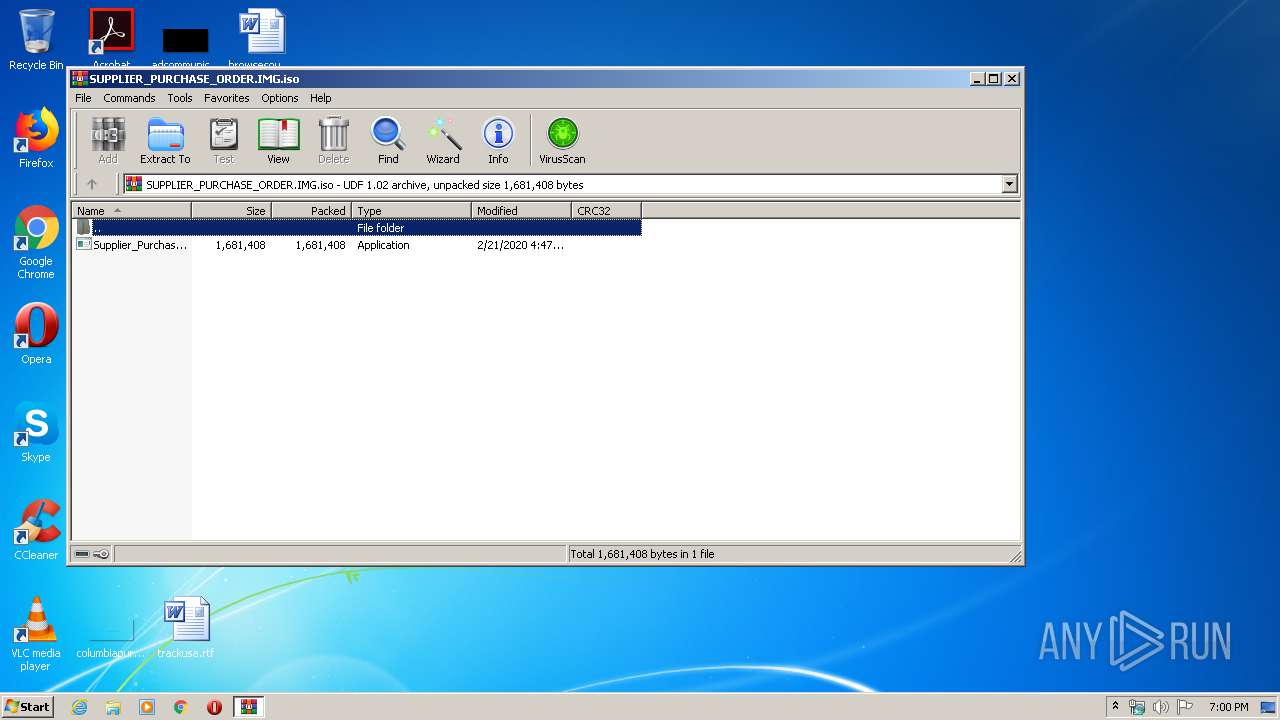
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) 'DESKTOP' |
| MD5: | 026E3E49B052437059A85EC673C6C494 |
| SHA1: | 62D64FEB0C53752326E6171F27444E123EE28768 |
| SHA256: | 6342D4838170DDE93F957C39E0DACD2A7761FD3739A89E03CBFCA759878976FB |
| SSDEEP: | 49152:6u0c++OCvkGs9FaTOGQymIC6F3+uRcYY:FB3vkJ9TjA3+E |
MALICIOUS
Application was dropped or rewritten from another process
- Supplier_Purchase_Order.exe (PID: 1920)
AGENTTESLA detected
- RegSvcs.exe (PID: 2484)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2484)
SUSPICIOUS
Reads Environment values
- RegSvcs.exe (PID: 2484)
Reads the cookies of Google Chrome
- RegSvcs.exe (PID: 2484)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3744)
Creates files in the user directory
- RegSvcs.exe (PID: 2484)
Reads the cookies of Mozilla Firefox
- RegSvcs.exe (PID: 2484)
Connects to SMTP port
- RegSvcs.exe (PID: 2484)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| VolumeName: | DESKTOP |
|---|---|
| VolumeBlockCount: | 1086 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2020:02:21 16:50:00+01:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2020:02:21 16:50:00.00+01:00 |
| VolumeModifyDate: | 2020:02:21 16:50:00.00+01:00 |
Composite
| VolumeSize: | 2.1 MB |
|---|
Total processes
37
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1920 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3744.13824\Supplier_Purchase_Order.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3744.13824\Supplier_Purchase_Order.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2484 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | Supplier_Purchase_Order.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3744 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SUPPLIER_PURCHASE_ORDER.IMG.iso" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
521
Read events
488
Write events
33
Delete events
0
Modification events
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SUPPLIER_PURCHASE_ORDER.IMG.iso | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\h21uzyto.qrh\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 2484 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\h21uzyto.qrh\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2484 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\077a3c94-3024-497b-9d85-8d823d90b06c | sqlite | |
MD5:— | SHA256:— | |||
| 2484 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\h21uzyto.qrh.zip | compressed | |
MD5:— | SHA256:— | |||
| 3744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3744.13824\Supplier_Purchase_Order.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2484 | RegSvcs.exe | 110.4.45.37:587 | mail.elkat.com.my | Exa Bytes Network Sdn.Bhd. | MY | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.elkat.com.my |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2484 | RegSvcs.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2484 | RegSvcs.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |