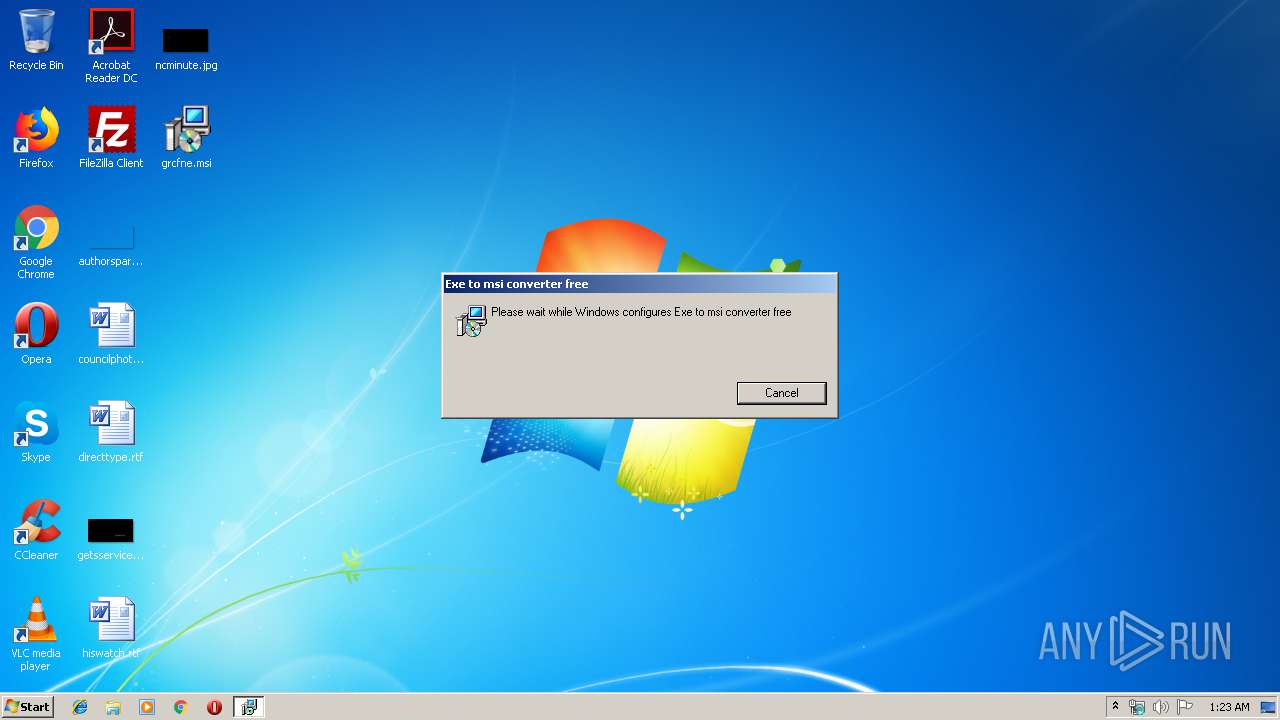
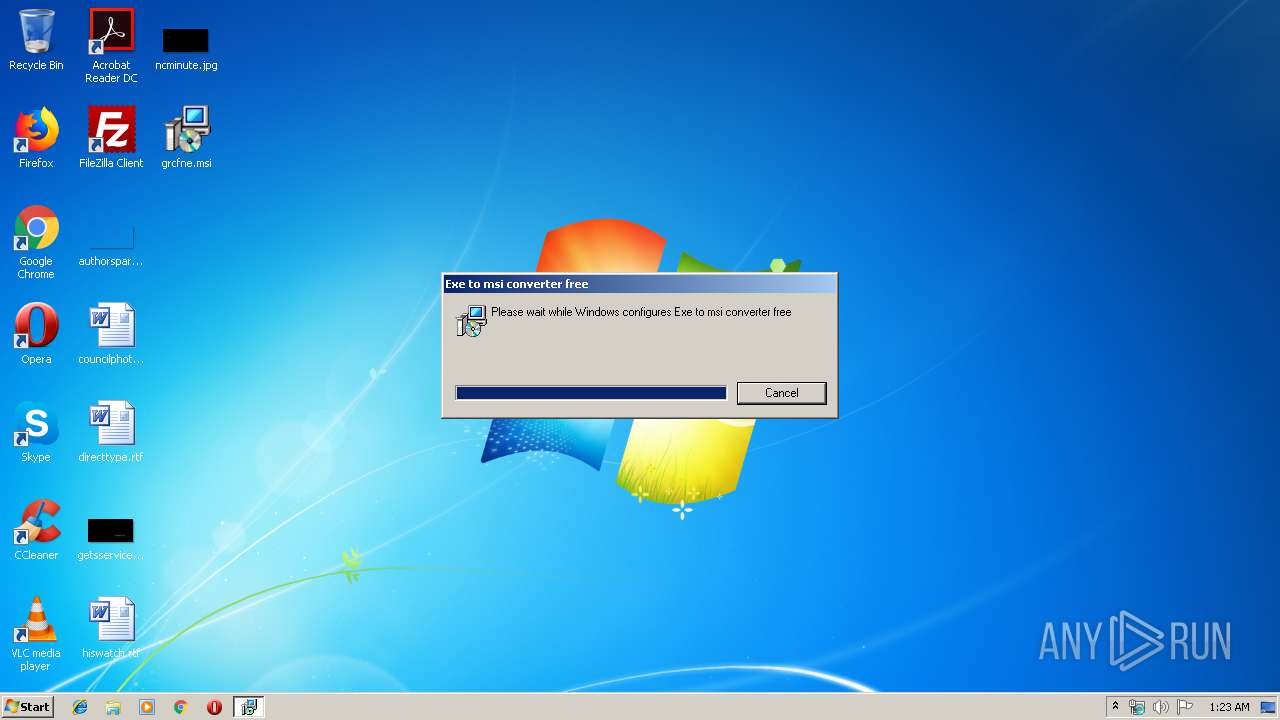
| File name: | grcfne.msi |
| Full analysis: | https://app.any.run/tasks/8e6be81b-ad40-492a-b11e-b2af43f5e0d9 |
| Verdict: | Malicious activity |
| Threats: | Loda is a remote access trojan (RAT) that has been in active use among multiple threat actors since 2016. The malware’s functionality includes stealing passwords and other sensitive information, keylogging, capturing screenshots, and delivering other malicious payloads. Loda is typically distributed as part of phishing email campaigns. |
| Analysis date: | December 03, 2019, 01:22:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Title: Exe to msi converter free, Author: www.exetomsi.com, Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0 |
| MD5: | C0CDD7F5824CAB358C18FE146F4B024D |
| SHA1: | 023F7BDFBEF59E0D3174693349DBC5FAE72F5350 |
| SHA256: | 633F3970C31C9CB849BD5F66C3A783538BB2327B4BEC5774B870F8B3B53EA3C1 |
| SSDEEP: | 24576:6EnthEVaPqL5Y644A1gOGKnpWMGXuzkeY0oGK:6ErEVUc5Yp4A1gAWMKuz5JBK |
MALICIOUS
Changes the autorun value in the registry
- MSI1E04.tmp (PID: 784)
LODA was detected
- MSI1E04.tmp (PID: 784)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 992)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 656)
Connects to CnC server
- MSI1E04.tmp (PID: 784)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3608)
- MSI1E04.tmp (PID: 784)
Executed as Windows Service
- vssvc.exe (PID: 3332)
Creates files in the user directory
- MSI1E04.tmp (PID: 784)
Drop ExeToMSI Application
- msiexec.exe (PID: 3608)
Starts CMD.EXE for commands execution
- MSI1E04.tmp (PID: 784)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3332)
Application was dropped or rewritten from another process
- MSI1E04.tmp (PID: 784)
Starts application with an unusual extension
- msiexec.exe (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Title: | Exe to msi converter free |
| Subject: | - |
| Author: | www.exetomsi.com |
| Keywords: | - |
| Comments: | - |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | C:\Windows\system32\cmd.exe /c schtasks /create /tn XNAEAL.exe /tr C:\Users\admin\AppData\Roaming\Windata\JLMWFF.exe /sc minute /mo 1 | C:\Windows\system32\cmd.exe | MSI1E04.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 784 | "C:\Windows\Installer\MSI1E04.tmp" | C:\Windows\Installer\MSI1E04.tmp | msiexec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 992 | schtasks /create /tn XNAEAL.exe /tr C:\Users\admin\AppData\Roaming\Windata\JLMWFF.exe /sc minute /mo 1 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\grcfne.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3608 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
578
Read events
429
Write events
149
Delete events
0
Modification events
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000AC7A483D78A9D501180E0000A00F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000006DD4A3D78A9D501180E0000A00F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000163BAA3D78A9D501180E0000A00F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000709DAC3D78A9D501180E0000B40E0000E803000001000000000000000000000053AE636D7AF93D4EBFCA2C6E1C918E270000000000000000 | |||
| (PID) Process: | (3332) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D826B63D78A9D501040D0000540F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3332) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D826B63D78A9D501040D000048010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3332) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D826B63D78A9D501040D000004090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3332) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D826B63D78A9D501040D0000AC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3332) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 400000000000000040B0BF3D78A9D501040D000004090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF39DE77EB3D14799C.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6d63ae53-f97a-4e3d-bfca-2c6e1c918e27}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\MSI1E04.tmp | executable | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\MSI1CC9.tmp | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\3916ff.ipi | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\3916fd.msi | executable | |
MD5:— | SHA256:— | |||
| 784 | MSI1E04.tmp | C:\Users\admin\AppData\Roaming\Windata\JLMWFF.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
11
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
784 | MSI1E04.tmp | 79.142.76.244:53916 | 4success.zapto.org | AltusHost B.V. | SE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
4success.zapto.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.zapto .org |
784 | MSI1E04.tmp | A Network Trojan was detected | MALWARE [PTsecurity] Loda Logger CnC Beacon |
9 ETPRO signatures available at the full report