| File name: | 0.exe |
| Full analysis: | https://app.any.run/tasks/d9c57b15-ba64-4a67-a8d5-4949f850b922 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | May 21, 2022, 07:22:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AEA1462E5F1F31DD74DF7833B5A07305 |
| SHA1: | CEA53B9B3311F1003DF5D9266F9E3FBD5C971F28 |
| SHA256: | 62C957DB467D22CF12AF74A4DAE478E7D239ECAE5D53F3C6399583F38F5224AF |
| SSDEEP: | 1536:rT2xEbTOfbXx5EujP3kjG2F3EyCRP69EK0L3FpgVv:rT2xNfzEmPUac0yCRS9EK0TLmv |
MALICIOUS
Connects to CnC server
- svchost.exe (PID: 3748)
Changes the login/logoff helper path in the registry
- svchost.exe (PID: 3748)
Uses SVCHOST.EXE for hidden code execution
- WaterMark.exe (PID: 3532)
RAMNIT was detected
- svchost.exe (PID: 3748)
Application was injected by another process
- csrss.exe (PID: 340)
- wininit.exe (PID: 376)
- services.exe (PID: 468)
- svchost.exe (PID: 760)
- lsm.exe (PID: 492)
- csrss.exe (PID: 384)
- svchost.exe (PID: 592)
- svchost.exe (PID: 672)
- winlogon.exe (PID: 432)
- smss.exe (PID: 260)
- spoolsv.exe (PID: 1236)
- svchost.exe (PID: 968)
- svchost.exe (PID: 860)
- svchost.exe (PID: 796)
- svchost.exe (PID: 1088)
- svchost.exe (PID: 1936)
- svchost.exe (PID: 1264)
- lsass.exe (PID: 484)
- svchost.exe (PID: 824)
- svchost.exe (PID: 1352)
- Explorer.EXE (PID: 1464)
- SearchProtocolHost.exe (PID: 3628)
- DllHost.exe (PID: 888)
- SearchFilterHost.exe (PID: 3752)
- IMEDICTUPDATE.EXE (PID: 1424)
- ctfmon.exe (PID: 1396)
- Dwm.exe (PID: 936)
- taskeng.exe (PID: 288)
- SearchIndexer.exe (PID: 2544)
Drops executable file immediately after starts
- svchost.exe (PID: 3748)
- 0.exe (PID: 3608)
Runs injected code in another process
- svchost.exe (PID: 1836)
SUSPICIOUS
Reads the computer name
- WaterMark.exe (PID: 3532)
- csrss.exe (PID: 384)
Creates files in the Windows directory
- svchost.exe (PID: 3748)
Checks supported languages
- 0.exe (PID: 3608)
- WaterMark.exe (PID: 3532)
Starts itself from another location
- 0.exe (PID: 3608)
Executable content was dropped or overwritten
- svchost.exe (PID: 3748)
- 0.exe (PID: 3608)
Drops a file with a compile date too recent
- svchost.exe (PID: 3748)
- 0.exe (PID: 3608)
Creates files in the program directory
- 0.exe (PID: 3608)
INFO
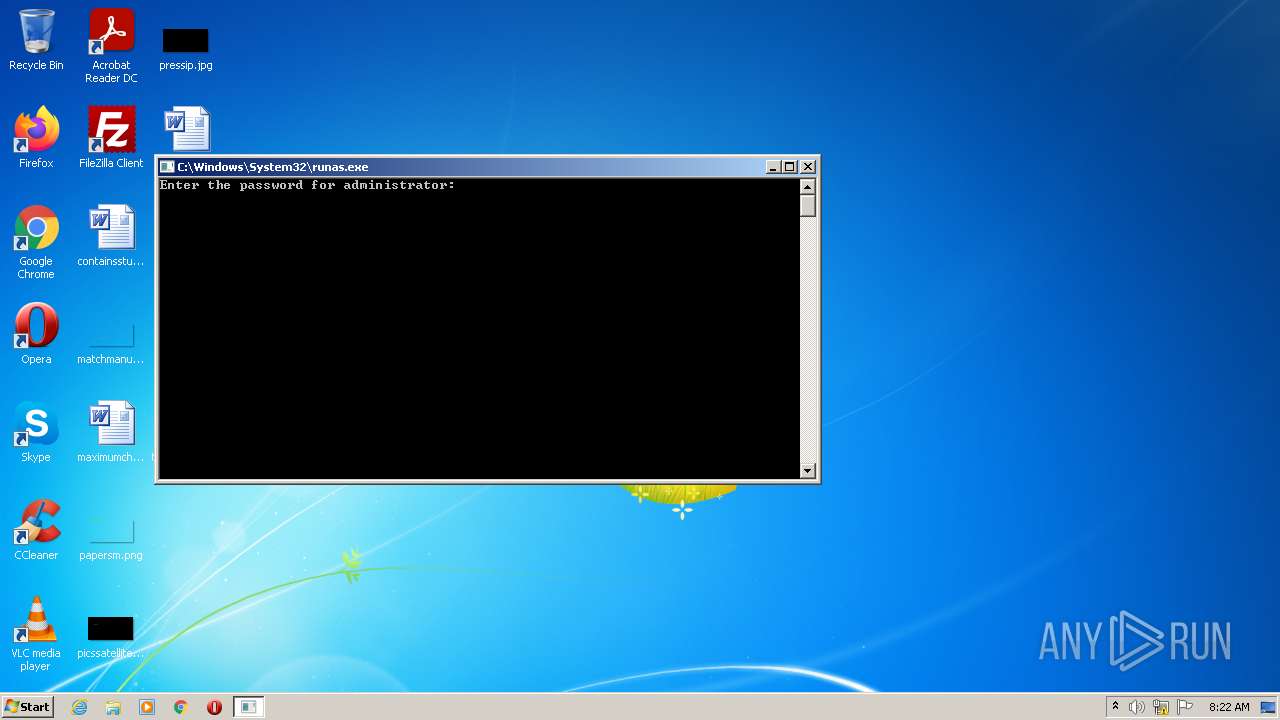
Reads the computer name
- runas.exe (PID: 628)
- svchost.exe (PID: 3748)
- DllHost.exe (PID: 888)
- svchost.exe (PID: 1836)
Checks supported languages
- svchost.exe (PID: 1836)
- runas.exe (PID: 628)
- DllHost.exe (PID: 888)
- svchost.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Debugger: | - |
|---|---|
| ProductVersion: | 8,0,22,0 |
| OriginalFileName: | npswf32.dll |
| LegalTrademarks: | Macromedia Flash Player |
| LegalCopyright: | Copyright © 1996-2005 Macromedia, Inc. |
| InternalName: | Macromedia Flash Player 8.0 |
| FileVersion: | 8,0,22,0 |
| ProductName: | Shockwave Flash |
| MIMEType: | application/x-shockwave-flash|application/futuresplash |
| FileOpenName: | Macromedia Flash movie (*.swf)|FutureSplash movie (*.spl)|Macromedia Flash Paper (*.mfp) |
| FileExtents: | swf|spl|mfp |
| FileDescription: | Shockwave Flash 8.0 r22 |
| CompanyName: | Macromedia, Inc. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 8.0.22.0 |
| FileVersionNumber: | 8.0.22.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 5.1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1138 |
| UninitializedDataSize: | 512 |
| InitializedDataSize: | 106496 |
| CodeSize: | 8704 |
| LinkerVersion: | 4.1 |
| PEType: | PE32 |
| TimeStamp: | 2003:05:21 23:25:03+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-May-2003 21:25:03 |
| Detected languages: |
|
| CompanyName: | Macromedia, Inc. |
| FileDescription: | Shockwave Flash 8.0 r22 |
| FileExtents: | swf|spl|mfp |
| FileOpenName: | Macromedia Flash movie (*.swf)|FutureSplash movie (*.spl)|Macromedia Flash Paper (*.mfp) |
| MIMEType: | application/x-shockwave-flash|application/futuresplash |
| ProductName: | Shockwave Flash |
| FileVersion: | 8,0,22,0 |
| InternalName: | Macromedia Flash Player 8.0 |
| LegalCopyright: | Copyright © 1996-2005 Macromedia, Inc. |
| LegalTrademarks: | Macromedia Flash Player |
| OriginalFilename: | npswf32.dll |
| ProductVersion: | 8,0,22,0 |
| Debugger: | 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 21-May-2003 21:25:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000021F3 | 0x00002200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.28283 |
.data | 0x00004000 | 0x000097BB | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.84517 |
.rsrc | 0x0000E000 | 0x00000920 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.02899 |
.rdata | 0x0000F000 | 0x00011F93 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.93757 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52421 | 1340 | Latin 1 / Western European | Hebrew - Israel | RT_VERSION |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
39
Monitored processes
34
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | \SystemRoot\System32\smss.exe | \SystemRoot\System32\smss.exe | System | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 288 | taskeng.exe {BB154EF7-42D4-42F2-B57F-9CBB745DE3E3} | C:\Windows\system32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | taskhost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | wininit.exe | C:\Windows\system32\wininit.exe | taskhost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 384 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 432 | winlogon.exe | C:\Windows\system32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 468 | C:\Windows\system32\services.exe | C:\Windows\system32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 484 | C:\Windows\system32\lsass.exe | C:\Windows\system32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7601.24545 (win7sp1_ldr_escrow.200102-1707) Modules
| |||||||||||||||
| 492 | C:\Windows\system32\lsm.exe | C:\Windows\system32\lsm.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 724
Read events
1 707
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1088) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: 5254006FB319 | |||
| (PID) Process: | (484) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\000001F4 |
| Operation: | write | Name: | F |
Value: 0200010000000000A0F79F93E36CD8010000000000000000468F64CCFD88CB0100000000000000000000000000000000F401000001020000100200000000000000003C00010000000000000088523500 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | Flags |
Value: 0 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | State |
Value: 256 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | Sid |
Value: 0105000000000005150000007C3E9B4DF44C73593E88FD13F4010000 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | ProfileLoadTimeLow |
Value: 0 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | ProfileLoadTimeHigh |
Value: 0 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-500\Software\Classes |
| Operation: | write | Name: | SymbolicLinkValue |
Value: \Registry\User\S-1-5-21-1302019708-1500728564-335382590-500_Classes | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-500 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\ehanf.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
Executable files
6
Suspicious files
1
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Windows\system32\dmlconf.dat | binary | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ccme_asym.dll | executable | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Legal\ENU\license.html | html | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\cryptocme.dll | executable | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ccme_ecc.dll | executable | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource0\index.html | html | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ngl_resources\resources\ui\index.html | html | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ccme_base_non_fips.dll | executable | |
MD5:— | SHA256:— | |||
| 3748 | svchost.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ccme_base.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
3
Threats
7
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | svchost.exe | 142.250.185.238:80 | — | Google Inc. | US | whitelisted |
3748 | svchost.exe | 91.220.62.30:443 | — | ZAO Sotal-Interactive | RU | malicious |
3748 | svchost.exe | 204.95.99.221:443 | rterybrstutnrsbberve.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rterybrstutnrsbberve.com |
| malicious |
erwbtkidthetcwerc.com |
| malicious |
rvbwtbeitwjeitv.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3748 | svchost.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |