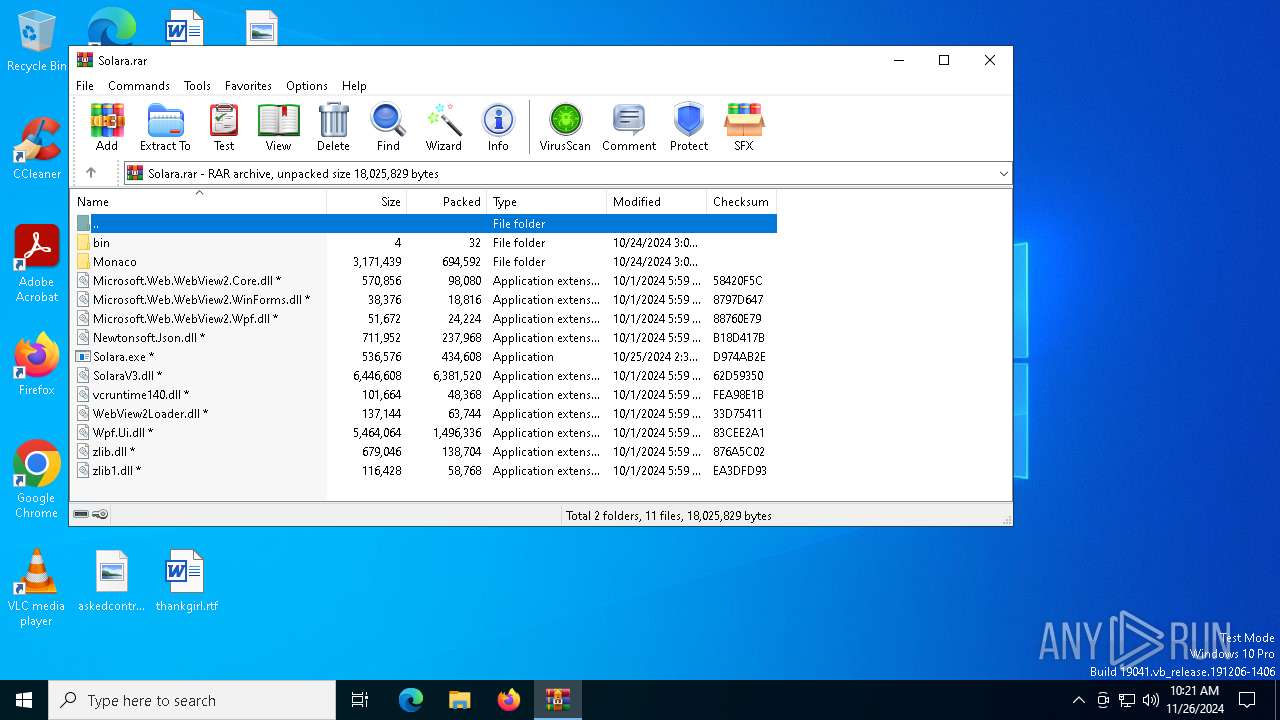
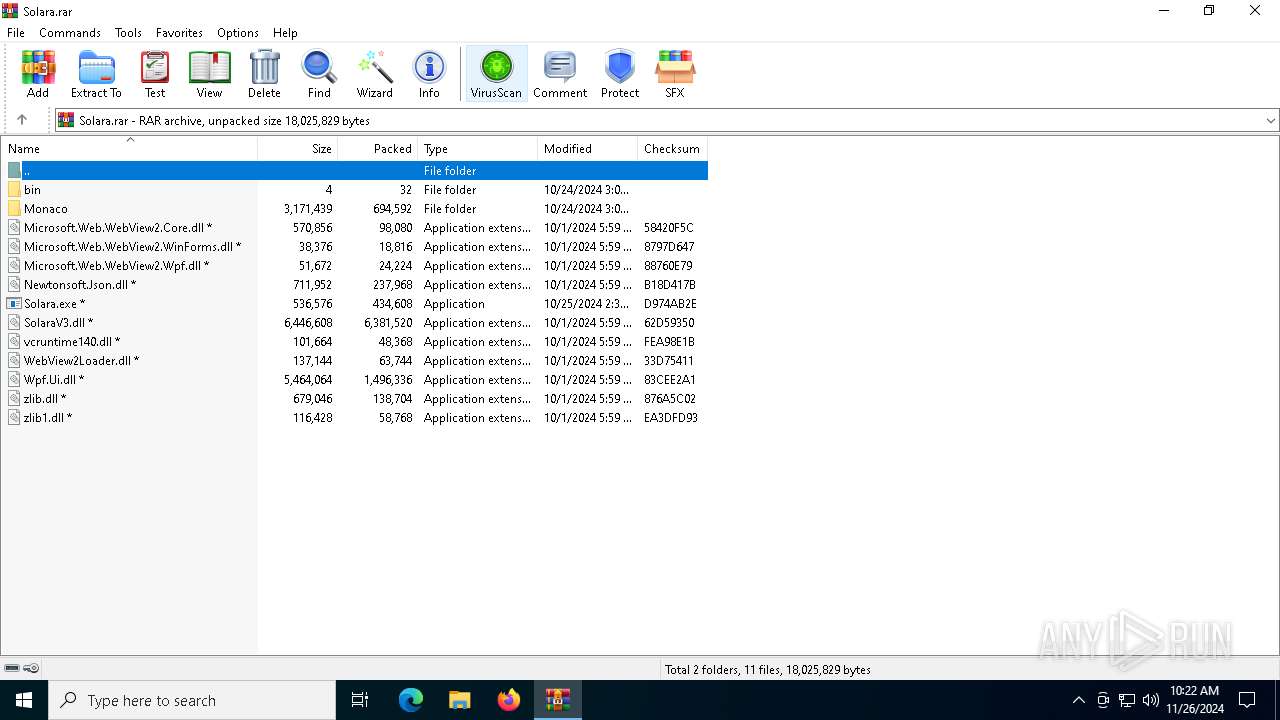
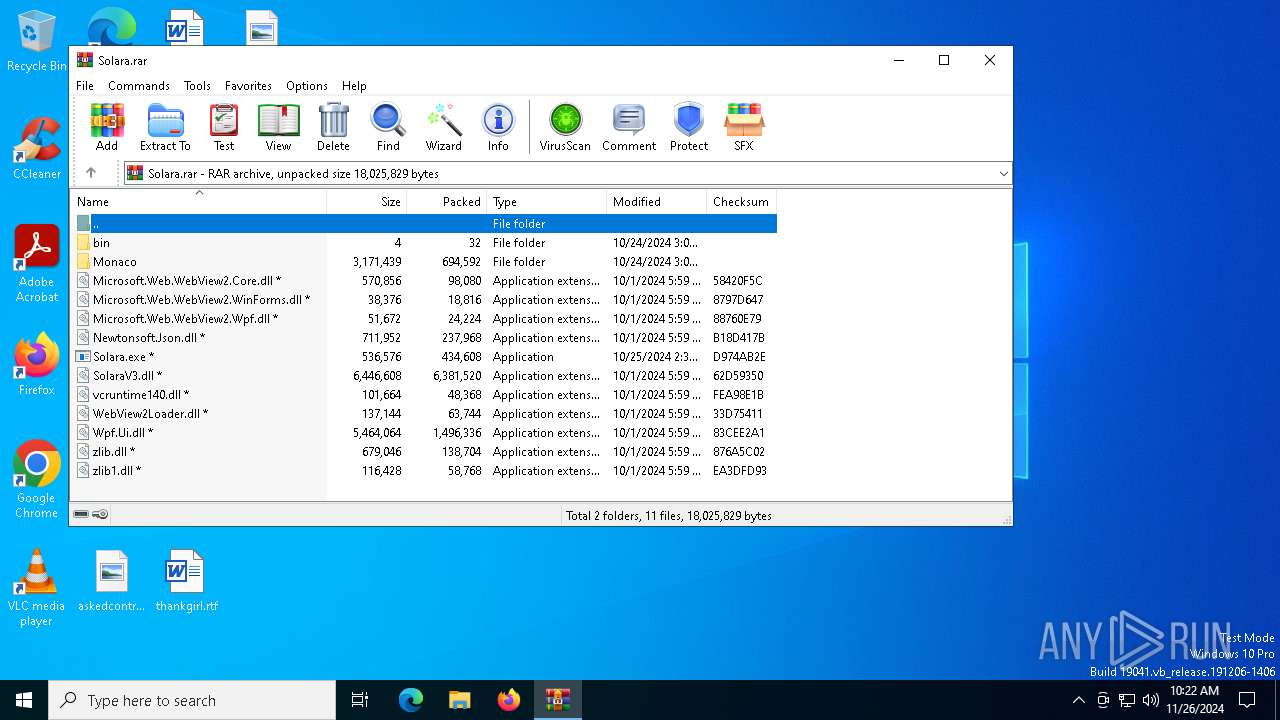
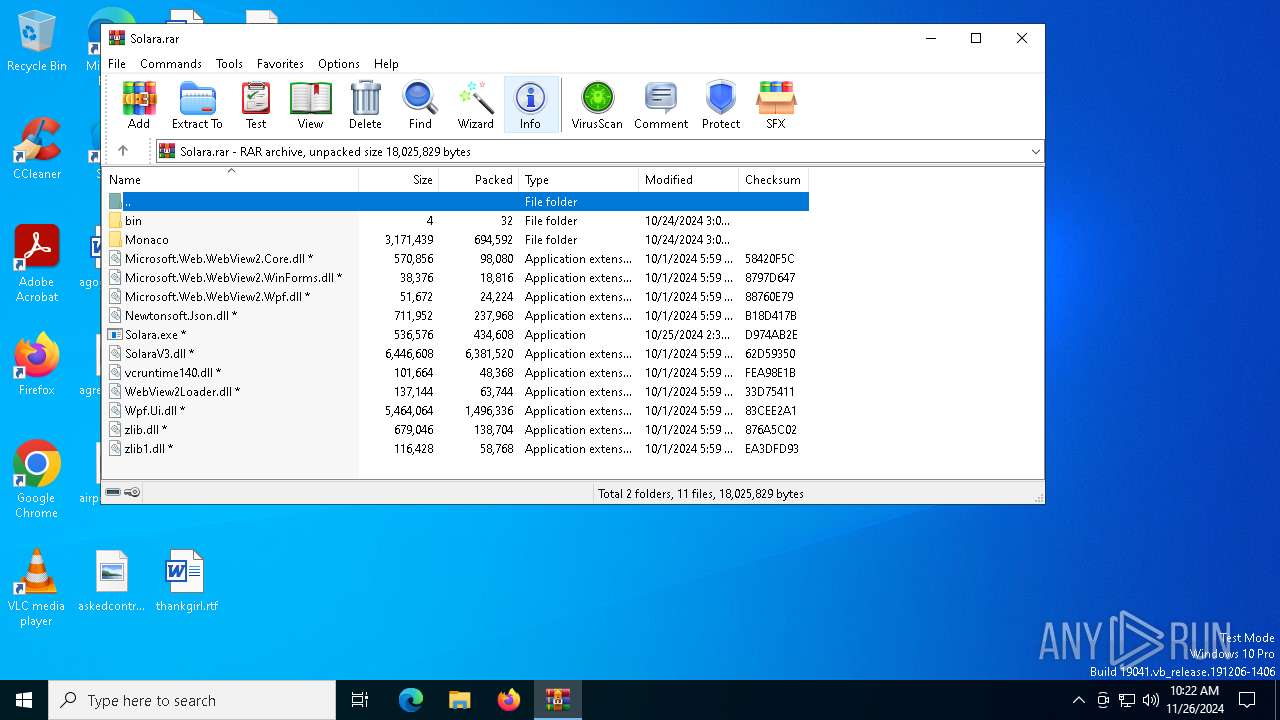
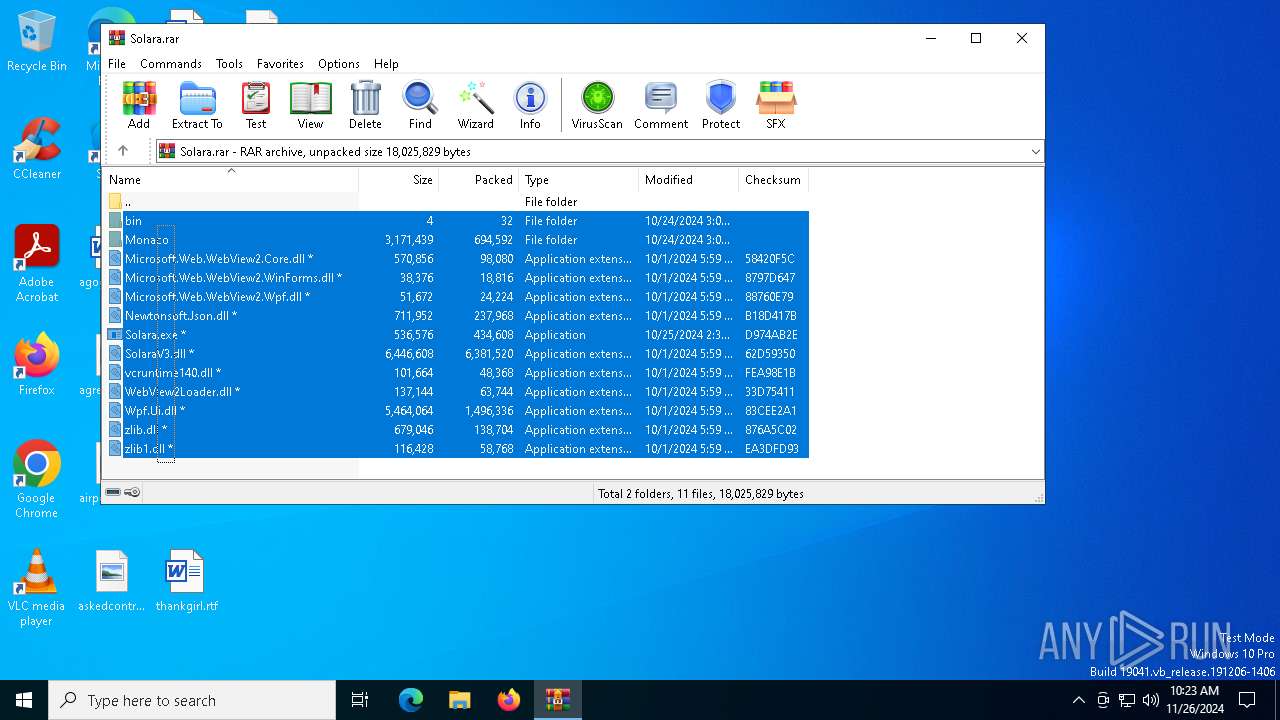
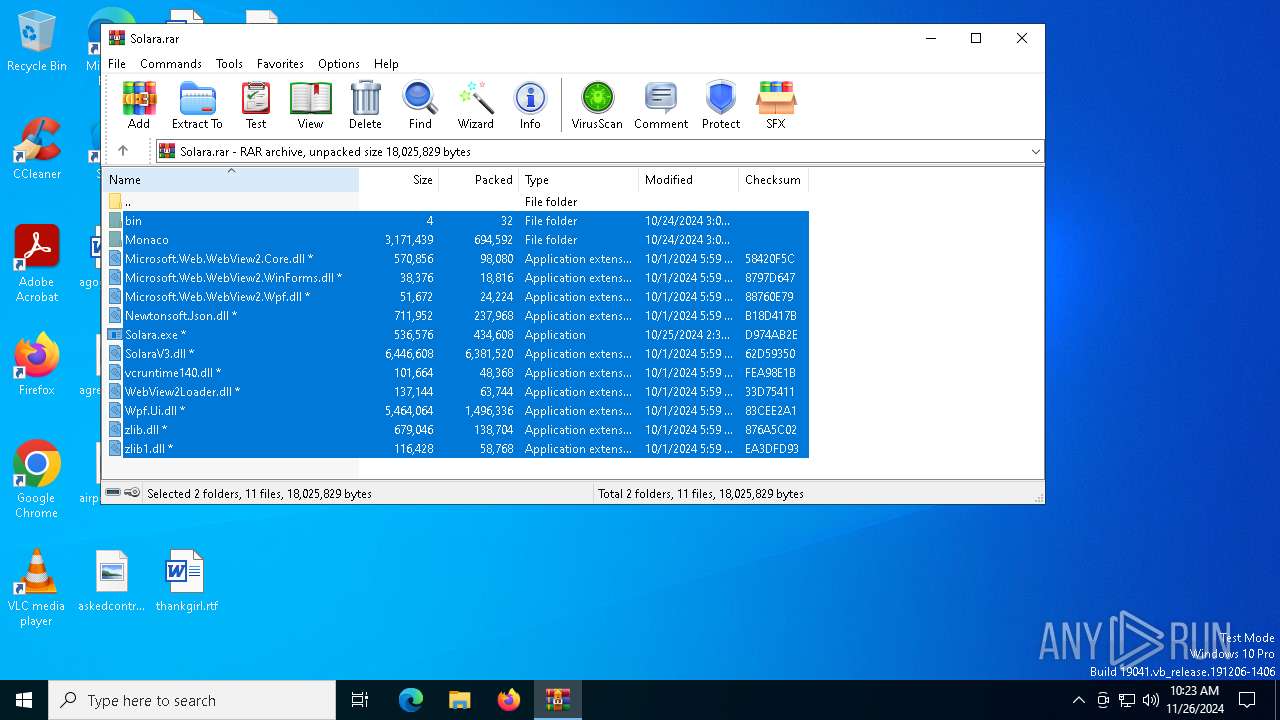
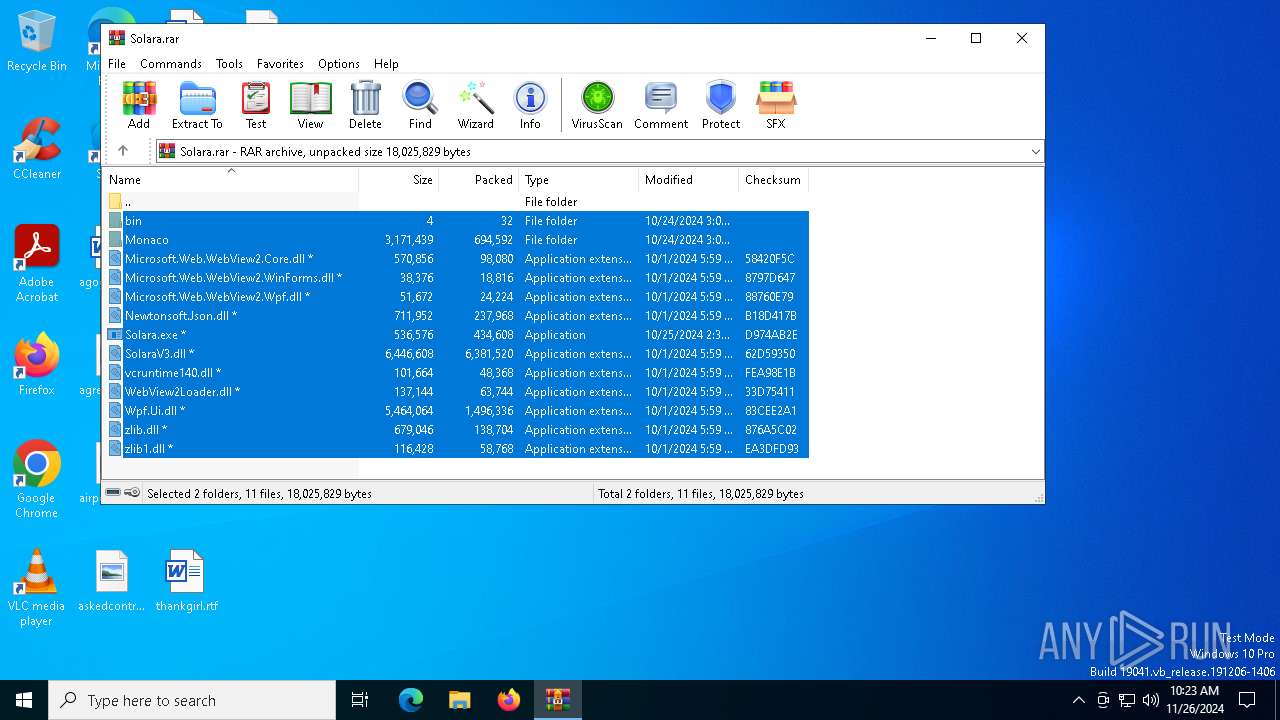
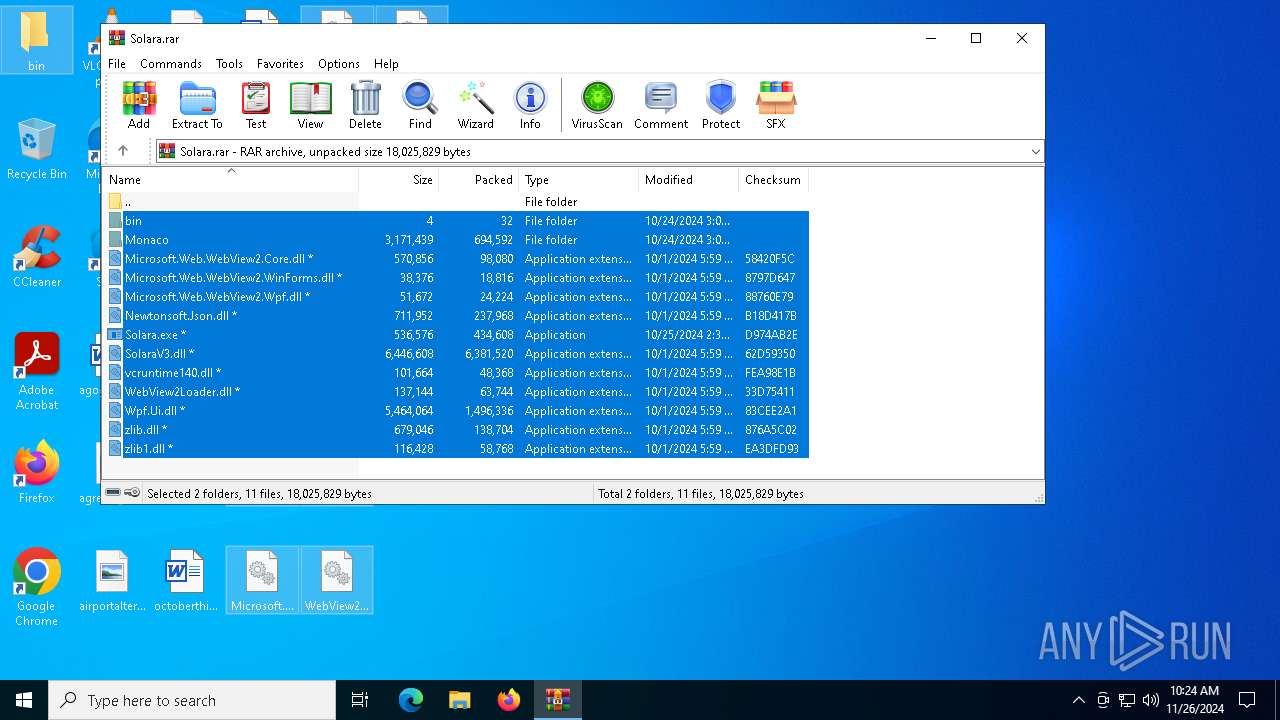
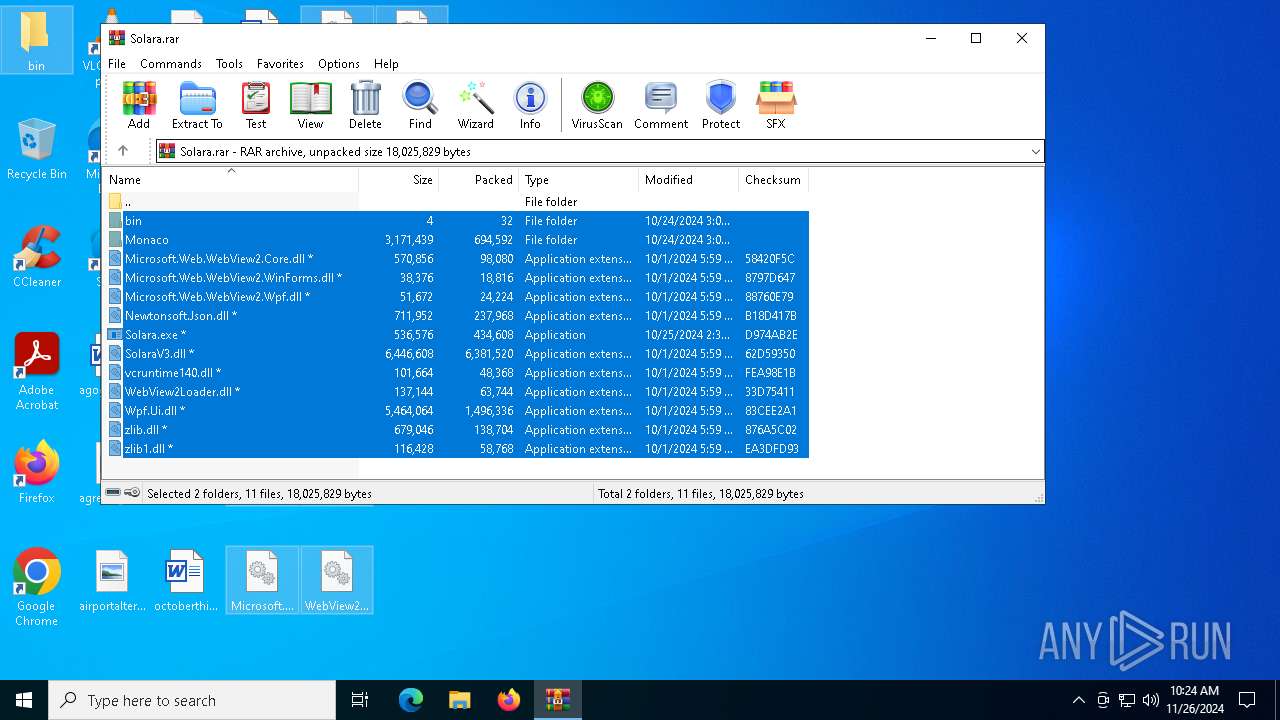
| download: | /Anviktor/Solara-Executor/releases/download/Download/Solara.rar |
| Full analysis: | https://app.any.run/tasks/920696b2-7556-456e-8b5f-a88a6d11998a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 26, 2024, 10:21:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8CFFCEA0D48F145C70FABBAAA4B2E12A |
| SHA1: | 7922A0AAA24833C3333944EADC504273730FAC4F |
| SHA256: | 62A864230570B2C77C51D4A171E9693B10E809161EDE1FCB51015B6296FB1700 |
| SSDEEP: | 98304:TC1nmnyYSuNb38uHkgTWnyQIr1SnBv4zcwk87wTyy+Fg8tdRzLs5ZY4hzaDQHV5k:D4vvMh8O/ePQNsC3T |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2192)
LUMMA has been detected (SURICATA)
- Solara.exe (PID: 2736)
- svchost.exe (PID: 2192)
SUSPICIOUS
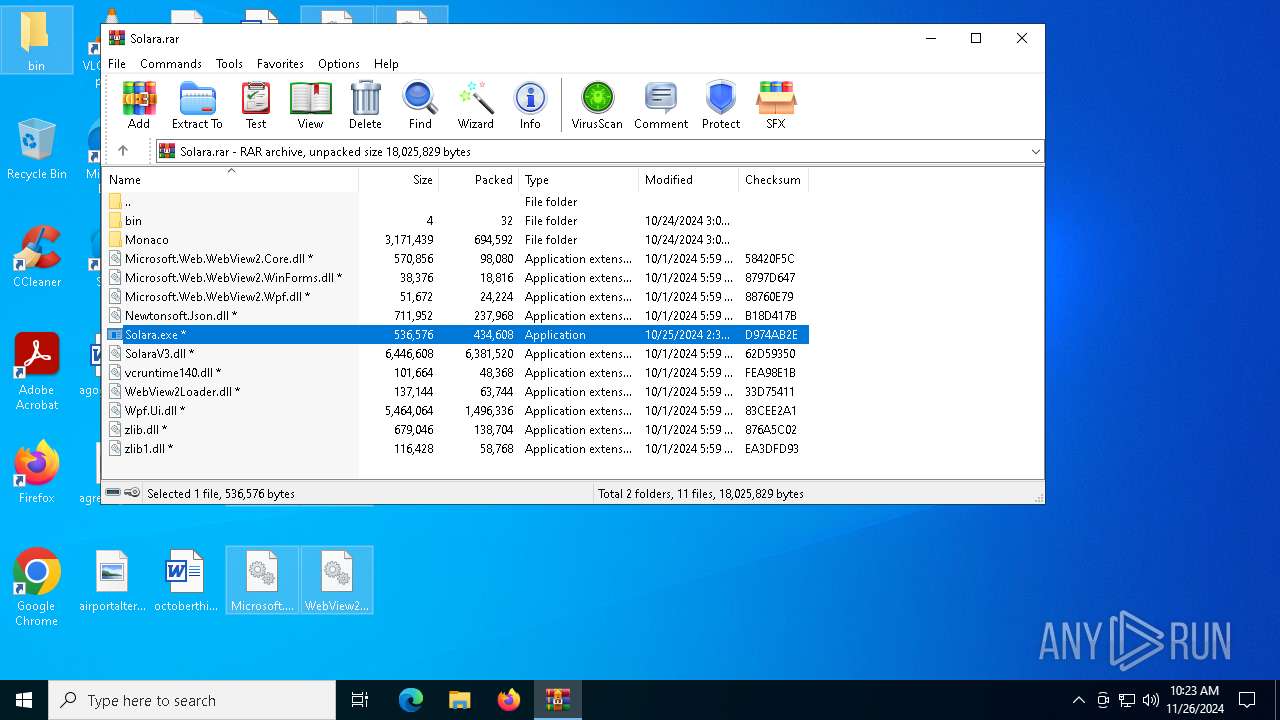
Process drops legitimate windows executable
- WinRAR.exe (PID: 7020)
Starts a Microsoft application from unusual location
- Solara.exe (PID: 6928)
- Solara.exe (PID: 2736)
Application launched itself
- Solara.exe (PID: 6928)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- Solara.exe (PID: 2736)
Executes application which crashes
- Solara.exe (PID: 6928)
INFO
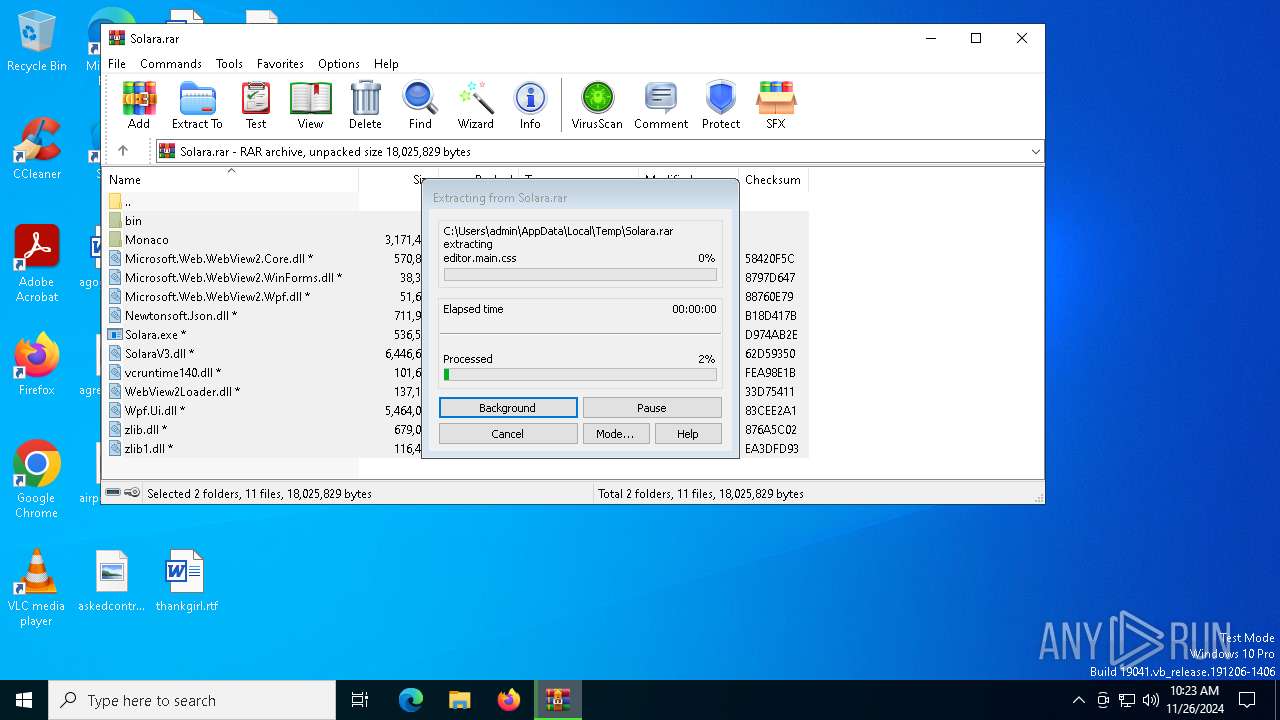
The process uses the downloaded file
- WinRAR.exe (PID: 7020)
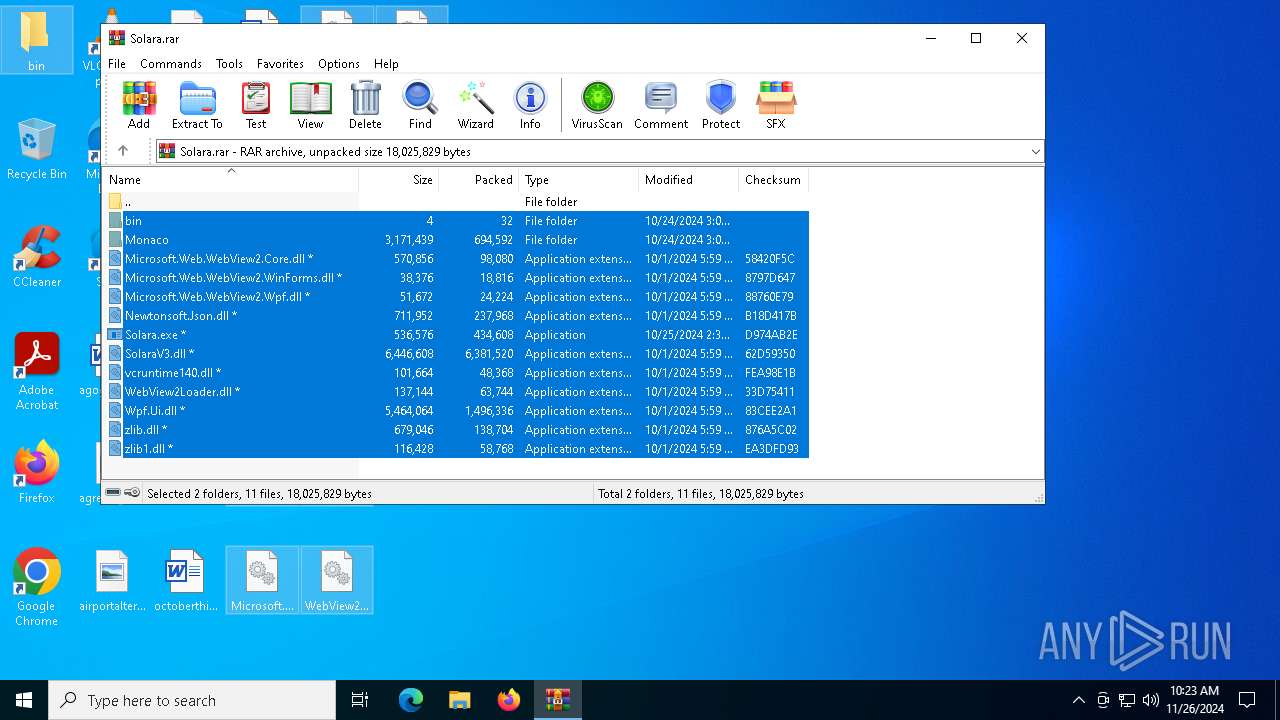
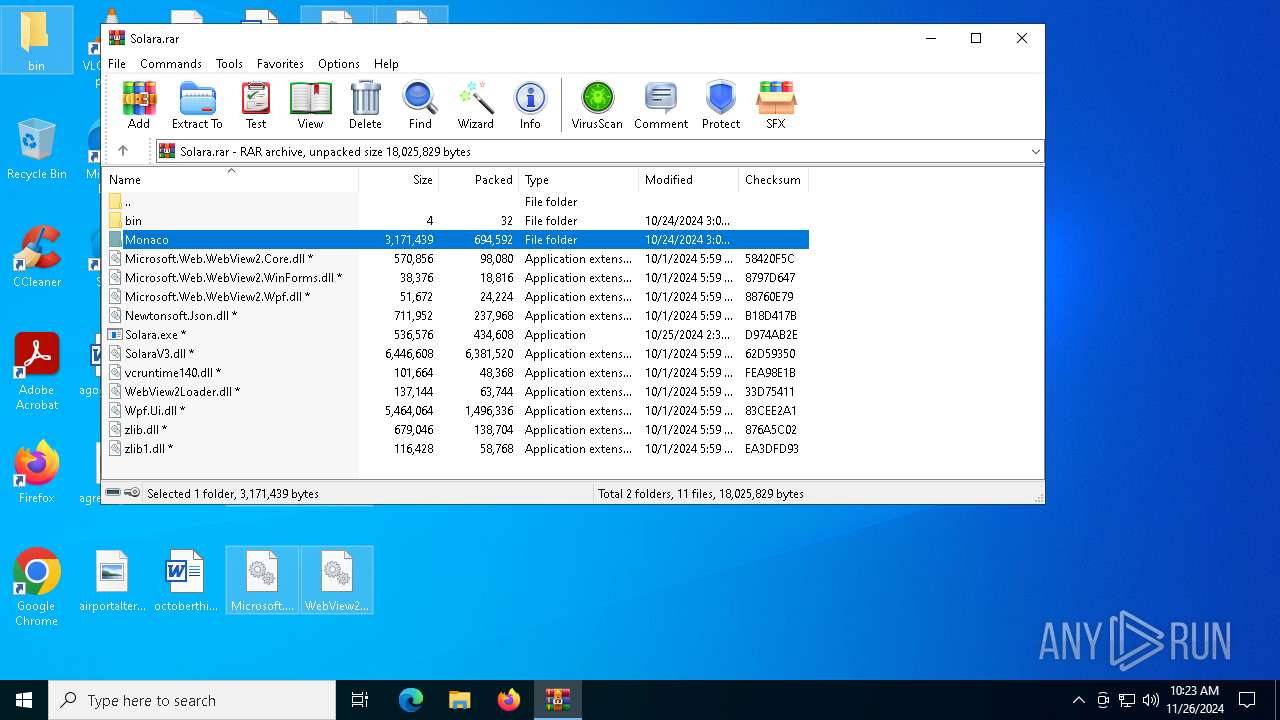
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7020)
Manual execution by a user
- Solara.exe (PID: 6928)
Reads the computer name
- Solara.exe (PID: 2736)
Reads the software policy settings
- WerFault.exe (PID: 6404)
- Solara.exe (PID: 2736)
Checks proxy server information
- WerFault.exe (PID: 6404)
Checks supported languages
- Solara.exe (PID: 6928)
- Solara.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 16 |
| UncompressedSize: | - |
| OperatingSystem: | Win32 |
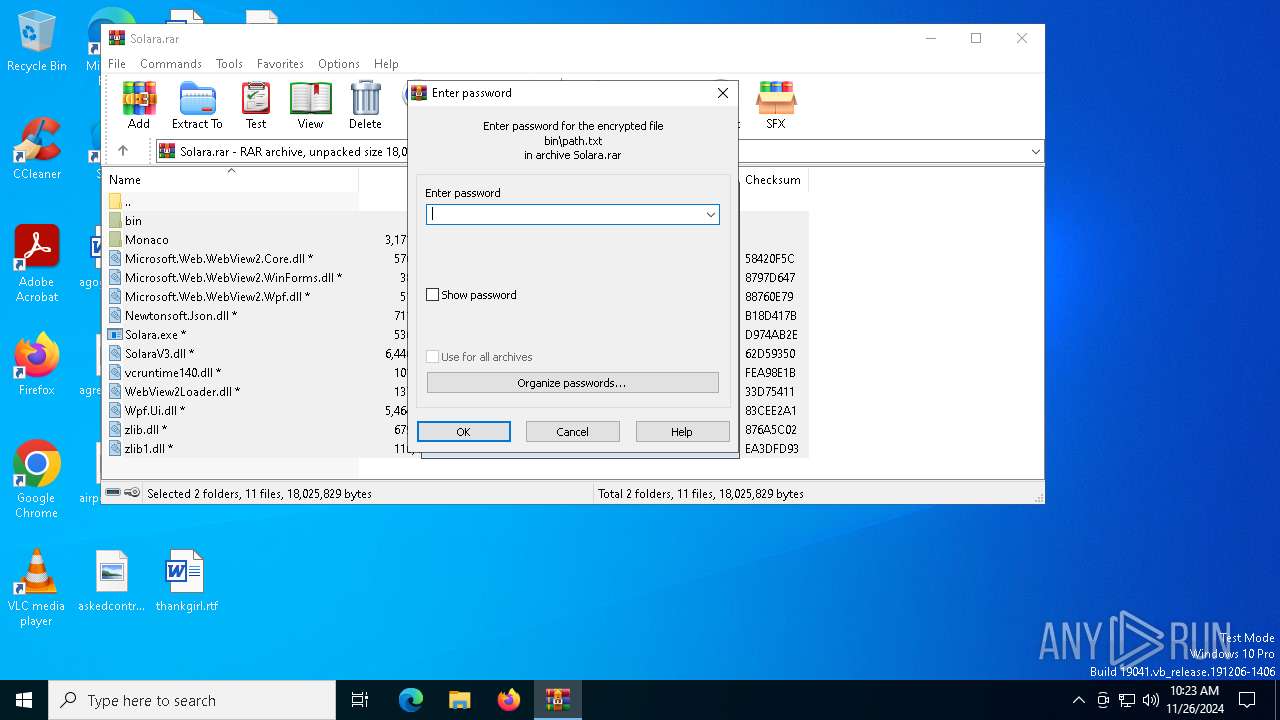
| ArchivedFileName: | bin/path.txt |
Total processes
124
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\Desktop\Solara.exe" | C:\Users\admin\Desktop\Solara.exe | Solara.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6928 -s 348 | C:\Windows\SysWOW64\WerFault.exe | Solara.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6928 | "C:\Users\admin\Desktop\Solara.exe" | C:\Users\admin\Desktop\Solara.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print Utility Exit code: 3221225477 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Solara.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 237
Read events
5 228
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Solara.rar | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
10
Suspicious files
183
Text files
8
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\index.js | binary | |
MD5:0E709BFB5675FF0531C925B909B58008 | SHA256:ED94FD8980C043BAD99599102291E3285323B99CE0EB5D424C00E3DEA1A34E67 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\combined.html | html | |
MD5:AA2CA4C253C6D910B5B82D45511278A6 | SHA256:497433C79B98E15BEF1F21F53858396347341796DAABBA408DF2D703D45602E9 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\bin\version.txt | text | |
MD5:F316C11A8ED434C596323EC515FF4779 | SHA256:00CF137BB82661B4E73DF6EE0163B78F993CBDB3534788E9ECBEF30850A53033 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\array-flatten\array-flatten.js | binary | |
MD5:4B17FA06C54846B686B8B799E9DD253A | SHA256:766CA145B6D25E3D60F352A716E8FA1876BCDF362C0767C360CF24F335BC281E | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\body-parser\lib\types\text.js | binary | |
MD5:BEB4ADA09306F8D6435566D9E88076D3 | SHA256:54A6E8EF720B06A300B21F6C60387805DEC743A64154784A609DFE8C6860776A | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\body-parser\lib\types\json.js | binary | |
MD5:6B036408F968978BF9668496DB9953BA | SHA256:44F8B529333004E2AAFF6DB3A1DBE7068F1AC5FA1173E9634686A78C2262AF35 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\array-flatten\package.json | binary | |
MD5:CB1AA7F817100A03395DD0163BF6EBE9 | SHA256:5C5E0E10CFA23F163D1FE68AA57A881D09CAC39D720E1361C697B86C4D33E0F5 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\accepts\index.js | binary | |
MD5:4FE4D2C90A2FD19D6E97443A7D24F815 | SHA256:BE2DECBD50610E8F995C1E312EE4DD6D7C1244CFDF03EE4C4A3DA68E572DADA1 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\body-parser\lib\types\urlencoded.js | binary | |
MD5:906A833480CE8841BFA5AEB95B5C085F | SHA256:752717D87AAD57451638AF2073B04EBA964F348910C0BCF0070C43E732DE5EB2 | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7020.41523\Monaco\fileaccess\node_modules\accepts\package.json | binary | |
MD5:32A15D6909FCAE63E52D8664593D32D5 | SHA256:E5716D5D939DB08C5C28EC6AE86ED67BE5320F91089E2673FCA1C5B876E57AA3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
46
DNS requests
34
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6404 | WerFault.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6404 | WerFault.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
2160 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
2160 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 23.212.110.210:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2160 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (fadehairucw .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (crisiwarny .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (thumbystriw .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (messejawu .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (presticitpo .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (necklacedmny .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (scriptyprefej .store) |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious Domain by Cloudflare (founpiuer .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (founpiuer .store) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (navygenerayk .store) |