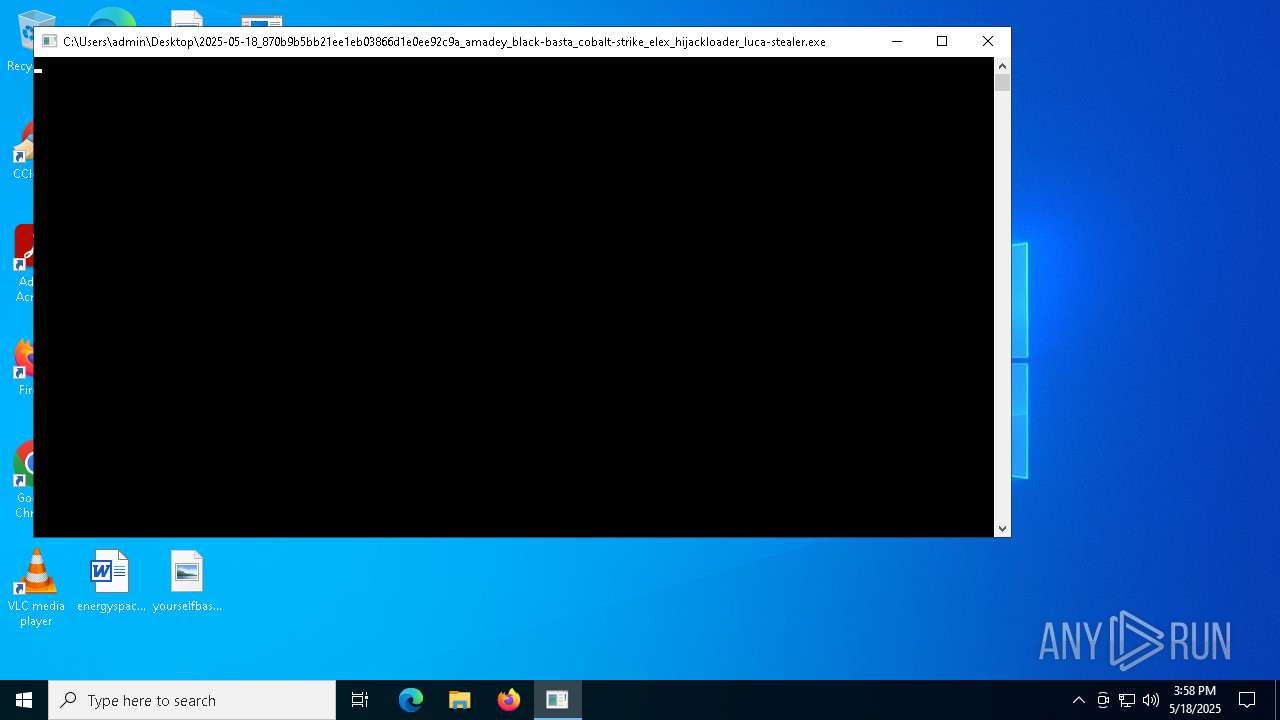
| File name: | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer |
| Full analysis: | https://app.any.run/tasks/de0a88cd-b046-4be4-b09c-45d2cc30bb51 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | May 18, 2025, 15:58:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 870B9B5BB21EE1EB03866D1E0EE92C9A |
| SHA1: | EB2185DD93D61357C5AA6A0AE320A3D3B1B18F04 |
| SHA256: | 62A3266F5FE8FFC5CE1A1B9E0FDCF75F1FAE2AD40FE5C4F3C02D406EA64ABDA1 |
| SSDEEP: | 6144:sdaAn+pJ6QrOawPzog8XVLwgUXTSuNpoIIaU:sdaAn+poPzogKEgwSu0IIaU |
MALICIOUS
Changes the autorun value in the registry
- 1128318430.exe (PID: 5936)
Connects to the CnC server
- syscrondvr.exe (PID: 5164)
PHORPIEX has been detected (SURICATA)
- syscrondvr.exe (PID: 5164)
PHORPIEX has been detected (YARA)
- syscrondvr.exe (PID: 5164)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
- syscrondvr.exe (PID: 5164)
Executable content was dropped or overwritten
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
- 1128318430.exe (PID: 5936)
Connects to the server without a host name
- C025.exe (PID: 1180)
- syscrondvr.exe (PID: 5164)
Potential Corporate Privacy Violation
- C025.exe (PID: 1180)
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
Process requests binary or script from the Internet
- C025.exe (PID: 1180)
Starts itself from another location
- 1128318430.exe (PID: 5936)
Contacting a server suspected of hosting an CnC
- syscrondvr.exe (PID: 5164)
Connects to unusual port
- syscrondvr.exe (PID: 5164)
INFO
Checks proxy server information
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
- syscrondvr.exe (PID: 5164)
- slui.exe (PID: 3300)
Create files in a temporary directory
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
Checks supported languages
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- 1128318430.exe (PID: 5936)
- syscrondvr.exe (PID: 5164)
- C025.exe (PID: 1180)
- syscrondvr.exe (PID: 3888)
Reads the computer name
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
- syscrondvr.exe (PID: 5164)
Creates files or folders in the user directory
- 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe (PID: 4040)
- C025.exe (PID: 1180)
Failed to create an executable file in Windows directory
- 1128318430.exe (PID: 5936)
Auto-launch of the file from Registry key
- 1128318430.exe (PID: 5936)
Reads the machine GUID from the registry
- syscrondvr.exe (PID: 5164)
Reads the software policy settings
- slui.exe (PID: 3300)
Manual execution by a user
- syscrondvr.exe (PID: 3888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1970:01:01 15:50:05+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 186880 |
| InitializedDataSize: | 61440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
132
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Users\admin\AppData\Local\Temp\C025.exe" | C:\Users\admin\AppData\Local\Temp\C025.exe | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | C:\Users\admin\syscrondvr.exe | C:\Users\admin\syscrondvr.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\Desktop\2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe" | C:\Users\admin\Desktop\2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5164 | C:\Users\admin\syscrondvr.exe | C:\Users\admin\syscrondvr.exe | 1128318430.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5936 | C:\Users\admin\AppData\Local\Temp\1128318430.exe | C:\Users\admin\AppData\Local\Temp\1128318430.exe | C025.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 347
Read events
7 337
Write events
10
Delete events
0
Modification events
| (PID) Process: | (4040) 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4040) 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4040) 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1180) C025.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1180) C025.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1180) C025.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5936) 1128318430.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Settings |
Value: C:\Users\admin\syscrondvr.exe | |||
| (PID) Process: | (5164) syscrondvr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5164) syscrondvr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5164) syscrondvr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
5
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1180 | C025.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\newtpp[1].exe | executable | |
MD5:F30FDBF3448F67CBC3566F31729CB7A6 | SHA256:3A902ABB21D204ED6A0776789C9661F8B98E561FD0CA661EE37A7D8BD079E57B | |||
| 4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\32[1].exe | executable | |
MD5:0EC46393976EB51F307CC11D80BAE845 | SHA256:9175BA77AC91AFDC513CA64788A72BF12915247F64BB1F95C06B5A1938FA4A84 | |||
| 4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\C025.exe | executable | |
MD5:0EC46393976EB51F307CC11D80BAE845 | SHA256:9175BA77AC91AFDC513CA64788A72BF12915247F64BB1F95C06B5A1938FA4A84 | |||
| 5164 | syscrondvr.exe | C:\Users\admin\tbtnds.dat | binary | |
MD5:17945376C8CFC10E90F1ECD4626B7D3F | SHA256:400AD7A456827E9576DF54FAE7D887016EF6E92E08168F778EA15D15BCD67FB1 | |||
| 1180 | C025.exe | C:\Users\admin\AppData\Local\Temp\1128318430.exe | executable | |
MD5:F30FDBF3448F67CBC3566F31729CB7A6 | SHA256:3A902ABB21D204ED6A0776789C9661F8B98E561FD0CA661EE37A7D8BD079E57B | |||
| 5936 | 1128318430.exe | C:\Users\admin\syscrondvr.exe | executable | |
MD5:F30FDBF3448F67CBC3566F31729CB7A6 | SHA256:3A902ABB21D204ED6A0776789C9661F8B98E561FD0CA661EE37A7D8BD079E57B | |||
| 5164 | syscrondvr.exe | C:\Users\admin\tbtcmds.dat | binary | |
MD5:A690BB166290B53E7CC3C5CFD6AA9BC2 | SHA256:02573F4B0B52B69CE2F0932FB9A40D678F2A8C4B54D89E430C3EB6FC4D29CF96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
83
DNS requests
19
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5164 | syscrondvr.exe | GET | 404 | 185.156.72.39:80 | http://185.156.72.39/2 | unknown | — | — | malicious |
5164 | syscrondvr.exe | GET | 404 | 185.156.72.39:80 | http://185.156.72.39/1 | unknown | — | — | malicious |
4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | GET | 200 | 185.156.72.39:80 | http://185.156.72.39/32.exe | unknown | — | — | malicious |
2104 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1180 | C025.exe | GET | 200 | 185.156.72.39:80 | http://185.156.72.39/newtpp.exe | unknown | — | — | malicious |
5428 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
1180 | C025.exe | GET | 200 | 185.156.72.39:80 | http://185.156.72.39/peinstall.php | unknown | — | — | malicious |
5428 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5428 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | 185.156.72.39:80 | — | Tov Vaiz Partner | RU | malicious |
2104 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1180 | C025.exe | 185.156.72.39:80 | — | Tov Vaiz Partner | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | A Network Trojan was detected | ET MALWARE JS/Nemucod requesting EXE payload 2016-02-01 |
4040 | 2025-05-18_870b9b5bb21ee1eb03866d1e0ee92c9a_amadey_black-basta_cobalt-strike_elex_hijackloader_luca-stealer.exe | A Network Trojan was detected | ET MALWARE Possible Malicious Macro DL EXE Feb 2016 |
1180 | C025.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1180 | C025.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
1180 | C025.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5164 | syscrondvr.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
5164 | syscrondvr.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
5164 | syscrondvr.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
5164 | syscrondvr.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |