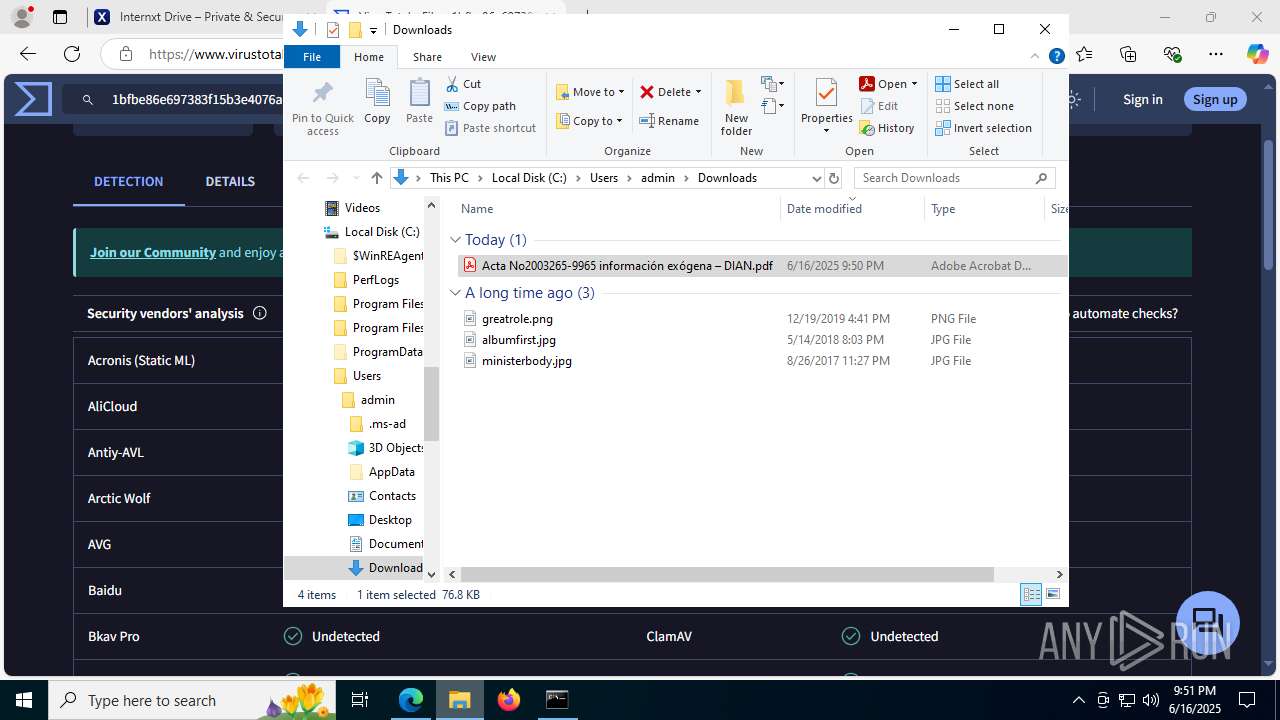
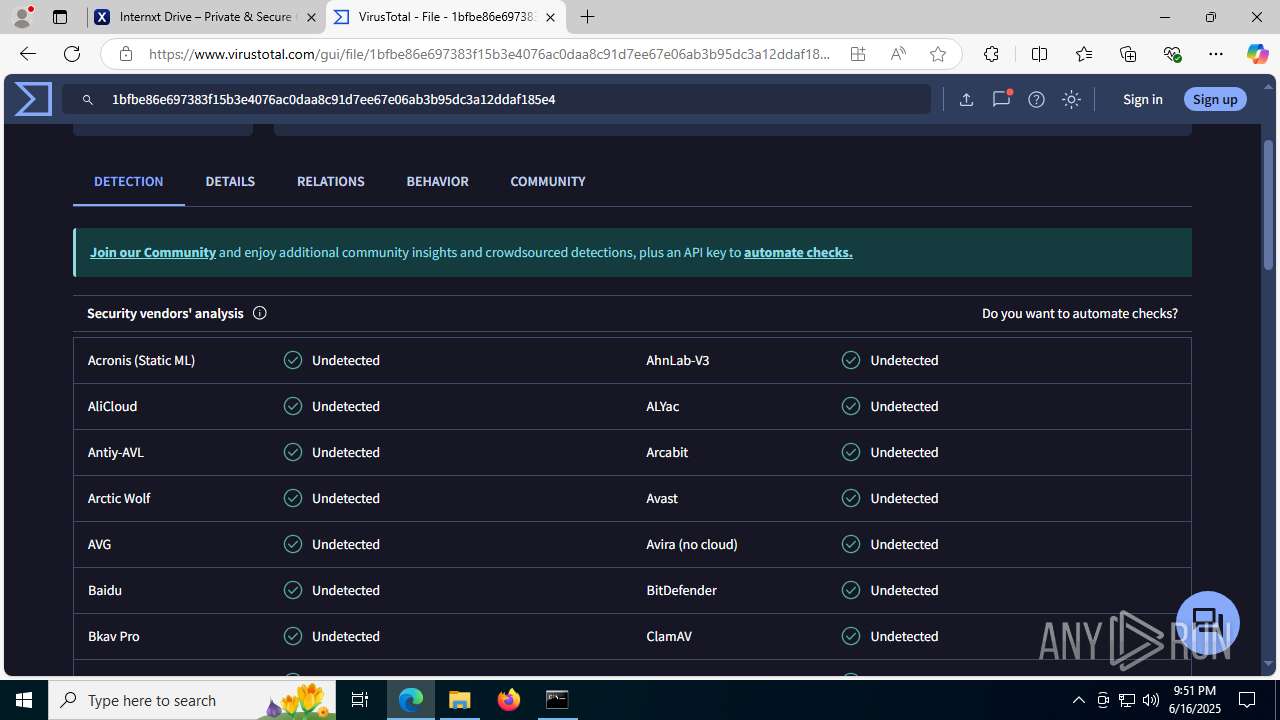
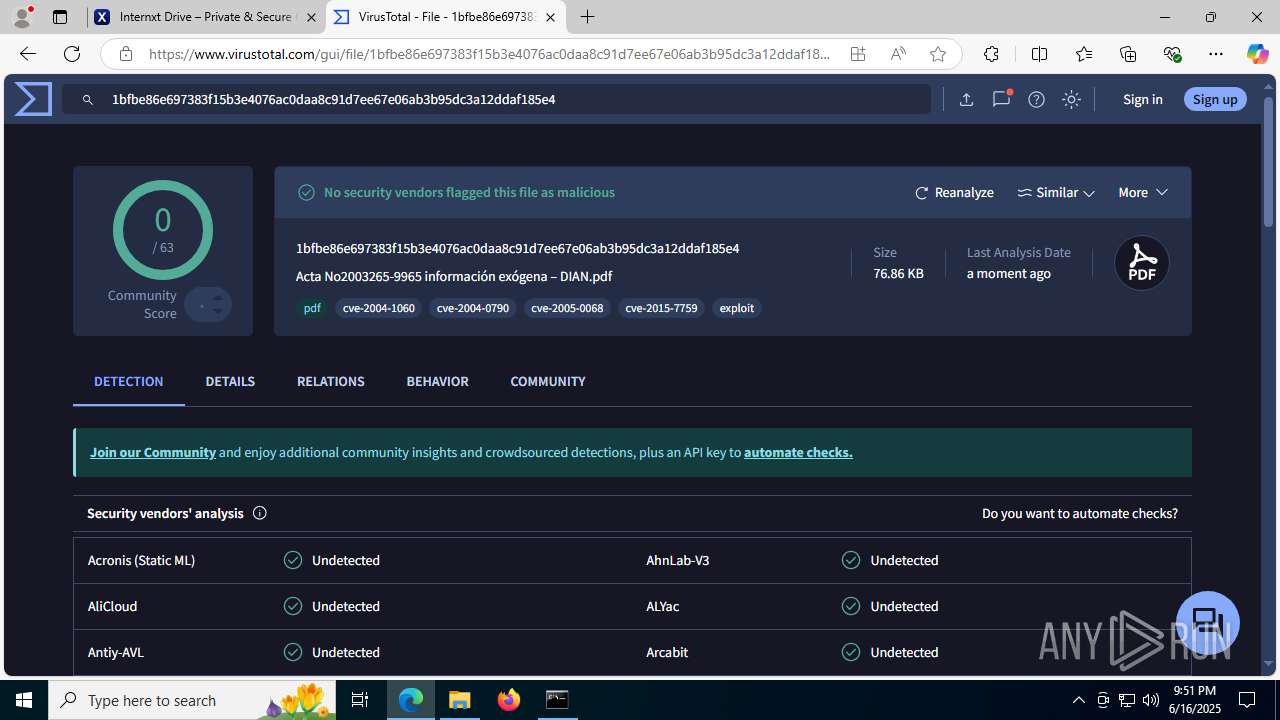
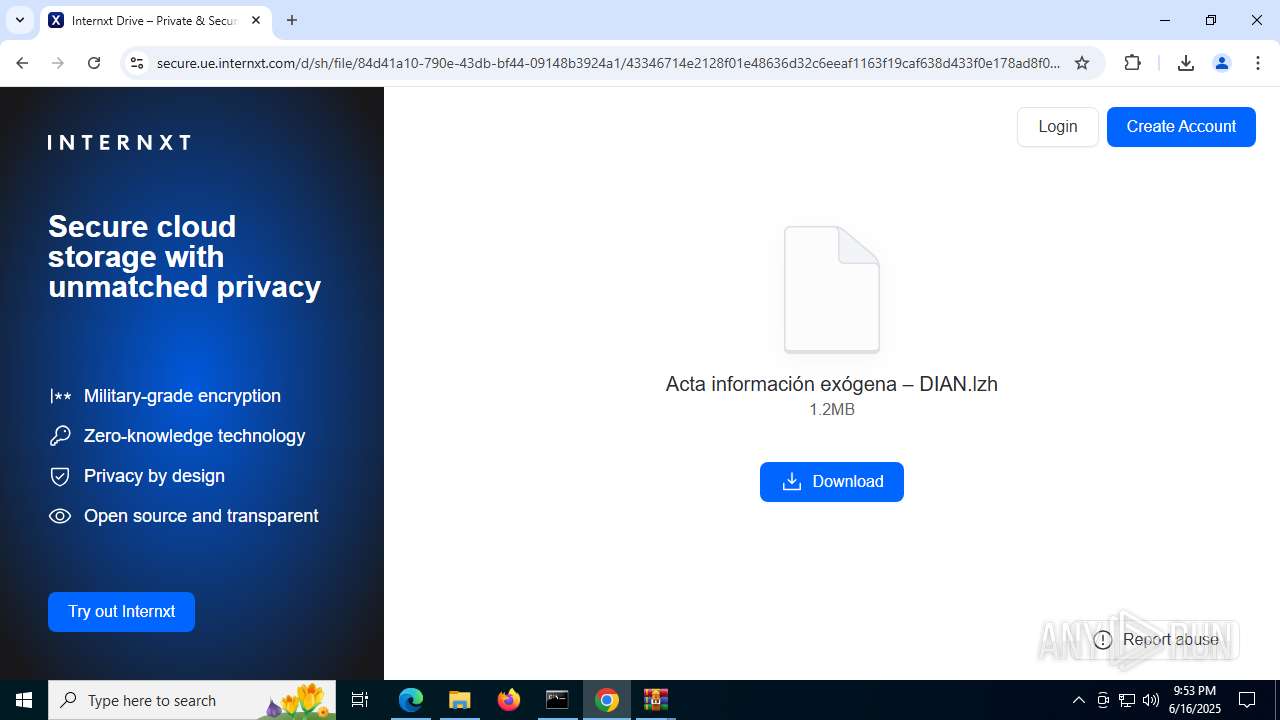
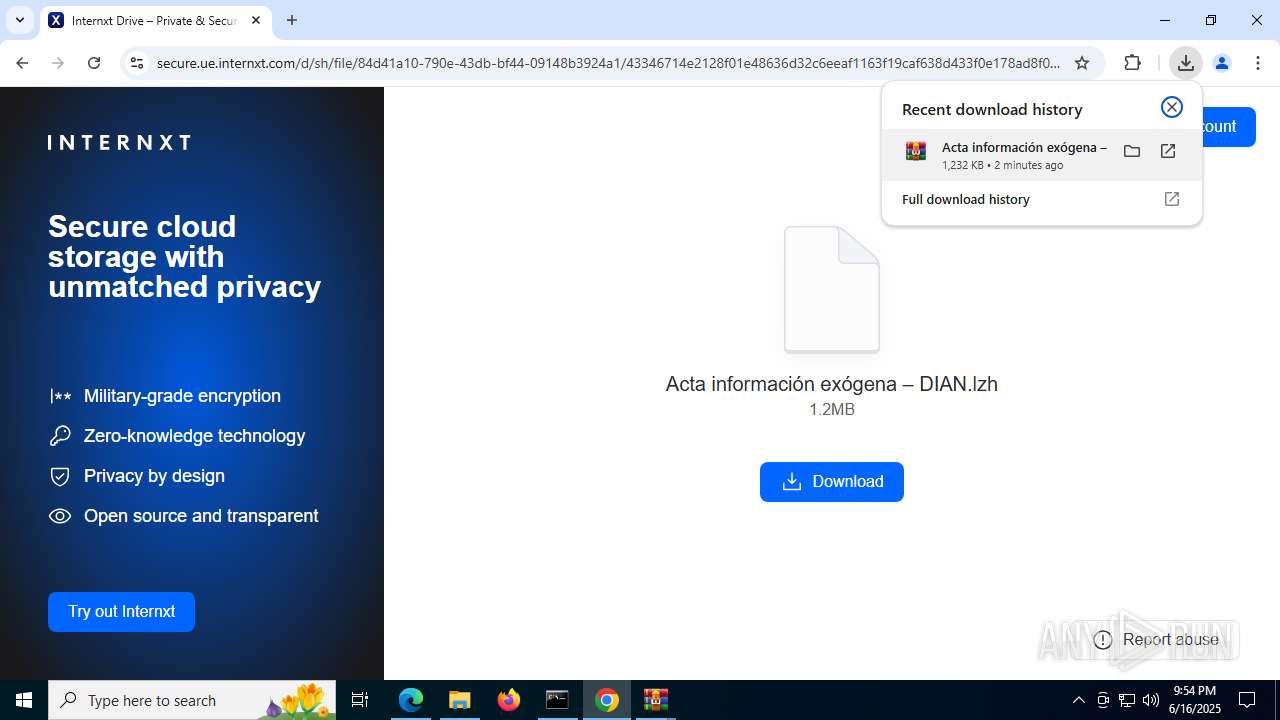
| URL: | https://share.eu.internxt.com/d/sh/file/78818e7f-9839-47bd-a9a6-b6912e9ed4d7/8b2de6fd86893a8558482bdc8696e3531c84e4486b6e03ebf7351fa8860588d5 |
| Full analysis: | https://app.any.run/tasks/538dfda9-362f-4d01-832c-ff90a7663439 |
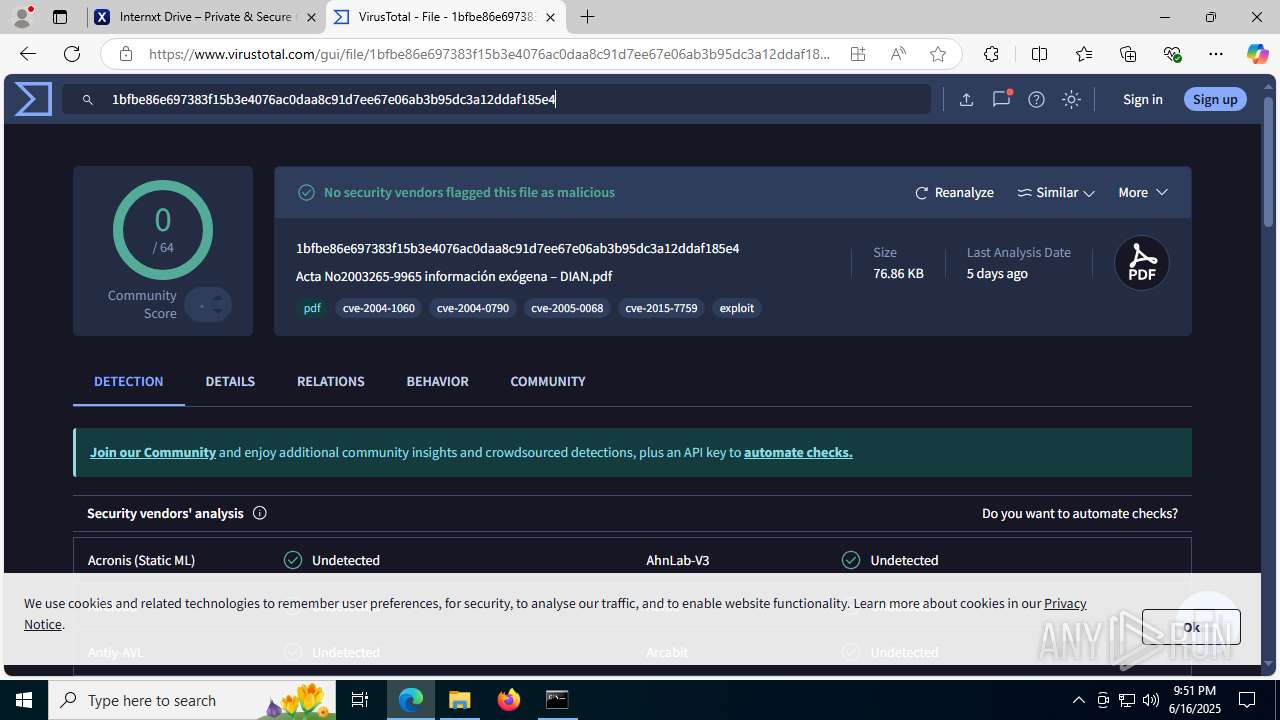
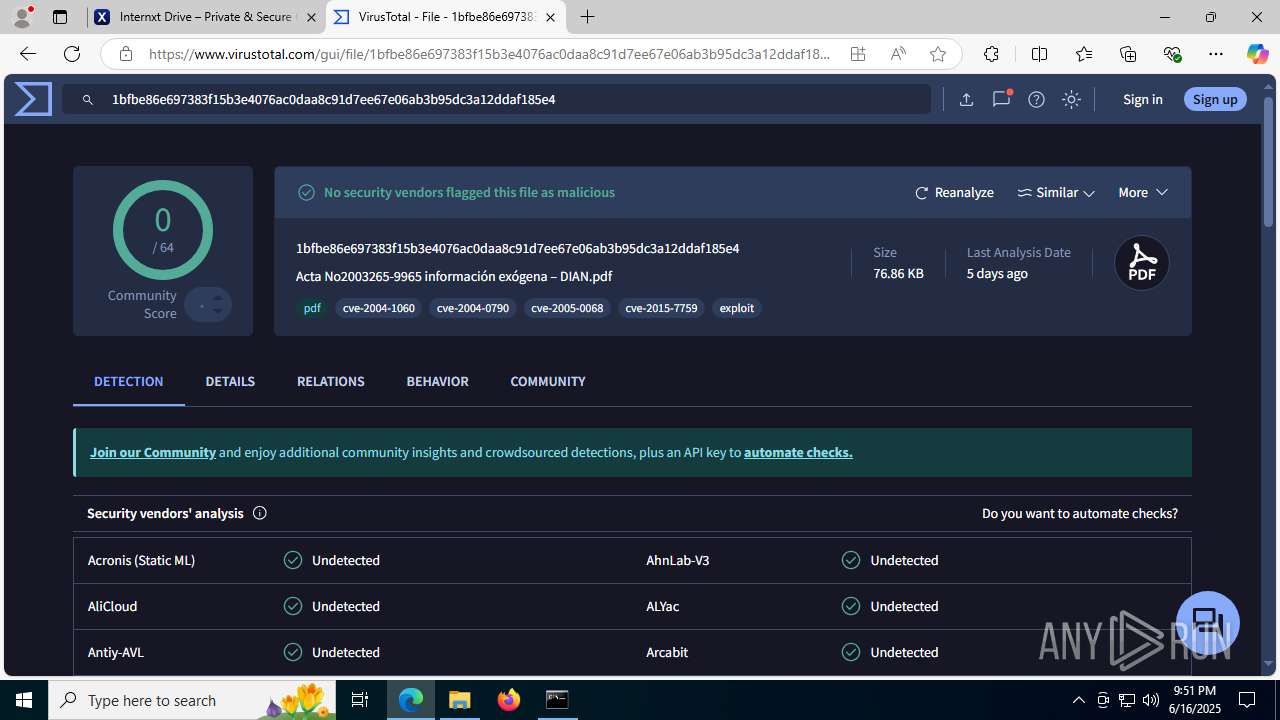
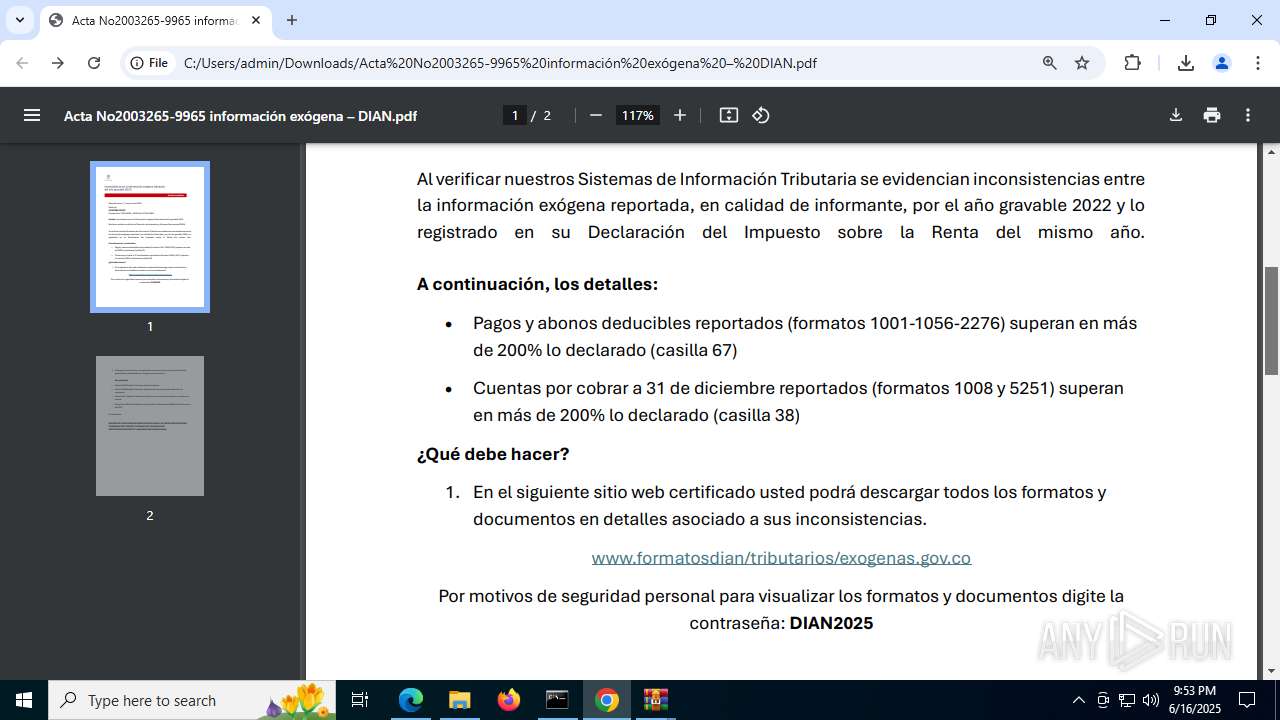
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 16, 2025, 21:50:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
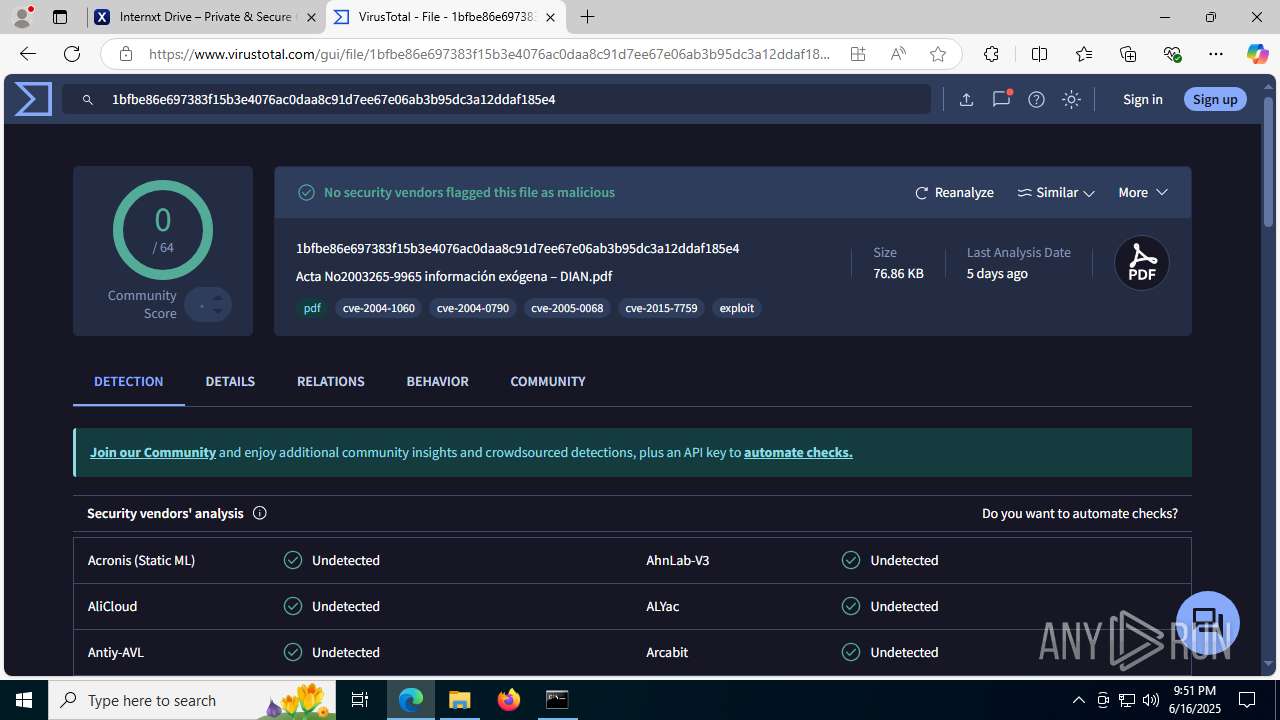
| MD5: | 14C93743416320243F22A4DF8196F8E9 |
| SHA1: | F3927E32DB740085660AF7604C00886A08C63190 |
| SHA256: | 62730E6AA2BE06966263D807F520FF05D8972E9E99FC9FEFD56C7EFF71F9CCA6 |
| SSDEEP: | 3:N8ADAeMlY9IBKXSB93d16IBAH5U7KwRqQBRhTwHHDSEYdR6ddmn:2ADAeMlYq93d1j6UewEAhUHH7YdMMn |
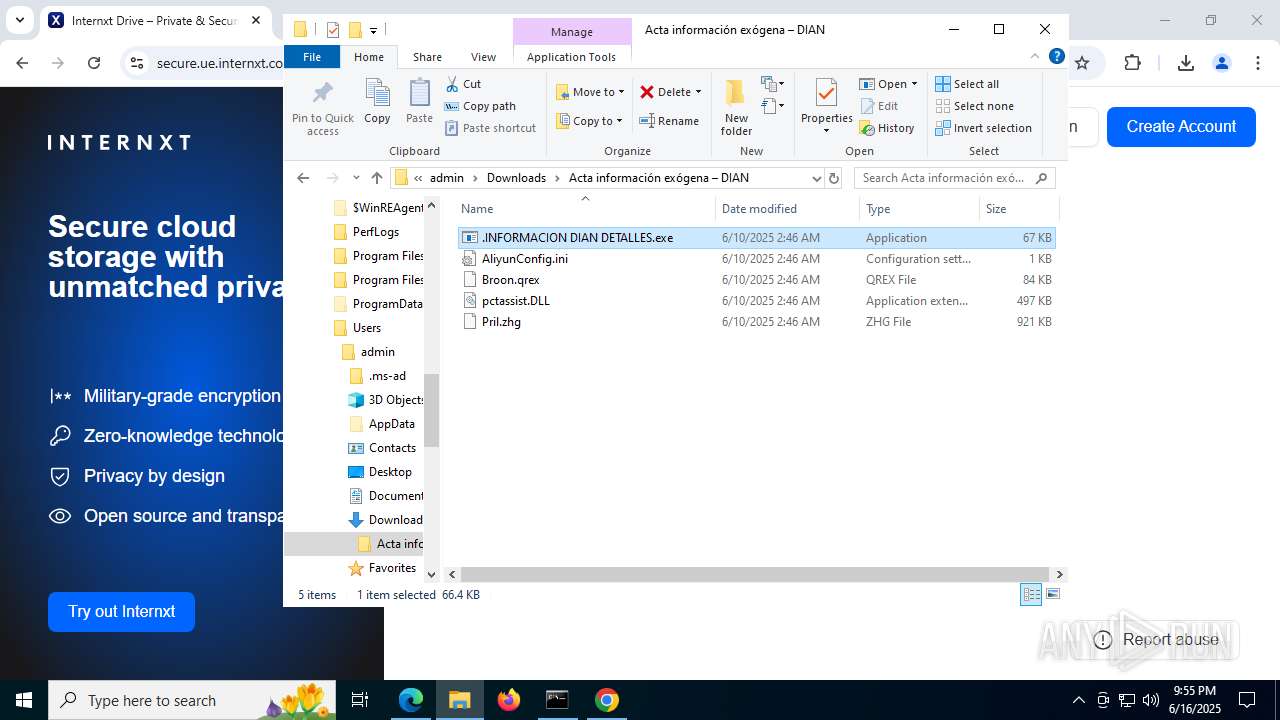
MALICIOUS
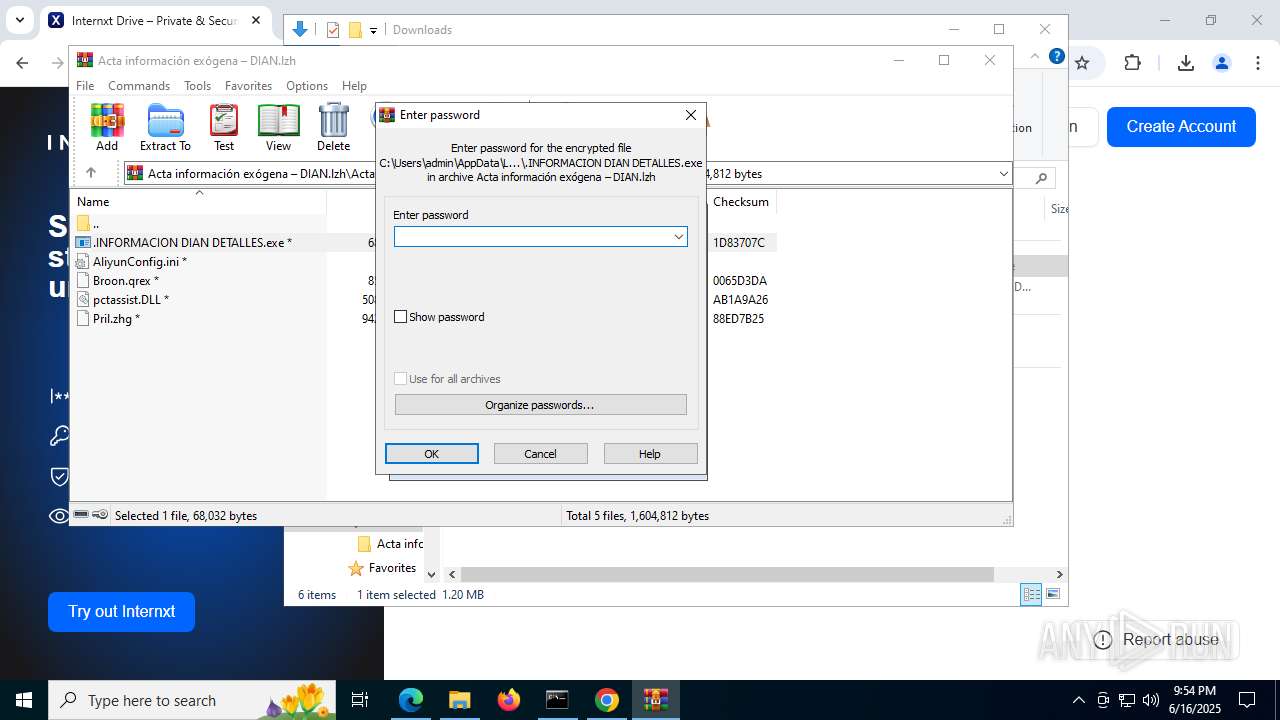
Executing a file with an untrusted certificate
- UltraInterfac32.exe (PID: 7212)
- UltraInterfac32.exe (PID: 7432)
- UltraInterfac32.exe (PID: 5124)
- UltraInterfac32.exe (PID: 1212)
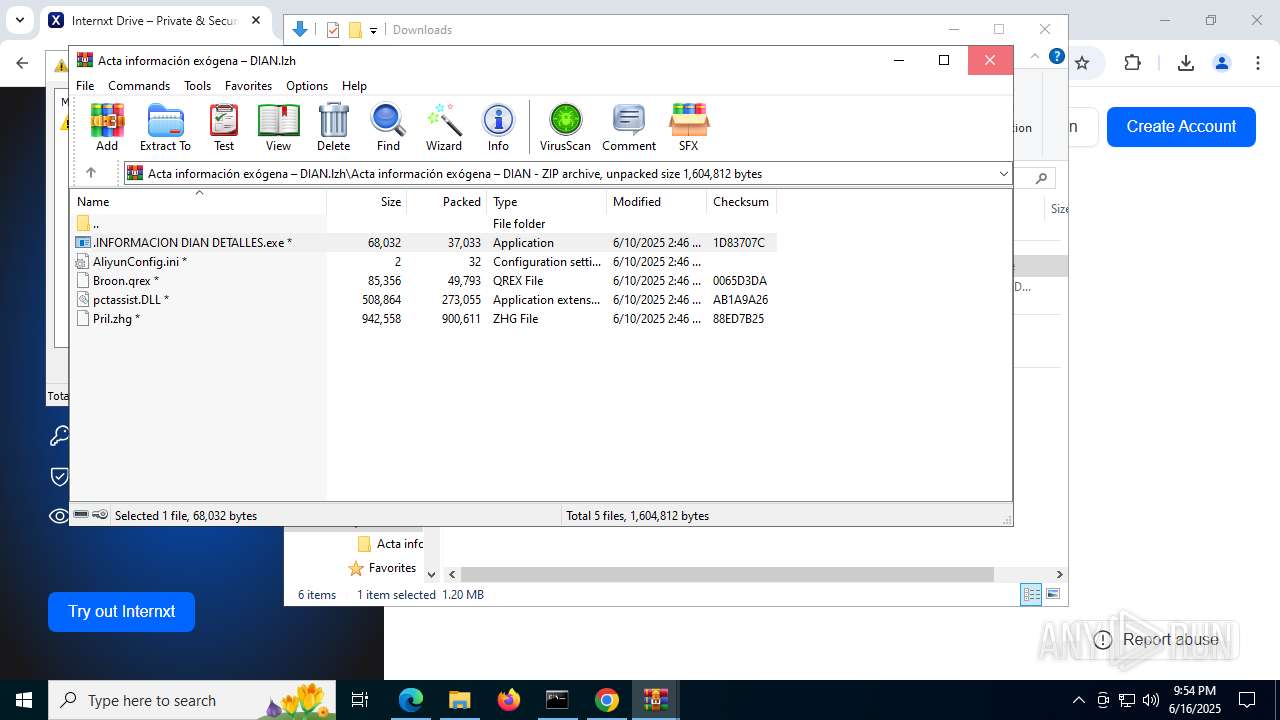
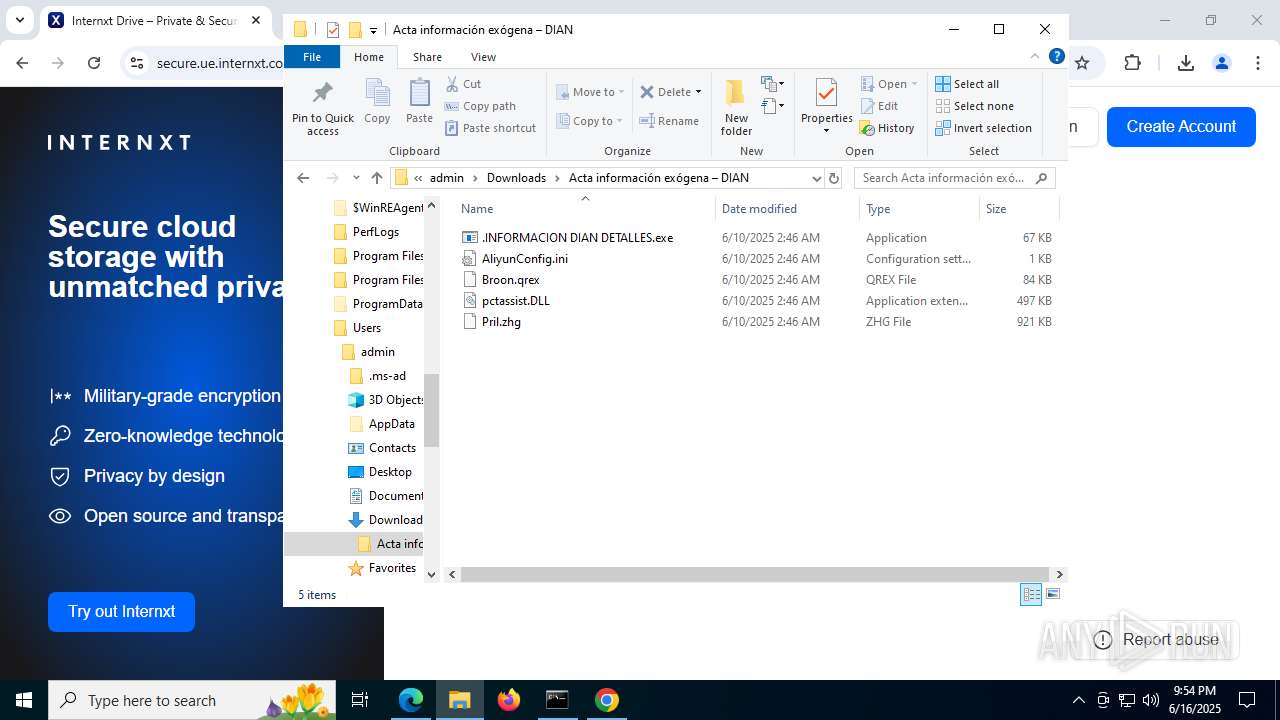
GENERIC has been found (auto)
- .INFORMACION DIAN DETALLES.exe (PID: 6308)
ASYNCRAT has been detected (SURICATA)
- UltraInterfac32.exe (PID: 7212)
SUSPICIOUS
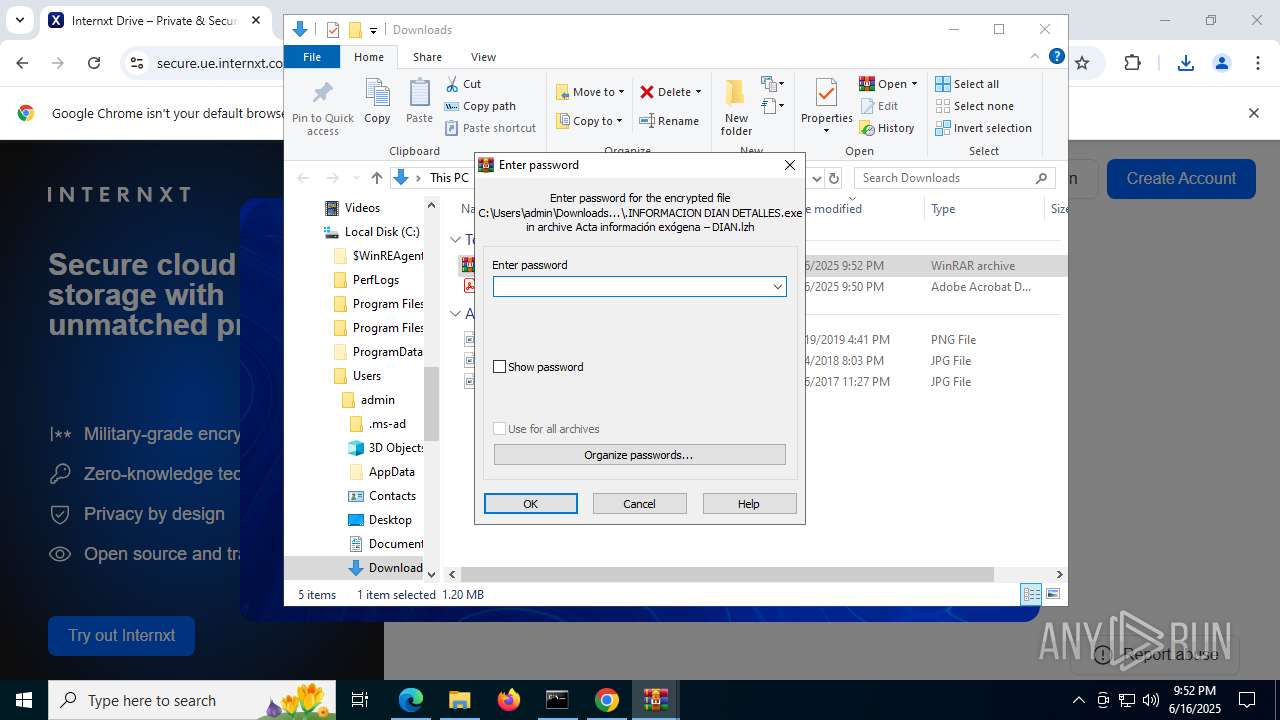
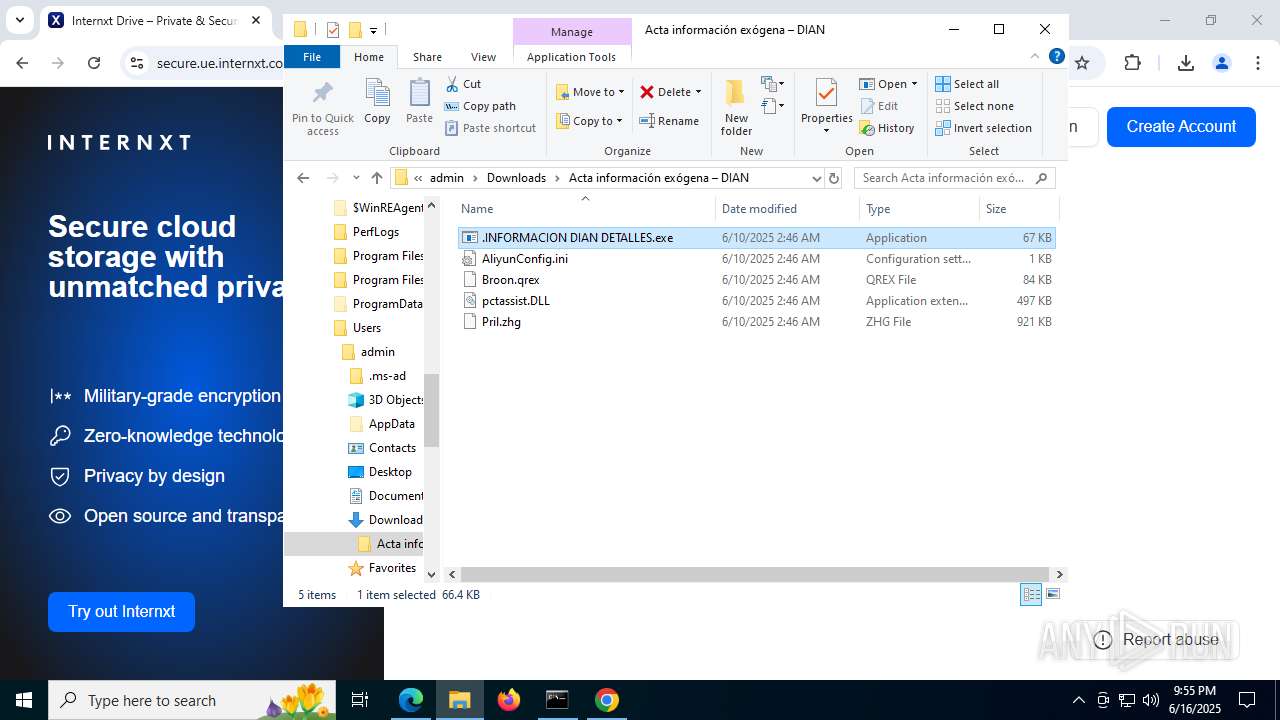
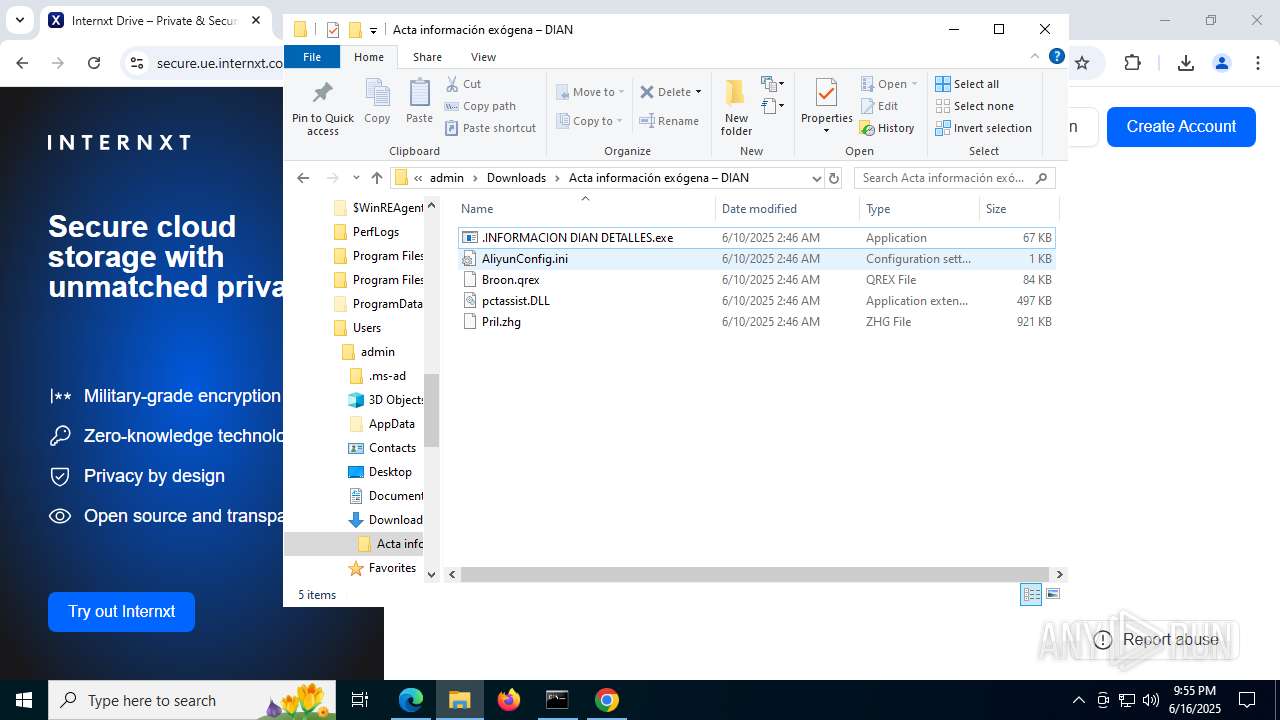
Executable content was dropped or overwritten
- .INFORMACION DIAN DETALLES.exe (PID: 6308)
Contacting a server suspected of hosting an CnC
- UltraInterfac32.exe (PID: 7212)
Connects to unusual port
- UltraInterfac32.exe (PID: 7212)
INFO
Reads the computer name
- identity_helper.exe (PID: 7520)
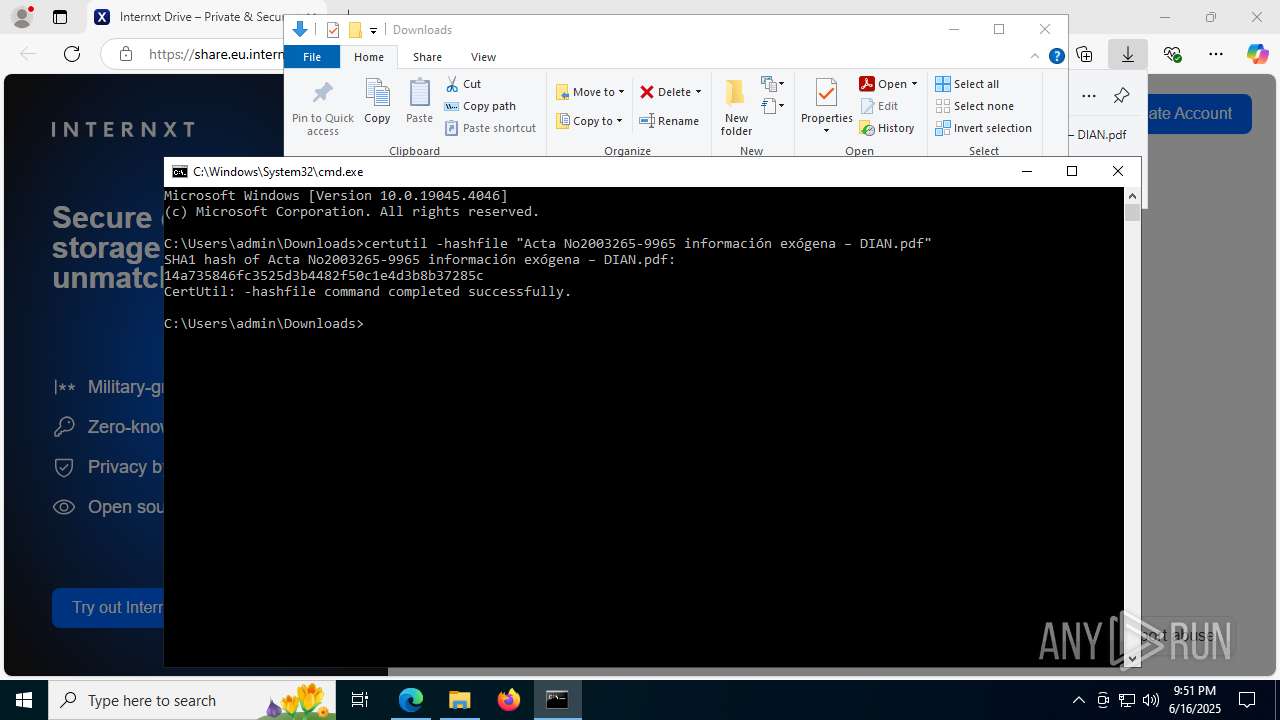
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 7448)
Checks supported languages
- identity_helper.exe (PID: 7520)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8172)
Reads Environment values
- identity_helper.exe (PID: 7520)
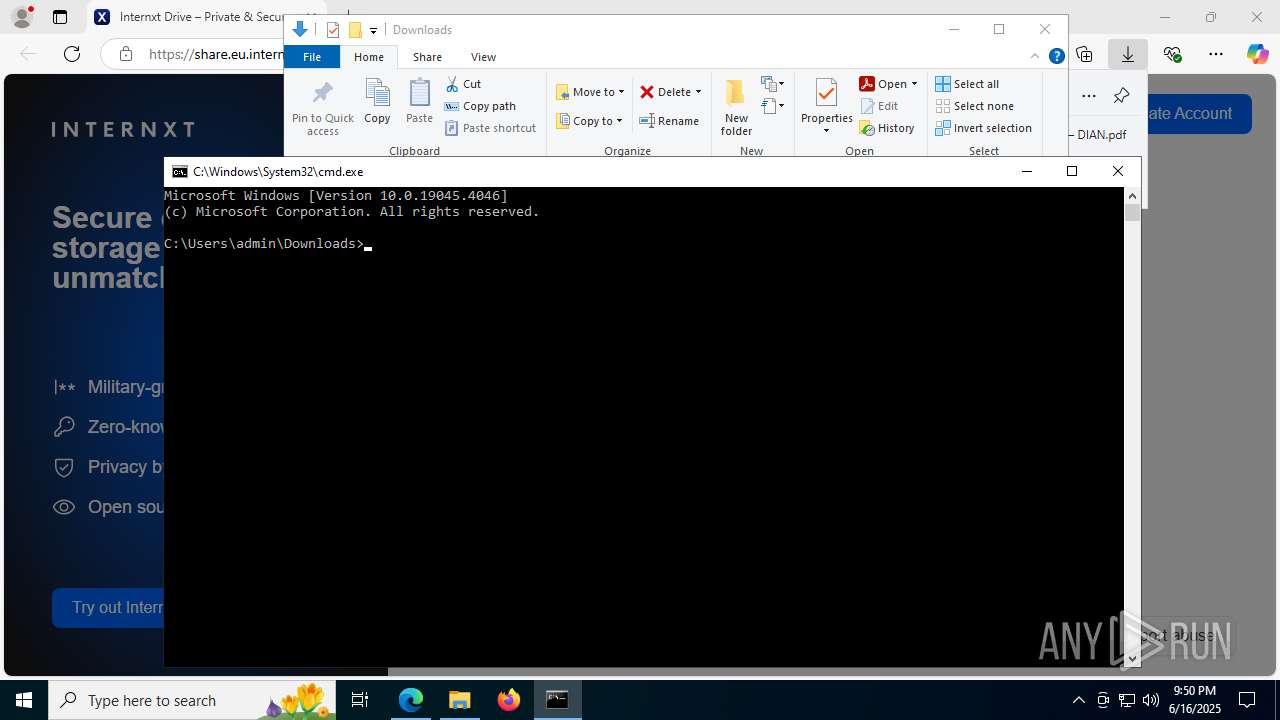
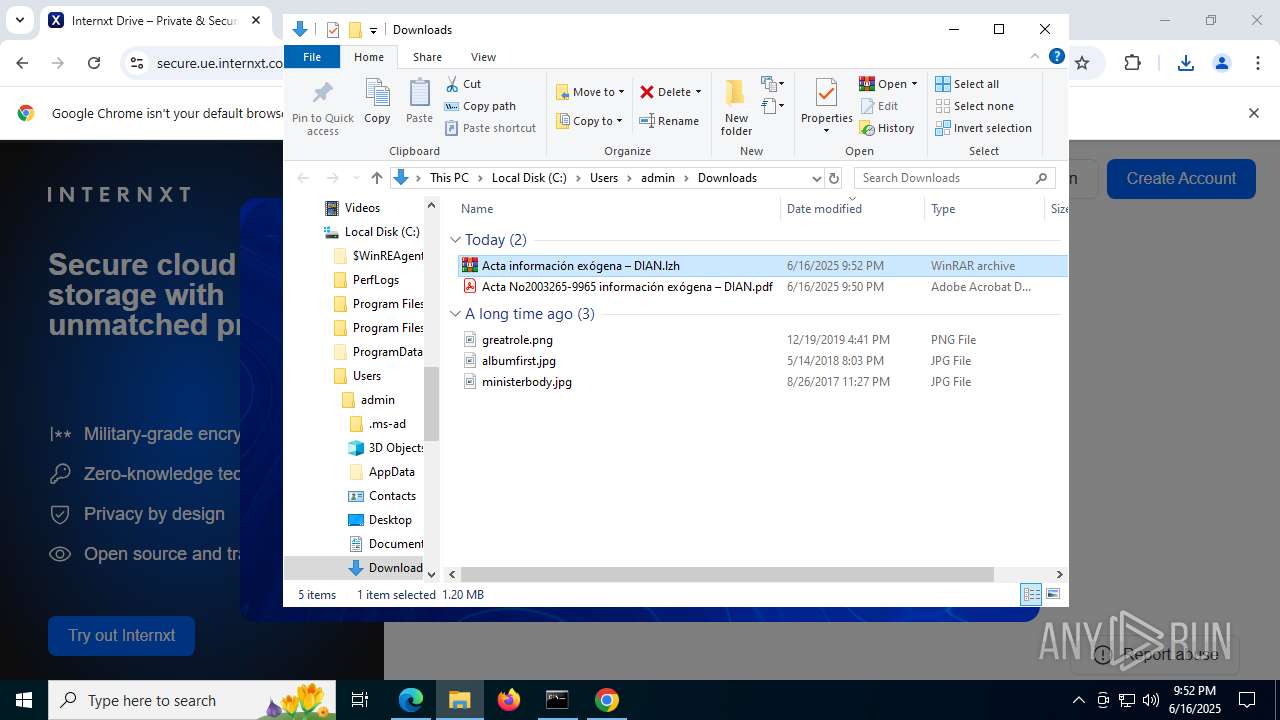
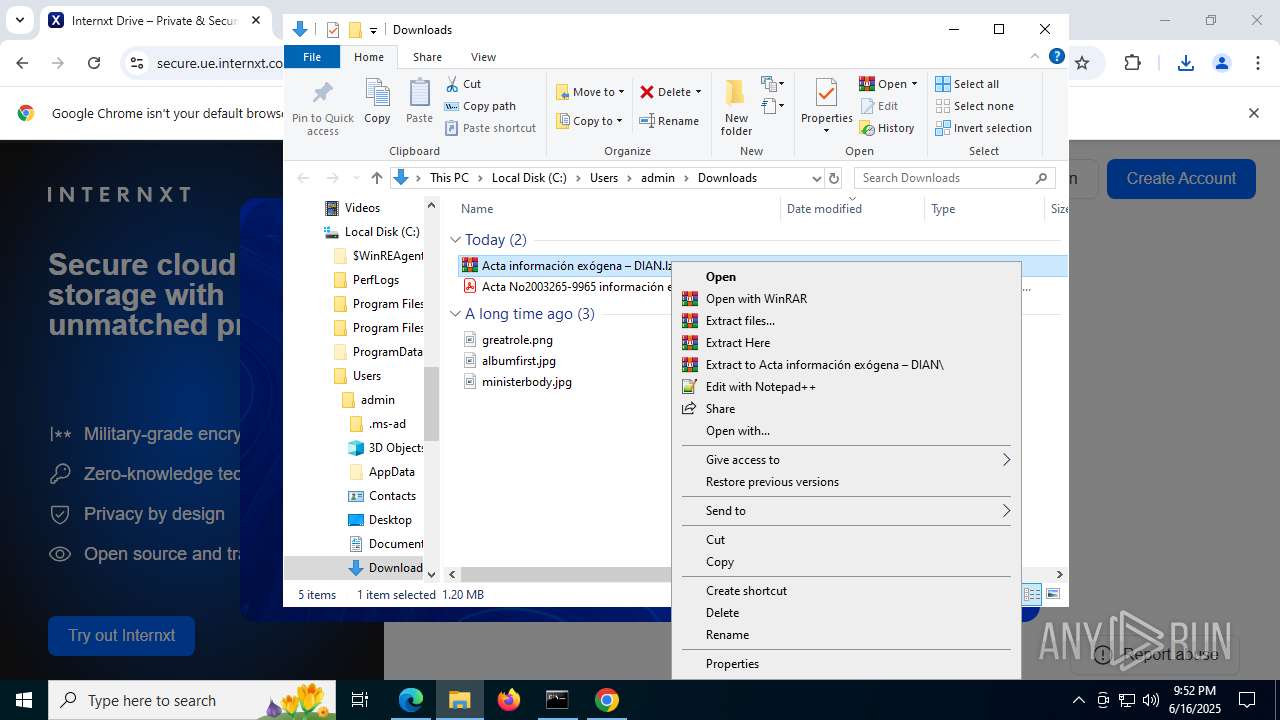
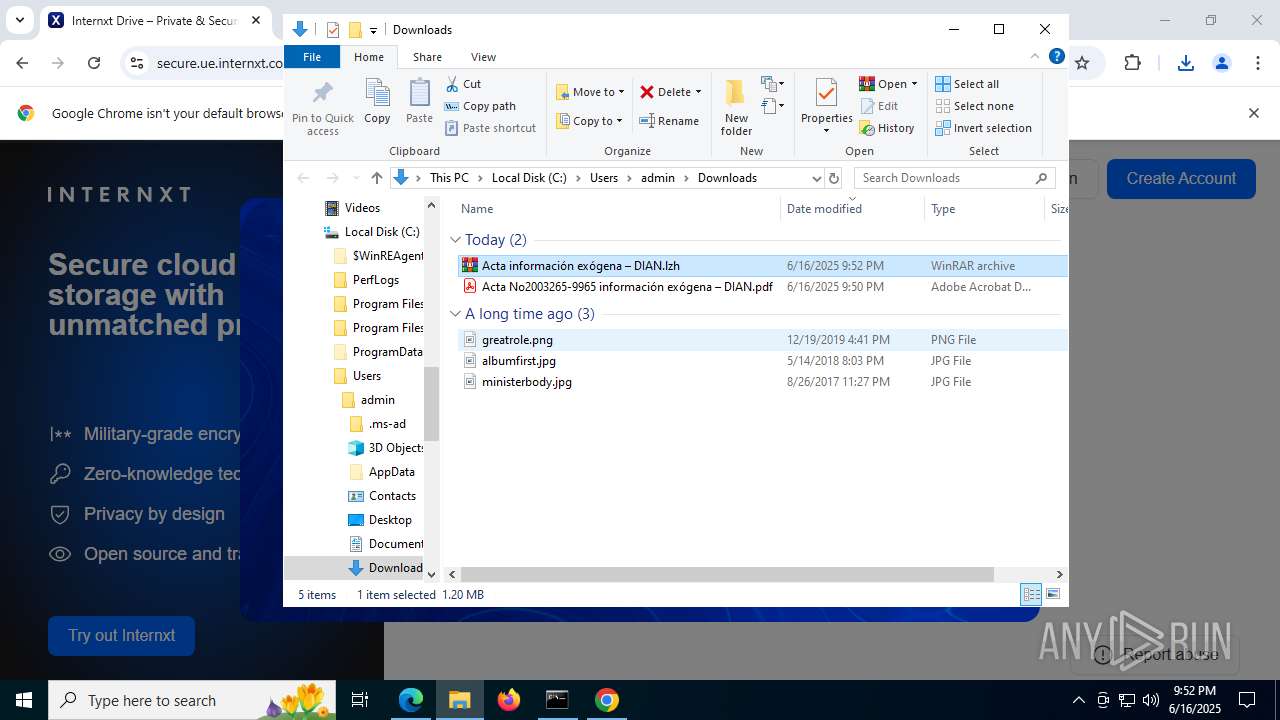
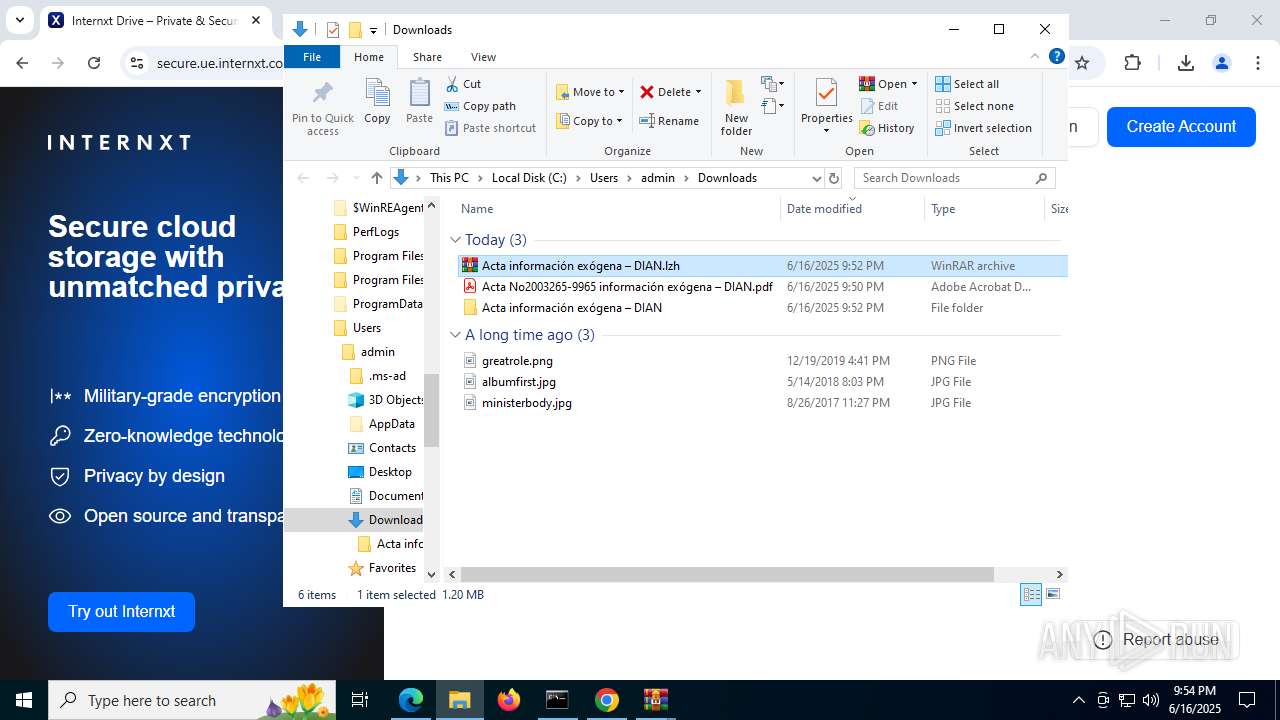
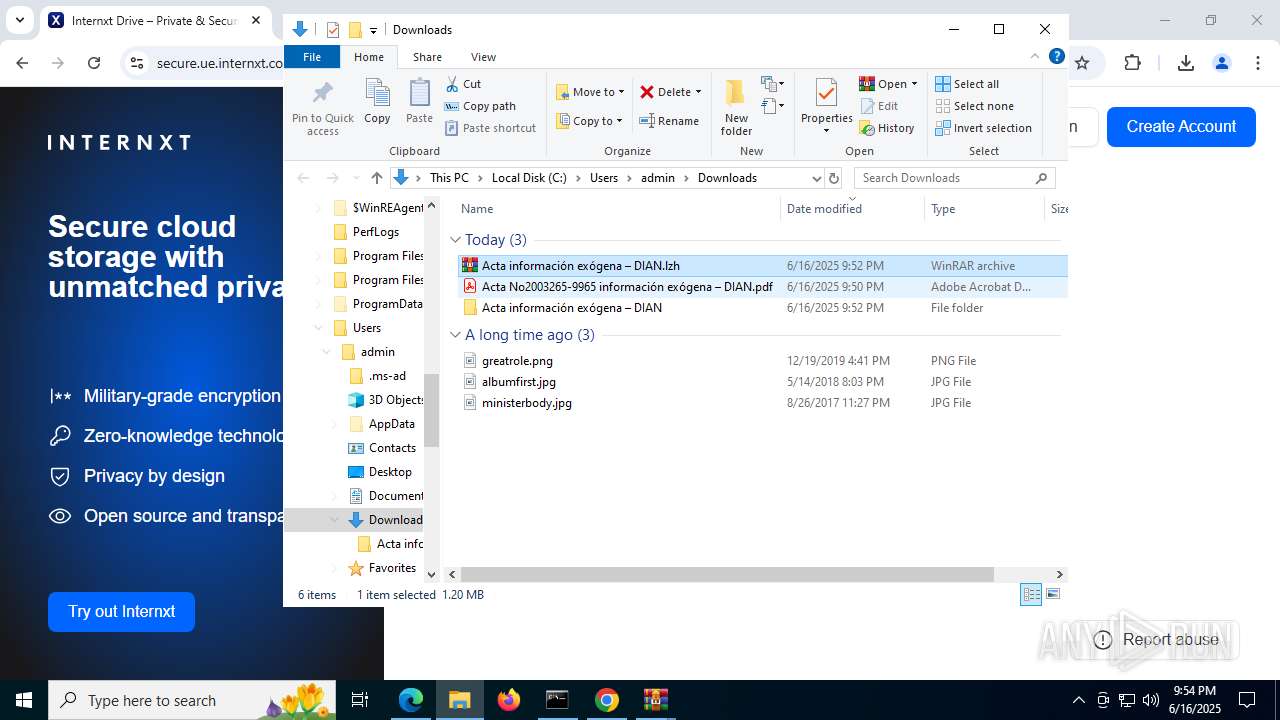
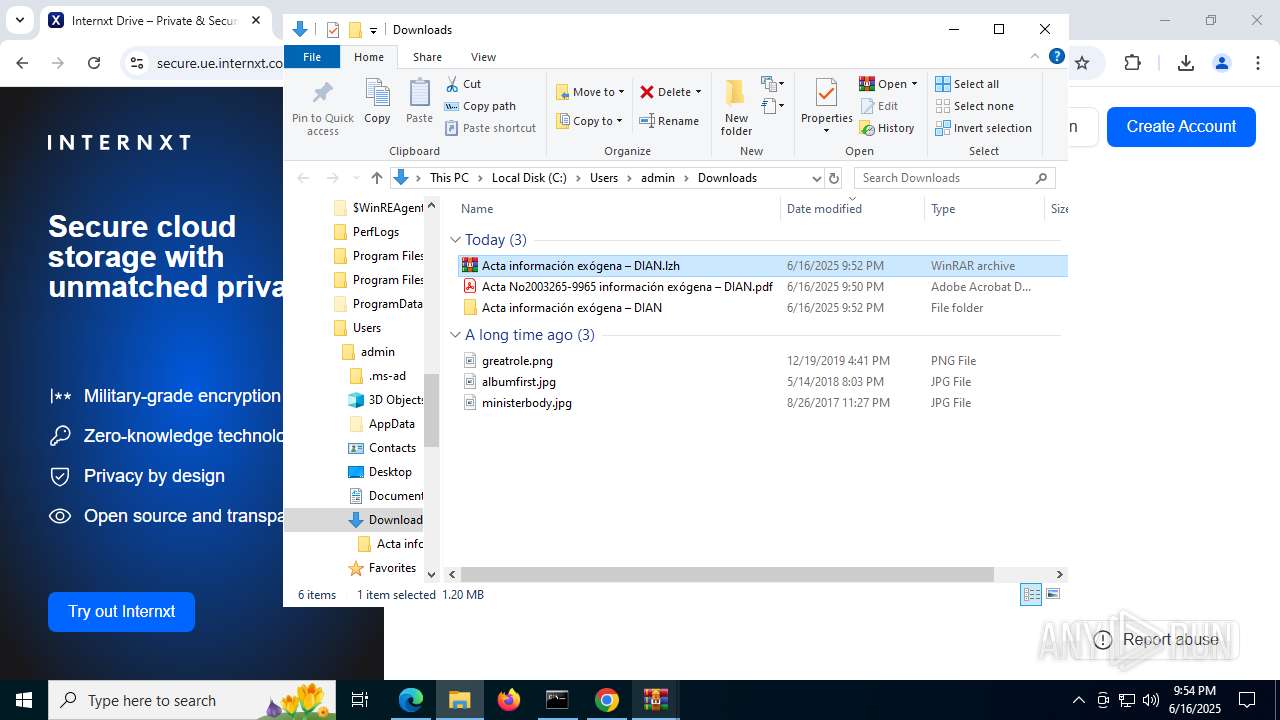
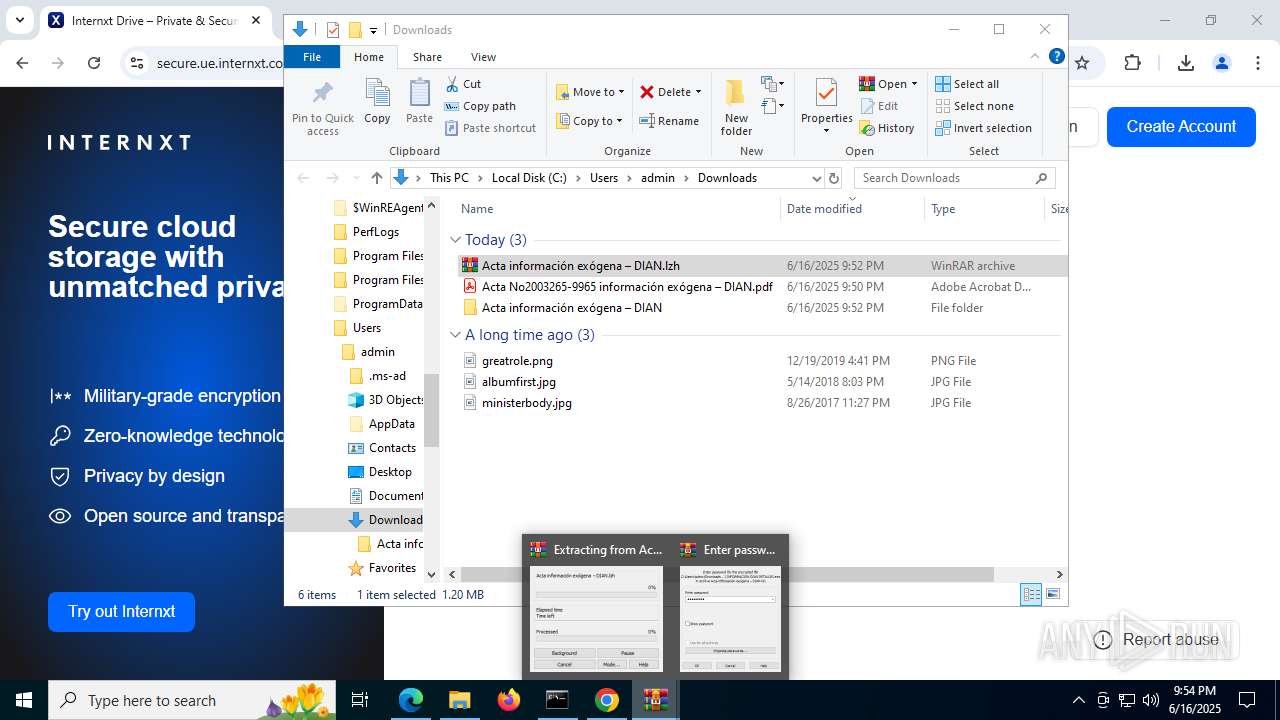
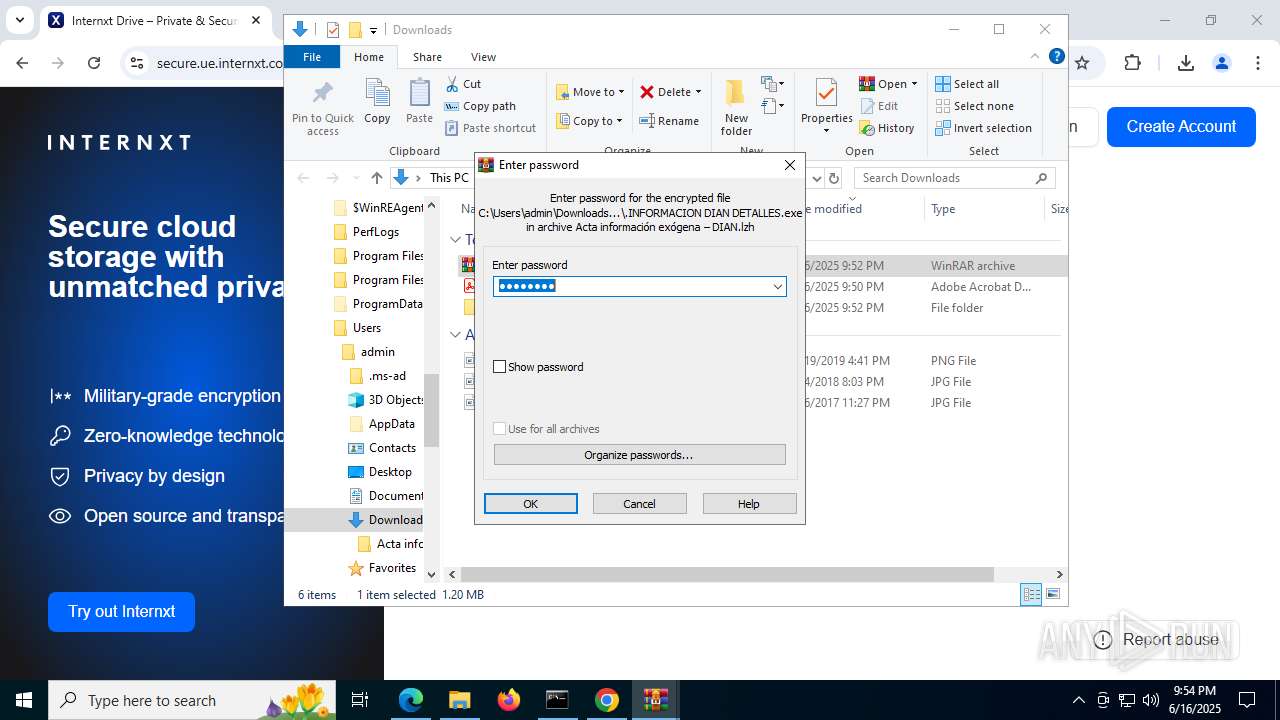
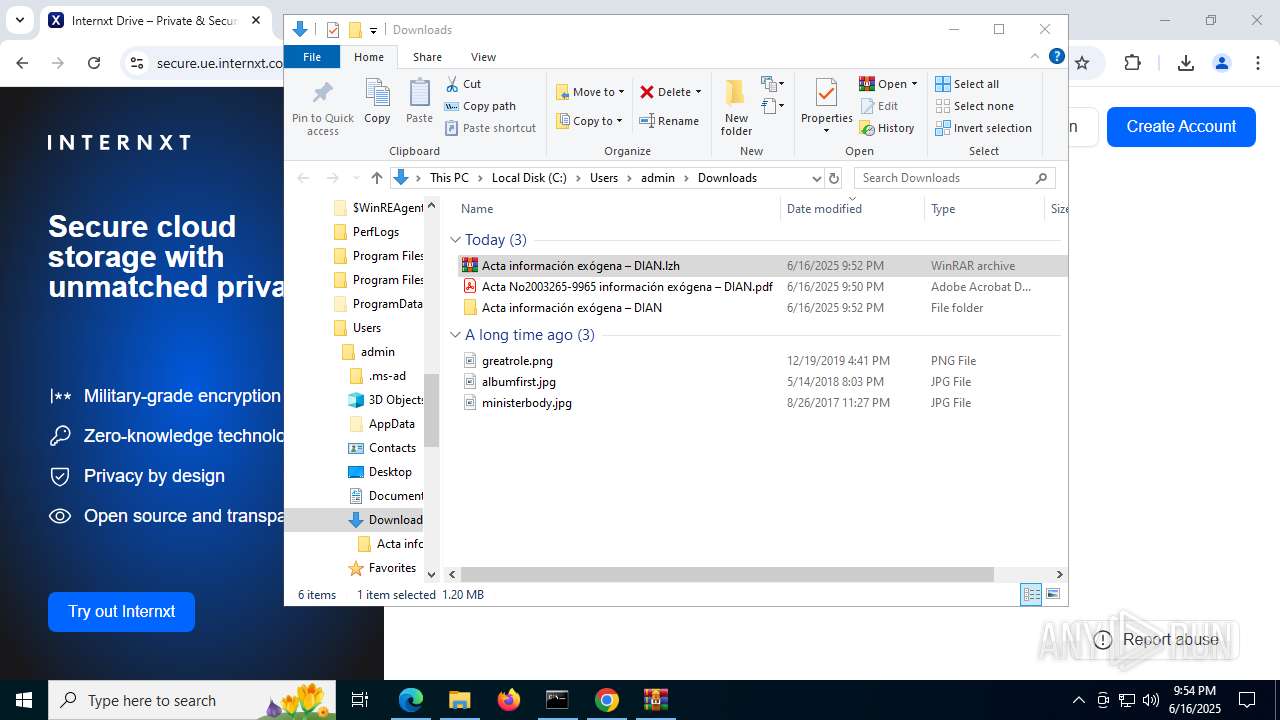
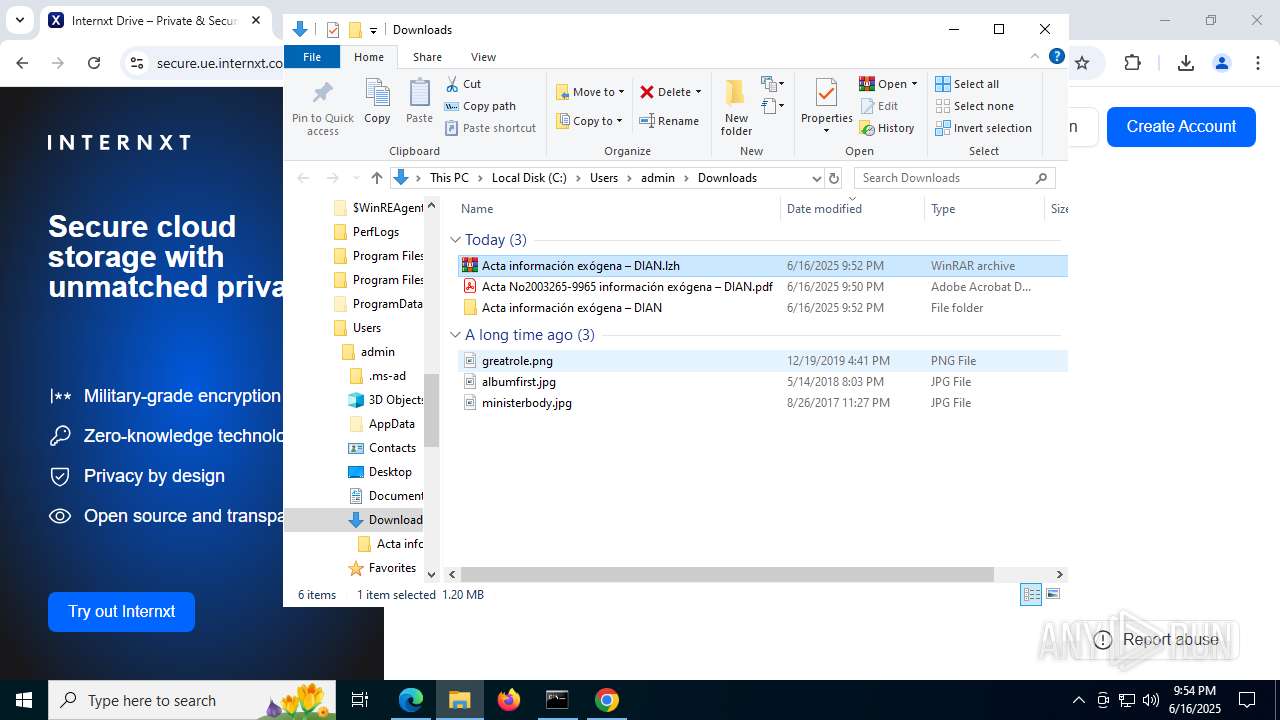
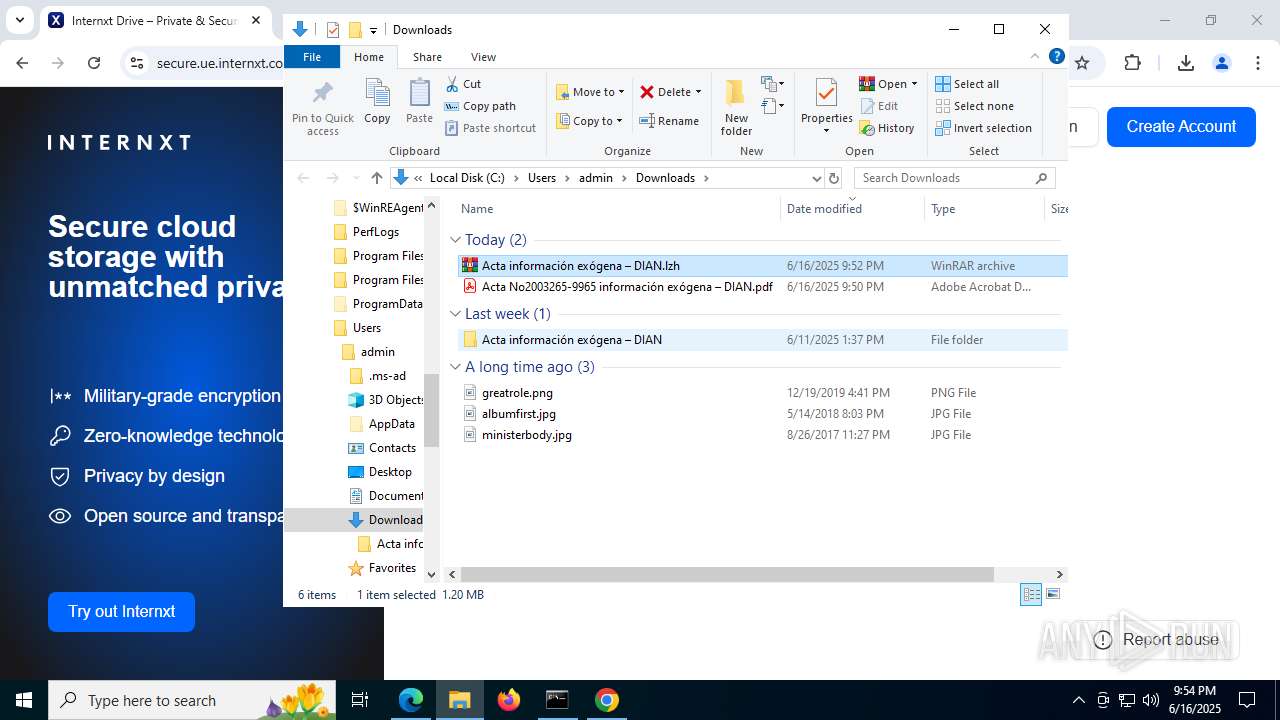
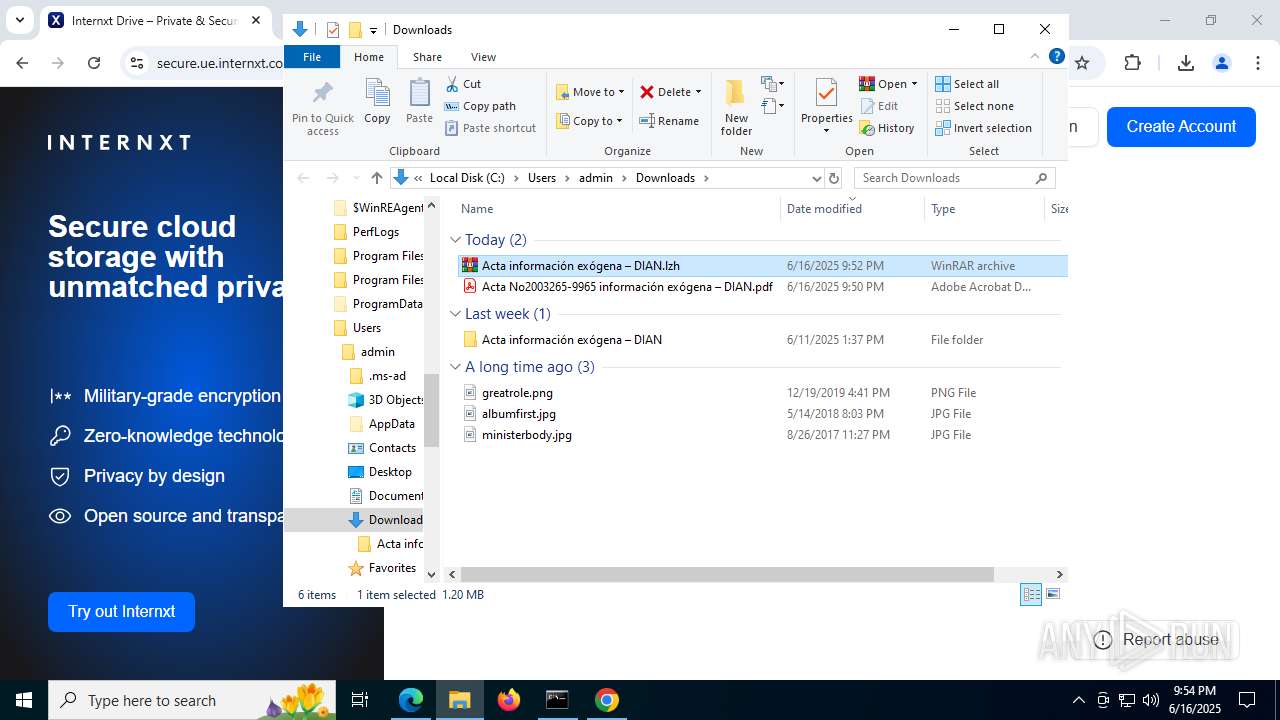
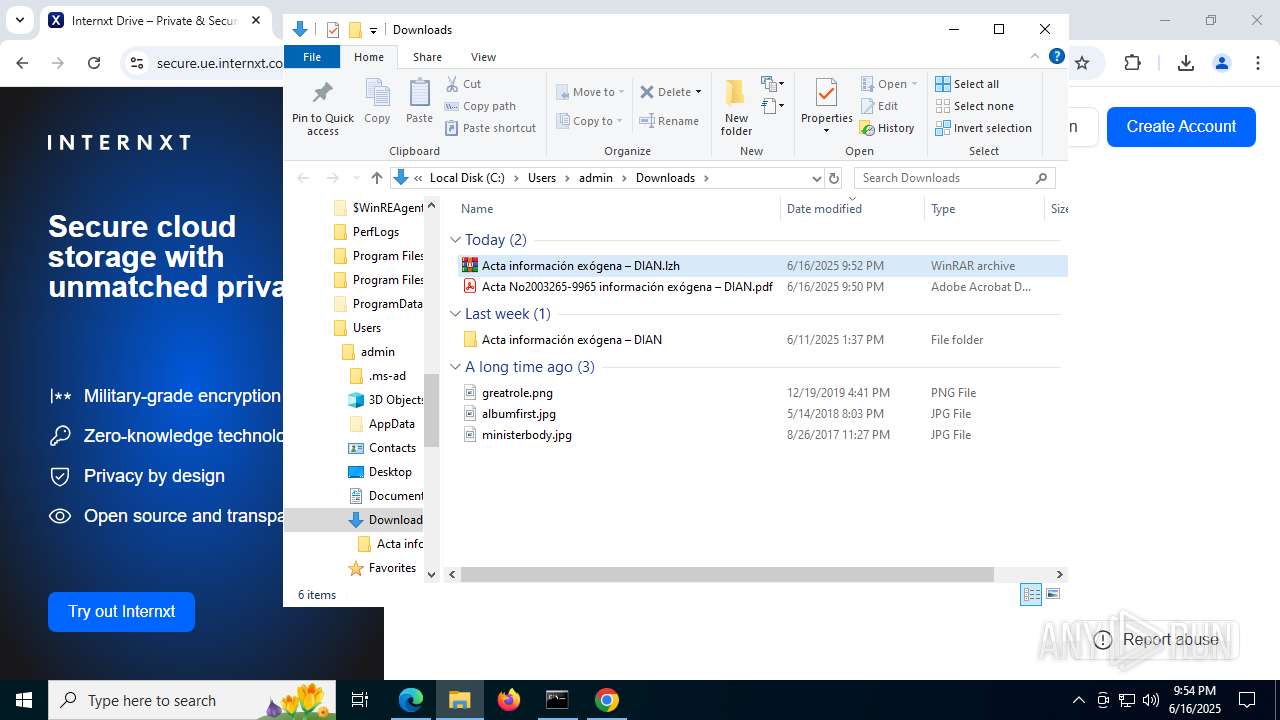
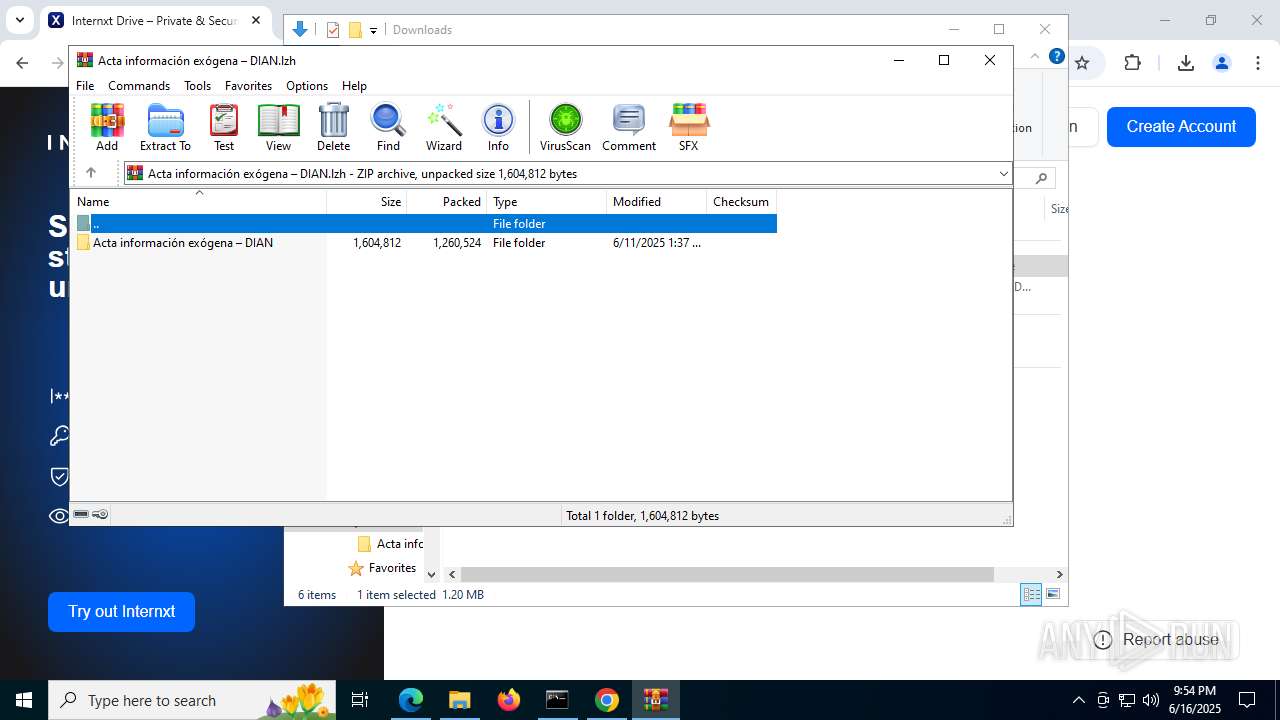
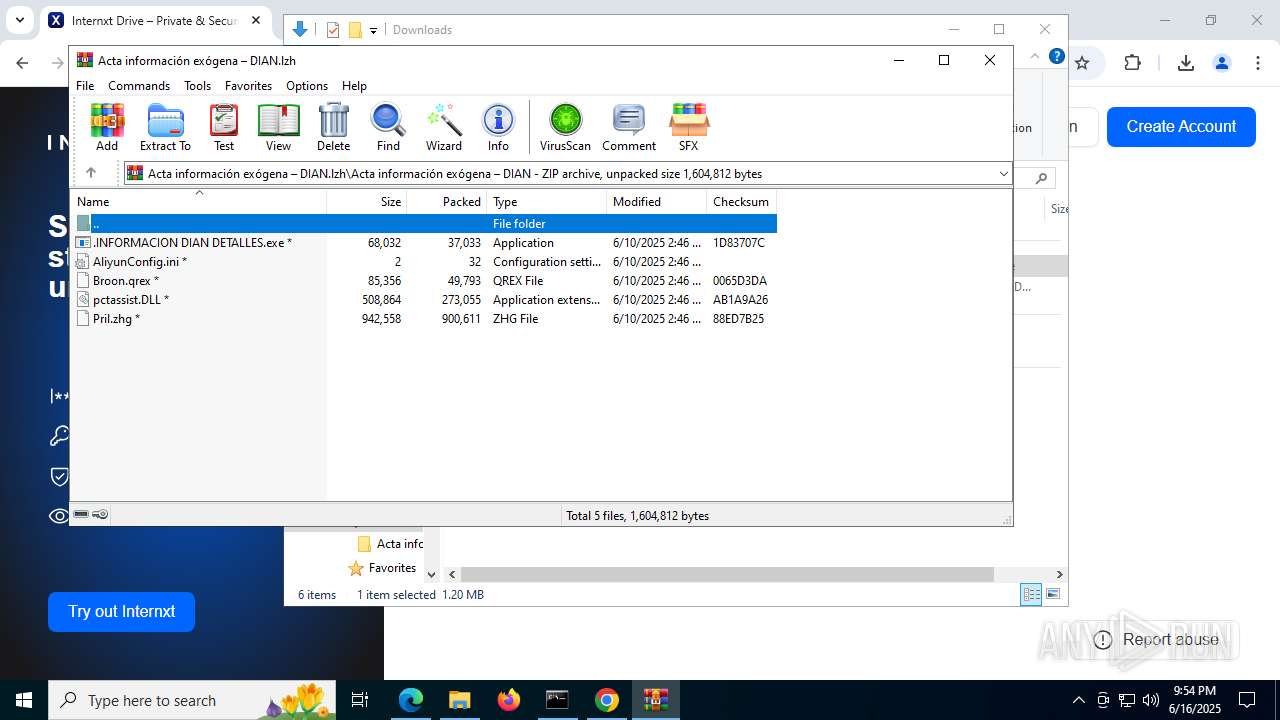
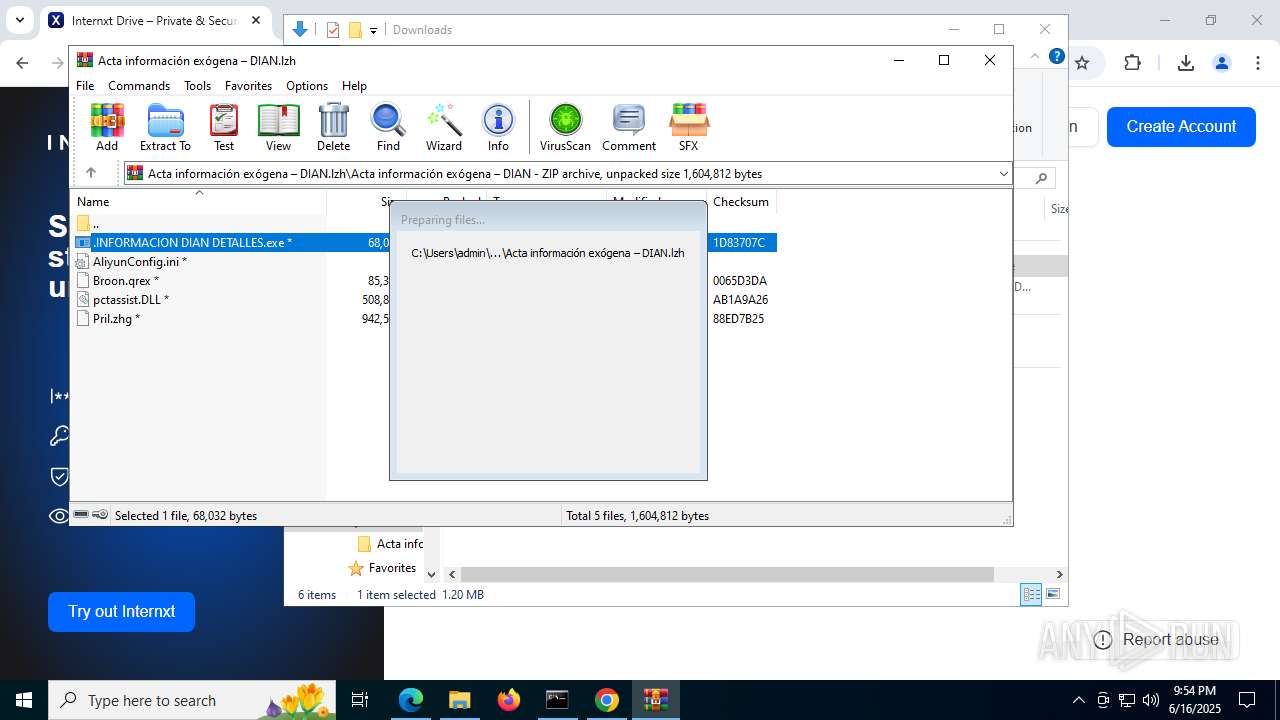
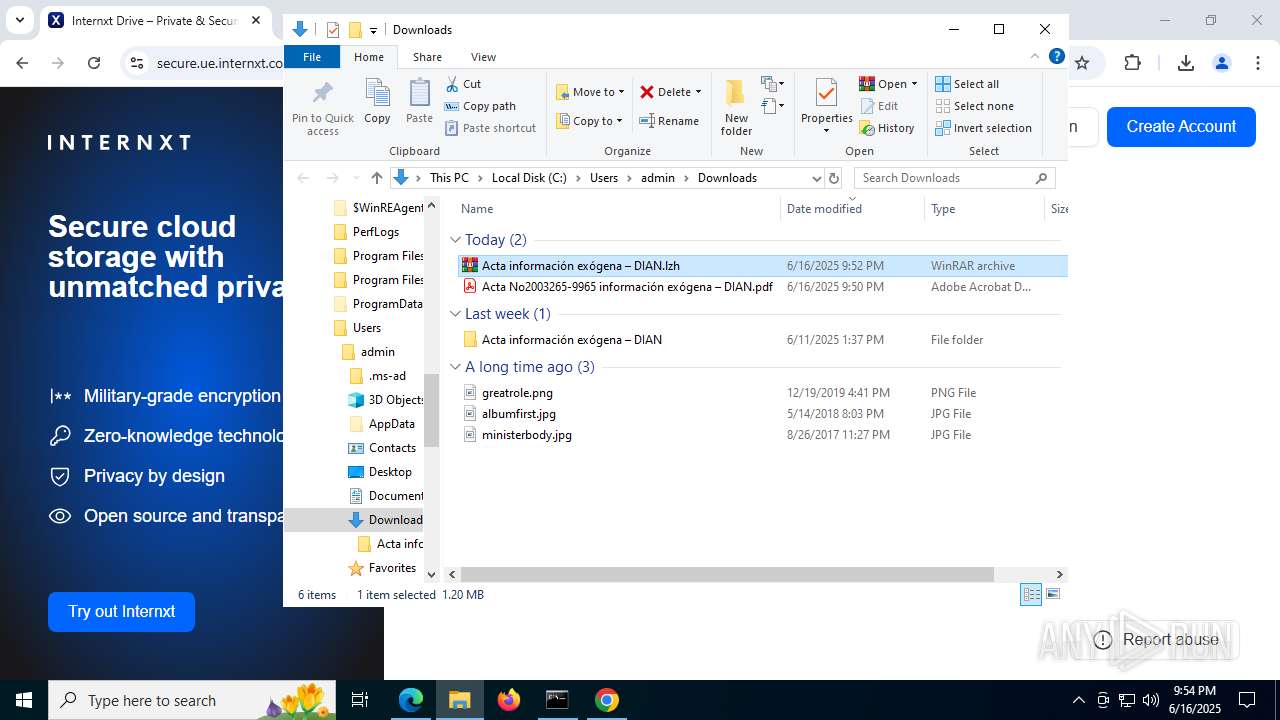
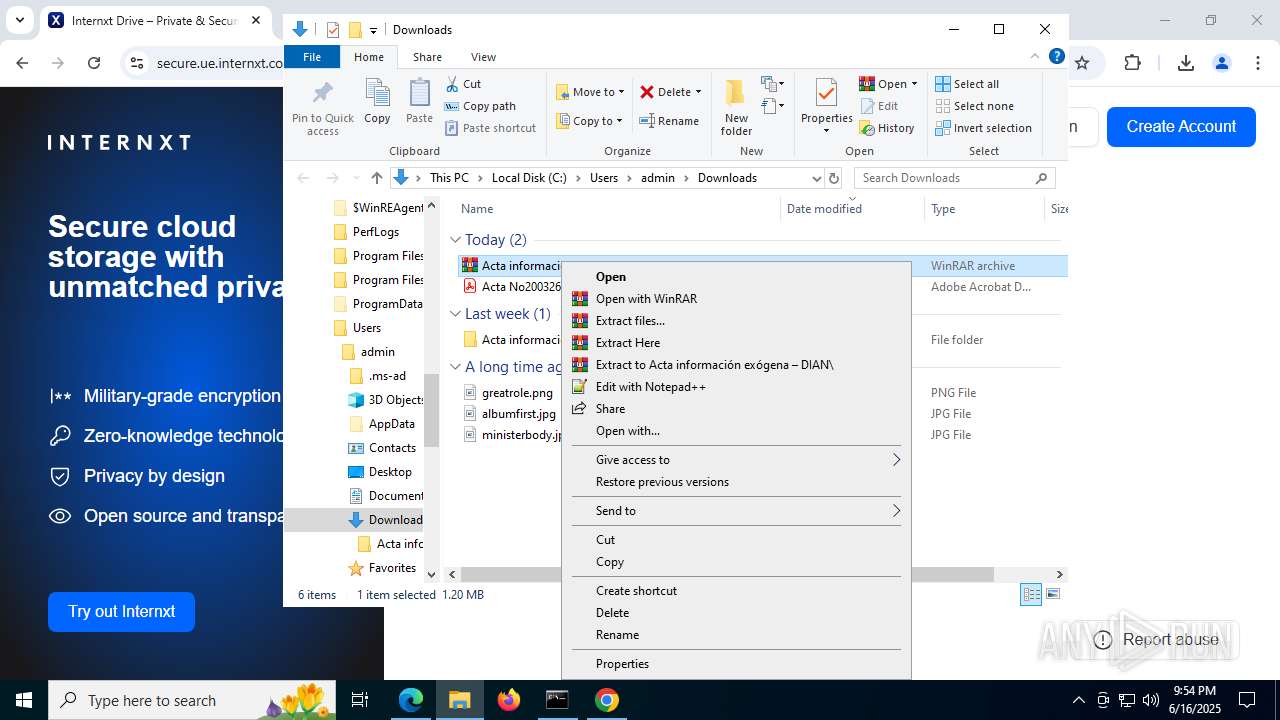
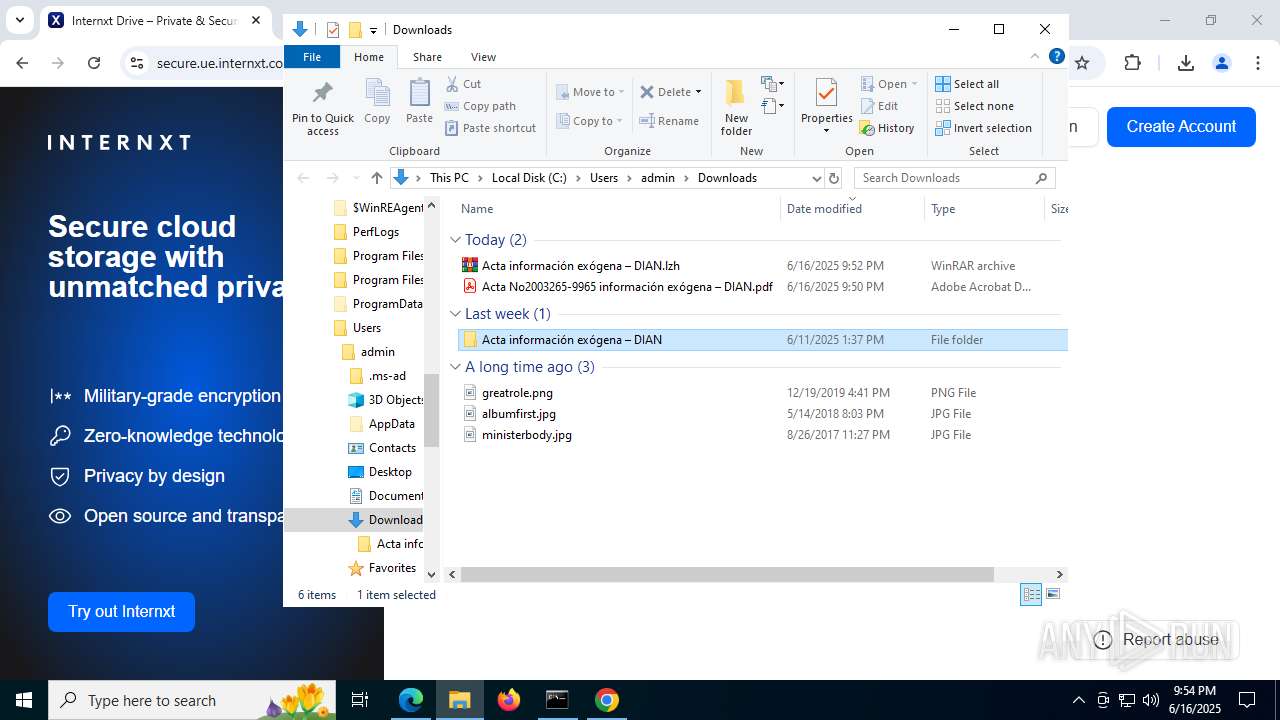
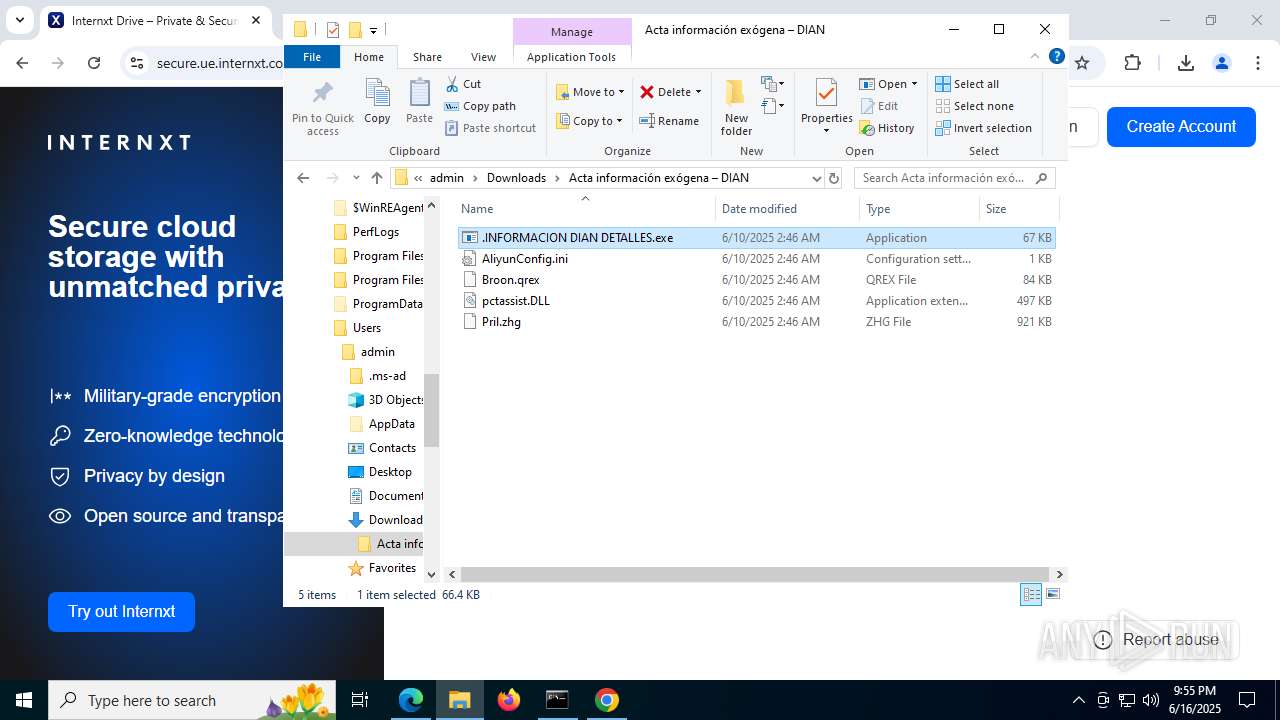
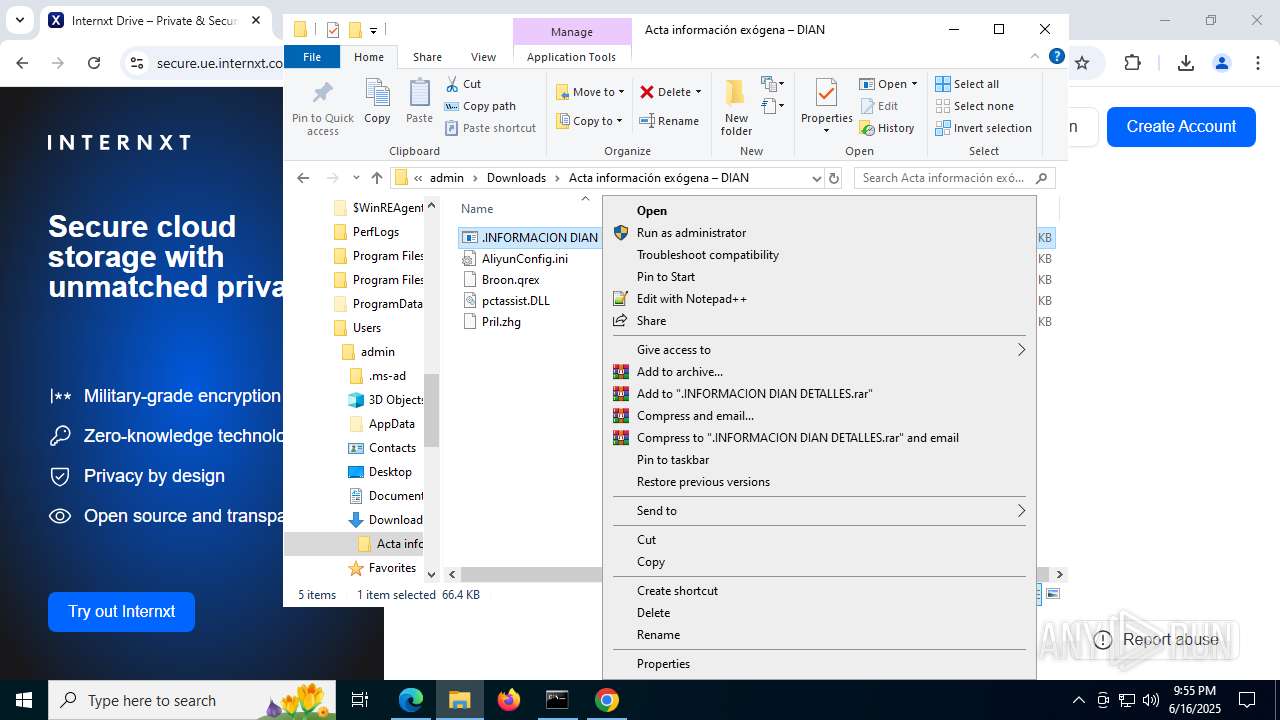
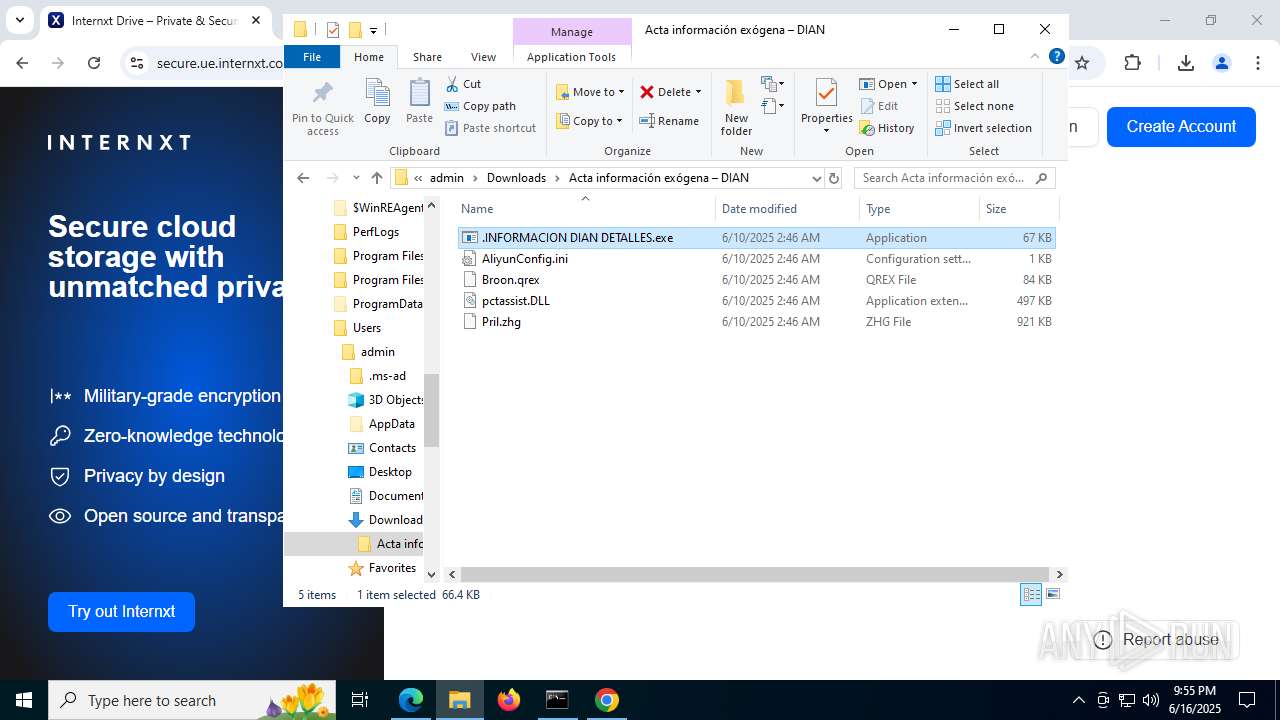
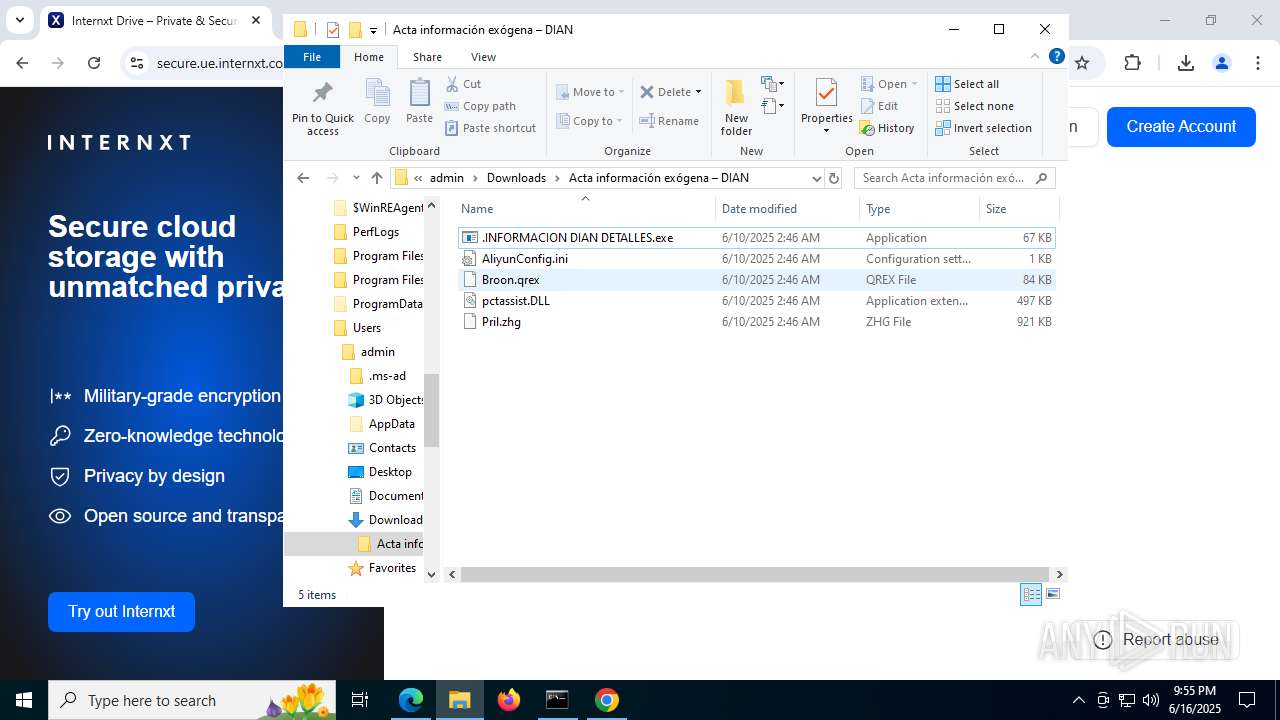
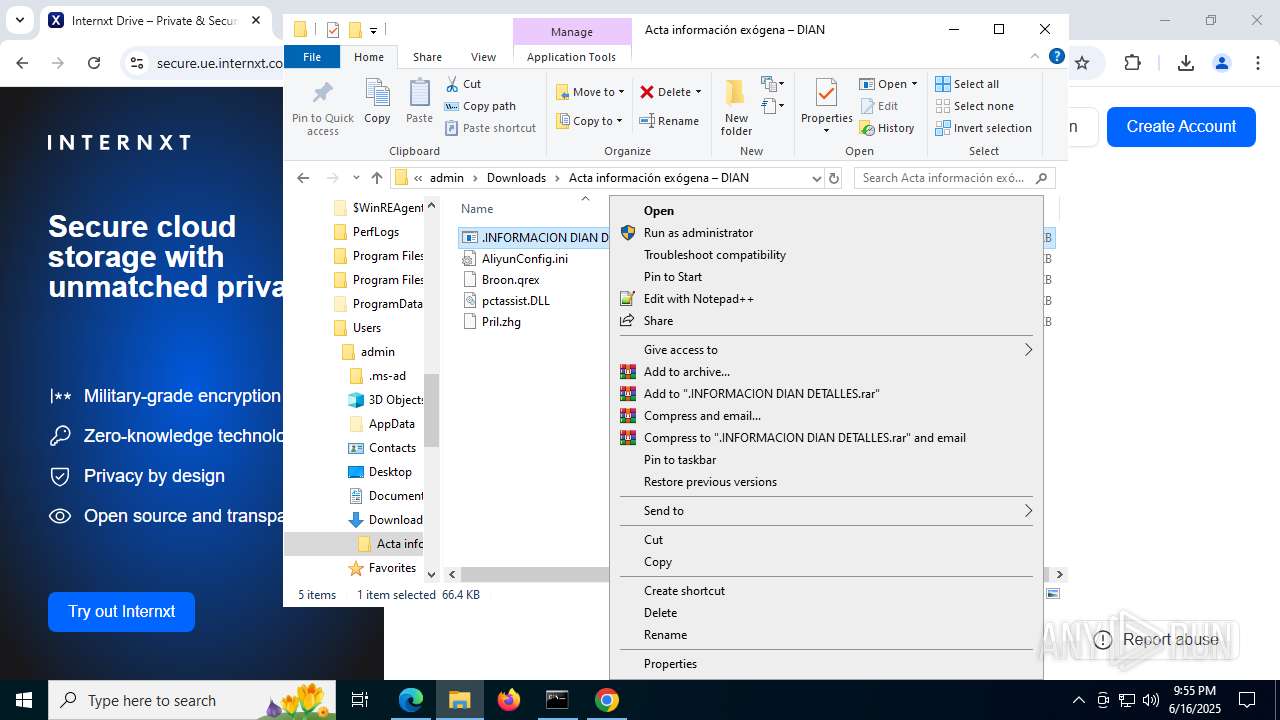
Manual execution by a user
- WinRAR.exe (PID: 6428)
- cmd.exe (PID: 316)
- .INFORMACION DIAN DETALLES.exe (PID: 8172)
- WinRAR.exe (PID: 5372)
- .INFORMACION DIAN DETALLES.exe (PID: 6308)
- .INFORMACION DIAN DETALLES.exe (PID: 2064)
- .INFORMACION DIAN DETALLES.exe (PID: 8104)
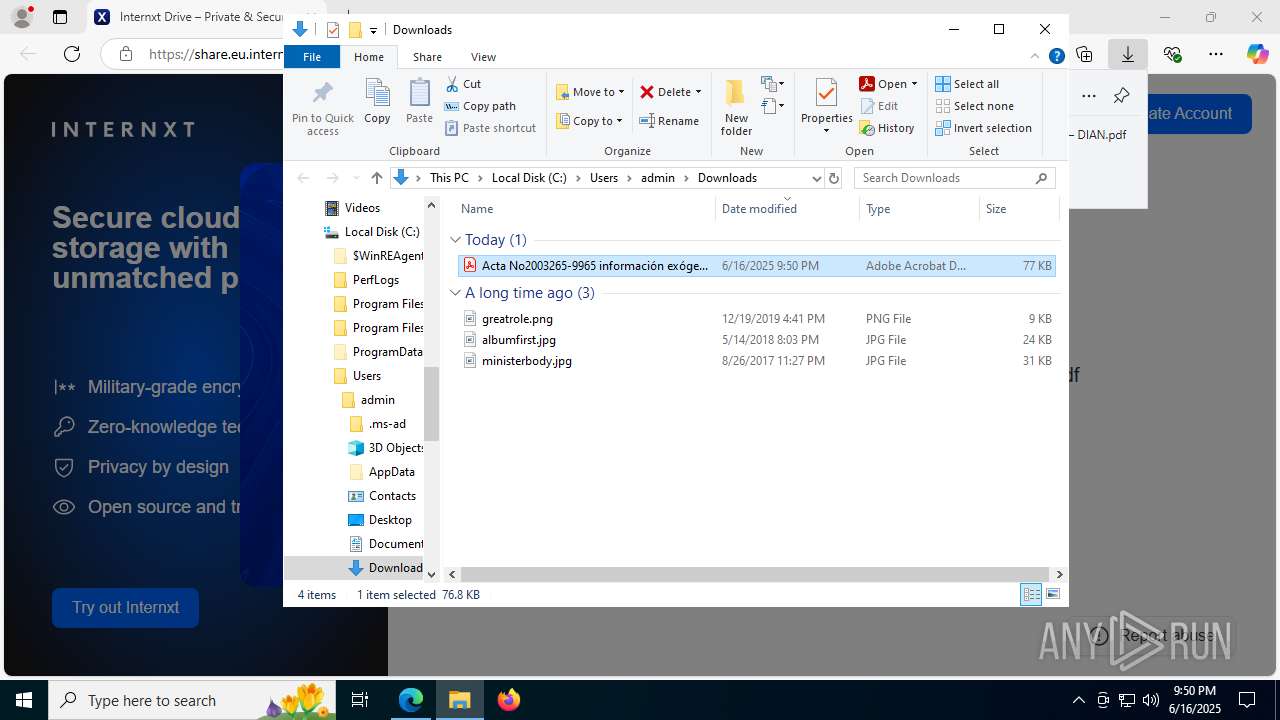
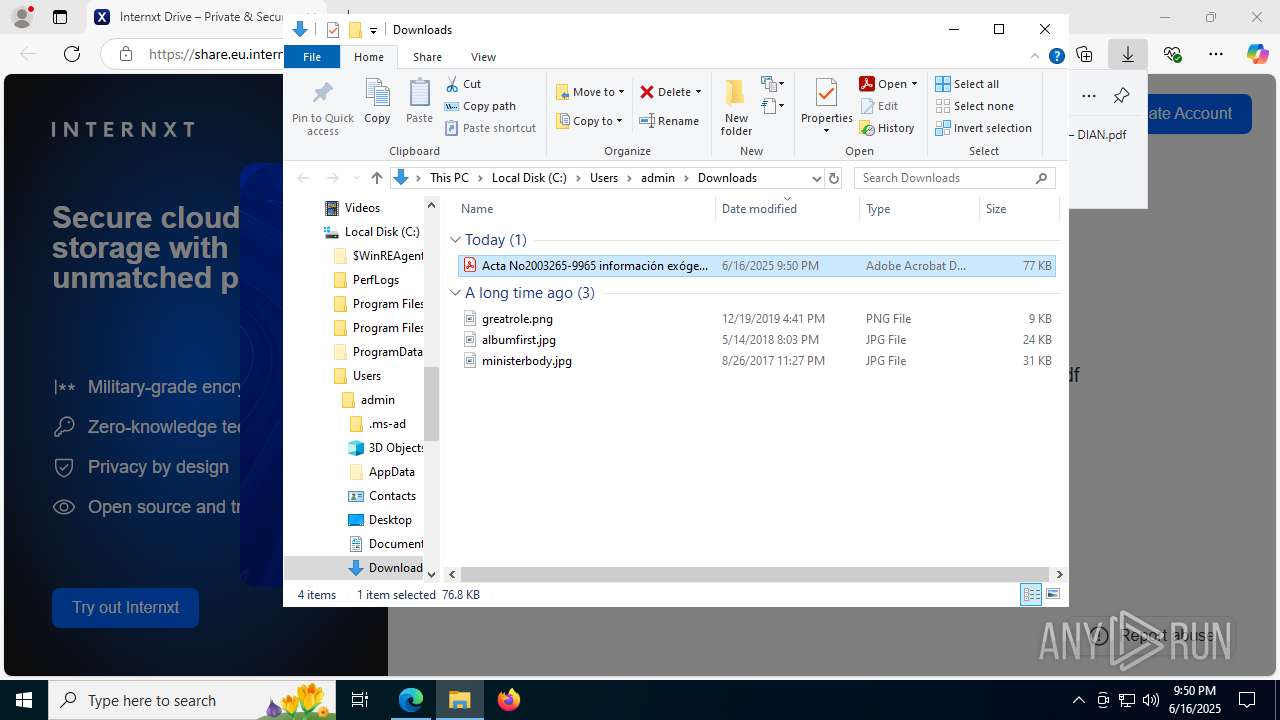
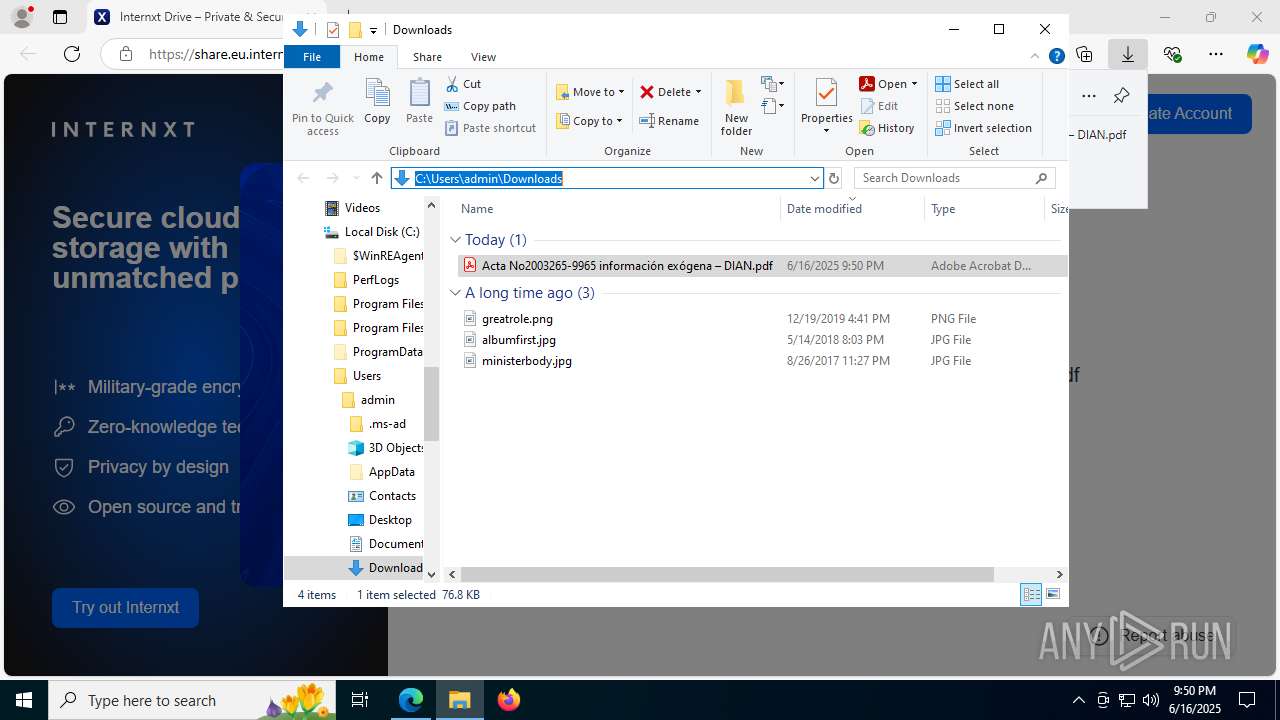
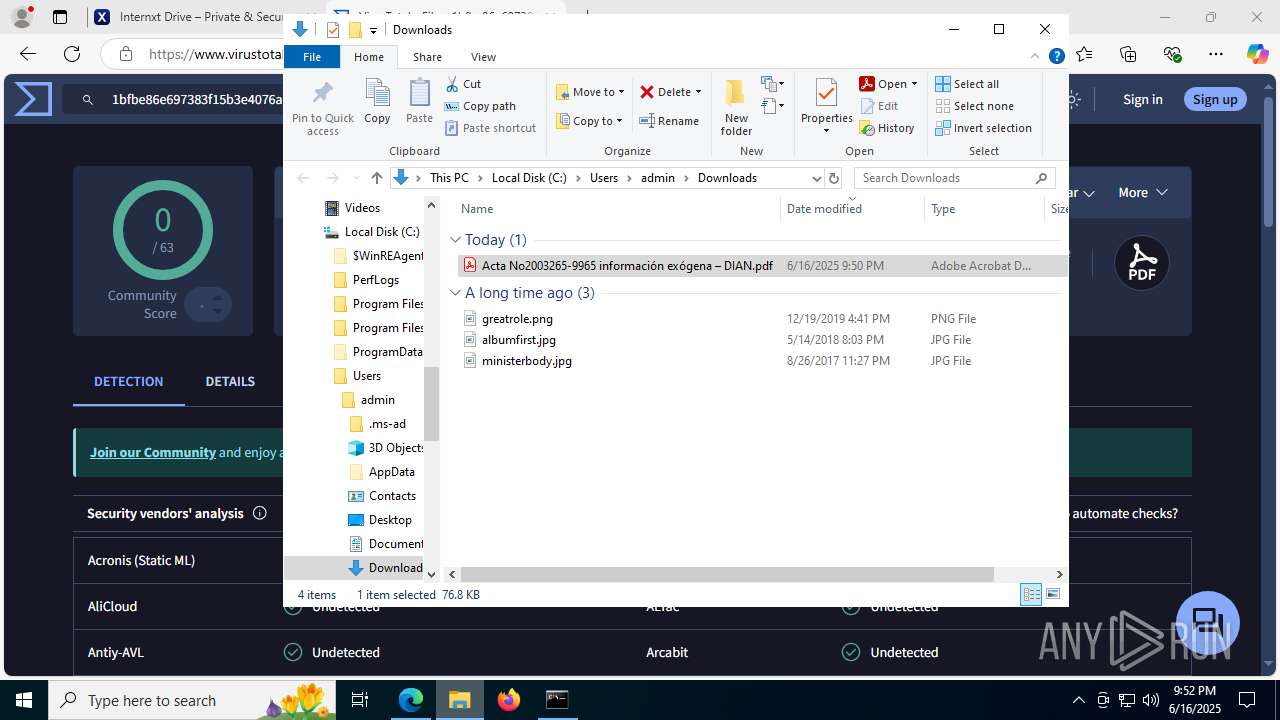
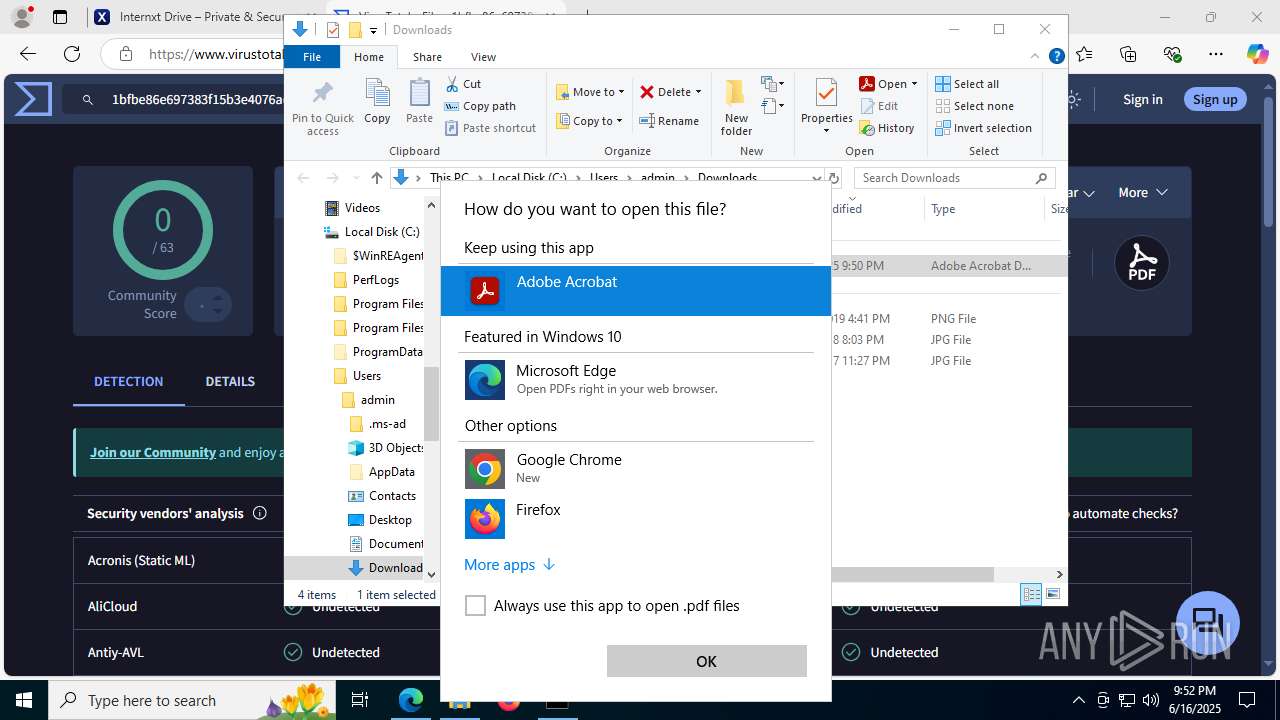
Launching a file from the Downloads directory
- chrome.exe (PID: 2996)
- msedge.exe (PID: 6620)
Application launched itself
- msedge.exe (PID: 6620)
- chrome.exe (PID: 2996)
The sample compiled with chinese language support
- .INFORMACION DIAN DETALLES.exe (PID: 6308)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6428)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
262
Monitored processes
109
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --field-trial-handle=4332,i,16373762917532570622,1280324196988062472,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3480 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | C:\Users\admin\UltraInterfac32.exe | C:\Users\admin\UltraInterfac32.exe | — | .INFORMACION DIAN DETALLES.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=3544,i,16373762917532570622,1280324196988062472,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6432 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --pdf-renderer --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--jitless --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=3972,i,16373762917532570622,1280324196988062472,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1816 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7548,i,14249855224226518847,18184649687807924591,262144 --variations-seed-version --mojo-platform-channel-handle=7736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5908,i,16373762917532570622,1280324196988062472,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\Downloads\Acta información exógena – DIAN\.INFORMACION DIAN DETALLES.exe" | C:\Users\admin\Downloads\Acta información exógena – DIAN\.INFORMACION DIAN DETALLES.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 113
Read events
30 025
Write events
82
Delete events
6
Modification events
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8D248FAB4D962F00 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ECA7A828-BE49-4C58-A642-529A71486ADA} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CDA3BA6F-9662-42AD-9717-B819A29ED46A} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {13E09297-FFCC-4FB4-B942-E1F60324235D} | |||
Executable files
5
Suspicious files
805
Text files
166
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176496.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1764a5.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1764e4.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1764f3.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1764f3.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1764f3.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
310
DNS requests
253
Threats
124
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3980 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CK5L9058ih-zUN-5p12AyxOWT8Zrt5Z6FIinSOMLHNY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2764 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2876 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2876 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7856 | svchost.exe | HEAD | 200 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750171519&P2=404&P3=2&P4=COLLWYtqyl3xsfxd4pHnMaRB8o%2bPsl2ofZ9X%2foaQPXv2SRCzTyQP2yEBGz5YA1YXAlmg%2fLZsovbovKkdqR%2fxDA%3d%3d | unknown | — | — | whitelisted |
7856 | svchost.exe | HEAD | 200 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750175120&P2=404&P3=2&P4=Tu%2fGYa%2fpnimo4nIge%2b1LA1hu7YGO988UGqvY0tcqHmfHl%2bXxp7a6nHiBs8WKQOHqXjQ1d7YO1FLatVYZLtYk2w%3d%3d | unknown | — | — | whitelisted |
7856 | svchost.exe | HEAD | 200 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1750171520&P2=404&P3=2&P4=IQqT%2fDeELXuGdsivLJSNEWse%2bPR3wyQ2wUEYe3ETwQHXAm1drALTjmko1pp6teKrhLLMa9Mt%2fLsG3ed%2fDFQfLw%3d%3d | unknown | — | — | whitelisted |
7856 | svchost.exe | GET | 206 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750171519&P2=404&P3=2&P4=COLLWYtqyl3xsfxd4pHnMaRB8o%2bPsl2ofZ9X%2foaQPXv2SRCzTyQP2yEBGz5YA1YXAlmg%2fLZsovbovKkdqR%2fxDA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6404 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3980 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3980 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3980 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3980 | msedge.exe | 162.19.108.149:443 | share.eu.internxt.com | OVH SAS | FR | suspicious |
3980 | msedge.exe | 2.19.195.43:443 | copilot.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
share.eu.internxt.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
share.internxt.com |
| unknown |
s3.us-east-1.wasabisys.com |
| whitelisted |
assets.mailerlite.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3980 | msedge.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
3980 | msedge.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
3980 | msedge.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in TLS SNI |
3980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3980 | msedge.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
3980 | msedge.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
3980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |