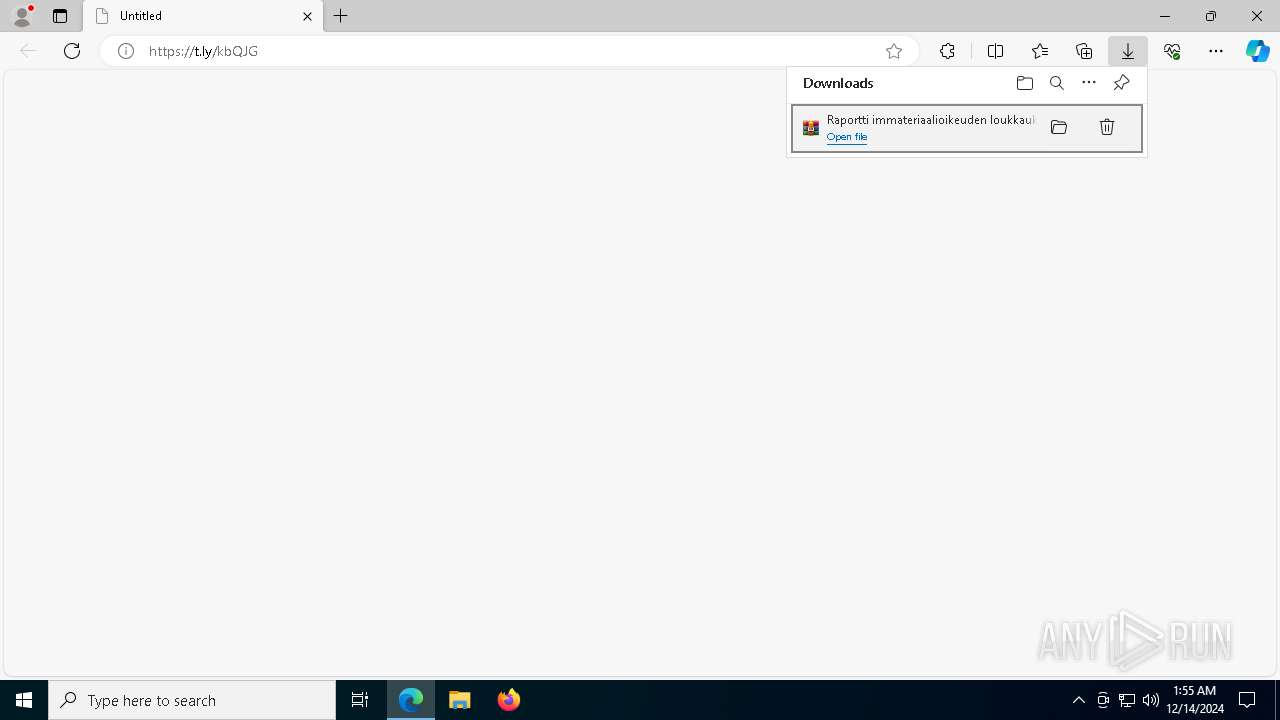
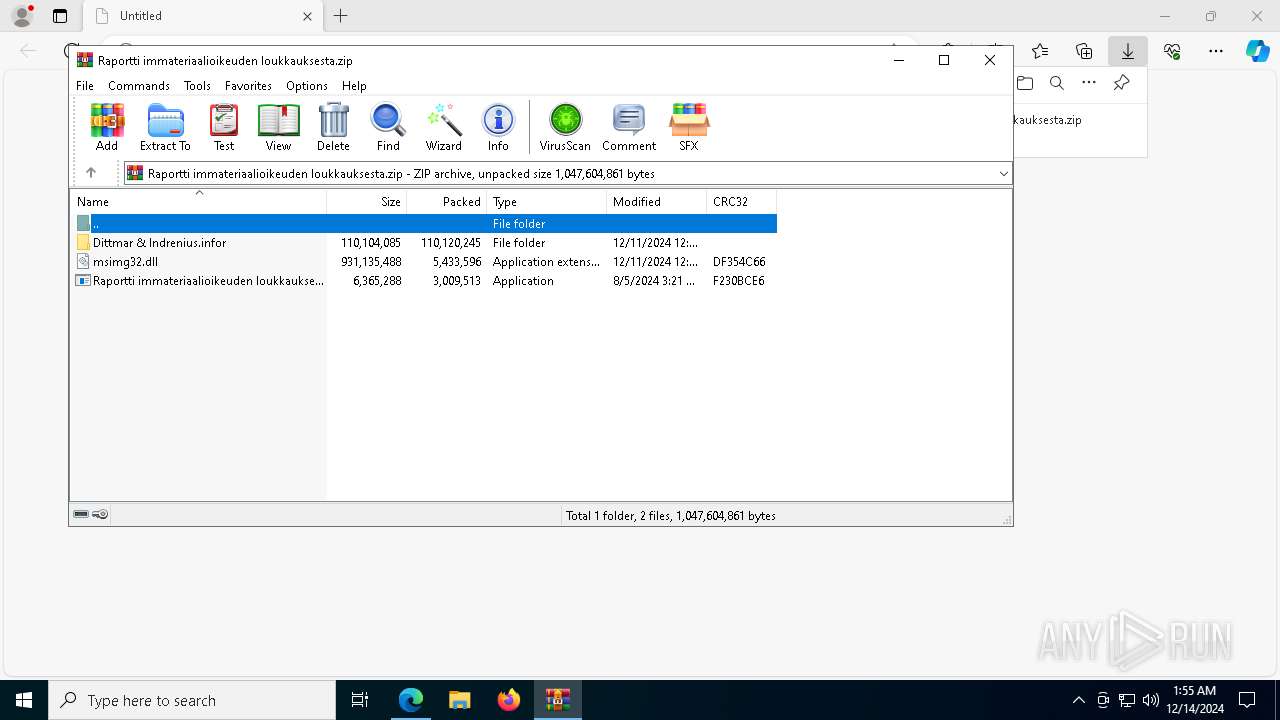
| URL: | https://t.ly/kbQJG |
| Full analysis: | https://app.any.run/tasks/df725700-3108-4c36-8f41-48b0cac820c1 |
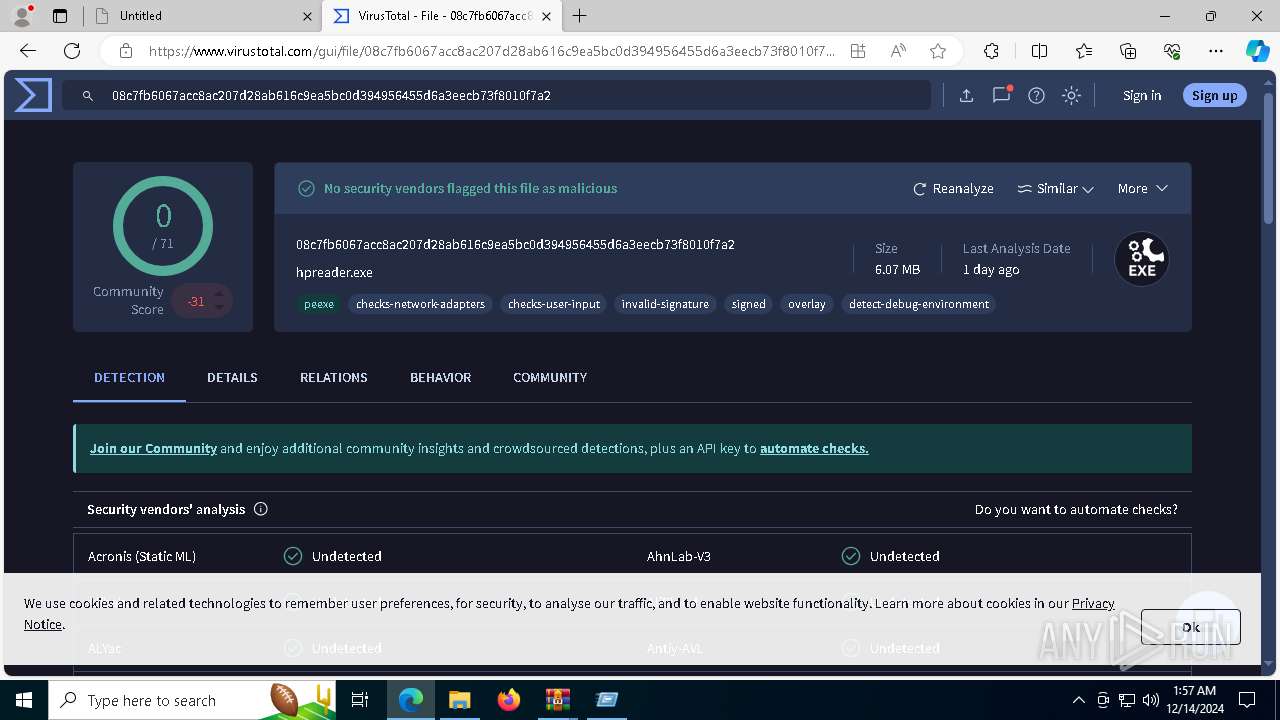
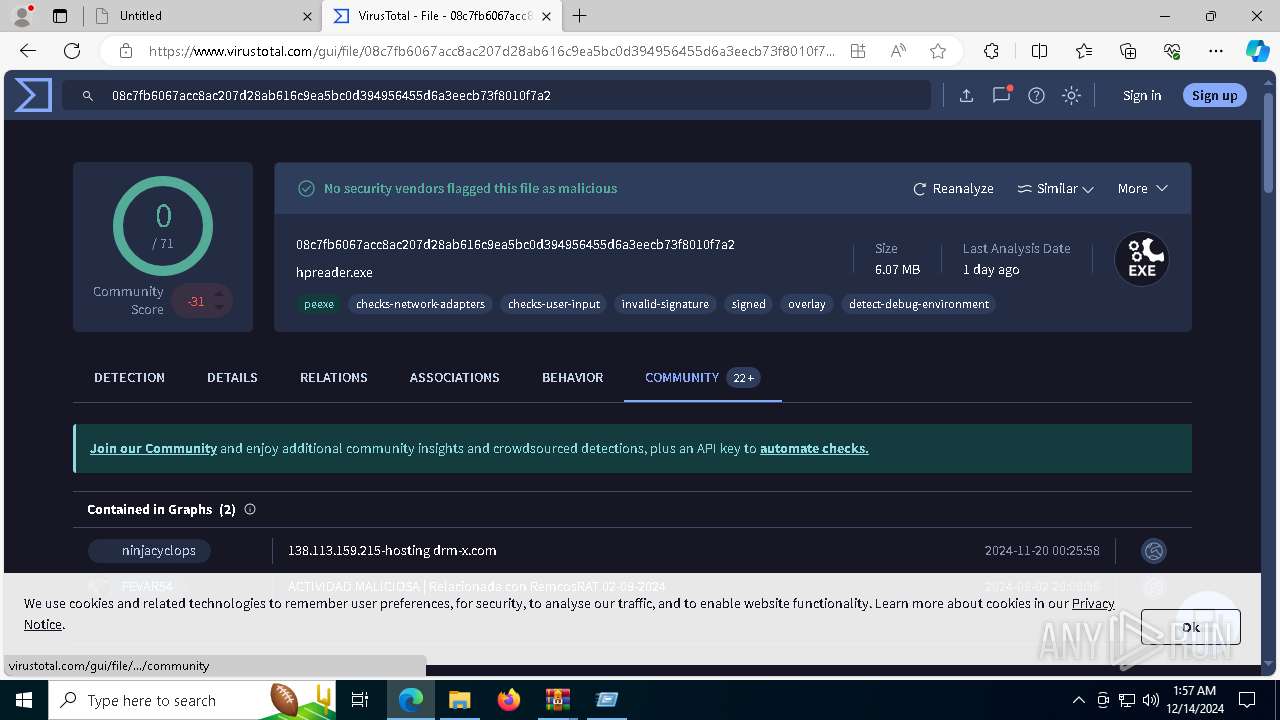
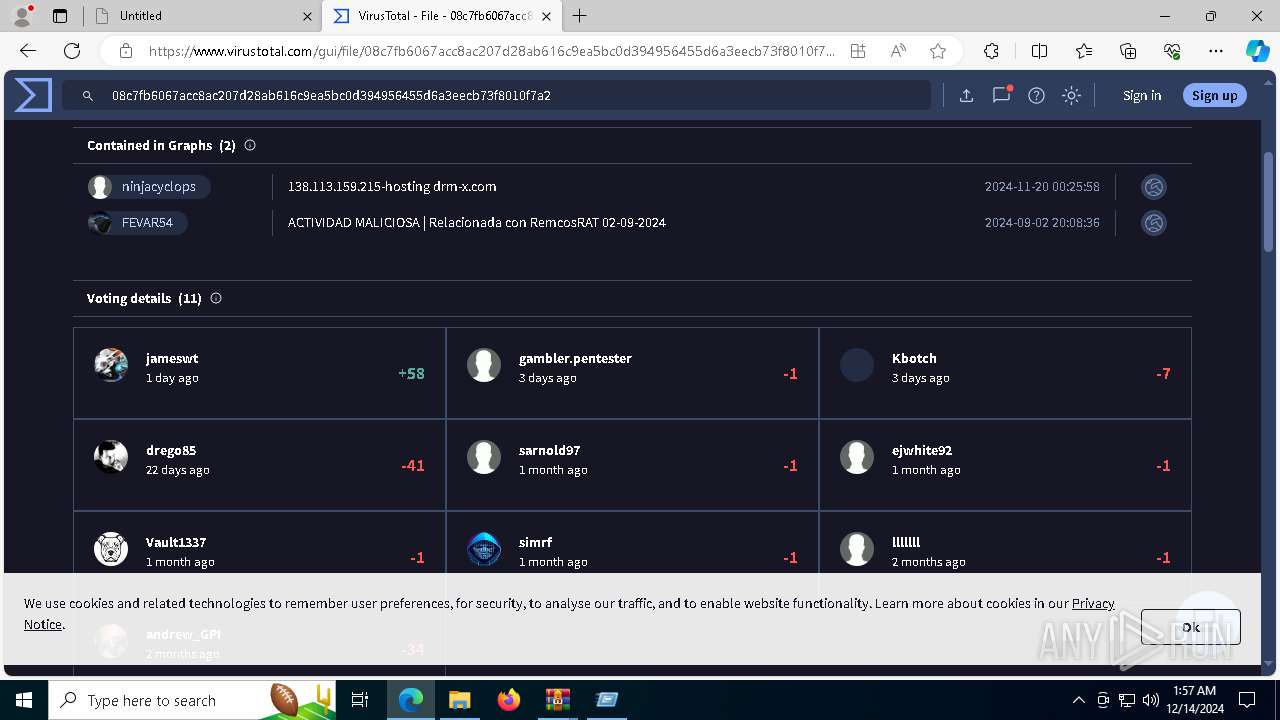
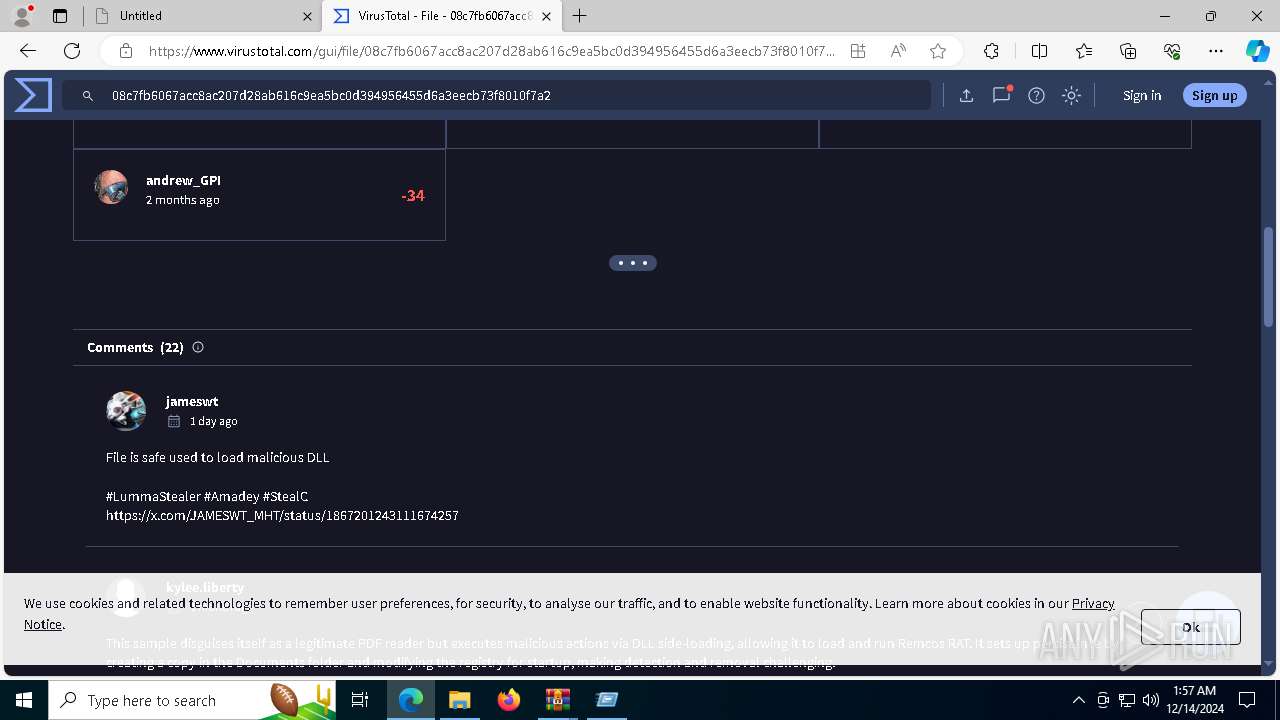
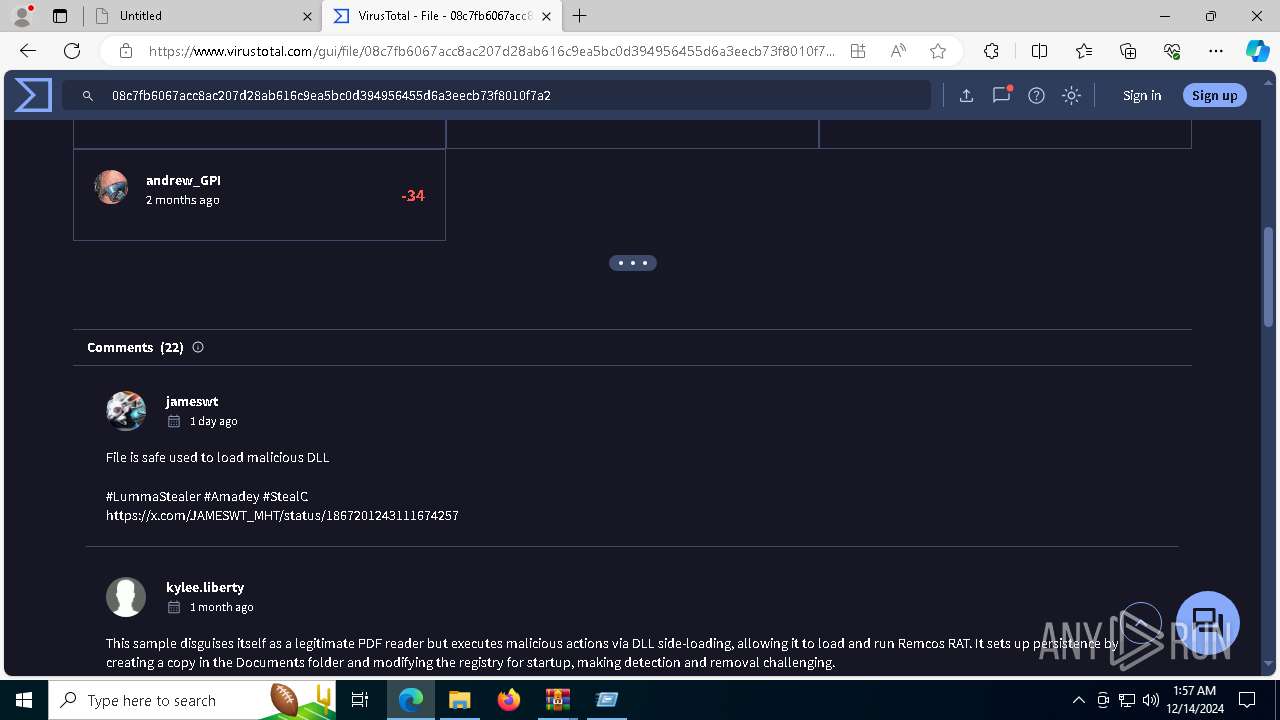
| Verdict: | Malicious activity |
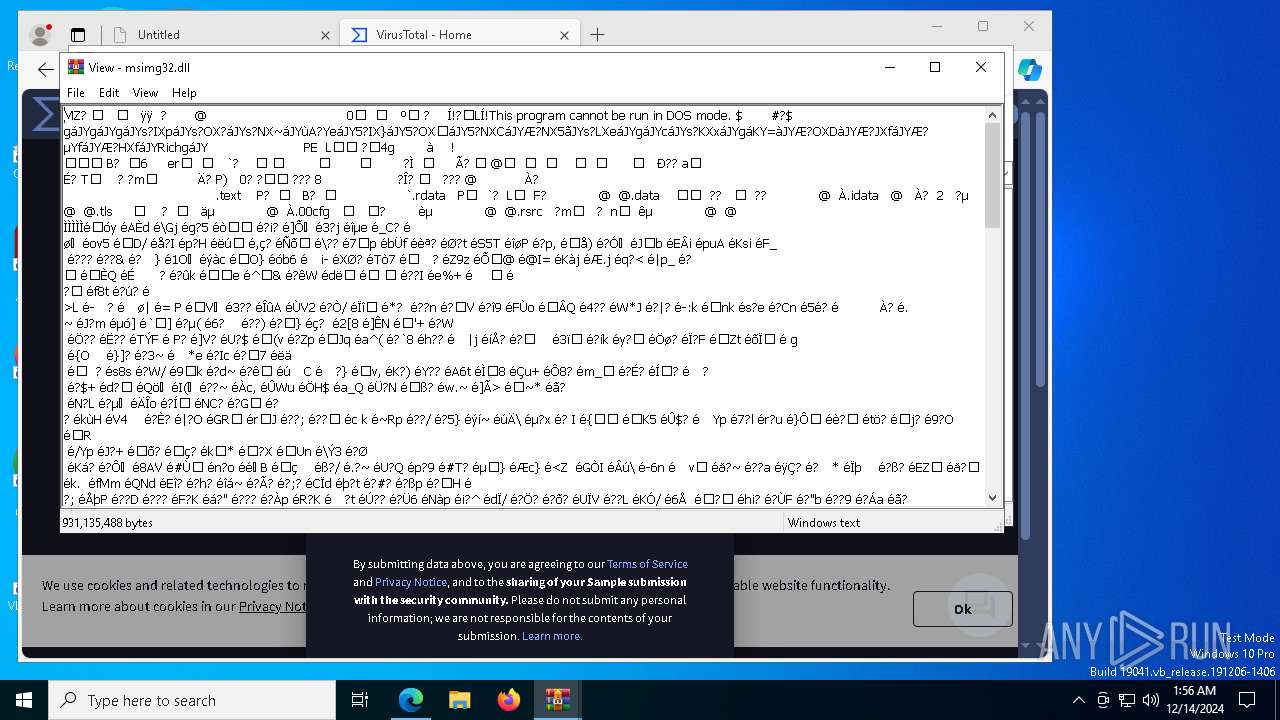
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | December 14, 2024, 01:54:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9419827E6C90933ABFB5F3F09624B9B2 |
| SHA1: | F486406E24C59463DDEC7C91B3AEFF112ED3D85A |
| SHA256: | 62537949D693981CE9377A87A40717727F648E0EC0EEB9A4456513037BF2F5B9 |
| SSDEEP: | 3:N8D5OUvi:2tBi |
MALICIOUS
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 3848)
- svchost.exe (PID: 5496)
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
- dllhost.exe (PID: 8096)
- dllhost.exe (PID: 2956)
Actions looks like stealing of personal data
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
Steals credentials from Web Browsers
- msedge.exe (PID: 7332)
- msedge.exe (PID: 8088)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3144)
- msedge.exe (PID: 7332)
- msedge.exe (PID: 8088)
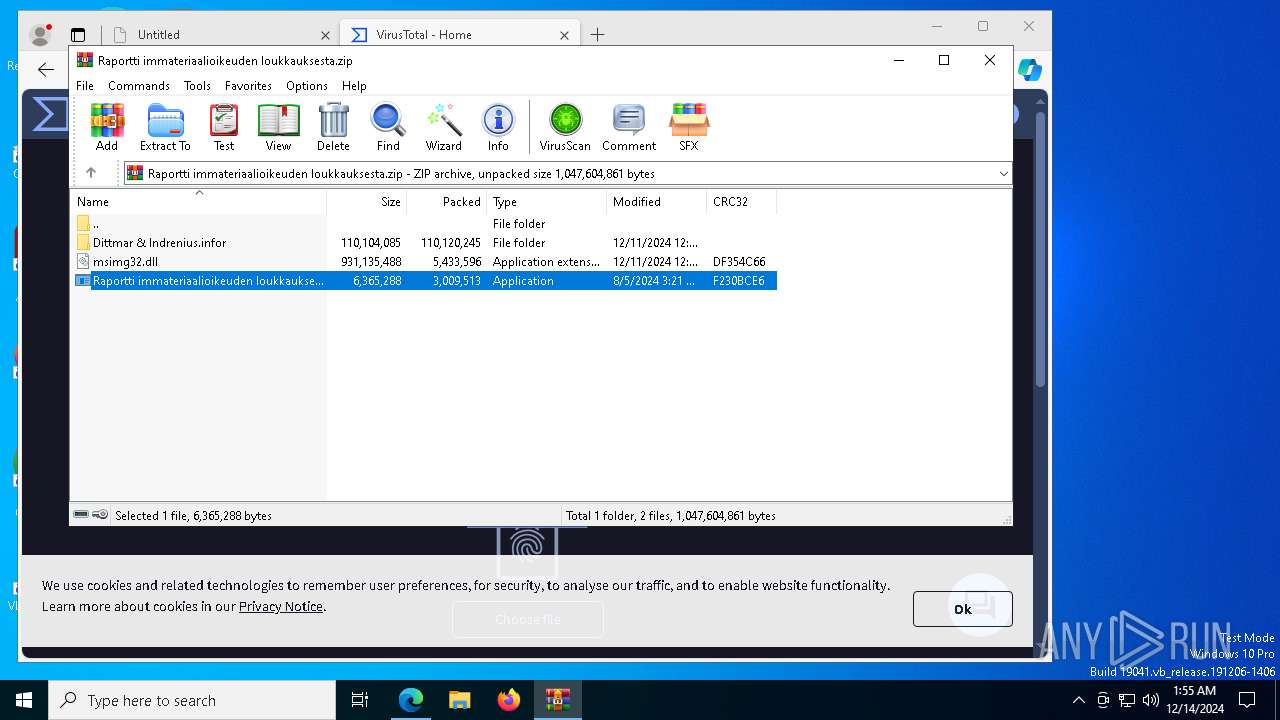
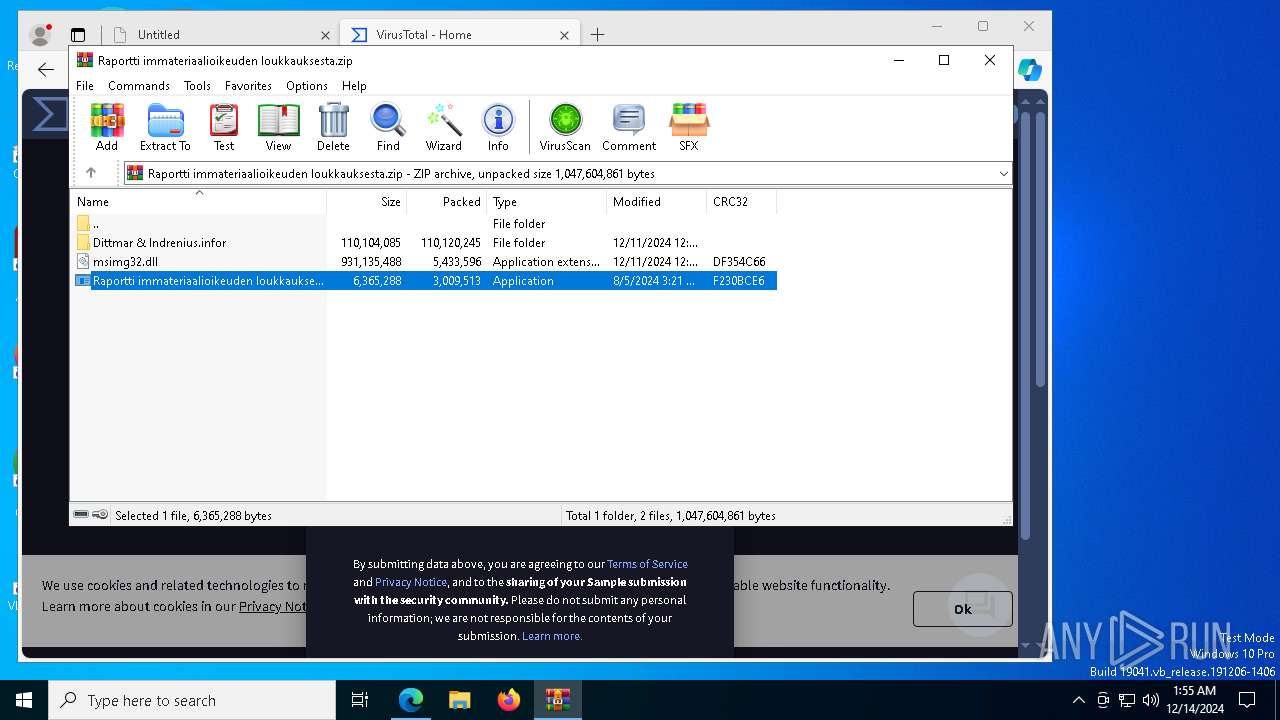
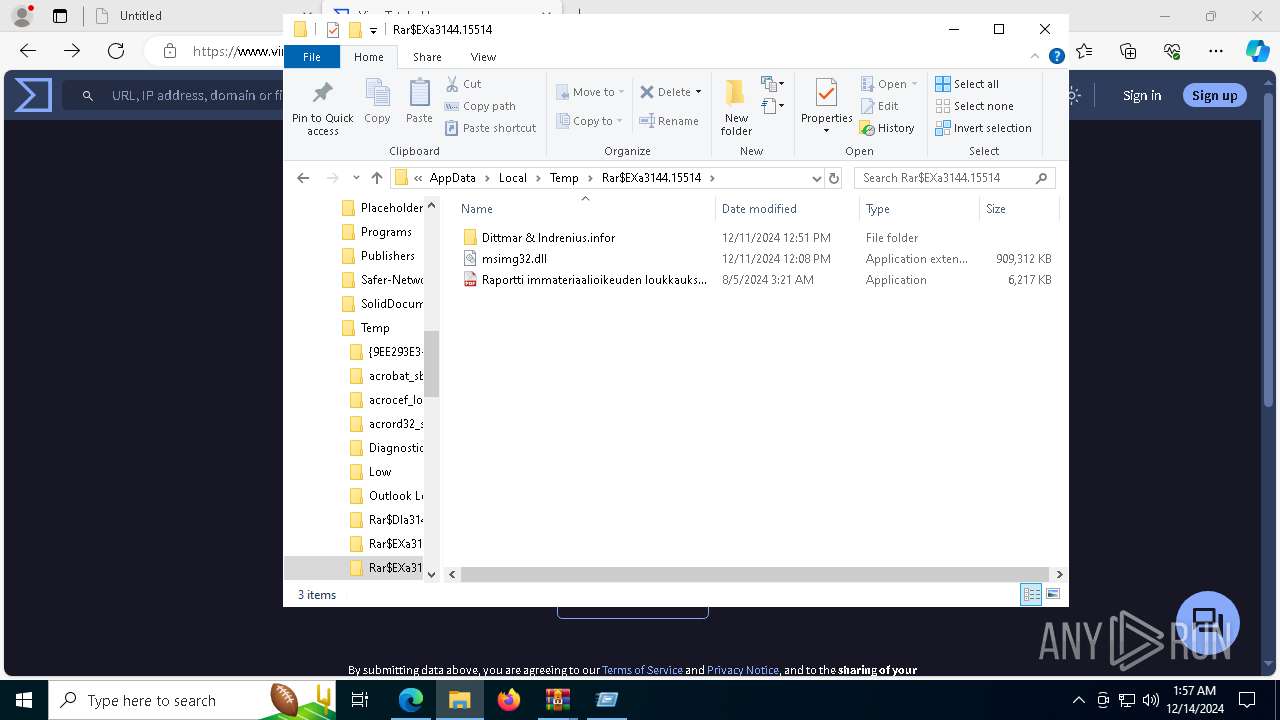
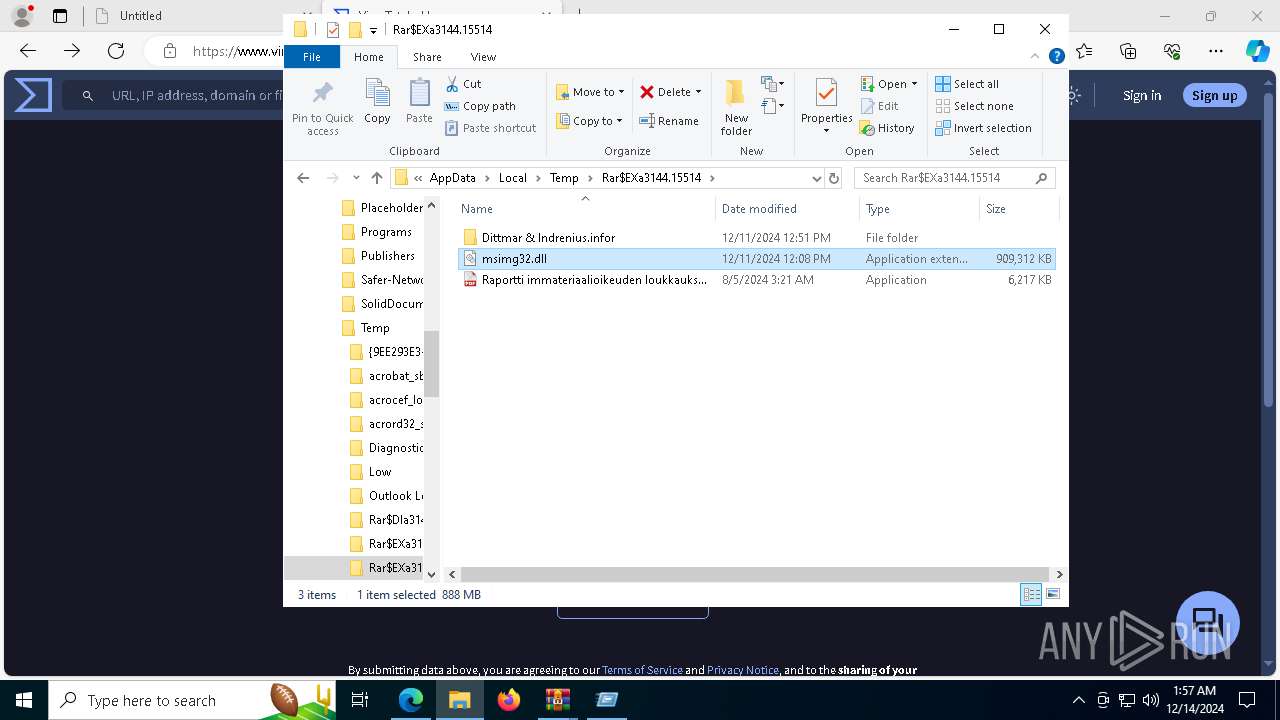
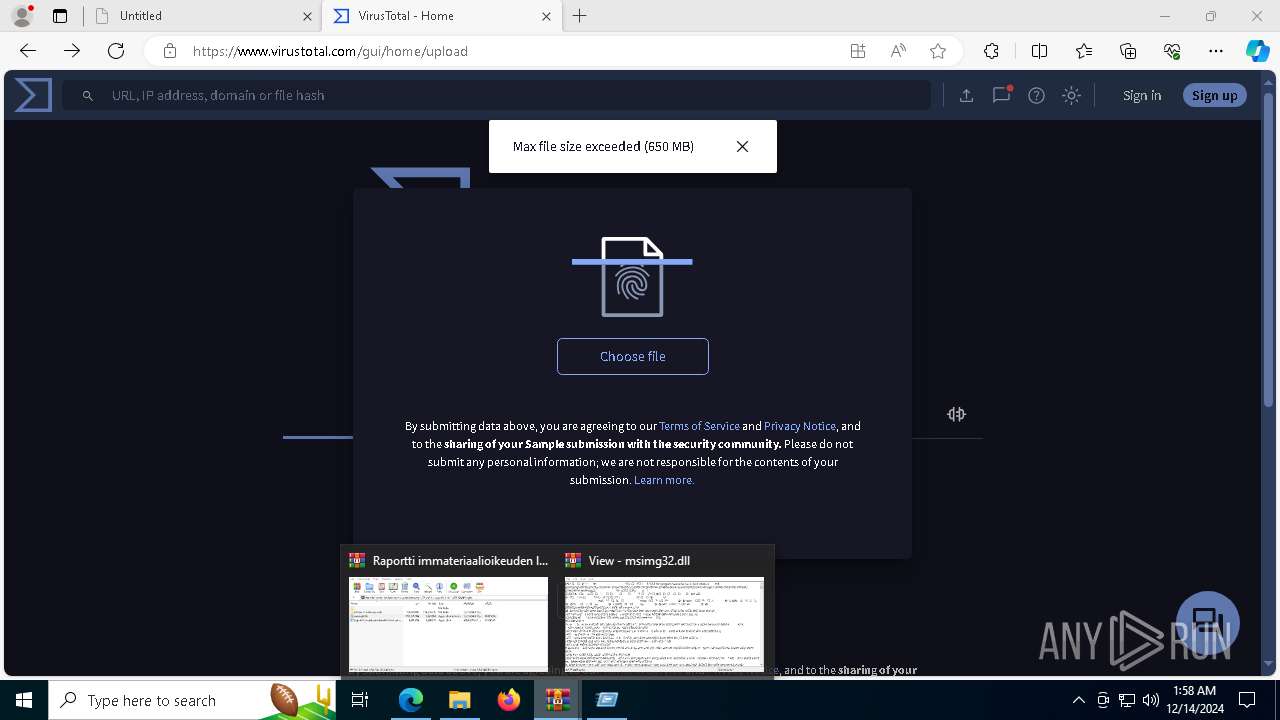
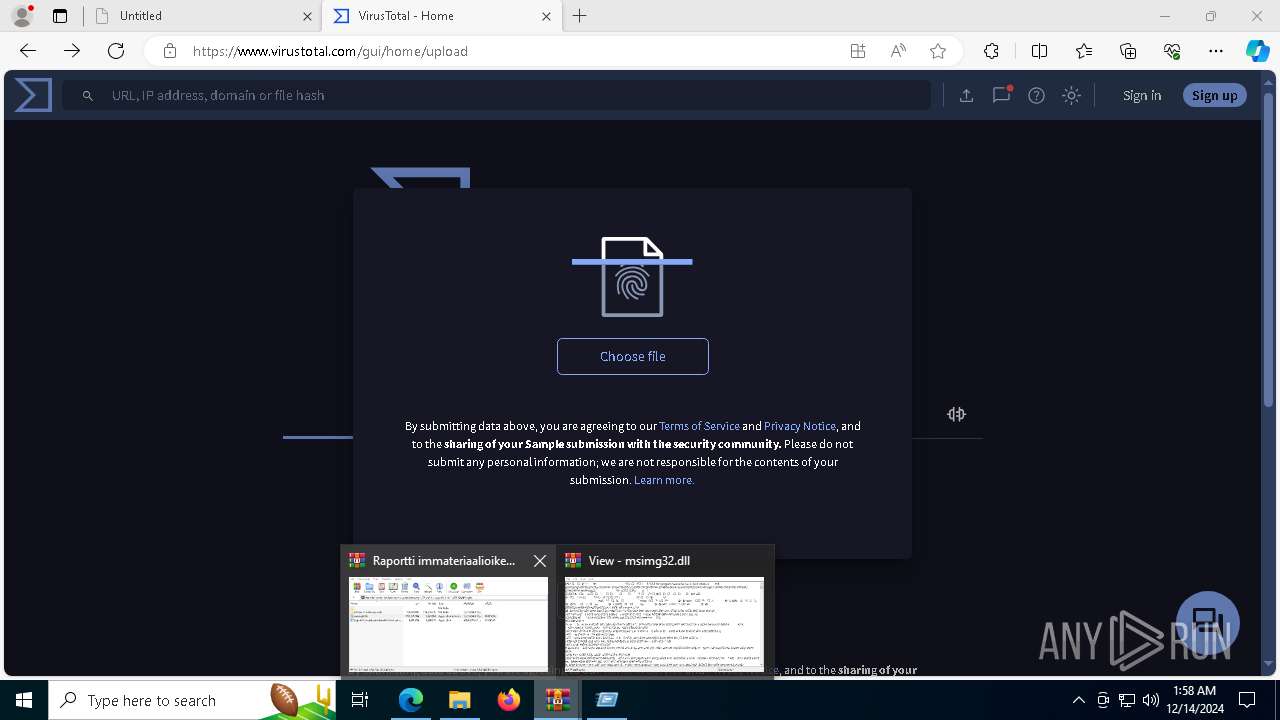
Application launched itself
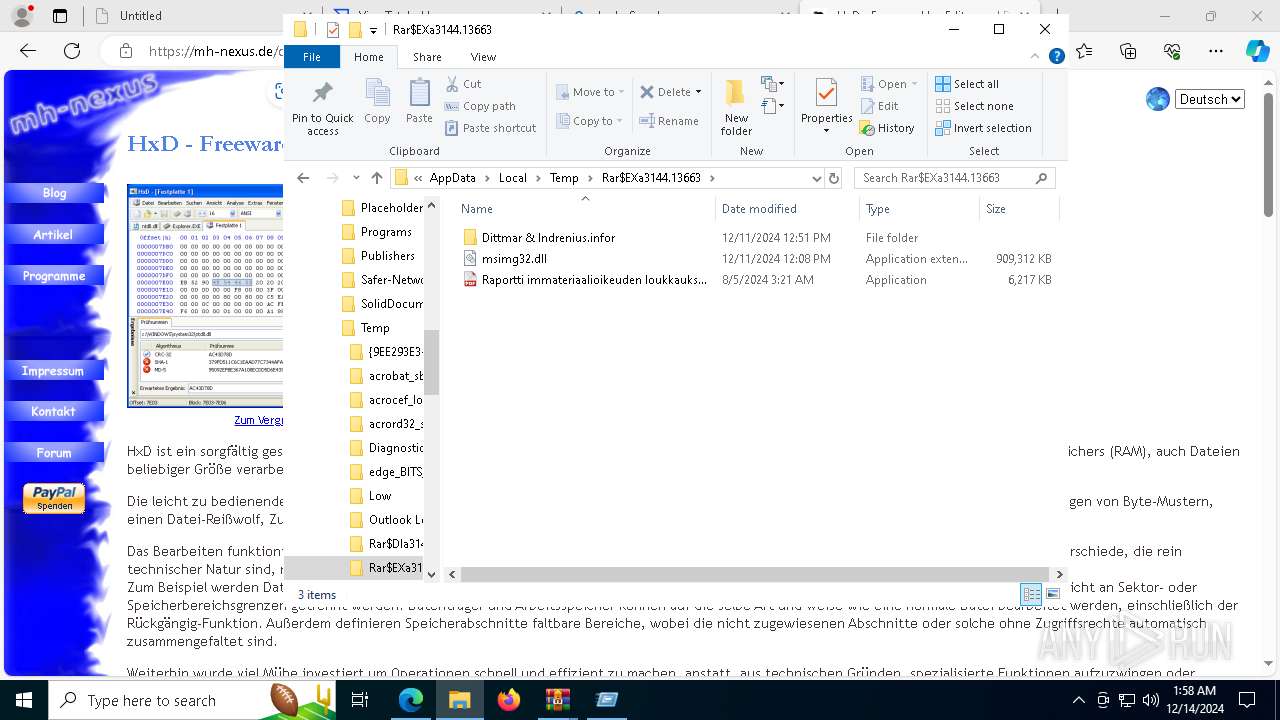
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 4944)
- chrome.exe (PID: 7084)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 7072)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 3848)
- svchost.exe (PID: 5496)
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
- dllhost.exe (PID: 8096)
- dllhost.exe (PID: 2956)
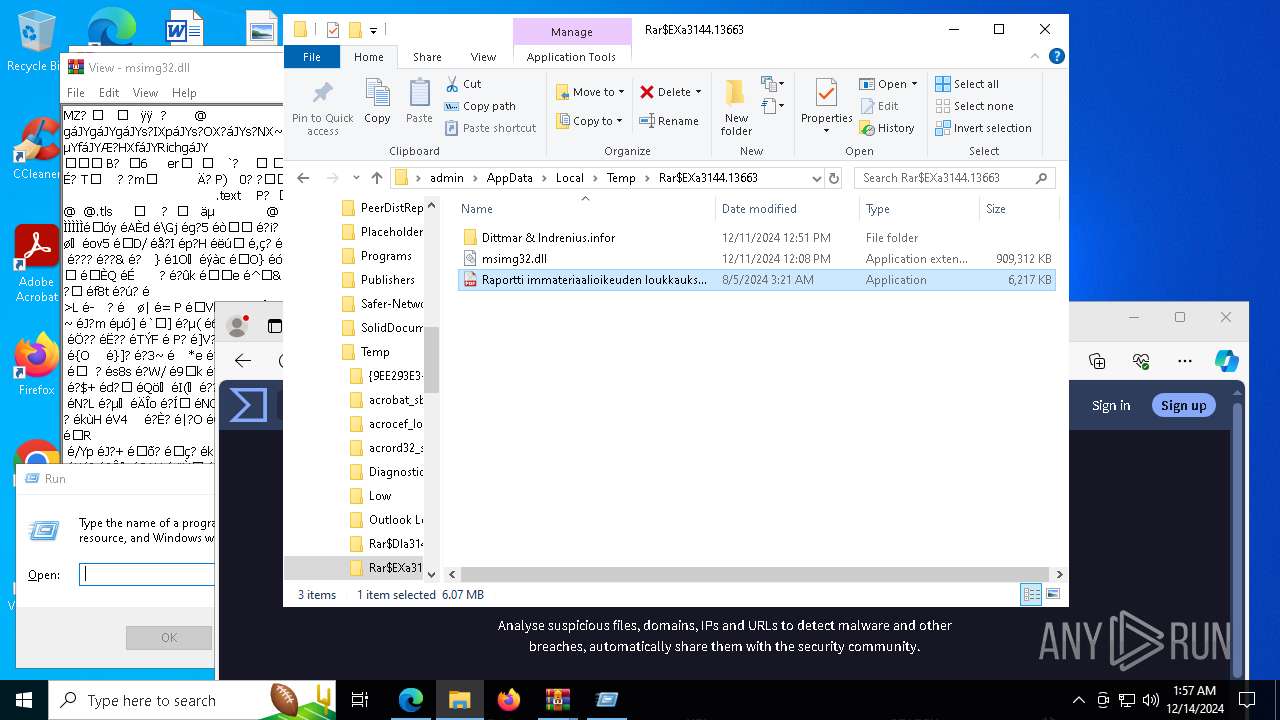
Executes application which crashes
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 6744)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 1344)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 5496)
- svchost.exe (PID: 3848)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 7332)
- msedge.exe (PID: 8088)
Connects to unusual port
- svchost.exe (PID: 5496)
- svchost.exe (PID: 3848)
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
Searches for installed software
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
INFO
Checks supported languages
- SearchApp.exe (PID: 5064)
- identity_helper.exe (PID: 2100)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 4944)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 7072)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 1344)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 6744)
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- setup_wm.exe (PID: 7296)
- msedge.exe (PID: 8088)
Reads Environment values
- identity_helper.exe (PID: 2100)
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
Reads the computer name
- identity_helper.exe (PID: 2100)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 4944)
- Raportti immateriaalioikeuden loukkauksesta.exe (PID: 7072)
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
- setup_wm.exe (PID: 7296)
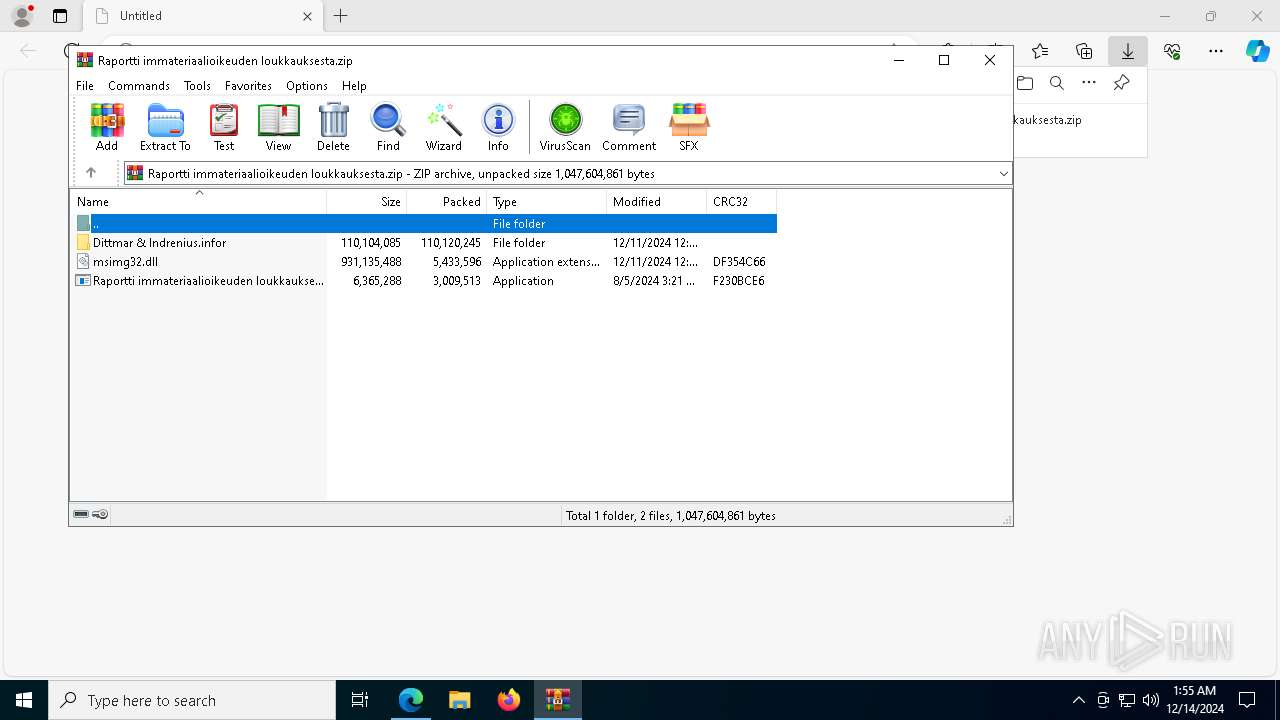
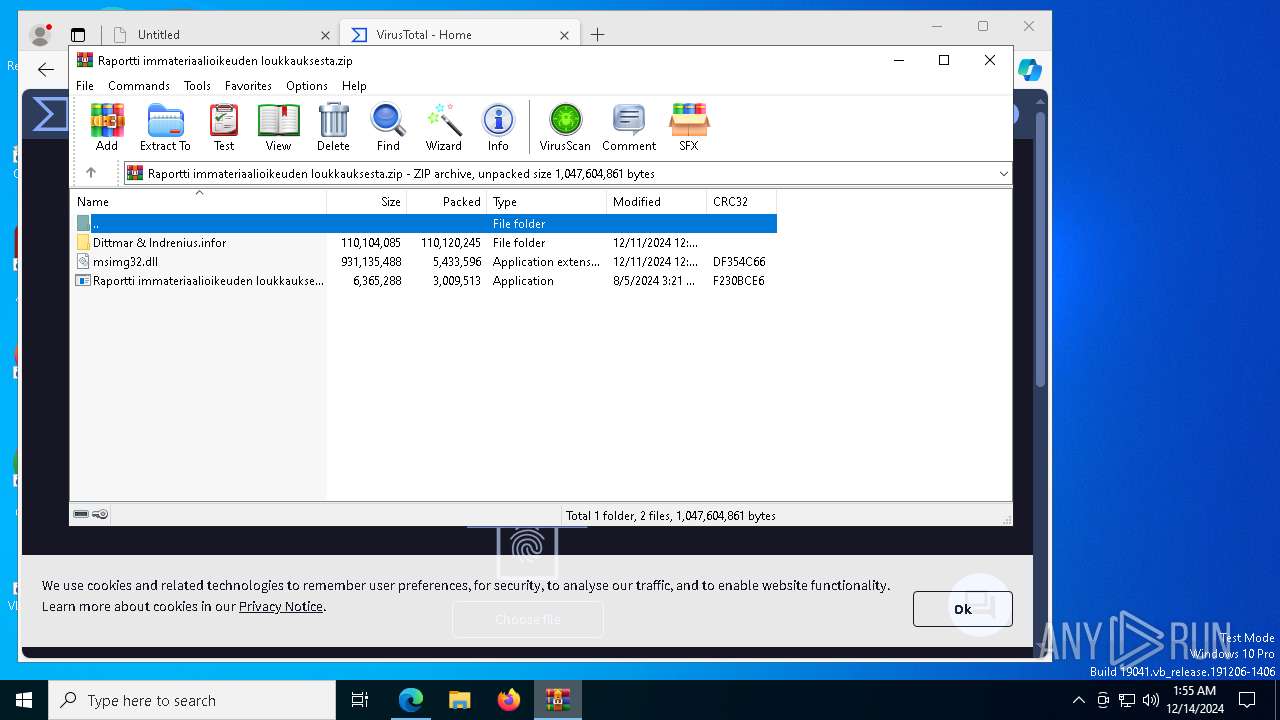
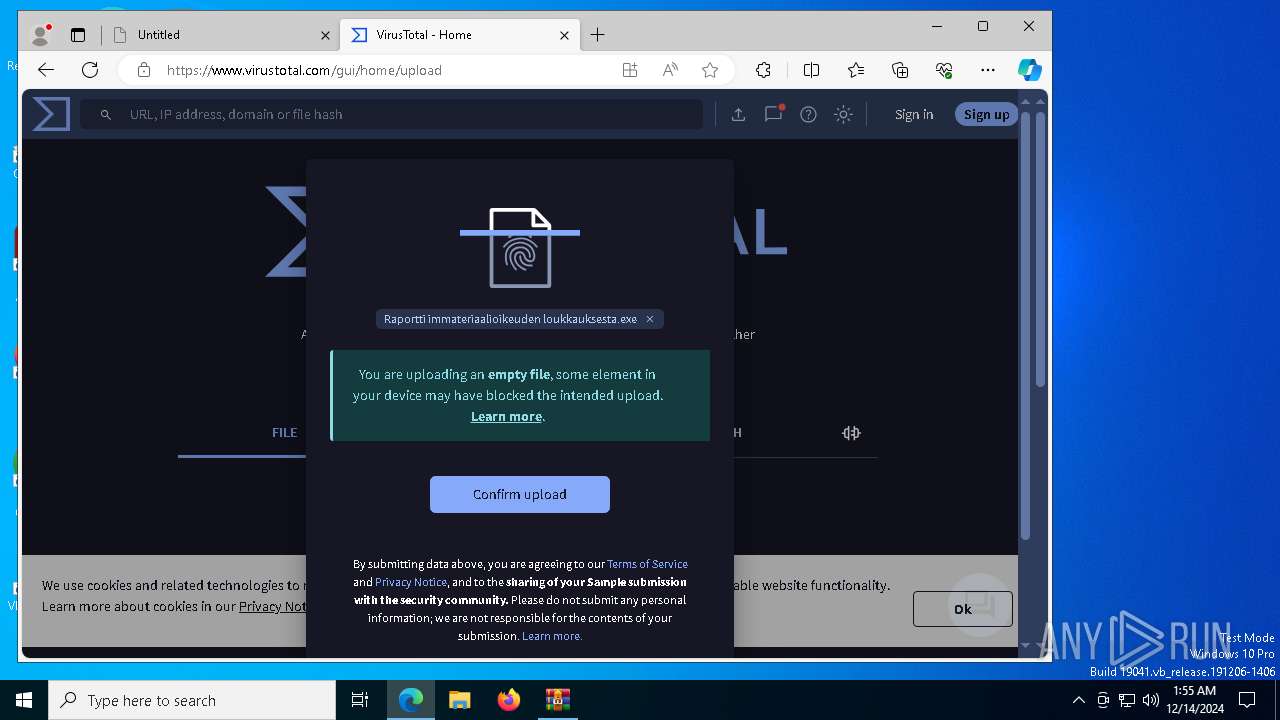
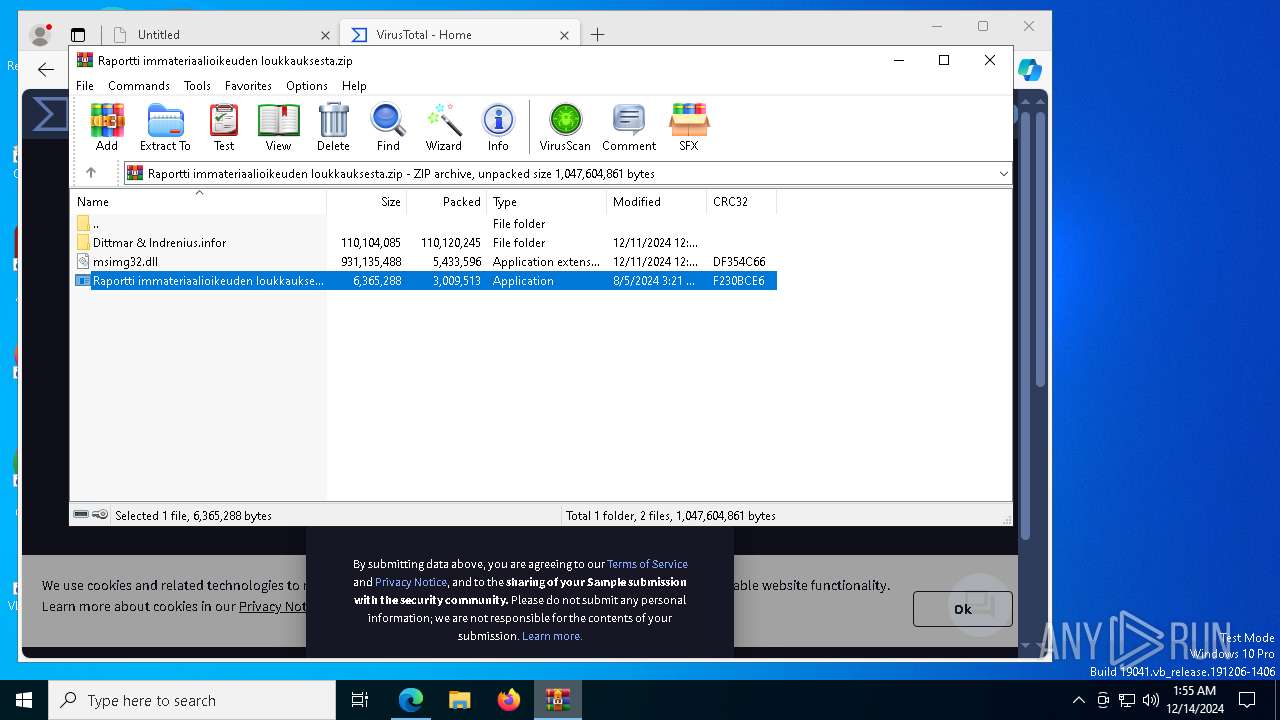
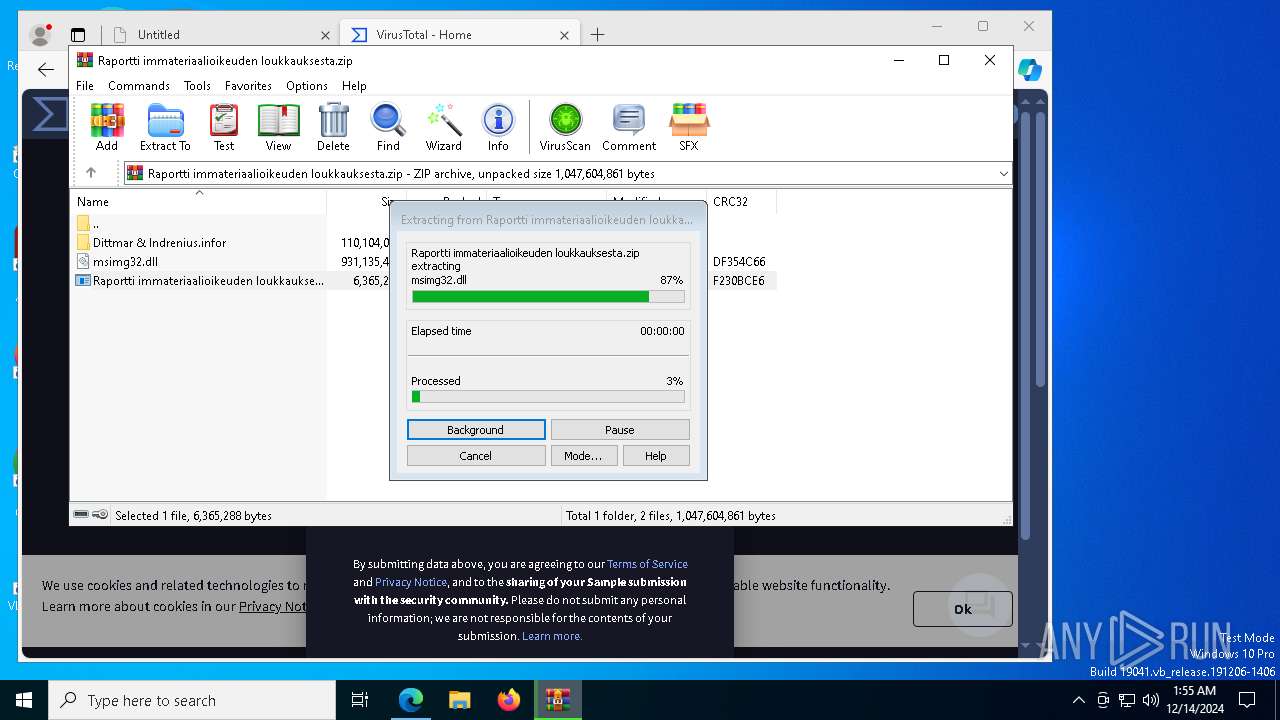
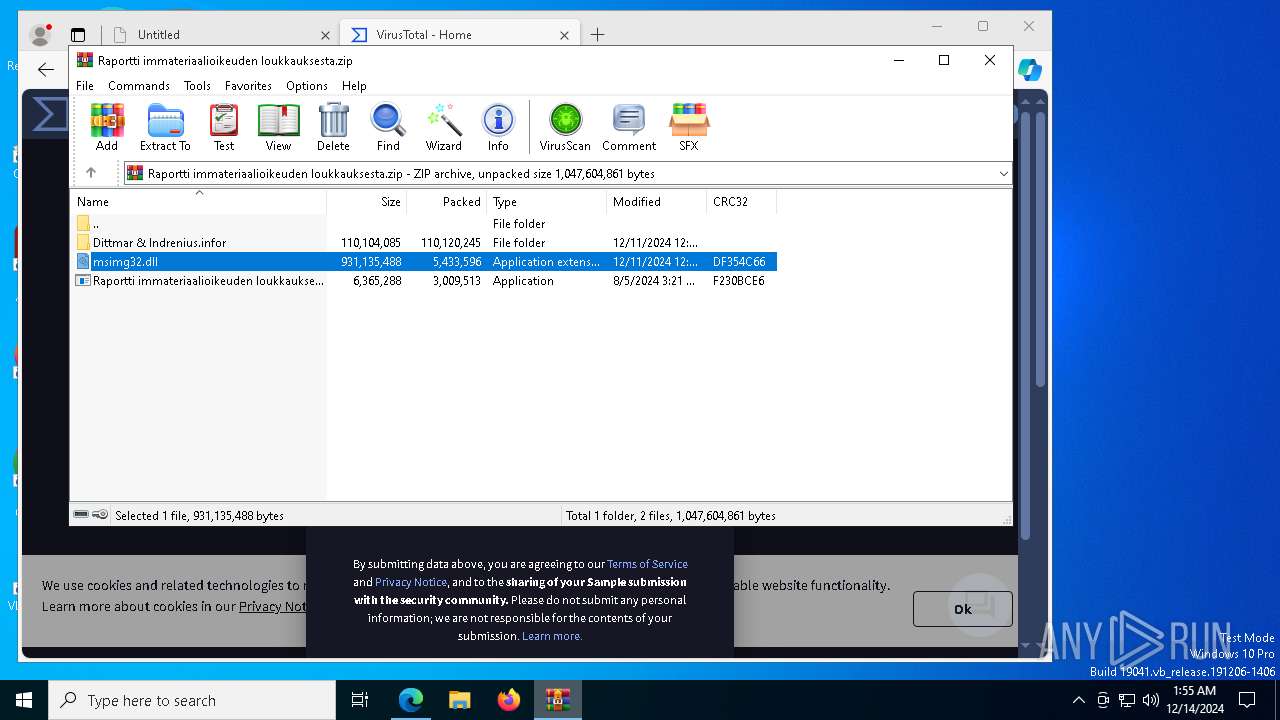
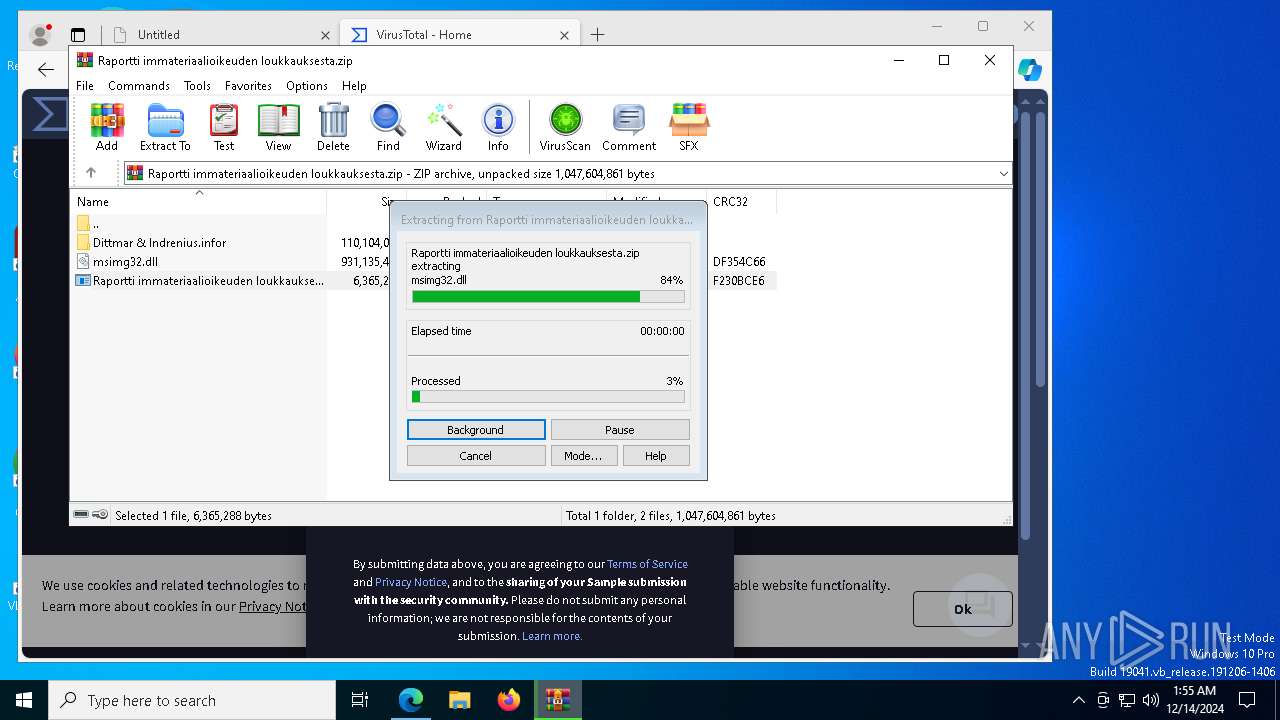
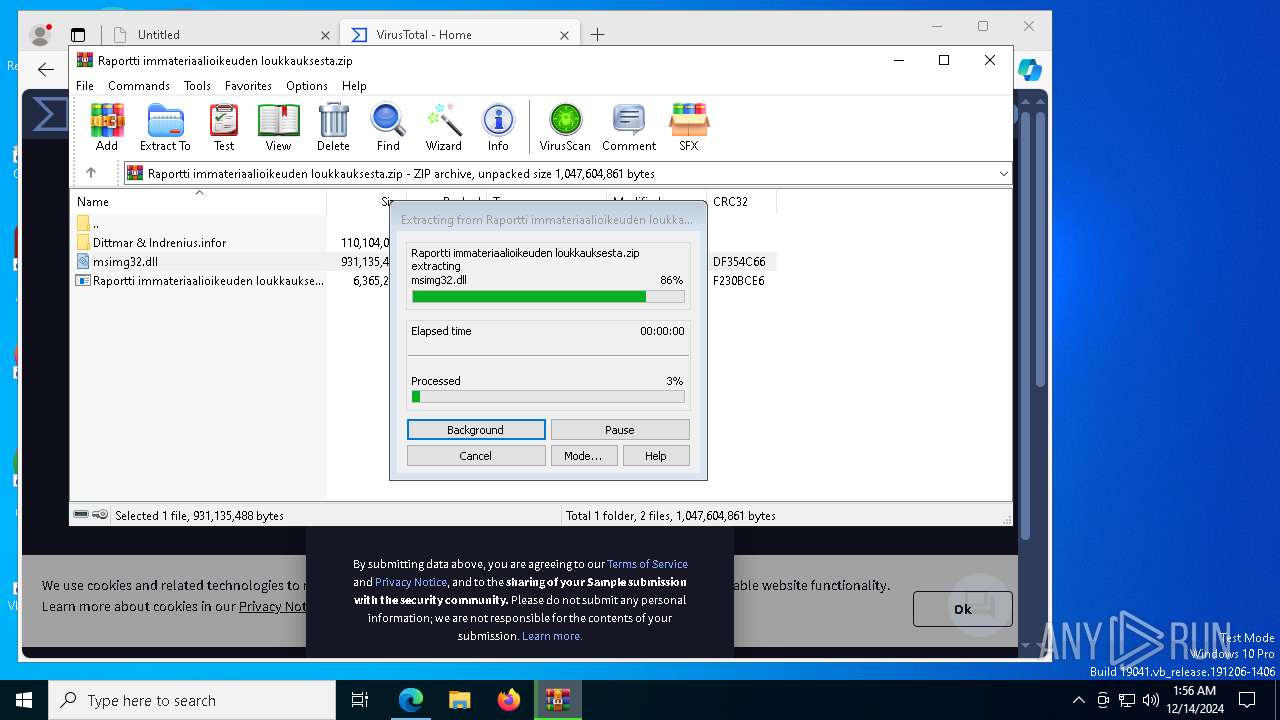
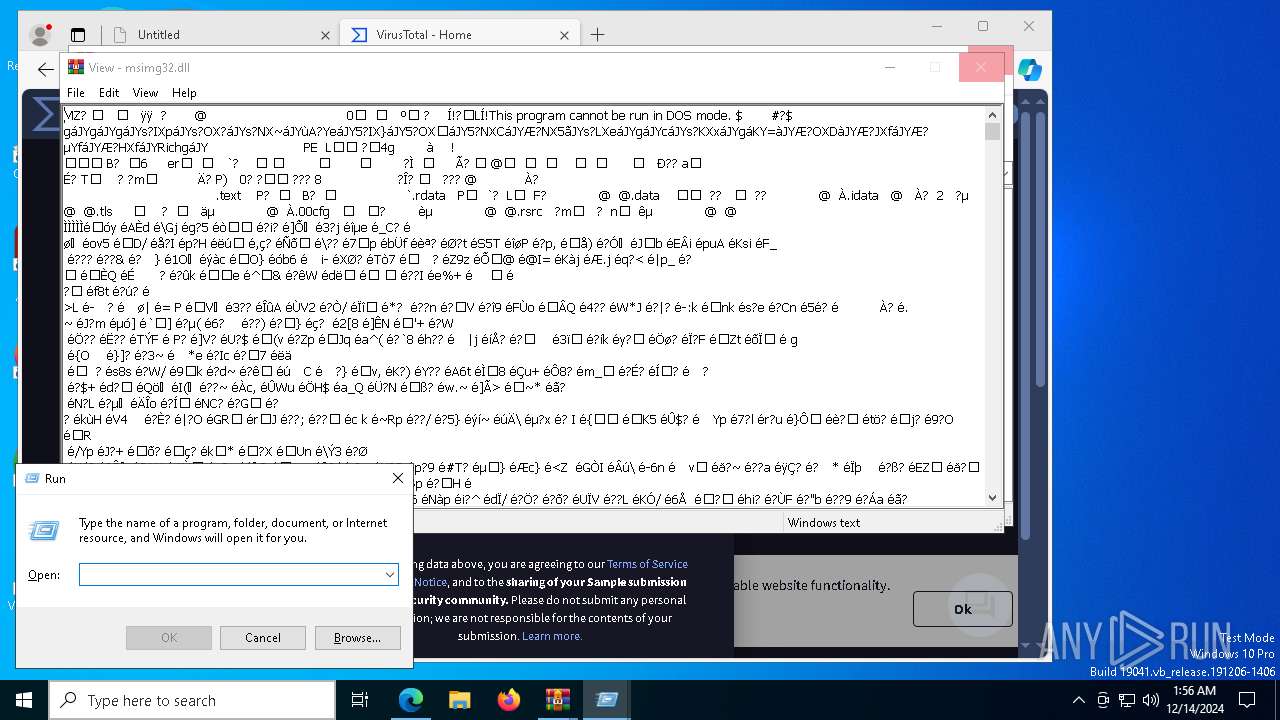
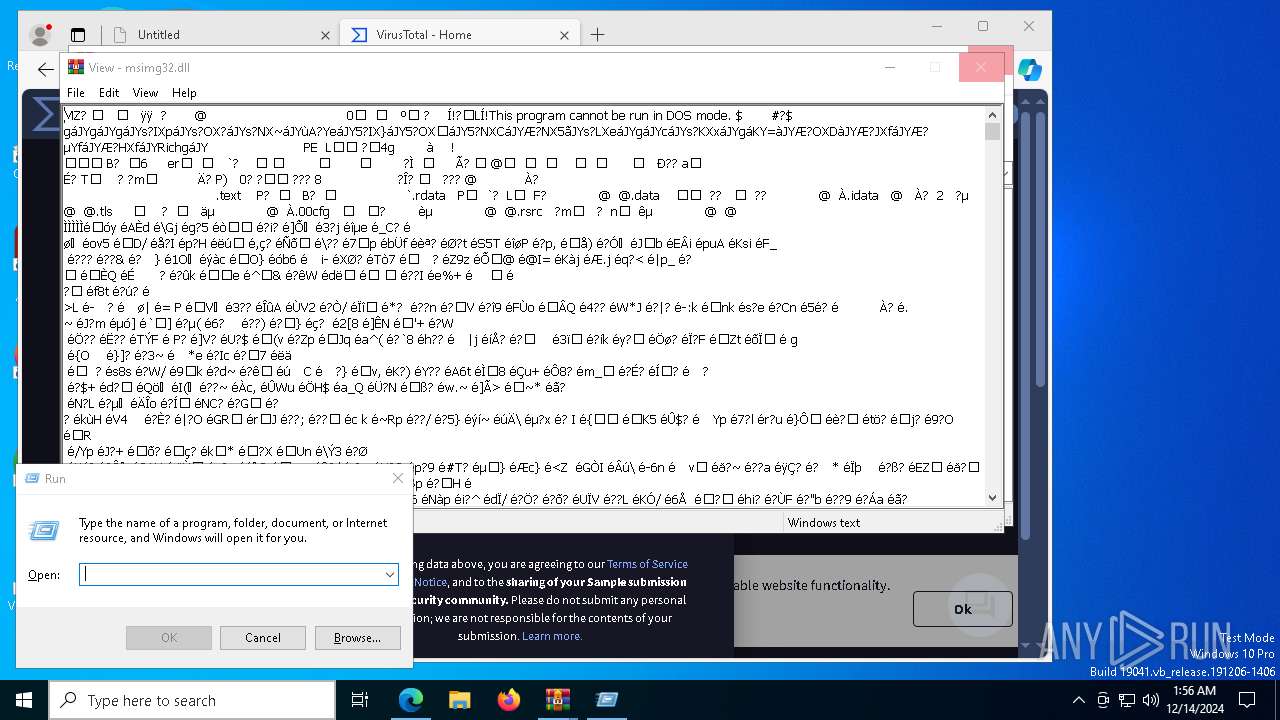
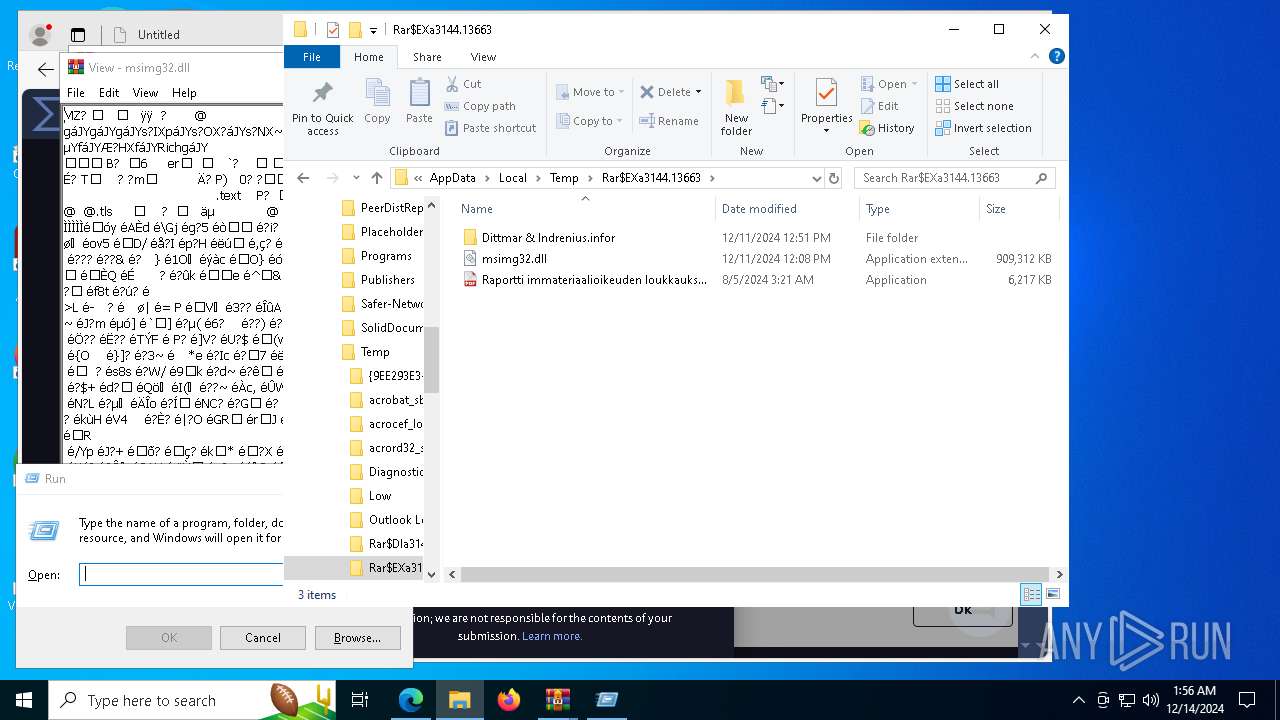
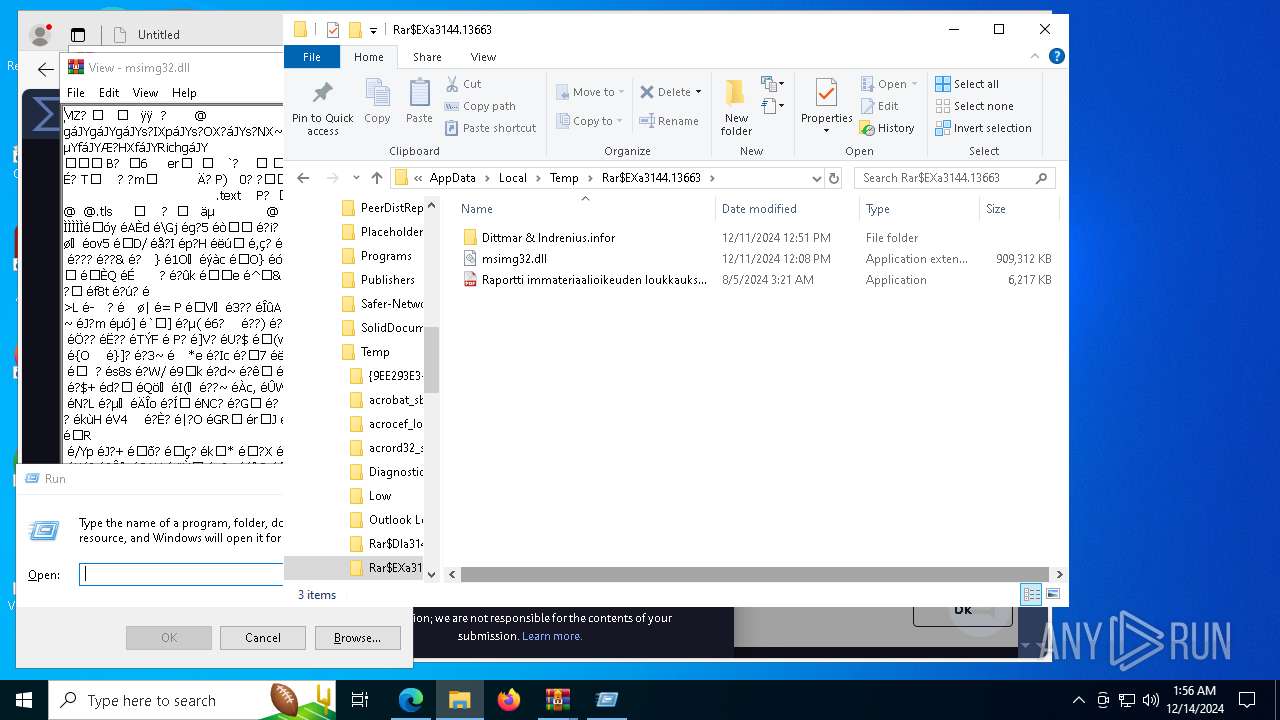
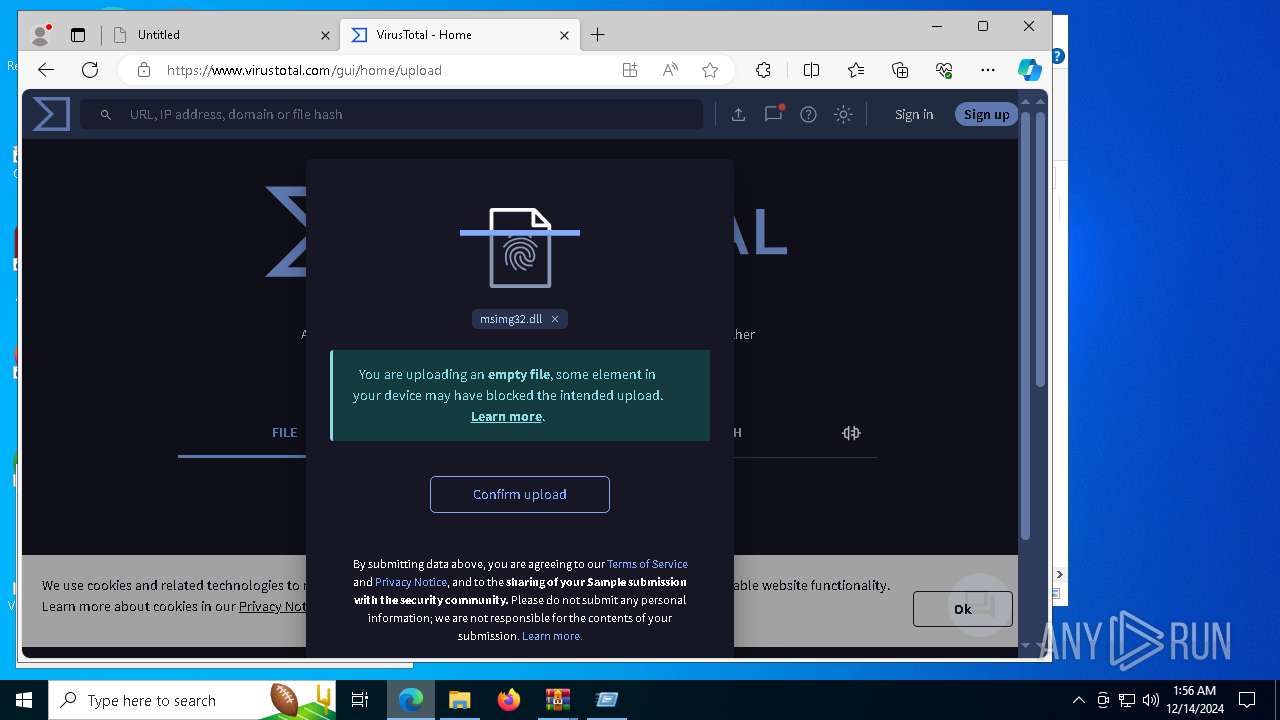
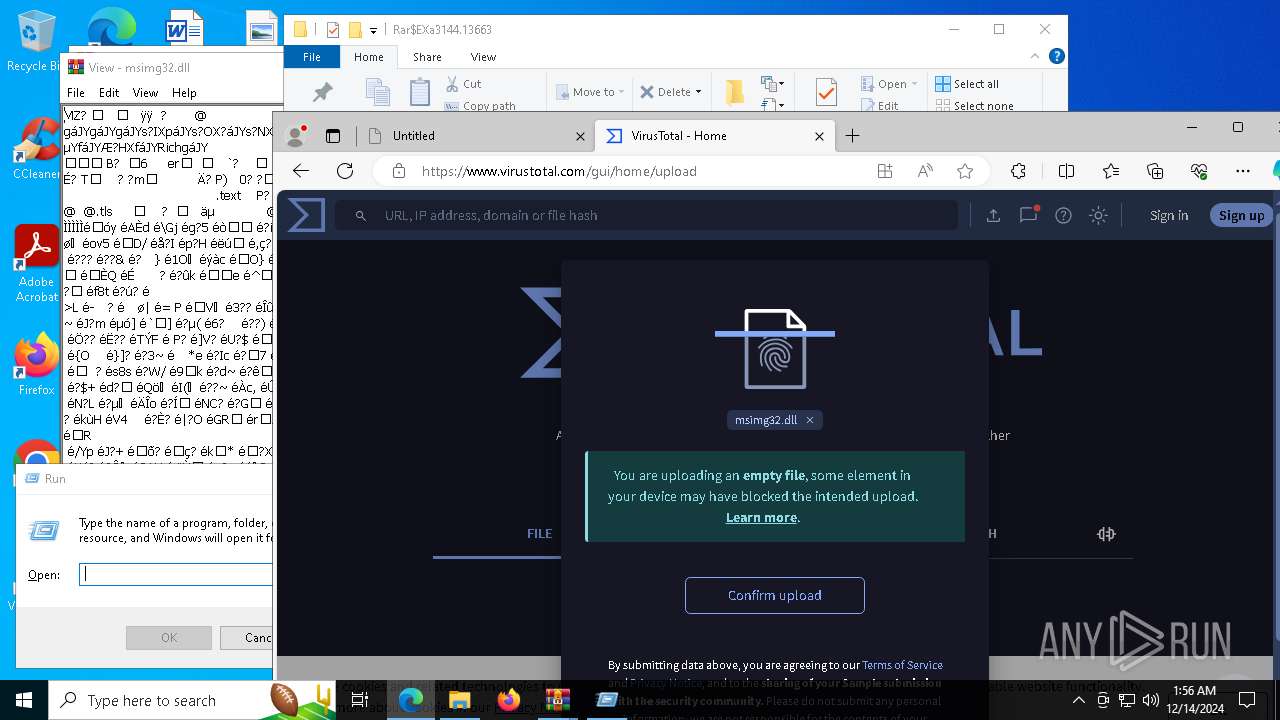
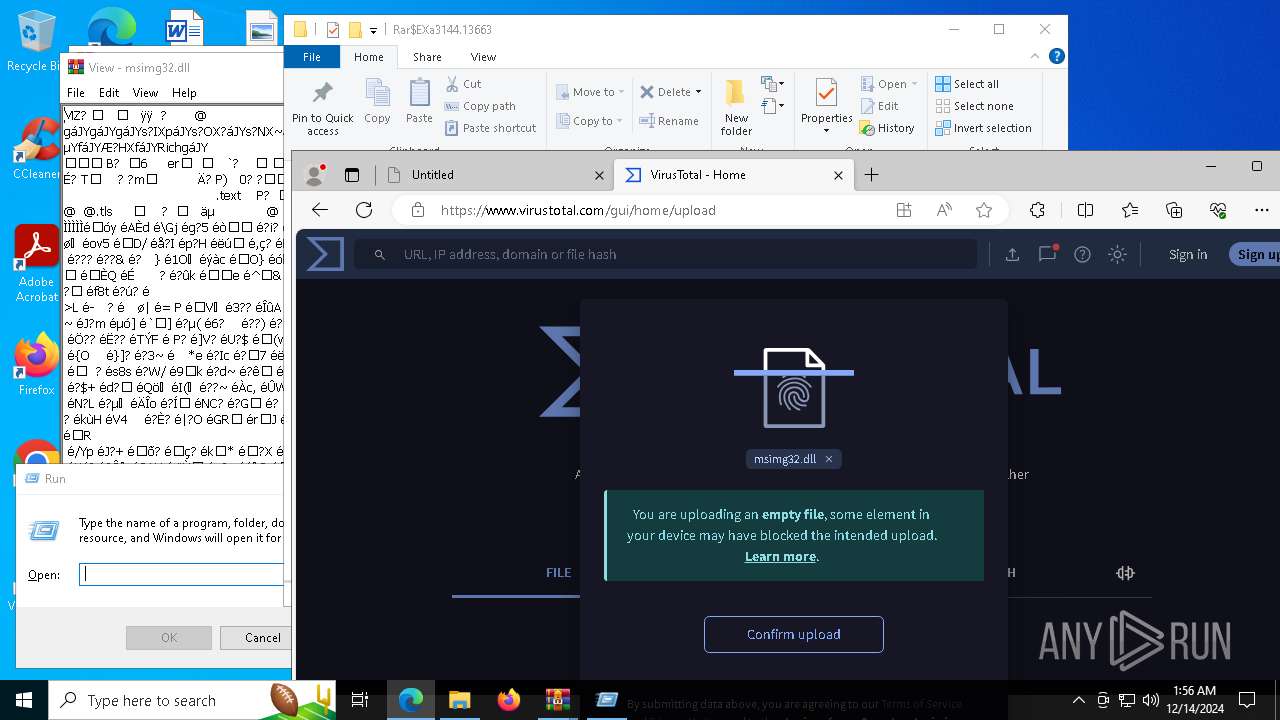
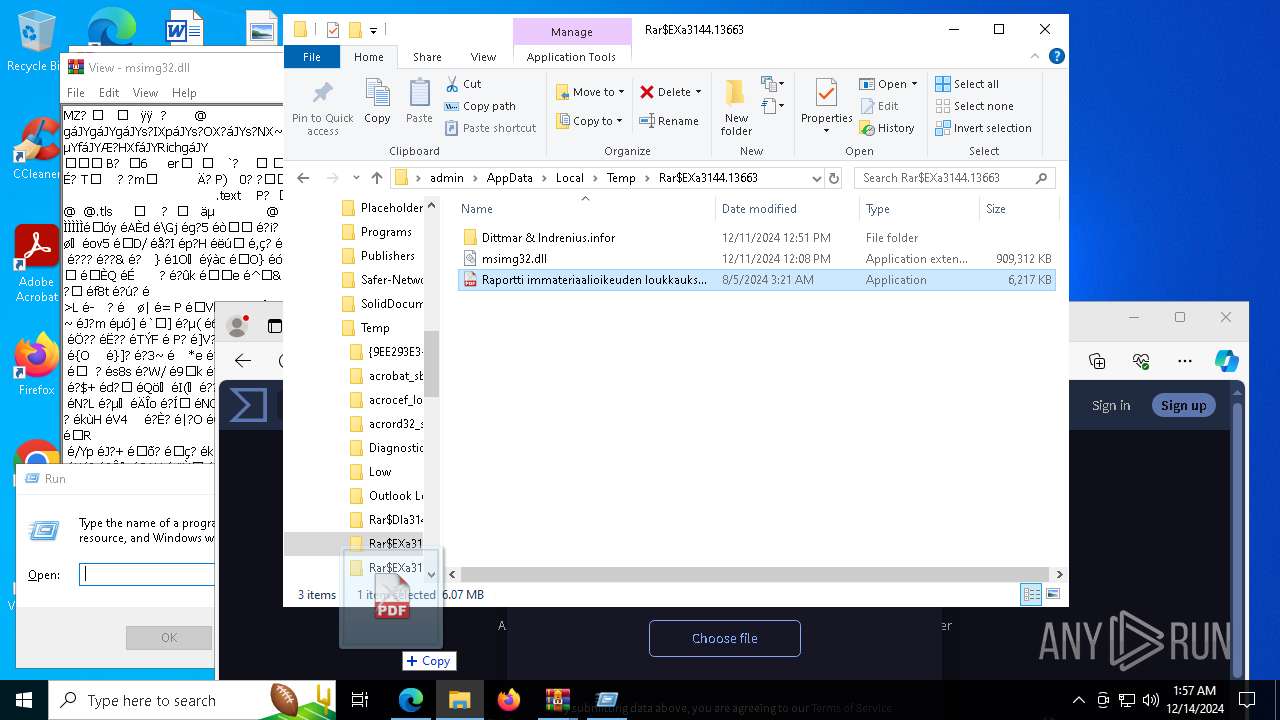
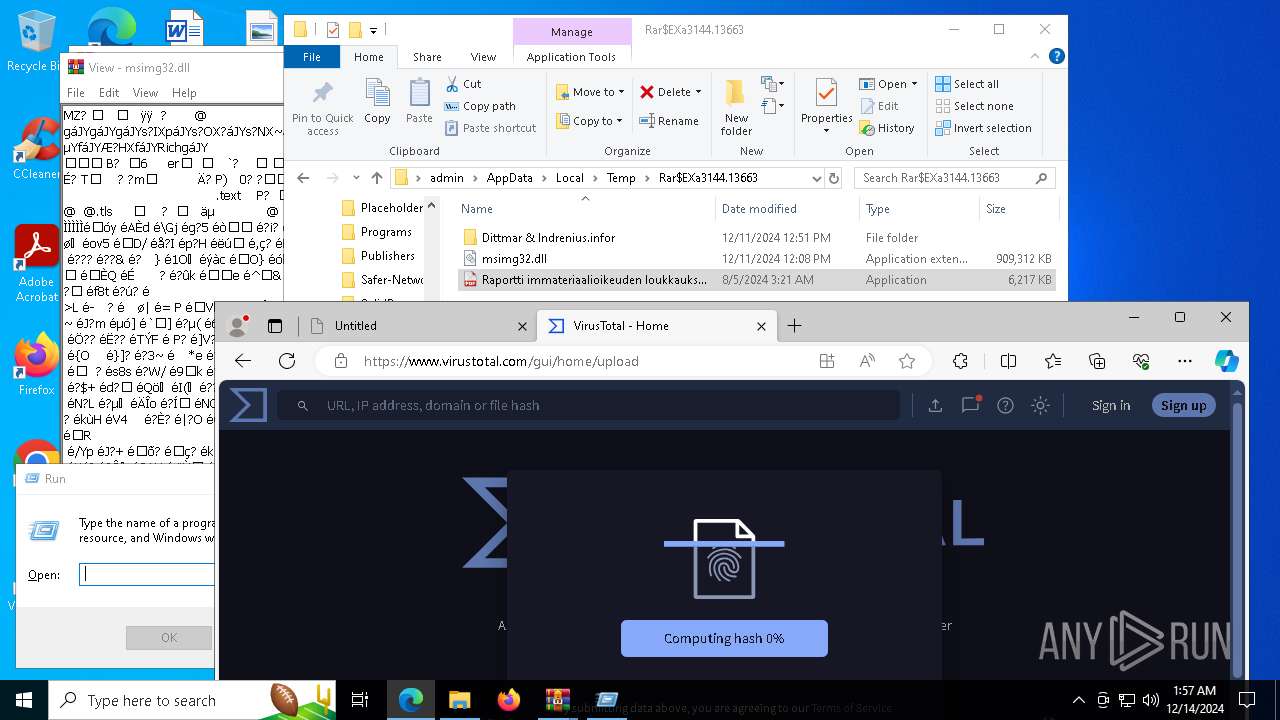
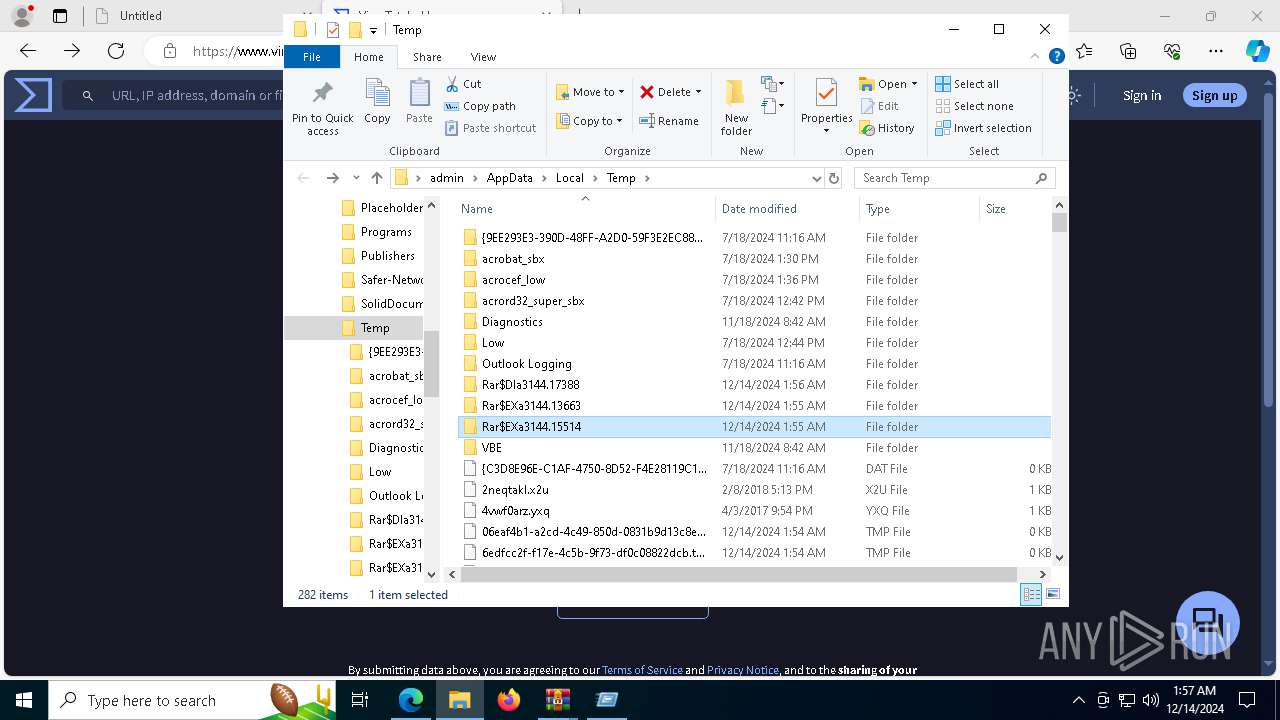
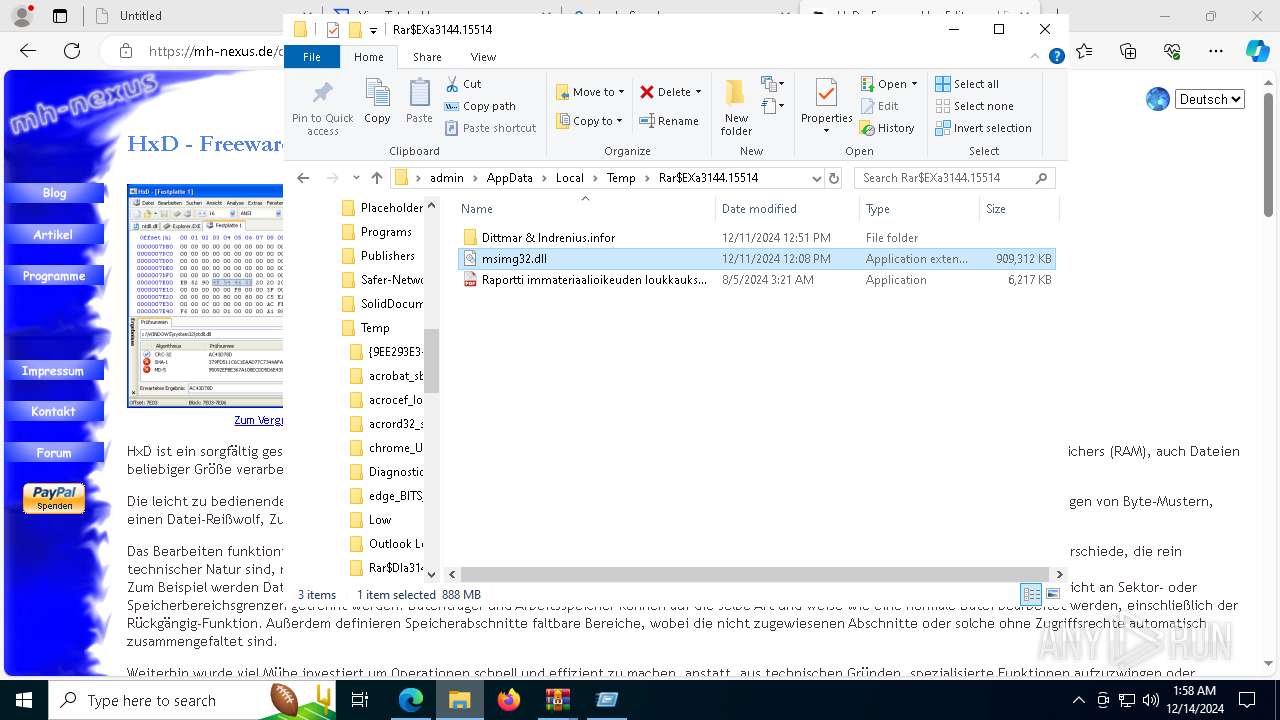
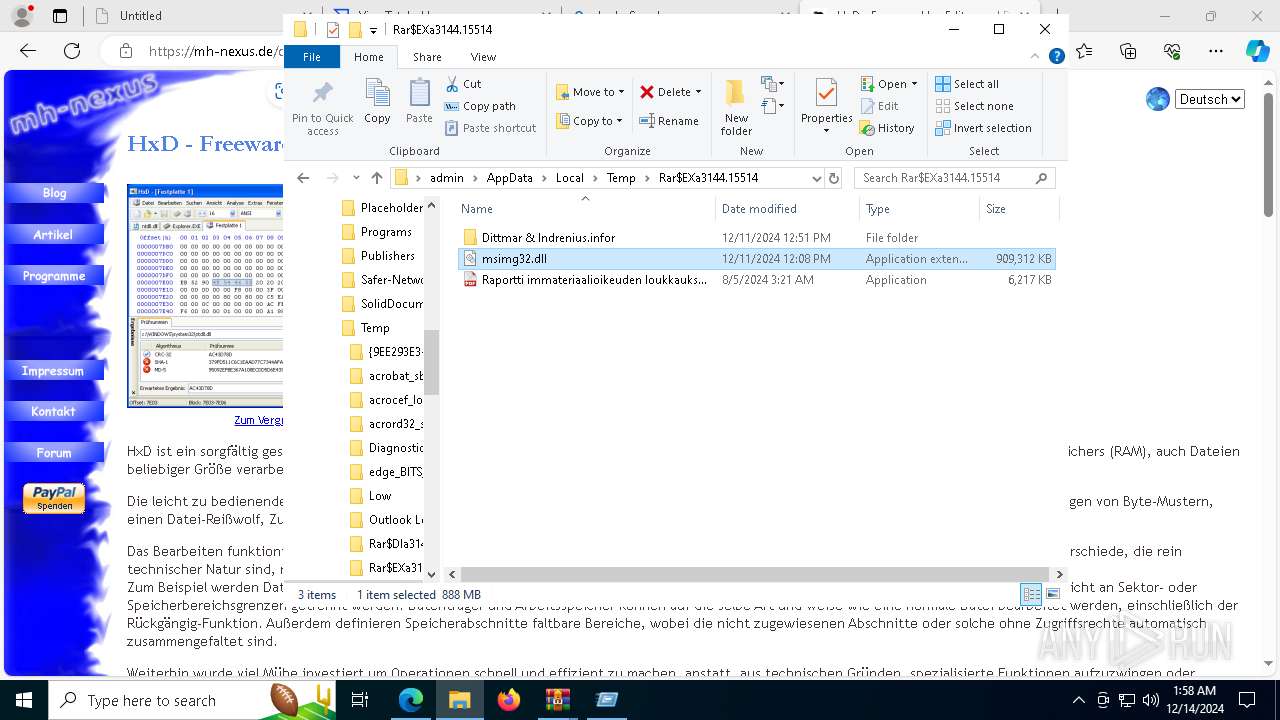
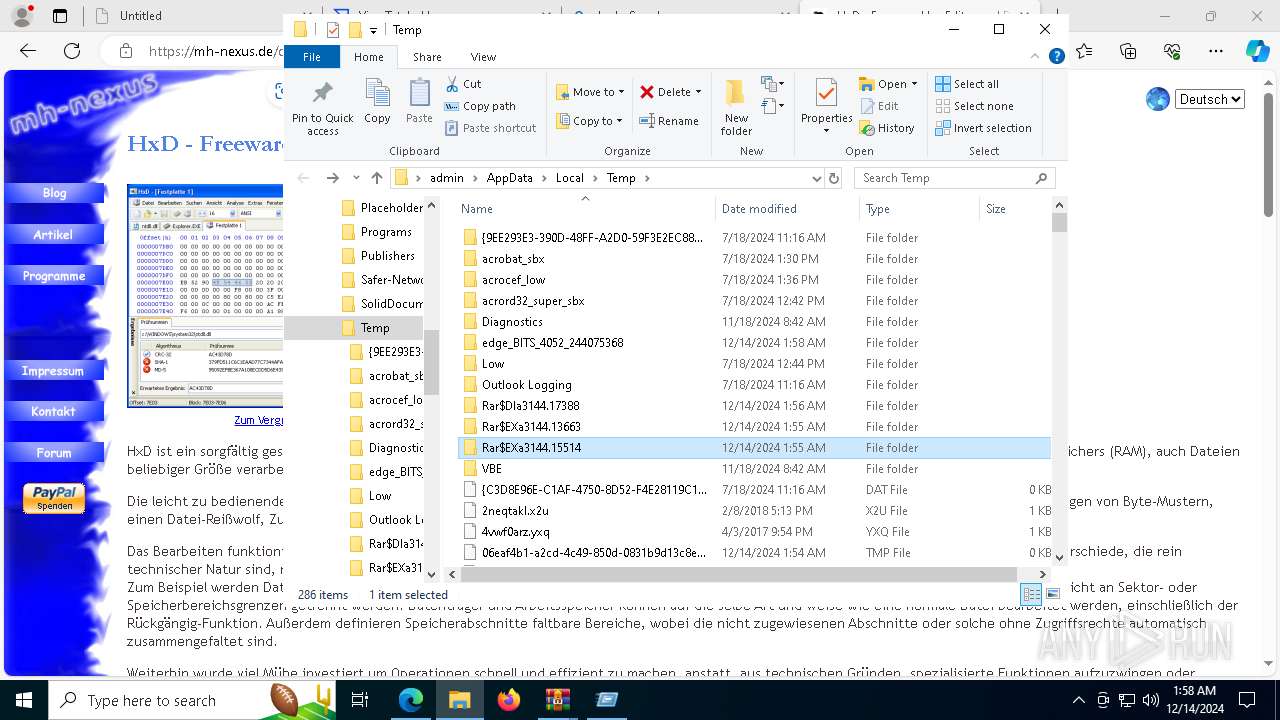
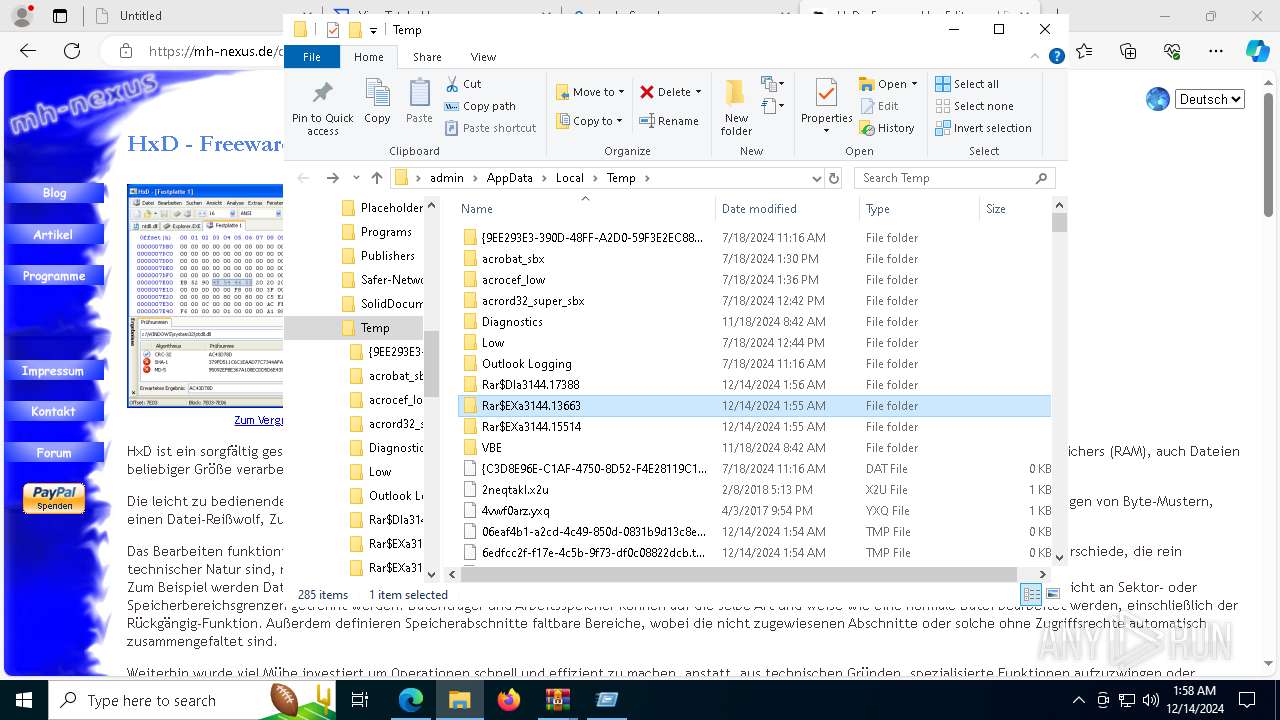
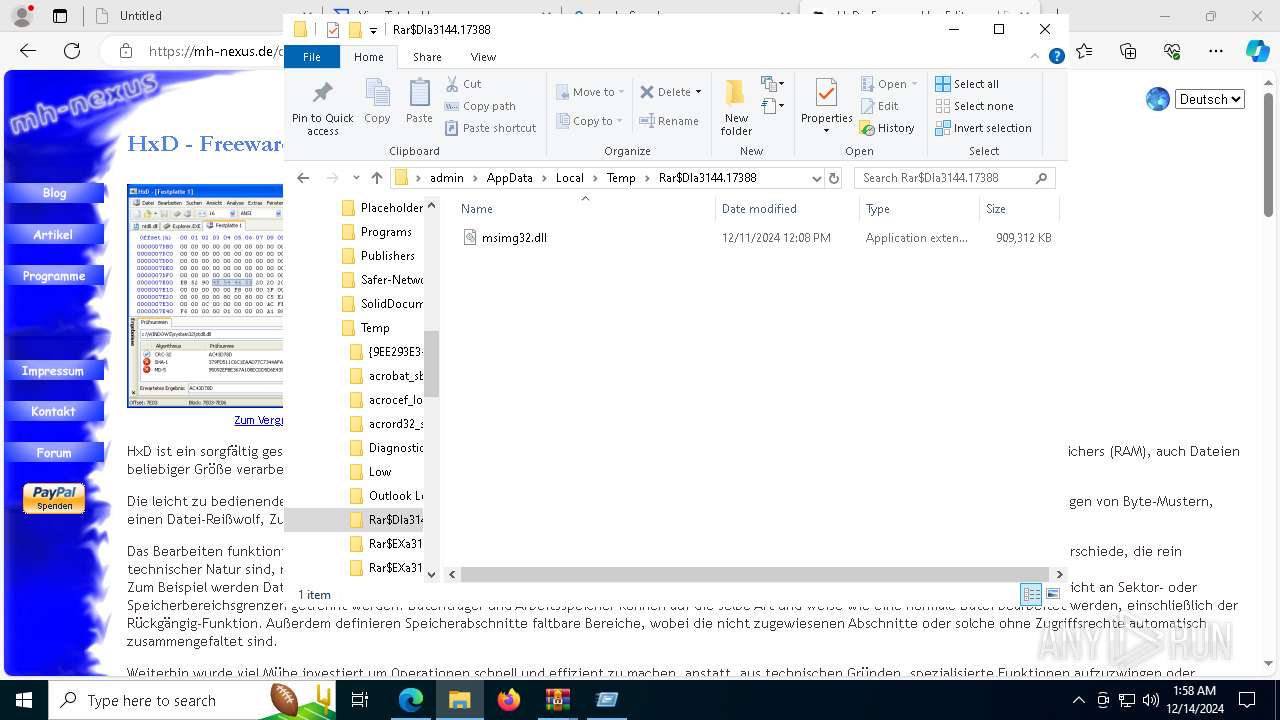
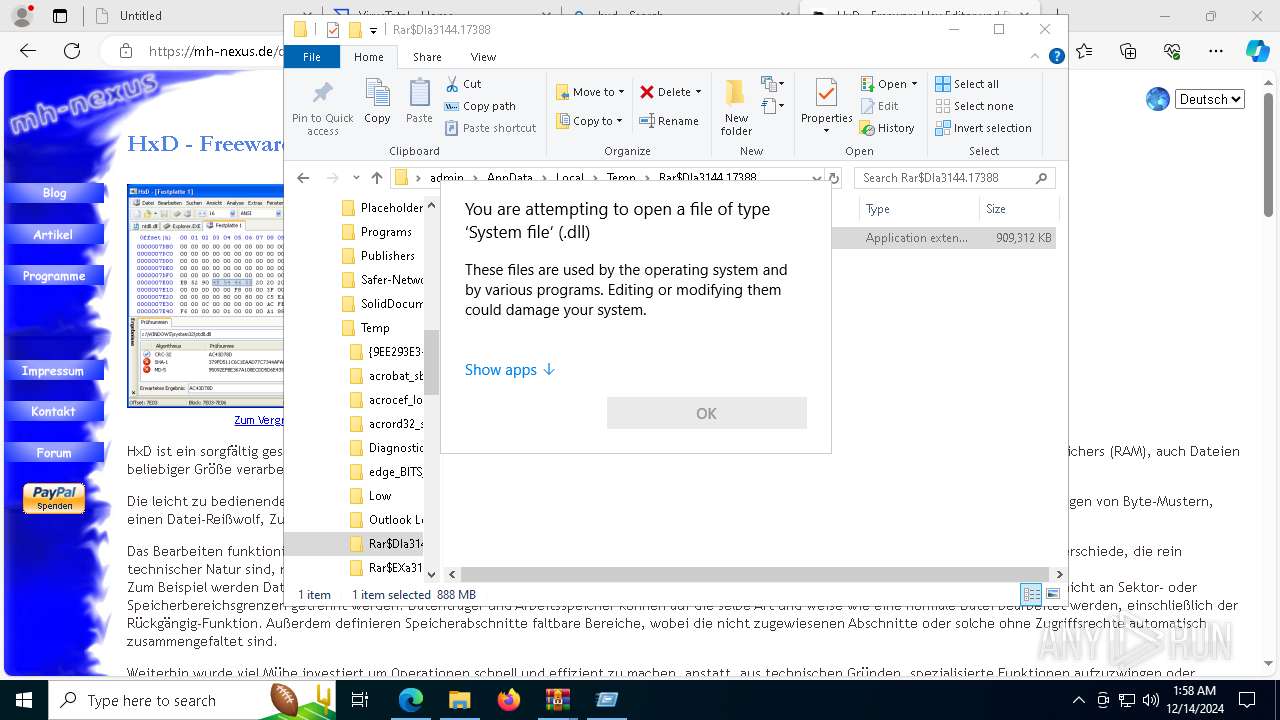
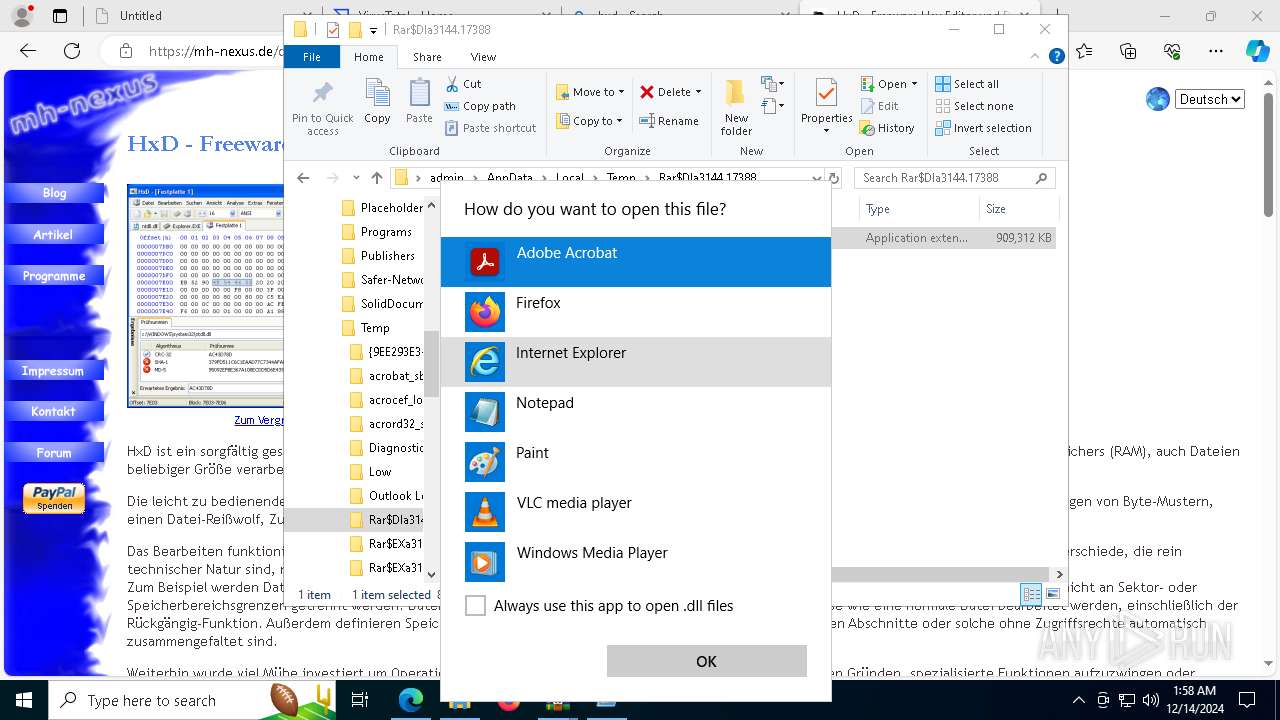
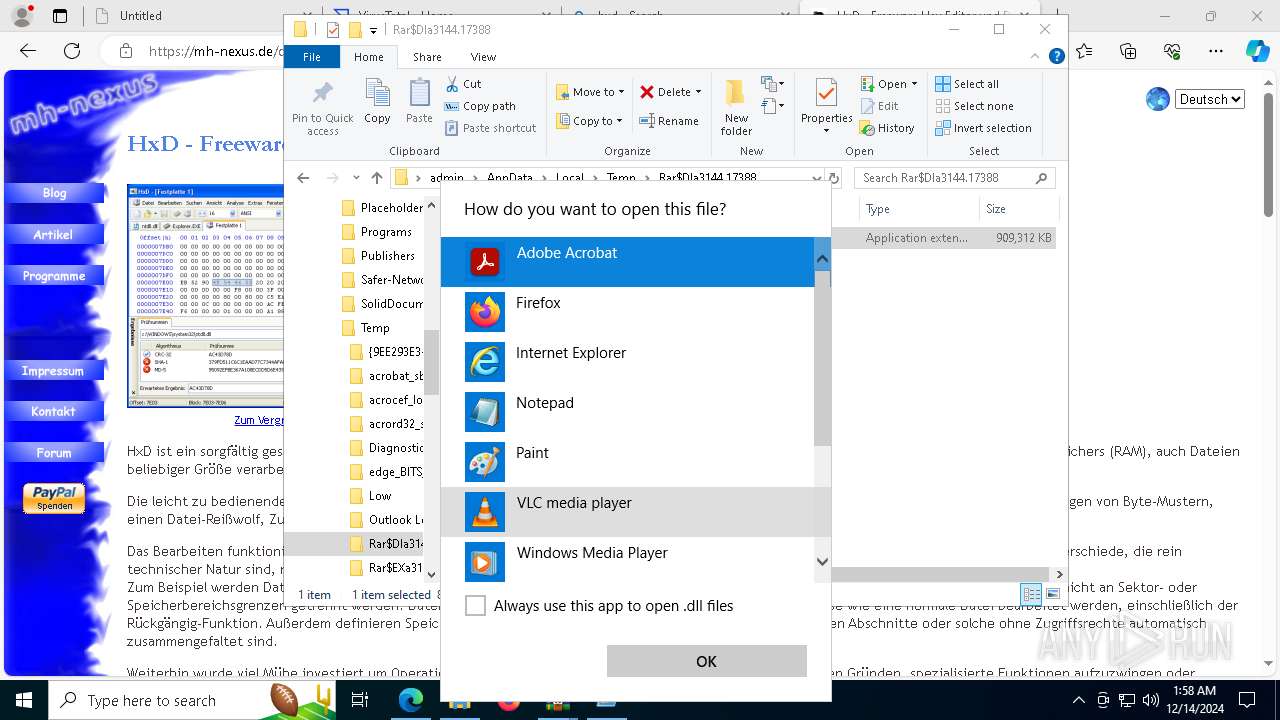
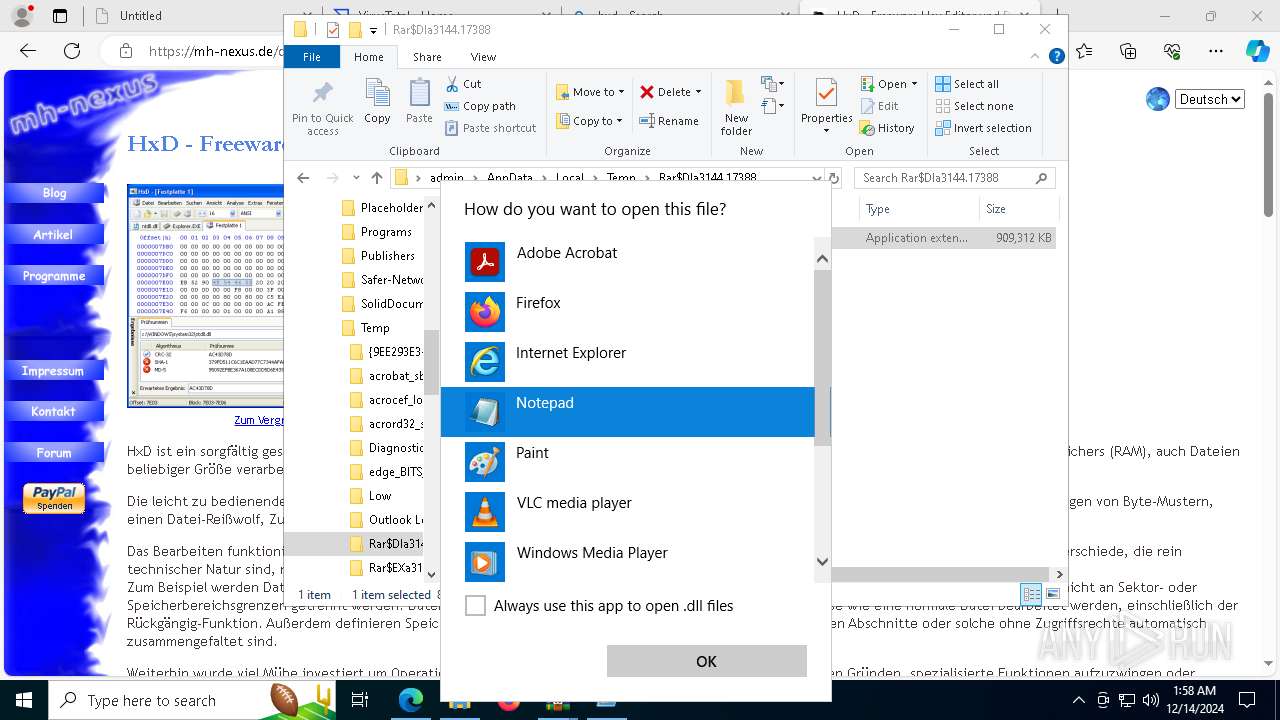
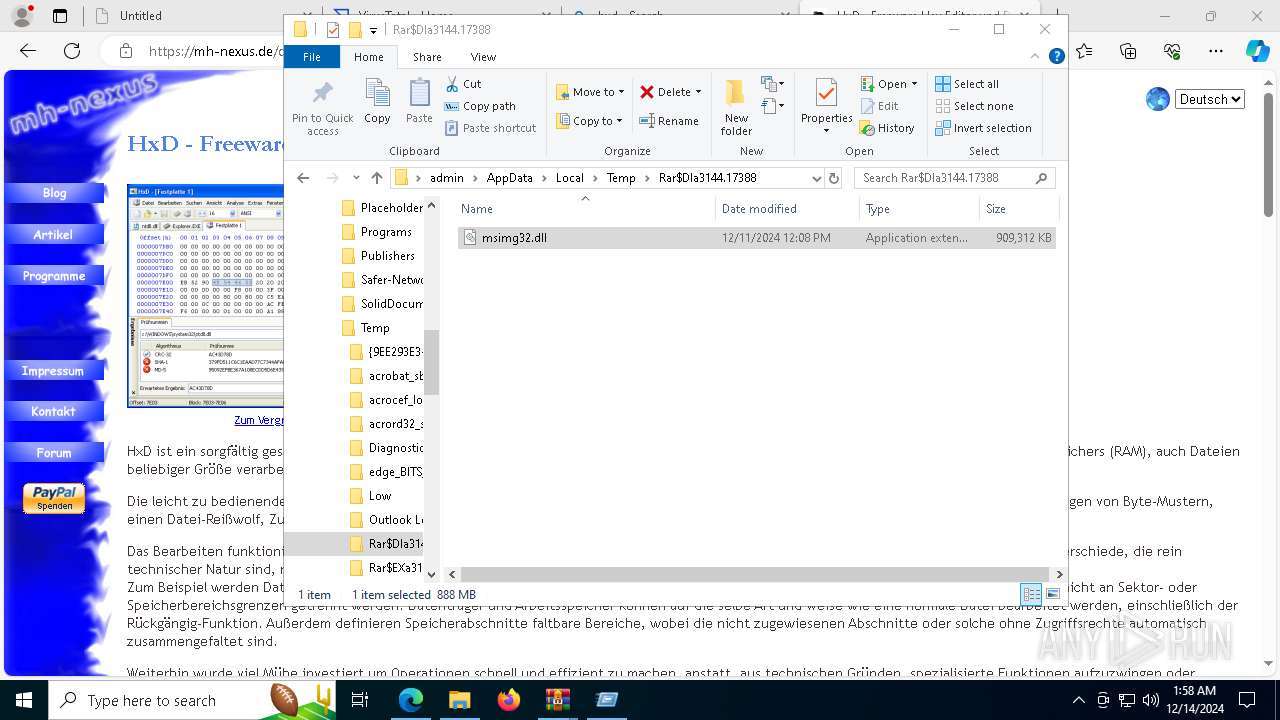
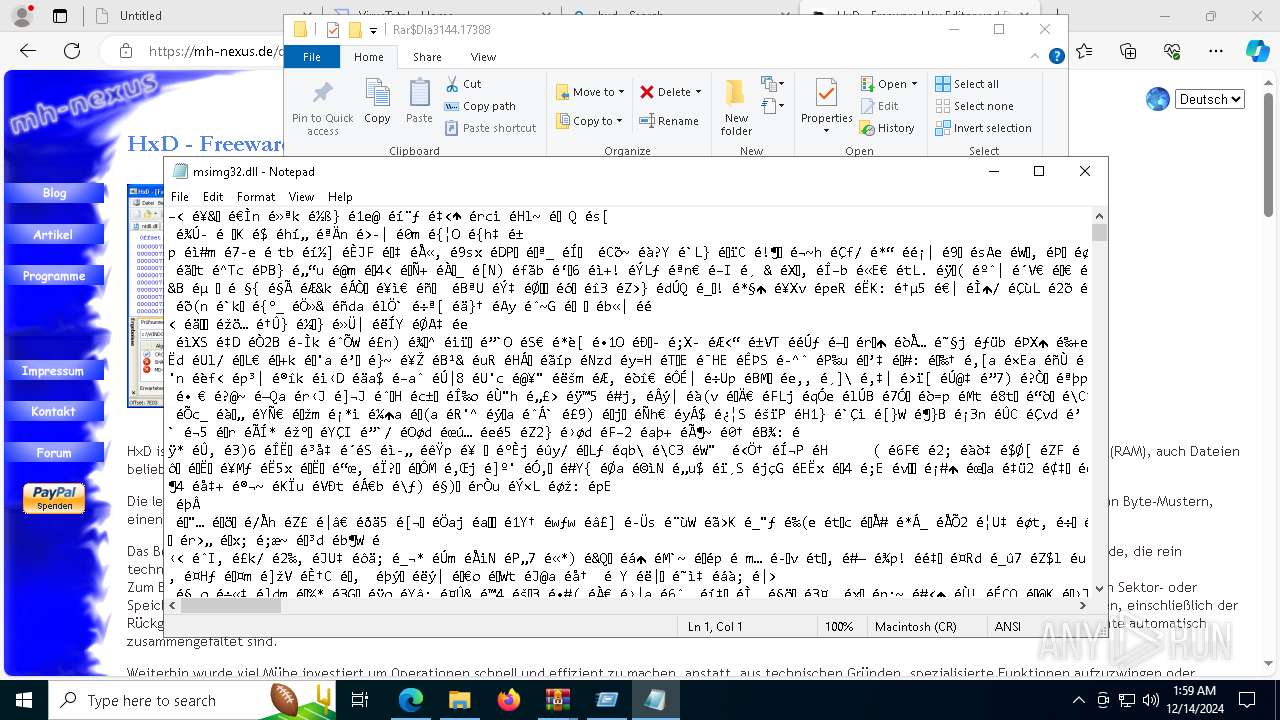
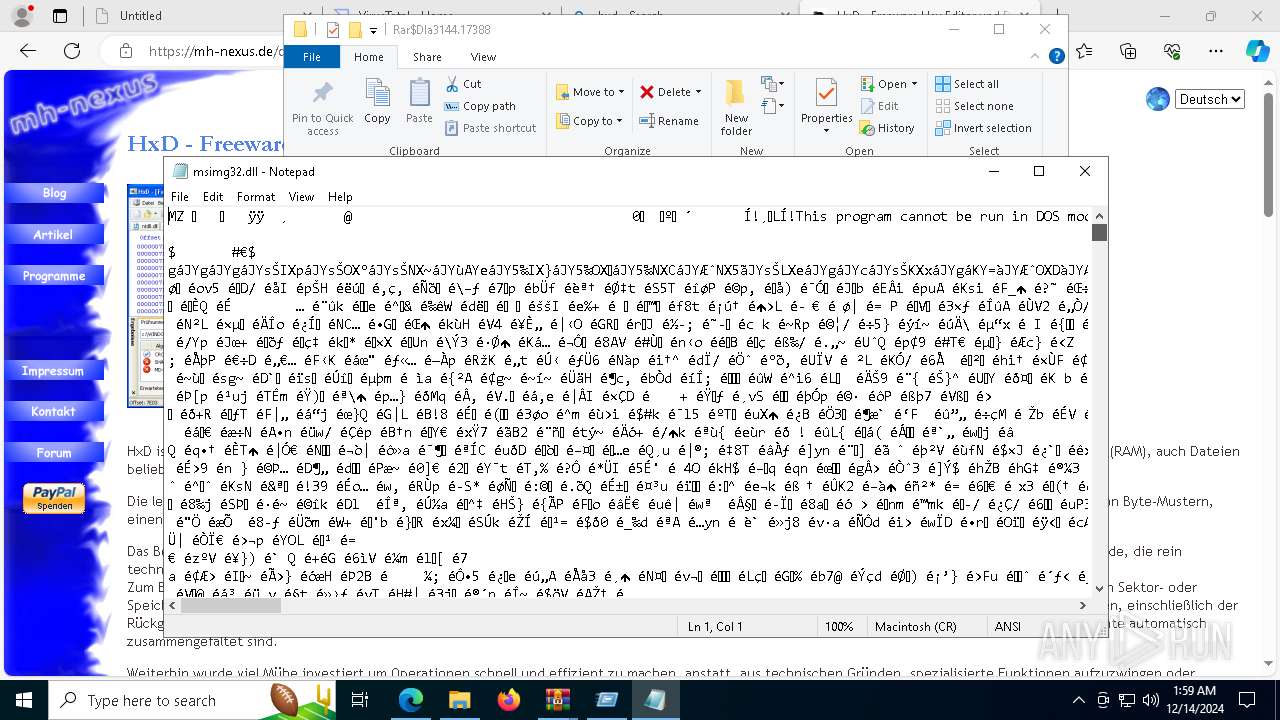
The process uses the downloaded file
- msedge.exe (PID: 880)
- msedge.exe (PID: 4052)
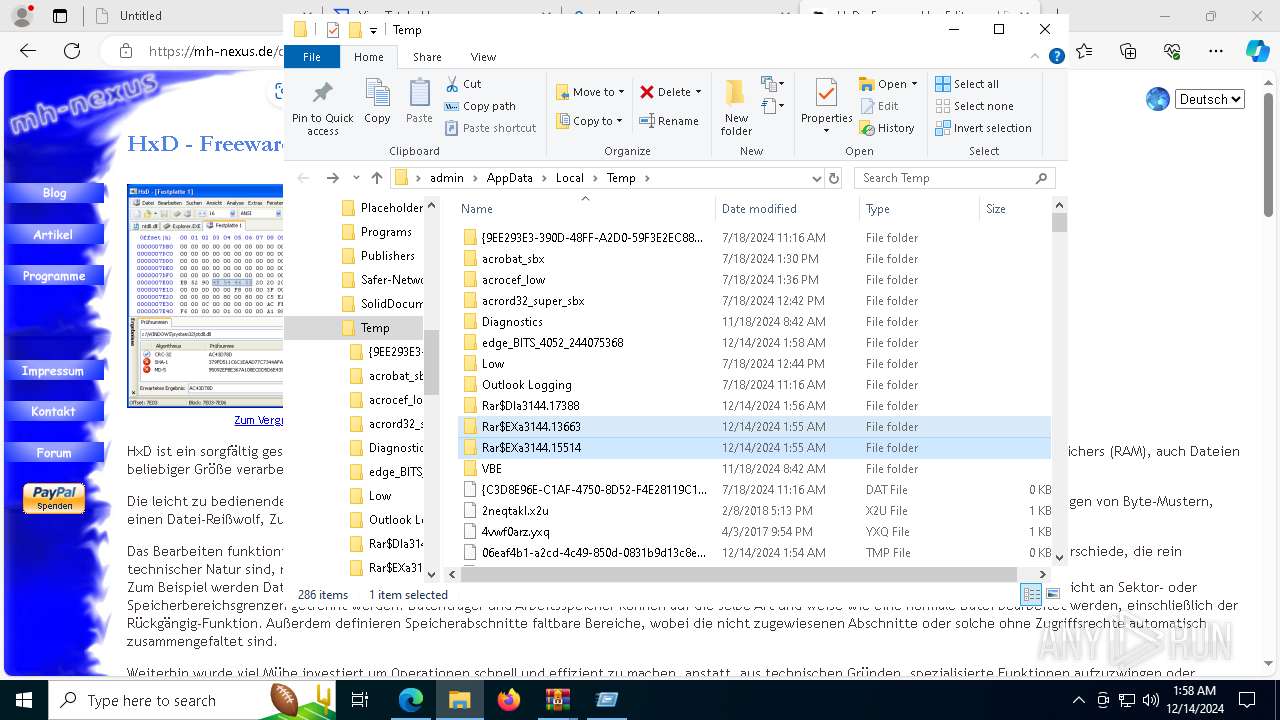
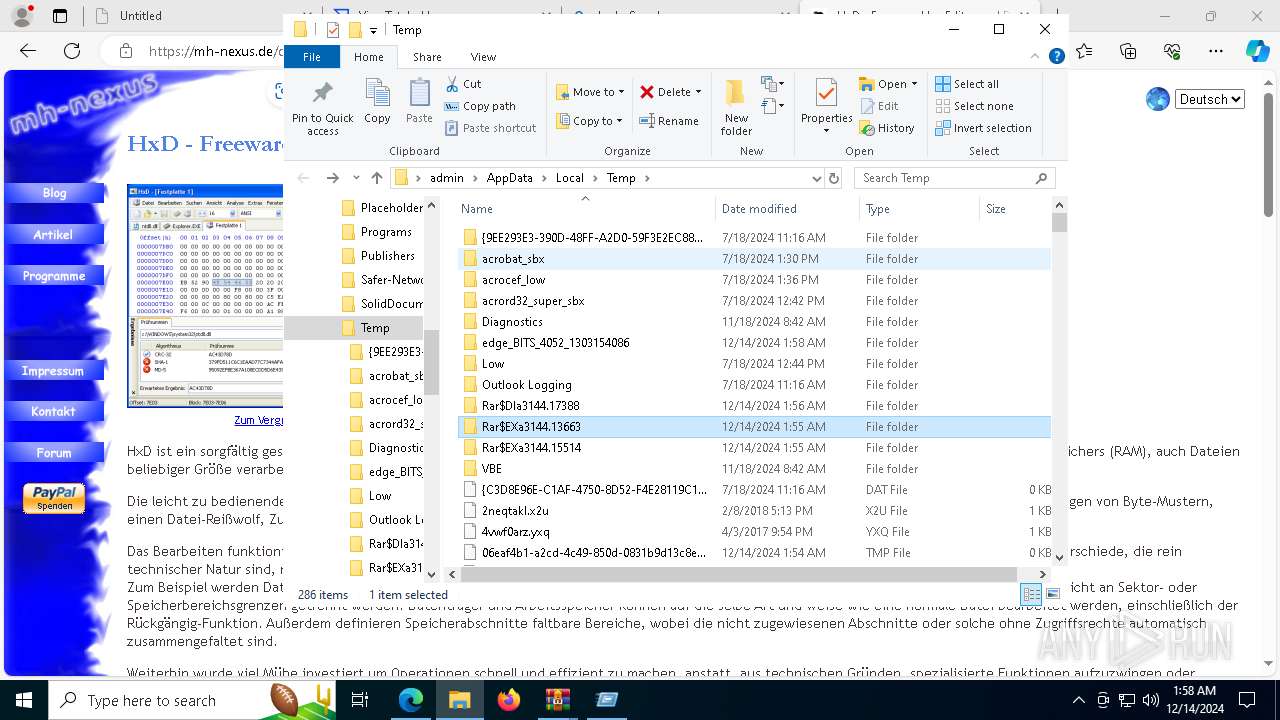
- WinRAR.exe (PID: 3144)
- OpenWith.exe (PID: 6092)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4052)
- OpenWith.exe (PID: 6092)
Application launched itself
- msedge.exe (PID: 4052)
The sample compiled with english language support
- WinRAR.exe (PID: 3144)
- msedge.exe (PID: 5592)
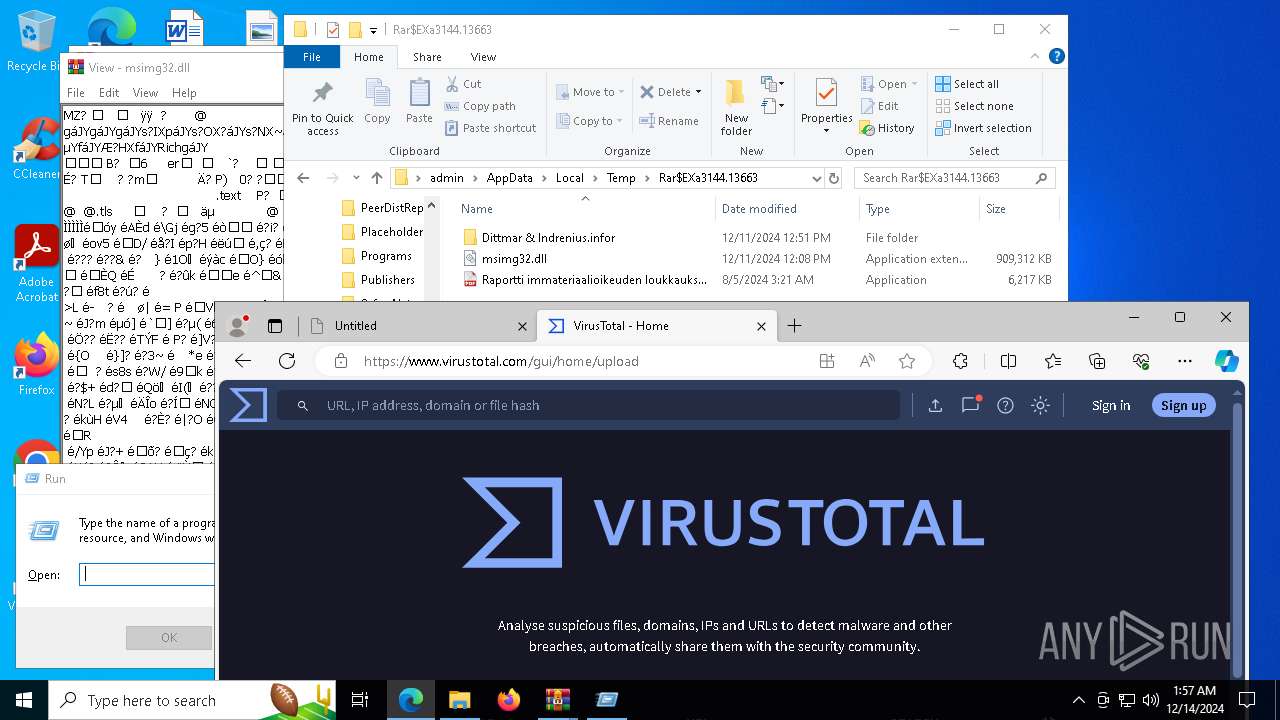
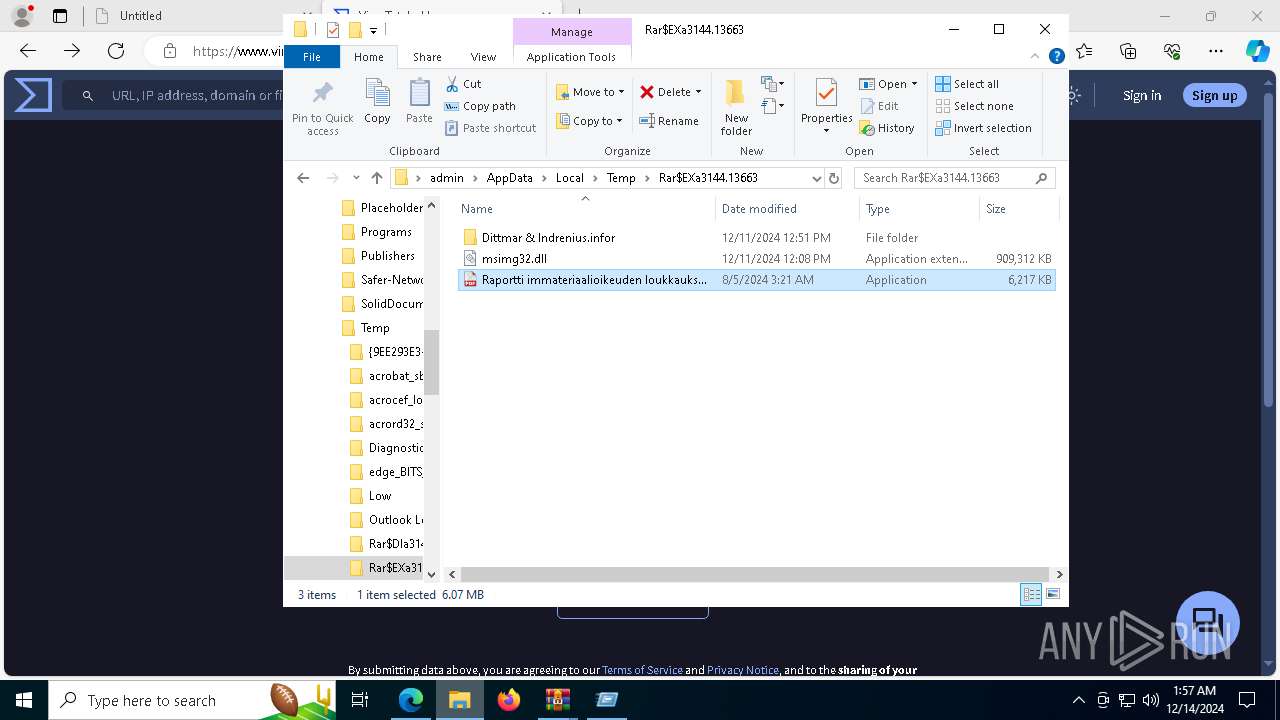
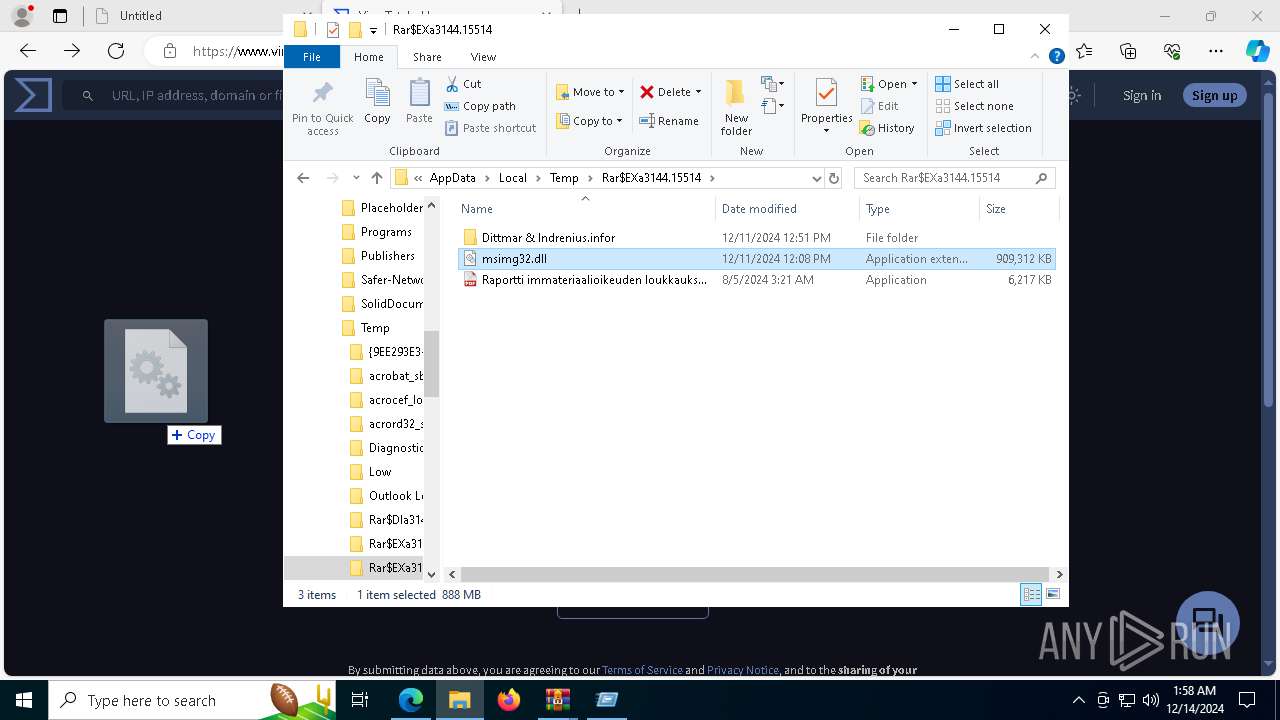
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3144)
- msedge.exe (PID: 5592)
Manual execution by a user
- svchost.exe (PID: 4504)
- svchost.exe (PID: 5496)
- svchost.exe (PID: 3848)
- svchost.exe (PID: 7188)
Drops encrypted VBS script (Microsoft Script Encoder)
- svchost.exe (PID: 4504)
- svchost.exe (PID: 7188)
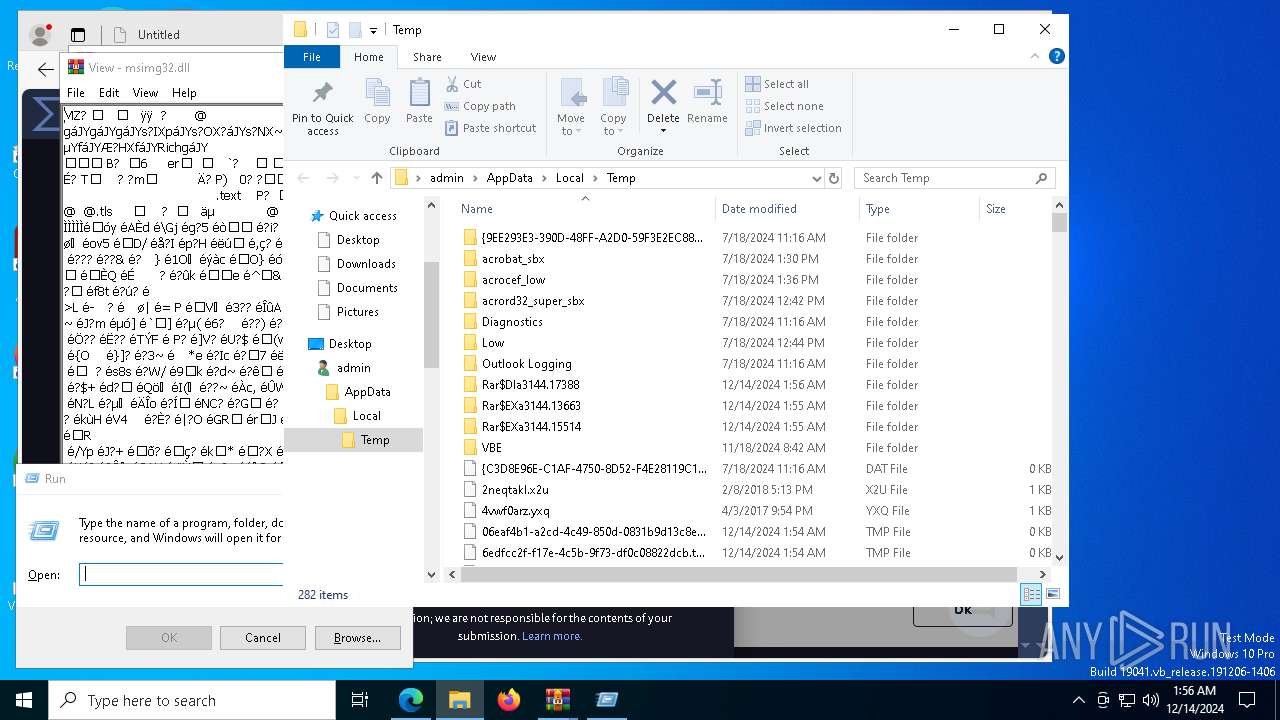
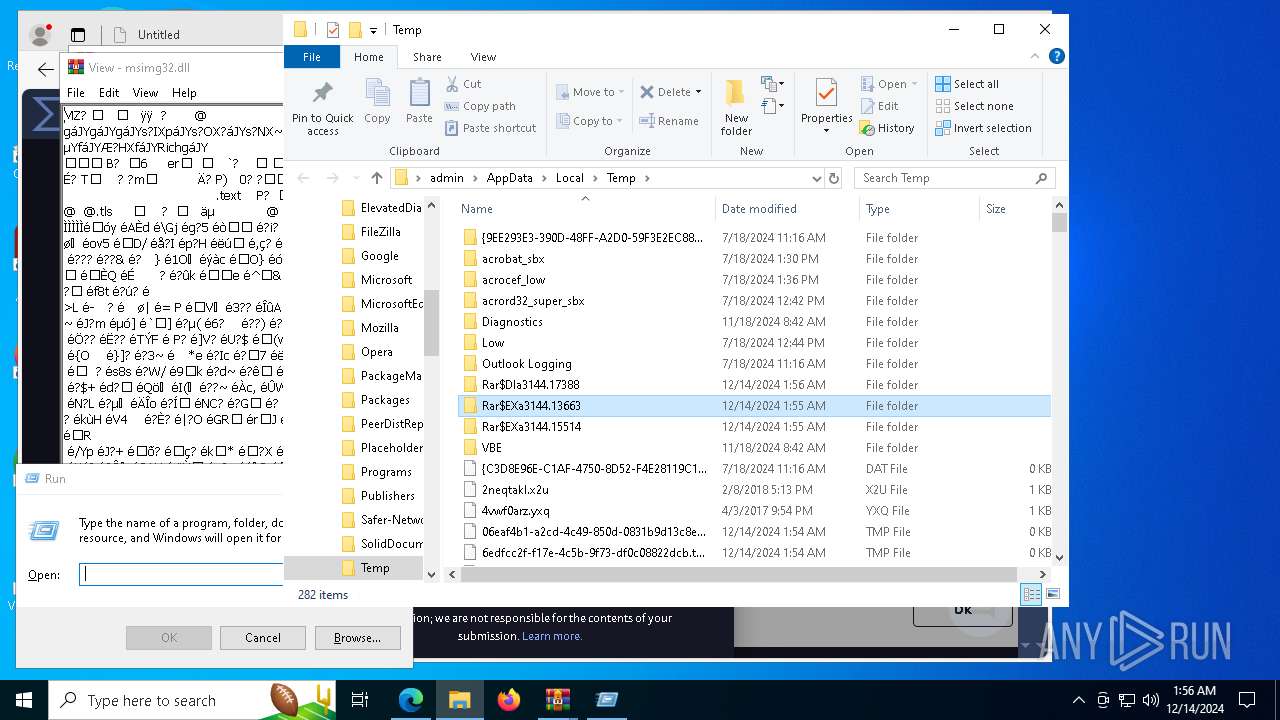
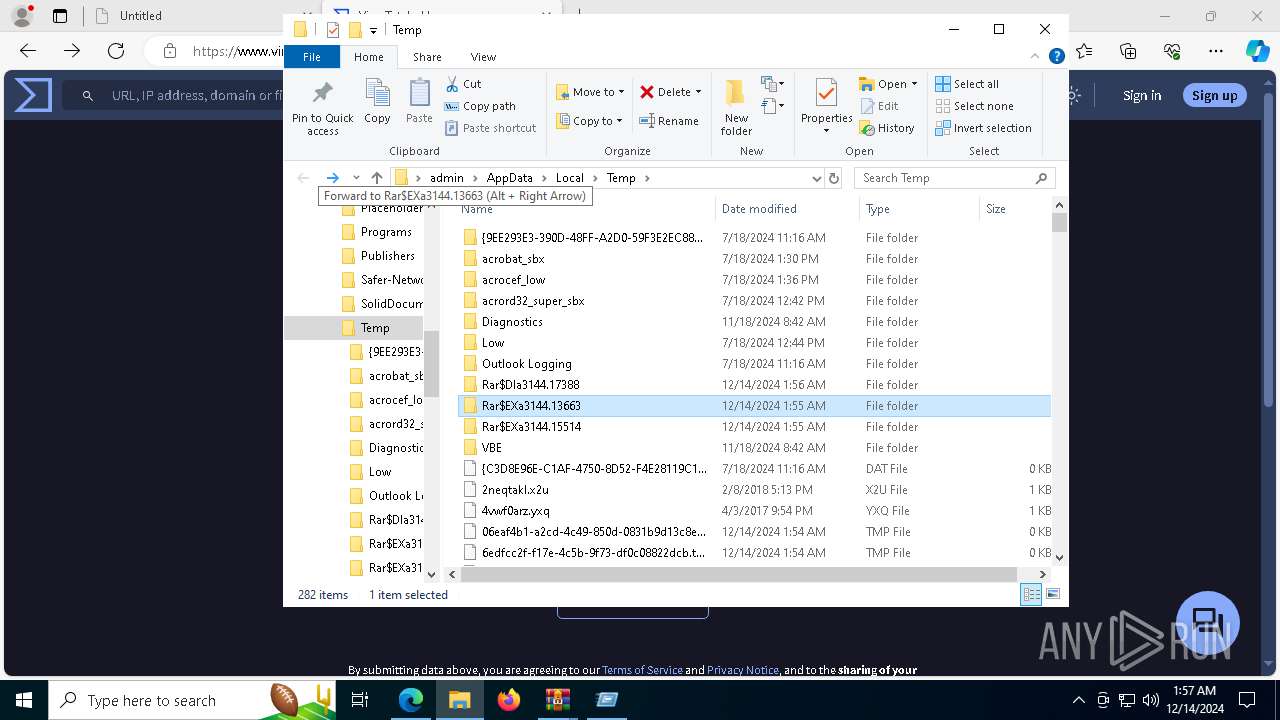
Create files in a temporary directory
- svchost.exe (PID: 4504)
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- svchost.exe (PID: 7188)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
Sends debugging messages
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
- dllhost.exe (PID: 8096)
- dllhost.exe (PID: 2956)
Reads the machine GUID from the registry
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- setup_wm.exe (PID: 7296)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
- SearchApp.exe (PID: 5064)
Process checks computer location settings
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
- SearchApp.exe (PID: 5064)
Checks proxy server information
- chrome.exe (PID: 7084)
- msedge.exe (PID: 7332)
- chrome.exe (PID: 7528)
- msedge.exe (PID: 8088)
Process checks whether UAC notifications are on
- msedge.exe (PID: 7332)
- msedge.exe (PID: 8088)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
Reads security settings of Internet Explorer
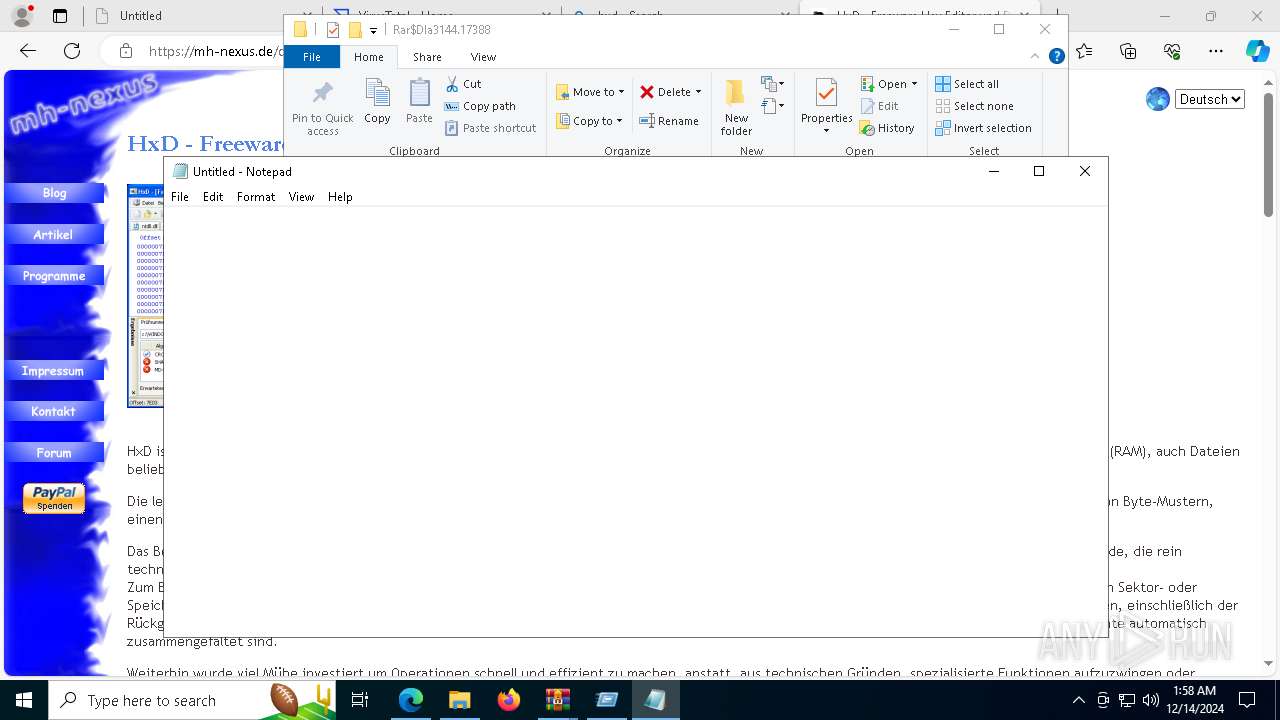
- notepad.exe (PID: 7332)
- OpenWith.exe (PID: 6092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
273
Monitored processes
137
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6908 --field-trial-handle=2408,i,3302004838488024378,14902039590486030337,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6344 --field-trial-handle=2408,i,3302004838488024378,14902039590486030337,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5144 --field-trial-handle=2404,i,9379289357220547293,11154739775158004589,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6360 --field-trial-handle=2408,i,3302004838488024378,14902039590486030337,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2232 --field-trial-handle=1896,i,3037192317179595796,17556527111688514894,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=3736 --field-trial-handle=2408,i,3302004838488024378,14902039590486030337,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3144.13663\Raportti immateriaalioikeuden loukkauksesta.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3144.13663\Raportti immateriaalioikeuden loukkauksesta.exe | Raportti immateriaalioikeuden loukkauksesta.exe | ||||||||||||
User: admin Company: Haihaisoft Limited Integrity Level: MEDIUM Description: Haihaisoft PDF Reader Exit code: 3221225477 Version: 1.5.7.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4568 --field-trial-handle=2404,i,9379289357220547293,11154739775158004589,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1792 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6744 -s 200 | C:\Windows\SysWOW64\WerFault.exe | — | Raportti immateriaalioikeuden loukkauksesta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8676 --field-trial-handle=2408,i,3302004838488024378,14902039590486030337,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
26 889
Read events
26 697
Write events
189
Delete events
3
Modification events
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6AEDEB82C7872F00 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4F07F482C7872F00 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EF61DEB7-80C7-4258-B8E7-C2E114137F06} | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 929 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AC0EA319-32E9-401A-8D5B-A0BA8FE32CE1} | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D00000042400D1FCB4DDB01 | |||
Executable files
26
Suspicious files
1 445
Text files
563
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1376f8.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1376f8.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1376f8.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1376f8.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1376f8.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
309
DNS requests
306
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7012 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4264 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734210175&P2=404&P3=2&P4=gz5R3d77EkwHug%2f%2b63JuppWnvlnxcrdlpYK10nTO%2bR9ES%2bunUE30DBJJj%2bO%2fNKuq%2bNhFCbS1eOIzKc2sQKIxrg%3d%3d | unknown | — | — | whitelisted |
4264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734210175&P2=404&P3=2&P4=gz5R3d77EkwHug%2f%2b63JuppWnvlnxcrdlpYK10nTO%2bR9ES%2bunUE30DBJJj%2bO%2fNKuq%2bNhFCbS1eOIzKc2sQKIxrg%3d%3d | unknown | — | — | whitelisted |
4264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734210175&P2=404&P3=2&P4=gz5R3d77EkwHug%2f%2b63JuppWnvlnxcrdlpYK10nTO%2bR9ES%2bunUE30DBJJj%2bO%2fNKuq%2bNhFCbS1eOIzKc2sQKIxrg%3d%3d | unknown | — | — | whitelisted |
4264 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1734210175&P2=404&P3=2&P4=gz5R3d77EkwHug%2f%2b63JuppWnvlnxcrdlpYK10nTO%2bR9ES%2bunUE30DBJJj%2bO%2fNKuq%2bNhFCbS1eOIzKc2sQKIxrg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3836 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6352 | msedge.exe | 104.20.7.133:443 | t.ly | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
t.ly |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6352 | msedge.exe | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
6352 | msedge.exe | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
4504 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
4504 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
7188 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
7188 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
12 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr1268.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr22E4.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr58A9.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr676F.tmp directory exists )
|
dllhost.exe | ba 61 fe af b5 22 de 41
|
dllhost.exe | [service_reconnect_interval] set timer
|
dllhost.exe | [backend_tunnel_on_connect] set timer
|
dllhost.exe | ba 61 fe af b5 22 de 41
|
dllhost.exe | [service_reconnect_interval] set timer
|
dllhost.exe | [backend_tunnel_on_connect] set timer
|