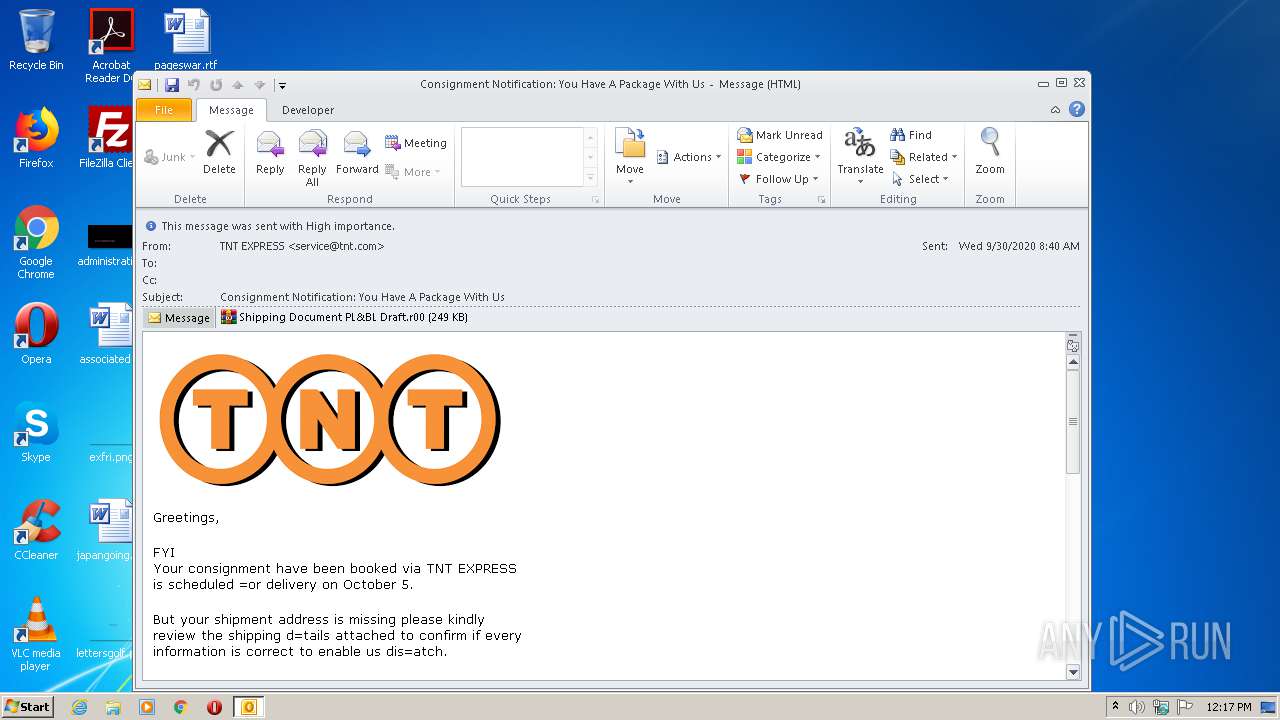
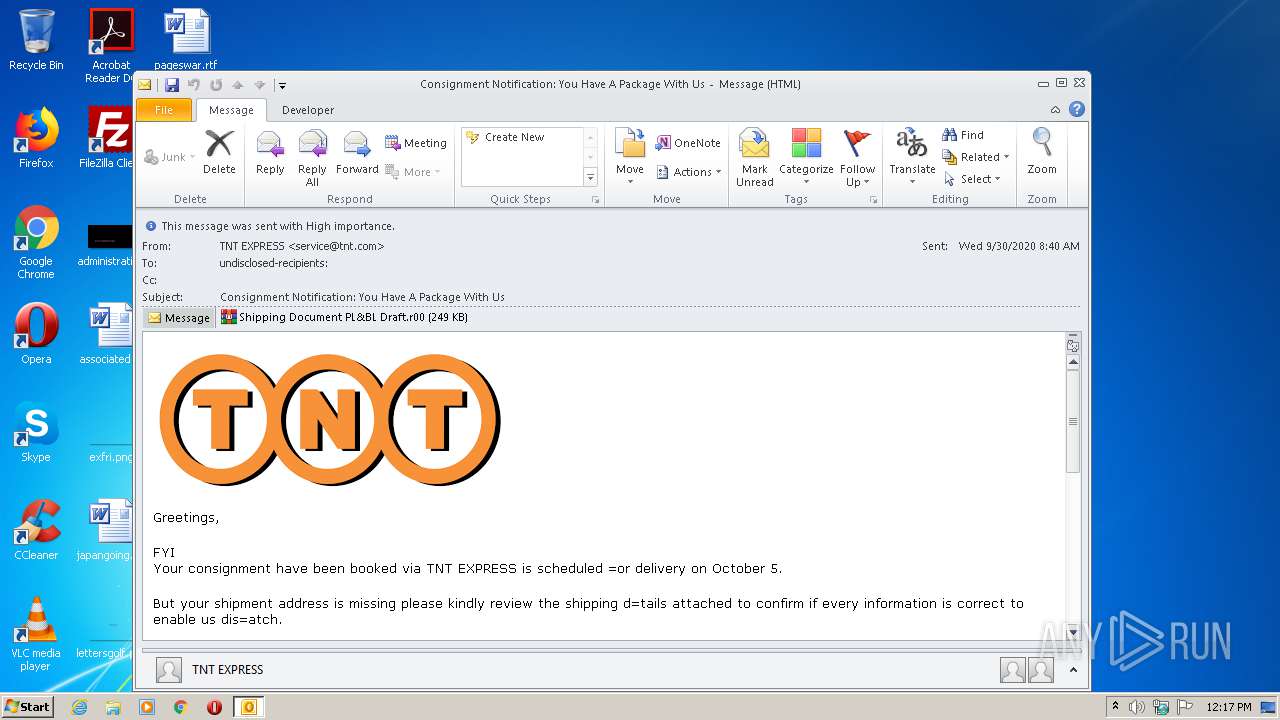
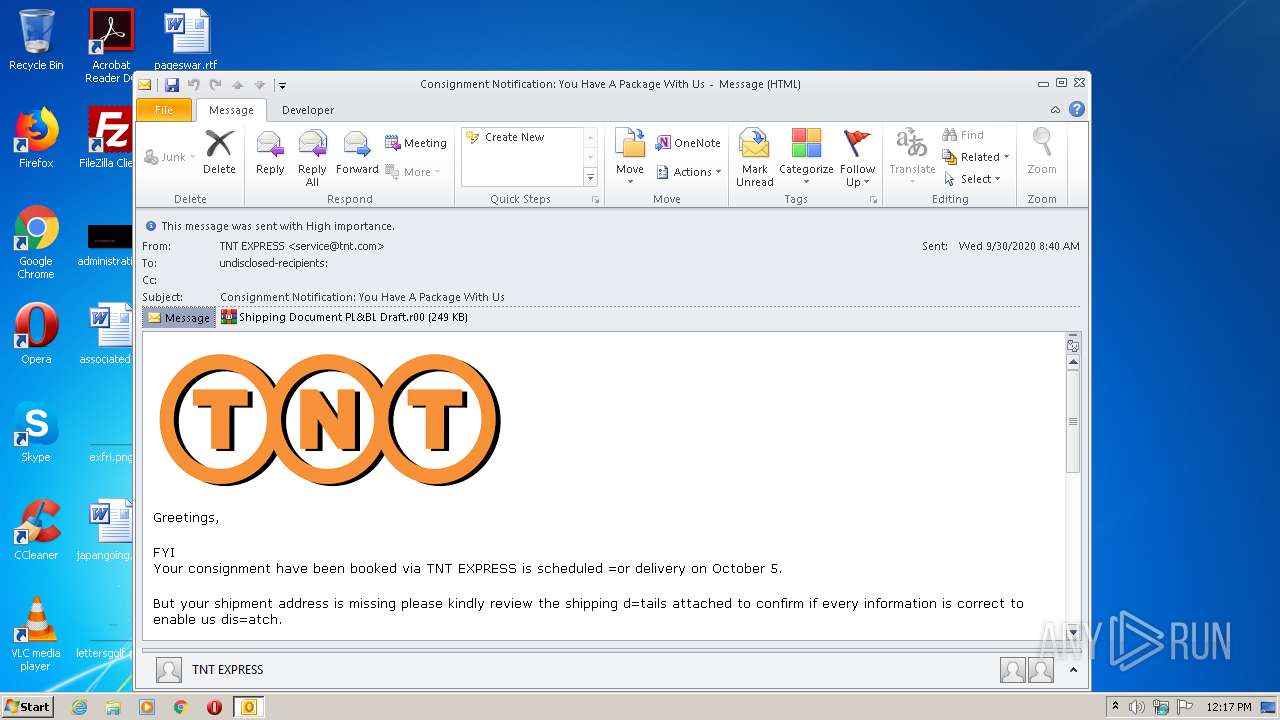
| File name: | Consignment Notification_ You Have A Package With Us.eml |
| Full analysis: | https://app.any.run/tasks/3b4fa571-0f7c-4640-9f69-b6d49a987dfd |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 30, 2020, 11:17:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text |
| MD5: | 0ECB4FF6AC30A41AD531B39B16DB1453 |
| SHA1: | A3E2C06222253D7EB1061FB868742C72F5B7F265 |
| SHA256: | 612870E0CF6B573BD69DE0B4DB7A4AF992211832F03AEC0B32418BB9516C0BCD |
| SSDEEP: | 6144:QSvbzQoqfBPgpK6uwiQGRfH22xxCXxaeB6HBxxL/+jDkcecYjoVCTbrn1jwJo:ZQnfWTiJ1W+x2gh+wLcYjhTbrd |
MALICIOUS
Application was dropped or rewritten from another process
- Shipping Document PL&BL Draft.exe (PID: 3204)
- Shipping Document PL&BL Draft.exe (PID: 2568)
AGENTTESLA was detected
- Shipping Document PL&BL Draft.exe (PID: 2568)
Actions looks like stealing of personal data
- Shipping Document PL&BL Draft.exe (PID: 2568)
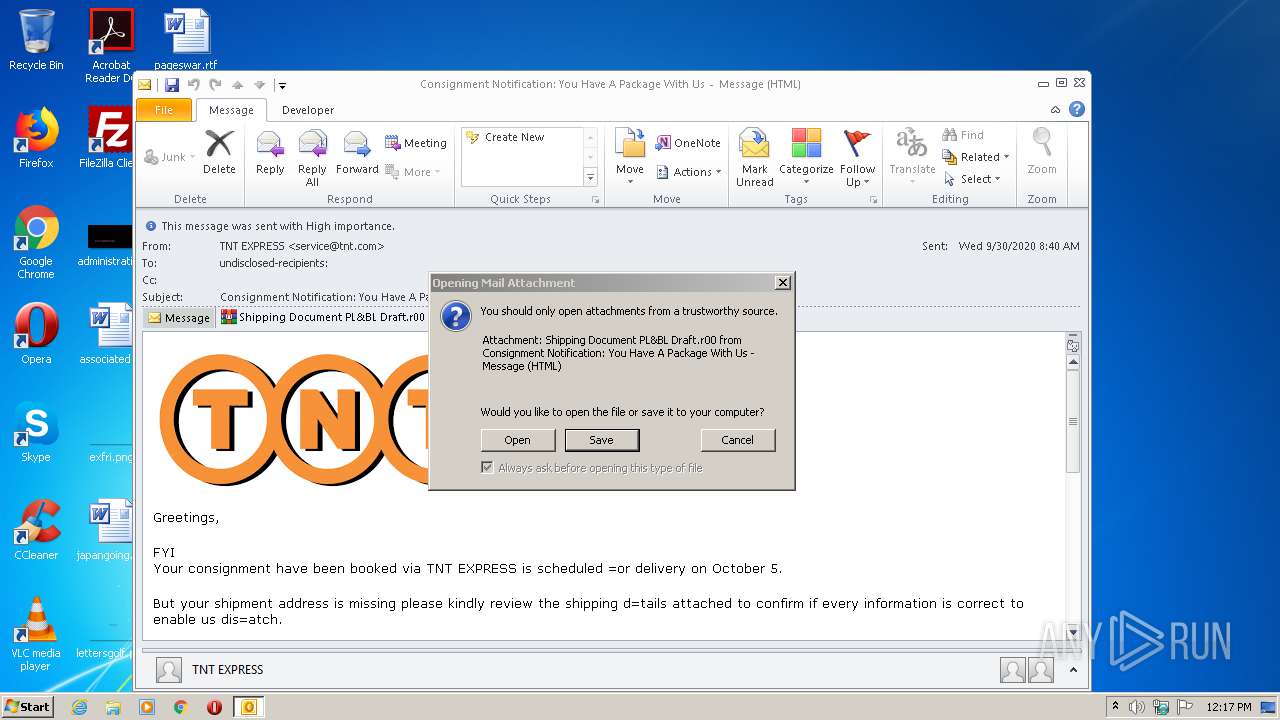
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2876)
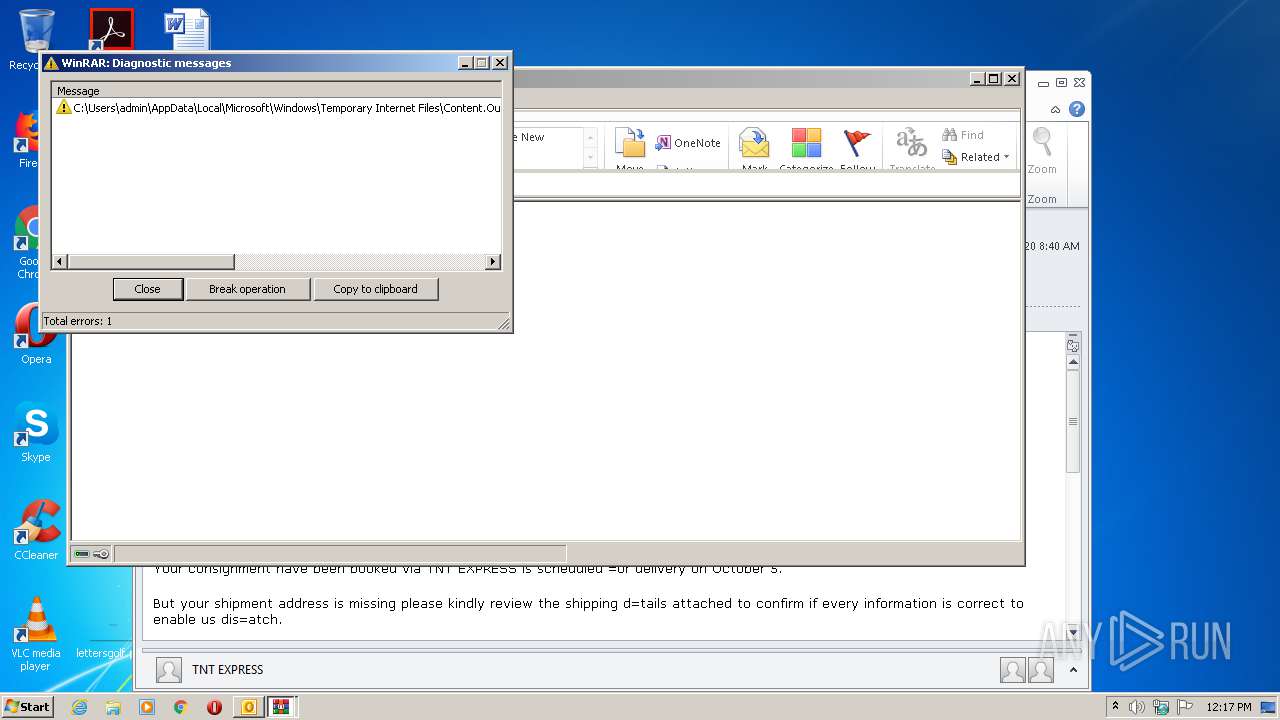
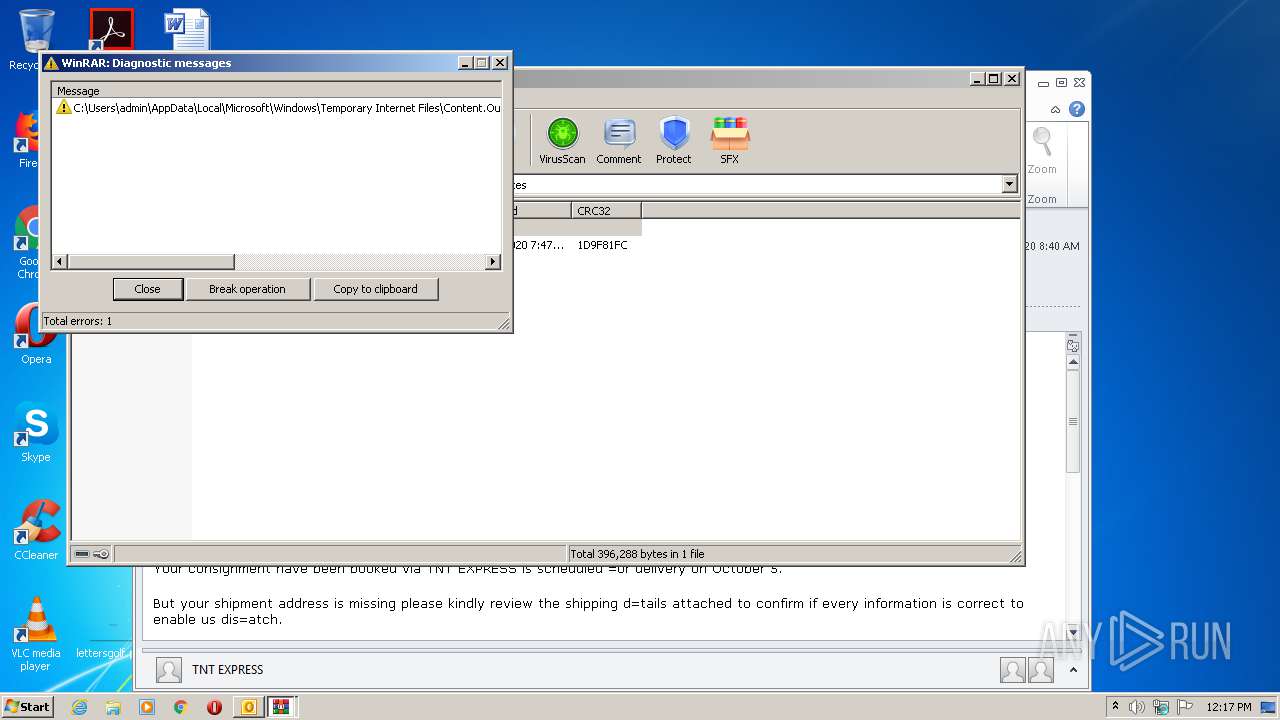
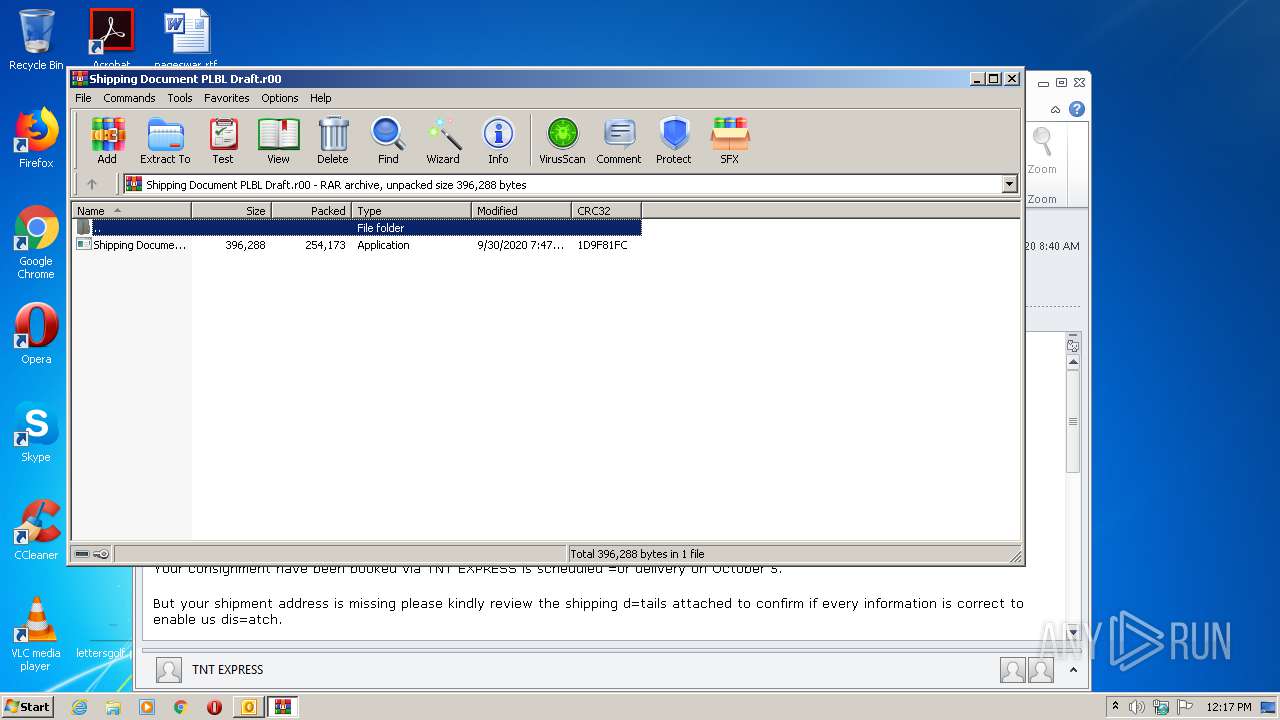
Executable content was dropped or overwritten
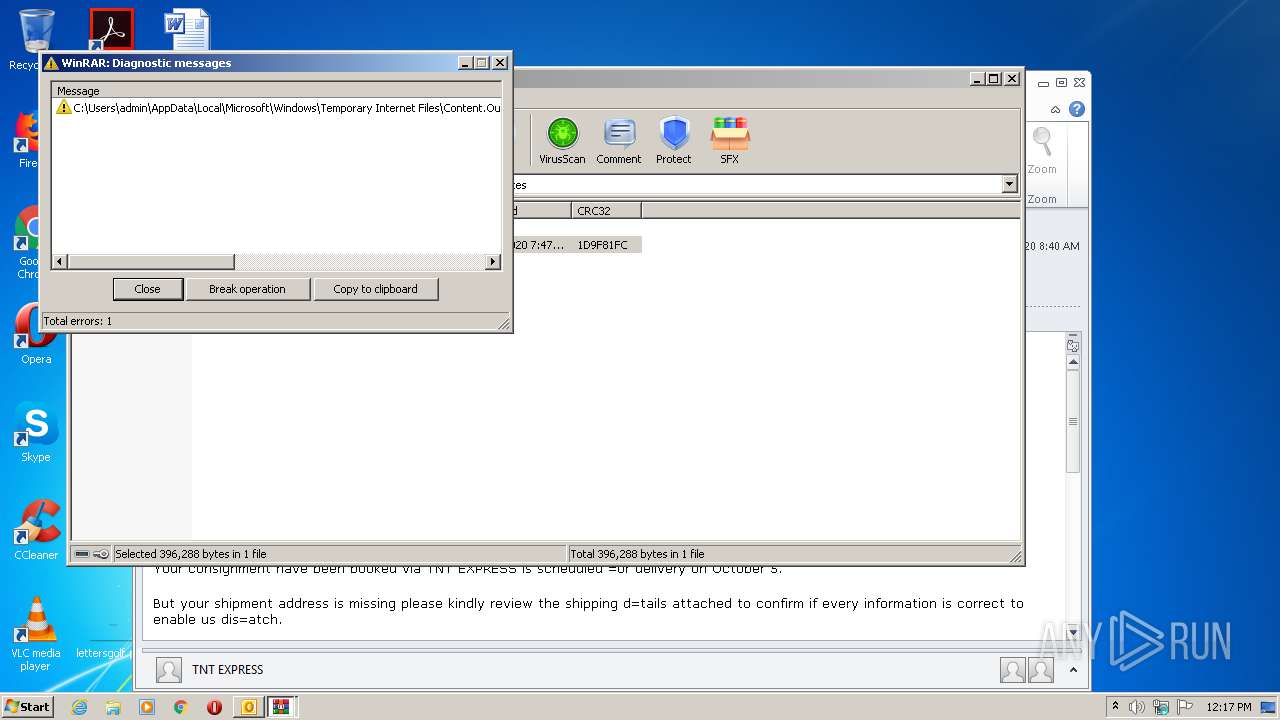
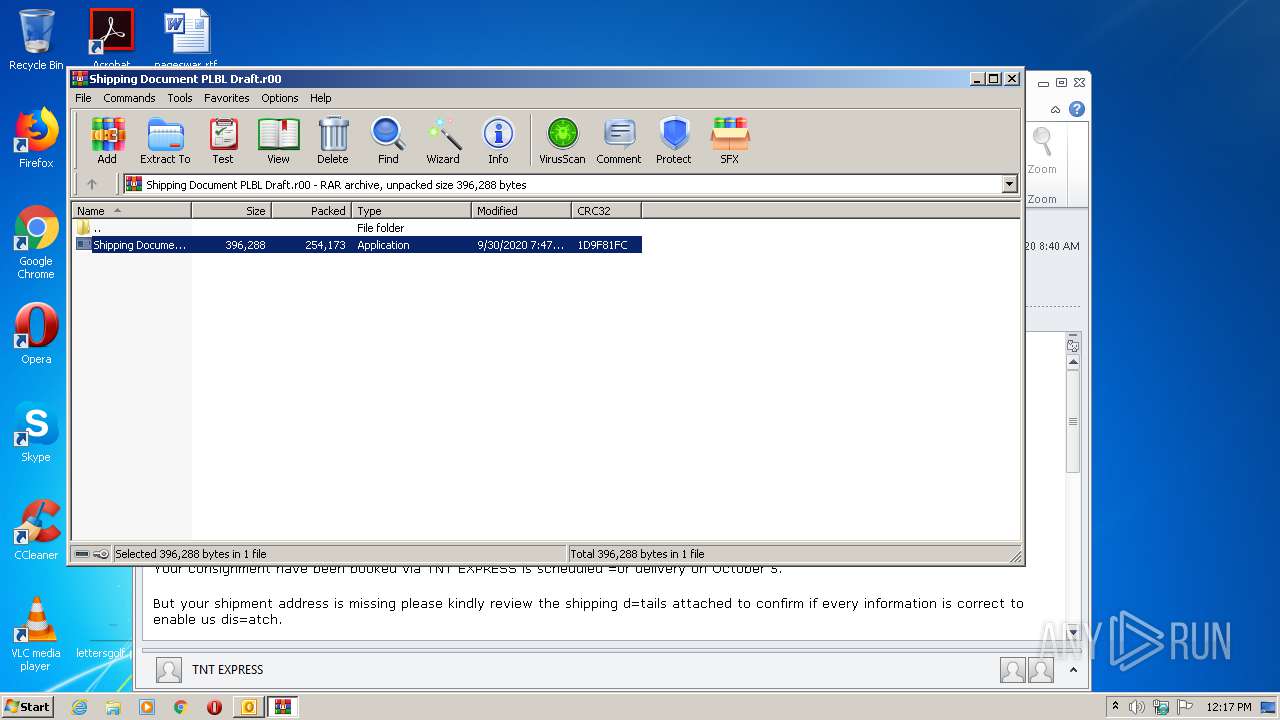
- WinRAR.exe (PID: 908)
- Shipping Document PL&BL Draft.exe (PID: 3204)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2876)
Application launched itself
- Shipping Document PL&BL Draft.exe (PID: 3204)
Reads Environment values
- Shipping Document PL&BL Draft.exe (PID: 2568)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
41
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AJGJN1LC\Shipping Document PLBL Draft.r00" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa908.084\Shipping Document PL&BL Draft.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa908.084\Shipping Document PL&BL Draft.exe | Shipping Document PL&BL Draft.exe | ||||||||||||
User: admin Company: f}51p%r#67y/:8 Integrity Level: MEDIUM Description: 4d?~6lq)23z, Exit code: 0 Version: 6.8.11.14 Modules
| |||||||||||||||
| 2876 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Consignment Notification_ You Have A Package With Us.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa908.084\Shipping Document PL&BL Draft.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa908.084\Shipping Document PL&BL Draft.exe | WinRAR.exe | ||||||||||||
User: admin Company: f}51p%r#67y/:8 Integrity Level: MEDIUM Description: 4d?~6lq)23z, Exit code: 0 Version: 6.8.11.14 Modules
| |||||||||||||||
Total events
2 356
Read events
1 763
Write events
574
Delete events
19
Modification events
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
29
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR7A99.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp7CCC.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AJGJN1LC\Shipping Document PLBL Draft (2).r00\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 908 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa908.084\Shipping Document PL&BL Draft.exe | executable | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AJGJN1LC\Shipping Document PLBL Draft.r00 | compressed | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AJGJN1LC\Shipping Document PLBL Draft (2).r00 | compressed | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6B5113F5.dat | image | |
MD5:— | SHA256:— | |||
| 2876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B3FEA172.dat | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2876 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2568 | Shipping Document PL&BL Draft.exe | 85.187.154.178:587 | mail.flood-protection.org | A2 Hosting, Inc. | US | malicious |
2568 | Shipping Document PL&BL Draft.exe | 54.225.66.103:443 | api.ipify.org | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
mail.flood-protection.org |
| malicious |
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2568 | Shipping Document PL&BL Draft.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2568 | Shipping Document PL&BL Draft.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
2568 | Shipping Document PL&BL Draft.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2568 | Shipping Document PL&BL Draft.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report