| File name: | Dokumenty 31.03.2020.exe |
| Full analysis: | https://app.any.run/tasks/a985a652-c163-4526-8ac5-61951b0dd338 |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
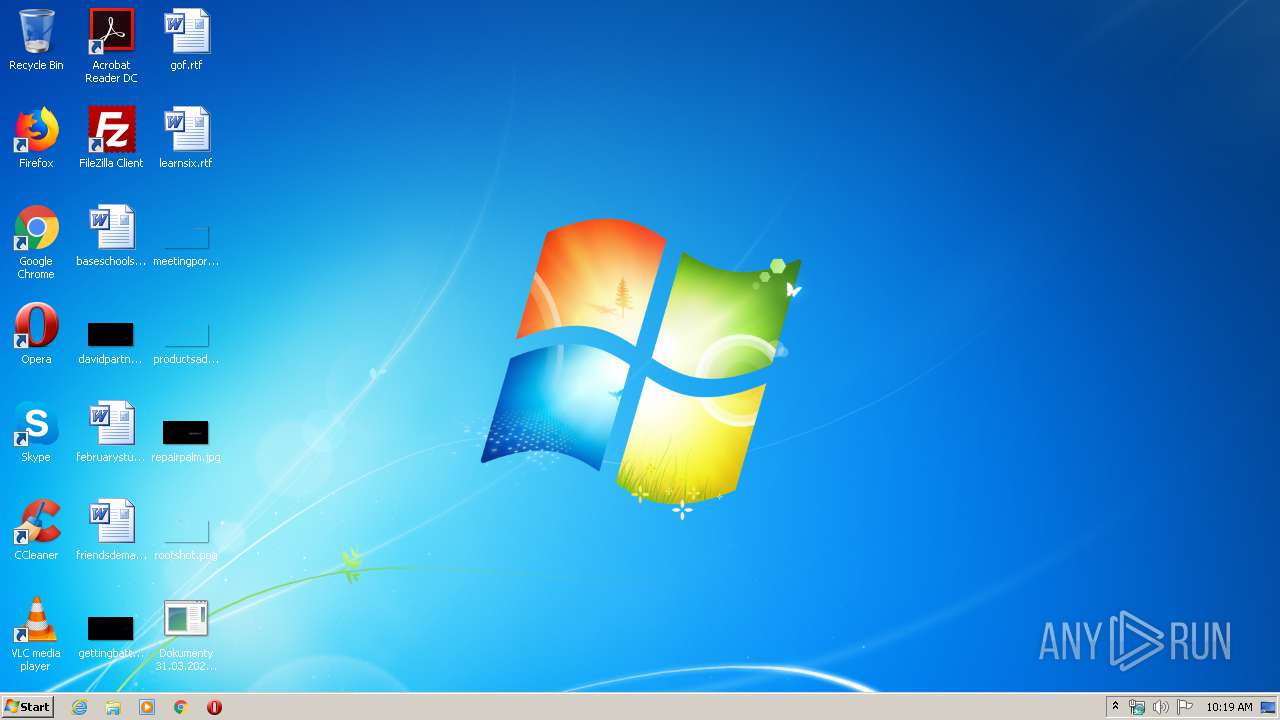
| Analysis date: | March 31, 2020, 09:19:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C2758444569BD312F5A47EB4EBAAF7CF |
| SHA1: | 9FF4C4DF05E20DB3D81E73025BBE0CAD310E51C7 |
| SHA256: | 60BA39104CE41BAE1AB530032F8BE0491435BD2936A4869F499F84DC9E7CB685 |
| SSDEEP: | 1536:J+F2H9pW+pyQWJSNqaw+JDgWZNxzOIKqll/M+k:J1dxgRJSNfw8kWZKZqX/x |
MALICIOUS
Detected Pony/Fareit Trojan
- Dokumenty 31.03.2020.exe (PID: 3128)
PONY was detected
- Dokumenty 31.03.2020.exe (PID: 3128)
Connects to CnC server
- Dokumenty 31.03.2020.exe (PID: 3128)
Actions looks like stealing of personal data
- Dokumenty 31.03.2020.exe (PID: 3128)
Changes settings of System certificates
- Dokumenty 31.03.2020.exe (PID: 3128)
SUSPICIOUS
Reads Internet Cache Settings
- Dokumenty 31.03.2020.exe (PID: 3128)
Creates files in the user directory
- Dokumenty 31.03.2020.exe (PID: 3128)
Starts CMD.EXE for commands execution
- Dokumenty 31.03.2020.exe (PID: 3128)
Searches for installed software
- Dokumenty 31.03.2020.exe (PID: 3128)
Connects to server without host name
- Dokumenty 31.03.2020.exe (PID: 3128)
Starts CMD.EXE for self-deleting
- Dokumenty 31.03.2020.exe (PID: 3128)
Adds / modifies Windows certificates
- Dokumenty 31.03.2020.exe (PID: 3128)
INFO
Reads settings of System Certificates
- Dokumenty 31.03.2020.exe (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:04 06:37:30+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 13.1 |
| CodeSize: | 6656 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1050 |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Aug-2018 04:37:30 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Aug-2018 04:37:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00001956 | 0x00001A00 | IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.39125 |
.kdata | 0x00003000 | 0x00013C40 | 0x00013E00 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.37268 |
.rsrc | 0x00017000 | 0x00001EE0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.24201 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 512 | UNKNOWN | English - United States | RT_MESSAGETABLE |
Imports
kernel32.dll |
nddeapi.dll |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3128 | "C:\Users\admin\Desktop\Dokumenty 31.03.2020.exe" dfsr | C:\Users\admin\Desktop\Dokumenty 31.03.2020.exe | Dokumenty 31.03.2020.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3224 | cmd.exe /c ping 127.0.0.1 & del /F /Q "C:\Users\admin\Desktop\Dokumenty 31.03.2020.exe" | C:\Windows\system32\cmd.exe | — | Dokumenty 31.03.2020.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3536 | ping 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\Desktop\Dokumenty 31.03.2020.exe" | C:\Users\admin\Desktop\Dokumenty 31.03.2020.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
3 654
Read events
102
Write events
2 367
Delete events
1 185
Modification events
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\CDD4EEAE6000AC7F40C3802C171E30148030C072 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000391BE92883D52509155BFEAE27B9BD340170B76B030000000100000014000000CDD4EEAE6000AC7F40C3802C171E30148030C0720B000000010000004A0000004D006900630072006F0073006F0066007400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900000069000000010000000E000000300C060A2B0601040182373C030220000000010000009D0500003082059930820381A003020102021079AD16A14AA0A5AD4C7358F407132E65300D06092A864886F70D0101050500305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F72697479301E170D3031303530393233313932325A170D3231303530393233323831335A305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A0282020100F35DFA8067D45AA7A90C2C9020D035083C7584CDB707899C89DADECEC360FA91685A9E94712918767CC2E0C82576940E58FA043436E6DFAFF780BAE9580B2B93E59D05E3772291F734643C22911D5EE10990BC14FEFC755819E179B70792A3AE885908D89F07CA0358FC68296D32D7D2A8CB4BFCE10B48324FE6EBB8AD4FE45C6F139499DB95D575DBA81AB79491B4775BF5480C8F6A797D1470047D6DAF90F5DA70D847B7BF9B2F6CE705B7E11160AC7991147CC5D6A6E4E17ED5C37EE592D23C00B53682DE79E16DF3B56EF89F33C9CB527D739836DB8BA16BA295979BA3DEC24D26FF0696672506C8E7ACE4EE1233953199C835084E34CA7953D5B5BE6332594036C0A54E044D3DDB5B0733E458BFEF3F5364D842593557FD0F457C24044D9ED6387411972290CE684474926FD54B6FB086E3C73642A0D0FCC1C05AF9A361B9304771960A16B091C04295EF107F286AE32A1FB1E4CD033F777104C720FC490F1D4588A4D7CB7E88AD8E2DEC45DBC45104C92AFCEC869E9A11975BDECE5388E6E2B7FDAC95C22840DBEF0490DF813339D9B245A5238706A5558931BB062D600E41187D1F2EB597CB11EB15D524A594EF151489FD4B73FA325BFCD13300F95962700732EA2EAB402D7BCADD21671B30998F16AA23A841D1B06E119B36C4DE40749CE15865C1601E7A5B38C88FBB04267CD41640E5B66B6CAA86FD00BFCEC1350203010001A351304F300B0603551D0F0404030201C6300F0603551D130101FF040530030101FF301D0603551D0E041604140EAC826040562797E52513FC2AE10A539559E4A4301006092B06010401823715010403020100300D06092A864886F70D01010505000382020100C5114D033A60DD5D5211778FB2BB36C8B205BFB4B7A8D8209D5C1303B61C22FA061335B6C863D49A476F2657D255F104B1265FD6A95068A0BCD2B86ECCC3E9ACDF19CD78AC5974AC663436C41B3E6C384C330E30120DA326FE515300FFAF5A4E840D0F1FE46D052E4E854B8D6C336F54D264ABBF50AF7D7A39A037ED63030FFC1306CE1636D4543B951B51623AE54D17D40539929A27A85BAABDECBBBEE3208960716C56B3A513D06D0E237E9503ED683DF2D863B86B4DB6E830B5E1CA944BF7A2AA5D9930B23DA7C2516C28200124272B4B00B79D116B70BEB21082BC0C9B68D08D3B2487AA9928729D335F5990BDF5DE939E3A625A3439E288551DB906B0C1896B2DD769C319123684D0C9A0DAFF2F6978B2E57ADAEBD70CC0F7BD6317B8391338A2365B7BF285566A1D6462C138E2AABF5166A294F5129C6622106BF2B730922DF229F03D3B144368A2F19C2937CBCE3820256D7C67F37E24122403088147ECA59E97F518D7CFBBD5EF7696EFFDCEDB569D95A042F99758E1D73122D35F59E63E6E2200EA4384B625DBD9F3085668C0646B1D7CECB693A262576E2ED8E7588FC4314926DDDE293587F53071705B143C69BD89127DEB2EA3FED87F9E825A520A2BC1432BD930889FC810FB898DE6A18575337E6C9EDB7313646269A52F7DCA966D9FF8044D30923D6E211421C93DE0C3FD8A6B9D4AFDD1A19D9943773FB0DA | |||
| (PID) Process: | (3128) Dokumenty 31.03.2020.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\CDD4EEAE6000AC7F40C3802C171E30148030C072 |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3128 | Dokumenty 31.03.2020.exe | C:\Users\admin\AppData\Local\Temp\917A.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | Dokumenty 31.03.2020.exe | C:\Users\admin\AppData\Local\Temp\917B.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | Dokumenty 31.03.2020.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\A2FOJUQP.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3128 | Dokumenty 31.03.2020.exe | GET | 200 | 195.123.224.44:80 | http://195.123.224.44/viewtopic.php?f576=0?f948=61646d696e?f783=555345522d5043 | BG | binary | 97.0 Kb | malicious |
3128 | Dokumenty 31.03.2020.exe | POST | — | 195.123.224.44:80 | http://195.123.224.44/p/z05857687.php | BG | — | — | malicious |
3128 | Dokumenty 31.03.2020.exe | POST | — | 195.123.224.44:80 | http://195.123.224.44/p/z05857687.php | BG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3128 | Dokumenty 31.03.2020.exe | 195.123.224.44:80 | — | ITL Company | BG | malicious |
3128 | Dokumenty 31.03.2020.exe | 104.16.55.3:443 | blockchain.info | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blockchain.info |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3128 | Dokumenty 31.03.2020.exe | A Network Trojan was detected | MALWARE [PTsecurity] RTM.Payload.xor |
3128 | Dokumenty 31.03.2020.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3128 | Dokumenty 31.03.2020.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |