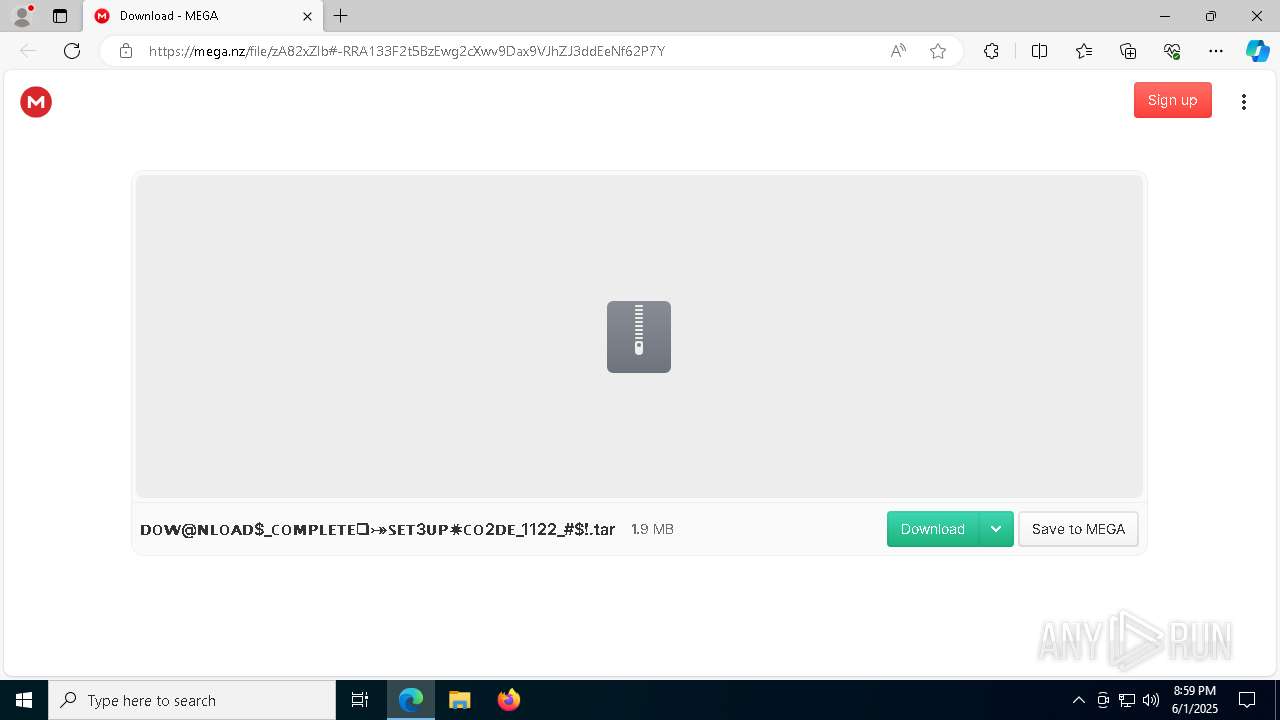
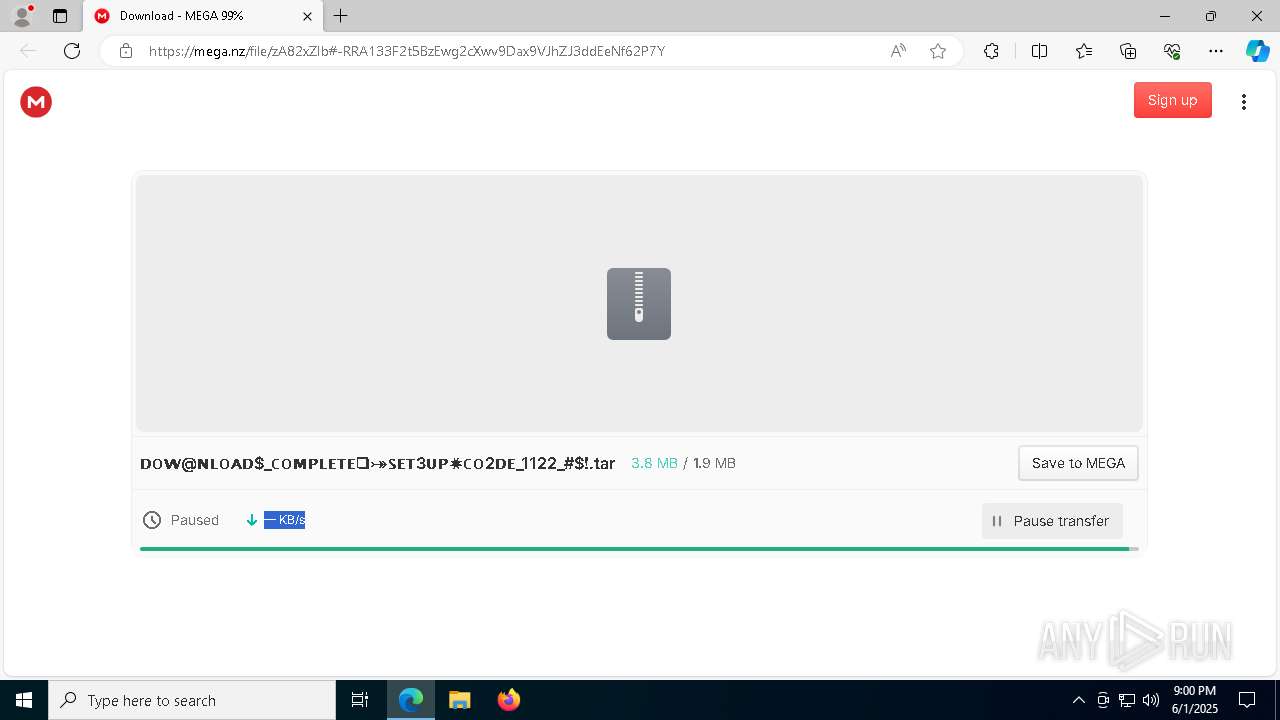
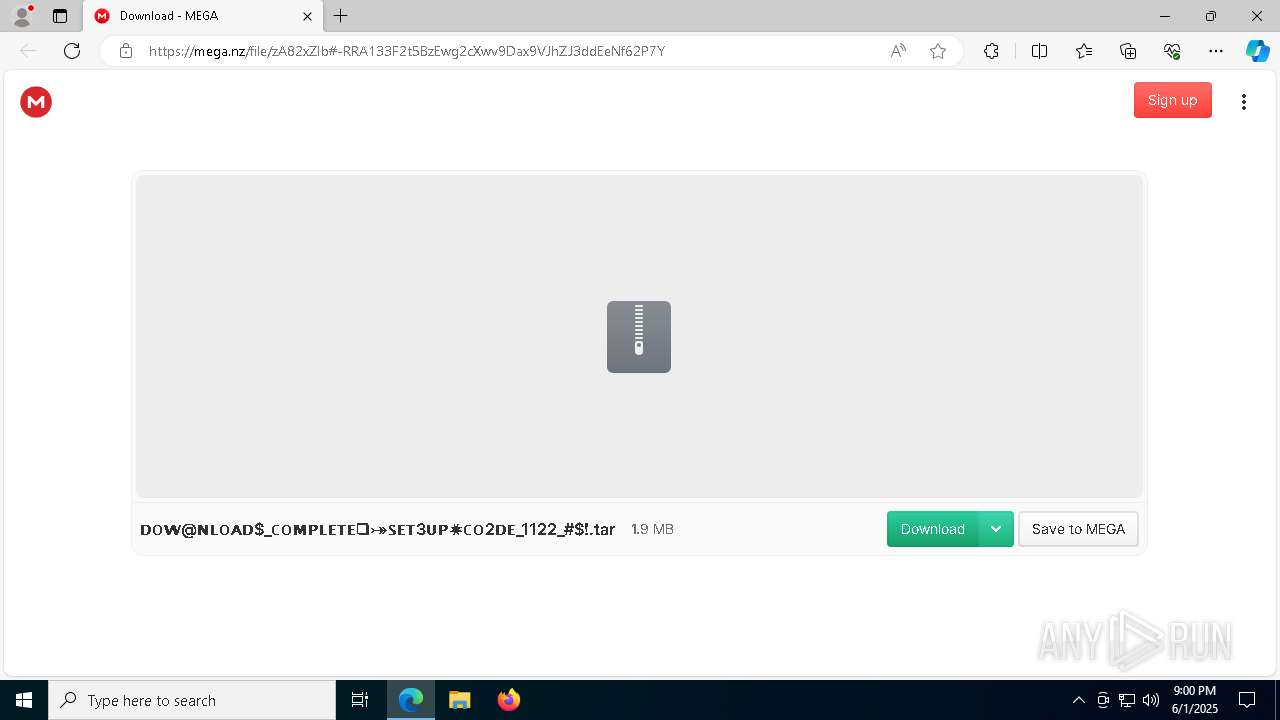
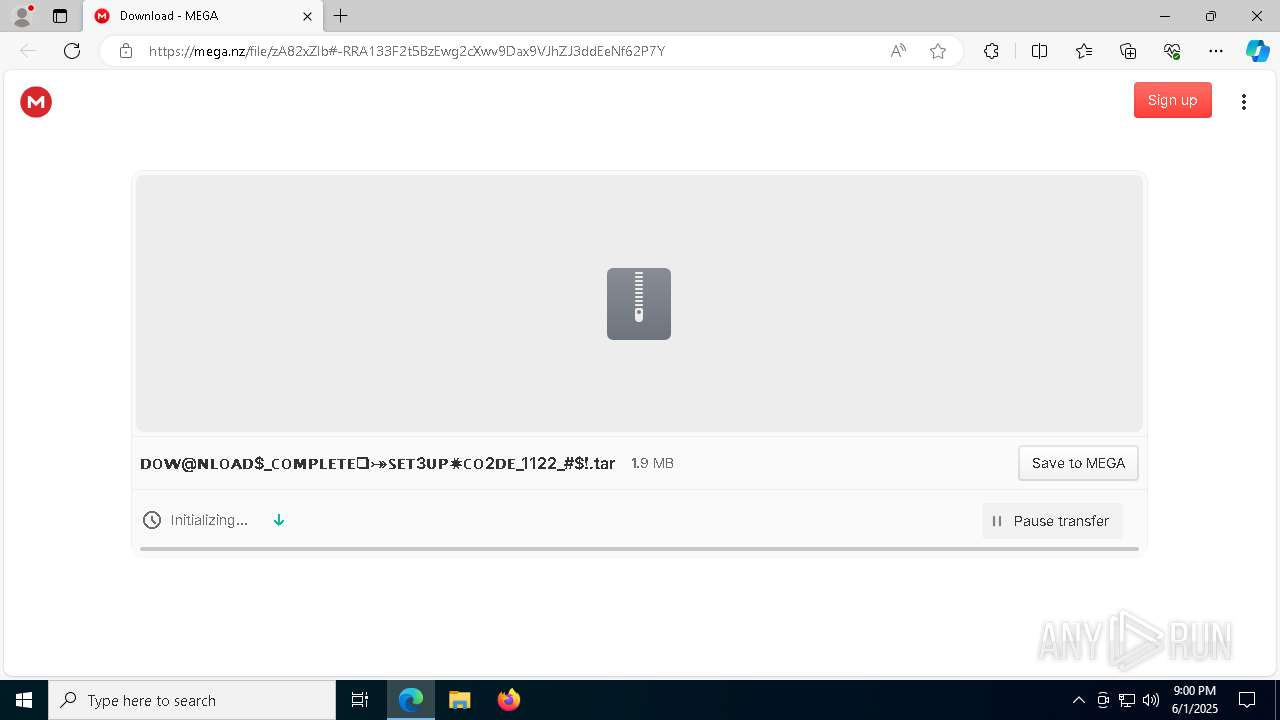
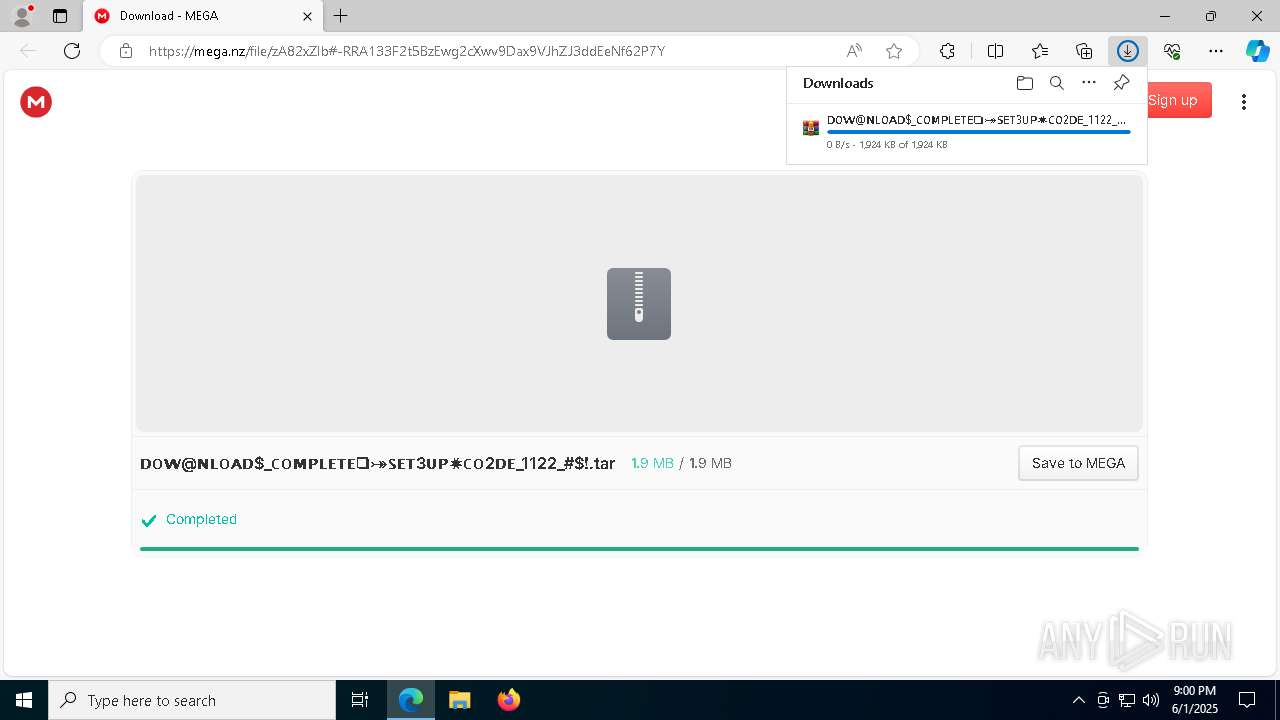
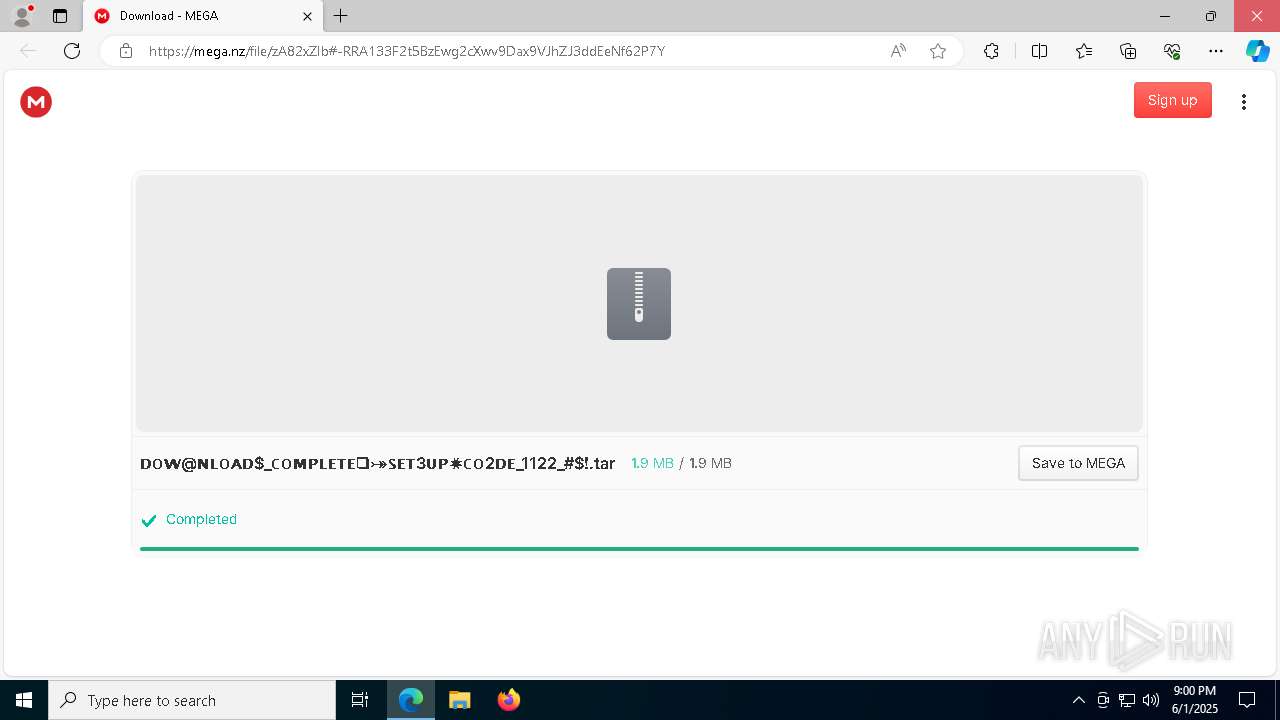
| URL: | https://mega.nz/file/zA82xZIb#-RRA133F2t5BzEwg2cXwv9Dax9VJhZJ3ddEeNf62P7Y |
| Full analysis: | https://app.any.run/tasks/13090f40-40e3-48b4-b00f-eff12b621345 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 01, 2025, 20:59:41 |
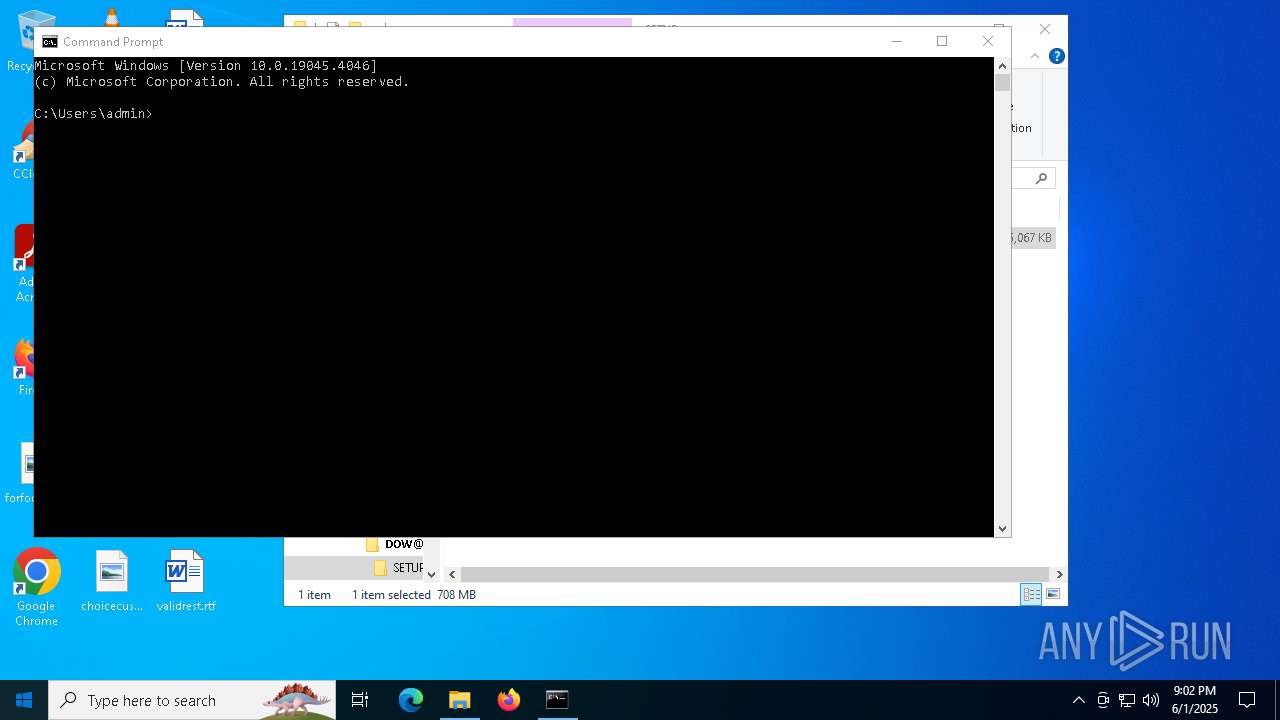
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99D79E3F3606B2B44927393F04394A47 |
| SHA1: | AC33A78E1A5AD49DB7578FDBBE4A05AFBB0D0E51 |
| SHA256: | 6055F3DC27FC2EC4DB162EF7589087A93930179DCB24C5A3CCBB0AE3538997B3 |
| SSDEEP: | 3:N8X/iz/mfHk2EC50pVuV:2tfhOpgV |
MALICIOUS
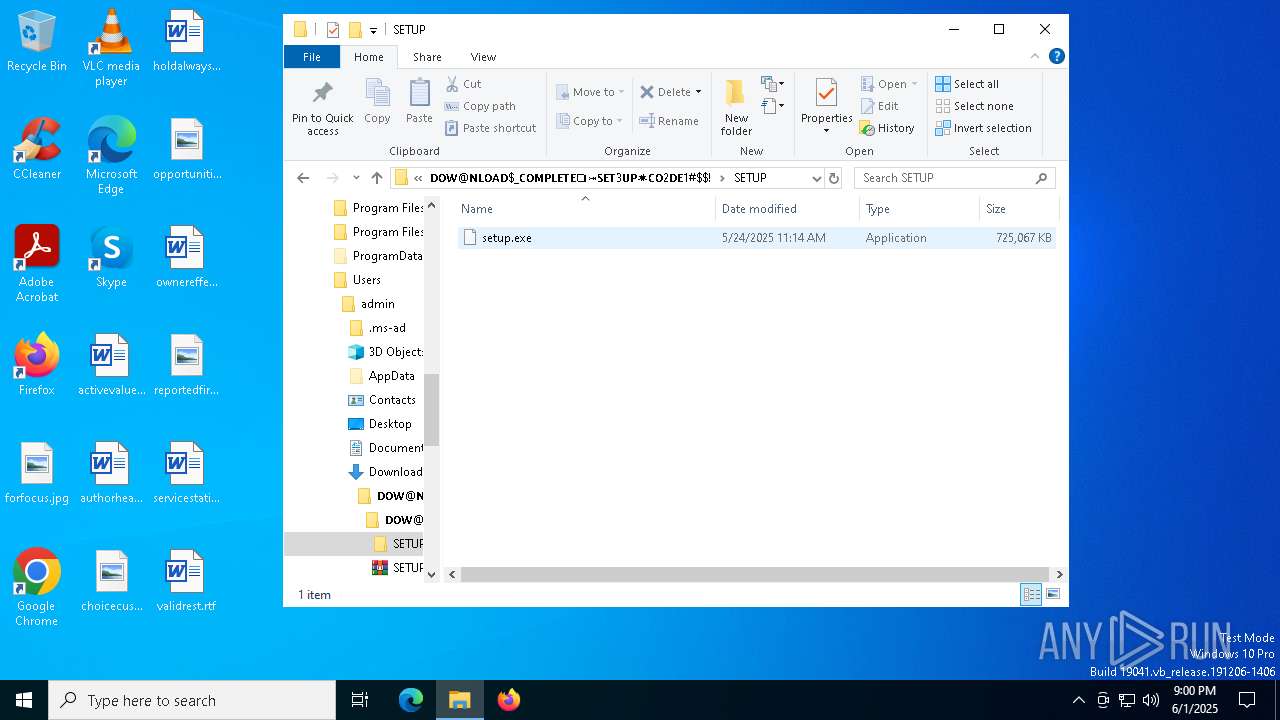
Executing a file with an untrusted certificate
- setup.exe (PID: 5960)
- hjksfwz.exe (PID: 3676)
- hjksfjd.exe (PID: 5360)
- NahimicSvc64.exe (PID: 7272)
- shark.exe (PID: 2800)
- shark.exe (PID: 7040)
- NahimicSvc64.exe (PID: 6696)
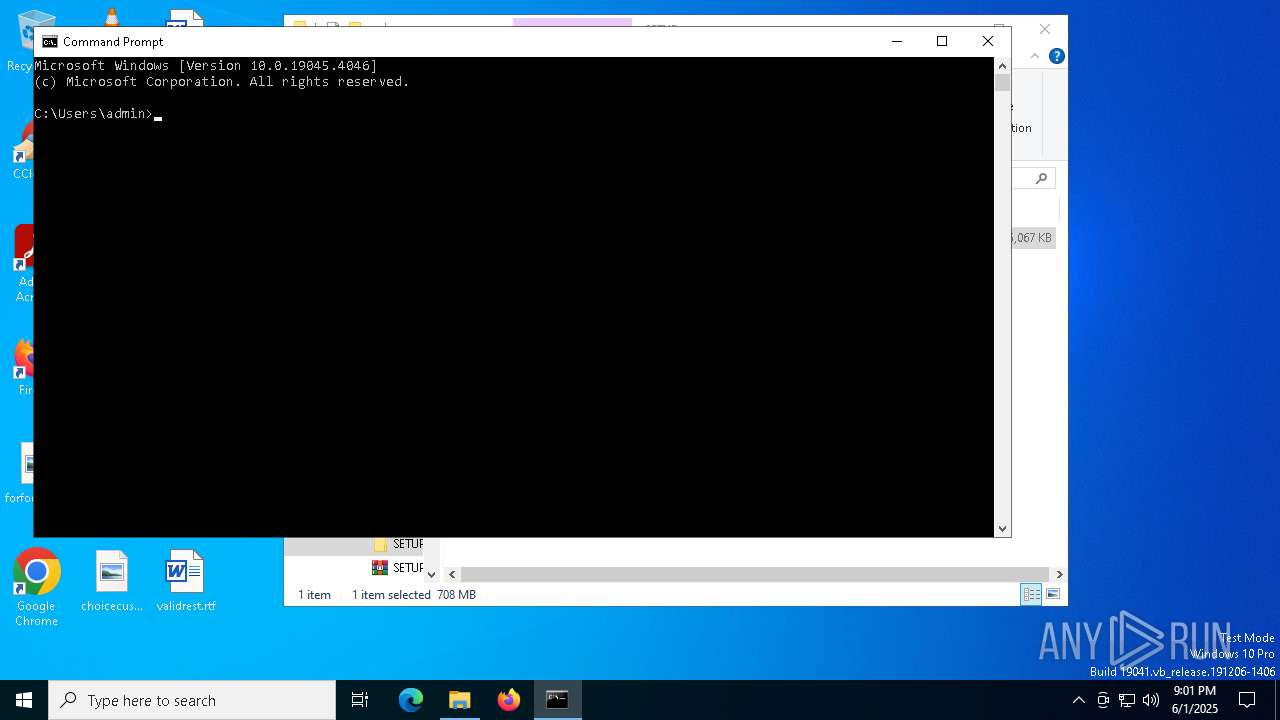
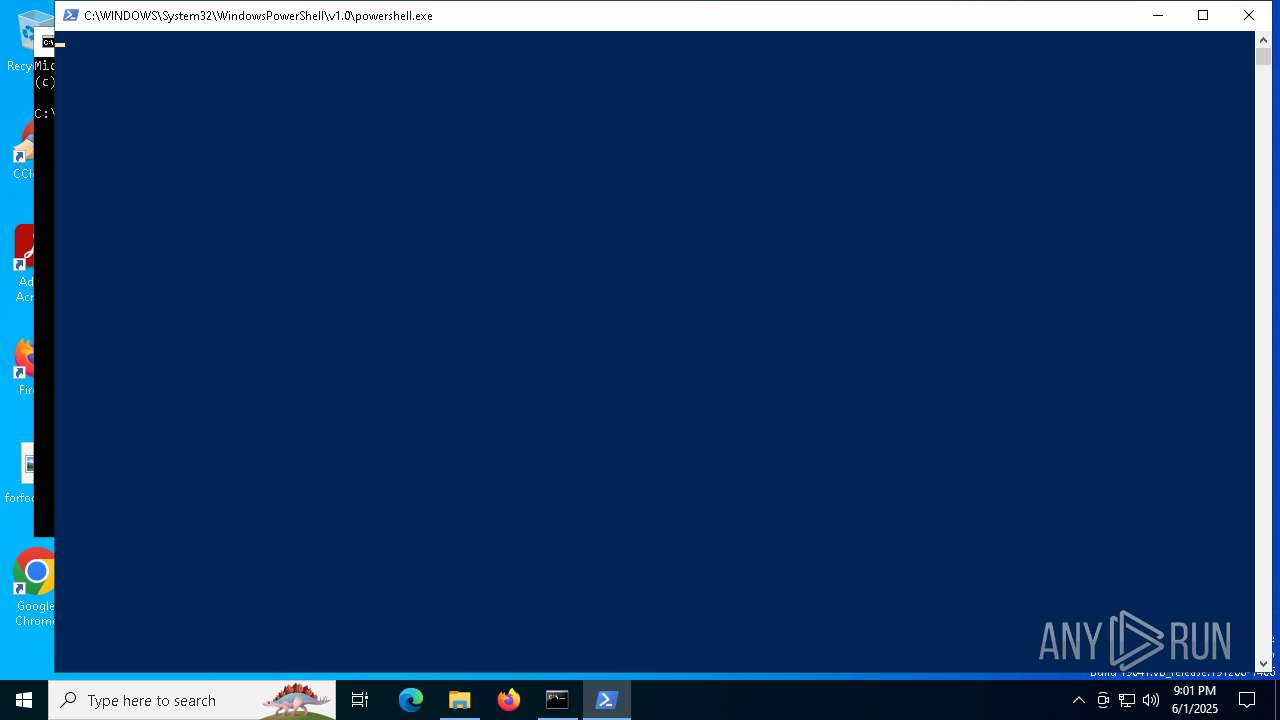
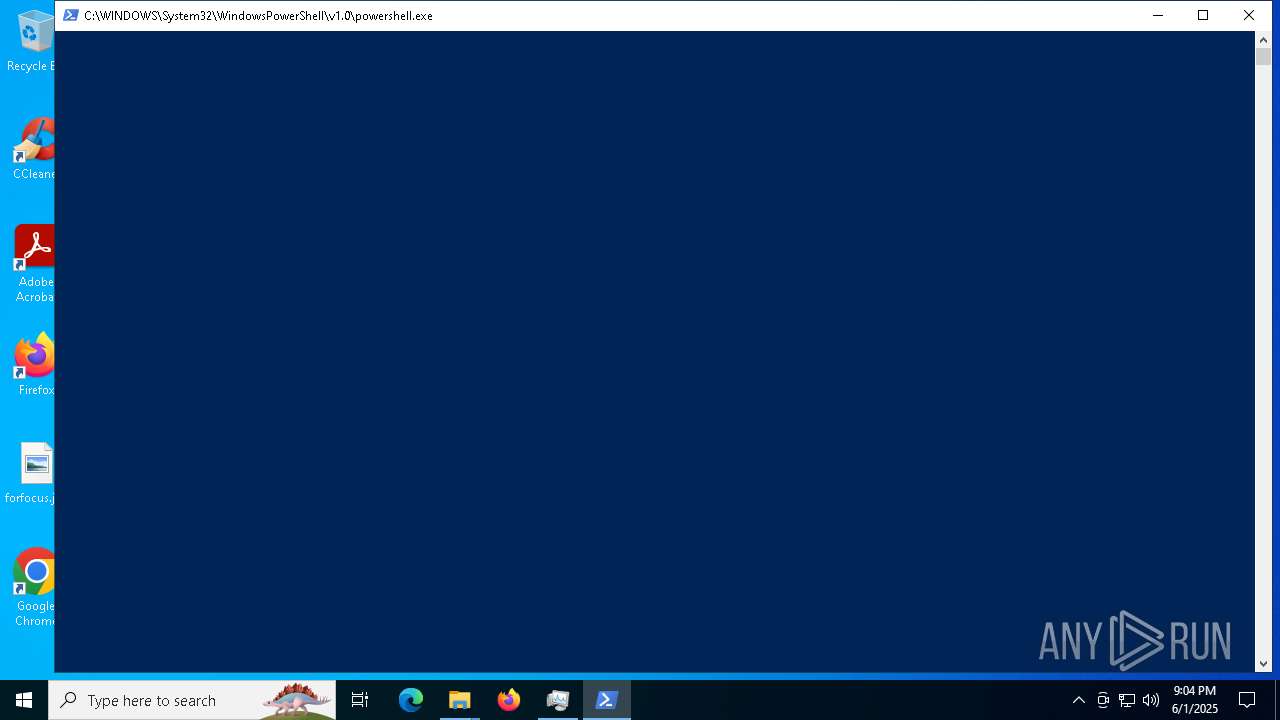
Changes powershell execution policy (Bypass)
- setup.exe (PID: 5960)
Bypass execution policy to execute commands
- powershell.exe (PID: 8040)
GENERIC has been found (auto)
- setup.exe (PID: 5960)
- hjksfjd.exe (PID: 5360)
HIJACKLOADER has been detected (YARA)
- Nahimic.exe (PID: 5384)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2612)
AMADEY has been detected (YARA)
- rca.com (PID: 6032)
AMADEY has been detected (SURICATA)
- rca.com (PID: 6032)
SUSPICIOUS
Possibly a phishing URL contains email has been detected
- msedge.exe (PID: 2600)
The process executes Powershell scripts
- setup.exe (PID: 5960)
Starts POWERSHELL.EXE for commands execution
- setup.exe (PID: 5960)
- explorer.exe (PID: 6028)
- shark.exe (PID: 2800)
- shark.exe (PID: 7040)
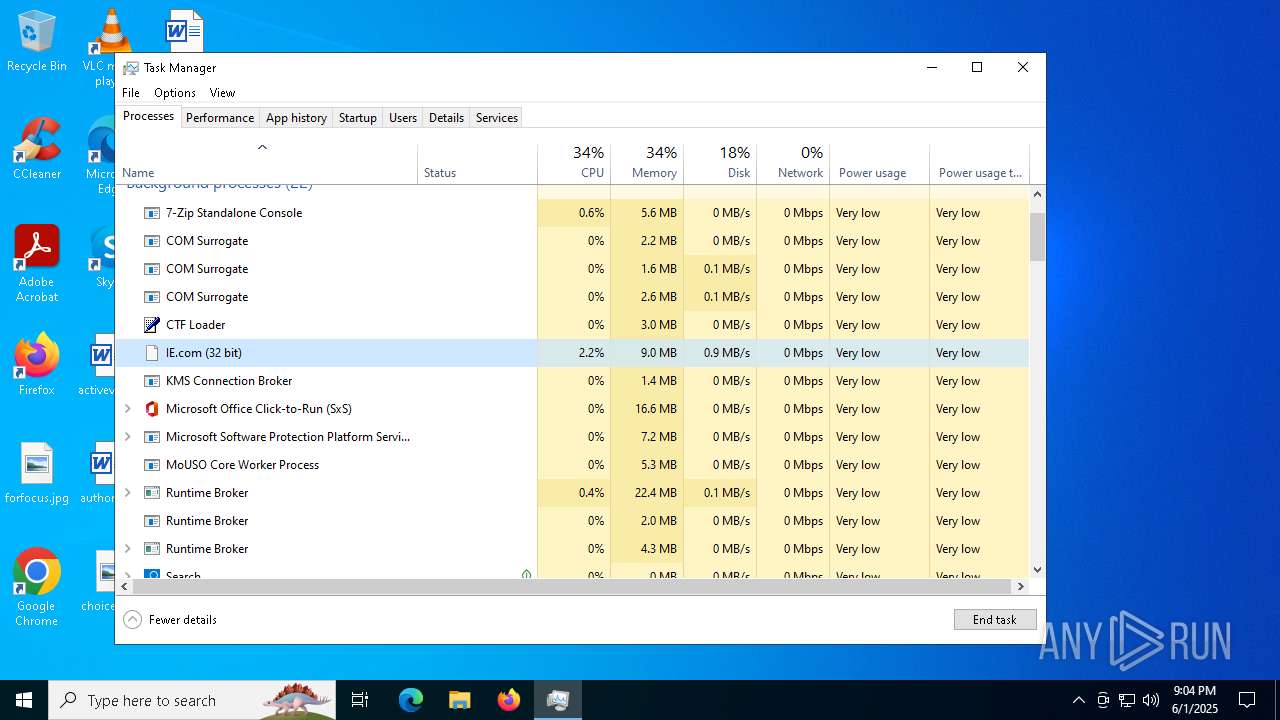
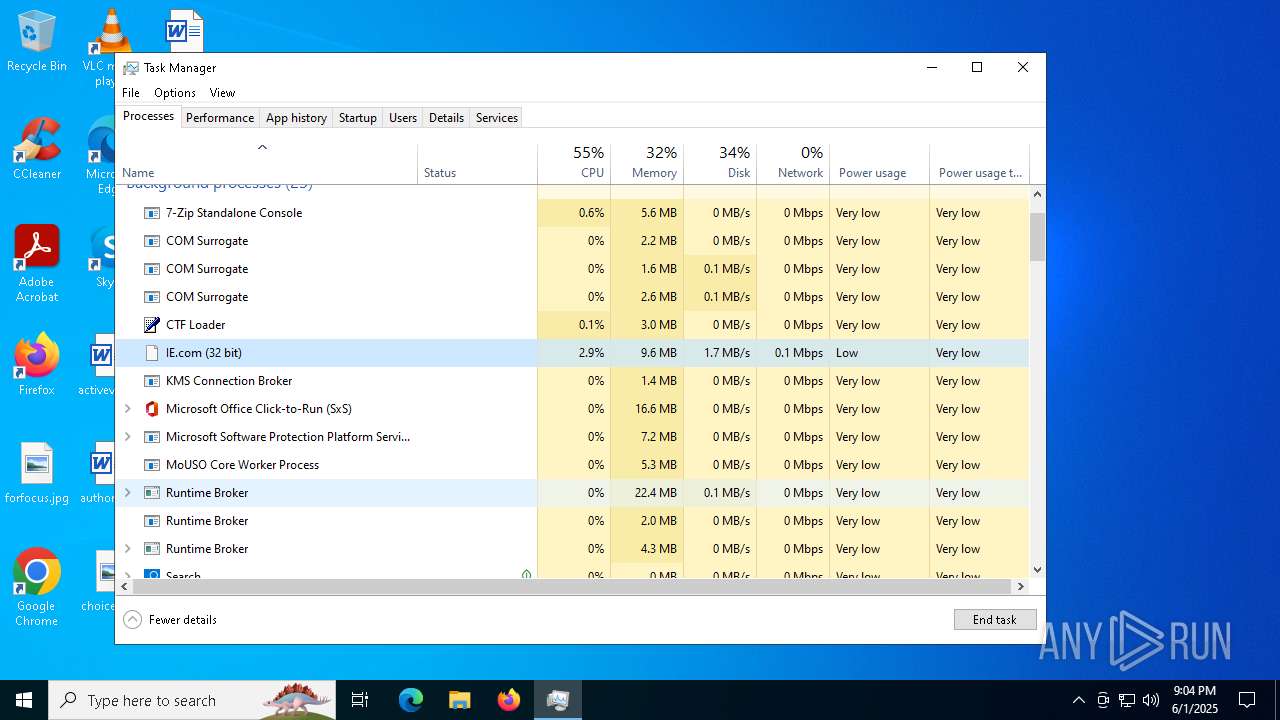
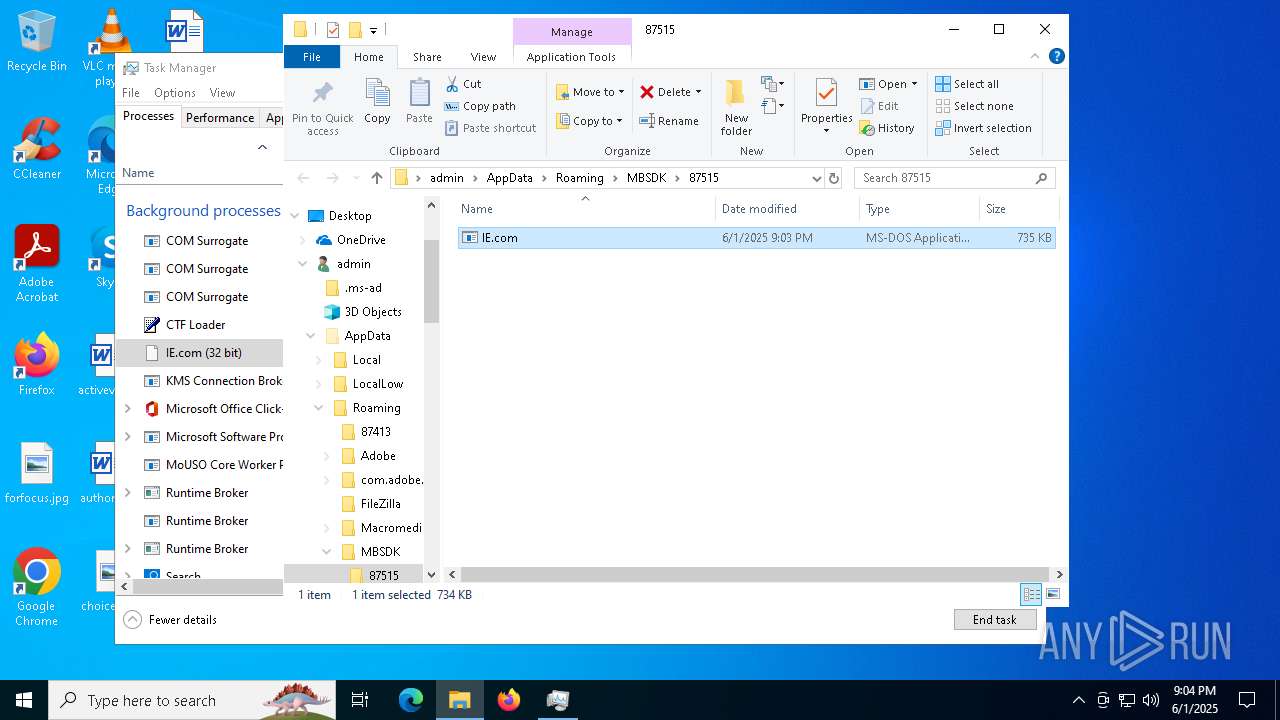
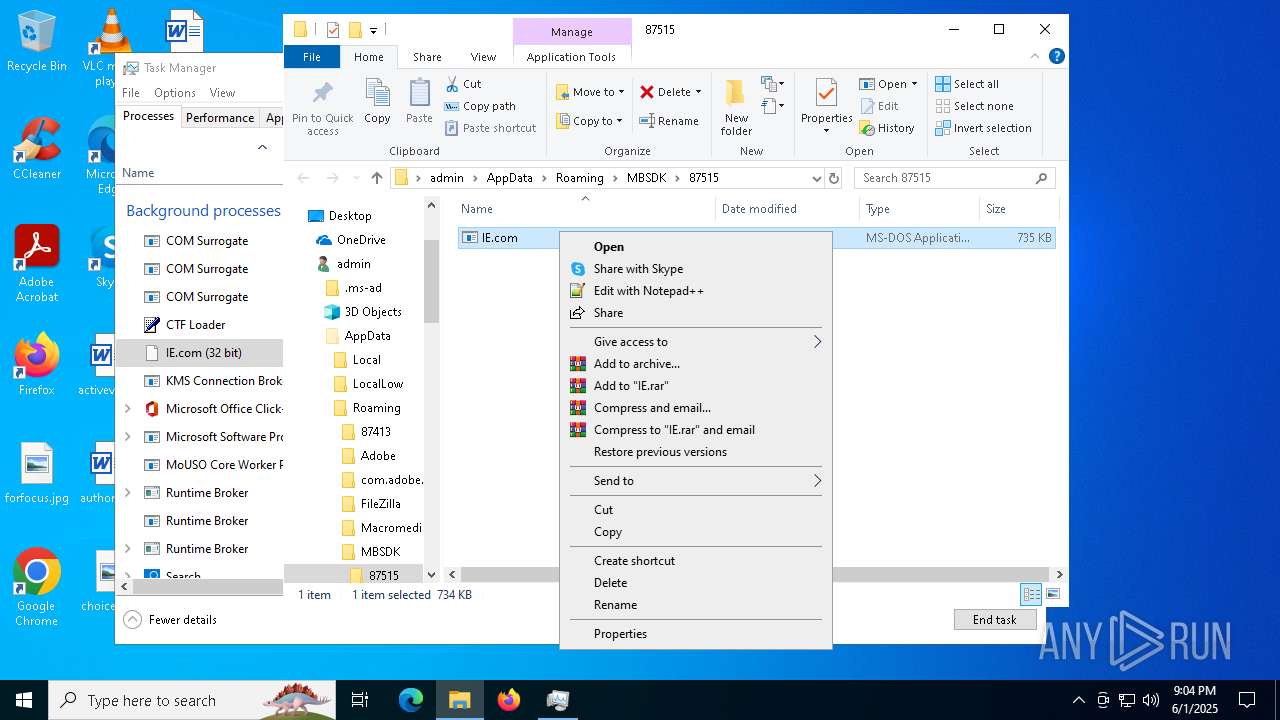
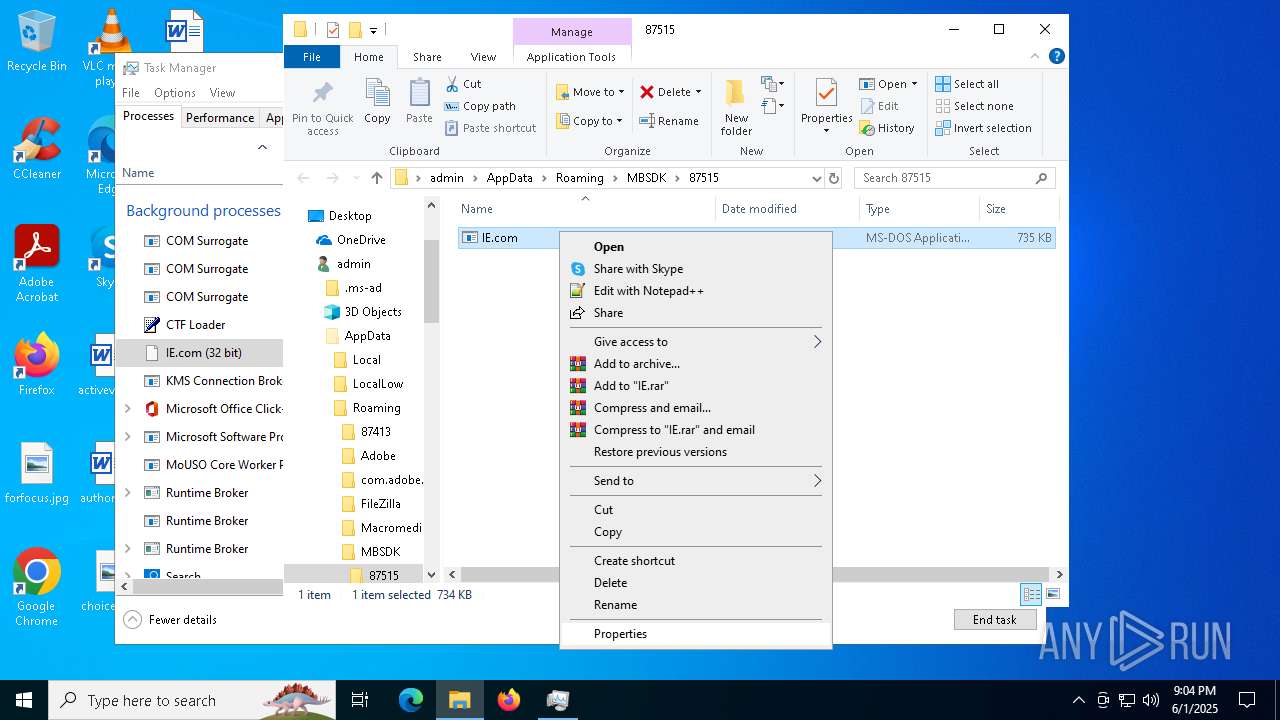
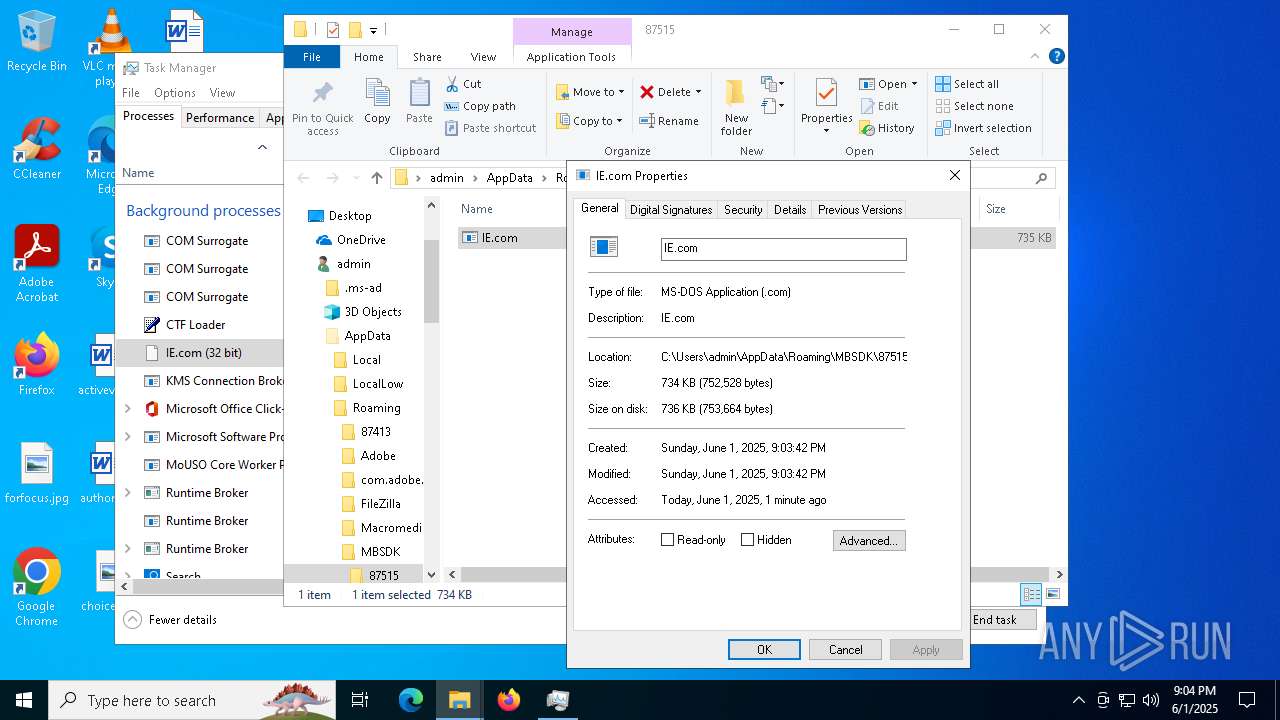
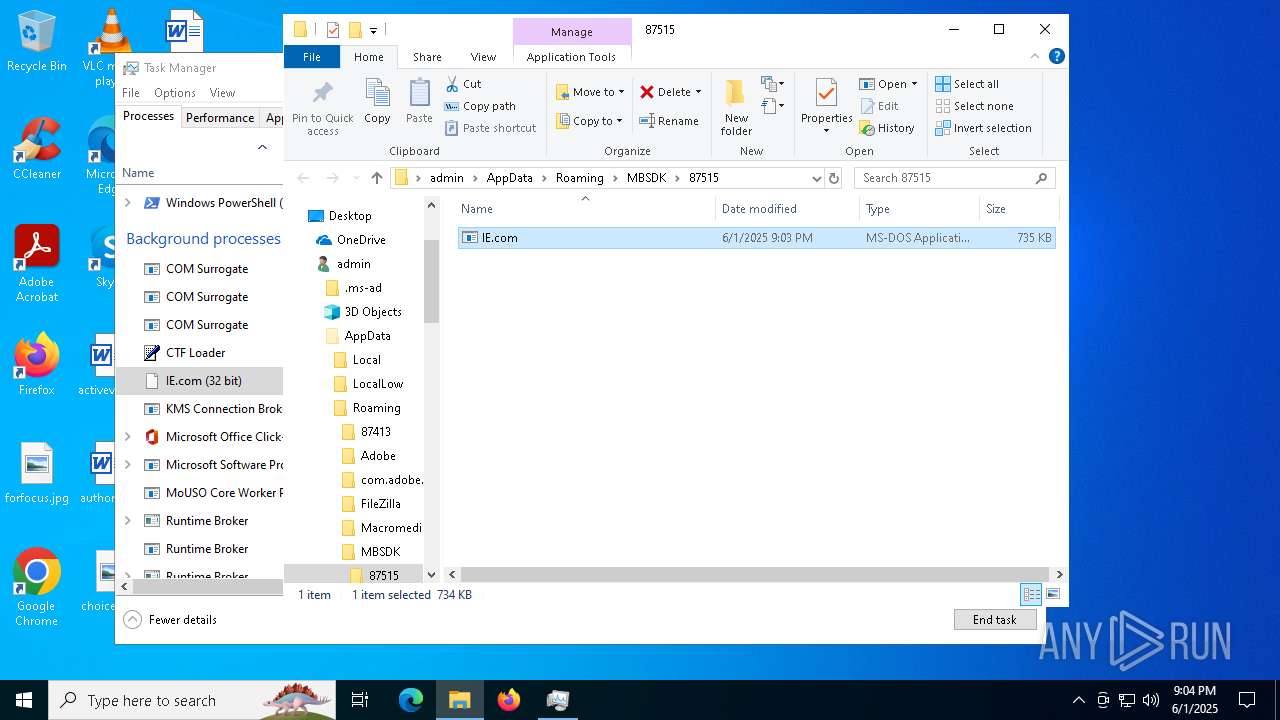
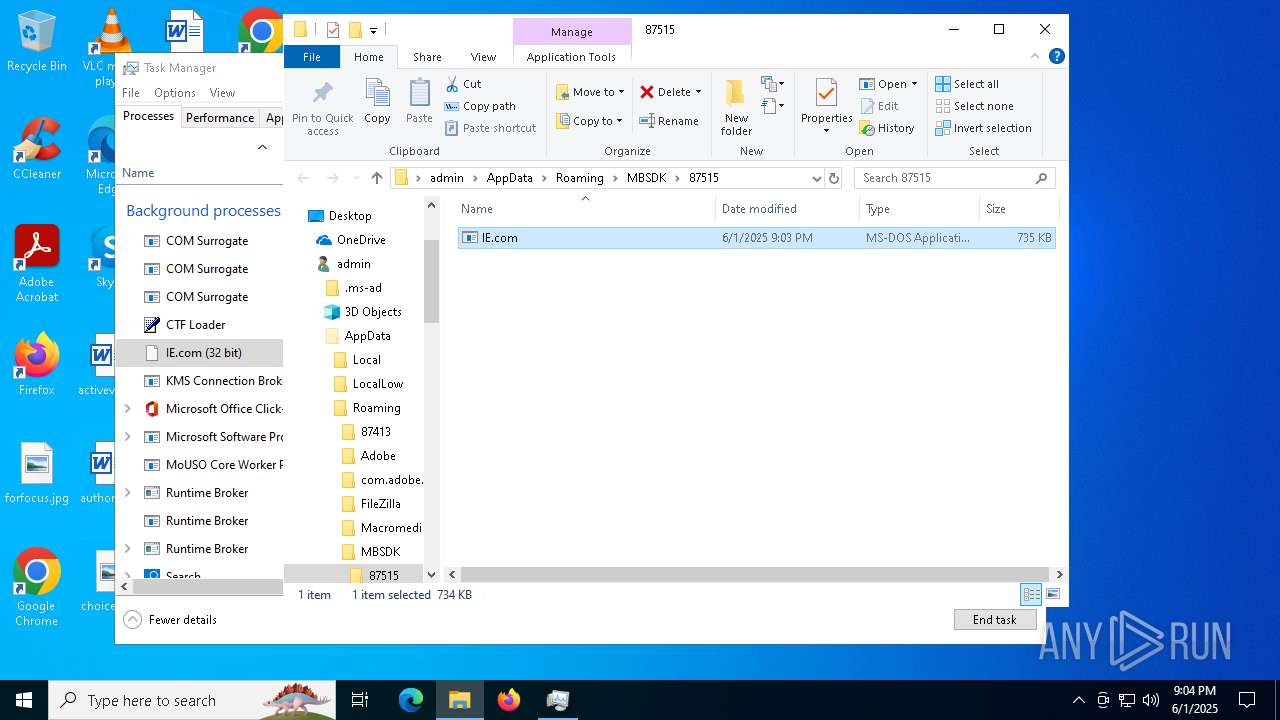
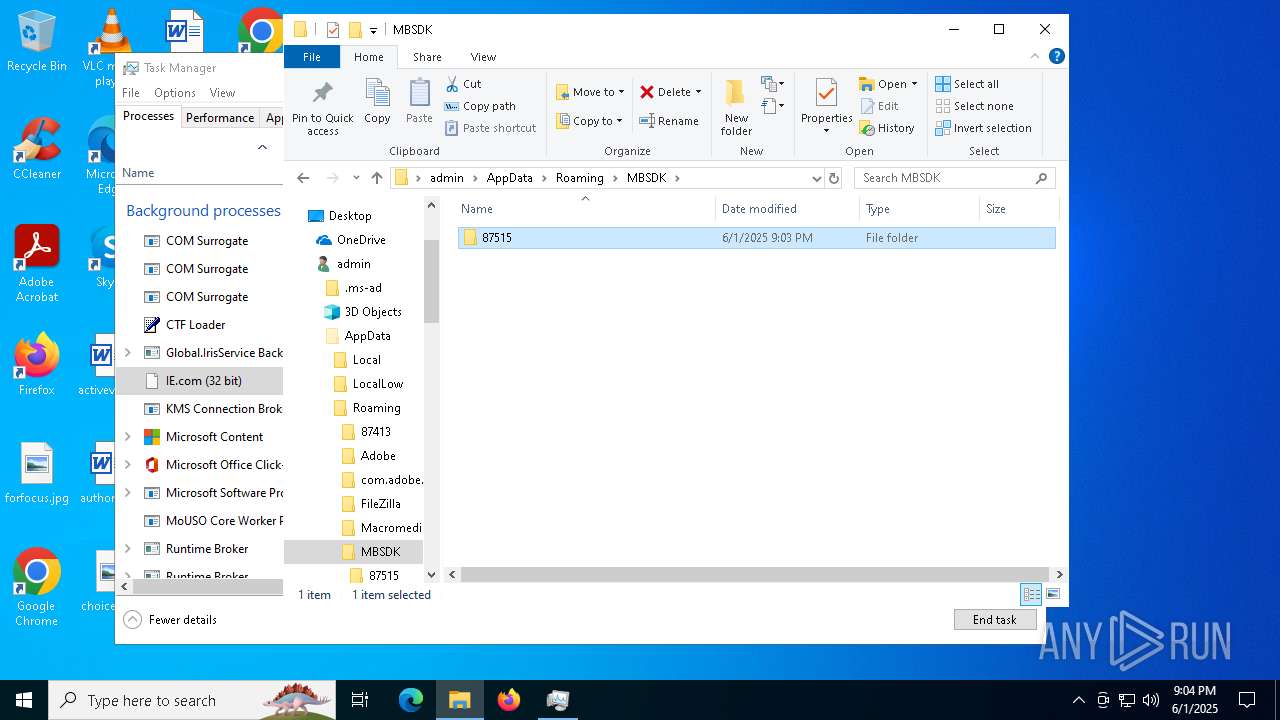
- IE.com (PID: 6772)
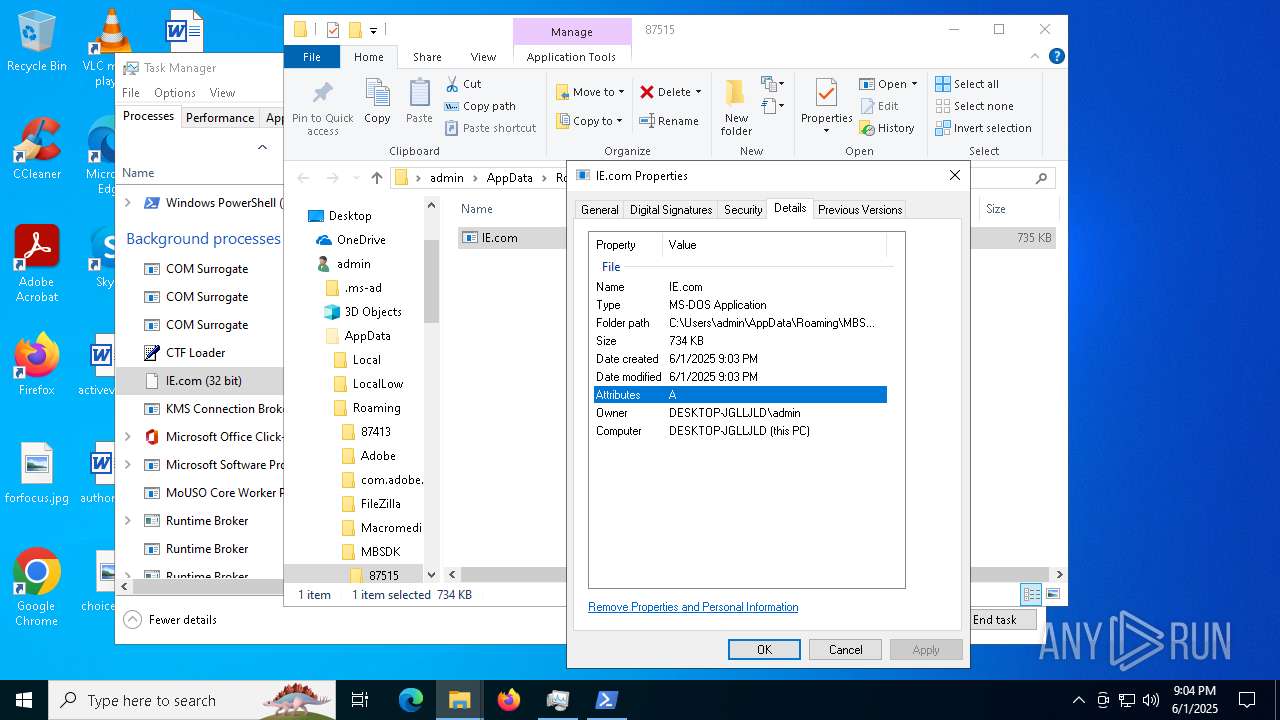
Executable content was dropped or overwritten
- setup.exe (PID: 5960)
- Nahimic.exe (PID: 5384)
- hjksfwz.exe (PID: 3676)
- NahimicSvc64.exe (PID: 7272)
- hjksfjd.exe (PID: 5360)
- explorer.exe (PID: 6028)
- MicrosoftEdgeWebview2Setup.exe (PID: 2236)
- NahimicSvc64.exe (PID: 6696)
- IE.com (PID: 6772)
- MicrosoftEdgeWebview2Setup.exe (PID: 6796)
Process requests binary or script from the Internet
- setup.exe (PID: 5960)
Potential Corporate Privacy Violation
- setup.exe (PID: 5960)
Process drops legitimate windows executable
- hjksfjd.exe (PID: 5360)
- NahimicSvc64.exe (PID: 7272)
- MicrosoftEdgeWebview2Setup.exe (PID: 2236)
- MicrosoftEdgeUpdate.exe (PID: 2868)
- NahimicSvc64.exe (PID: 6696)
- MicrosoftEdgeWebview2Setup.exe (PID: 6796)
- MicrosoftEdgeUpdate.exe (PID: 4796)
- IE.com (PID: 6772)
The process drops C-runtime libraries
- hjksfjd.exe (PID: 5360)
- NahimicSvc64.exe (PID: 7272)
- NahimicSvc64.exe (PID: 6696)
The process bypasses the loading of PowerShell profile settings
- setup.exe (PID: 5960)
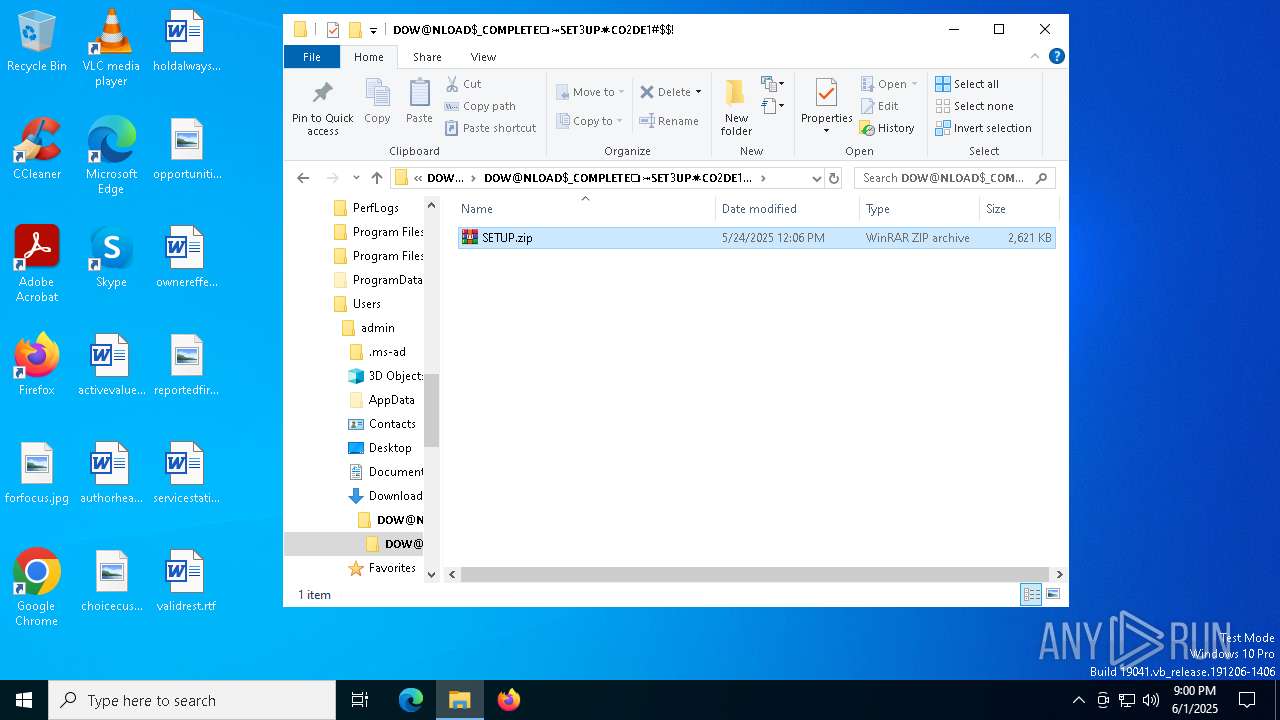
Drops 7-zip archiver for unpacking
- NahimicSvc64.exe (PID: 7272)
- NahimicSvc64.exe (PID: 6696)
Starts application with an unusual extension
- Nahimic.exe (PID: 5384)
- NahimicSvc64.exe (PID: 6696)
Executes application which crashes
- hjksfwz.exe (PID: 3676)
- shark.exe (PID: 2800)
- shark.exe (PID: 7040)
There is functionality for taking screenshot (YARA)
- hjksfjd.exe (PID: 5360)
- Nahimic.exe (PID: 5384)
- rca.com (PID: 6032)
Starts CMD.EXE for commands execution
- hjksfwz.exe (PID: 3676)
Contacting a server suspected of hosting an CnC
- rca.com (PID: 6032)
Connects to unusual port
- explorer.exe (PID: 6028)
- IE.com (PID: 6772)
- shark.exe (PID: 2800)
- shark.exe (PID: 7040)
Starts process via Powershell
- powershell.exe (PID: 680)
- powershell.exe (PID: 548)
The process executes via Task Scheduler
- shark.exe (PID: 2800)
- shark.exe (PID: 7040)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 2868)
- MicrosoftEdgeUpdate.exe (PID: 4796)
There is functionality for enable RDP (YARA)
- rca.com (PID: 6032)
INFO
Reads the computer name
- identity_helper.exe (PID: 7036)
- identity_helper.exe (PID: 6248)
Application launched itself
- msedge.exe (PID: 2600)
- msedge.exe (PID: 4028)
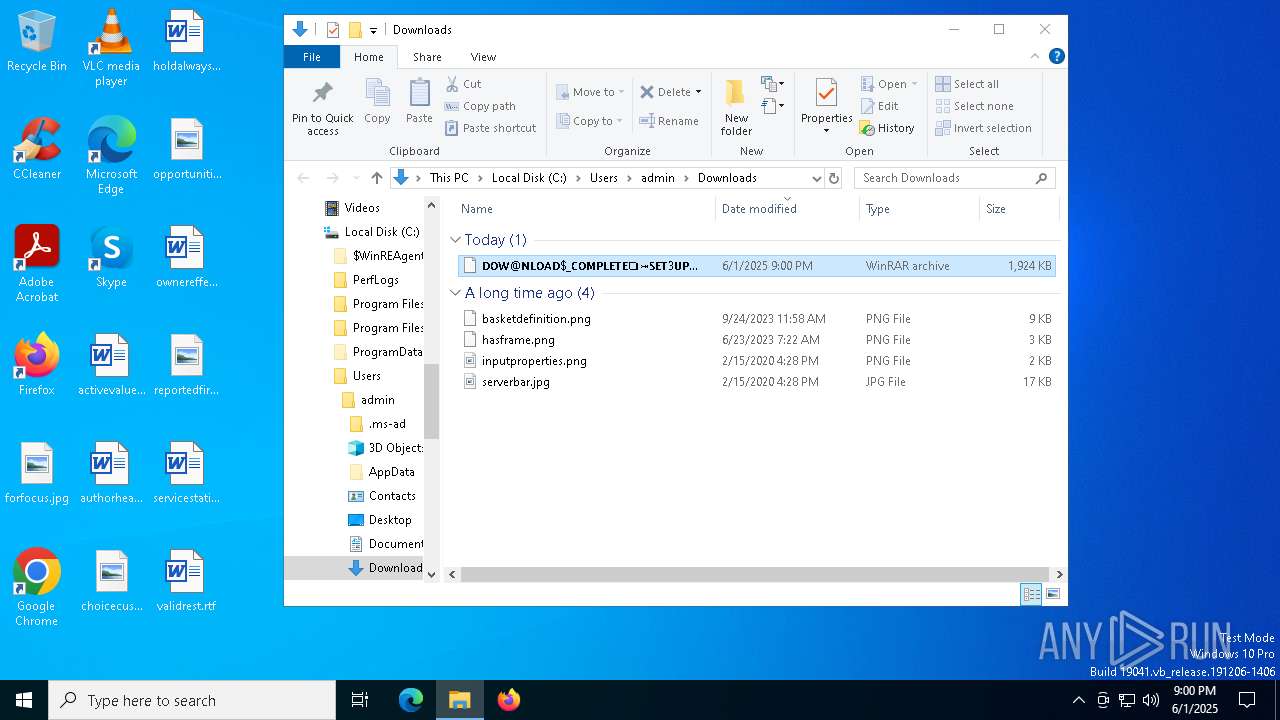
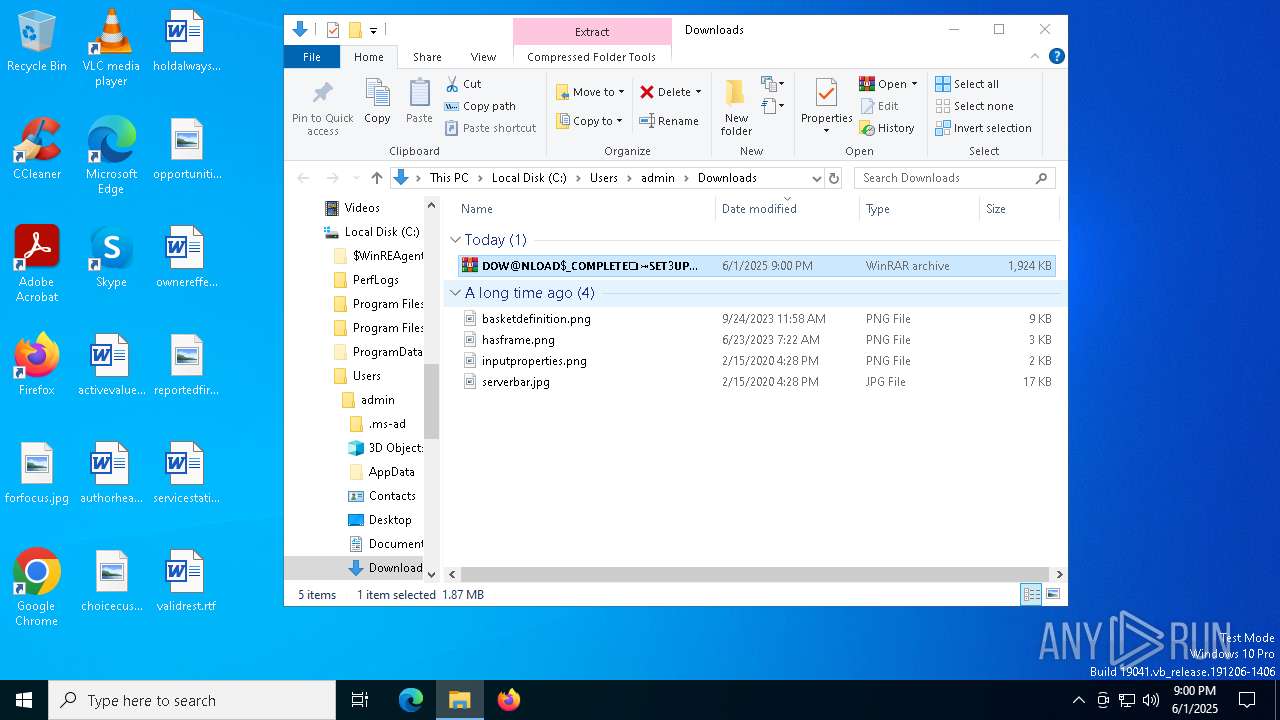
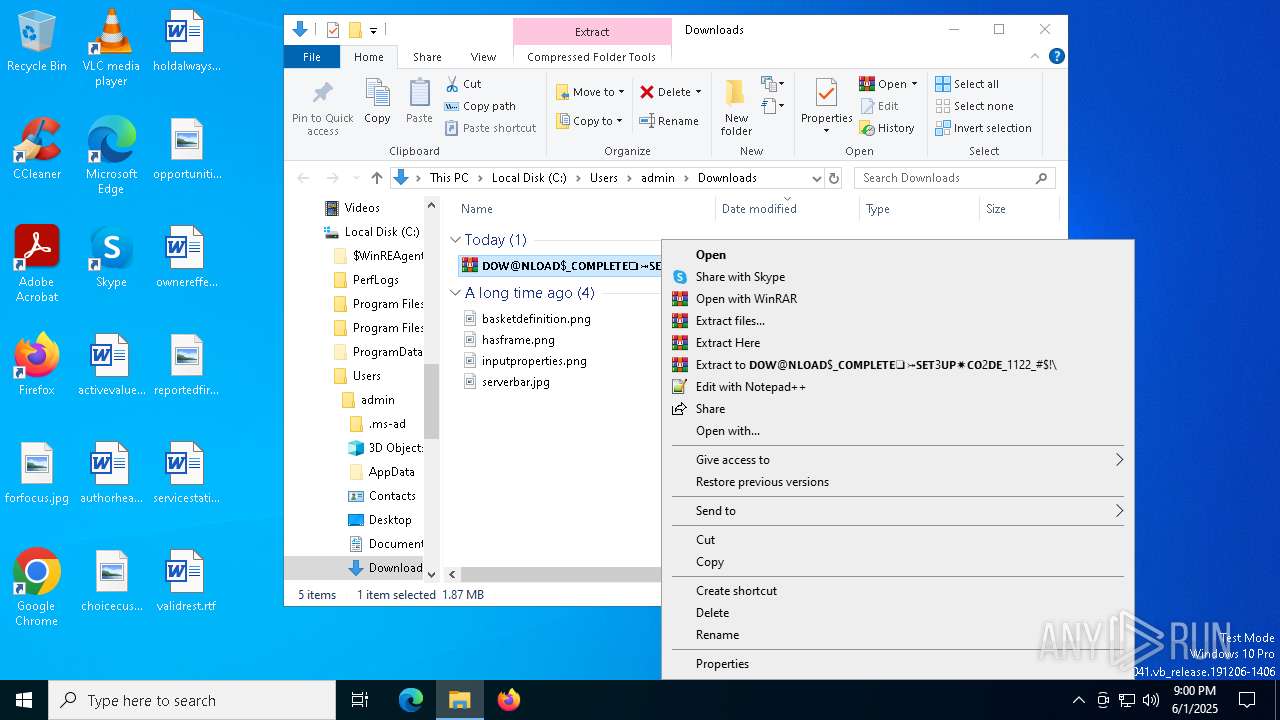
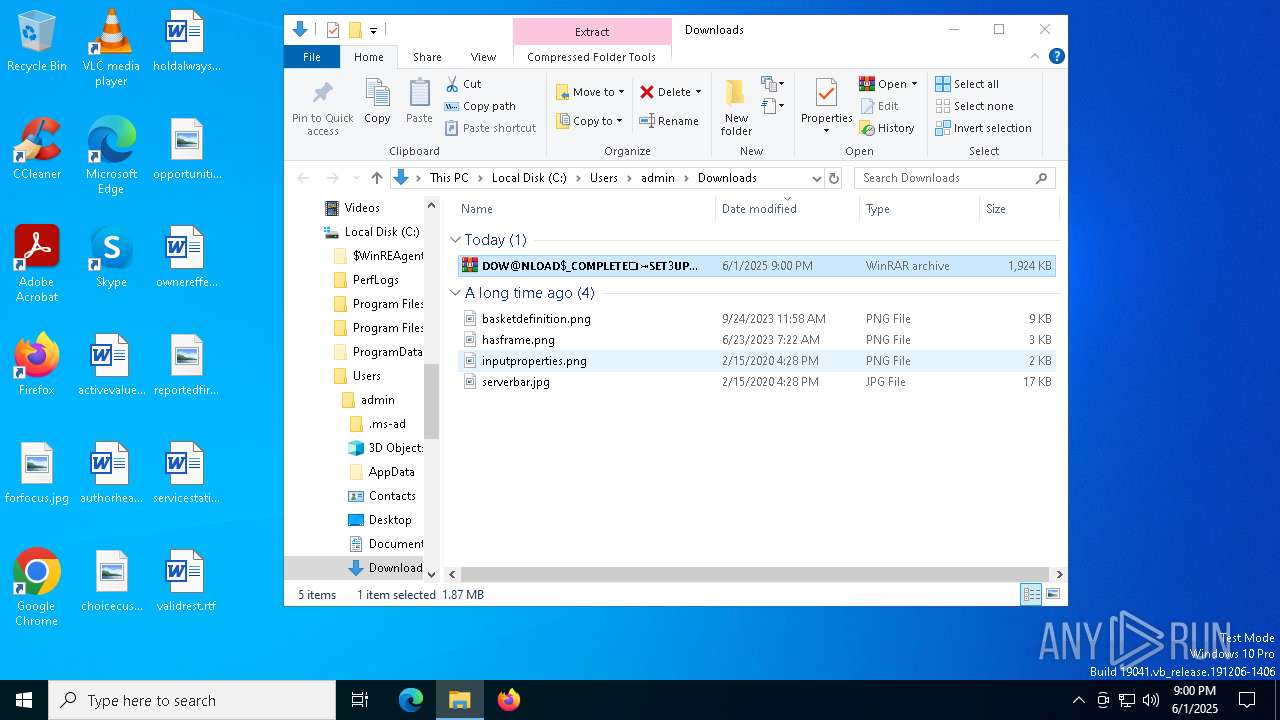
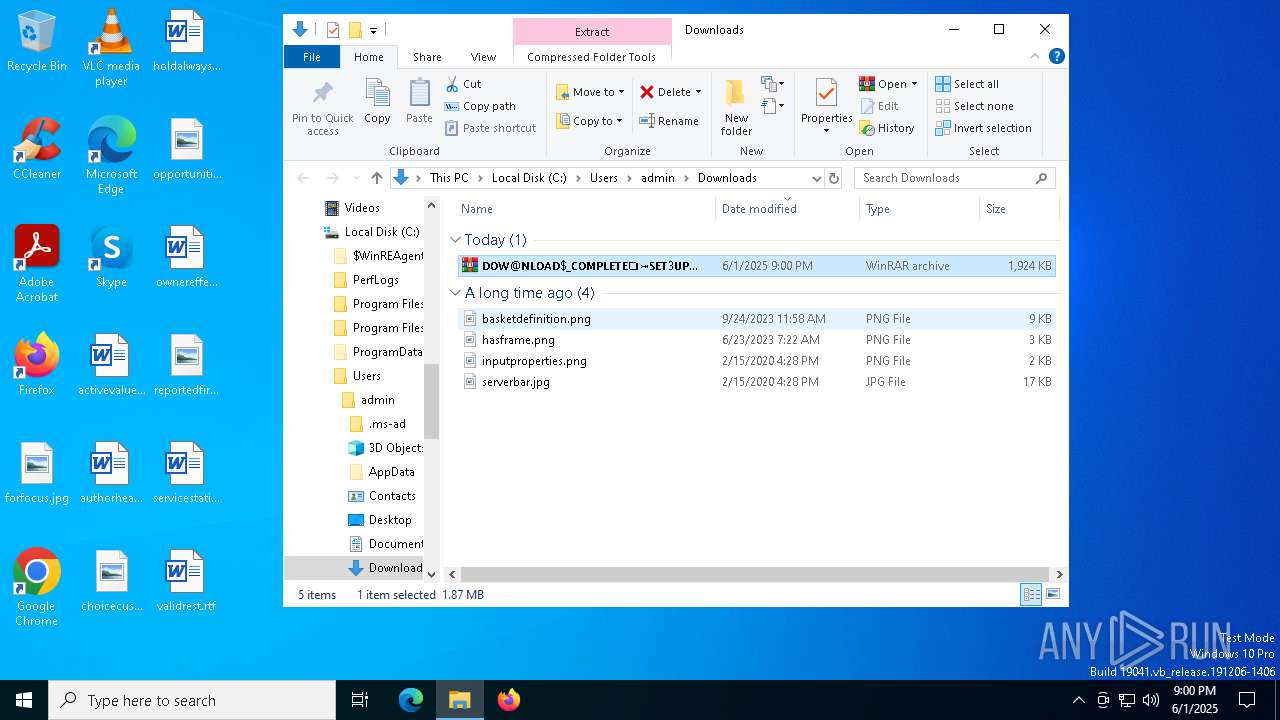
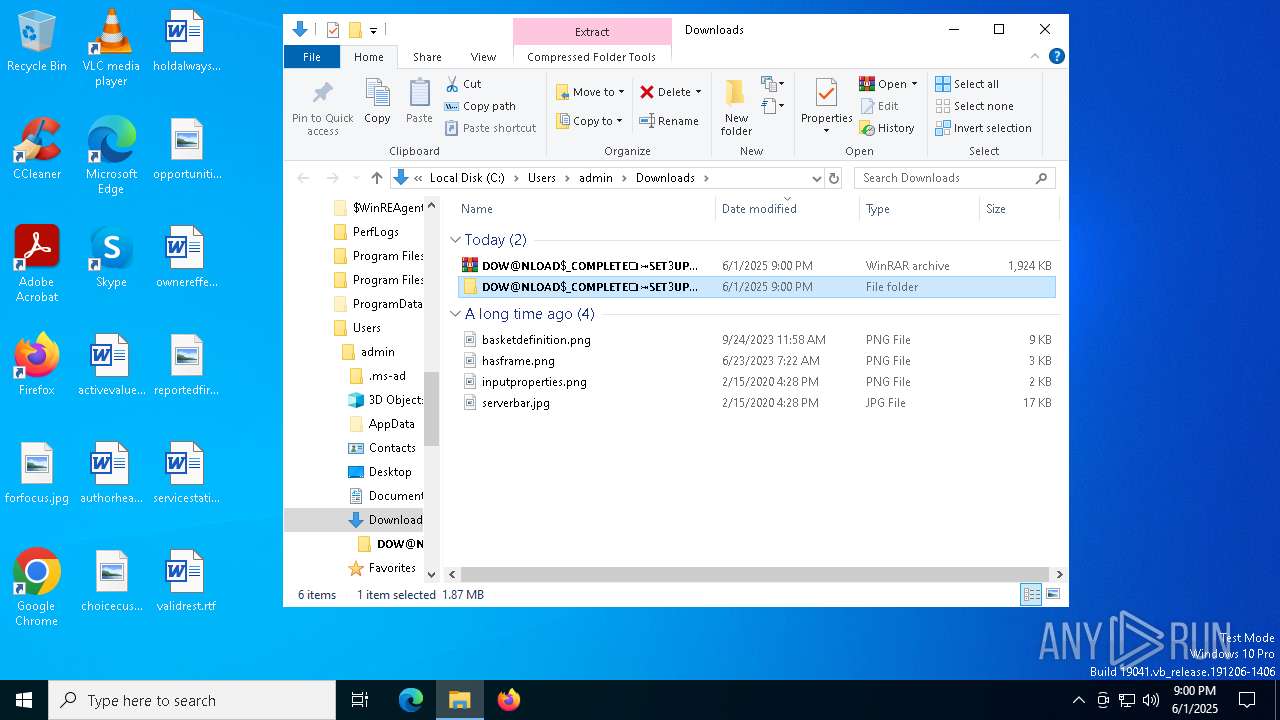
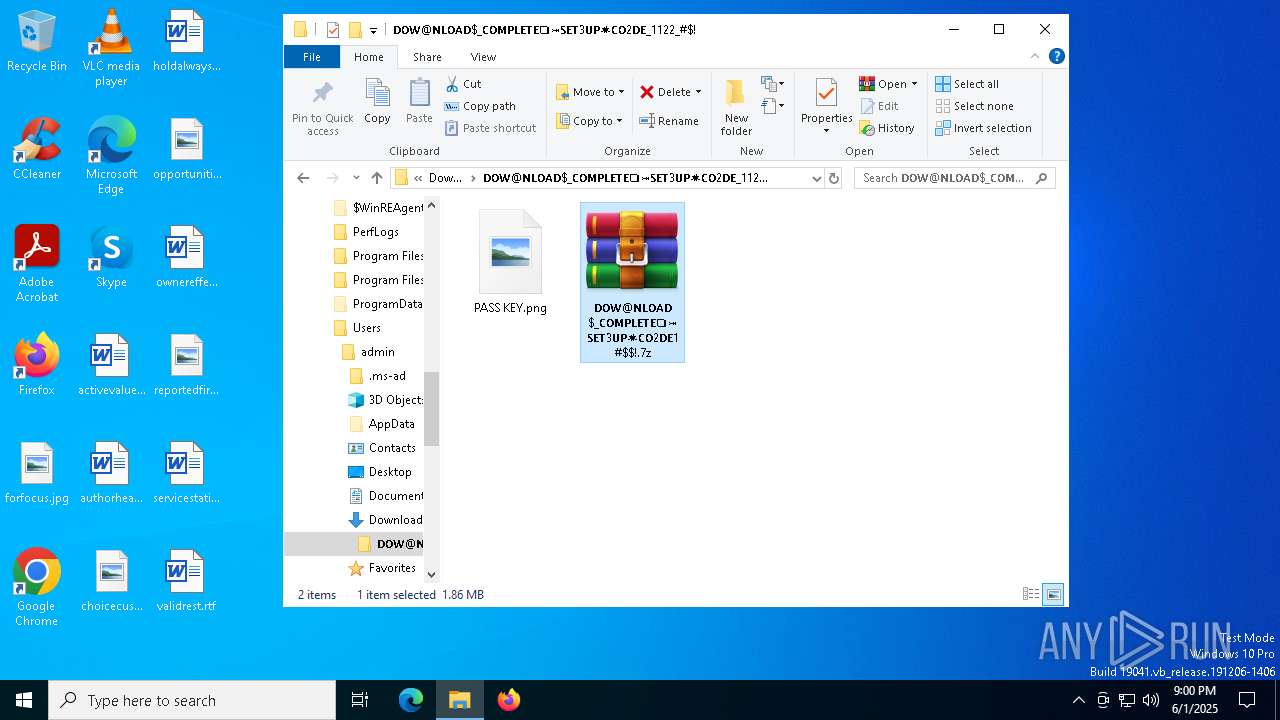
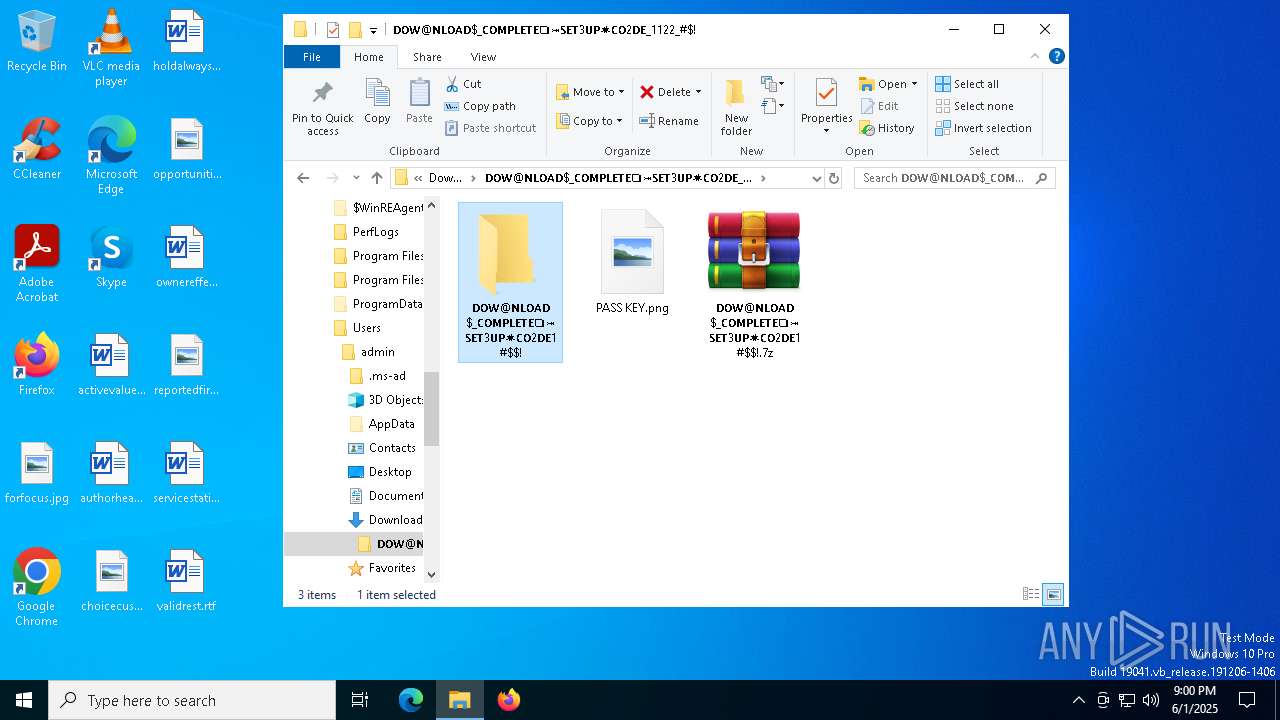
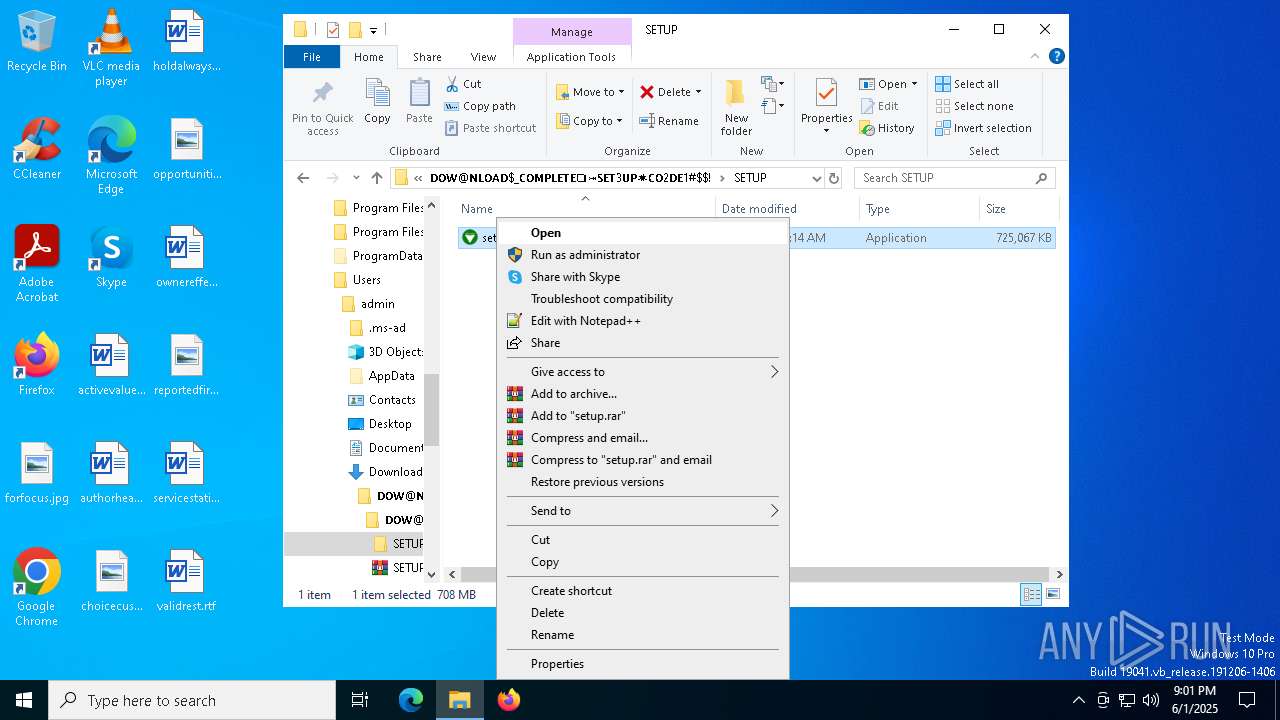
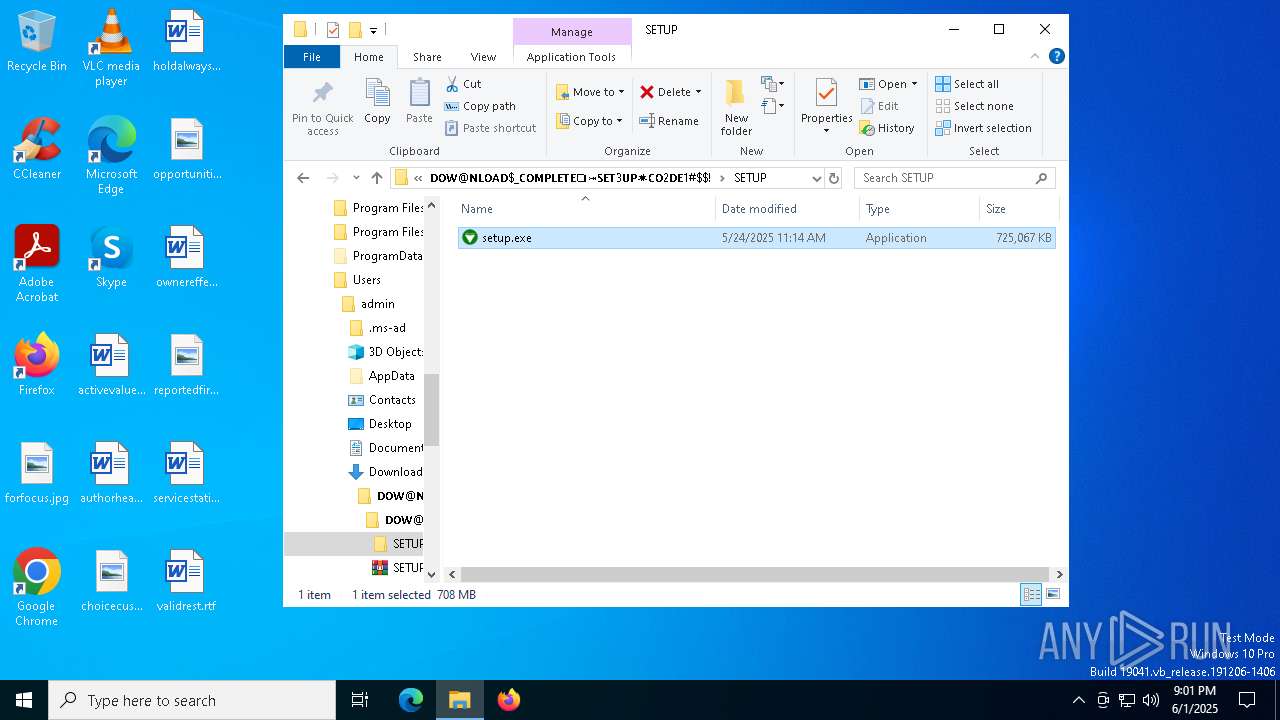
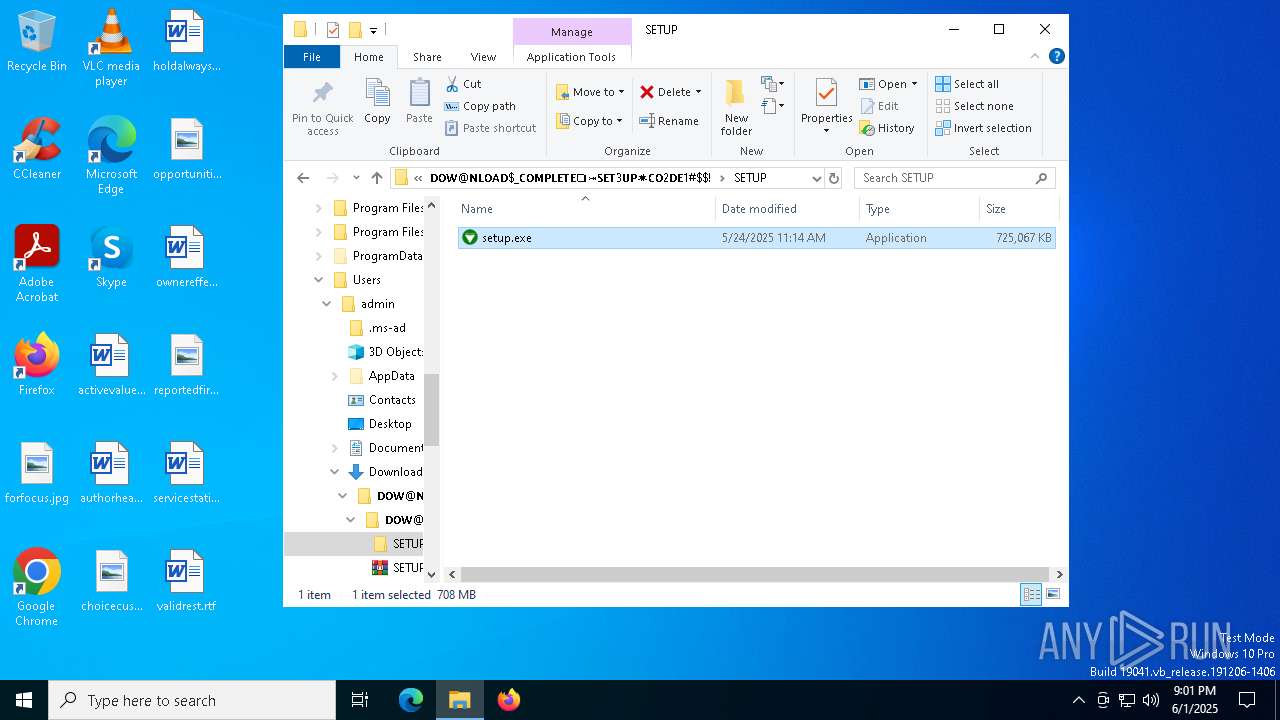
Launch of the file from Downloads directory
- msedge.exe (PID: 2600)
Checks supported languages
- identity_helper.exe (PID: 6248)
- identity_helper.exe (PID: 7036)
Reads Environment values
- identity_helper.exe (PID: 7036)
- identity_helper.exe (PID: 6248)
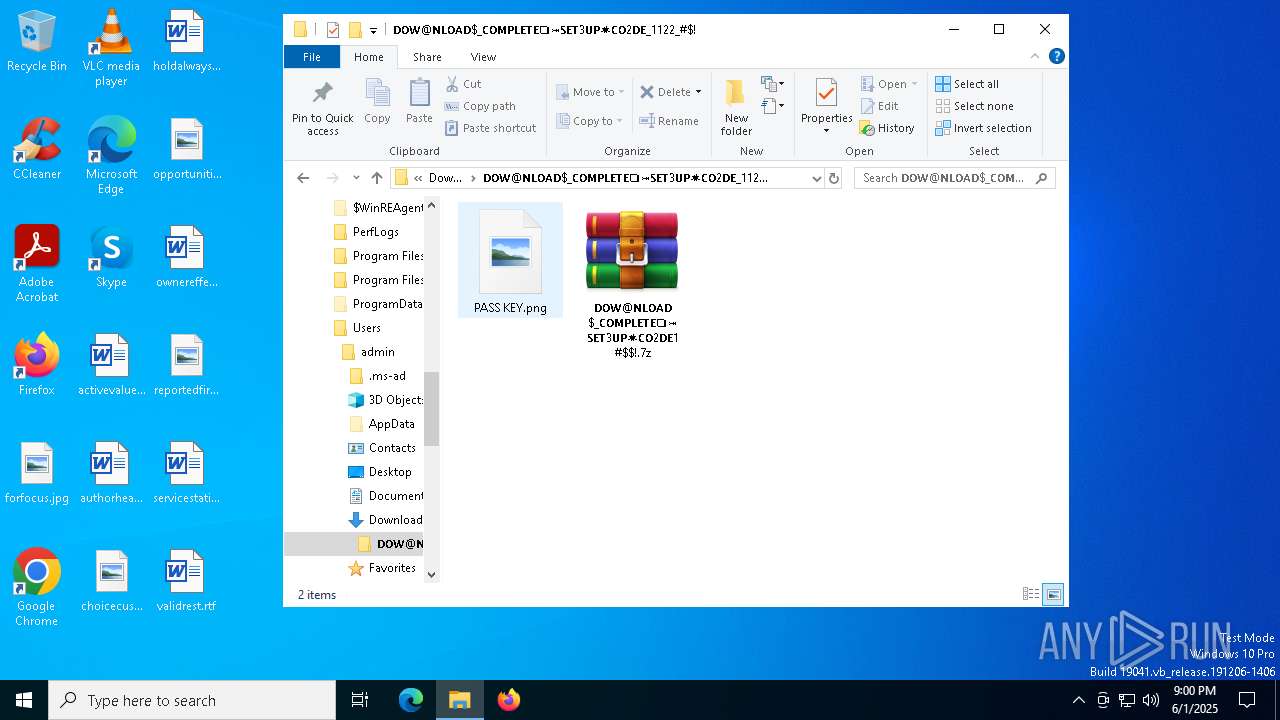
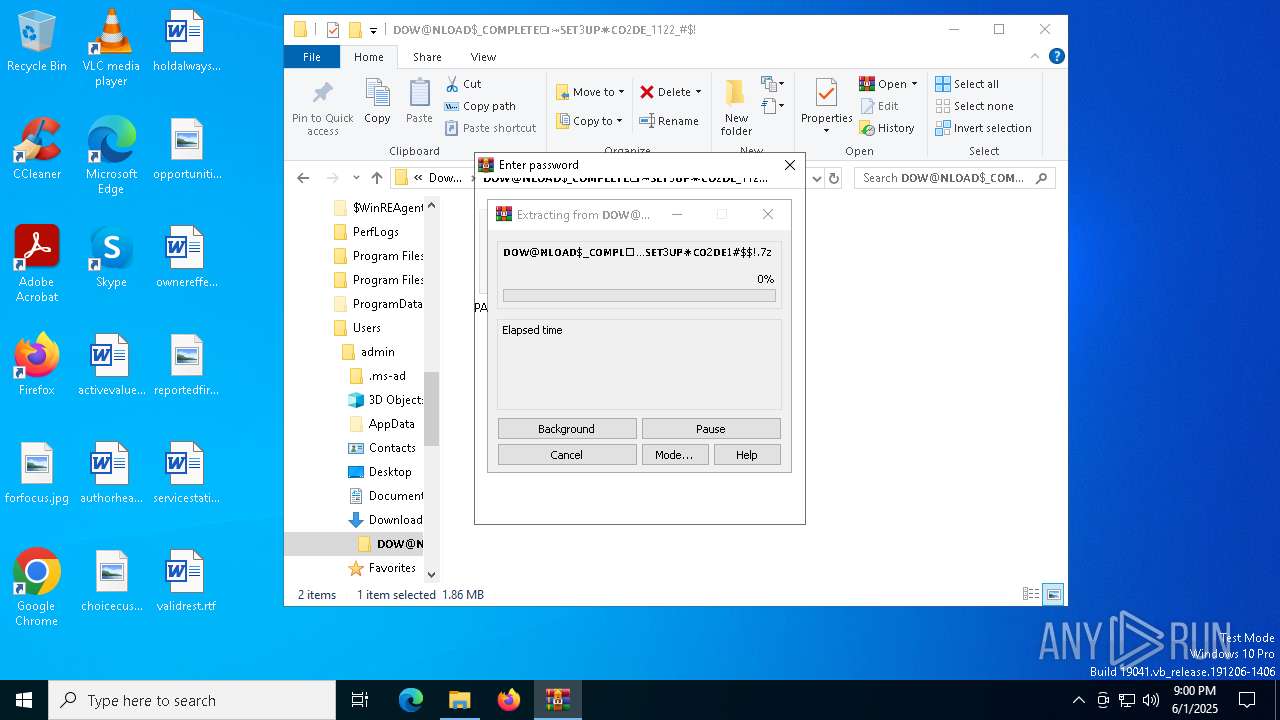
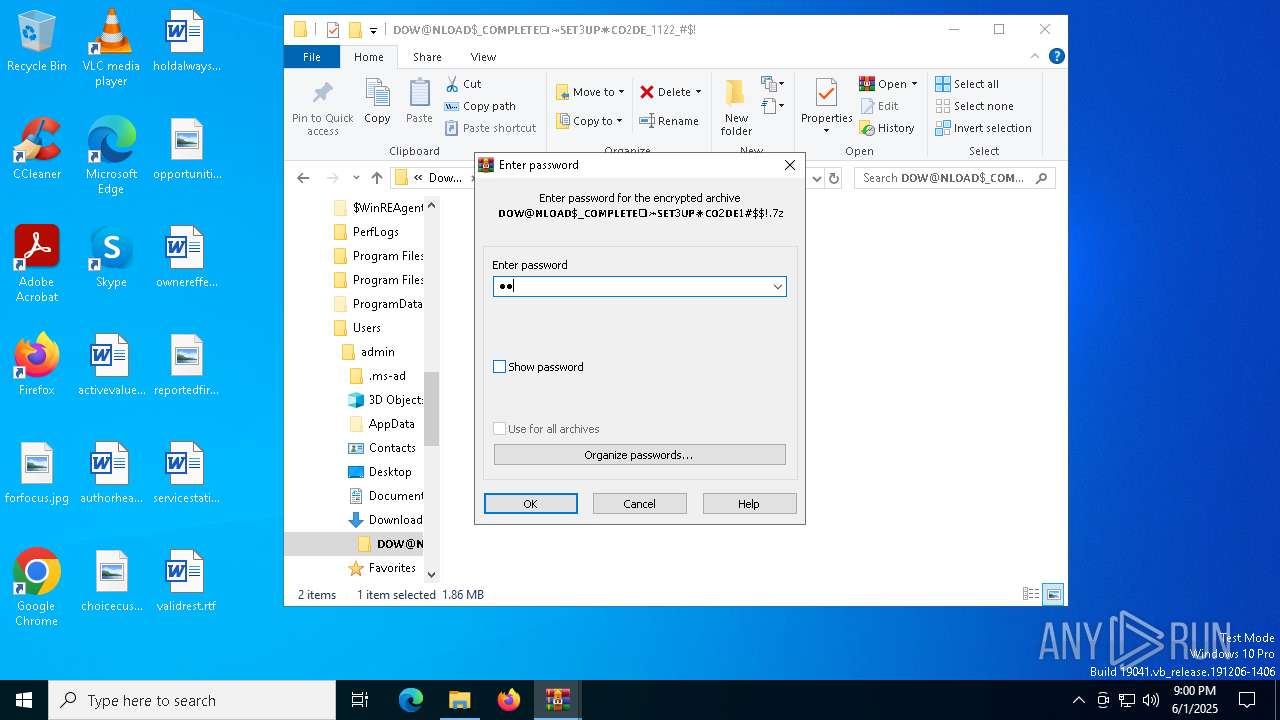
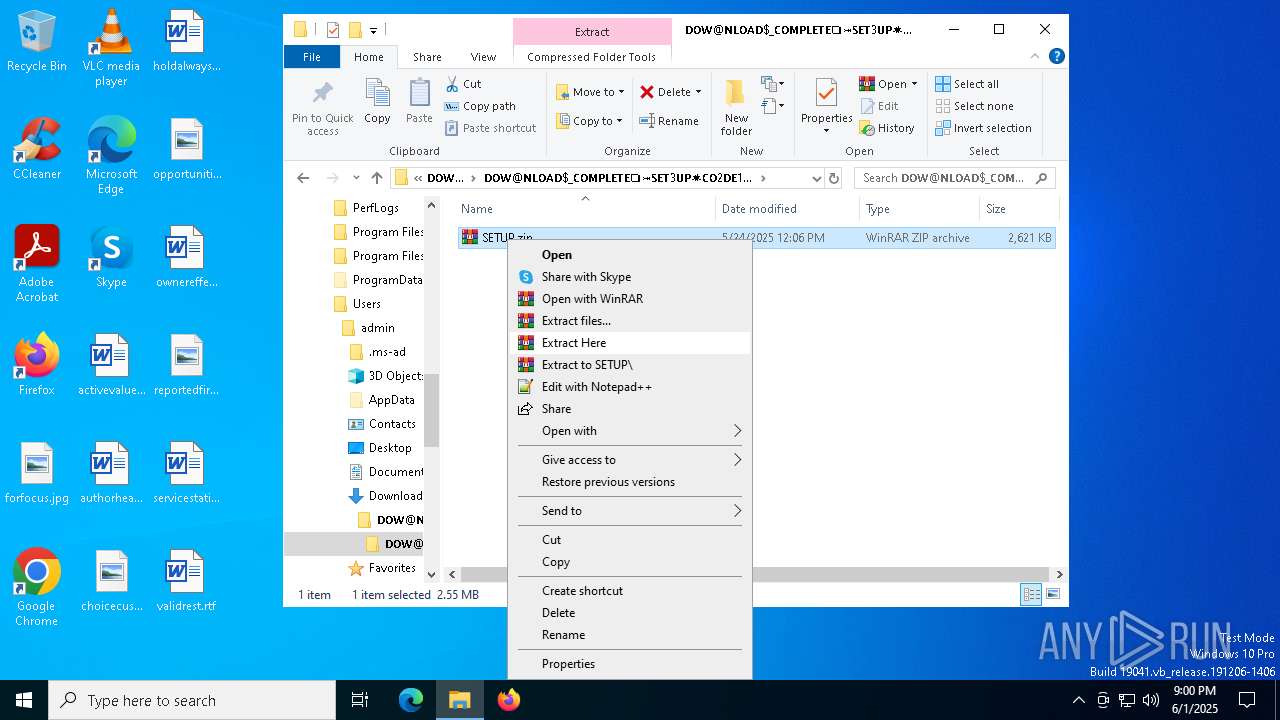
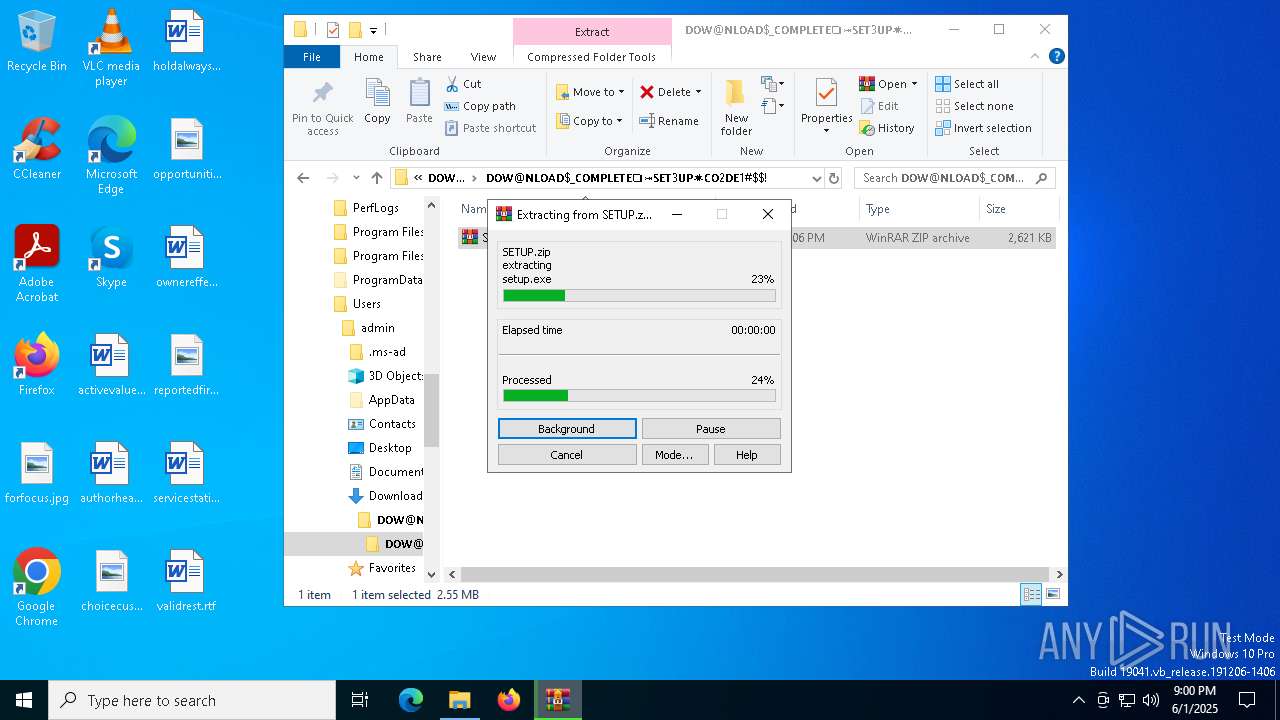
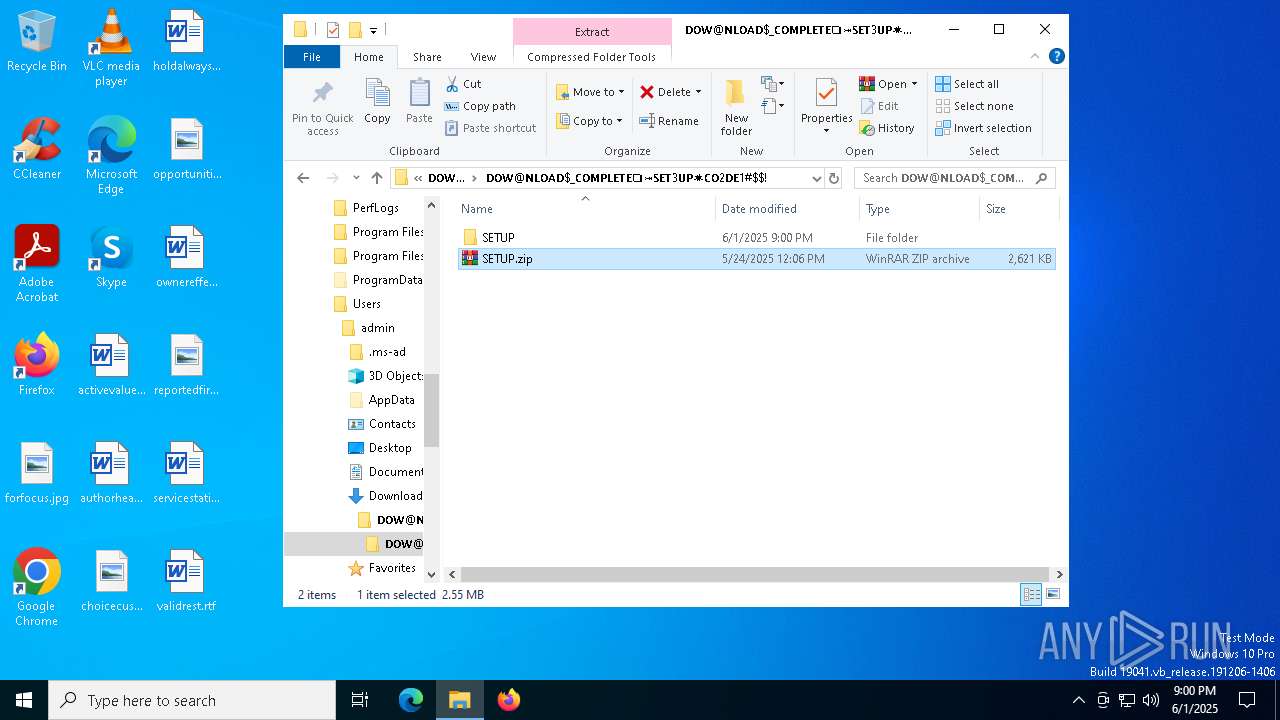
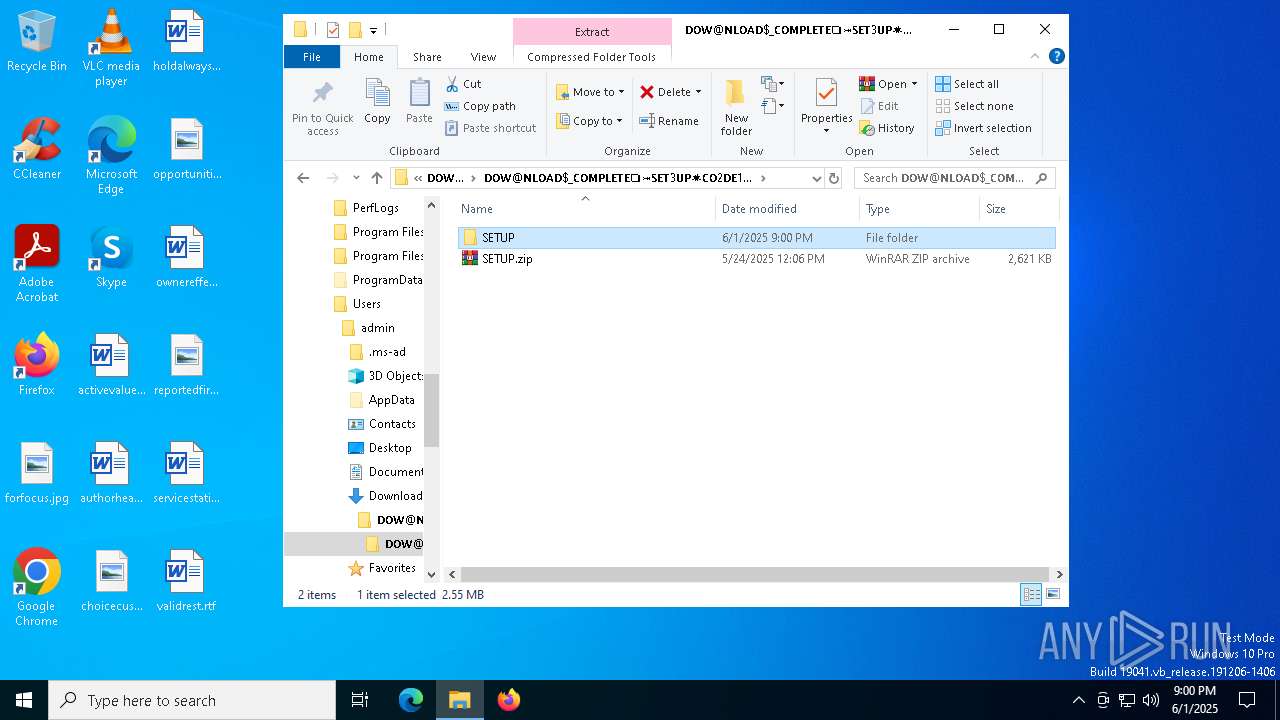
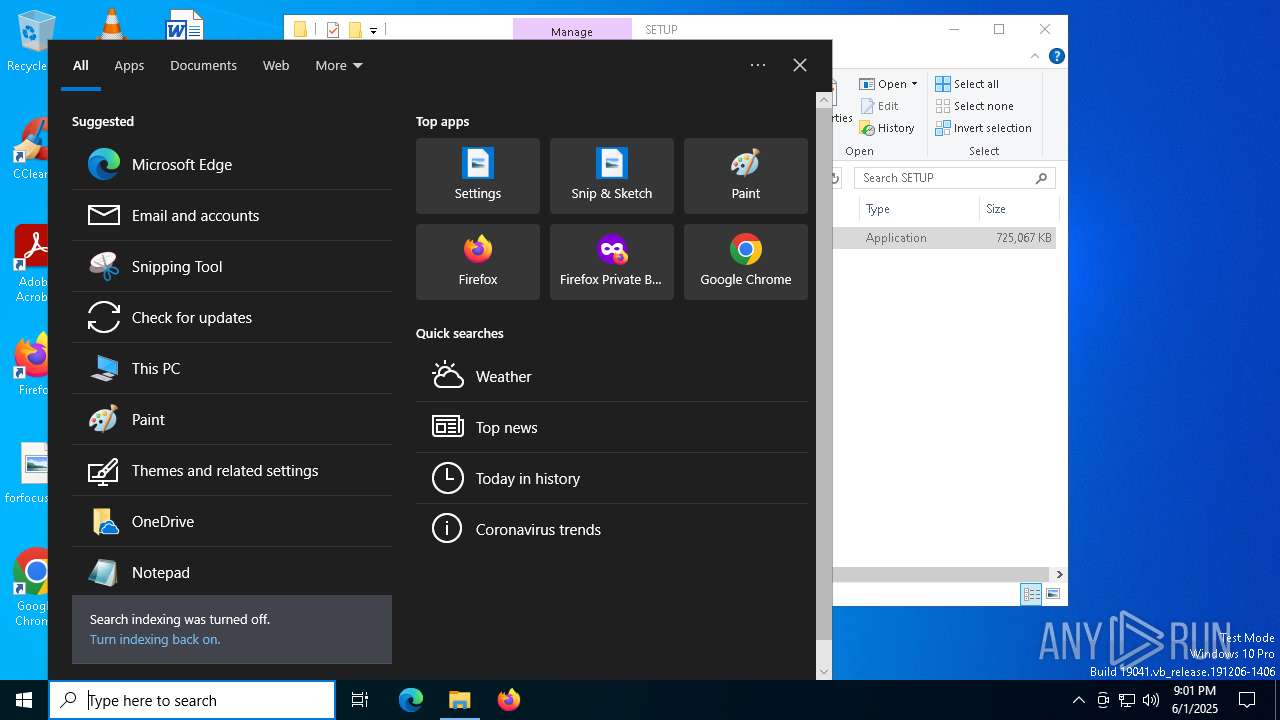
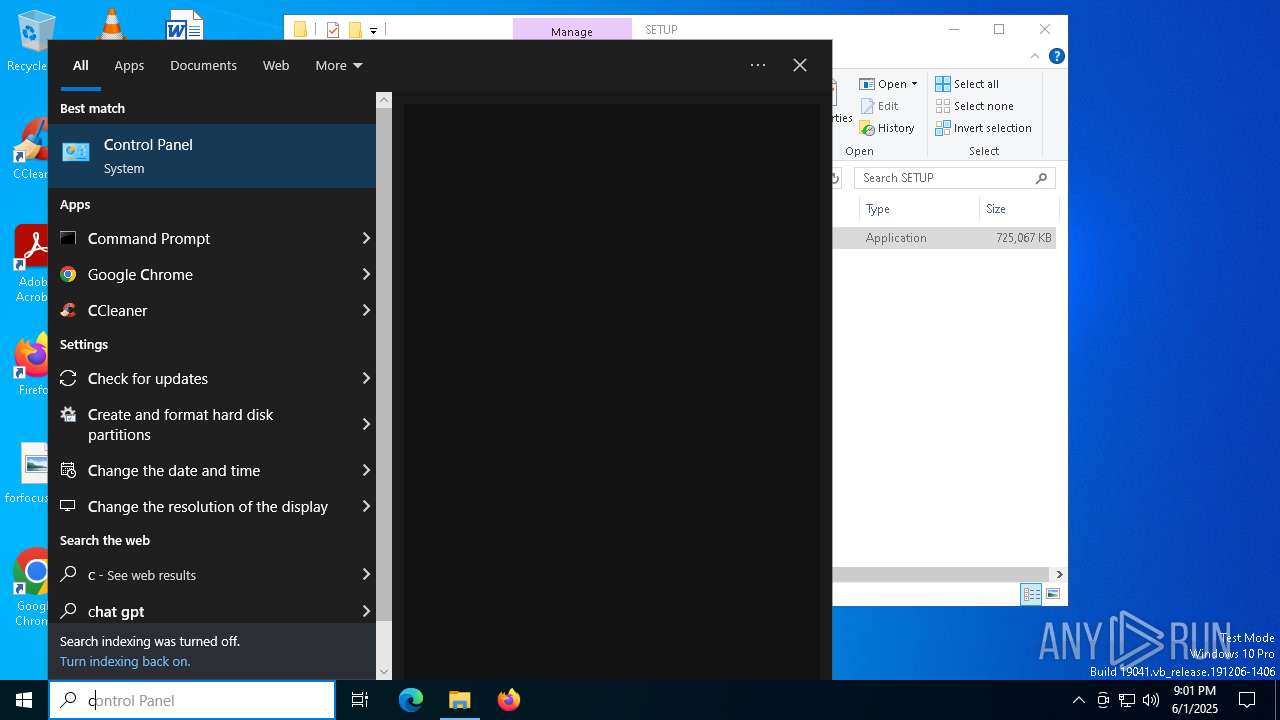
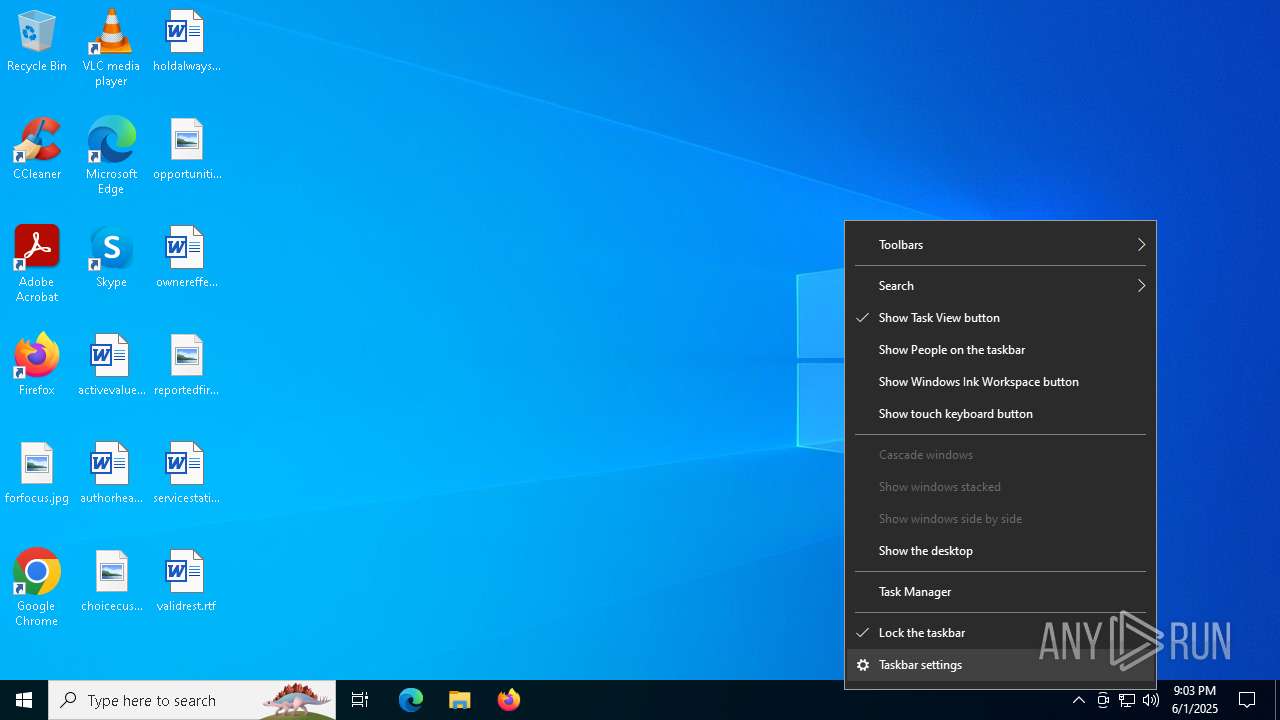
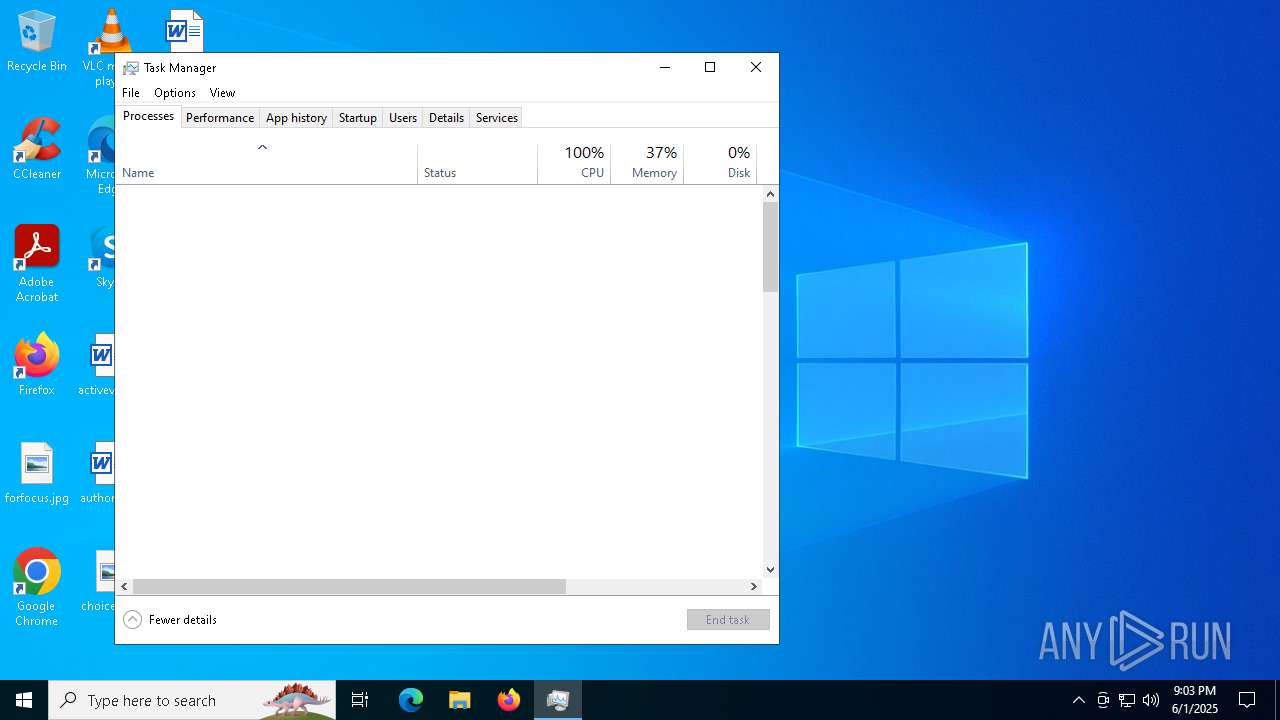
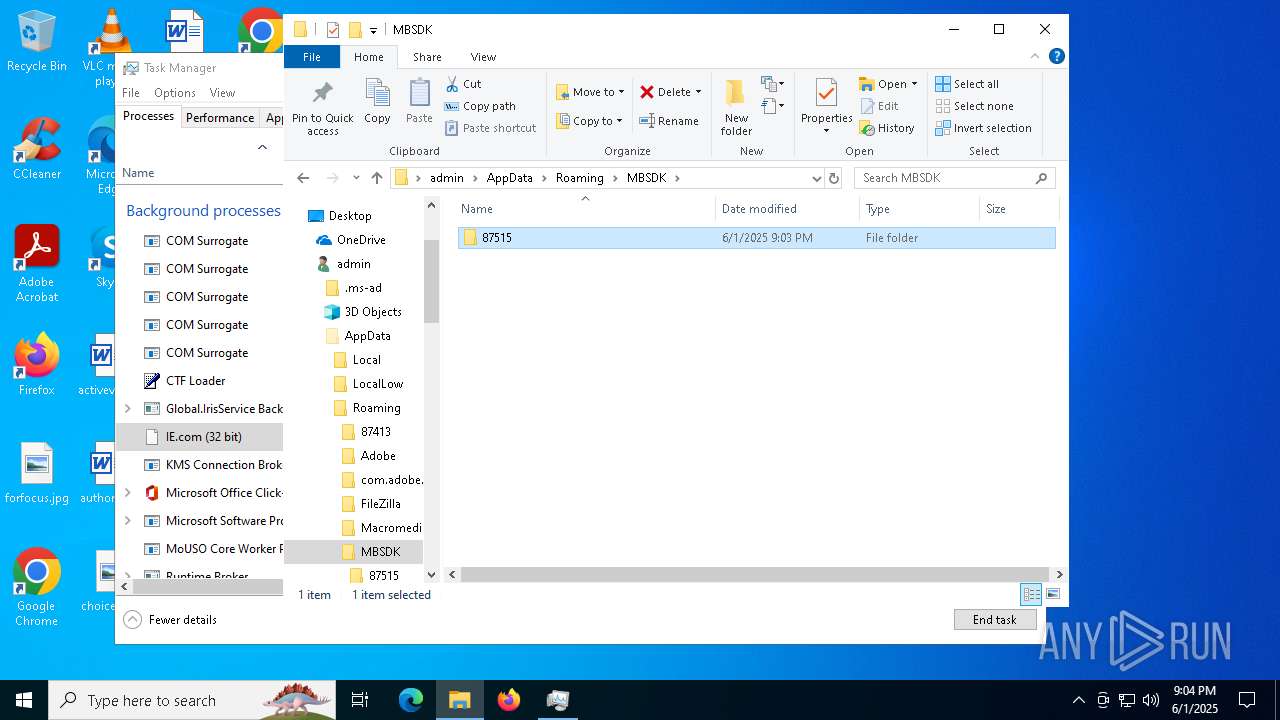
Manual execution by a user
- WinRAR.exe (PID: 5392)
- WinRAR.exe (PID: 7052)
- WinRAR.exe (PID: 1852)
- setup.exe (PID: 5960)
- cmd.exe (PID: 6184)
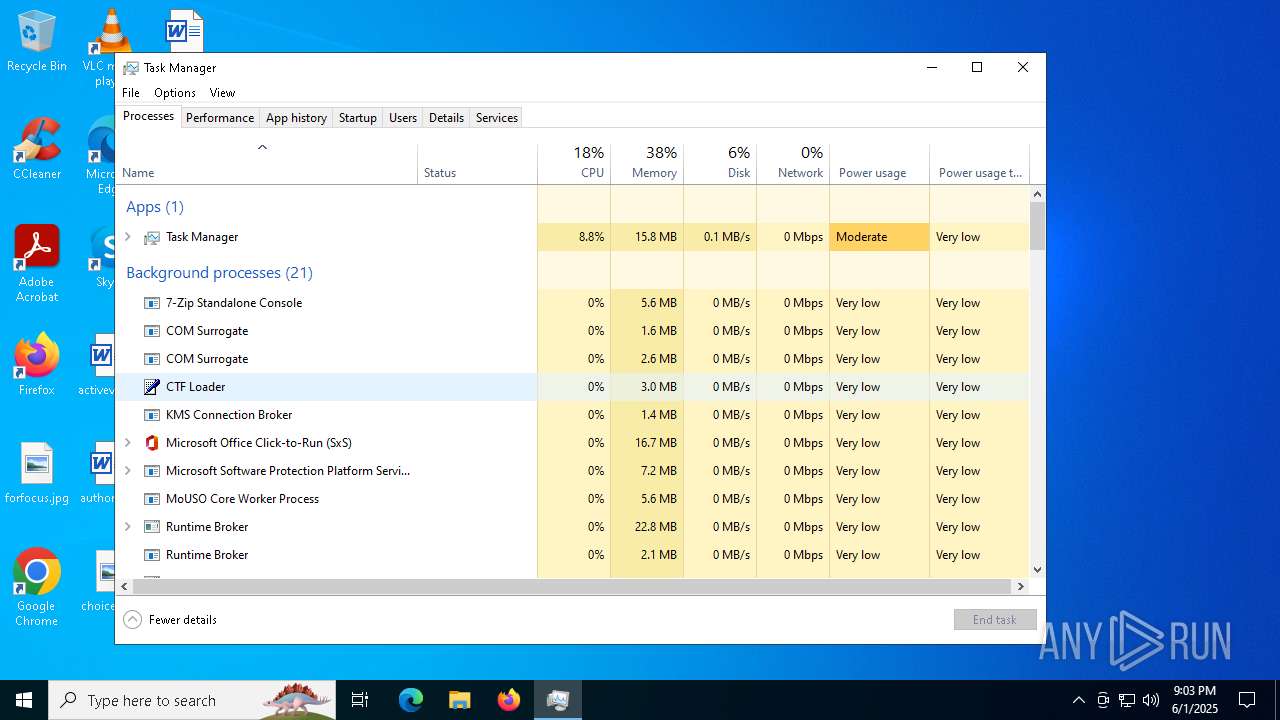
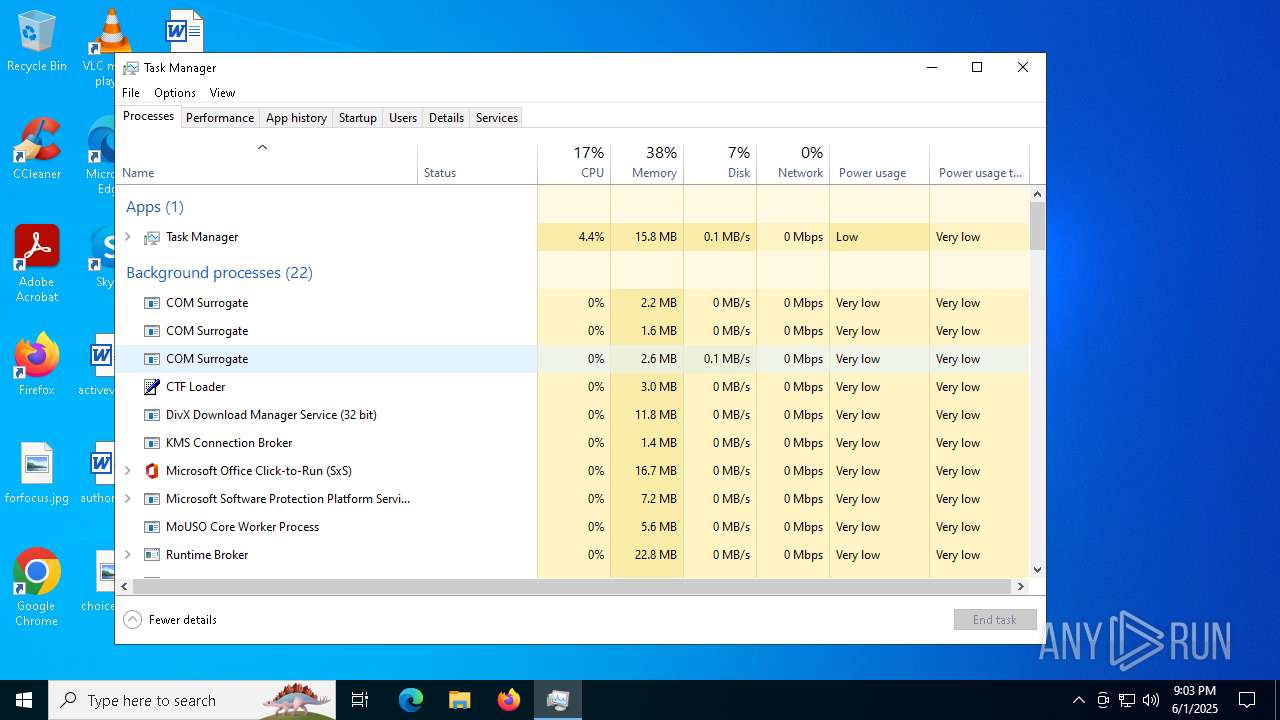
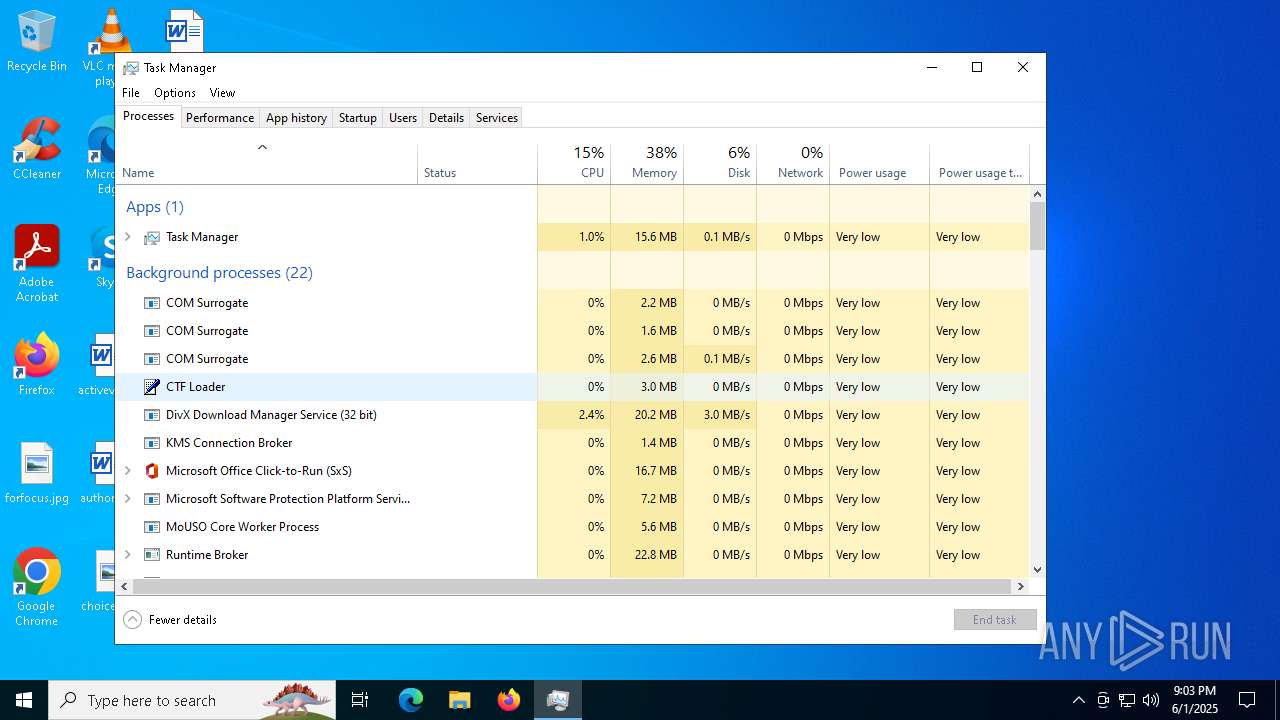
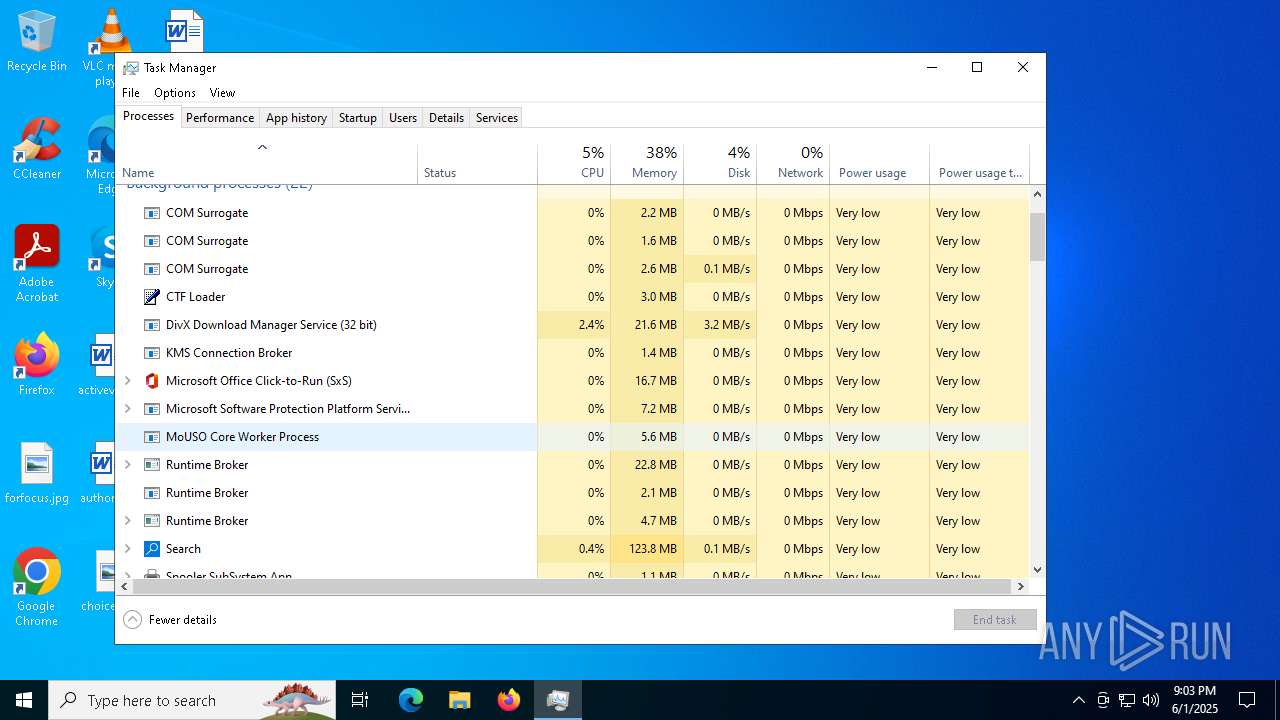
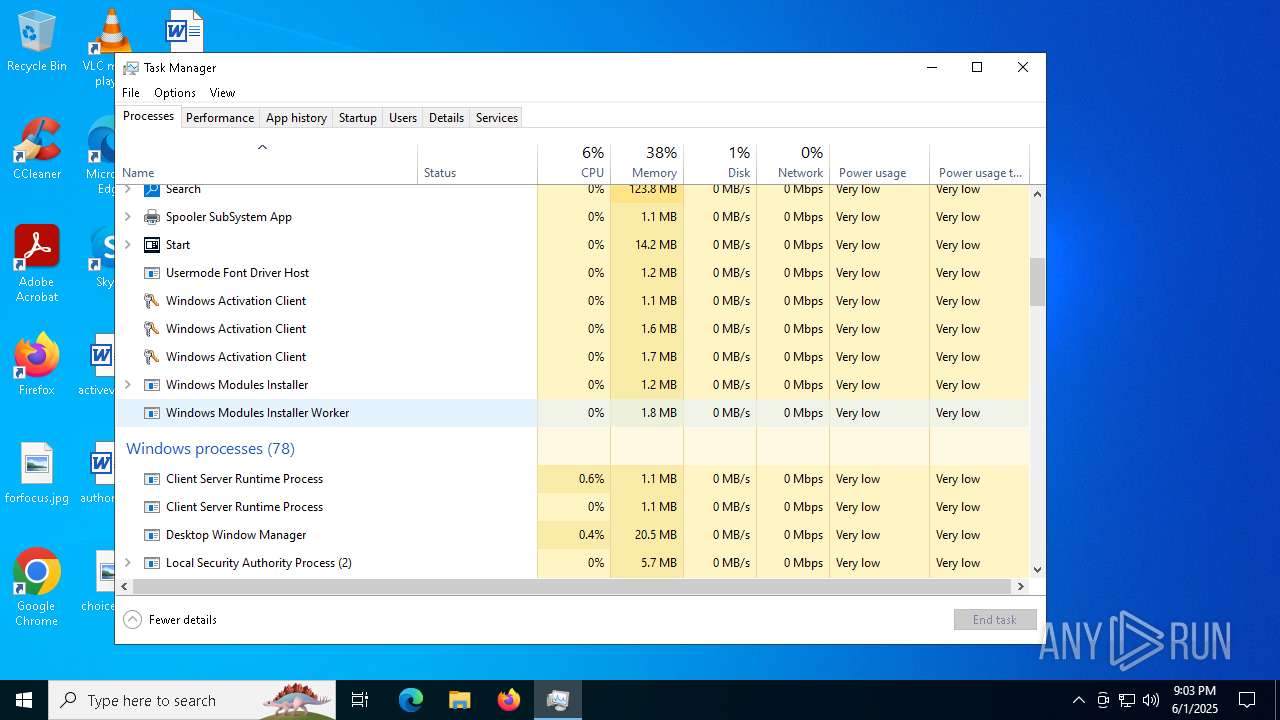
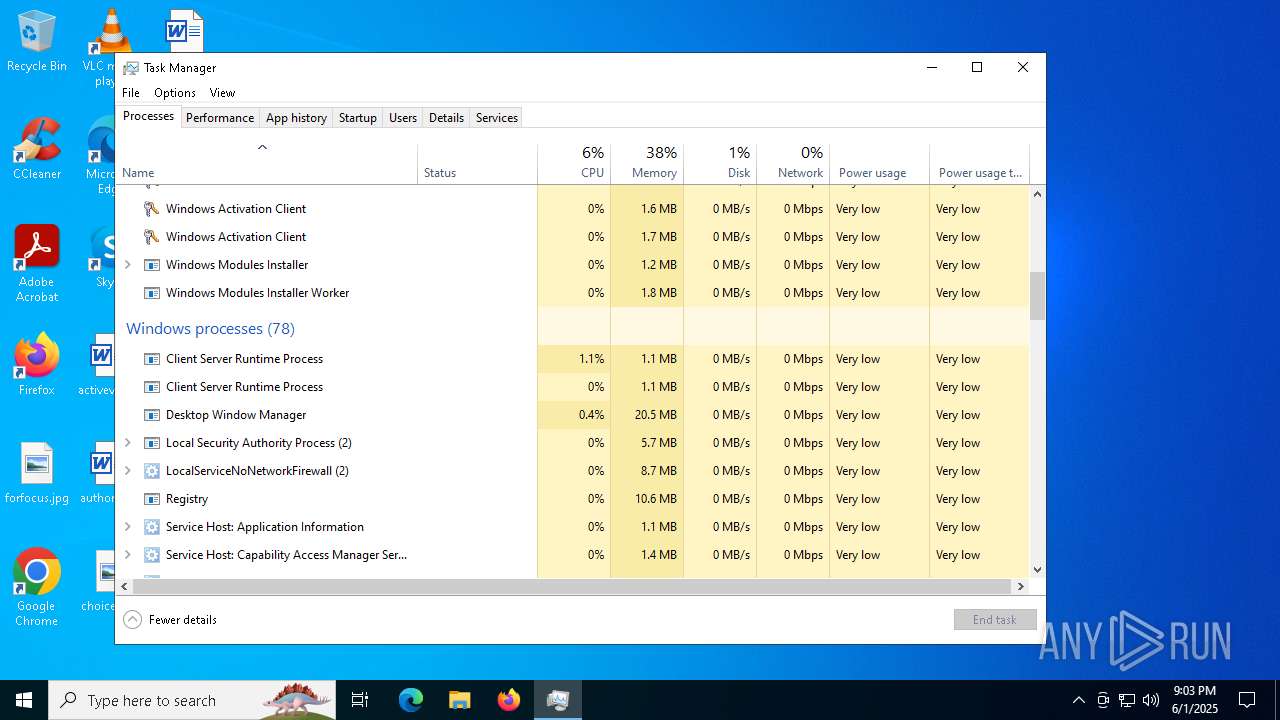
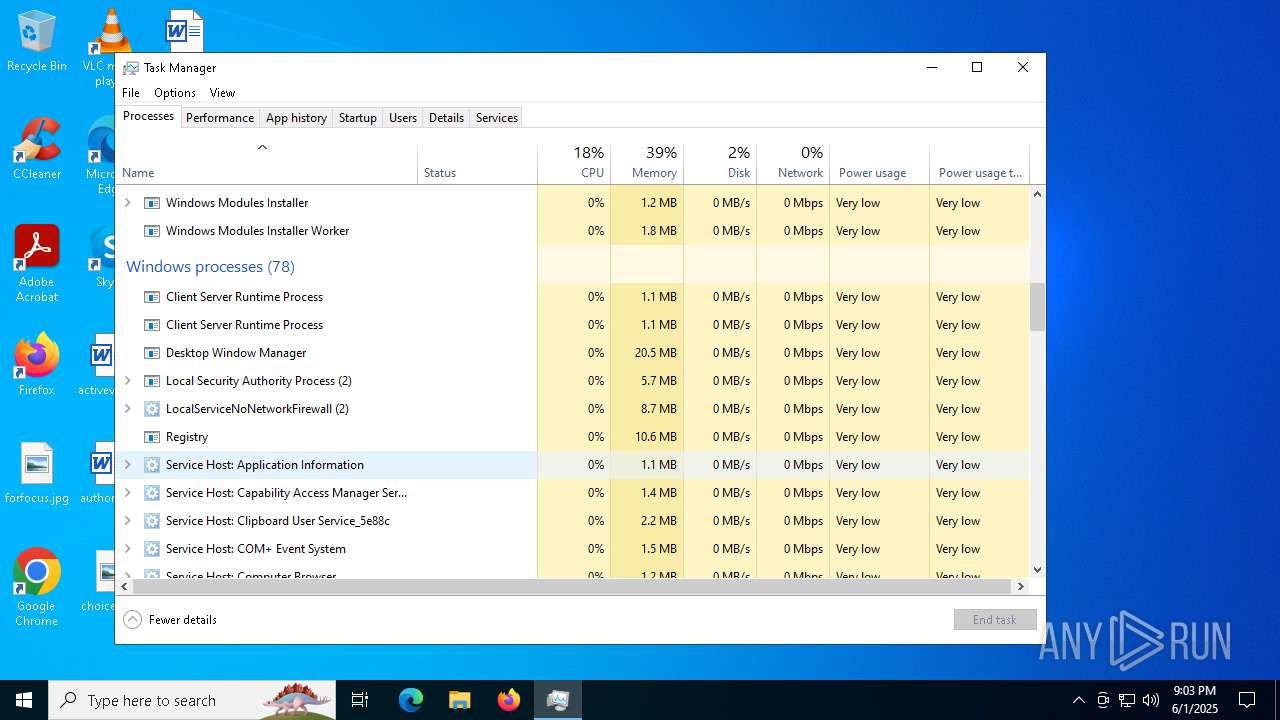
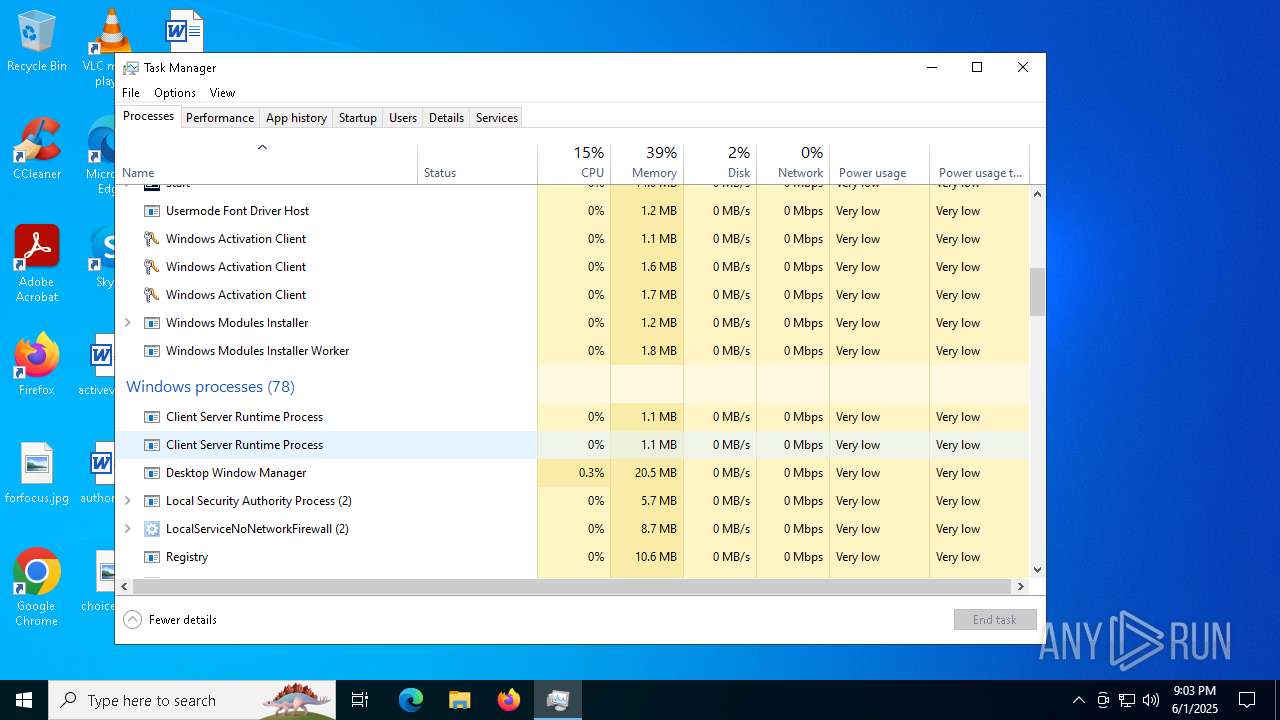
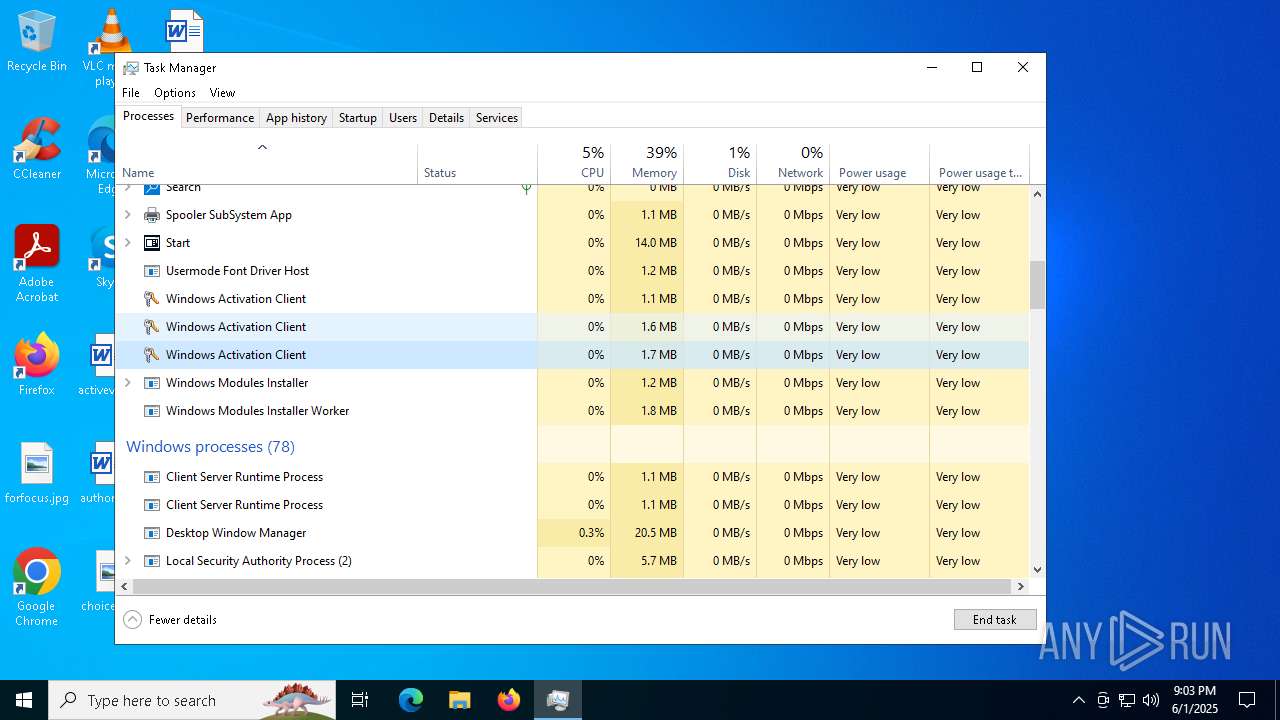
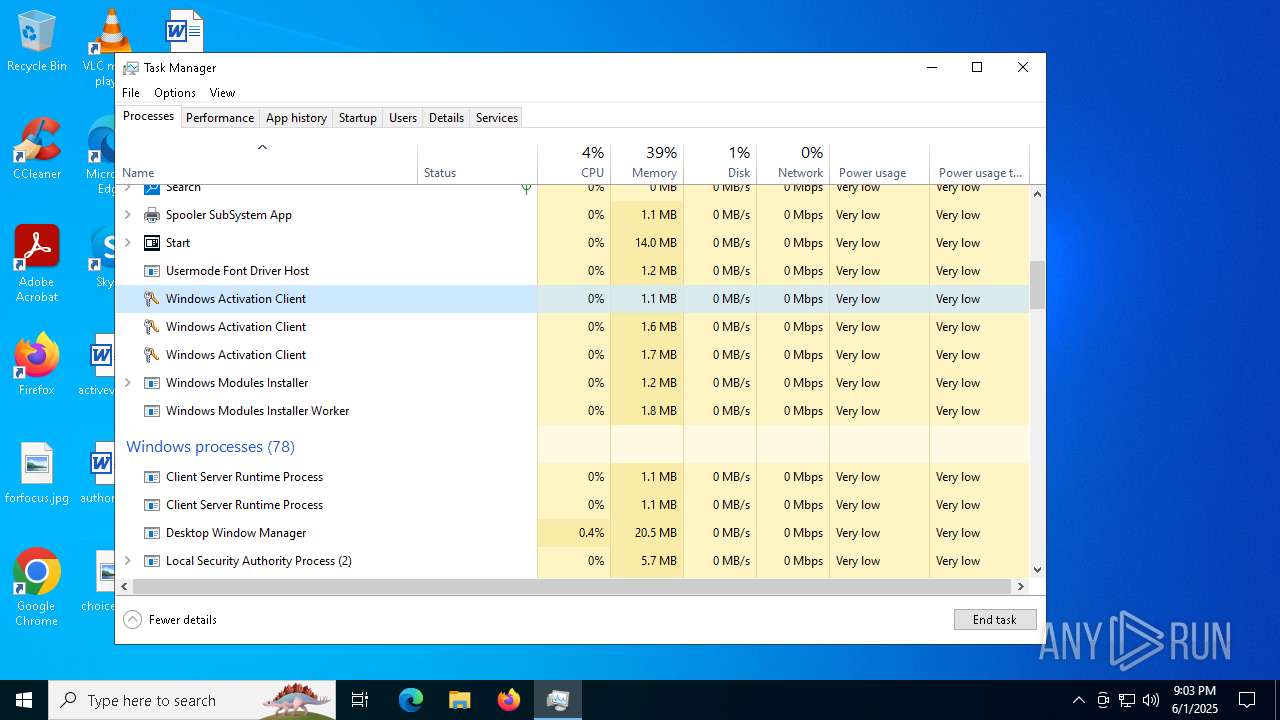
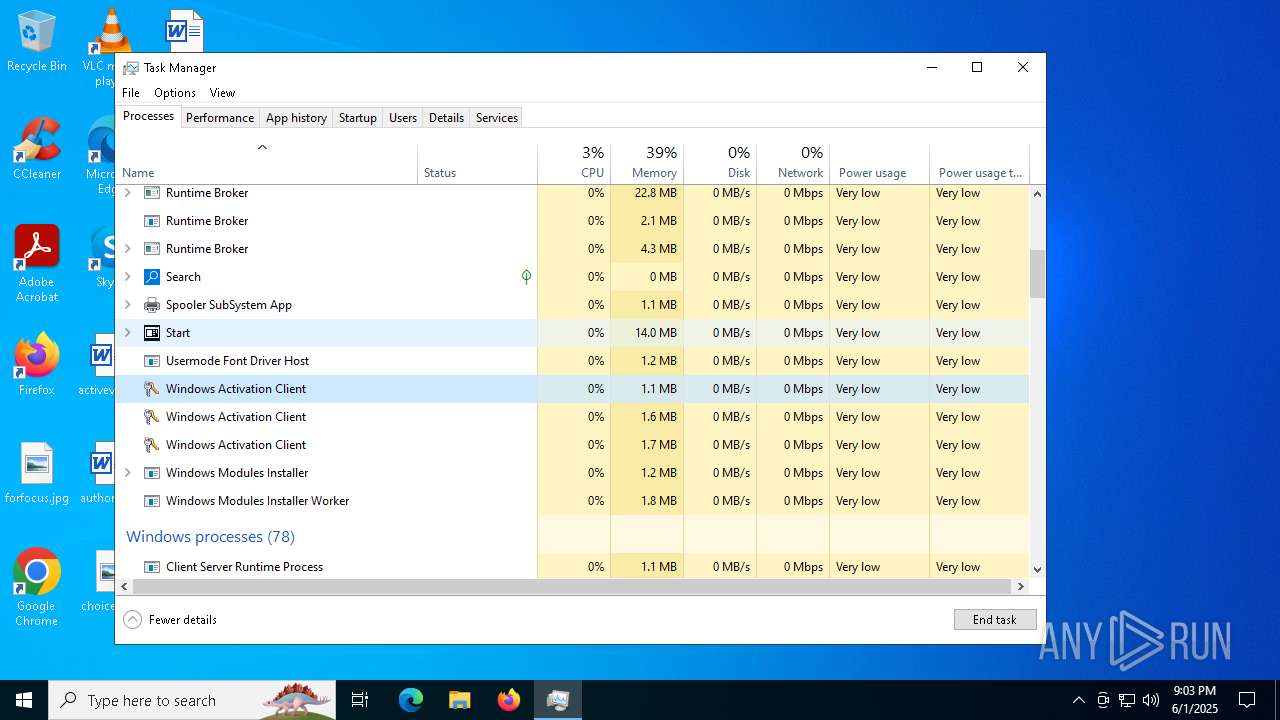
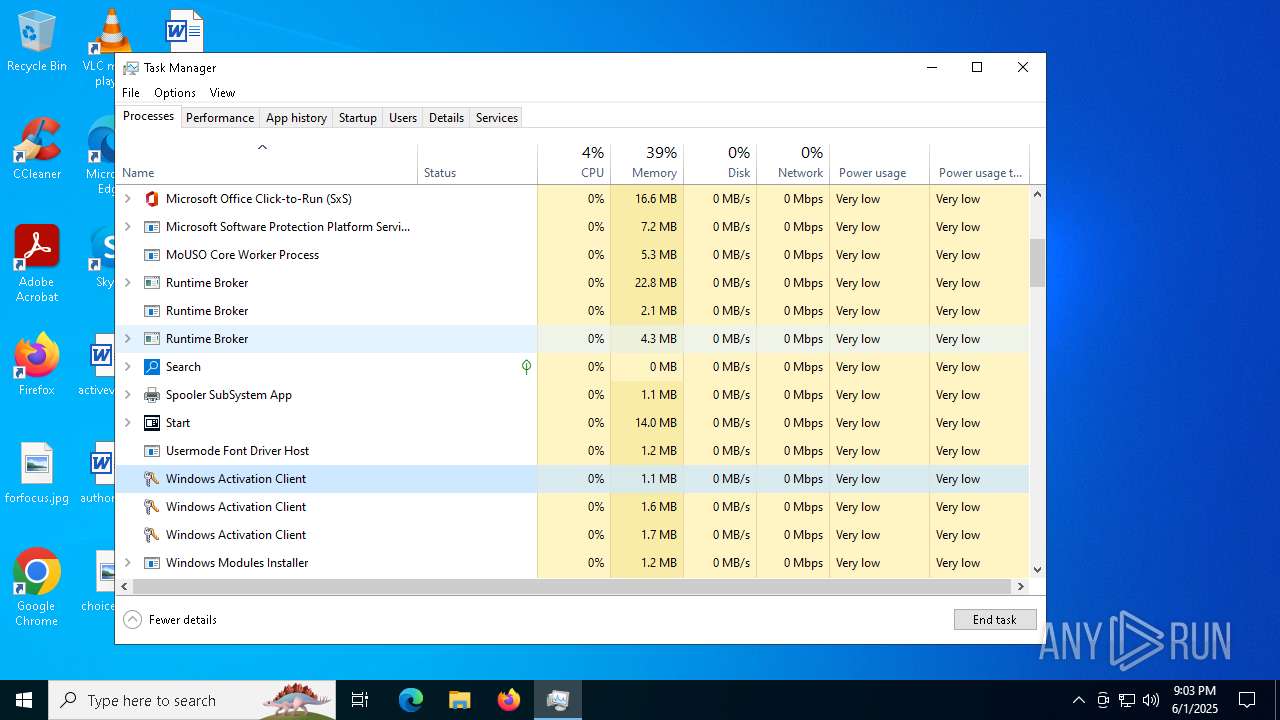
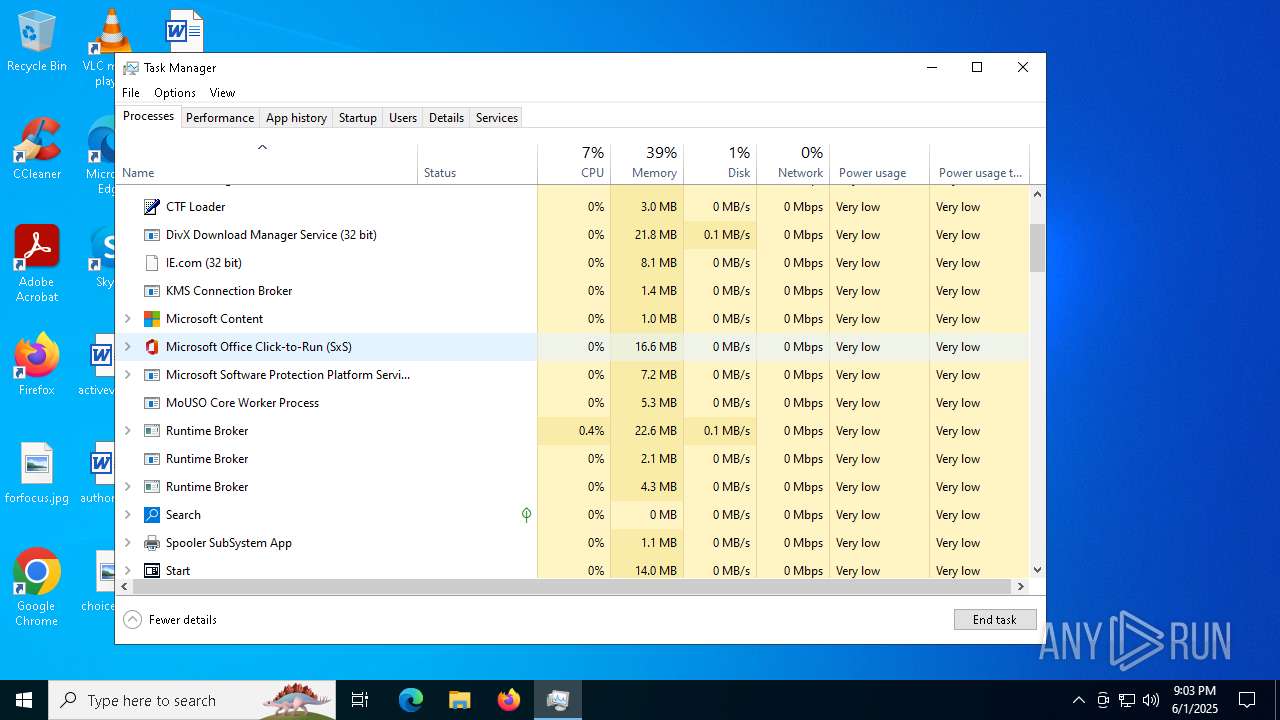
- Taskmgr.exe (PID: 6368)
- Taskmgr.exe (PID: 6452)
Reads the software policy settings
- slui.exe (PID: 6564)
Executes as Windows Service
- elevation_service.exe (PID: 6852)
The sample compiled with english language support
- Nahimic.exe (PID: 5384)
- setup.exe (PID: 5960)
- NahimicSvc64.exe (PID: 7272)
- hjksfjd.exe (PID: 5360)
- MicrosoftEdgeWebview2Setup.exe (PID: 2236)
- explorer.exe (PID: 6028)
- MicrosoftEdgeUpdate.exe (PID: 2868)
- NahimicSvc64.exe (PID: 6696)
- IE.com (PID: 6772)
- MicrosoftEdgeWebview2Setup.exe (PID: 6796)
- MicrosoftEdgeUpdate.exe (PID: 4796)
Compiled with Borland Delphi (YARA)
- conhost.exe (PID: 1764)
- Nahimic.exe (PID: 5384)
- hjksfjd.exe (PID: 5360)
Application based on Golang
- shark.exe (PID: 2800)
Detects GO elliptic curve encryption (YARA)
- shark.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
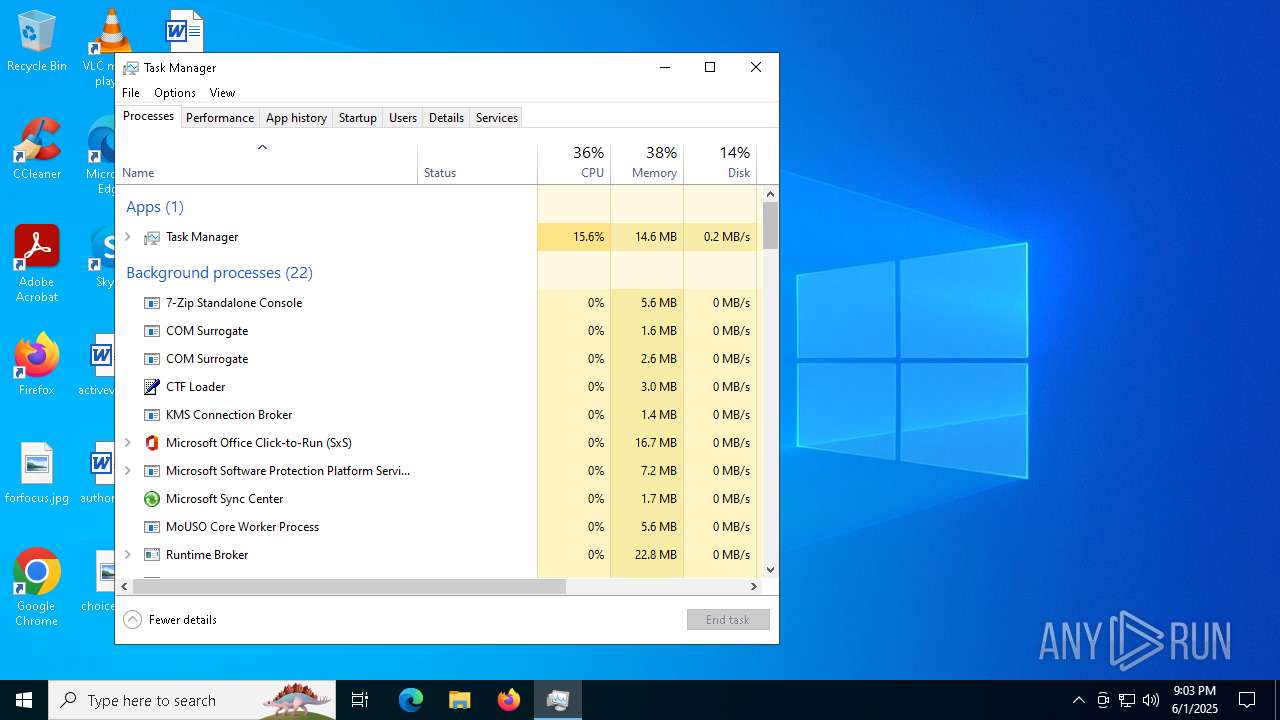
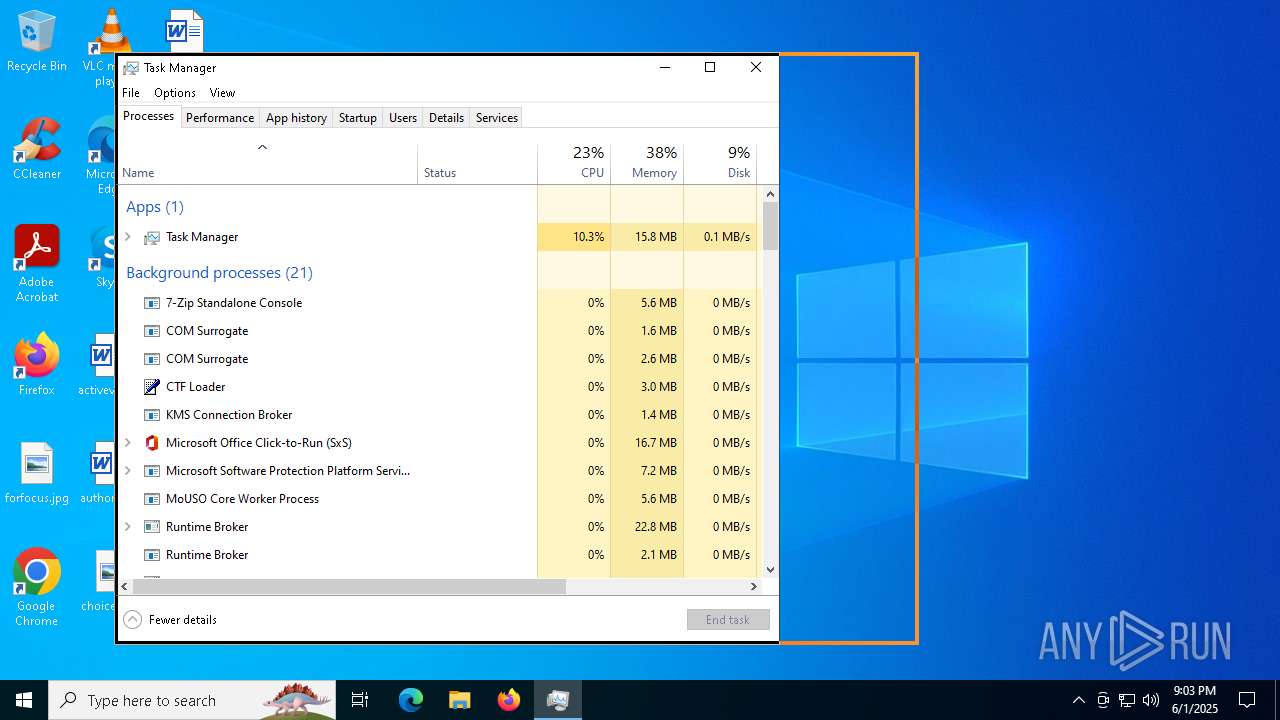
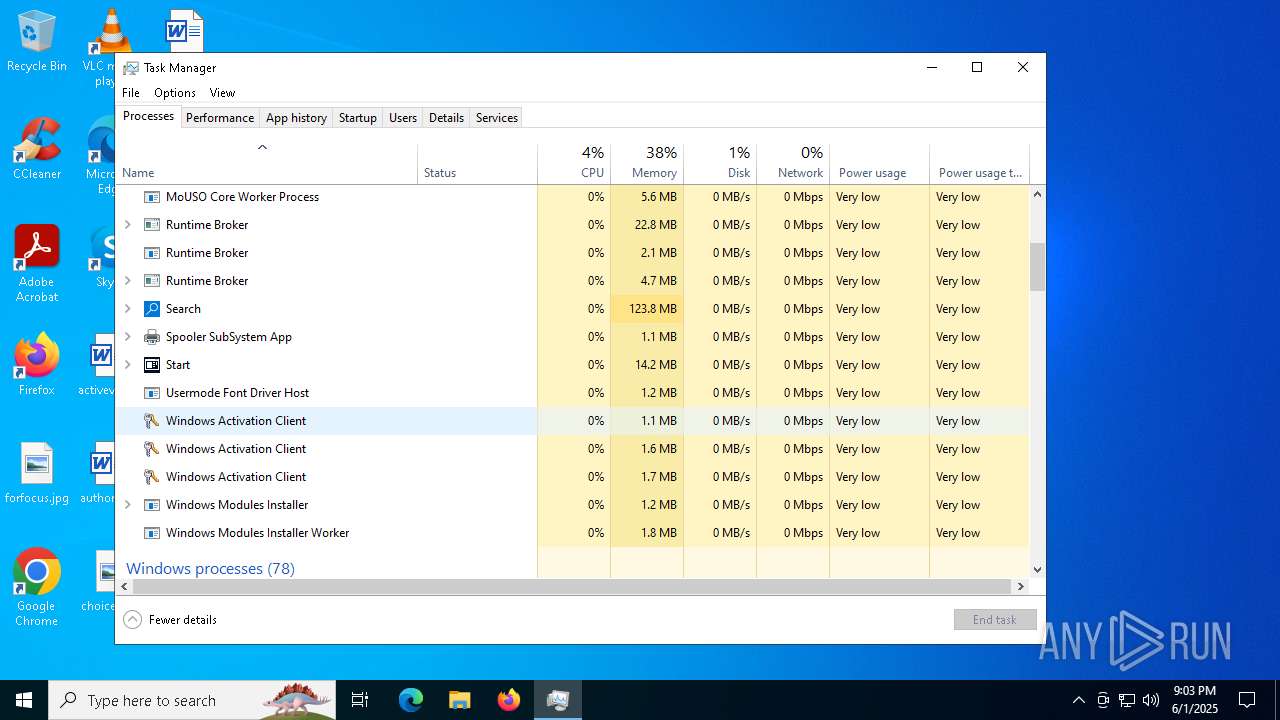
Total processes
428
Monitored processes
142
Malicious processes
13
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | setup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 548 | powershell.exe -Command "Start-Process 'C:\ProgramData\MicrosoftEdgeWebview2Setup.exe' -ArgumentList '/silent','/install' -Wait" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | IE.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2868" "1824" "1744" "1804" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | powershell.exe -Command "Start-Process 'C:\ProgramData\MicrosoftEdgeWebview2Setup.exe' -ArgumentList '/silent','/install' -Wait" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6024 --field-trial-handle=2416,i,12323212889207146418,562820706803972246,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5564 --field-trial-handle=2416,i,12323212889207146418,562820706803972246,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7180 --field-trial-handle=2416,i,12323212889207146418,562820706803972246,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5108 --field-trial-handle=2312,i,509457706338134195,7804282073425421719,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2488 --field-trial-handle=2312,i,509457706338134195,7804282073425421719,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
73 461
Read events
73 286
Write events
169
Delete events
6
Modification events
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7ED5D8351F952F00 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74D7DF351F952F00 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852158 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1F8EA47D-8A25-45F6-B5A4-2A0165C4DF27} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852158 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F71744E0-A3B5-4F41-871E-A4CC02930225} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852158 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {856AD485-EBD8-4ADB-9CA4-F0C50EE1FADC} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852158 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5905C3C7-8101-4C5D-A707-70915983AF99} | |||
Executable files
336
Suspicious files
289
Text files
83
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f46f.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f48e.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f48e.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f4ae.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f4bd.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f4bd.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
216
DNS requests
112
Threats
54
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7636 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5960 | setup.exe | GET | 200 | 104.21.112.1:80 | http://ns.thumbsemifinal.top/caUvXyK.ps1 | unknown | — | — | unknown |
4452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5960 | setup.exe | GET | 200 | 104.21.112.1:80 | http://mi.spokesmangraveyard.top/kernelbase64.bin | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7636 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2600 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3124 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3124 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
3124 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
3124 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |