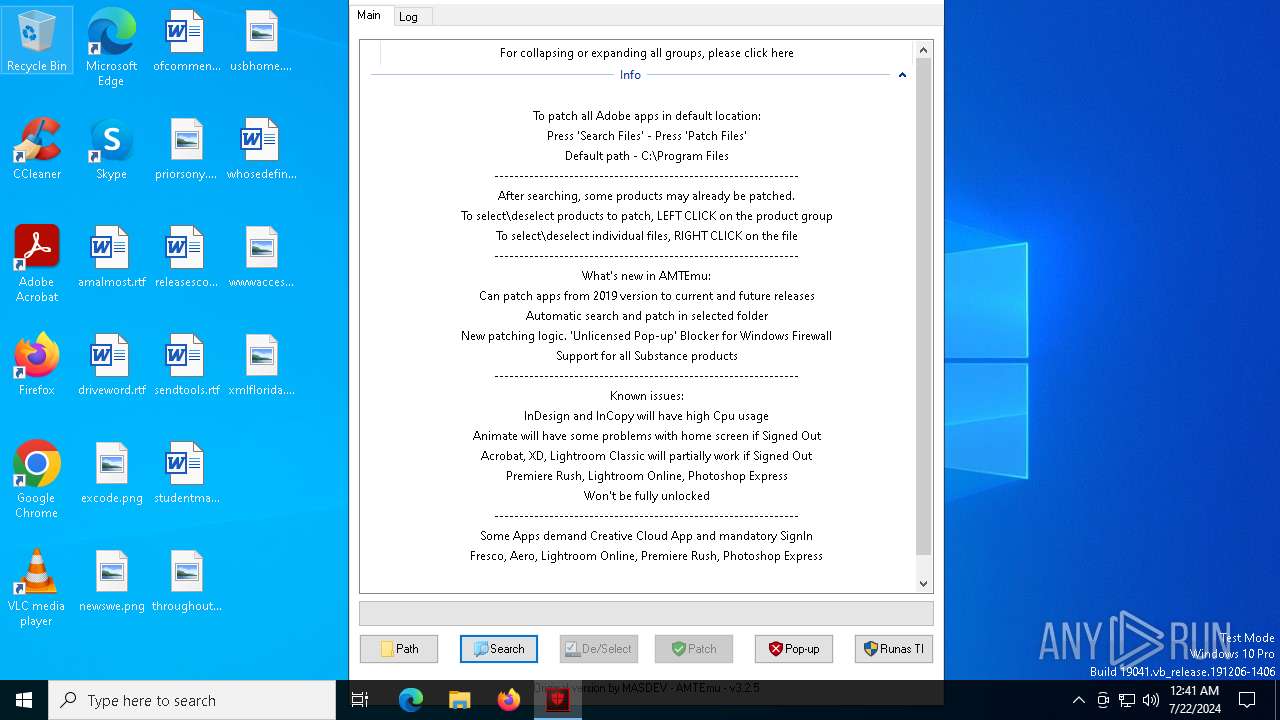
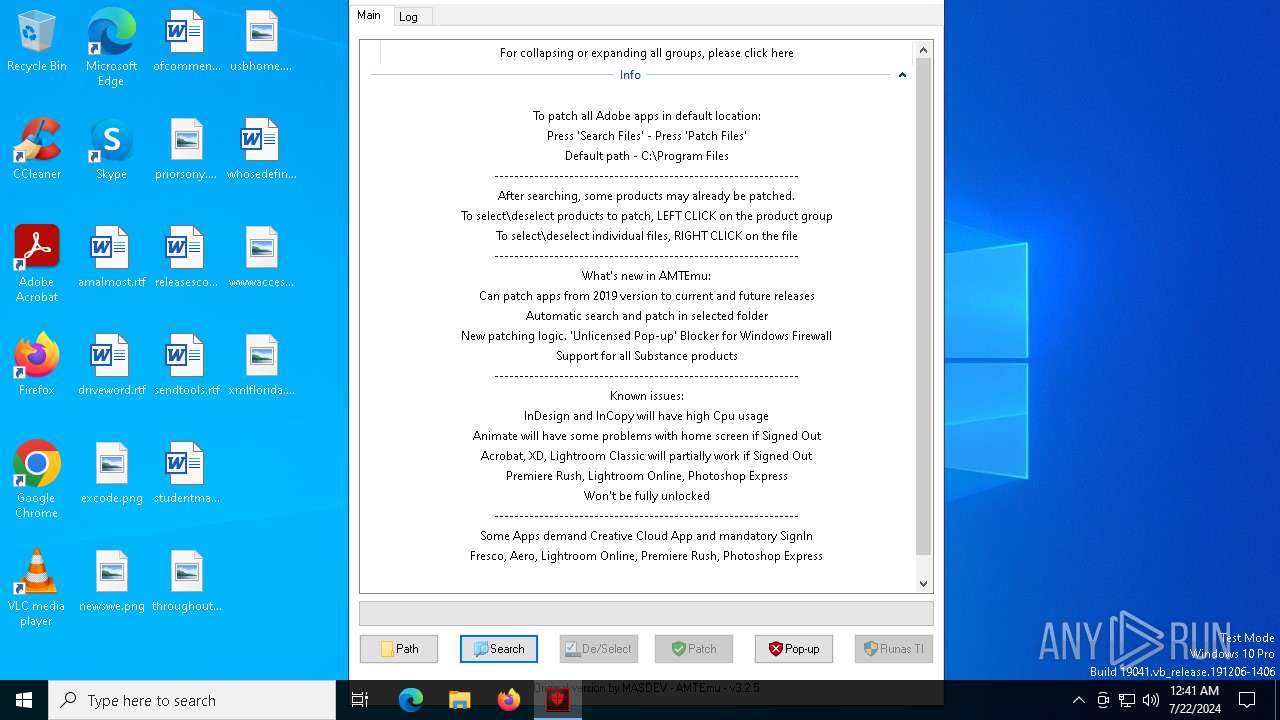
| File name: | AMTEmu-Ai-Universal-Patcher-2024.exe |
| Full analysis: | https://app.any.run/tasks/64ac98a0-da16-40c8-9876-5d44514b1771 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 22, 2024, 00:41:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 071573C639DC9F2806A00357AF45D77F |
| SHA1: | B2060C99741771AFD054C91EB9DAD1FE3D2E74A7 |
| SHA256: | 5FD5E773DE8B468FE02761C000B3B236B978EE638E9C47F90A6E5A599E97C5B2 |
| SSDEEP: | 98304:+9rem5OidPnpnazJQb6eB9ZgE6/vTXSSzzxhuw4rXg+s8Op+eMPV4fyXNnPCAynn:QnhF3 |
MALICIOUS
Drops the executable file immediately after the start
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
- updater.exe (PID: 7332)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 6980)
- cmd.exe (PID: 6240)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 3384)
Modifies hosts file to block updates
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
Adds extension to the Windows Defender exclusion list
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
SILENTCRYPTOMINER has been detected (SURICATA)
- explorer.exe (PID: 1212)
Connects to the CnC server
- explorer.exe (PID: 1212)
SUSPICIOUS
Starts CMD.EXE for commands execution
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6240)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 3384)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6240)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 3384)
- updater.exe (PID: 7332)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
Executable content was dropped or overwritten
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
- updater.exe (PID: 7332)
Application launched itself
- RunAsTI.exe (PID: 4984)
Starts SC.EXE for service management
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
Executes as Windows Service
- updater.exe (PID: 7332)
Process uninstalls Windows update
- wusa.exe (PID: 8084)
- wusa.exe (PID: 7616)
Uses powercfg.exe to modify the power settings
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
Script adds exclusion extension to Windows Defender
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- updater.exe (PID: 7332)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 7332)
Crypto Currency Mining Activity Detected
- explorer.exe (PID: 1212)
Connects to unusual port
- explorer.exe (PID: 1212)
INFO
Checks supported languages
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
- RunAsTI.exe (PID: 4984)
- RunAsTI.exe (PID: 3848)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
- updater.exe (PID: 7332)
- AMTEmu-2024-Universal-Patcher.exe (PID: 3532)
Reads mouse settings
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
Create files in a temporary directory
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
Reads the computer name
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7604)
- RunAsTI.exe (PID: 4984)
- RunAsTI.exe (PID: 3848)
- AMTEmu-Ai-Universal-Patcher-2024.exe (PID: 7660)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7144)
- powershell.exe (PID: 620)
- powershell.exe (PID: 4720)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6868)
Creates files in the program directory
- AMTEmu-2024-Universal-Patcher.exe (PID: 7060)
UPX packer has been detected
- explorer.exe (PID: 1212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:03:04 21:41:00+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 3517440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
216
Monitored processes
77
Malicious processes
5
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | AMTEmu-2024-Universal-Patcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | powershell.exe -Command "Add-MpPreference -ExclusionPath \"C:\", \"C:\Windows\Temp\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | C:\WINDOWS\system32\cmd.exe /c wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\cmd.exe | — | AMTEmu-2024-Universal-Patcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | explorer.exe | C:\Windows\explorer.exe | updater.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramData) -ExclusionExtension '.exe' -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AMTEmu-2024-Universal-Patcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | C:\WINDOWS\system32\sc.exe start "GoogleUpdateTaskMachineQC" | C:\Windows\System32\sc.exe | — | AMTEmu-2024-Universal-Patcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1053 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 467
Read events
41 441
Write events
26
Delete events
0
Modification events
| (PID) Process: | (4720) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4720) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4720) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4720) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6268) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6268) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6268) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6268) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7060) AMTEmu-2024-Universal-Patcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
| (PID) Process: | (6868) powershell.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
9
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | AMTEmu-Ai-Universal-Patcher-2024.exe | C:\Users\admin\AppData\Local\Temp\autAA0A.tmp | executable | |
MD5:D671C0A5E92F558A41156FA2C2E0C5E0 | SHA256:2A7CEF29B364D8C5ED6A185B4722489CCFA73B6FE545DB628ACDC281C45BC528 | |||
| 620 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v1isqvn4.usf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7604 | AMTEmu-Ai-Universal-Patcher-2024.exe | C:\Users\admin\AppData\Local\Temp\autAB91.tmp | binary | |
MD5:30C40F60A224AB7566F3056B11FD8748 | SHA256:5E4A61BF72EA2345DC0B4A12815F8F346AA13754D67F0F635F7446CB5760ECF4 | |||
| 6268 | powershell.exe | C:\WINDOWS\TEMP\__PSScriptPolicyTest_jssrtg4v.vhj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nmujc0hn.wnn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7604 | AMTEmu-Ai-Universal-Patcher-2024.exe | C:\Users\admin\AppData\Local\Temp\config.ini | ini | |
MD5:78CE4F67BC103A49D5C626D666709421 | SHA256:EA88F7092328BB76B5650CC815097F148D31F43FD2356D0407D560474920B48B | |||
| 7604 | AMTEmu-Ai-Universal-Patcher-2024.exe | C:\Windows\Temp\AMTEmu-2024-Universal-Patcher.exe | executable | |
MD5:D671C0A5E92F558A41156FA2C2E0C5E0 | SHA256:2A7CEF29B364D8C5ED6A185B4722489CCFA73B6FE545DB628ACDC281C45BC528 | |||
| 6268 | powershell.exe | C:\WINDOWS\TEMP\__PSScriptPolicyTest_pwn3wkbq.kml.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6268 | powershell.exe | C:\WINDOWS\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A583E2A51BFBDC1E492A57B7C8325850 | binary | |
MD5:355FC7923FAFD8CAC4127F916D2406A7 | SHA256:6601A48C7B95CED12510D19D36F86345F7F712D8154D53FA27493D02CC70D7B8 | |||
| 4720 | powershell.exe | C:\WINDOWS\TEMP\__PSScriptPolicyTest_s2fww3ah.24t.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
40
DNS requests
14
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1212 | explorer.exe | POST | 200 | 38.180.0.98:7891 | http://38.180.0.98:7891/api/endpoint.php | unknown | — | — | unknown |
1212 | explorer.exe | POST | 200 | 38.180.0.98:7891 | http://38.180.0.98:7891/api/endpoint.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7856 | svchost.exe | 4.209.32.198:443 | licensing.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3404 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4716 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5460 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1212 | explorer.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M3 |
1212 | explorer.exe | A Network Trojan was detected | ET MALWARE SilentCryptoMiner Agent Config Inbound |
1212 | explorer.exe | Crypto Currency Mining Activity Detected | ET MALWARE [ANY.RUN] SilentCryptoMiner Check-in POST Request |
1212 | explorer.exe | A Network Trojan was detected | ET MALWARE SilentCryptoMiner Agent Config Inbound |
1212 | explorer.exe | Crypto Currency Mining Activity Detected | MINER [ANY.RUN] SilentCryptoMiner HTTP Request to UnamWebPanel |