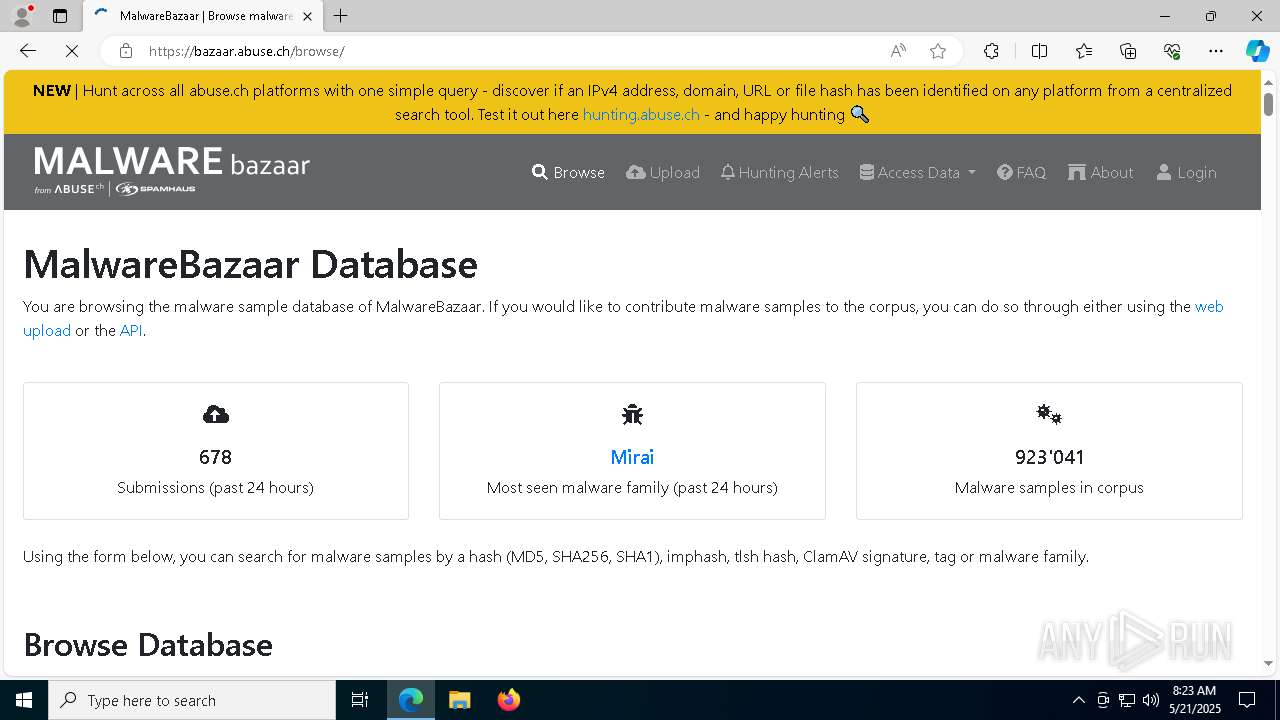
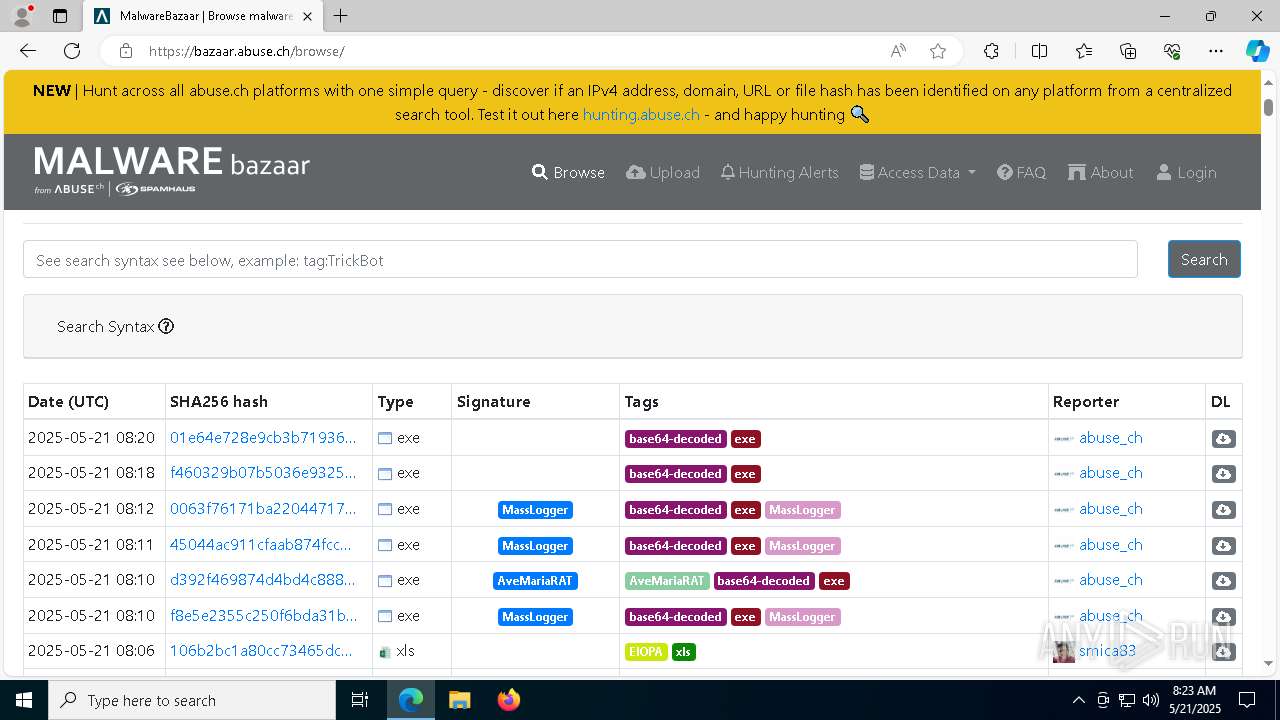
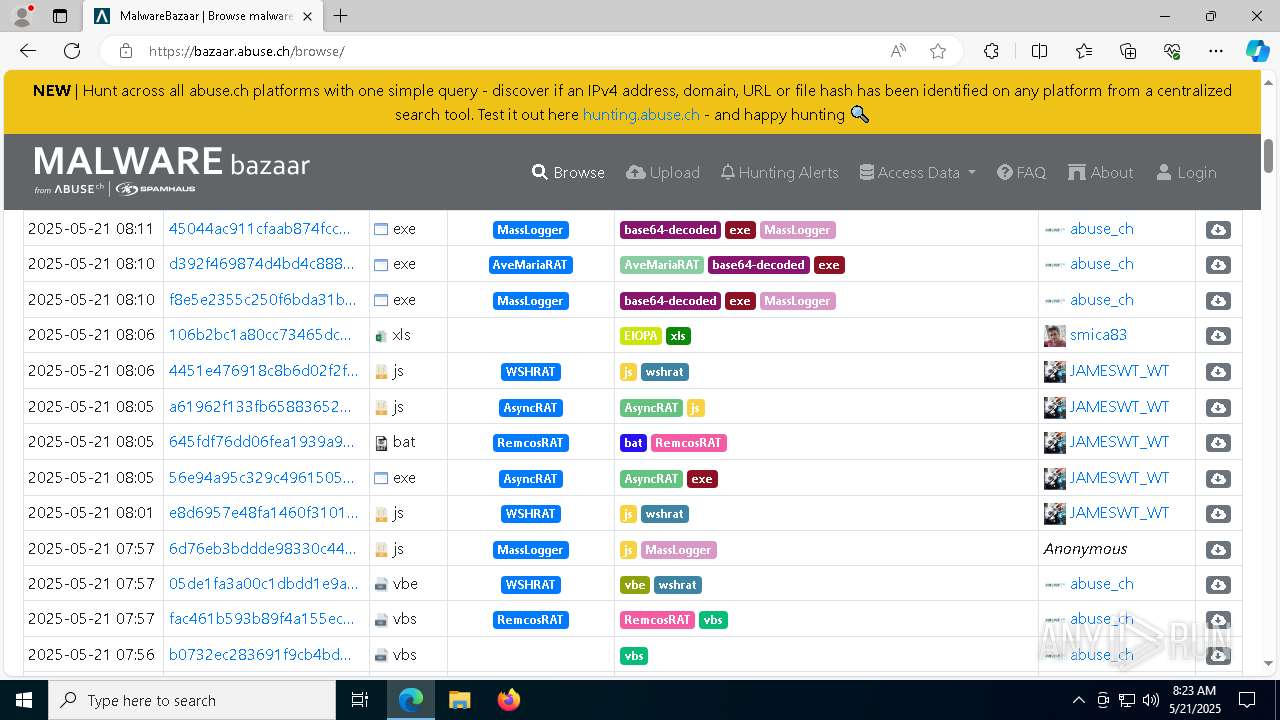
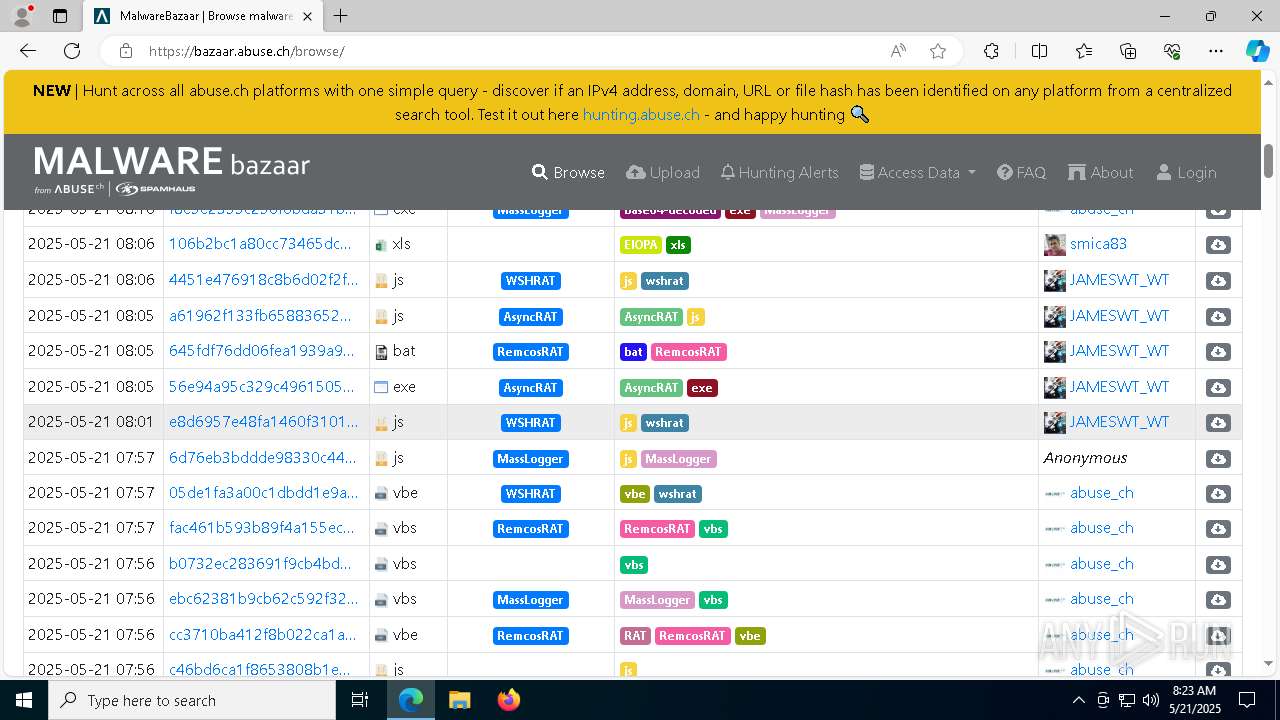
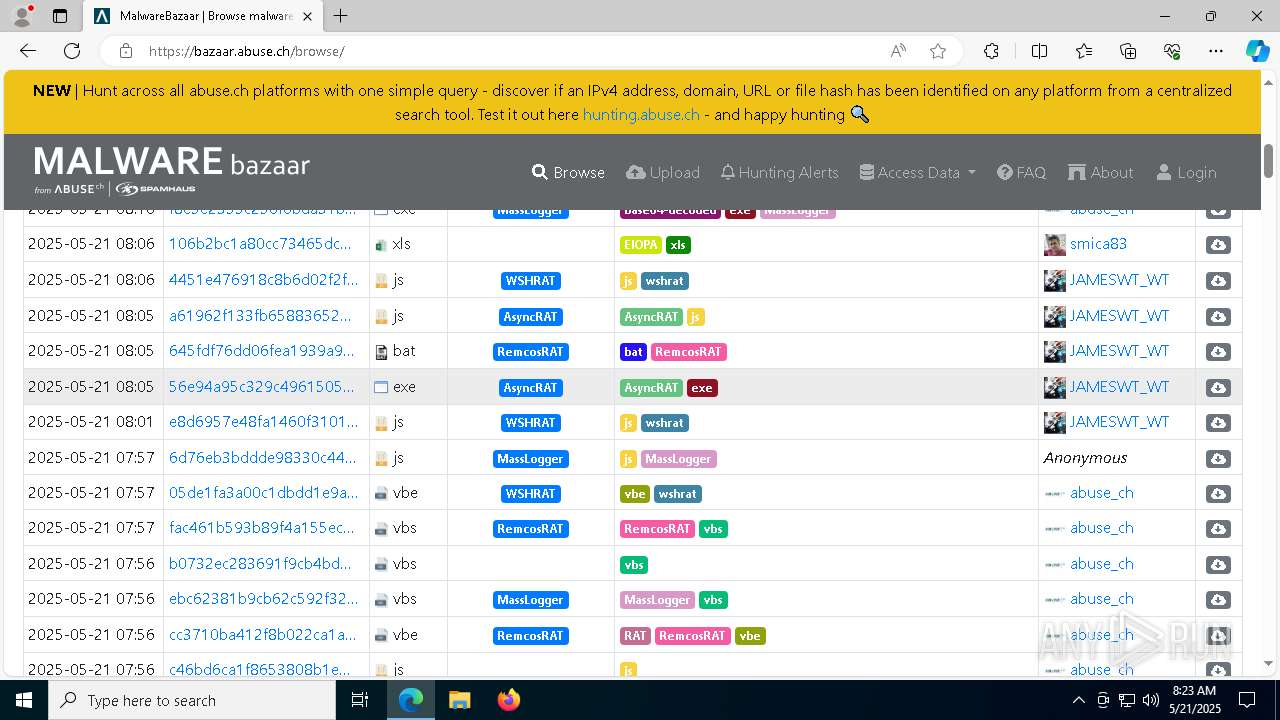
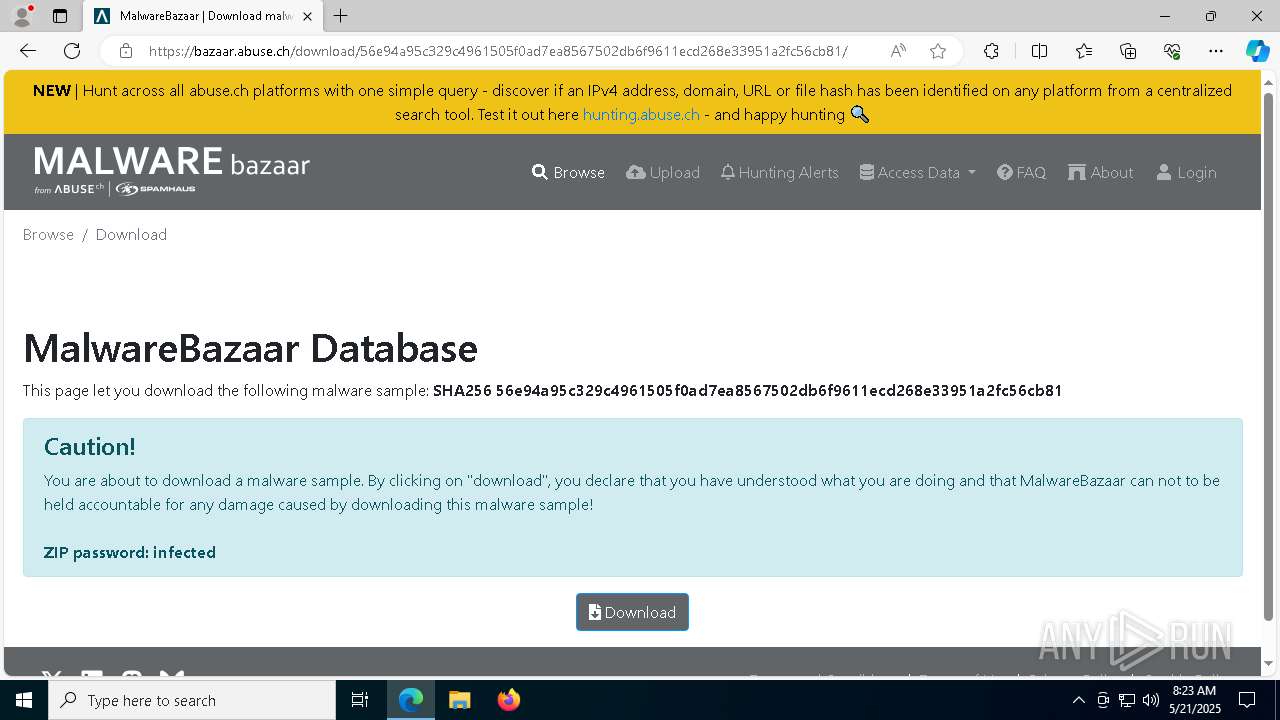
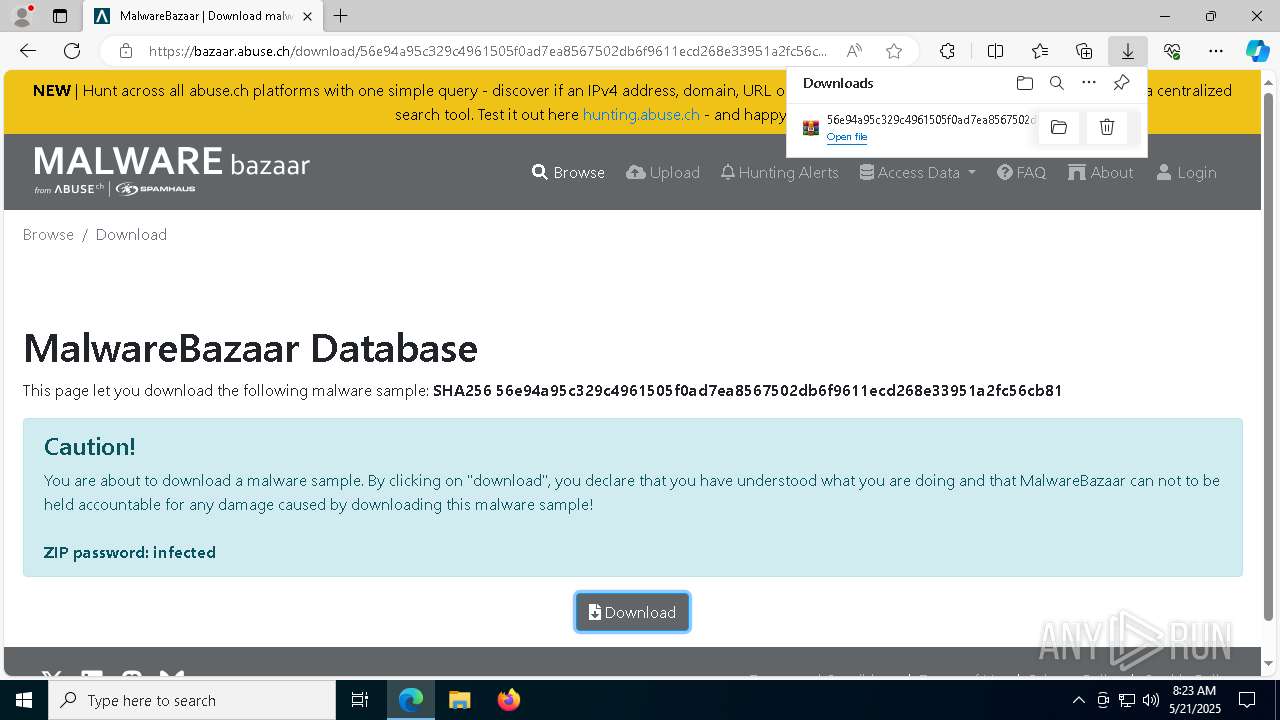
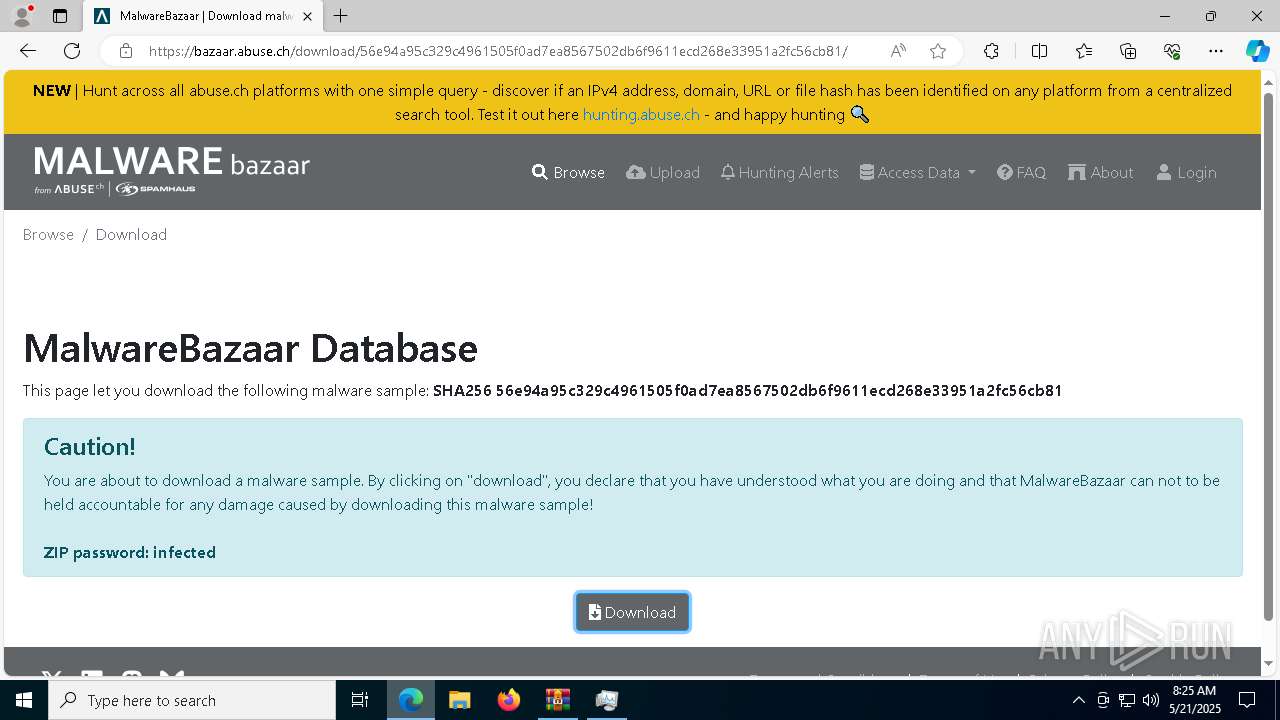
| URL: | https://bazaar.abuse.ch/browse/ |
| Full analysis: | https://app.any.run/tasks/83880f78-a139-446c-bdc8-3e4ab402fe2a |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
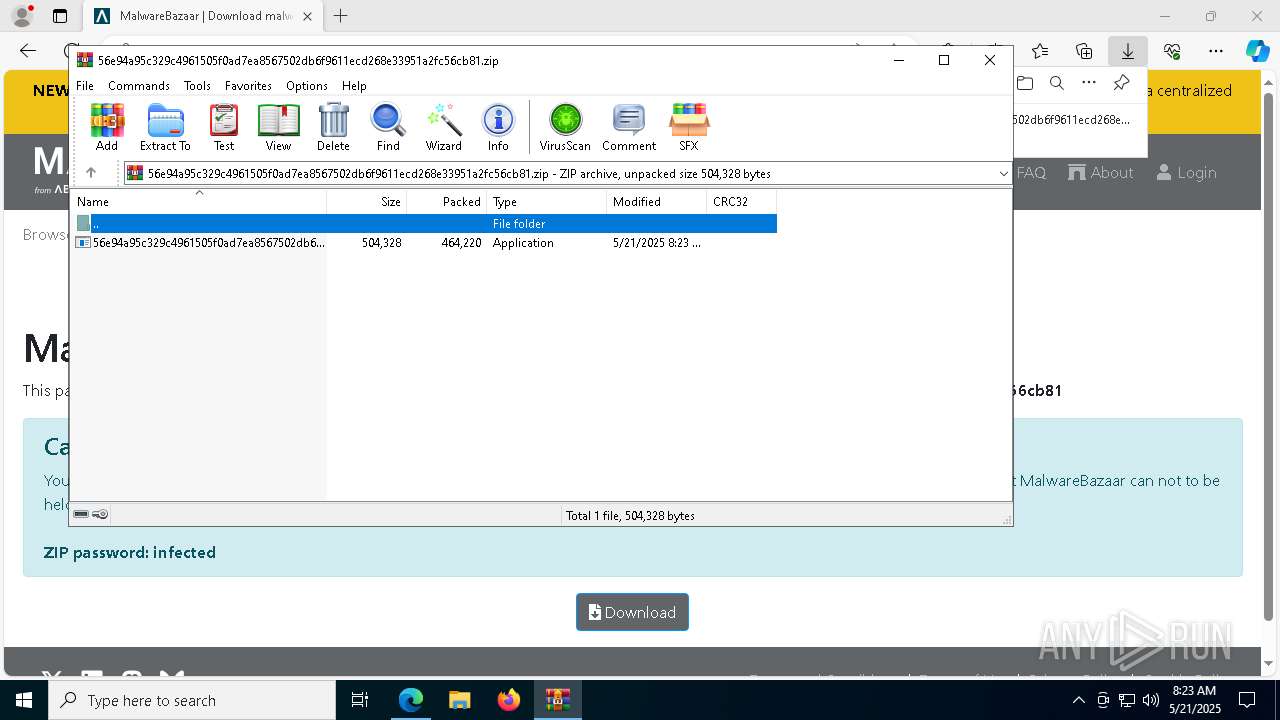
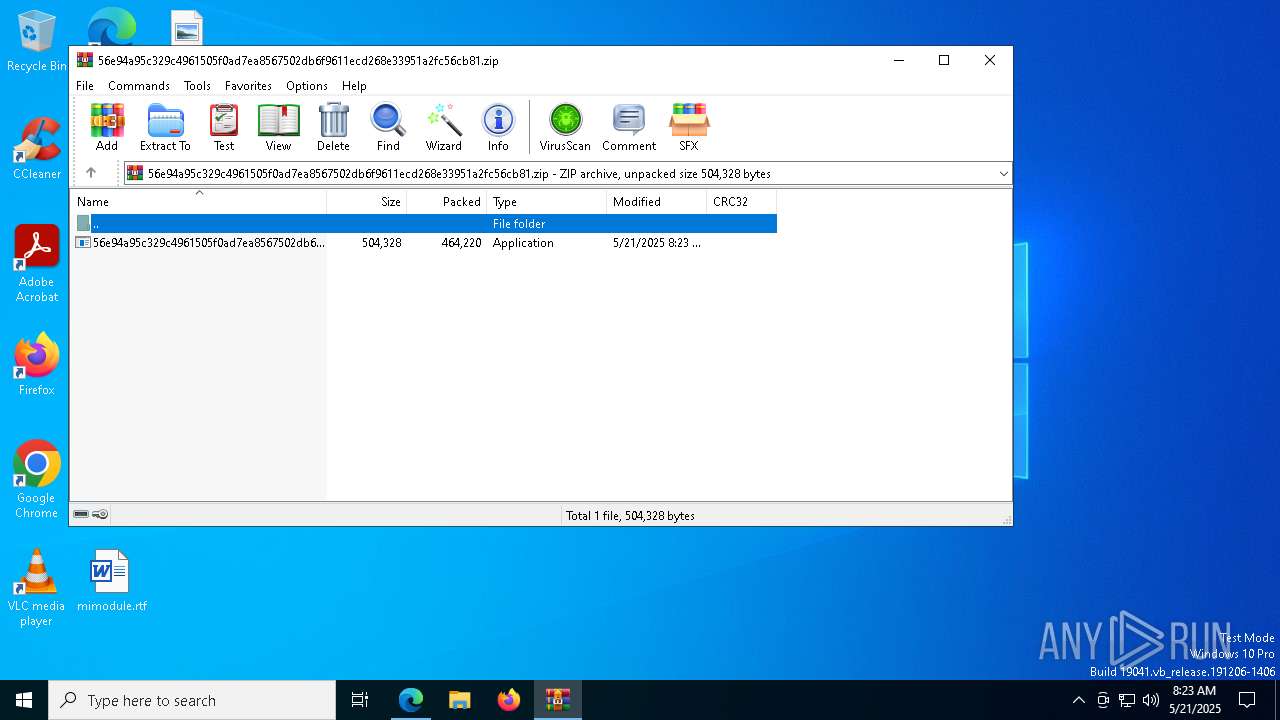
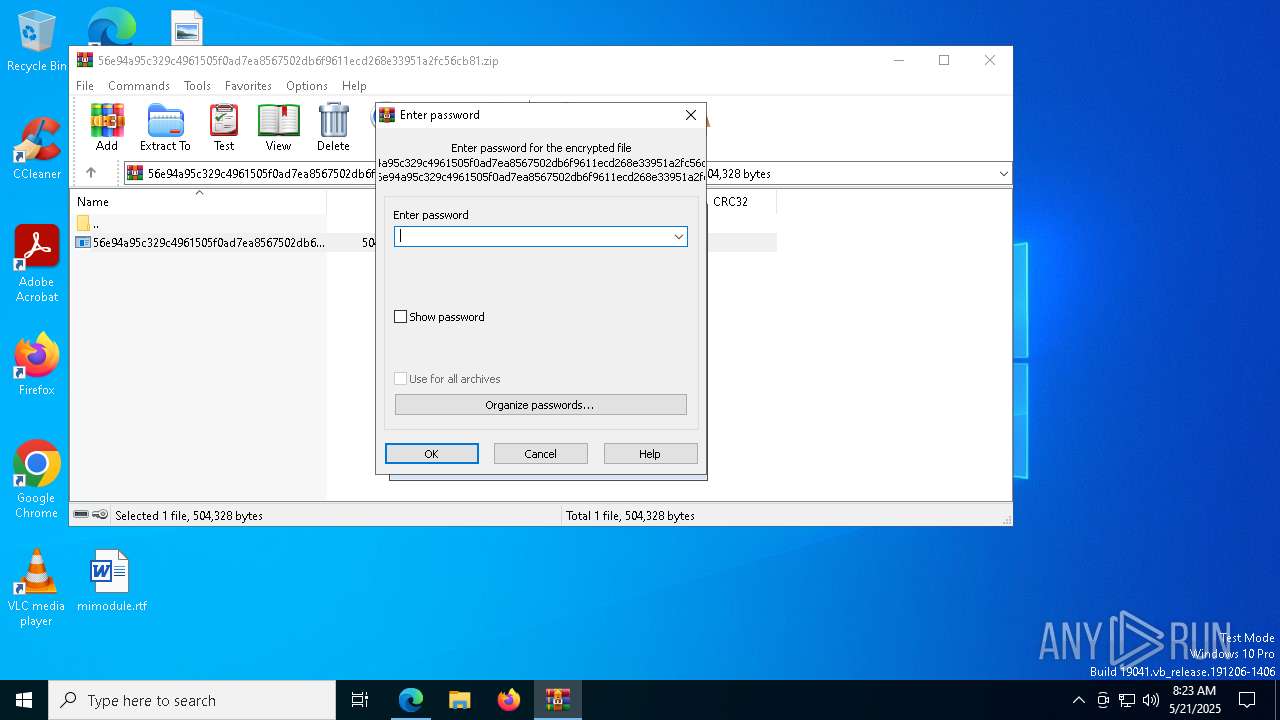
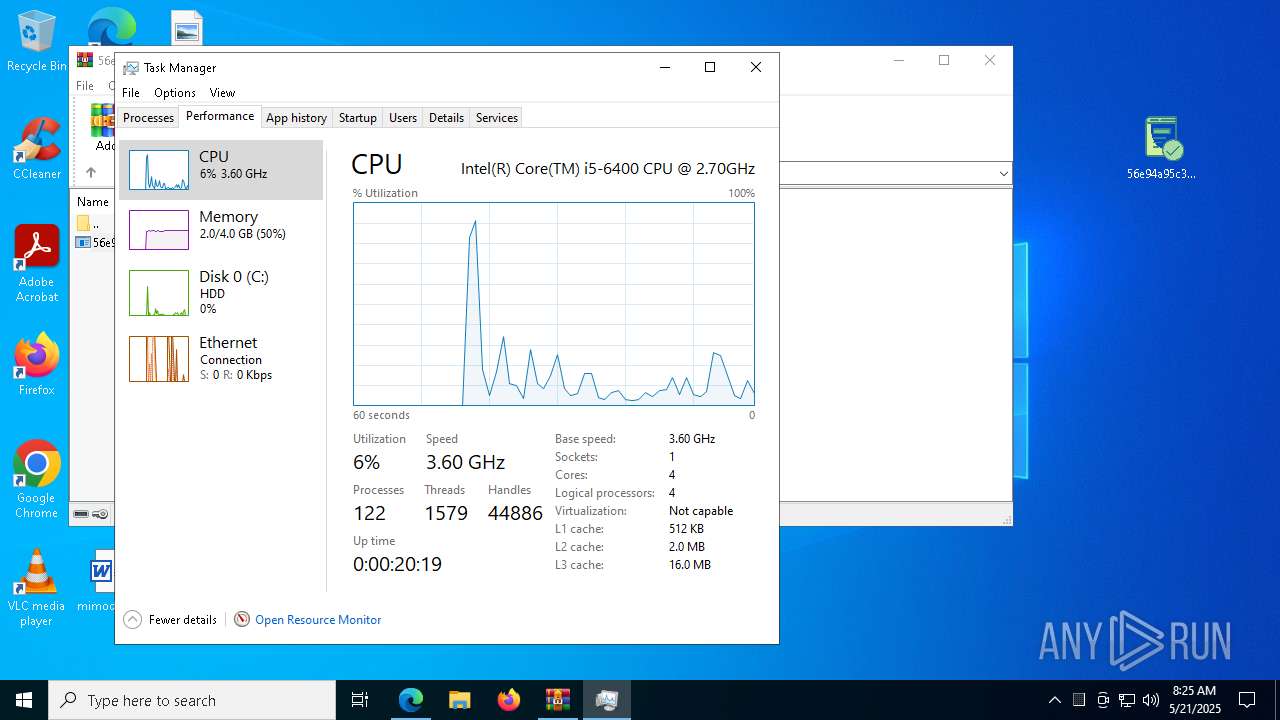
| Analysis date: | May 21, 2025, 08:23:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 795F5641CCD3DFF86DCD367836C7B9E8 |
| SHA1: | FEA906E160EC0EE8145CCFDBD3AB0459E811CFA7 |
| SHA256: | 5FD287342B02CD1D1FE57258D81B38FFBCE8850B5E404D8B83758D9A21872C2F |
| SSDEEP: | 3:N8N0uDWHXKBn:23AaBn |
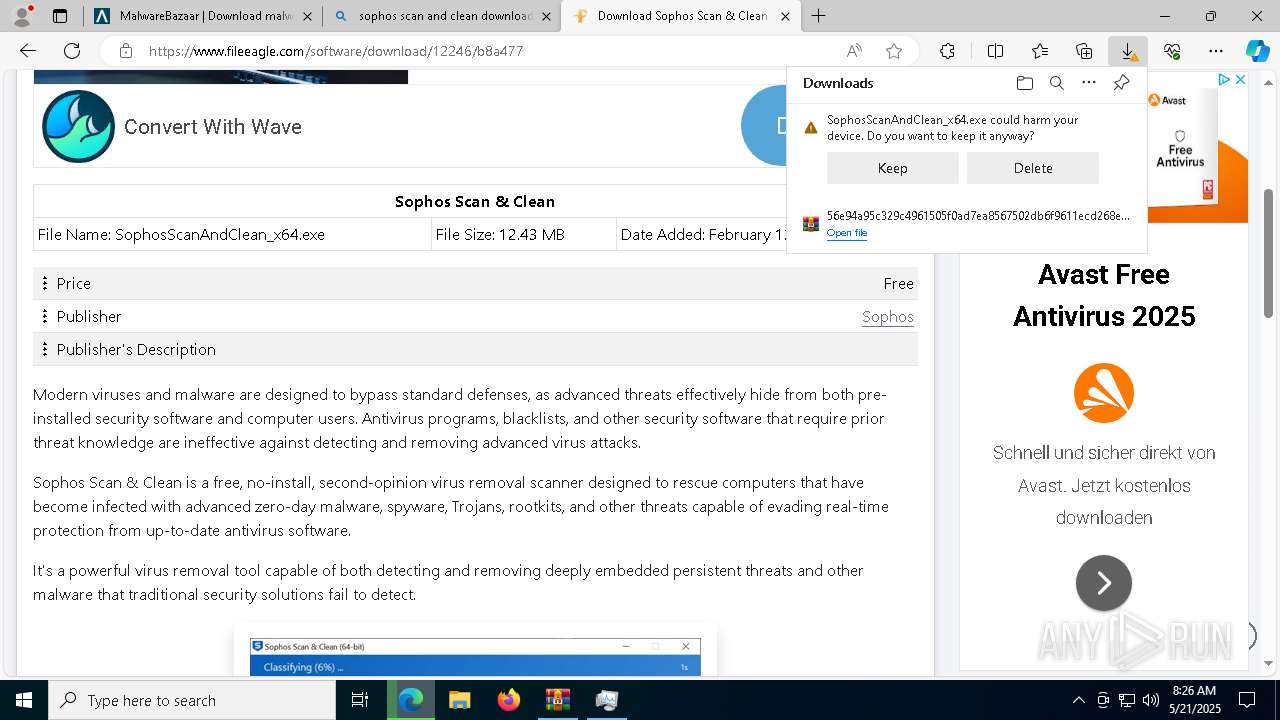
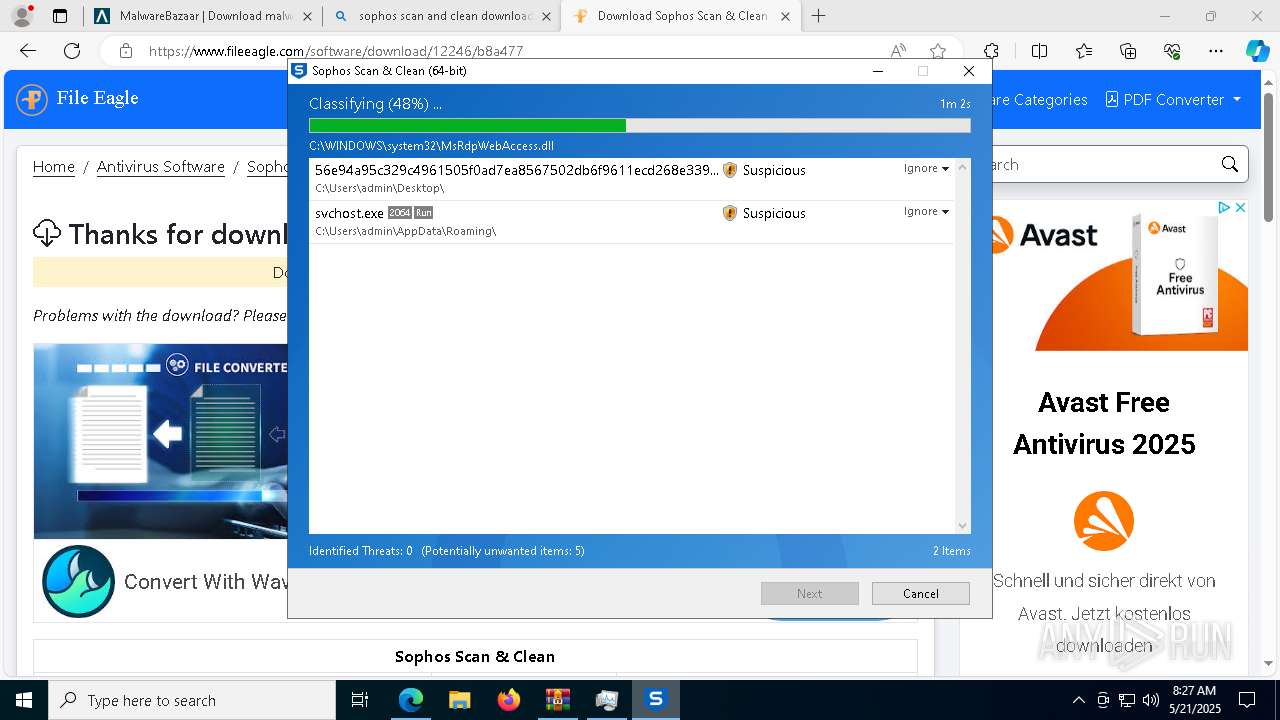
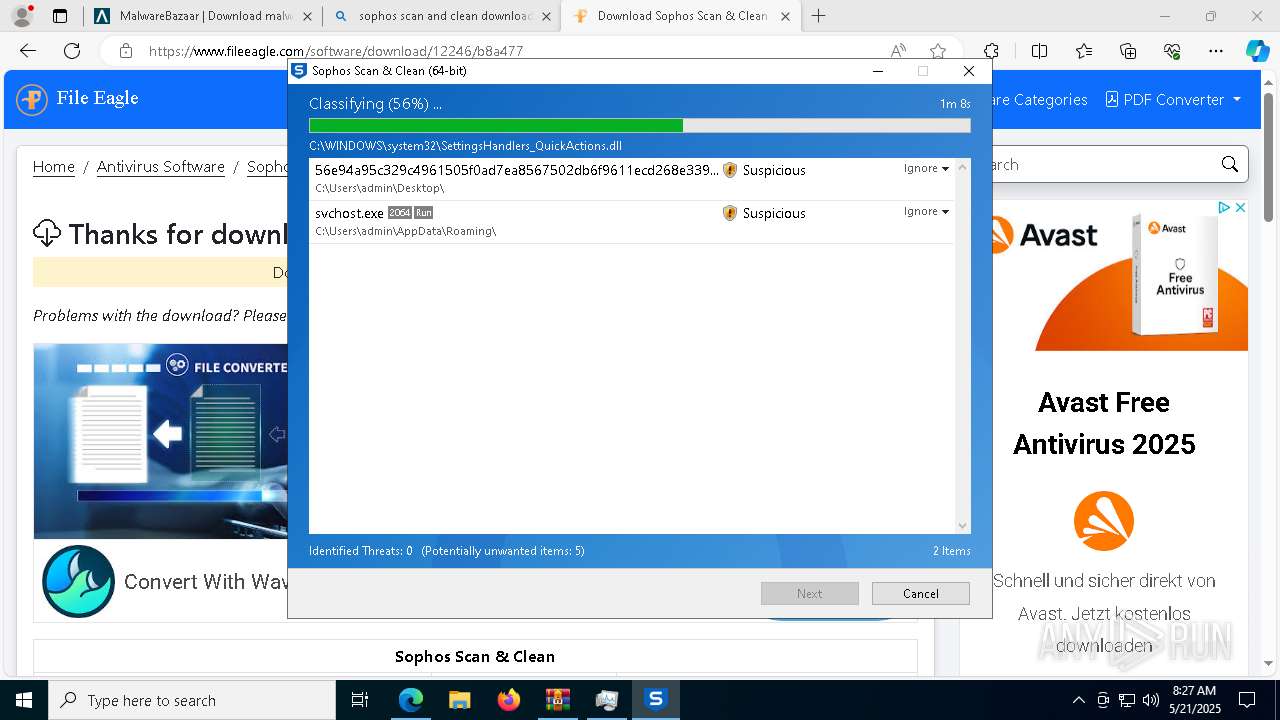
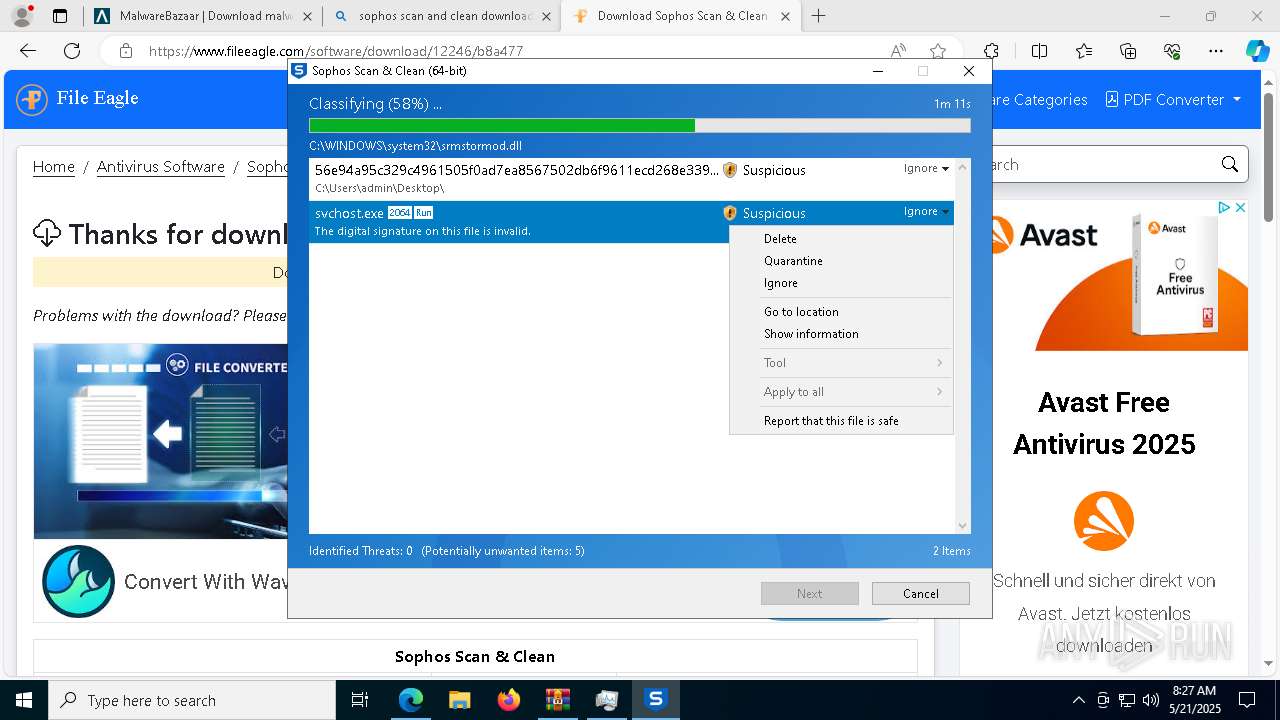
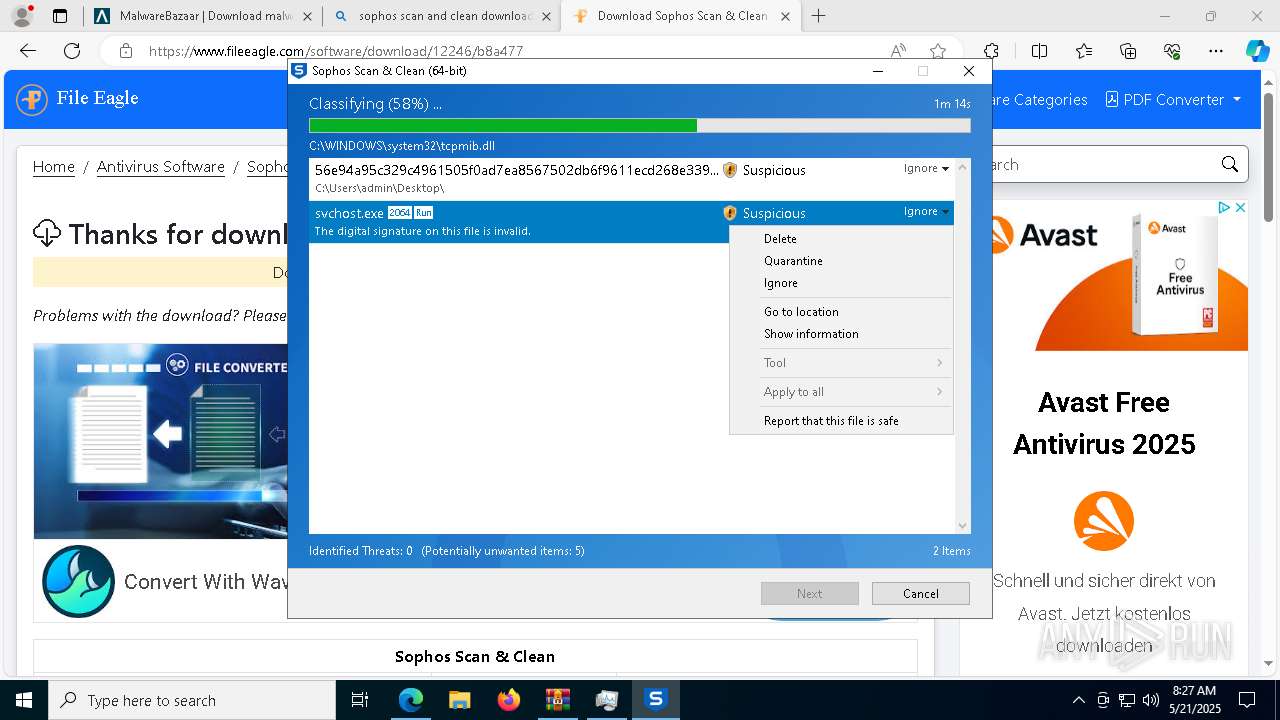
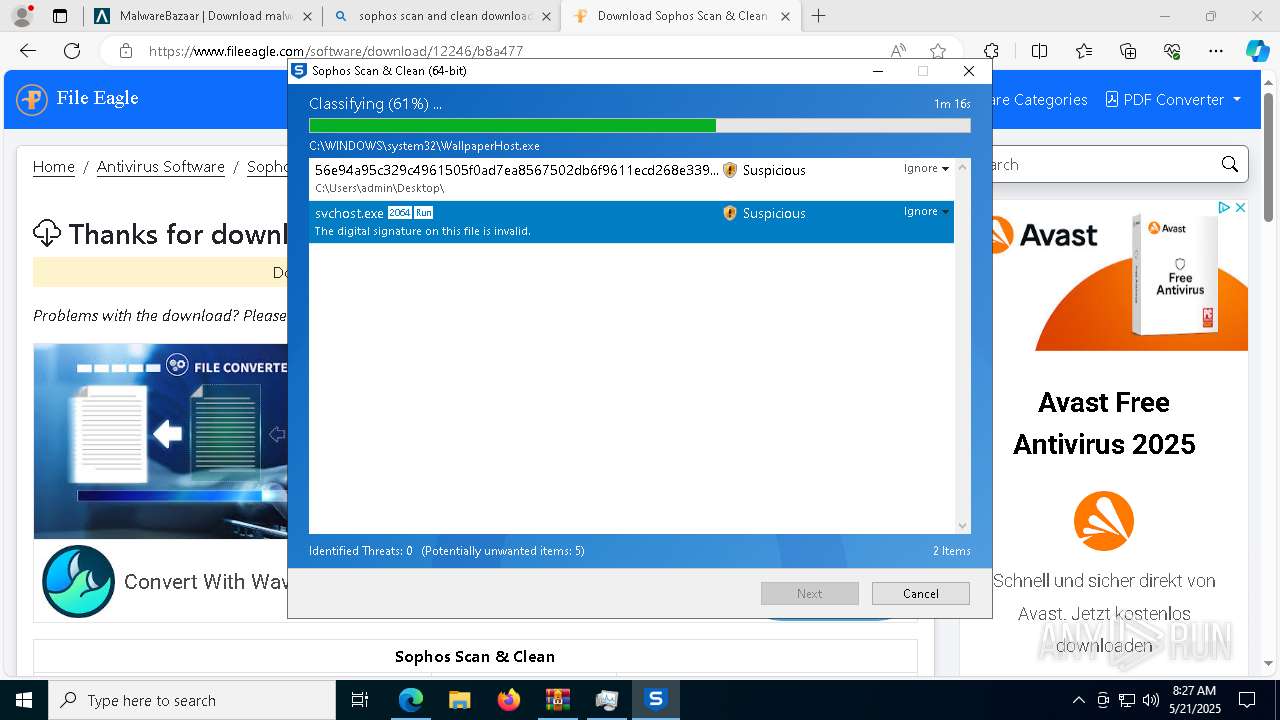
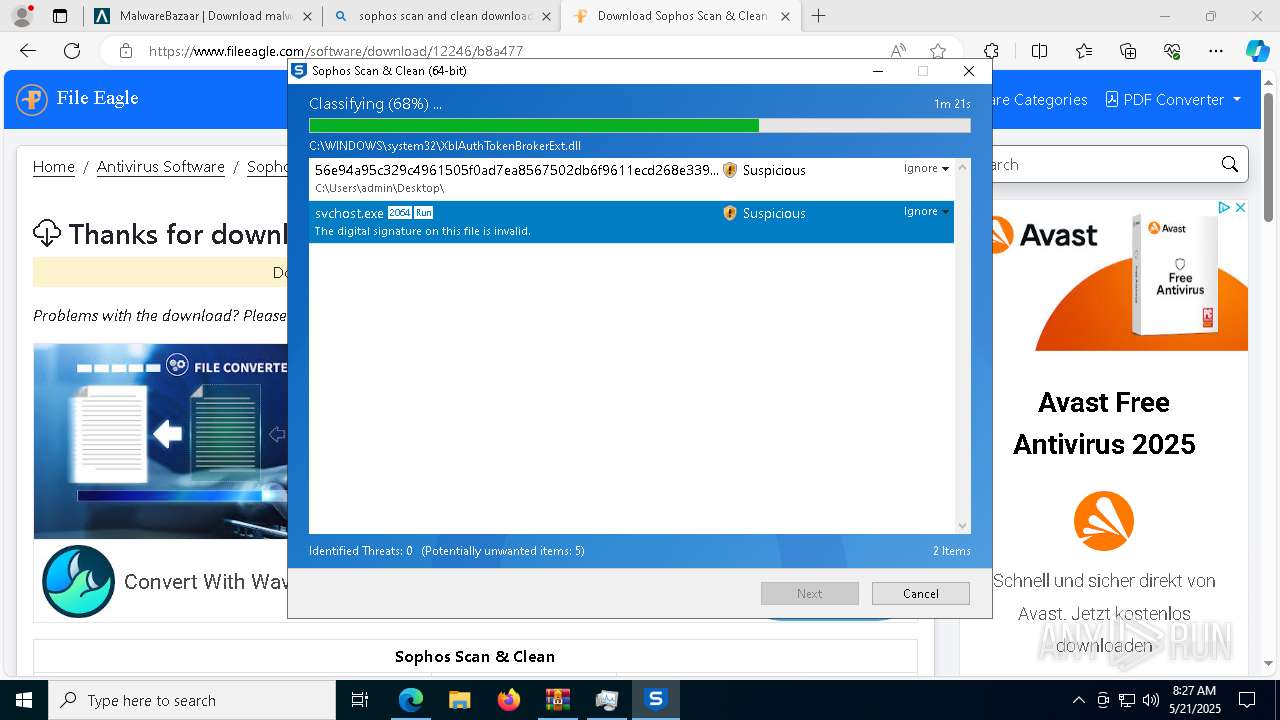
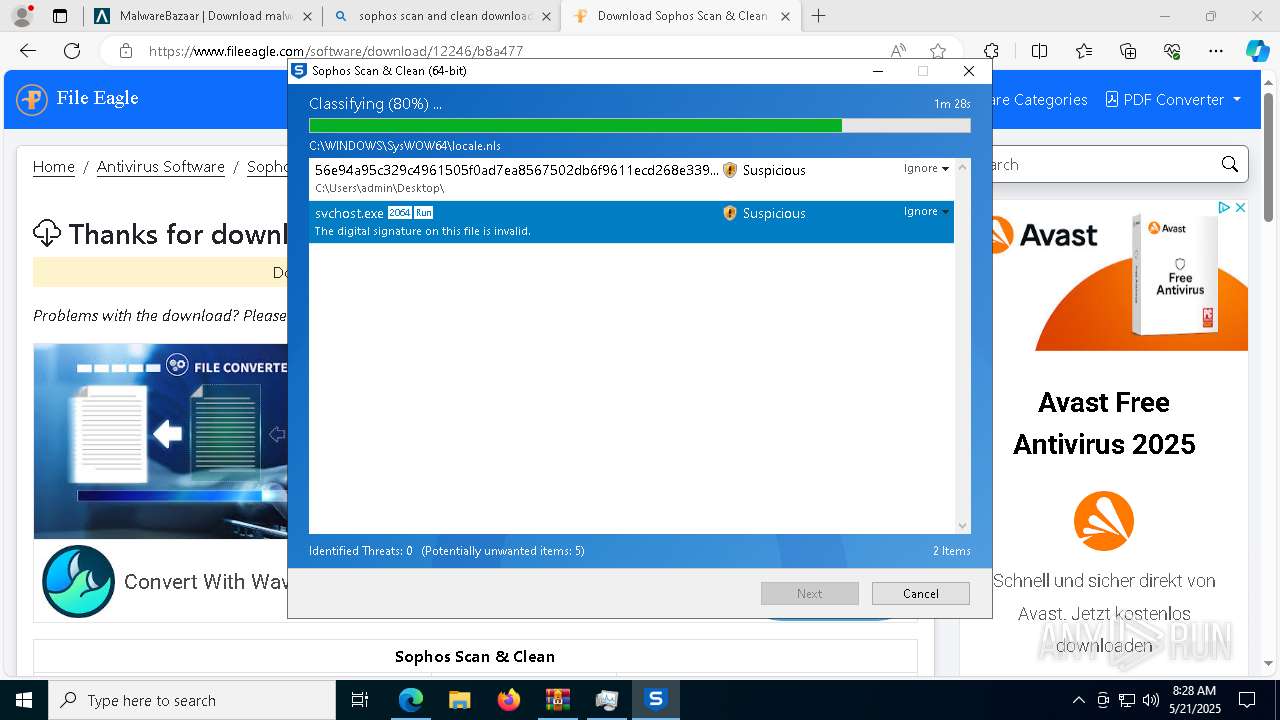
MALICIOUS
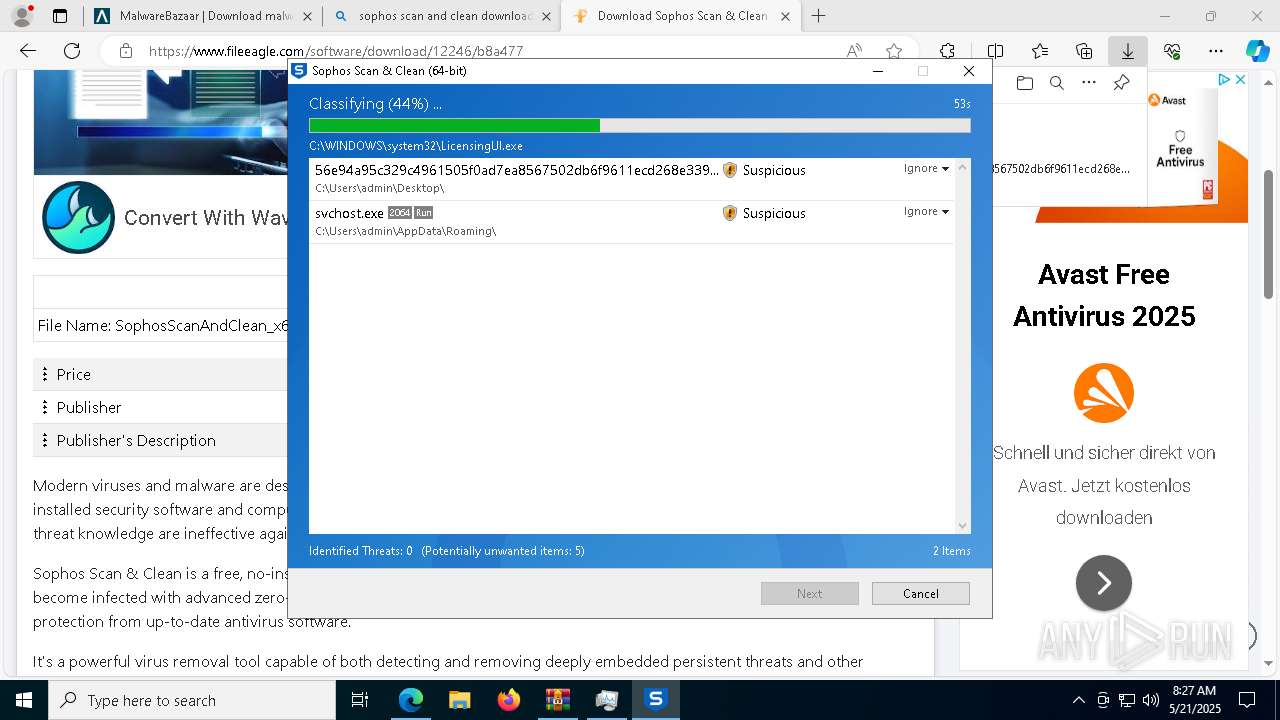
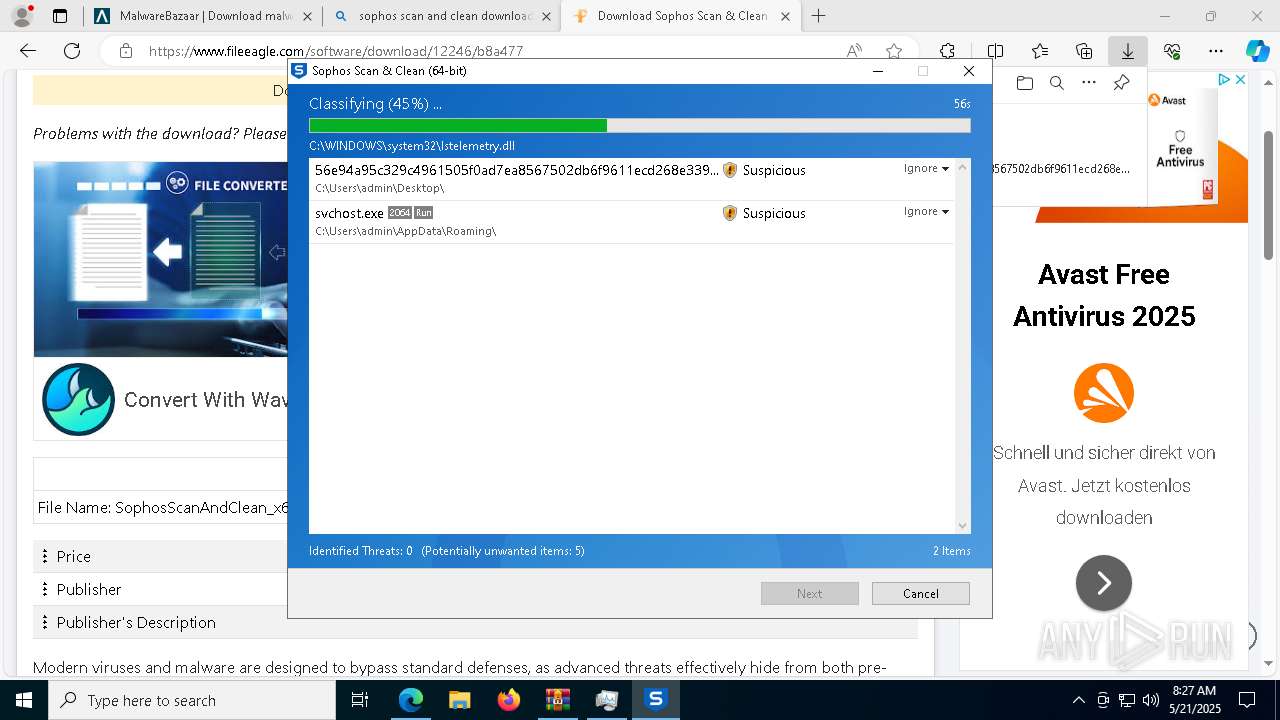
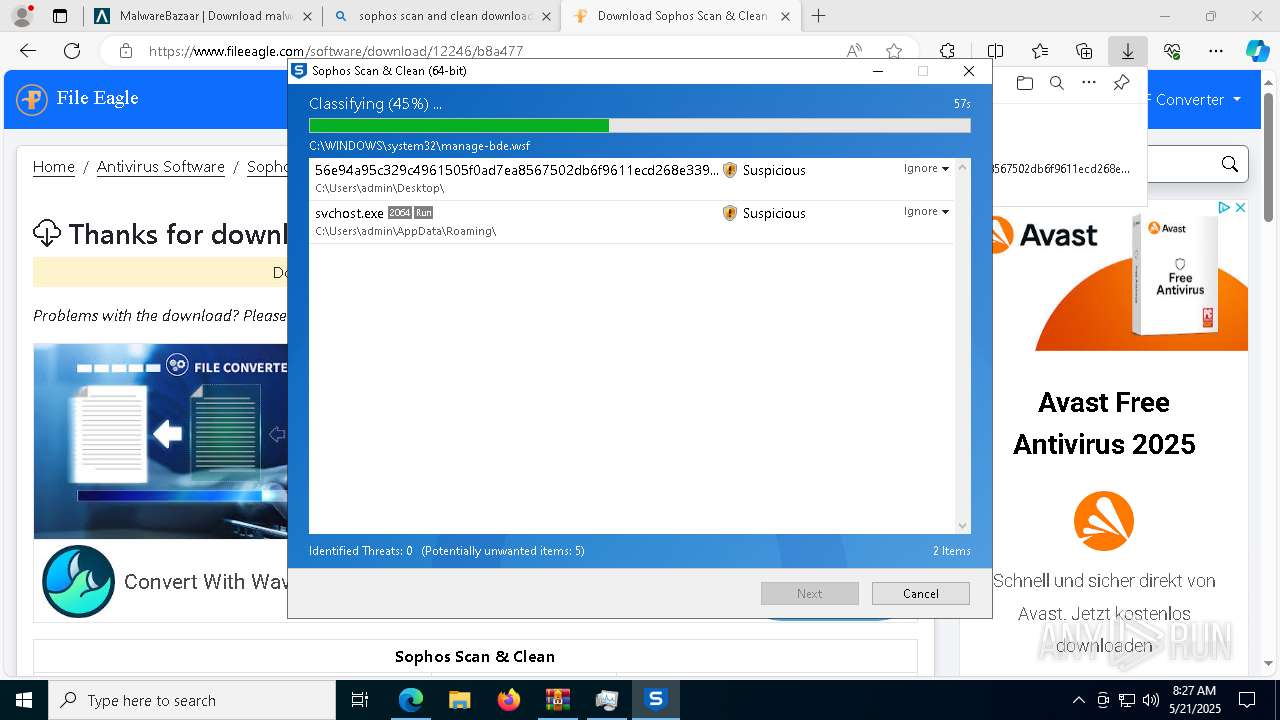
Executing a file with an untrusted certificate
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- svchost.exe (PID: 8076)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
- svchost.exe (PID: 5780)
- svchost.exe (PID: 6592)
- svchost.exe (PID: 2064)
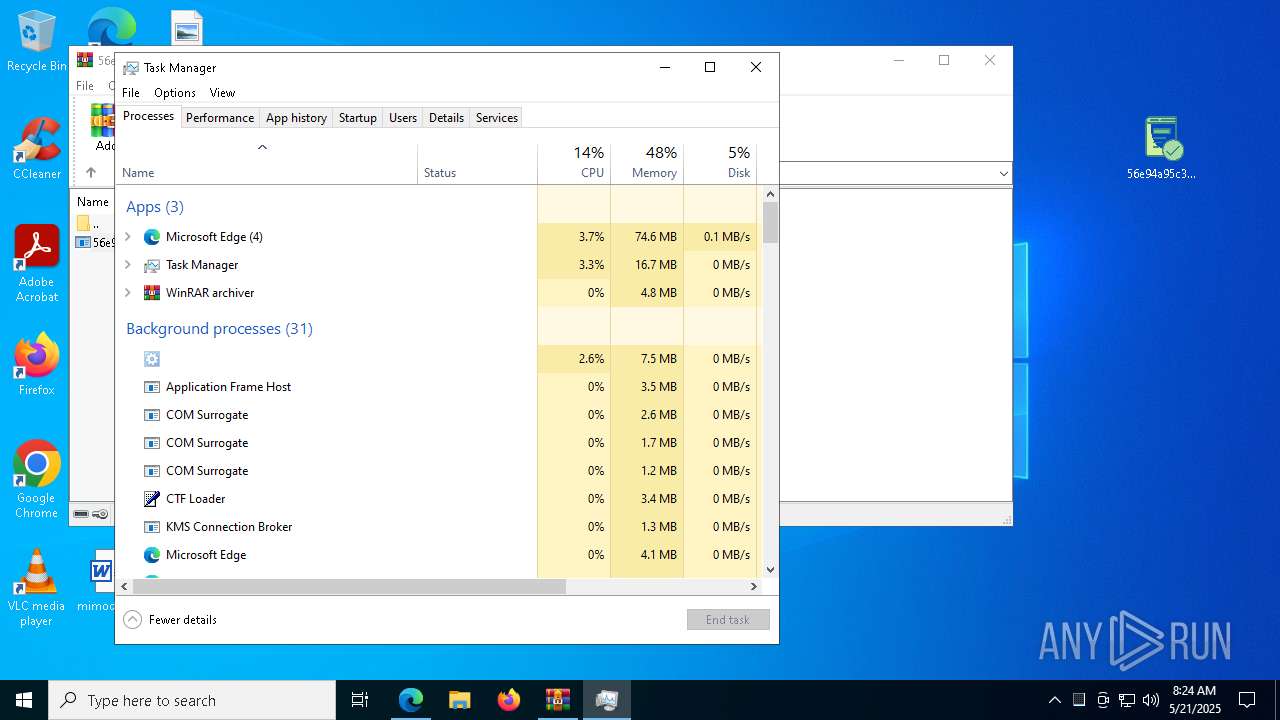
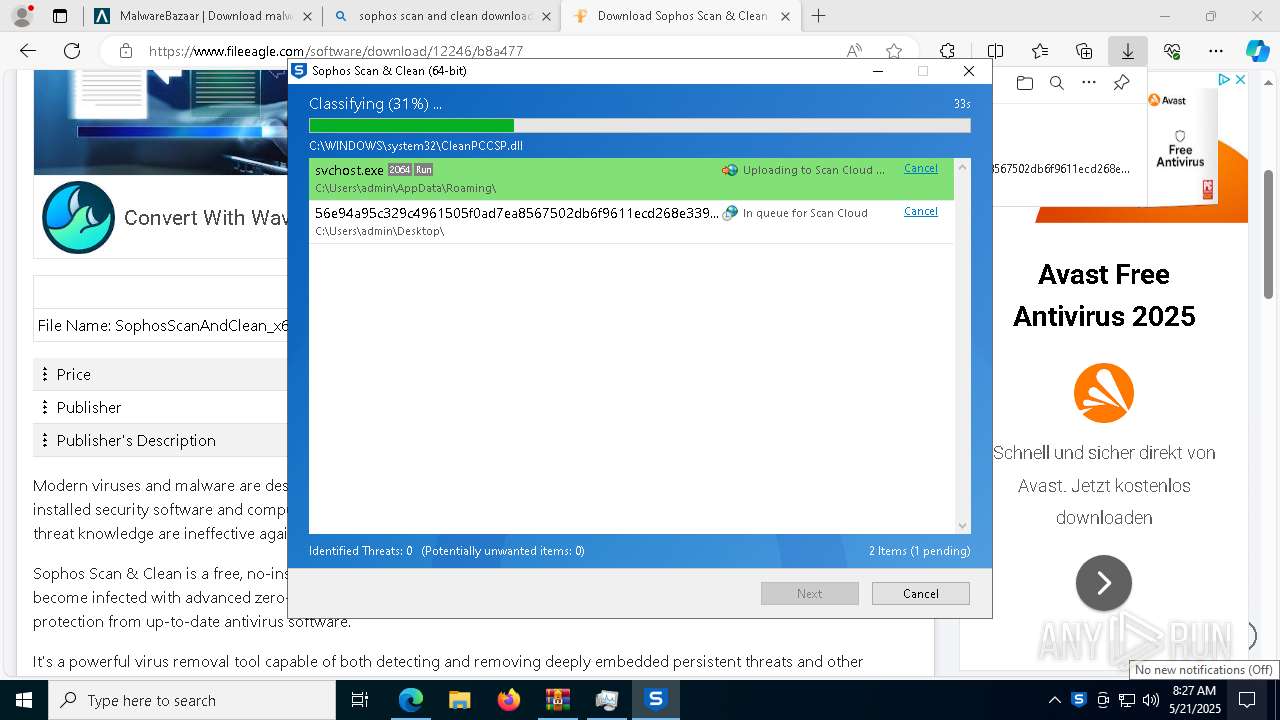
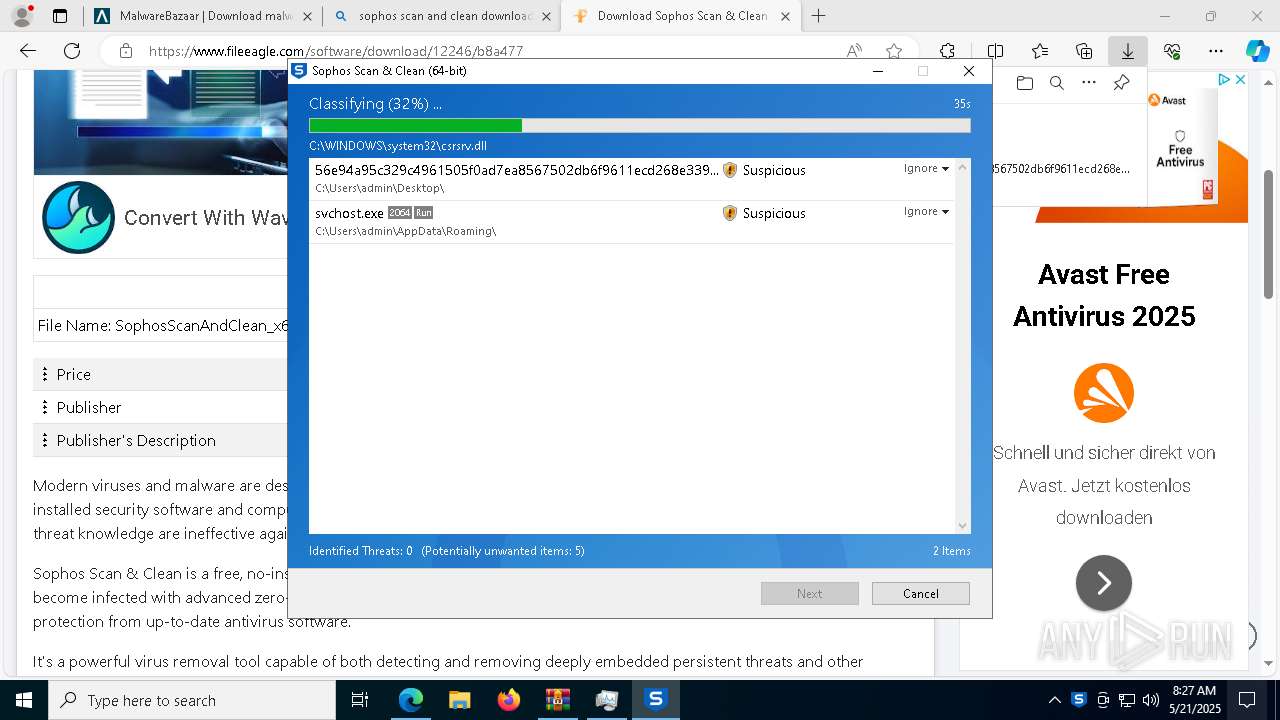
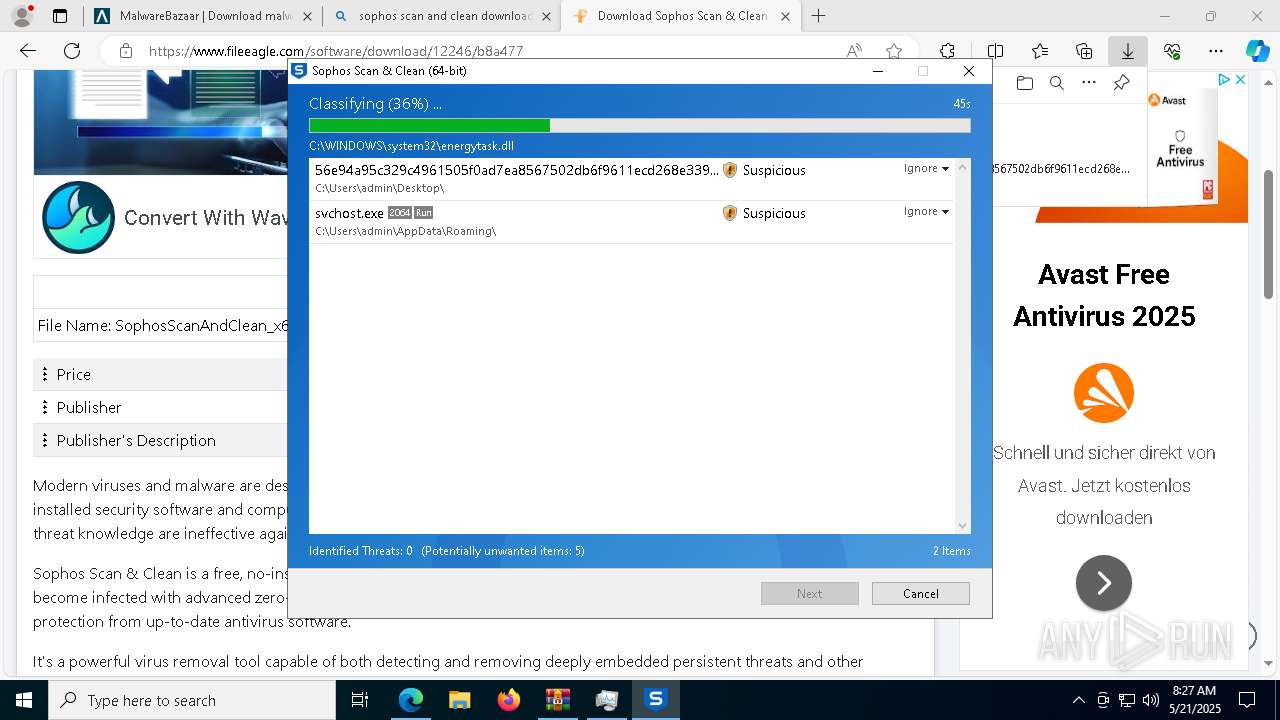
ASYNCRAT has been detected (MUTEX)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
- svchost.exe (PID: 2064)
Changes the autorun value in the registry
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
ASYNCRAT has been detected (SURICATA)
- svchost.exe (PID: 2064)
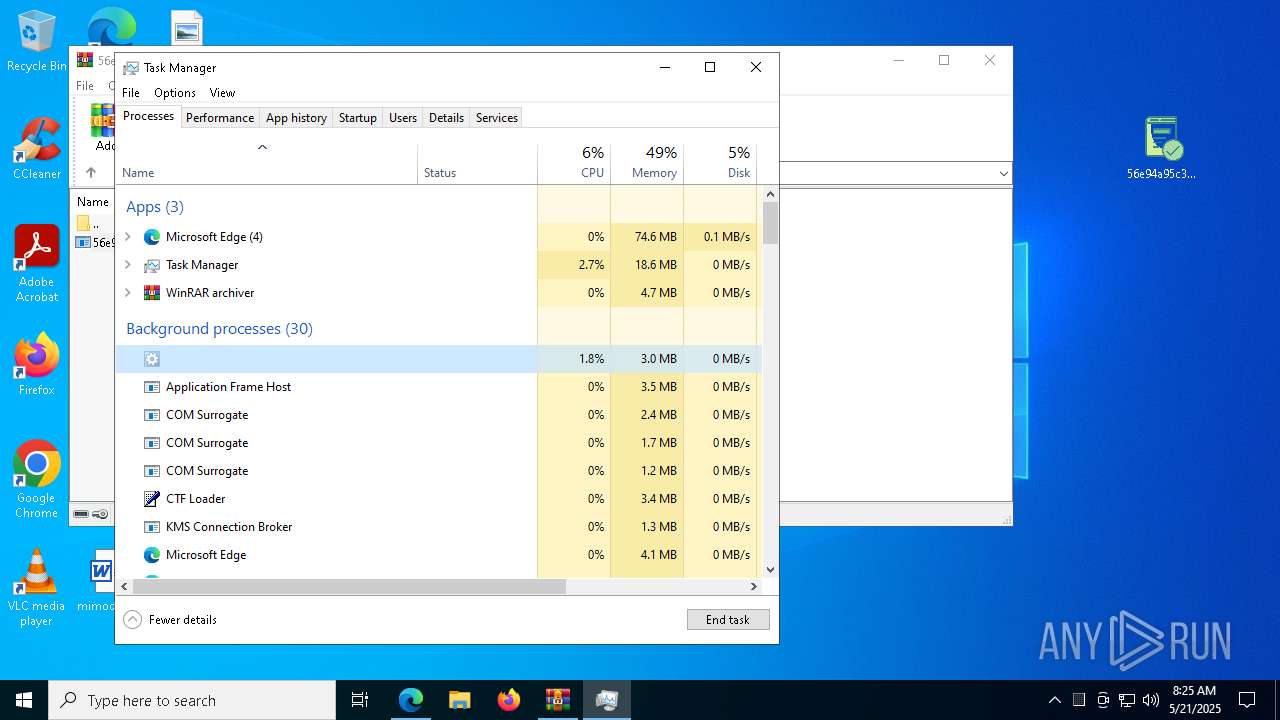
SUSPICIOUS
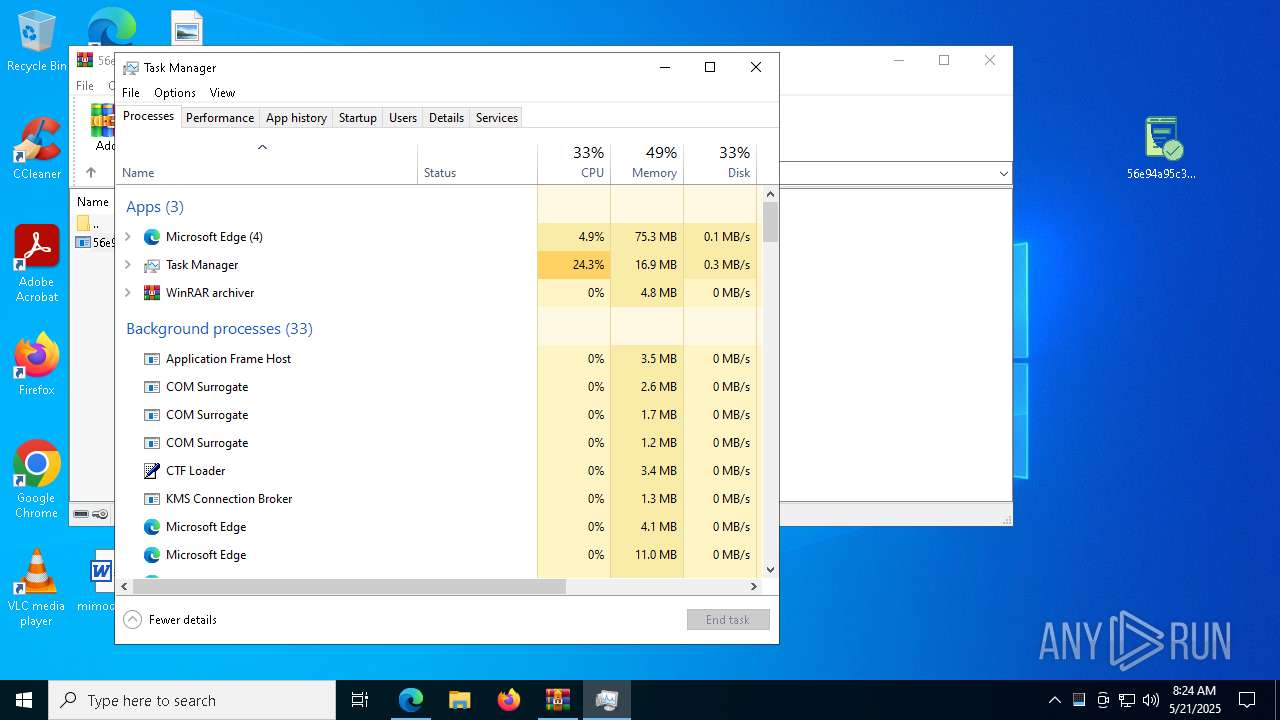
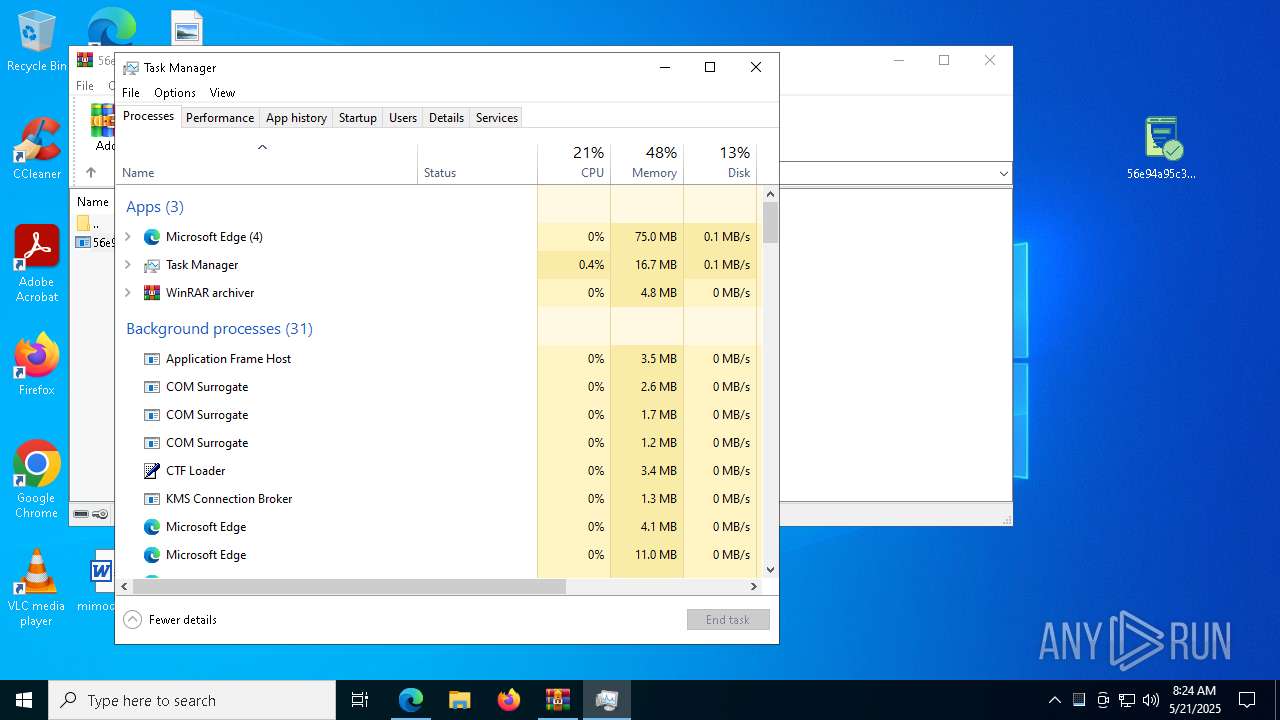
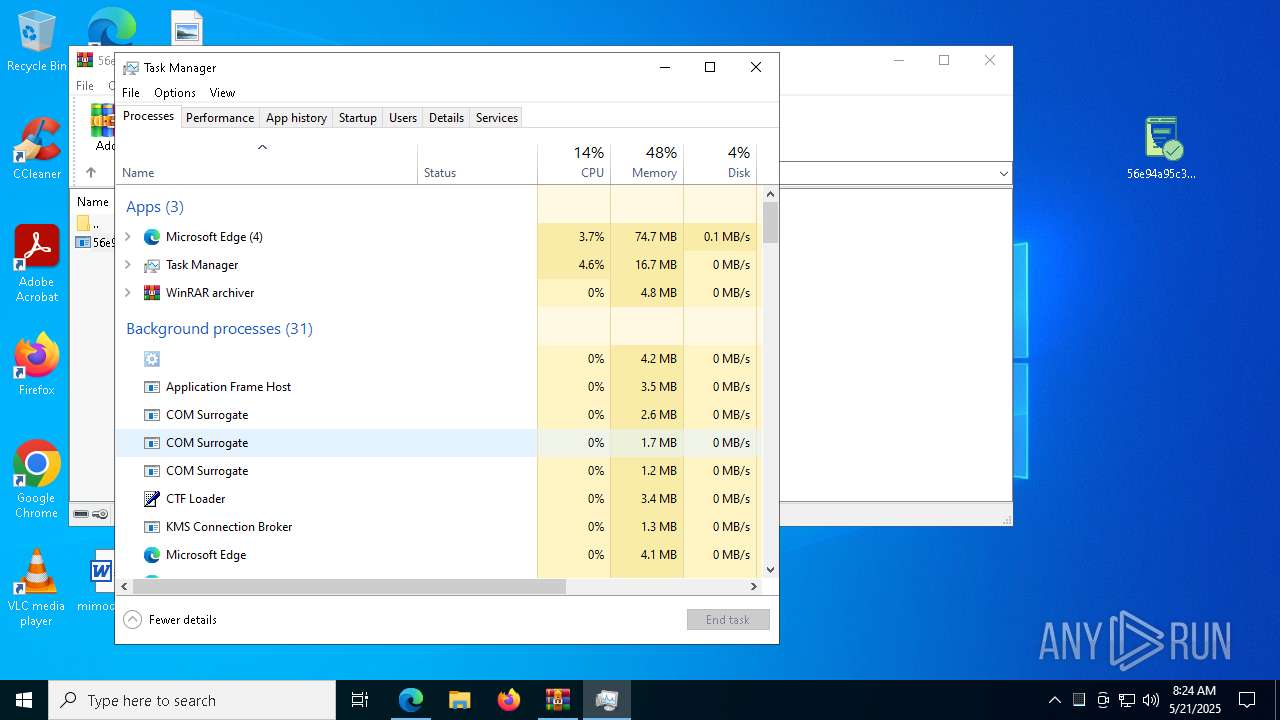
Application launched itself
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
- svchost.exe (PID: 6592)
The process creates files with name similar to system file names
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
Executable content was dropped or overwritten
- Taskmgr.exe (PID: 4188)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
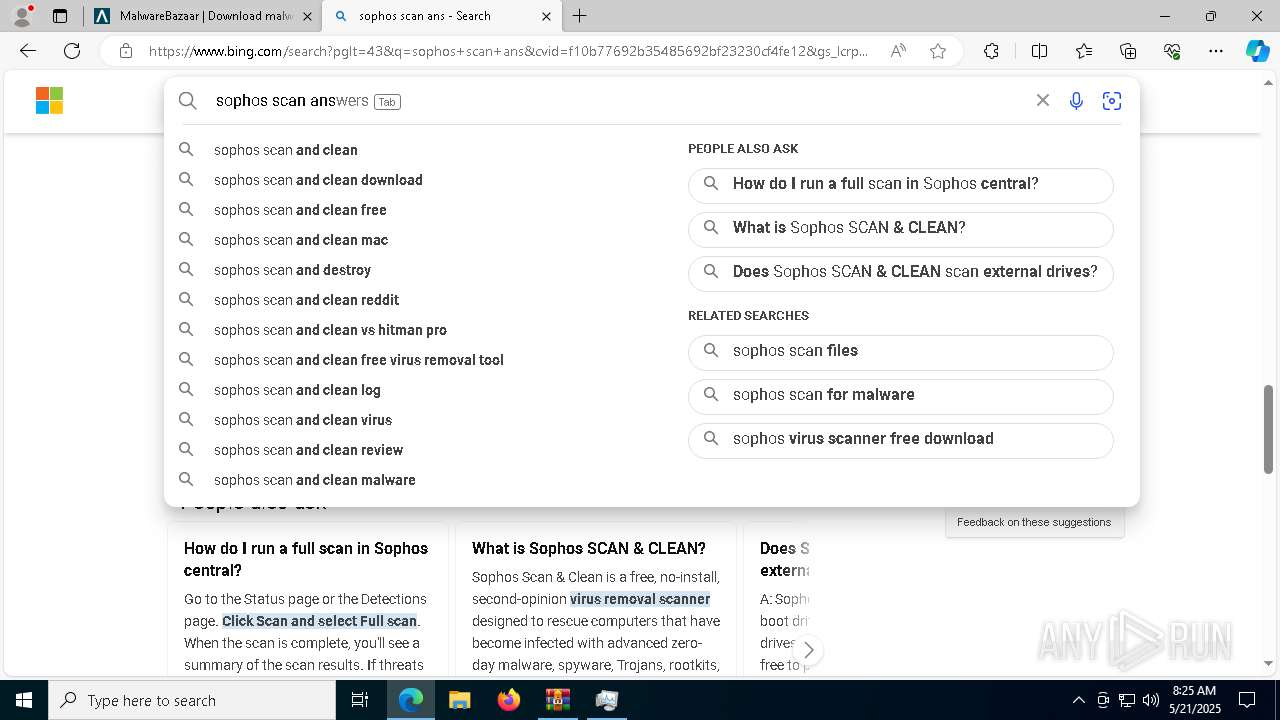
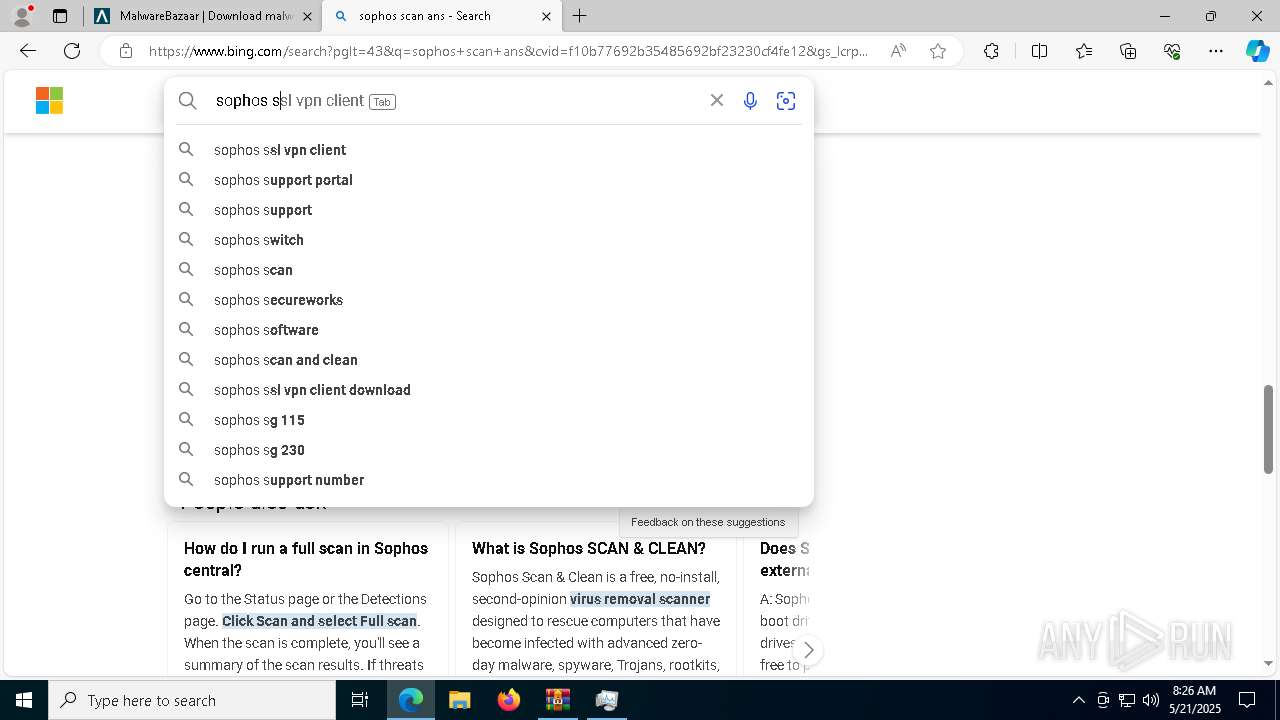
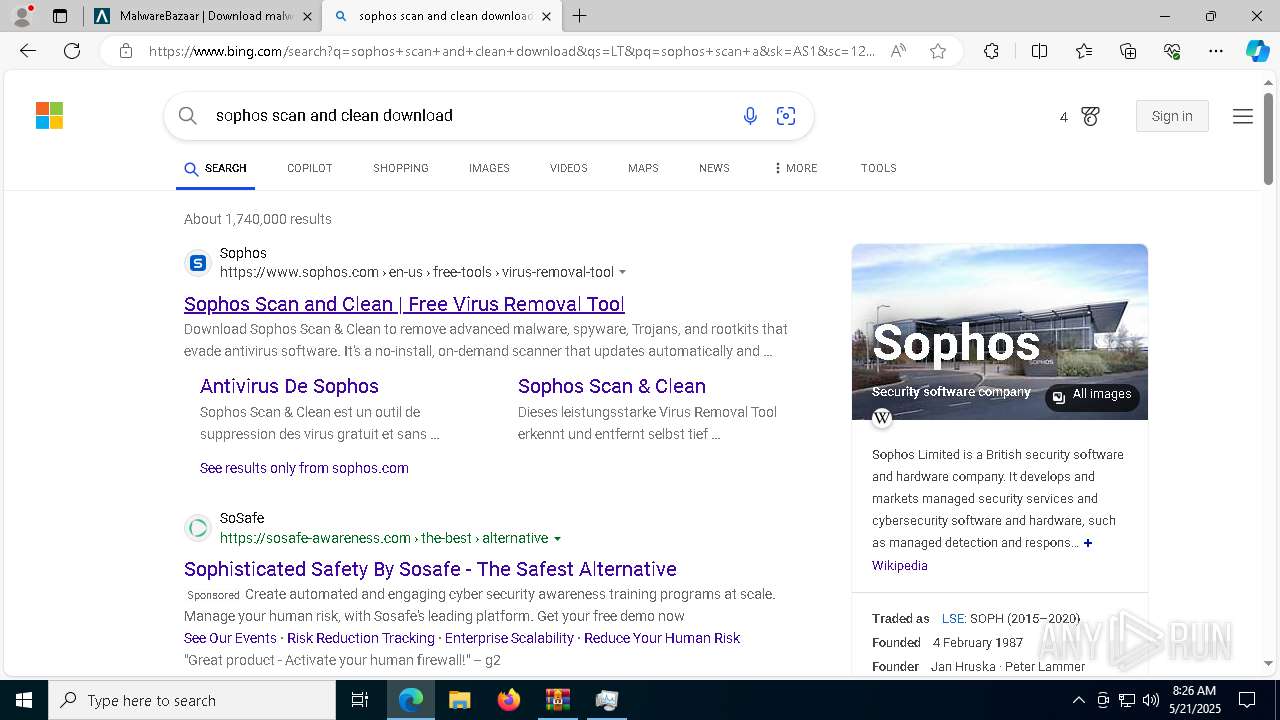
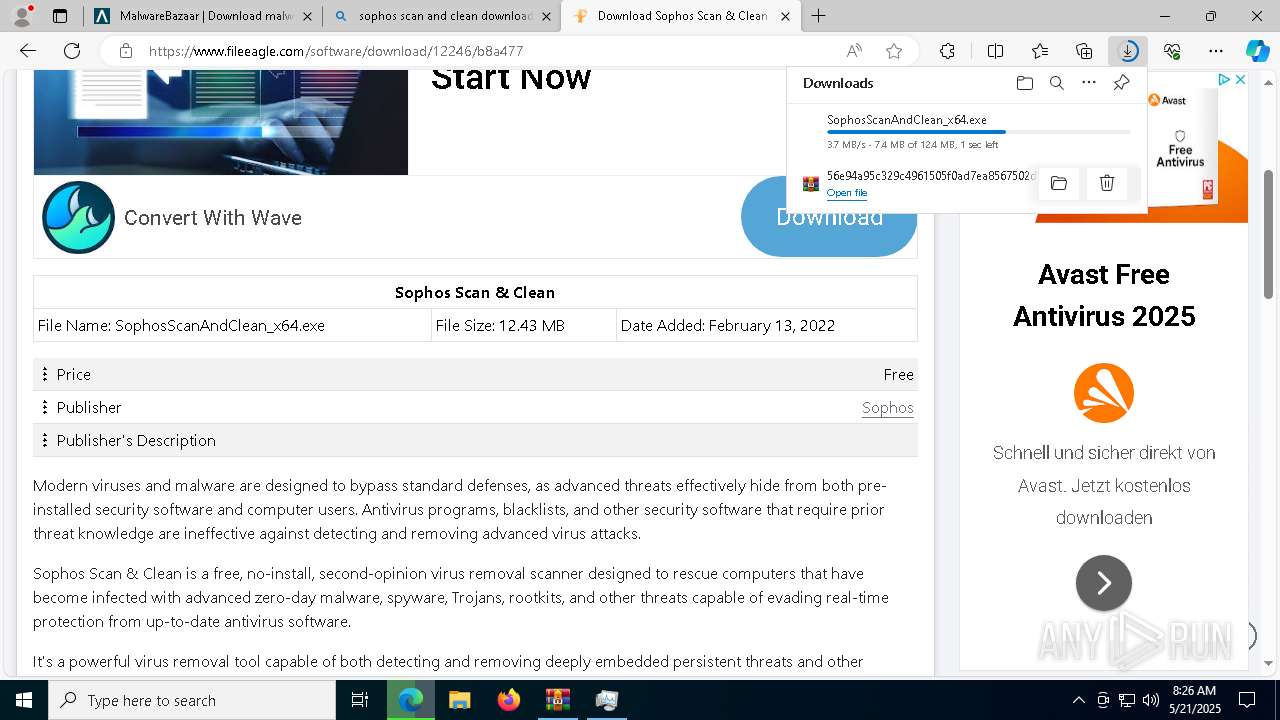
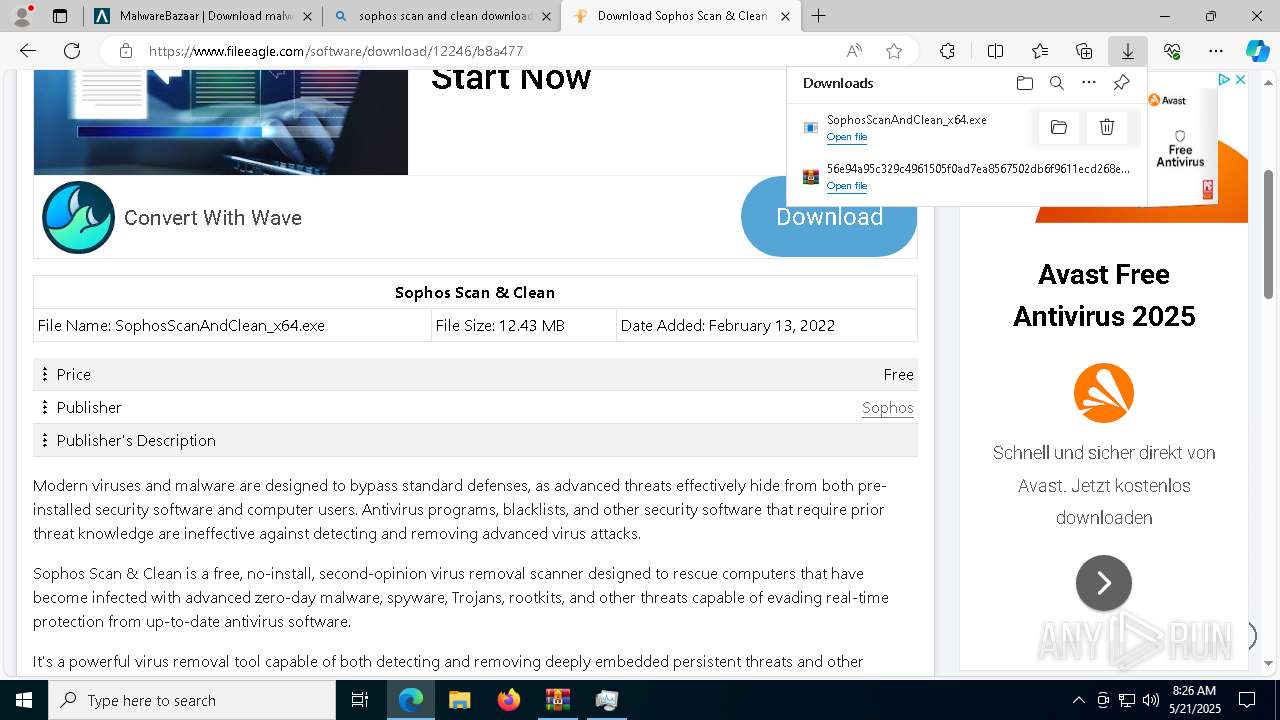
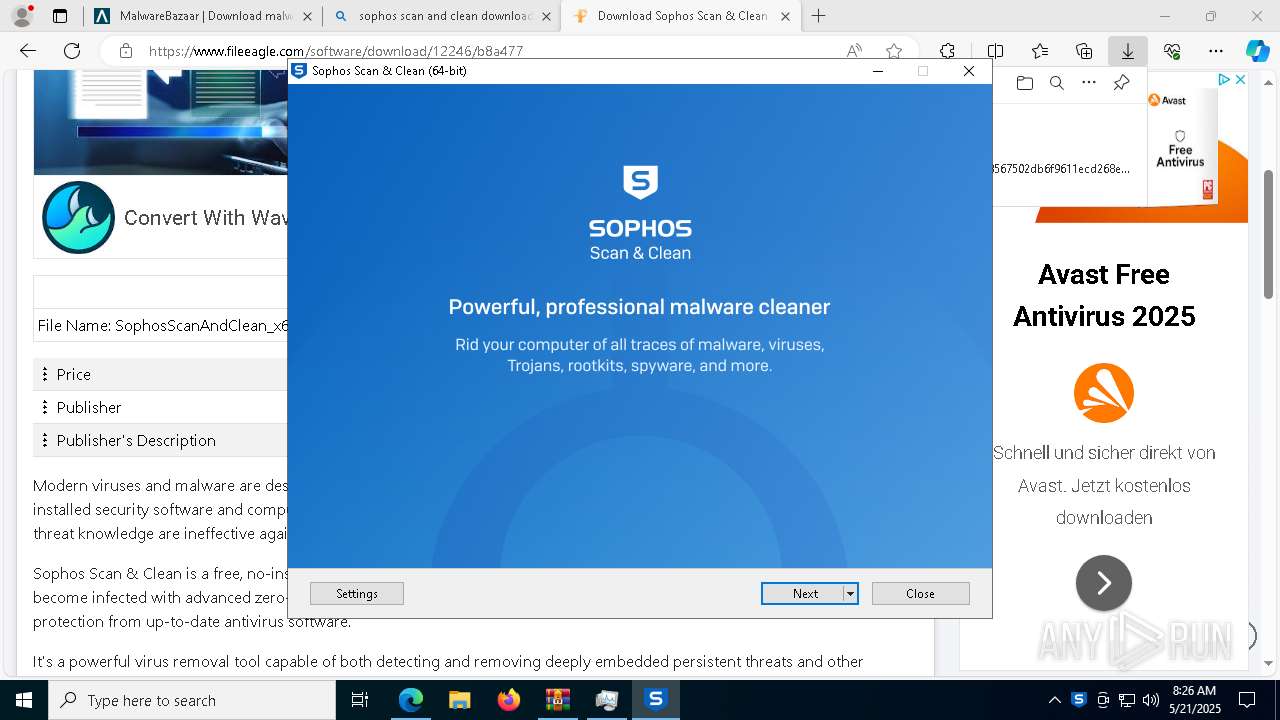
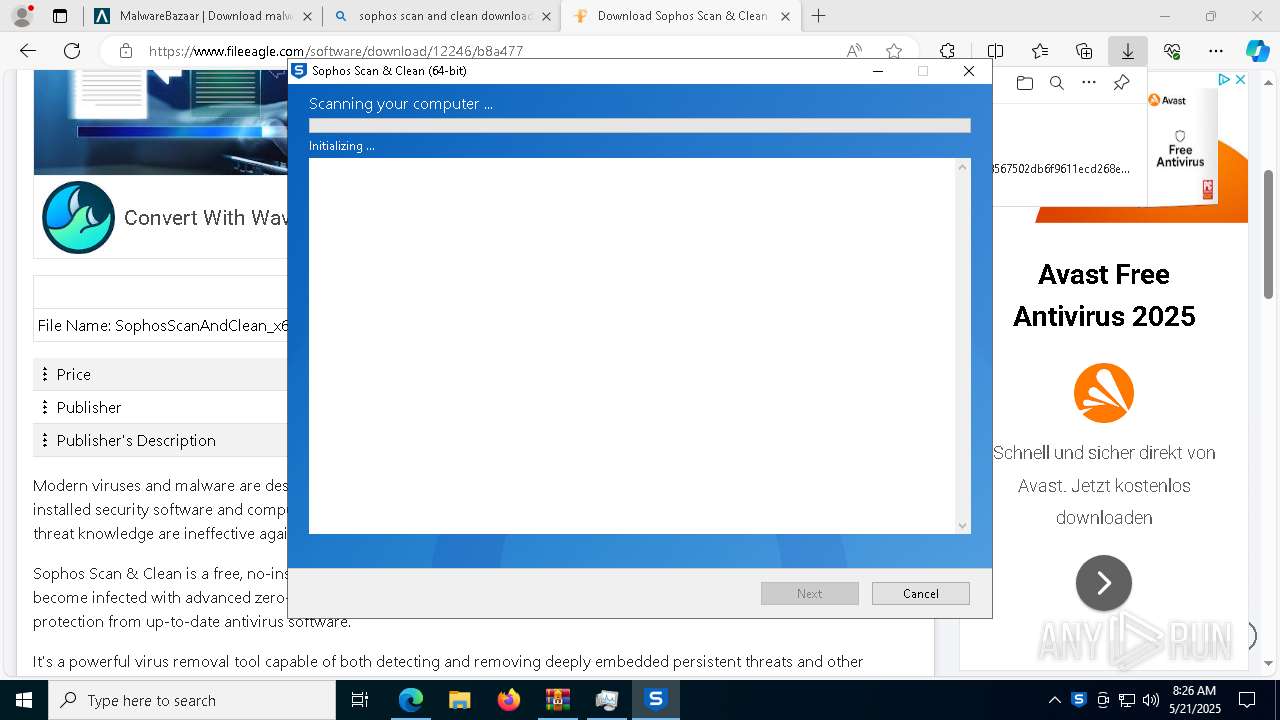
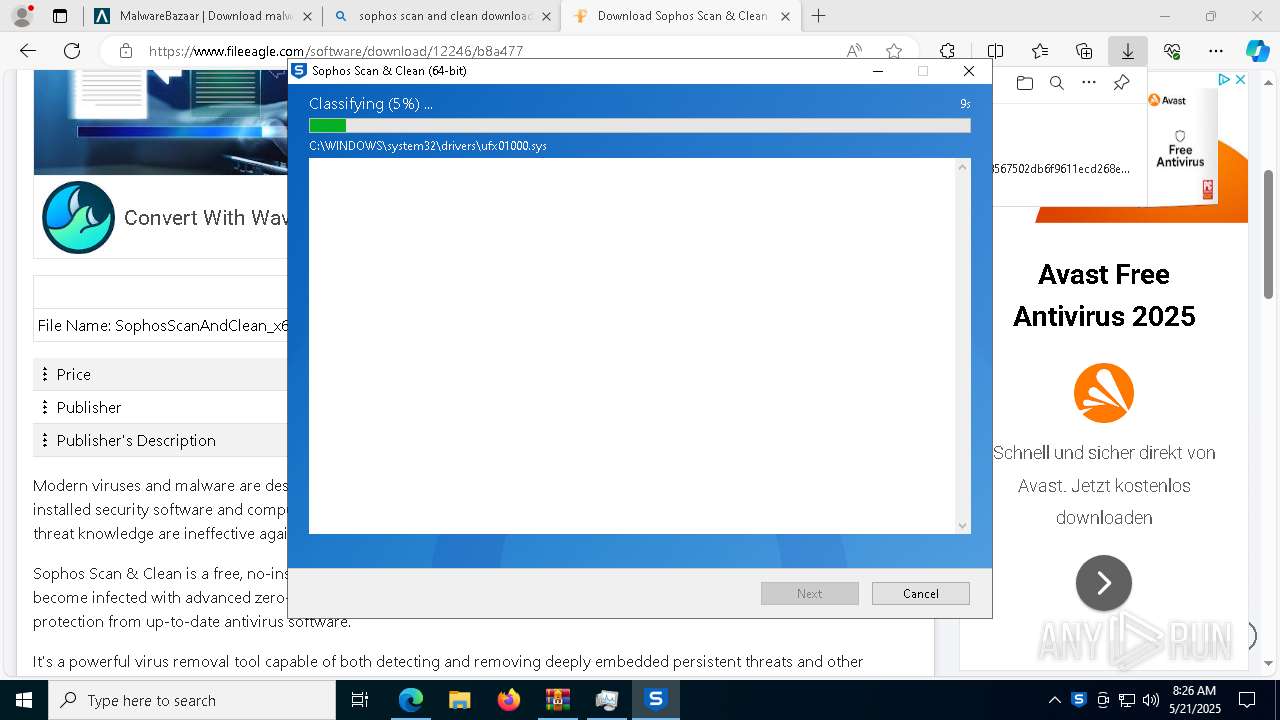
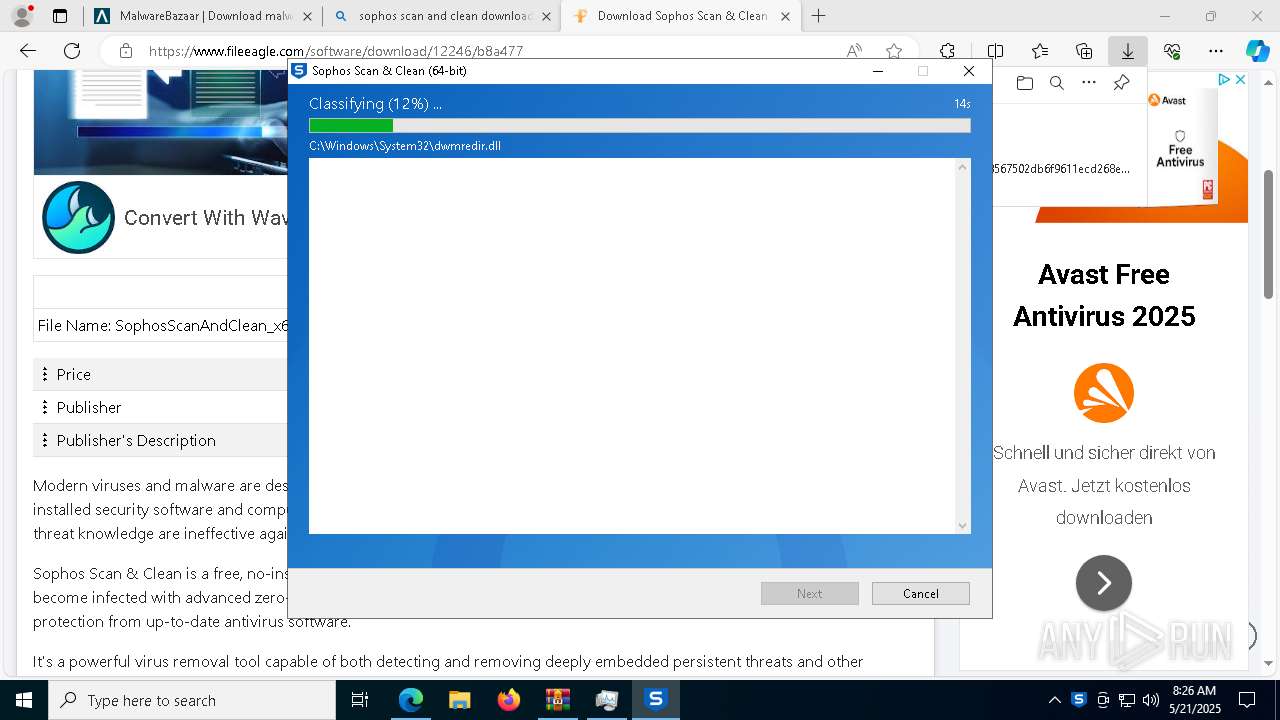
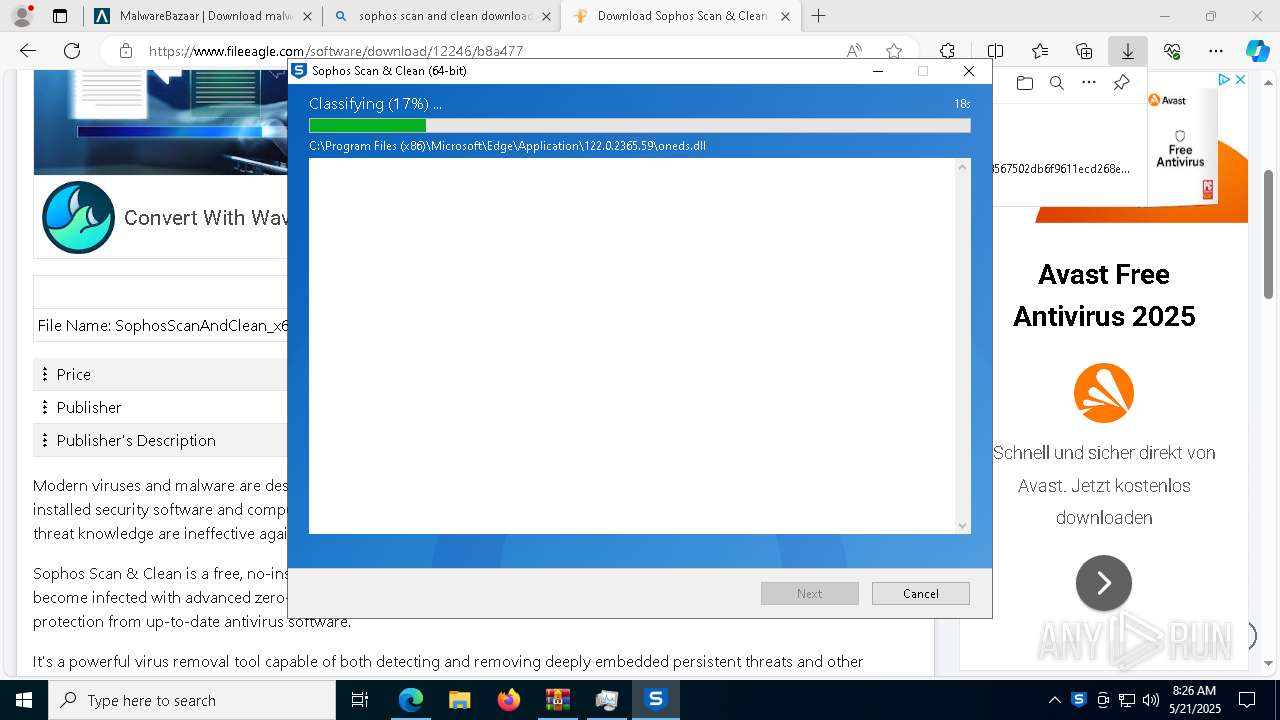
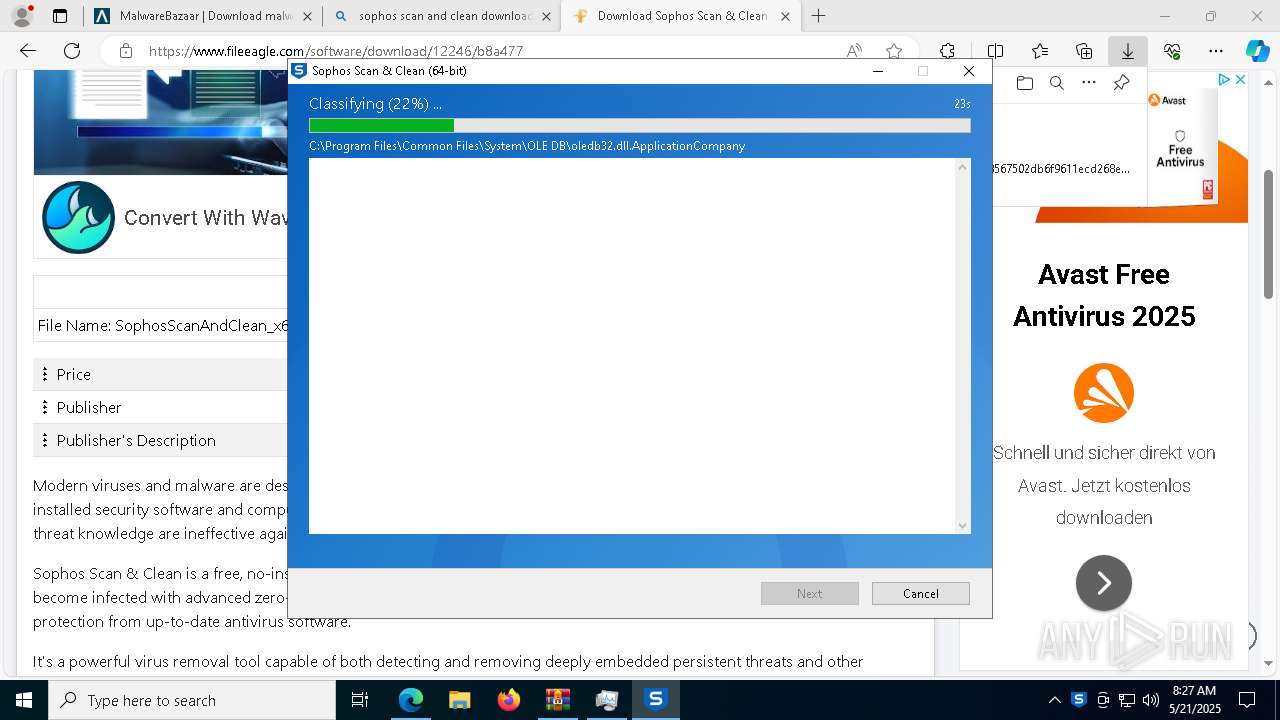
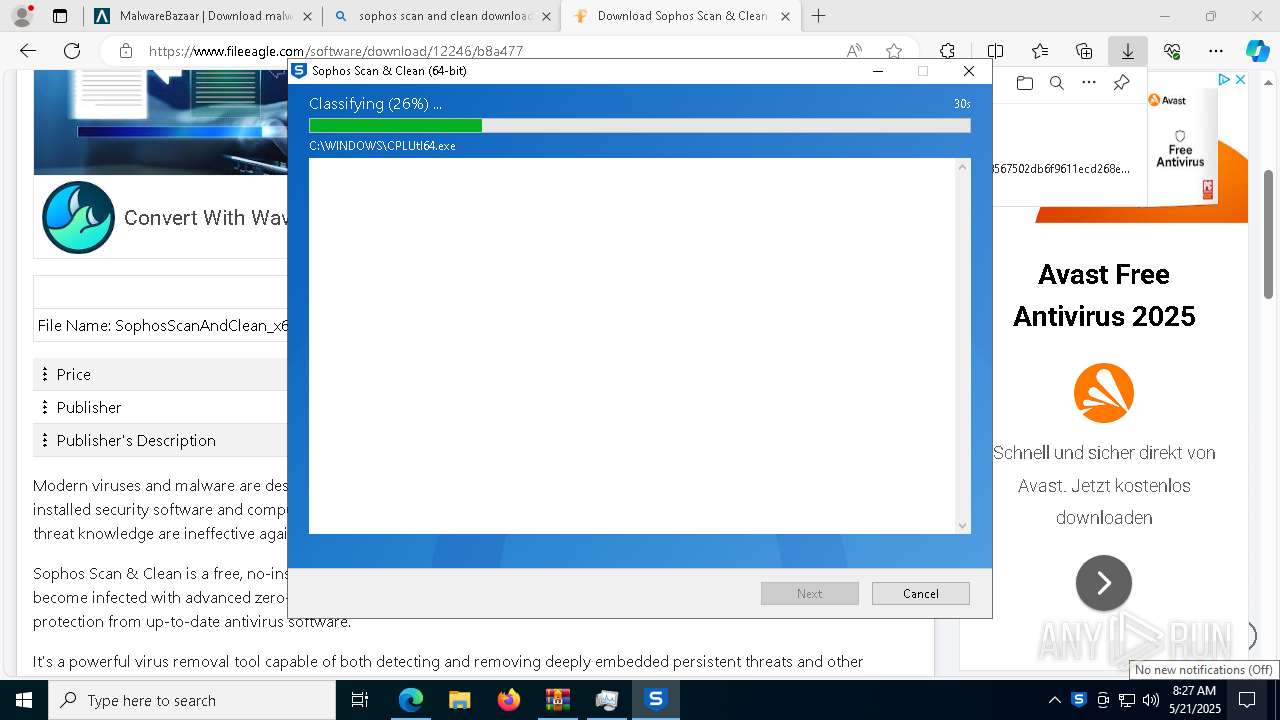
- SophosScanAndClean_x64.exe (PID: 7832)
Starts CMD.EXE for commands execution
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7756)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 7888)
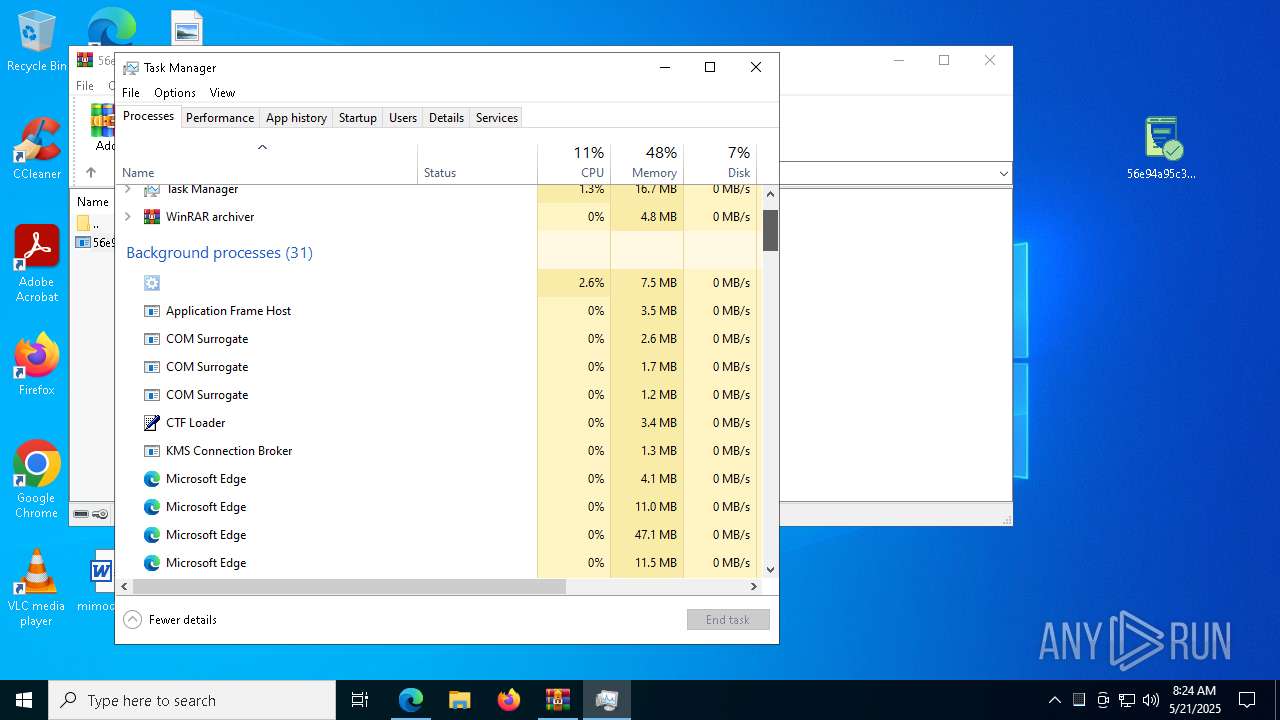
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 8076)
- svchost.exe (PID: 5780)
- svchost.exe (PID: 6592)
Executing commands from a ".bat" file
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2064)
Connects to unusual port
- svchost.exe (PID: 2064)
Drops a system driver (possible attempt to evade defenses)
- SophosScanAndClean_x64.exe (PID: 7832)
INFO
Reads Environment values
- identity_helper.exe (PID: 6388)
Reads the computer name
- identity_helper.exe (PID: 6388)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- svchost.exe (PID: 8076)
- svchost.exe (PID: 5780)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
- svchost.exe (PID: 6592)
- svchost.exe (PID: 2064)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2800)
Checks supported languages
- identity_helper.exe (PID: 6388)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- svchost.exe (PID: 8076)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
- svchost.exe (PID: 5780)
- svchost.exe (PID: 6592)
- svchost.exe (PID: 2064)
Application launched itself
- msedge.exe (PID: 2800)
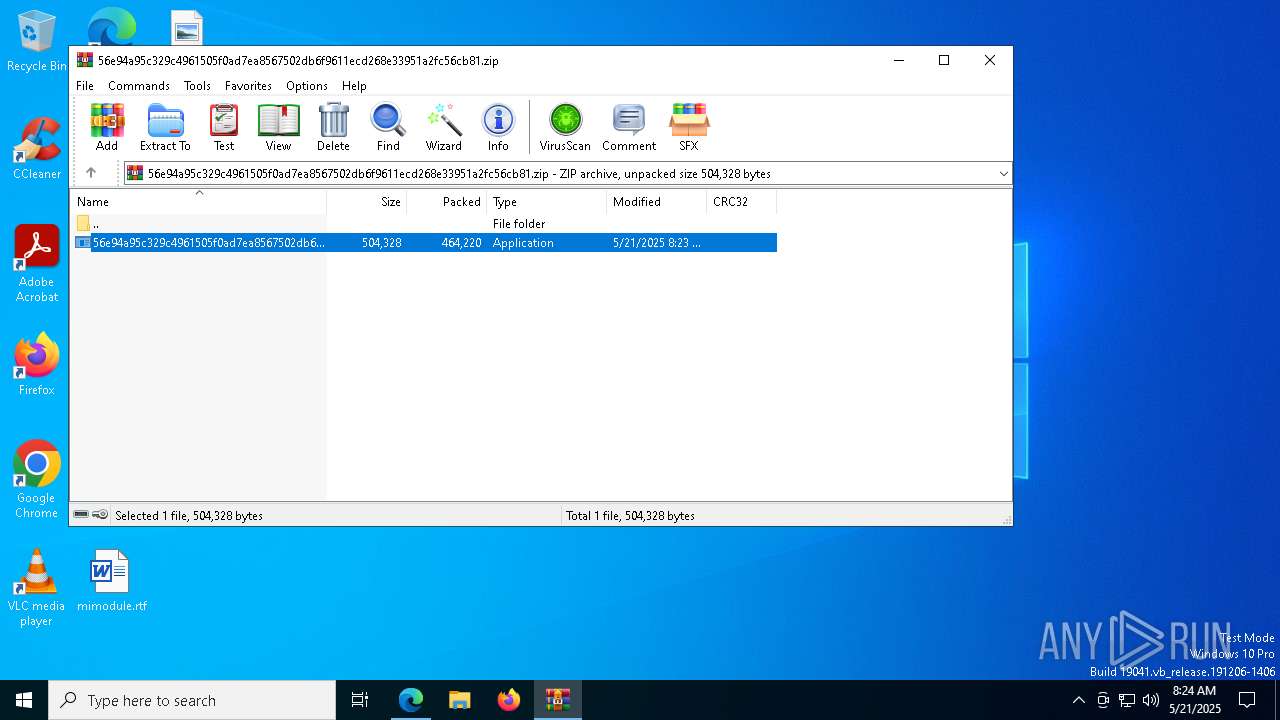
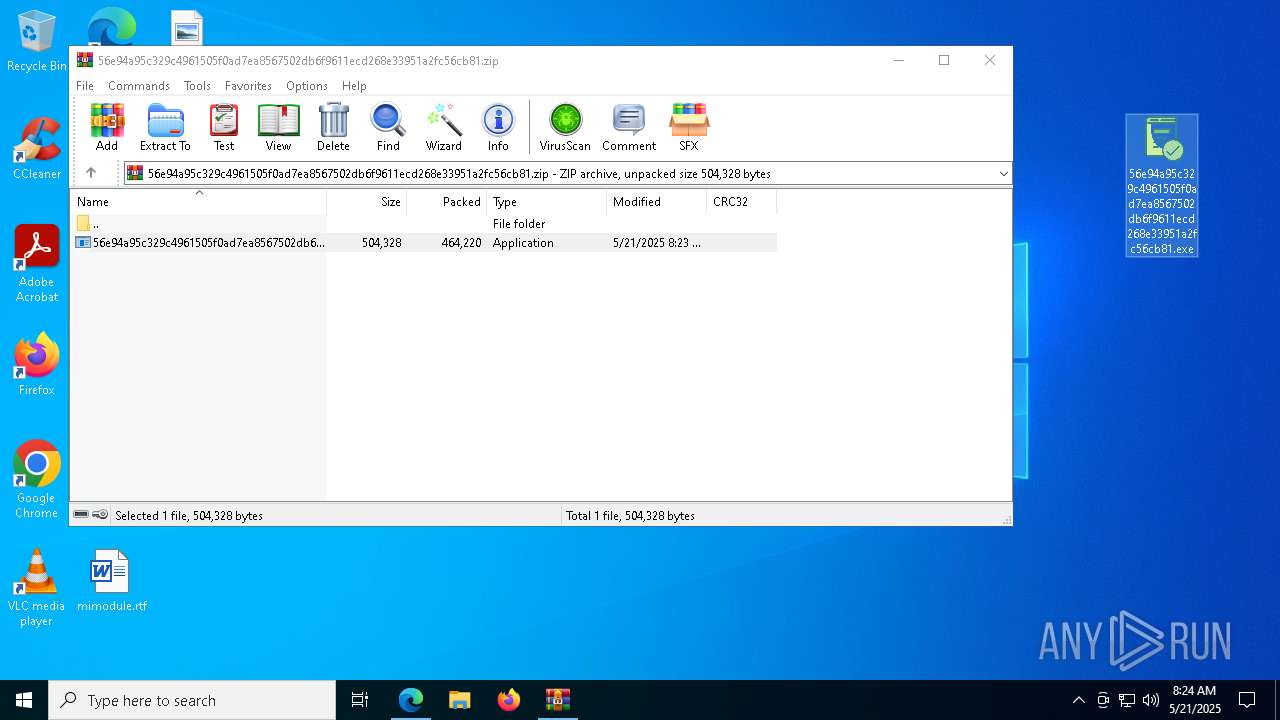
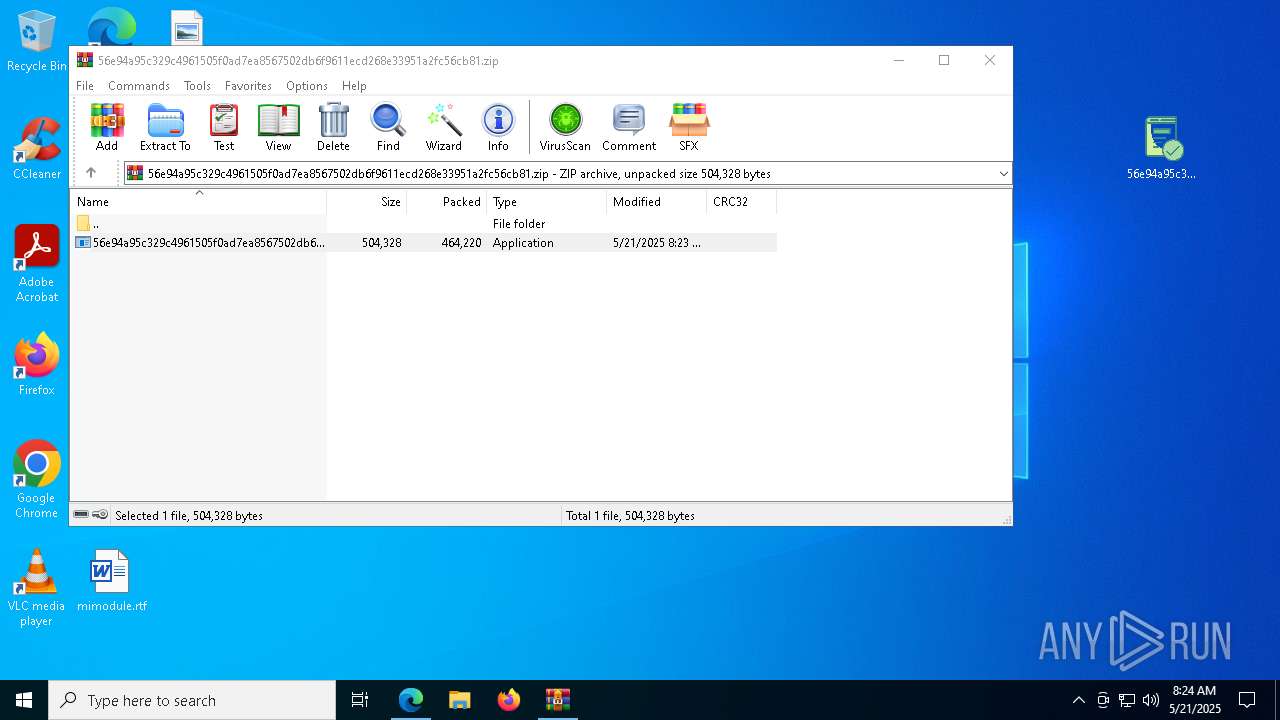
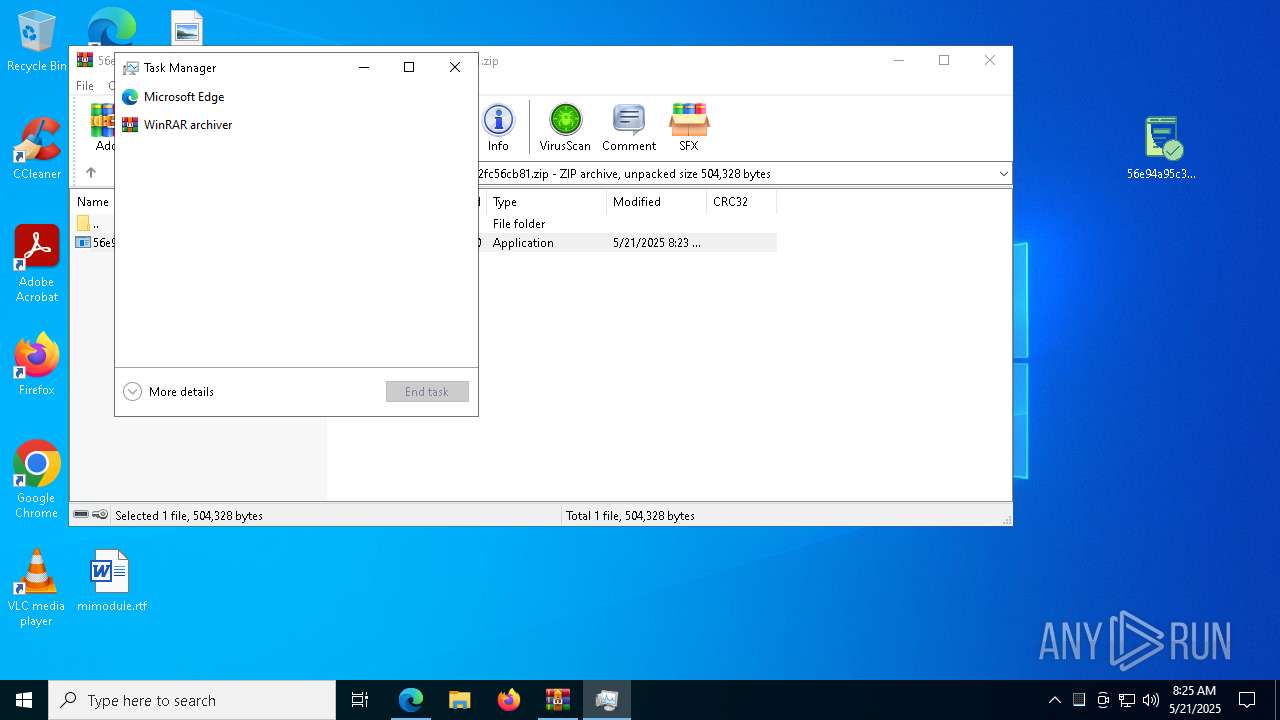
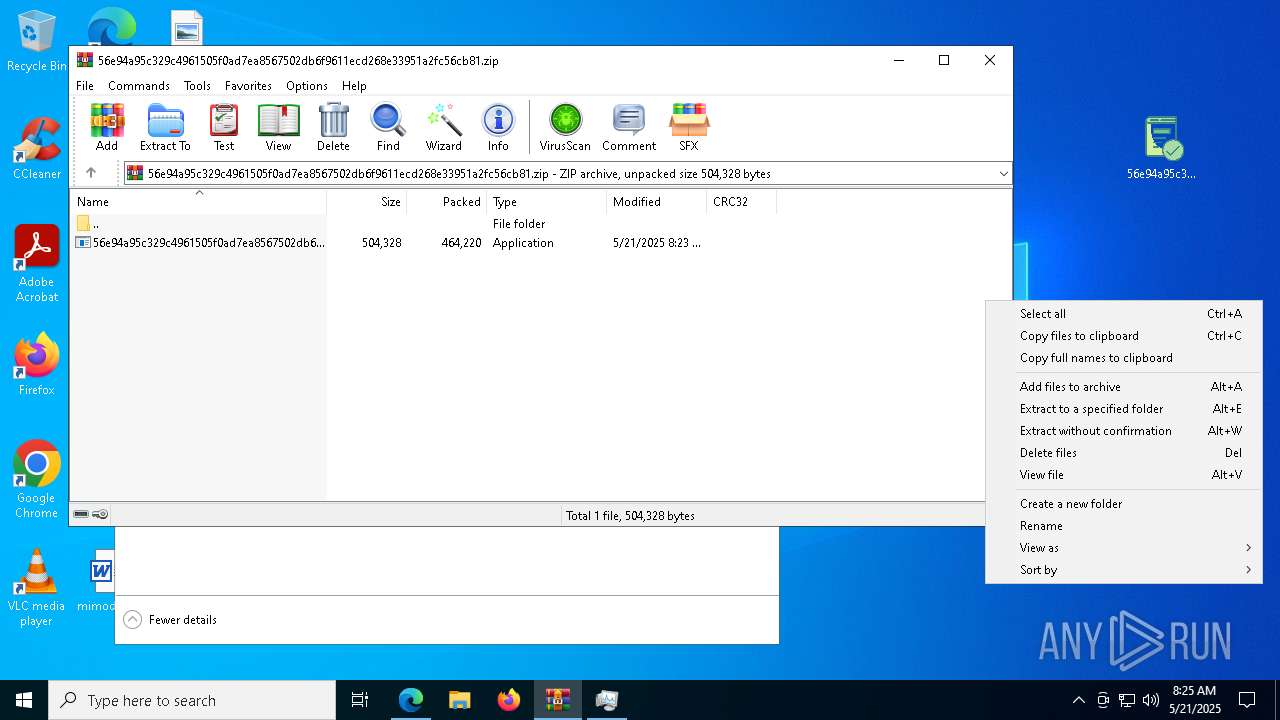
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7520)
- msedge.exe (PID: 2800)
- msedge.exe (PID: 7260)
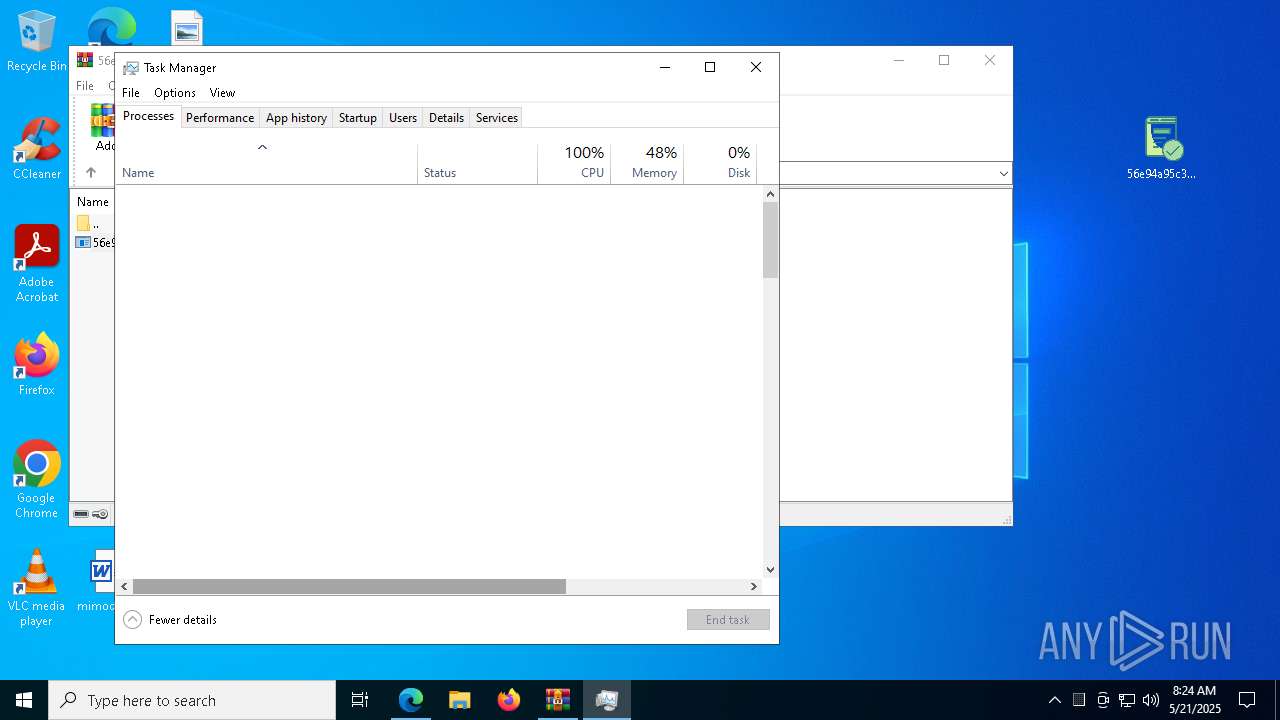
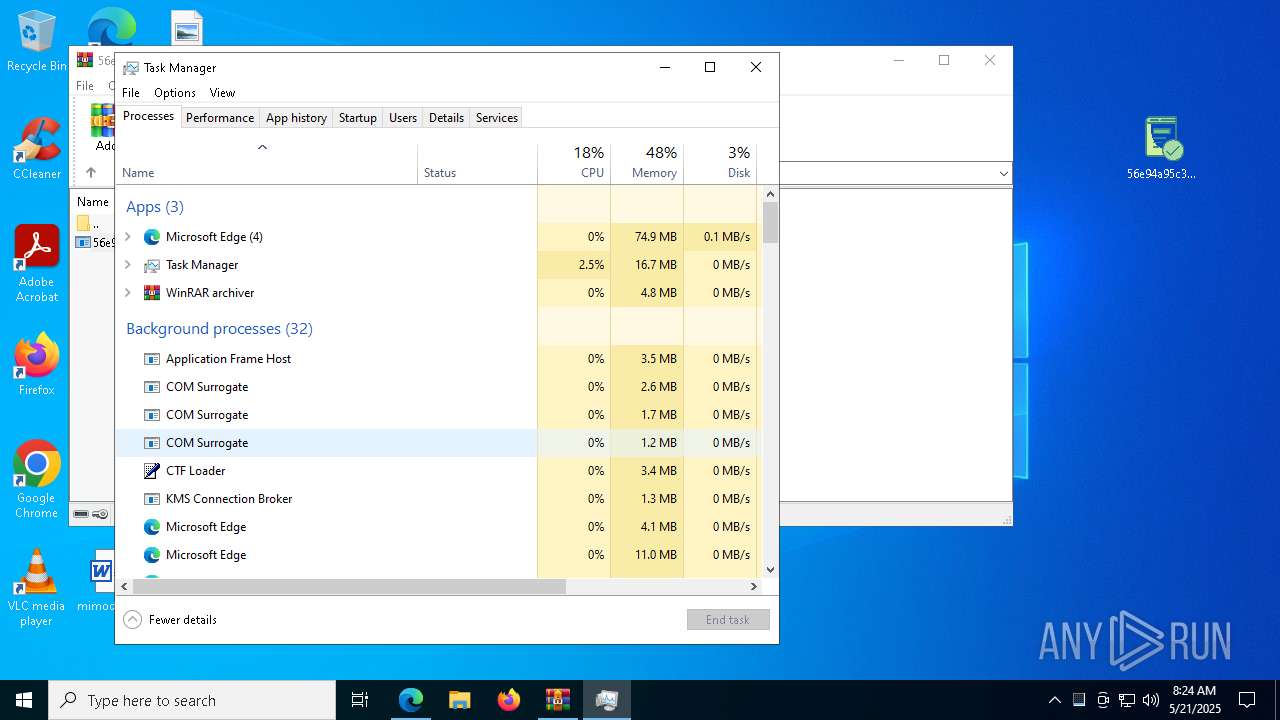
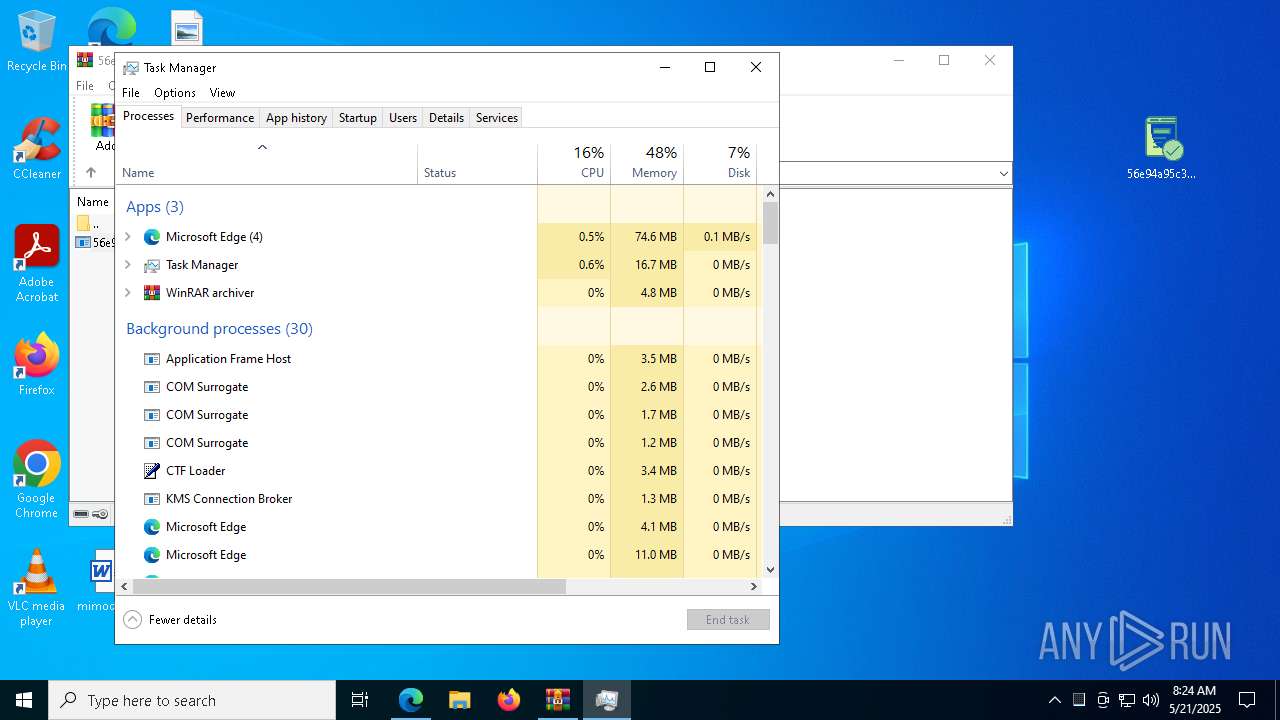
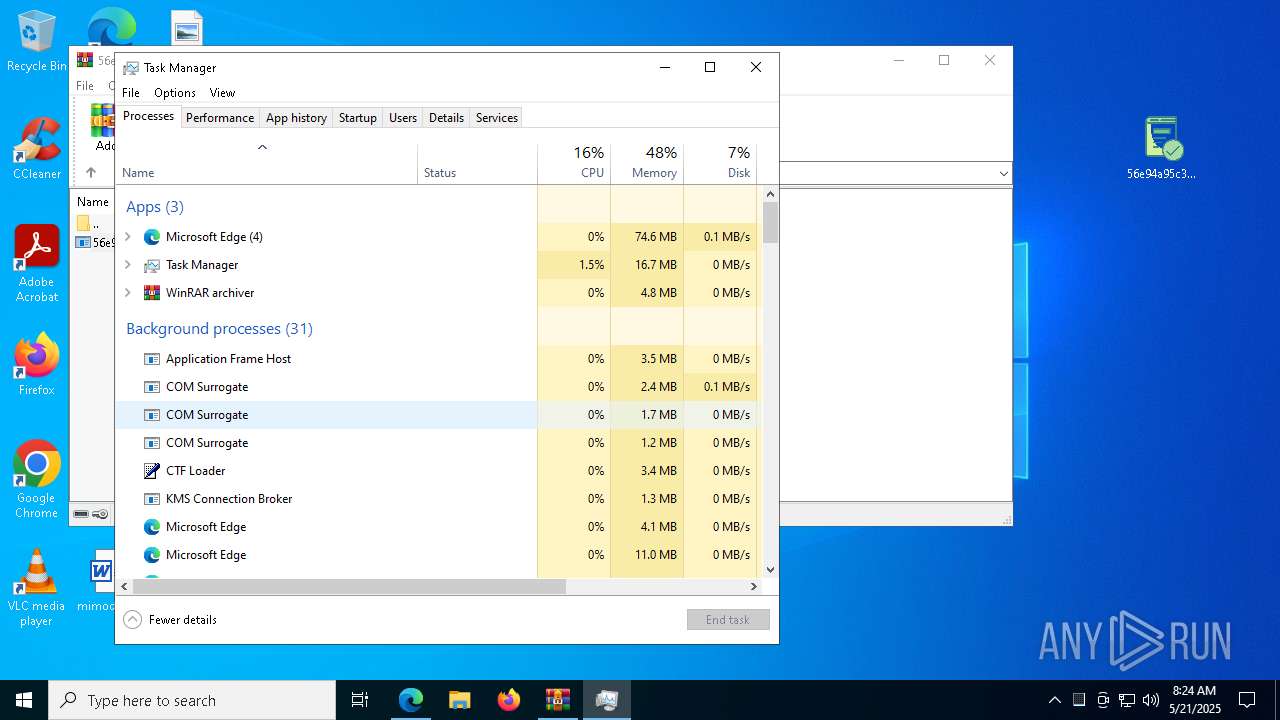
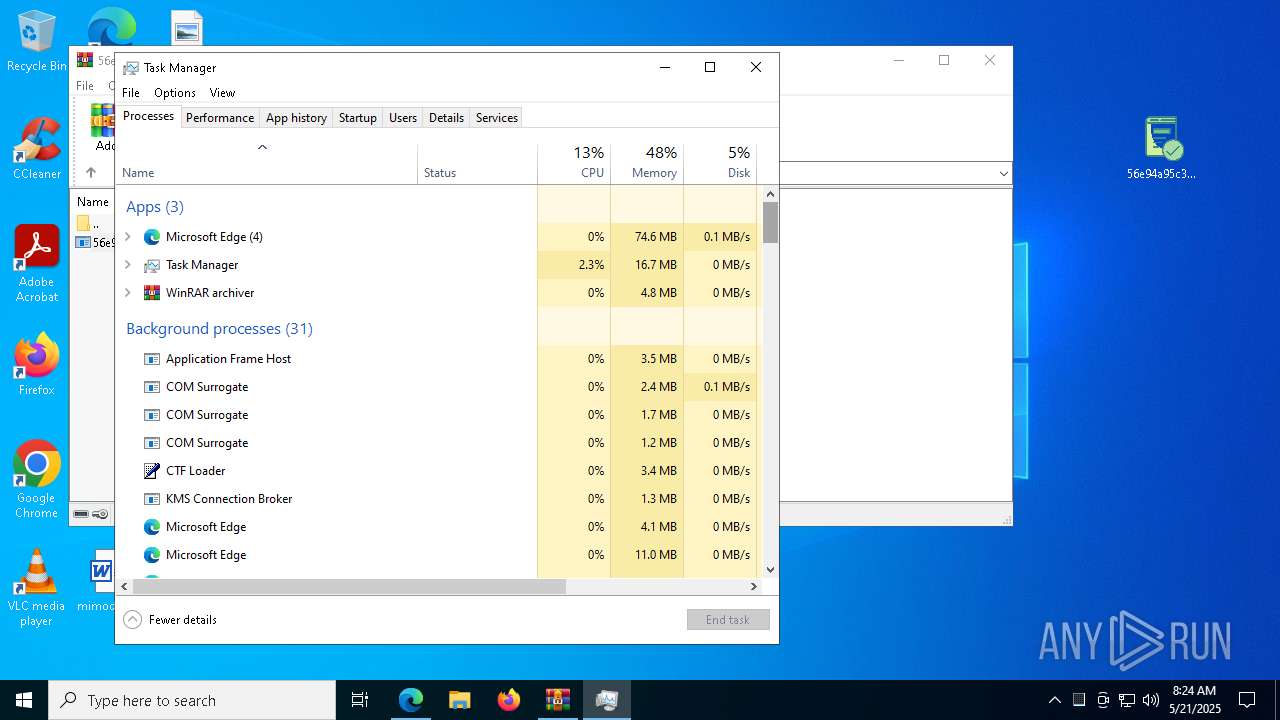
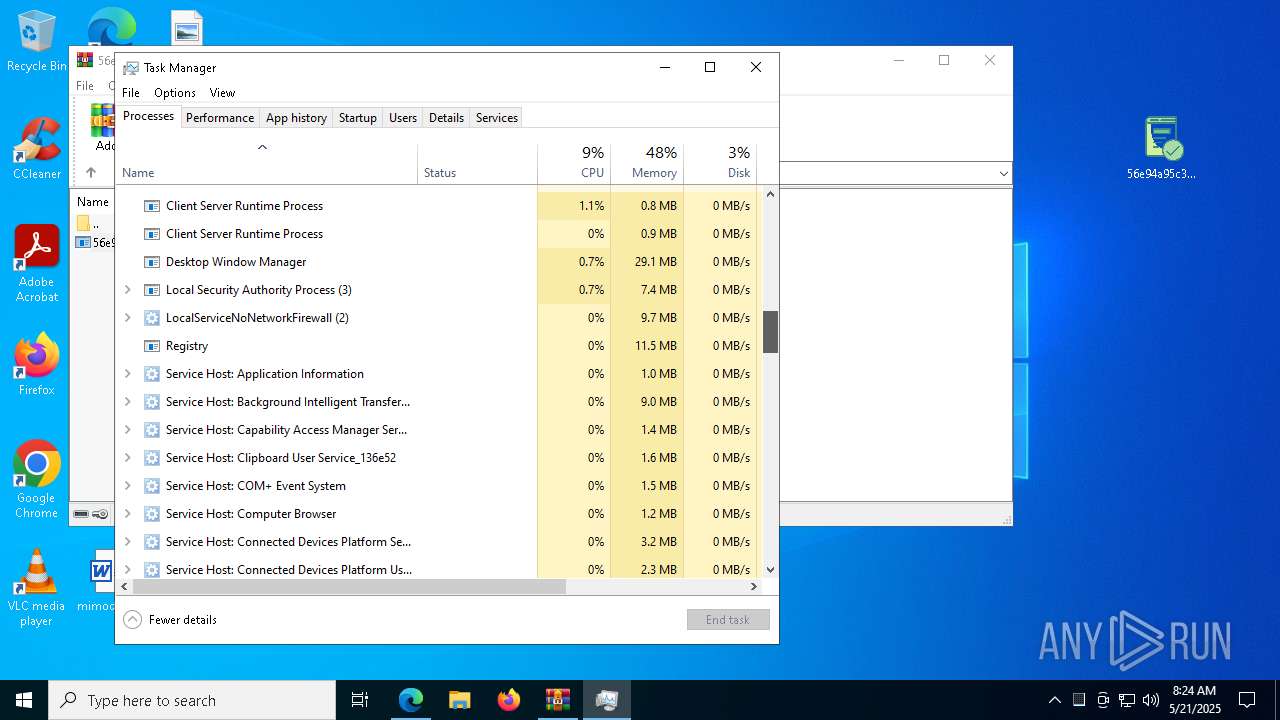
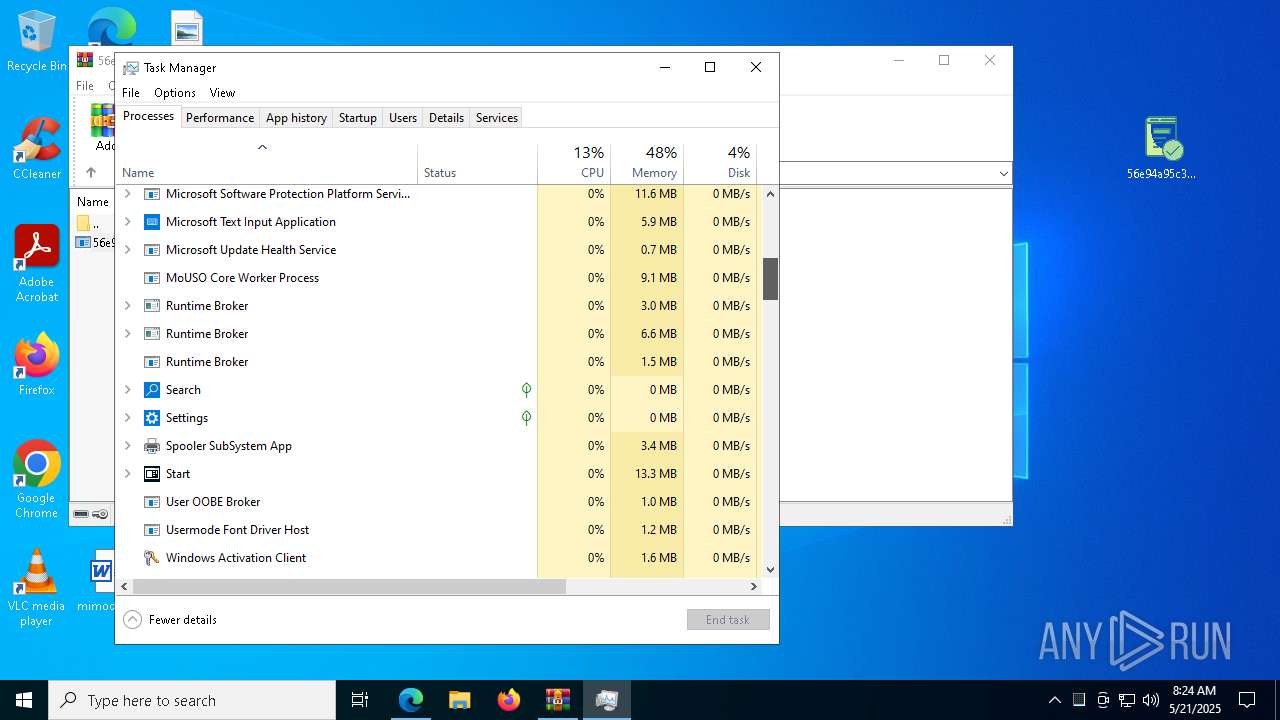
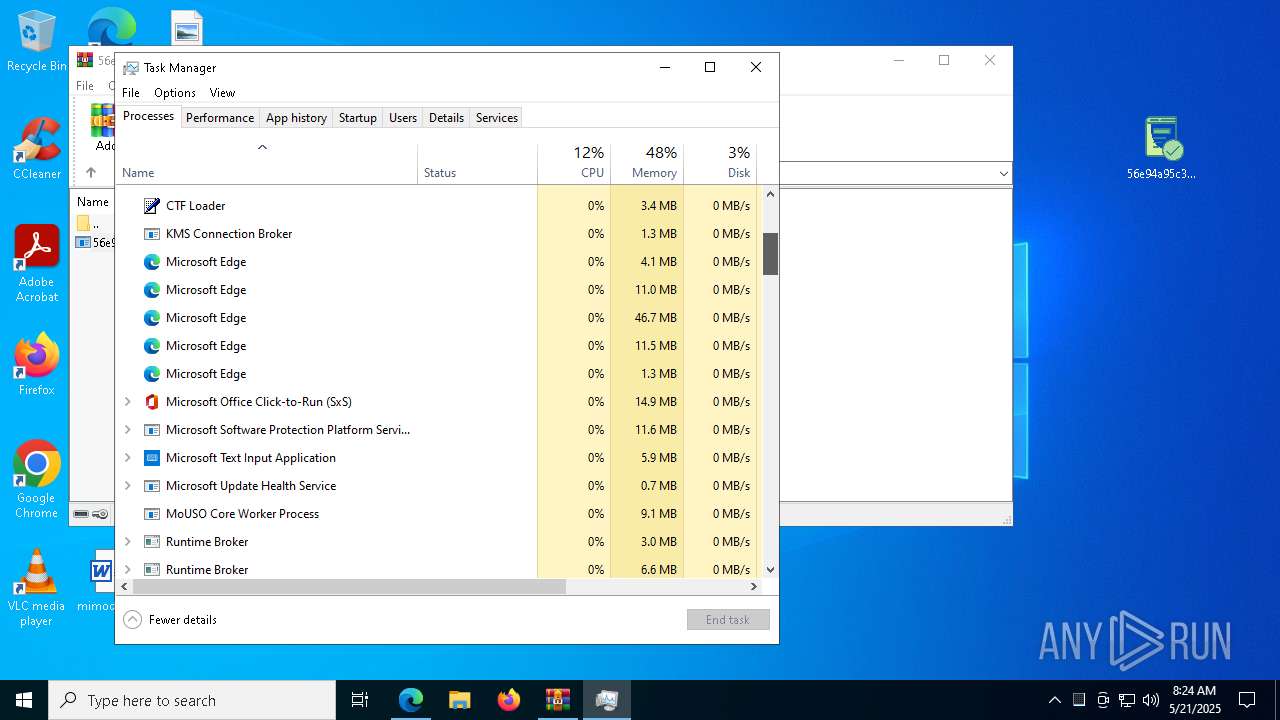
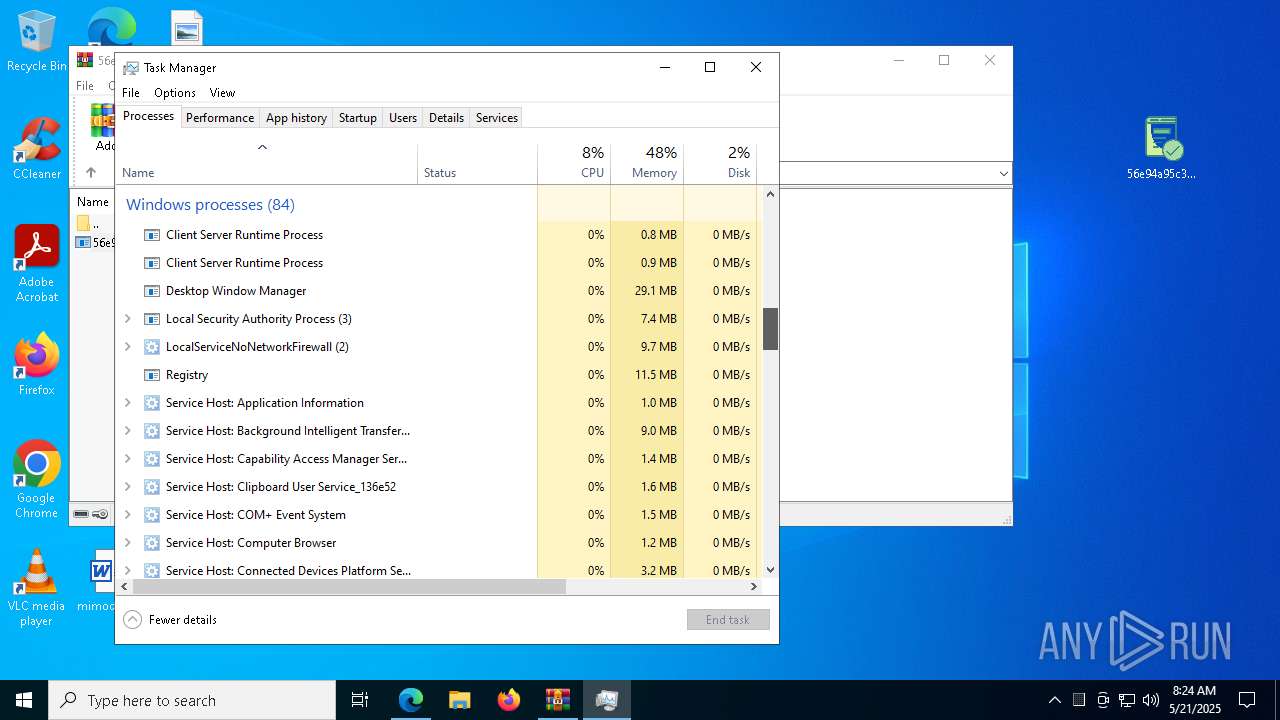
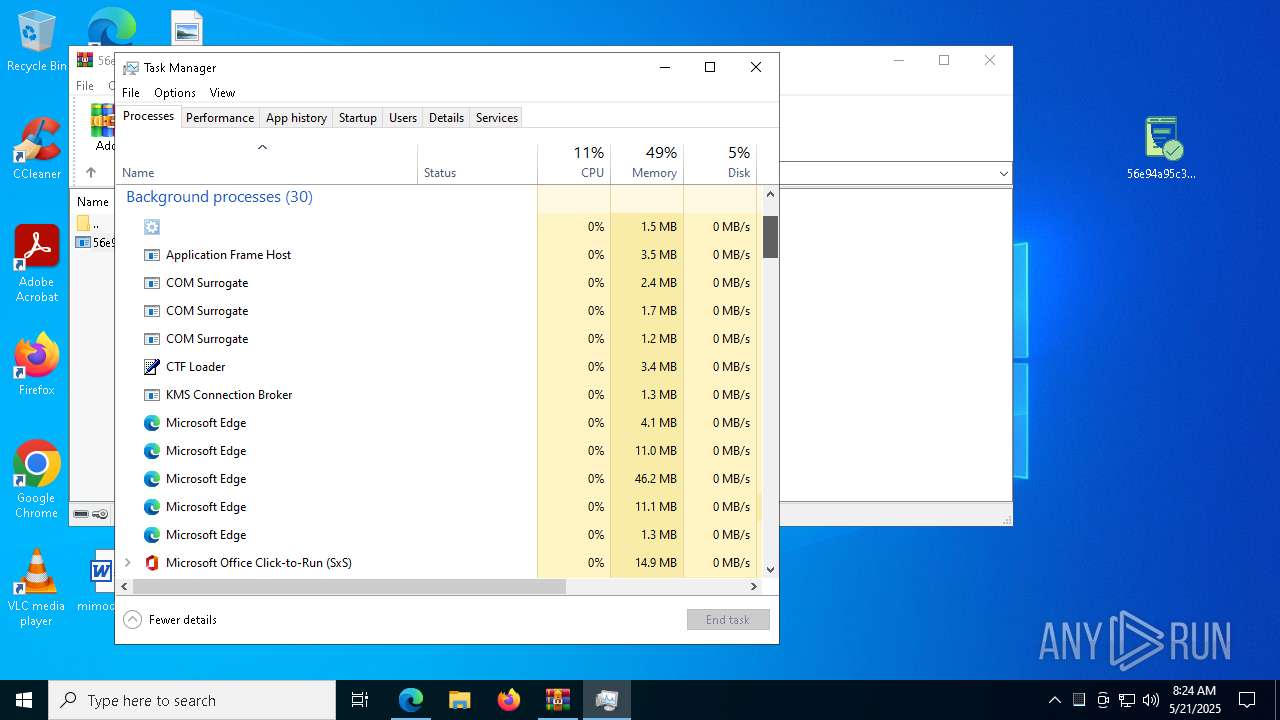
Manual execution by a user
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
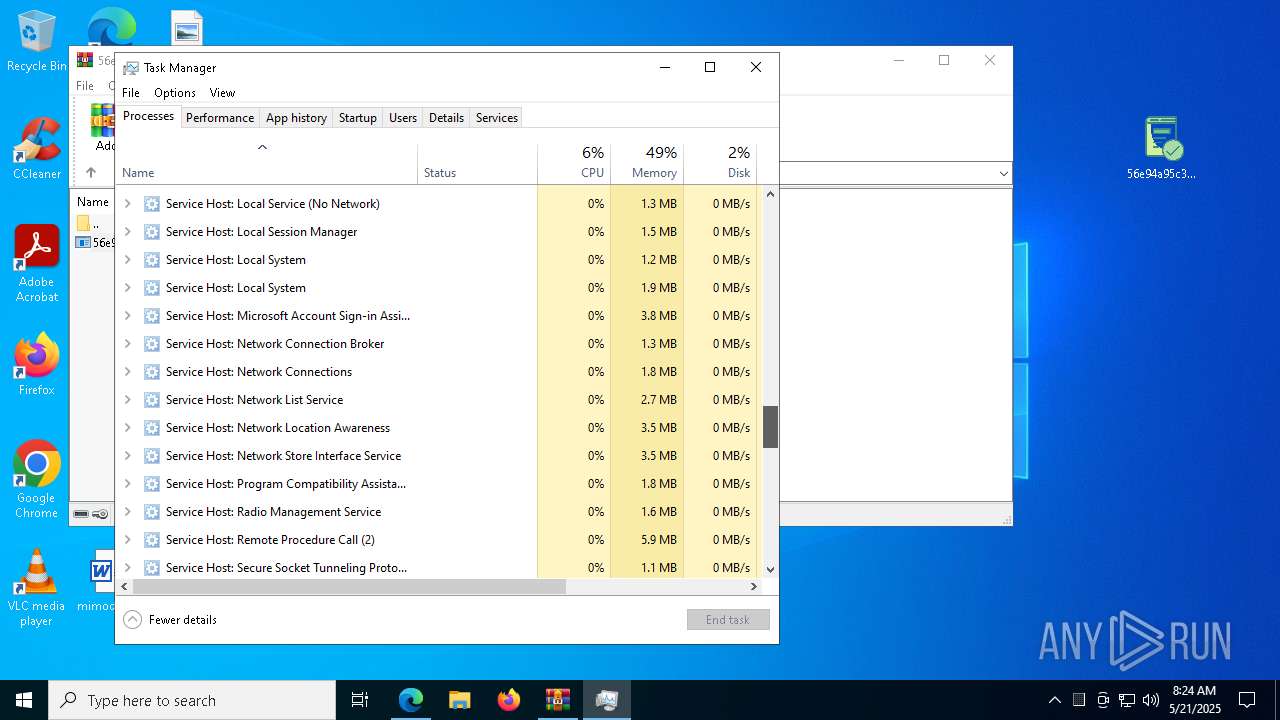
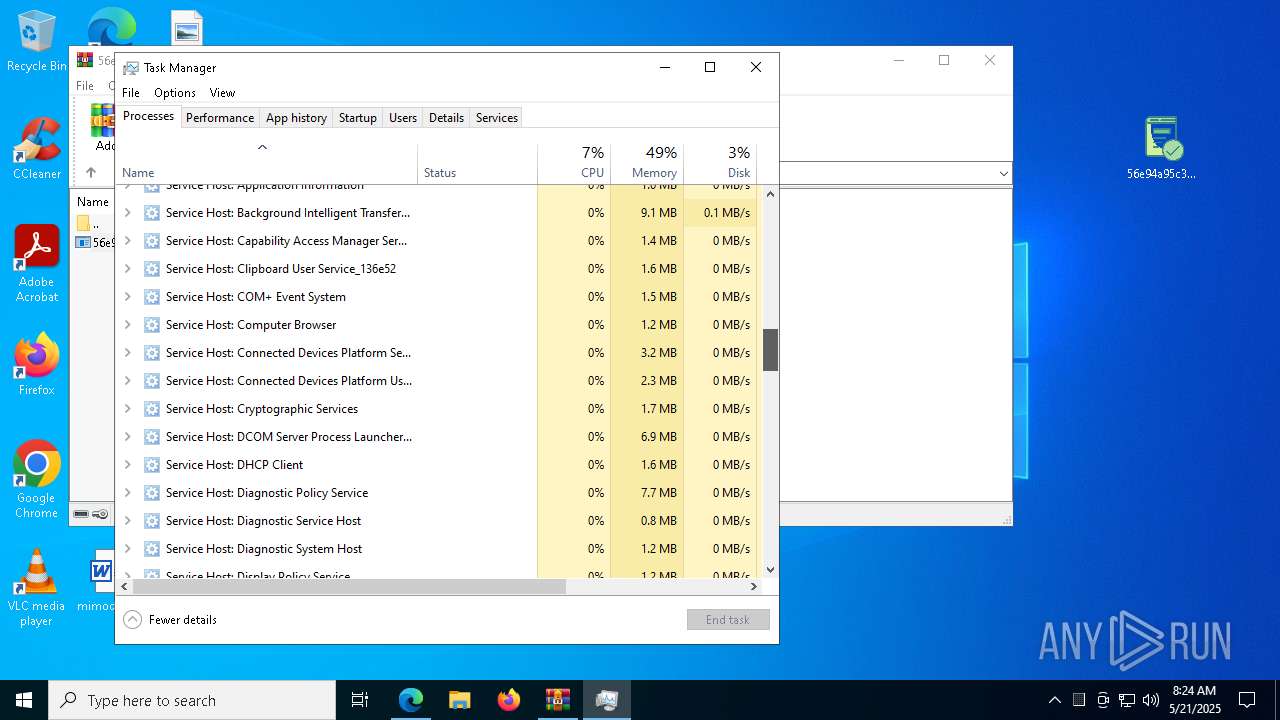
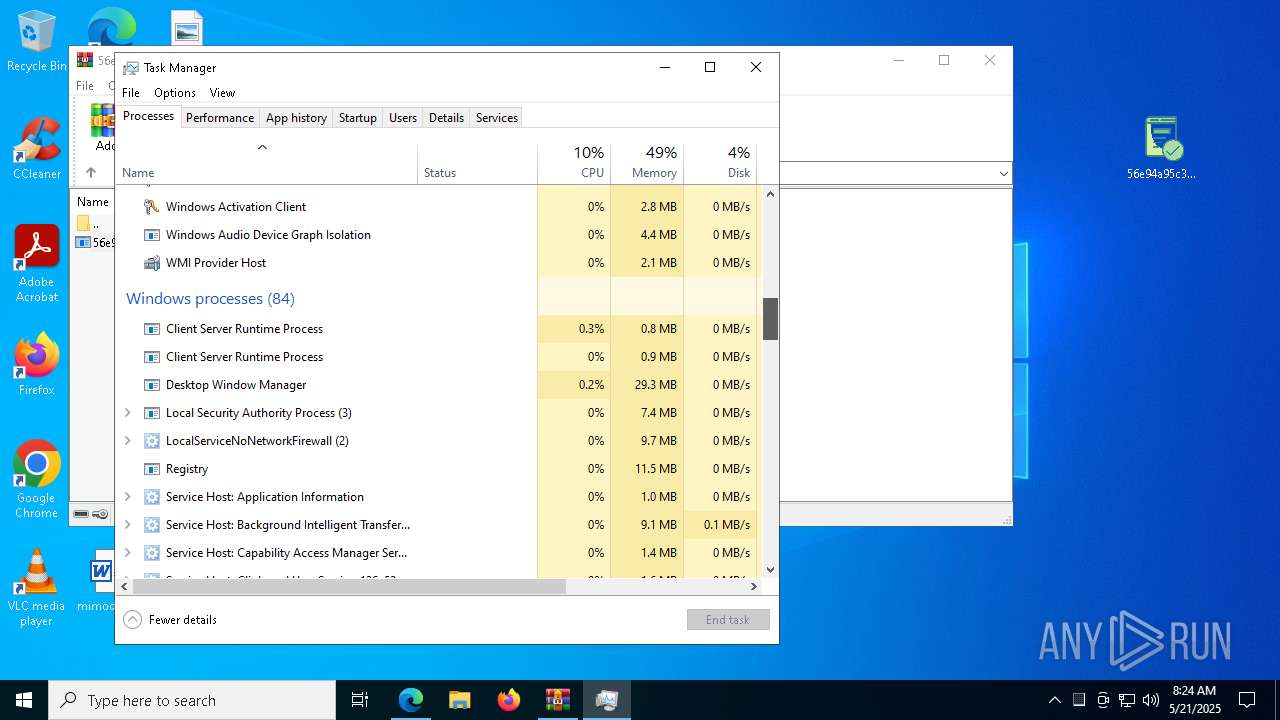
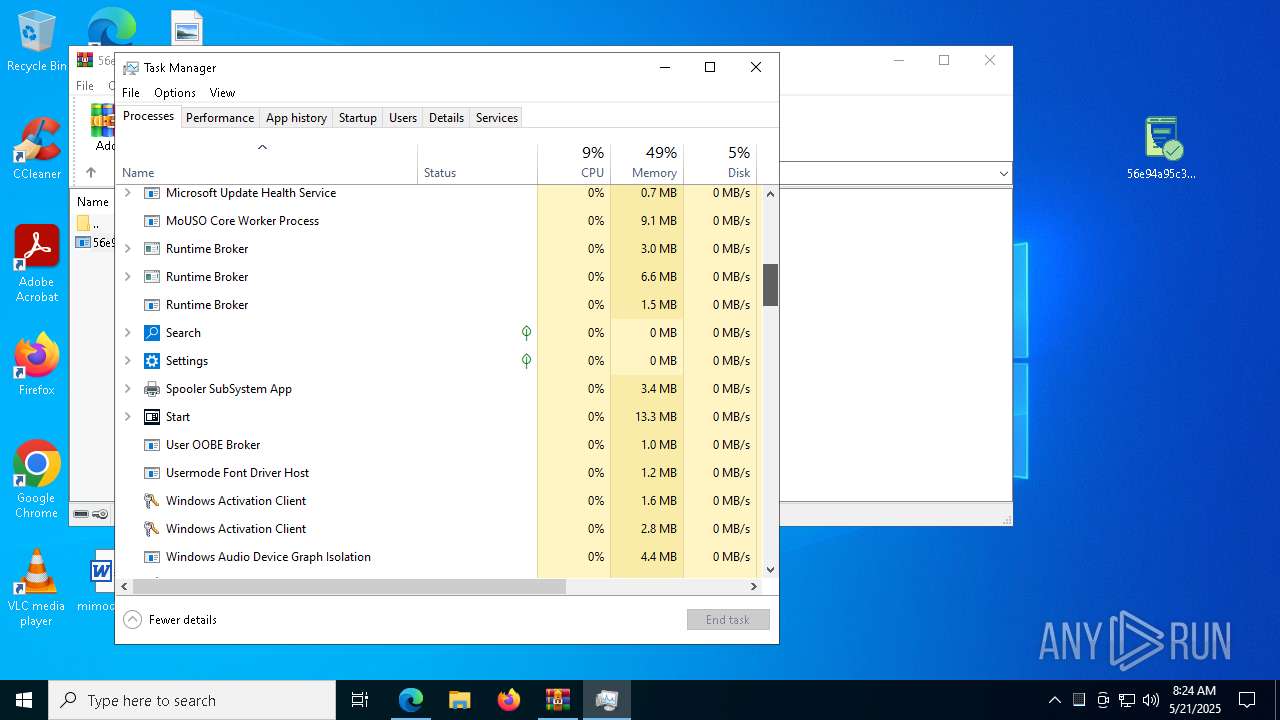
- Taskmgr.exe (PID: 4188)
- Taskmgr.exe (PID: 6148)
Reads the machine GUID from the registry
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 4488)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- svchost.exe (PID: 8076)
- svchost.exe (PID: 5780)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
- svchost.exe (PID: 6592)
- svchost.exe (PID: 2064)
.NET Reactor protector has been detected
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 2240)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 6424)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 4188)
Reads the software policy settings
- slui.exe (PID: 7476)
- svchost.exe (PID: 2064)
- slui.exe (PID: 6824)
Create files in a temporary directory
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
Creates files or folders in the user directory
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 7740)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 5988)
- 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe (PID: 660)
Checks proxy server information
- slui.exe (PID: 6824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
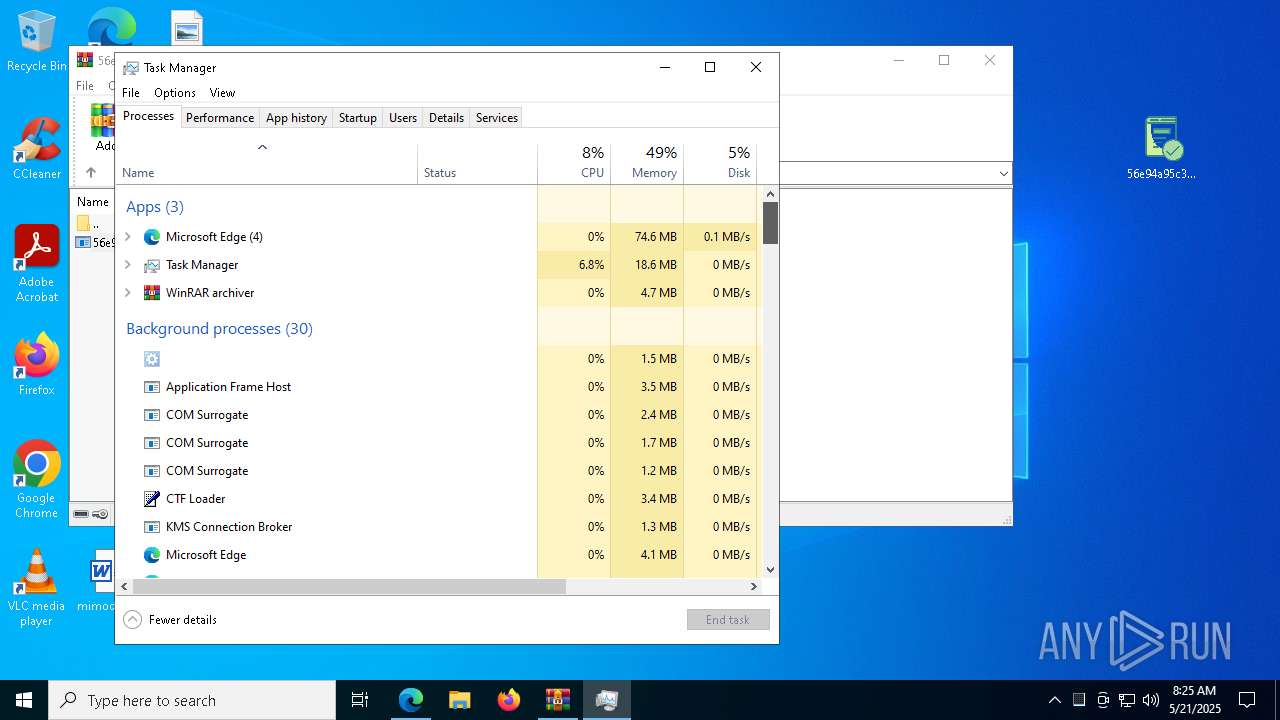
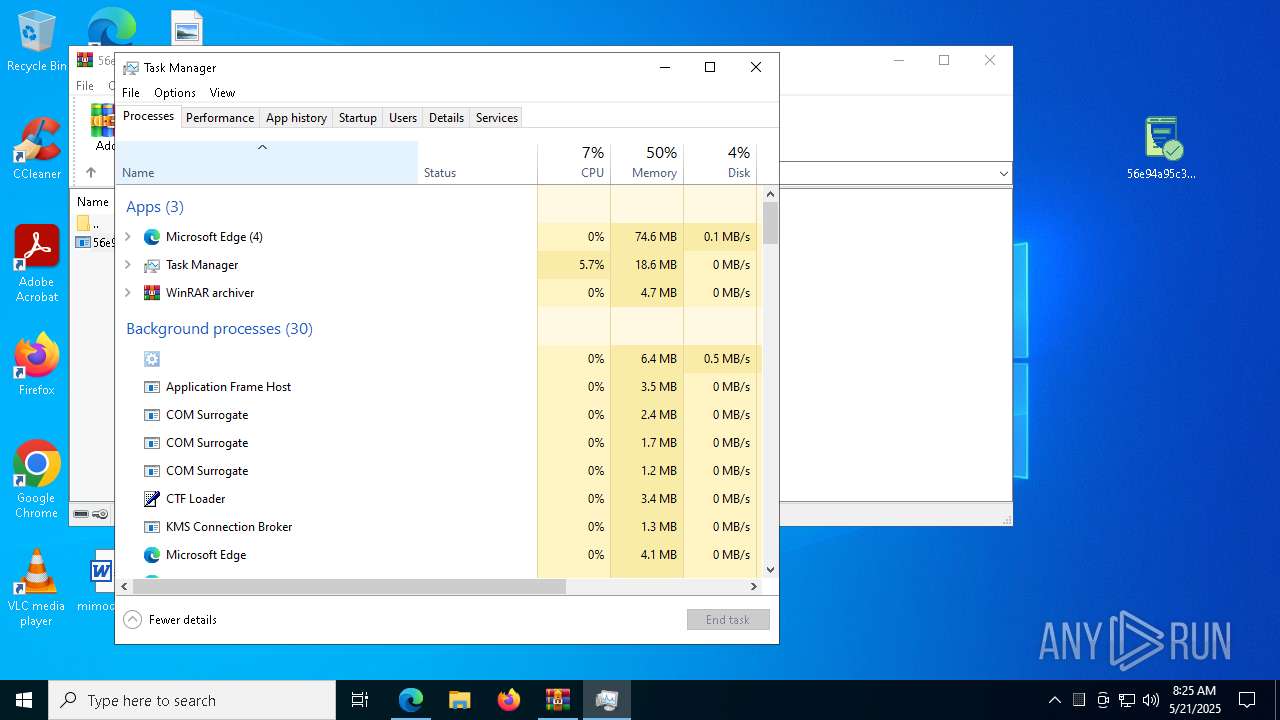
Total processes
226
Monitored processes
89
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\Desktop\56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe" | C:\Users\admin\Desktop\56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe | 56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe | ||||||||||||
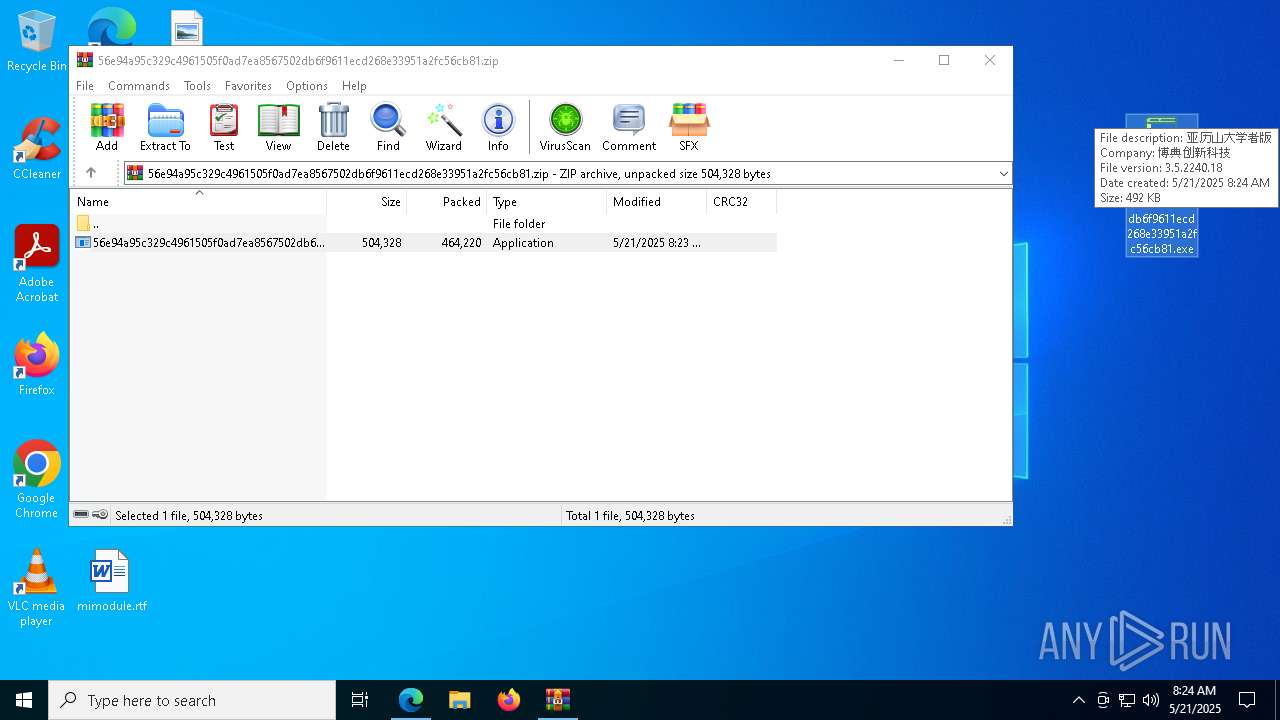
User: admin Company: 博典创新科技 Integrity Level: MEDIUM Description: 亚历山大学者版 Exit code: 0 Version: 3.5.2240.18 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6864 --field-trial-handle=2284,i,1240297481815831849,3812843454289307648,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --mojo-platform-channel-handle=5116 --field-trial-handle=2284,i,1240297481815831849,3812843454289307648,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=6008 --field-trial-handle=2284,i,1240297481815831849,3812843454289307648,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
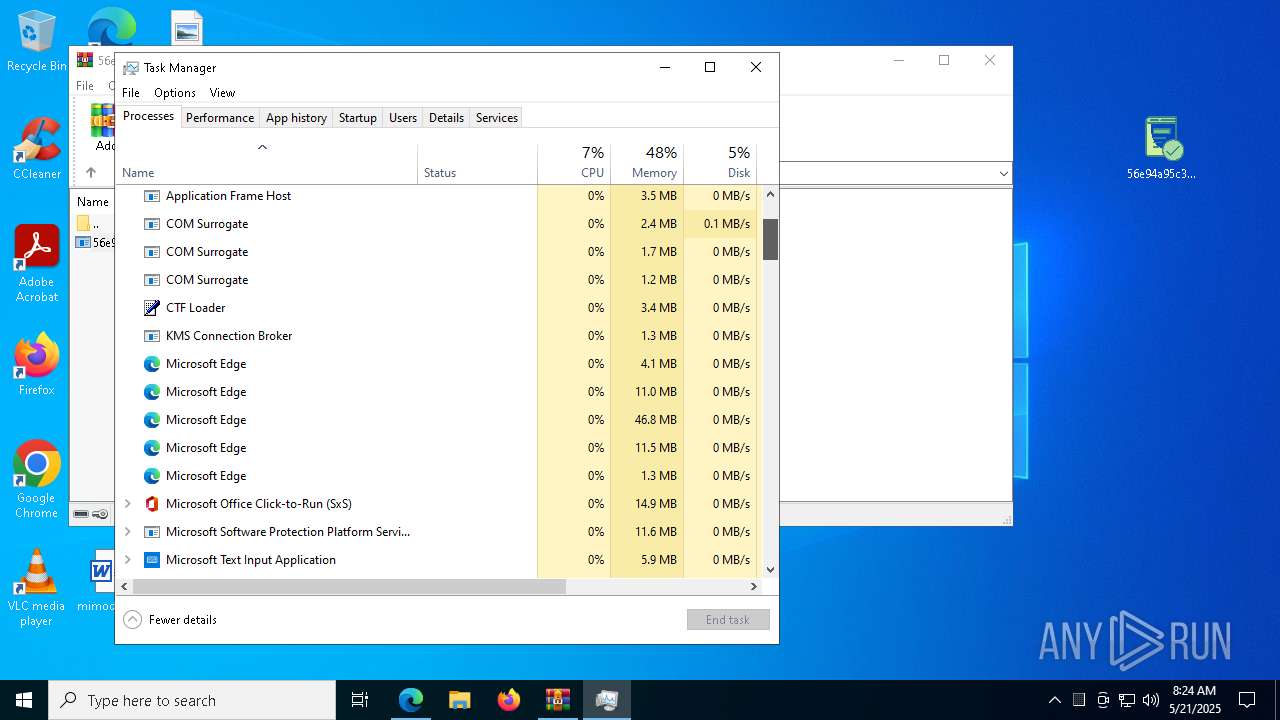
| 2064 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: 博典创新科技 Integrity Level: MEDIUM Description: 亚历山大学者版 Version: 3.5.2240.18 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6764 --field-trial-handle=2284,i,1240297481815831849,3812843454289307648,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\Desktop\56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe" | C:\Users\admin\Desktop\56e94a95c329c4961505f0ad7ea8567502db6f9611ecd268e33951a2fc56cb81.exe | — | explorer.exe | |||||||||||
User: admin Company: 博典创新科技 Integrity Level: MEDIUM Description: 亚历山大学者版 Exit code: 0 Version: 3.5.2240.18 Modules
| |||||||||||||||
| 2772 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://bazaar.abuse.ch/browse/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
57 879
Read events
57 771
Write events
96
Delete events
12
Modification events
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D528F65B37942F00 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AF3E495C37942F00 | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262994 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D90F59F7-51B2-4A0D-A566-227D4F294B0D} | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262994 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C797E16F-39A8-4CB8-B5C1-809B13EFB1CA} | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262994 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FED8FBFB-1A18-4917-A2A0-020D36FEA9BF} | |||
| (PID) Process: | (2800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262994 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E866373C-AD11-471B-B36C-3C6FE145B266} | |||
Executable files
51
Suspicious files
720
Text files
124
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d2f2.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d2f2.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d301.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d301.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d34f.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
162
DNS requests
181
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6132 | svchost.exe | HEAD | 200 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1748301539&P2=404&P3=2&P4=XNFFPjjJ4LBzli7KzZMbTIcYRwo6dRX7mBFbCiO6LTrpxdq4k2ULsEAuOpqj0ioYwUp%2fElUWunXUEk68rlUJQg%3d%3d | unknown | — | — | whitelisted |
6132 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1748301539&P2=404&P3=2&P4=XNFFPjjJ4LBzli7KzZMbTIcYRwo6dRX7mBFbCiO6LTrpxdq4k2ULsEAuOpqj0ioYwUp%2fElUWunXUEk68rlUJQg%3d%3d | unknown | — | — | whitelisted |
6132 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1748301539&P2=404&P3=2&P4=XNFFPjjJ4LBzli7KzZMbTIcYRwo6dRX7mBFbCiO6LTrpxdq4k2ULsEAuOpqj0ioYwUp%2fElUWunXUEk68rlUJQg%3d%3d | unknown | — | — | whitelisted |
6132 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1748301539&P2=404&P3=2&P4=XNFFPjjJ4LBzli7KzZMbTIcYRwo6dRX7mBFbCiO6LTrpxdq4k2ULsEAuOpqj0ioYwUp%2fElUWunXUEk68rlUJQg%3d%3d | unknown | — | — | whitelisted |
6132 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1748301539&P2=404&P3=2&P4=XNFFPjjJ4LBzli7KzZMbTIcYRwo6dRX7mBFbCiO6LTrpxdq4k2ULsEAuOpqj0ioYwUp%2fElUWunXUEk68rlUJQg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2800 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7260 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7260 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
2064 | svchost.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2064 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
2064 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |