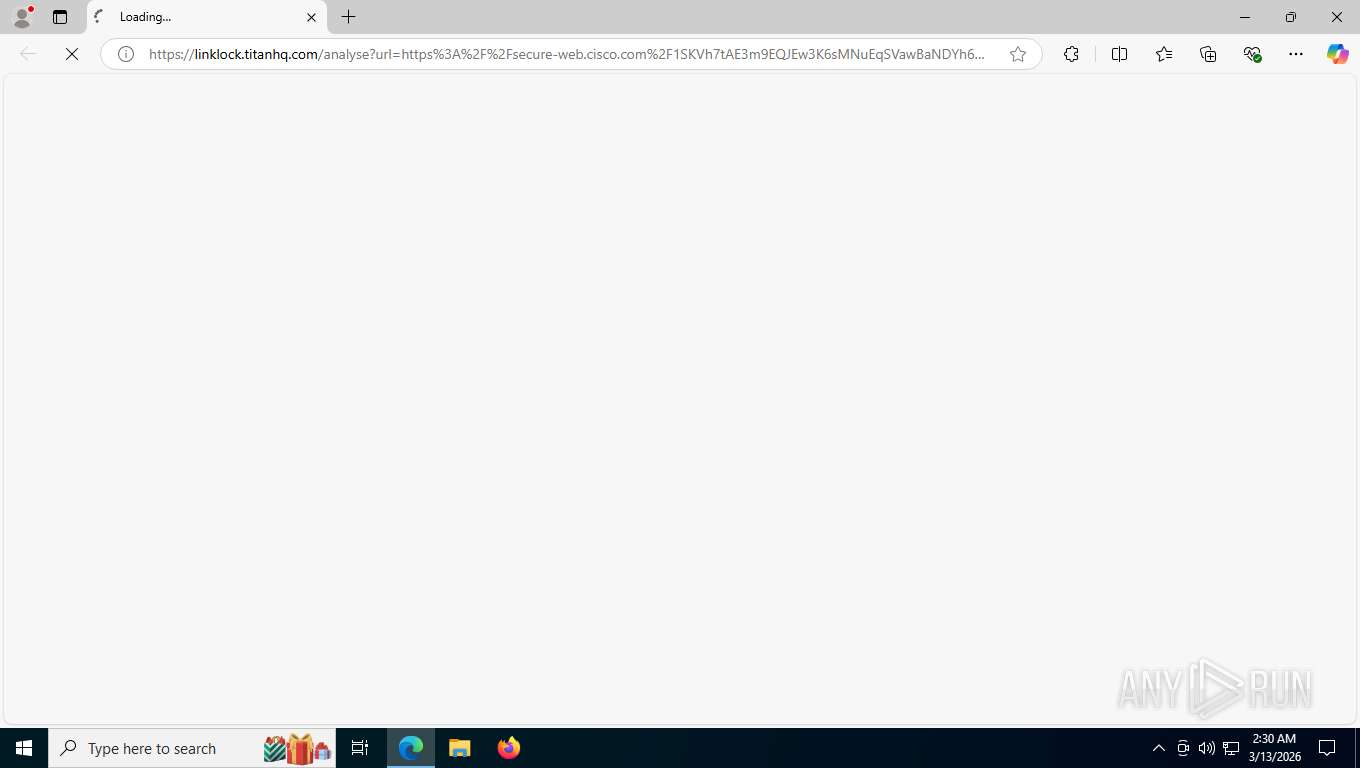
| URL: | https://linklock.titanhq.com/analyse?url=https%3A%2F%2Fsecure-web.cisco.com%2F1SKVh7tAE3m9EQJEw3K6sMNuEqSVawBaNDYh6n74jx-aX900oaWWT8L2T06OzbmKwTigwM6e0M-xaoFuDig_F58s7kRTGtFuE9EAW-7gfjy-HtU3W6TrzMKUlW_XW-RjtU4LzLaciZ67Ts_wVHKedbCrU3MfGIVRDdKLWeFtqAcpGXOdwbaUDPxyp-MoN6QxLQekbxb5IJa13XoG9-01y6ew32onHtiy1Zz028XEoPVPwwolOx8nMEtxsS6gPJa9C4yvrokAZ5QgtvWFKCh2I-ddF5ITEnHuGBR6ImHt0jeeLx2LlOB4JQy4GBF4jzaGyyILfLQClRrRdfixGPTr2nkBpT4fxWgq6WRT-0z84uSndO2MYqrhldbTXyMD4v07gwH4wHaOGqT-HHutWhzatY6B5ogdDGuNWy4G8WWRm_ZLfdGOELf2-woXfyYe-_pvkye4EbuW9OuuCqBBAkkFTyg%2Fhttps%253A%252F%252Fnotification.tokposter.com%252F&data=eJxlkkmTokAQhX9N940OZCng4AGURQFRRAu9GAUUiyylUMjy64eeOU5ERh7yvcw8vC9eA16RViKQWSDLq-9kXRUNRm1LSFo02U9M6u963XNxpEqq0Xkw_u7WT9IgmqPmS2BJFZO-oe2Uorb-627XcUW6Zbdb5P-P9euc0lf3xatfnLFUh-O-xcyAo5-46GLya1rGq7N9zSWq6nyt6Ke9PvA26NxDr7_PVzRo6LC95aCRhOfIoFBhWYIgDGSHC1jgzVFtD0GRDS7ArMuMiBj9tsgehih3UukHJjV6XdFVyEhZ-pwYi154CIJ2du1LBR8hZPwnvQjO7KC4uAMp6B7D1bJxEm3aC--m5u7qbxPbgdigbzV-maGXDBG6bI_j9GJccgCn0TnhMhojcbdHKz4kpsKwqwnggedIY9FiWt1nlpNDnRyvx2EglTfKjavTsTuD7LhHykaYPi0p1bt4yugHGvYm53ZMkhjiLtAbqzc1H-xqi7JPjJ2RcypPE_anSTA1Q3jOyJymnZM6p03lt36SFqN5DFquKbVXIKQjzN4A-gHDzrLQn5vE49zbu82rJArCyd0KH1bKBksYLOSZ74CxrJ7CfEb0BjSRZMnW7A9weSVD6NePu5Mmpqc7KccMJEynG2Yer085YUGPeqh4fb95a5palkYwZUuy_-LnxF8AxF8EltYQWqRFjGhBmh9KyhfpKG7_obDIfwBKxuPB |
| Full analysis: | https://app.any.run/tasks/02f940d8-171b-4cf5-ba2f-b11df3681ba7 |
| Verdict: | Malicious activity |
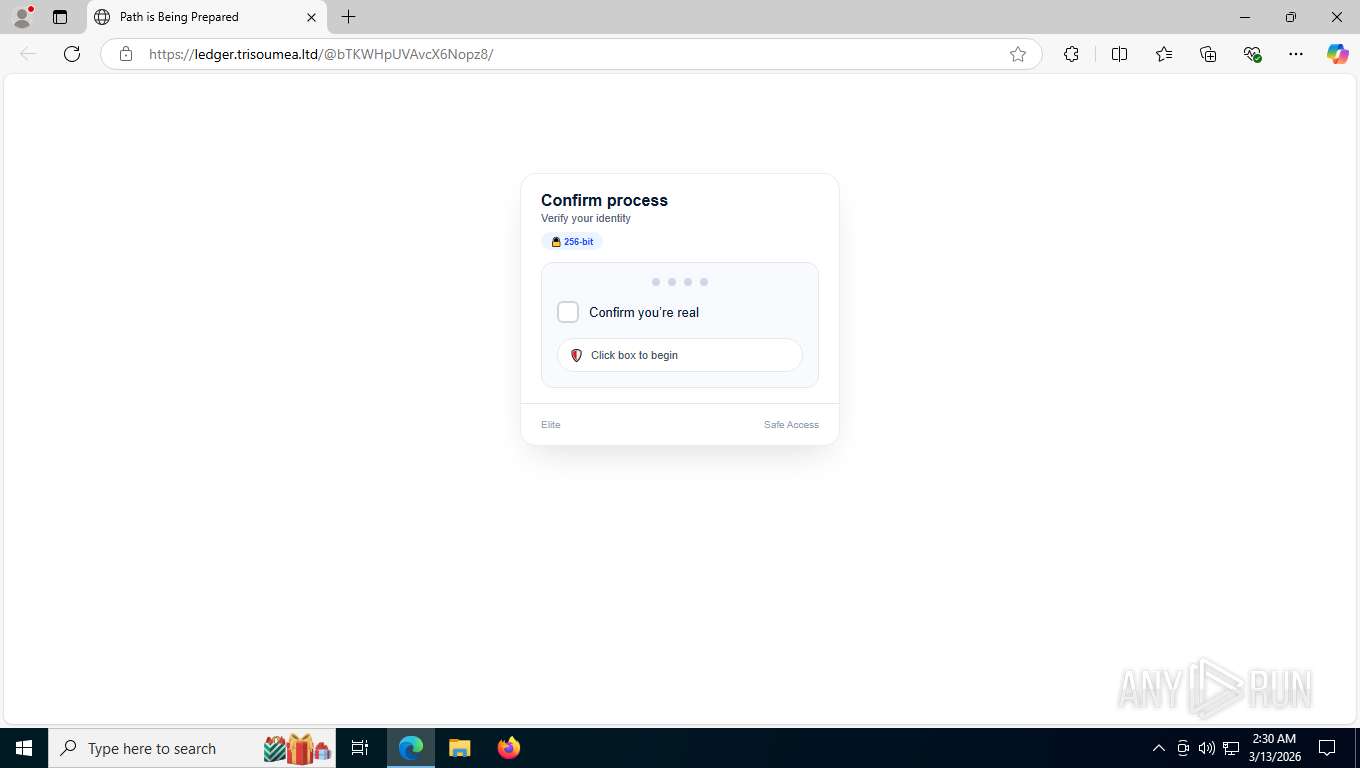
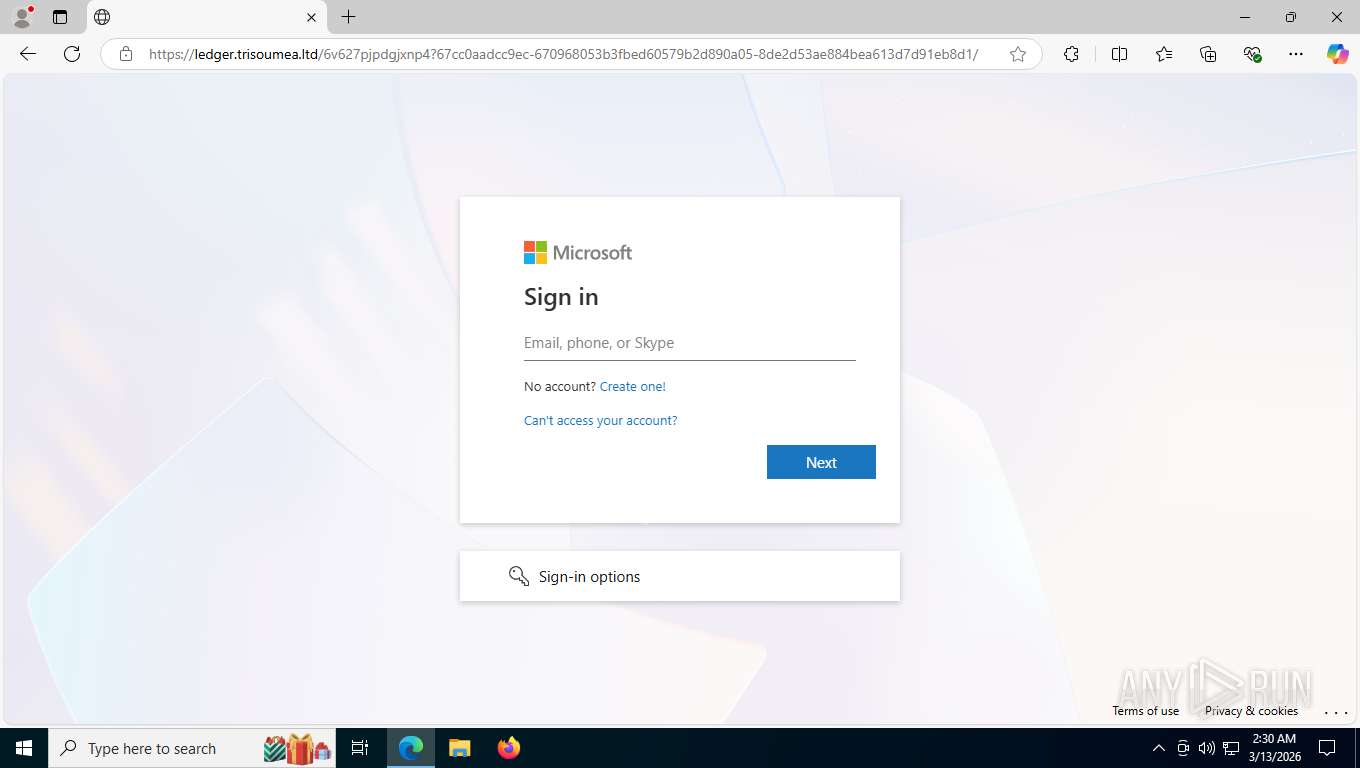
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | March 13, 2026, 06:30:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99B09CD38A2949C20CA0FD1E48779F4A |
| SHA1: | 0DED2DF36489743DCAB92919DA6CA23EC8C9476C |
| SHA256: | 5FA7AC3B94404A3A1889D3DD401158A822DF462A49D4149432DD8A956B28FFA4 |
| SSDEEP: | 24:2PevKlAb9BEtljPq0uK5JBXjFE326wVAHaum/QvbtKvDH:mwnEtl+4FjFS262A6HYRKLH |
MALICIOUS
PHISHING has been detected (ML)
- msedge.exe (PID: 8412)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 5440)
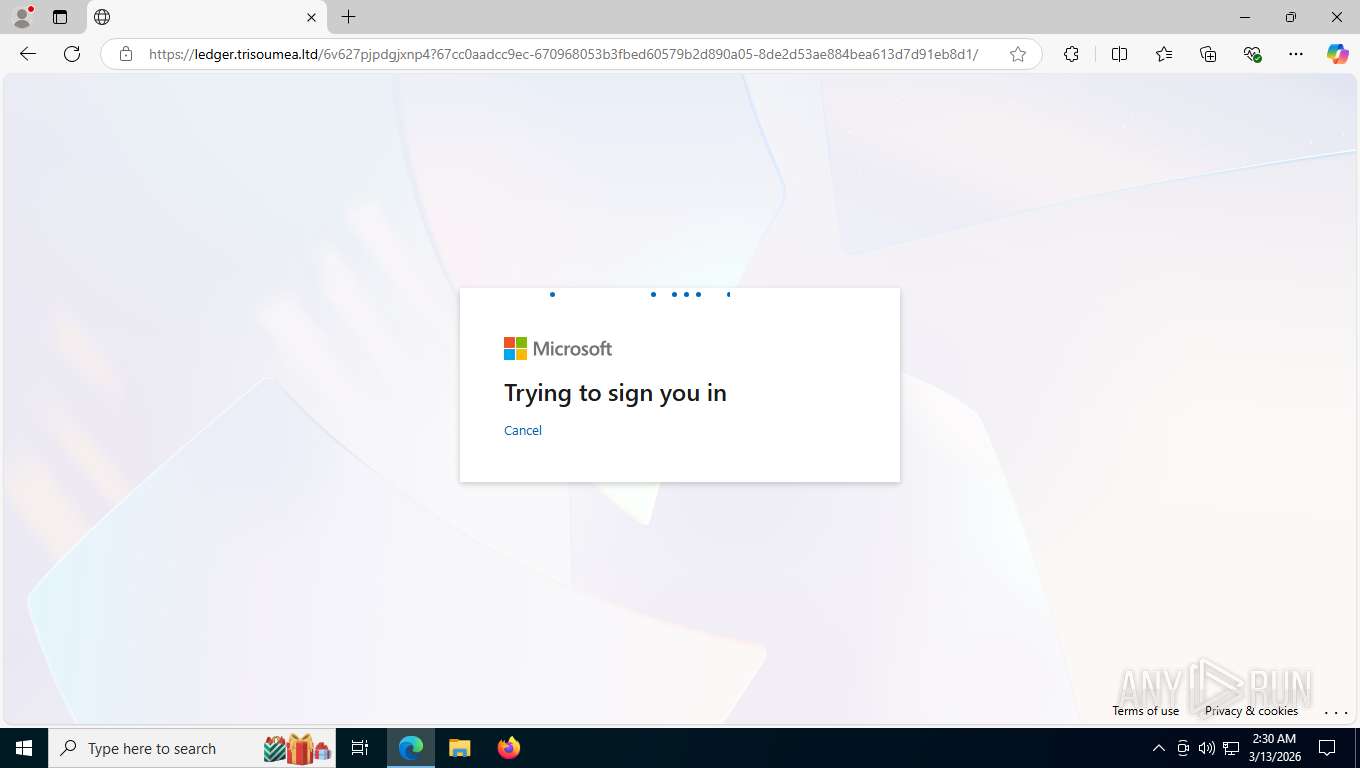
Tycoon 2FA phishing kit has been detected
- msedge.exe (PID: 8412)
Fake Microsoft Authentication Page has been detected
- msedge.exe (PID: 8412)
SUSPICIOUS
Page with zero-length space title
- msedge.exe (PID: 8412)
INFO
Reads Environment values
- identity_helper.exe (PID: 8652)
Checks supported languages
- identity_helper.exe (PID: 8652)
Reads the computer name
- identity_helper.exe (PID: 8652)
Application launched itself
- msedge.exe (PID: 8412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=14 --always-read-main-dll --field-trial-handle=6484,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6732 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3584 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3976,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5496 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5892,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4040 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4160,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6504 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=3780,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6408 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2312,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2460 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3700,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3752 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2268,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2232 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6036 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6320,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6288 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5604,i,17249433875484392965,299223407694916673,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5916 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
569
Read events
569
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
54
Text files
88
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e566b.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e566b.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e567a.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e567a.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e567a.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
99
TCP/UDP connections
59
DNS requests
106
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5440 | msedge.exe | GET | 302 | 146.112.255.69:443 | https://secure-web.cisco.com/1SKVh7tAE3m9EQJEw3K6sMNuEqSVawBaNDYh6n74jx-aX900oaWWT8L2T06OzbmKwTigwM6e0M-xaoFuDig_F58s7kRTGtFuE9EAW-7gfjy-HtU3W6TrzMKUlW_XW-RjtU4LzLaciZ67Ts_wVHKedbCrU3MfGIVRDdKLWeFtqAcpGXOdwbaUDPxyp-MoN6QxLQekbxb5IJa13XoG9-01y6ew32onHtiy1Zz028XEoPVPwwolOx8nMEtxsS6gPJa9C4yvrokAZ5QgtvWFKCh2I-ddF5ITEnHuGBR6ImHt0jeeLx2LlOB4JQy4GBF4jzaGyyILfLQClRrRdfixGPTr2nkBpT4fxWgq6WRT-0z84uSndO2MYqrhldbTXyMD4v07gwH4wHaOGqT-HHutWhzatY6B5ogdDGuNWy4G8WWRm_ZLfdGOELf2-woXfyYe-_pvkye4EbuW9OuuCqBBAkkFTyg/https%3A%2F%2Fnotification.tokposter.com%2F | unknown | — | — | unknown |
5440 | msedge.exe | GET | 302 | 198.252.102.17:443 | https://notification.tokposter.com/z0f76a1d14fd21a8fb5fd0d03e0fdc3d3cedae52f?wsidchk=6539110&pdata=https%253A%252F%252Fnotification.tokposter.com&id=7fa3b767c460b54a2be4d49030b349c7&ts=1773383413 | unknown | — | — | unknown |
5440 | msedge.exe | GET | 302 | 198.252.102.17:443 | https://notification.tokposter.com/ | unknown | — | — | unknown |
5440 | msedge.exe | GET | 302 | 198.252.102.17:443 | https://notification.tokposter.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
5568 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
5440 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.42 Kb | whitelisted |
5440 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
5440 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Gj-Rv_eM3JkOWOx8zhzd9PbZ_JOetFBuW-om-WiCM8U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5440 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8568 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7544 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.21.245.24:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5568 | SearchApp.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5440 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
linklock.titanhq.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
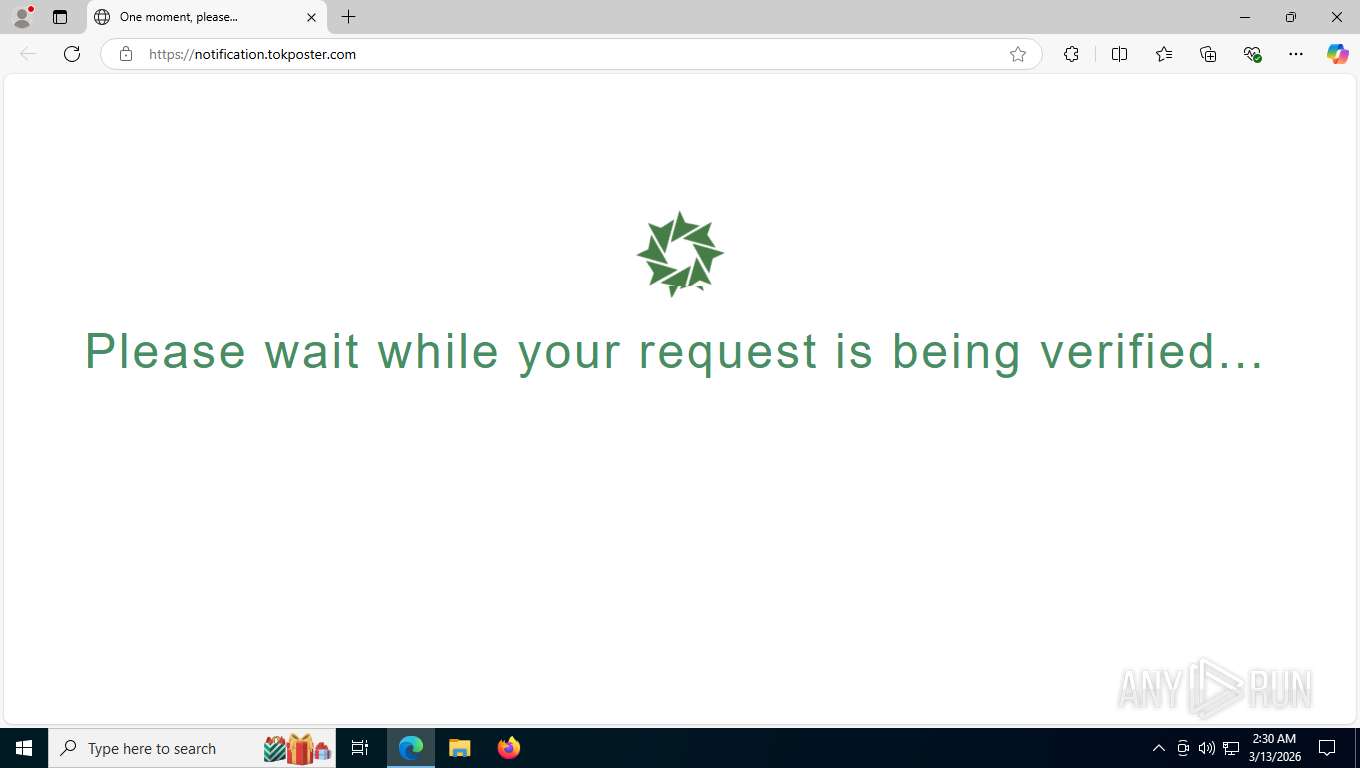
5440 | msedge.exe | Misc activity | HUNTING [ANY.RUN] Green Spinner browser checking page often used in phishing campaigns |
5440 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
5440 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
5440 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
5440 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
8568 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5440 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon2FA related URL pattern observed (tilda-variant) |
5440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |