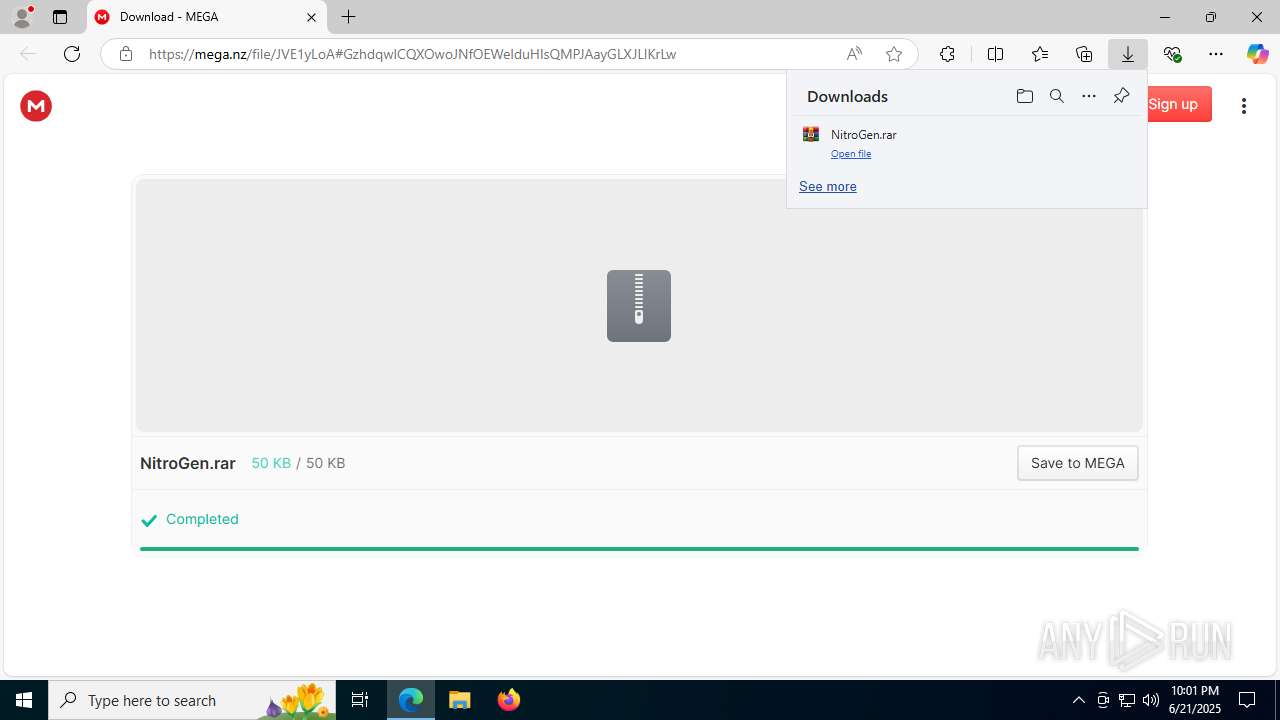
| URL: | https://mega.nz/file/JVE1yLoA#GzhdqwICQXOwoJNfOEWelduHIsQMPJAayGLXJLlKrLw |
| Full analysis: | https://app.any.run/tasks/3e5f4fd7-68fa-42fc-aa94-dd4196ee6443 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | June 21, 2025, 22:01:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C503733A086F491987681327C12DA6A1 |
| SHA1: | AFC39E2D6C6E12B0BE323197648507B218BCF936 |
| SHA256: | 5F6C7EBFE2AC5B245F6CFAF7E491363F3ECCFFB01C1046BDC77E6EDB775403AD |
| SSDEEP: | 3:N8X/ivJBU+vq8m6oYrX8:2+RAsrX8 |
MALICIOUS
Changes Windows Defender settings
- cmd.exe (PID: 2536)
- cmd.exe (PID: 7220)
Adds extension to the Windows Defender exclusion list
- cmd.exe (PID: 2536)
- cmd.exe (PID: 7220)
Changes the autorun value in the registry
- NitroGen.exe (PID: 7868)
Uses Task Scheduler to autorun other applications
- svhost.exe (PID: 7100)
QUASAR has been detected (YARA)
- svhost.exe (PID: 7100)
- svchost.exe (PID: 4120)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 6124)
- WinRAR.exe (PID: 7316)
- powershell.exe (PID: 5744)
- svchost.exe (PID: 5612)
Executing commands from a ".bat" file
- NitroGen.exe (PID: 7624)
- wscript.exe (PID: 4196)
- NitroGen.exe (PID: 7868)
- wscript.exe (PID: 2716)
Starts a Microsoft application from unusual location
- NitroGen.exe (PID: 7624)
- NitroGen.exe (PID: 7868)
Starts CMD.EXE for commands execution
- NitroGen.exe (PID: 7624)
- wscript.exe (PID: 4196)
- NitroGen.exe (PID: 7868)
- wscript.exe (PID: 2716)
Script adds exclusion extension to Windows Defender
- cmd.exe (PID: 2536)
- cmd.exe (PID: 7220)
The process executes VB scripts
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7076)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2536)
- cmd.exe (PID: 7220)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2536)
- cmd.exe (PID: 7220)
The process creates files with name similar to system file names
- powershell.exe (PID: 5744)
- svchost.exe (PID: 5612)
Executable content was dropped or overwritten
- powershell.exe (PID: 5744)
- svchost.exe (PID: 5612)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 4120)
- svchost.exe (PID: 5612)
Starts itself from another location
- svchost.exe (PID: 5612)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2716)
Connects to unusual port
- svhost.exe (PID: 7100)
INFO
Checks supported languages
- identity_helper.exe (PID: 7788)
- identity_helper.exe (PID: 7280)
- NitroGen.exe (PID: 7624)
- curl.exe (PID: 7748)
- curl.exe (PID: 7176)
- svchost.exe (PID: 4120)
- NitroGen.exe (PID: 7868)
- curl.exe (PID: 4768)
- curl.exe (PID: 3864)
- svchost.exe (PID: 5612)
Reads the computer name
- identity_helper.exe (PID: 7788)
- identity_helper.exe (PID: 7280)
- curl.exe (PID: 7176)
- curl.exe (PID: 7748)
- svchost.exe (PID: 4120)
- curl.exe (PID: 4768)
- curl.exe (PID: 3864)
- svchost.exe (PID: 5612)
Application launched itself
- msedge.exe (PID: 3572)
- msedge.exe (PID: 6124)
The sample compiled with english language support
- msedge.exe (PID: 6124)
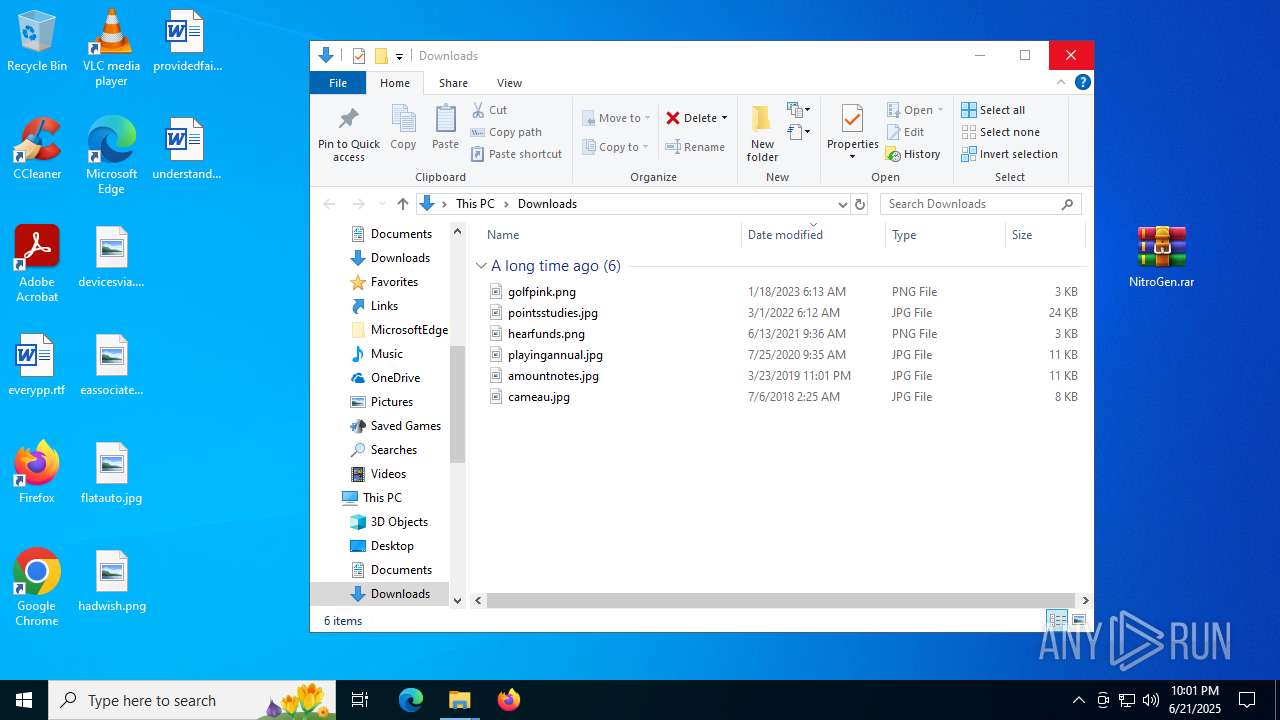
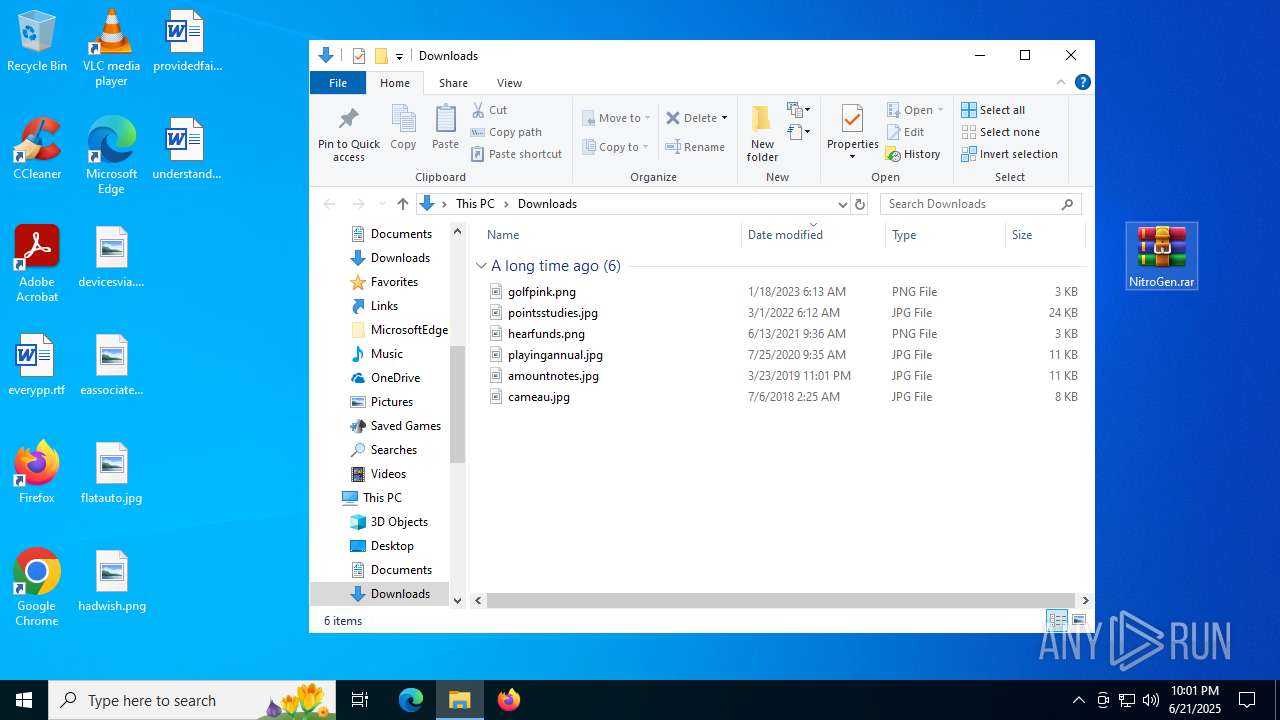
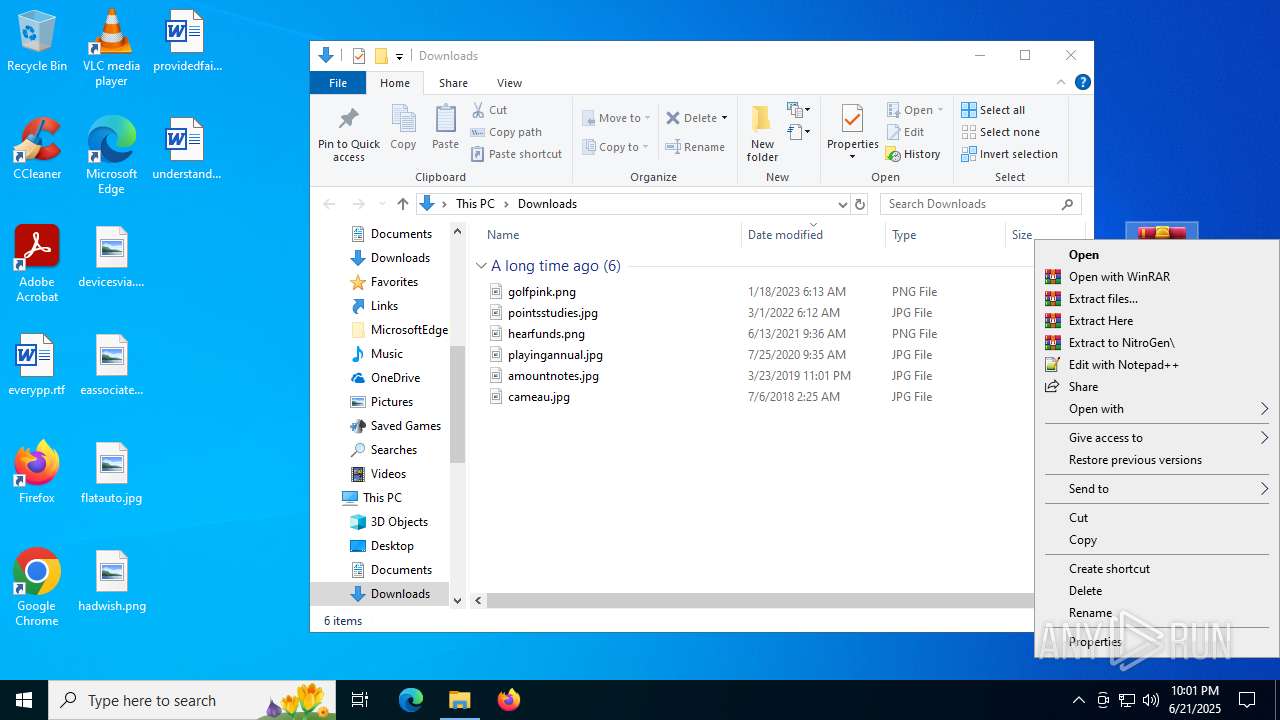
- WinRAR.exe (PID: 7316)
Executable content was dropped or overwritten
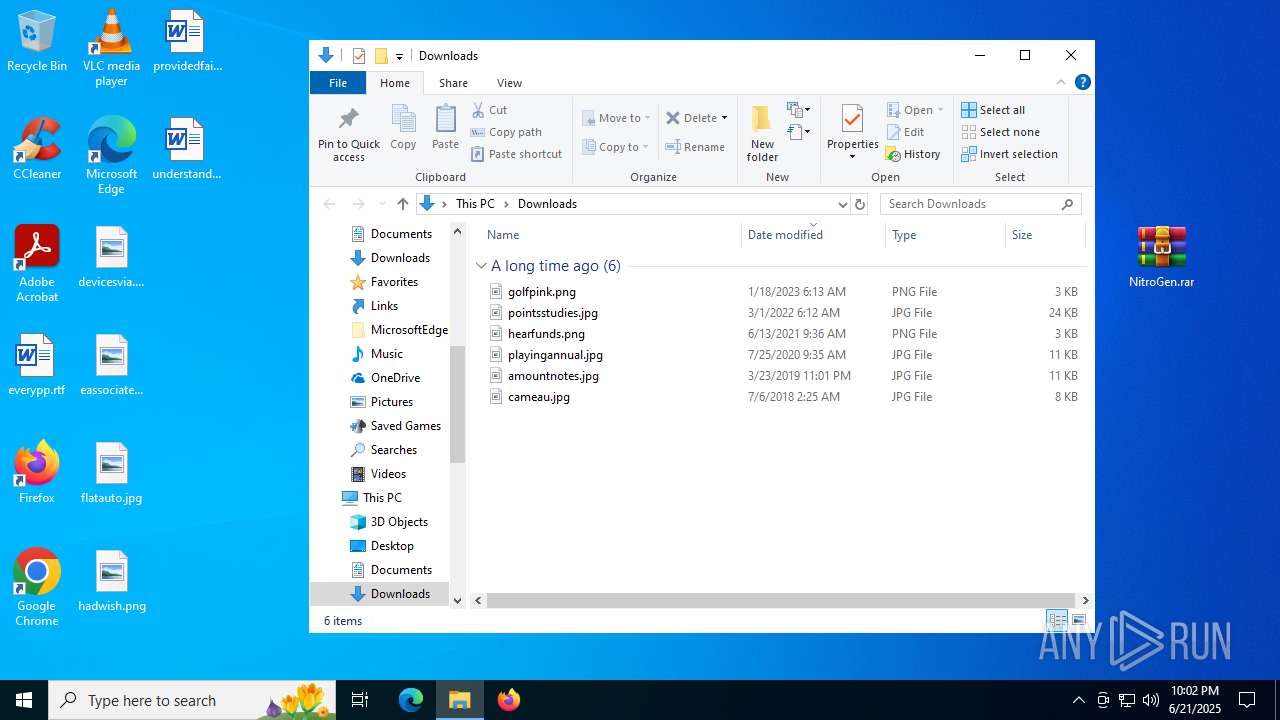
- WinRAR.exe (PID: 7316)
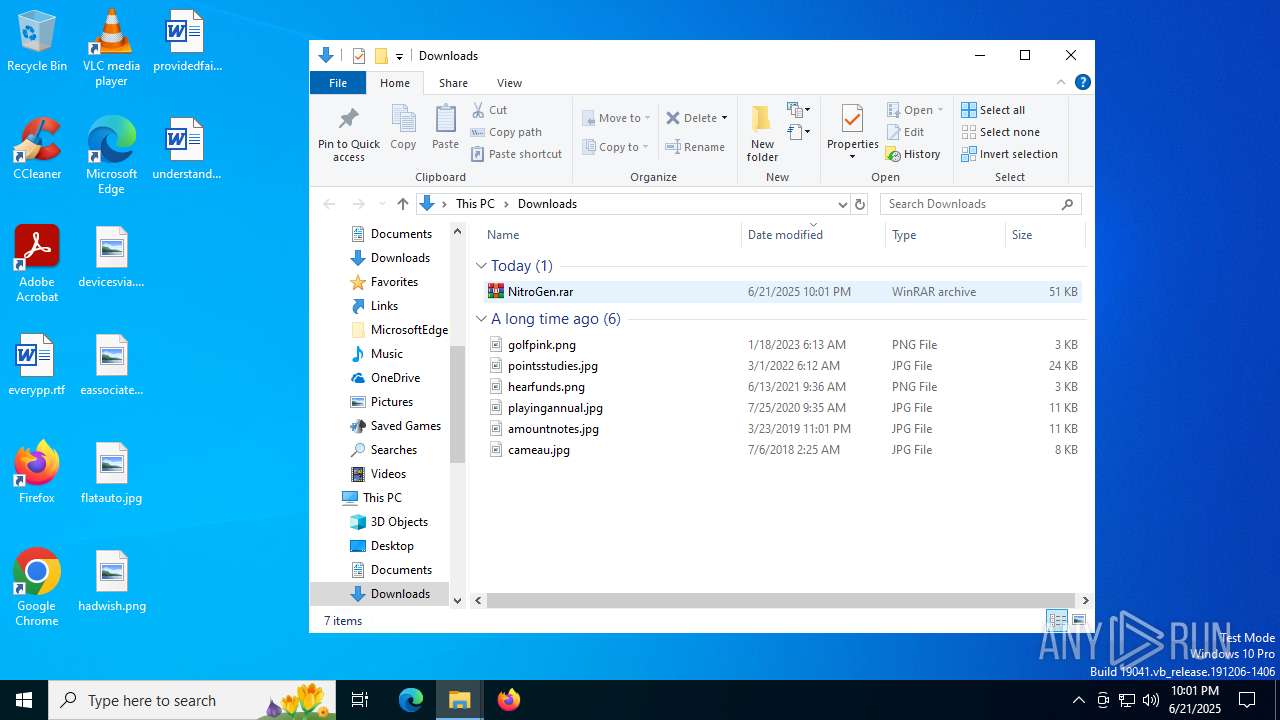
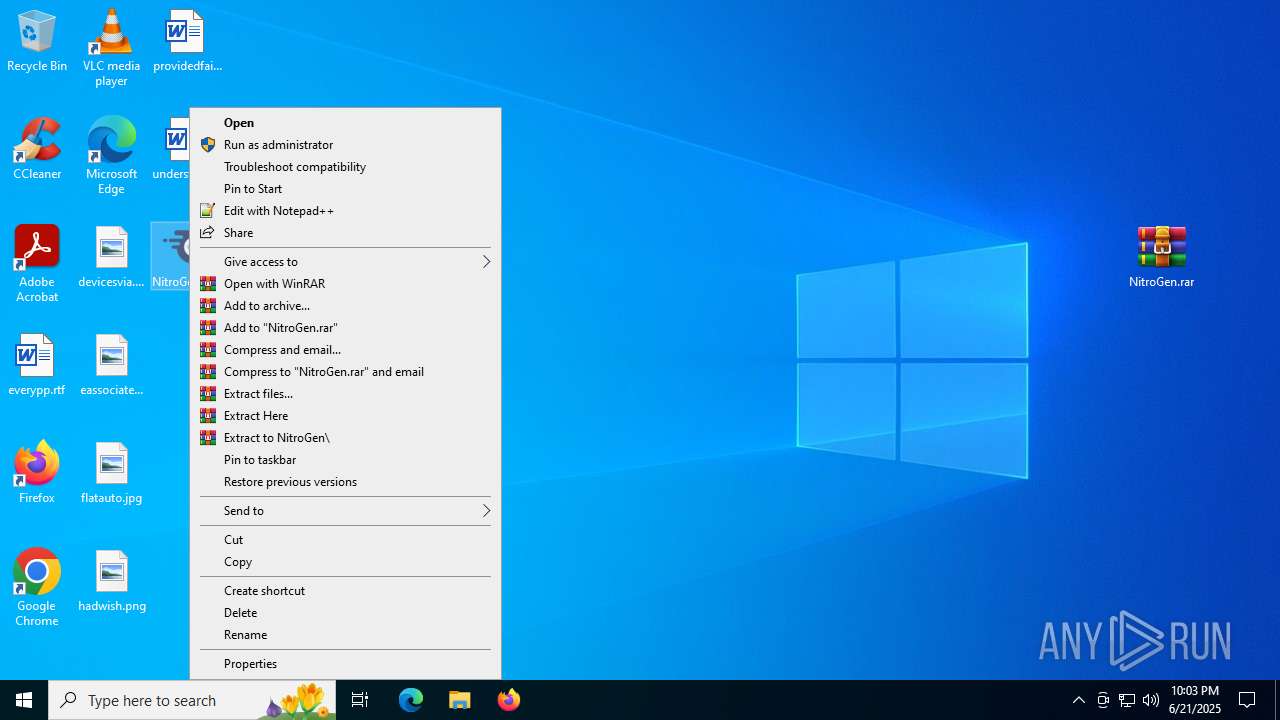
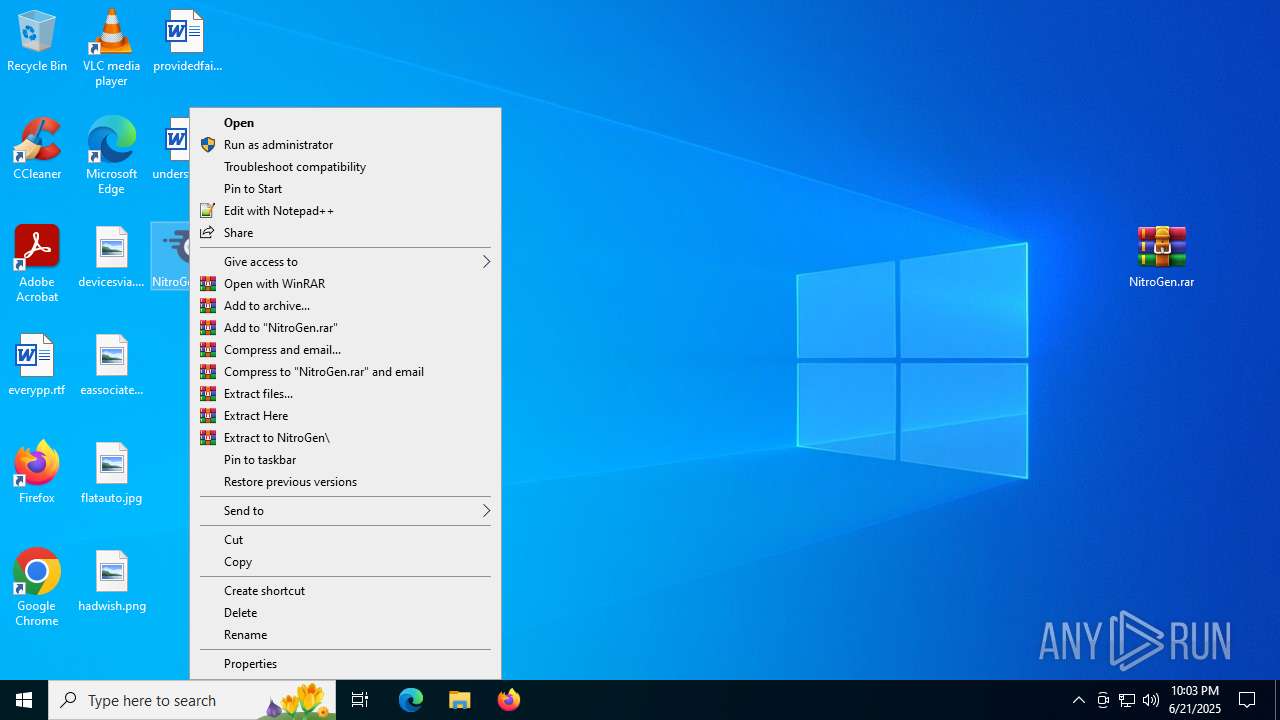
Manual execution by a user
- NitroGen.exe (PID: 7624)
- WinRAR.exe (PID: 7316)
- NitroGen.exe (PID: 7868)
Reads Environment values
- identity_helper.exe (PID: 7280)
- identity_helper.exe (PID: 7788)
- svchost.exe (PID: 4120)
- svchost.exe (PID: 5612)
Create files in a temporary directory
- NitroGen.exe (PID: 7624)
- NitroGen.exe (PID: 7868)
Creates files or folders in the user directory
- curl.exe (PID: 7748)
- curl.exe (PID: 7176)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 6896)
Disables trace logs
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4664)
Checks proxy server information
- powershell.exe (PID: 5744)
- slui.exe (PID: 4808)
- powershell.exe (PID: 4664)
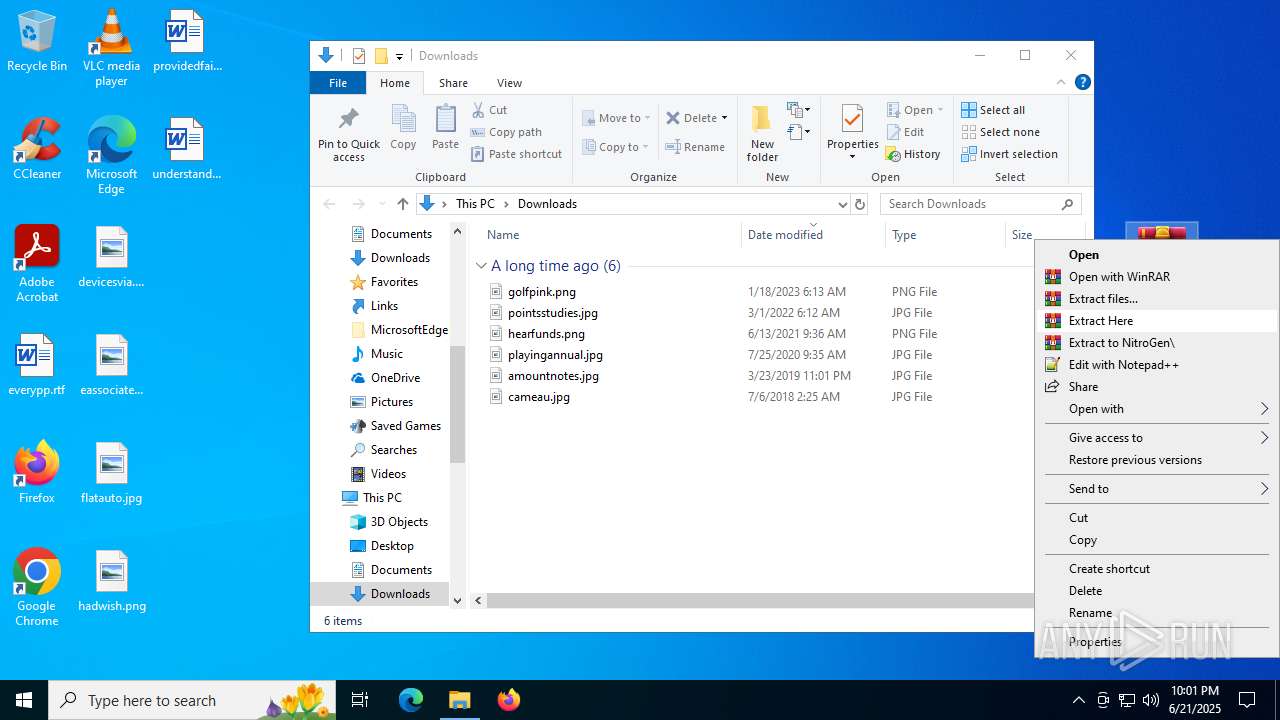
Launching a file from the Downloads directory
- msedge.exe (PID: 6124)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 6896)
- powershell.exe (PID: 4664)
Execution of CURL command
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7076)
Launching a file from a Registry key
- NitroGen.exe (PID: 7868)
Reads the software policy settings
- slui.exe (PID: 4808)
Failed to create an executable file in Windows directory
- svchost.exe (PID: 4120)
Reads the machine GUID from the registry
- svchost.exe (PID: 4120)
- svchost.exe (PID: 5612)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- svchost.exe (PID: 5612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(4120) svchost.exe
Version1.4.1
C2 (2)5.253.247.131:4782
Sub_Dir
Install_Namesvhost.exe
Mutex4ce1fc5c-80b6-4559-86c9-9b36bf115656
StartupHostProcess for Windows Services
TagWorm
LogDirLogs
SignatureV+J8y7jOycz7N/u/QeNl5xsJhRsFw2d7ZRvQK1ZX6qr7gzFCCSToOOp/W4ydu/qElShC5yUka6AICSnmEIm8SeGXCysNkN+jxL2lCcOmsuTyVbc5va/5LJv5mndrghWAyOmE2qgSoQlEcEBwzDDs18BTnHVDw/MTfgApSt33hQ670io52GMIa5j7WwslZg0k4ae4pHkjRlLvzaysi73kn2YA89fk2WEVGWrUaOq951muBY63P841BL+mXocDHqwyEBzvKhivtt4xY52C8F8aPP9NZ7KUs/8fTOO025zW1D4l...
CertificateMIIE9DCCAtygAwIBAgIQAMtVO29EsdZKiMSZxM6GIzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxNTExNTU0N1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAncTTjDzeXF7iAc0g1/OZ4VgtB1k46kSnJ4HY77A0ka3nP+hXQhj+4a5XOKYzW2IfzQHPRWHY...
(PID) Process(7100) svhost.exe
Version1.4.1
C2 (2)5.253.247.131:4782
Sub_Dir
Install_Namesvhost.exe
Mutex4ce1fc5c-80b6-4559-86c9-9b36bf115656
StartupHostProcess for Windows Services
TagWorm
LogDirLogs
SignatureV+J8y7jOycz7N/u/QeNl5xsJhRsFw2d7ZRvQK1ZX6qr7gzFCCSToOOp/W4ydu/qElShC5yUka6AICSnmEIm8SeGXCysNkN+jxL2lCcOmsuTyVbc5va/5LJv5mndrghWAyOmE2qgSoQlEcEBwzDDs18BTnHVDw/MTfgApSt33hQ670io52GMIa5j7WwslZg0k4ae4pHkjRlLvzaysi73kn2YA89fk2WEVGWrUaOq951muBY63P841BL+mXocDHqwyEBzvKhivtt4xY52C8F8aPP9NZ7KUs/8fTOO025zW1D4l...
CertificateMIIE9DCCAtygAwIBAgIQAMtVO29EsdZKiMSZxM6GIzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxNTExNTU0N1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAncTTjDzeXF7iAc0g1/OZ4VgtB1k46kSnJ4HY77A0ka3nP+hXQhj+4a5XOKYzW2IfzQHPRWHY...
Total processes
229
Monitored processes
80
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2608,i,6231571412248952307,10209144797761765677,262144 --variations-seed-version --mojo-platform-channel-handle=2616 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2980,i,6231571412248952307,10209144797761765677,262144 --variations-seed-version --mojo-platform-channel-handle=3860 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3828,i,6231571412248952307,10209144797761765677,262144 --variations-seed-version --mojo-platform-channel-handle=4836 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5204,i,6231571412248952307,10209144797761765677,262144 --variations-seed-version --mojo-platform-channel-handle=5304 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2736,i,17841829707411933666,1392155364745990476,262144 --variations-seed-version --mojo-platform-channel-handle=2700 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | attrib +h +s run.vbs | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | attrib +h +s installer.bat | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5152,i,6231571412248952307,10209144797761765677,262144 --variations-seed-version --mojo-platform-channel-handle=5052 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
33 725
Read events
33 687
Write events
37
Delete events
1
Modification events
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EC709267B2962F00 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590334 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0A71383B-D62C-40C2-BFE5-E37548E60358} | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590334 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D657D5E8-6524-44D8-929F-45B107415A6E} | |||
| (PID) Process: | (6124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590334 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {54A0332A-4415-4CAB-BADE-1D8A74A8D65A} | |||
Executable files
19
Suspicious files
249
Text files
109
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176457.TMP | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176467.TMP | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176467.TMP | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176476.TMP | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176496.TMP | — | |
MD5:— | SHA256:— | |||
| 6124 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
110
DNS requests
84
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6772 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:IqLqhC-HrK5zNH005cm41xsAFi_k7yQE7YMe9V1sxI8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
892 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8084 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8084 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7732 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751018024&P2=404&P3=2&P4=CANPcI4FLhq7EeIQaIPuEFPSbUGVU9uBX8q6g9oaDGyNMGz3Fyiq327wqJOzU1ErvshZO0aKqR%2fGphdOyGjwpA%3d%3d | unknown | — | — | whitelisted |
7732 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751018023&P2=404&P3=2&P4=Qa6B8JfUN9OofafXsE2bQCNpP7HUFO1Bj02OodteAhVx1leLSTZjE2Bbu3E4jx7UVwl%2b0U6u88%2bX3jxcUc8GPQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4816 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6772 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
6772 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6772 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |