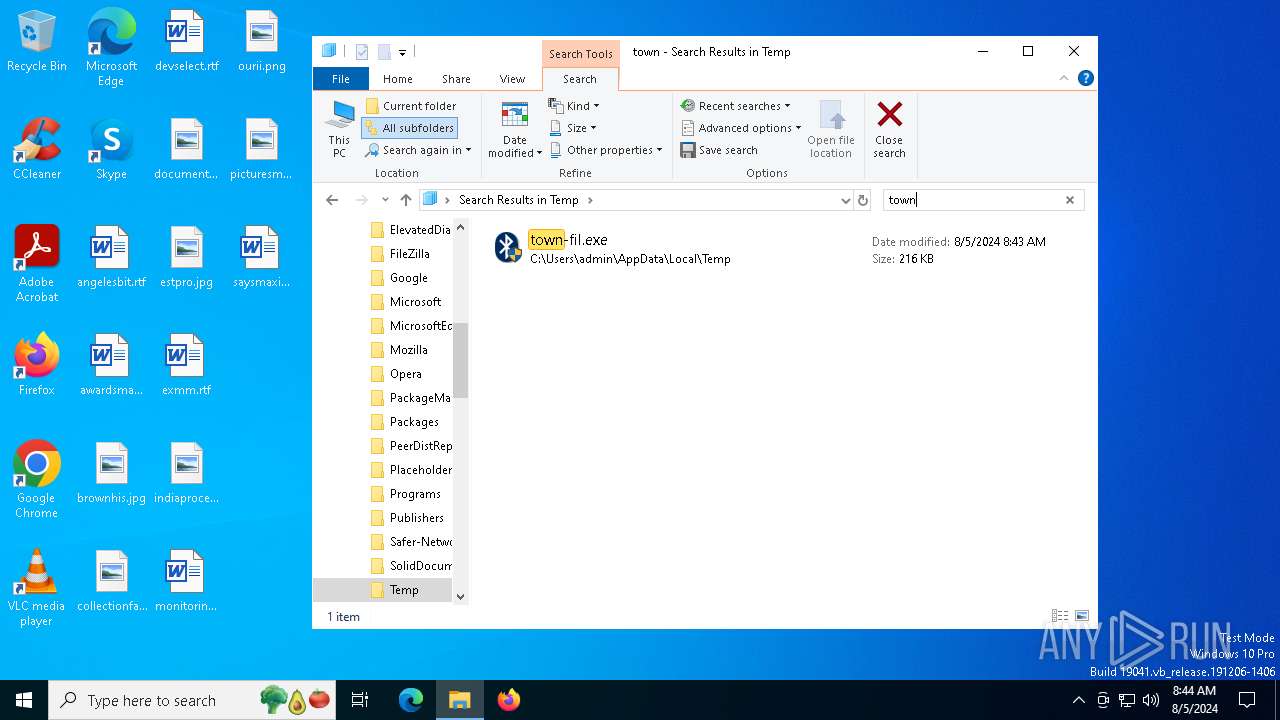
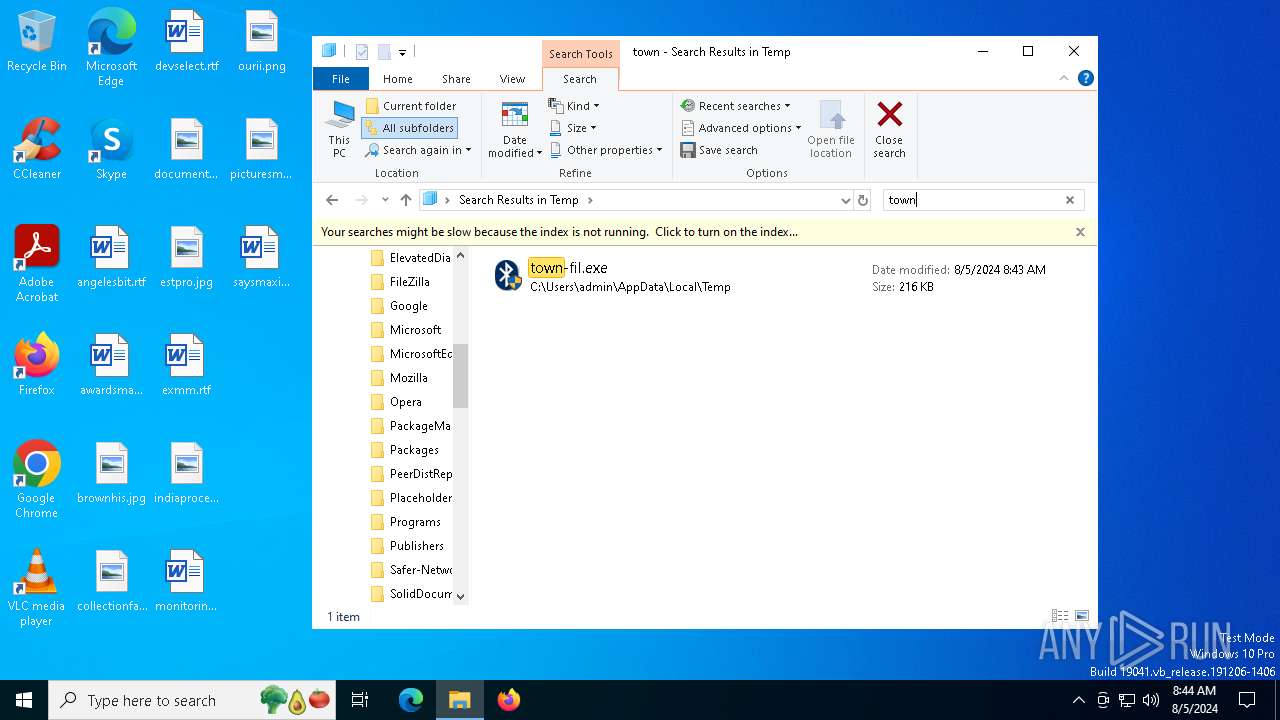
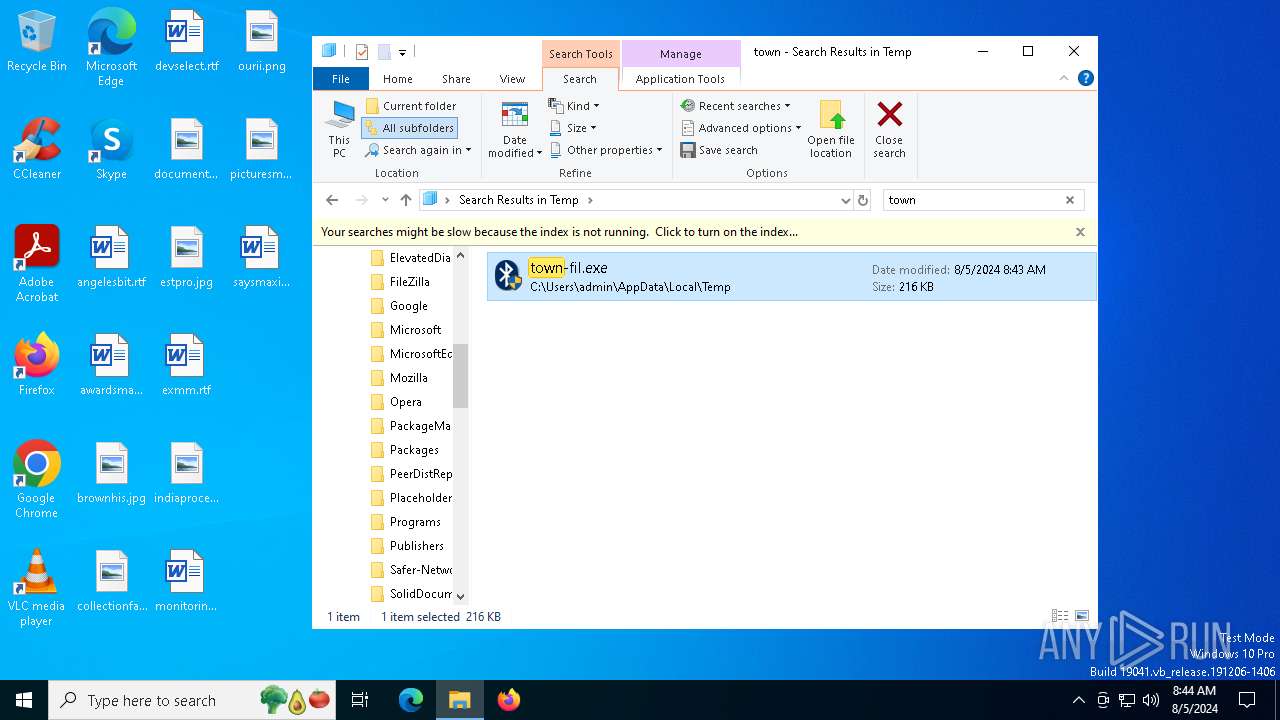
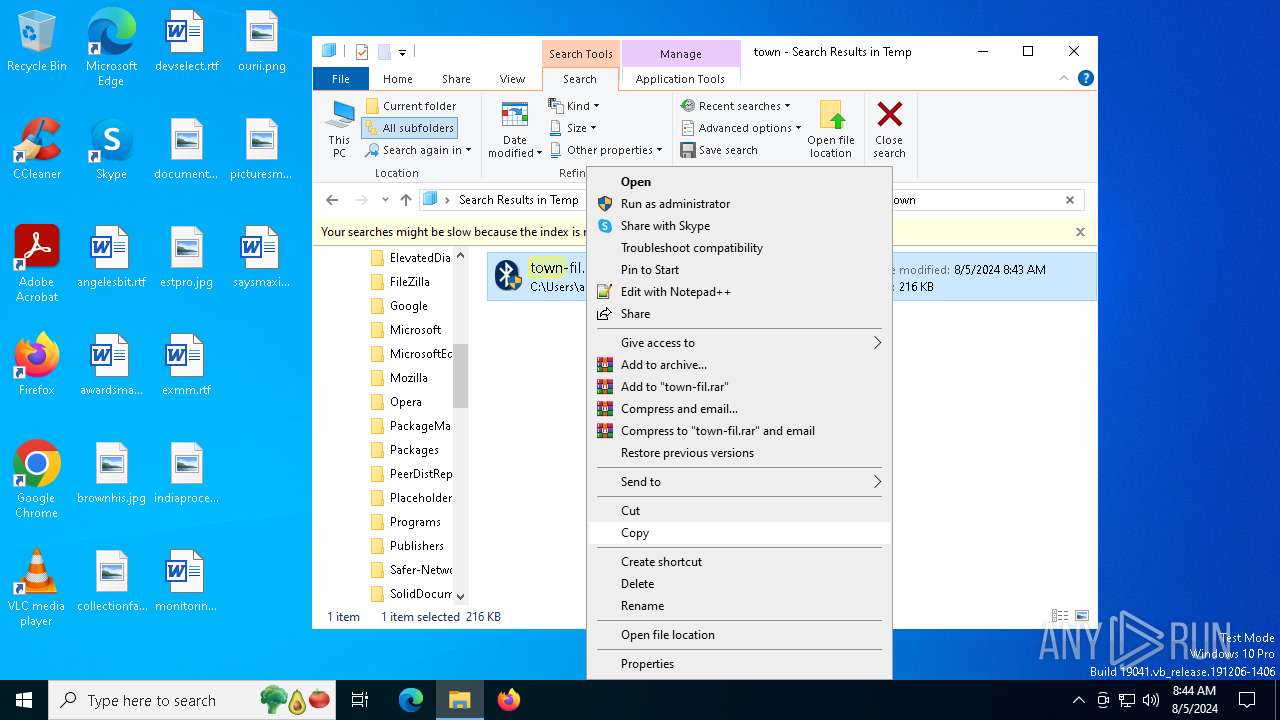
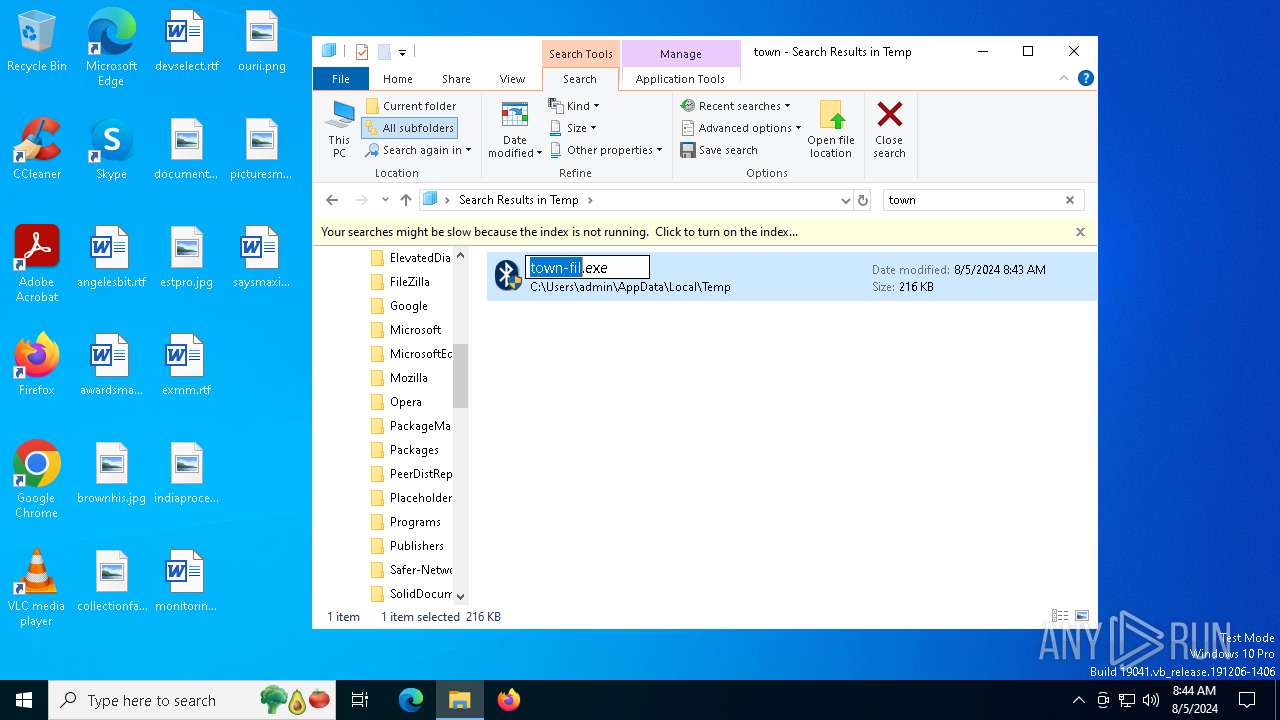
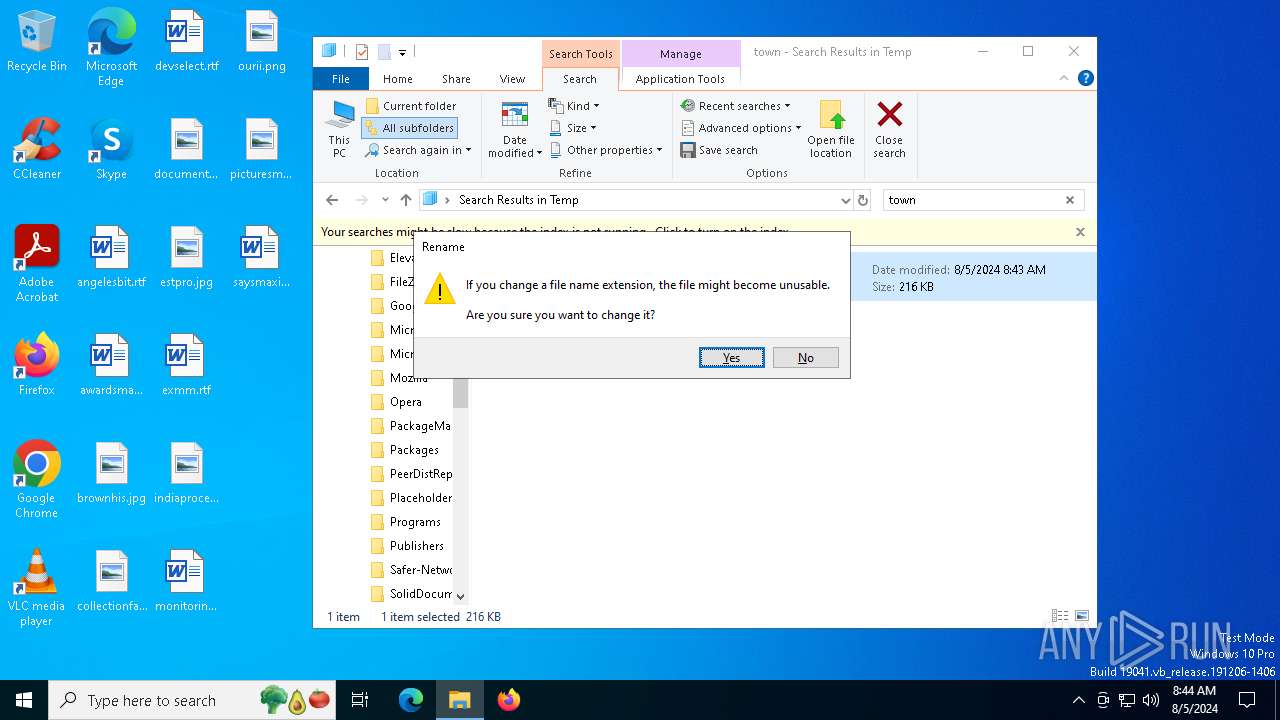
| File name: | town-fil.exe |
| Full analysis: | https://app.any.run/tasks/cde78cdd-0138-43f6-b80e-777369050c30 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 05, 2024, 08:43:47 |
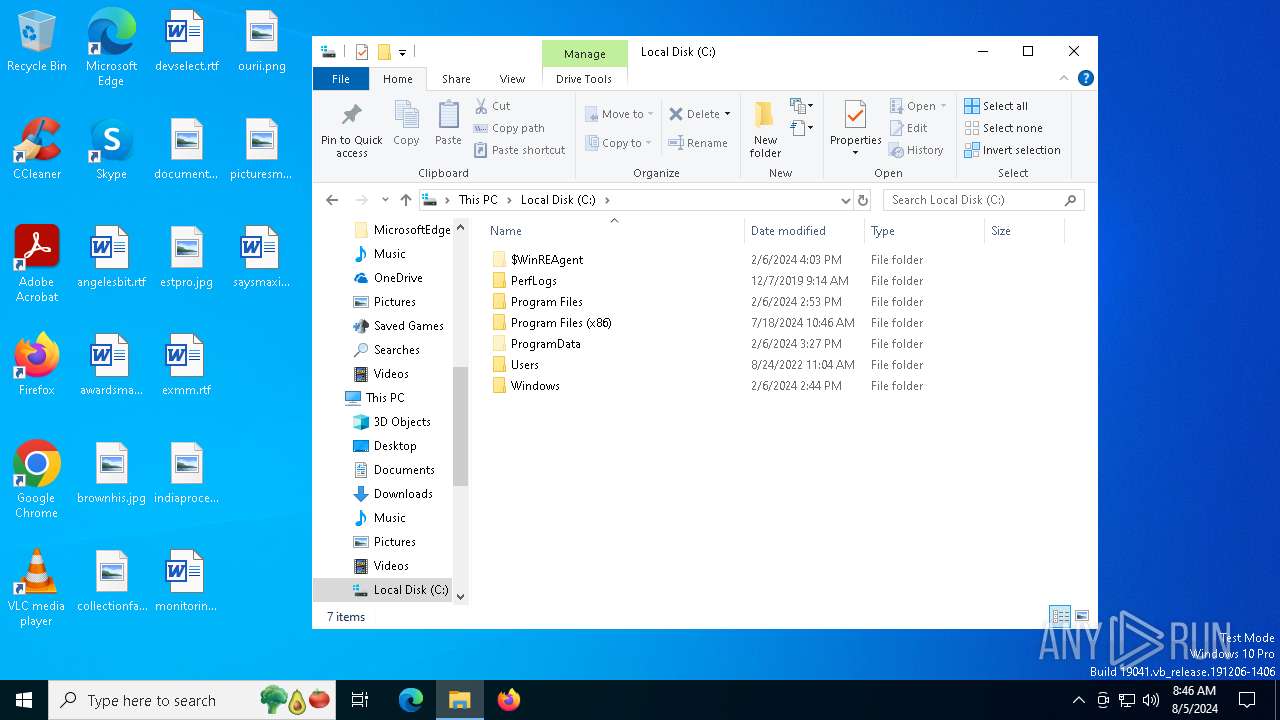
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 86A133BFAD915A04254032E77EAC3B8D |
| SHA1: | E0D2541D93FB0700262B0B7CF2BCDFE8A6BC980B |
| SHA256: | 5F4CF4082DBD503C6F0B652DDD22675F4427A907726E2F8D08C718ADEAFBB568 |
| SSDEEP: | 6144:3WDnDoVVnVbqHWDnDoVVnVbqAfWDnDoVVnVbqWWDnDoVVnVbq:GDnDoVVnVbq2DnDoVVnVbqJDnDoVVnVu |
MALICIOUS
Drops the executable file immediately after the start
- town-fil.exe (PID: 6356)
- powershell.exe (PID: 6500)
- BitLockerToGo.exe (PID: 5632)
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 6484)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6500)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6500)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6500)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6500)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6500)
LUMMA has been detected (YARA)
- ashampoo.exe (PID: 6768)
Changes the autorun value in the registry
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
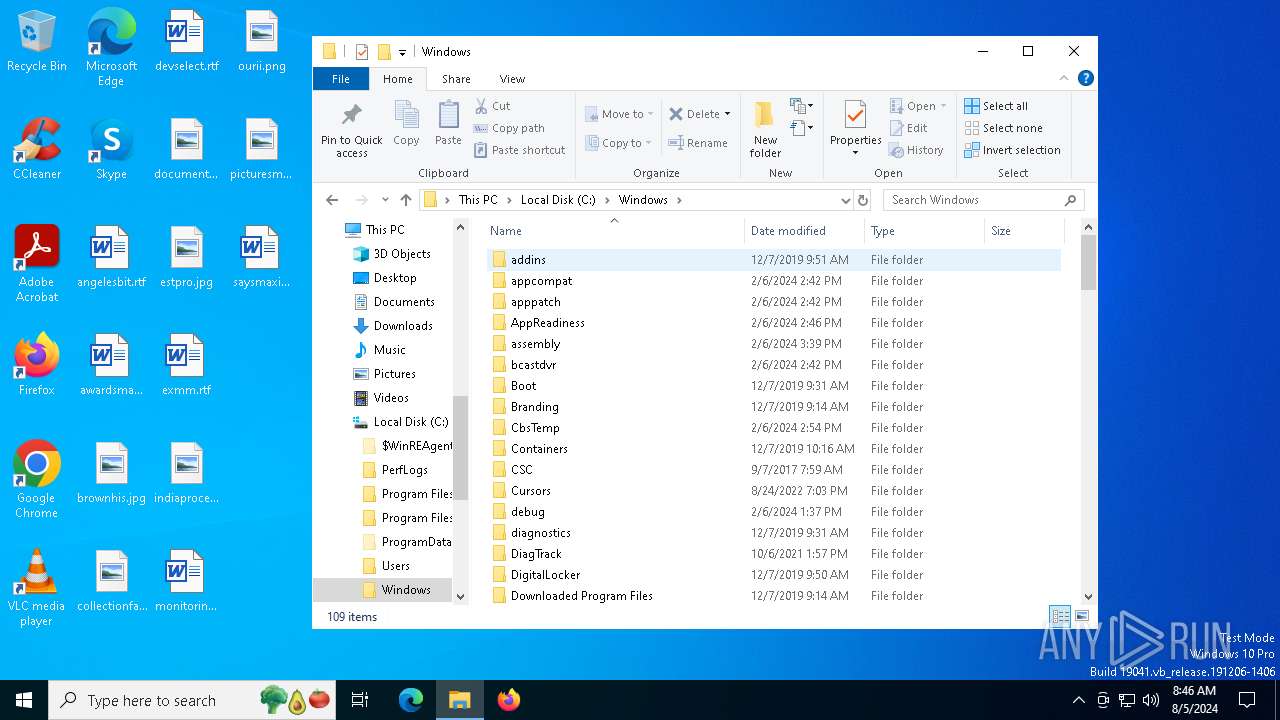
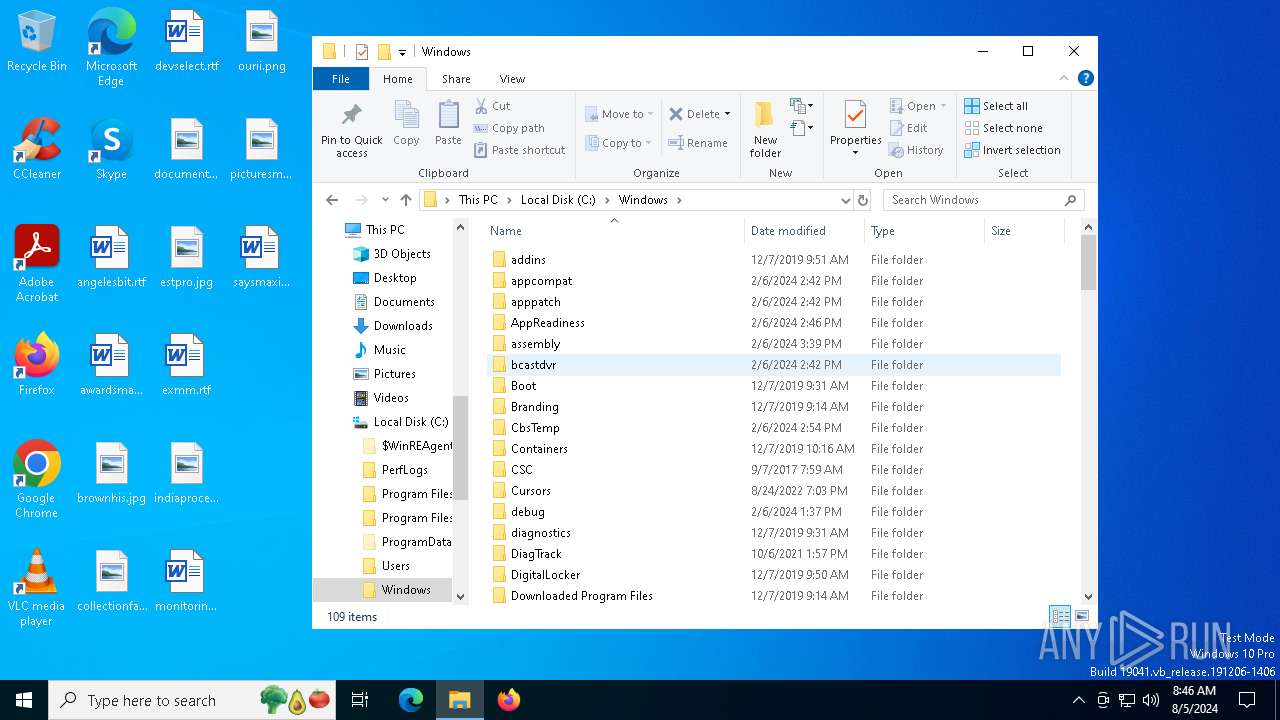
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 5632)
Run PowerShell with an invisible window
- powershell.exe (PID: 6500)
SUSPICIOUS
Starts a Microsoft application from unusual location
- town-fil.exe (PID: 6308)
- town-fil.exe (PID: 6356)
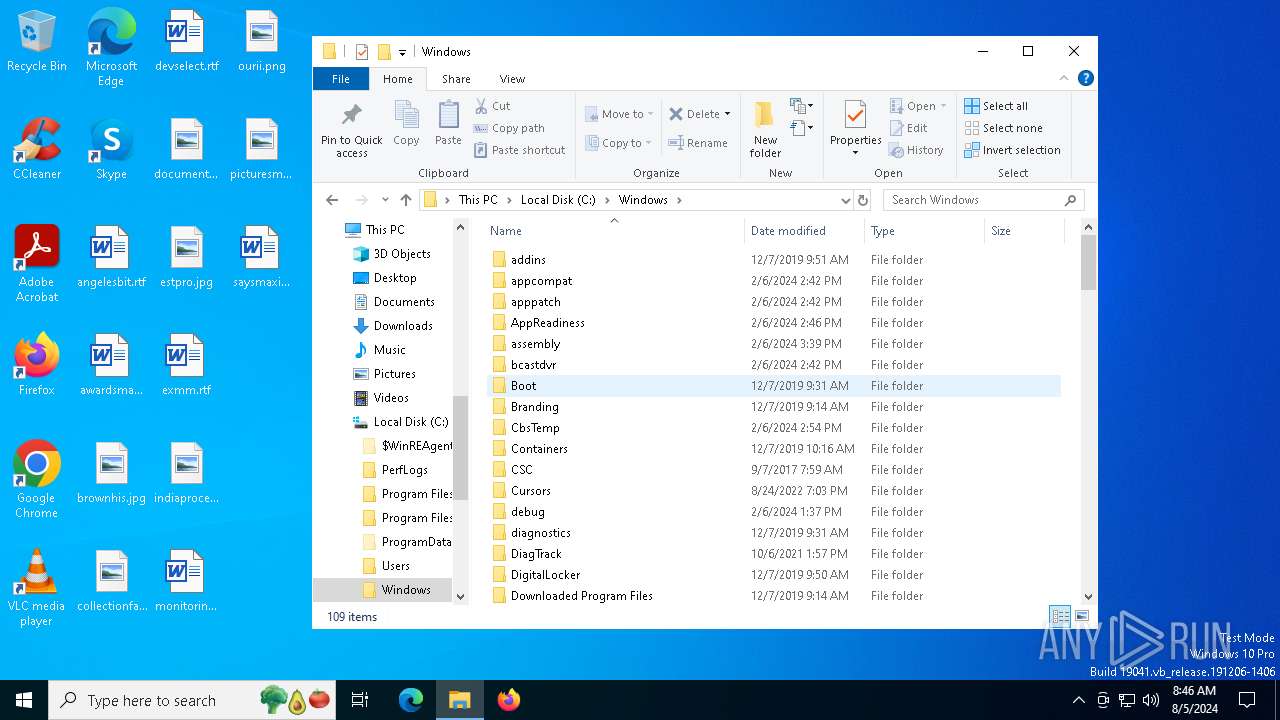
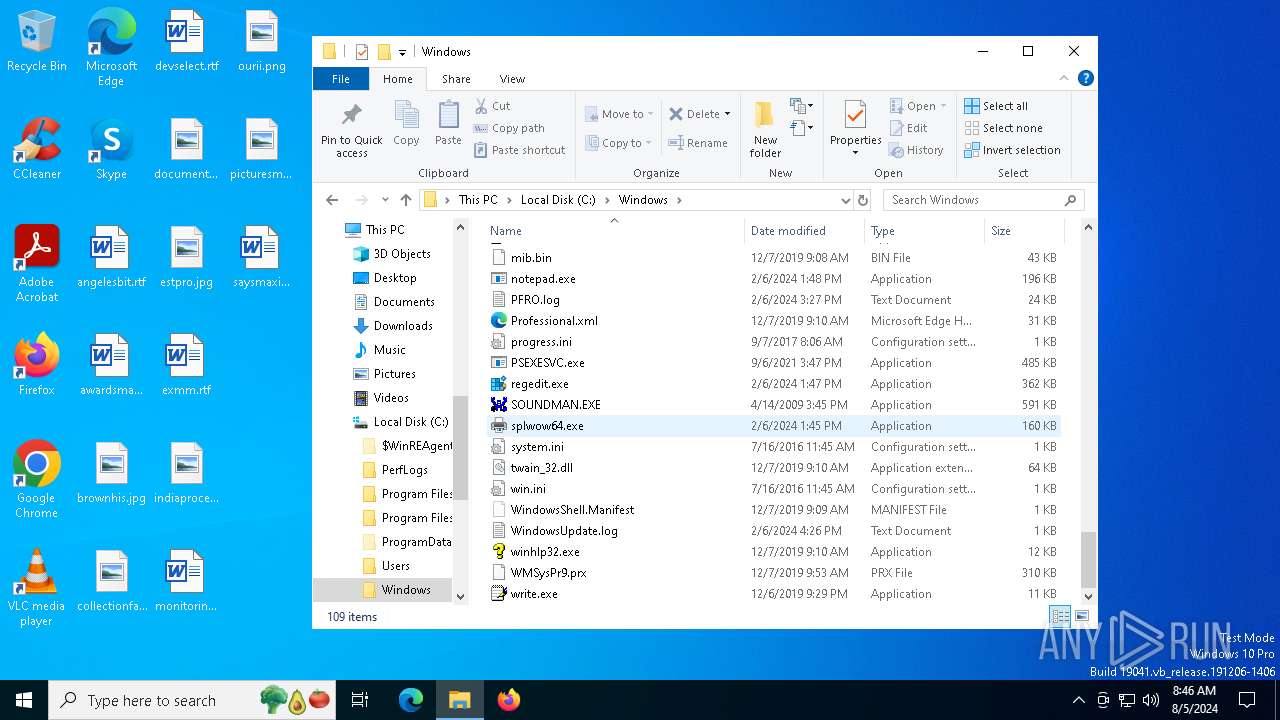
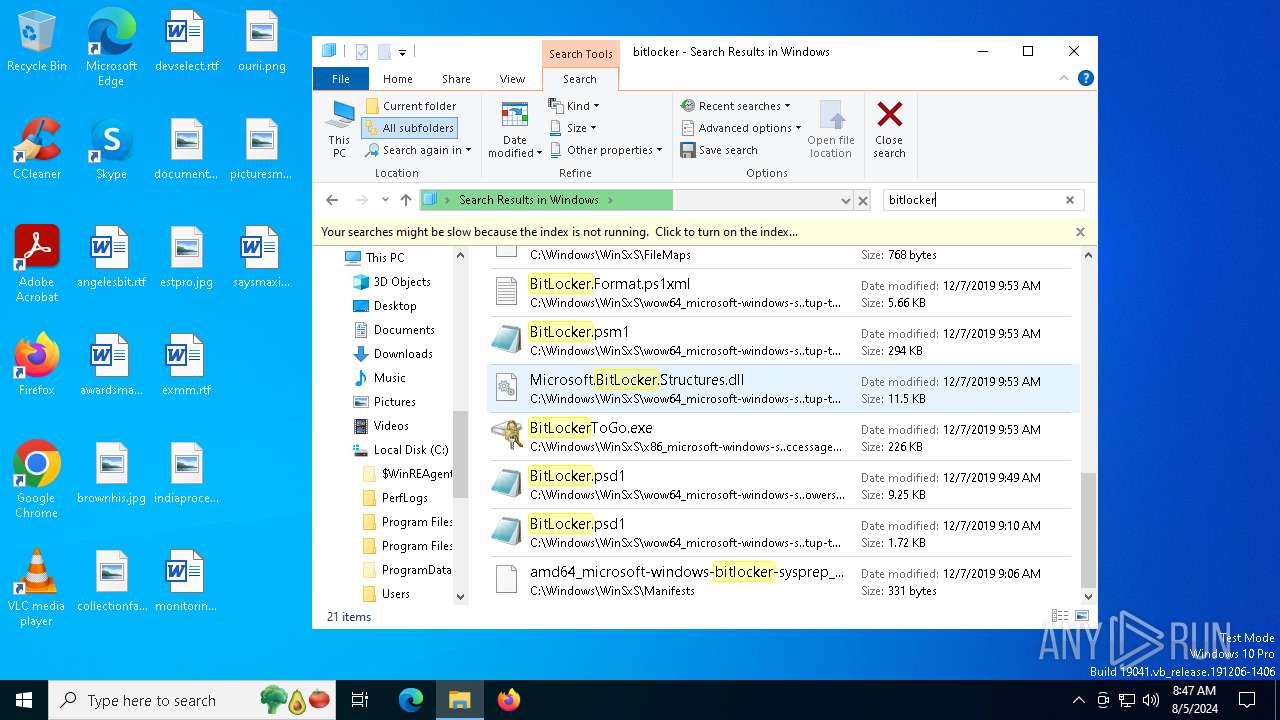
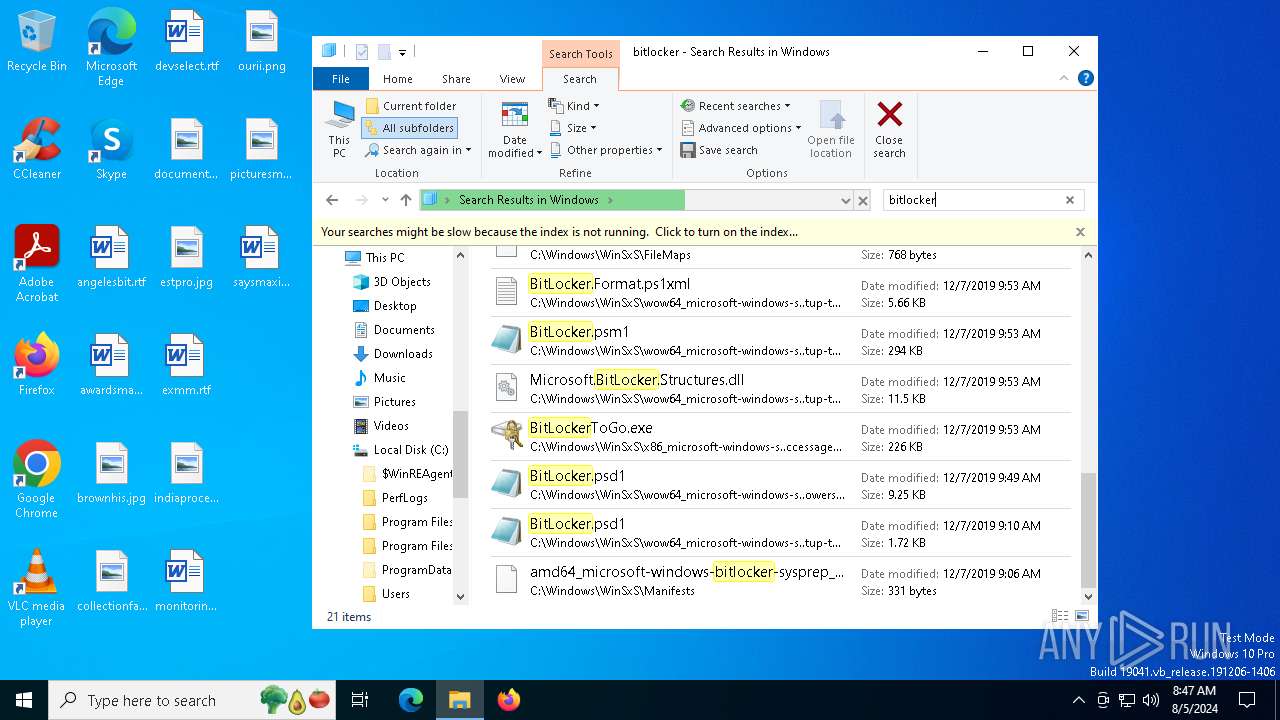
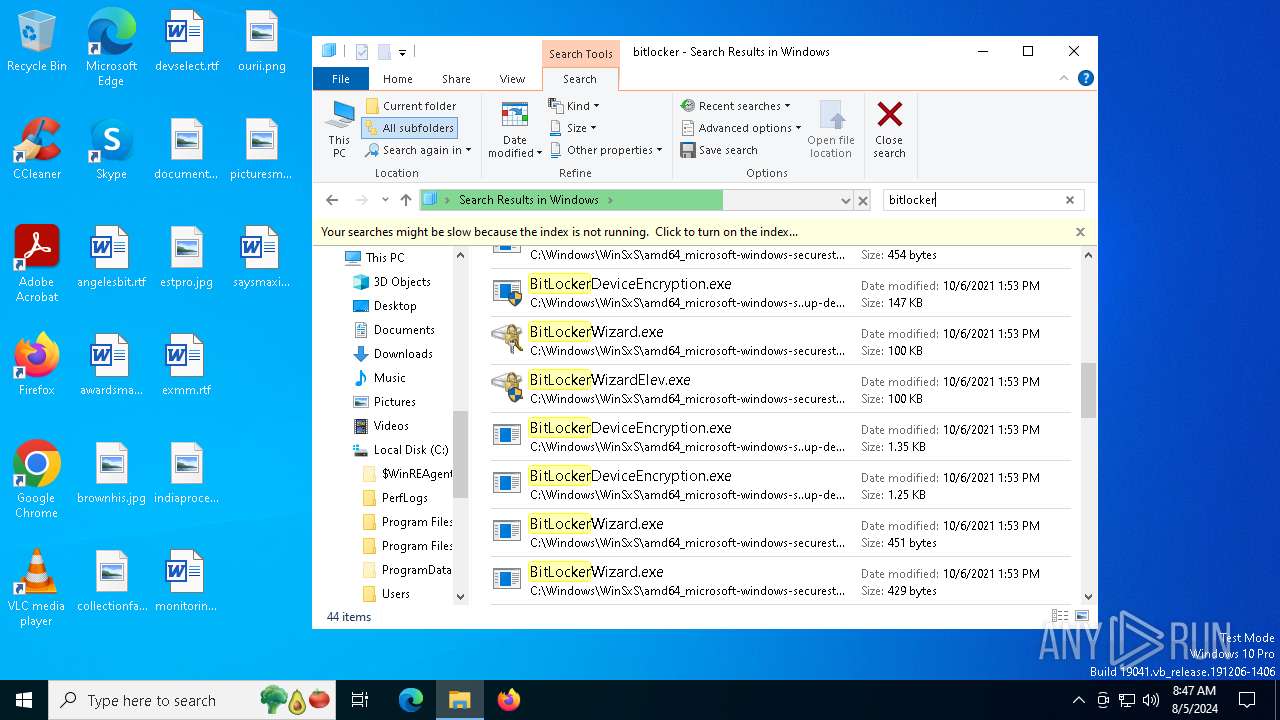
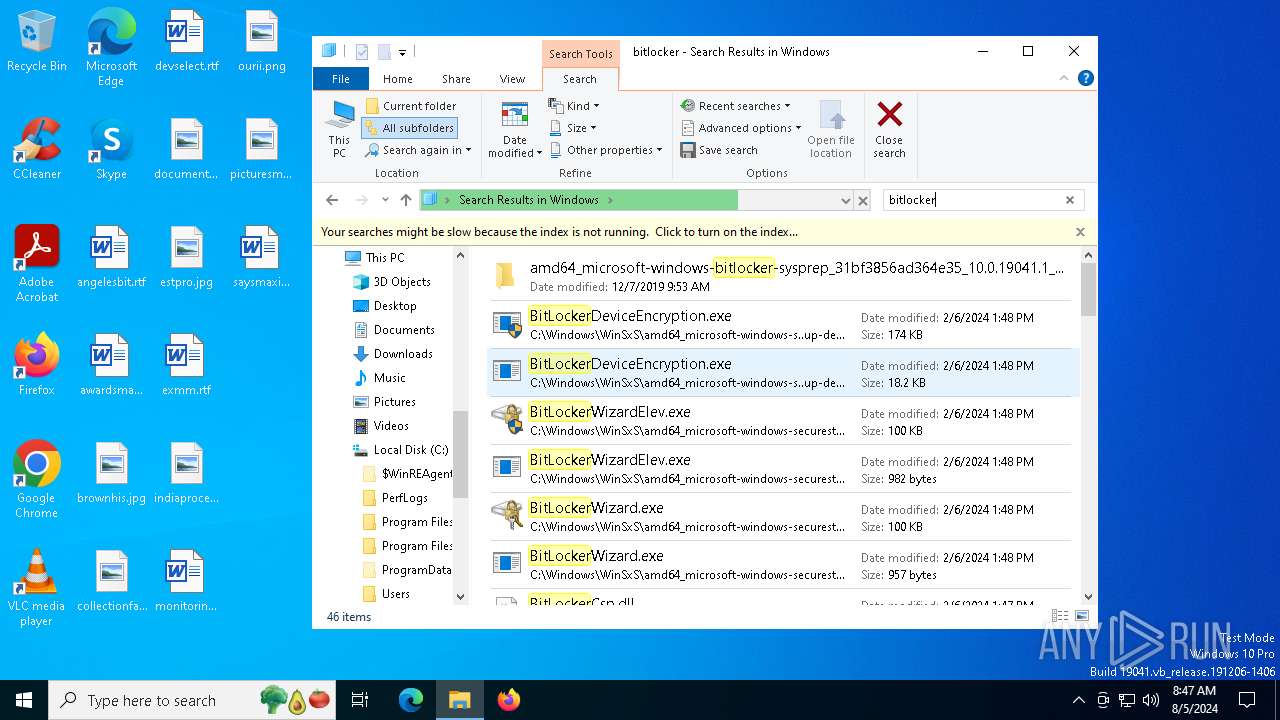
Process drops legitimate windows executable
- town-fil.exe (PID: 6356)
- powershell.exe (PID: 6500)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6484)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6500)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6500)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6500)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6500)
Executable content was dropped or overwritten
- powershell.exe (PID: 6500)
- BitLockerToGo.exe (PID: 5632)
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
The process drops C-runtime libraries
- powershell.exe (PID: 6500)
There is functionality for communication over UDP network (YARA)
- ashampoo.exe (PID: 6768)
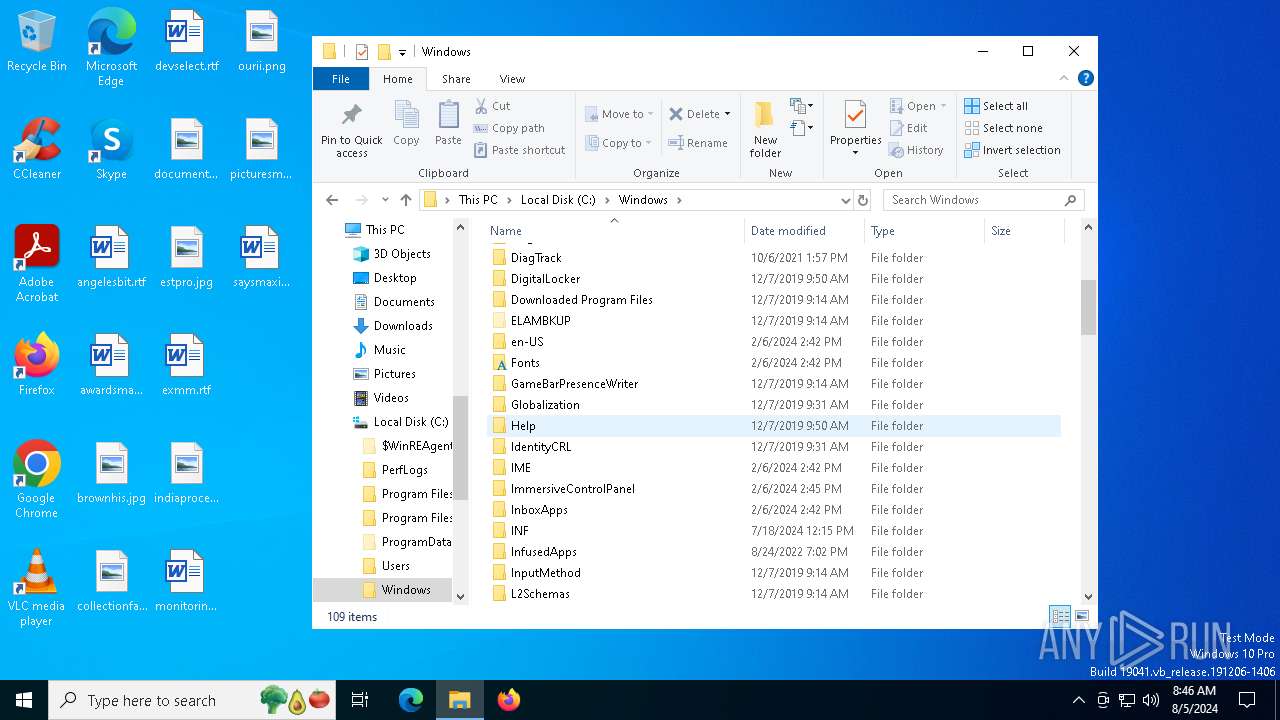
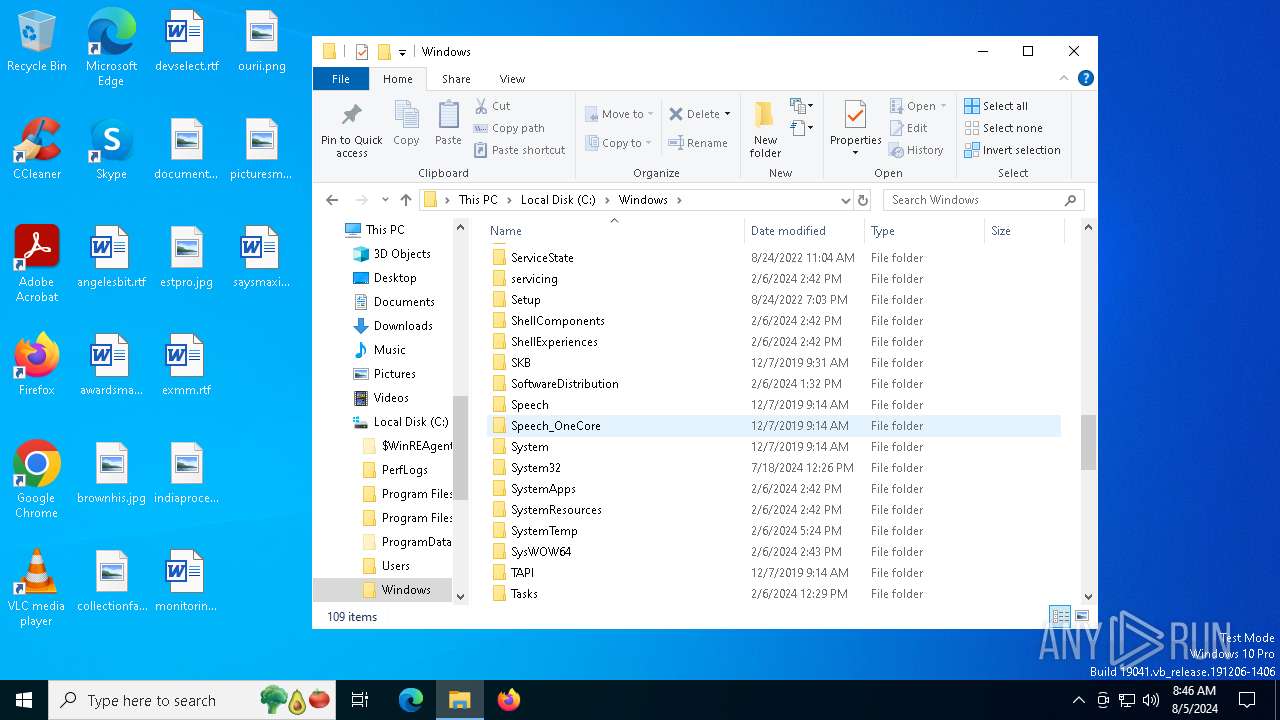
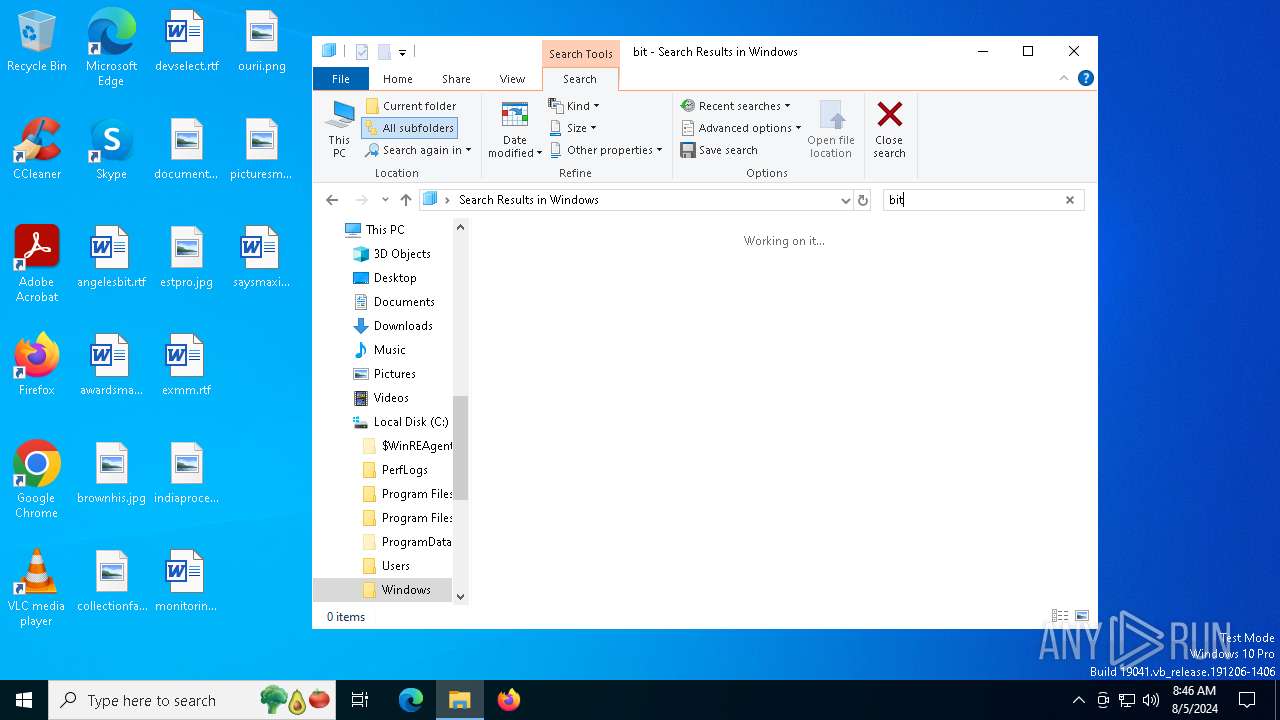
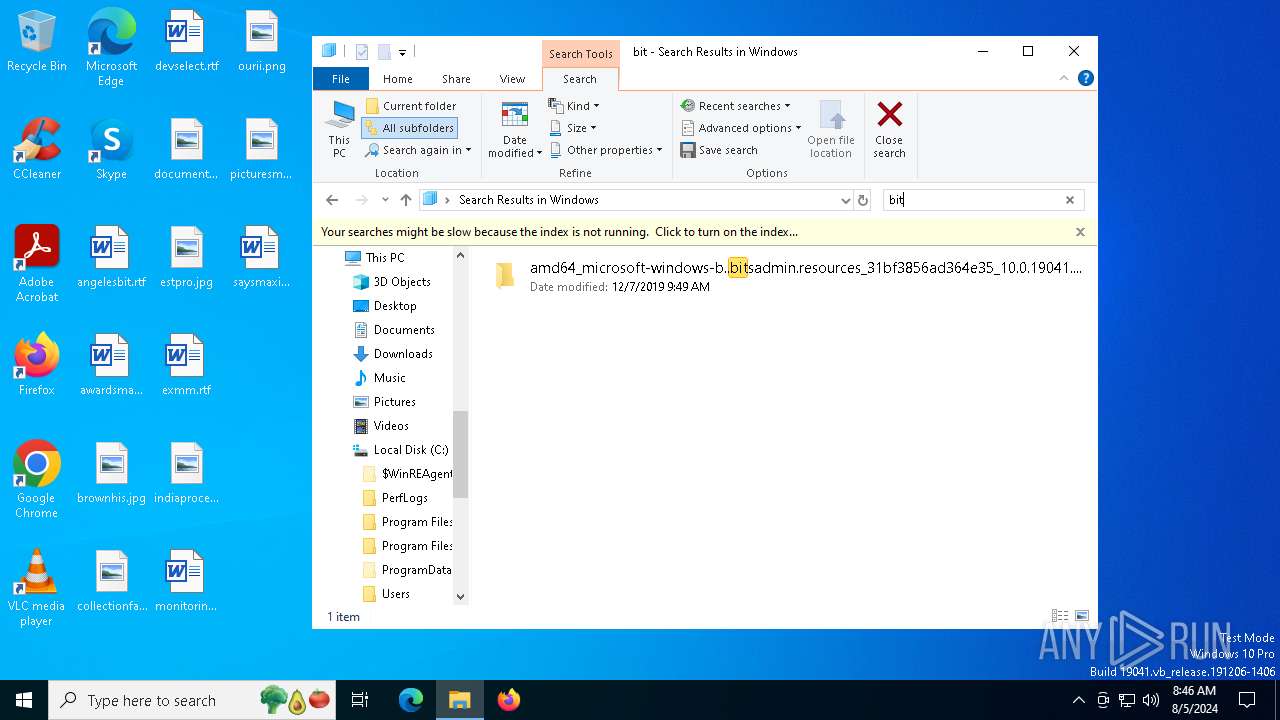
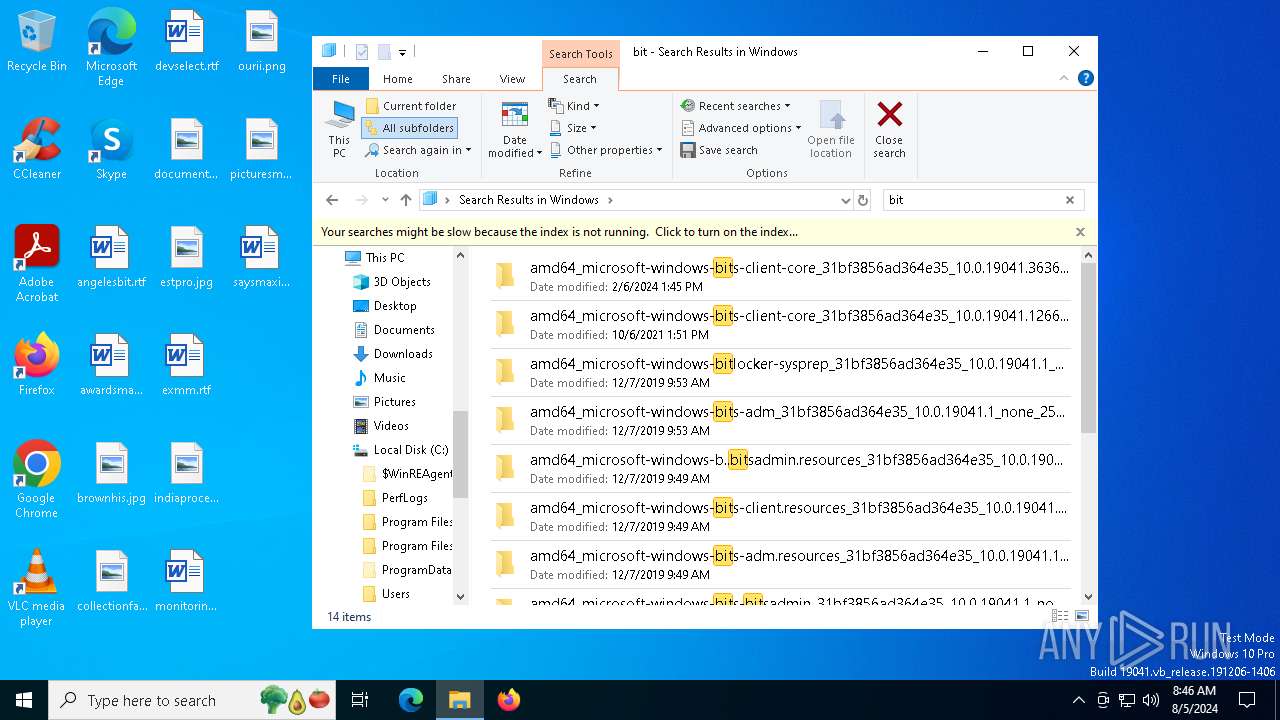
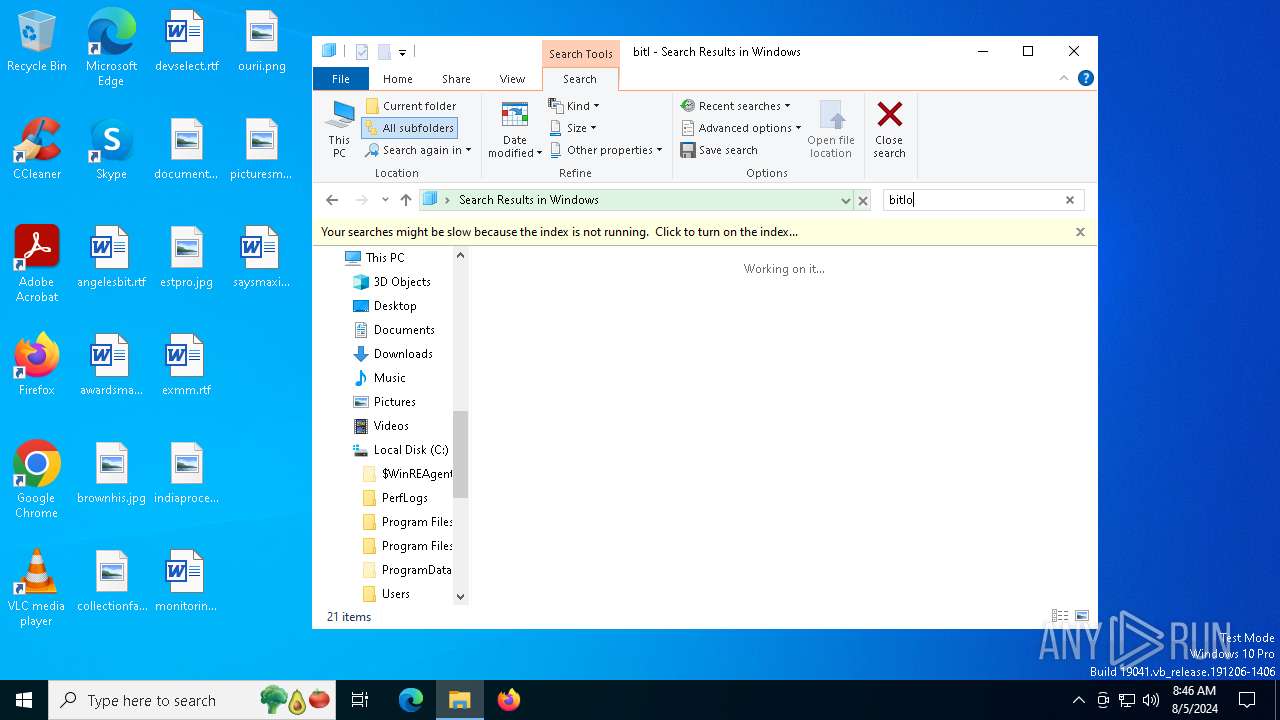
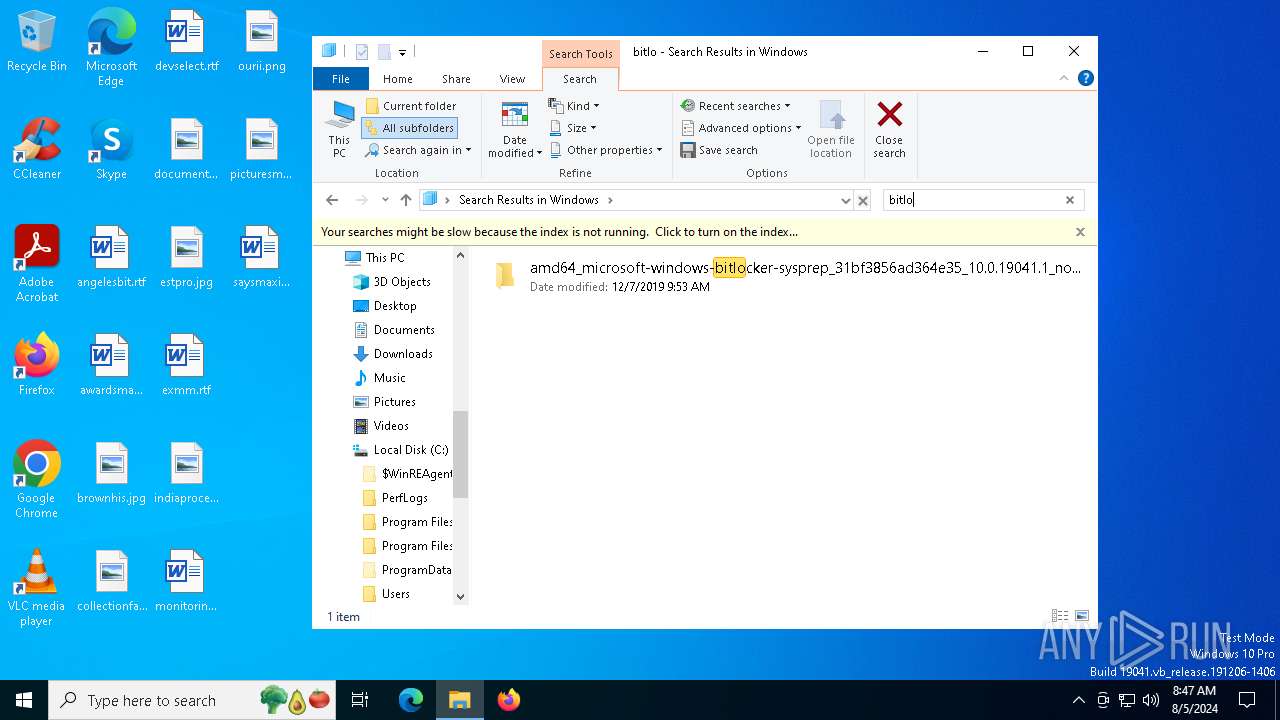
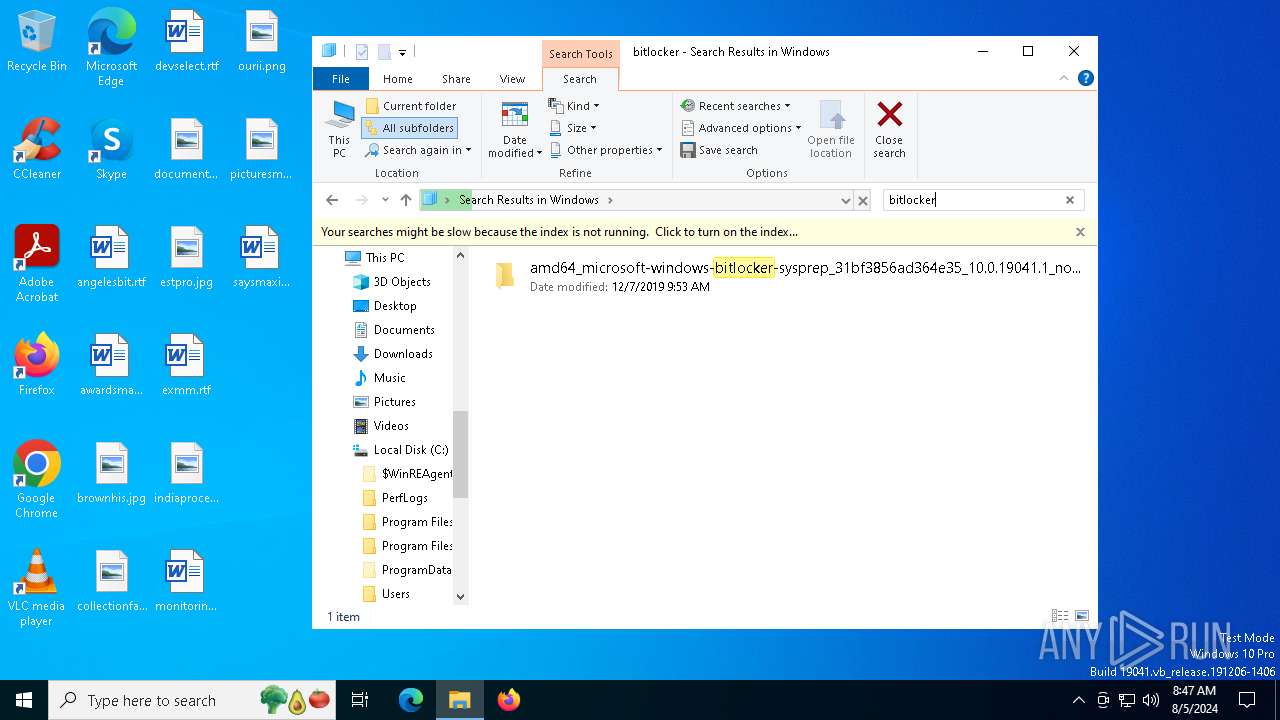
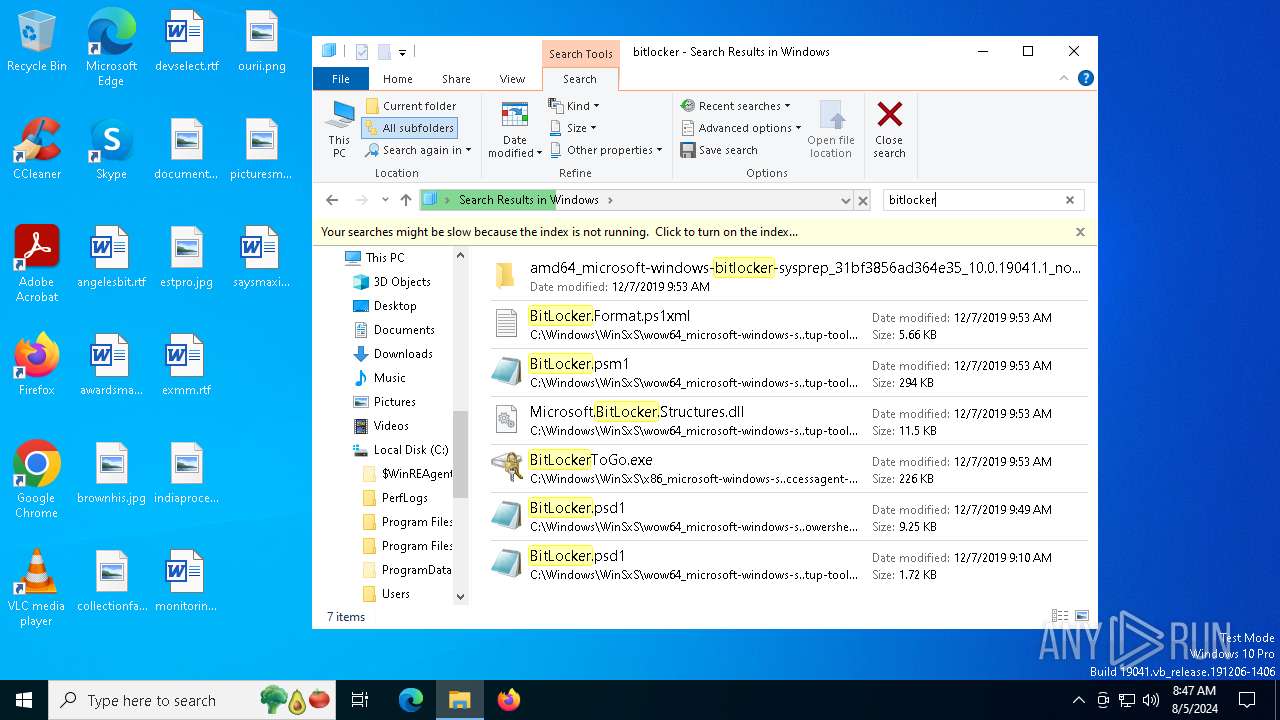
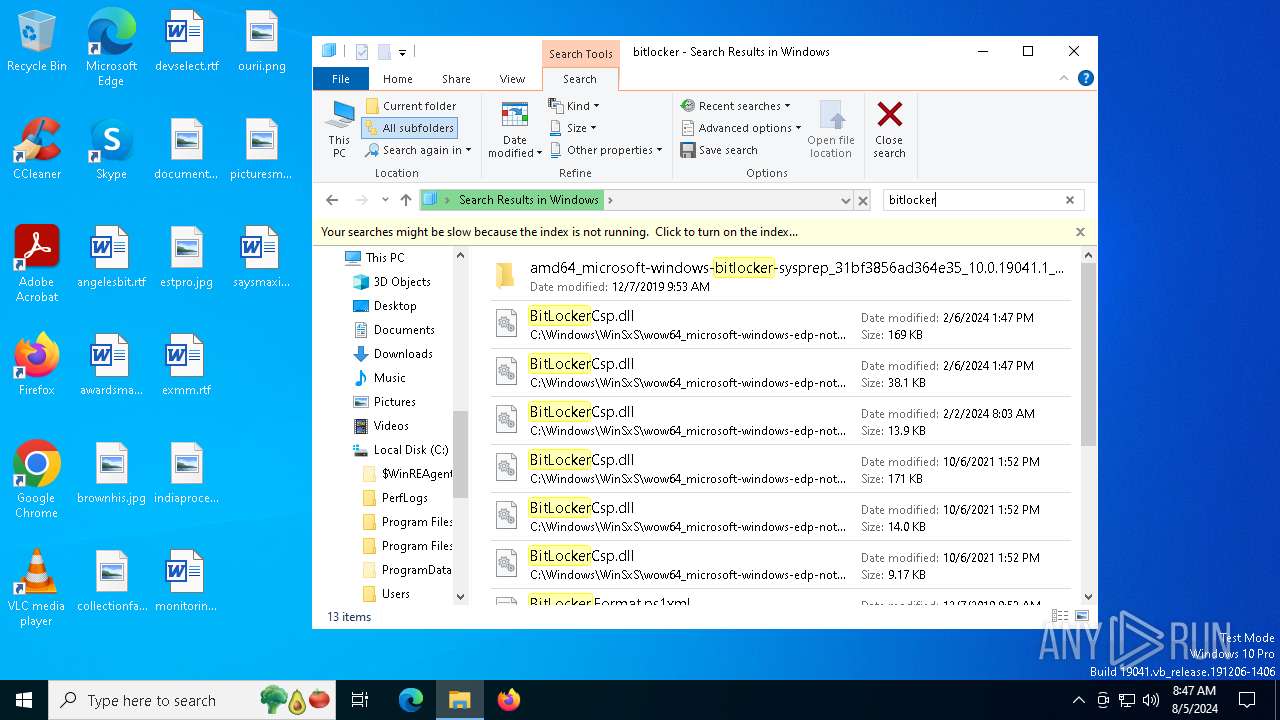
Searches for installed software
- BitLockerToGo.exe (PID: 5632)
Starts itself from another location
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
Changes internet zones settings
- 1C05CB940DFB3E6E1CDBC63A18737937.exe (PID: 4484)
Cryptography encrypted command line is found
- powershell.exe (PID: 6500)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6484)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6484)
INFO
Checks supported languages
- TextInputHost.exe (PID: 5032)
- town-fil.exe (PID: 6356)
- ashampoo.exe (PID: 6768)
- BitLockerToGo.exe (PID: 5632)
- 1C05CB940DFB3E6E1CDBC63A18737937.exe (PID: 4484)
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6500)
Manual execution by a user
- mshta.exe (PID: 6484)
Disables trace logs
- powershell.exe (PID: 6500)
Checks proxy server information
- powershell.exe (PID: 6500)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6500)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6500)
The executable file from the user directory is run by the Powershell process
- ashampoo.exe (PID: 6768)
Reads the computer name
- BitLockerToGo.exe (PID: 5632)
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
- 1C05CB940DFB3E6E1CDBC63A18737937.exe (PID: 4484)
- TextInputHost.exe (PID: 5032)
Reads the software policy settings
- BitLockerToGo.exe (PID: 5632)
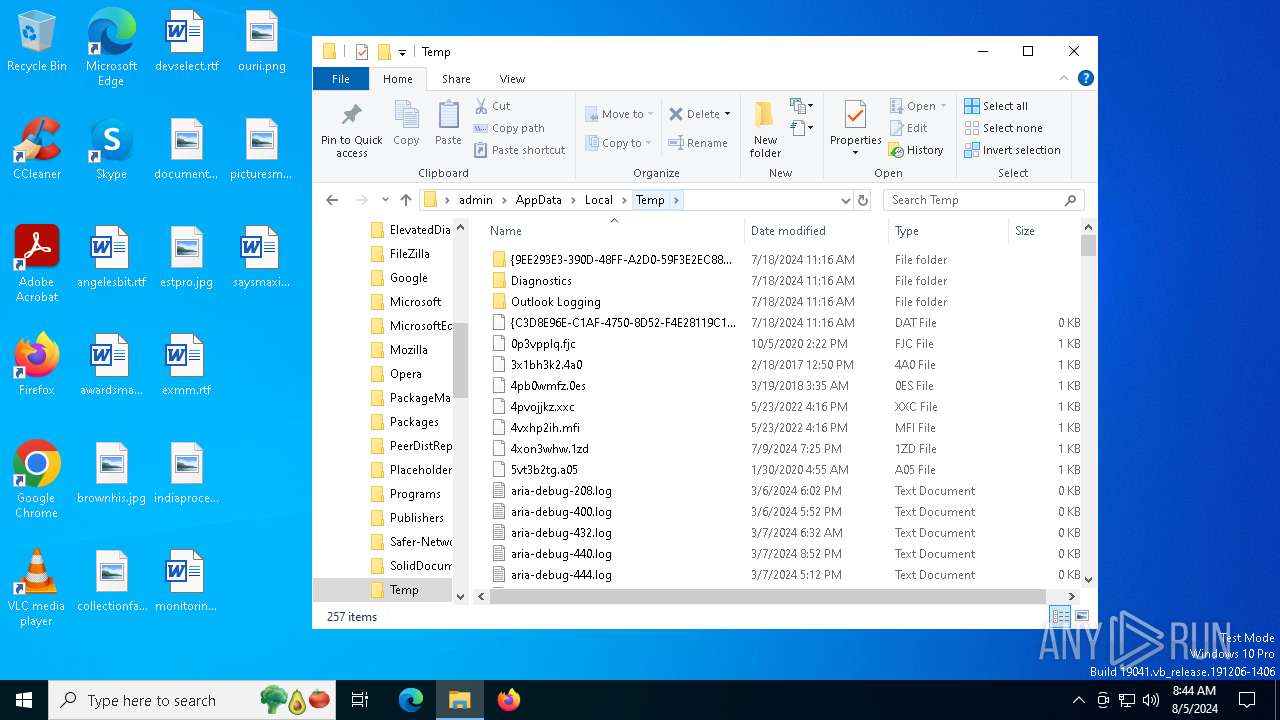
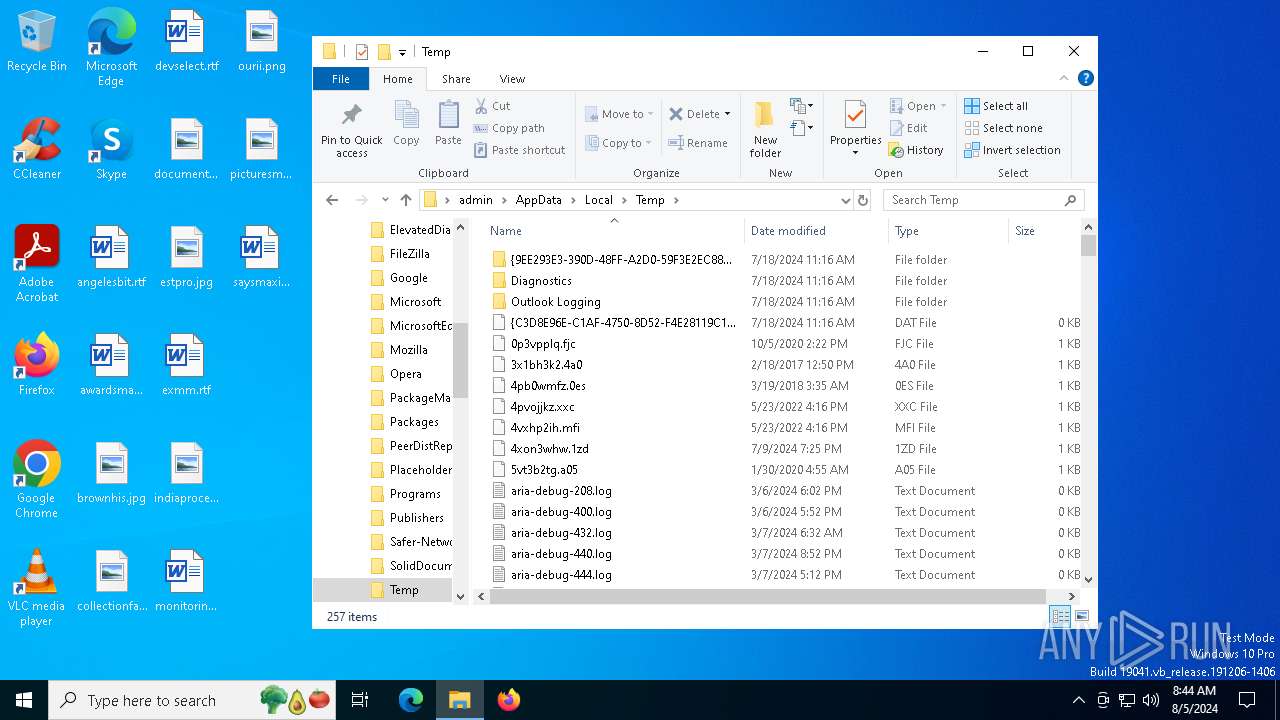
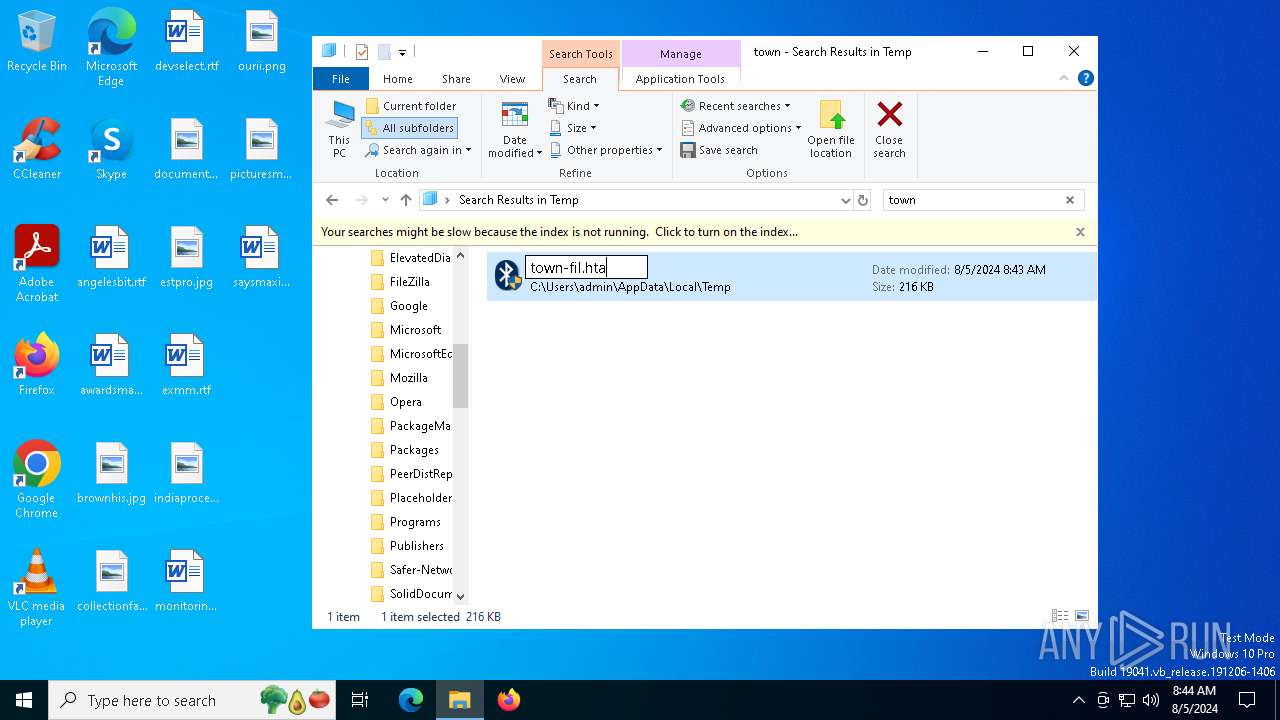
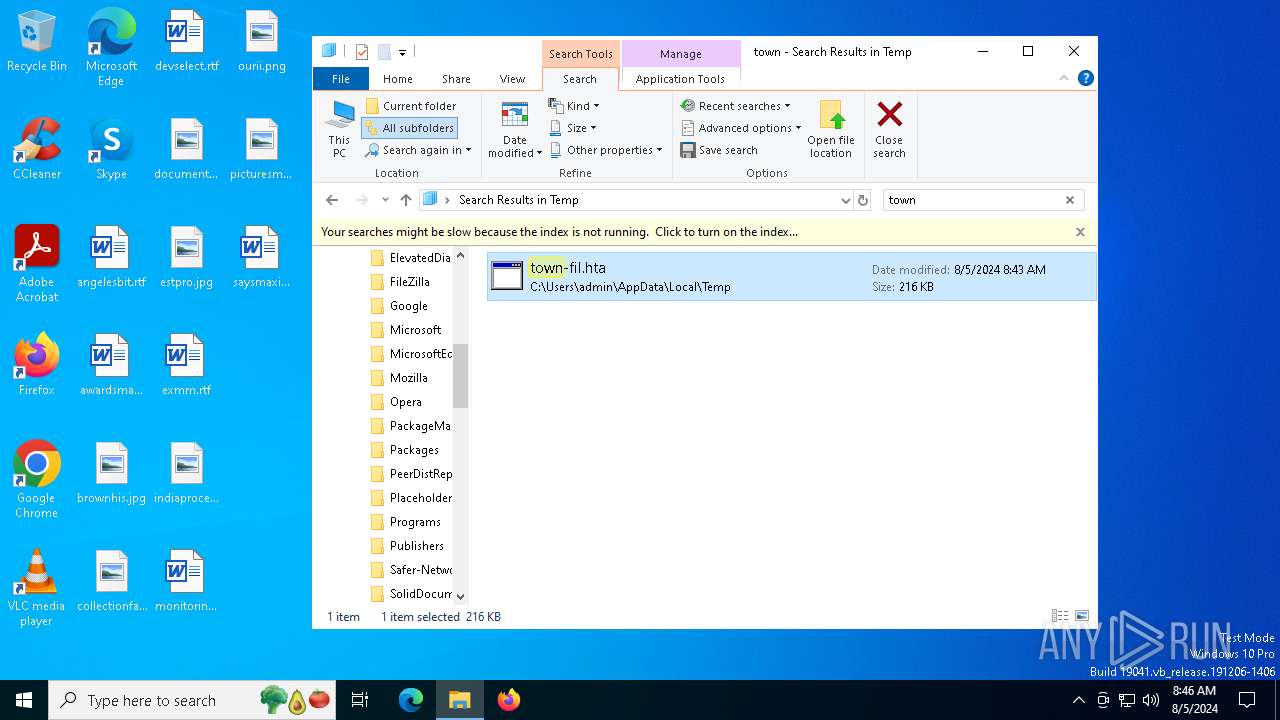
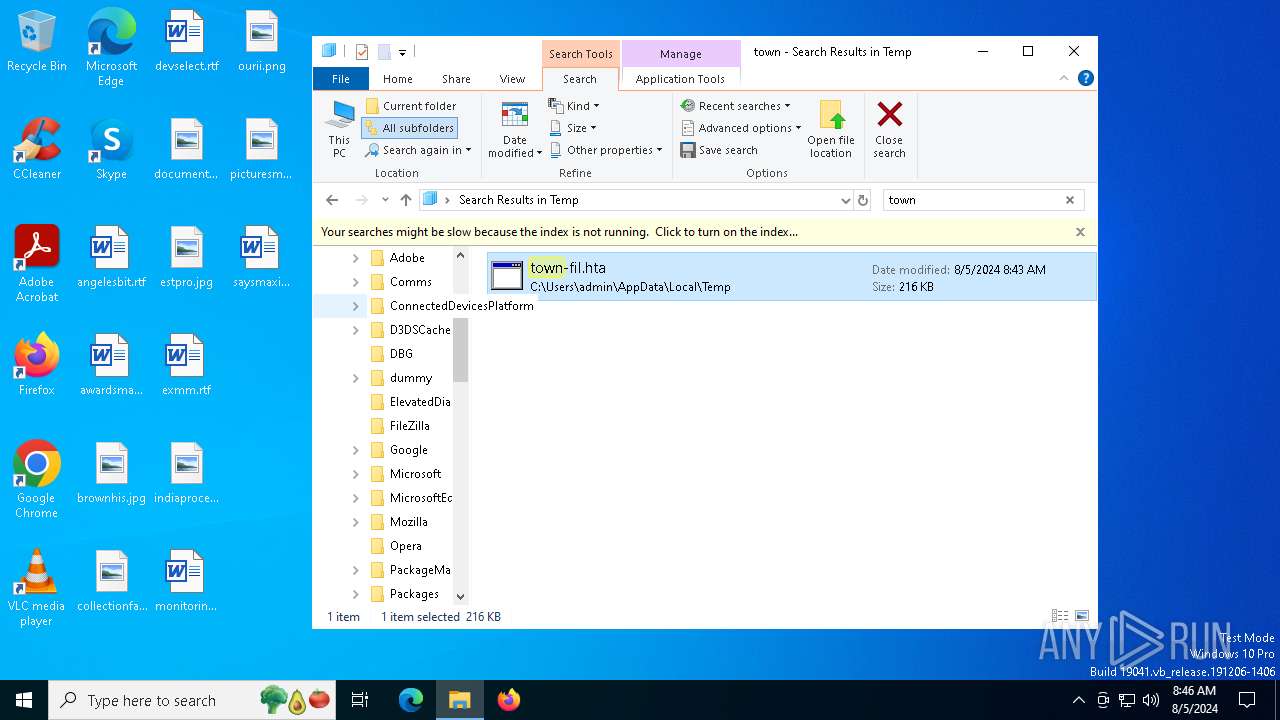
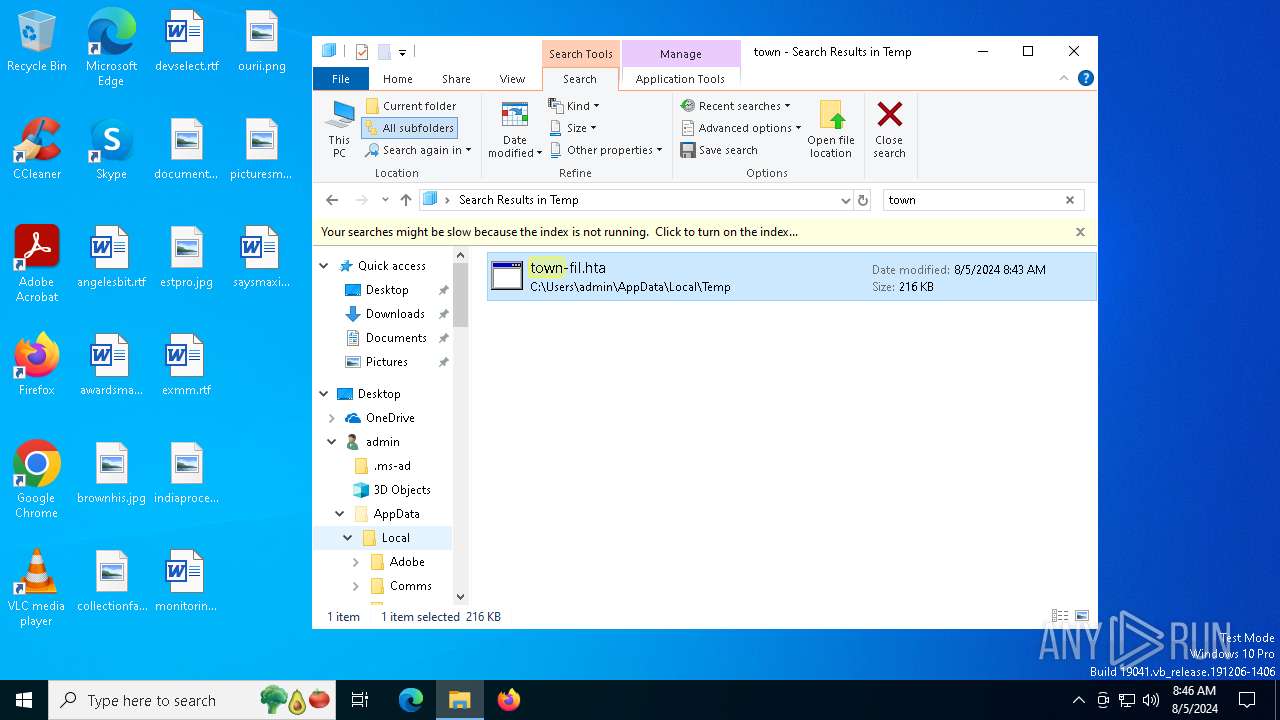
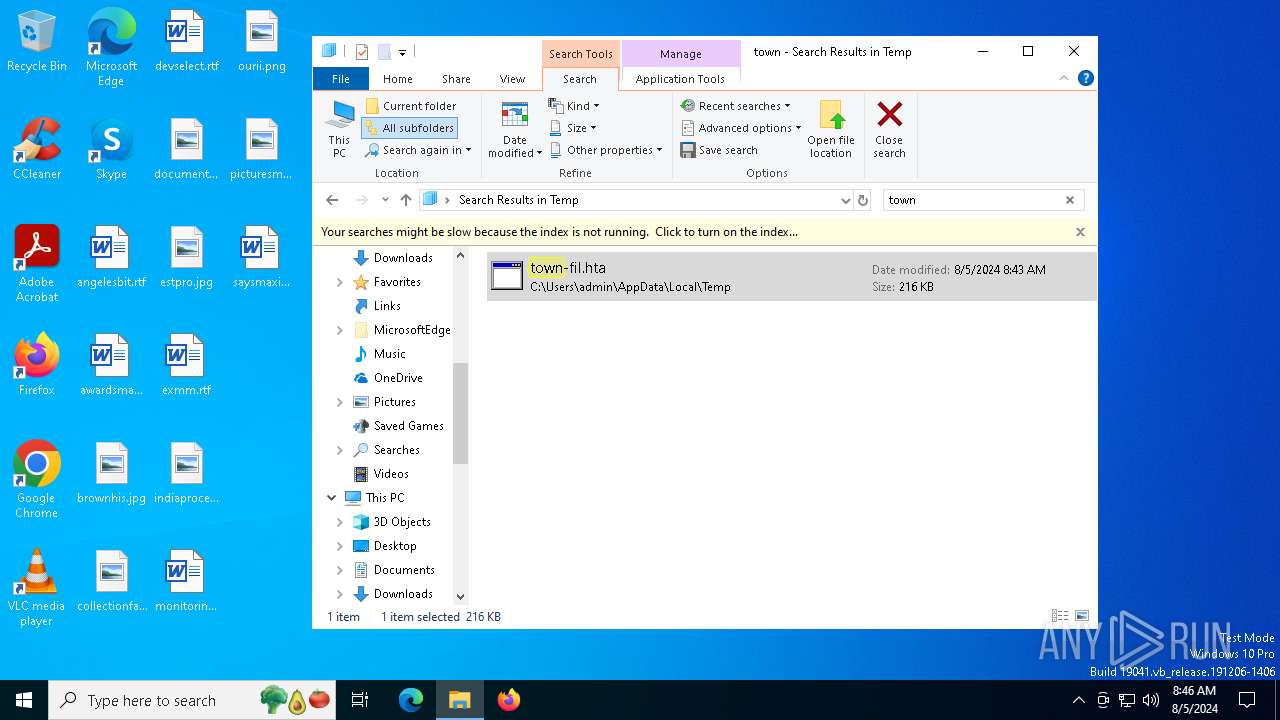
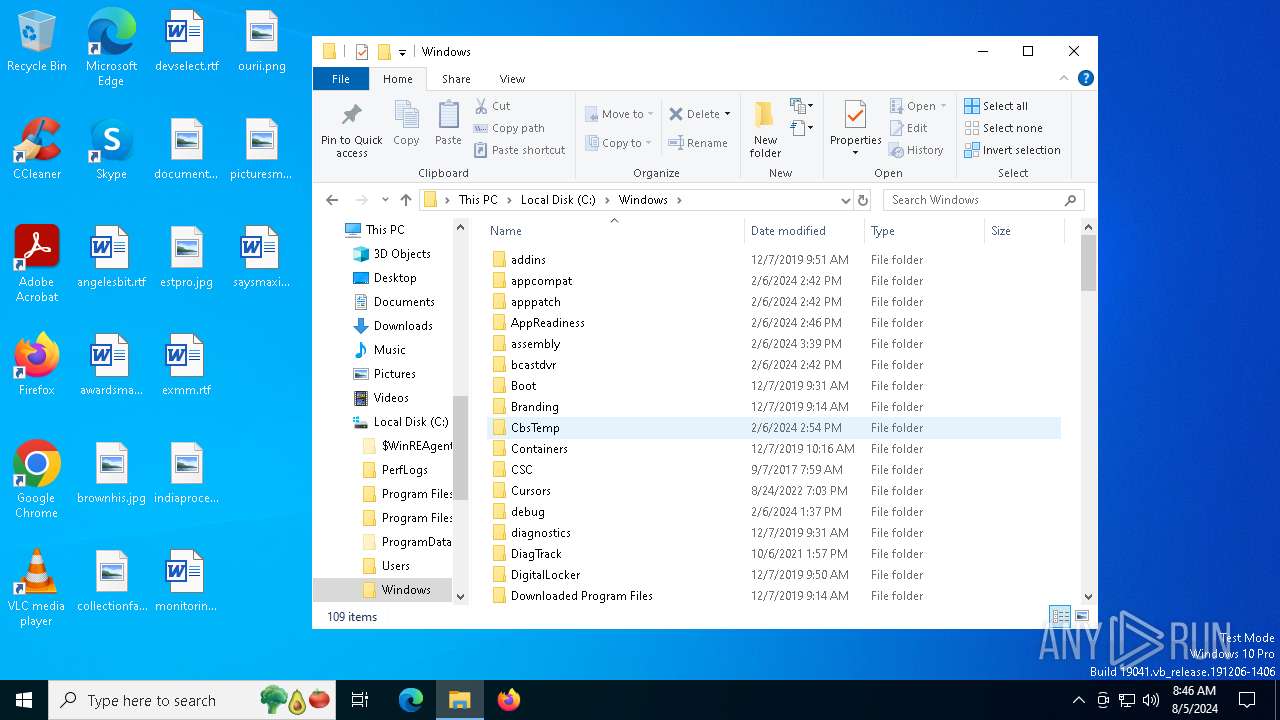
Create files in a temporary directory
- BitLockerToGo.exe (PID: 5632)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6500)
Reads the machine GUID from the registry
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
- 1C05CB940DFB3E6E1CDBC63A18737937.exe (PID: 4484)
Creates files or folders in the user directory
- 74YS17MPZL2E894217F968M.exe (PID: 4128)
Reads Internet Explorer settings
- mshta.exe (PID: 6484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6768) ashampoo.exe
C2 (9)boattyownerwrv.shop
definitonizmnx.shop
assumedtribsosp.shop
chippyfroggsyhz.shop
budgetttysnzm.shop
creepydxzoxmj.shop
sulphurhsum.shop
empiredzmwnx.shop
rainbowmynsjn.shop
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2102:03:02 16:08:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.26 |
| CodeSize: | 5632 |
| InitializedDataSize: | 32256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d00 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.20348.1 |
| ProductVersionNumber: | 10.0.20348.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Bluetooth Uninstall Device Task |
| FileVersion: | 10.0.20348.1 (WinBuild.160101.0800) |
| InternalName: | BthUdTask |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | BthUdTask.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.20348.1 |
Total processes
151
Monitored processes
13
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2392 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | "C:\WINDOWS\system32\dllhost.exe" | C:\Windows\SysWOW64\dllhost.exe | 1C05CB940DFB3E6E1CDBC63A18737937.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4128 | "C:\Users\admin\AppData\Local\Temp\74YS17MPZL2E894217F968M.exe" | C:\Users\admin\AppData\Local\Temp\74YS17MPZL2E894217F968M.exe | BitLockerToGo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4484 | "C:\Users\admin\AppData\Roaming\1C05CB940DFB3E6E1CDBC63A18737937\1C05CB940DFB3E6E1CDBC63A18737937.exe" | C:\Users\admin\AppData\Roaming\1C05CB940DFB3E6E1CDBC63A18737937\1C05CB940DFB3E6E1CDBC63A18737937.exe | 74YS17MPZL2E894217F968M.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5032 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 5632 | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | ashampoo.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
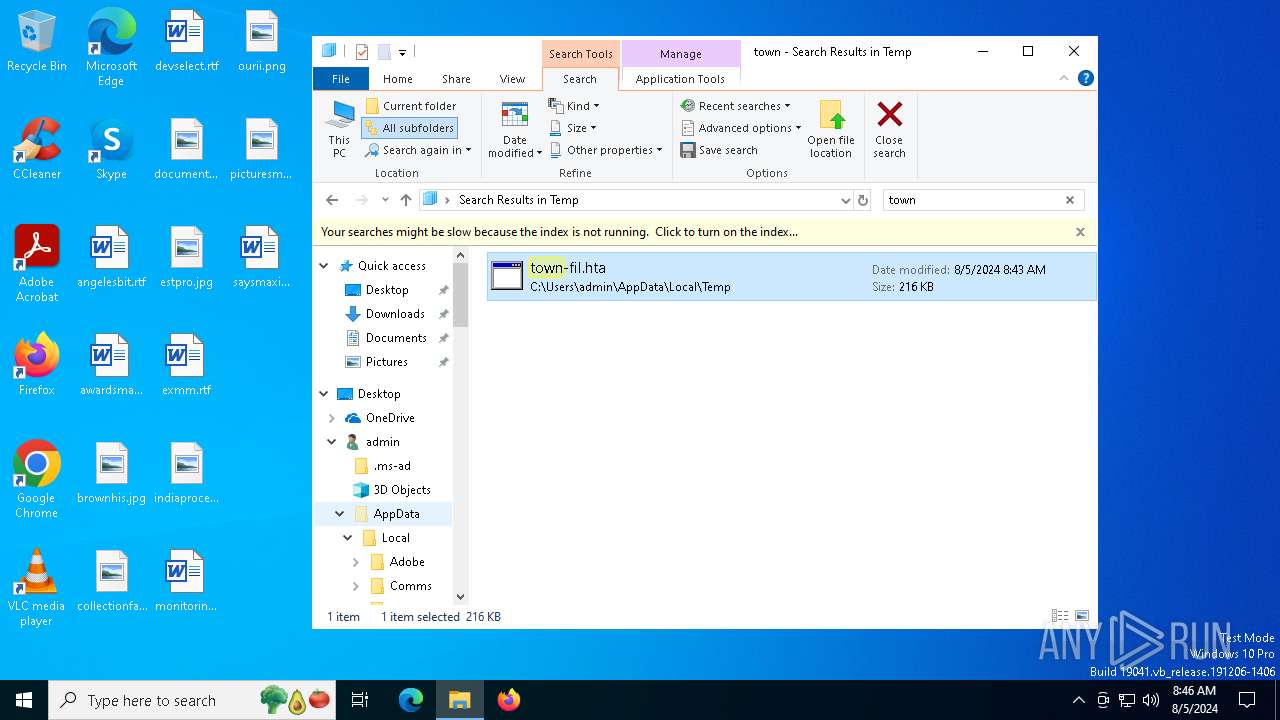
| 6308 | "C:\Users\admin\AppData\Local\Temp\town-fil.exe" | C:\Users\admin\AppData\Local\Temp\town-fil.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bluetooth Uninstall Device Task Exit code: 3221226540 Version: 10.0.20348.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6356 | "C:\Users\admin\AppData\Local\Temp\town-fil.exe" | C:\Users\admin\AppData\Local\Temp\town-fil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Bluetooth Uninstall Device Task Exit code: 0 Version: 10.0.20348.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | town-fil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6464 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 709
Read events
19 424
Write events
285
Delete events
0
Modification events
| (PID) Process: | (6484) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6484) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6484) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6484) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6500) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
9
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6768 | ashampoo.exe | C:\Users\Public\Libraries\igcdh.scif | — | |
MD5:— | SHA256:— | |||
| 6768 | ashampoo.exe | C:\Users\Public\Libraries\ihhne.scif | — | |
MD5:— | SHA256:— | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iwgbgp1f.um0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lx1xavh2.t40.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ashampoo\vk_swiftshader.dll | executable | |
MD5:43EDB274F096F152DB2C50E66490DBE6 | SHA256:3E5D7EF83FBD7FB5B8901D15232978BCD0478A60DB7B927ADBC1535A75BB4CB7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4fcrruof.iy5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ashampoo\vulkan-1.dll | executable | |
MD5:324AFF6C3EB09B8975A40C3BFBAB2E64 | SHA256:4D18B4CE03DE6FE581F5F003365B39AC1E71D9B7497FC787EDF23A7F45361052 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kitdwnlf.hkb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2wmuv0cw.rkc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6500 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:5F62DFB53E47D6CD6715ABE772A855F8 | SHA256:C327736DF96A1BC7AC8A64CFC9935A7665EE601ACCC469BAB24E3822FA7AEFC0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
56
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6856 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6908 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4128 | 74YS17MPZL2E894217F968M.exe | POST | 200 | 89.248.206.222:80 | http://vamplersam.info/cfg | unknown | — | — | unknown |
2796 | dllhost.exe | GET | 302 | 172.217.16.206:80 | http://google.com/webhp | unknown | — | — | whitelisted |
4484 | 1C05CB940DFB3E6E1CDBC63A18737937.exe | POST | 200 | 89.248.206.222:80 | http://vamplersam.info/cfg | unknown | — | — | unknown |
2796 | dllhost.exe | POST | 200 | 89.248.206.222:80 | http://vamplersam.info/ | unknown | — | — | unknown |
2796 | dllhost.exe | POST | 200 | 89.248.206.222:80 | http://vamplersam.info/cfg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6080 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3164 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 92.123.104.27:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
640 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |