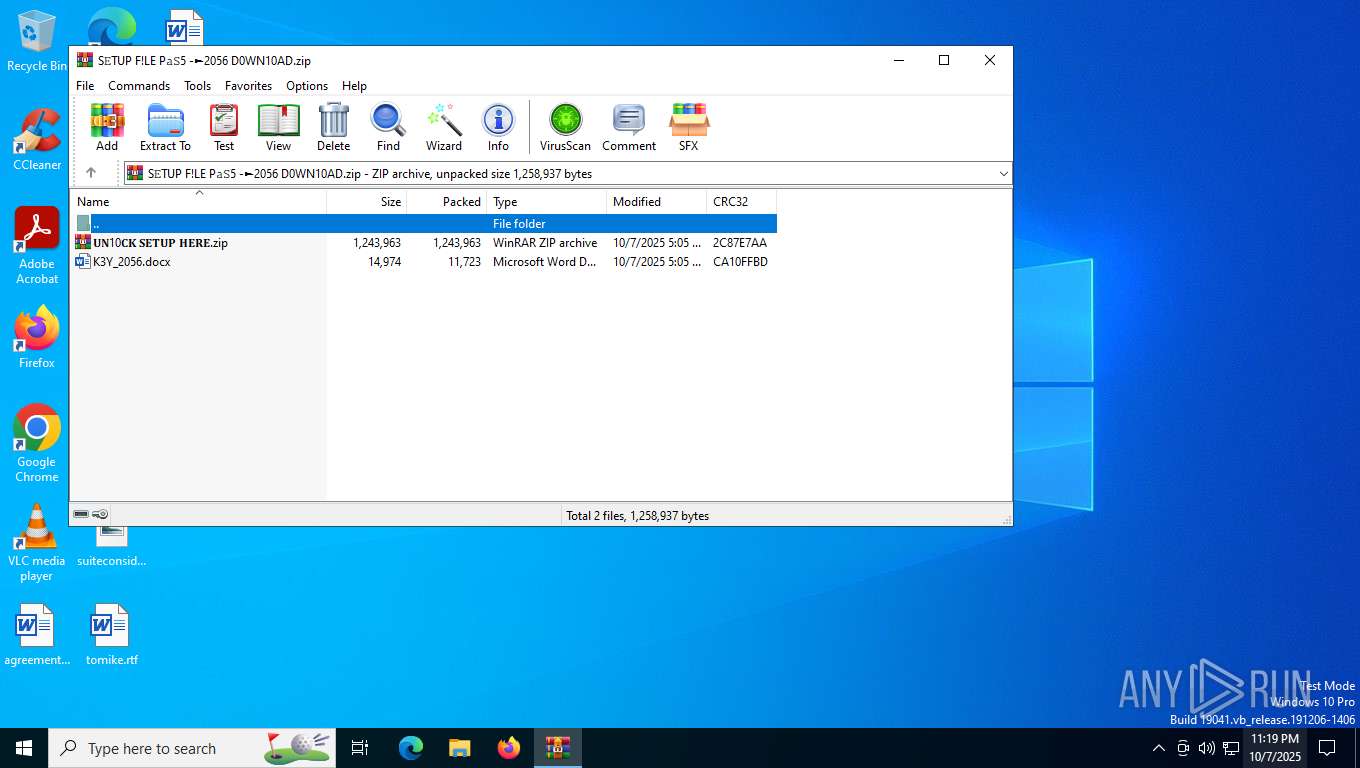
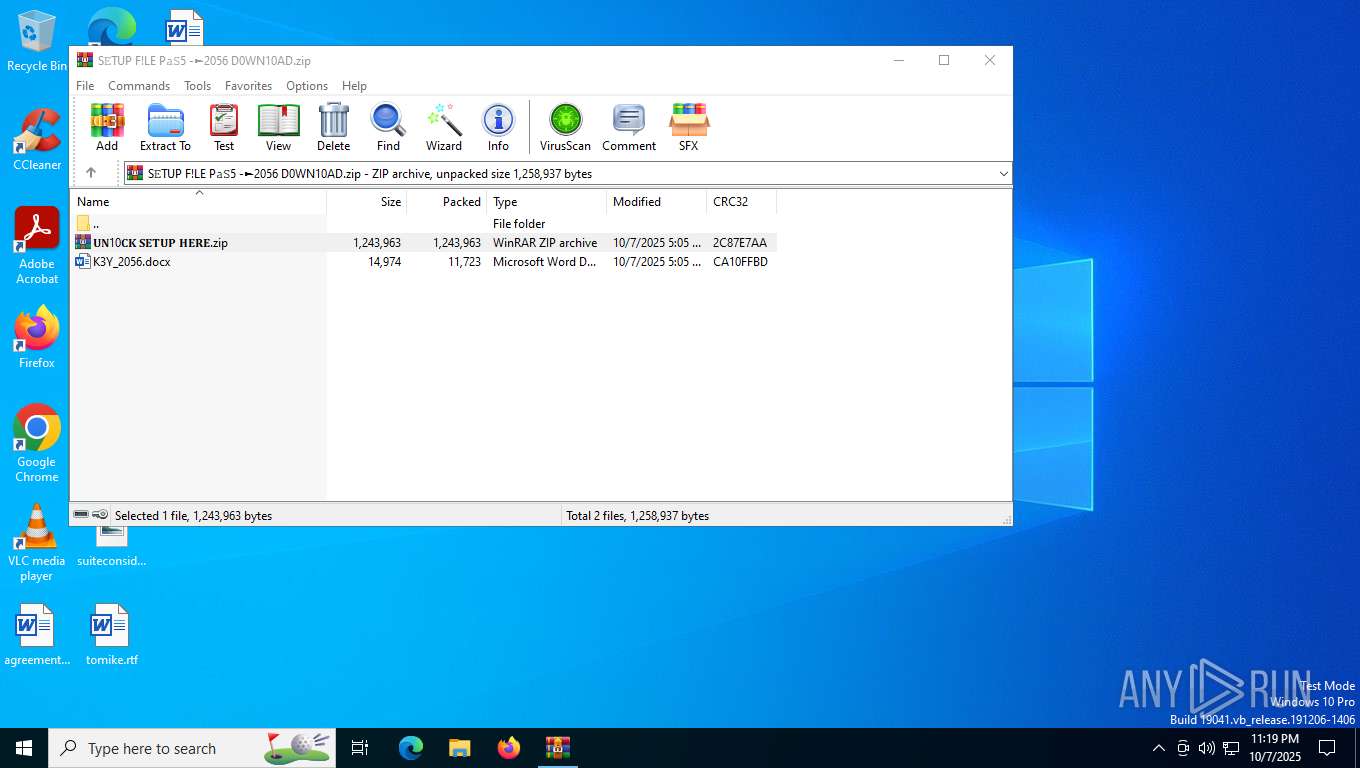
| File name: | S𝙴TUP F!LE P𝚊𝚂5 -►2056 D0WN10AD.zip |
| Full analysis: | https://app.any.run/tasks/07811234-2366-4031-a526-94636fca5706 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 07, 2025, 23:18:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 8EA374BDF53EB72BEFCC0F7D50C925F1 |
| SHA1: | EB98FA21E491E6A0B6F84503E5E92C80D7FA16C6 |
| SHA256: | 5F1CCD62998CE2193934794728654C5EB3028B7CBA628CFE3416725A8C4FB1A2 |
| SSDEEP: | 49152:WLrSyGfMmbJcLJH5Kg6GX2VQt9Zhz+xpwoezCMZBzKrP+2CMK8qKvi/G9lz/LuXz:OSEmuLJH5rlXem9fzkJo9ePKMrI+Hz/Y |
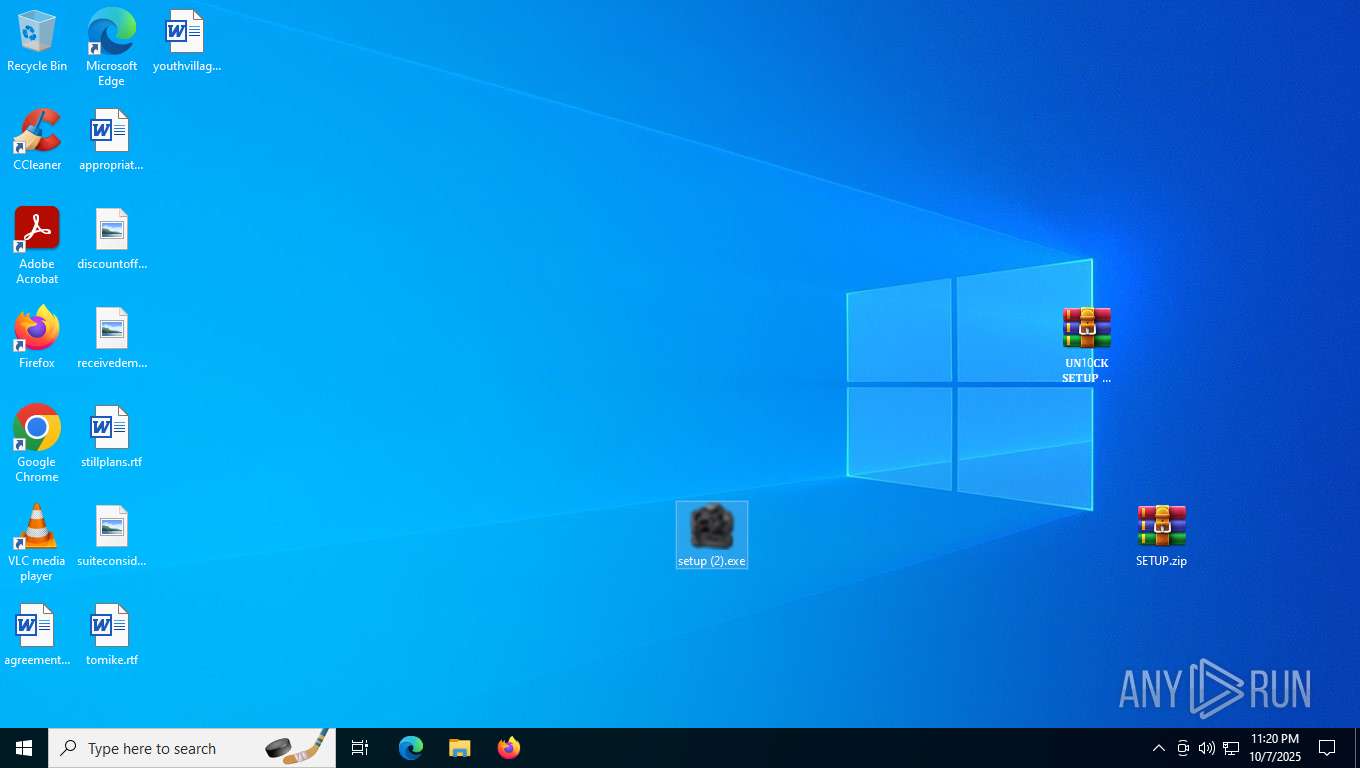
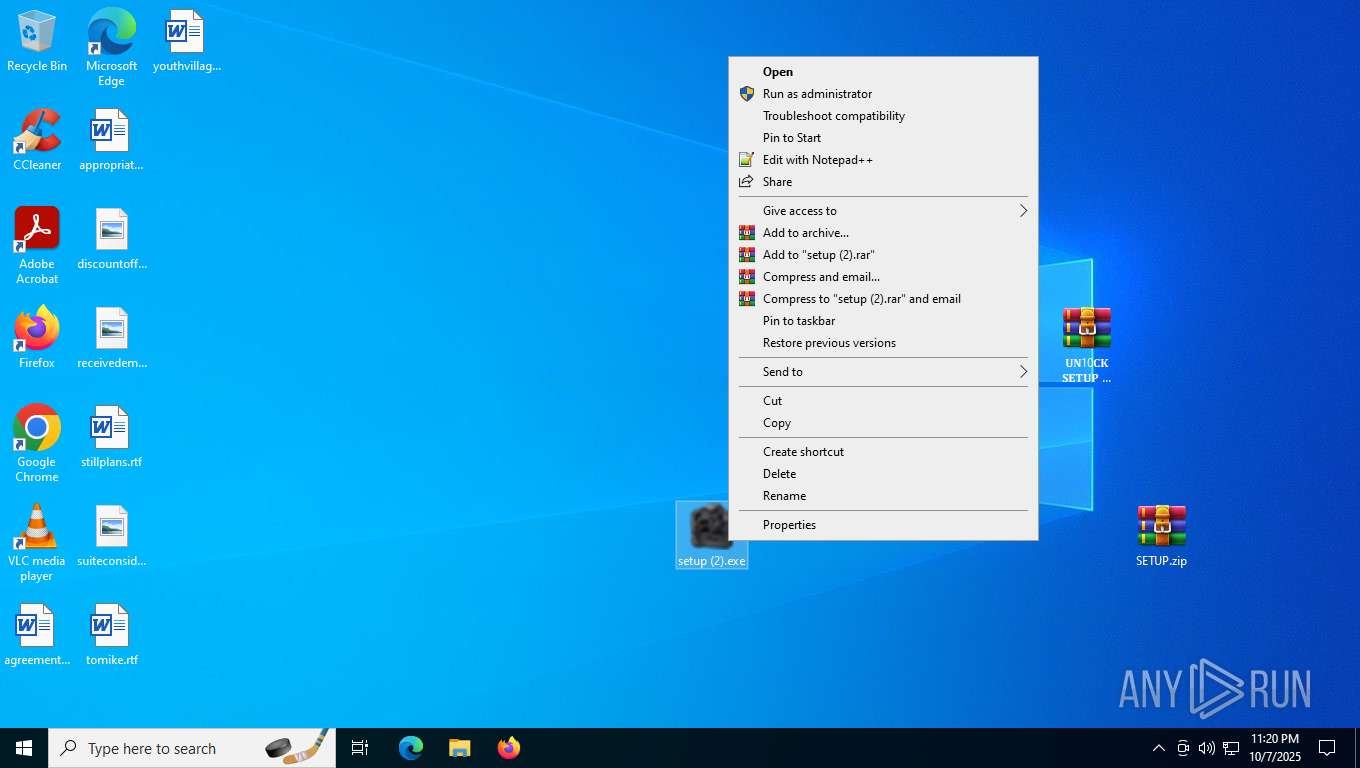
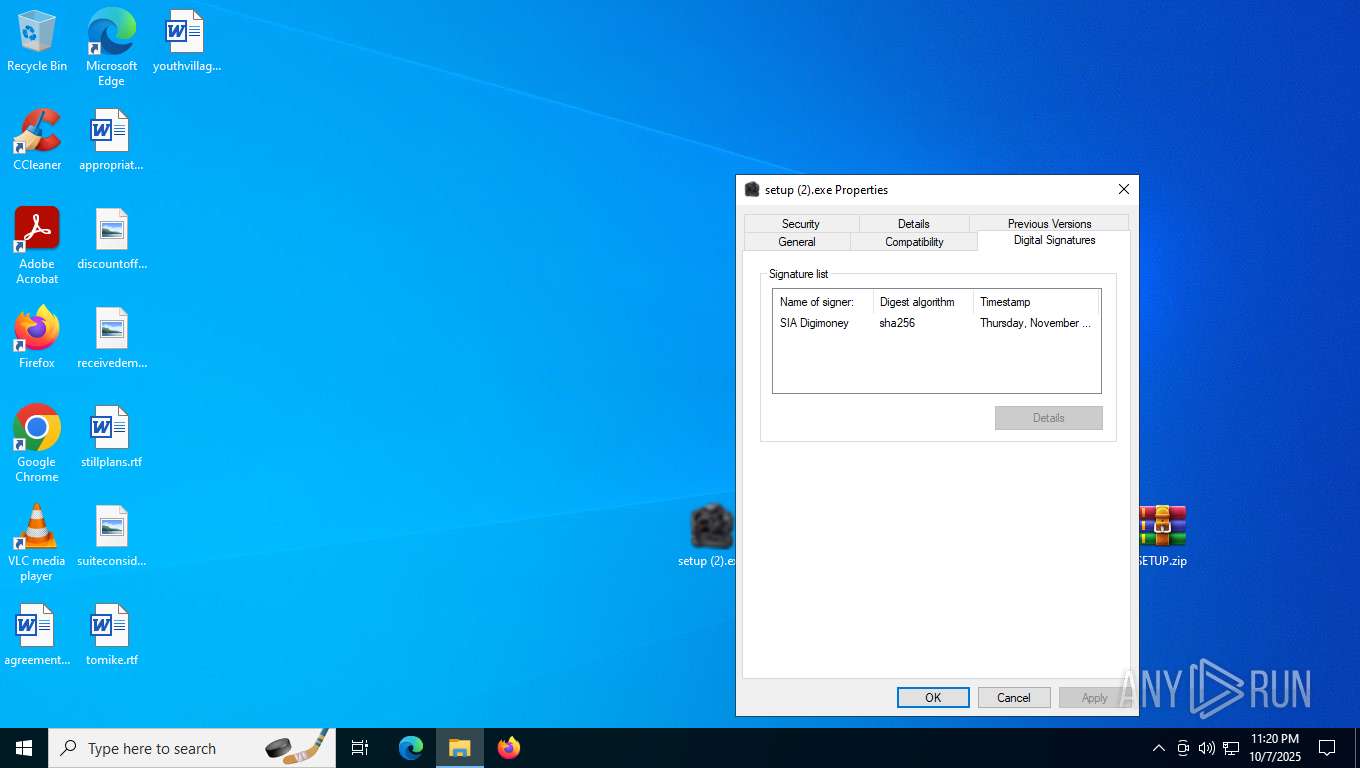
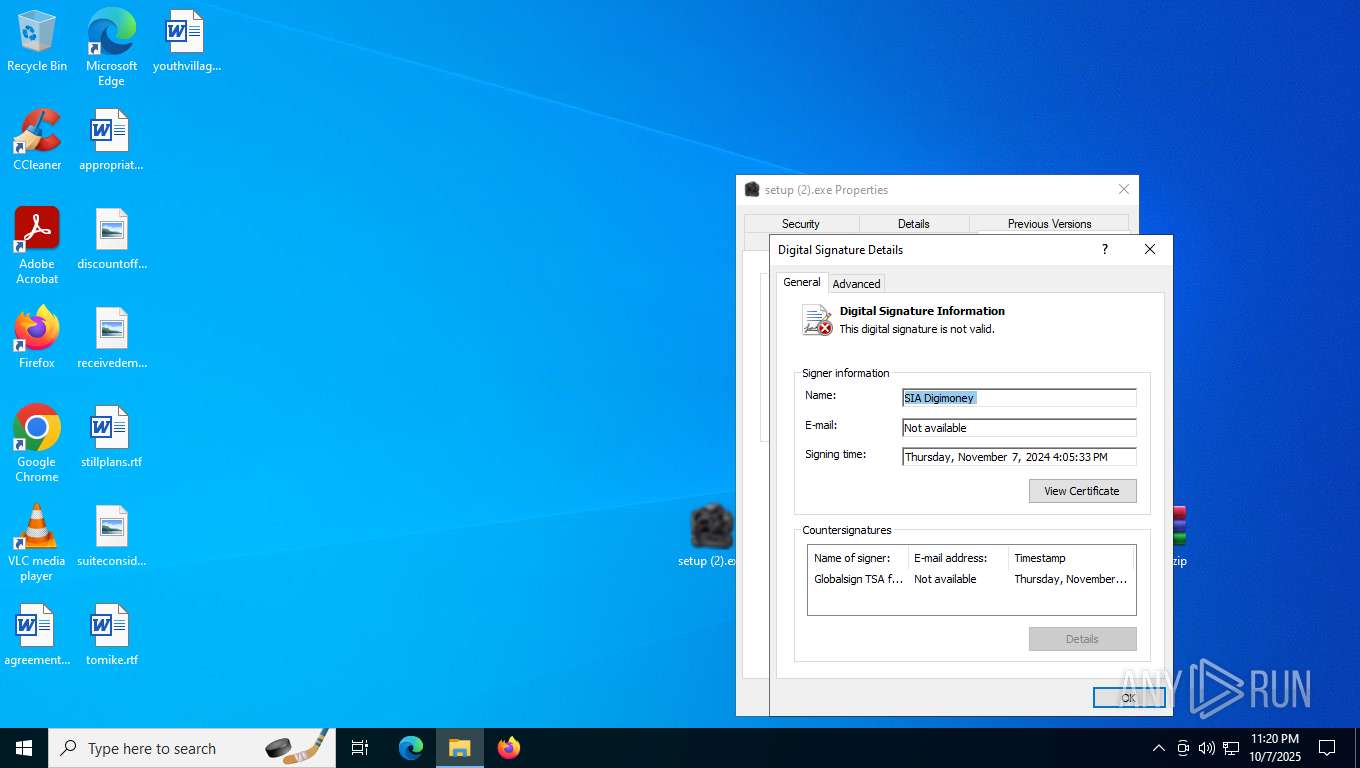
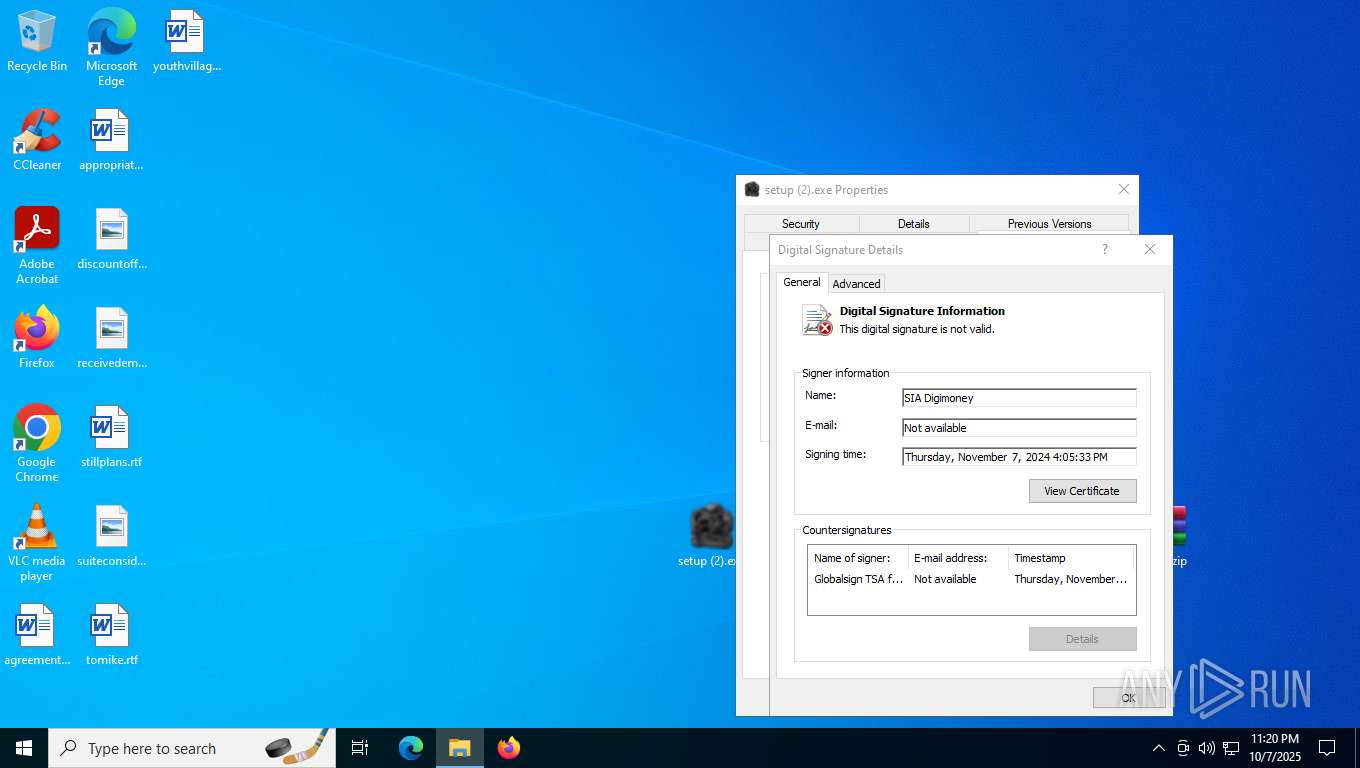
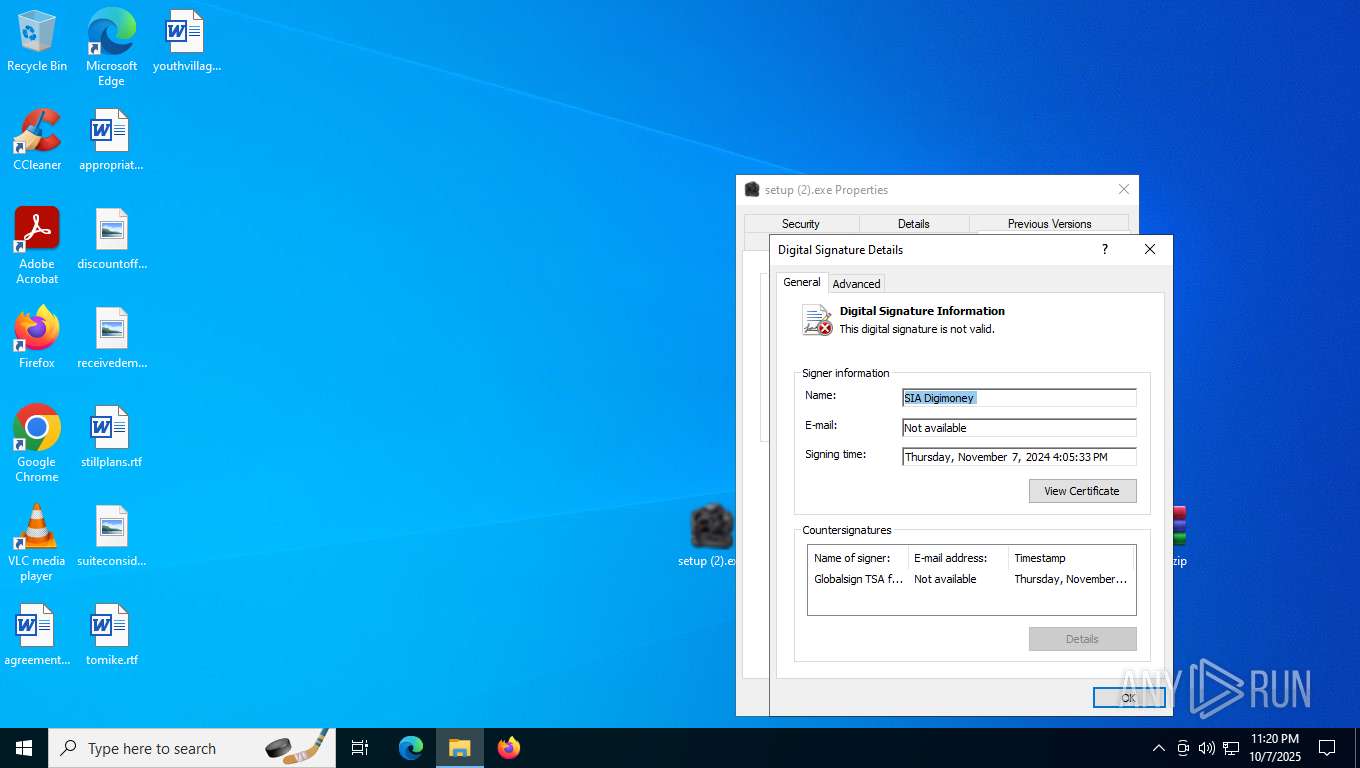
MALICIOUS
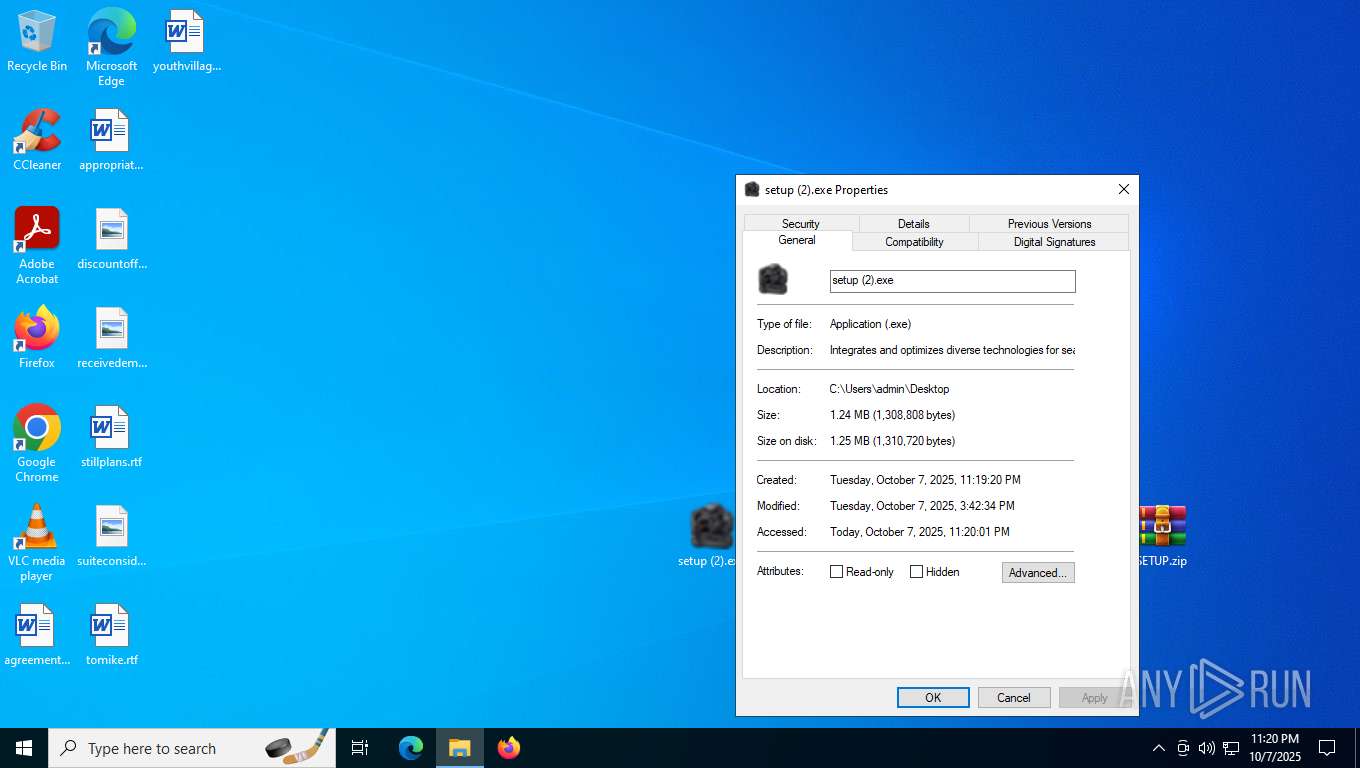
Executing a file with an untrusted certificate
- setup (2).exe (PID: 7464)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2428)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- setup (2).exe (PID: 7464)
Get information on the list of running processes
- cmd.exe (PID: 6340)
Starts CMD.EXE for commands execution
- setup (2).exe (PID: 7464)
Executing commands from a ".bat" file
- setup (2).exe (PID: 7464)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6340)
Executable content was dropped or overwritten
- explorer.exe (PID: 5156)
Starts application with an unusual extension
- cmd.exe (PID: 6340)
- explorer.exe (PID: 5156)
The executable file from the user directory is run by the CMD process
- Mainland.scr (PID: 2164)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6340)
- explorer.exe (PID: 5156)
Reads security settings of Internet Explorer
- Mainland.scr (PID: 8912)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Mainland.scr (PID: 8912)
INFO
Reads Microsoft Office registry keys
- explorer.exe (PID: 5156)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5156)
- HelpPane.exe (PID: 5584)
The sample compiled with english language support
- WinRAR.exe (PID: 1136)
- explorer.exe (PID: 5156)
- WinRAR.exe (PID: 3264)
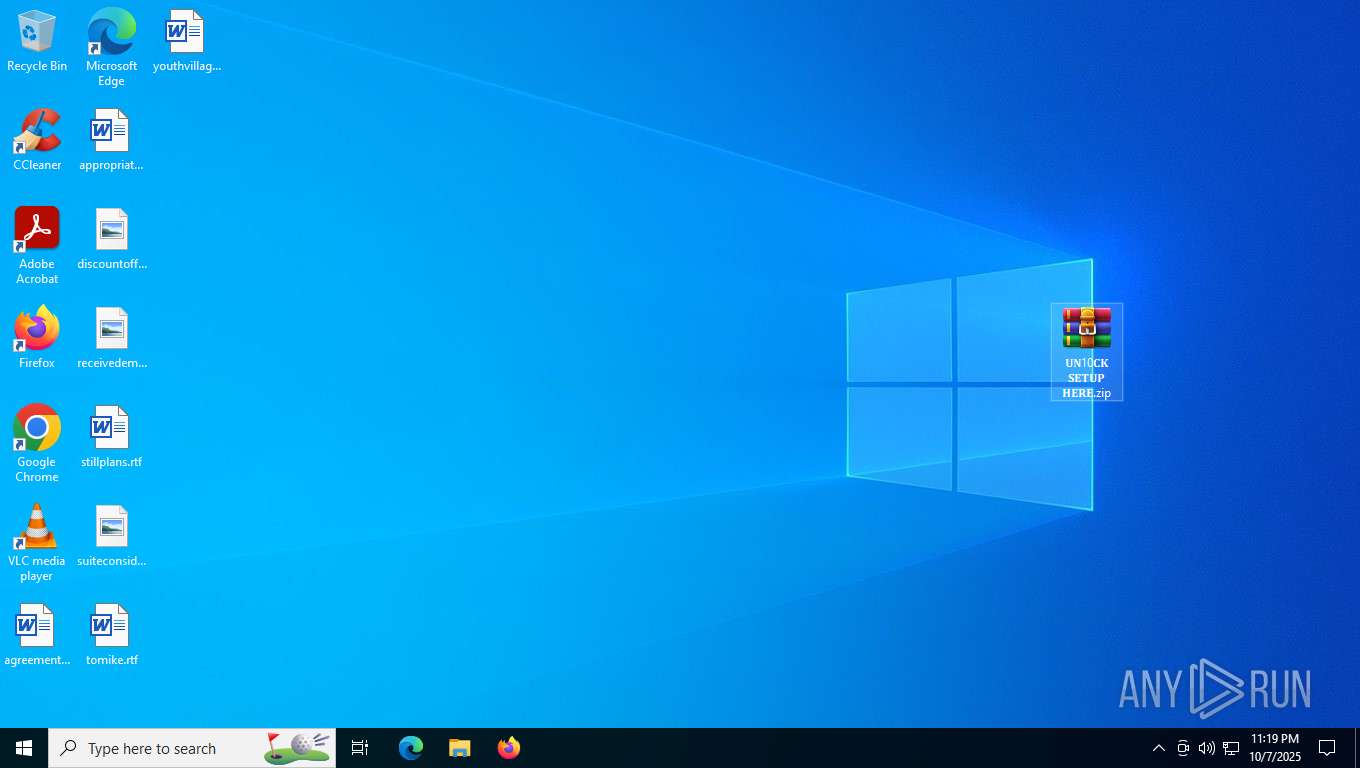
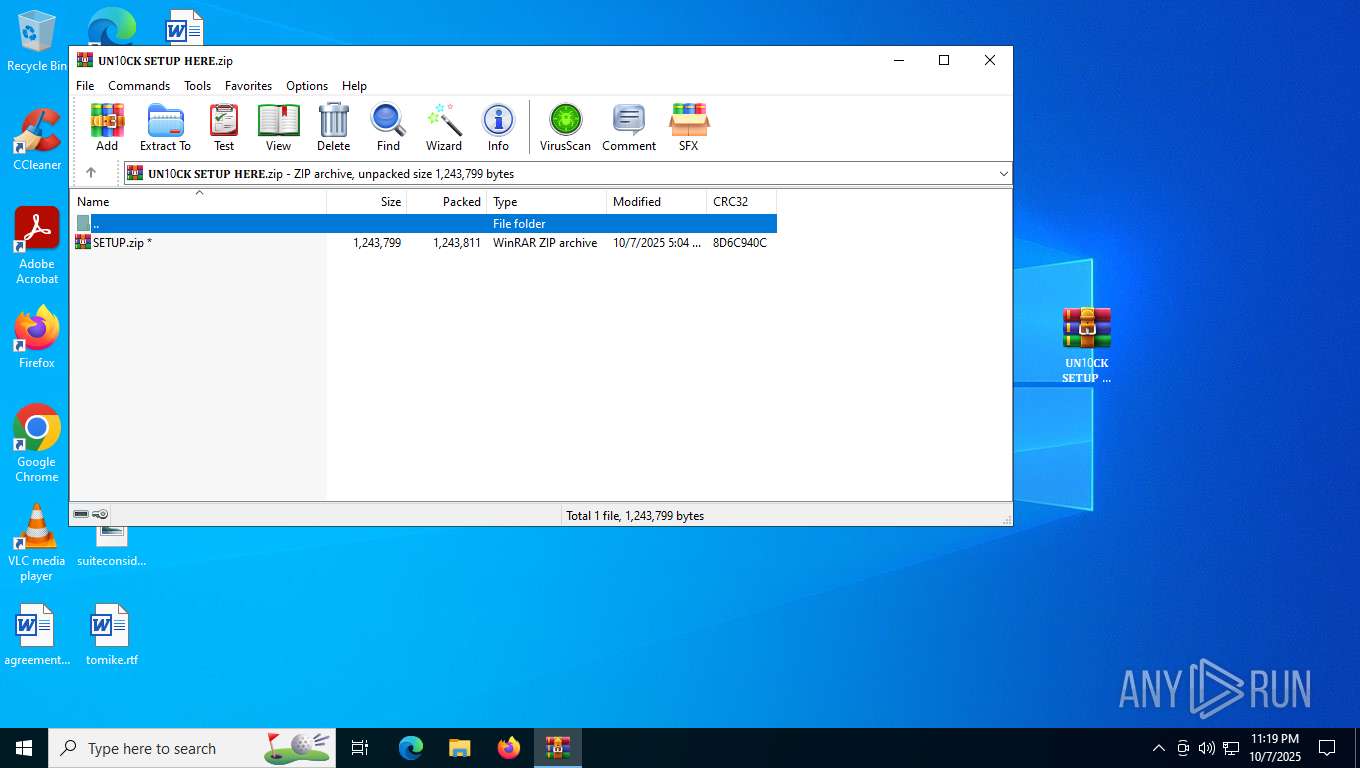
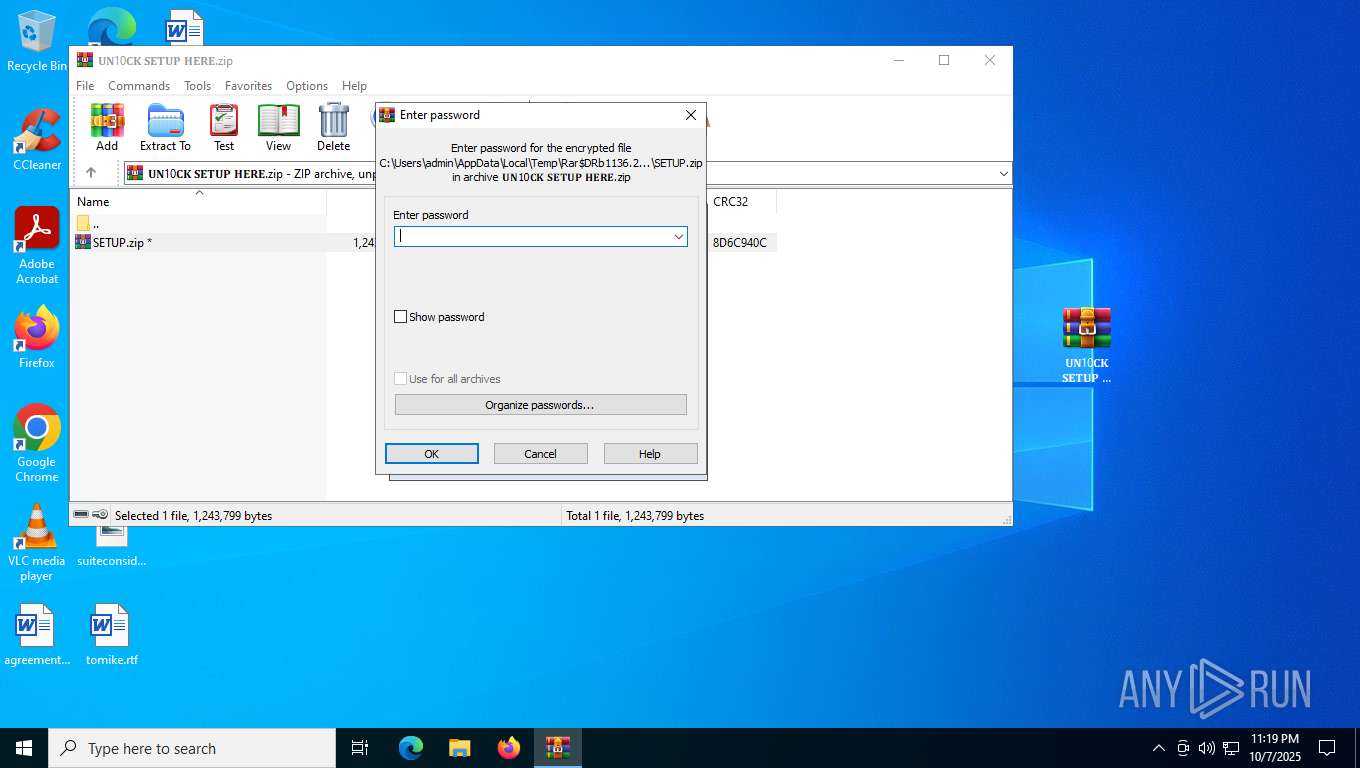
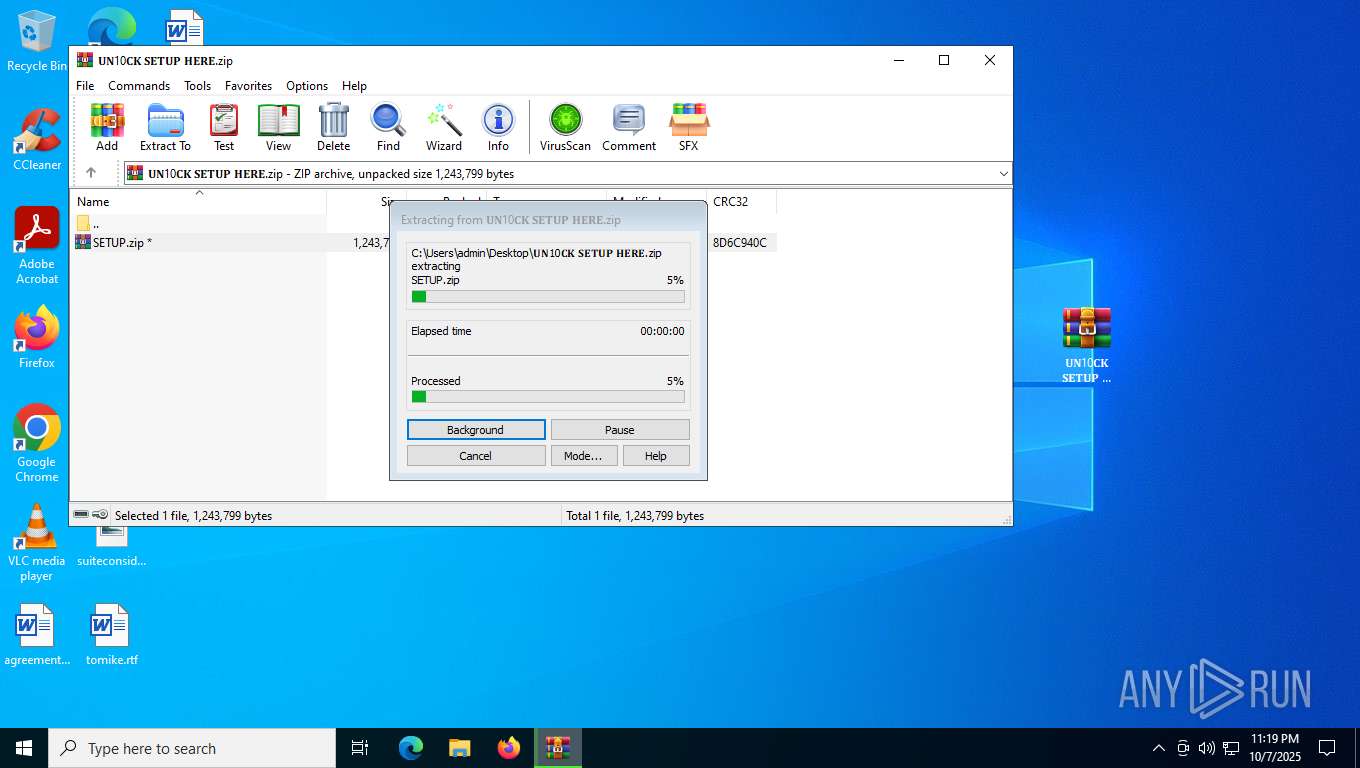
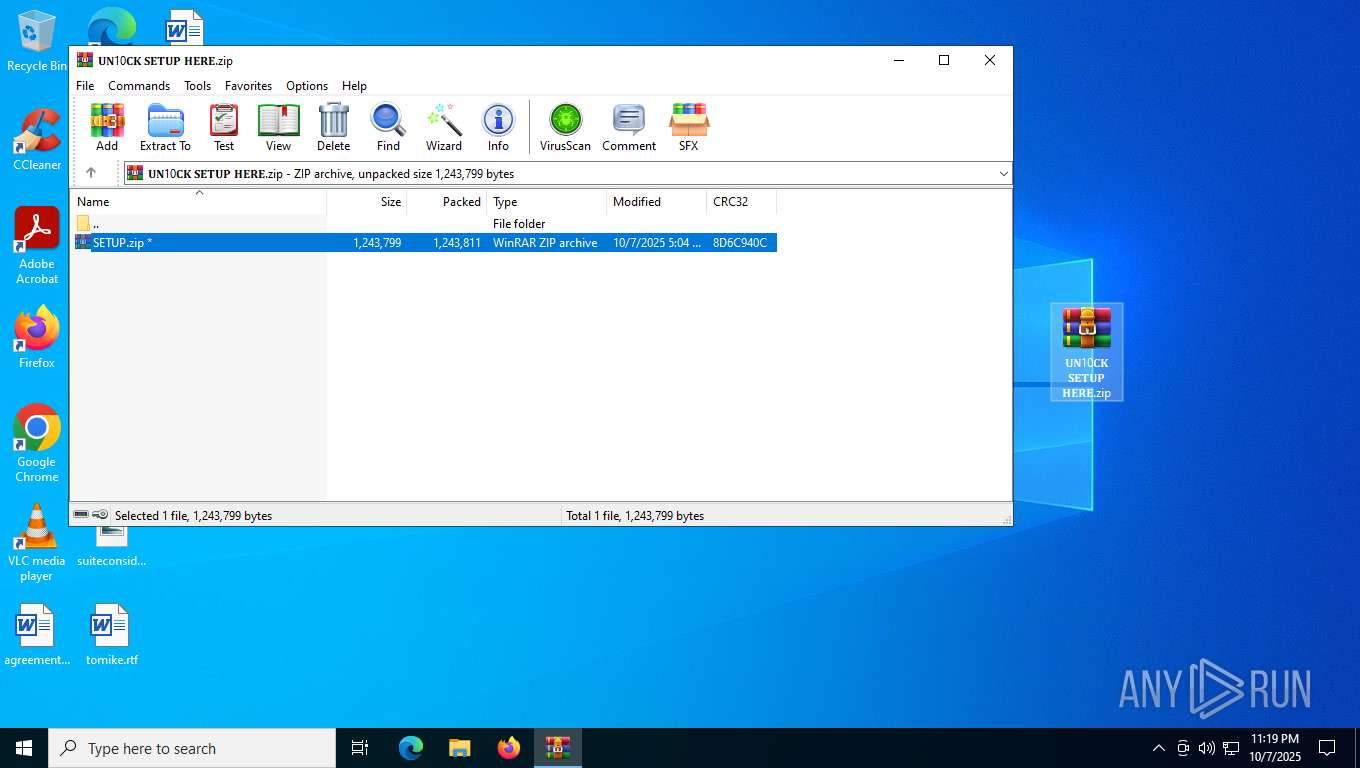
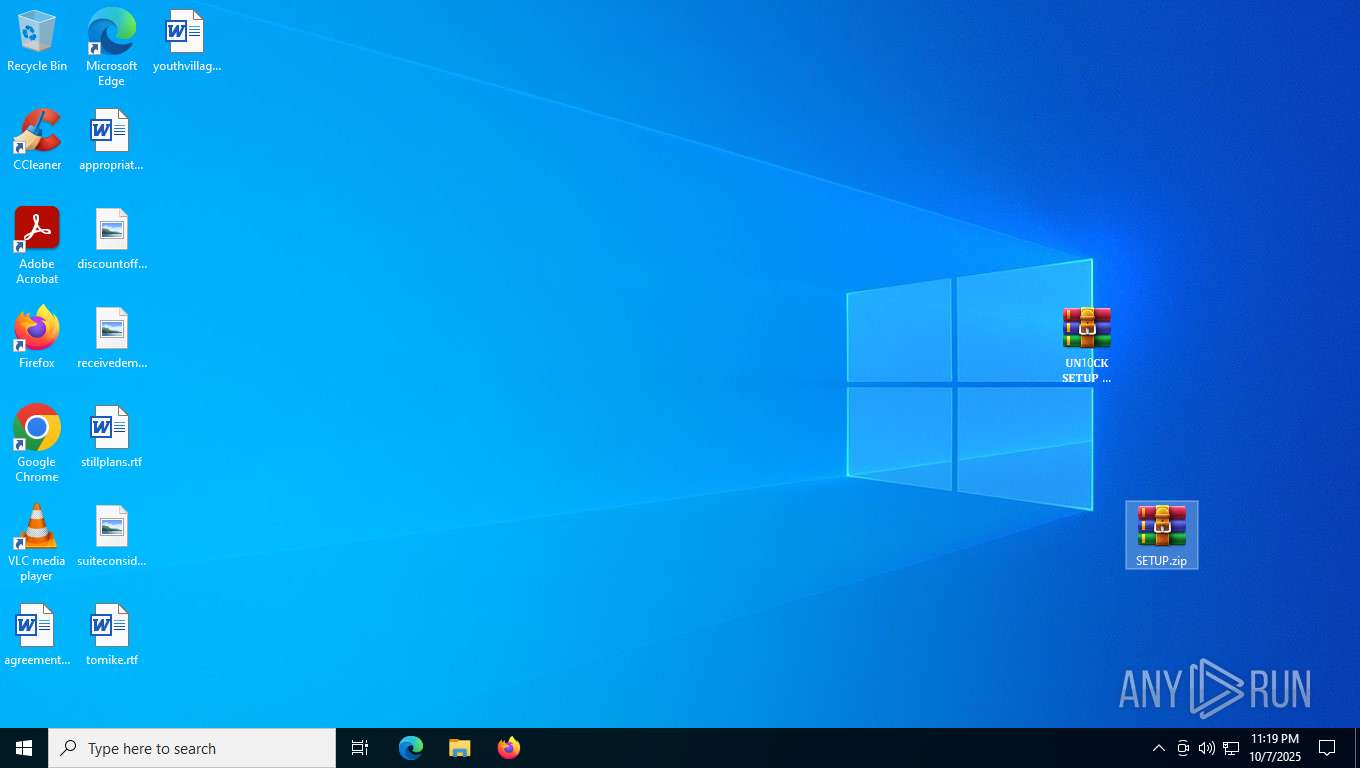
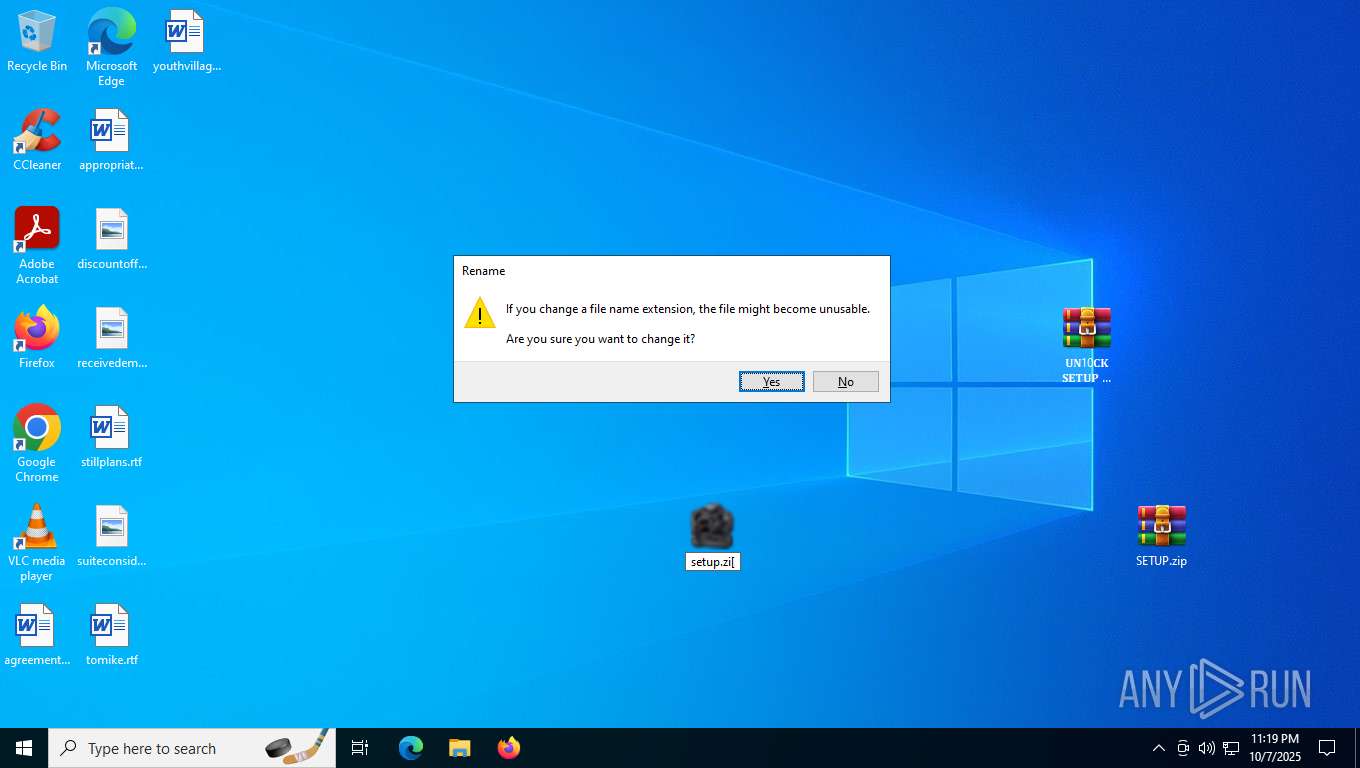
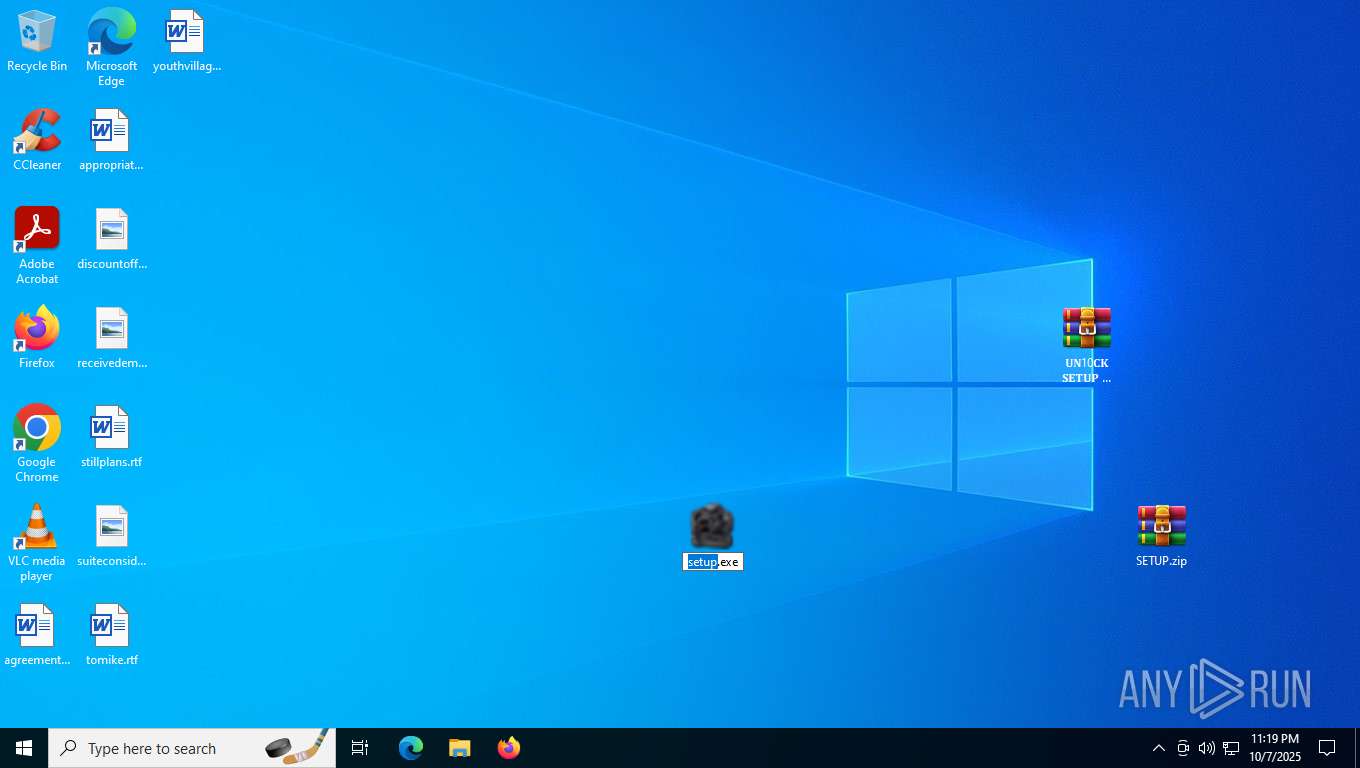
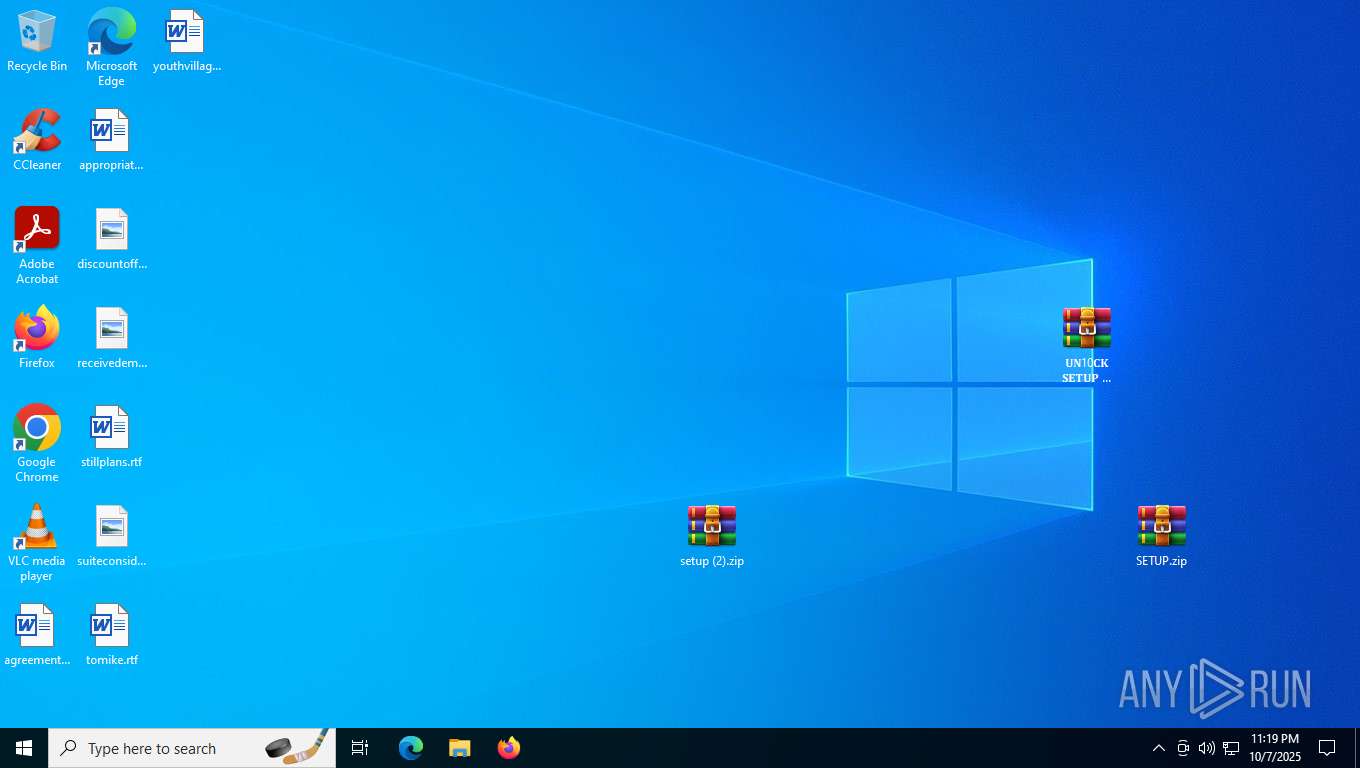
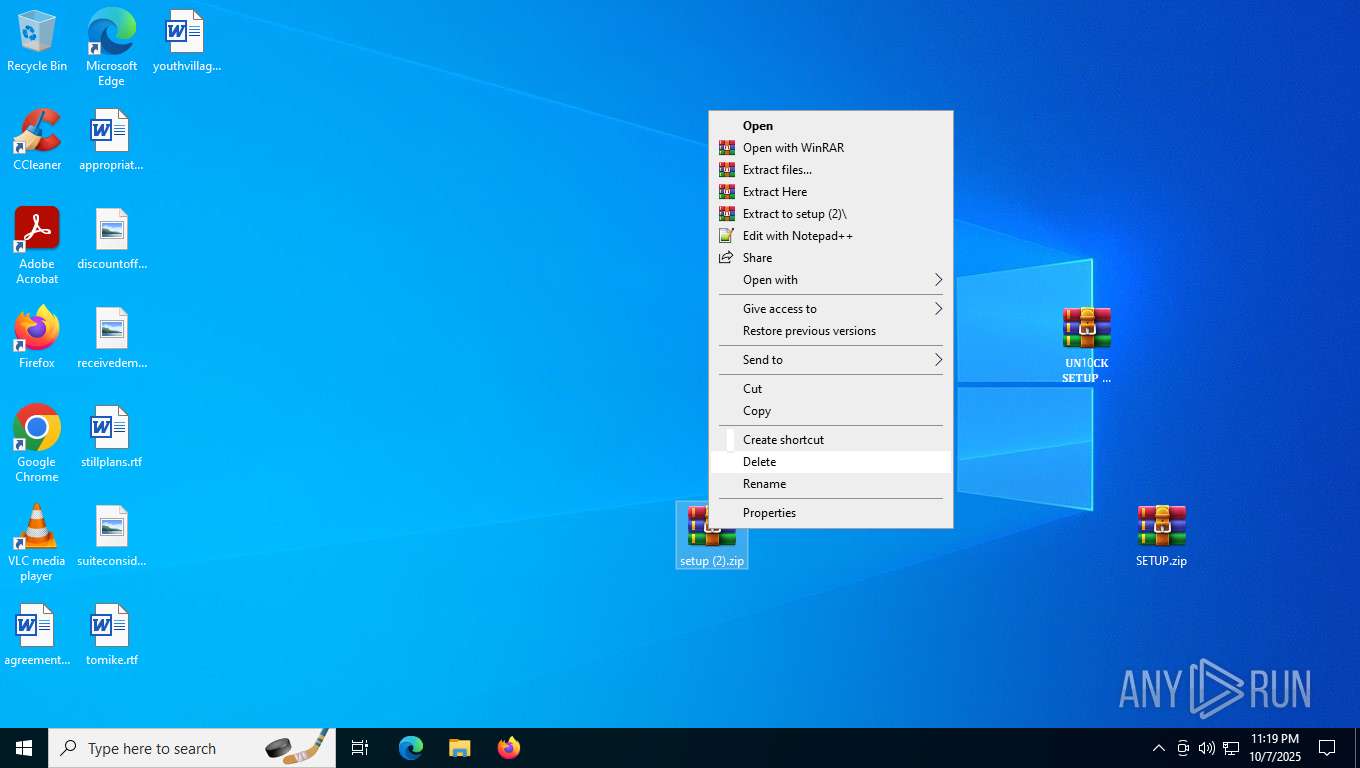
Manual execution by a user
- WinRAR.exe (PID: 3264)
- WinRAR.exe (PID: 1136)
- WinRAR.exe (PID: 2152)
- setup (2).exe (PID: 7464)
- WinRAR.exe (PID: 3120)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3264)
Checks supported languages
- setup (2).exe (PID: 7464)
- Mainland.scr (PID: 2164)
- extrac32.exe (PID: 5264)
- Mainland.scr (PID: 8912)
- identity_helper.exe (PID: 8788)
Create files in a temporary directory
- setup (2).exe (PID: 7464)
- extrac32.exe (PID: 5264)
Reads the computer name
- Mainland.scr (PID: 2164)
- extrac32.exe (PID: 5264)
- identity_helper.exe (PID: 8788)
- Mainland.scr (PID: 8912)
Reads the software policy settings
- explorer.exe (PID: 5156)
- HelpPane.exe (PID: 5584)
- Mainland.scr (PID: 8912)
- slui.exe (PID: 6240)
Reads mouse settings
- Mainland.scr (PID: 2164)
Checks proxy server information
- explorer.exe (PID: 5156)
- Mainland.scr (PID: 8912)
- slui.exe (PID: 6240)
Creates files or folders in the user directory
- explorer.exe (PID: 5156)
- Mainland.scr (PID: 8912)
Reads the machine GUID from the registry
- HelpPane.exe (PID: 5584)
- Mainland.scr (PID: 8912)
Application launched itself
- msedge.exe (PID: 2364)
Reads Environment values
- identity_helper.exe (PID: 8788)
Creates files in the program directory
- Mainland.scr (PID: 8912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:10:07 22:05:38 |
| ZipCRC: | 0xca10ffbd |
| ZipCompressedSize: | 11723 |
| ZipUncompressedSize: | 14974 |
| ZipFileName: | K3Y_2056.docx |
Total processes
209
Monitored processes
39
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
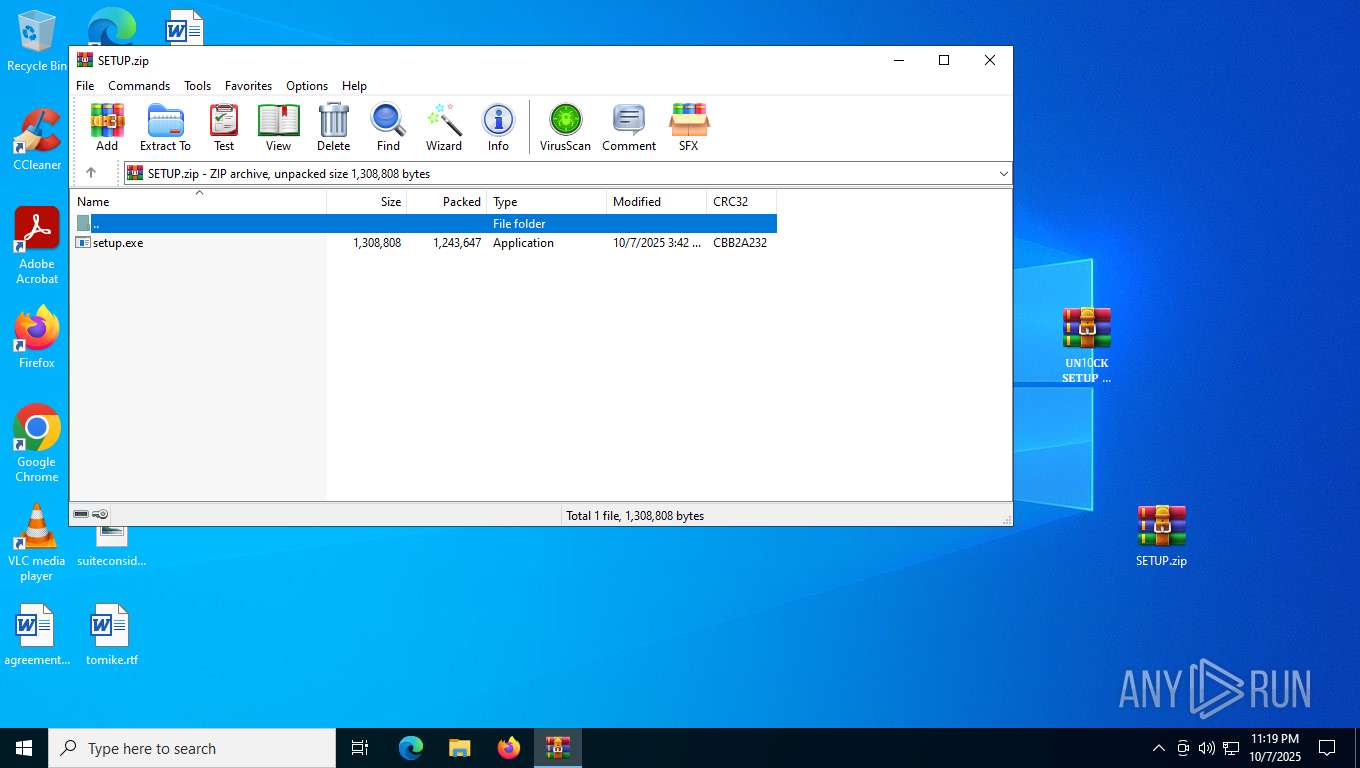
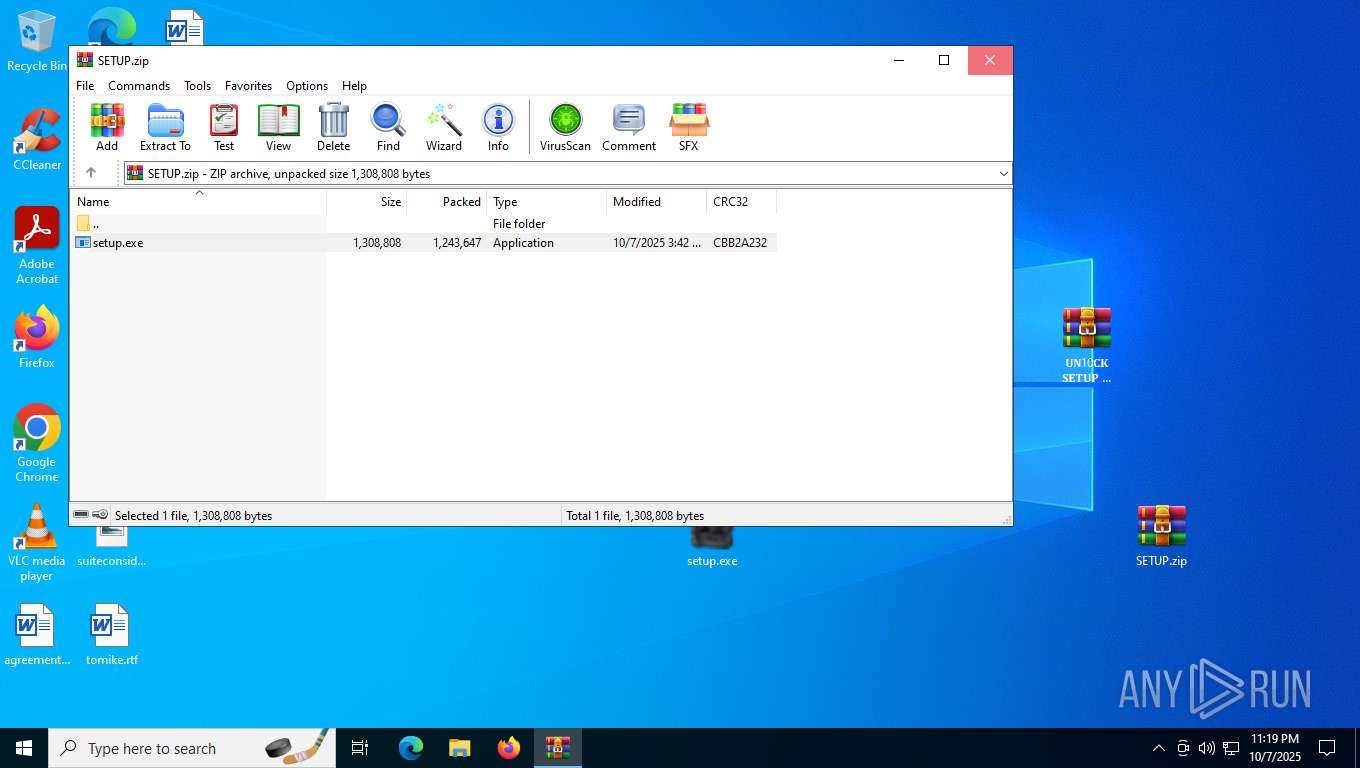
| 1136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\𝐔𝐍10𝐂𝐊 𝐒𝐄𝐓𝐔𝐏 𝐇𝐄𝐑𝐄.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1380 | attrib /64)6377266) | C:\Windows\System32\attrib.exe | — | setup (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
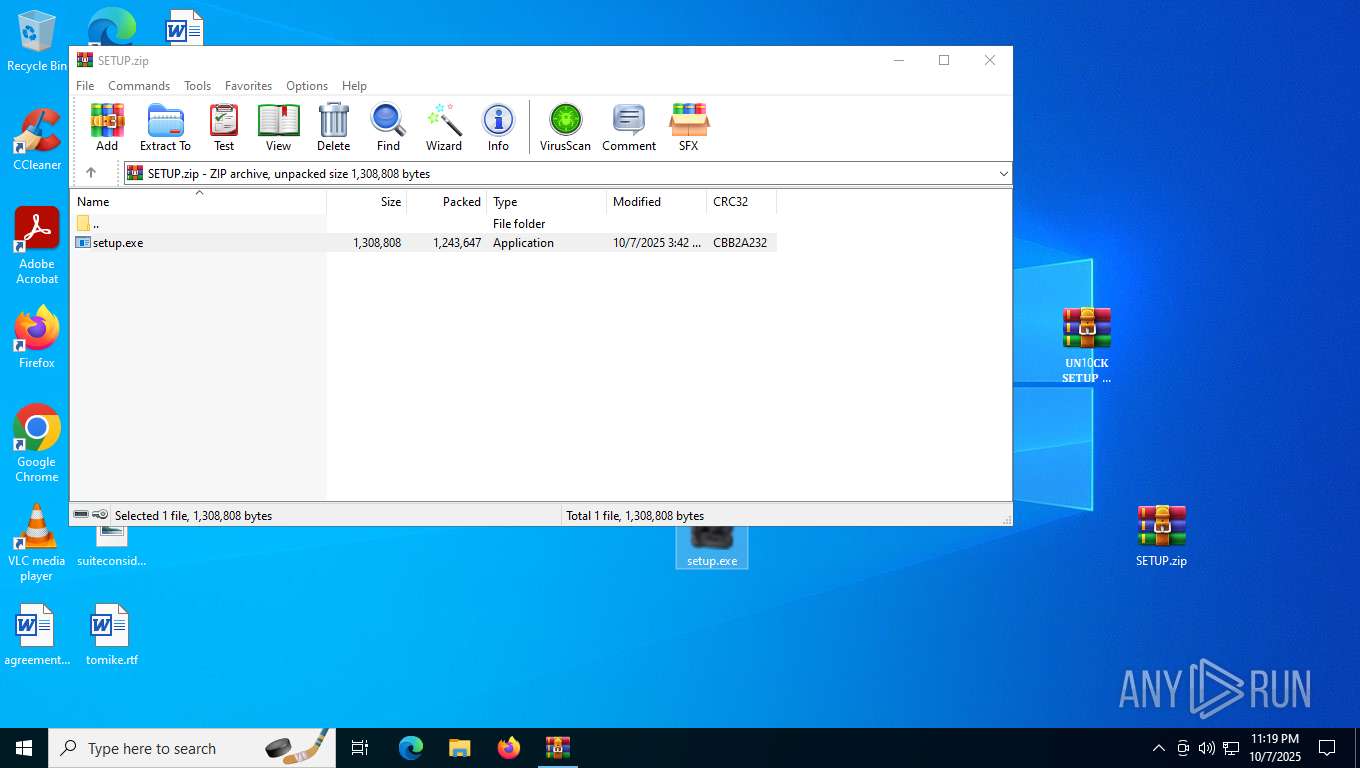
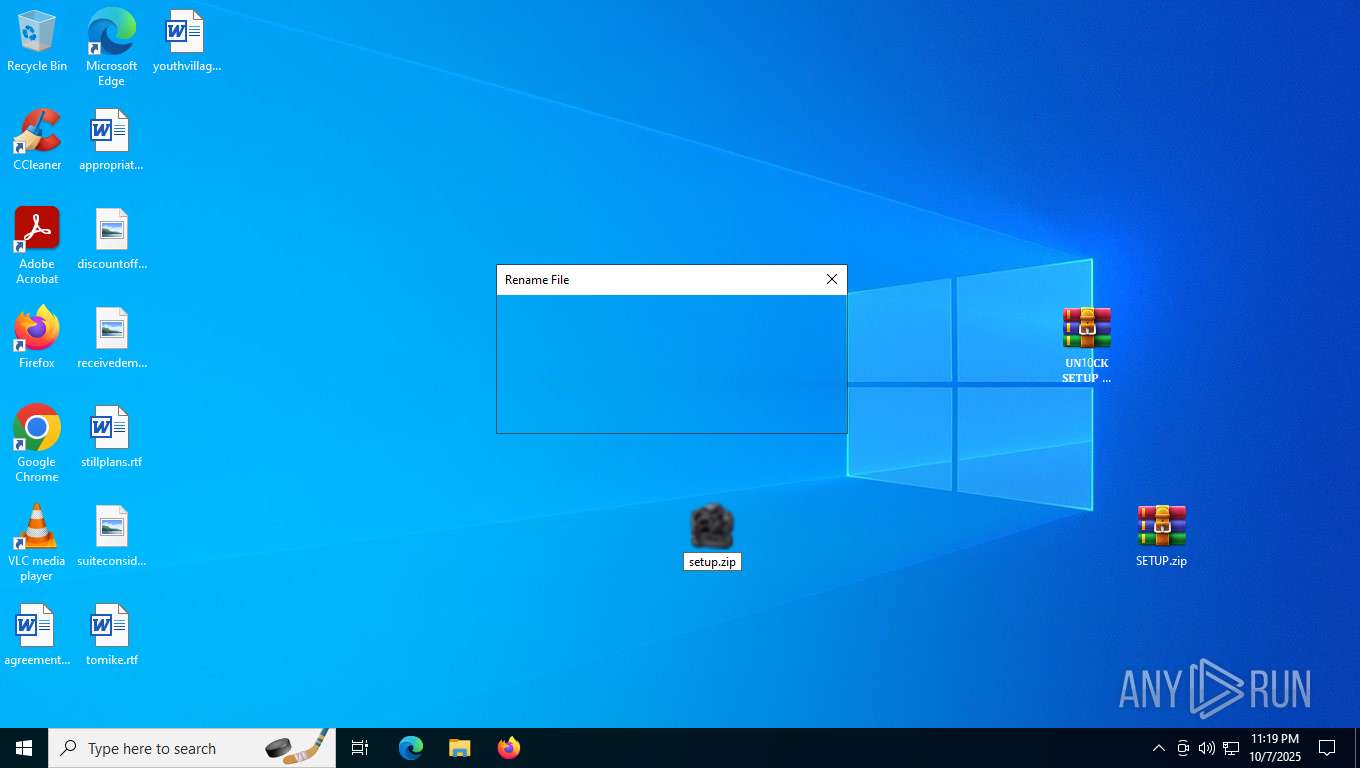
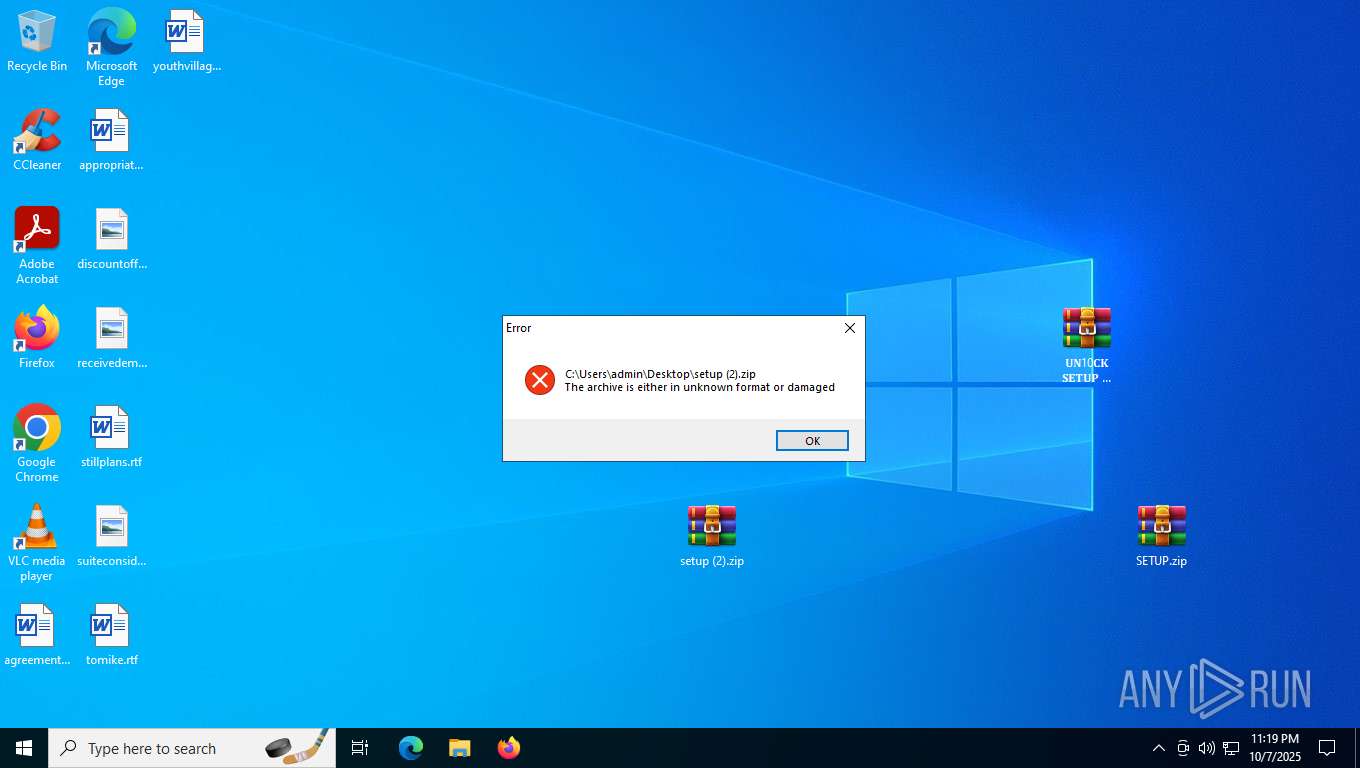
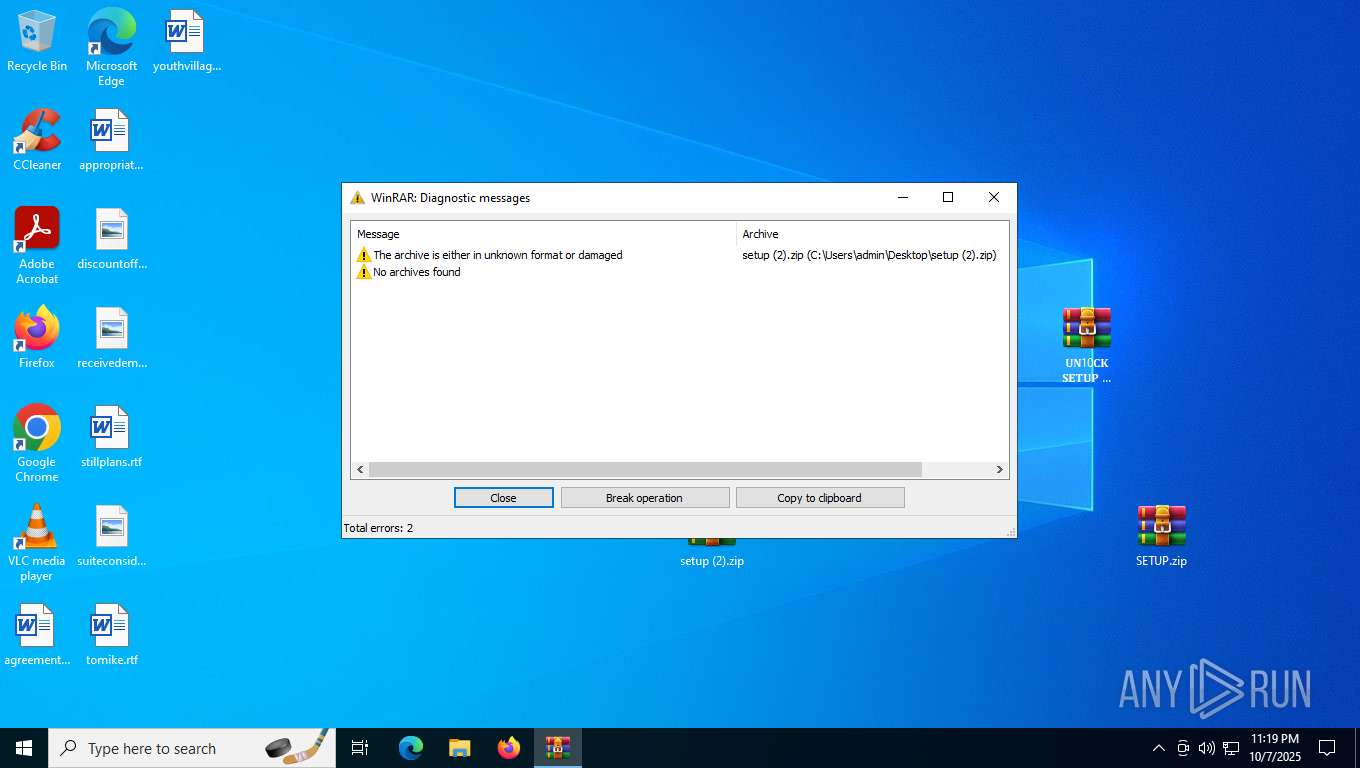
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\setup (2).zip" "C:\Users\admin\Desktop\setup (2)\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 2164 | Mainland.scr C | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\288641\Mainland.scr | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 2180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3592,i,240207294848025369,1035836526942925222,262144 --variations-seed-version --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2284,i,240207294848025369,1035836526942925222,262144 --variations-seed-version --mojo-platform-channel-handle=2424 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument microsoft-edge:https://go.microsoft.com/fwlink/?LinkId=528881 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | HelpPane.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 741
Read events
30 594
Write events
134
Delete events
13
Modification events
| (PID) Process: | (5156) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000400E6 |
| Operation: | write | Name: | VirtualDesktop |
Value: 100000003030445694ACE2E2F1AF094C9D246B54025DD75A | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\S𝙴TUP F!LE P𝚊𝚂5 -►2056 D0WN10AD.zip | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
9
Suspicious files
162
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5156 | explorer.exe | — | ||
MD5:— | SHA256:— | |||
| 5156 | explorer.exe | C:\Users\admin\Desktop\𝐔𝐍10𝐂𝐊 𝐒𝐄𝐓𝐔𝐏 𝐇𝐄𝐑𝐄.zip | compressed | |
MD5:FC178C3569976F3D6F2AA2A8C45FE992 | SHA256:C35DEB591A3C7220C915FD8EBBC5760509D48BF86C6F23B36F65D6754C6A12CF | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.28009\𝐔𝐍10𝐂𝐊 𝐒𝐄𝐓𝐔𝐏 𝐇𝐄𝐑𝐄.zip | compressed | |
MD5:FC178C3569976F3D6F2AA2A8C45FE992 | SHA256:C35DEB591A3C7220C915FD8EBBC5760509D48BF86C6F23B36F65D6754C6A12CF | |||
| 1136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1136.28786\SETUP.zip | compressed | |
MD5:57AAC4C8D28DCB96B2FA2B59AD8169FE | SHA256:DD3674ADC8921EC3E60AE60A645DF9CE9D7C2BD1BF28133CAF75FB82C5D13BAC | |||
| 5156 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 3264 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3264.29706\setup.exe | executable | |
MD5:A2462B636FC46AF4E005F0218F43C62F | SHA256:41D223F5A7540D5CEF87B3FD0A0E1ED42001AC2CD8AE8DF8058A5F9498A34FF3 | |||
| 7464 | setup (2).exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Suites.pptx | binary | |
MD5:3C279F7204E2F1A20E5D55BE1E9A83DE | SHA256:C457CEEB3E71DD4B5CCAB01671C33FACC7C19C95456BCAACDFE8E6A7C4FE30C0 | |||
| 5156 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:56D2845A18A5C086F4B980EE2B5A09B6 | SHA256:4935ED751595899A558D7E38F70E2865D1DA61BEA4D513C8016E2DAD47098919 | |||
| 5156 | explorer.exe | C:\Users\admin\Desktop\setup.exe | executable | |
MD5:A2462B636FC46AF4E005F0218F43C62F | SHA256:41D223F5A7540D5CEF87B3FD0A0E1ED42001AC2CD8AE8DF8058A5F9498A34FF3 | |||
| 5156 | explorer.exe | C:\Users\admin\Desktop\SETUP.zip | compressed | |
MD5:57AAC4C8D28DCB96B2FA2B59AD8169FE | SHA256:DD3674ADC8921EC3E60AE60A645DF9CE9D7C2BD1BF28133CAF75FB82C5D13BAC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
133
DNS requests
106
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4432 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4584 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
8912 | Mainland.scr | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCml4zJJc8tSg%3D%3D | US | binary | 2.06 Kb | whitelisted |
2312 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:-R5XFbRiIcl8qdTUk-QCaVbHTH047esNT4t8how1W9w&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
8912 | Mainland.scr | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | binary | 1.98 Kb | whitelisted |
8912 | Mainland.scr | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAsA6S1NbXMfyjBZx8seGIY%3D | US | binary | 312 b | whitelisted |
8912 | Mainland.scr | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | binary | 2.01 Kb | whitelisted |
8912 | Mainland.scr | GET | 200 | 104.18.21.213:80 | http://e8.c.lencr.org/120.crl | unknown | binary | 23.9 Kb | whitelisted |
8912 | Mainland.scr | GET | 200 | 104.18.21.213:80 | http://e7.c.lencr.org/56.crl | unknown | binary | 23.3 Kb | whitelisted |
8912 | Mainland.scr | GET | 200 | 104.18.21.213:80 | http://e8.c.lencr.org/13.crl | unknown | binary | 21.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4212 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5224 | SearchApp.exe | 23.3.89.89:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4432 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4432 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | — | US | whitelisted |
5224 | SearchApp.exe | 23.3.89.99:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4584 | backgroundTaskHost.exe | 23.3.89.89:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4584 | backgroundTaskHost.exe | 172.66.2.5:80 | ocsp.digicert.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2428 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |