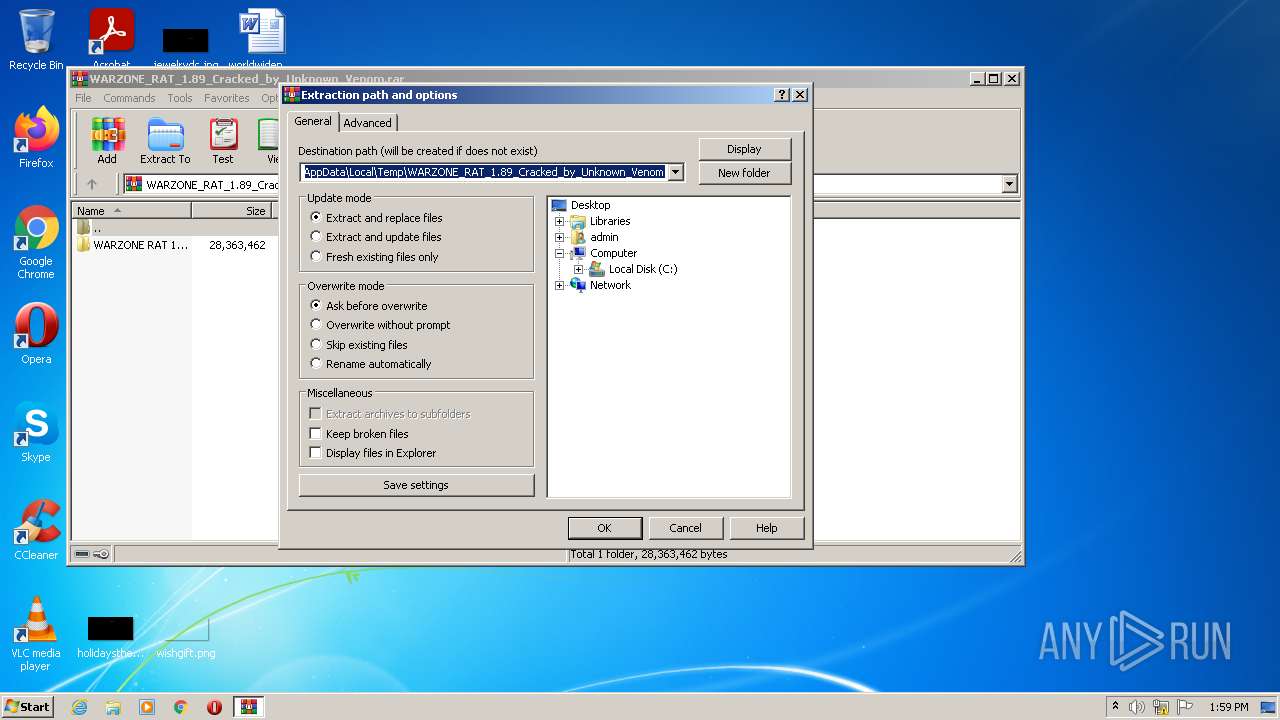
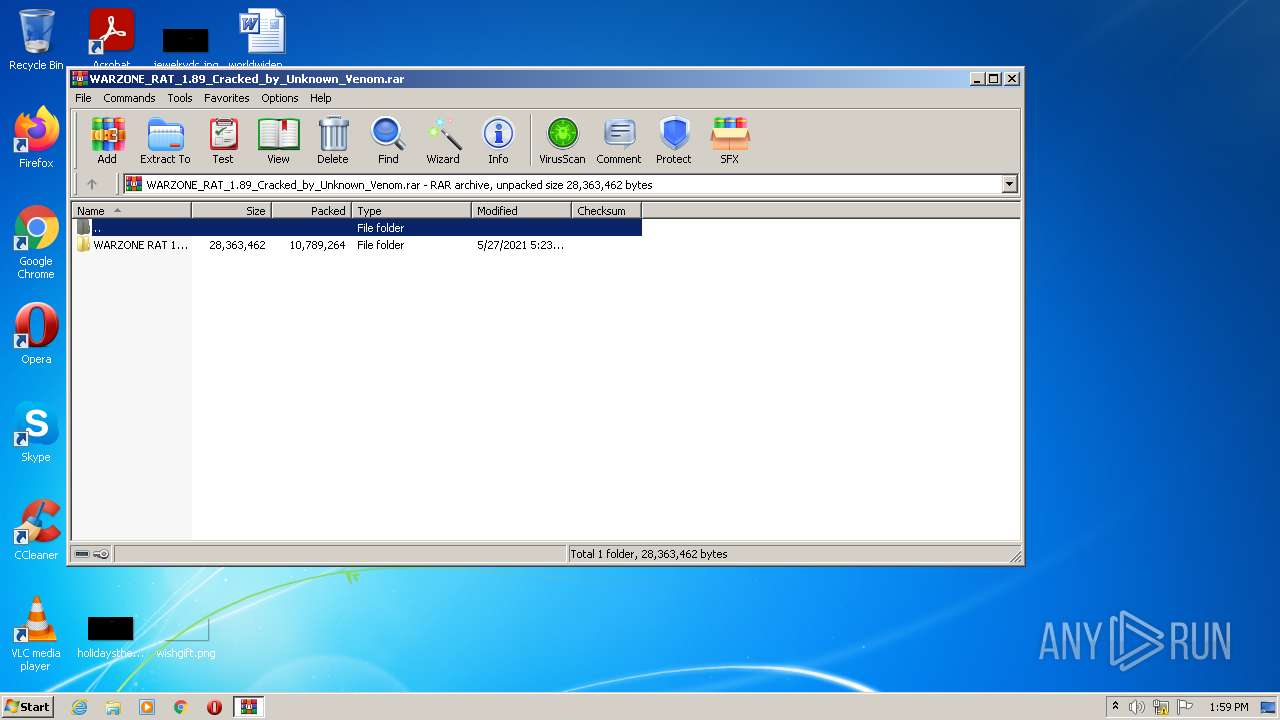
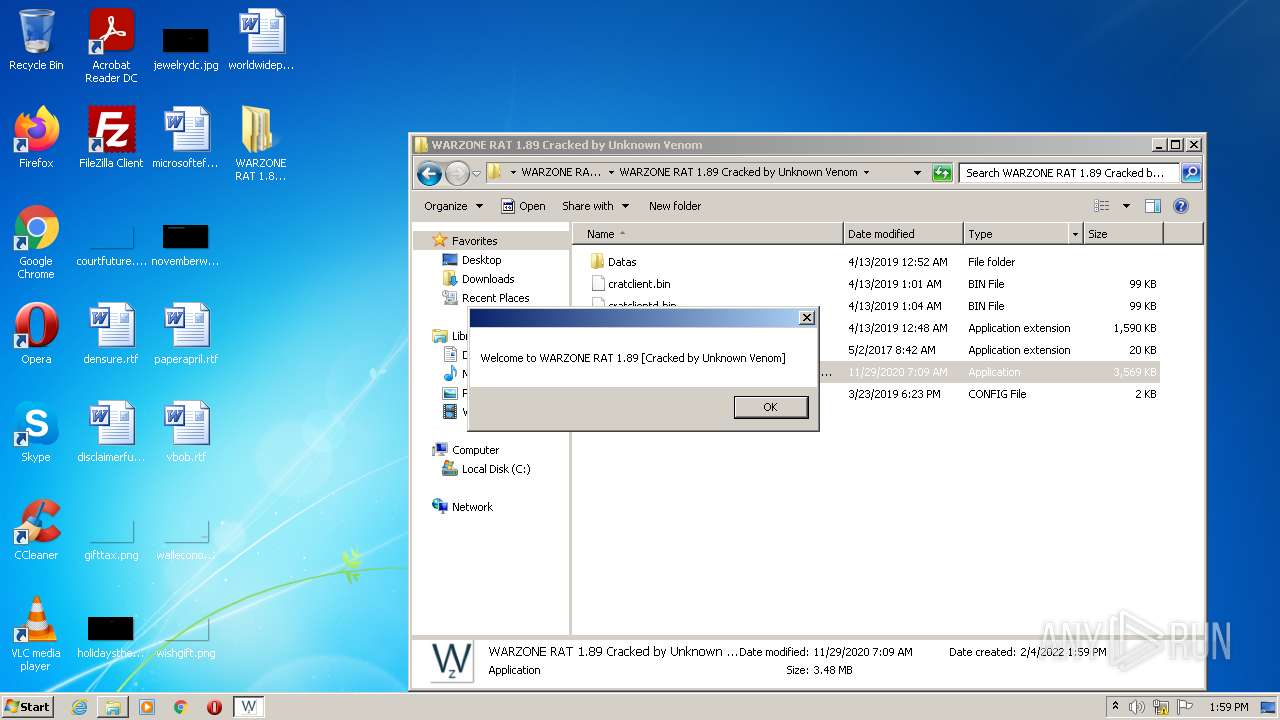
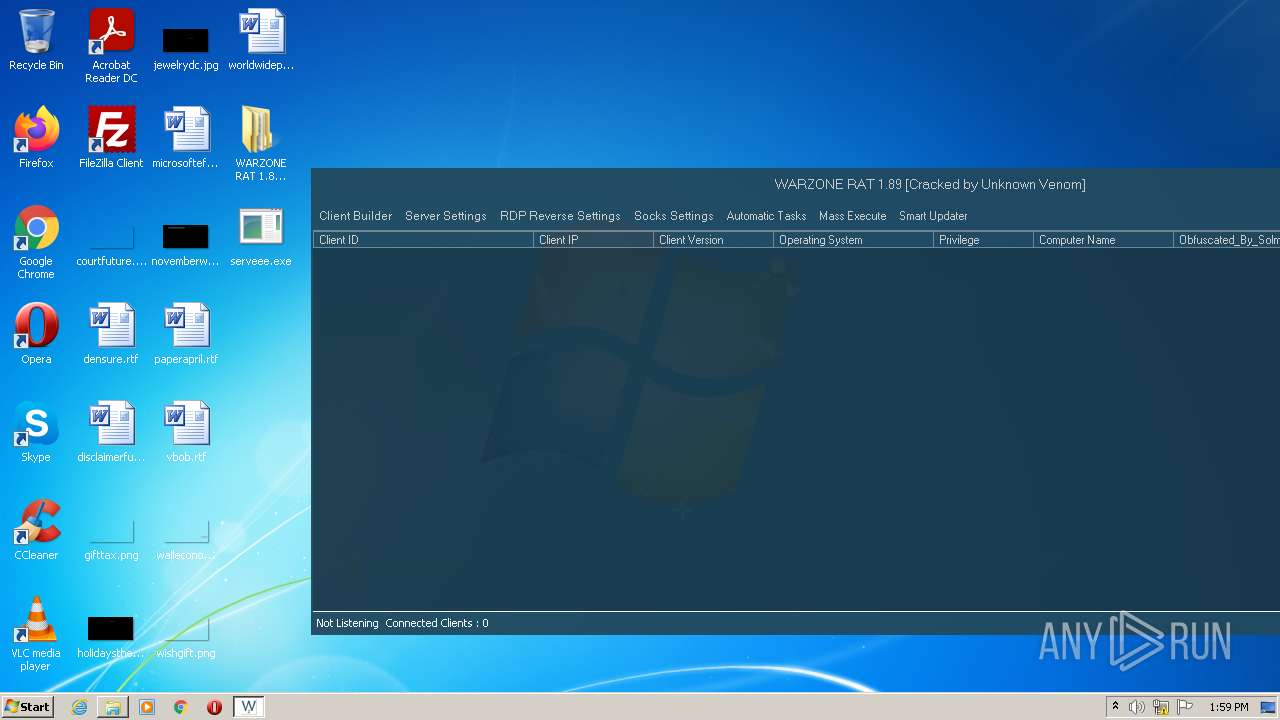
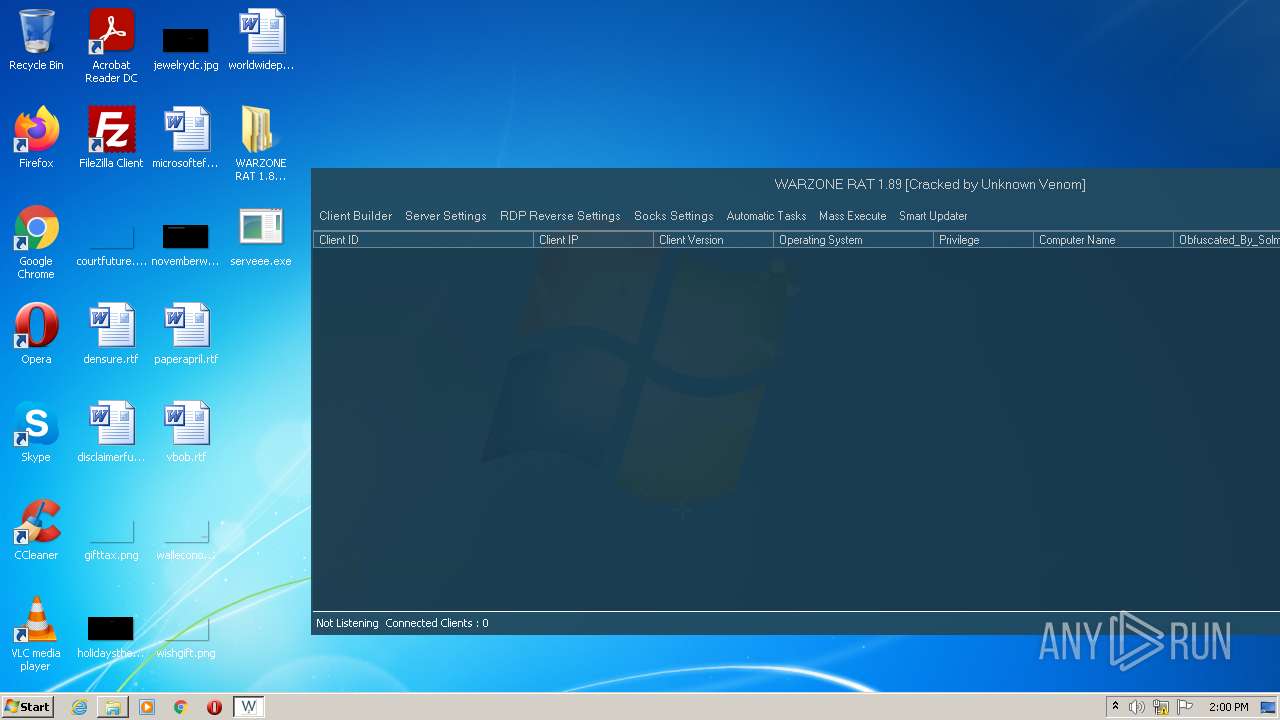
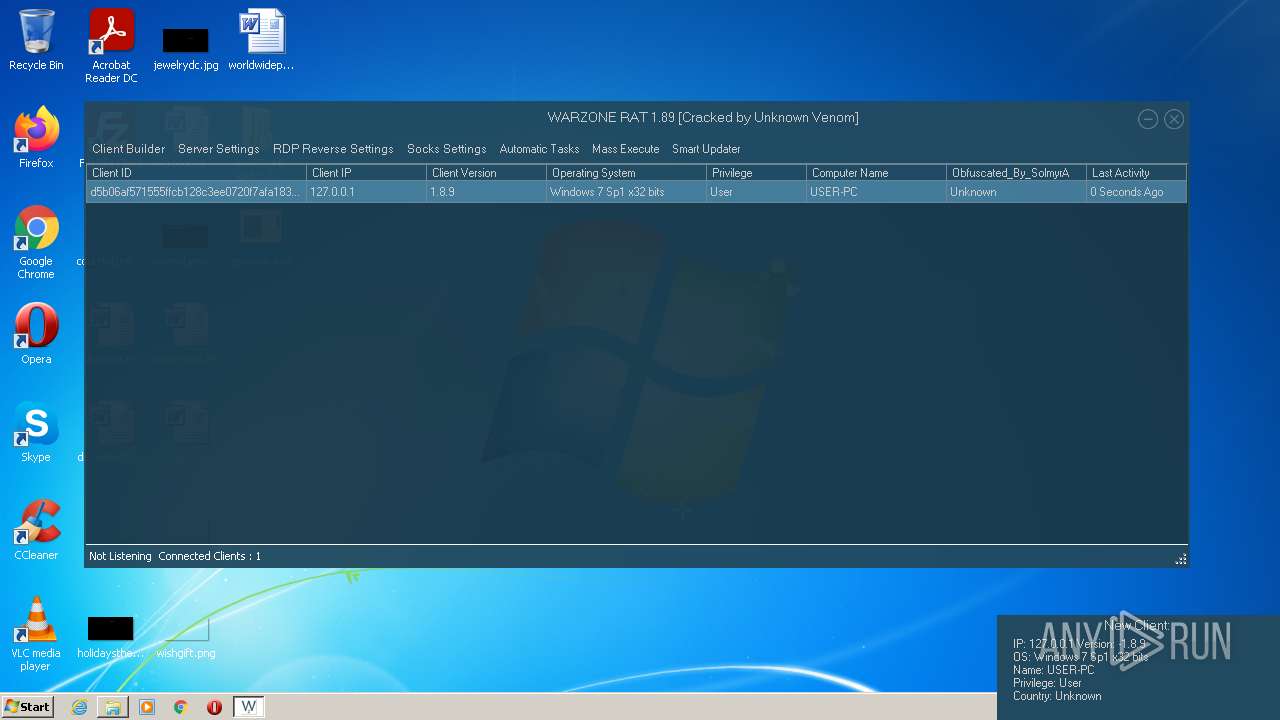
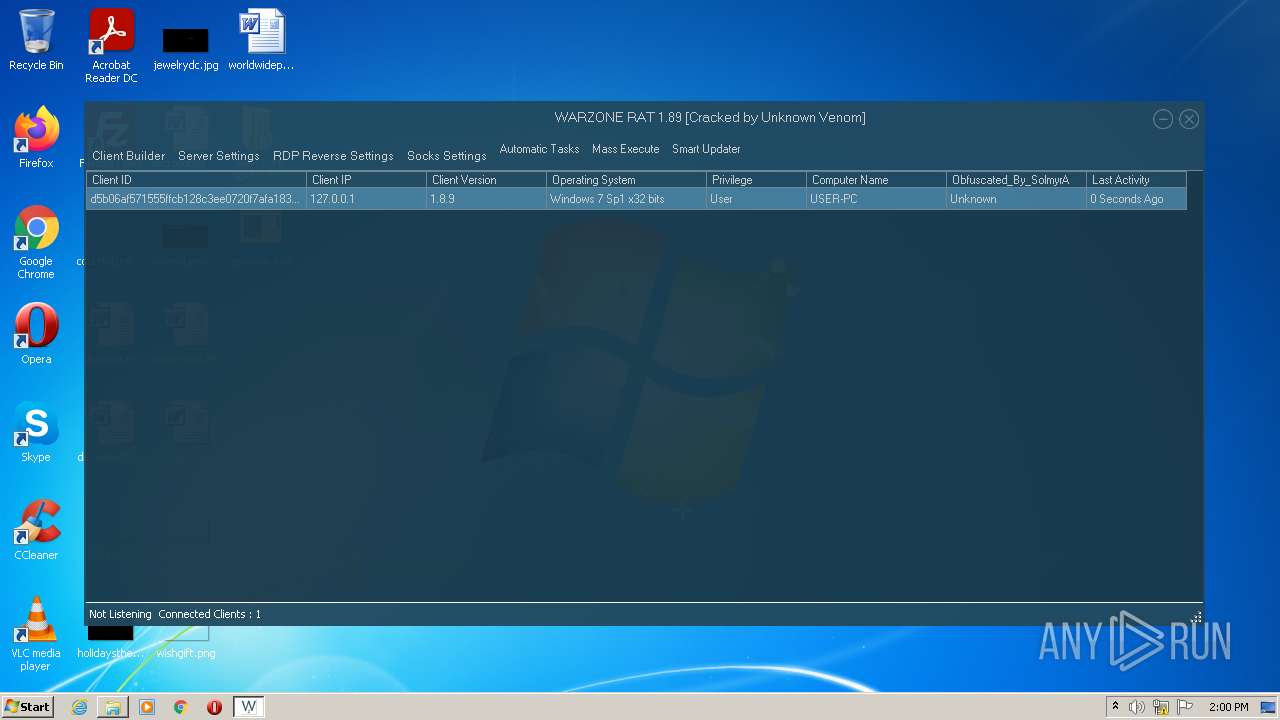
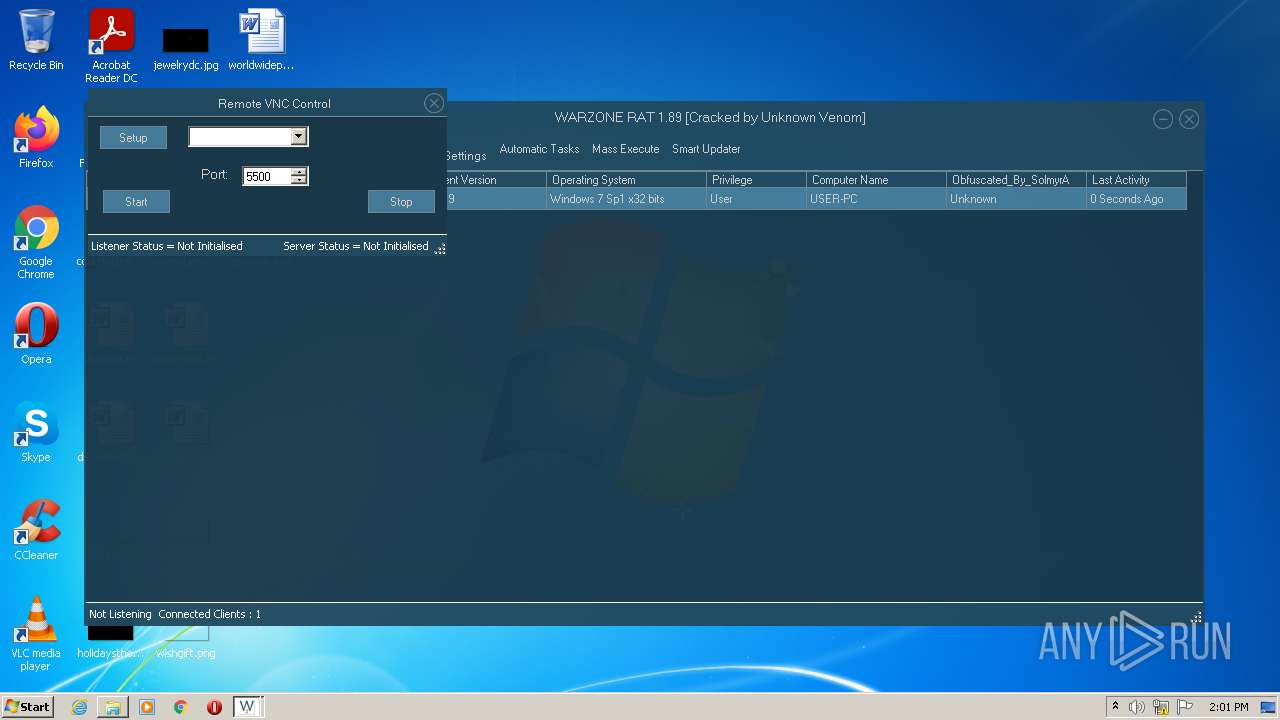
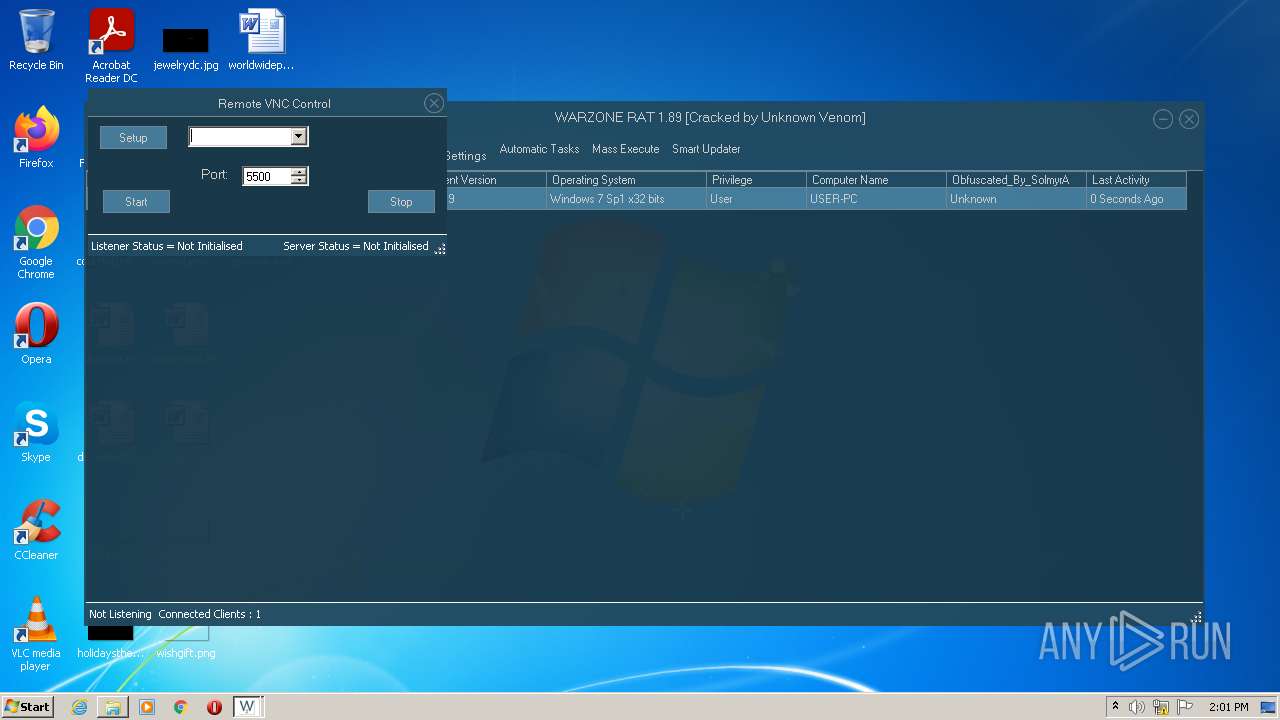
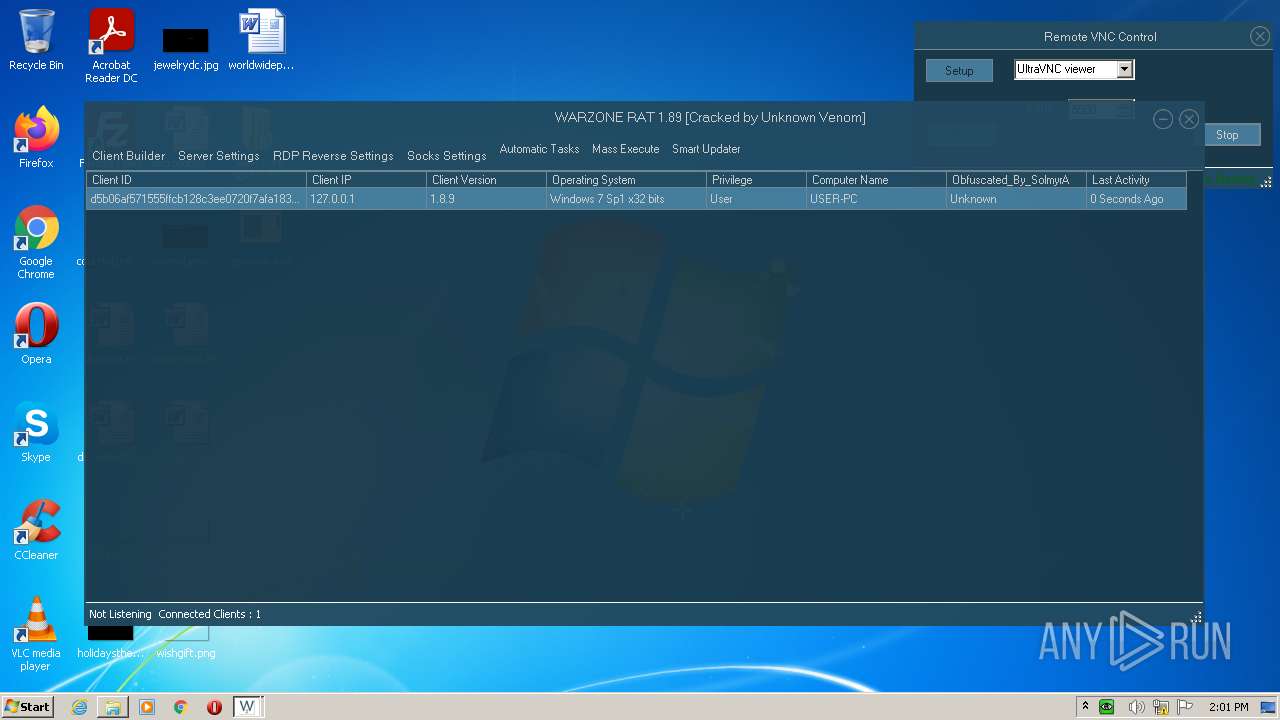
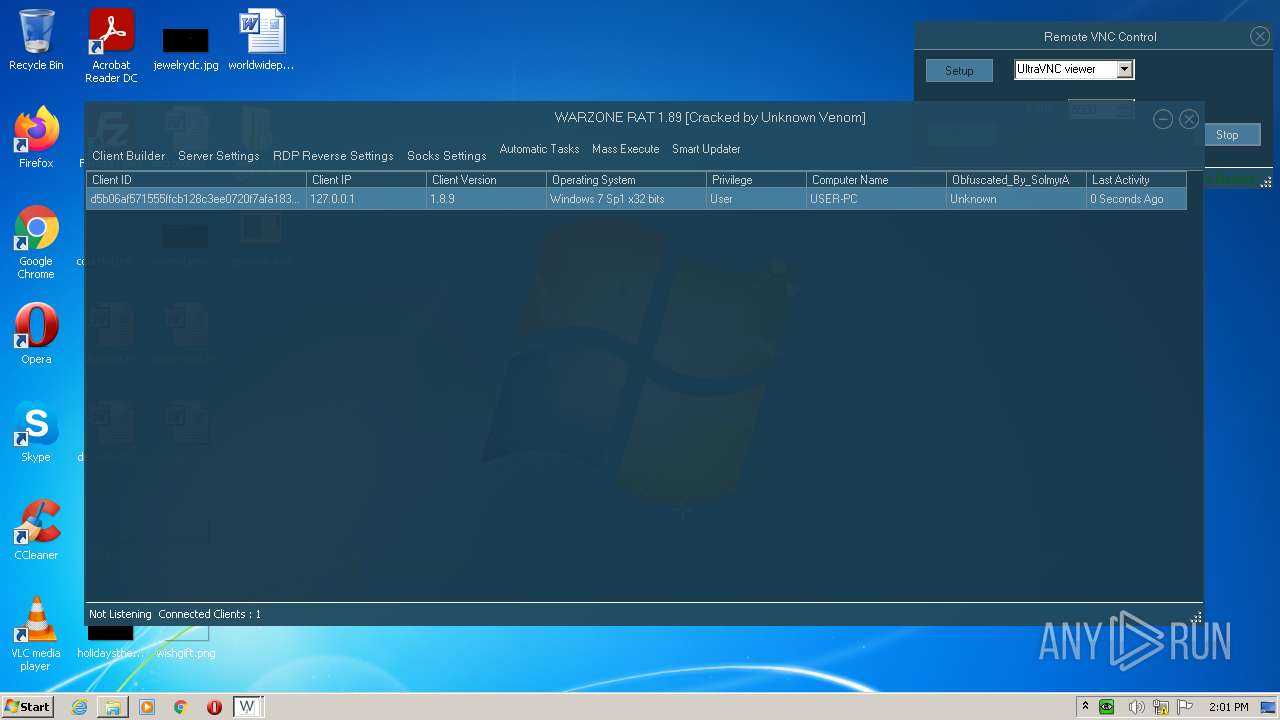
| File name: | WARZONE_RAT_1.89_Cracked_by_Unknown_Venom.rar |
| Full analysis: | https://app.any.run/tasks/a0563582-6ac2-4d15-934a-27d8ce264b4f |
| Verdict: | Malicious activity |
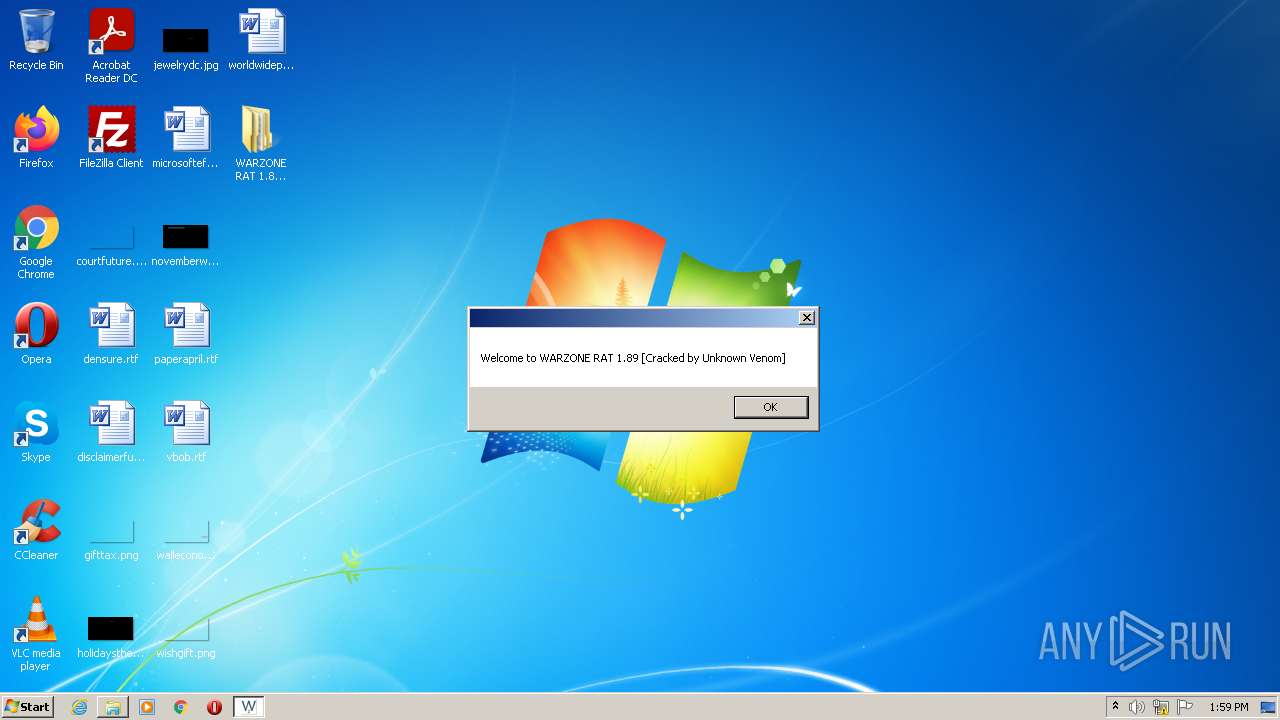
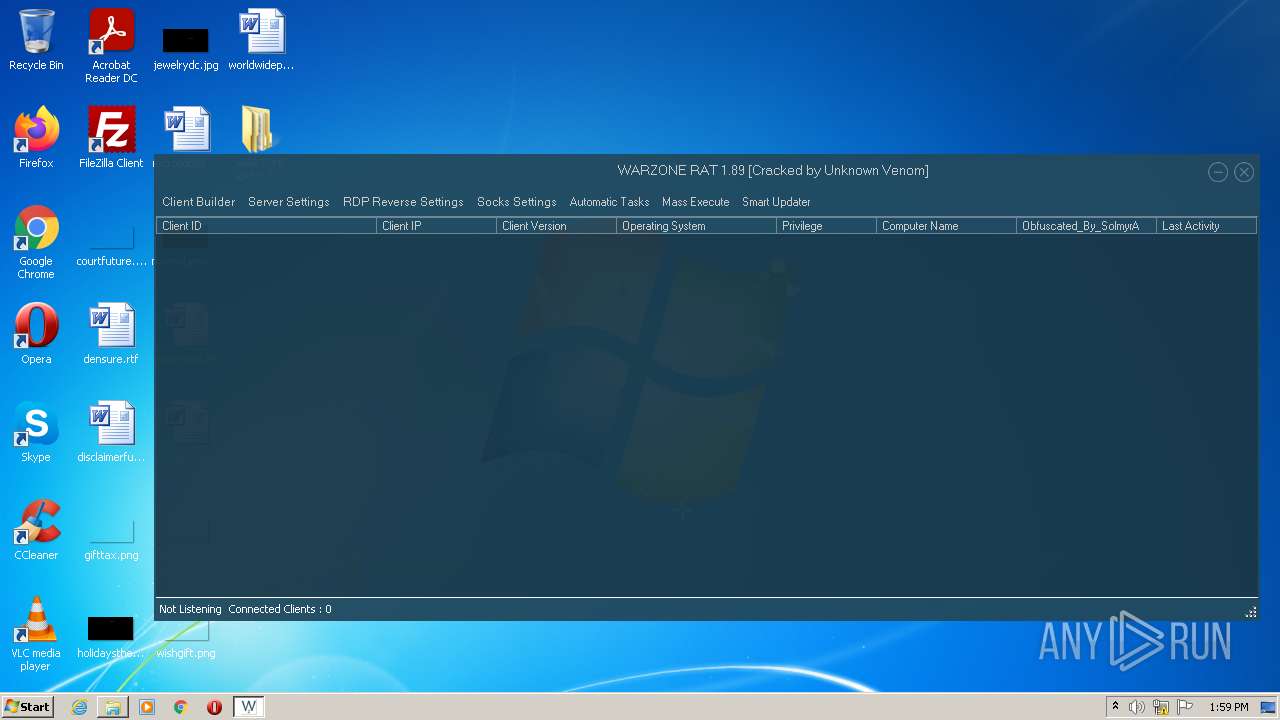
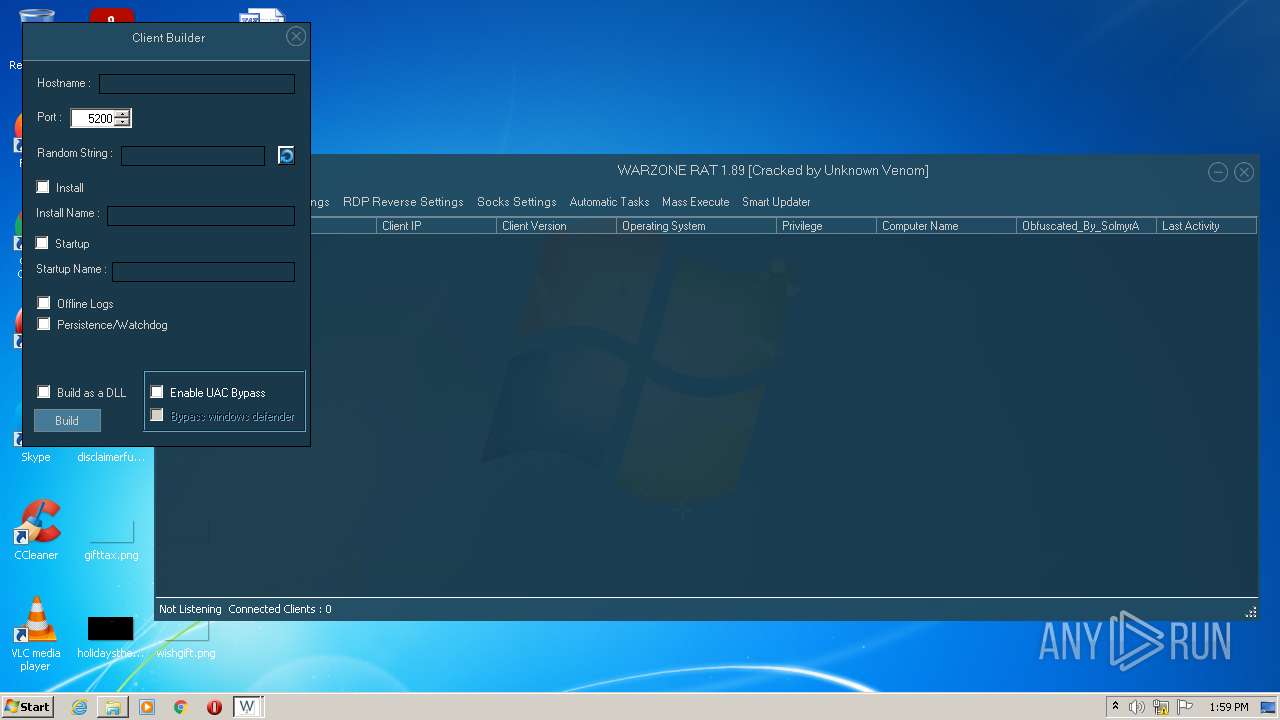
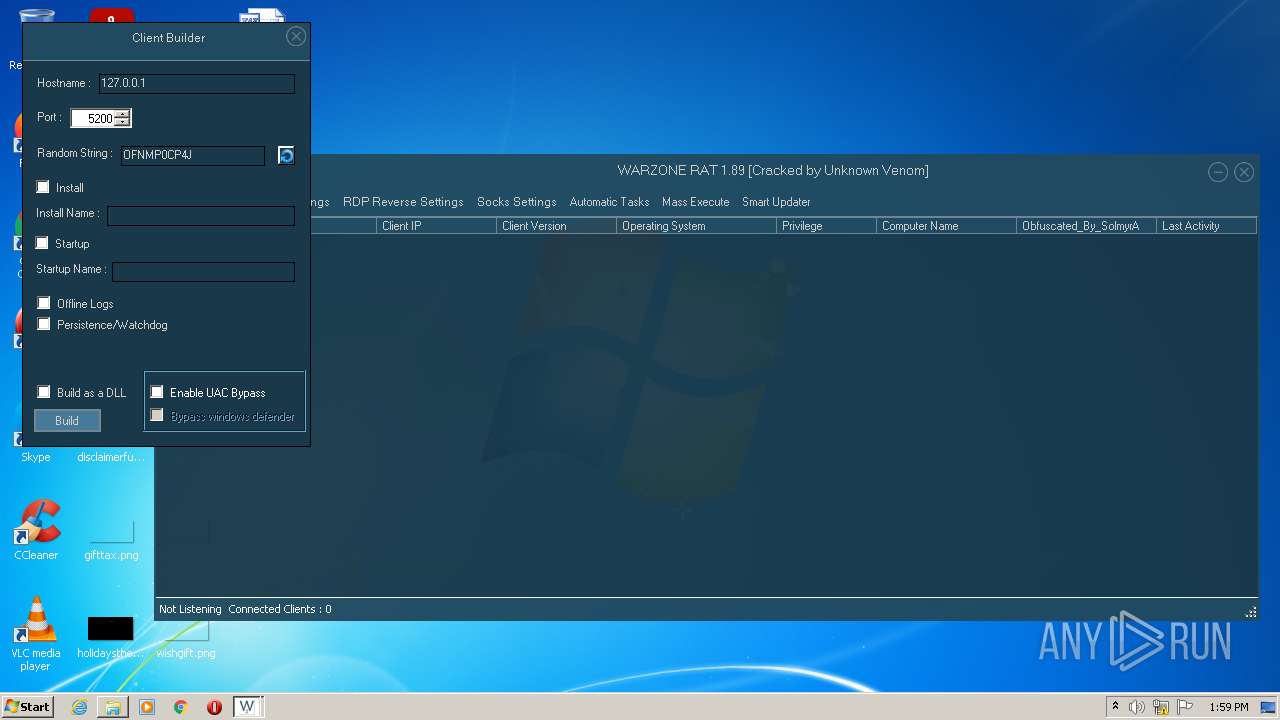
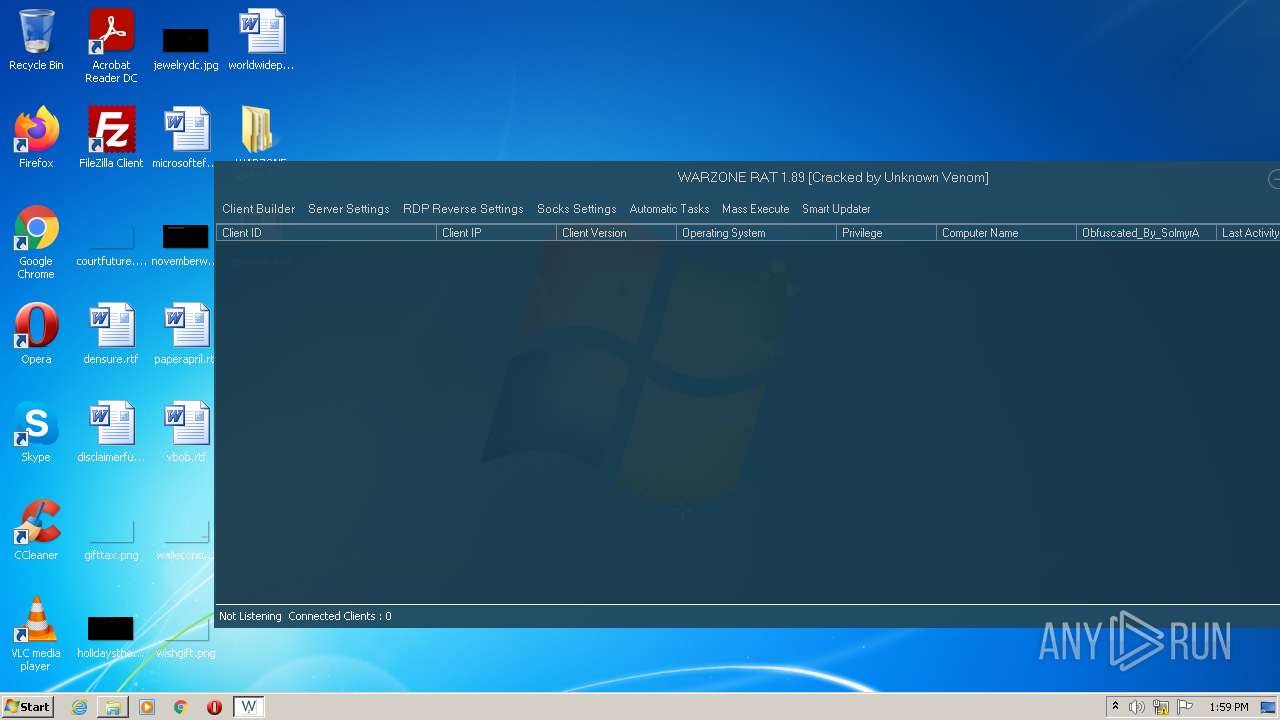
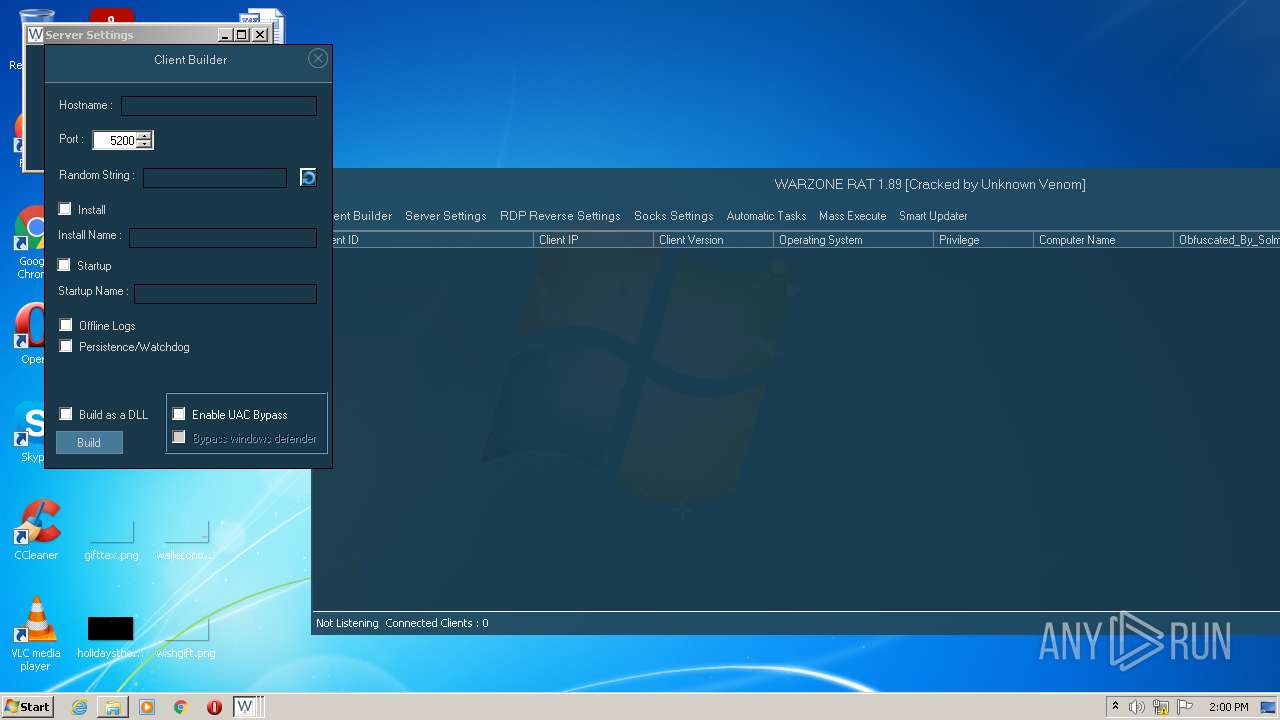
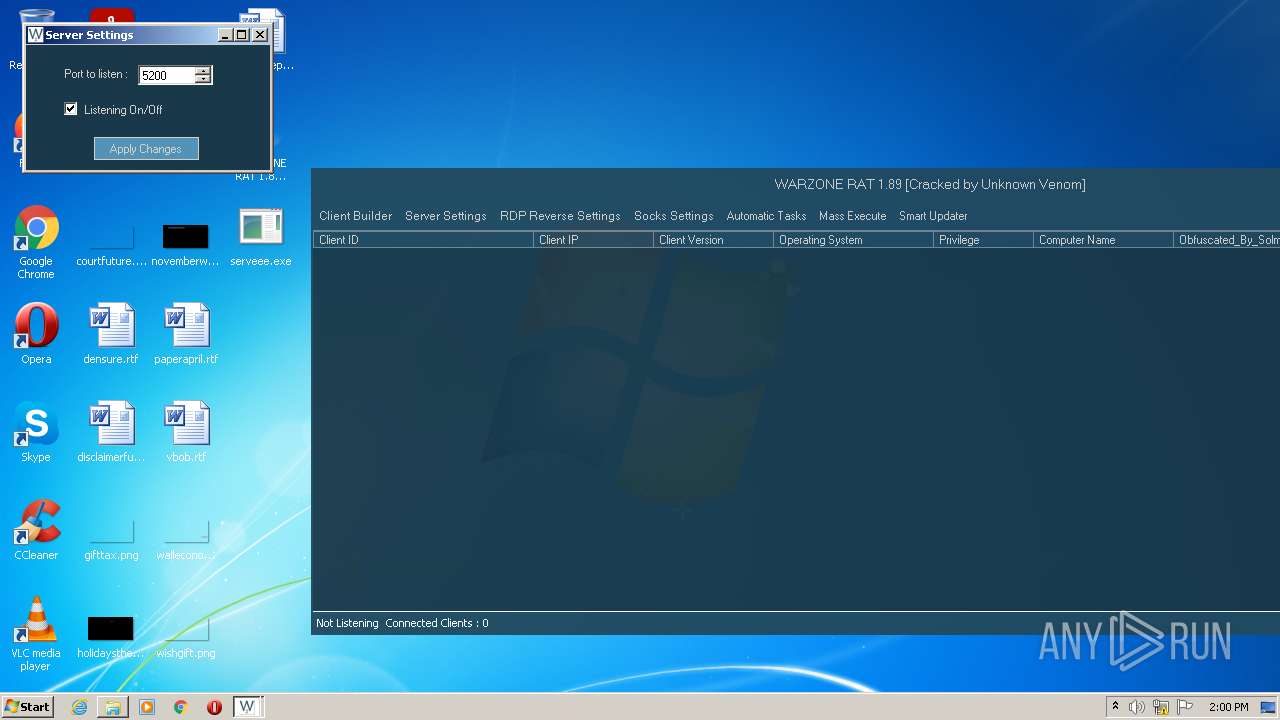
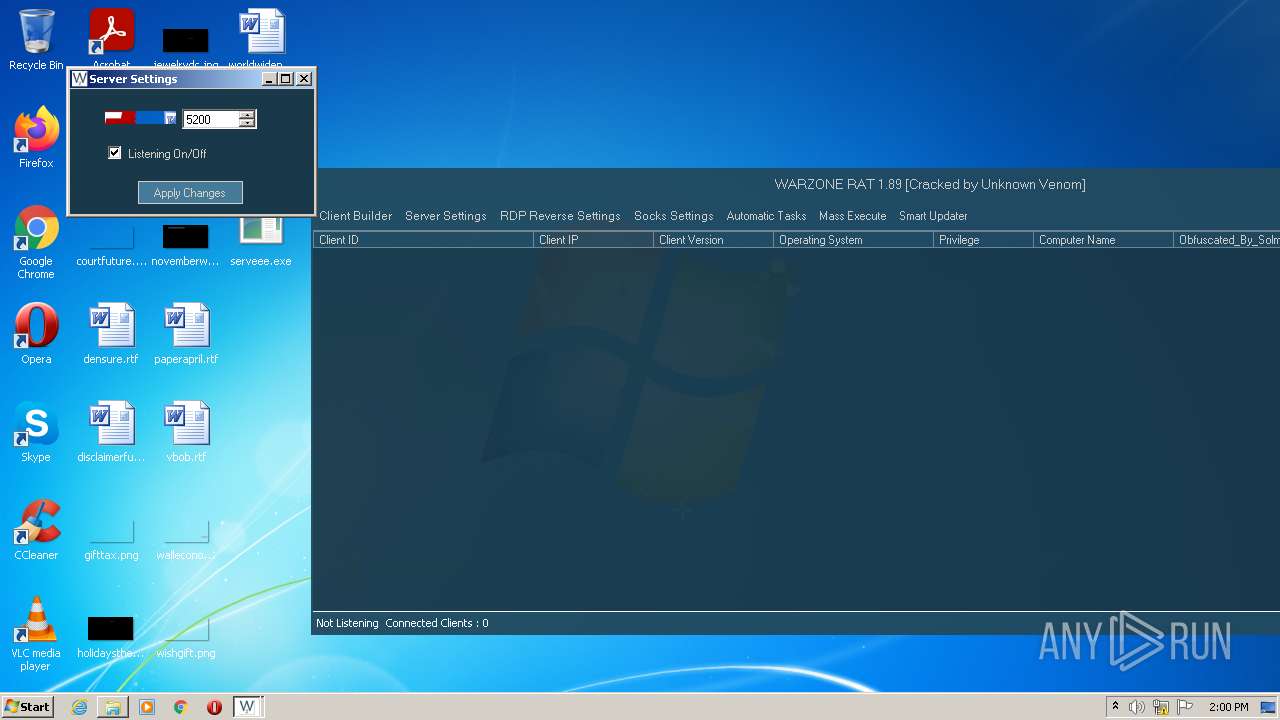
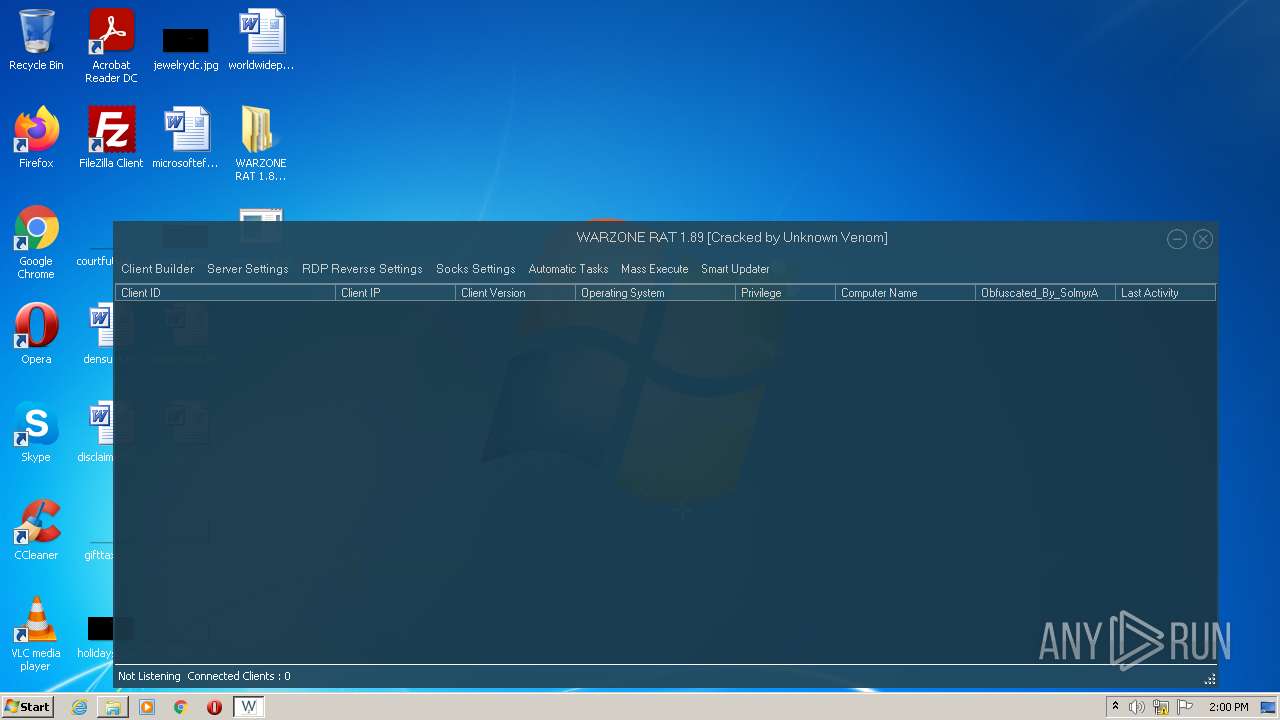
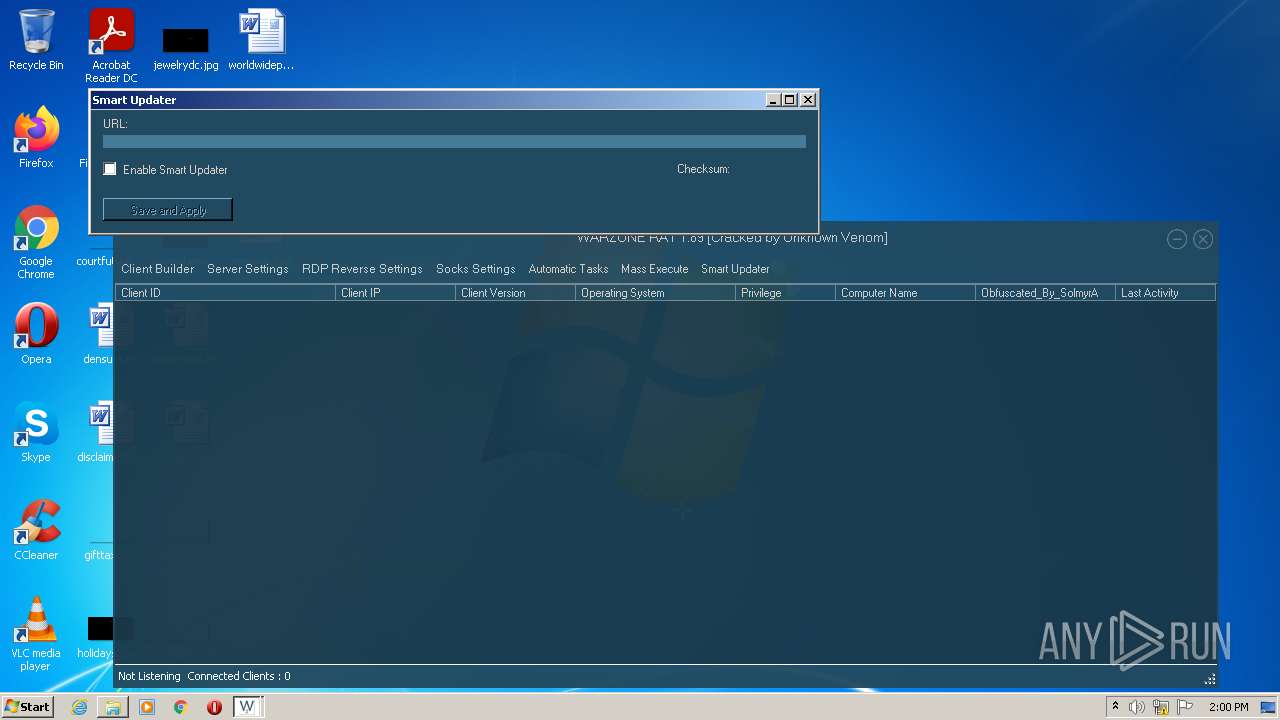
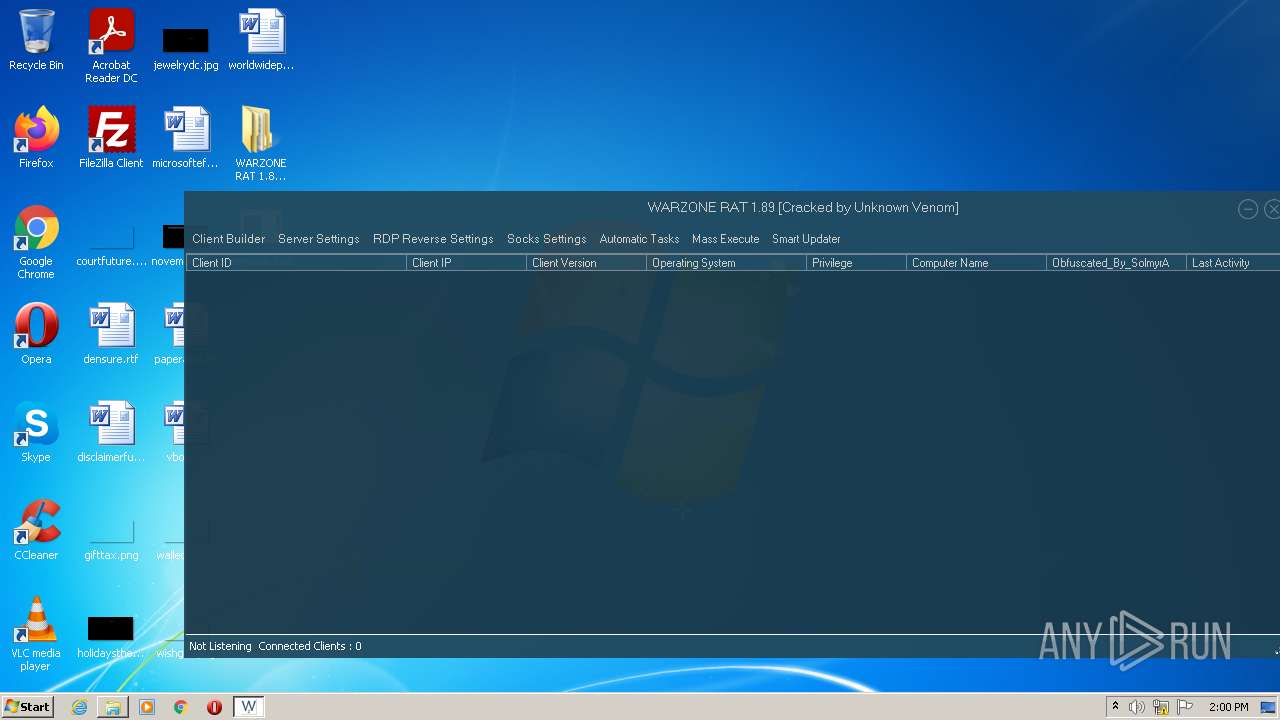
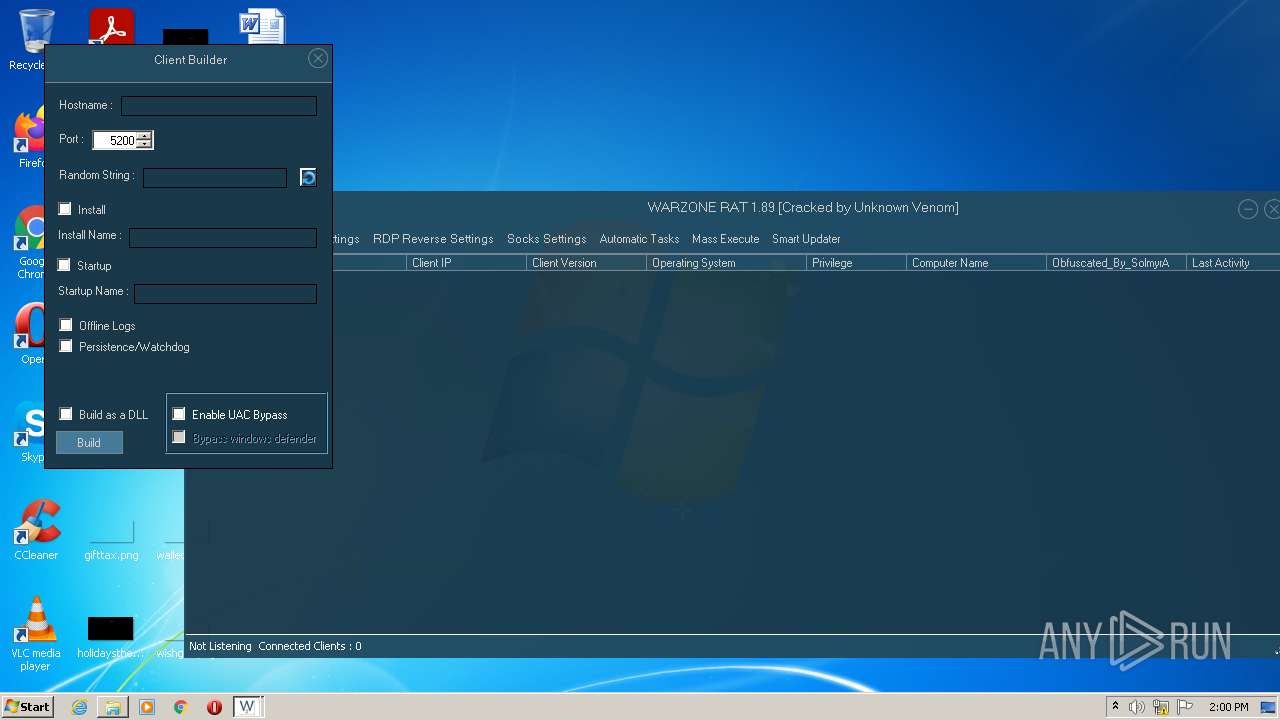
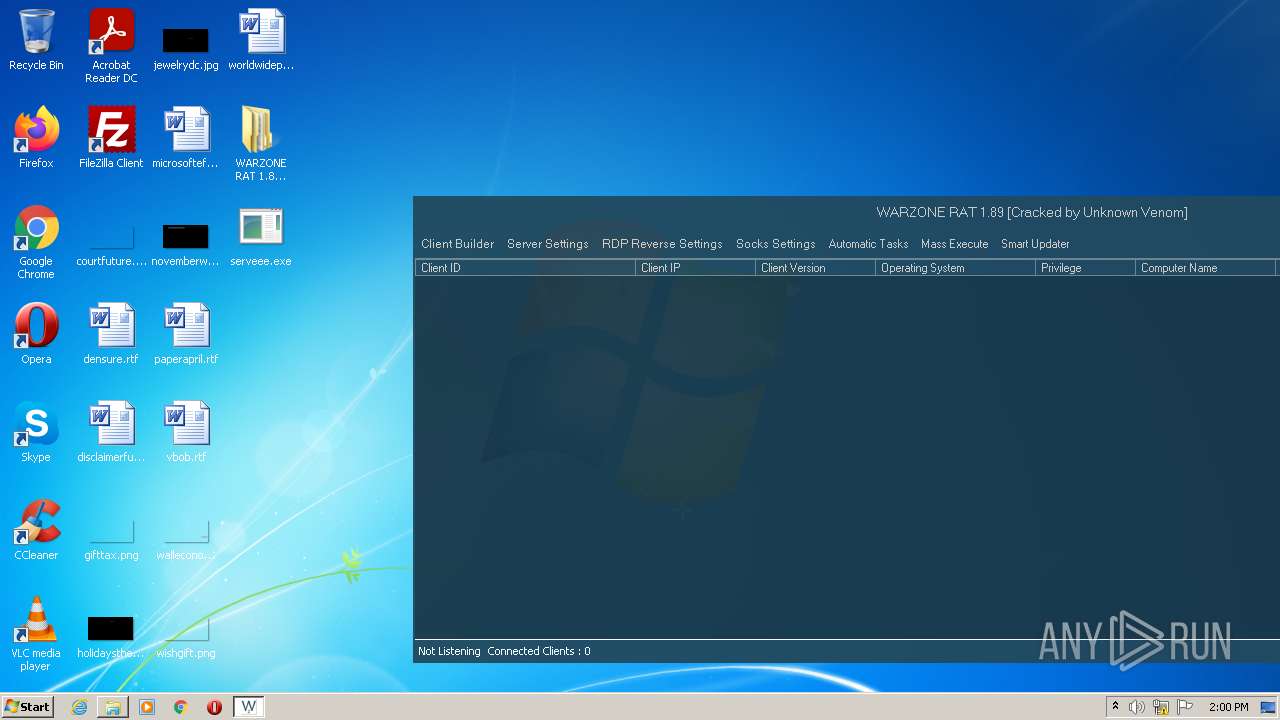
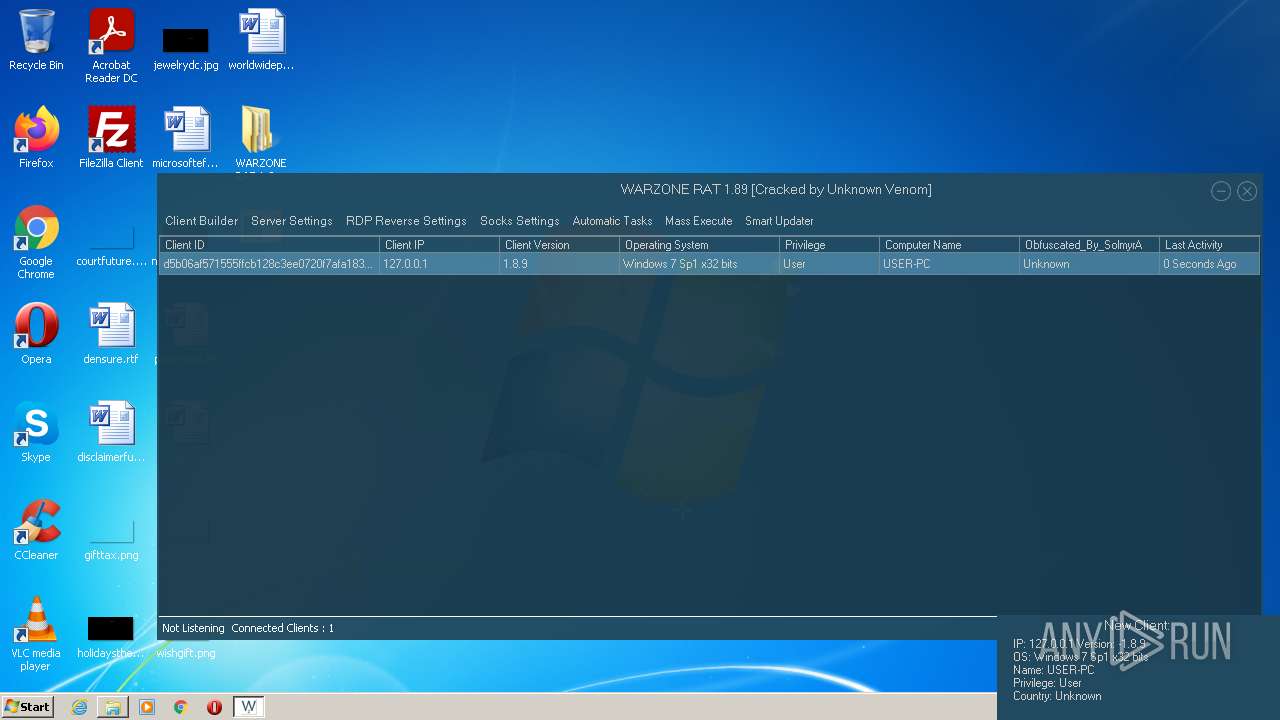
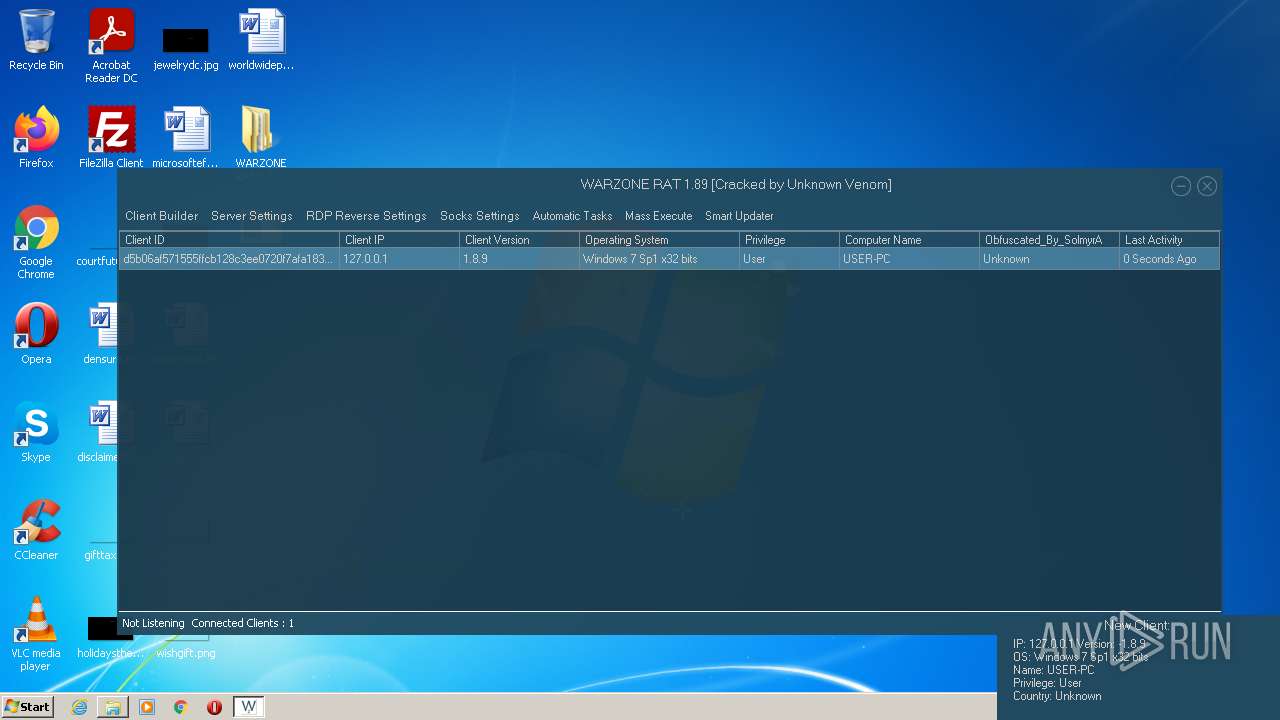
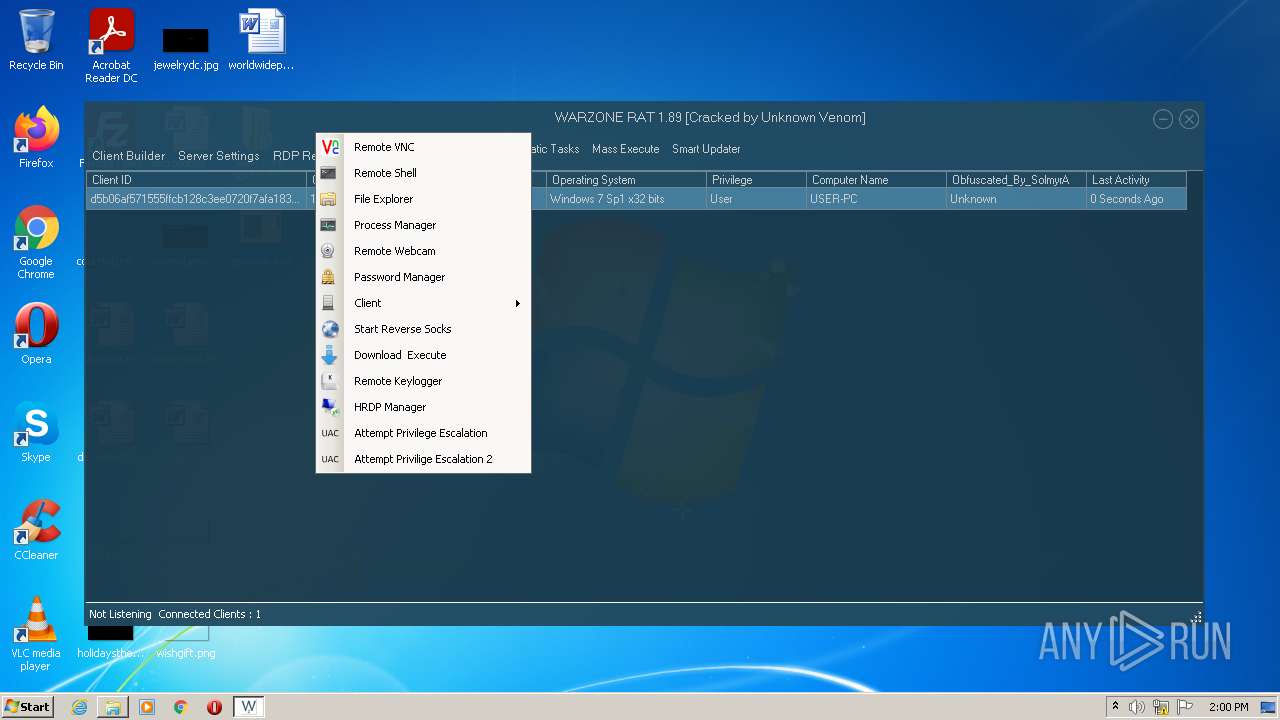
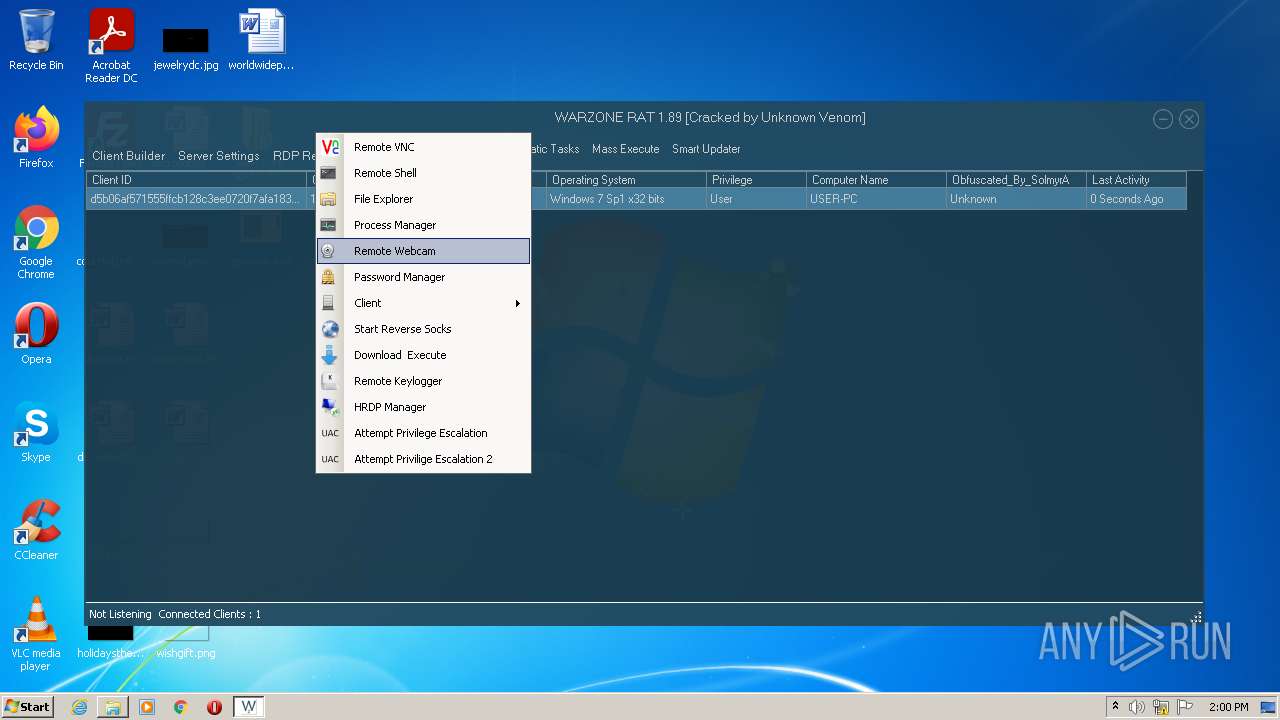
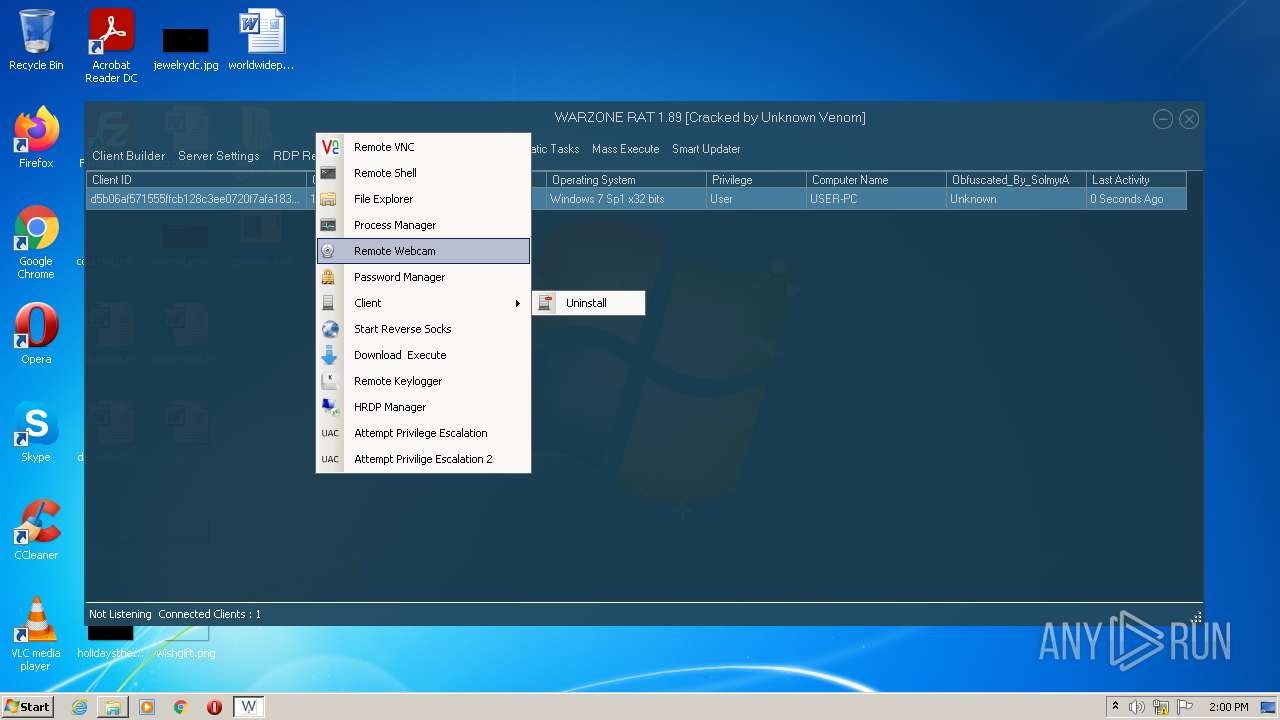
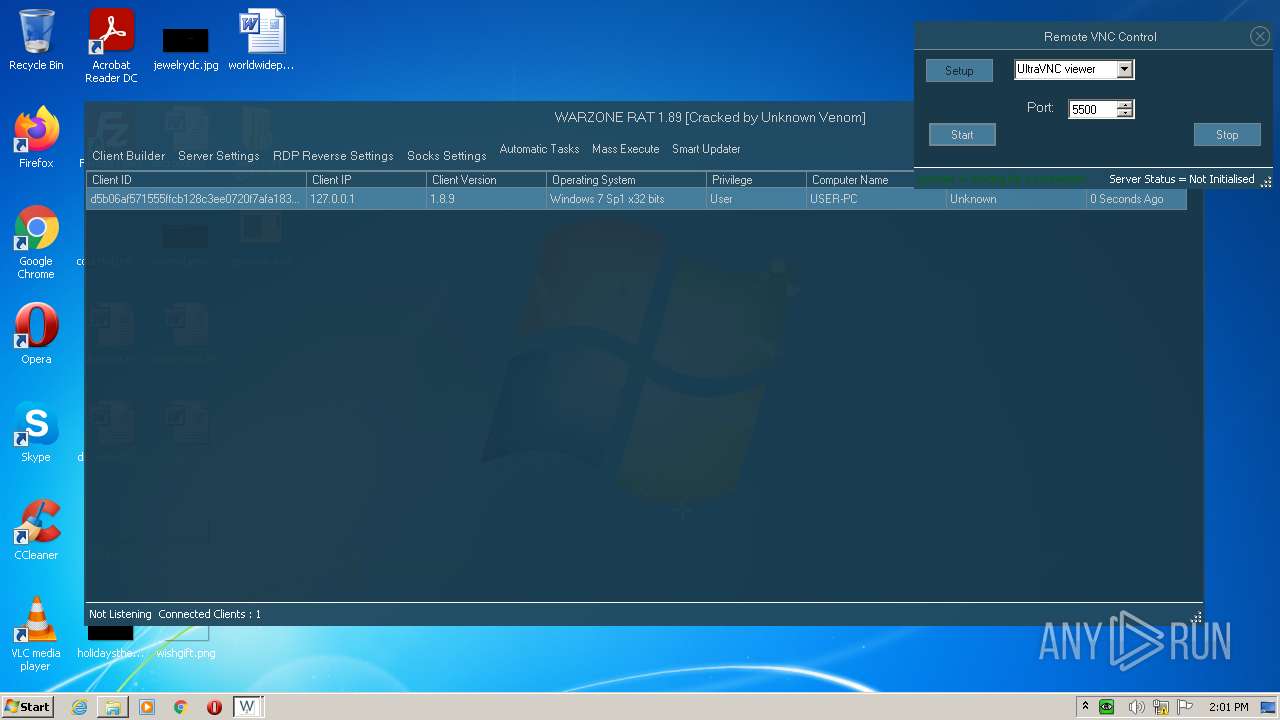
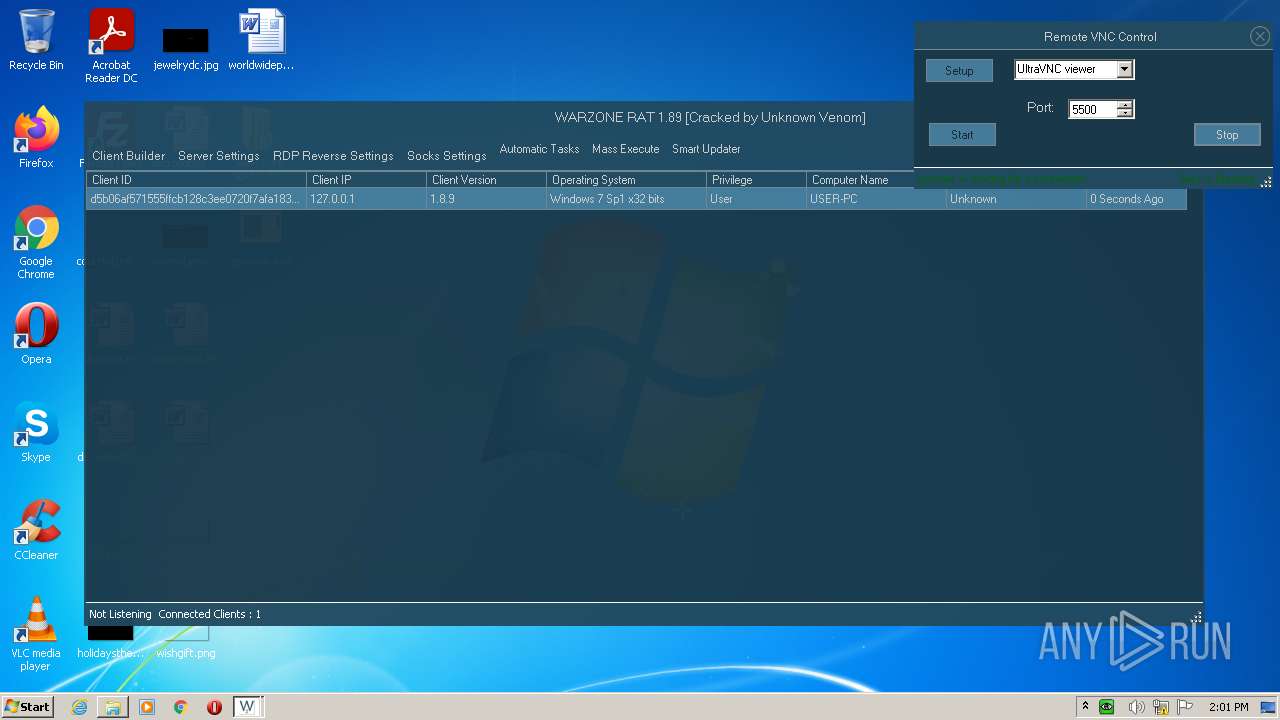
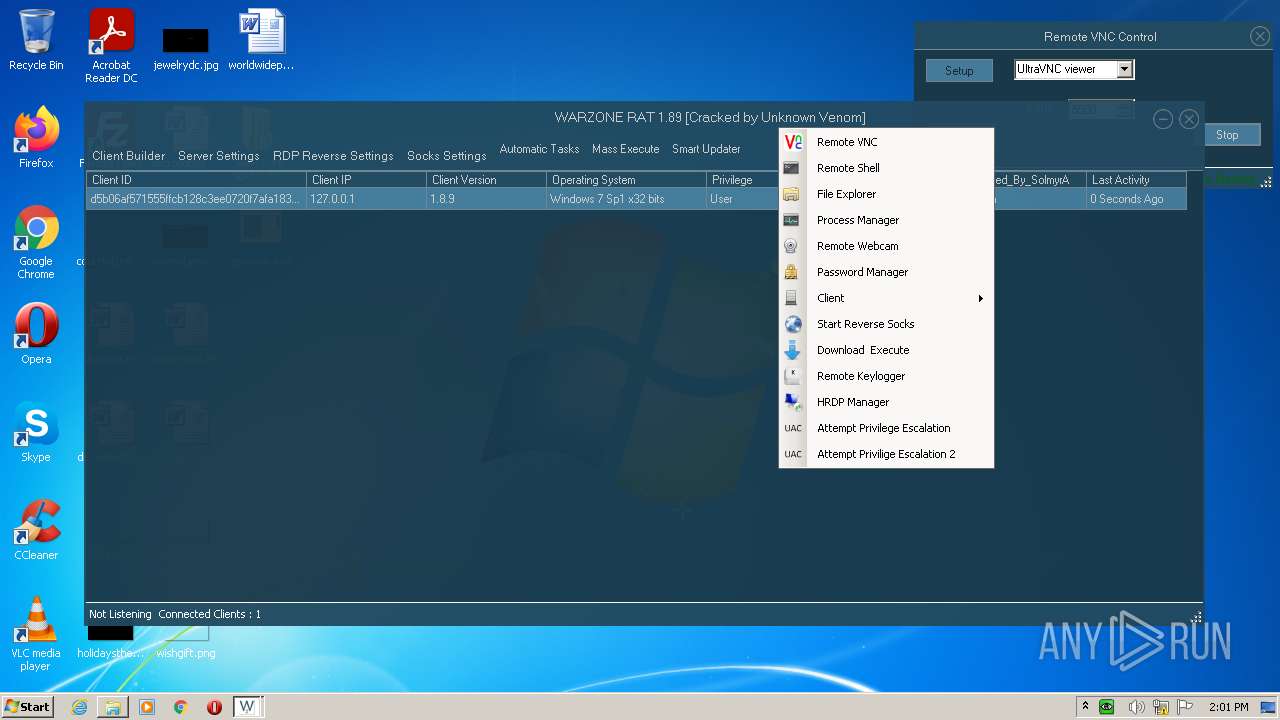
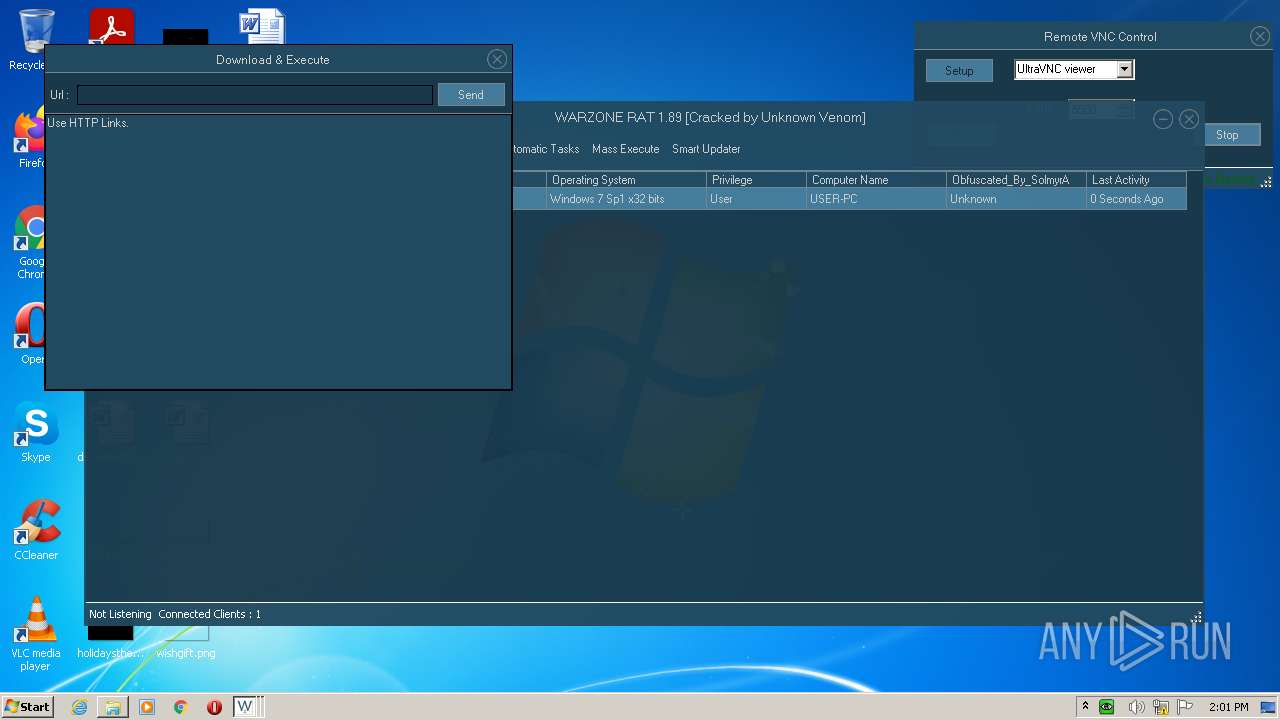
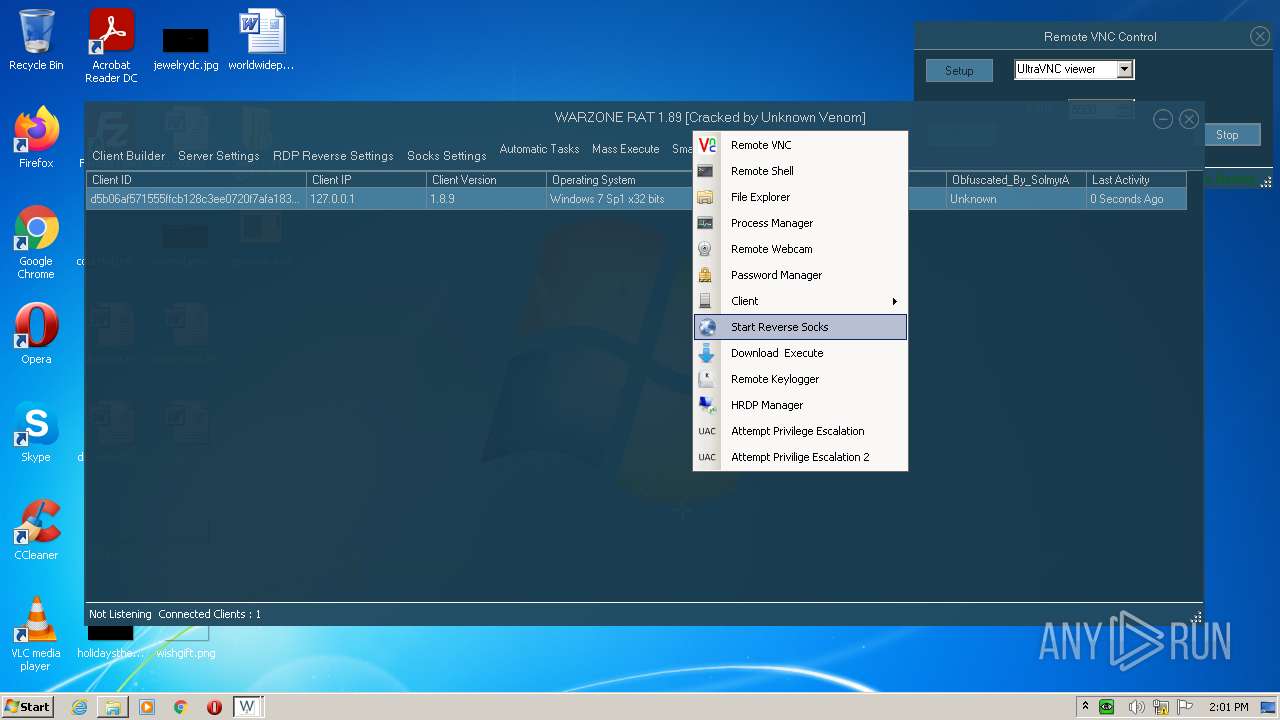
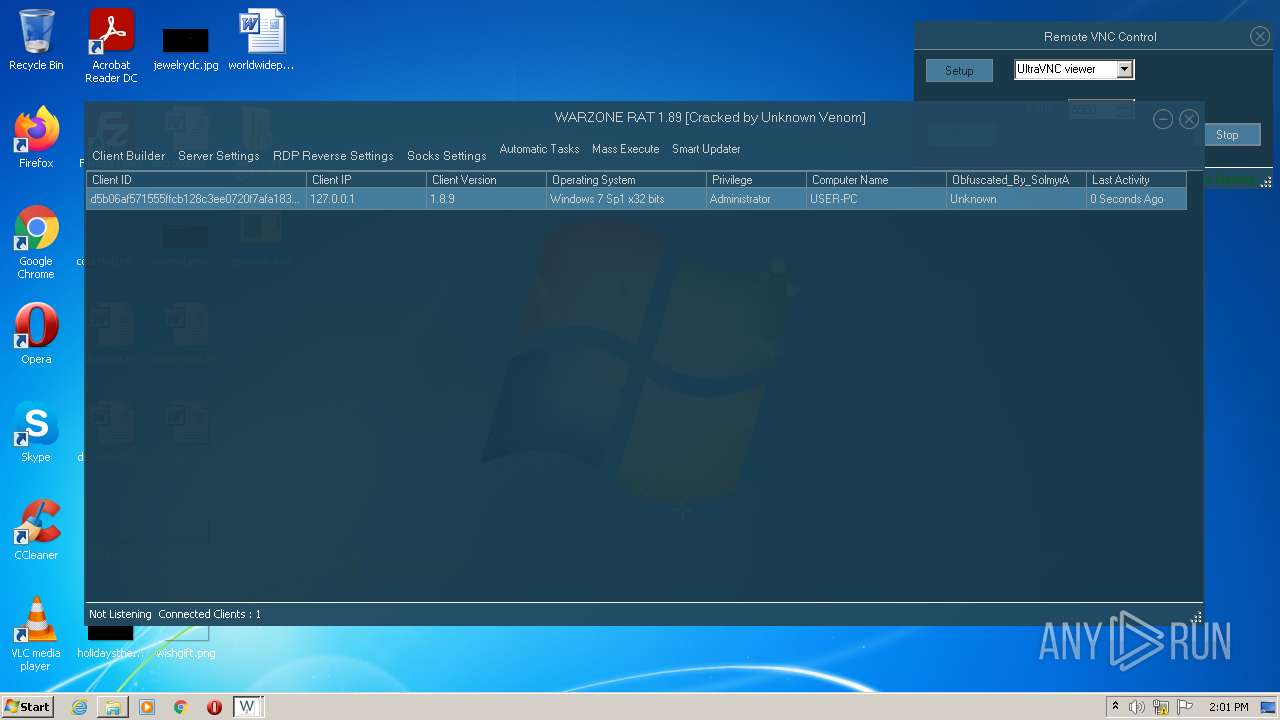
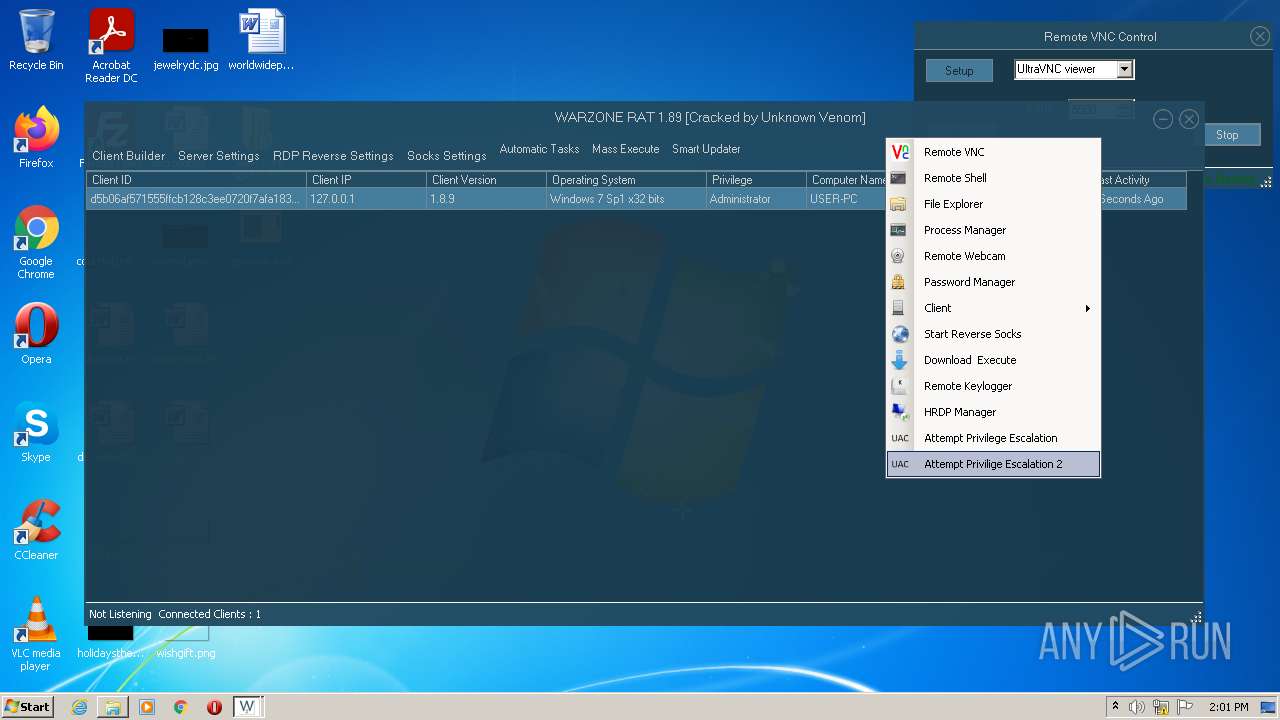
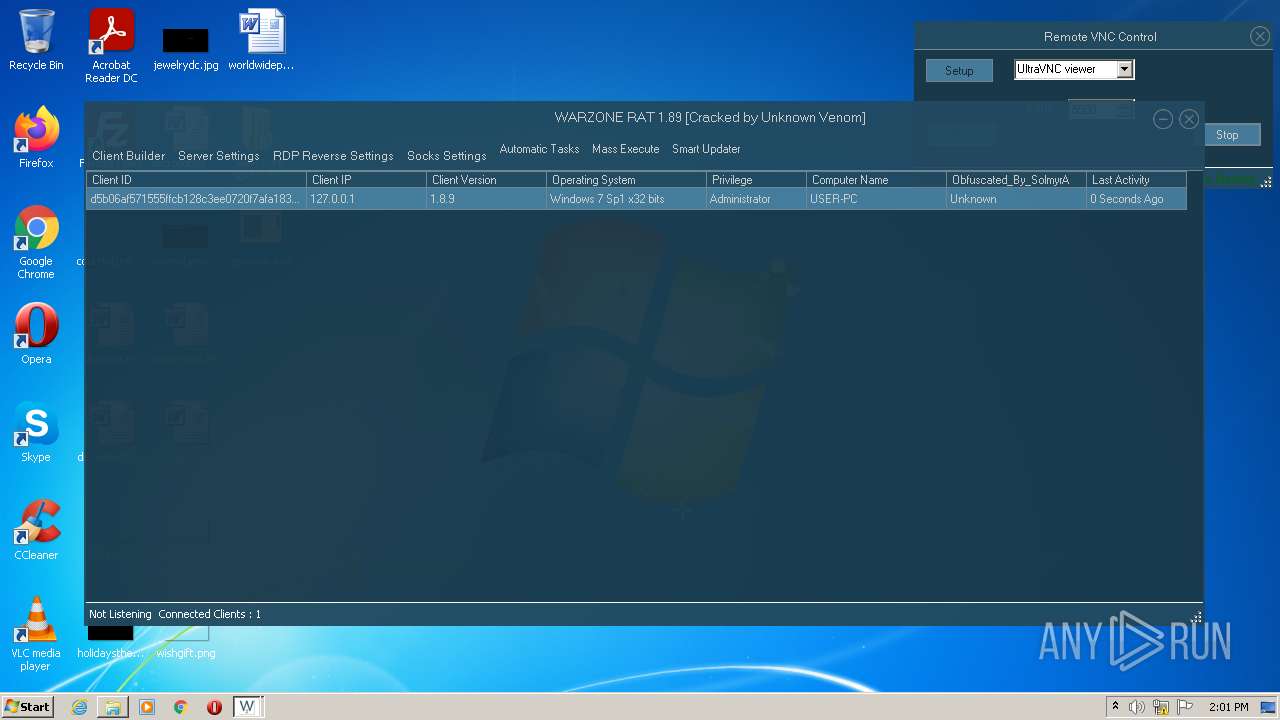
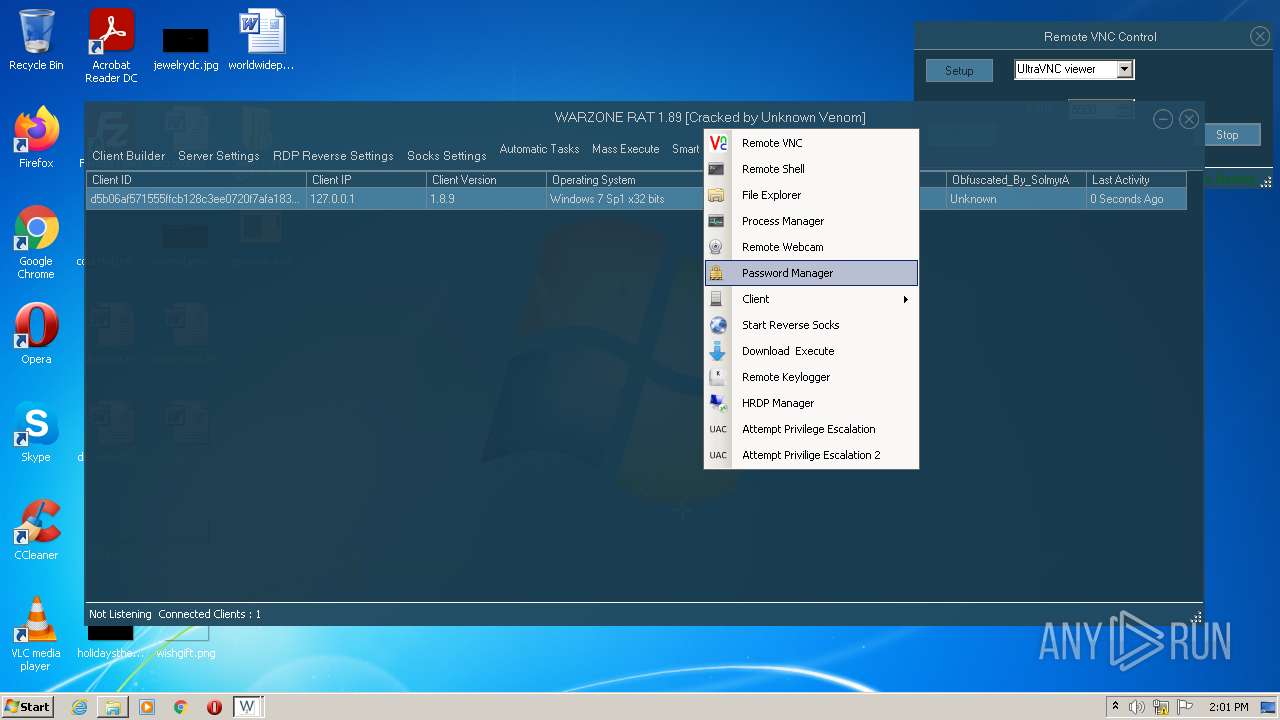
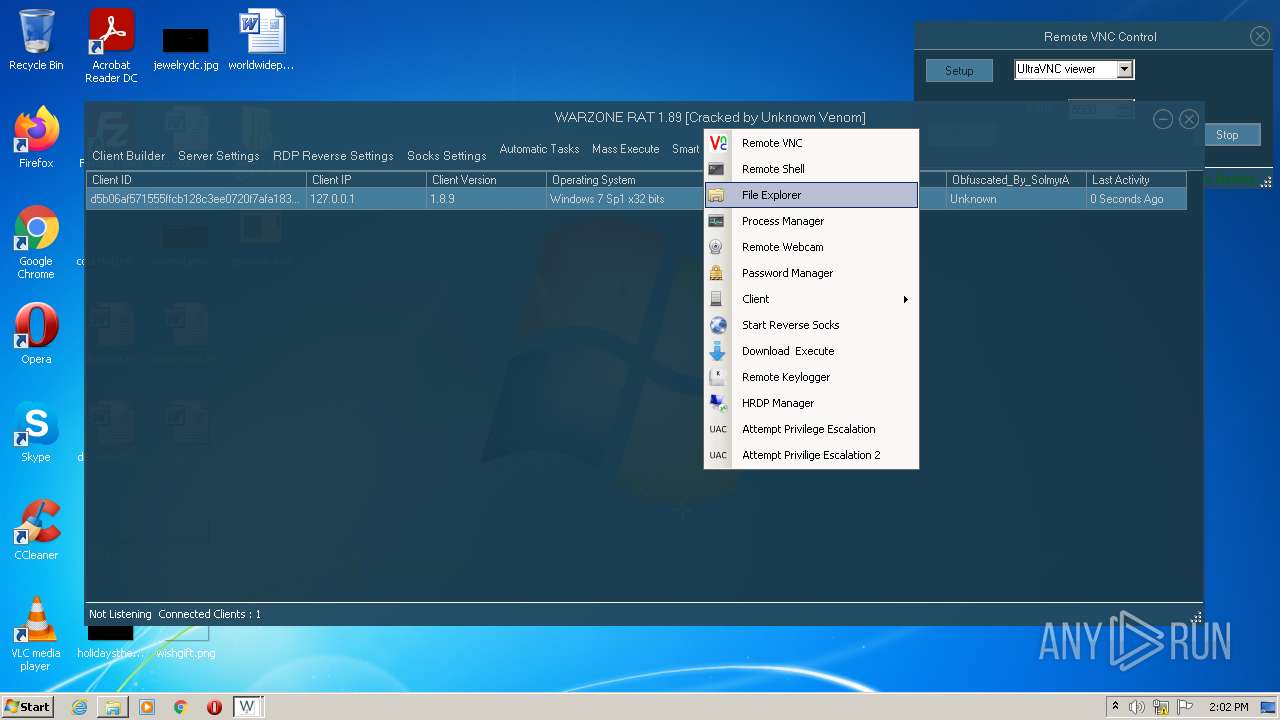
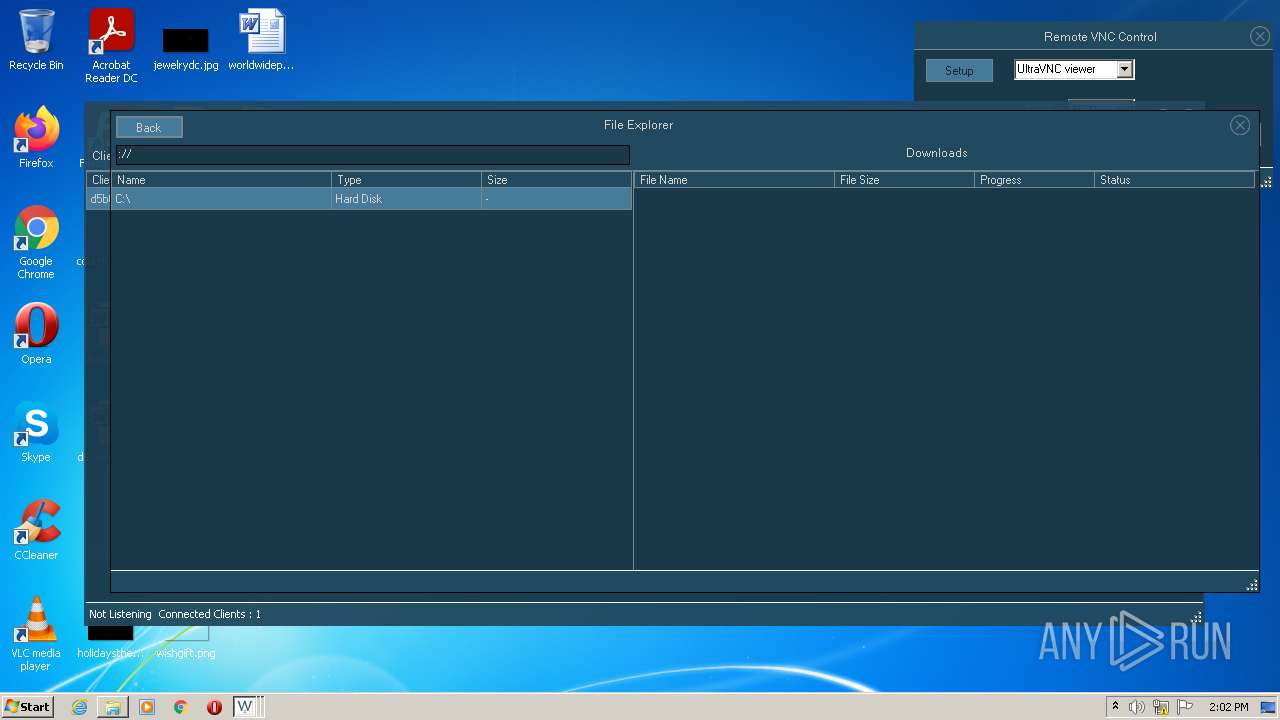
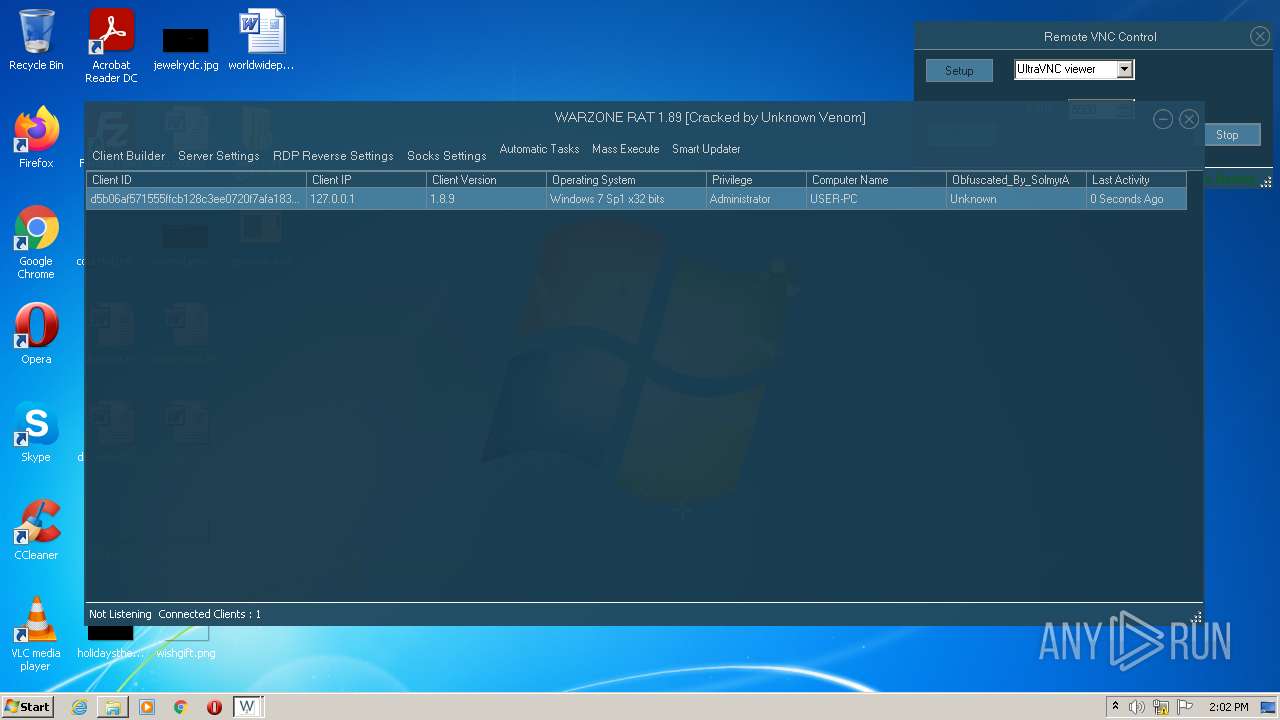
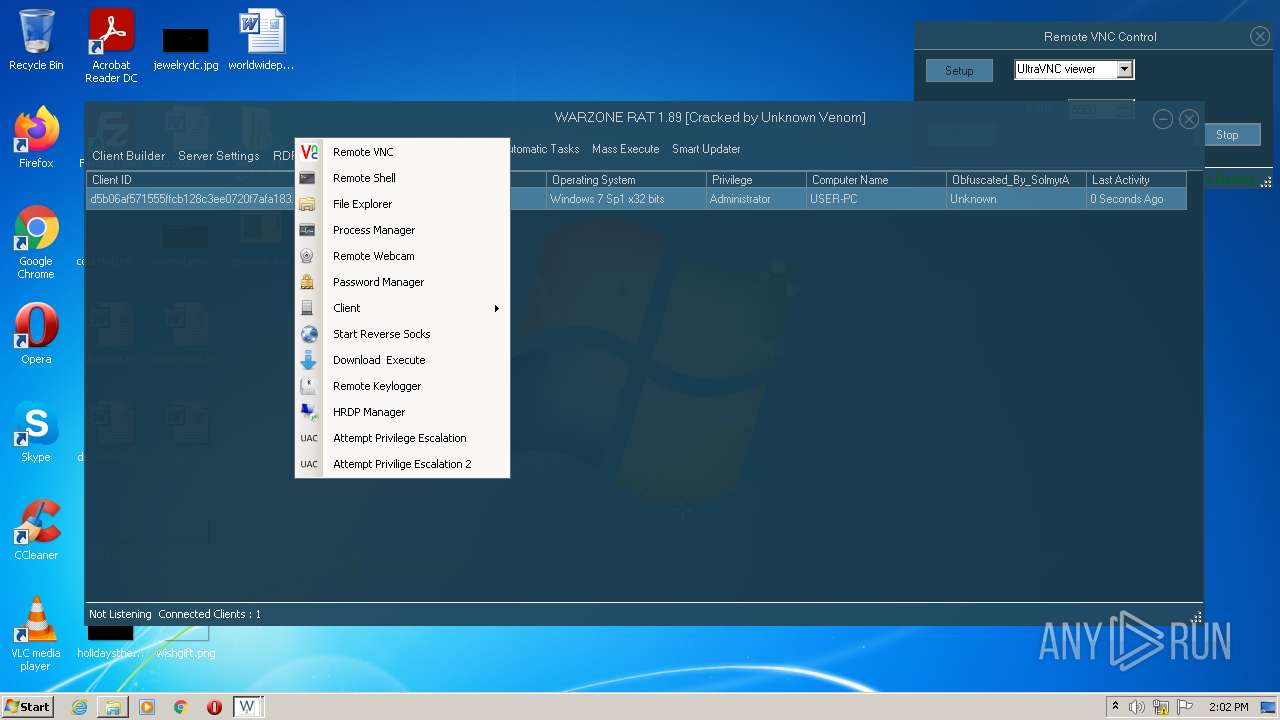
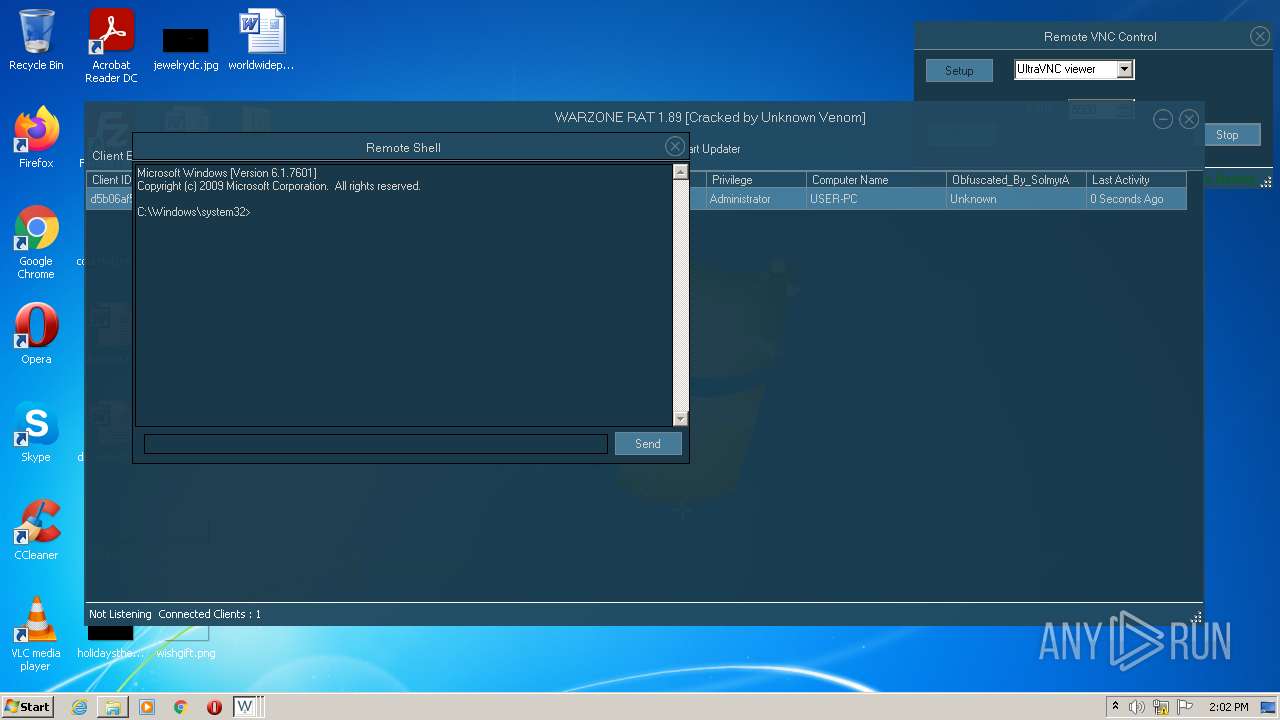
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | February 04, 2022, 13:59:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5F393437C61059C6D814173374215C36 |
| SHA1: | 5F00C76E20421548DA24046398BB4F31DE509CA9 |
| SHA256: | 5EDDECAE217BCD6060EAE7A9A7B2297E9D9BC1251D92EF65F3C29FA59E9210C2 |
| SSDEEP: | 196608:WJxGWlo8oW6KxqsFRfKMrsxkpEGL4tRnFwlHXO9LT1U51VuKaGppzyAWXh:zWlto7kqsJgxk+P3FCHXe61sfGpdKh |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3672)
- dism.exe (PID: 2740)
Application was dropped or rewritten from another process
- WARZONE RAT 1.89 Cracked by Unknown Venom.exe (PID: 2516)
- serveee.exe (PID: 3180)
- rvncviewer.exe (PID: 3868)
- serveee.exe (PID: 3384)
AVEMARIA was detected
- serveee.exe (PID: 3180)
Drops executable file immediately after starts
- cmd.exe (PID: 2748)
- DllHost.exe (PID: 2088)
Runs app for hidden code execution
- serveee.exe (PID: 3180)
- serveee.exe (PID: 3384)
SUSPICIOUS
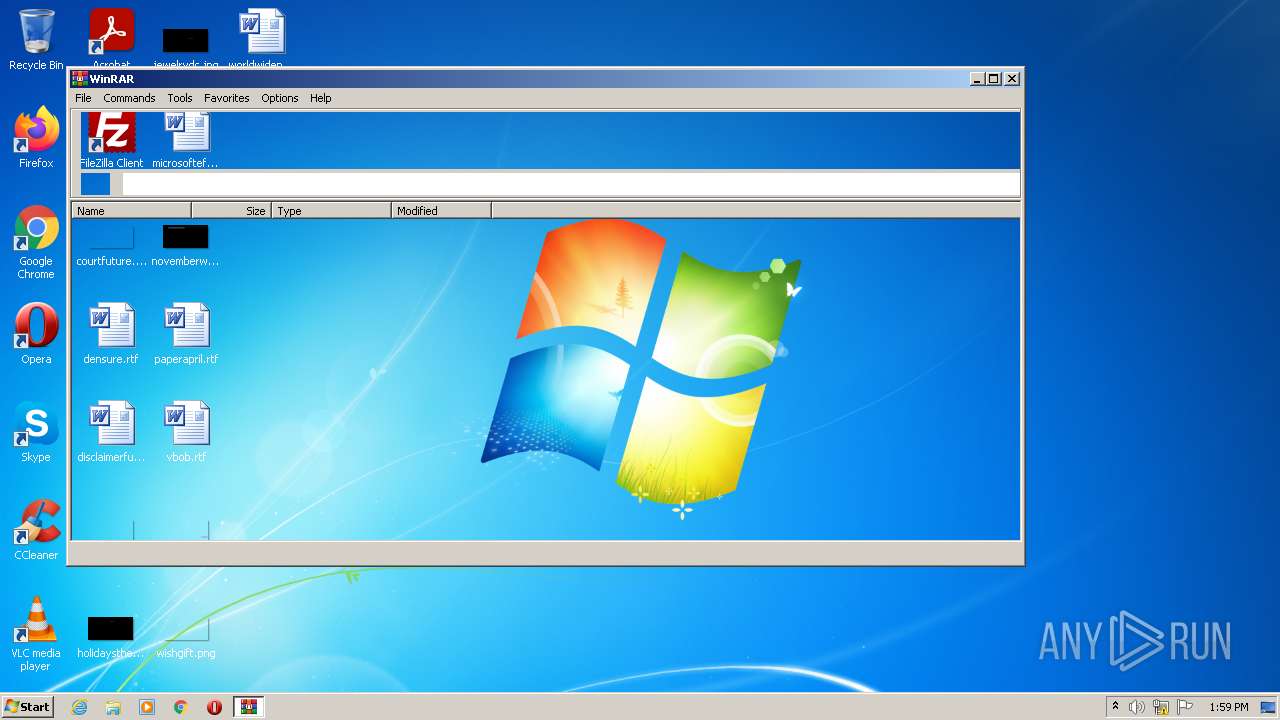
Checks supported languages
- WinRAR.exe (PID: 3812)
- WARZONE RAT 1.89 Cracked by Unknown Venom.exe (PID: 2516)
- serveee.exe (PID: 3180)
- rvncviewer.exe (PID: 3868)
- cmd.exe (PID: 2748)
- cmd.exe (PID: 3032)
- serveee.exe (PID: 3384)
Reads the computer name
- WinRAR.exe (PID: 3812)
- WARZONE RAT 1.89 Cracked by Unknown Venom.exe (PID: 2516)
- serveee.exe (PID: 3180)
- rvncviewer.exe (PID: 3868)
- cmd.exe (PID: 2748)
- serveee.exe (PID: 3384)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3812)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3812)
Executable content was dropped or overwritten
- WARZONE RAT 1.89 Cracked by Unknown Venom.exe (PID: 2516)
- WinRAR.exe (PID: 3812)
- cmd.exe (PID: 2748)
- DllHost.exe (PID: 2088)
Creates a directory in Program Files
- serveee.exe (PID: 3180)
- serveee.exe (PID: 3384)
Starts CMD.EXE for commands execution
- serveee.exe (PID: 3180)
- serveee.exe (PID: 3384)
Executed via COM
- DllHost.exe (PID: 2088)
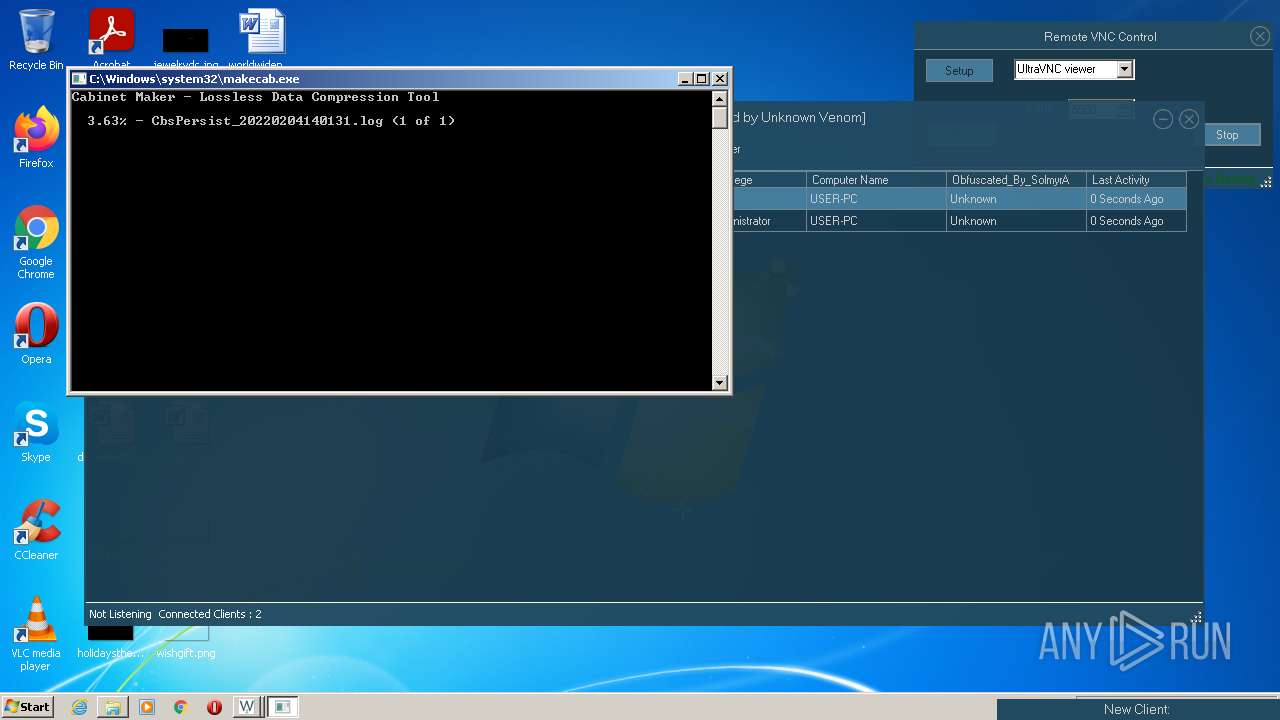
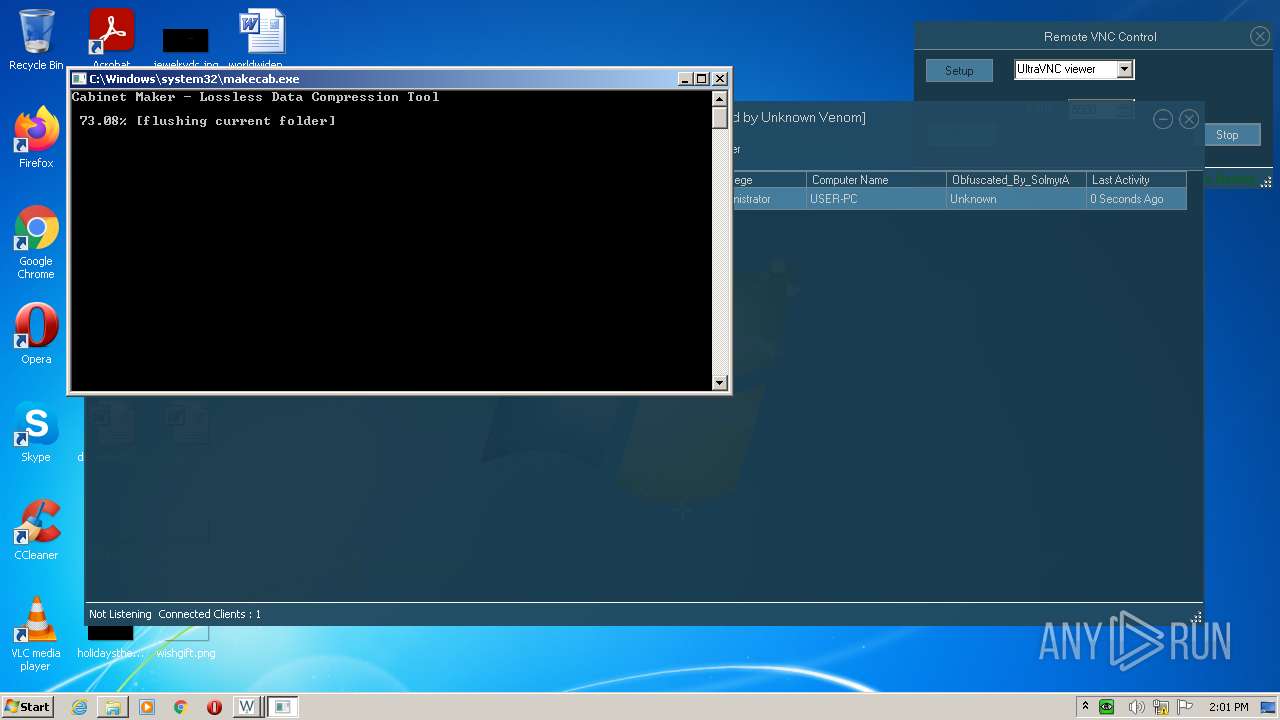
Creates files in the Windows directory
- pkgmgr.exe (PID: 832)
- makecab.exe (PID: 2728)
INFO
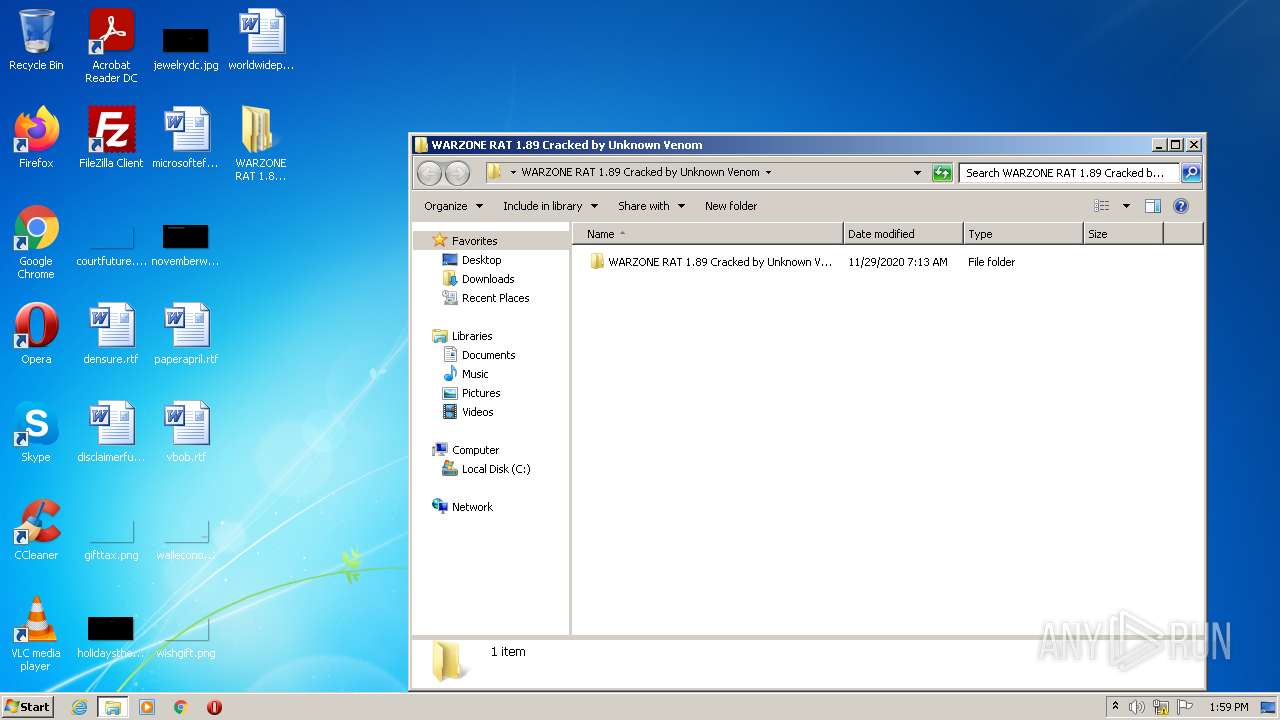
Manual execution by user
- WARZONE RAT 1.89 Cracked by Unknown Venom.exe (PID: 2516)
- serveee.exe (PID: 3180)
Checks supported languages
- DllHost.exe (PID: 2088)
- pkgmgr.exe (PID: 832)
- dism.exe (PID: 2740)
- makecab.exe (PID: 2728)
Reads the computer name
- DllHost.exe (PID: 2088)
- dism.exe (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
54
Monitored processes
13
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 832 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
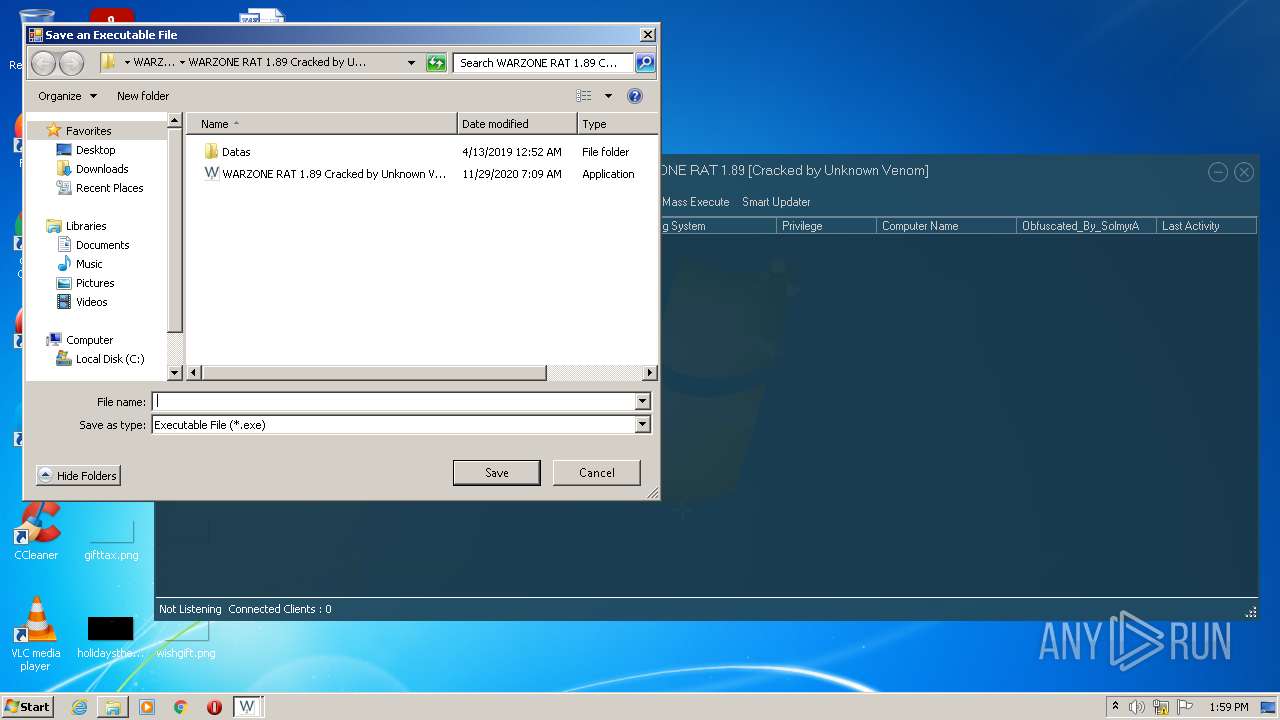
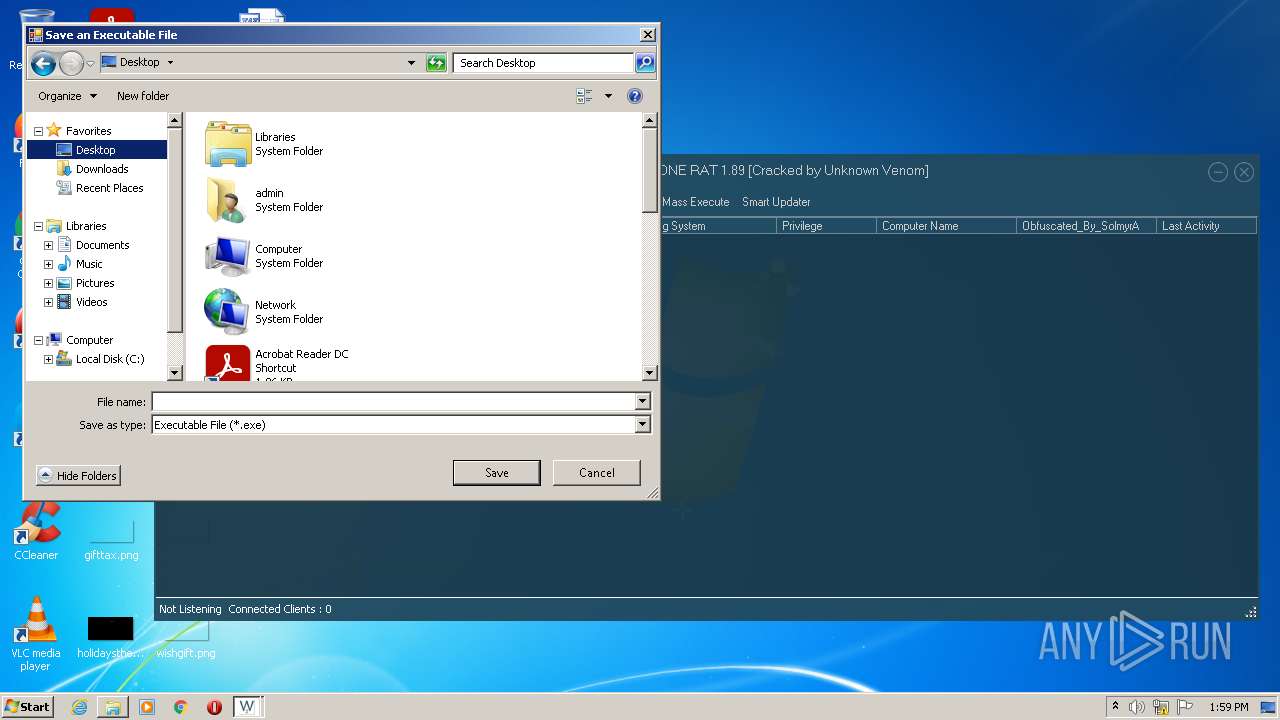
| 2516 | "C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom.exe" | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WARZONE RAT 1.89 Exit code: 0 Version: 1.8.9.0 Modules
| |||||||||||||||
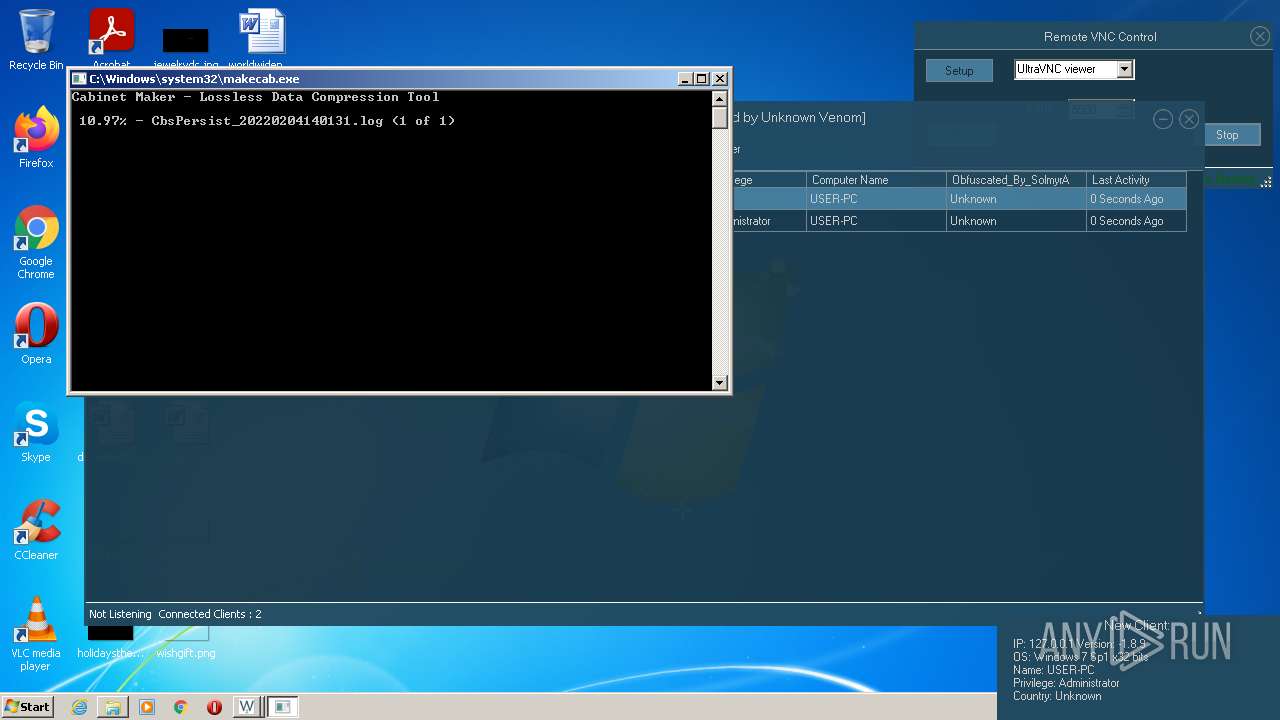
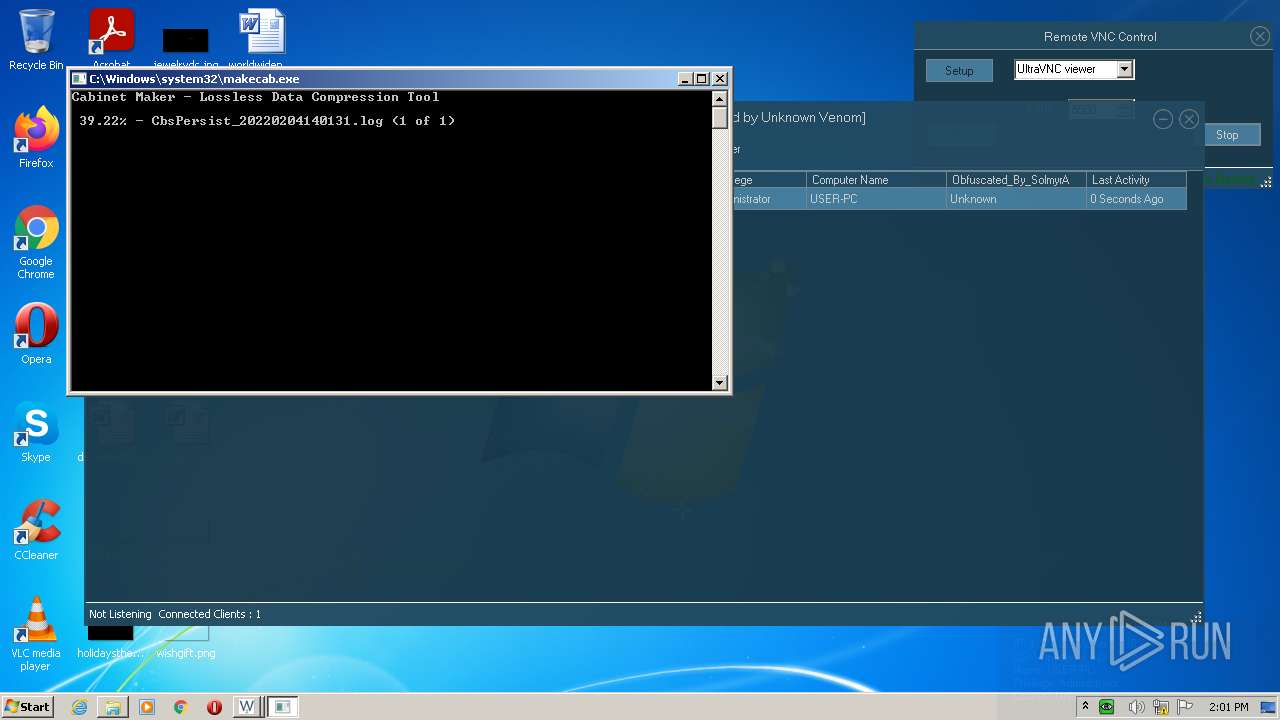
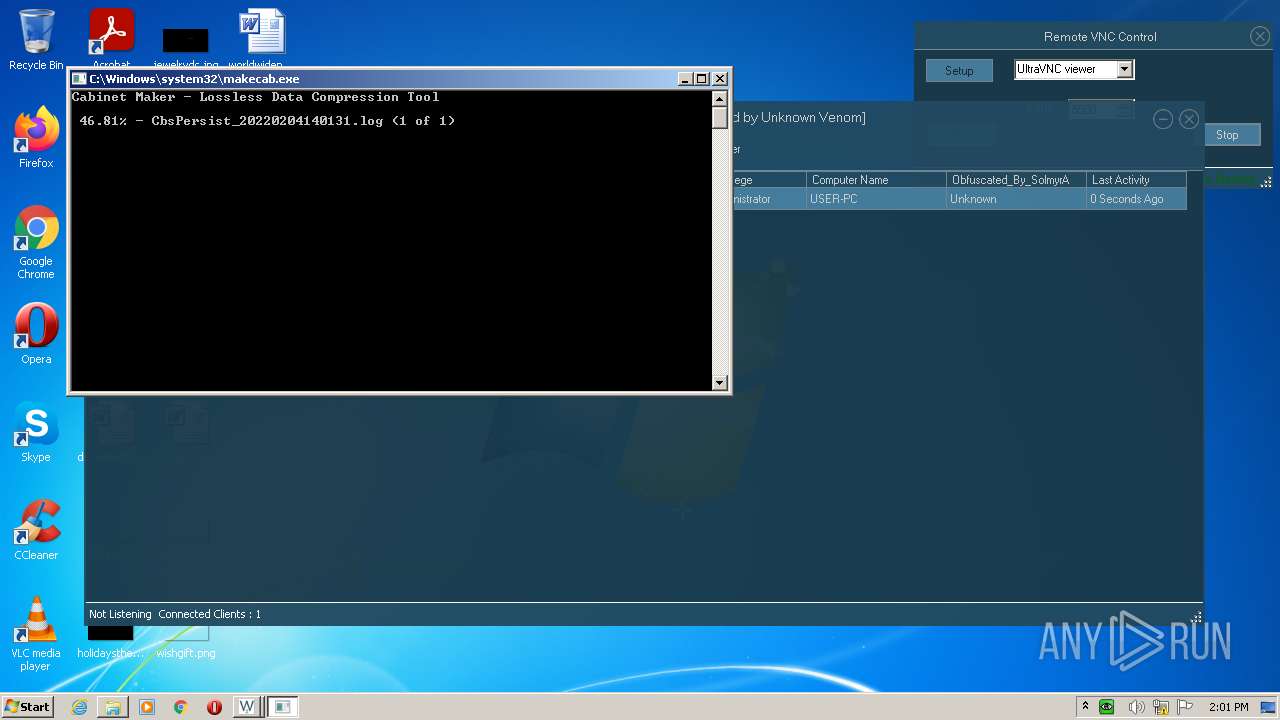
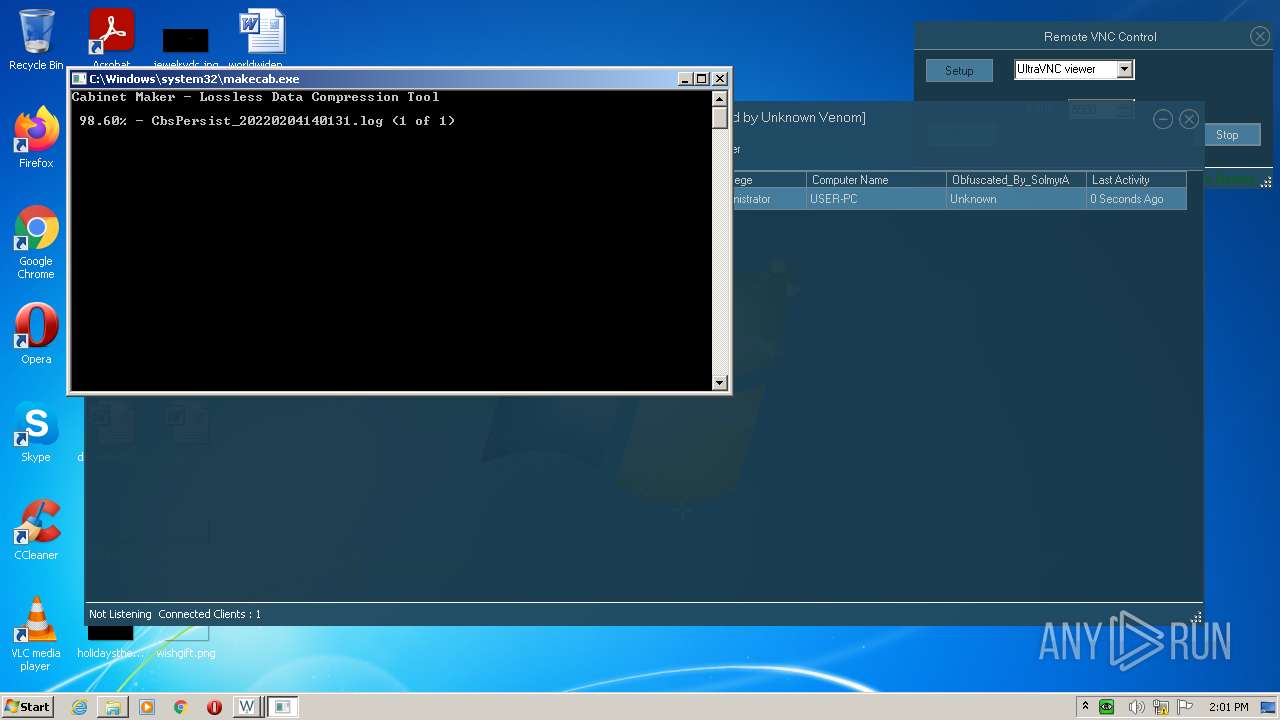
| 2728 | "C:\Windows\system32\makecab.exe" C:\Windows\Logs\CBS\CbsPersist_20220204140131.log C:\Windows\Logs\CBS\CbsPersist_20220204140131.cab | C:\Windows\system32\makecab.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | serveee.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3032 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | serveee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\Desktop\serveee.exe" | C:\Users\admin\Desktop\serveee.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\Desktop\serveee.exe" | C:\Users\admin\Desktop\serveee.exe | — | dism.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
7 991
Read events
7 872
Write events
116
Delete events
3
Modification events
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WARZONE_RAT_1.89_Cracked_by_Unknown_Venom.rar | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
16
Suspicious files
8
Text files
10
Unknown types
1
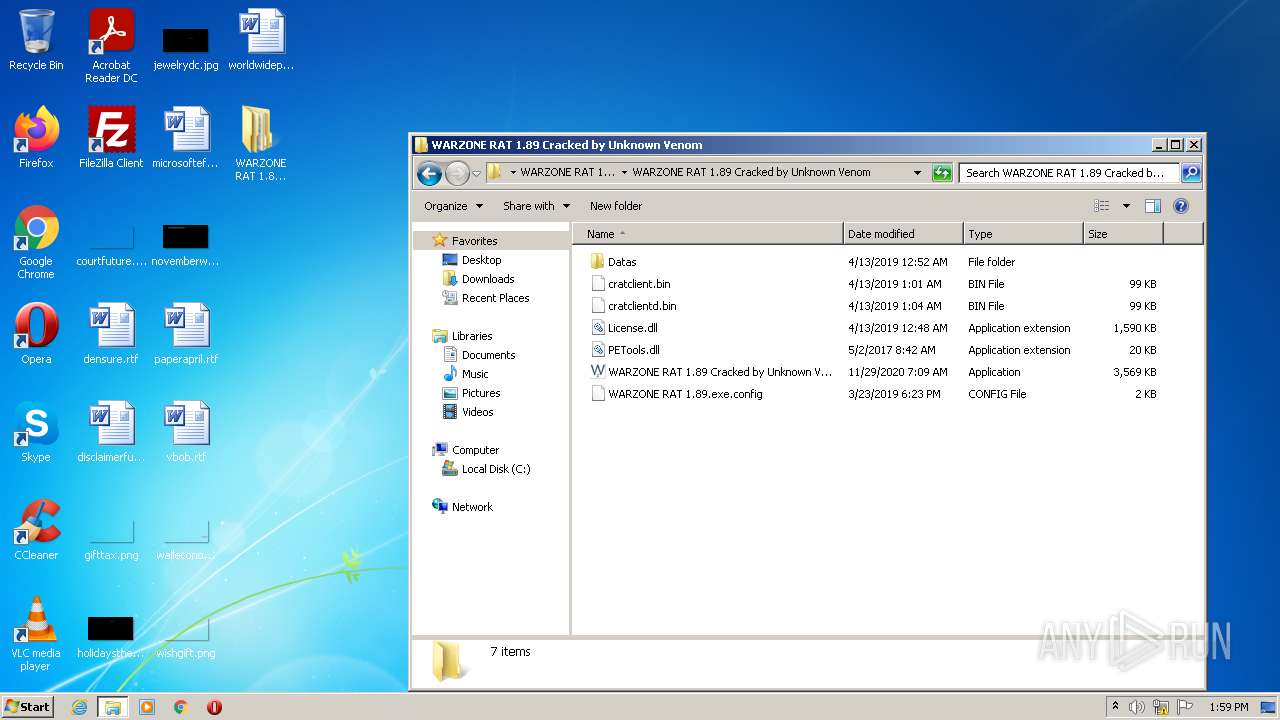
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
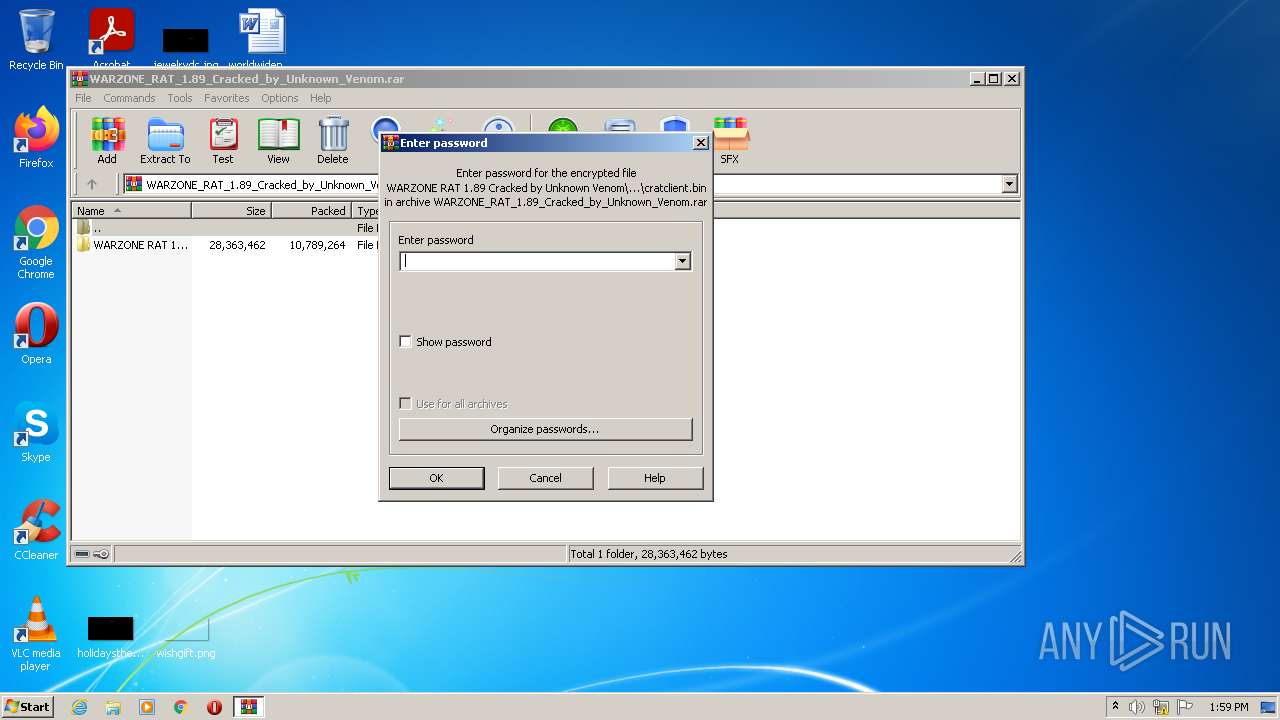
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\cratclientd.bin | executable | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\cratclient.bin | executable | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\License.dll | executable | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\Datas\tvnviewer.exe | executable | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\Datas\geoip\GeoIP.dat | binary | |
MD5:B64EA0C3E9617CCD2F22D8568676A325 | SHA256:432E12E688449C2CF1B184C94E2E964F9E09398C194888A7FE1A5B1F8CF3059B | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\Datas\sqlite3.dll | executable | |
MD5:D3979DB259F55D59B4EDB327673C1905 | SHA256:043E5570299C6099756C1809C5632EABEAB95ED3C1A55C86843C0EC218940E5A | |||
| 2516 | WARZONE RAT 1.89 Cracked by Unknown Venom.exe | C:\Users\admin\AppData\Local\WARZONE_RAT_1.89\WARZONE_RAT_1.89_Cracked__Url_3k0bz4xo0nz42srtg2mt0vl4ajsgtecq\1.8.9.0\1x4wksbc.newcfg | xml | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\Datas\SocksManager.exe | executable | |
MD5:55626BBDCE2962E1B451C8AFAE8FB1FA | SHA256:6D65C5918A1DE925E45154B5E9552C3BC44C624B78A663C685D450144712C1A6 | |||
| 832 | pkgmgr.exe | C:\Windows\Logs\CBS\CbsPersist_20220204140131.log | — | |
MD5:— | SHA256:— | |||
| 3812 | WinRAR.exe | C:\Users\admin\Desktop\WARZONE RAT 1.89 Cracked by Unknown Venom\WARZONE RAT 1.89 Cracked by Unknown Venom\Datas\rV.bsp1 | mp3 | |
MD5:46A3FB413EB81CBF9F53B6EE03A865CE | SHA256:2698FF8CB64E9B938855FC31015005E81F9E68D24C6375B402FE55A0E89DD2BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
WARZONE RAT 1.89 Cracked by Unknown Venom.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
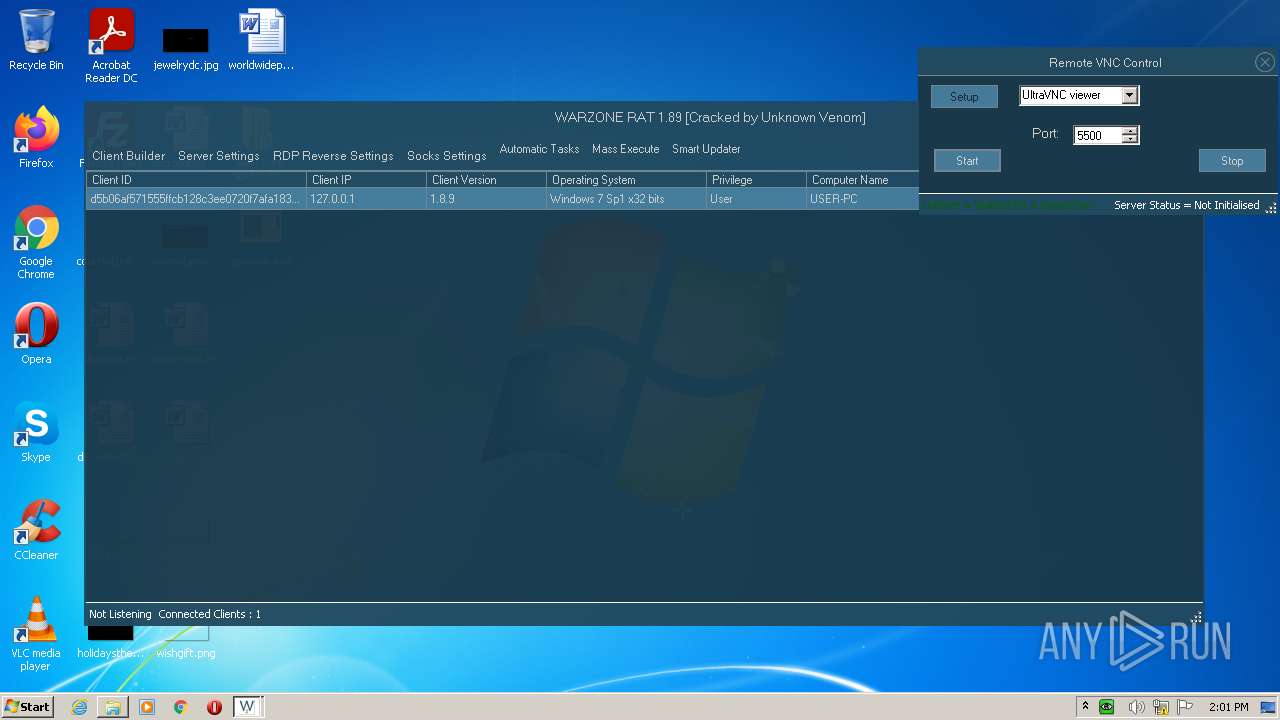
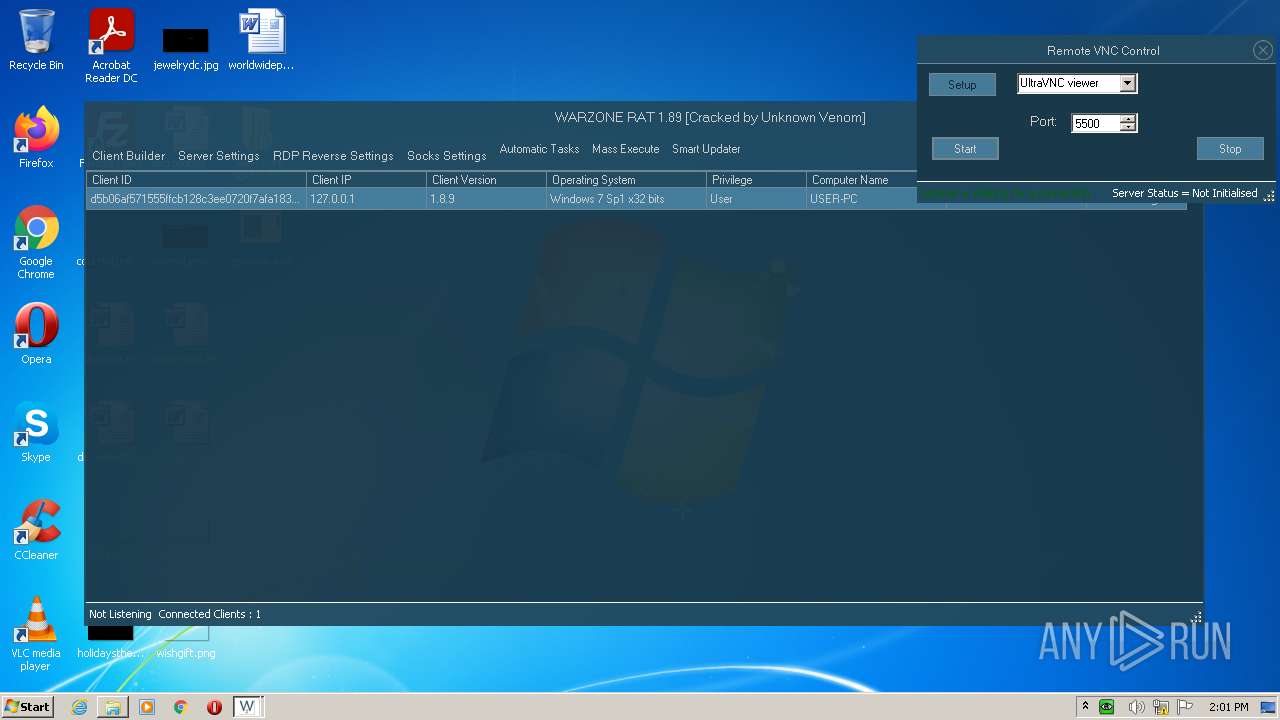
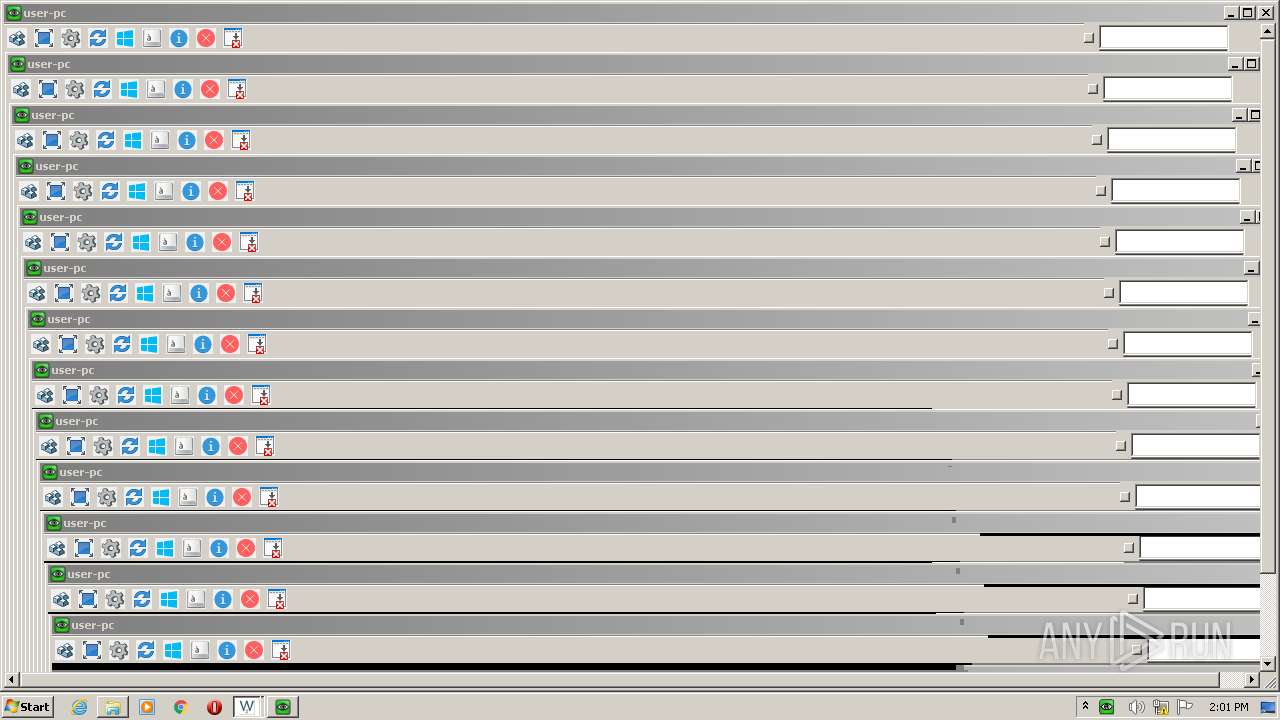
rvncviewer.exe | DSMPlugin not enabled
|
rvncviewer.exe | RFB server supports protocol version 3.8
|
rvncviewer.exe | Connected to RFB server, using protocol version 3.8
|
rvncviewer.exe | No authentication needed
|
rvncviewer.exe | Desktop name "user-pc "
|
rvncviewer.exe | rdr::Exception (1): rdr::SystemException: read: Unknown error (10004)
|