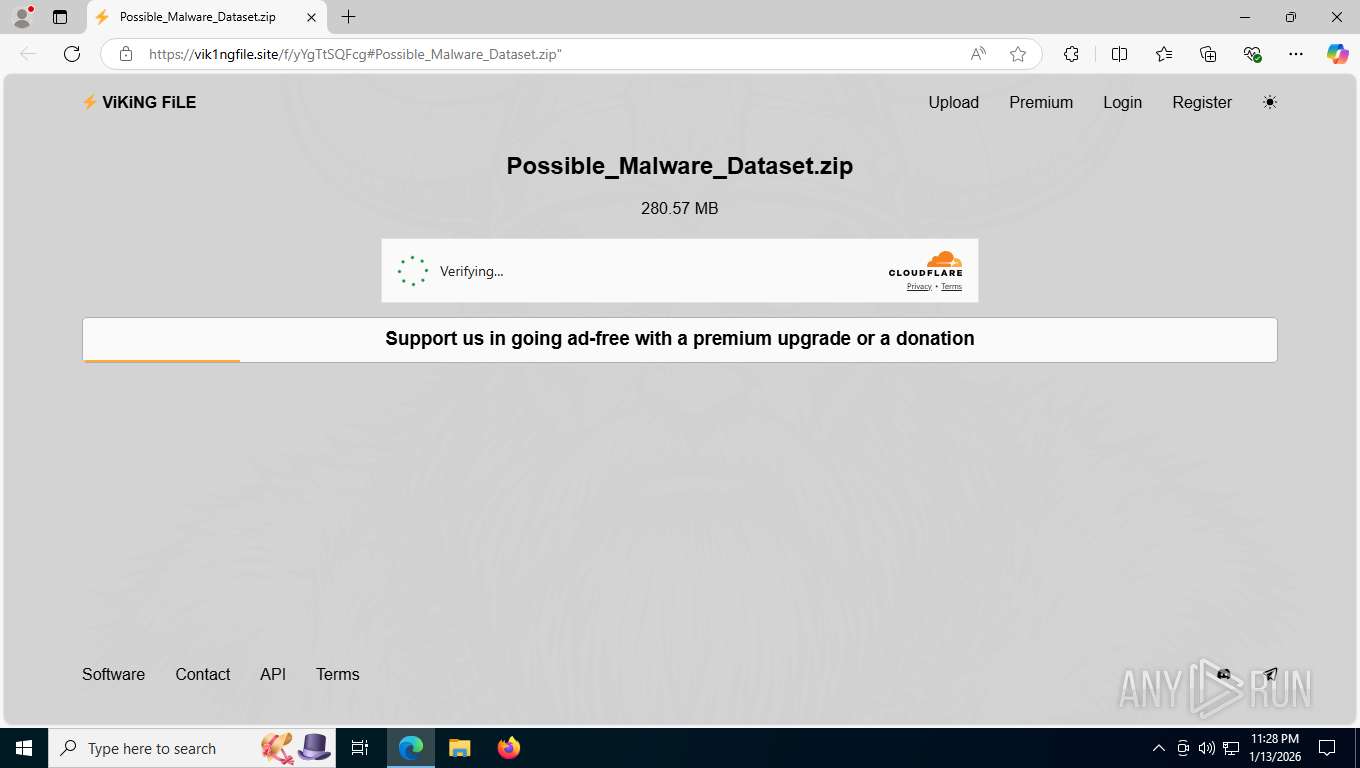
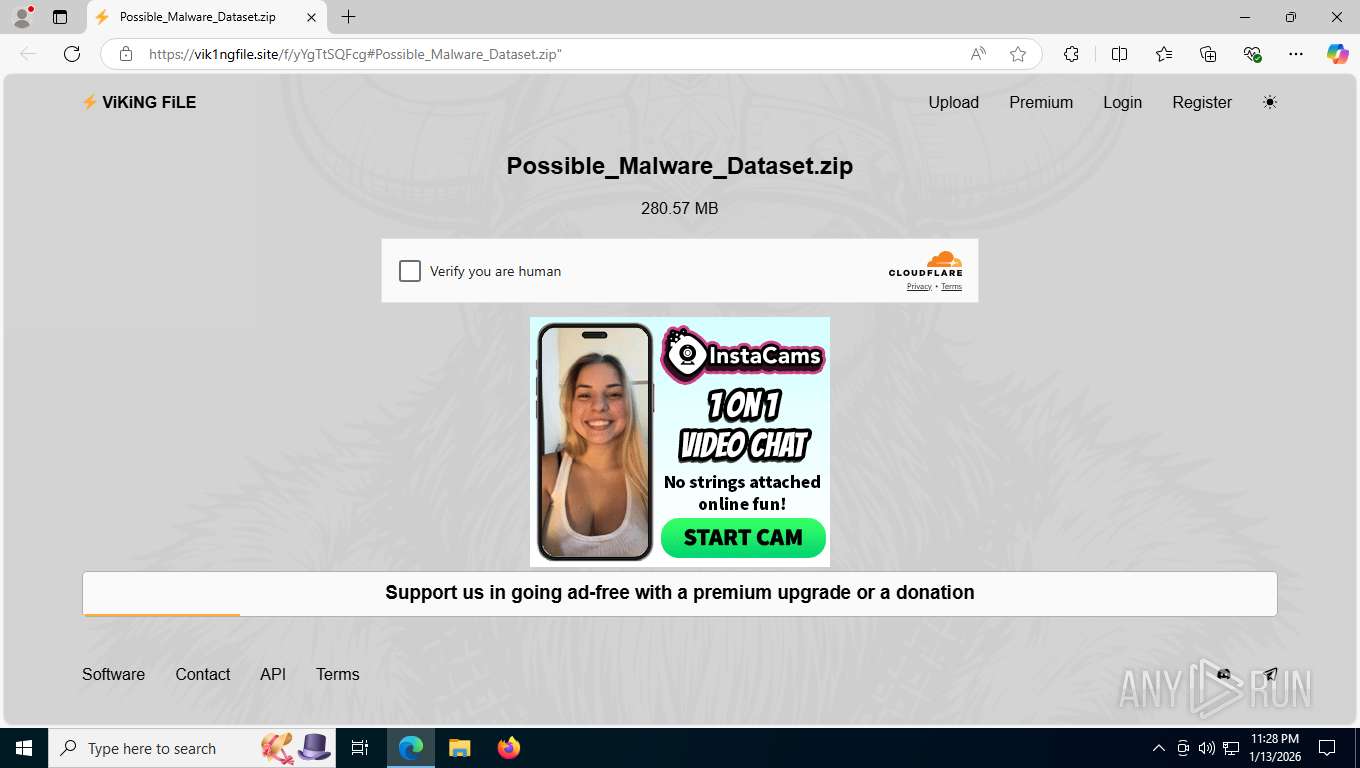
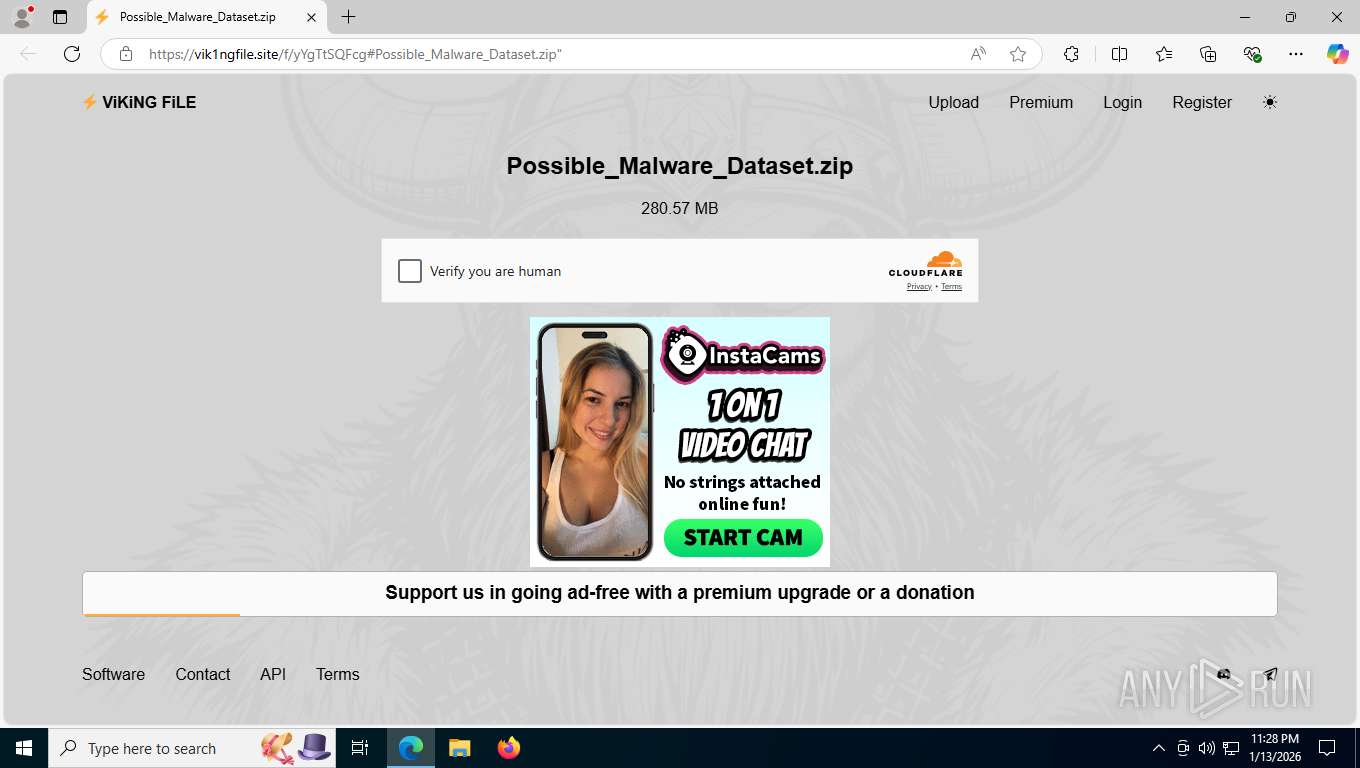
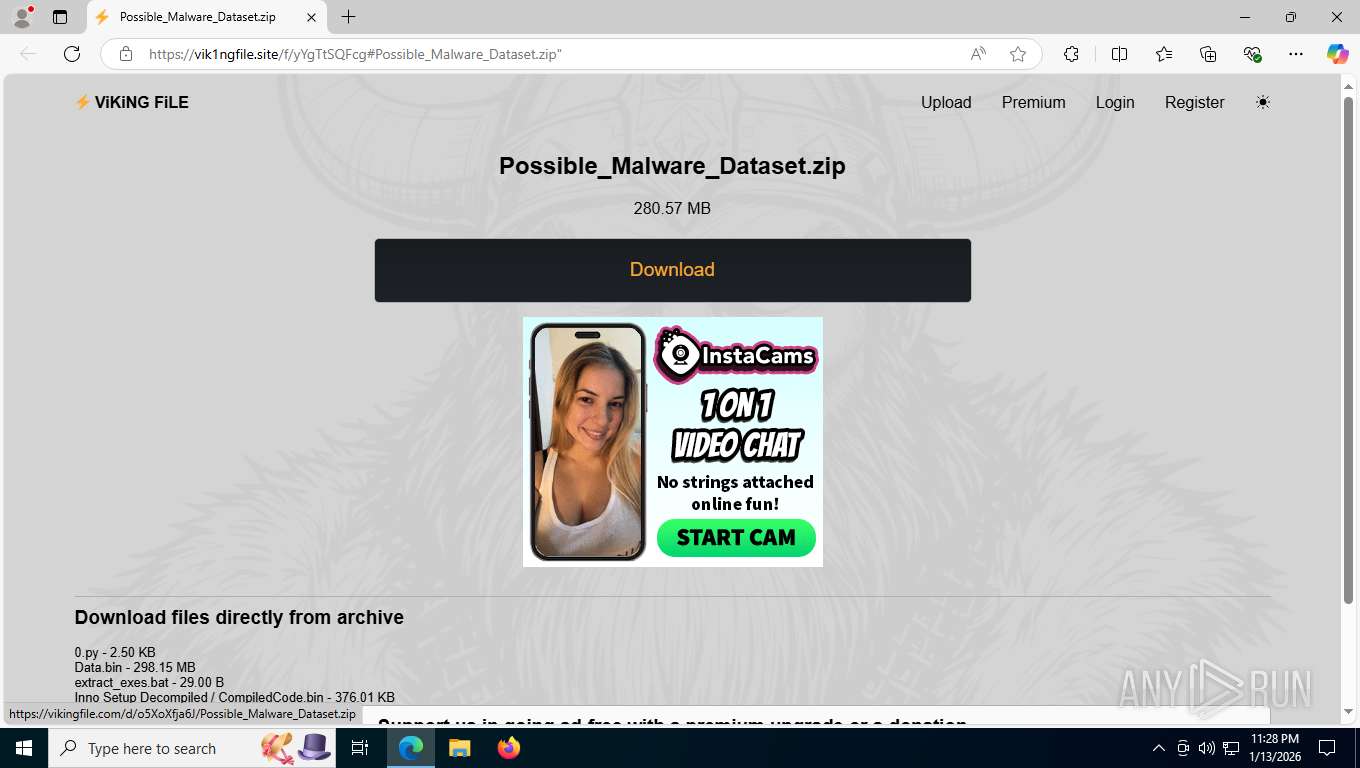
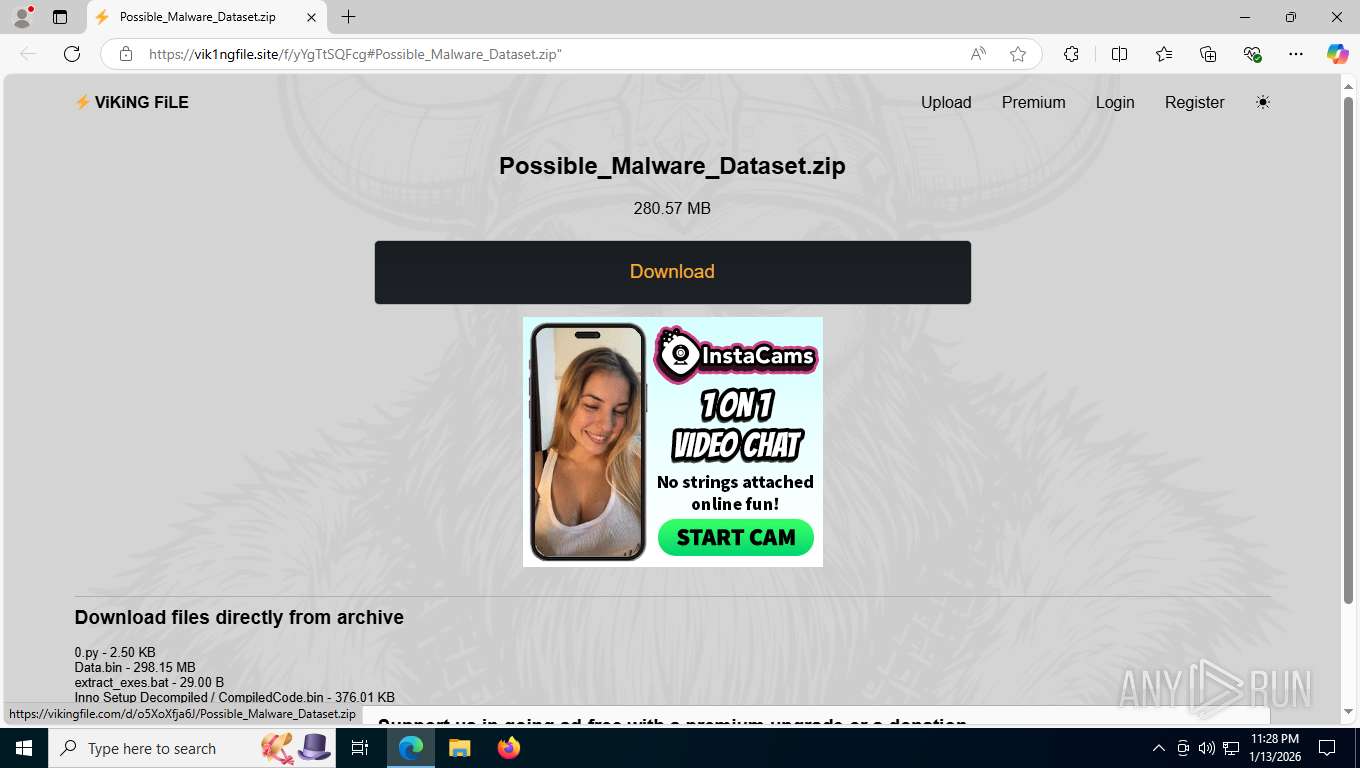
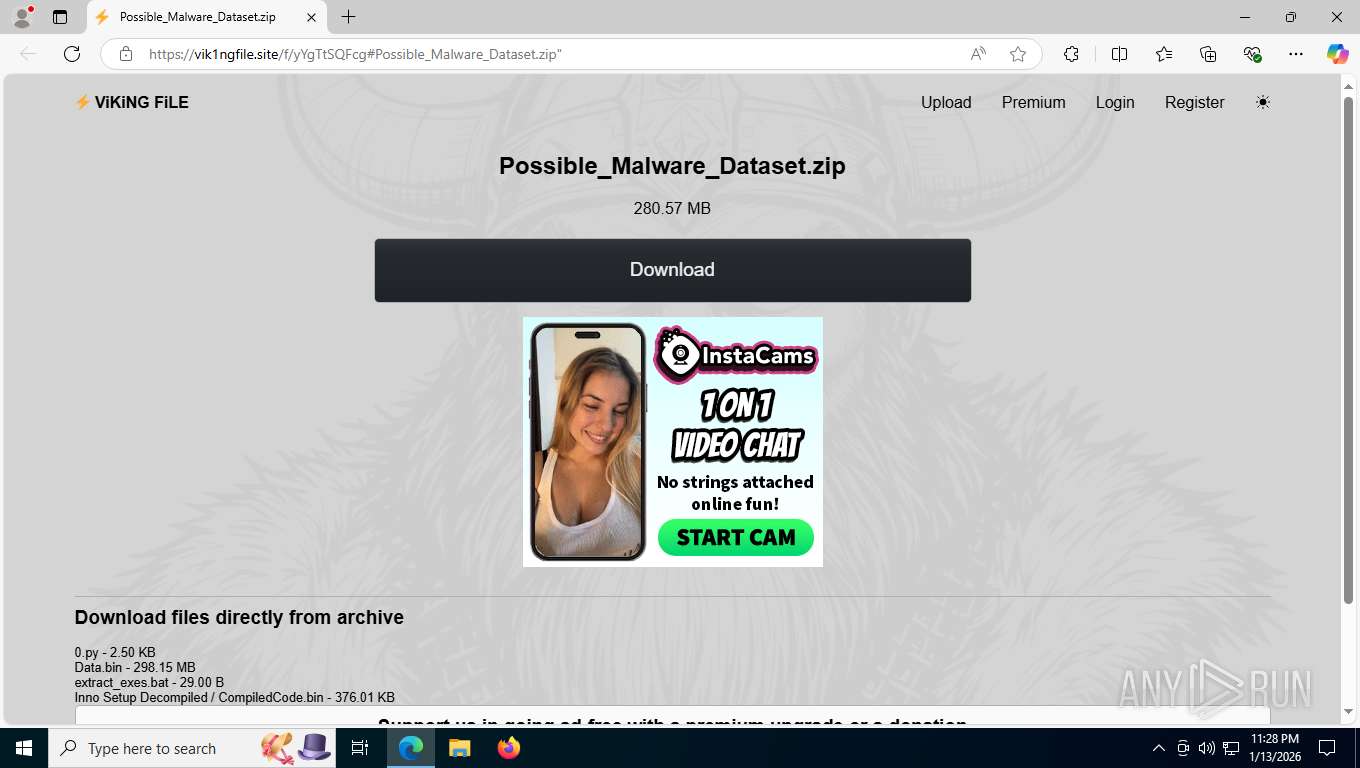
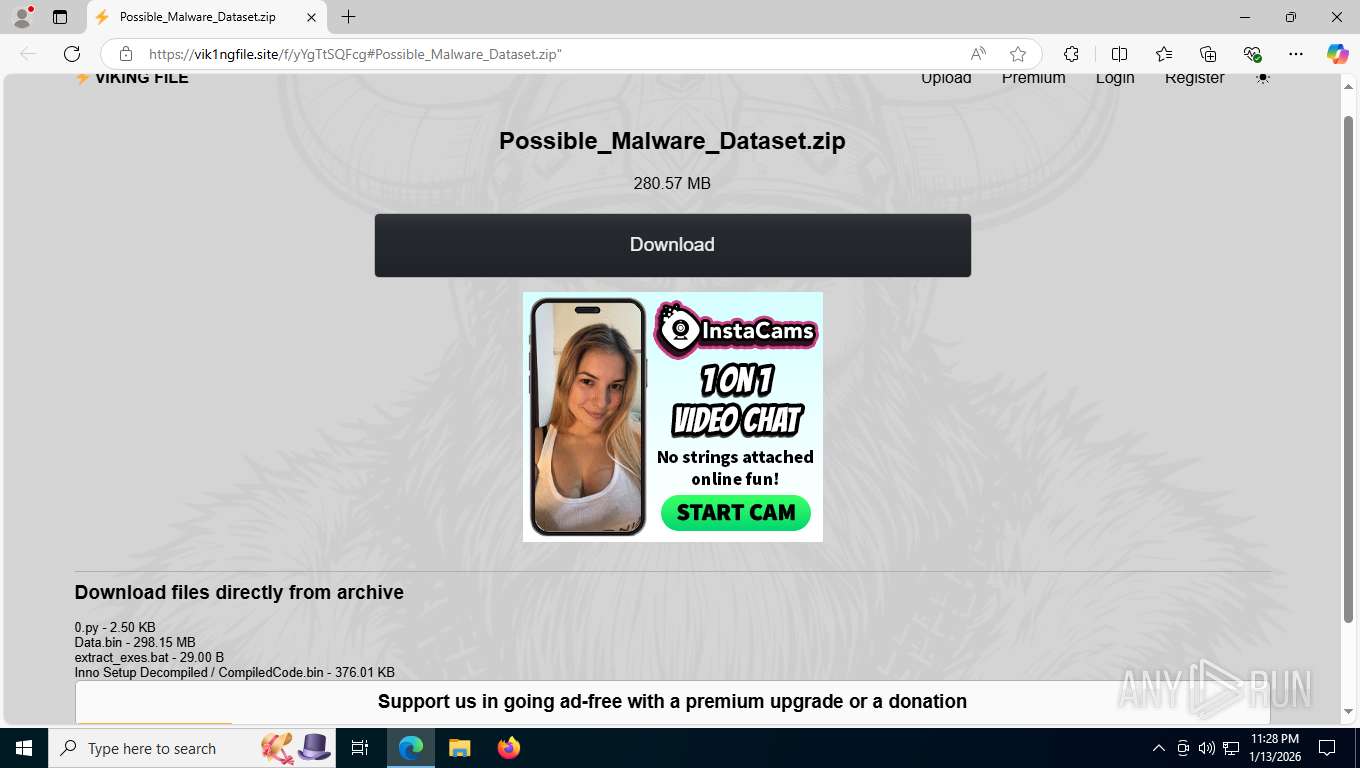
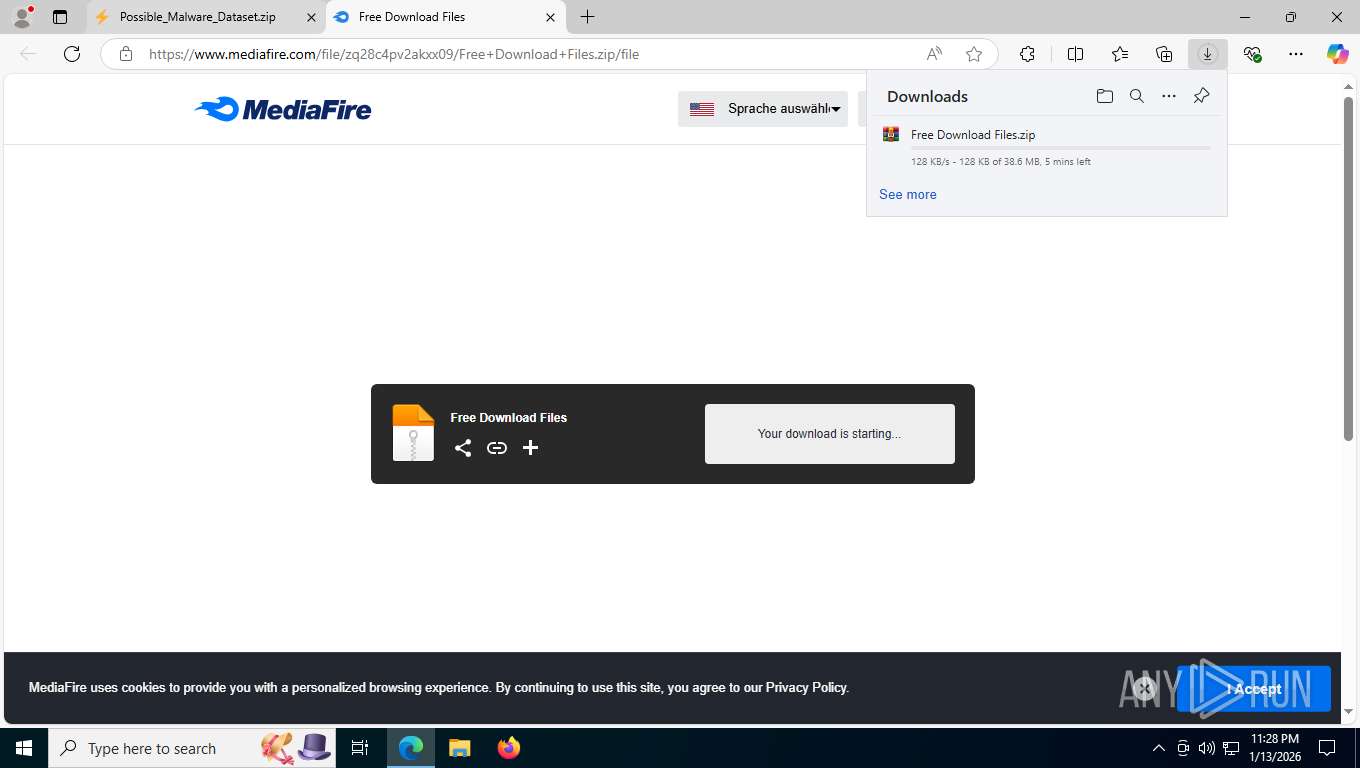
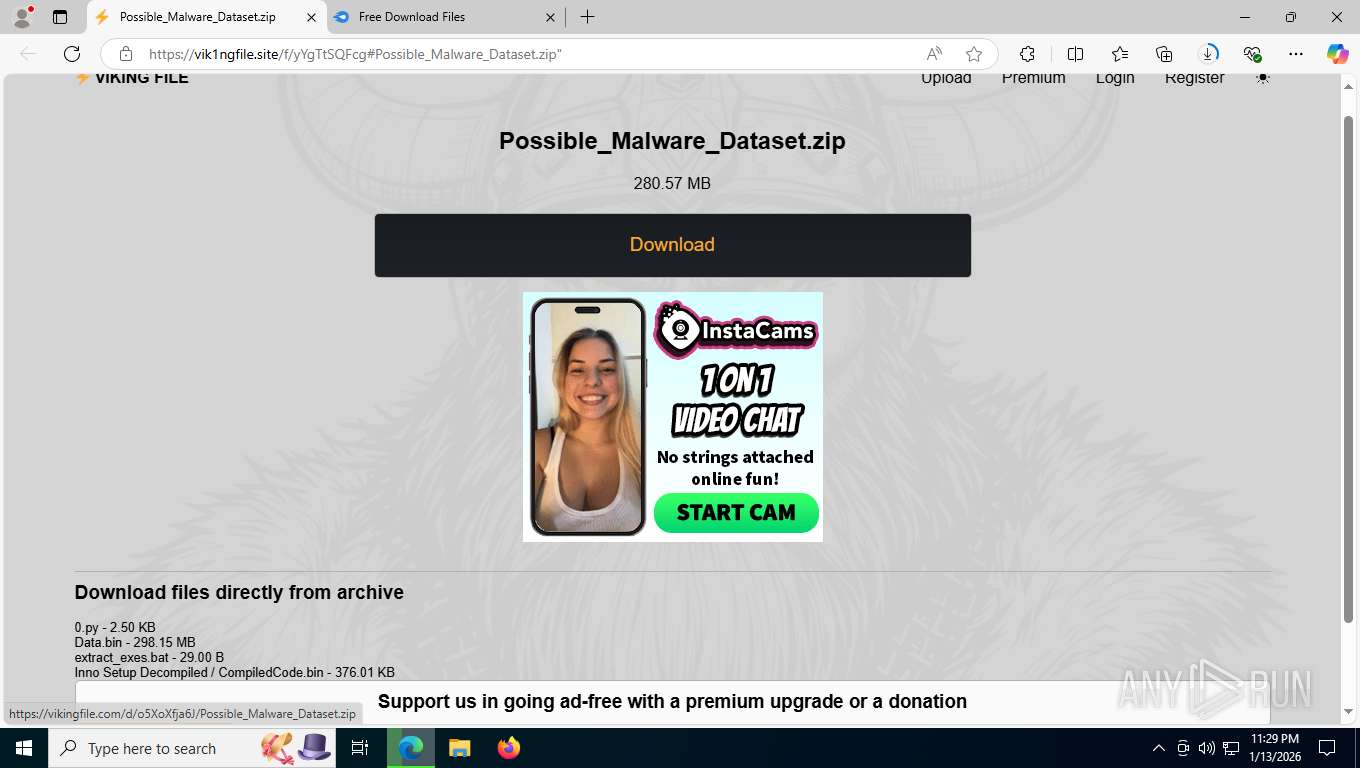
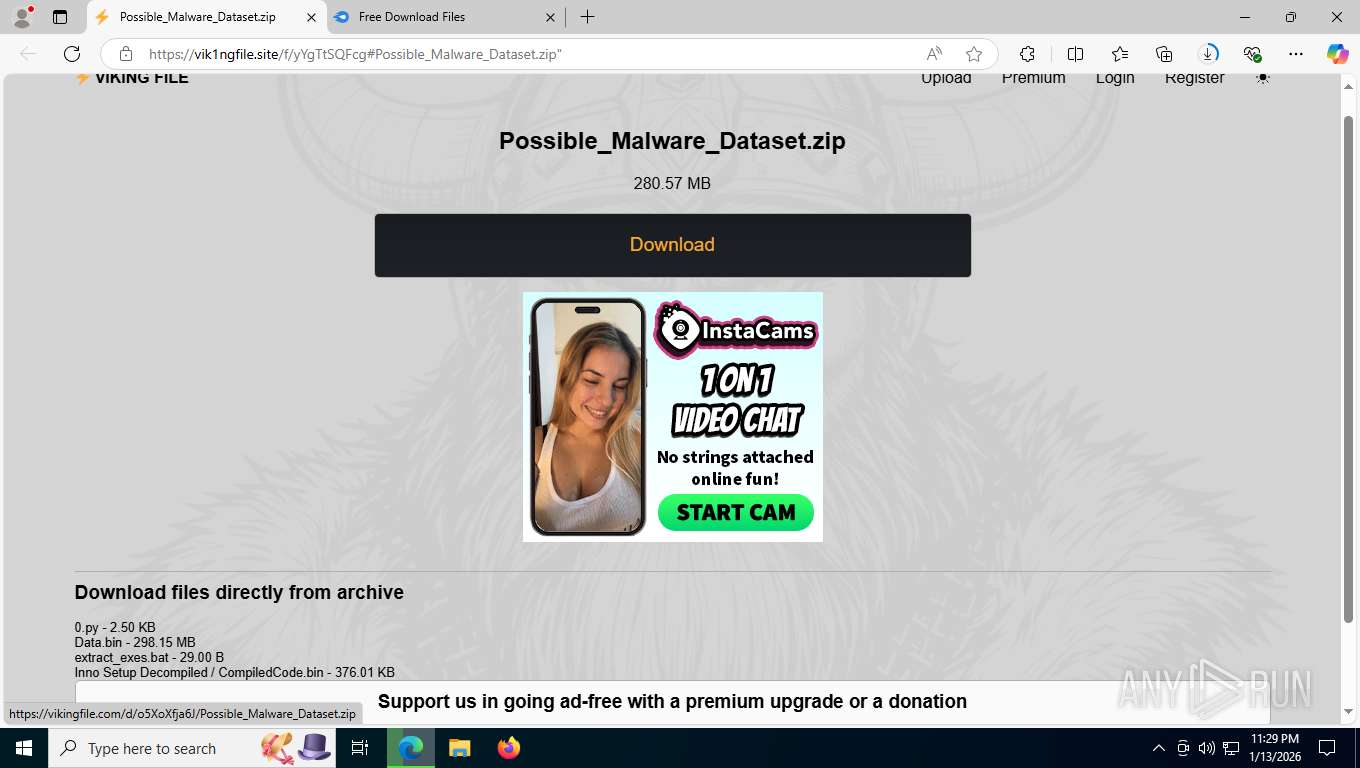
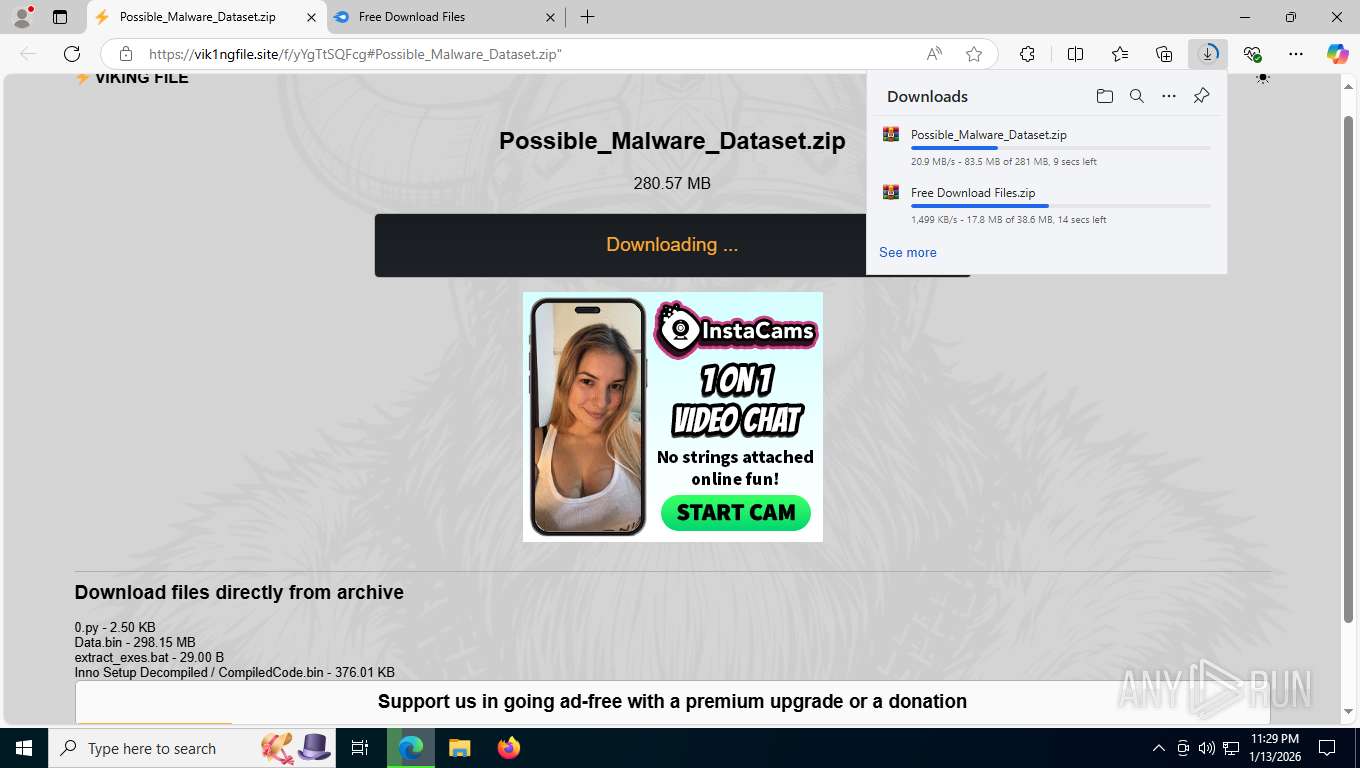
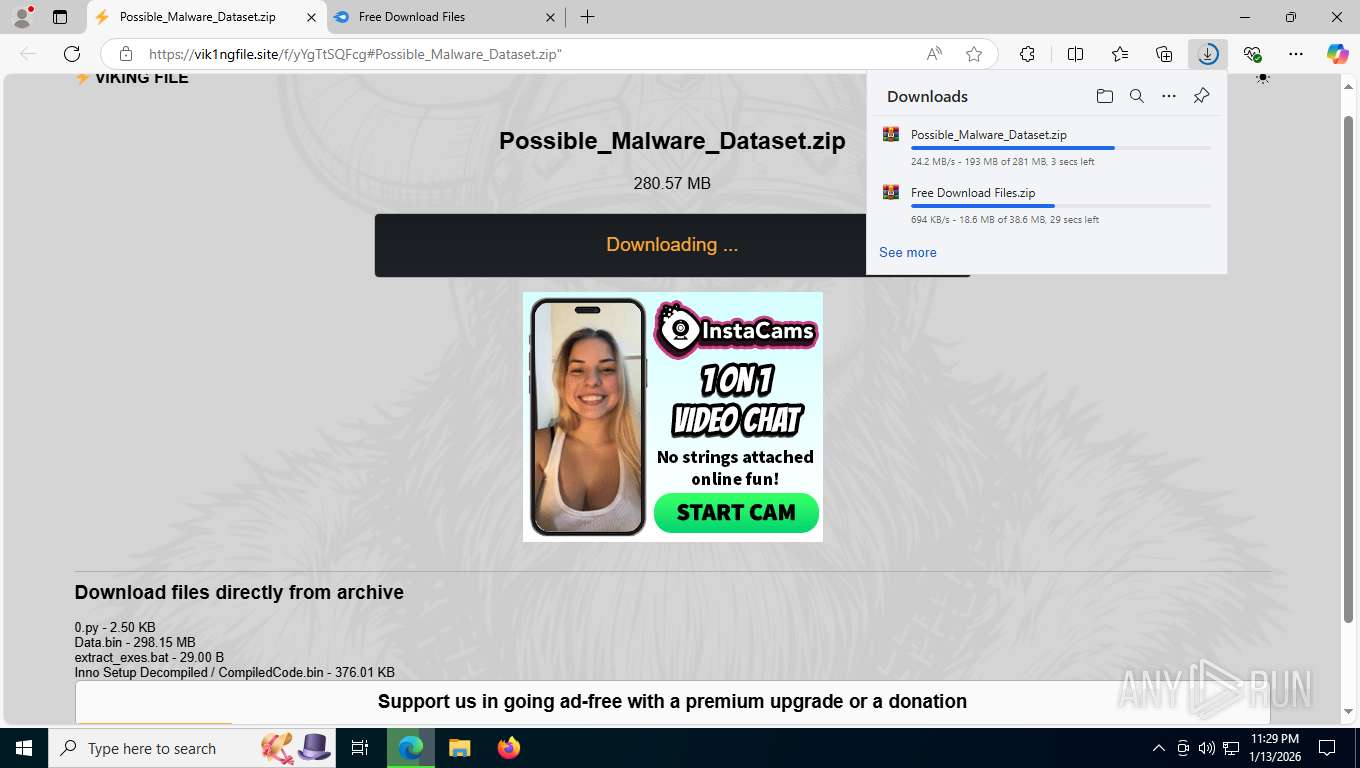
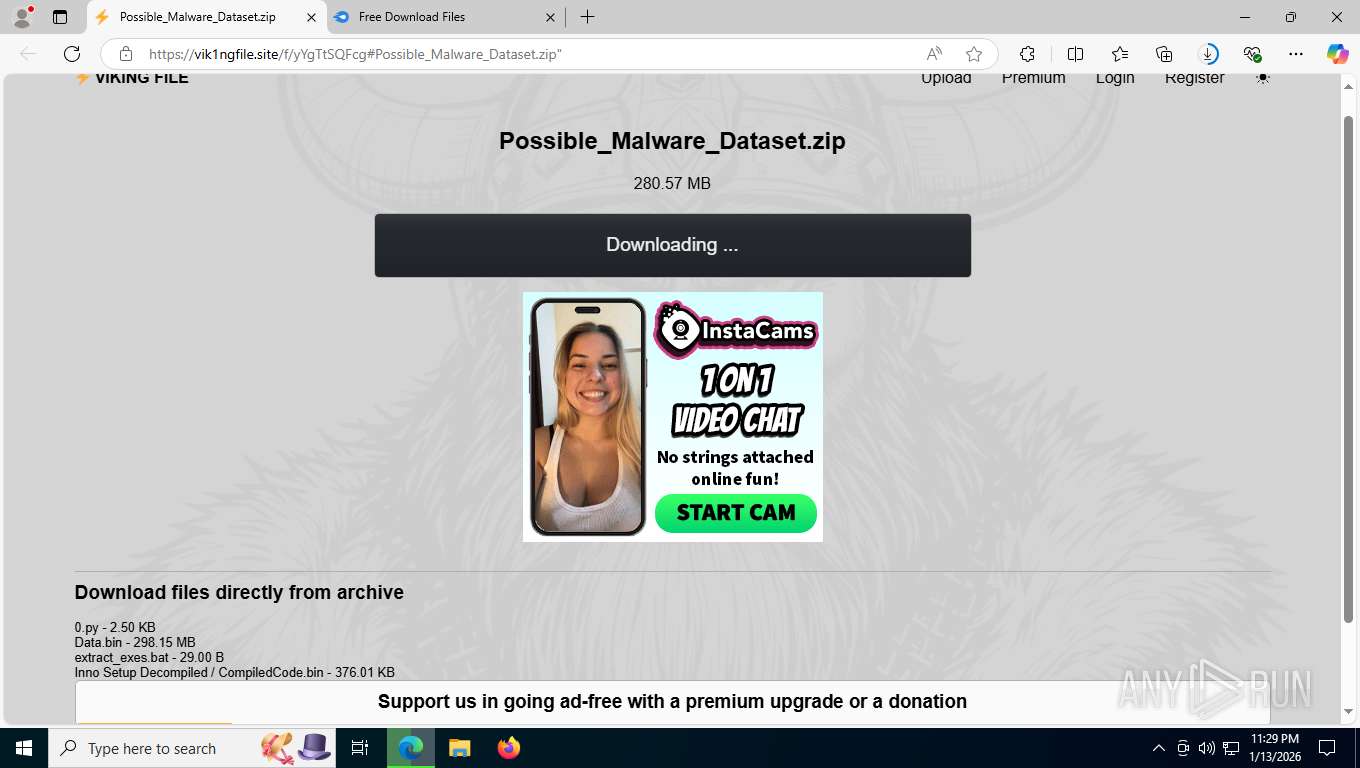
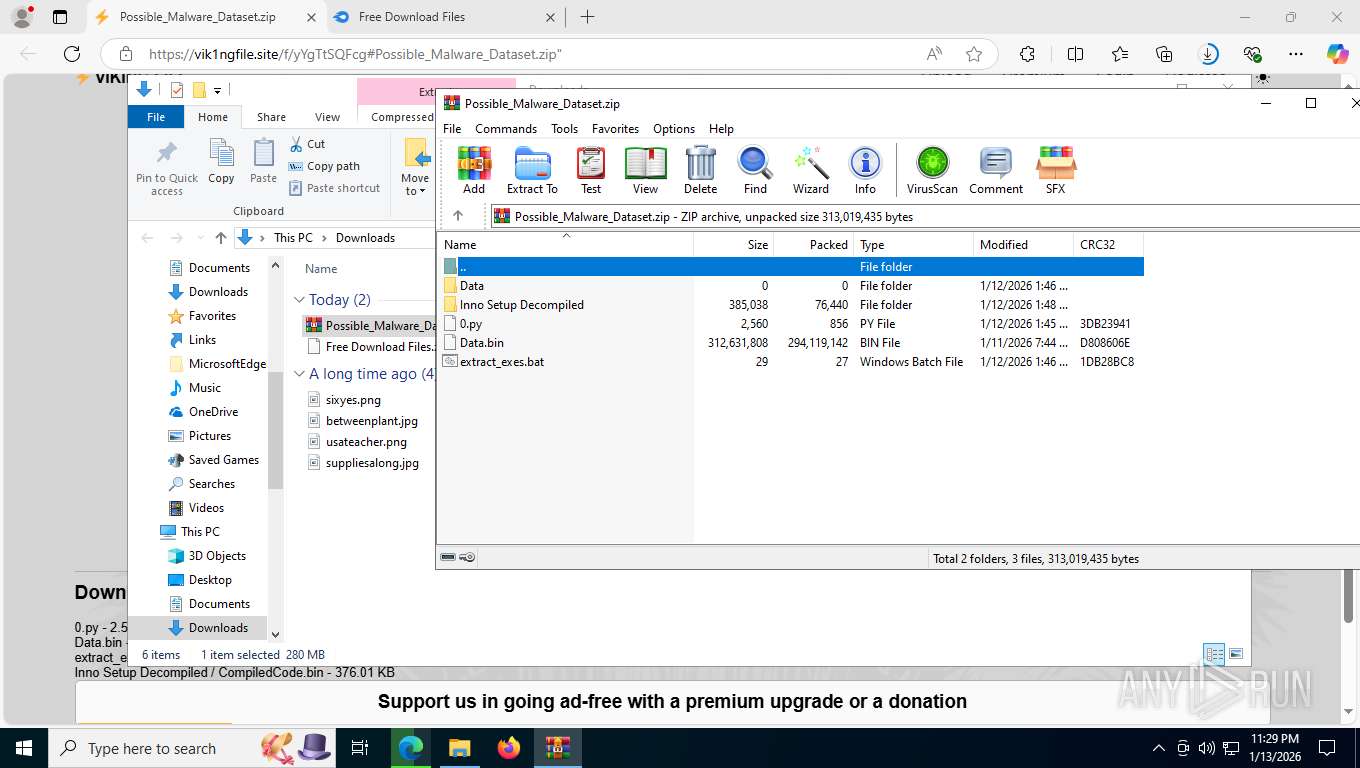
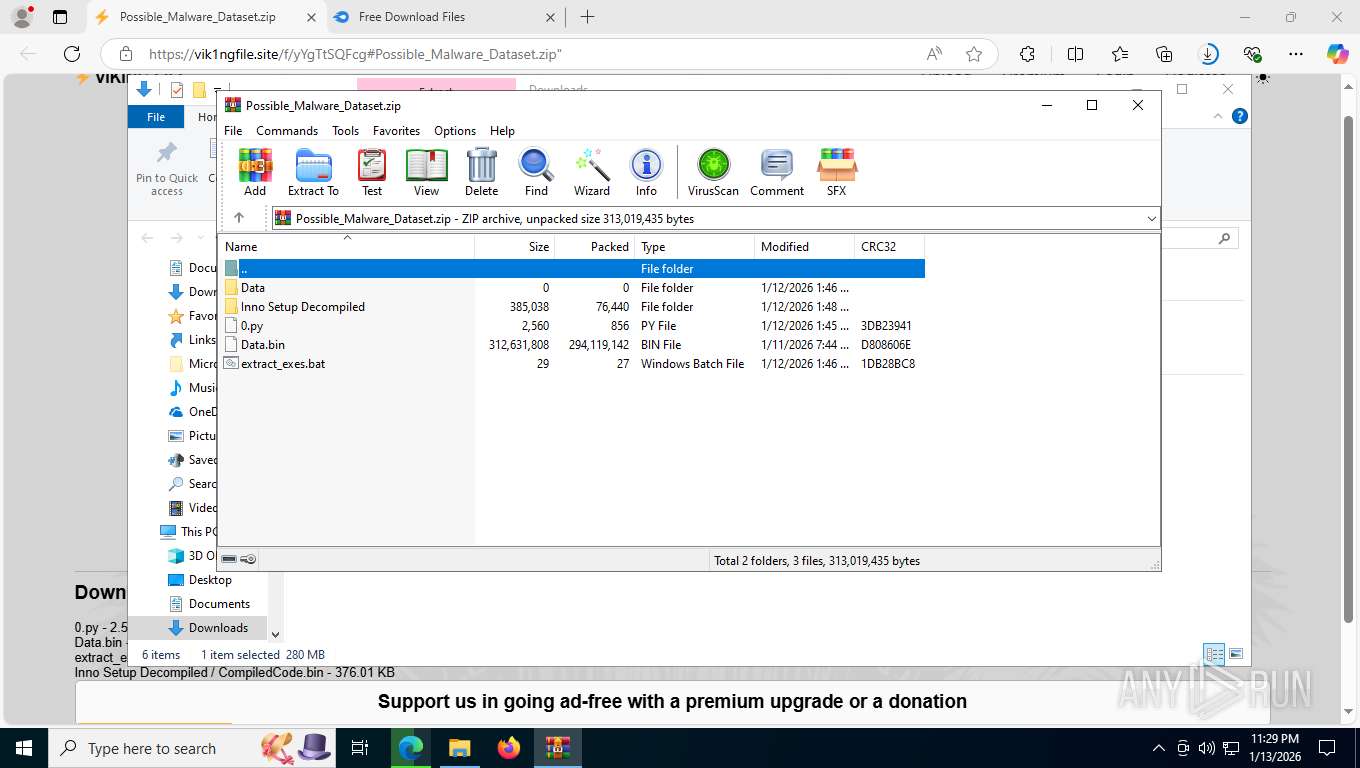
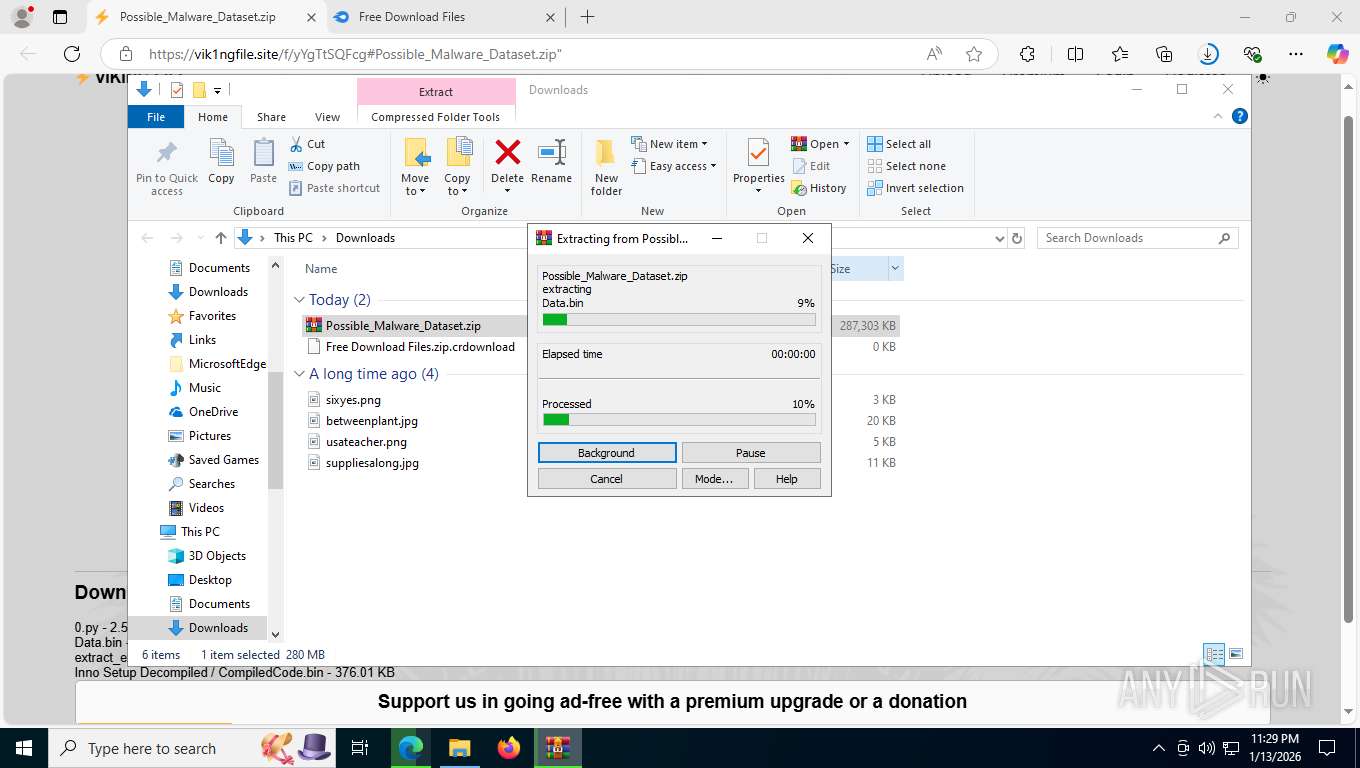
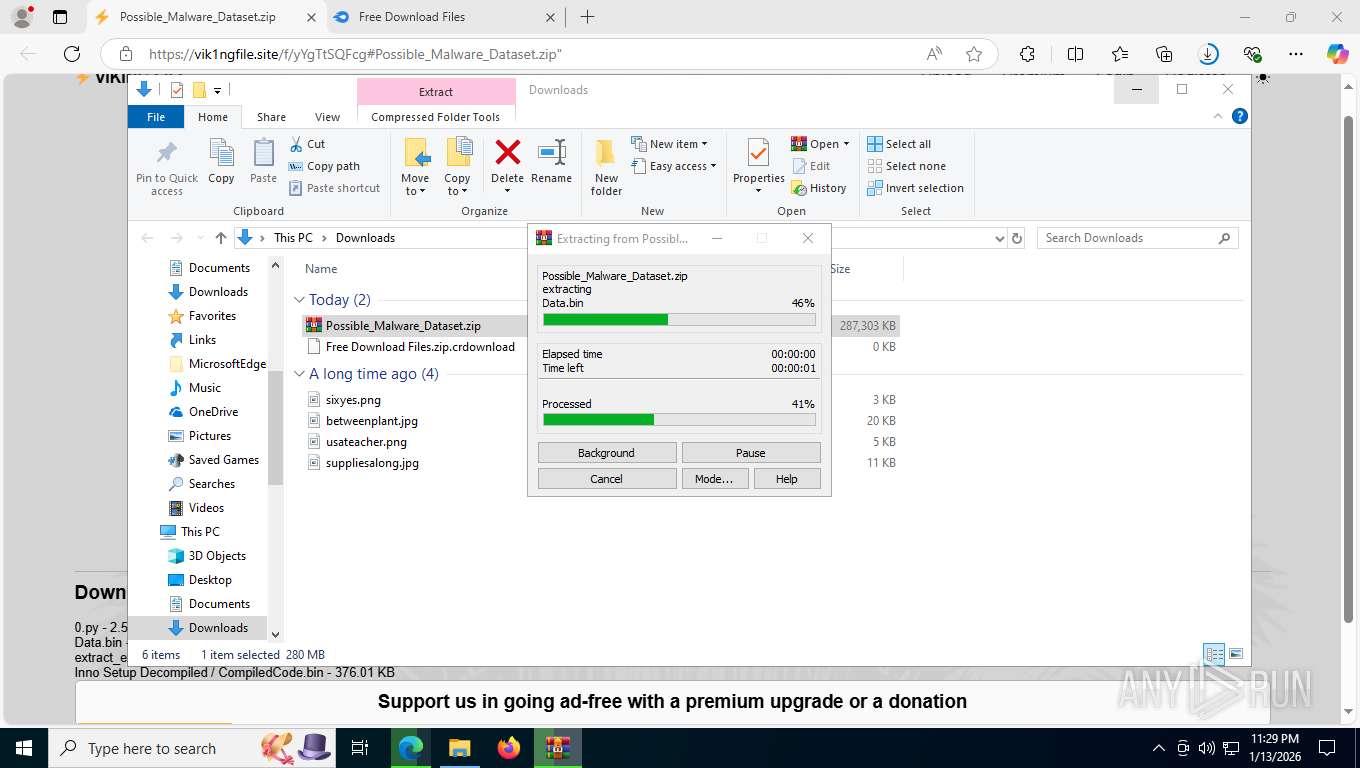
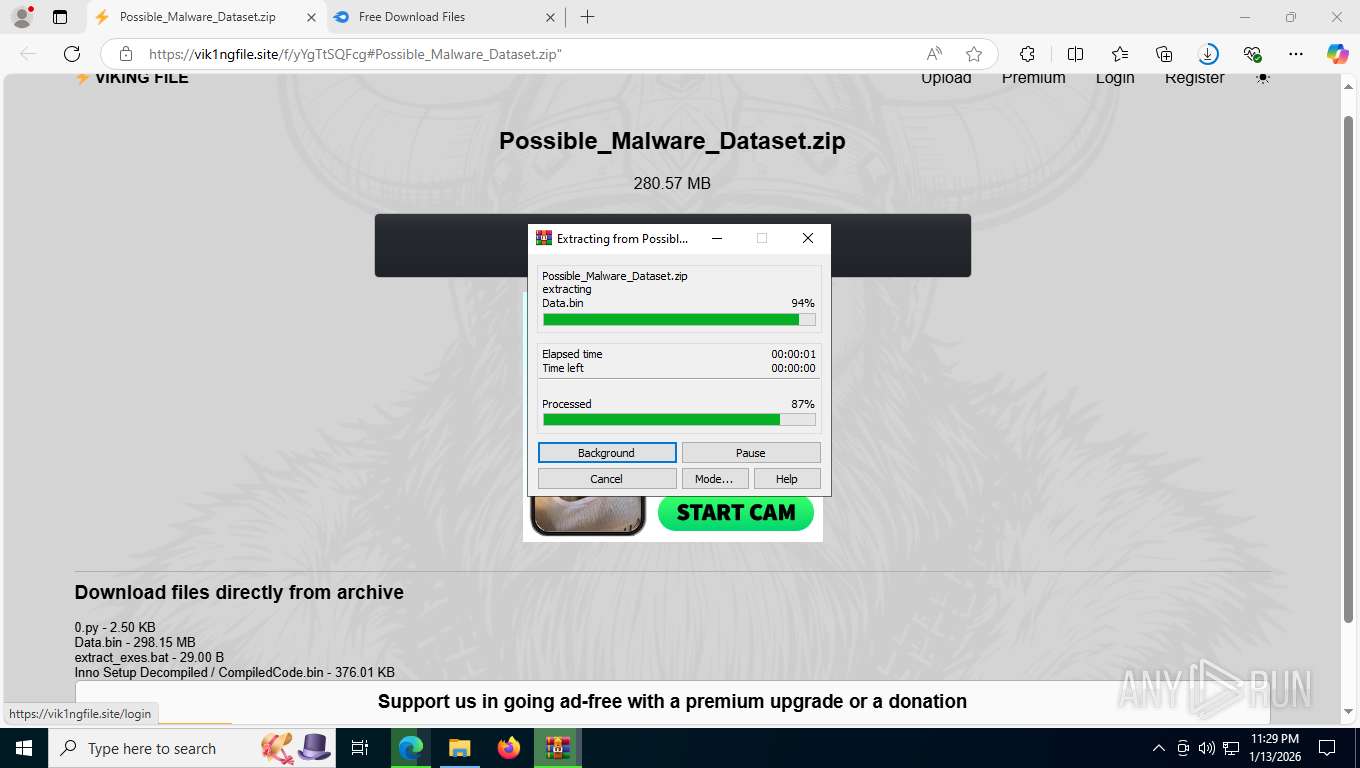
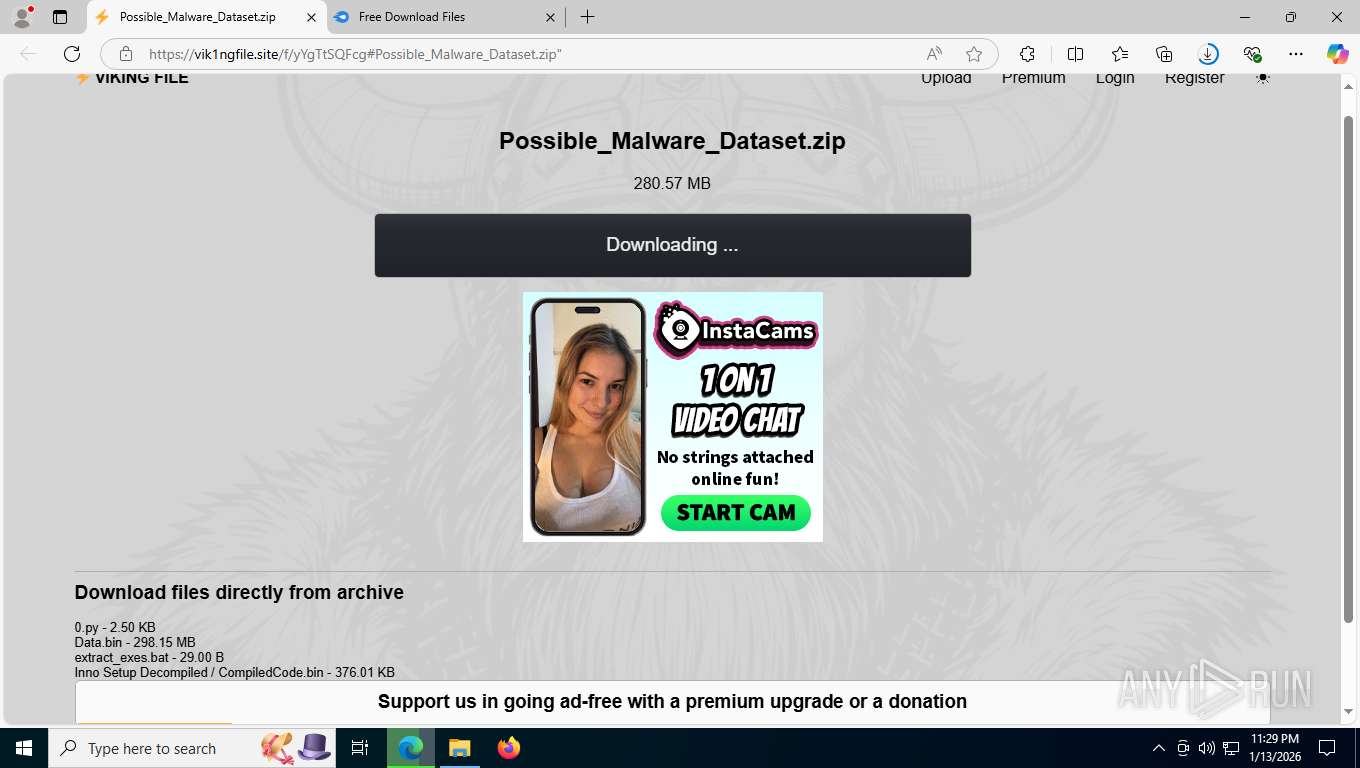
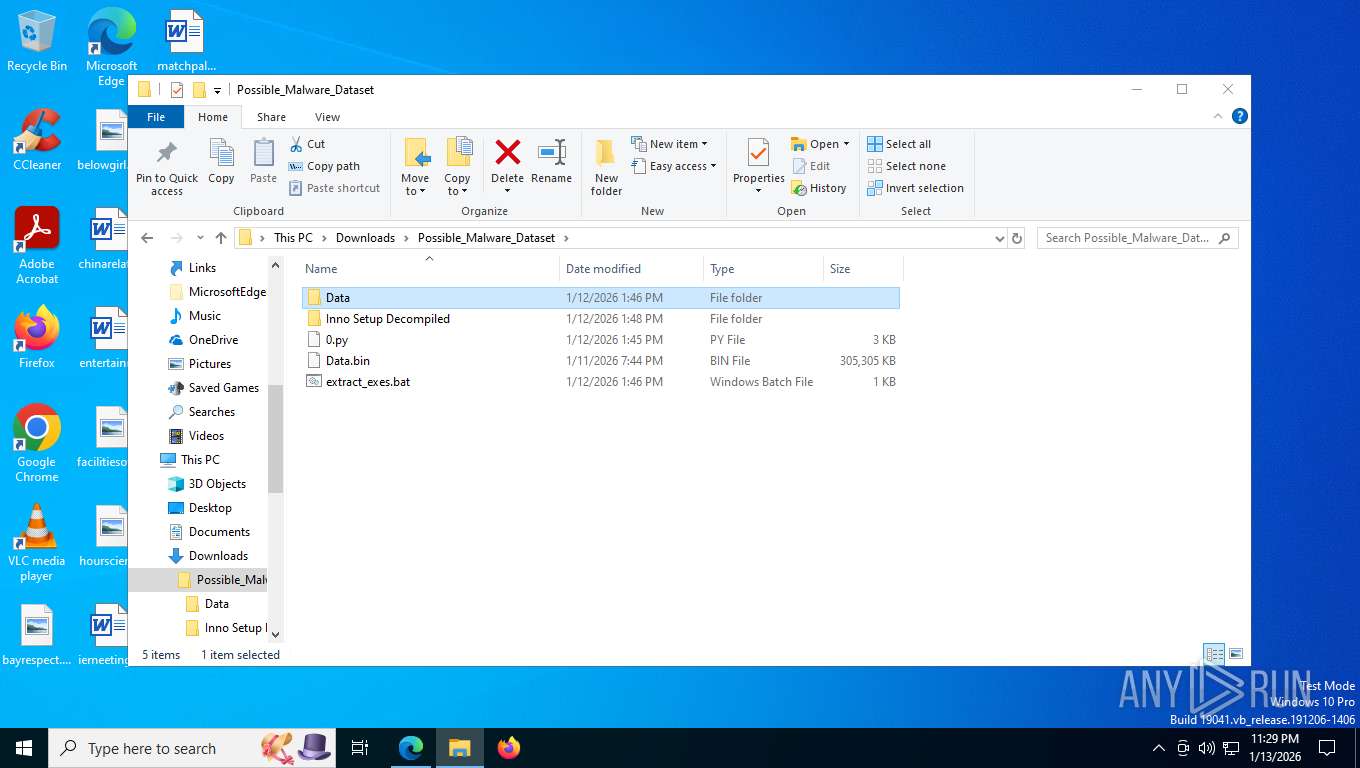
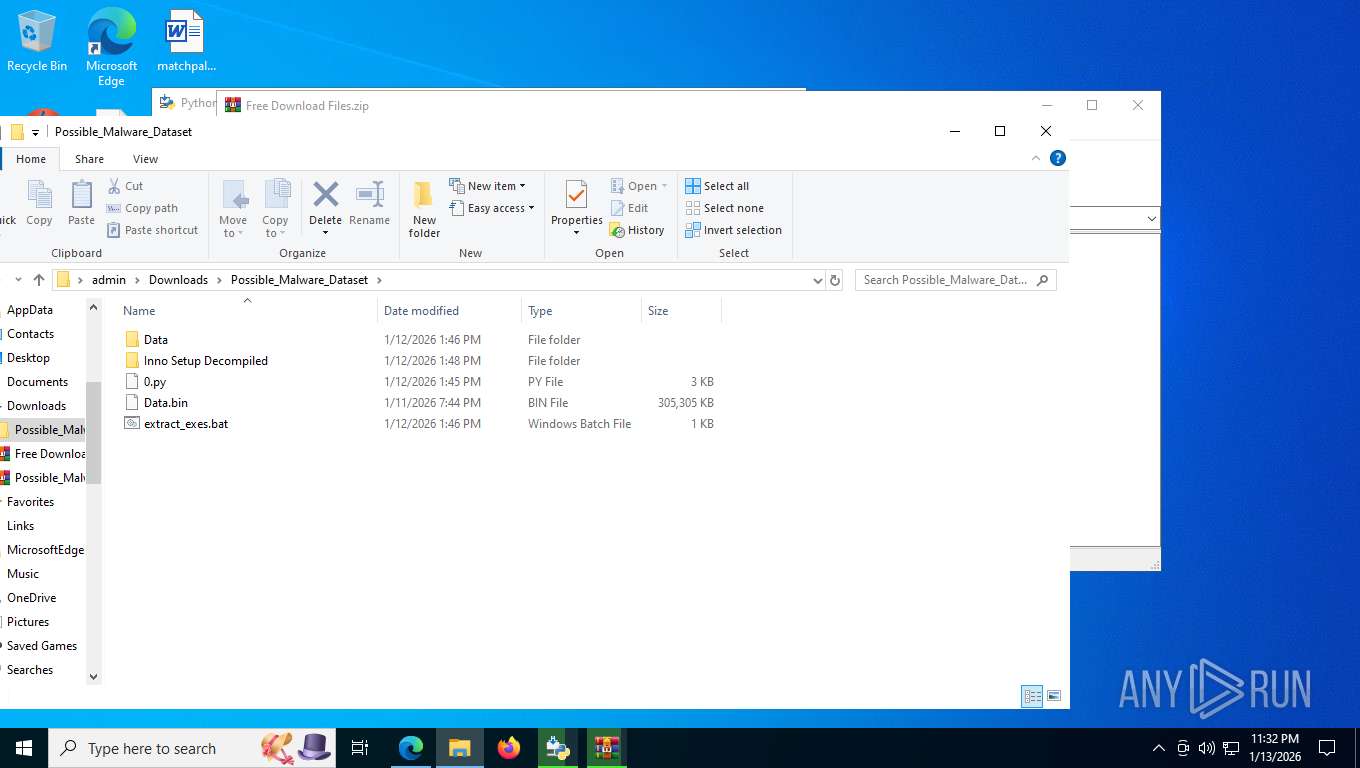
| URL: | https://vikingfile.com/f/yYgTtSQFcg#Possible_Malware_Dataset.zip%22 |
| Full analysis: | https://app.any.run/tasks/48cca64e-0492-4831-96a3-e3ca376c941b |
| Verdict: | Malicious activity |
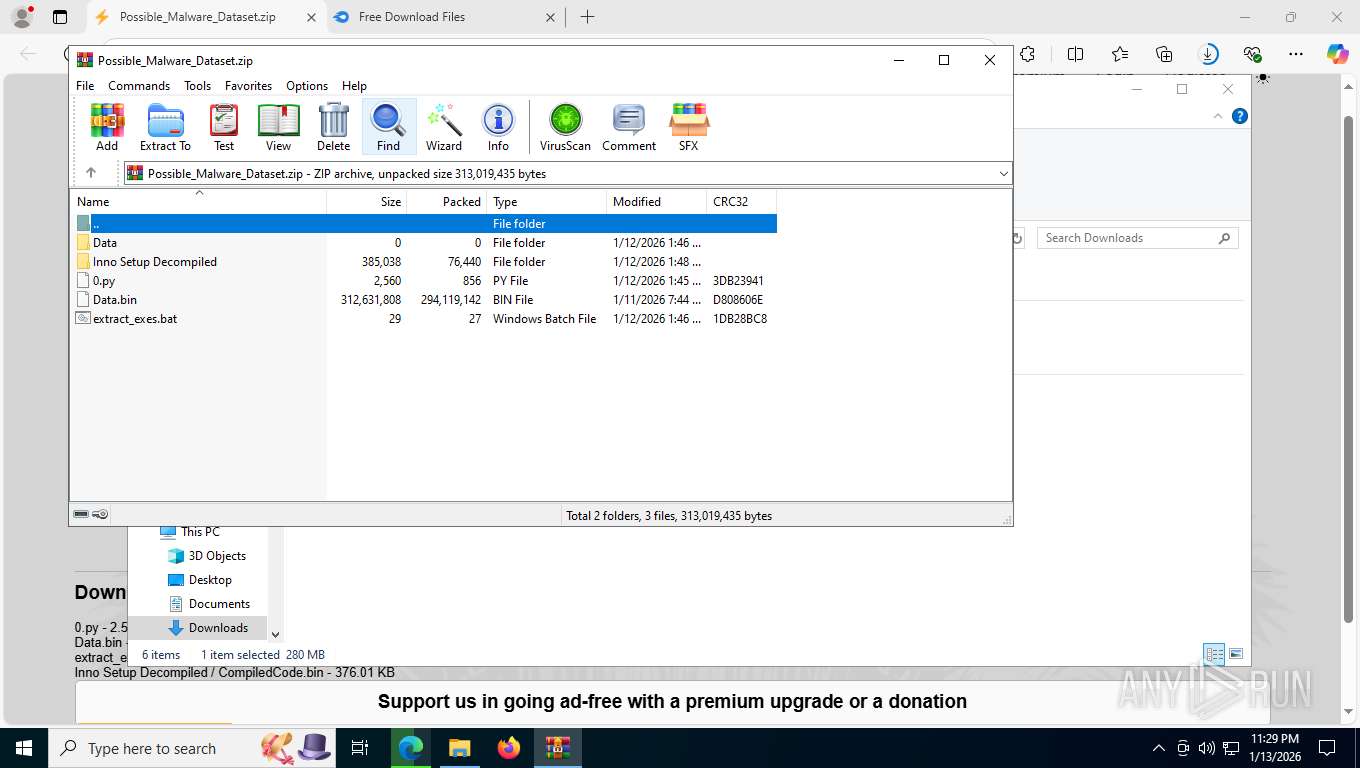
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 14, 2026, 04:28:22 |
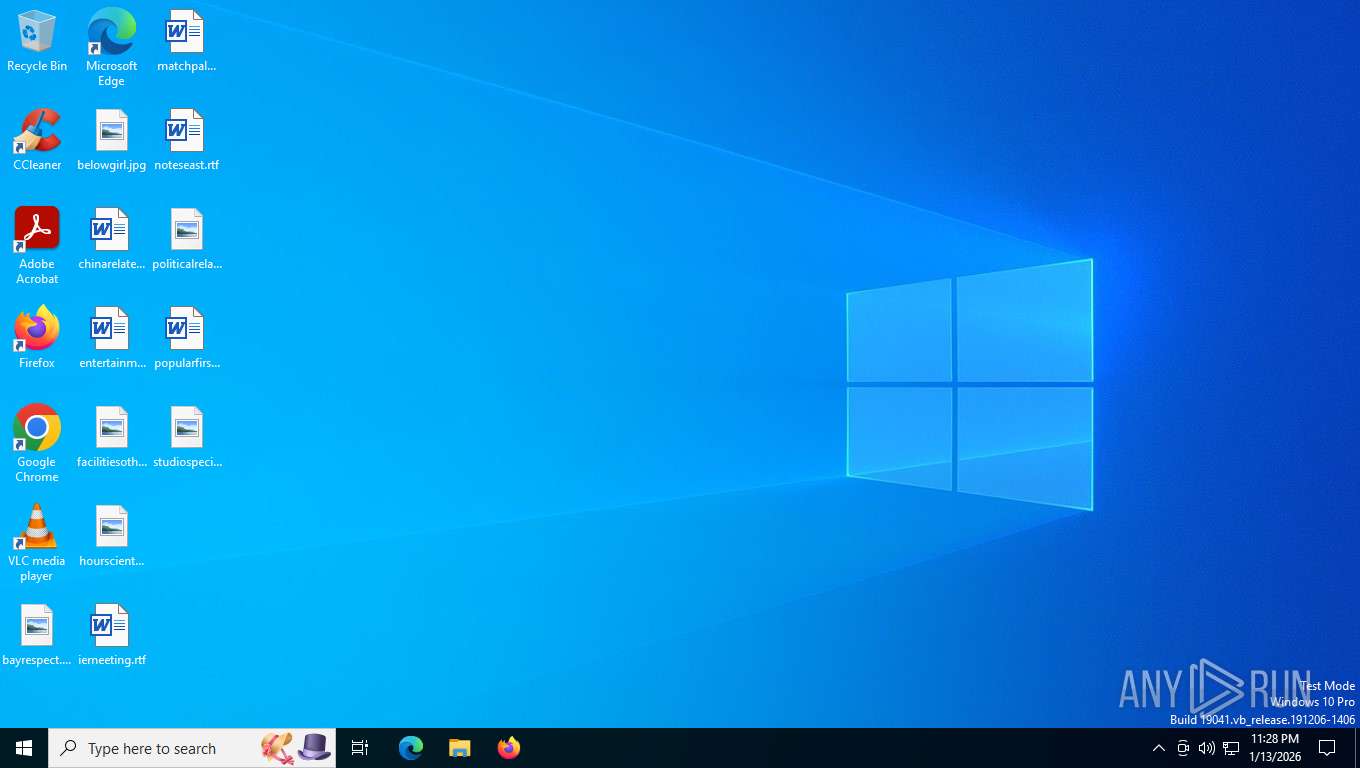
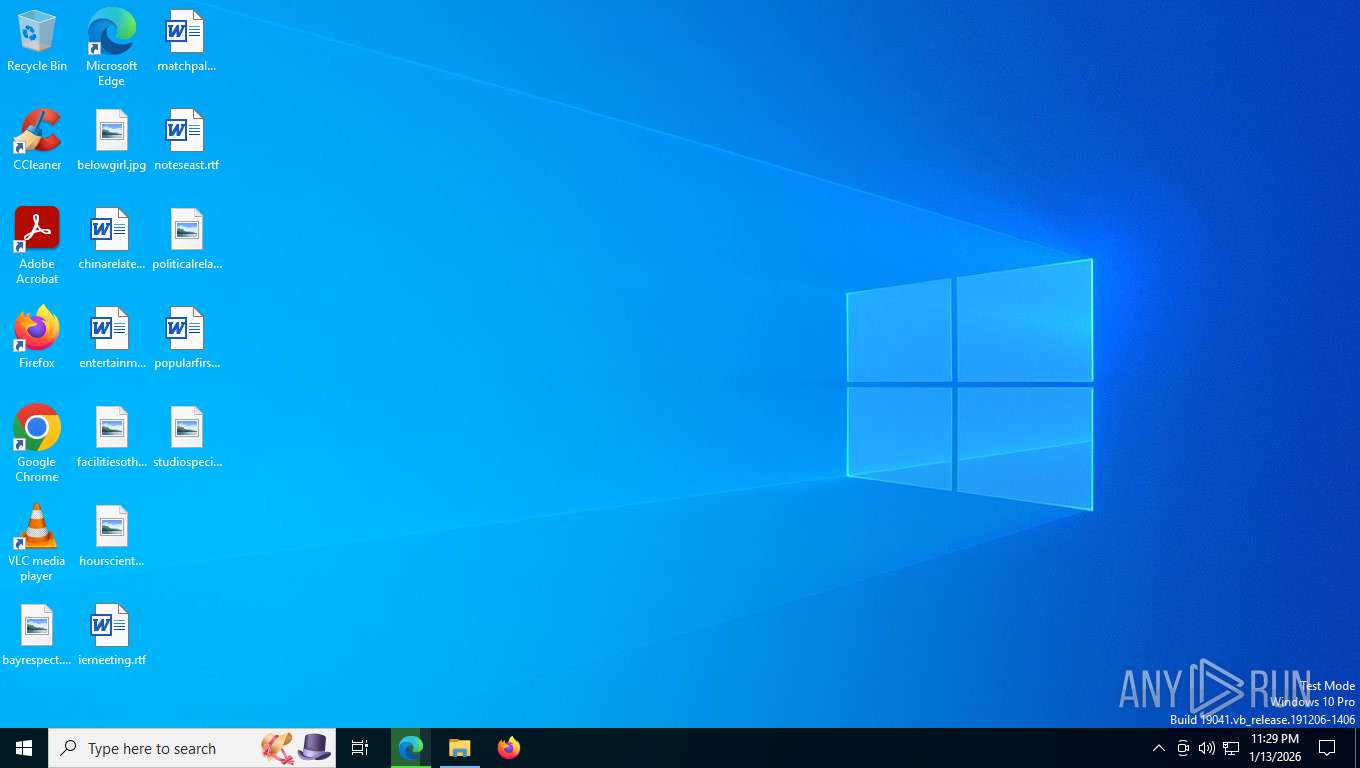
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0B2228776CEBEA813641ADA3DFAC497C |
| SHA1: | E2F04A6F4DC9459FD5D67825716FB7563D21C254 |
| SHA256: | 5E87D18C8573DE1964C83C81C125FCAFFA8EF81A4A2D35B5E63BB71E799185D7 |
| SSDEEP: | 3:N8BMzAyUKcfWzV3JttMVE:2BMzAyTdz |
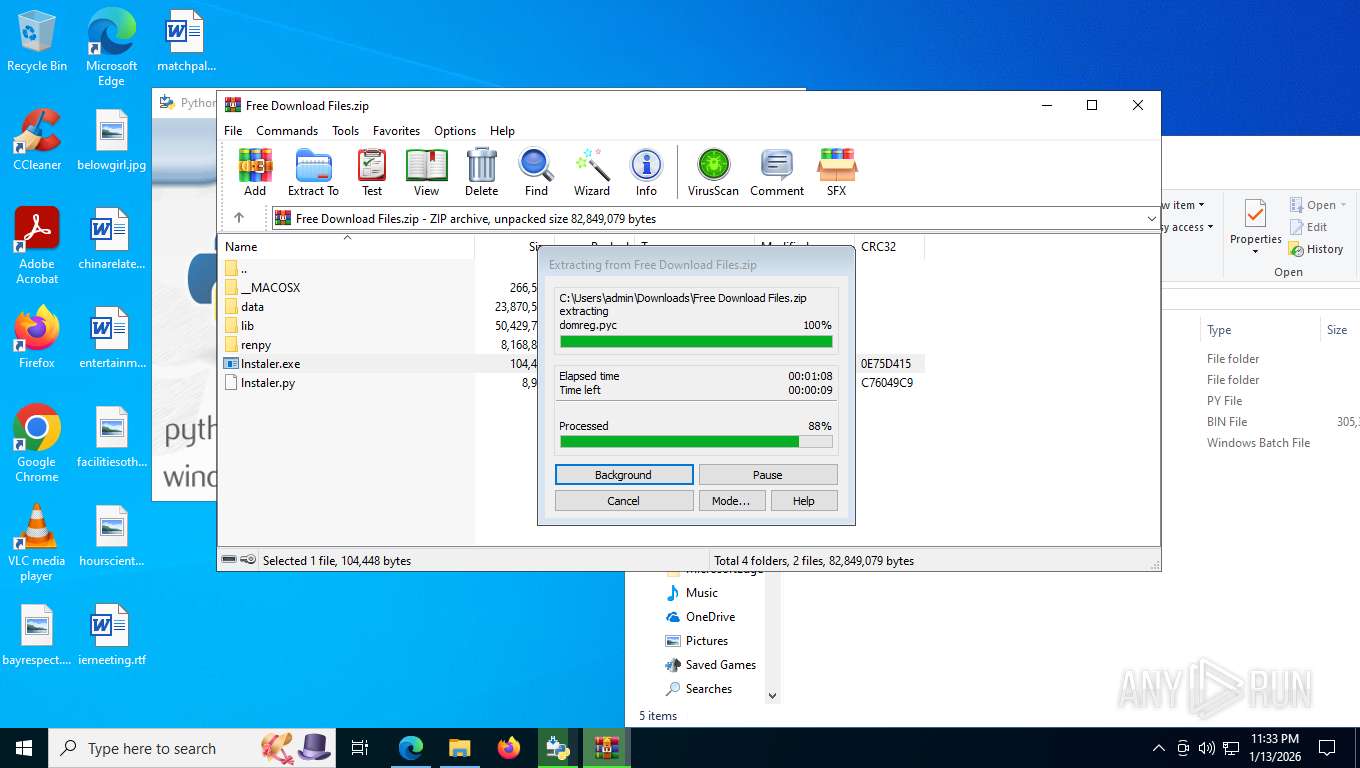
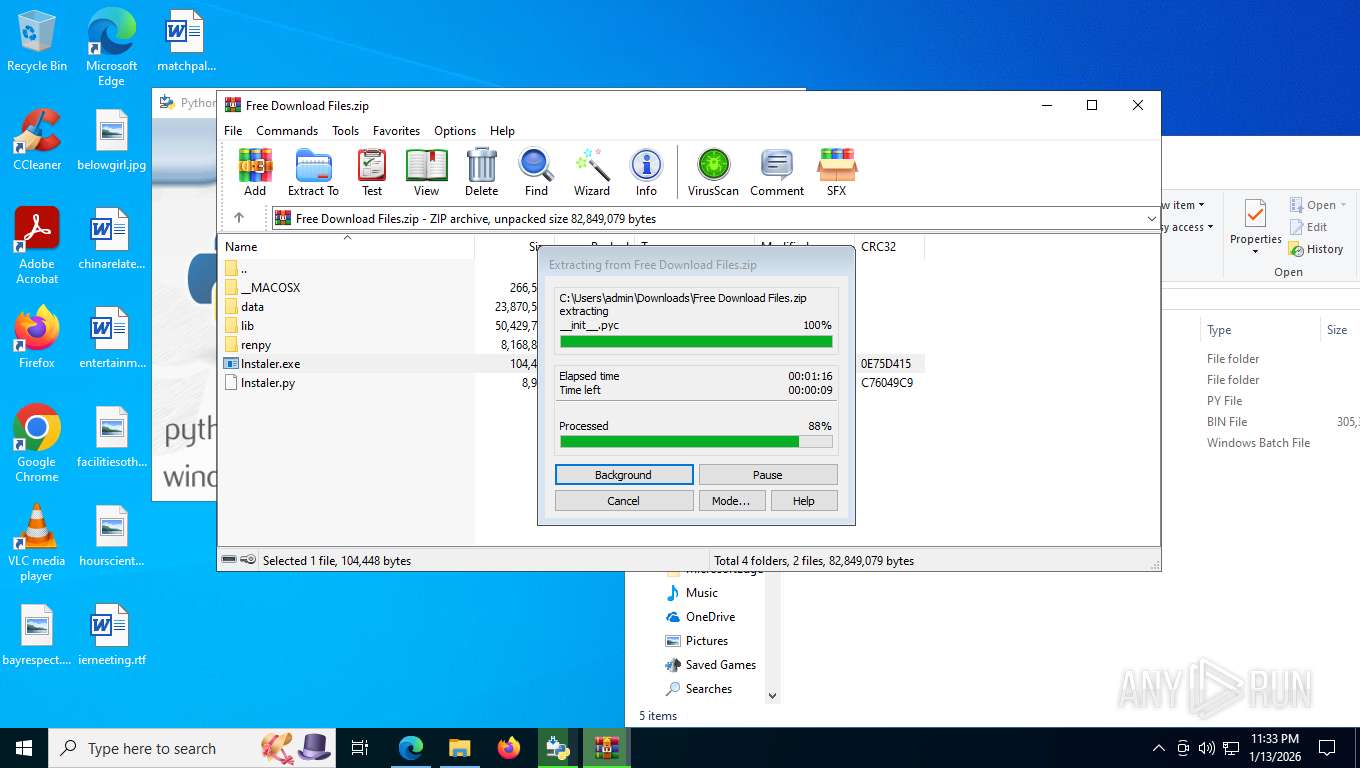
MALICIOUS
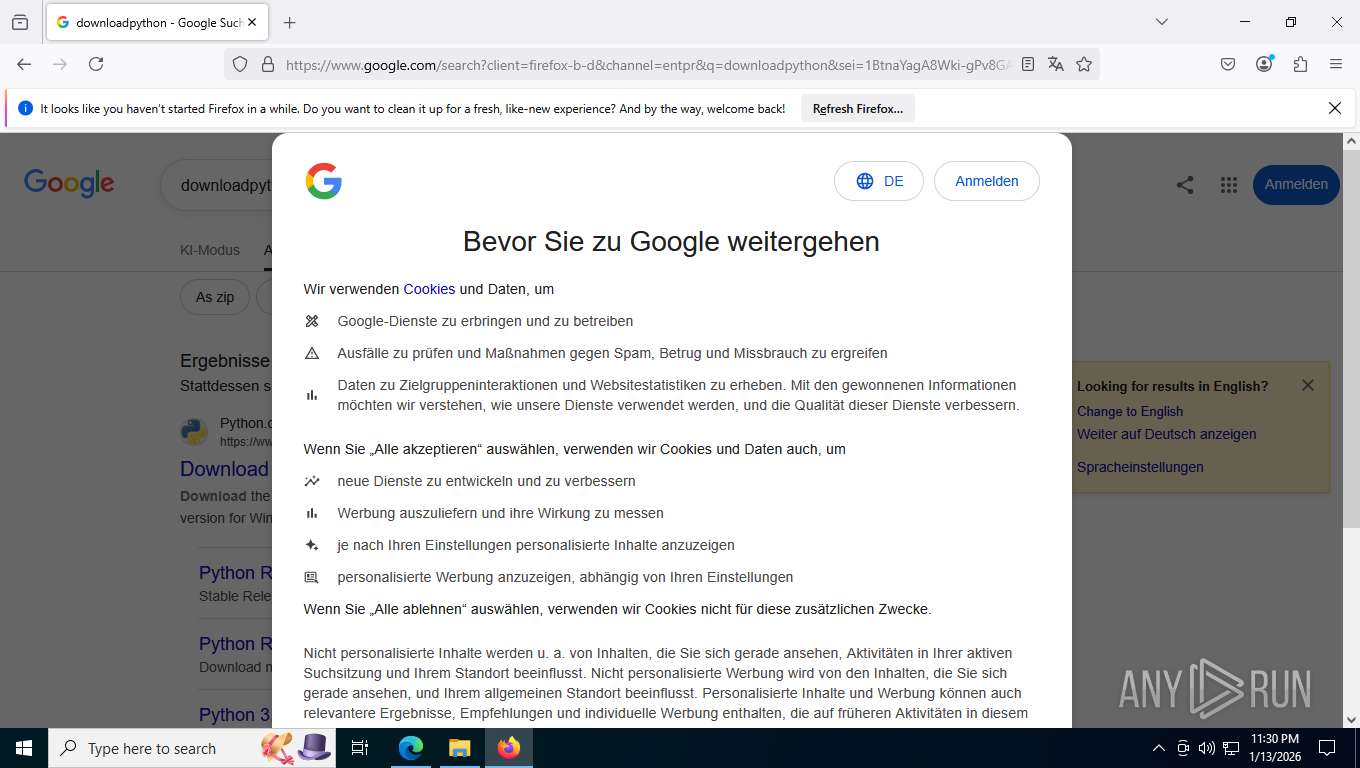
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7944)
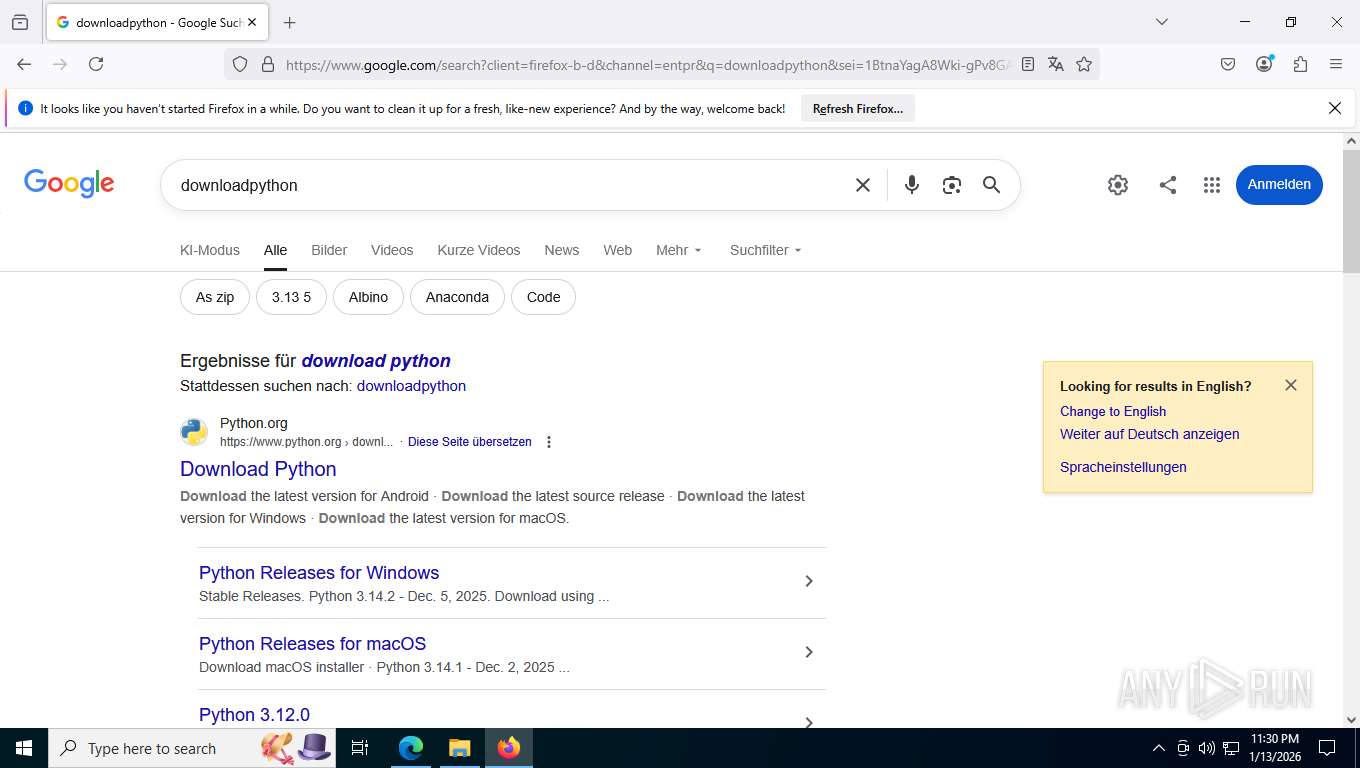
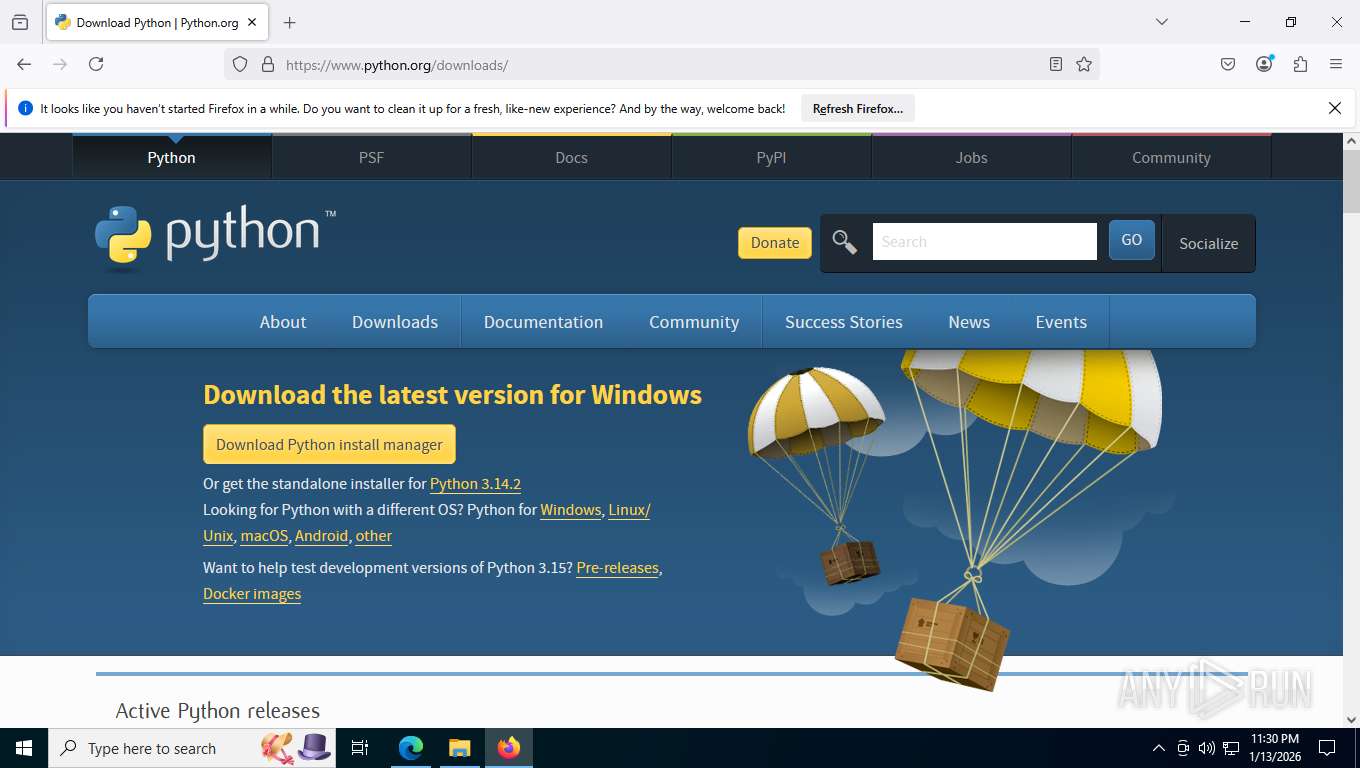
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 7944)
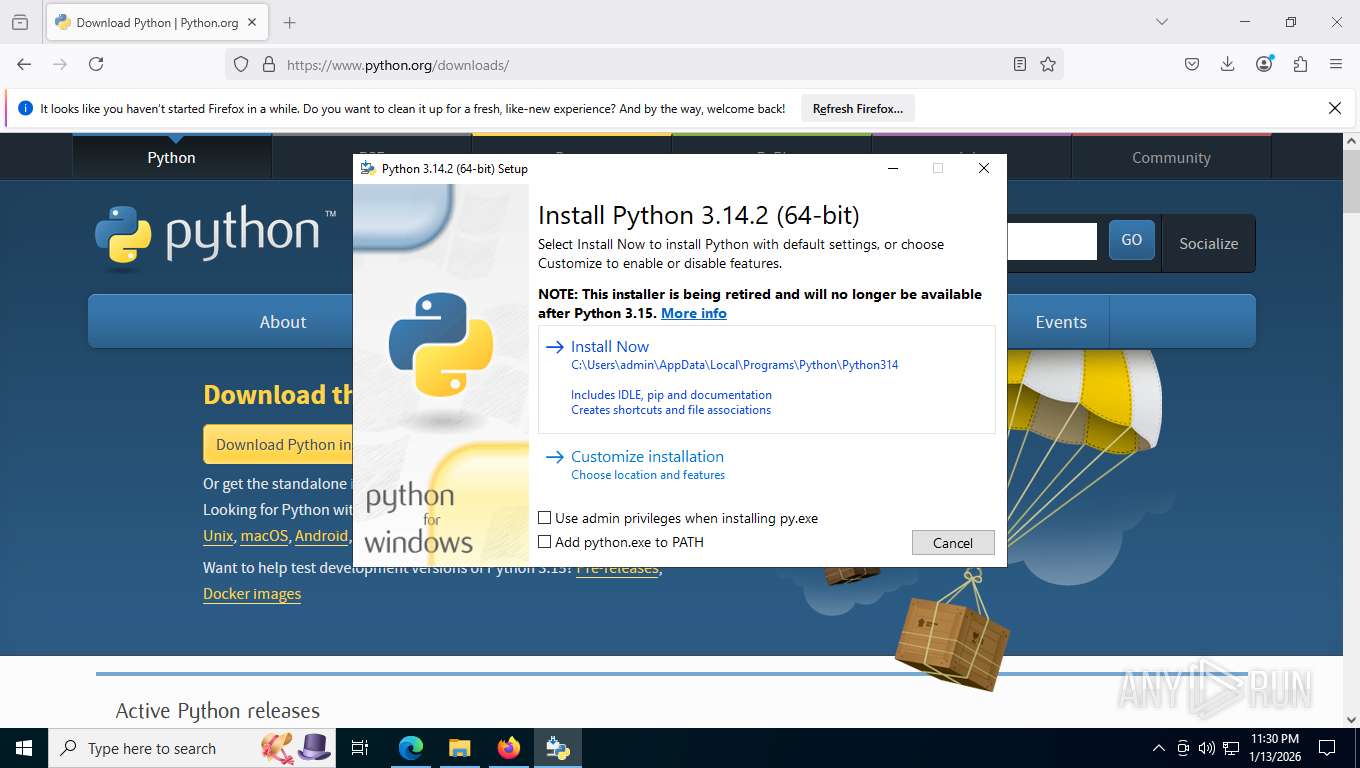
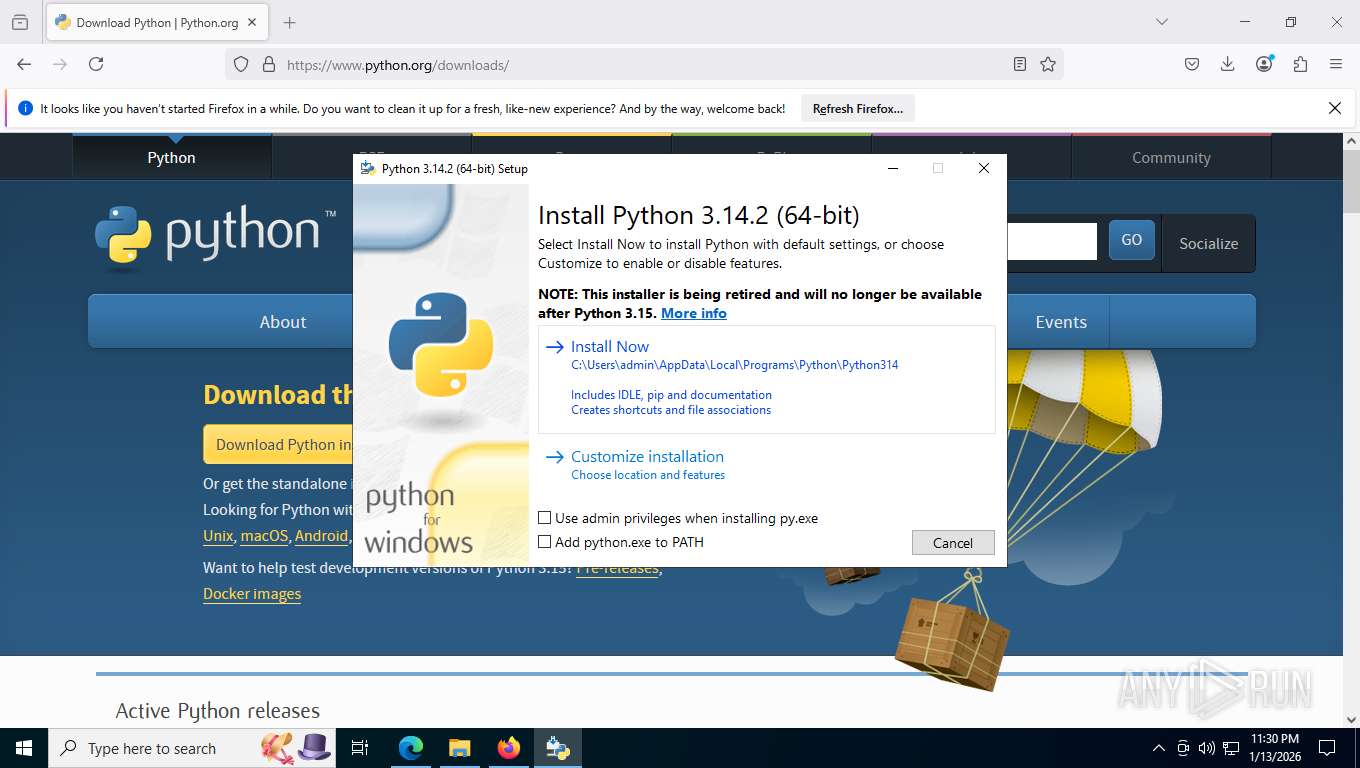
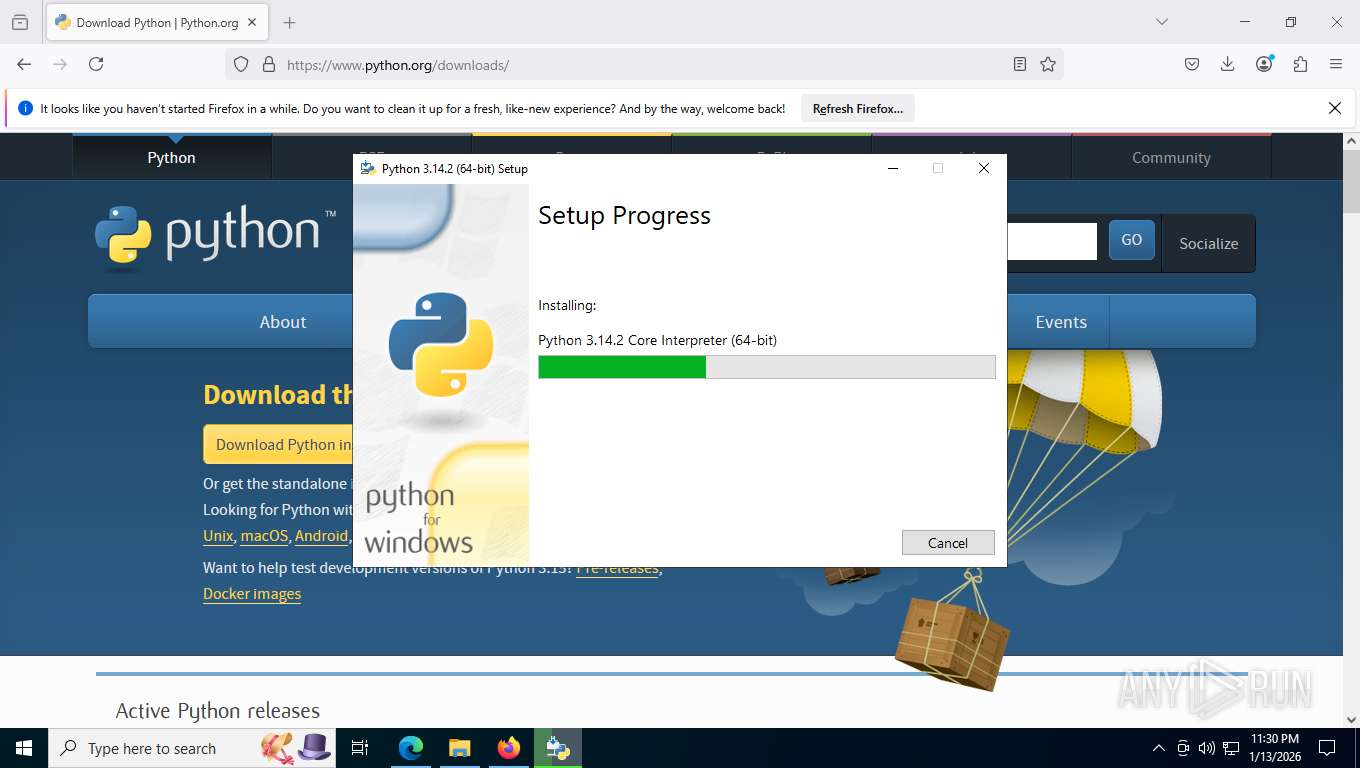
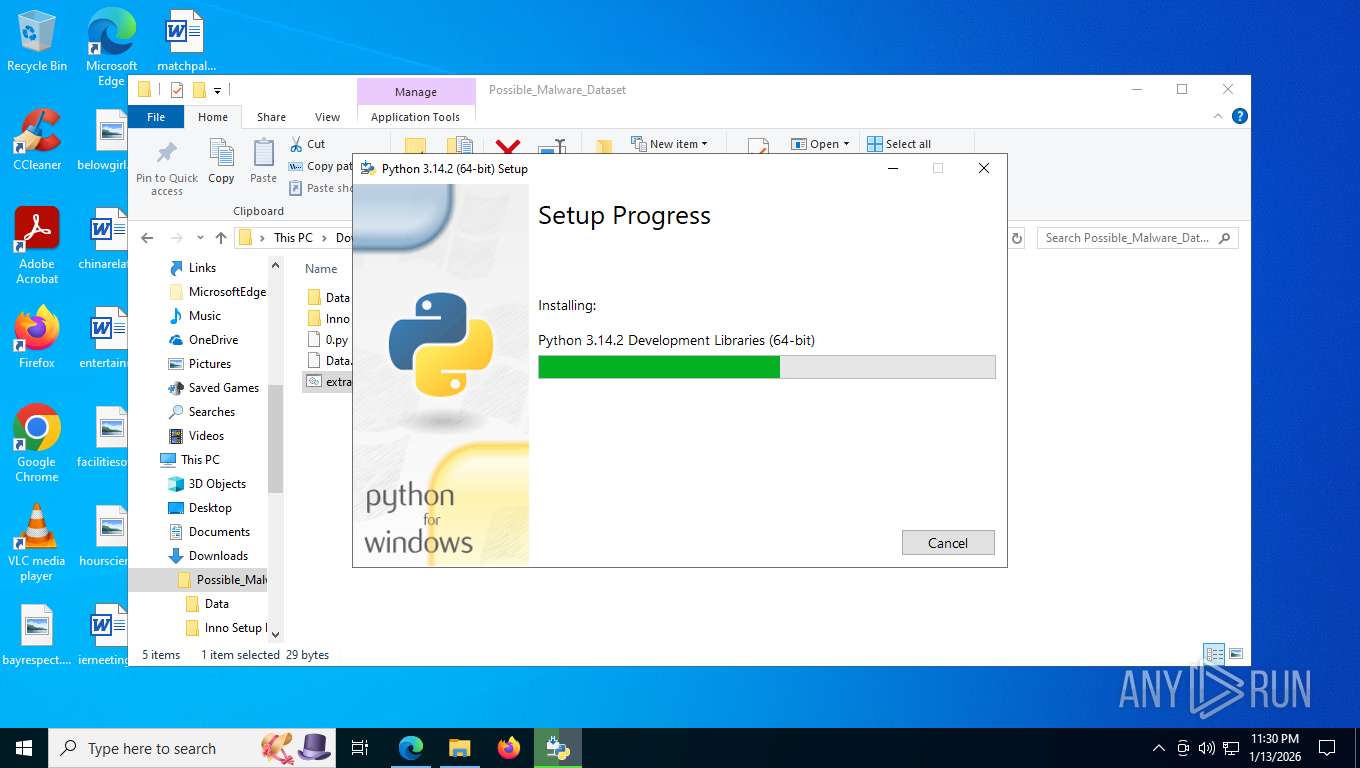
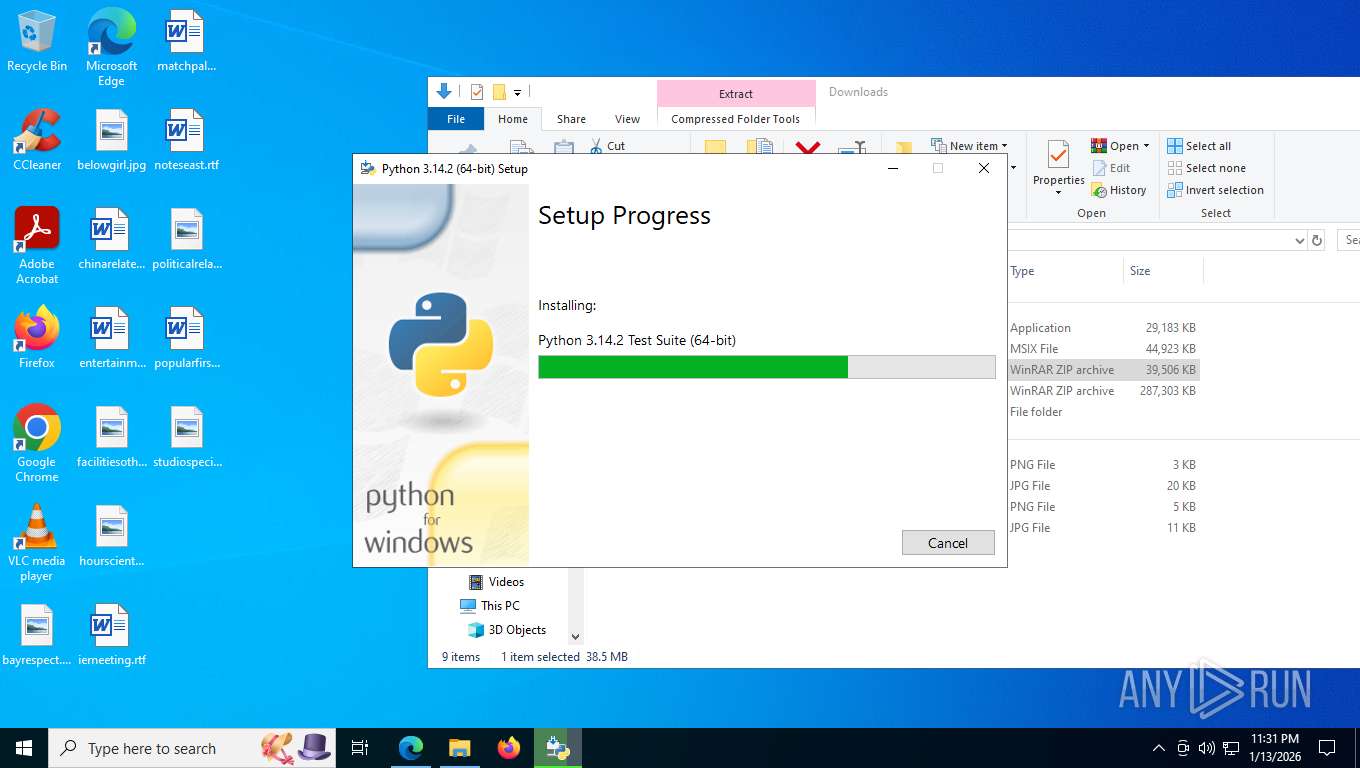
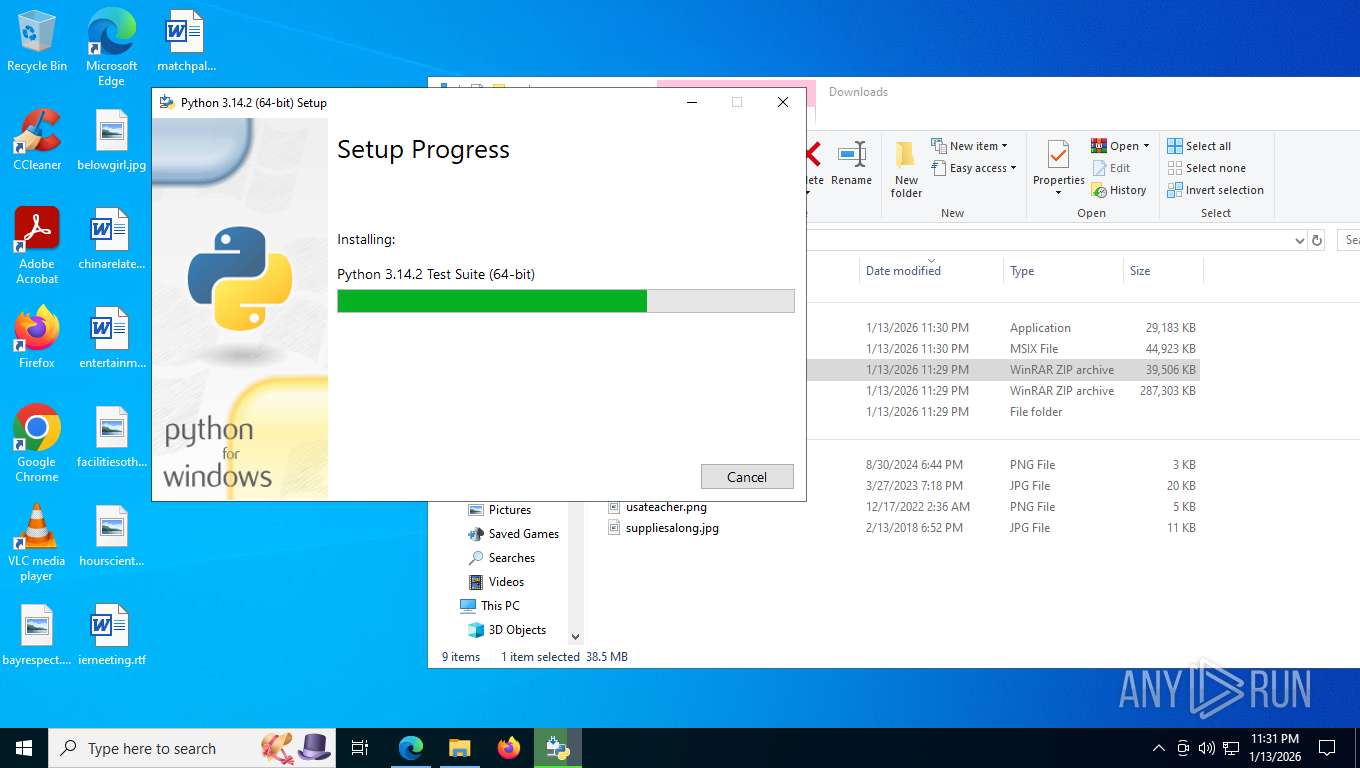
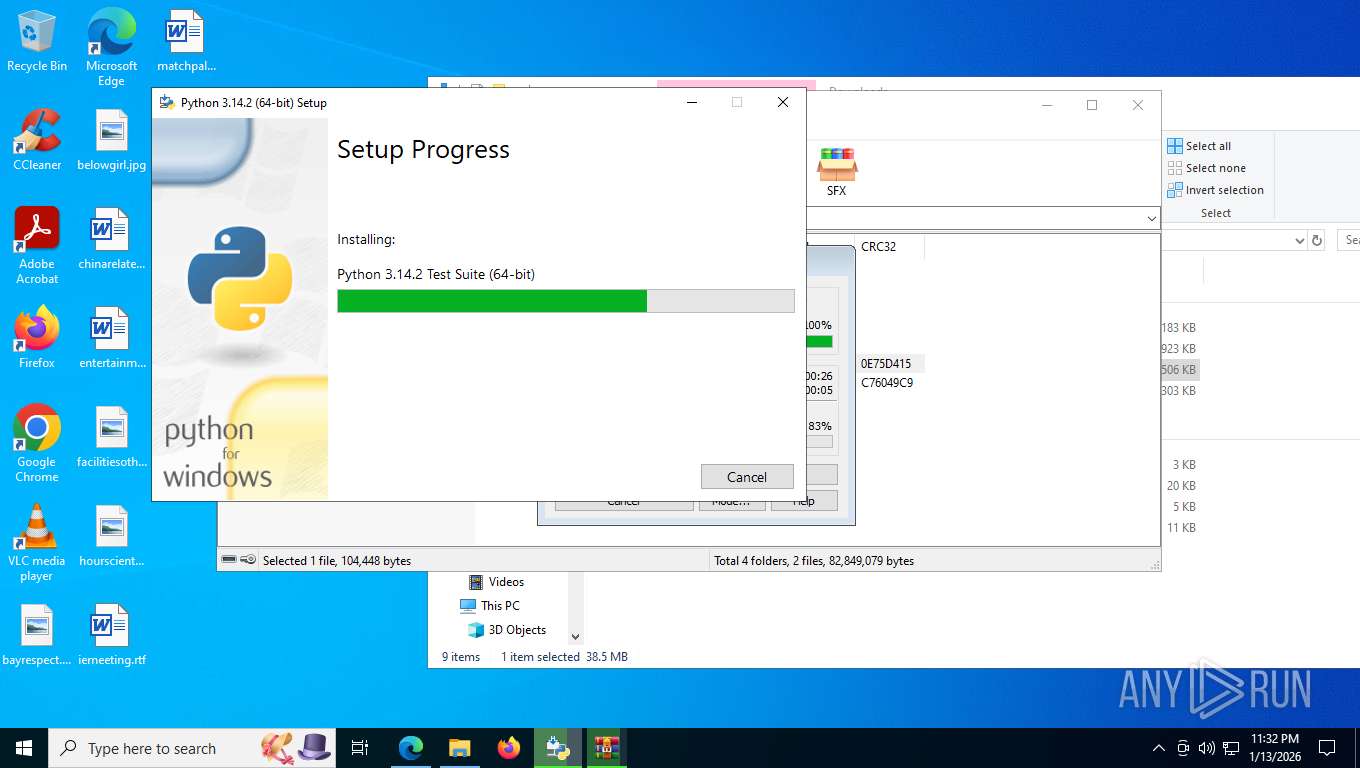
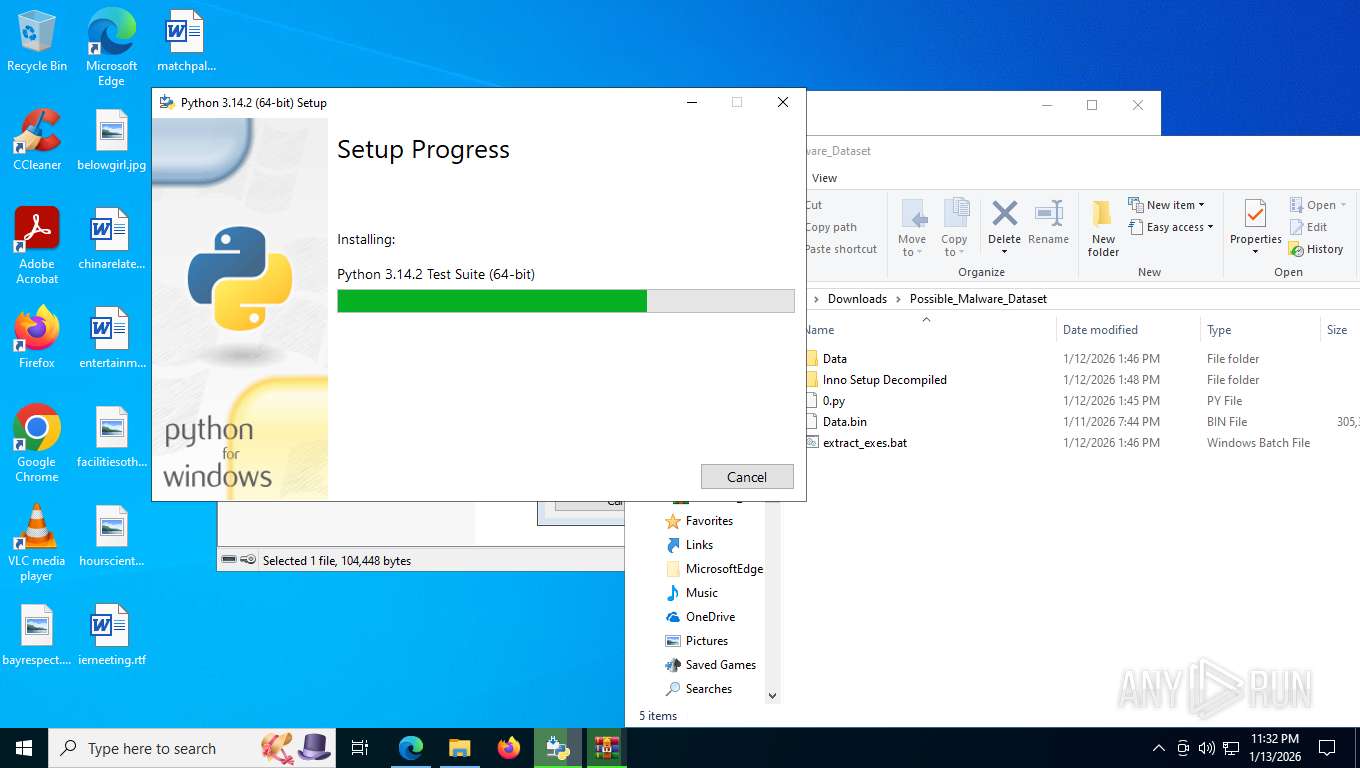
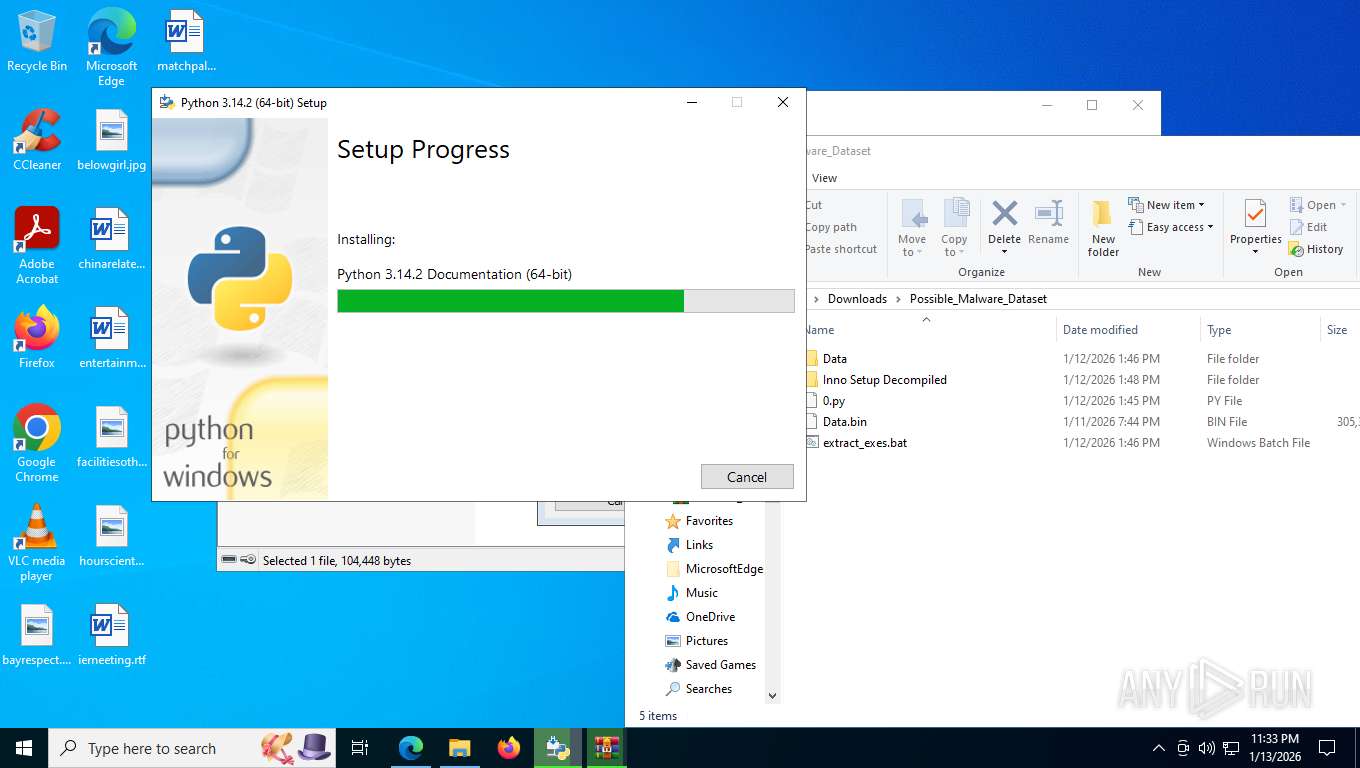
Changes the autorun value in the registry
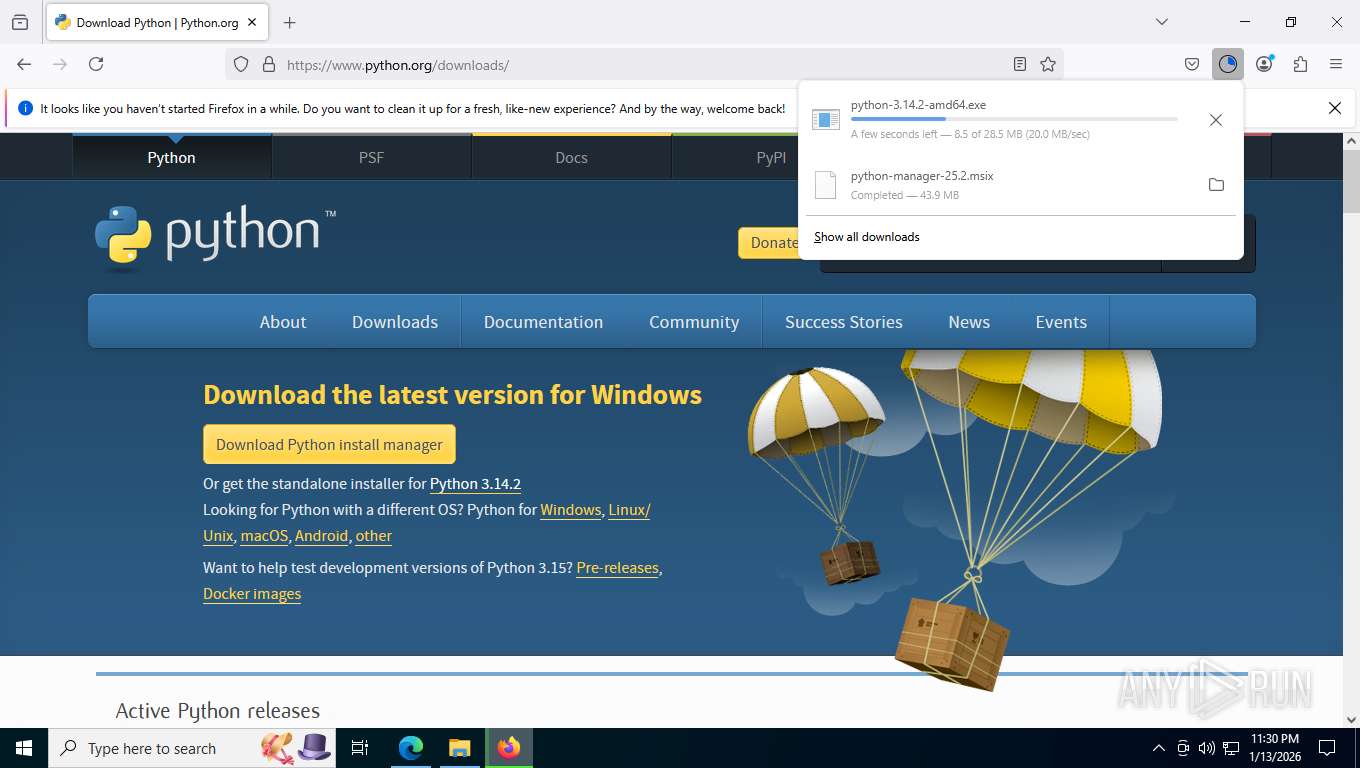
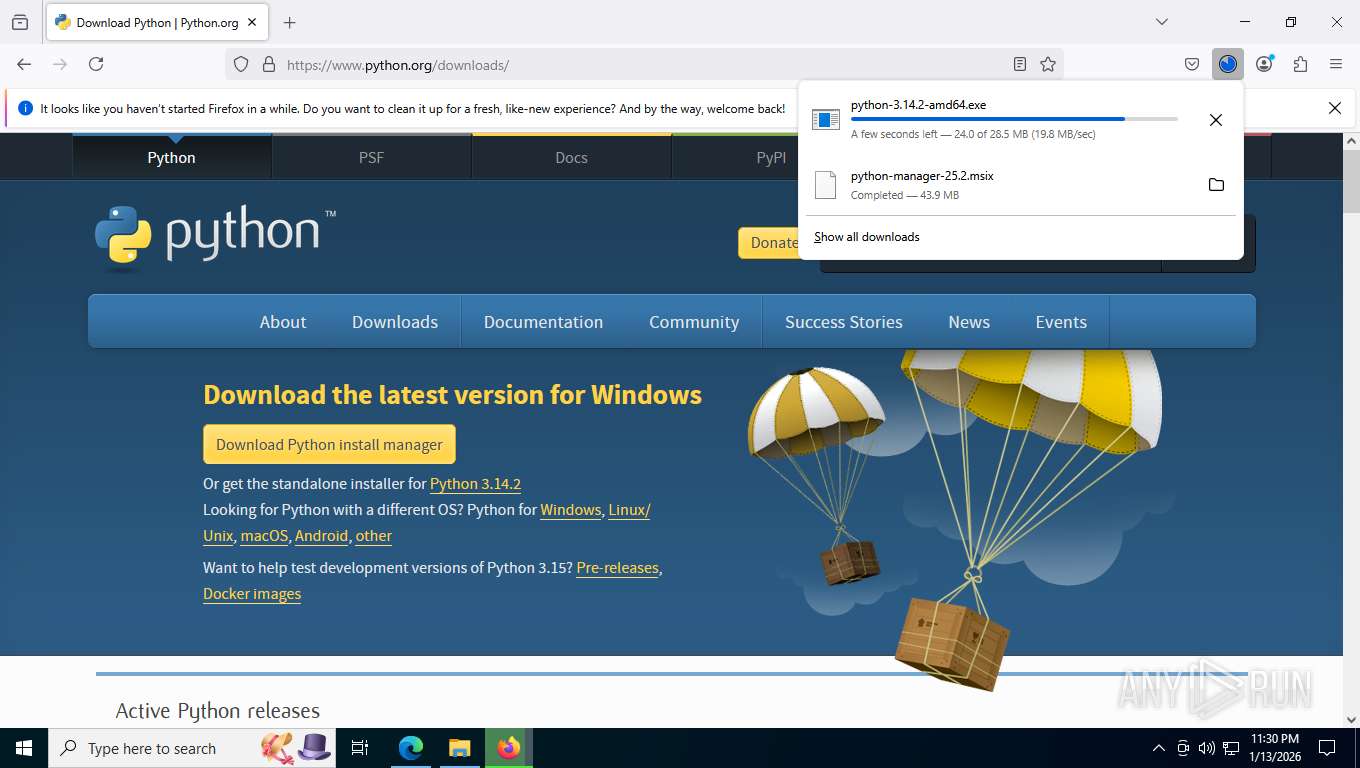
- python-3.14.2-amd64.exe (PID: 9108)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 7944)
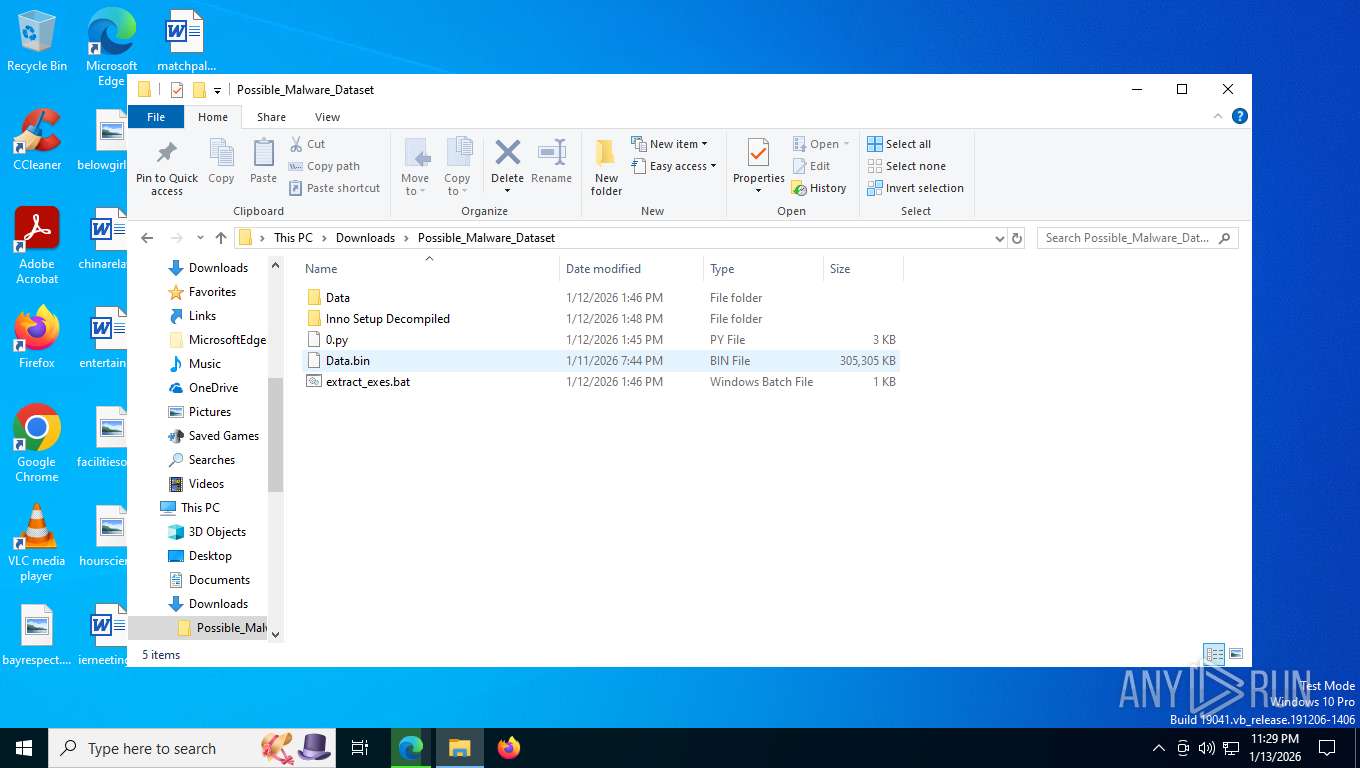
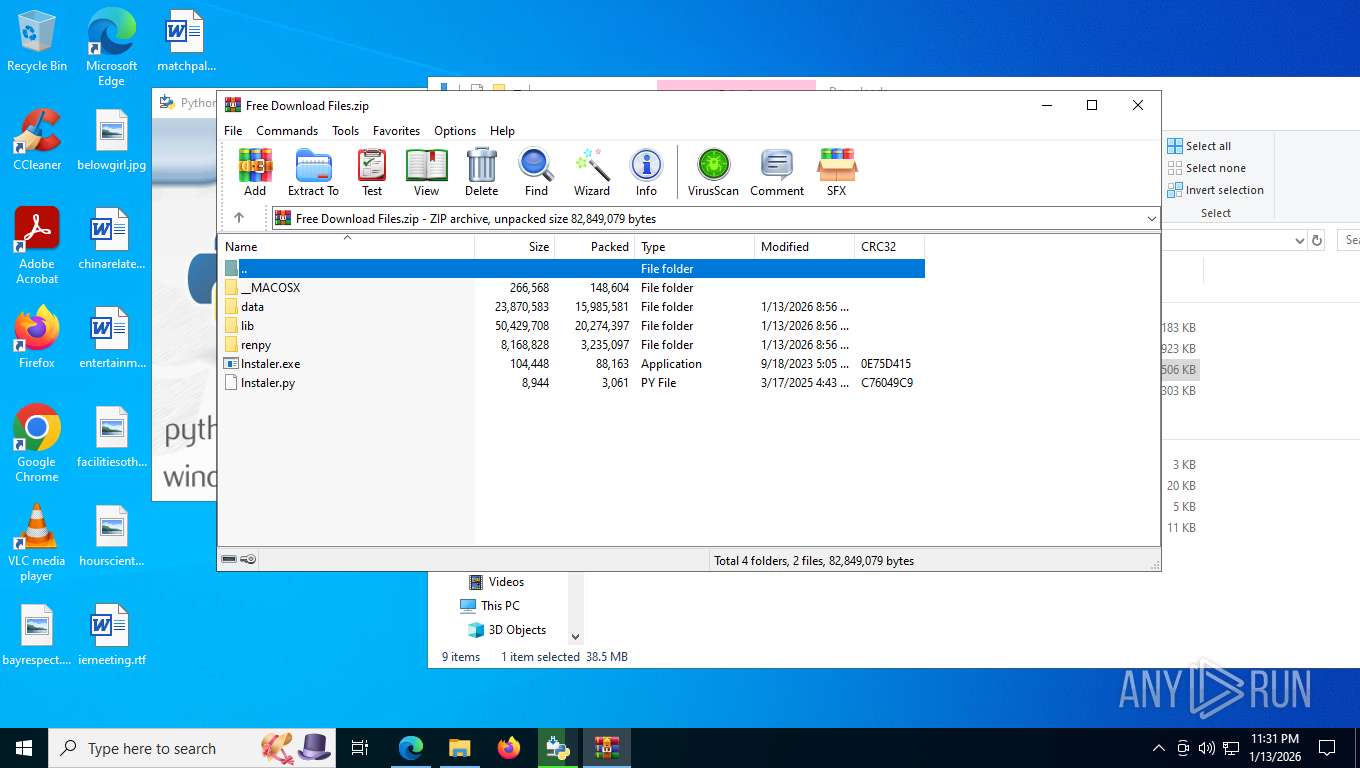
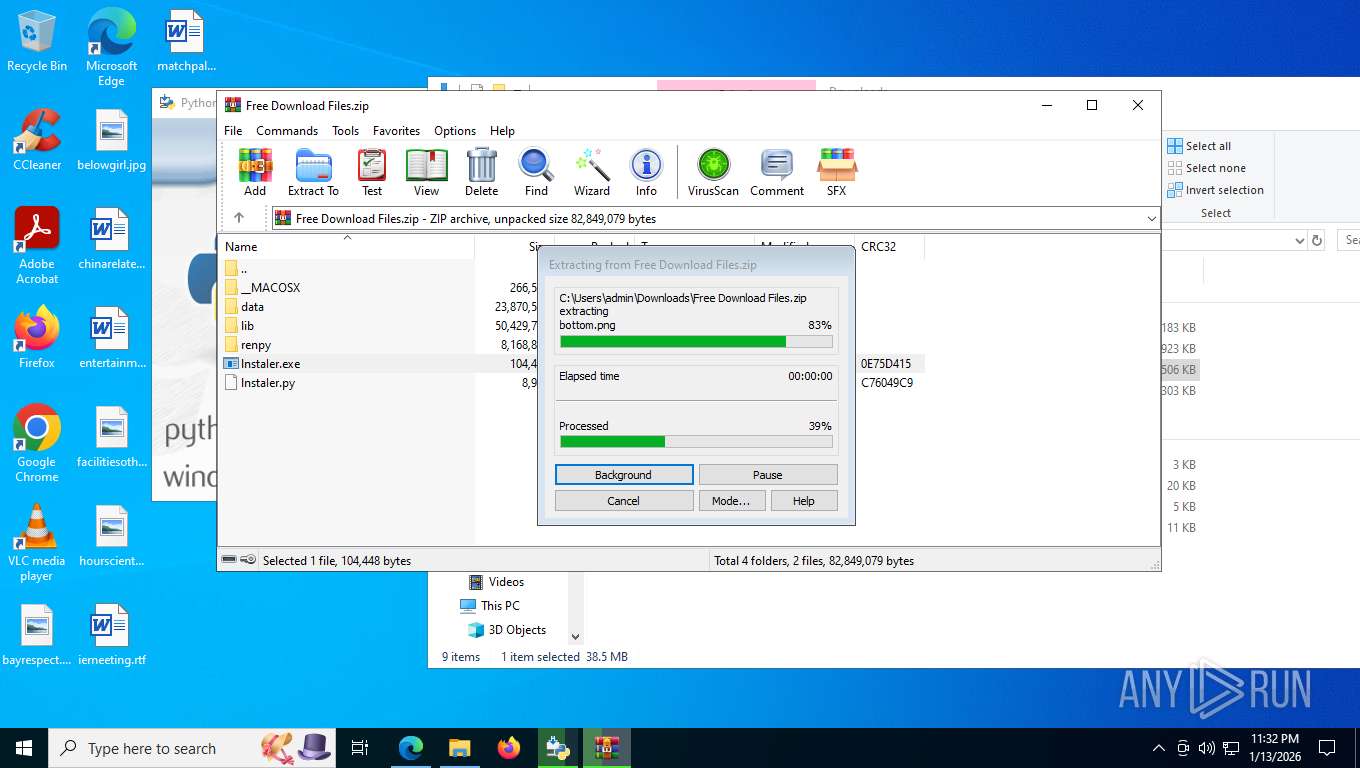
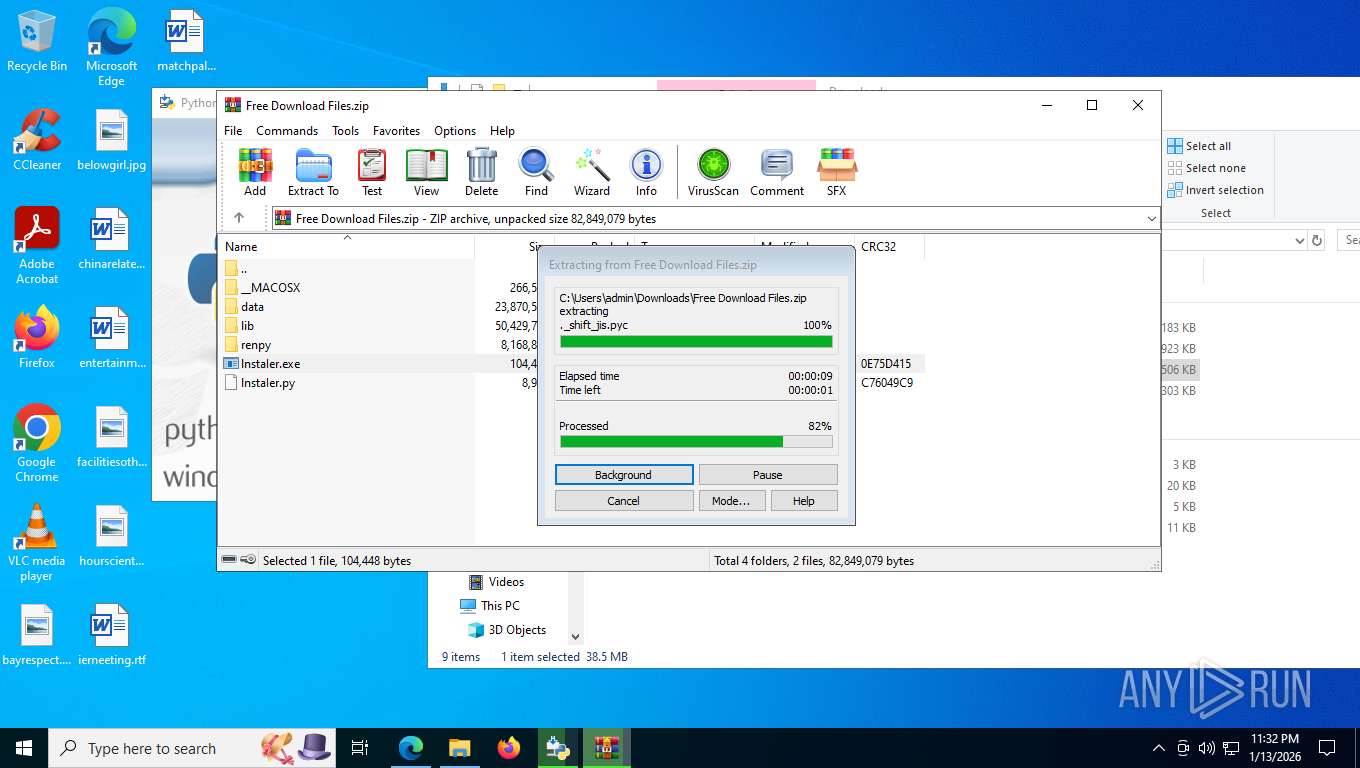
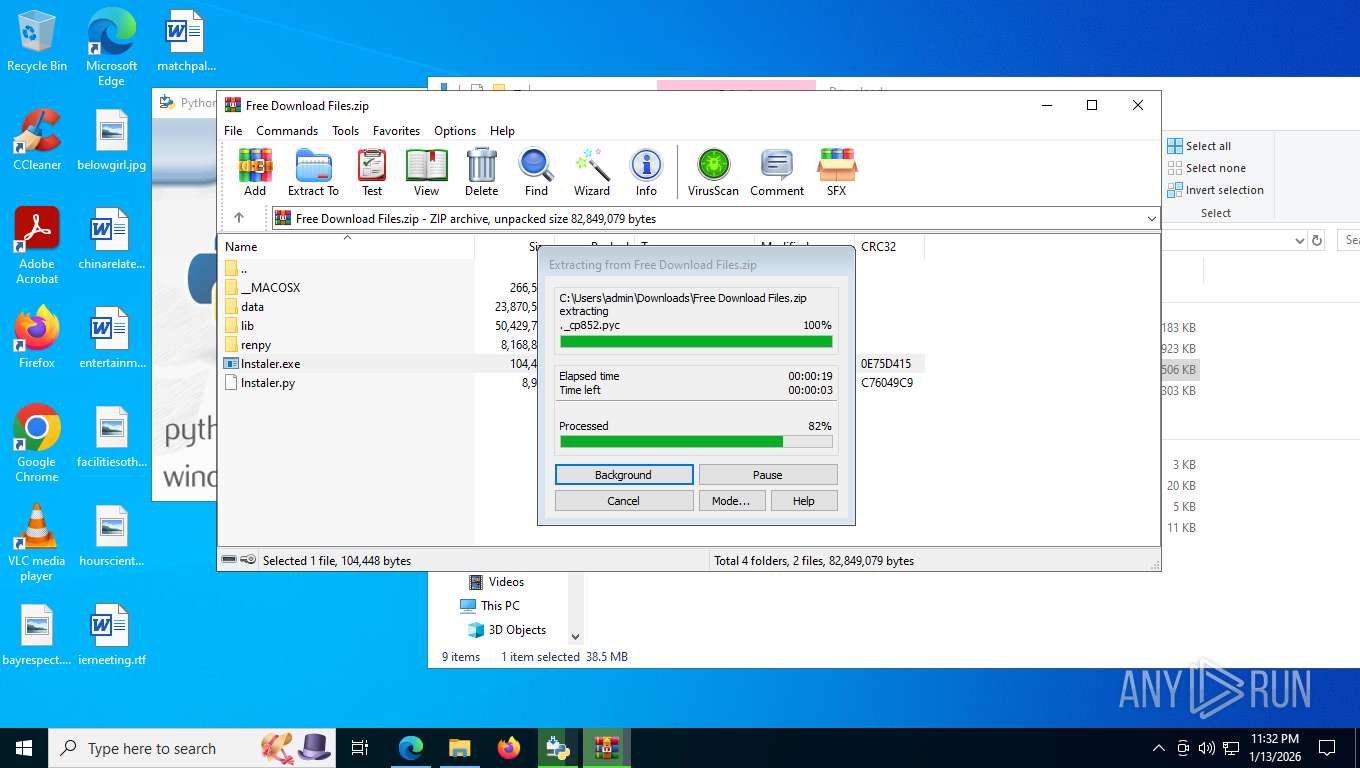
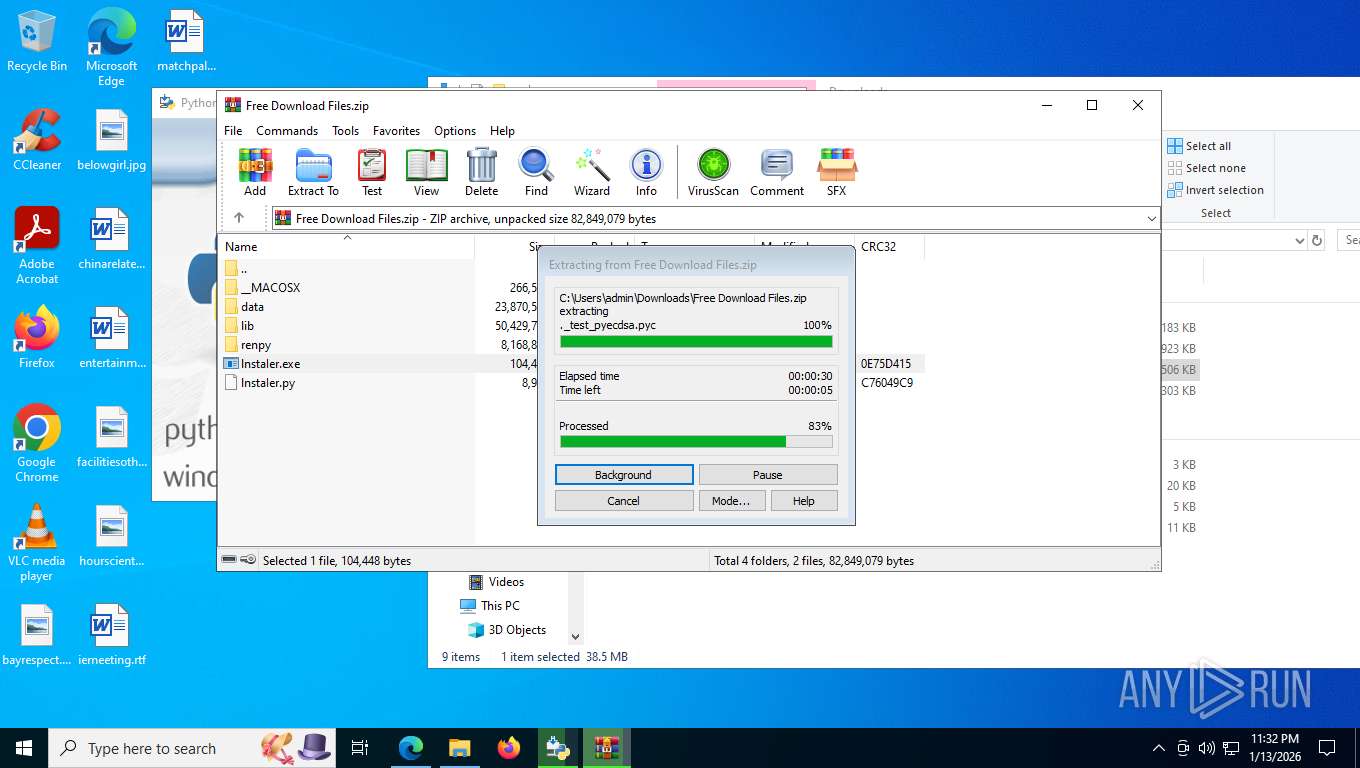
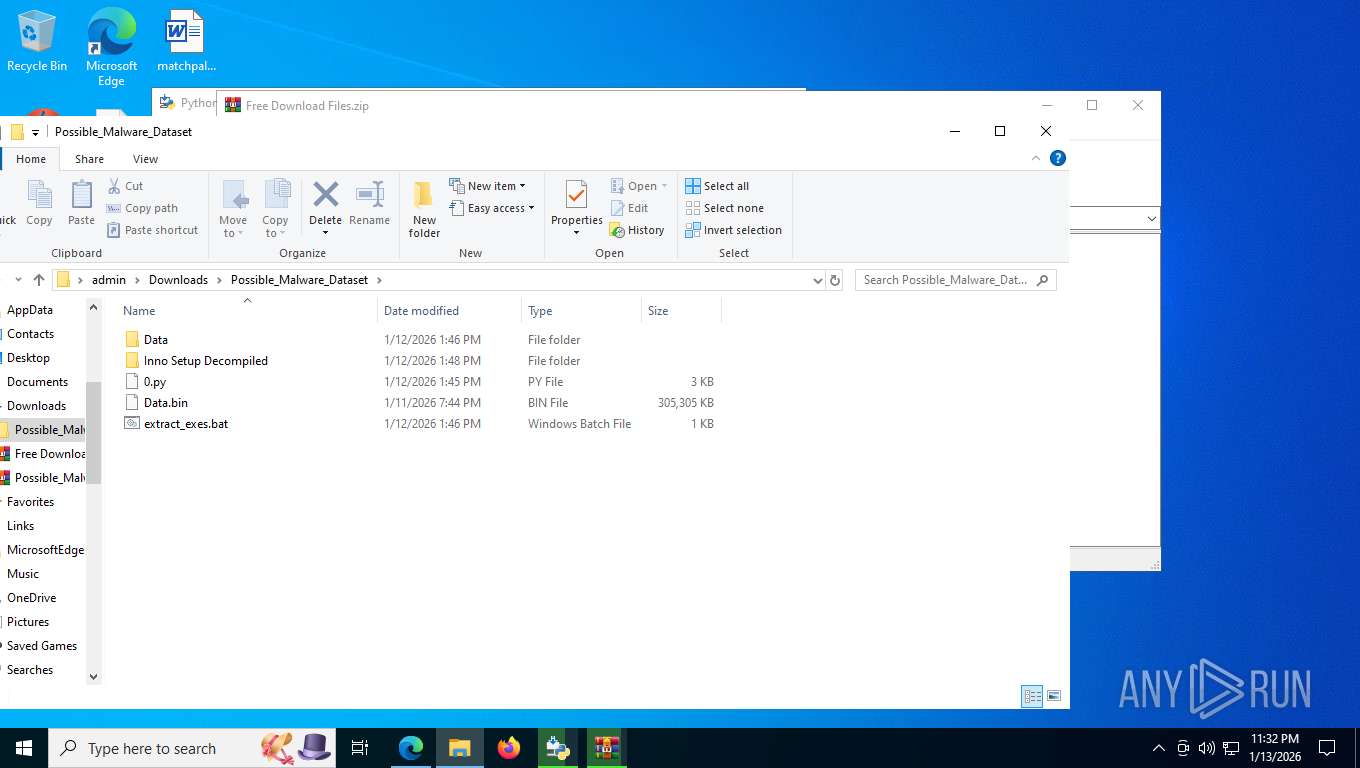
Executable content was dropped or overwritten
- python-3.14.2-amd64.exe (PID: 7332)
- python-3.14.2-amd64.exe (PID: 9108)
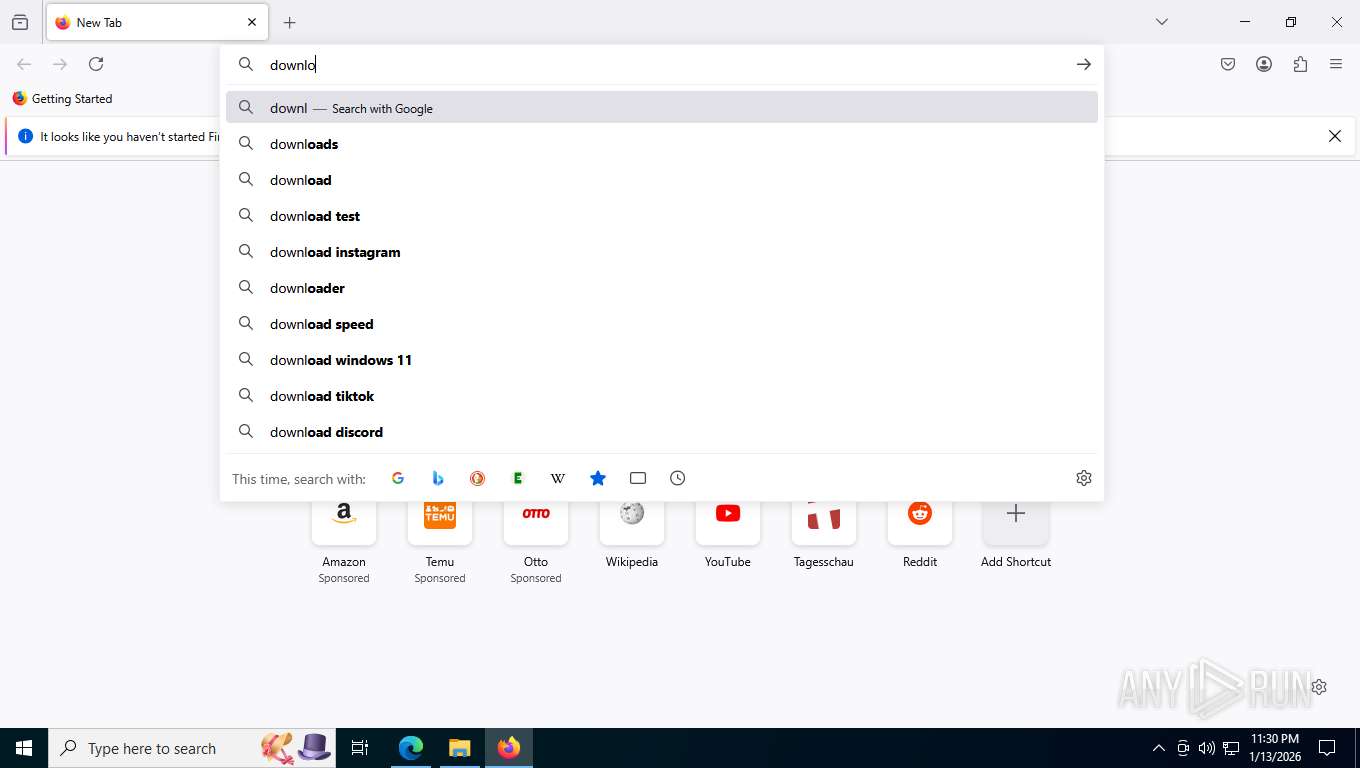
Searches for installed software
- python-3.14.2-amd64.exe (PID: 9108)
The process drops C-runtime libraries
- python-3.14.2-amd64.exe (PID: 9108)
- msiexec.exe (PID: 9148)
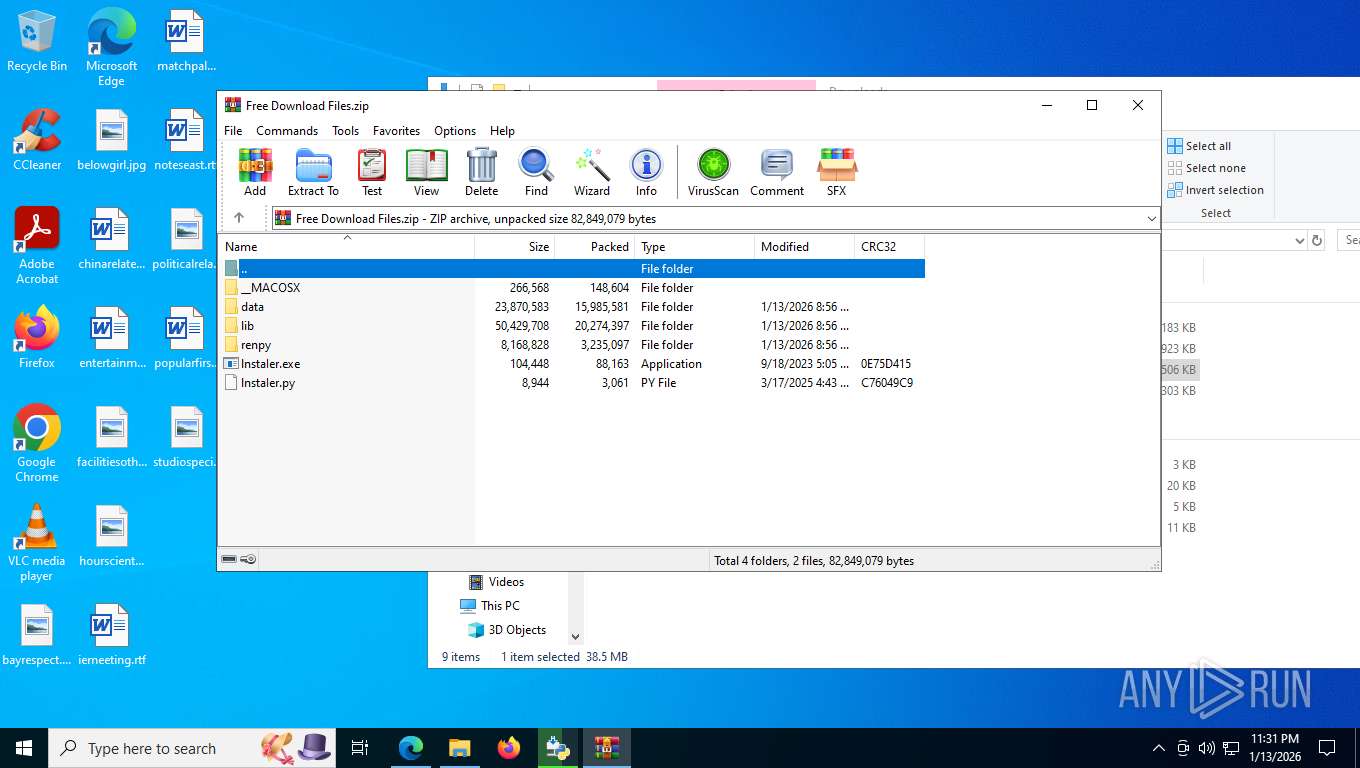
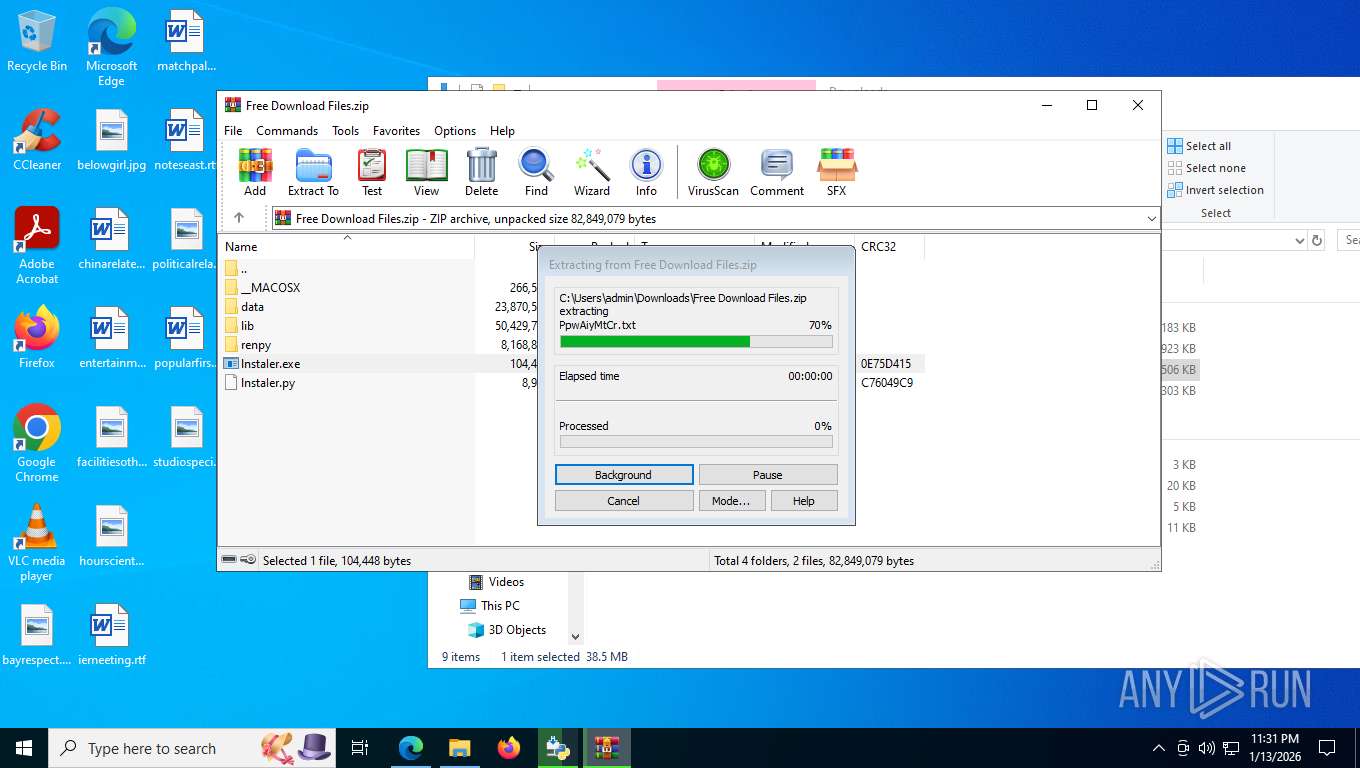
Process drops legitimate windows executable
- python-3.14.2-amd64.exe (PID: 9108)
- WinRAR.exe (PID: 8432)
- msiexec.exe (PID: 9148)
- WinRAR.exe (PID: 6600)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 9148)
Process drops python dynamic module
- msiexec.exe (PID: 9148)
There is functionality for taking screenshot (YARA)
- python-3.14.2-amd64.exe (PID: 9108)
INFO
Application launched itself
- msedge.exe (PID: 7620)
- firefox.exe (PID: 8240)
- firefox.exe (PID: 8232)
Reads Environment values
- identity_helper.exe (PID: 8316)
Checks supported languages
- identity_helper.exe (PID: 8316)
- TextInputHost.exe (PID: 8204)
- python-3.14.2-amd64.exe (PID: 7332)
- python-3.14.2-amd64.exe (PID: 9108)
- msiexec.exe (PID: 9148)
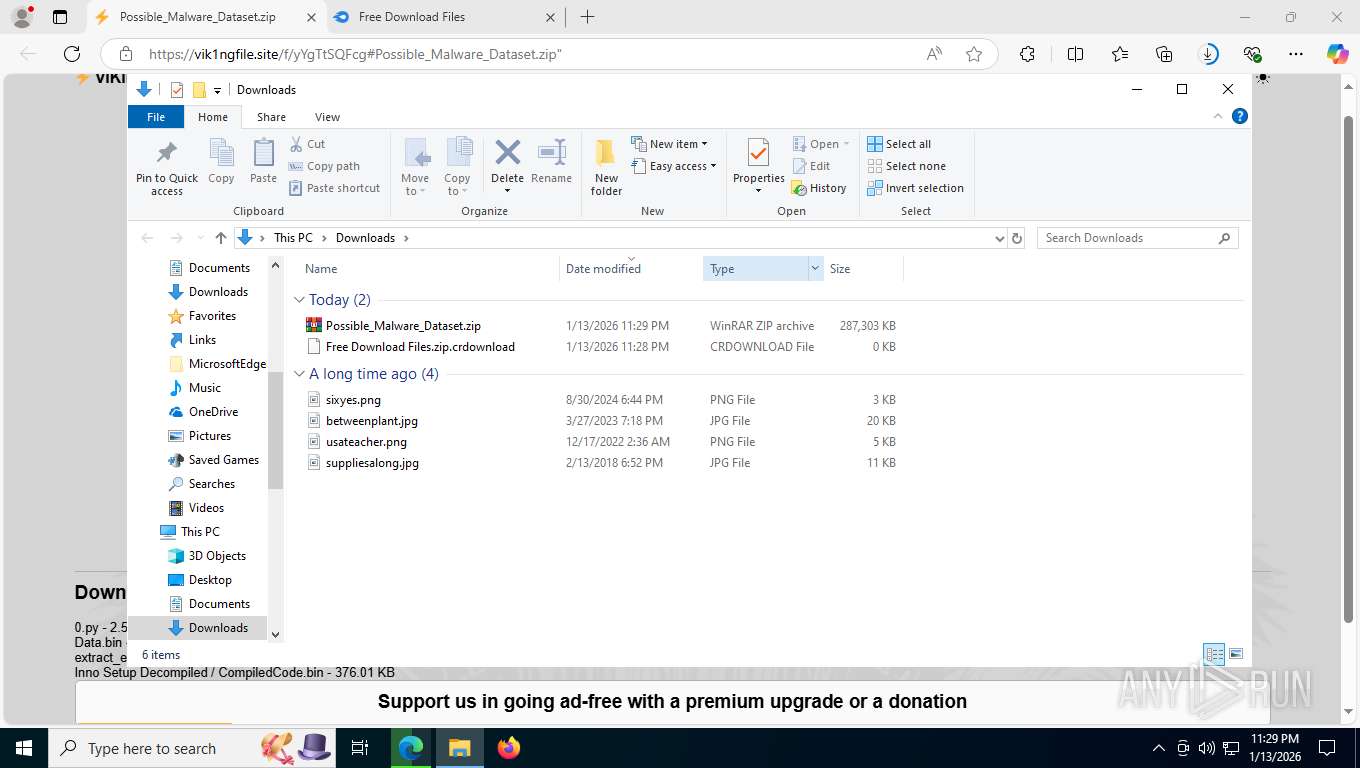
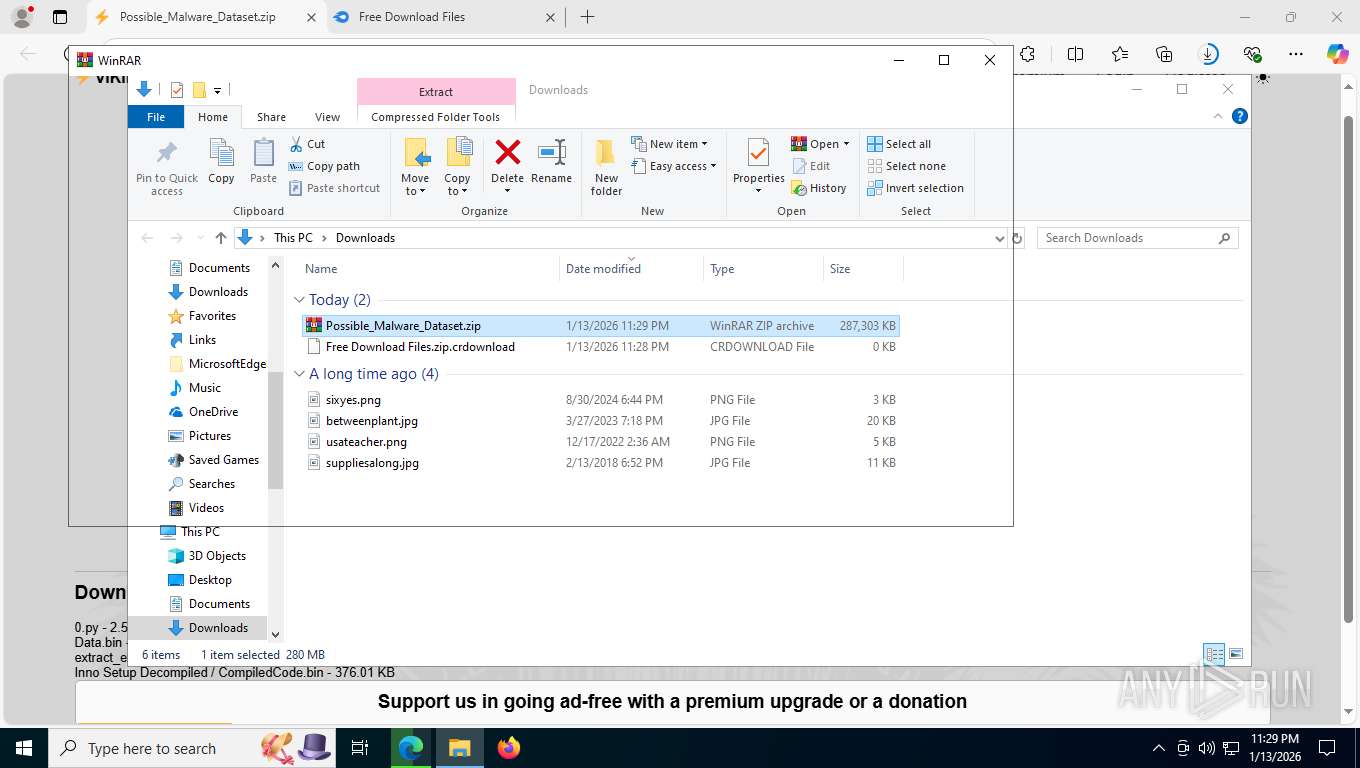
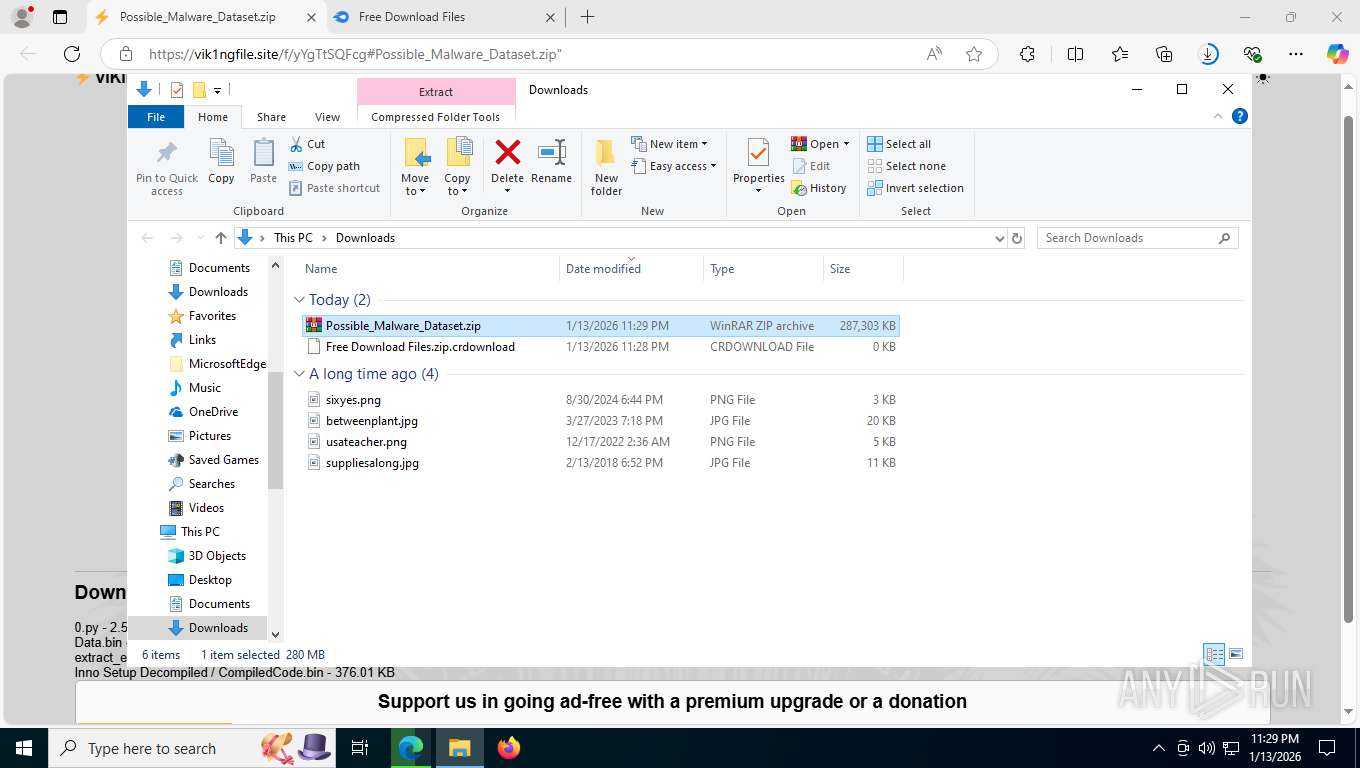
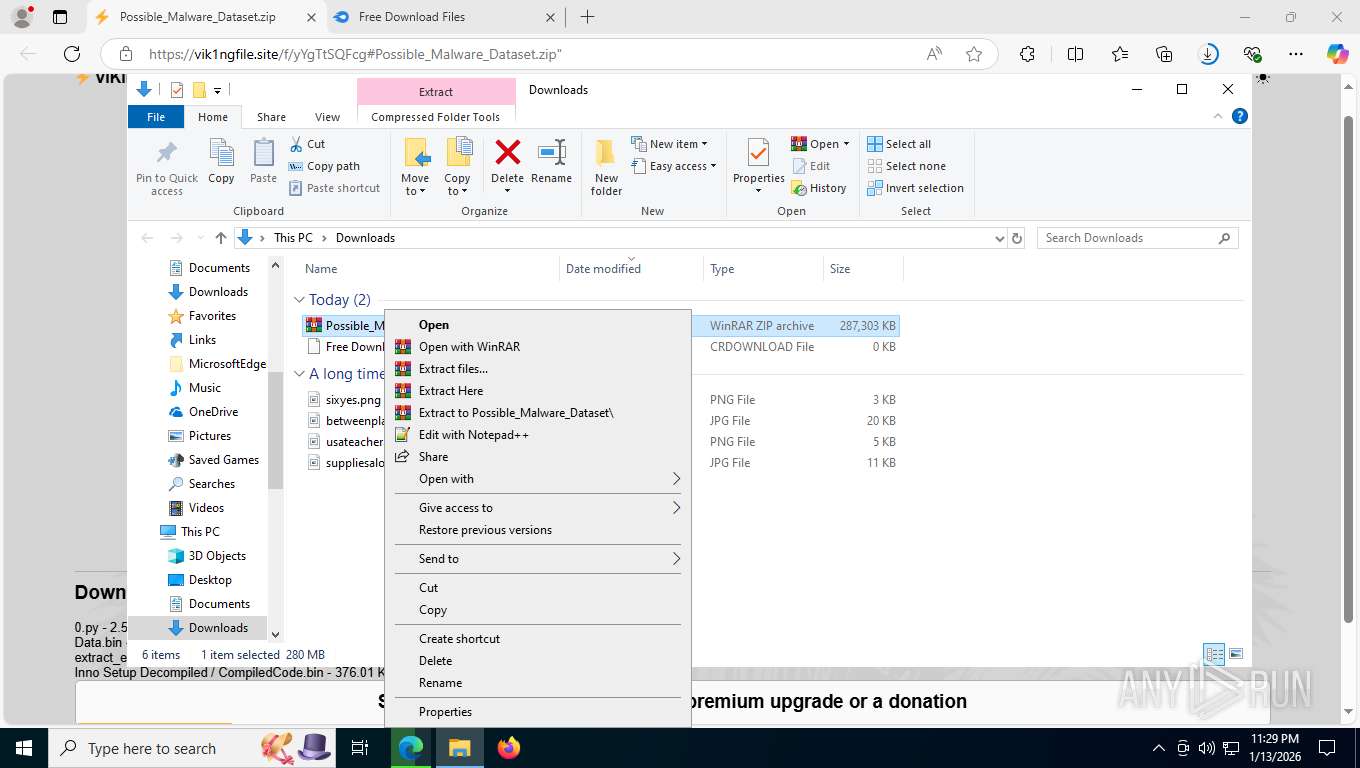
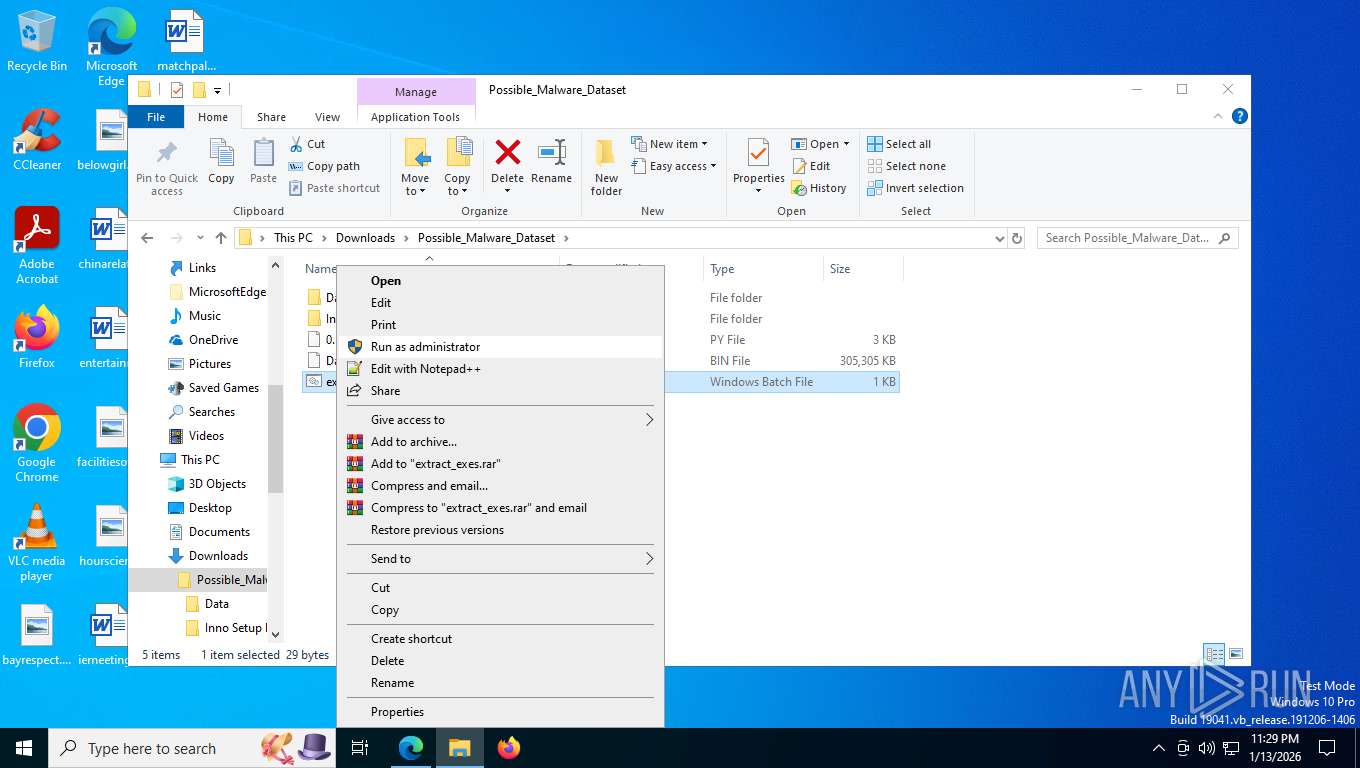
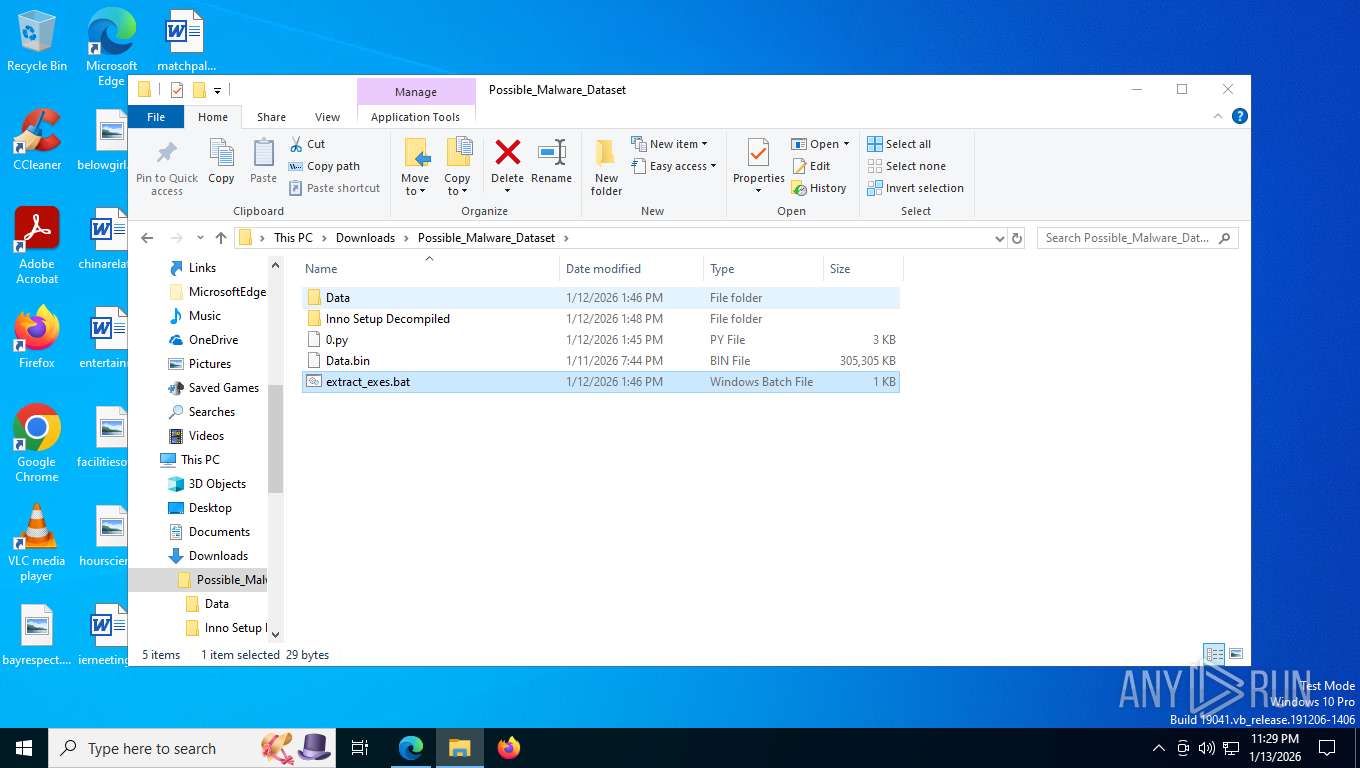
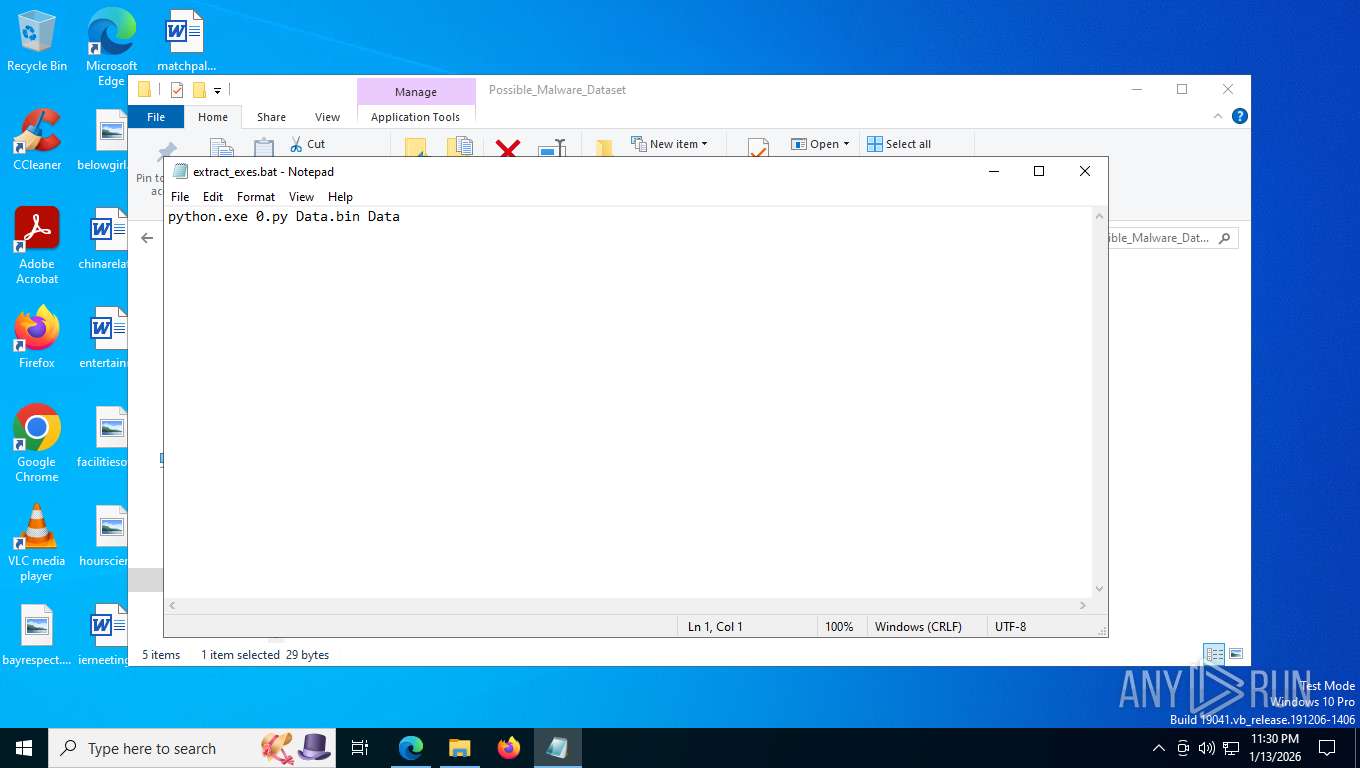
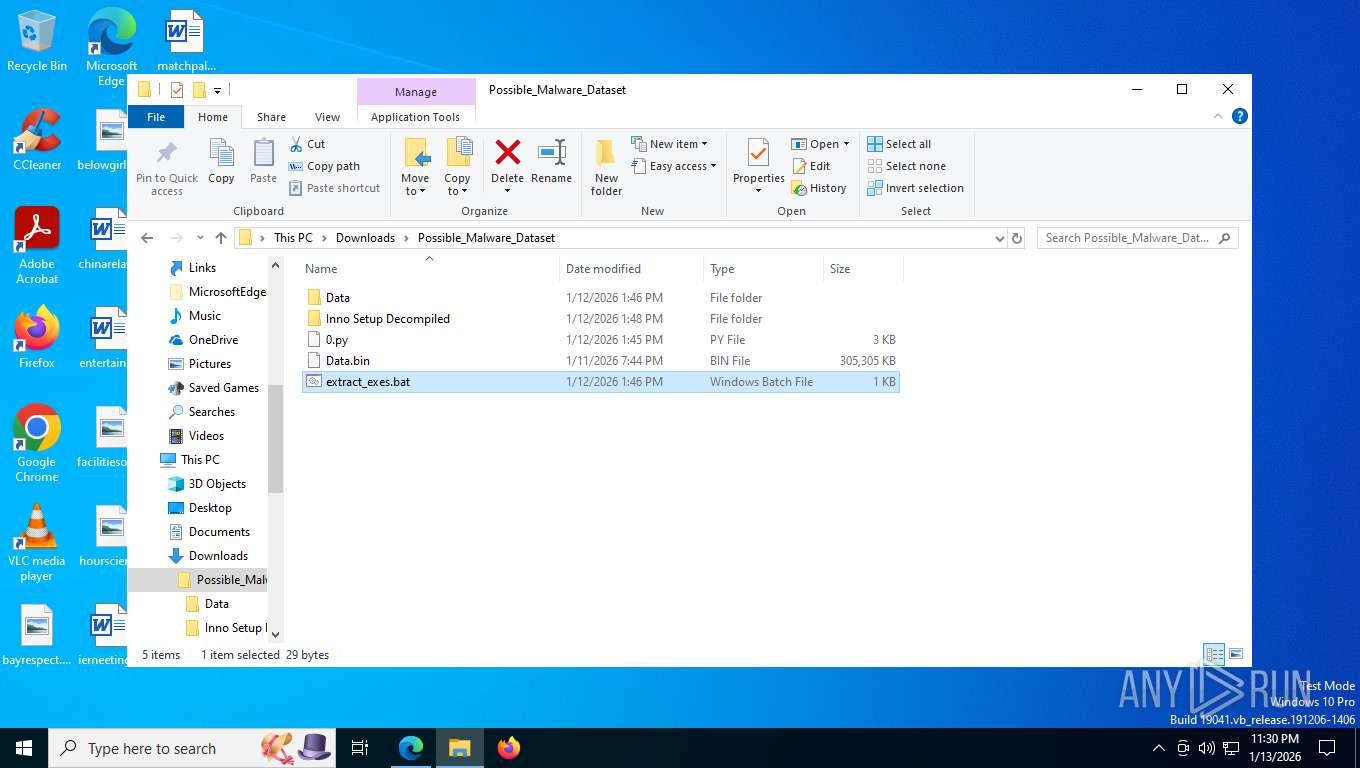
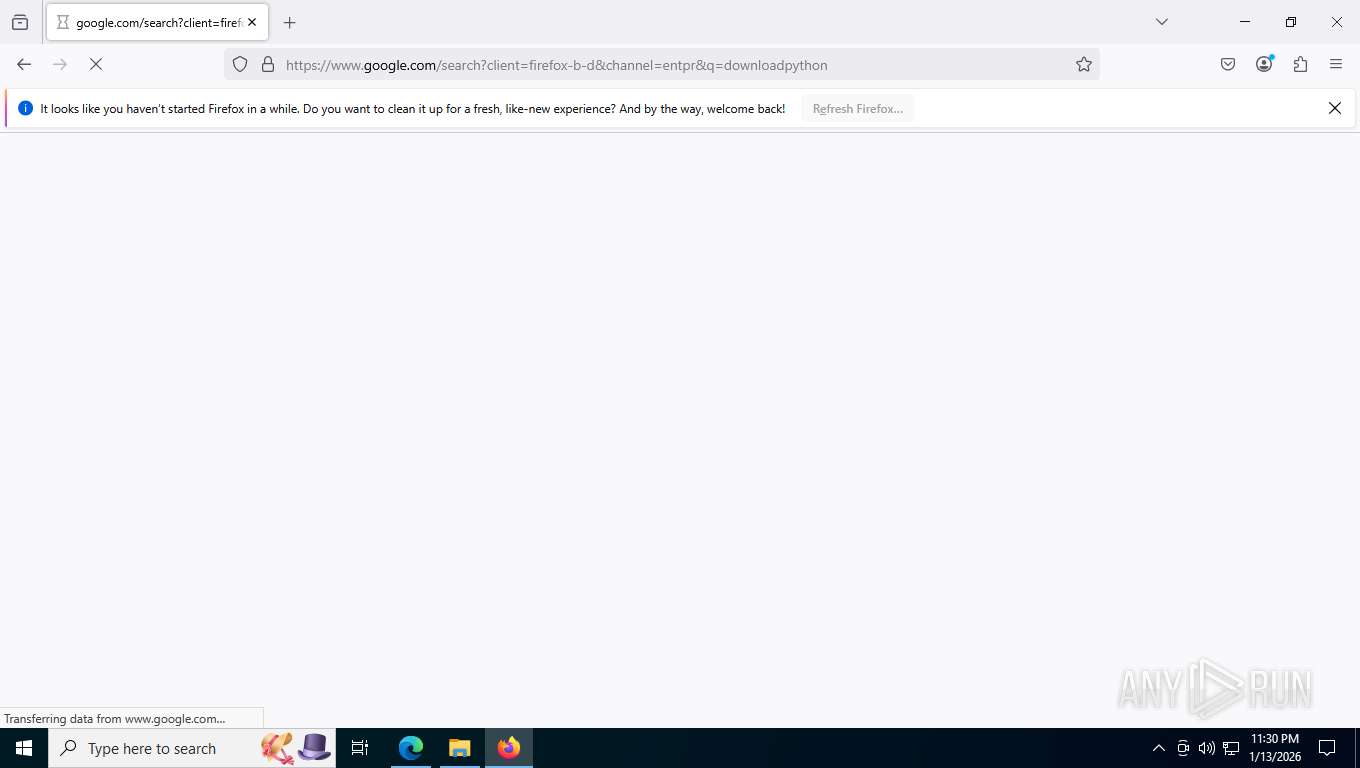
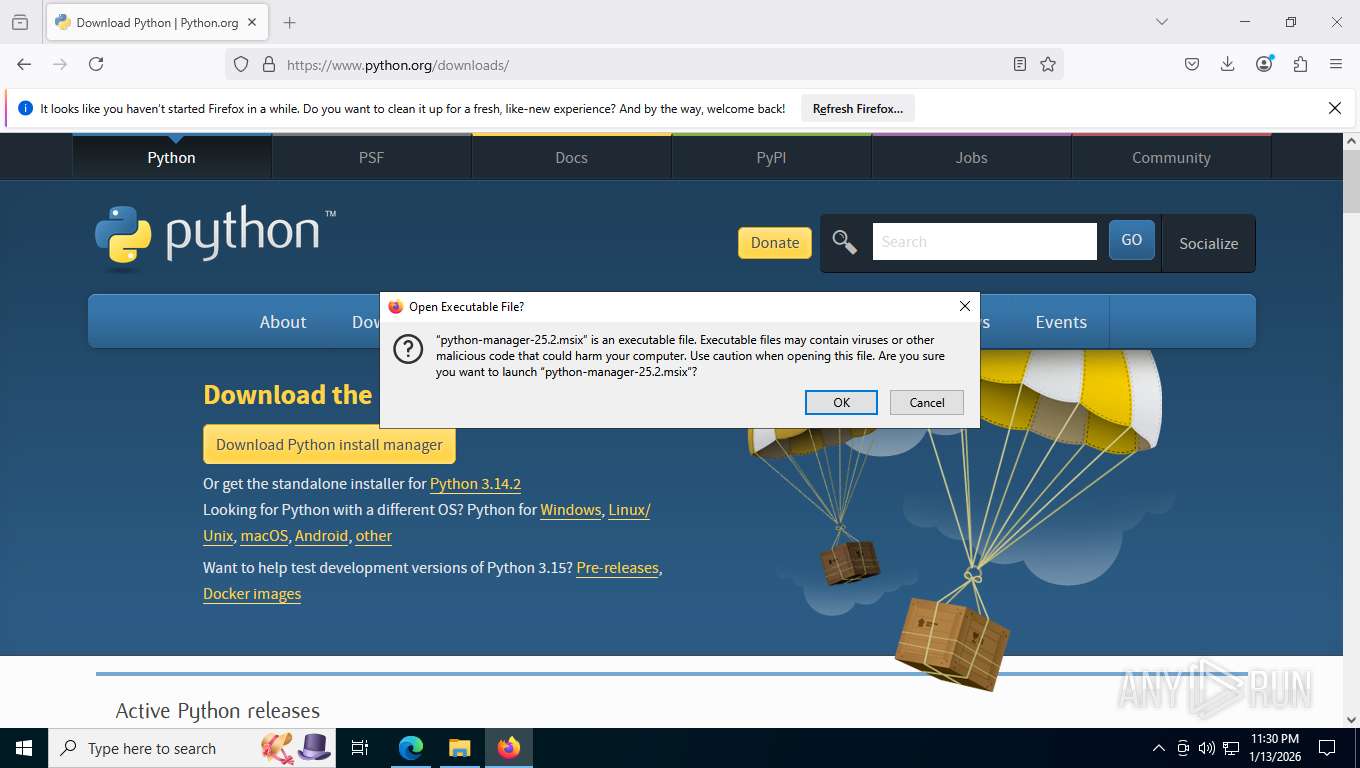
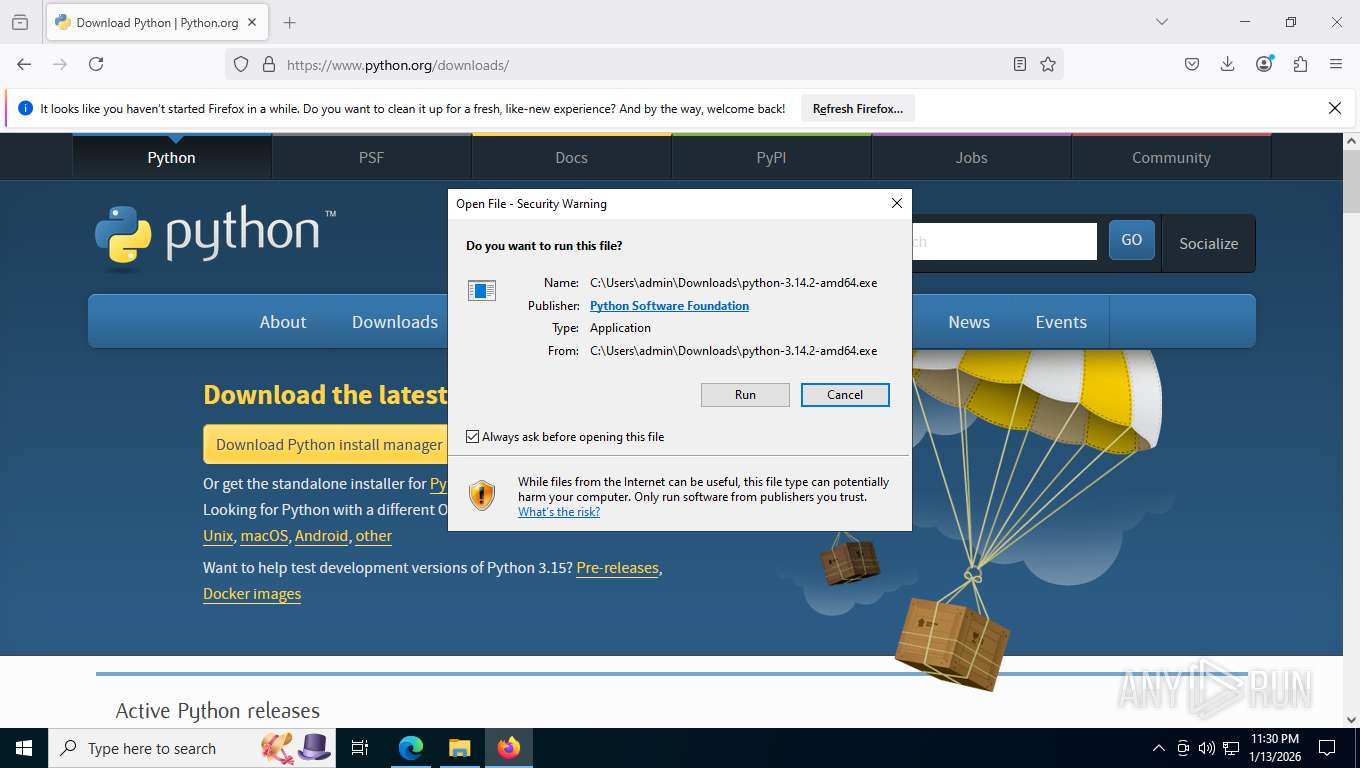
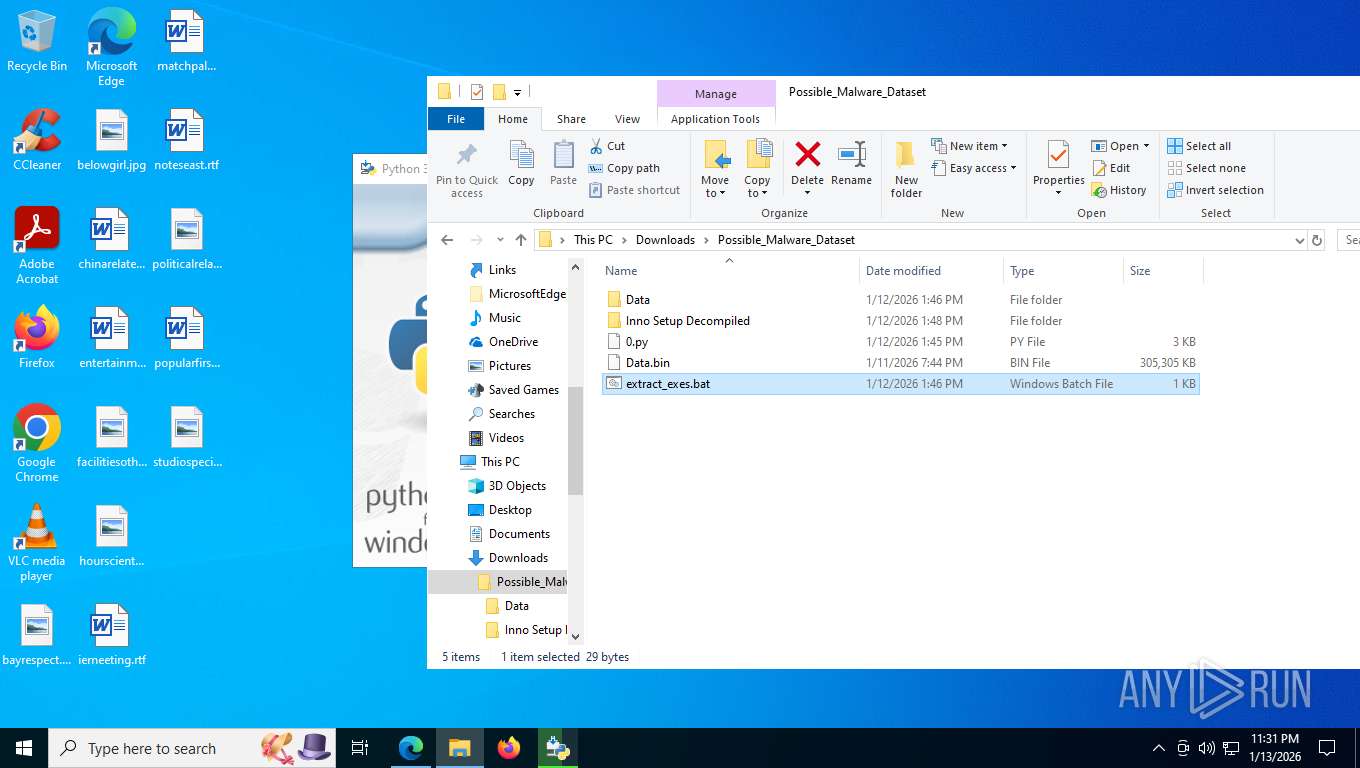
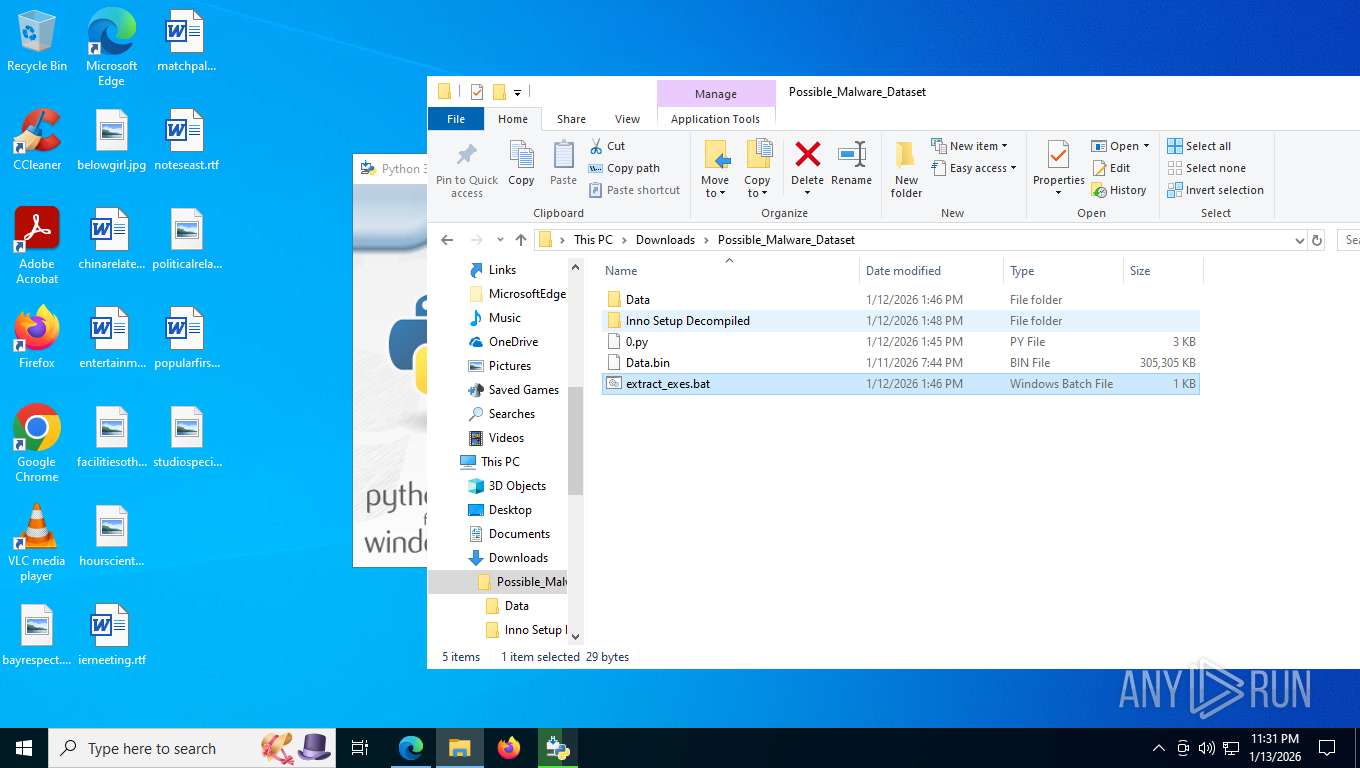
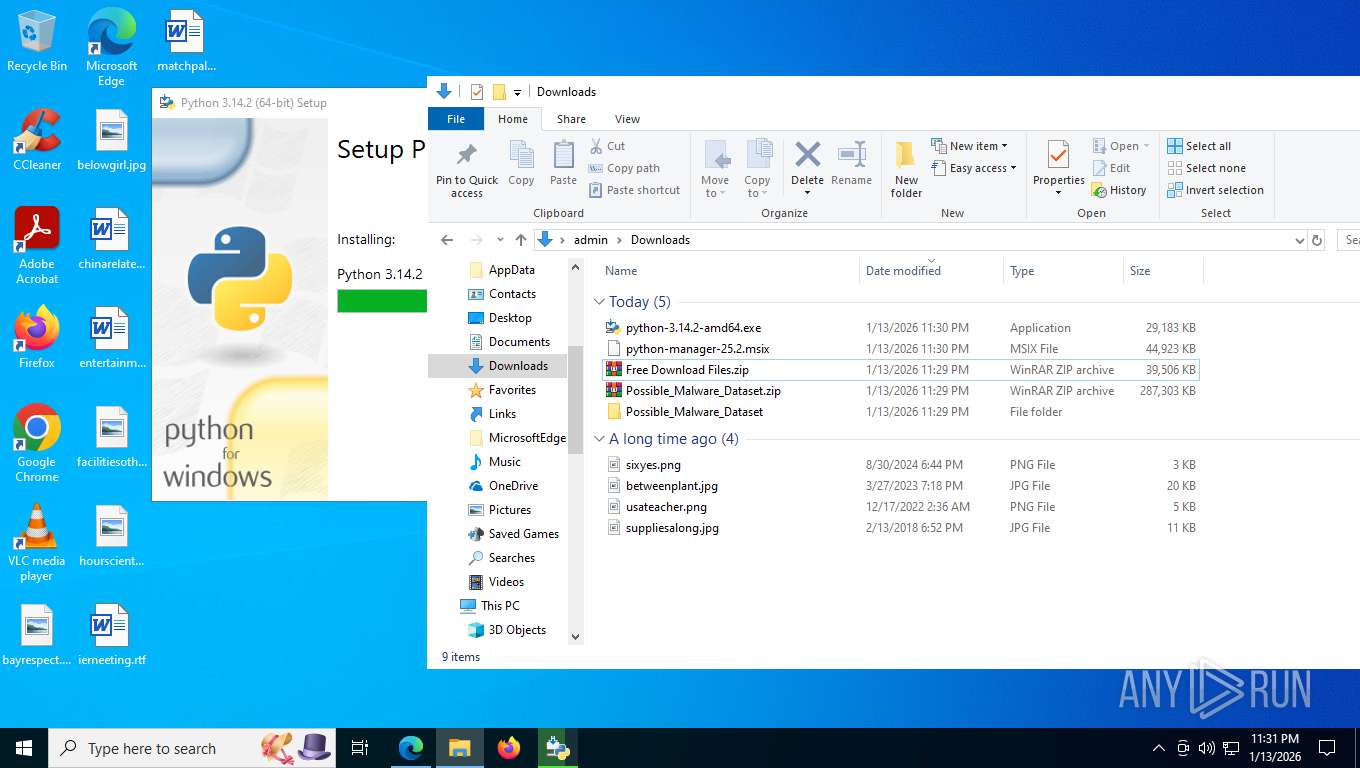
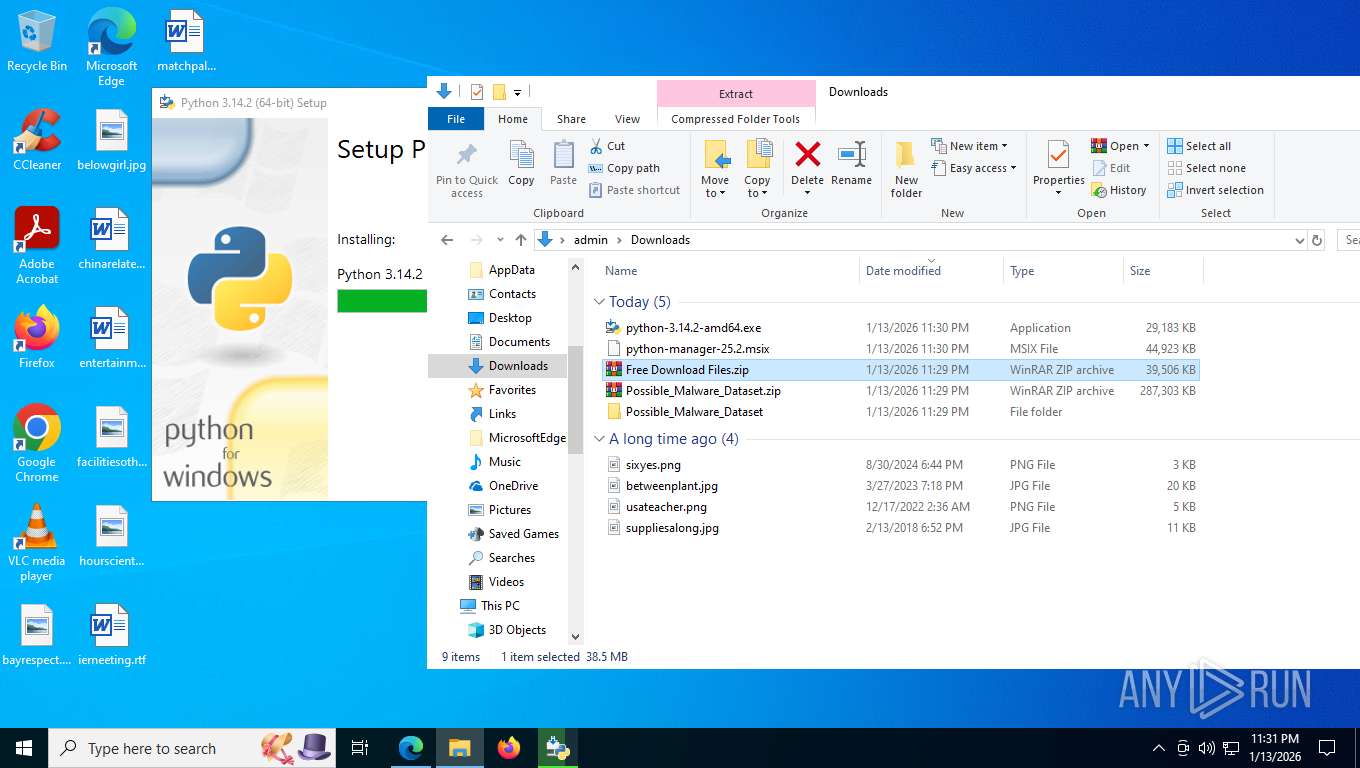
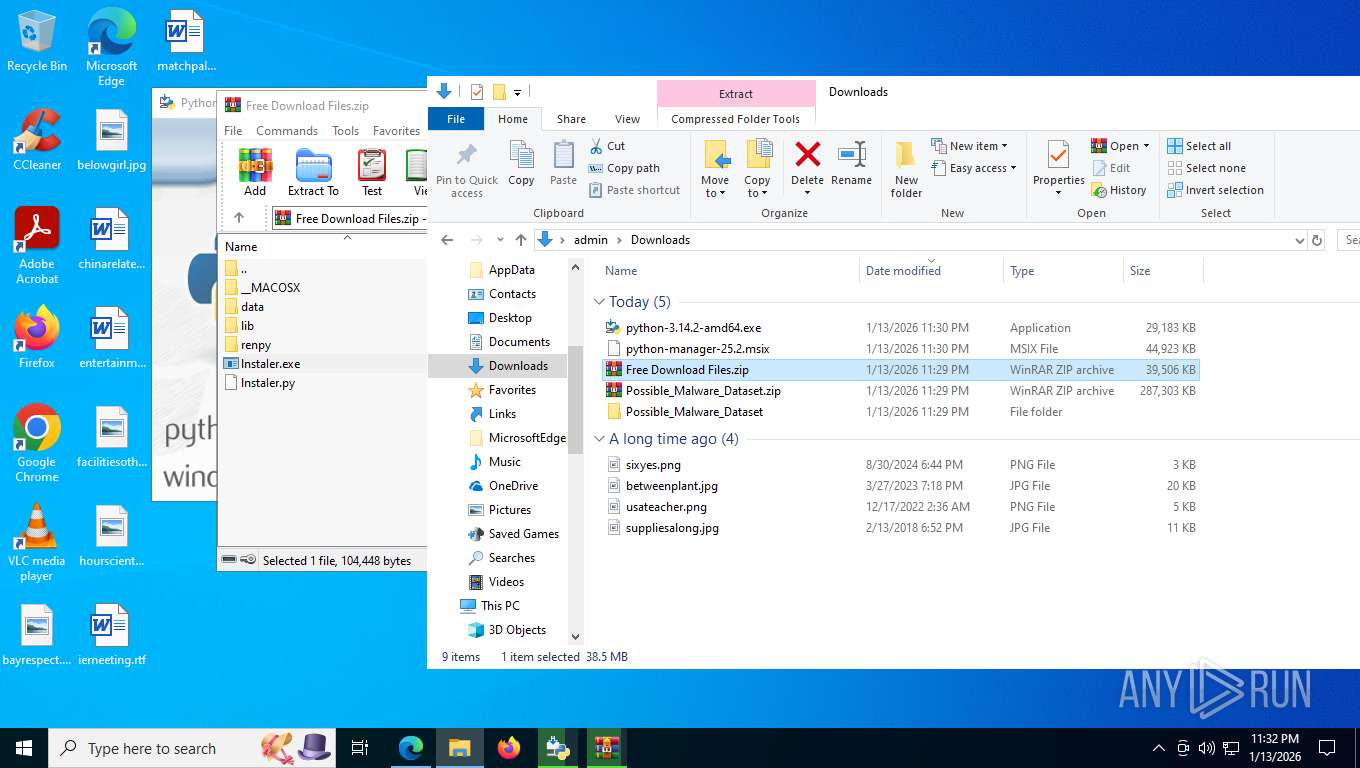
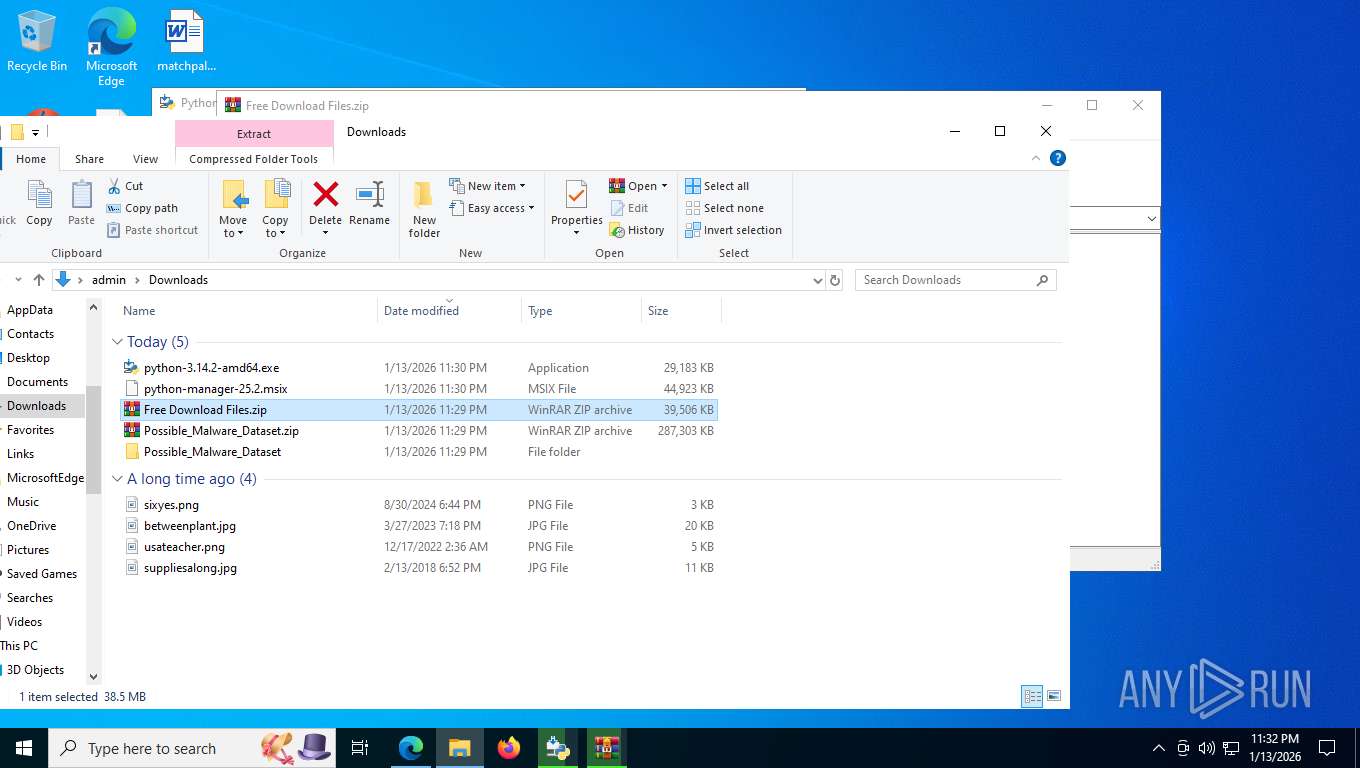
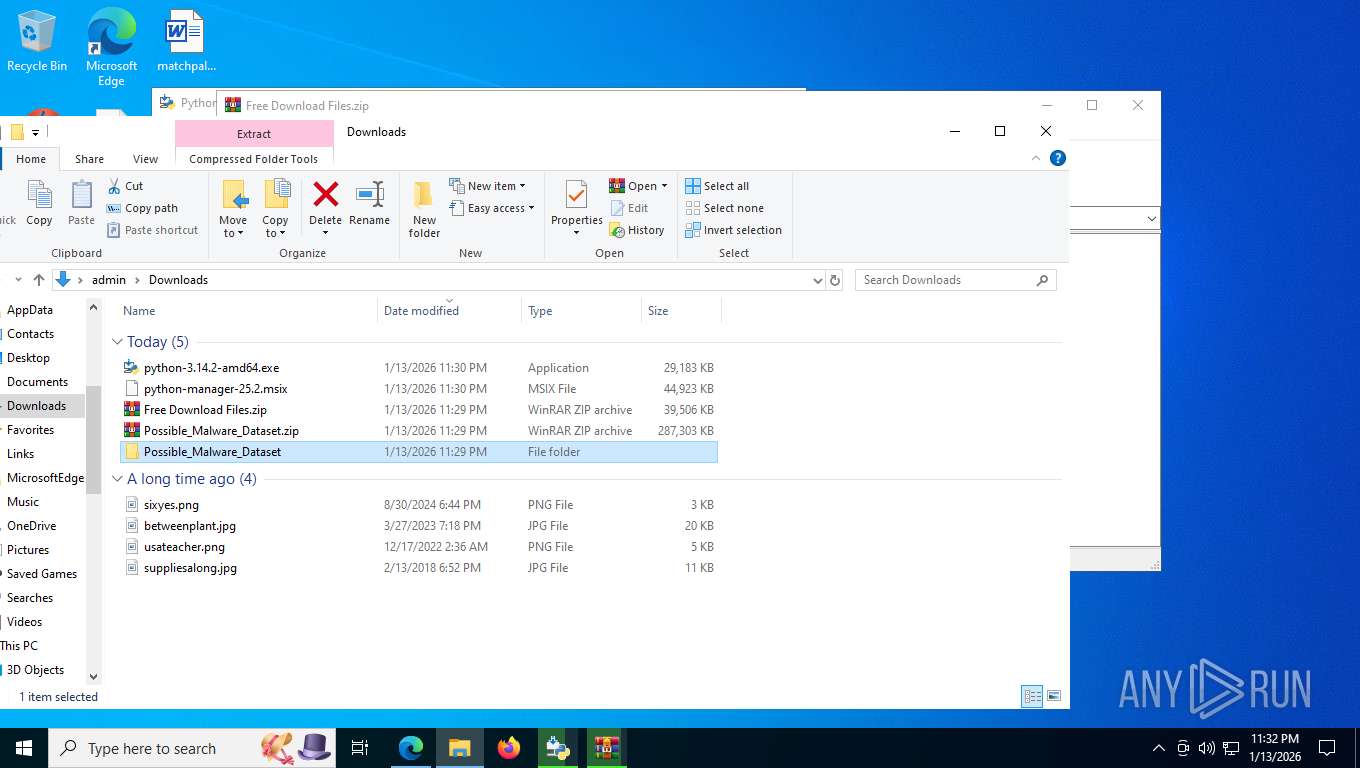
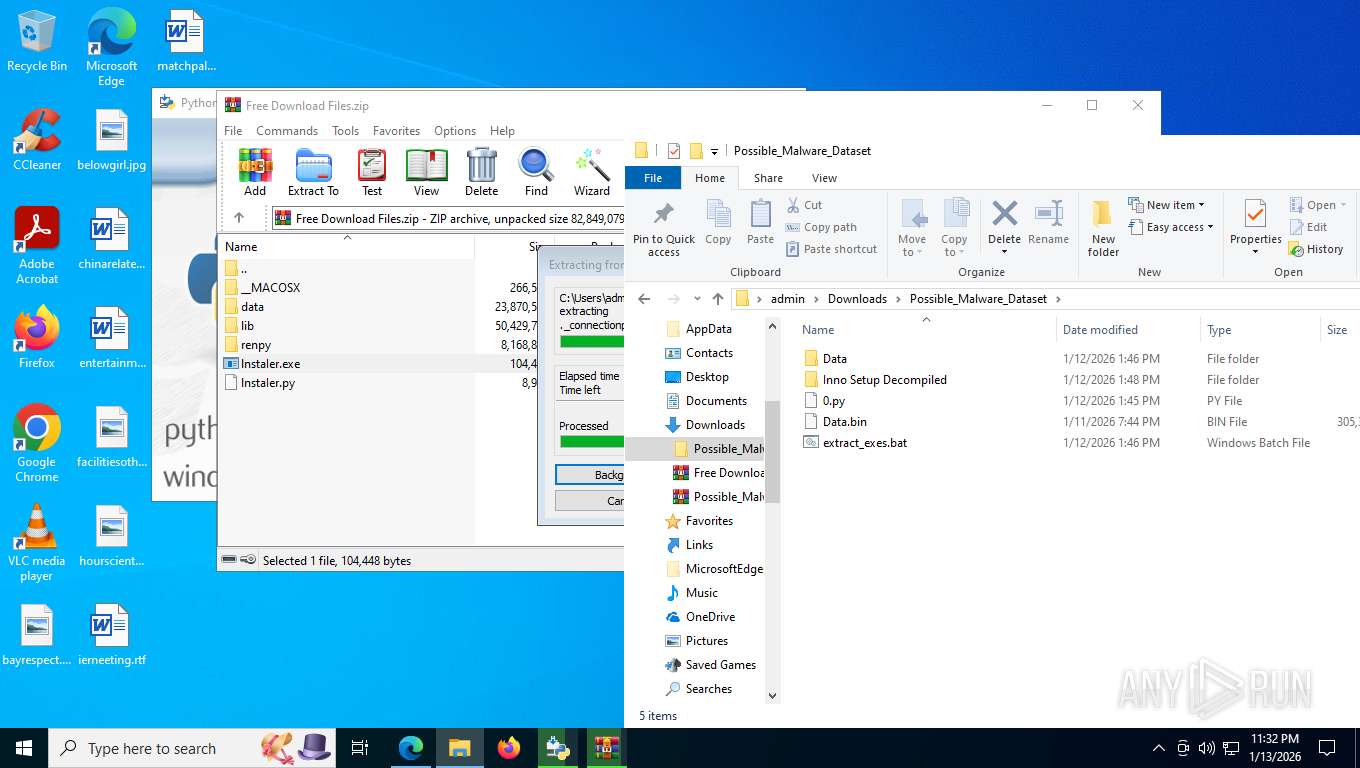
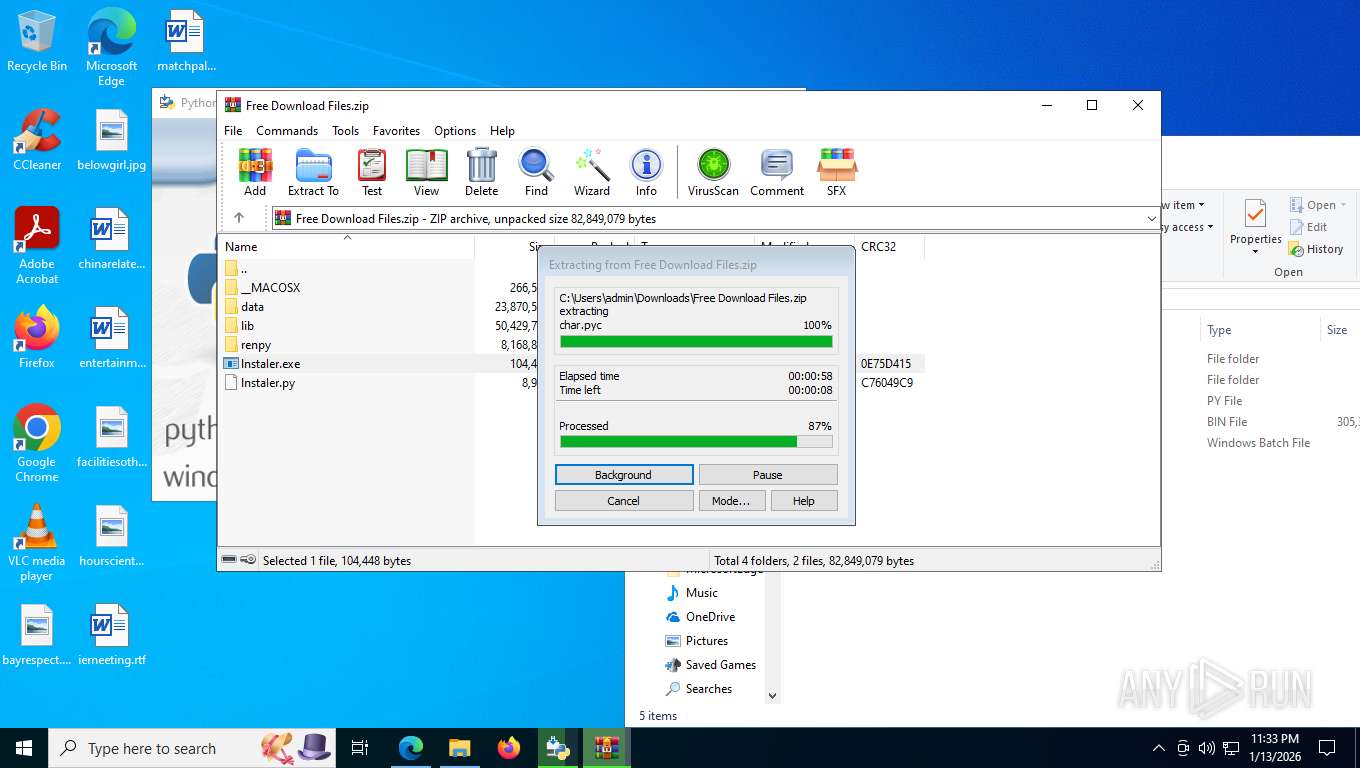
Manual execution by a user
- cmd.exe (PID: 7764)
- notepad.exe (PID: 8724)
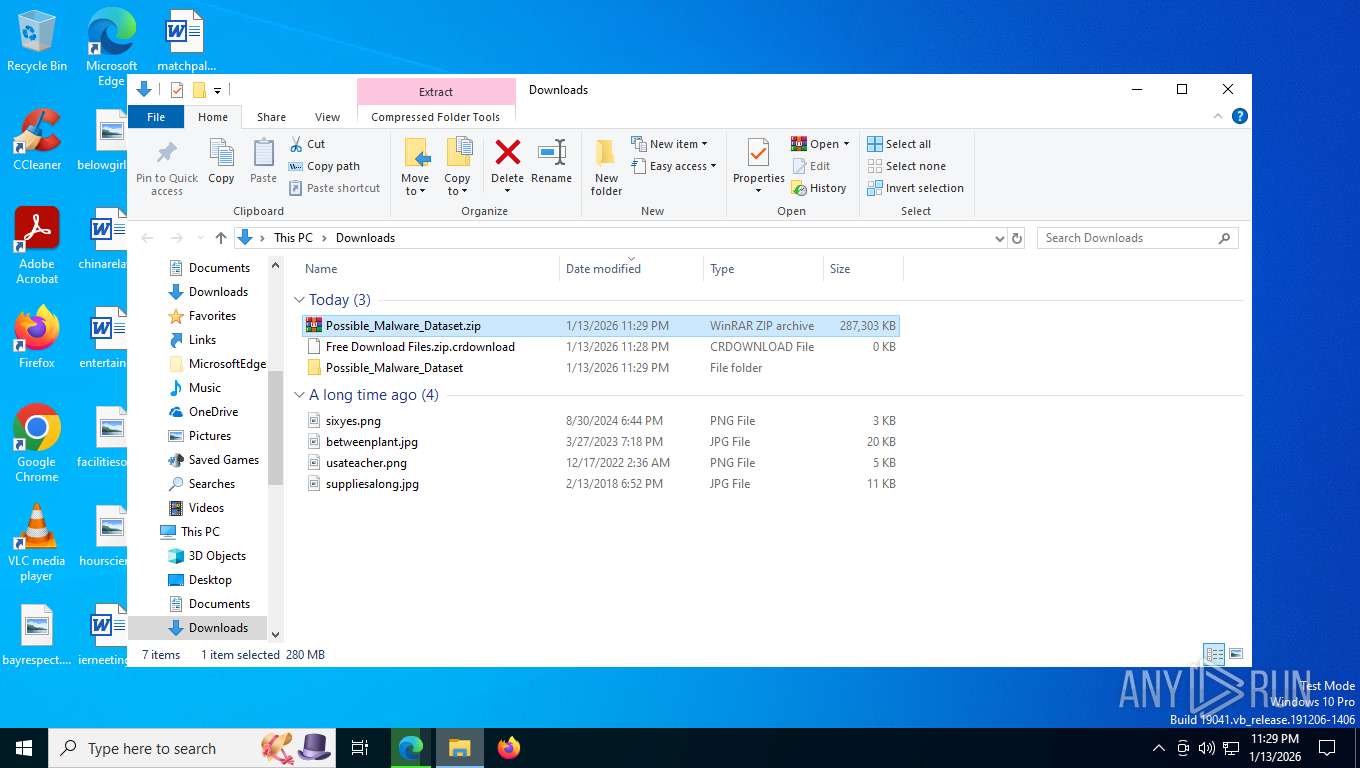
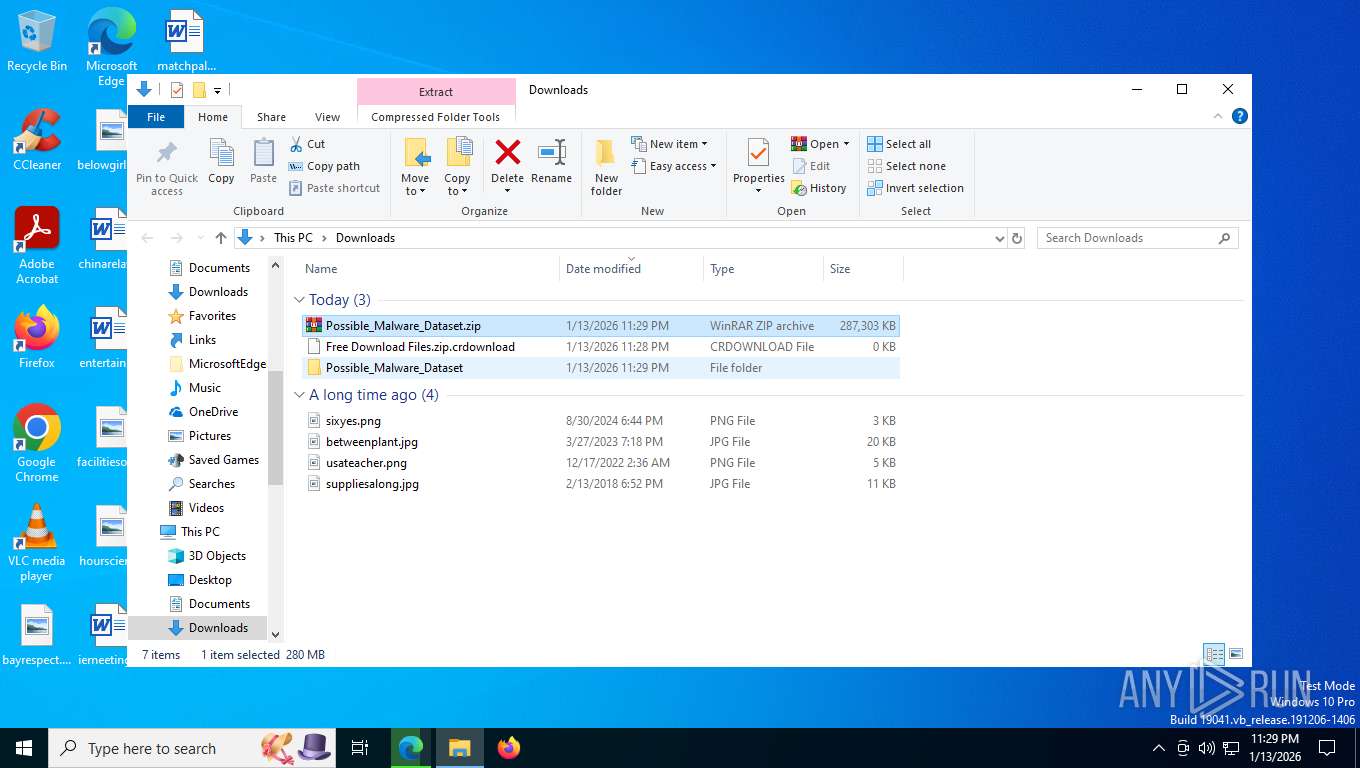
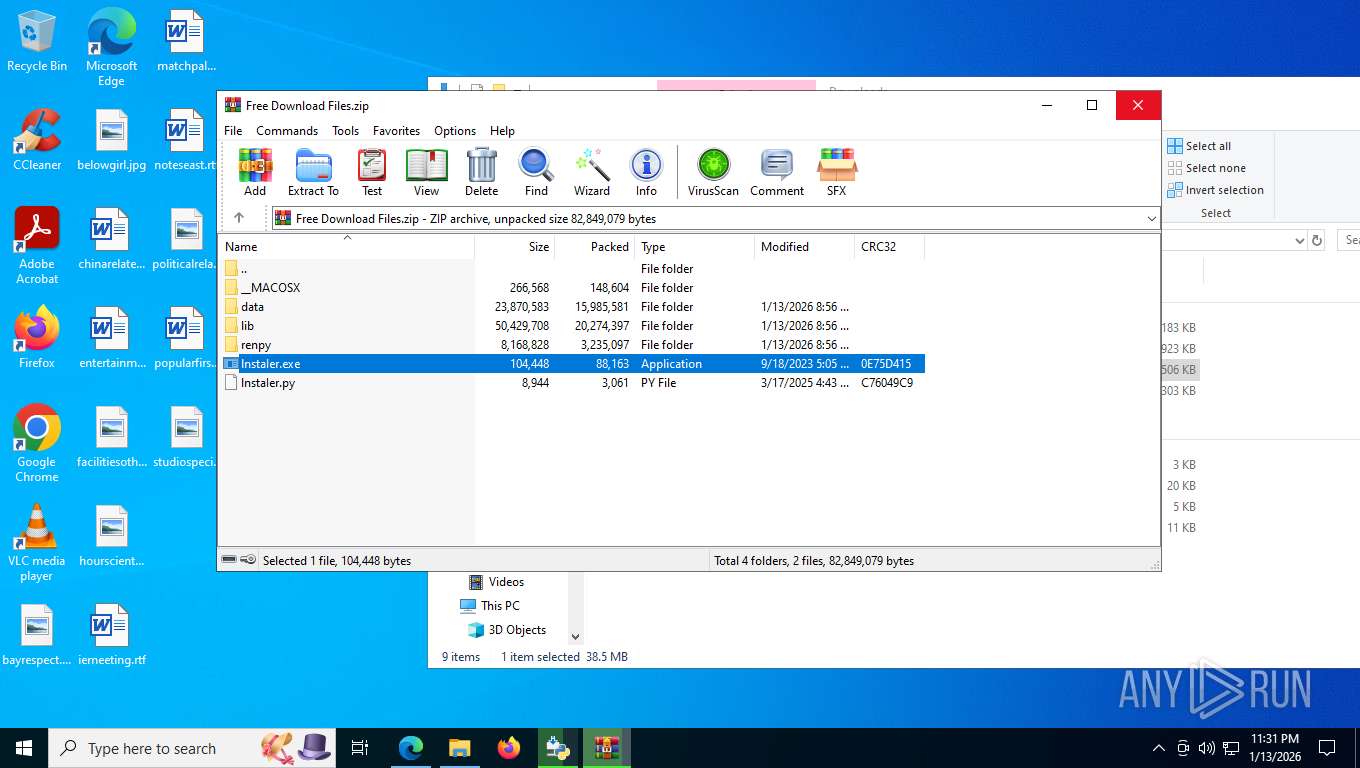
- WinRAR.exe (PID: 6892)
- WinRAR.exe (PID: 8528)
- firefox.exe (PID: 8240)
- WinRAR.exe (PID: 8432)
- WinRAR.exe (PID: 6600)
Reads the computer name
- identity_helper.exe (PID: 8316)
- TextInputHost.exe (PID: 8204)
- python-3.14.2-amd64.exe (PID: 9108)
- msiexec.exe (PID: 9148)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8724)
Executable content was dropped or overwritten
- firefox.exe (PID: 8232)
- msiexec.exe (PID: 9148)
- WinRAR.exe (PID: 8432)
- WinRAR.exe (PID: 6600)
Checks proxy server information
- slui.exe (PID: 9076)
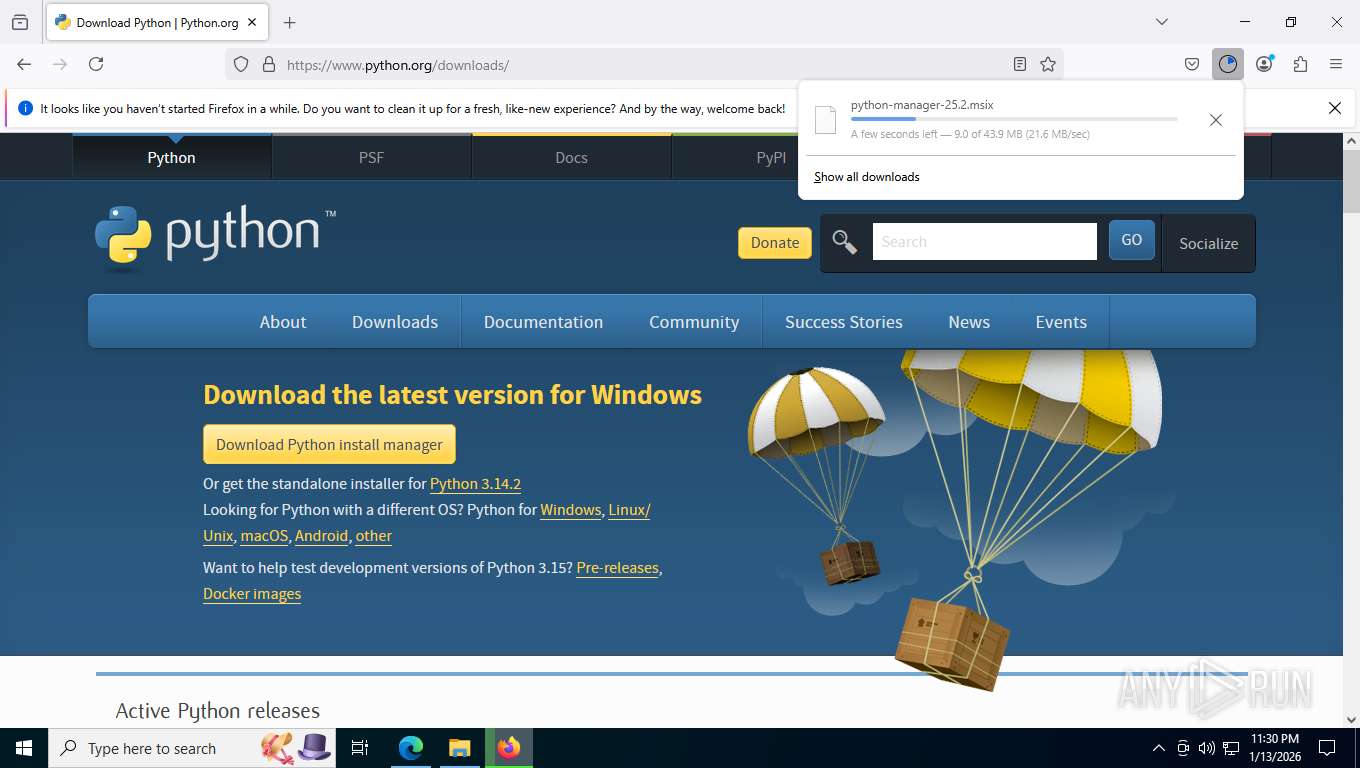
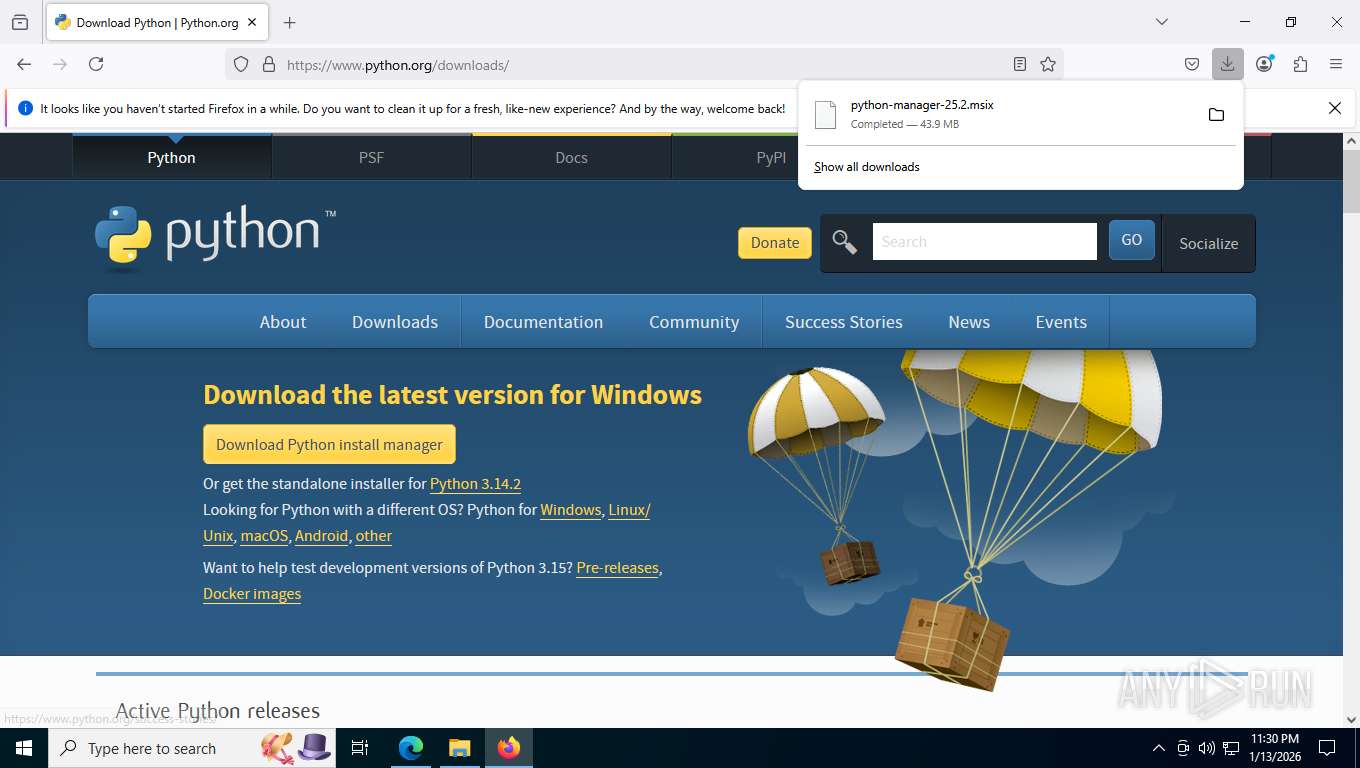
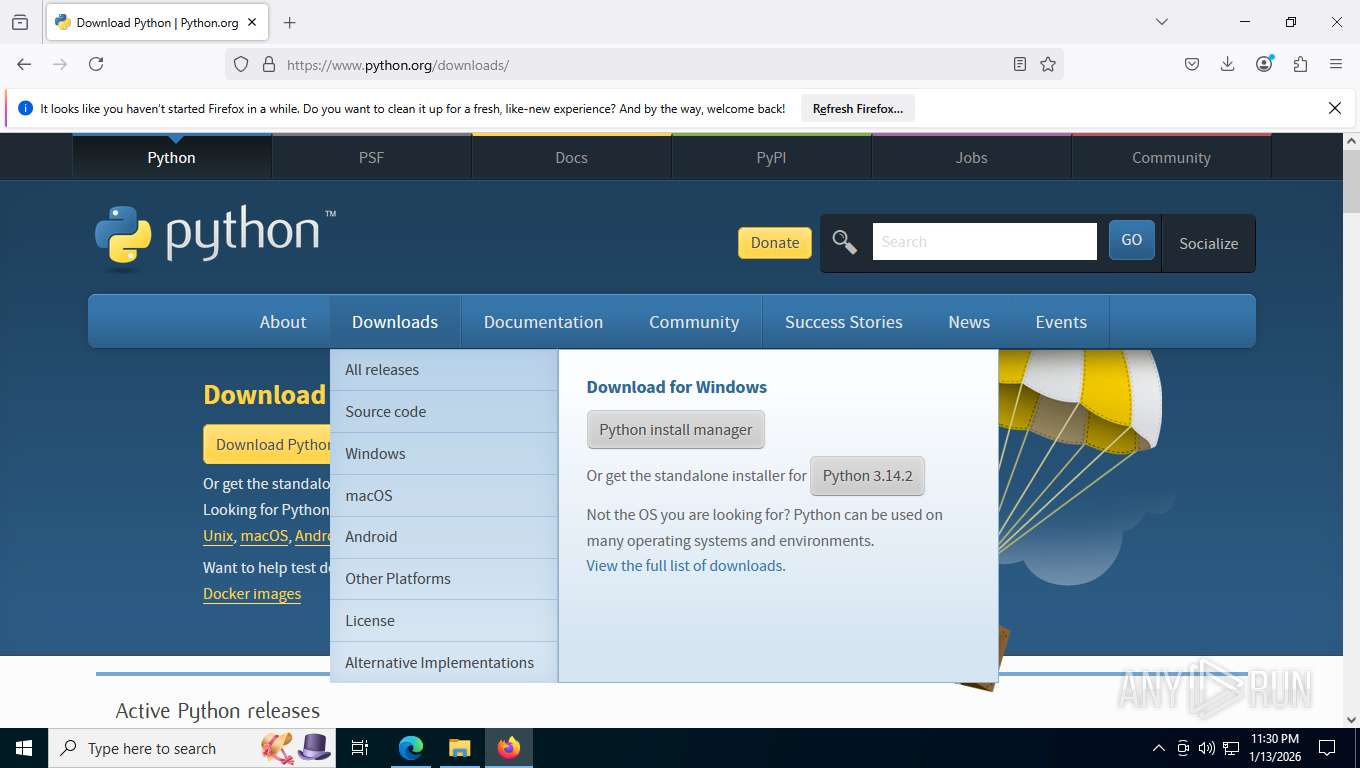
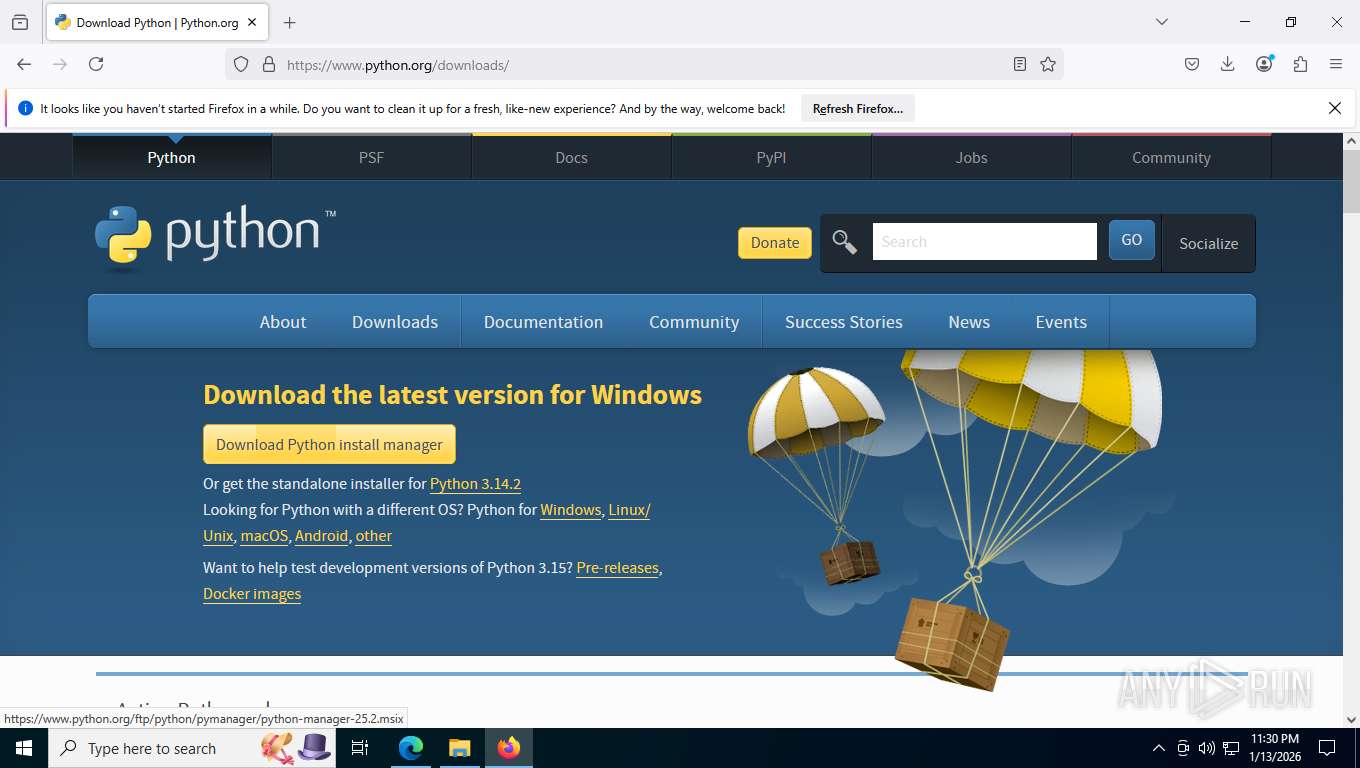
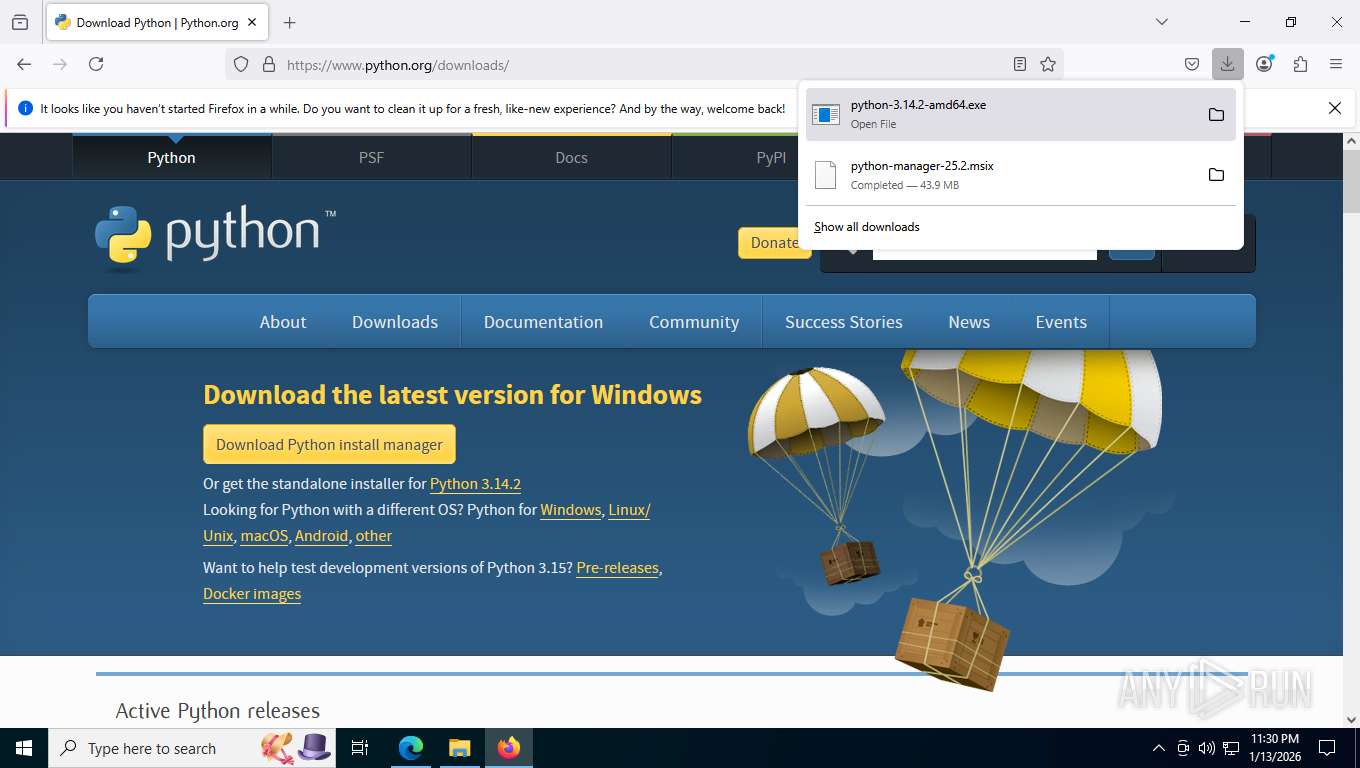
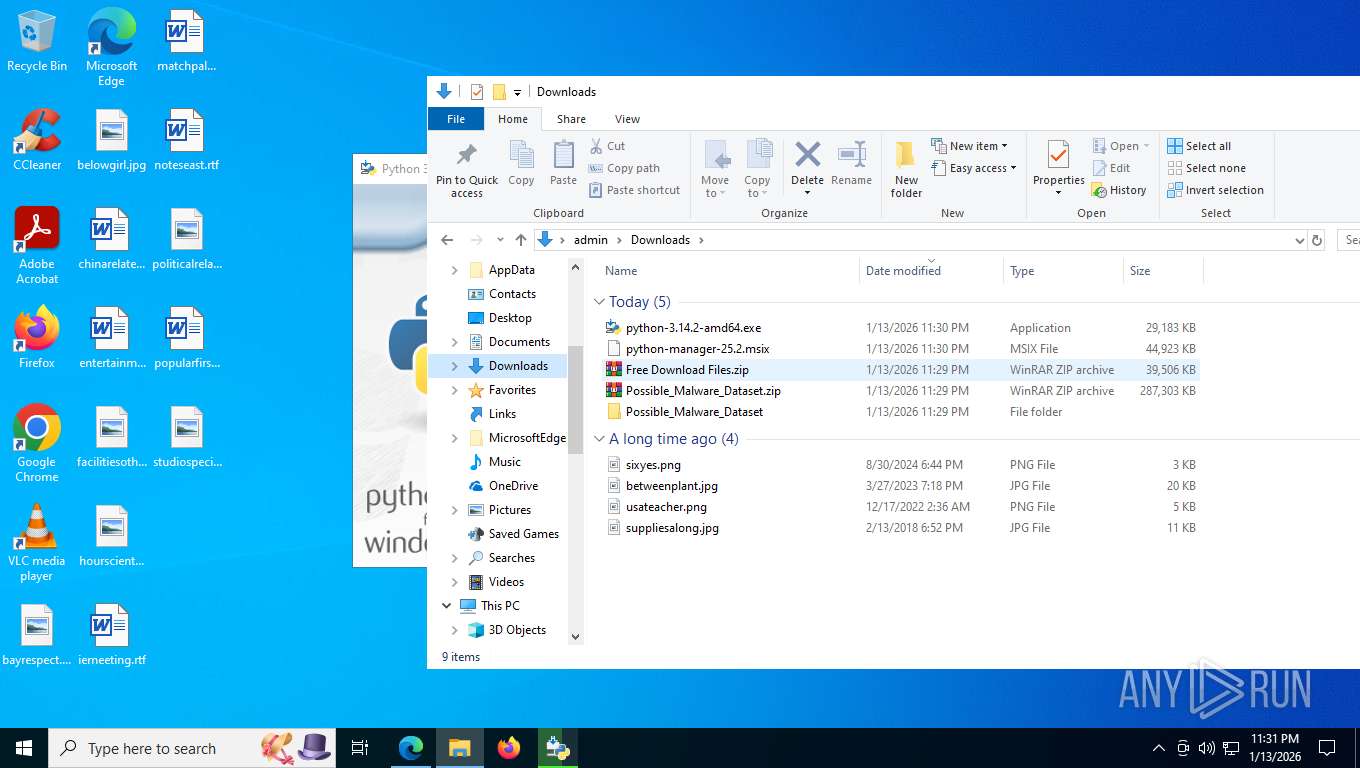
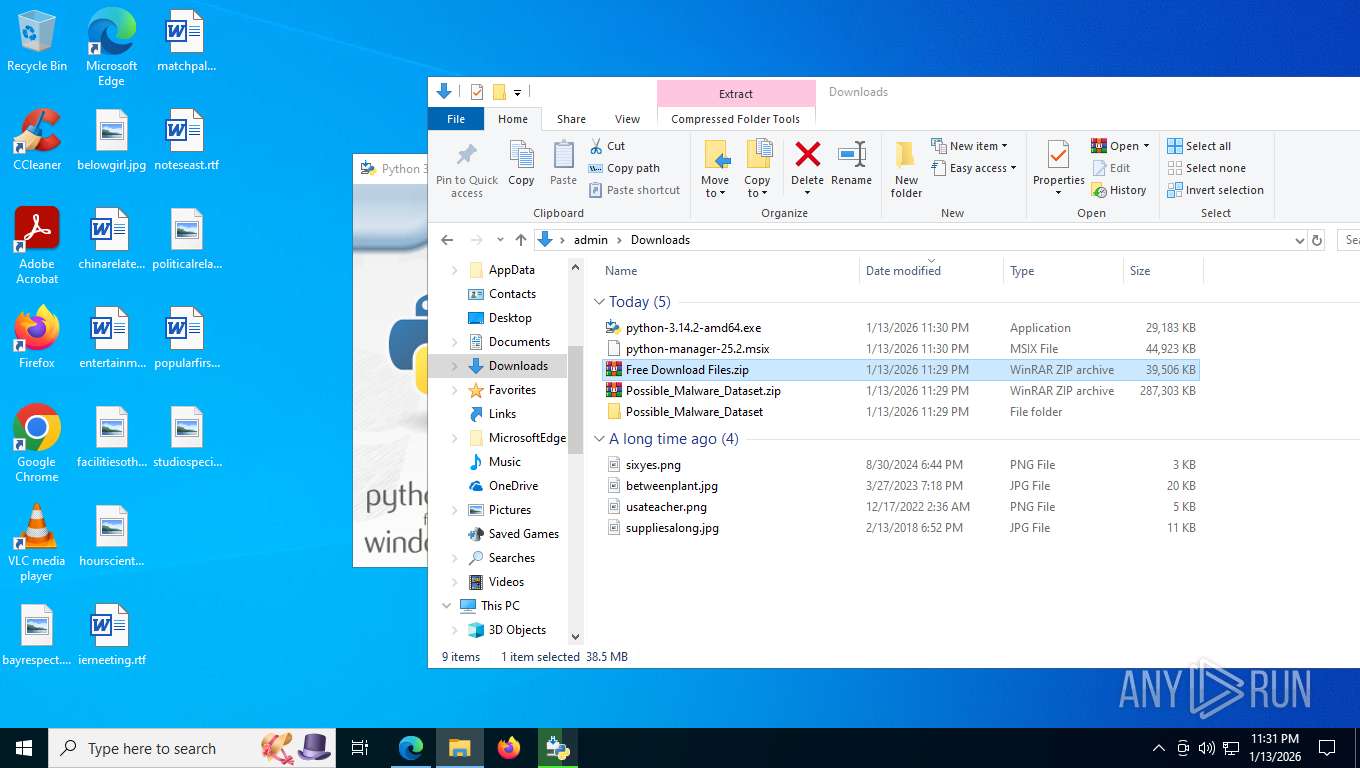
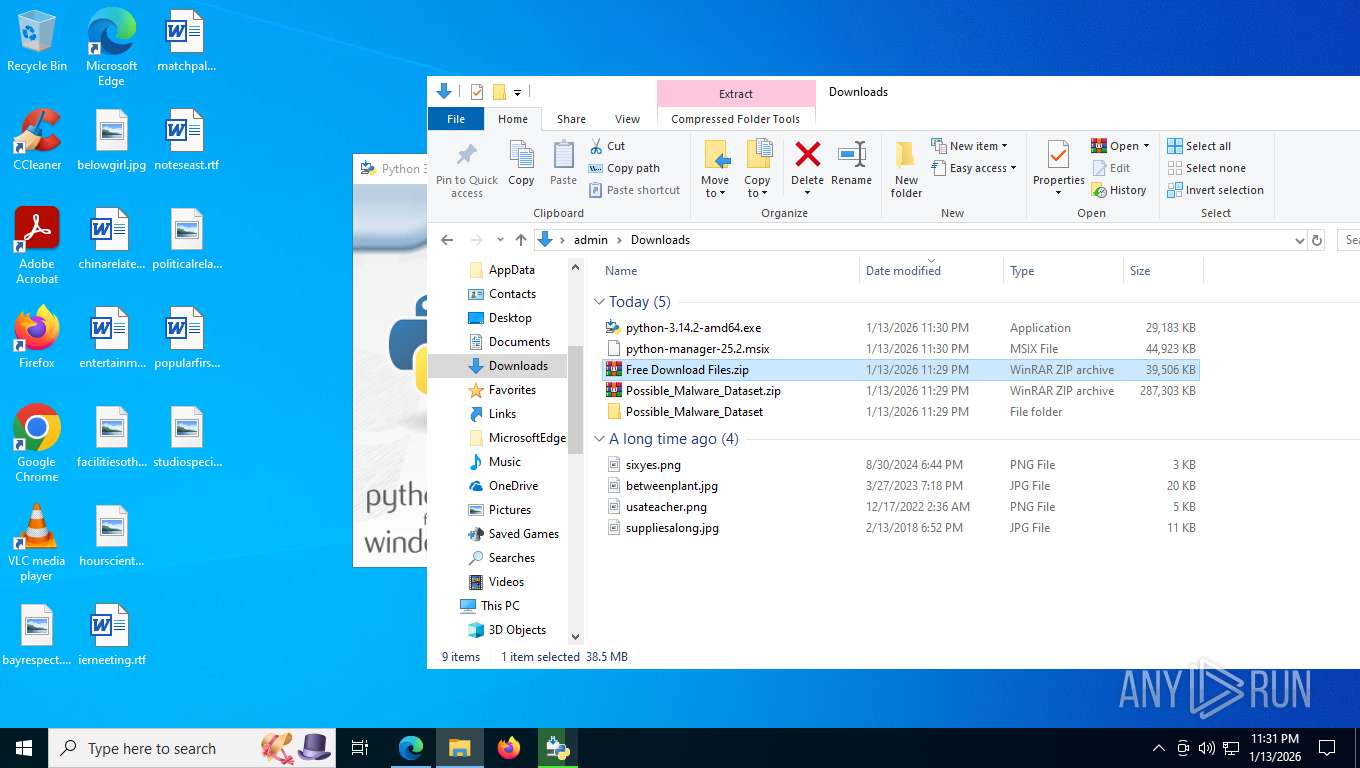
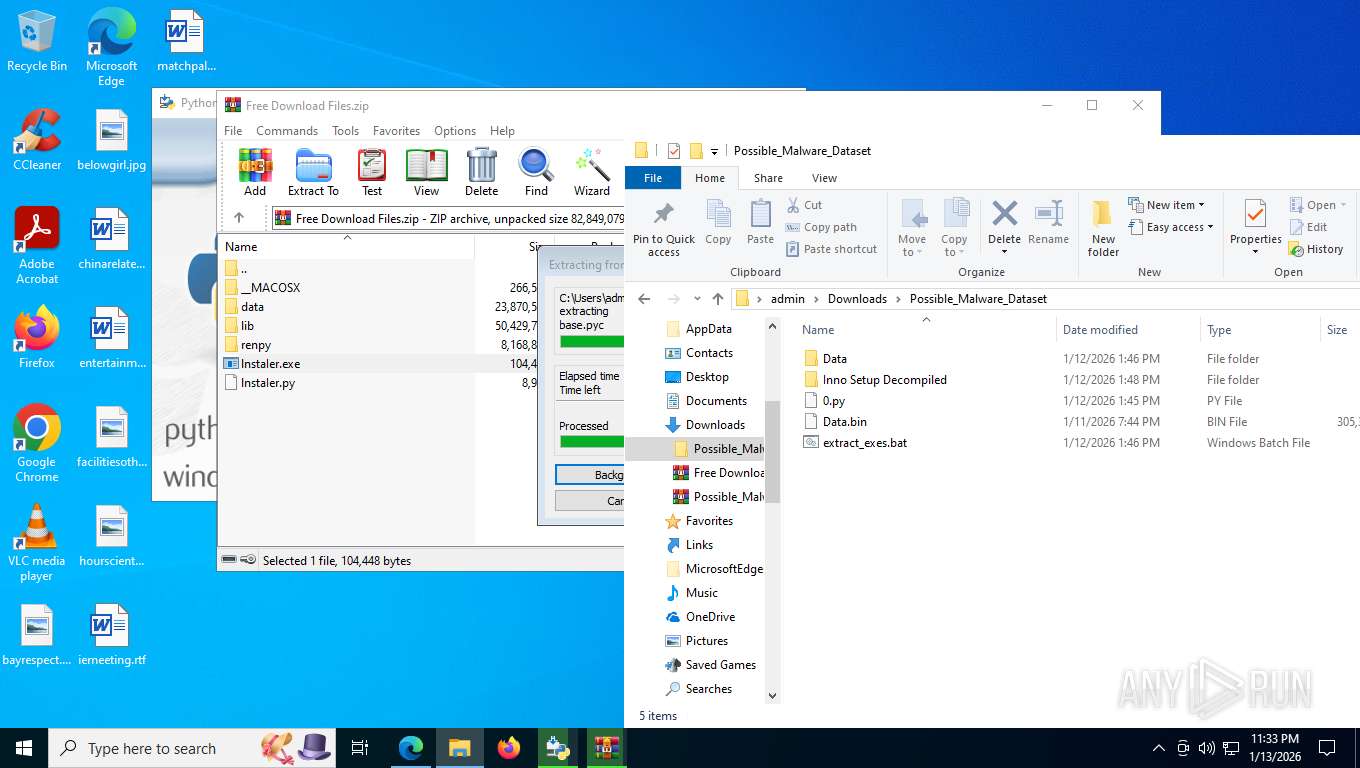
Launching a file from the Downloads directory
- firefox.exe (PID: 8232)
The sample compiled with english language support
- firefox.exe (PID: 8232)
- python-3.14.2-amd64.exe (PID: 9108)
- python-3.14.2-amd64.exe (PID: 7332)
- WinRAR.exe (PID: 8432)
- msiexec.exe (PID: 9148)
- WinRAR.exe (PID: 6600)
Create files in a temporary directory
- python-3.14.2-amd64.exe (PID: 7332)
- python-3.14.2-amd64.exe (PID: 9108)
Creates a software uninstall entry
- python-3.14.2-amd64.exe (PID: 9108)
- msiexec.exe (PID: 9148)
Launching a file from a Registry key
- python-3.14.2-amd64.exe (PID: 9108)
Creates files or folders in the user directory
- python-3.14.2-amd64.exe (PID: 9108)
- msiexec.exe (PID: 9148)
Reads the machine GUID from the registry
- msiexec.exe (PID: 9148)
- python-3.14.2-amd64.exe (PID: 9108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
77
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=24 --always-read-main-dll --field-trial-handle=7440,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=7328 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=35 --always-read-main-dll --field-trial-handle=6216,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=5364 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1448,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=8012 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1844 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6916,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=6432 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5684 -prefsLen 39283 -prefMapHandle 5688 -prefMapSize 273045 -jsInitHandle 5692 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5648 -initialChannelId {284599e3-6294-4f2f-9af2-683c78ccf2bd} -parentPid 8232 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8232" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3300 -prefsLen 37056 -prefMapHandle 3304 -prefMapSize 273045 -jsInitHandle 3308 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3316 -initialChannelId {624de0ab-bf9b-4cfa-8081-d7113e67ce34} -parentPid 8232 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8232" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 3 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2252 -prefsLen 36580 -prefMapHandle 2256 -prefMapSize 273045 -ipcHandle 2160 -initialChannelId {9110356d-ff65-4b37-b529-6cd7e8ef0c1c} -parentPid 8232 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8232" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 2 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=5312,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=6432 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3688 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4156 -prefsLen 45014 -prefMapHandle 4128 -prefMapSize 273045 -jsInitHandle 4136 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4168 -initialChannelId {071b9574-8bea-45a4-b75e-a714cdfd28a7} -parentPid 8232 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8232" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 4028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1480,i,5972539700384671117,15653023390906729929,262144 --variations-seed-version --mojo-platform-channel-handle=7668 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
35 148
Read events
31 094
Write events
3 998
Delete events
56
Modification events
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
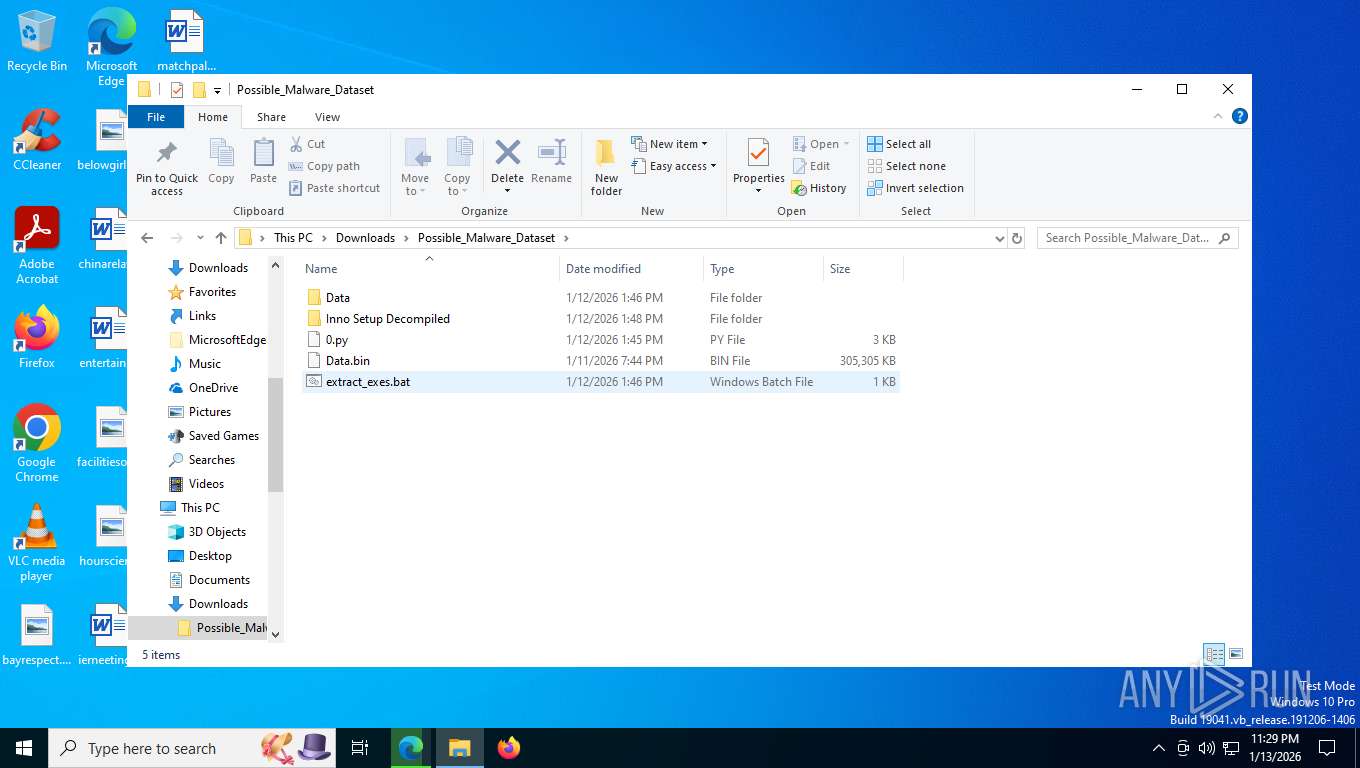
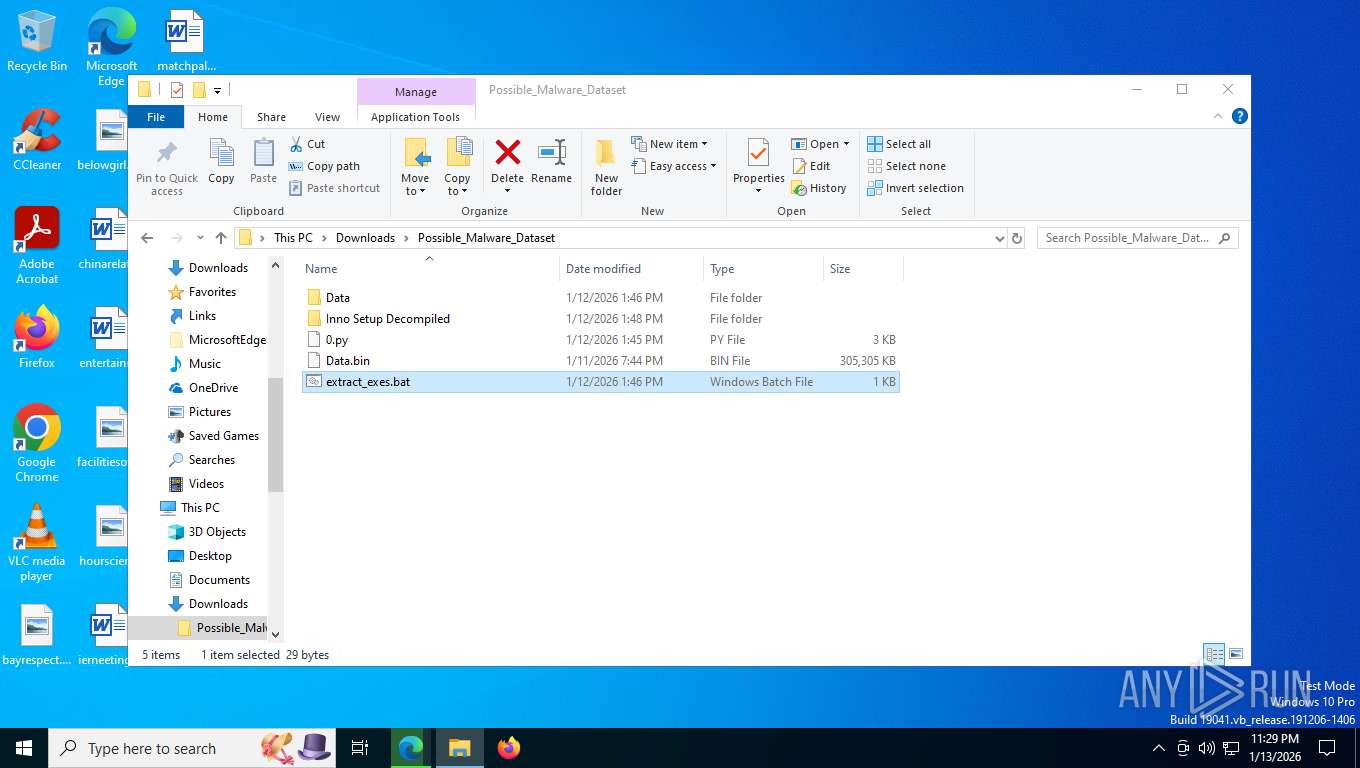
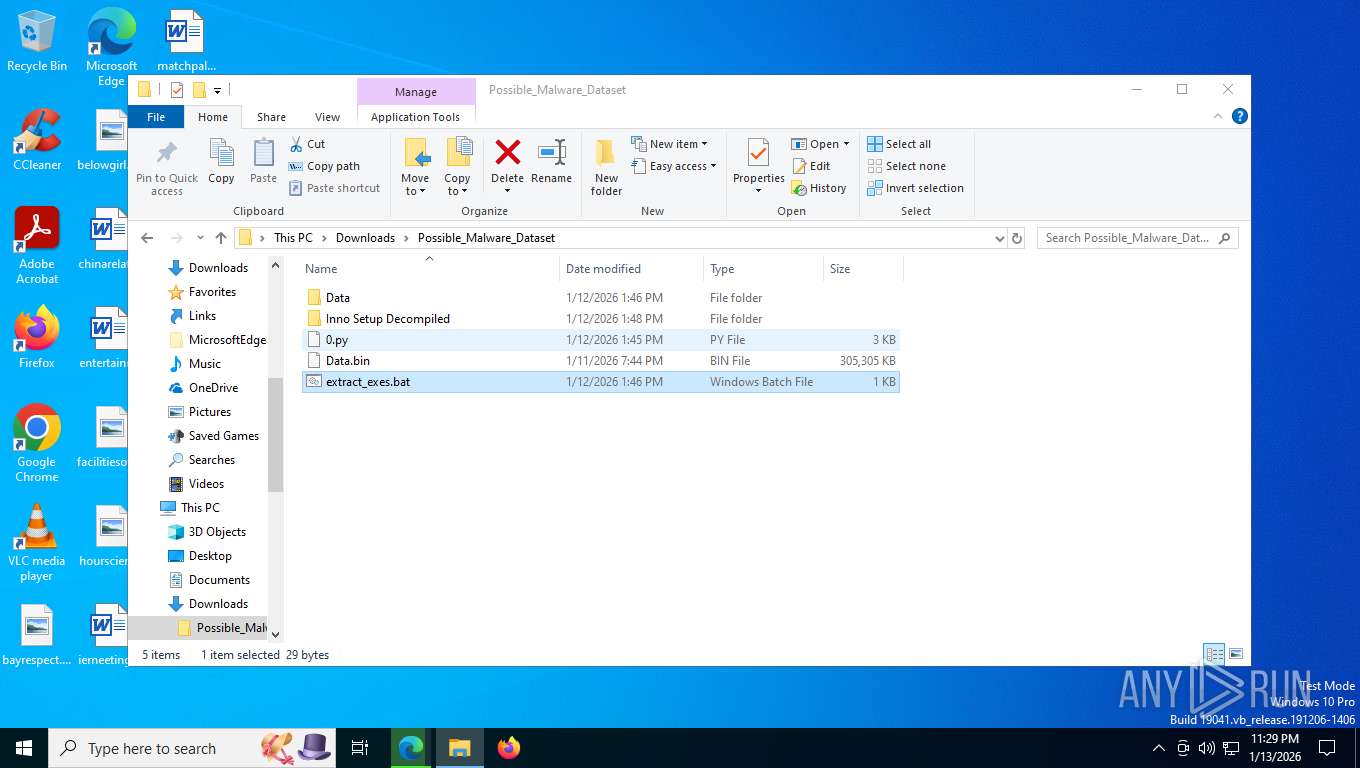
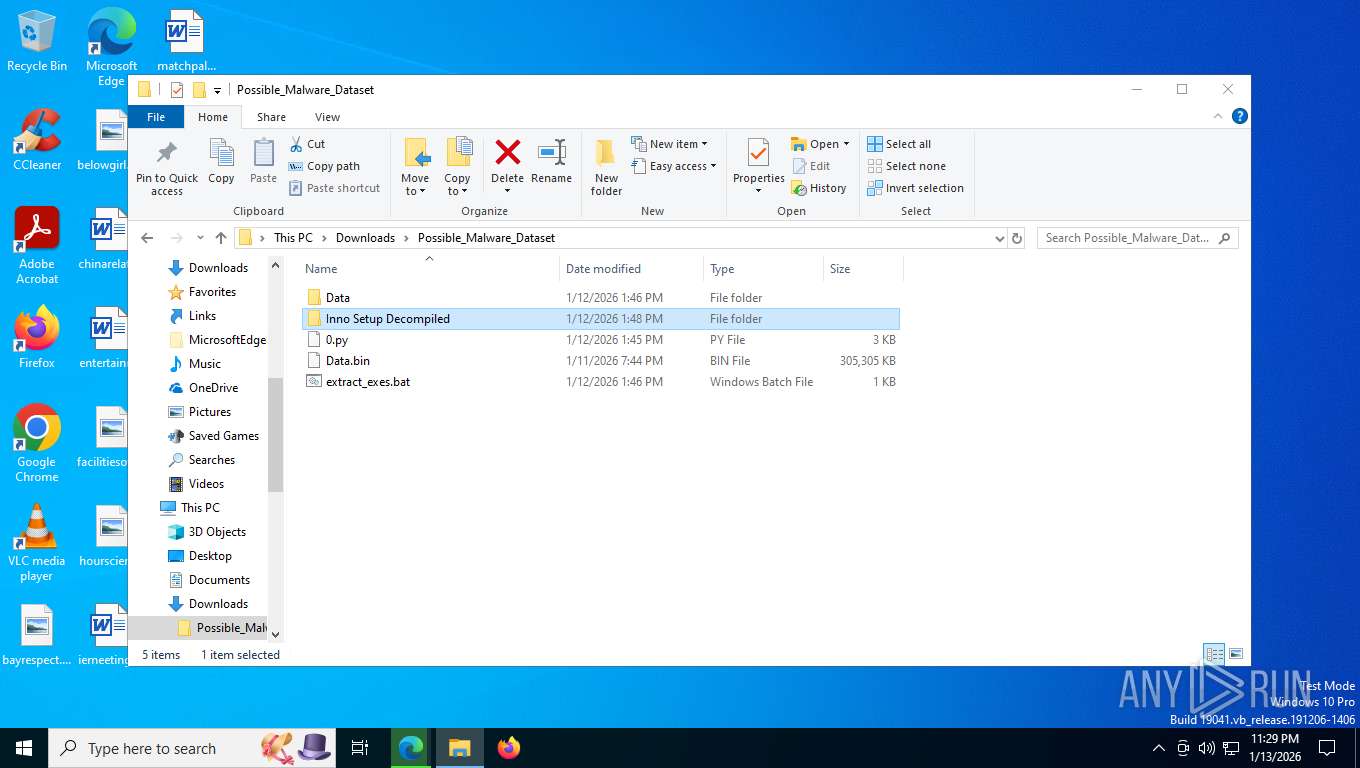
Value: C:\Users\admin\Downloads\Possible_Malware_Dataset.zip | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
96
Suspicious files
2 651
Text files
3 151
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe054.TMP | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe064.TMP | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe064.TMP | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe064.TMP | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe074.TMP | — | |
MD5:— | SHA256:— | |||
| 7620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
489
TCP/UDP connections
228
DNS requests
315
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7944 | msedge.exe | GET | 302 | 104.21.37.45:443 | https://vik1ngfile.site/cdn-cgi/challenge-platform/scripts/jsd/main.js | US | — | — | unknown |
7944 | msedge.exe | GET | 302 | 104.18.94.41:443 | https://challenges.cloudflare.com/turnstile/v0/api.js?onload=showCaptcha | US | — | — | unknown |
7944 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=pYdYe773SyqI1wqY70mAUWD2p8aPxlg6xDGNIiLt5YlMyefrS2lR1dd%2B9UUPKLP9Ztuqy%2F5RBHv99P8Y1A2TDwLkBhX%2FXbd%2FzSQ0tr%2FjuQ%3D%3D | US | — | — | unknown |
7944 | msedge.exe | GET | 200 | 104.18.94.41:443 | https://challenges.cloudflare.com/turnstile/v0/g/fc21b7e0d793/api.js | US | text | 49.2 Kb | unknown |
7944 | msedge.exe | GET | 200 | 34.160.111.145:443 | https://ipv4.jsonip.com/getIP4 | US | text | 30 b | unknown |
7944 | msedge.exe | POST | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=pYdYe773SyqI1wqY70mAUWD2p8aPxlg6xDGNIiLt5YlMyefrS2lR1dd%2B9UUPKLP9Ztuqy%2F5RBHv99P8Y1A2TDwLkBhX%2FXbd%2FzSQ0tr%2FjuQ%3D%3D | US | — | — | unknown |
7944 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7944 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:9fbJl9ZB5GEpYYW5onqQ5J5LjRyndJ5ikSxw5Kh_ppA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
7944 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
7944 | msedge.exe | GET | 200 | 104.21.37.45:443 | https://vik1ngfile.site/f/yYgTtSQFcg | US | html | 19.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5304 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7944 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7944 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7944 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7944 | msedge.exe | 188.114.96.3:443 | vikingfile.com | CLOUDFLARENET | US | whitelisted |
7944 | msedge.exe | 104.18.94.41:443 | challenges.cloudflare.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vikingfile.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
vik1ngfile.site |
| unknown |
www.bing.com |
| whitelisted |
ping.fb-cdn.net |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
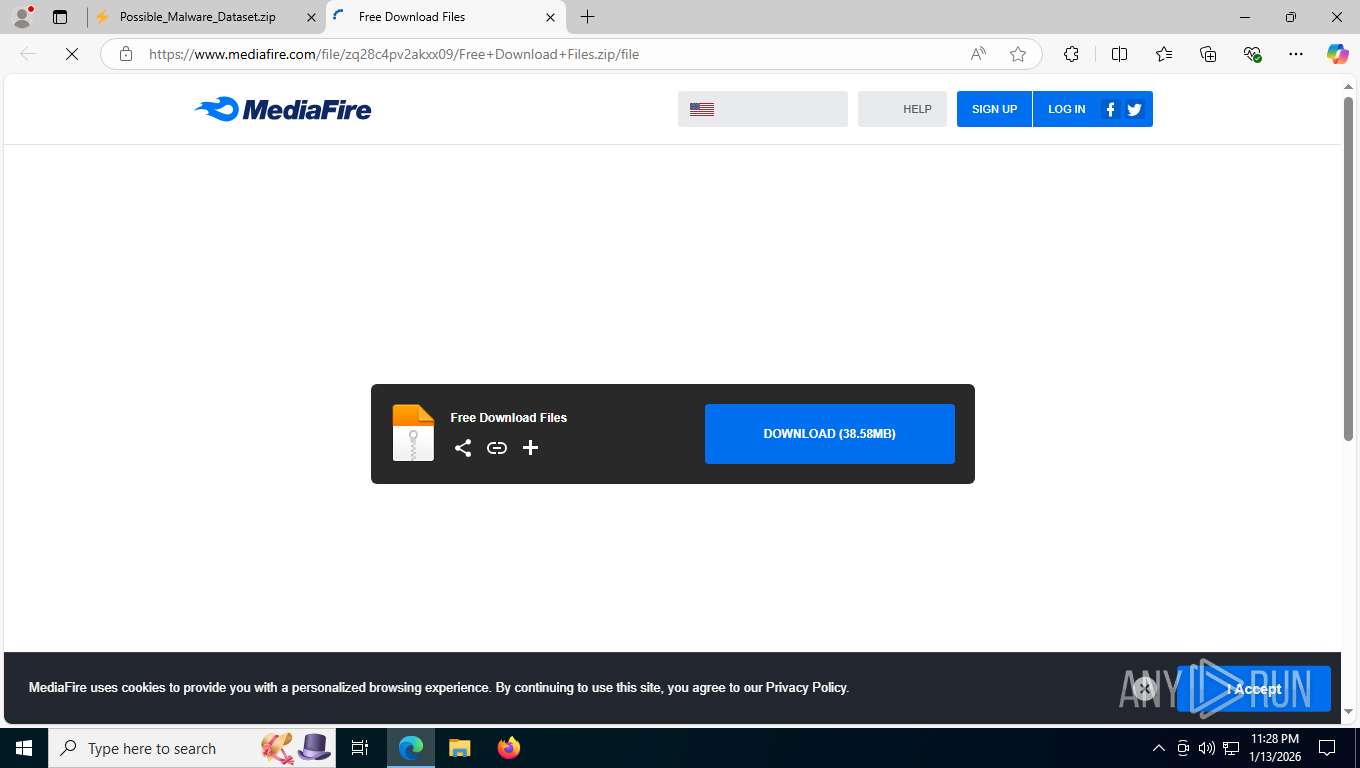
7944 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain (vikingfile .com) |
7944 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain (vikingfile .com) |
7944 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7944 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7944 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7944 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
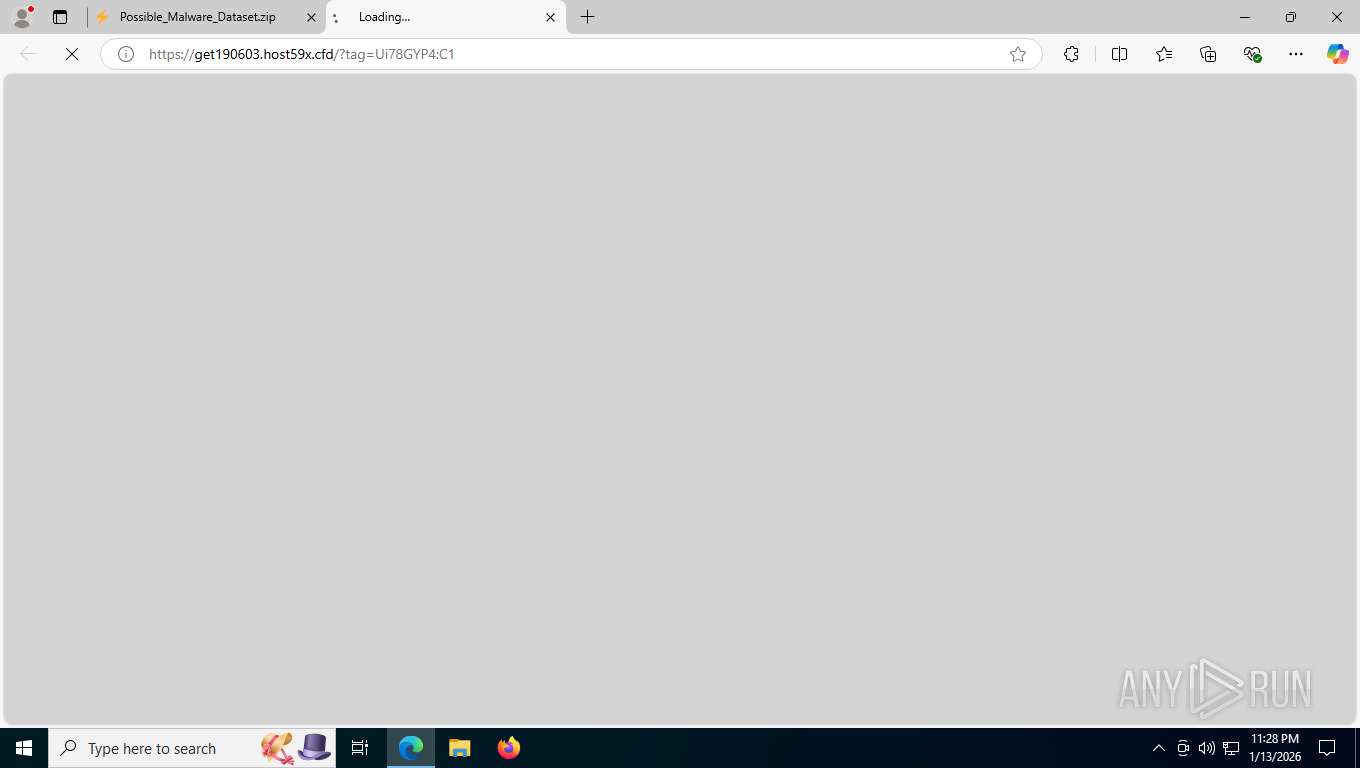
7944 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Malicious hex-DGA Pattern (.cfd TLD) |
7944 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
7944 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7944 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Malicious hex-DGA Pattern (.cfd TLD) |