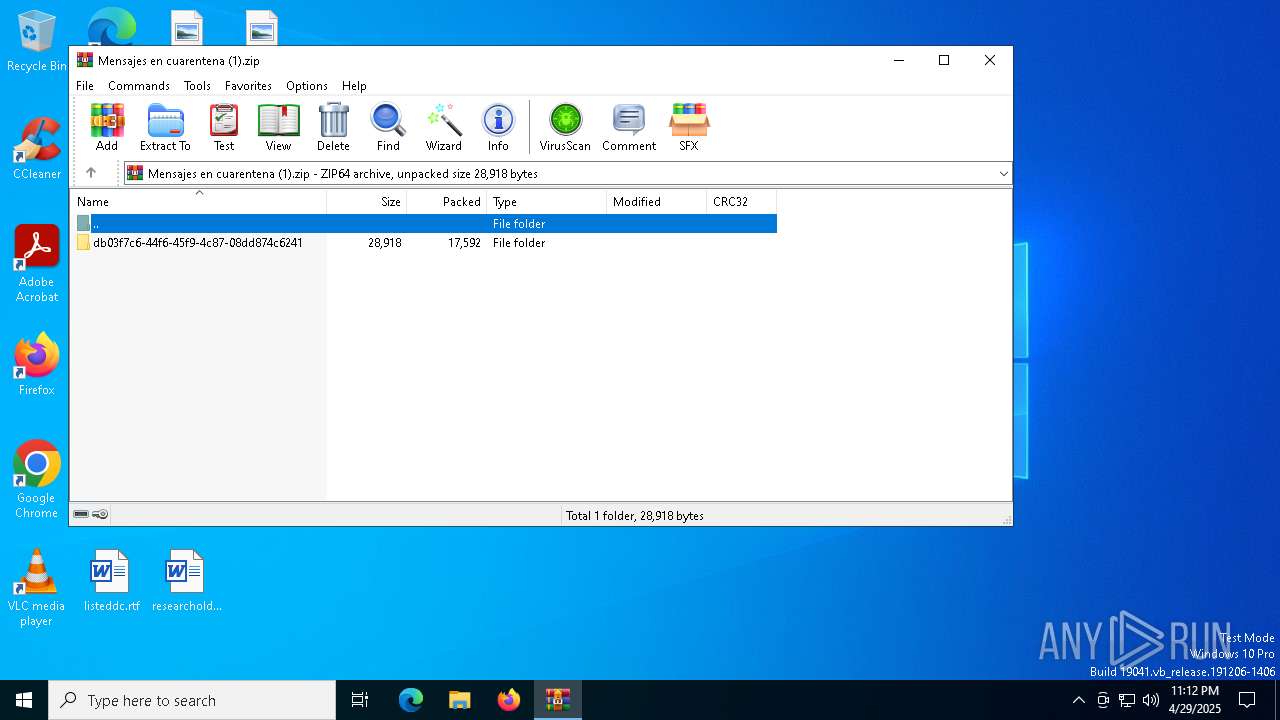
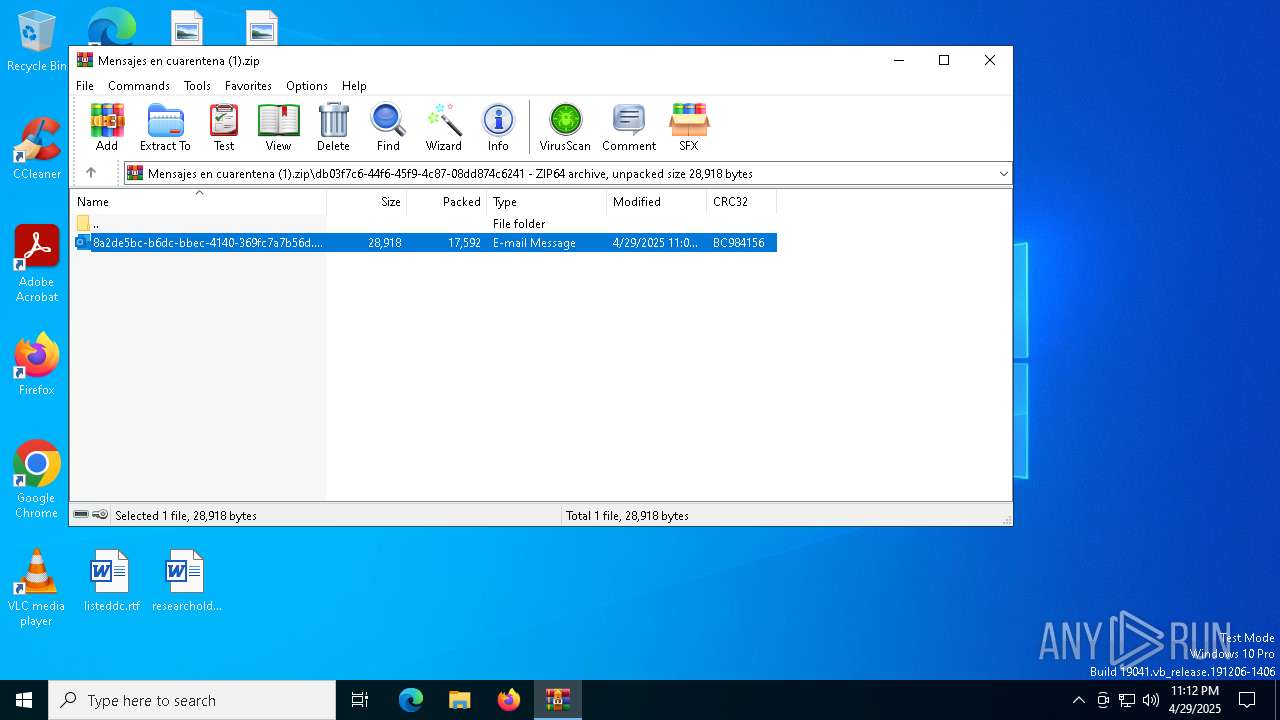
| File name: | Mensajes en cuarentena (1).zip |
| Full analysis: | https://app.any.run/tasks/5ed31fae-c8f5-499c-8ea0-d8aaf4ebb5dc |
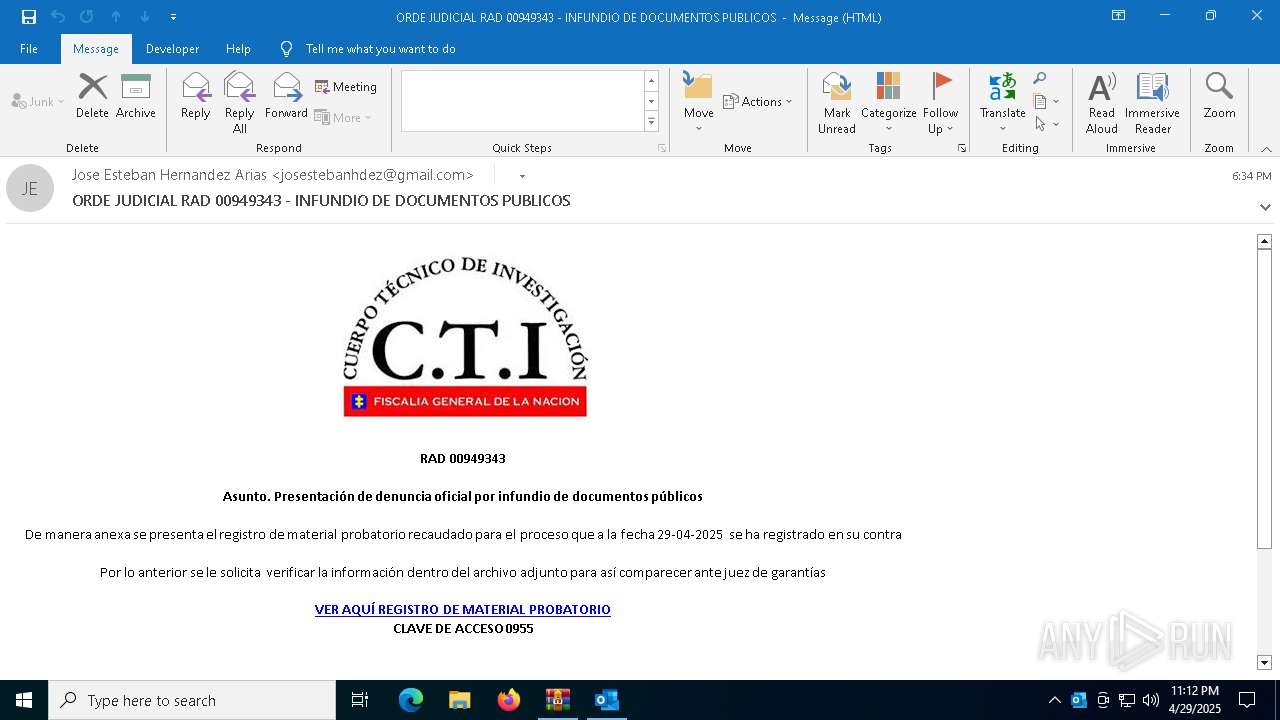
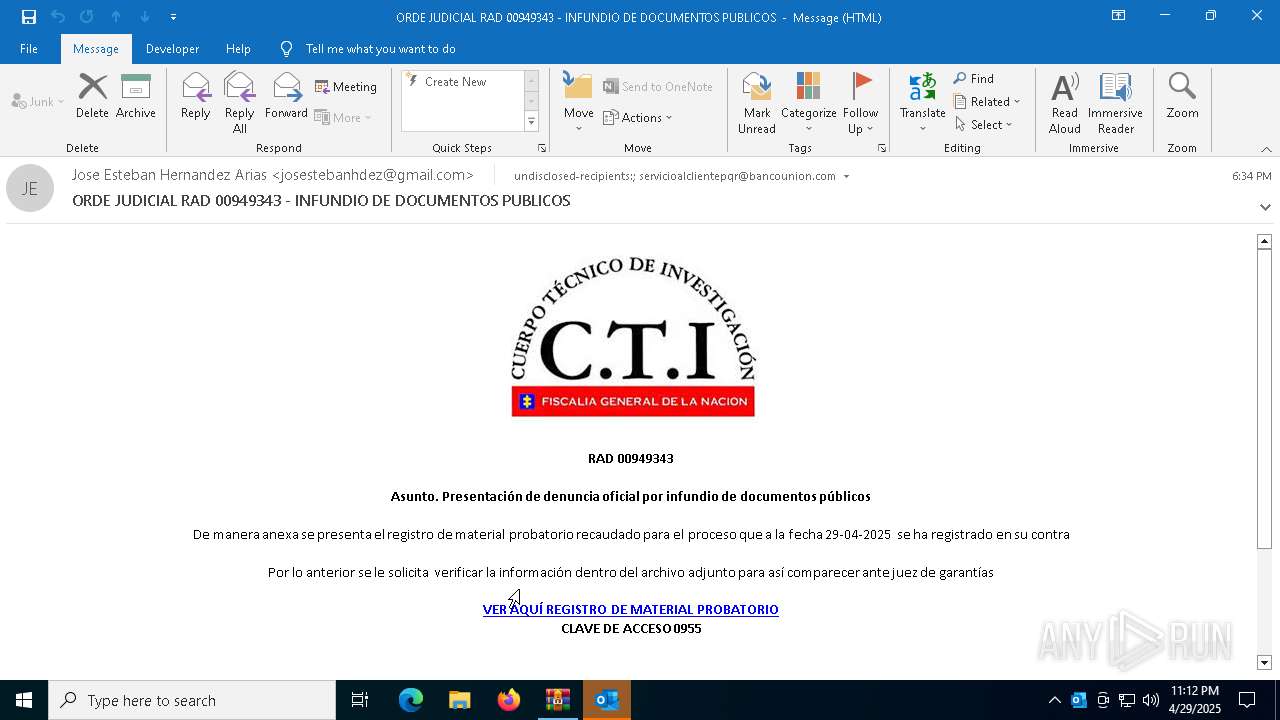
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 23:12:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
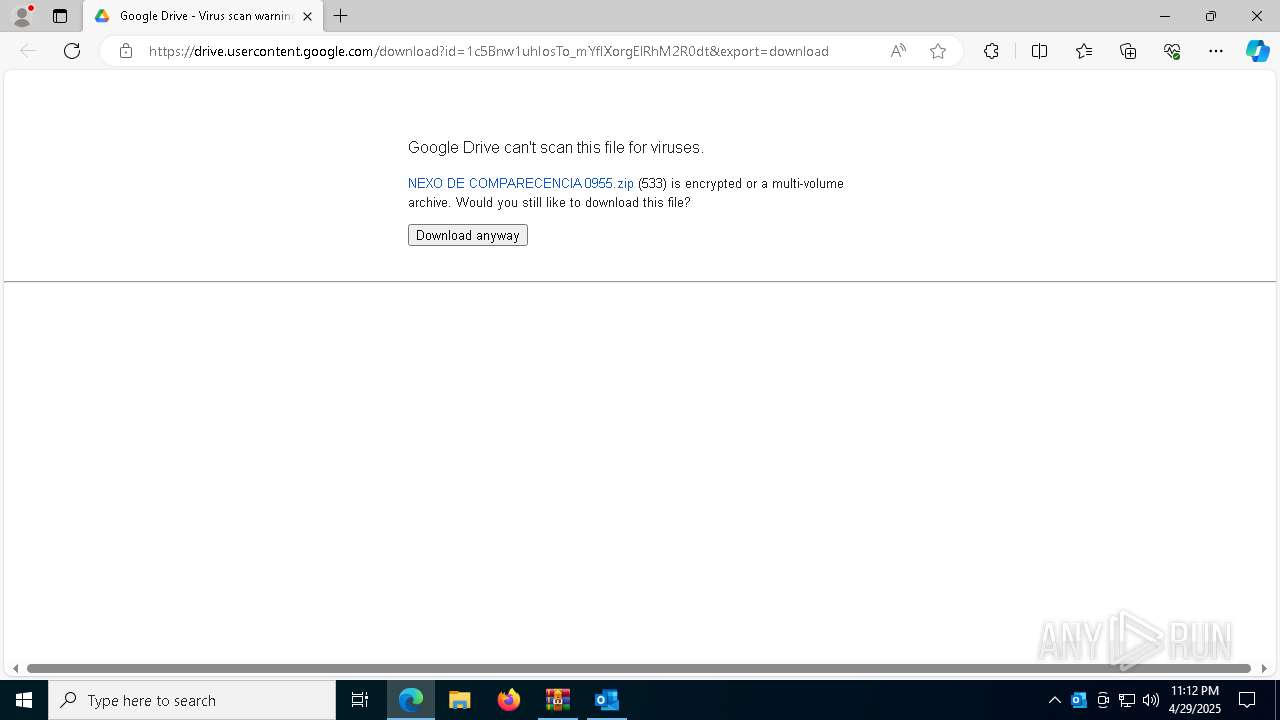
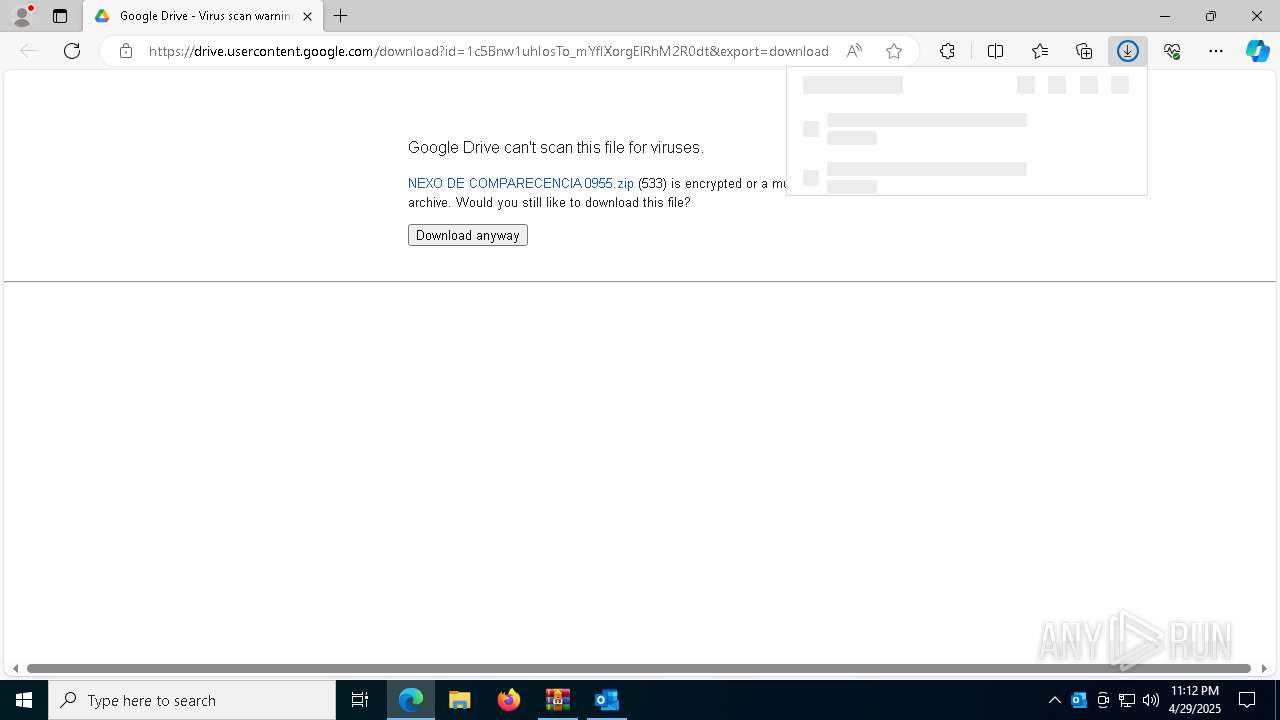
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 9CCBA8B4B989FB86E78D885BEEB7F6AF |
| SHA1: | 1FFA0DA99960A64D9E8945B49C4970130B4073E9 |
| SHA256: | 5E6A631D99A4BE7B0BE5A1231E24AC632791AFF01109E4C4B688B100AD40CA2F |
| SSDEEP: | 384:1HRY7XVMGD9GRBQRgOJ6Ht7FJplyZ8syTs/jjDVlVCfAhzsd:t6O+GUgtzplyZty4/DpCfAI |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Run PowerShell with an invisible window
- powershell.exe (PID: 5072)
- powershell.exe (PID: 4896)
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 1180)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5072)
SUSPICIOUS
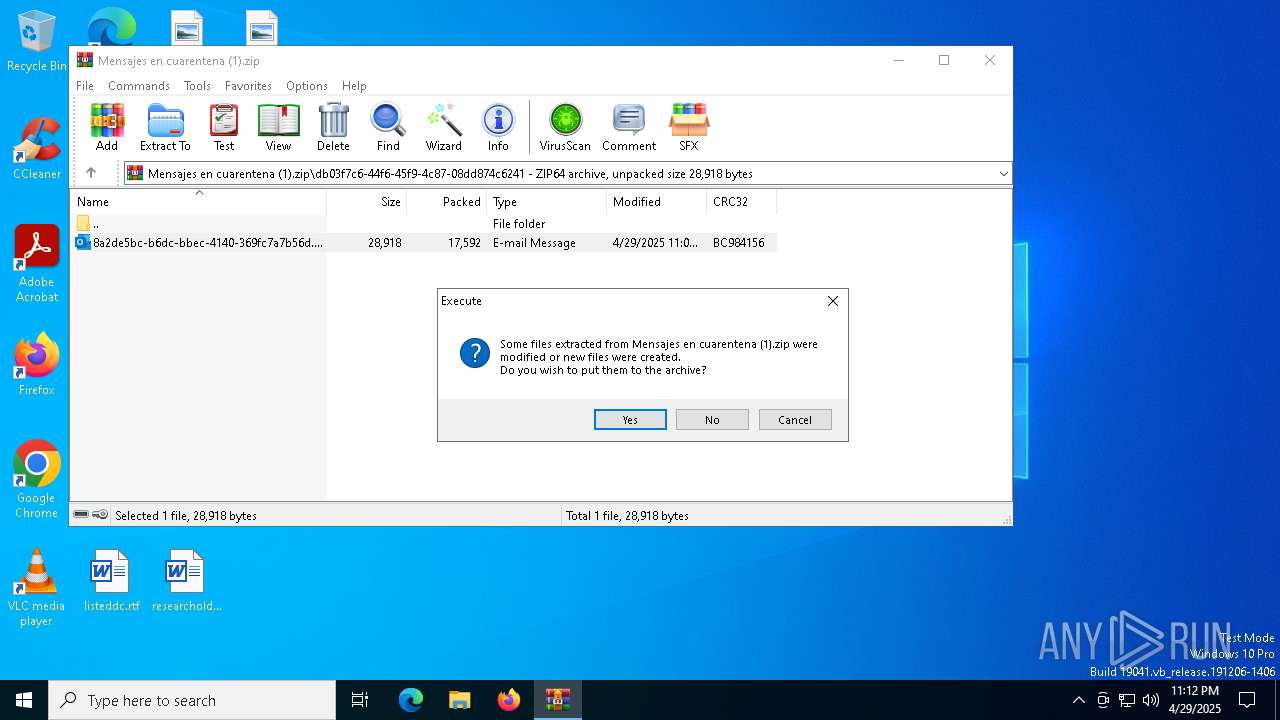
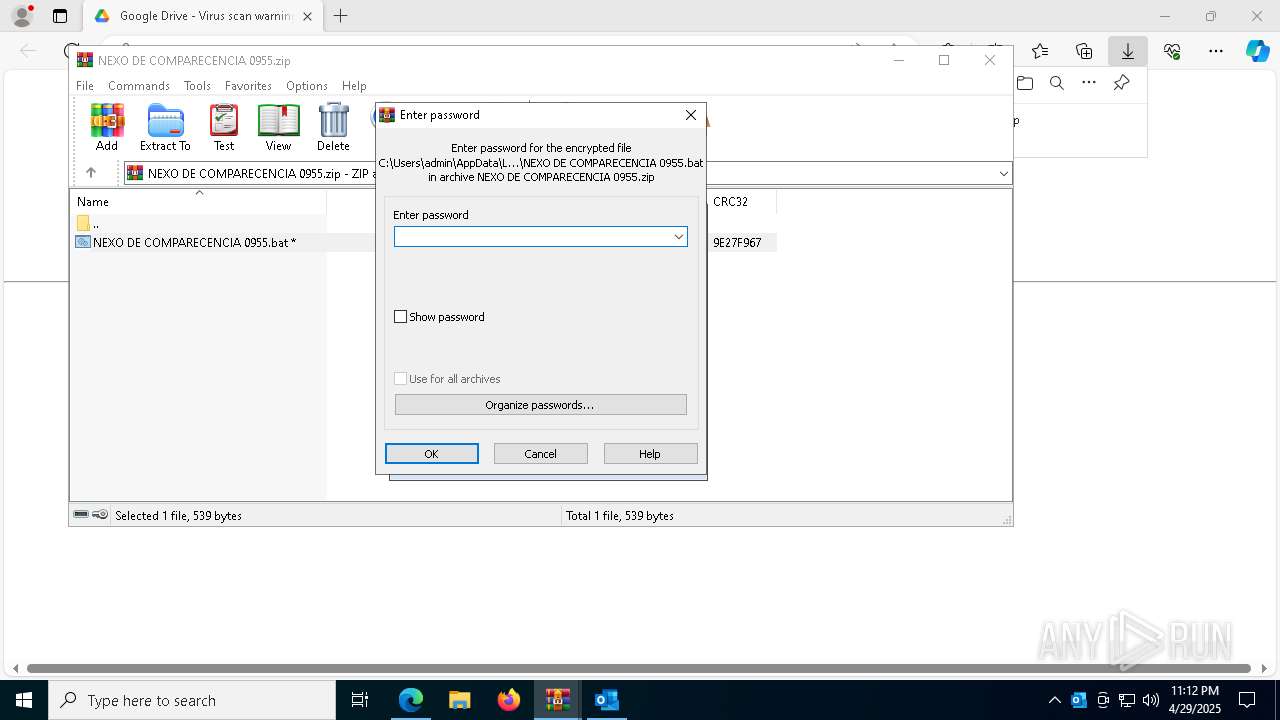
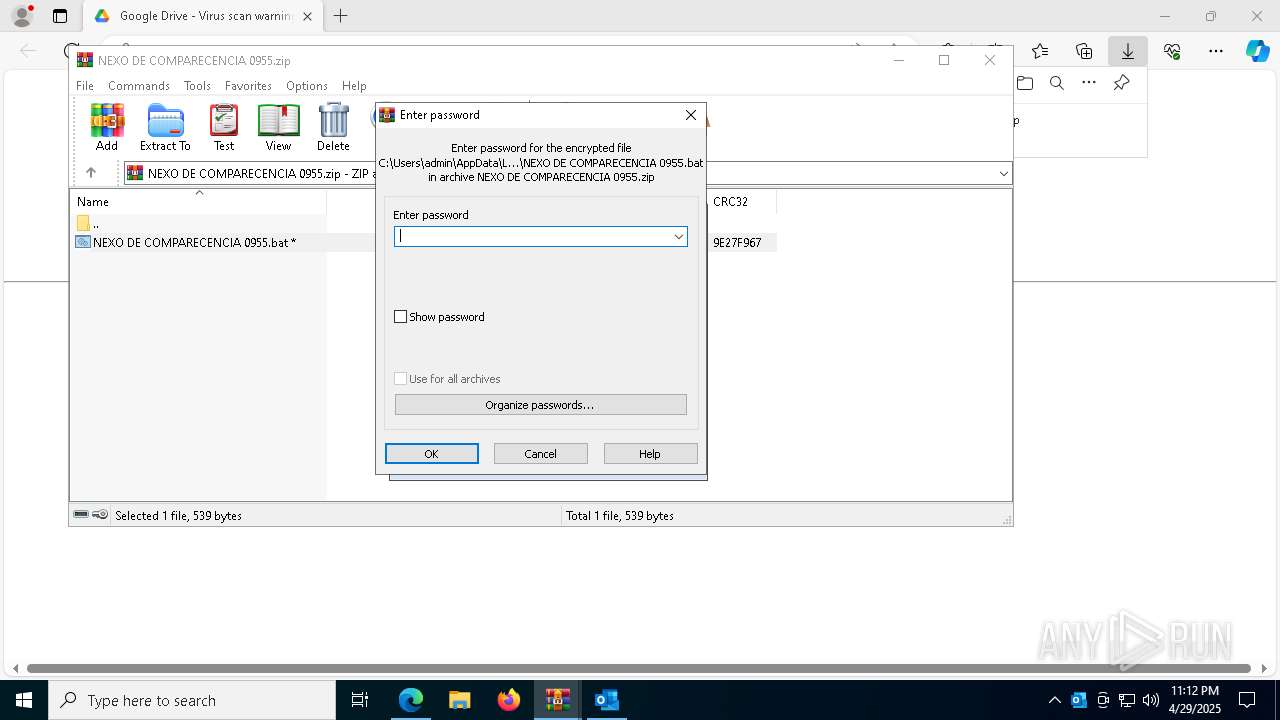
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2320)
- WinRAR.exe (PID: 8004)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 2320)
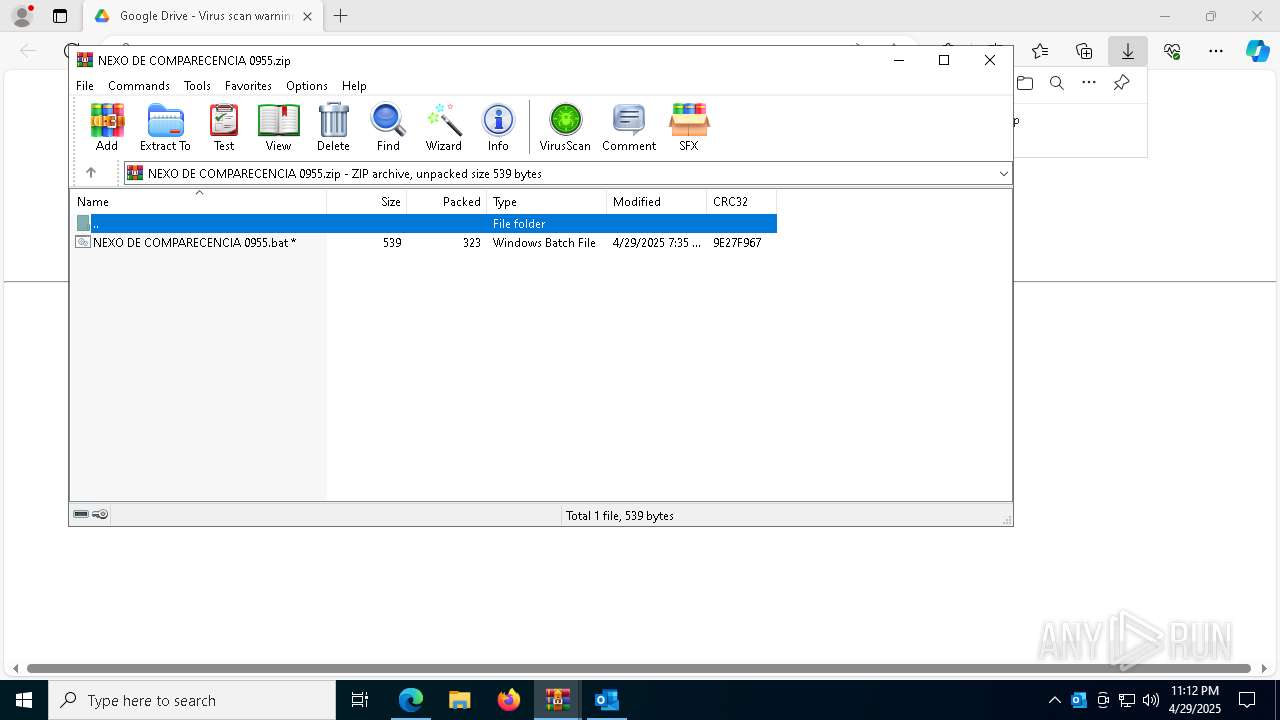
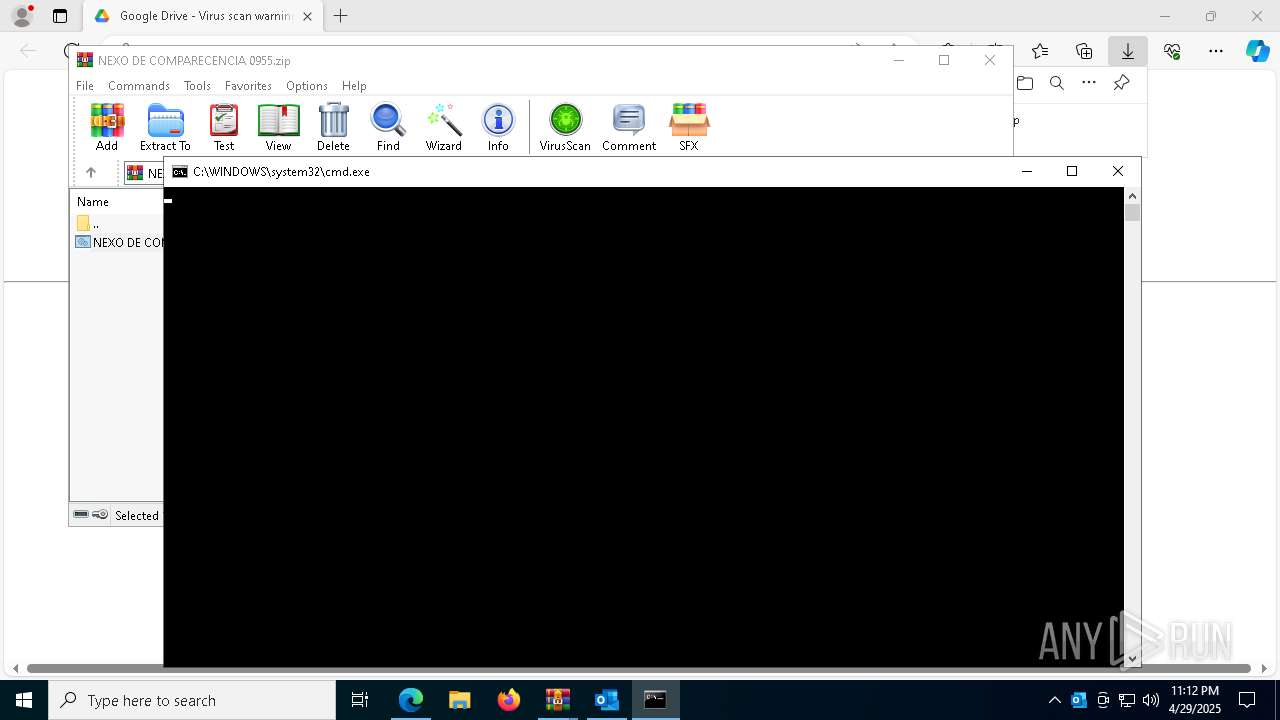
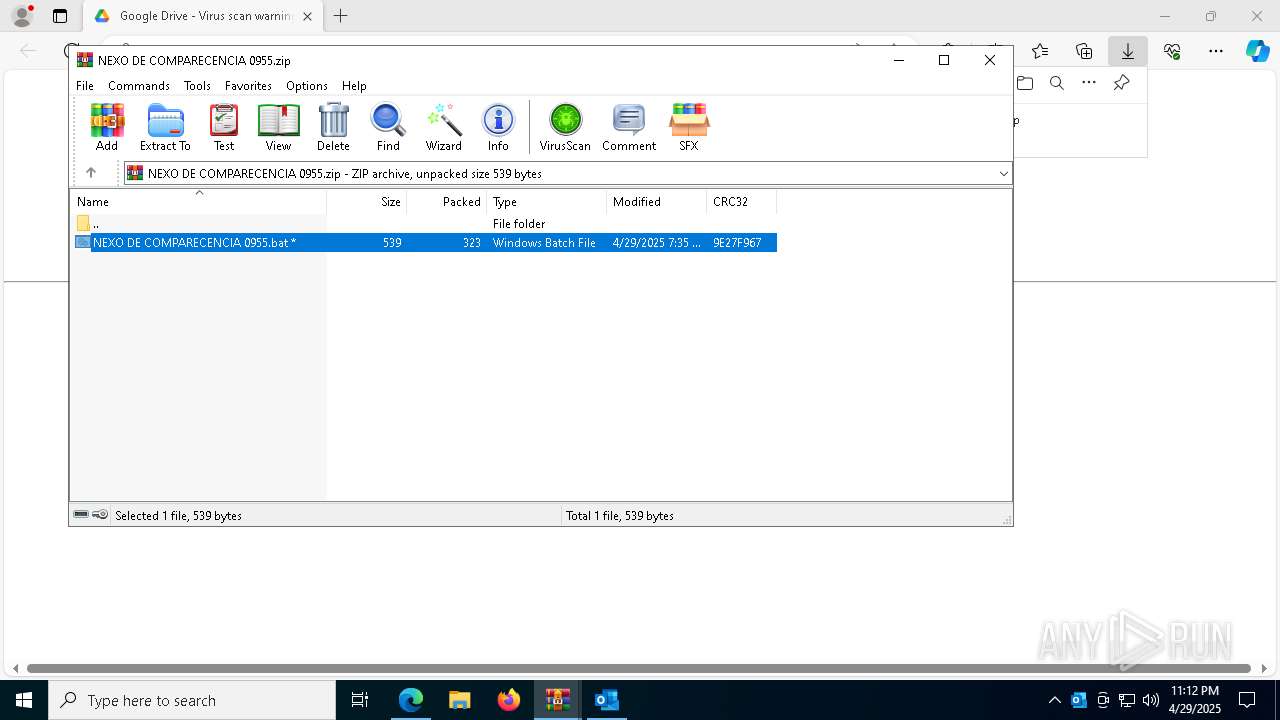
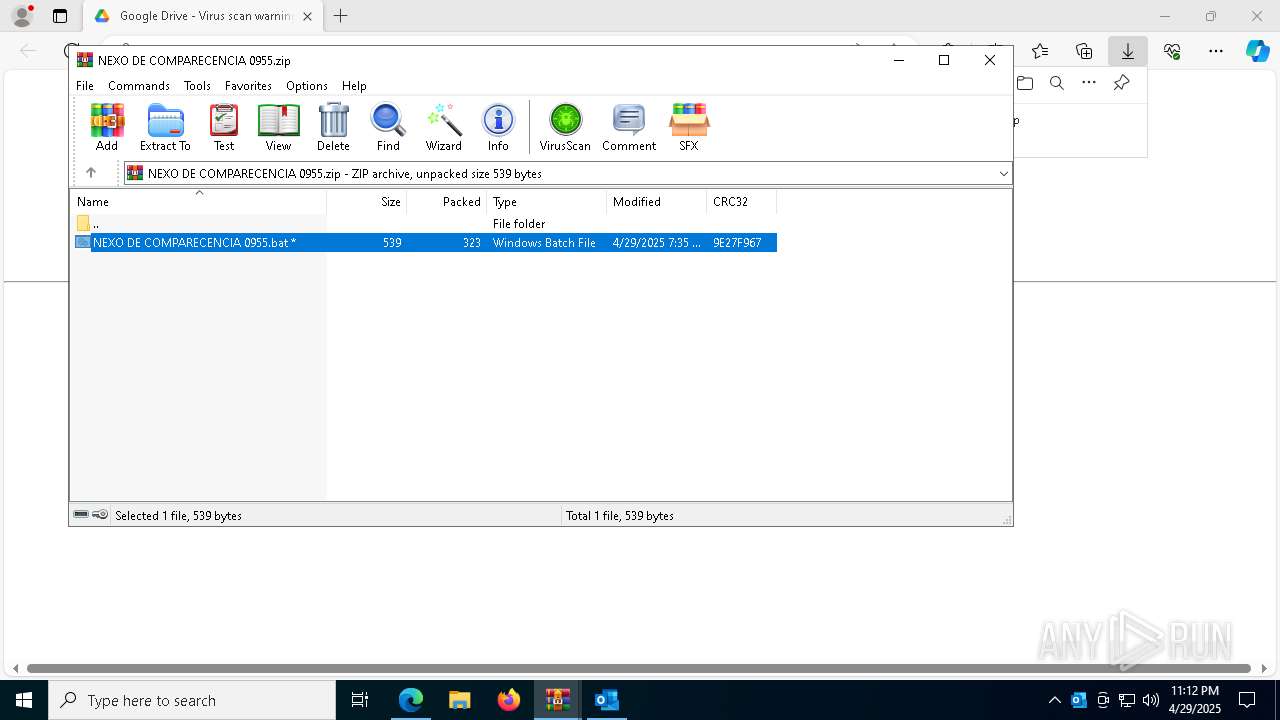
Executing commands from a ".bat" file
- WinRAR.exe (PID: 8004)
- powershell.exe (PID: 5072)
- powershell.exe (PID: 4896)
The process executes VB scripts
- cmd.exe (PID: 2192)
- cmd.exe (PID: 5008)
Runs WScript without displaying logo
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Potential Corporate Privacy Violation
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
- powershell.exe (PID: 5072)
- powershell.exe (PID: 4896)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 8004)
- powershell.exe (PID: 5072)
- powershell.exe (PID: 4896)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2192)
- cmd.exe (PID: 5008)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Executes script without checking the security policy
- powershell.exe (PID: 5072)
- powershell.exe (PID: 4896)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5072)
Base64-obfuscated command line is found
- wscript.exe (PID: 3020)
- wscript.exe (PID: 7640)
Connects to unusual port
- InstallUtil.exe (PID: 1180)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2908)
- cmd.exe (PID: 968)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 1180)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 3020)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2320)
- msedge.exe (PID: 5112)
Application launched itself
- msedge.exe (PID: 5112)
Reads the computer name
- identity_helper.exe (PID: 7816)
Checks supported languages
- identity_helper.exe (PID: 7816)
Reads Environment values
- identity_helper.exe (PID: 7816)
Checks proxy server information
- wscript.exe (PID: 7640)
- powershell.exe (PID: 5072)
- wscript.exe (PID: 3020)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5072)
Disables trace logs
- powershell.exe (PID: 5072)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
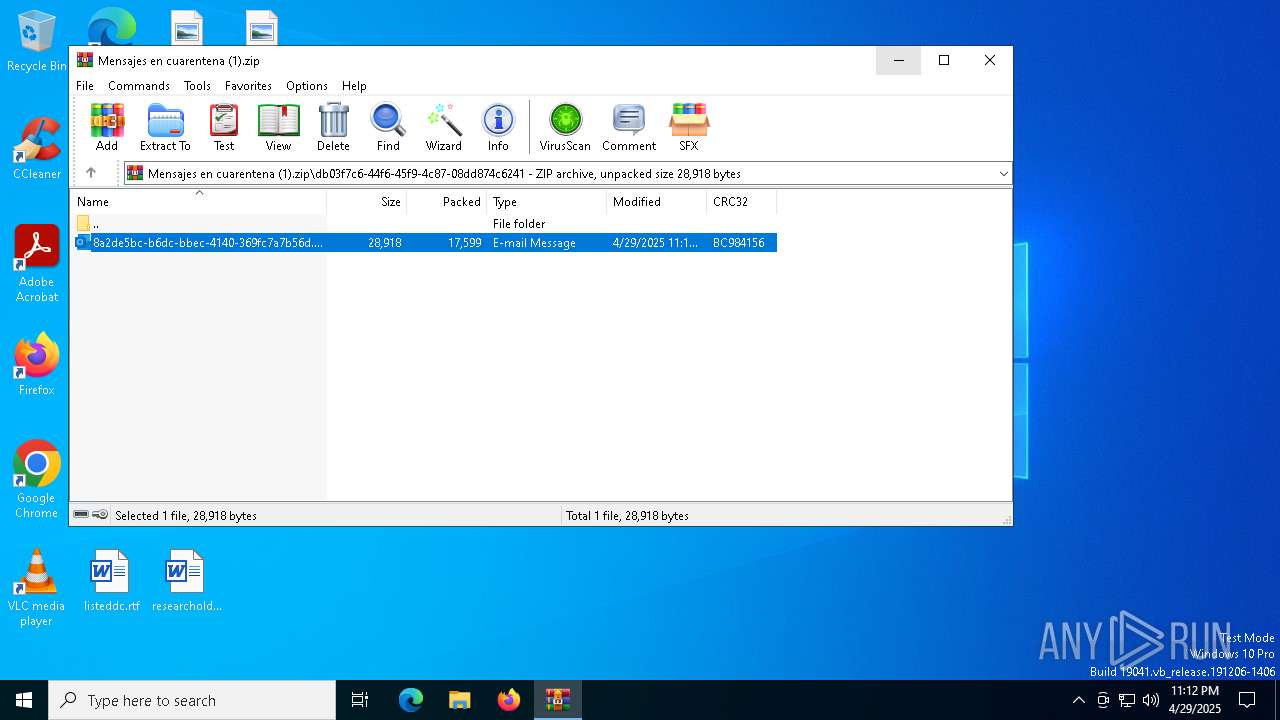
| ZipModifyDate: | 2025:04:29 23:09:52 |
| ZipCRC: | 0xbc984156 |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
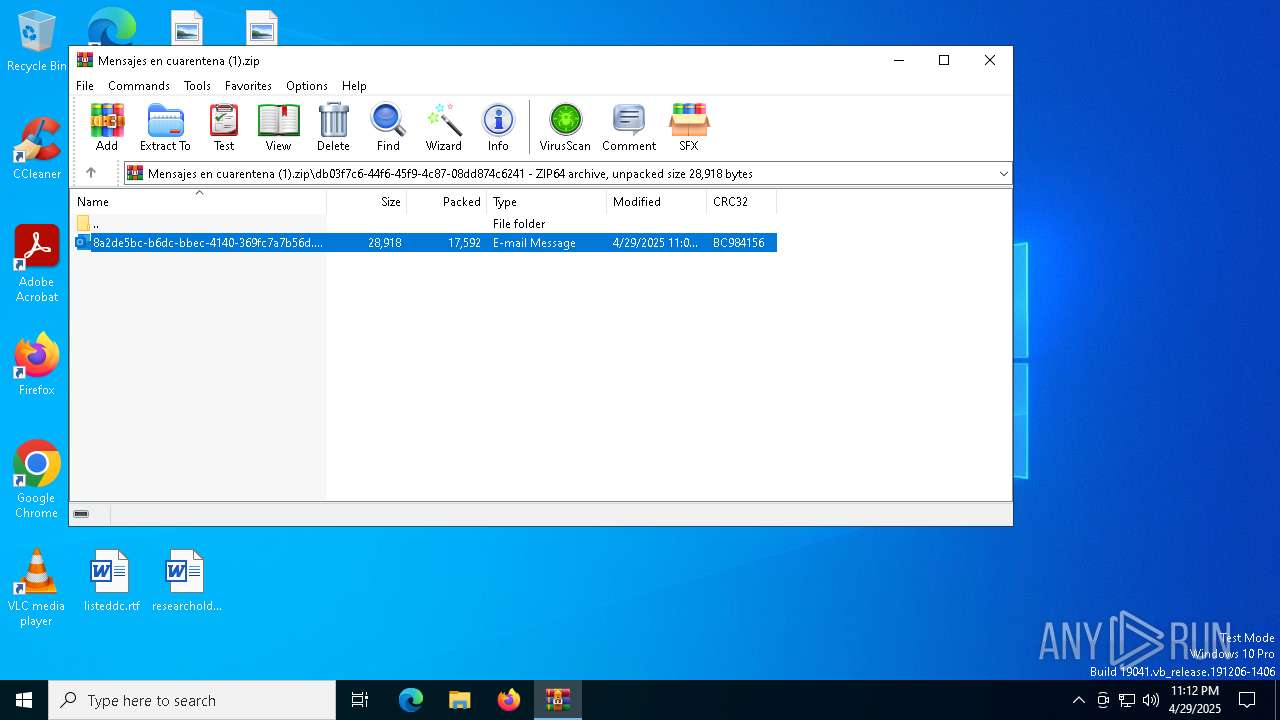
| ZipFileName: | db03f7c6-44f6-45f9-4c87-08dd874c6241/8a2de5bc-b6dc-bbec-4140-369fc7a7b56d.eml |
Total processes
191
Monitored processes
59
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6408 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2688 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5668 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5500 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Windows\System32\cmd.exe" /C copy *.bat "C:\Users\Public\Downloads\phason.bat" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "749D9CB4-B820-4254-B412-2D9FEA3ADF56" "2938F29D-AC0A-43B2-8972-97C5A7C30E30" "7468" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 1180 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5684 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7140 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5288 --field-trial-handle=2492,i,11942818836185571285,6380597999083495602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
35 788
Read events
35 365
Write events
373
Delete events
50
Modification events
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mensajes en cuarentena (1).zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
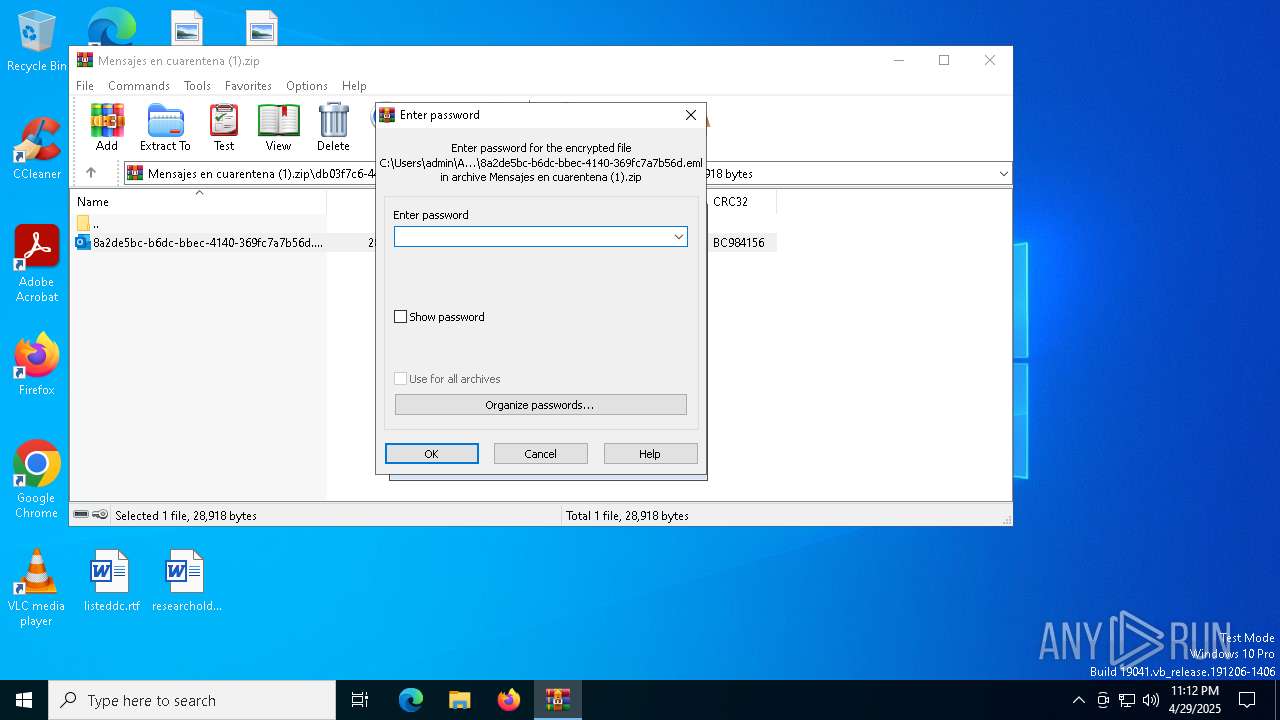
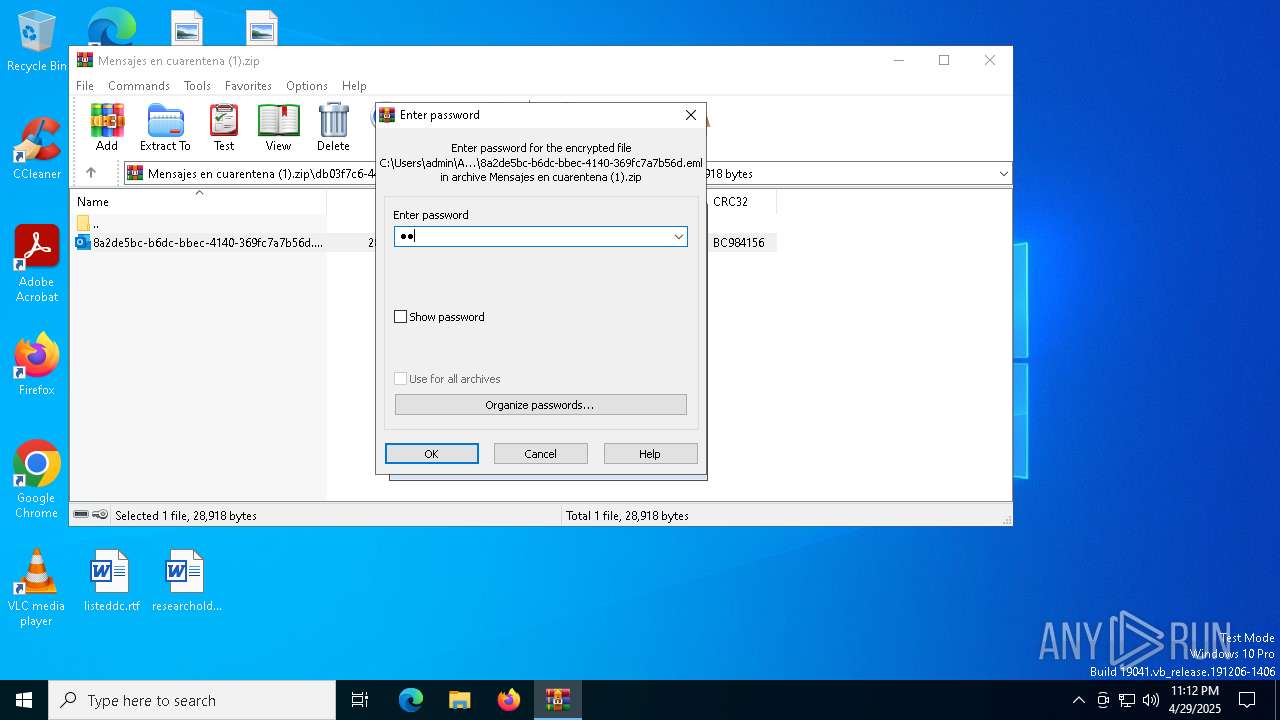
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
7
Suspicious files
205
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7468 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 2320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2320.14344\8a2de5bc-b6dc-bbec-4140-369fc7a7b56d.eml | binary | |
MD5:26498FC84F7A922EAE74B4300D26AC91 | SHA256:51A134835046E40C6FBBABD76BAD09D18BD8A1C00EFAC4C5C1A1D7BF8E0FD113 | |||
| 7468 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:5089F14AD56148030970842794105D38 | SHA256:8F4523C50419C1CDC9004B342B25DC9CC6244C4386BB8CC6466D5B447ABE979F | |||
| 7468 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\EF27650B.dat | image | |
MD5:A9C3FA7AE2D9BC4CBE31DD4211FDE1F2 | SHA256:A4524DCB07160B84C94D711AE435B4E224D234C459172121E507FC7BFEDE49F4 | |||
| 2320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_2320.15201 | compressed | |
MD5:7D2BD540C37A292F35CE5E24053F4949 | SHA256:01DA5369E595250EBE913420A962CA8AFBB81B8E16299590EEFF8C3FC68CAFCA | |||
| 7468 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:F419DF9C8CDEEFAD2296FCBDAF6CE89D | SHA256:44EEC50CA04E1581058B5C85A3101227BDDDC3DB0FF5EF954CDBBC3765C7E582 | |||
| 5112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1119bf.TMP | — | |
MD5:— | SHA256:— | |||
| 5112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF111a5b.TMP | — | |
MD5:— | SHA256:— | |||
| 5112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
56
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7640 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/VyosvvRj/0 | unknown | — | — | shared |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6652 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5072 | powershell.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/dwBy66KO/0 | unknown | — | — | shared |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3020 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/VyosvvRj/0 | unknown | — | — | shared |
7468 | OUTLOOK.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6652 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7468 | OUTLOOK.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7640 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
3020 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5072 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
1180 | InstallUtil.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
1180 | InstallUtil.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
1180 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
4896 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
1180 | InstallUtil.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |