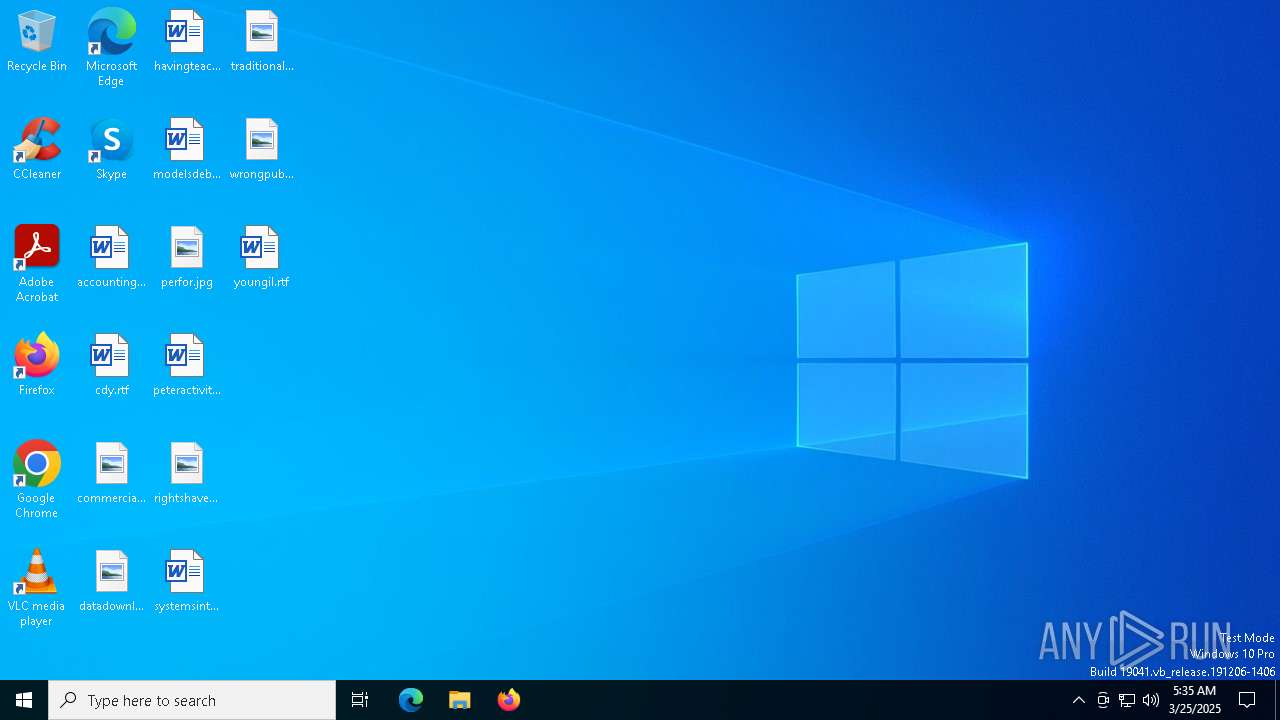
| File name: | 7af72d60902f6d9bd4ddb565cd4b0946.exe |
| Full analysis: | https://app.any.run/tasks/0e0997a1-c5e6-4bbb-a98e-167d427b3772 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | March 25, 2025, 05:35:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 7AF72D60902F6D9BD4DDB565CD4B0946 |
| SHA1: | 9A81B3D5D58E5F5AD4719DCF4FF3F5C59AEBBEBC |
| SHA256: | 5E597A1B3B27FC614676BC331E7134BDA14805AD4458D8649195AAB33A102AE5 |
| SSDEEP: | 98304:jw4Hk7p7NJUEWtf8LokyGjZi4VpcbL/vgJfiDmdBtqeJdrt7JpgtTF0FsM4QS5zs:U1E |
MALICIOUS
AMADEY has been detected (SURICATA)
- rapes.exe (PID: 5576)
Connects to the CnC server
- rapes.exe (PID: 5576)
AMADEY mutex has been found
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- Temp4PBIA6XYBAYJZMTAPHZ4H6PRQDGVUHPW.EXE (PID: 8024)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 7664)
- rapes.exe (PID: 3180)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7560)
- cmd.exe (PID: 7936)
- 01.exe (PID: 7576)
- download_807fb6fd5024da68.exe (PID: 7480)
Run PowerShell with an invisible window
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
AMADEY has been detected (YARA)
- rapes.exe (PID: 5576)
AMADEY has been found (auto)
- rapes.exe (PID: 5576)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
Changes the autorun value in the registry
- rapes.exe (PID: 5576)
- svchost.exe (PID: 7984)
GENERIC has been found (auto)
- 04c7ad2842.exe (PID: 7800)
- rapes.exe (PID: 5576)
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
Executing a file with an untrusted certificate
- iqvtNlb.exe (PID: 1912)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
LUMMA mutex has been found
- MSBuild.exe (PID: 8152)
- MSBuild.exe (PID: 7292)
- MSBuild.exe (PID: 7516)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 8152)
- MSBuild.exe (PID: 7292)
- MSBuild.exe (PID: 7516)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 8152)
- MSBuild.exe (PID: 7292)
- MSBuild.exe (PID: 7516)
Changes Windows Defender settings
- mmc.exe (PID: 7312)
Adds path to the Windows Defender exclusion list
- mmc.exe (PID: 7312)
SUSPICIOUS
Reads security settings of Internet Explorer
- rapes.exe (PID: 5576)
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
Connects to the server without a host name
- rapes.exe (PID: 5576)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
- Rr9IH1lm2.exe (PID: 8056)
- svchost.exe (PID: 7984)
- mmc.exe (PID: 7312)
Process requests binary or script from the Internet
- rapes.exe (PID: 5576)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
- busdrv.exe (PID: 1180)
Contacting a server suspected of hosting an CnC
- rapes.exe (PID: 5576)
Potential Corporate Privacy Violation
- rapes.exe (PID: 5576)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
- svchost015.exe (PID: 7808)
- svchost.exe (PID: 7984)
- busdrv.exe (PID: 1180)
- svchost015.exe (PID: 5116)
Executable content was dropped or overwritten
- rapes.exe (PID: 5576)
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
- 04c7ad2842.exe (PID: 7800)
- svchost015.exe (PID: 7808)
- svchost.exe (PID: 7984)
- mmc.exe (PID: 7312)
- 01.exe (PID: 7576)
- busdrv.exe (PID: 1180)
- download_807fb6fd5024da68.exe (PID: 7480)
- svchost015.exe (PID: 5116)
Reads the BIOS version
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- Temp4PBIA6XYBAYJZMTAPHZ4H6PRQDGVUHPW.EXE (PID: 8024)
- 04c7ad2842.exe (PID: 7800)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 7664)
- 549f352d3b.exe (PID: 7640)
- rapes.exe (PID: 3180)
Starts CMD.EXE for commands execution
- 4ae9cb1c69.exe (PID: 7540)
- rapes.exe (PID: 5576)
- cmd.exe (PID: 7936)
- svchost.exe (PID: 7984)
Probably download files using WebClient
- mshta.exe (PID: 7600)
- mshta.exe (PID: 7252)
Manipulates environment variables
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
Found IP address in command line
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7600)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7916)
- mshta.exe (PID: 7252)
- mmc.exe (PID: 7312)
Starts process via Powershell
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
There is functionality for enable RDP (YARA)
- rapes.exe (PID: 5576)
Executing commands from ".cmd" file
- rapes.exe (PID: 5576)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7936)
Starts itself from another location
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
Application launched itself
- cmd.exe (PID: 7936)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7916)
Searches for installed software
- MSBuild.exe (PID: 8152)
- MSBuild.exe (PID: 7292)
- MSBuild.exe (PID: 7516)
Process drops legitimate windows executable
- rapes.exe (PID: 5576)
Starts a Microsoft application from unusual location
- xu5e1_003.exe (PID: 7244)
The process executes via Task Scheduler
- rapes.exe (PID: 3180)
- PLUGScheduler.exe (PID: 1092)
Executing commands from a ".bat" file
- svchost.exe (PID: 7984)
Script adds exclusion path to Windows Defender
- mmc.exe (PID: 7312)
Drops a system driver (possible attempt to evade defenses)
- mmc.exe (PID: 7312)
Creates or modifies Windows services
- mmc.exe (PID: 7312)
Uses TASKKILL.EXE to kill process
- 01.exe (PID: 7576)
Checks for external IP
- svchost.exe (PID: 2196)
- busdrv.exe (PID: 1180)
- pcidrv.exe (PID: 4200)
Get information on the list of running processes
- download_807fb6fd5024da68.exe (PID: 7480)
Connects to unusual port
- pcidrv.exe (PID: 4200)
INFO
Checks supported languages
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- rapes.exe (PID: 5576)
- 4ae9cb1c69.exe (PID: 7540)
- Temp4PBIA6XYBAYJZMTAPHZ4H6PRQDGVUHPW.EXE (PID: 8024)
- 04c7ad2842.exe (PID: 7800)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 7664)
- svchost015.exe (PID: 7808)
- tK0oYx3.exe (PID: 8064)
- MSBuild.exe (PID: 8152)
- Rr9IH1lm2.exe (PID: 8056)
- svchost015.exe (PID: 5116)
- xu5e1_003.exe (PID: 7244)
- RTH4oNP.exe (PID: 4040)
- MSBuild.exe (PID: 7292)
- tzutil.exe (PID: 6032)
- w32tm.exe (PID: 7492)
- rapes.exe (PID: 3180)
- 549f352d3b.exe (PID: 7640)
- 01.exe (PID: 7576)
- busdrv.exe (PID: 1180)
- OkH8IPF.exe (PID: 7280)
- MSBuild.exe (PID: 7516)
- download_807fb6fd5024da68.exe (PID: 7480)
- pcidrv.exe (PID: 4200)
- PLUGScheduler.exe (PID: 1092)
Create files in a temporary directory
- rapes.exe (PID: 5576)
- 4ae9cb1c69.exe (PID: 7540)
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- 04c7ad2842.exe (PID: 7800)
- svchost.exe (PID: 7984)
- w32tm.exe (PID: 7492)
- svchost015.exe (PID: 7808)
- busdrv.exe (PID: 1180)
Reads the computer name
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
- 4ae9cb1c69.exe (PID: 7540)
- 549f352d3b.exe (PID: 7640)
- svchost015.exe (PID: 7808)
- MSBuild.exe (PID: 8152)
- svchost015.exe (PID: 5116)
- Rr9IH1lm2.exe (PID: 8056)
- xu5e1_003.exe (PID: 7244)
- MSBuild.exe (PID: 7292)
- tzutil.exe (PID: 6032)
- 04c7ad2842.exe (PID: 7800)
- w32tm.exe (PID: 7492)
- busdrv.exe (PID: 1180)
- MSBuild.exe (PID: 7516)
- pcidrv.exe (PID: 4200)
Reads mouse settings
- 4ae9cb1c69.exe (PID: 7540)
Autorun file from Task Scheduler
- cmd.exe (PID: 7560)
- cmd.exe (PID: 7936)
- 01.exe (PID: 7576)
- download_807fb6fd5024da68.exe (PID: 7480)
Reads Internet Explorer settings
- mshta.exe (PID: 7600)
- mshta.exe (PID: 7816)
- mshta.exe (PID: 7252)
Process checks computer location settings
- rapes.exe (PID: 5576)
- 7af72d60902f6d9bd4ddb565cd4b0946.exe (PID: 4300)
Manual execution by a user
- mshta.exe (PID: 7816)
- OpenWith.exe (PID: 4996)
- busdrv.exe (PID: 1180)
- pcidrv.exe (PID: 4200)
Themida protector has been detected
- rapes.exe (PID: 5576)
Disables trace logs
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7312)
Checks proxy server information
- powershell.exe (PID: 7728)
- rapes.exe (PID: 5576)
- BackgroundTransferHost.exe (PID: 6108)
- powershell.exe (PID: 7312)
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
- busdrv.exe (PID: 1180)
- pcidrv.exe (PID: 4200)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8068)
- BackgroundTransferHost.exe (PID: 6108)
- BackgroundTransferHost.exe (PID: 7652)
- BackgroundTransferHost.exe (PID: 3008)
- BackgroundTransferHost.exe (PID: 8148)
- svchost.exe (PID: 7984)
The executable file from the user directory is run by the Powershell process
- Temp4PBIA6XYBAYJZMTAPHZ4H6PRQDGVUHPW.EXE (PID: 8024)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 7664)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 6108)
- MSBuild.exe (PID: 8152)
- MSBuild.exe (PID: 7292)
- MSBuild.exe (PID: 7516)
- slui.exe (PID: 5728)
Creates files or folders in the user directory
- rapes.exe (PID: 5576)
- BackgroundTransferHost.exe (PID: 6108)
- svchost015.exe (PID: 5116)
- svchost015.exe (PID: 7808)
The sample compiled with english language support
- 04c7ad2842.exe (PID: 7800)
- rapes.exe (PID: 5576)
- svchost.exe (PID: 7984)
Reads the machine GUID from the registry
- svchost015.exe (PID: 7808)
- svchost015.exe (PID: 5116)
- w32tm.exe (PID: 7492)
Creates files in the program directory
- xu5e1_003.exe (PID: 7244)
- svchost.exe (PID: 7984)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7624)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:23 11:06:11+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 324096 |
| InitializedDataSize: | 115200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4bc000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
327
Monitored processes
80
Malicious processes
24
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\Drivers\busdrv.exe" | C:\Users\admin\Drivers\busdrv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "tasklist" | C:\Windows\System32\tasklist.exe | — | download_807fb6fd5024da68.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Local\Temp\10328510101\iqvtNlb.exe" | C:\Users\admin\AppData\Local\Temp\10328510101\iqvtNlb.exe | — | rapes.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\system32\cmd.exe /c powershell -command "-join ((48..57) + (65..90) + (97..122) | Get-Random -Count 9 | ForEach-Object {[char]$_})" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe" | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
38 778
Read events
38 717
Write events
61
Delete events
0
Modification events
| (PID) Process: | (5576) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5576) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5576) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7600) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7600) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7600) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5576) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 4ae9cb1c69.exe |
Value: C:\Users\admin\AppData\Local\Temp\10328010101\4ae9cb1c69.exe | |||
| (PID) Process: | (7728) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7728) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7728) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
38
Suspicious files
61
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6108 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9f3f76b5-3034-4492-9d86-5546ddd575f5.down_data | — | |
MD5:— | SHA256:— | |||
| 4300 | 7af72d60902f6d9bd4ddb565cd4b0946.exe | C:\Windows\Tasks\rapes.job | binary | |
MD5:1A7A521524263008A5410E7B7B2C0000 | SHA256:762409B144EDD1E602E46C4915580701089EF2E8CC6C6C44F139447597BB2D7E | |||
| 5576 | rapes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:12B5862A18C8D6C5AD42EAC8B8B25983 | SHA256:F7A170F384FB2C2D8296C8D6047C31B832D4502F3AED7E0718CFA34A9459DB27 | |||
| 7540 | 4ae9cb1c69.exe | C:\Users\admin\AppData\Local\Temp\smiBM3P37.hta | html | |
MD5:49FAB77A51F8710D2FD4CB44A27DBAC1 | SHA256:8CBA0AE46080D68C046422C9A68EE2939814049BF8F2EDAF9E14235F1BD925B7 | |||
| 4300 | 7af72d60902f6d9bd4ddb565cd4b0946.exe | C:\Users\admin\AppData\Local\Temp\bb556cff4a\rapes.exe | executable | |
MD5:7AF72D60902F6D9BD4DDB565CD4B0946 | SHA256:5E597A1B3B27FC614676BC331E7134BDA14805AD4458D8649195AAB33A102AE5 | |||
| 5576 | rapes.exe | C:\Users\admin\AppData\Local\Temp\10328010101\4ae9cb1c69.exe | executable | |
MD5:12B5862A18C8D6C5AD42EAC8B8B25983 | SHA256:F7A170F384FB2C2D8296C8D6047C31B832D4502F3AED7E0718CFA34A9459DB27 | |||
| 7728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uwptljqb.jka.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a5bo1bql.o54.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4448 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ytu5hh33.twl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5576 | rapes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\am_no[1].bat | text | |
MD5:CEDAC8D9AC1FBD8D4CFC76EBE20D37F9 | SHA256:5E951726842C371240A6AF79D8DA7170180F256DF94EAC5966C07F04EF4D120B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
148
TCP/UDP connections
104
DNS requests
32
Threats
97
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4736 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5576 | rapes.exe | POST | 200 | 176.113.115.6:80 | http://176.113.115.6/Ni9kiput/index.php | unknown | — | — | malicious |
5576 | rapes.exe | GET | 200 | 176.113.115.7:80 | http://176.113.115.7/test/am_no.bat | unknown | — | — | malicious |
7728 | powershell.exe | GET | 200 | 176.113.115.7:80 | http://176.113.115.7/mine/random.exe | unknown | — | — | malicious |
5576 | rapes.exe | POST | 200 | 176.113.115.6:80 | http://176.113.115.6/Ni9kiput/index.php | unknown | — | — | malicious |
6108 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5576 | rapes.exe | GET | 200 | 176.113.115.7:80 | http://176.113.115.7/files/unique2/random.exe | unknown | — | — | malicious |
5576 | rapes.exe | POST | 200 | 176.113.115.6:80 | http://176.113.115.6/Ni9kiput/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5576 | rapes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
5576 | rapes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
5576 | rapes.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
5576 | rapes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5576 | rapes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
5576 | rapes.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5576 | rapes.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5576 | rapes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7728 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7728 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |