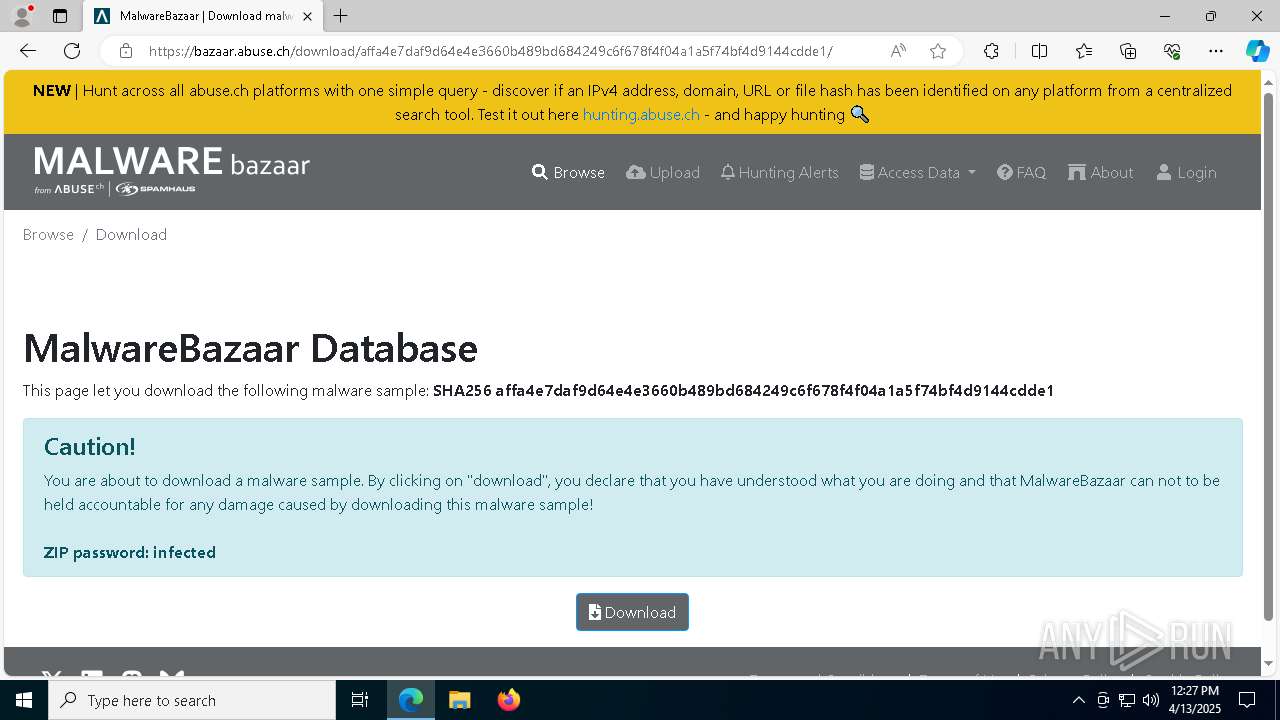
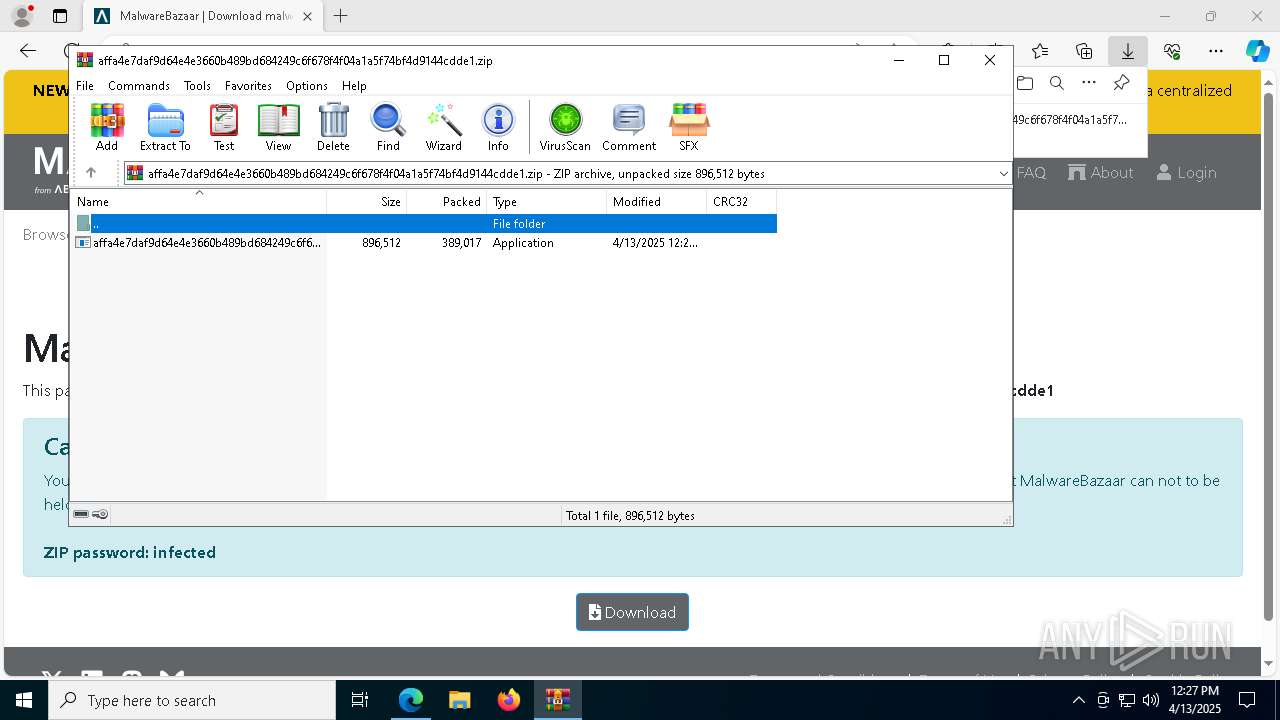
| URL: | https://bazaar.abuse.ch/download/affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1/ |
| Full analysis: | https://app.any.run/tasks/7380470f-576e-4631-ad0a-9bb299af8a5f |
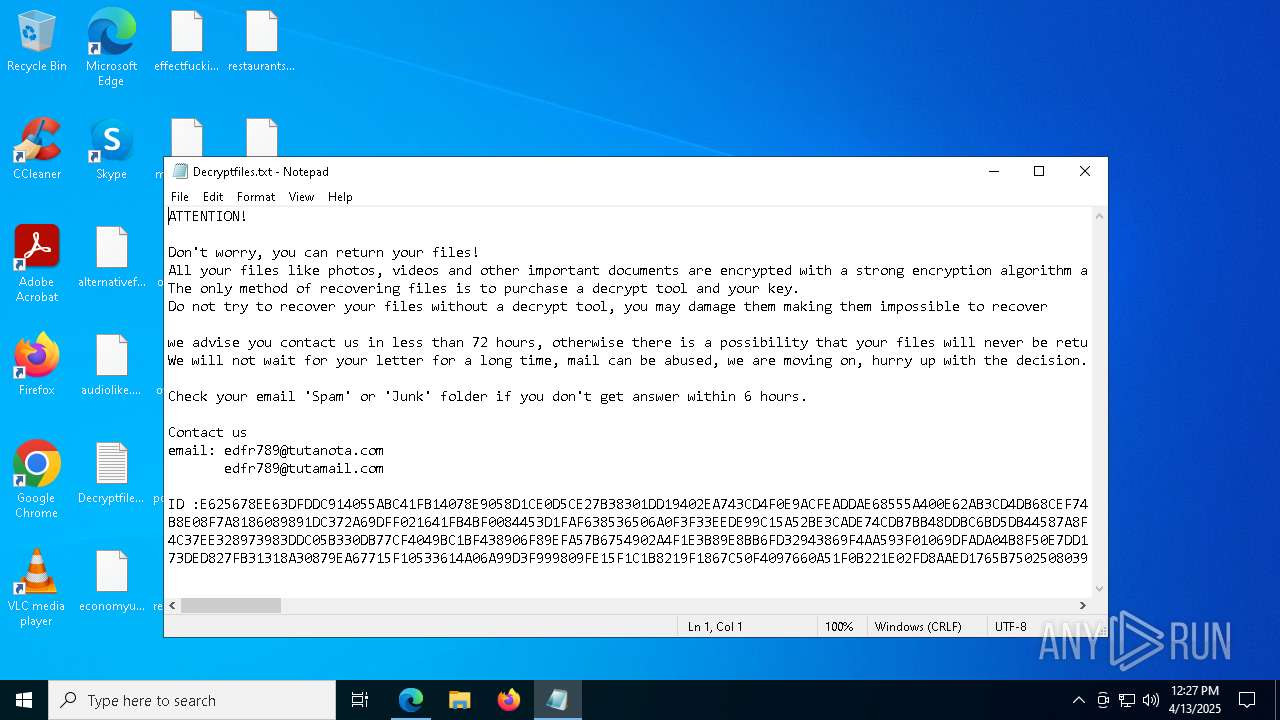
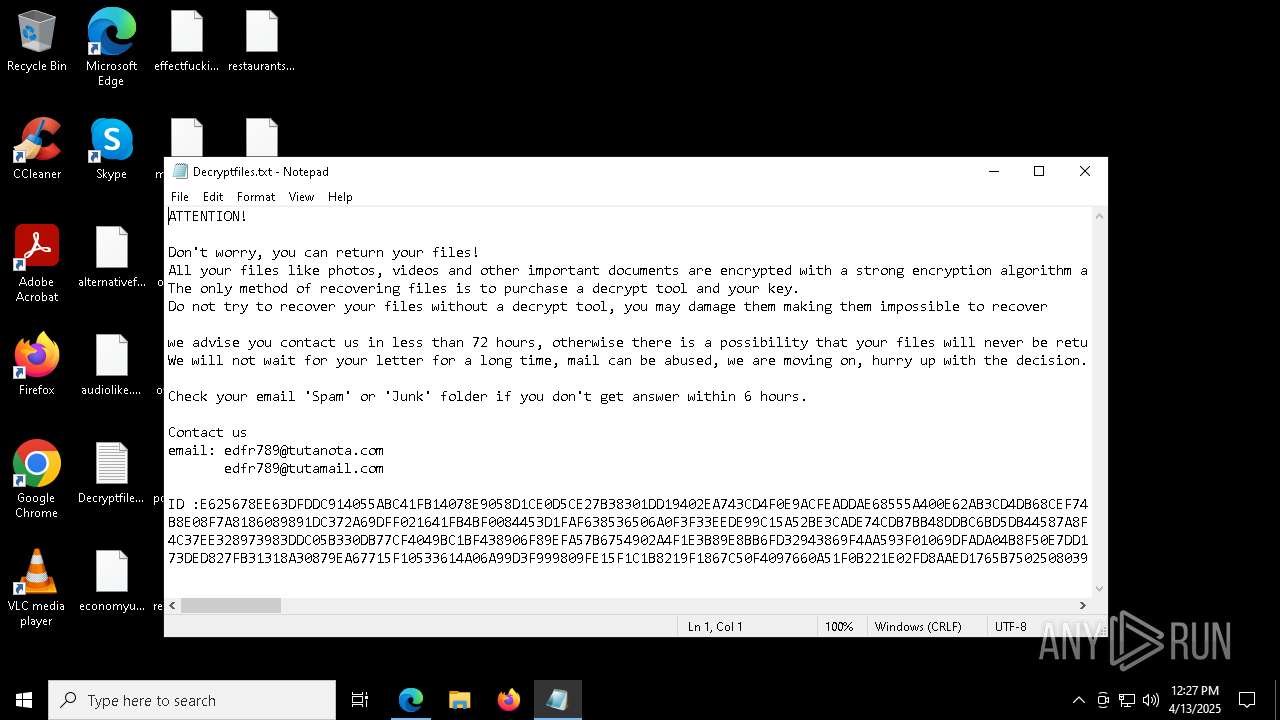
| Verdict: | Malicious activity |
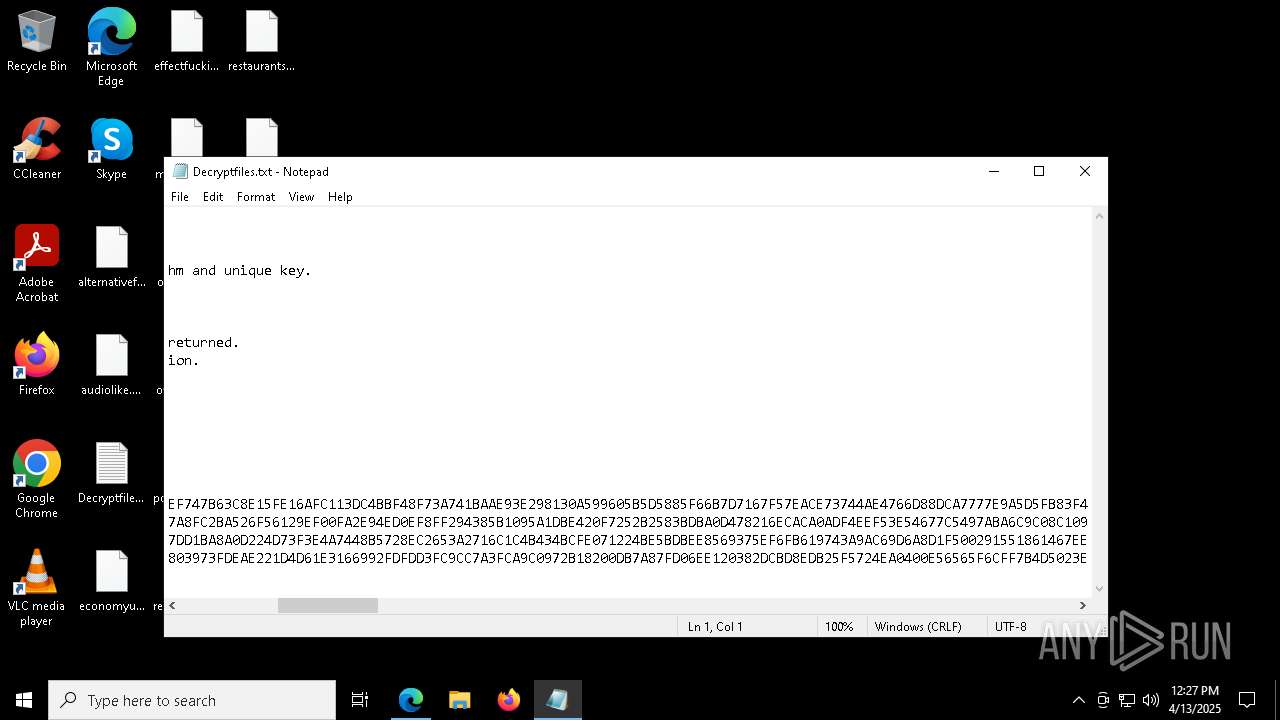
| Threats: | Cactus ransomware-as-a-service (RaaS) was first caught in March 2023 targeting corporate networks. It became known for its self-encrypting payload and double extortion tactics. Cactus primarily targets large enterprises across industries in finance, manufacturing, IT, and healthcare. It is known for using custom encryption techniques, remote access tools, and penetration testing frameworks to maximize damage. |
| Analysis date: | April 13, 2025, 12:26:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7009E1876469763AB46498E6713D576E |
| SHA1: | 1D9BF6DECA6FB075B23F2BE9CE7A0CE4B2286417 |
| SHA256: | 5DF64D663070989B48D8F7460DCCC9E91C77B5B1F380D1F9D267C49EC40165E7 |
| SSDEEP: | 3:N8N0uDWB4qD473WLeHHxhmzRn+tBlRWK:23GWWLeHTKp+zLN |
MALICIOUS
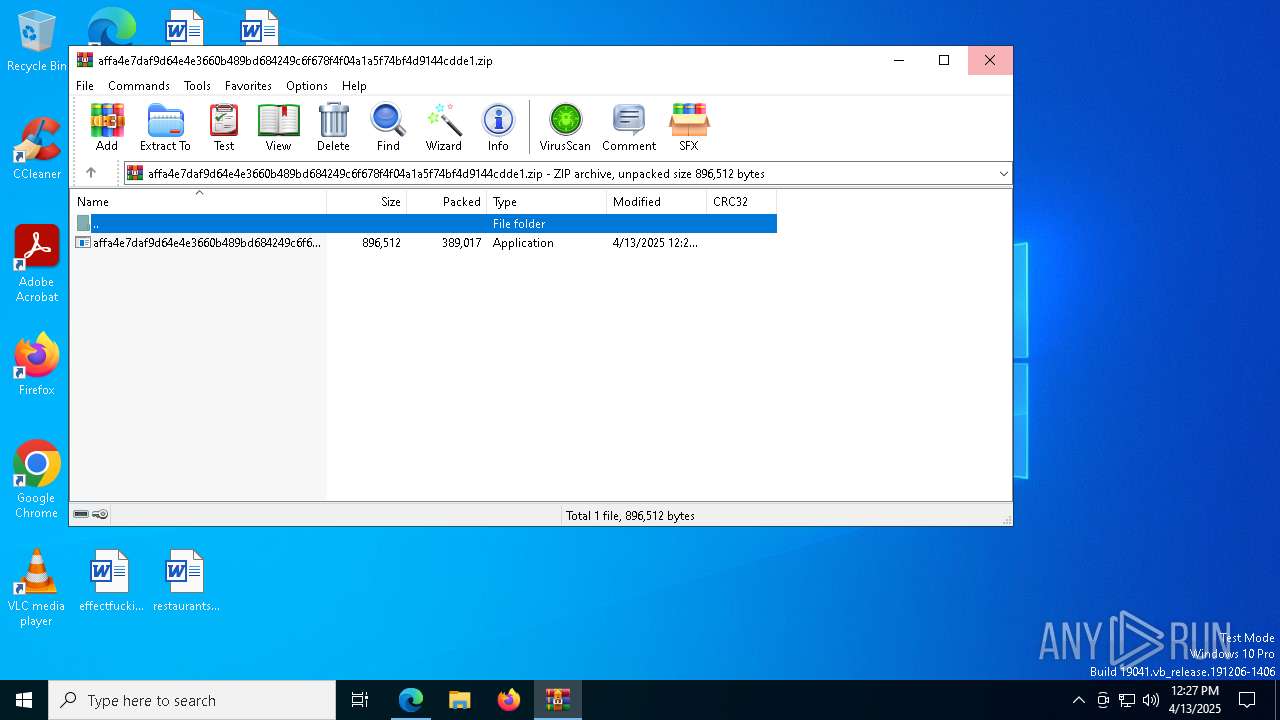
GENERIC has been found (auto)
- WinRAR.exe (PID: 4740)
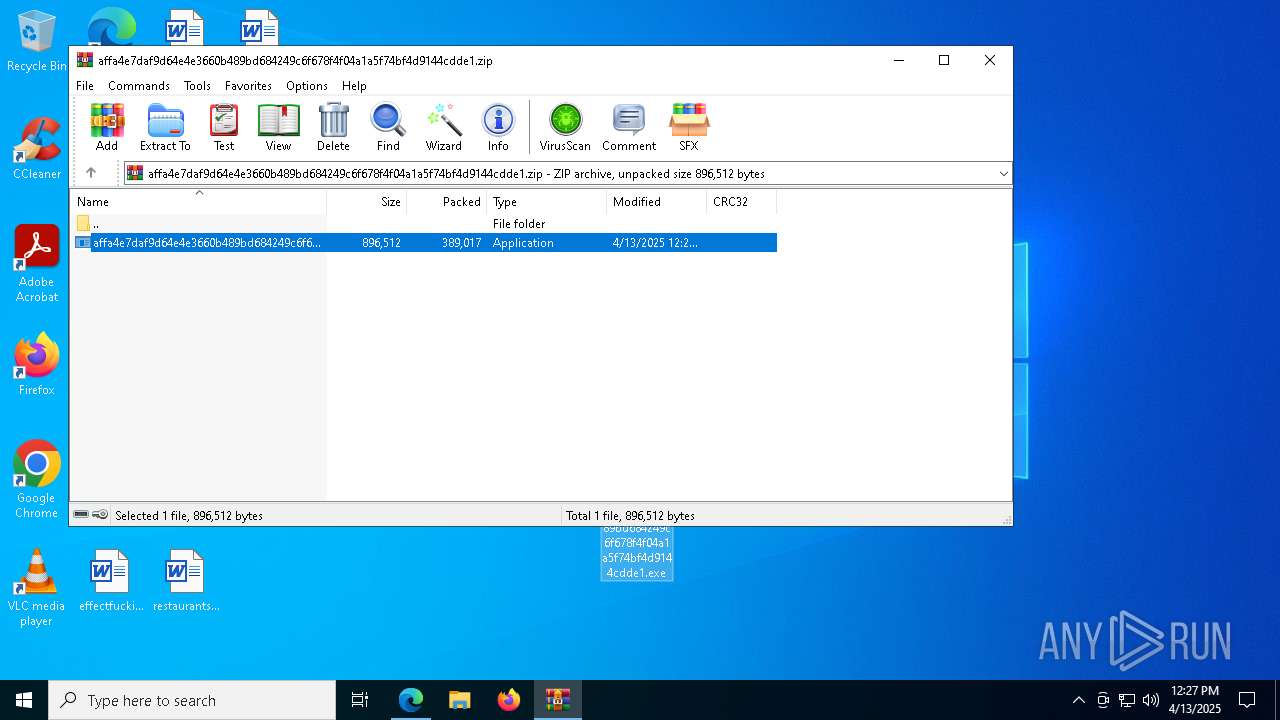
CACTUS has been detected
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
CACTUS mutex has been found
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Changes the autorun value in the registry
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
RANSOMWARE has been detected
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Deletes shadow copies
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
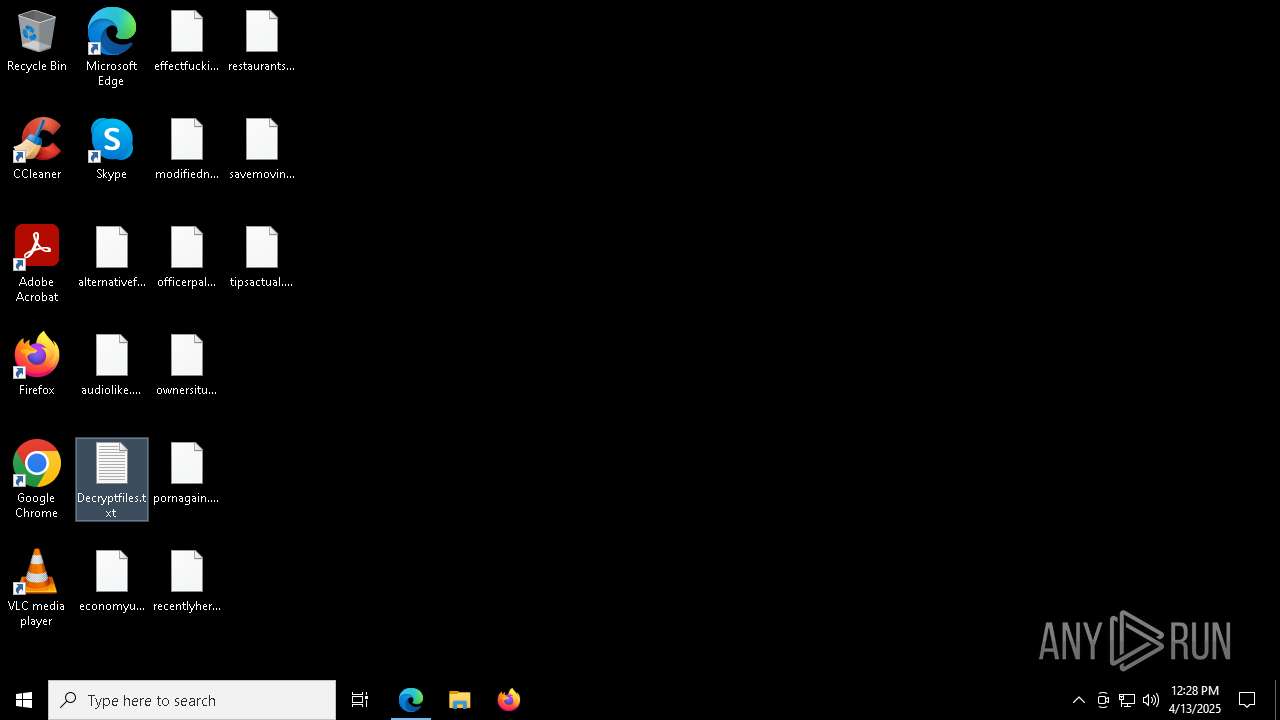
Renames files like ransomware
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
CACTUS has been detected (YARA)
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Create files in the Startup directory
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
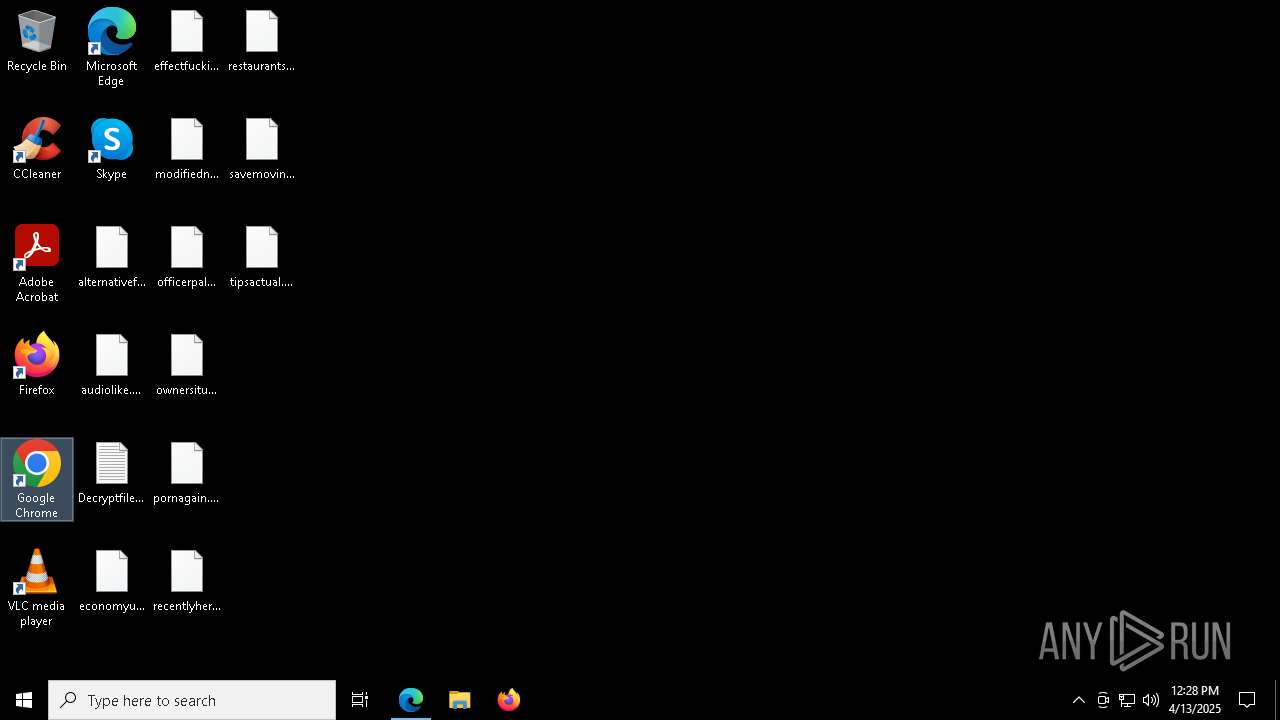
Actions looks like stealing of personal data
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Steals credentials from Web Browsers
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Starts CMD.EXE for self-deleting
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Writes a file to the Word startup folder
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
SUSPICIOUS
Creates file in the systems drive root
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Write to the desktop.ini file (may be used to cloak folders)
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Hides command output
- cmd.exe (PID: 7600)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7600)
Starts CMD.EXE for commands execution
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
INFO
Application launched itself
- msedge.exe (PID: 6668)
- chrome.exe (PID: 4008)
Autorun file from Downloads
- msedge.exe (PID: 6668)
- msedge.exe (PID: 1272)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6668)
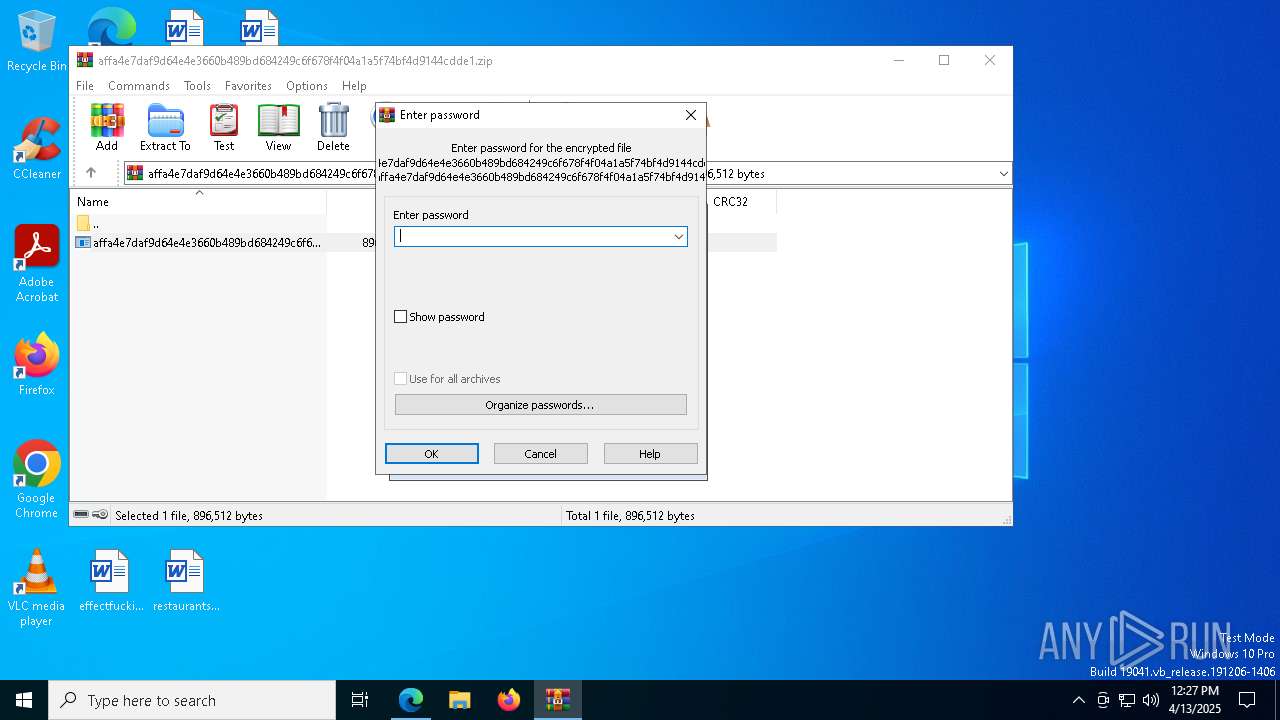
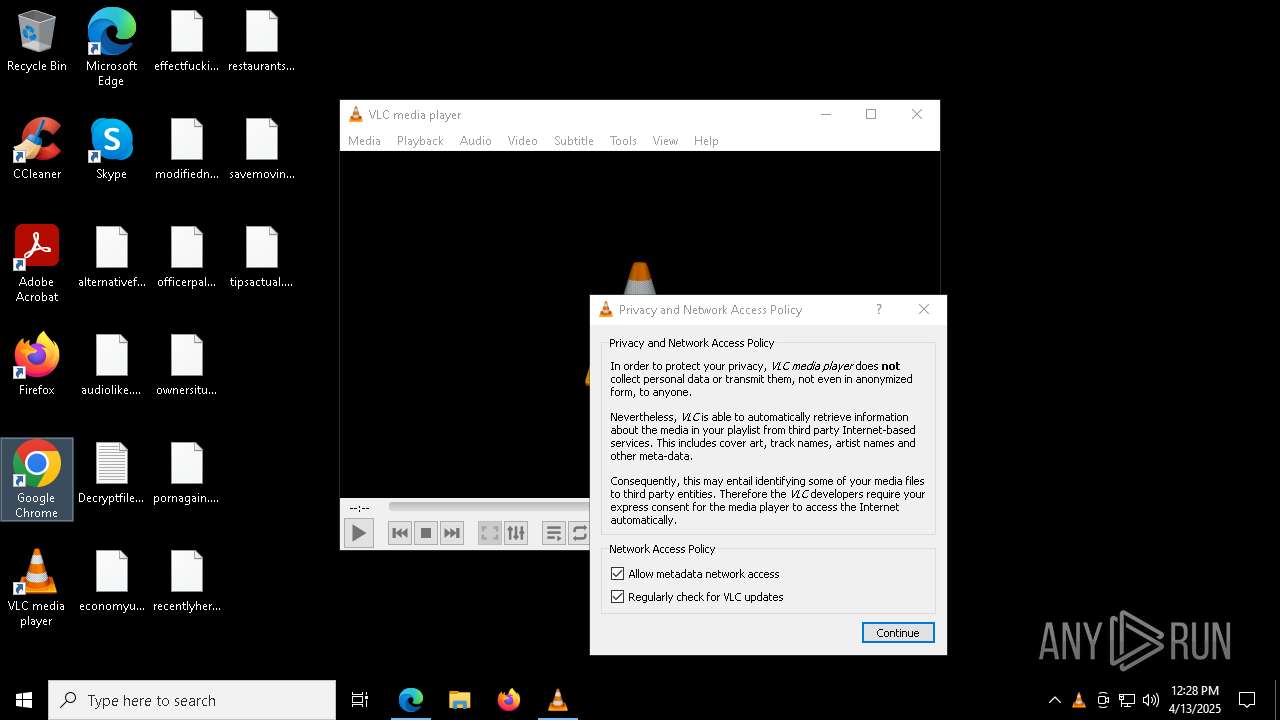
Manual execution by a user
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
- notepad.exe (PID: 2564)
- vlc.exe (PID: 8368)
- chrome.exe (PID: 4008)
Checks supported languages
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
- vlc.exe (PID: 8368)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4740)
- msedge.exe (PID: 4220)
Reads the computer name
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
- vlc.exe (PID: 8368)
Create files in a temporary directory
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8768)
- WMIC.exe (PID: 7696)
- notepad.exe (PID: 2564)
Creates files or folders in the user directory
- affa4e7daf9d64e4e3660b489bd684249c6f678f4f04a1a5f74bf4d9144cdde1.exe (PID: 8440)
Reads the software policy settings
- slui.exe (PID: 8172)
- slui.exe (PID: 4528)
Checks proxy server information
- slui.exe (PID: 4528)
The sample compiled with english language support
- msedge.exe (PID: 4220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
215
Monitored processes
77
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2916 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=3664 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6820 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1872 --field-trial-handle=1928,i,13713408157516783746,7982543729381696,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4556 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5388 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7376 --field-trial-handle=2320,i,2282563391861779381,15033068918208364667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | ping 1.1.1.1 -n 1 -w 3000 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
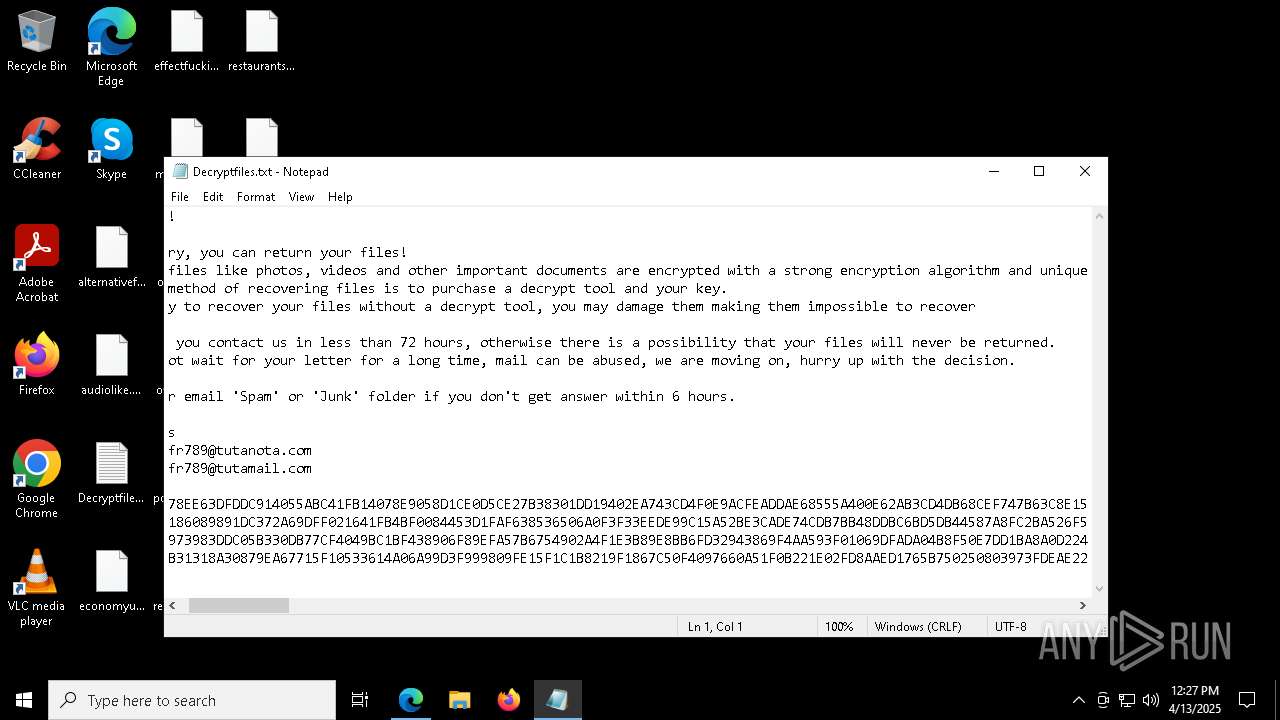
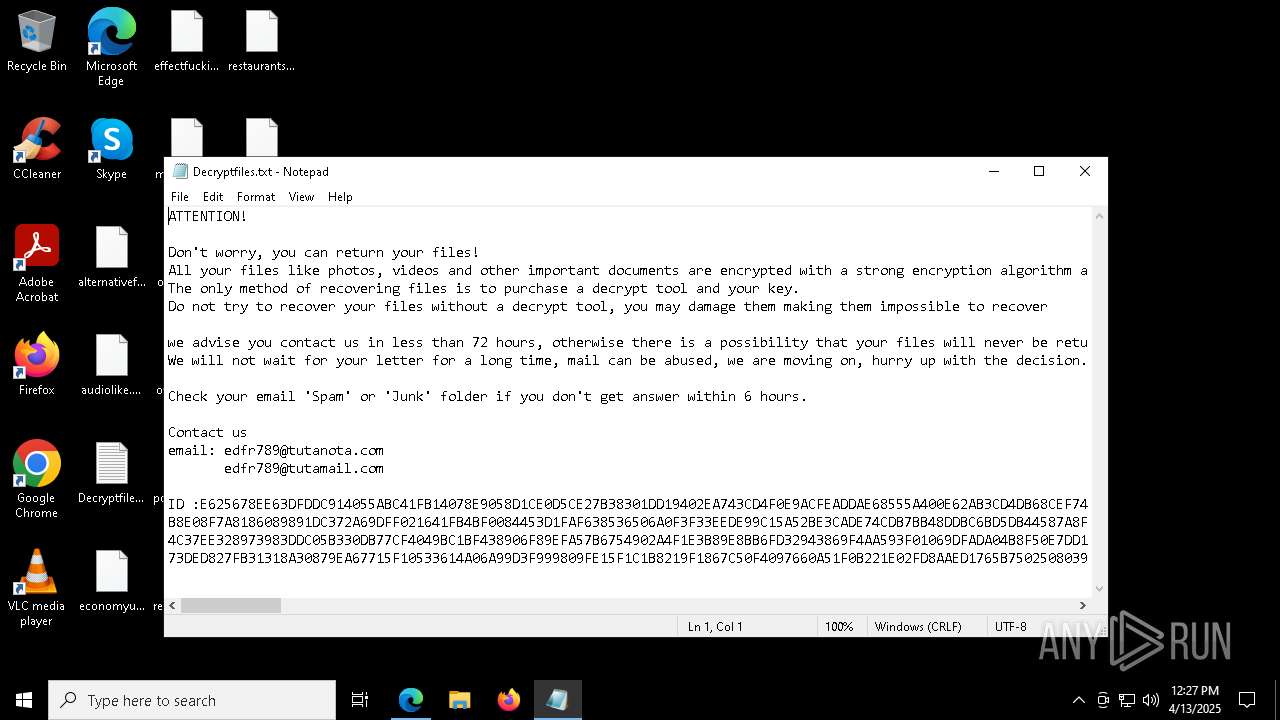
| 2564 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Decryptfiles.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3560 --field-trial-handle=1928,i,13713408157516783746,7982543729381696,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
11 151
Read events
11 101
Write events
49
Delete events
1
Modification events
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CABF8B543E912F00 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6C2C9B543E912F00 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0398C6B6-BE27-4B0E-B617-2D9B1310D36D} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2B591F82-9D64-4D04-8C2E-C86212951C5C} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B5ED76A6-988C-4665-920C-4B20B1AE338F} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {099AE242-6EA5-42F0-8BB2-1FB69E7901ED} | |||
Executable files
22
Suspicious files
1 238
Text files
425
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c98b.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c98b.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c98b.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c9ca.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c9e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
68
DNS requests
88
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
9168 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8984 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
9168 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8984 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
8984 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
8984 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
8984 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
8984 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954463&P2=404&P3=2&P4=mDxXyThypth87v9%2bJKzo8LZDR1yMOmlrMQqVH7DJK9gxMIn1oSvWKJzbm85NhW0dTPaH5O4YKLb5JFqOTNBgmg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6668 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7360 | msedge.exe | 151.101.194.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
7360 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
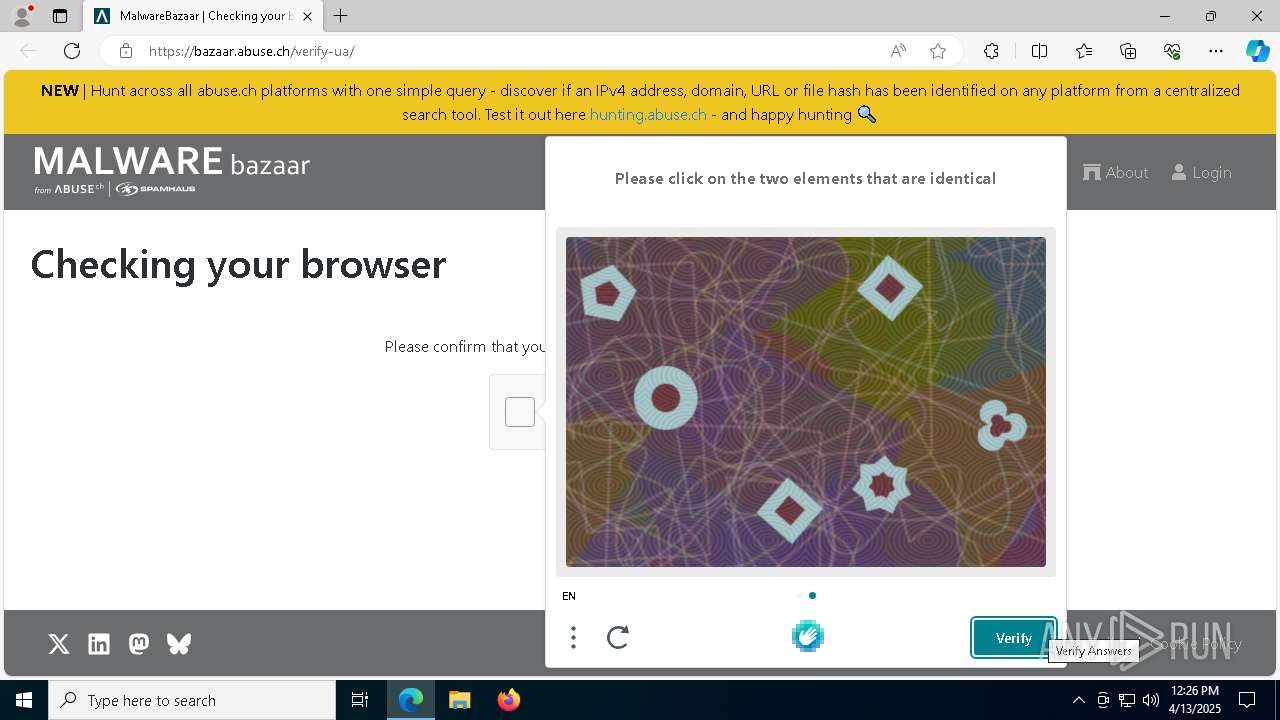
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |