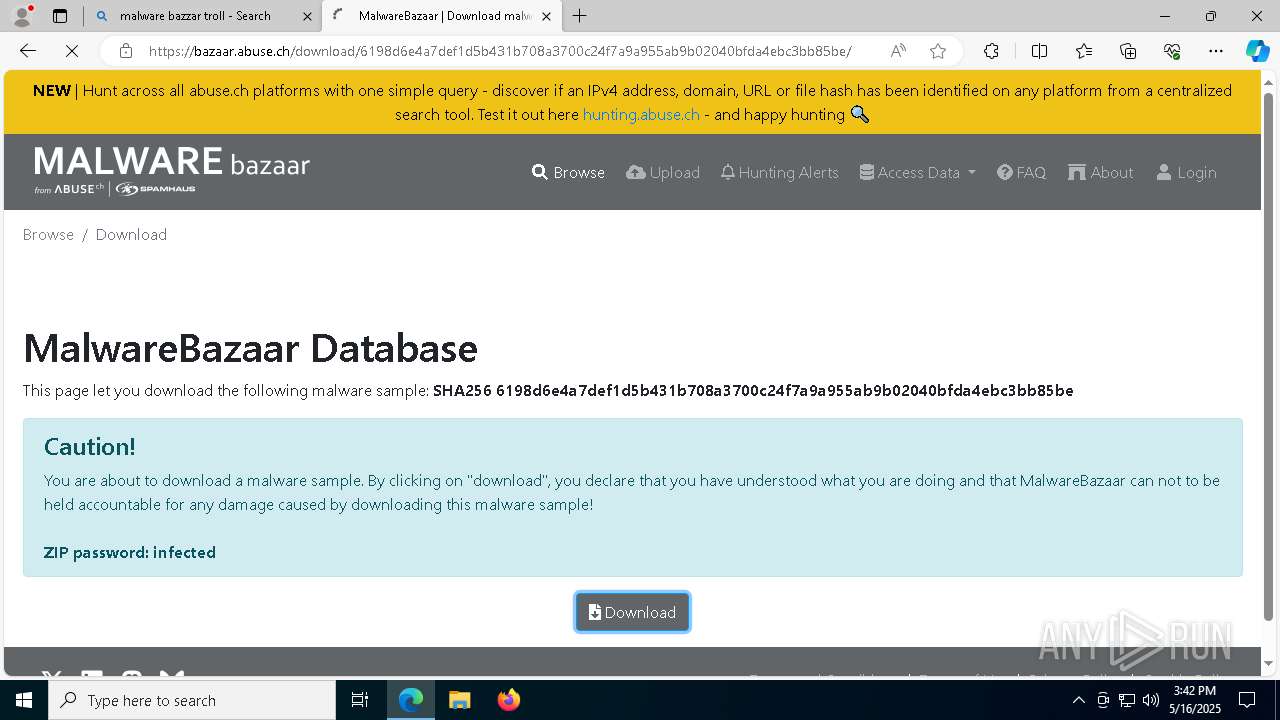
| File name: | 869705fd4dd777d4ab5c662806b42fe43bff6b58e085a64804486326b35fee47 |
| Full analysis: | https://app.any.run/tasks/1a06d07c-8e1c-4b4c-a439-47dbad50e601 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 16, 2025, 15:39:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (601) |
| MD5: | B98DE7E2400D9D1D03A293E17BE17AAC |
| SHA1: | D40C62937FB9EF26BFC7807BB868C788A9B6CCF0 |
| SHA256: | 5DC3CFAF500196FD23F4005840D167CA30C4A66DBAC6529C9817643B365415E8 |
| SSDEEP: | 96:GCOts9SfcKuKAxpPsCkHIB28E3CfOr7NVirCQXq+VoITMFZTwcfC4wxKA7ARKeRH:xOtshhsGB28E3nTirpoqc6487A0CGKsW |
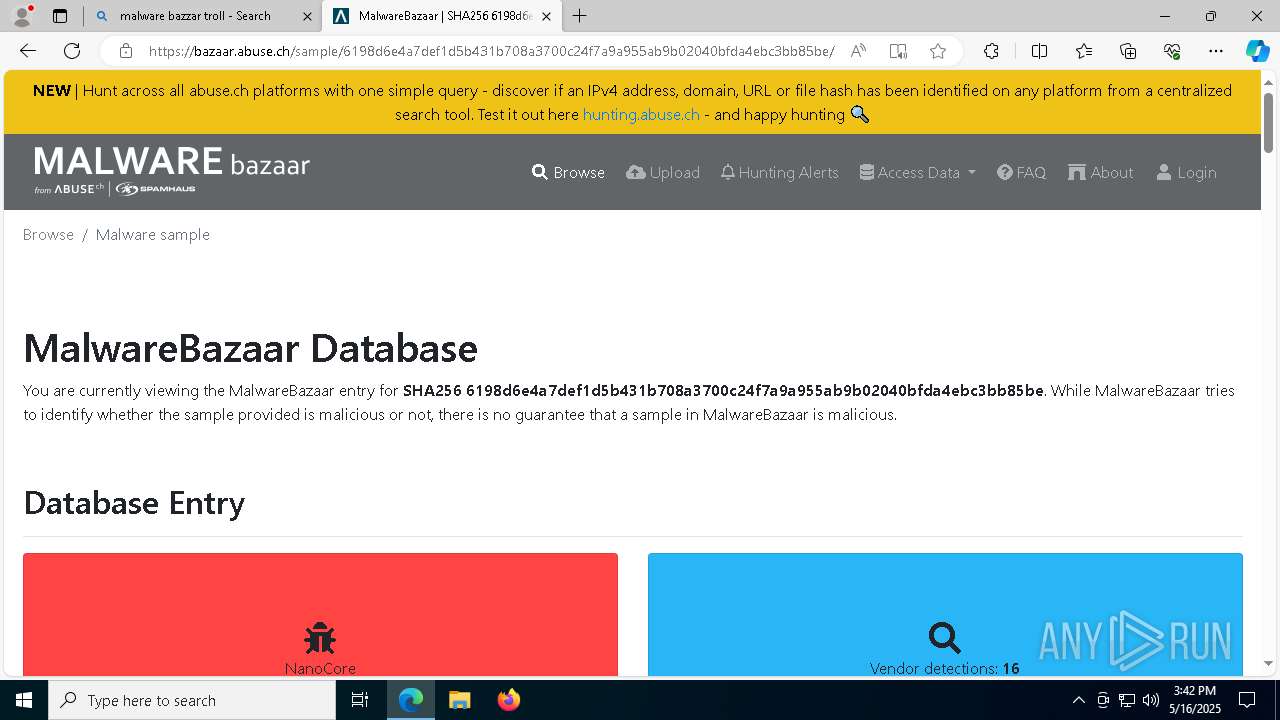
MALICIOUS
Changes the autorun value in the registry
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
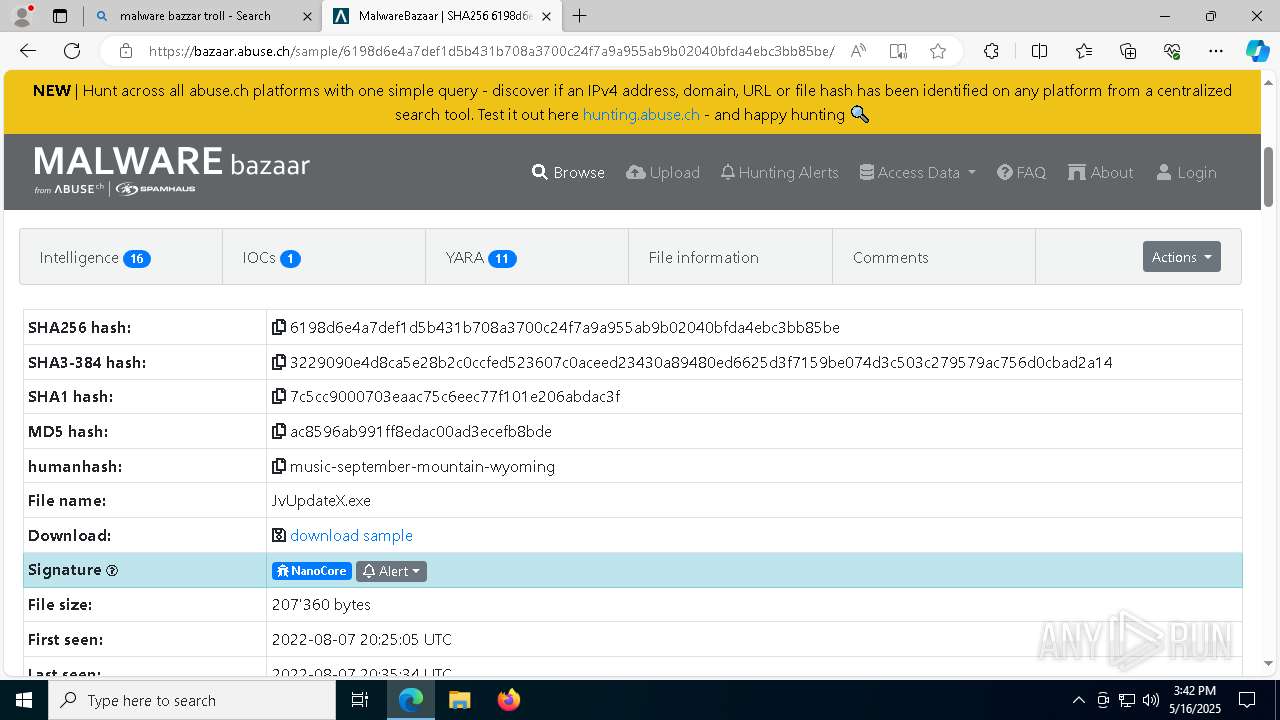
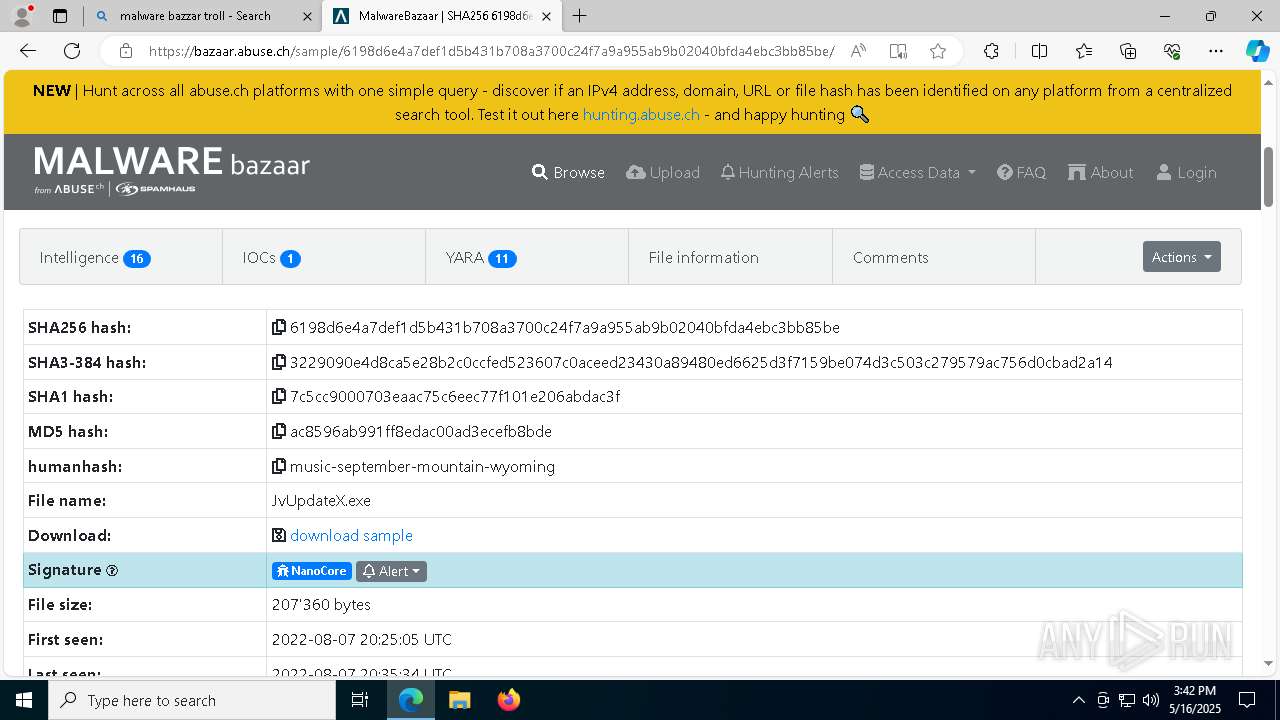
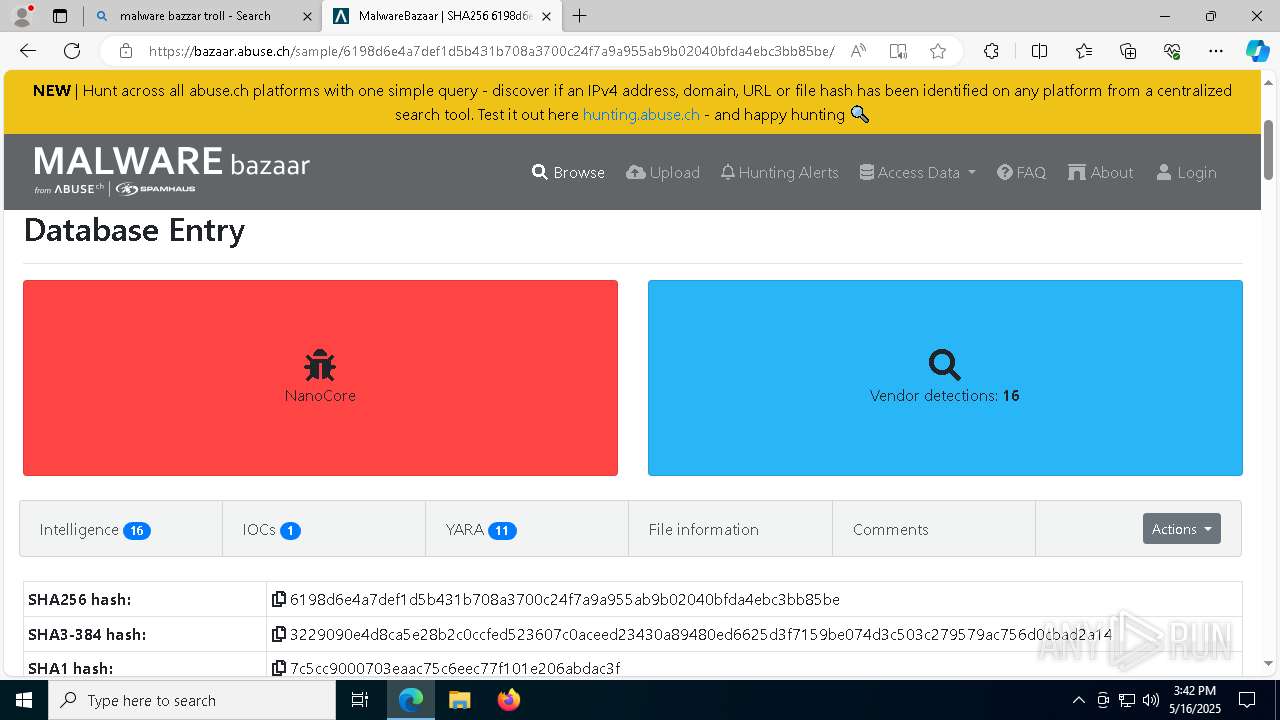
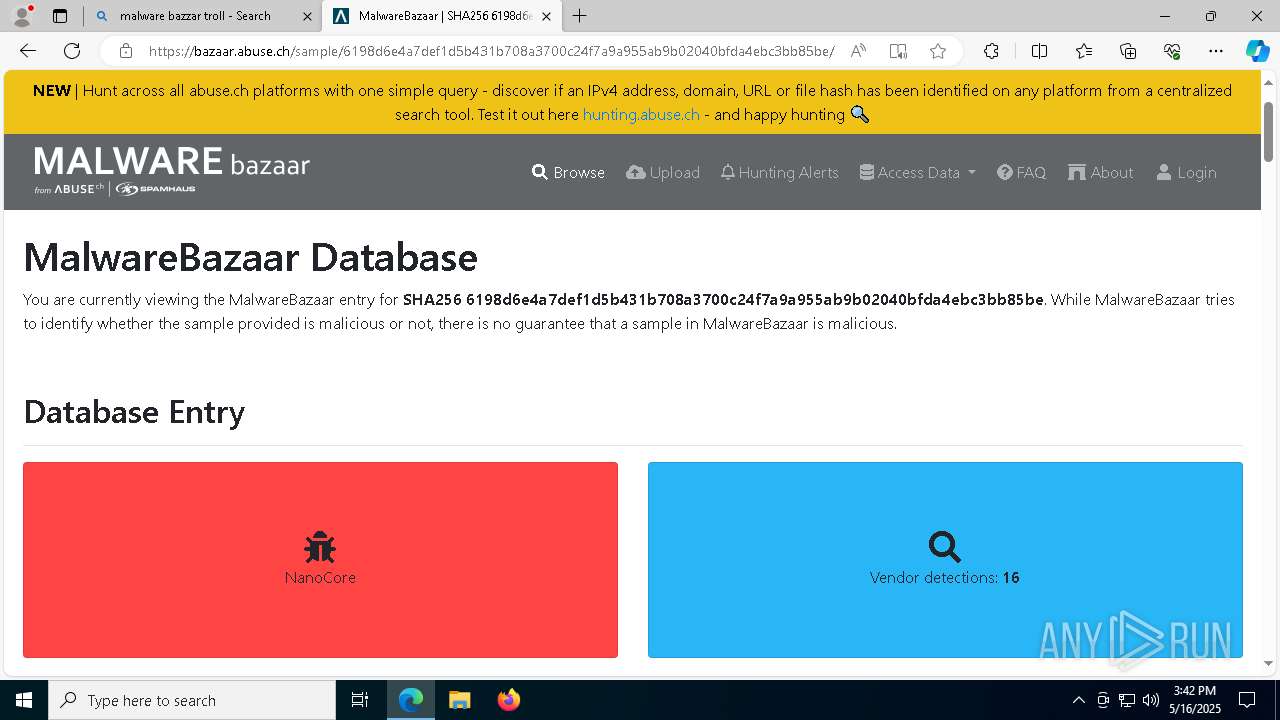
NANOCORE has been detected (YARA)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6112)
Run PowerShell with an invisible window
- powershell.exe (PID: 3884)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 3884)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 5736)
Connects to the CnC server
- ramez.exe (PID: 5736)
- svchost.exe (PID: 2196)
- cmd.exe (PID: 2644)
Known privilege escalation attack
- dllhost.exe (PID: 540)
- dllhost.exe (PID: 9060)
Changes Windows Defender settings
- WinTemp-v4.exe (PID: 1852)
Adds process to the Windows Defender exclusion list
- WinTemp-v4.exe (PID: 1852)
AMADEY has been detected (YARA)
- ramez.exe (PID: 5736)
Uses Task Scheduler to autorun other applications
- WinTemp-v4.exe (PID: 1852)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7796)
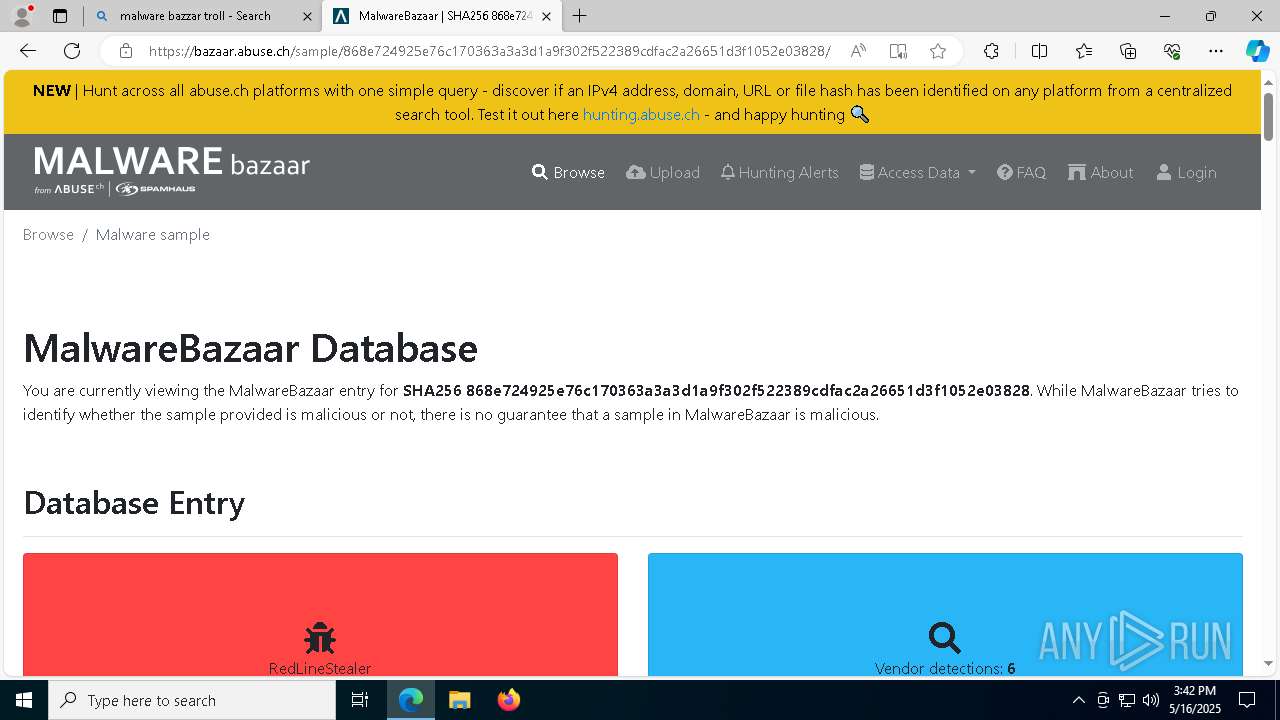
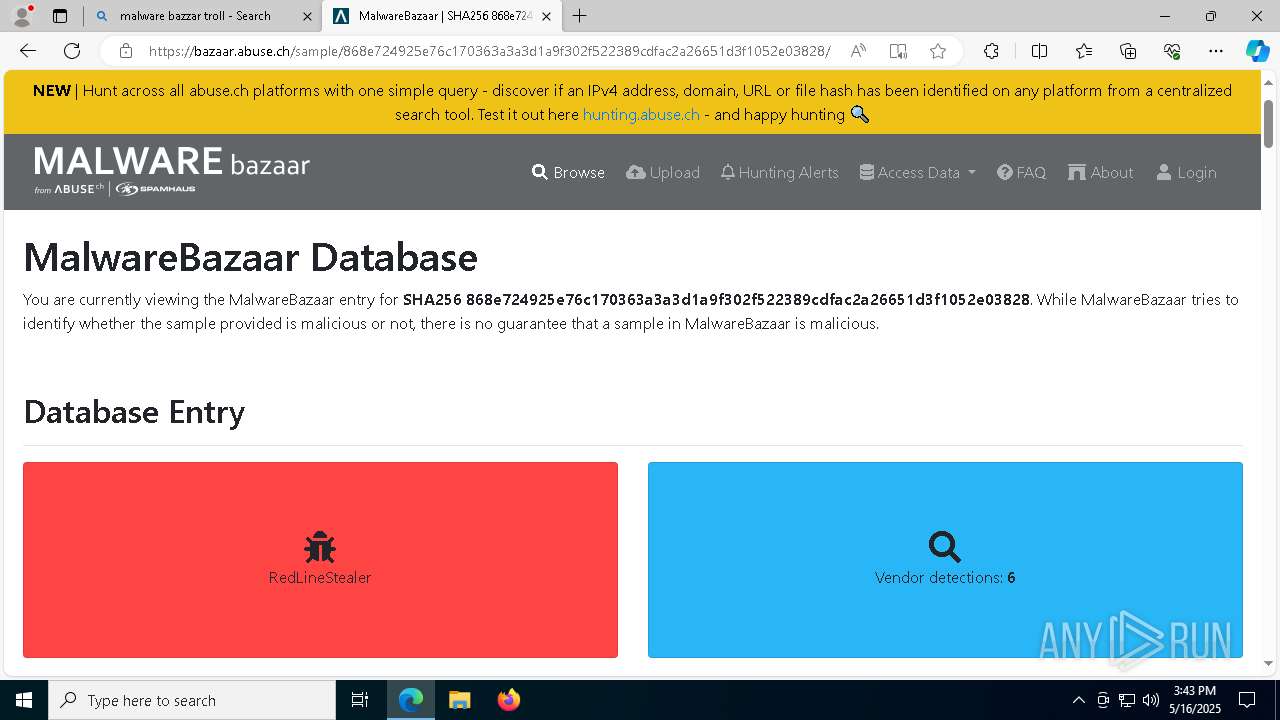
REDLINE has been detected (SURICATA)
- 3wQAlfL.exe (PID: 6252)
Executing a file with an untrusted certificate
- ra02W4S.exe (PID: 7084)
- SF32.exe (PID: 3012)
- SF32.exe (PID: 7048)
- SF32.exe (PID: 6744)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 1020)
Stealers network behavior
- 3wQAlfL.exe (PID: 6252)
MINER has been detected (SURICATA)
- cmd.exe (PID: 2644)
LEFTHOOK has been detected (SURICATA)
- 3wQAlfL.exe (PID: 6252)
REDLINE has been detected (YARA)
- 3wQAlfL.exe (PID: 6252)
METASTEALER has been detected (SURICATA)
- 3wQAlfL.exe (PID: 6252)
GCLEANER has been detected (SURICATA)
- ra02W4S.exe (PID: 7084)
- 907047daa9.exe (PID: 2656)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6148)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- WinRAR.exe (PID: 5156)
The process creates files with name similar to system file names
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
Executable content was dropped or overwritten
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
- powershell.exe (PID: 3884)
- TempHG0MFNP6VFRMWLZGT71JPPOWQPJU2G5J.EXE (PID: 1616)
- ramez.exe (PID: 5736)
- oxDU0MW.exe (PID: 7936)
- WinTemp-v4.exe (PID: 1852)
- SF32.exe (PID: 3012)
- 94eedabdb6.tmp (PID: 7668)
- ra02W4S.exe (PID: 7084)
- 94eedabdb6.exe (PID: 808)
- SF32.exe (PID: 6744)
Application launched itself
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
Probably download files using WebClient
- mshta.exe (PID: 2896)
Starts CMD.EXE for commands execution
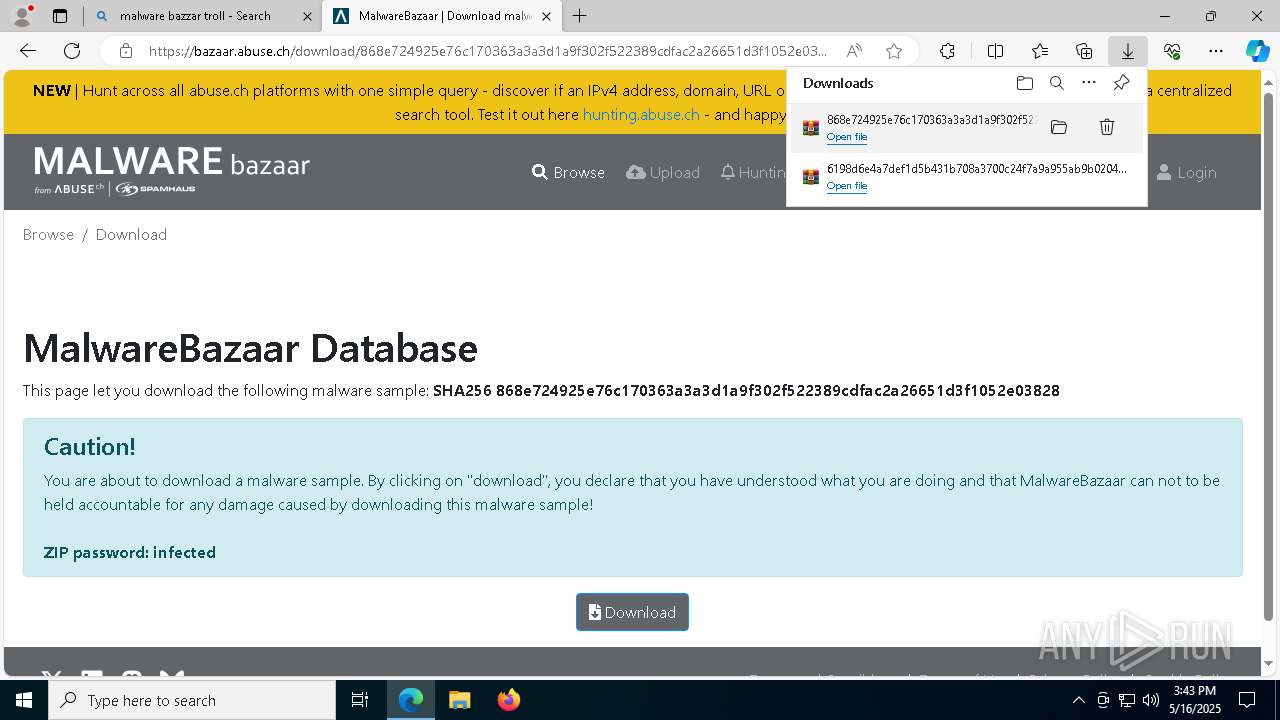
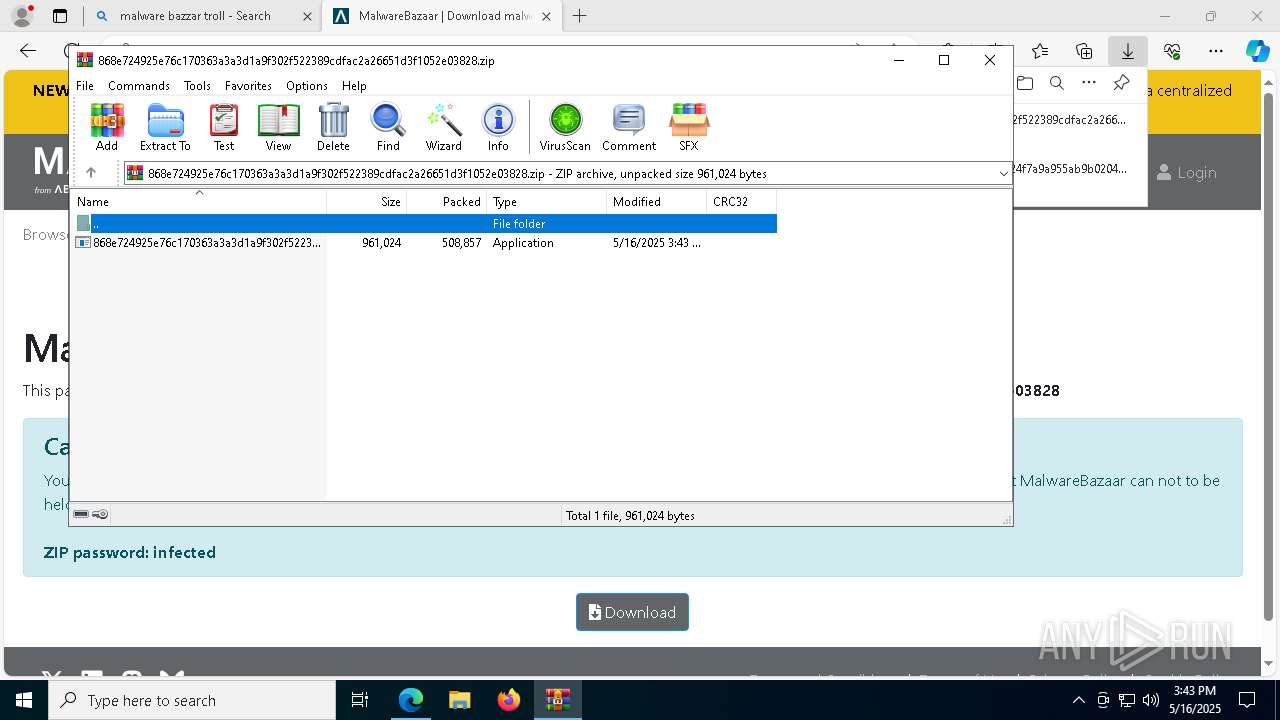
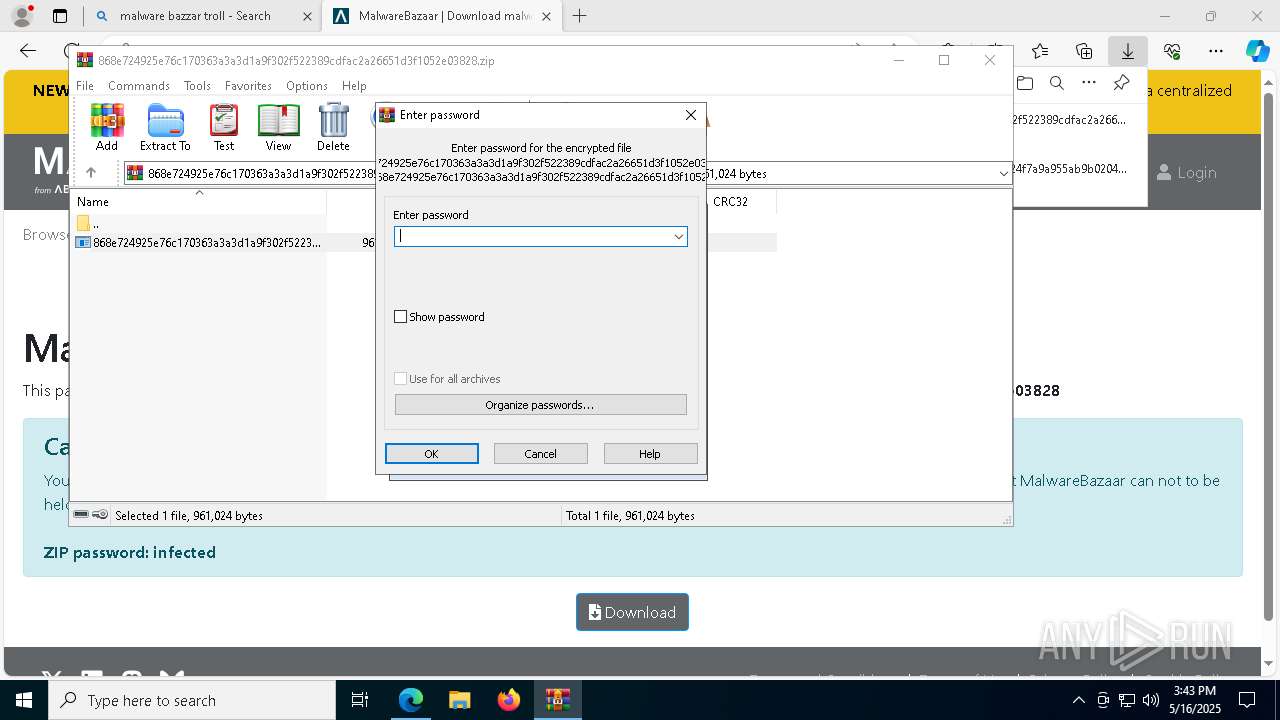
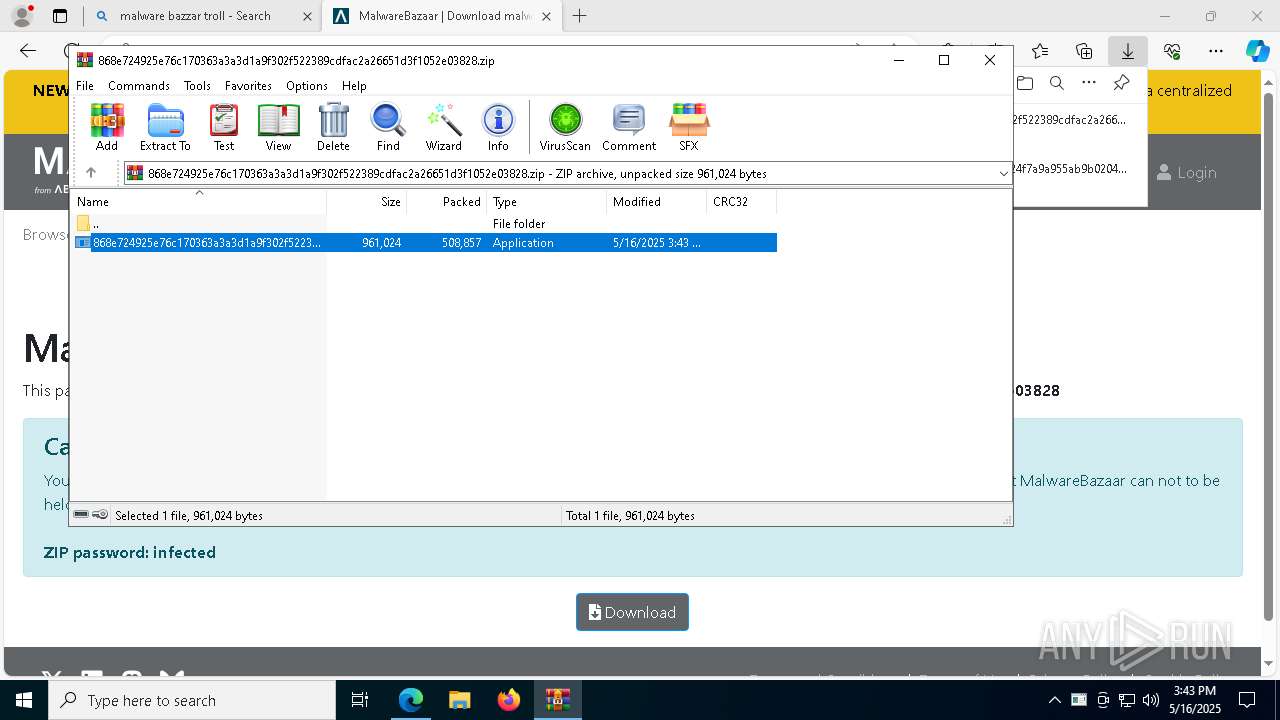
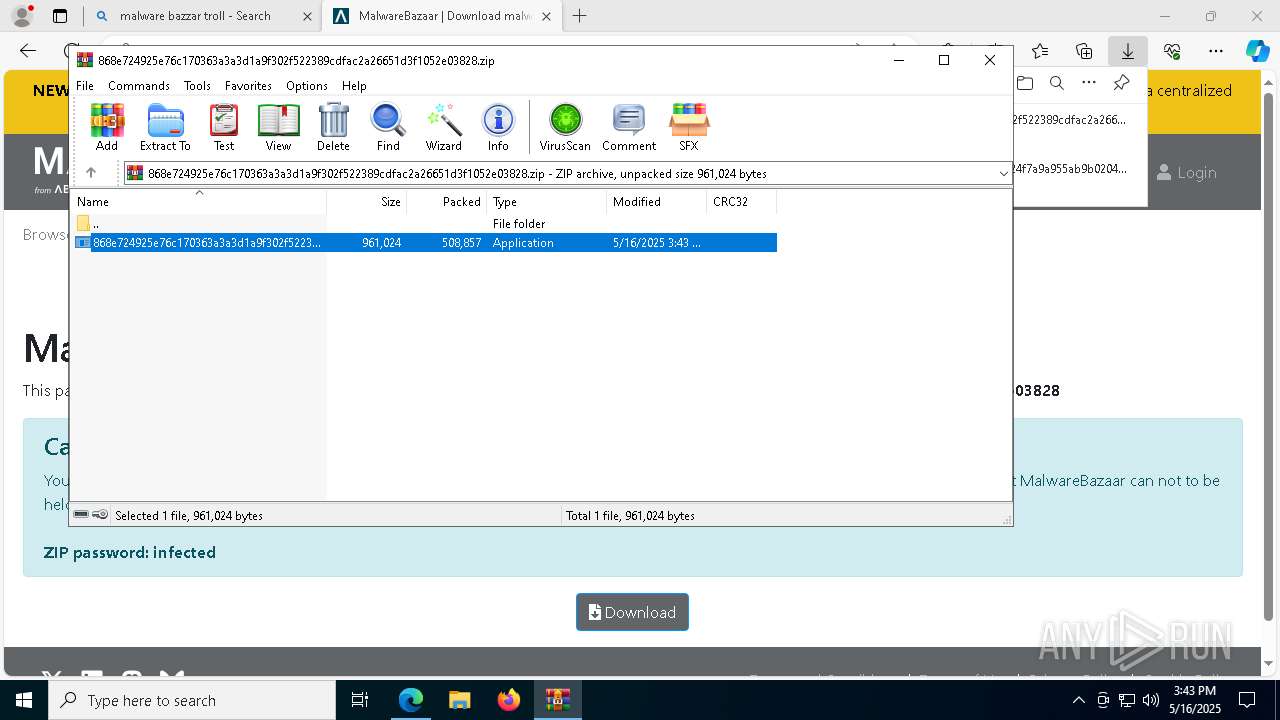
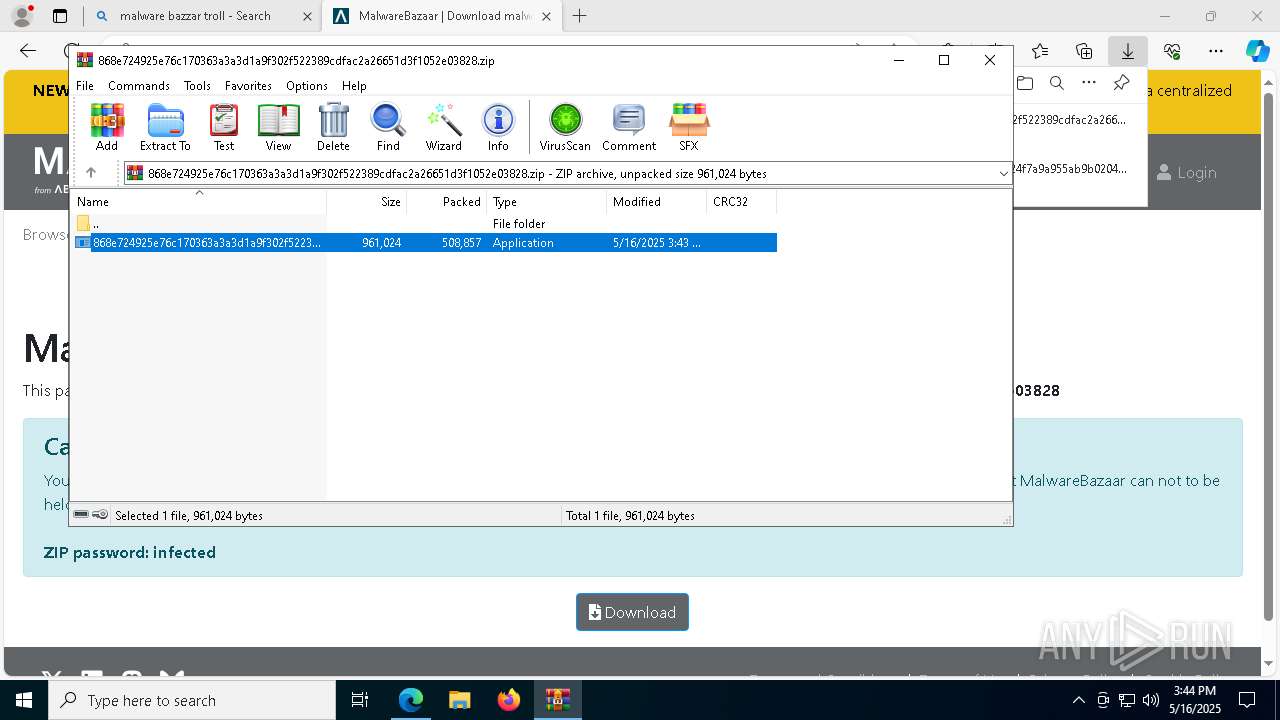
- 868e724925e76c170363a3a3d1a9f302f522389cdfac2a26651d3f1052e03828.exe (PID: 6184)
- WinTemp-v4.exe (PID: 1852)
- SF32.exe (PID: 7048)
Found IP address in command line
- powershell.exe (PID: 3884)
Starts process via Powershell
- powershell.exe (PID: 3884)
Manipulates environment variables
- powershell.exe (PID: 3884)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 2896)
- WinTemp-v4.exe (PID: 1852)
- cmd.exe (PID: 6300)
- MSBuild.exe (PID: 8228)
Process requests binary or script from the Internet
- powershell.exe (PID: 3884)
- ramez.exe (PID: 5736)
Connects to the server without a host name
- powershell.exe (PID: 3884)
- ramez.exe (PID: 5736)
- ra02W4S.exe (PID: 7084)
- 907047daa9.exe (PID: 2656)
Potential Corporate Privacy Violation
- powershell.exe (PID: 3884)
- ramez.exe (PID: 5736)
- cmd.exe (PID: 2644)
- ra02W4S.exe (PID: 7084)
Starts itself from another location
- TempHG0MFNP6VFRMWLZGT71JPPOWQPJU2G5J.EXE (PID: 1616)
- SF32.exe (PID: 3012)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 5736)
- 3wQAlfL.exe (PID: 6252)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 1020)
Script adds exclusion process to Windows Defender
- WinTemp-v4.exe (PID: 1852)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 5736)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 5736)
Script adds exclusion path to Windows Defender
- WinTemp-v4.exe (PID: 1852)
Connects to unusual port
- 3wQAlfL.exe (PID: 6252)
- cmd.exe (PID: 2644)
- WinTemp-v4.exe (PID: 1852)
Multiple wallet extension IDs have been found
- ramez.exe (PID: 5736)
- 3wQAlfL.exe (PID: 6252)
There is functionality for VM detection VMWare (YARA)
- WinTemp-v4.exe (PID: 1852)
The process executes via Task Scheduler
- ramez.exe (PID: 7800)
- ramez.exe (PID: 3620)
There is functionality for VM detection VirtualBox (YARA)
- WinTemp-v4.exe (PID: 1852)
Process drops legitimate windows executable
- ramez.exe (PID: 5736)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3968)
- cmd.exe (PID: 4572)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 5216)
Uses powercfg.exe to modify the power settings
- WinTemp-v4.exe (PID: 1852)
Hides command output
- cmd.exe (PID: 1204)
Starts a Microsoft application from unusual location
- 08IyOOF.exe (PID: 6340)
Checks for external IP
- WinTemp-v4.exe (PID: 1852)
- svchost.exe (PID: 2196)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 1760)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6300)
Executes application which crashes
- core.exe (PID: 1704)
- Win-v41.exe (PID: 2204)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 8228)
The process hide an interactive prompt from the user
- MSBuild.exe (PID: 8228)
BASE64 encoded PowerShell command has been detected
- MSBuild.exe (PID: 8228)
The process bypasses the loading of PowerShell profile settings
- MSBuild.exe (PID: 8228)
Executes as Windows Service
- cmd.exe (PID: 6300)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4988)
- csc.exe (PID: 3240)
- csc.exe (PID: 4968)
Base64-obfuscated command line is found
- MSBuild.exe (PID: 8228)
INFO
Checks supported languages
- identity_helper.exe (PID: 1676)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 924)
- 868e724925e76c170363a3a3d1a9f302f522389cdfac2a26651d3f1052e03828.exe (PID: 6184)
Application launched itself
- msedge.exe (PID: 5972)
- chrome.exe (PID: 9188)
- chrome.exe (PID: 7828)
- chrome.exe (PID: 8500)
- chrome.exe (PID: 8876)
- chrome.exe (PID: 5528)
Reads the computer name
- identity_helper.exe (PID: 1676)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 924)
- 868e724925e76c170363a3a3d1a9f302f522389cdfac2a26651d3f1052e03828.exe (PID: 6184)
Reads Environment values
- identity_helper.exe (PID: 1676)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5972)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6148)
- msedge.exe (PID: 7828)
- WinRAR.exe (PID: 5156)
- msiexec.exe (PID: 5216)
Reads the software policy settings
- slui.exe (PID: 8100)
- slui.exe (PID: 6184)
Reads the machine GUID from the registry
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 924)
Process checks whether UAC notifications are on
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
Creates files or folders in the user directory
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
Process checks computer location settings
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 5204)
Creates files in the program directory
- 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe (PID: 4868)
Checks proxy server information
- slui.exe (PID: 6184)
The sample compiled with english language support
- WinRAR.exe (PID: 5156)
- msedge.exe (PID: 7828)
- ramez.exe (PID: 5736)
- SF32.exe (PID: 3012)
- msiexec.exe (PID: 5216)
- SF32.exe (PID: 6744)
Reads mouse settings
- 868e724925e76c170363a3a3d1a9f302f522389cdfac2a26651d3f1052e03828.exe (PID: 6184)
Create files in a temporary directory
- 868e724925e76c170363a3a3d1a9f302f522389cdfac2a26651d3f1052e03828.exe (PID: 6184)
Reads Internet Explorer settings
- mshta.exe (PID: 2896)
The executable file from the user directory is run by the Powershell process
- TempHG0MFNP6VFRMWLZGT71JPPOWQPJU2G5J.EXE (PID: 1616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
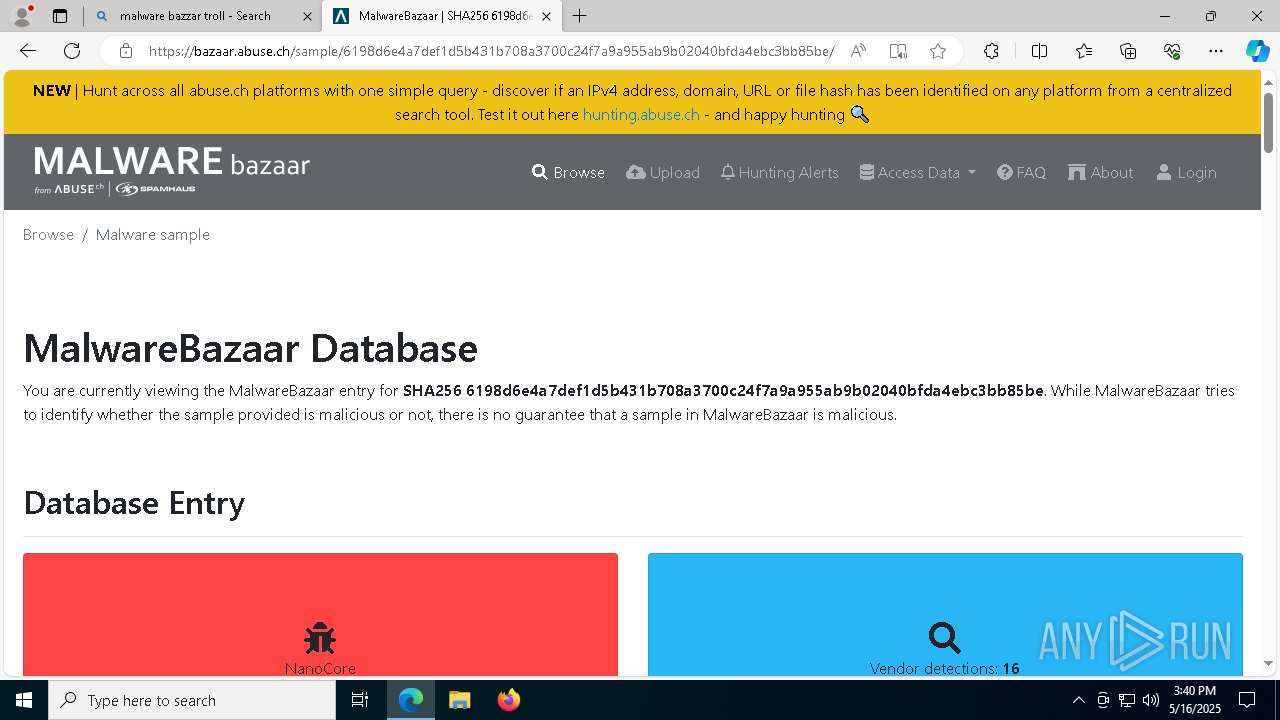
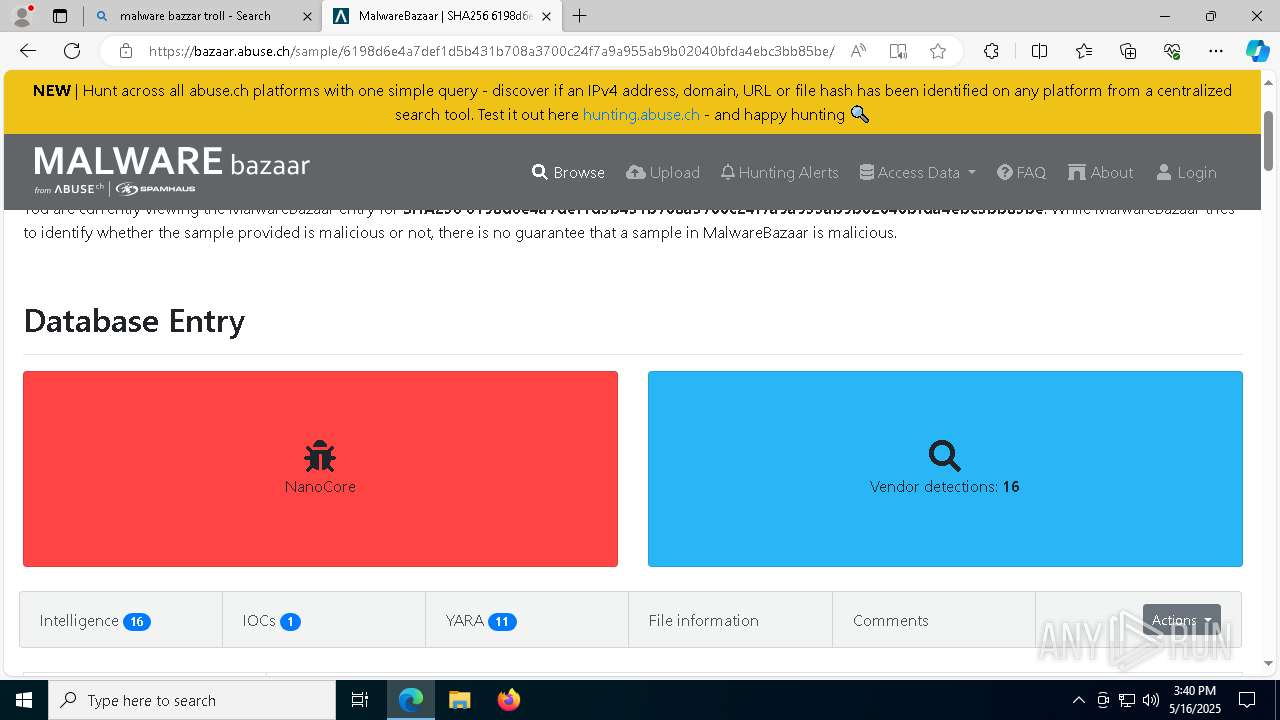
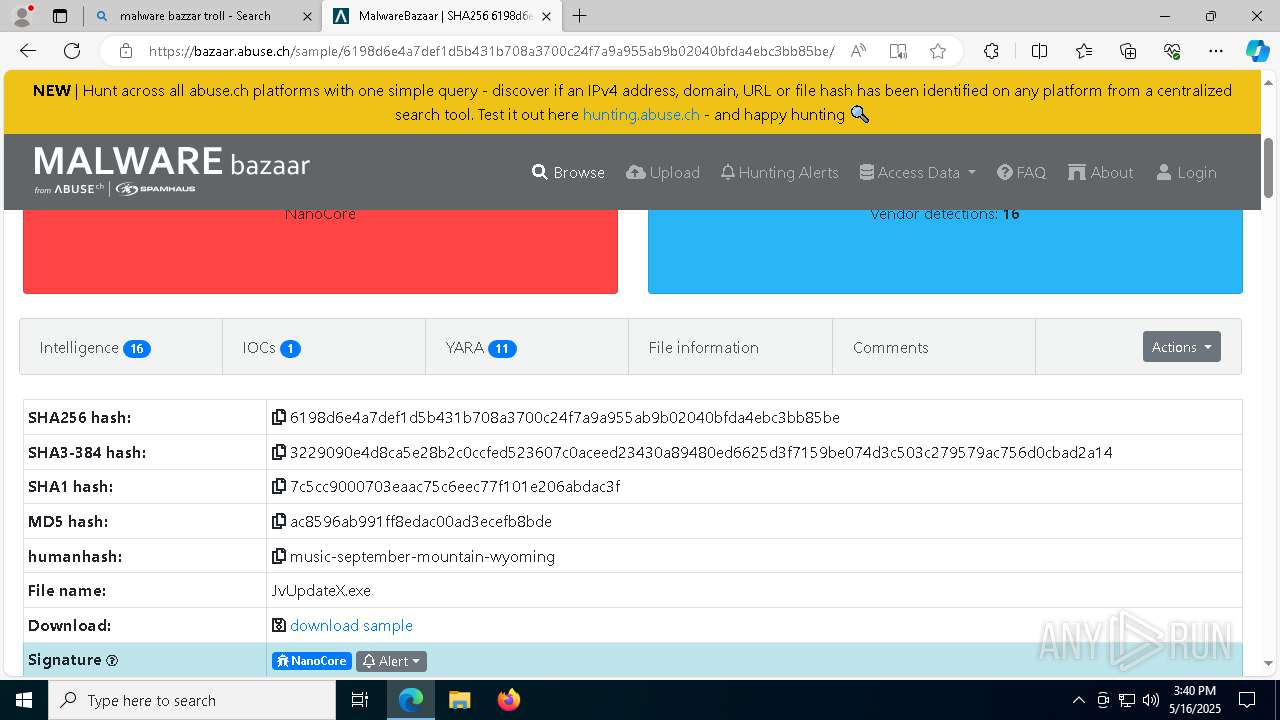
Nanocore
(PID) Process(4868) 6198d6e4a7def1d5b431b708a3700c24f7a9a955ab9b02040bfda4ebc3bb85be.exe
KeyboardLoggingTrue
BuildTime2022-08-07 20:24:24.368392
Version1.2.2.0
Mutexbceb253a-e8e2-4b9e-b56d-a05378b7d66f
DefaultGroupDefault
PrimaryConnectionHostsusyamog458dhref34.ddns.net
BackupConnectionHostsusyamog458dhref34.ddns.net
ConnectionPort54984
RunOnStartupTrue
RequestElevationTrue
BypassUserAccountControlFalse
ClearZoneIdentifierTrue
ClearAccessControlFalse
SetCriticalProcessTrue
PreventSystemSleepTrue
ActivateAwayModeFalse
EnableDebugModeFalse
RunDelay0
ConnectDelay4000
RestartDelay4988
TimeoutInterval5000
KeepAliveTimeout30000
MutexTimeout5000
LanTimeout2500
WanTimeout8000
BufferSize65535
MaxPacketSize10485760
GCThreshold10485760
UseCustomDnsServerTrue
PrimaryDnsServer8.8.8.8
BackupDnsServer8.8.4.4
Amadey
(PID) Process(5736) ramez.exe
C2185.156.72.96
URLhttp://185.156.72.96/te4h2nus/index.php
Version5.34
Options
Drop directoryd610cf342e
Drop nameramez.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
d610cf342e
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
Norton
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
/te4h2nus/index.php
------
5.34
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
ramez.exe
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
185.156.72.96
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
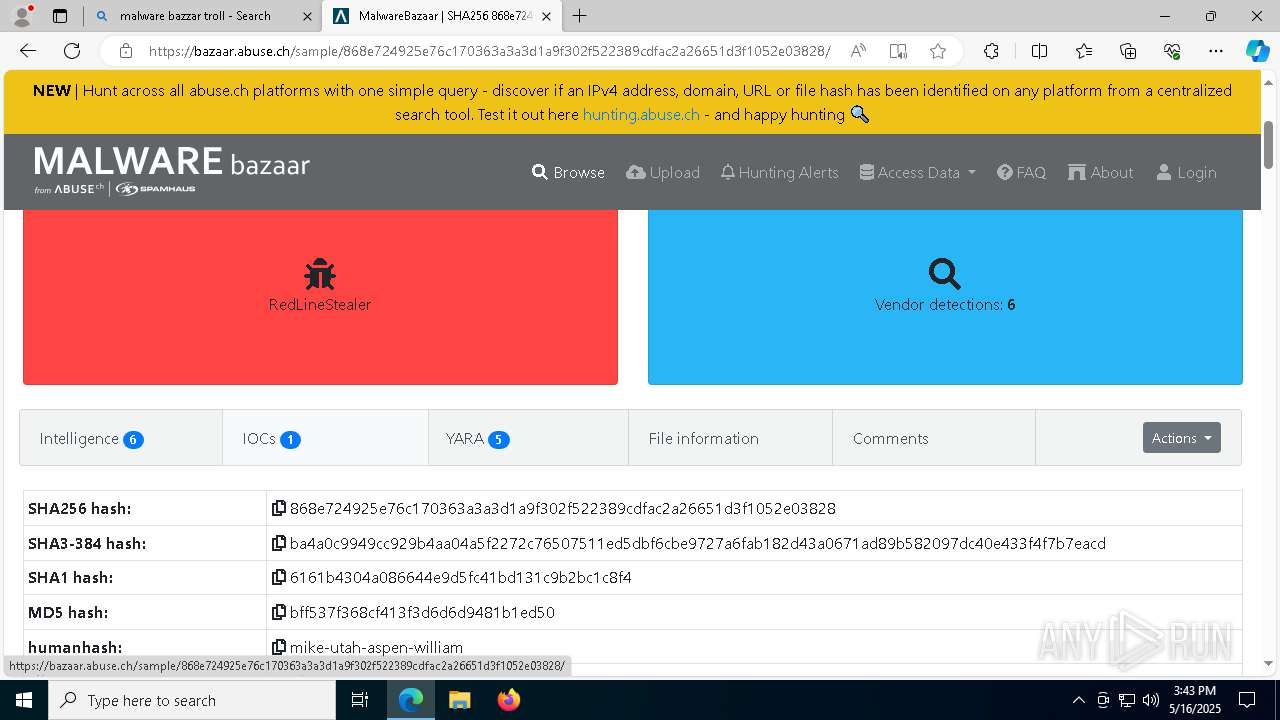
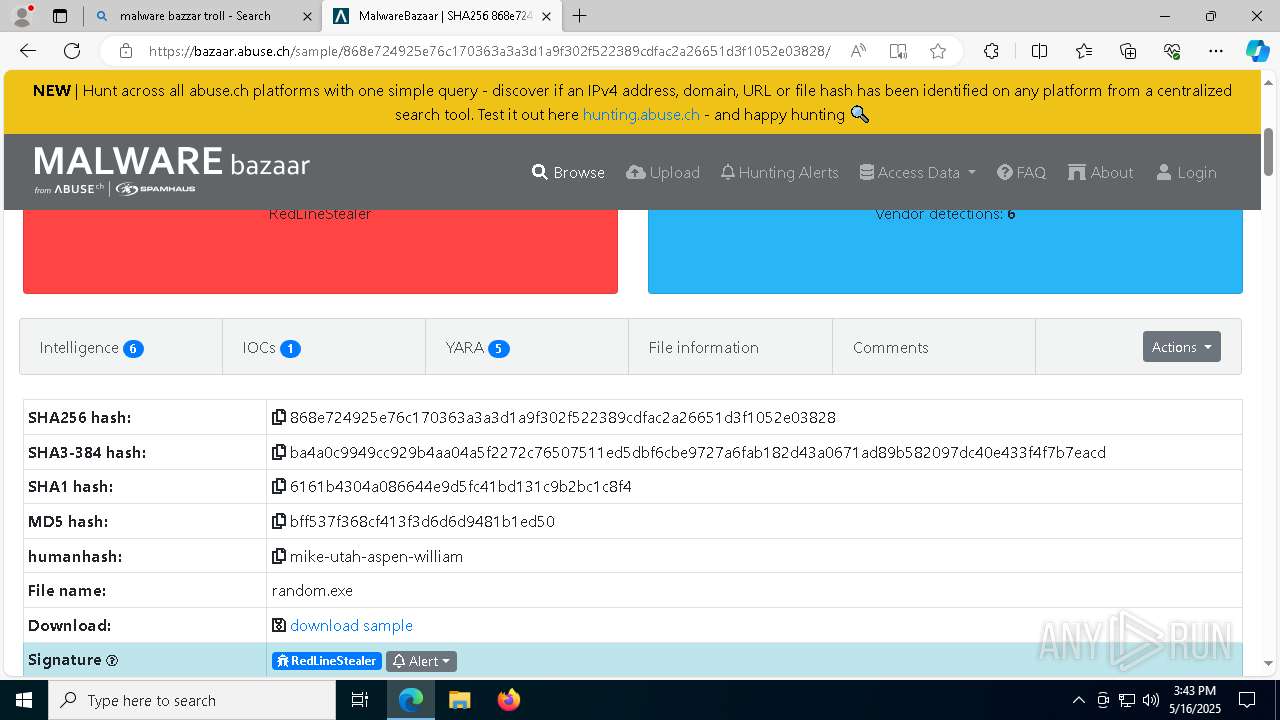
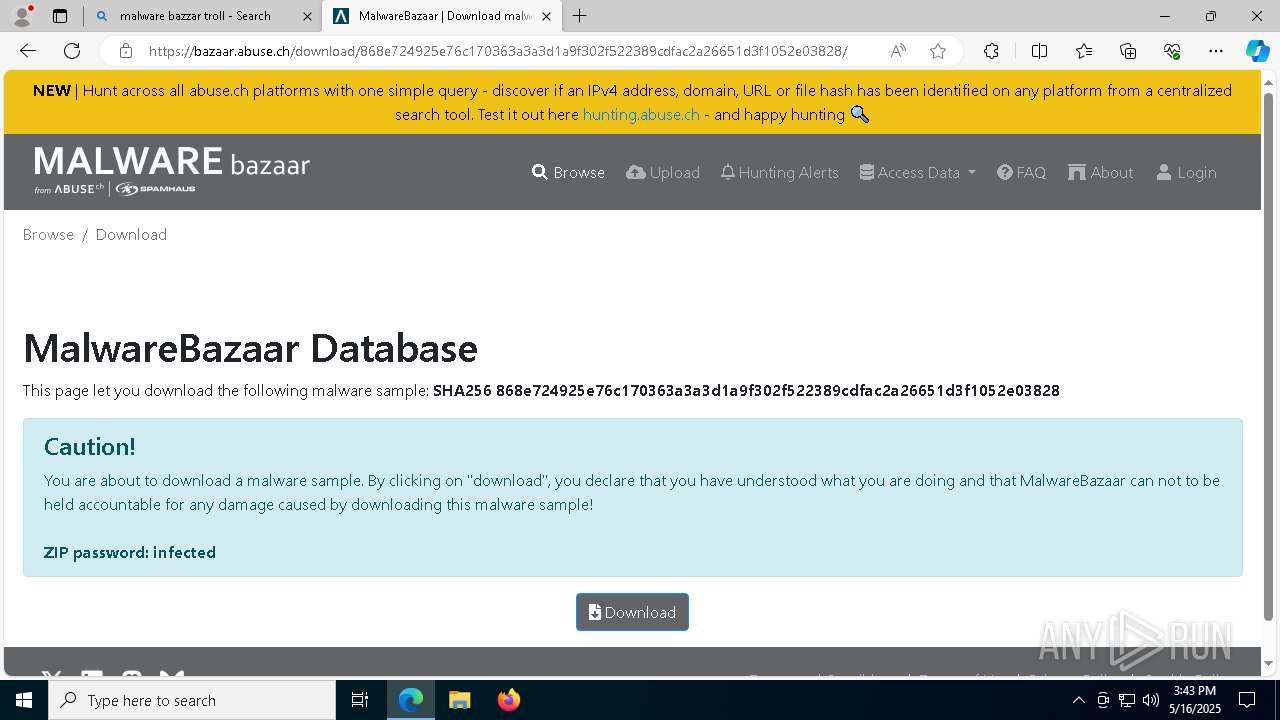
RedLine
(PID) Process(6252) 3wQAlfL.exe
C2 (1)154.91.34.165:64951
Botnetcheat
Keys
Xor
Options
ErrorMessage
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| Robots: | noindex |
|---|---|
| Viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
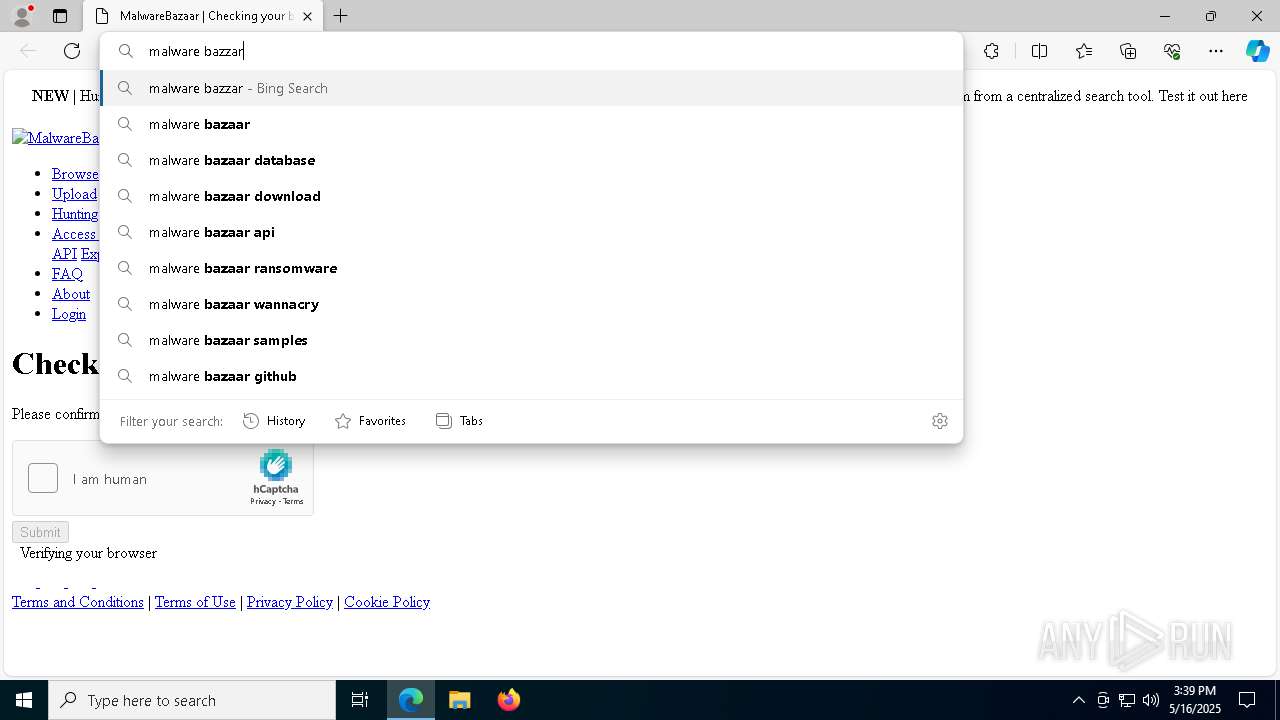
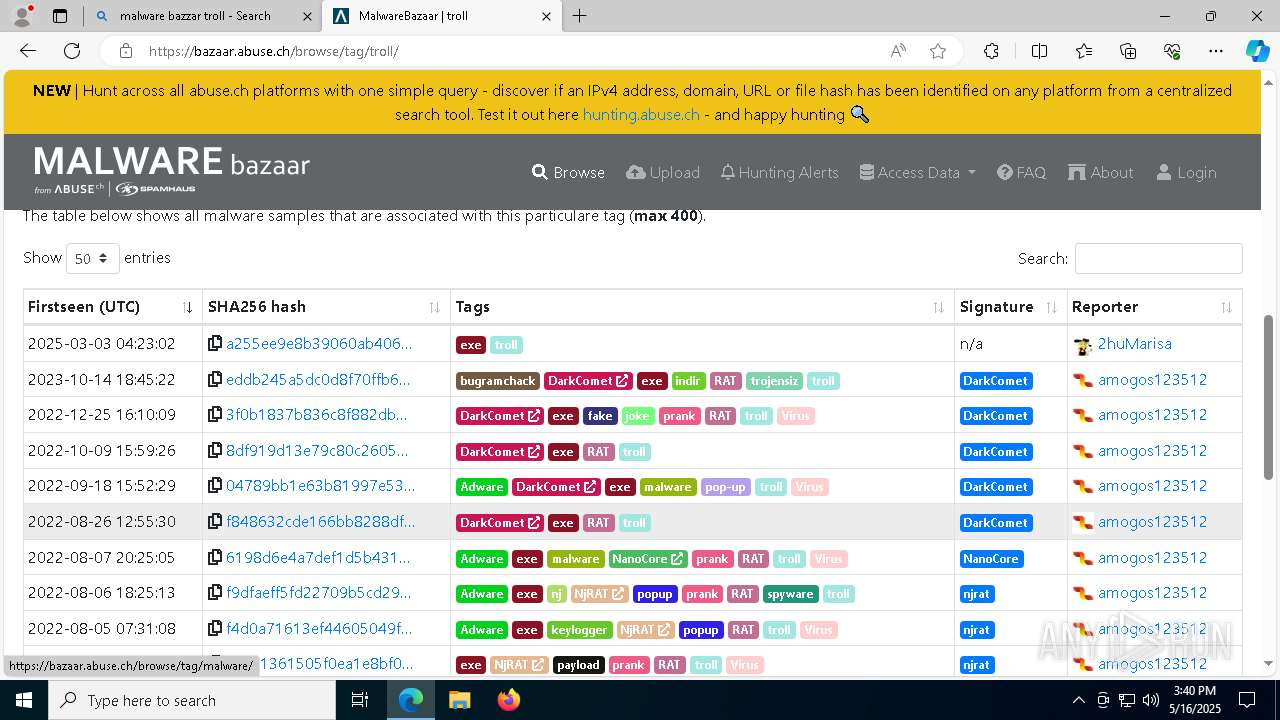
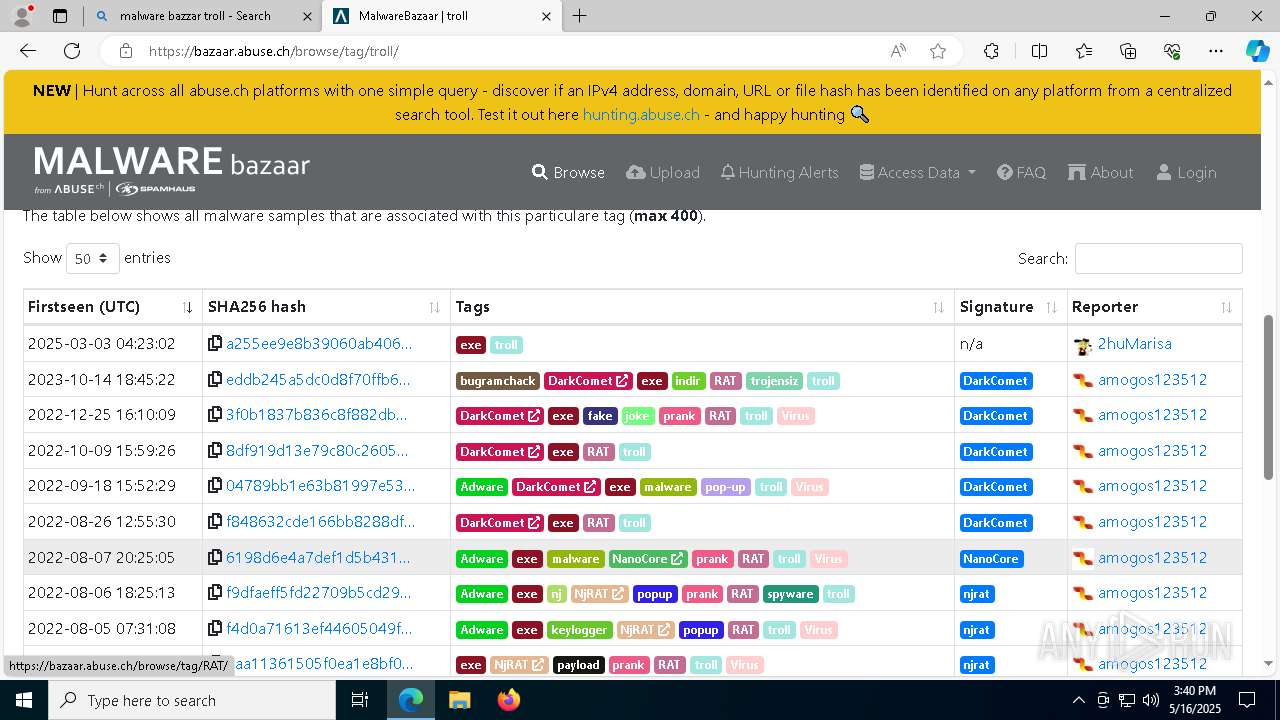
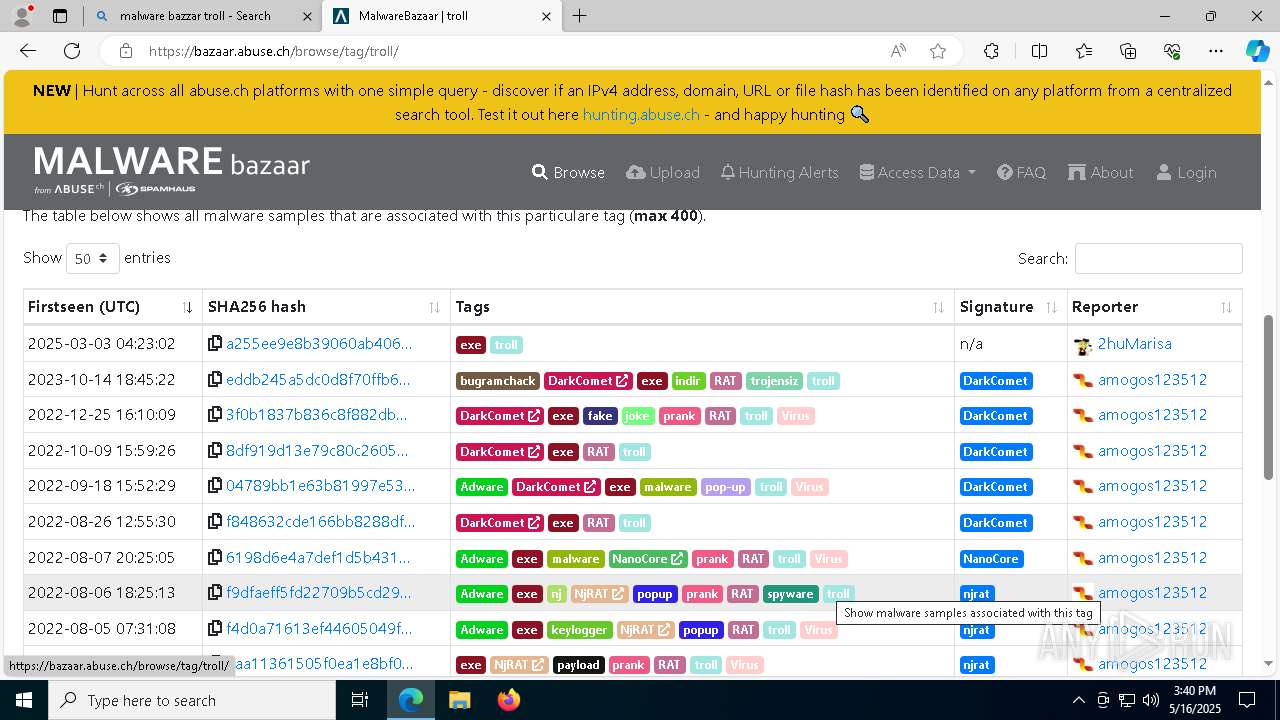
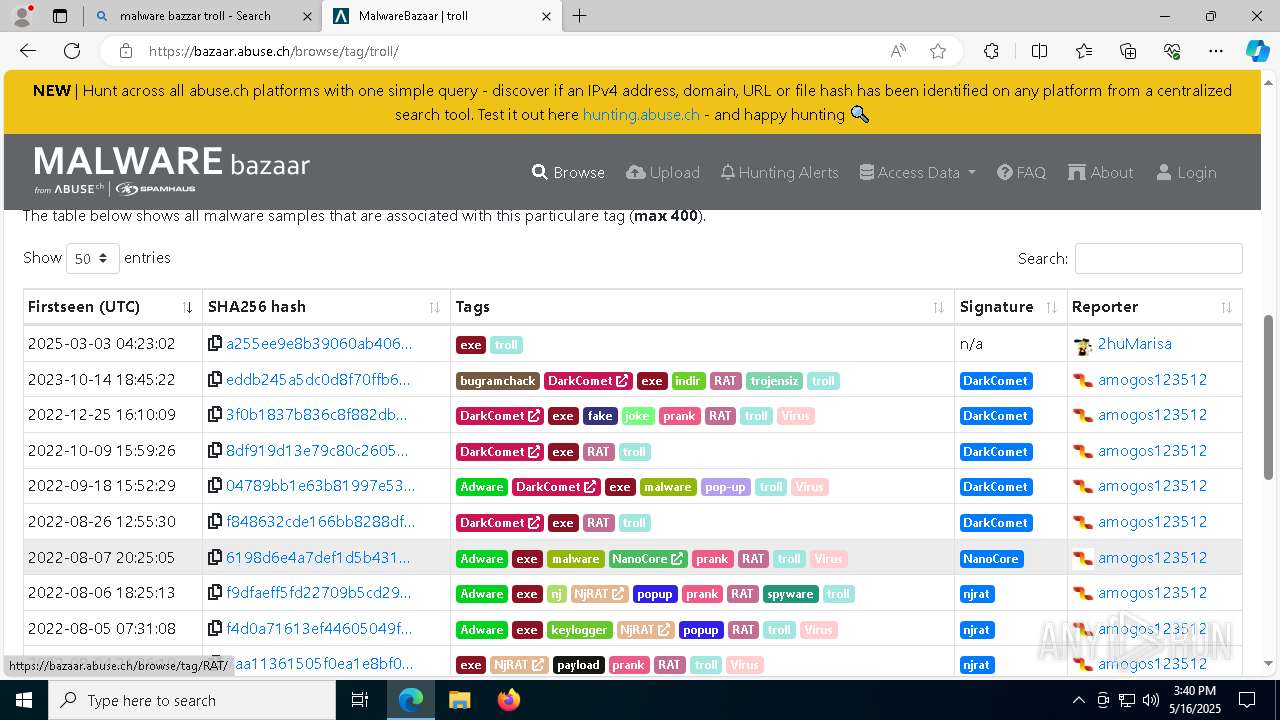
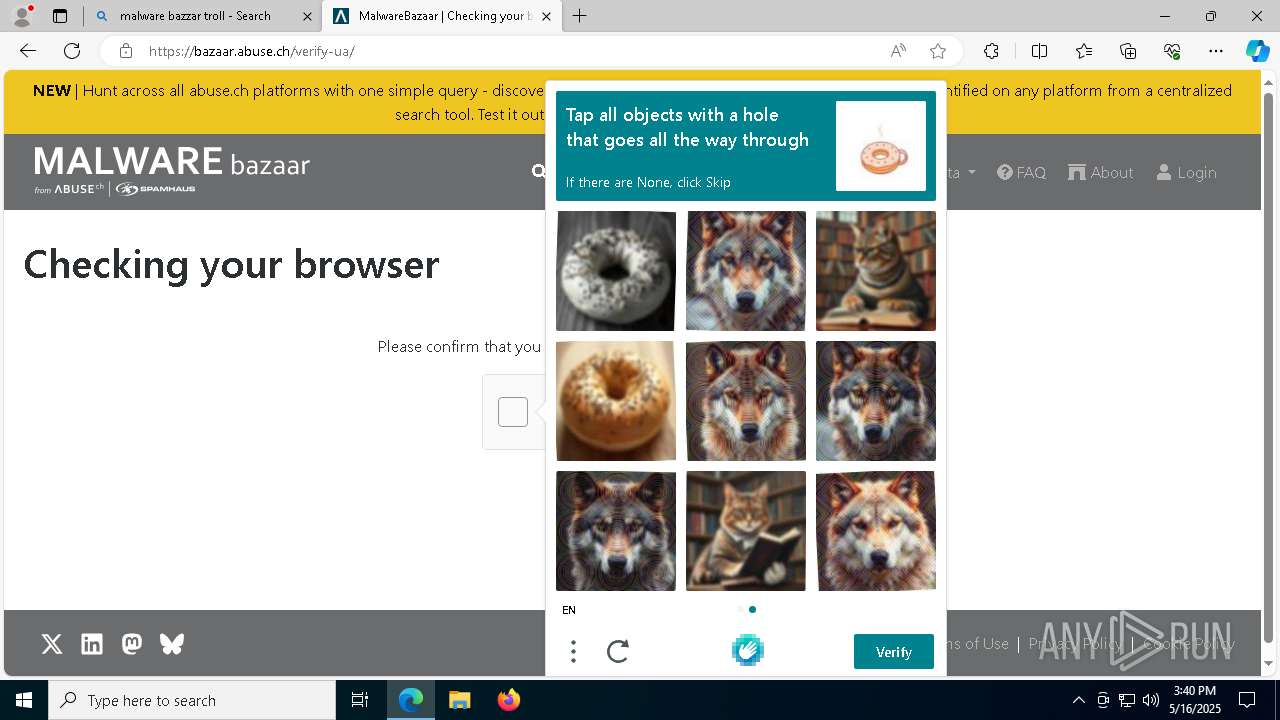
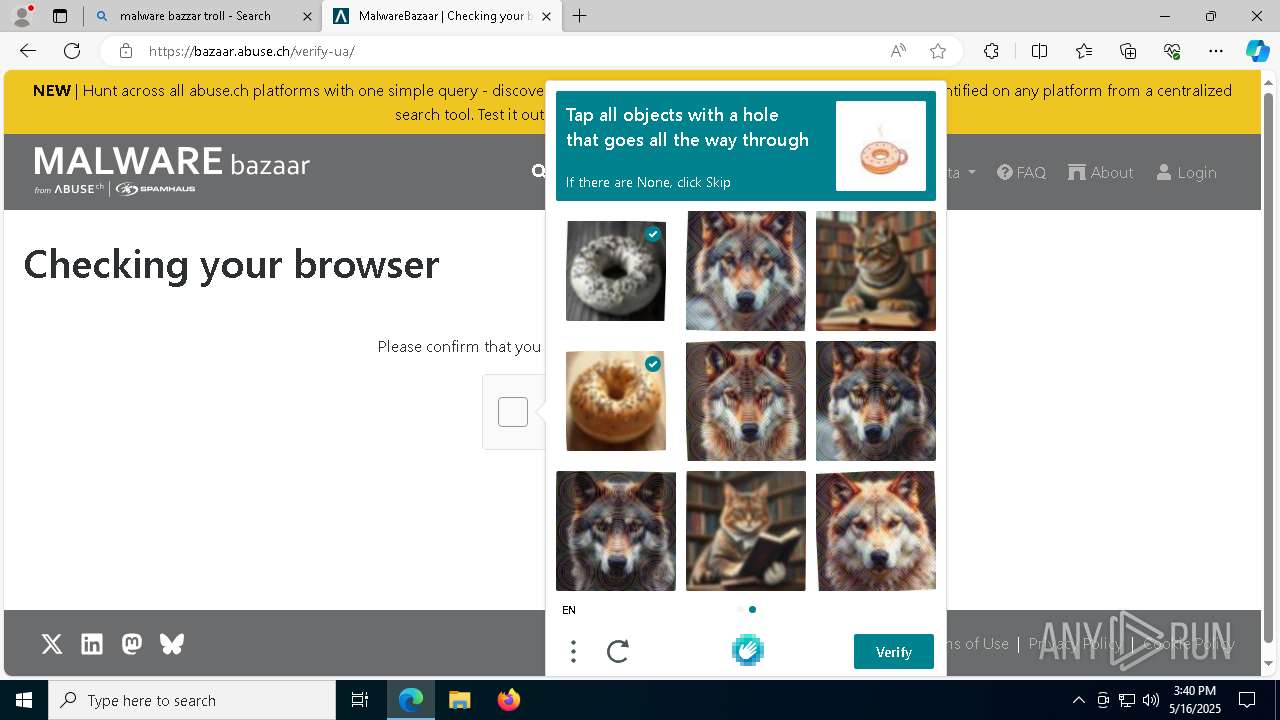
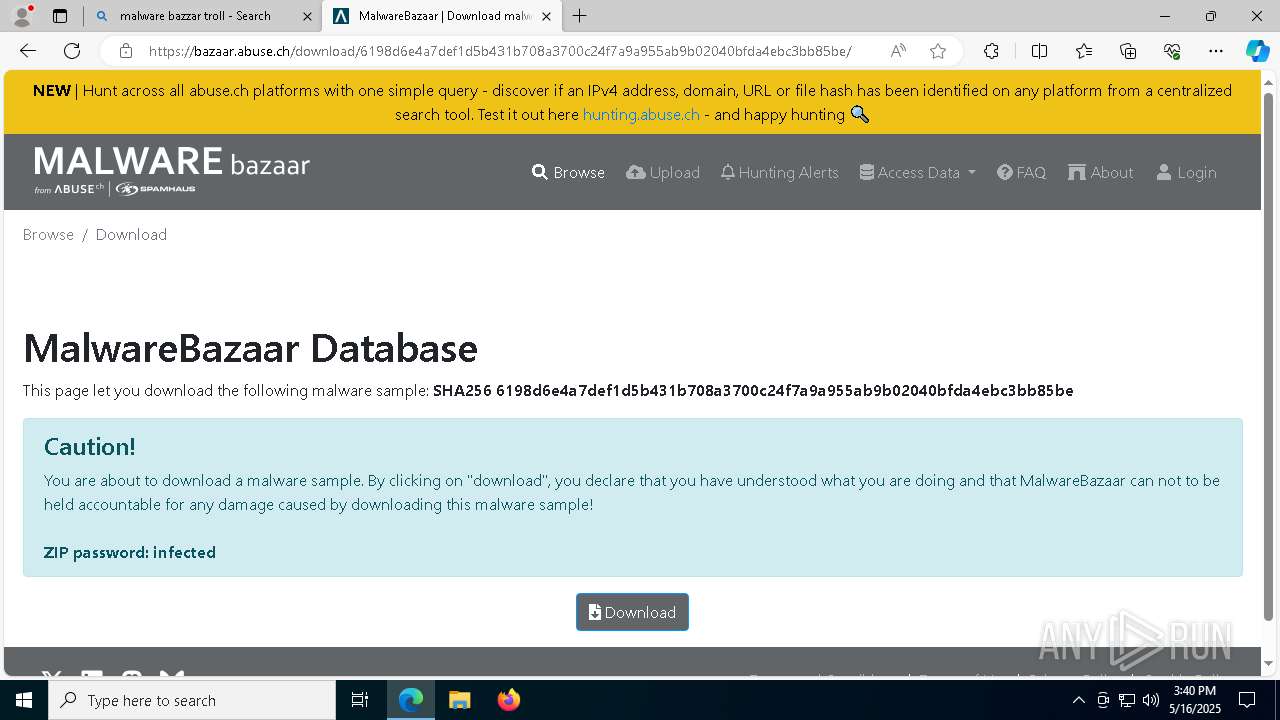
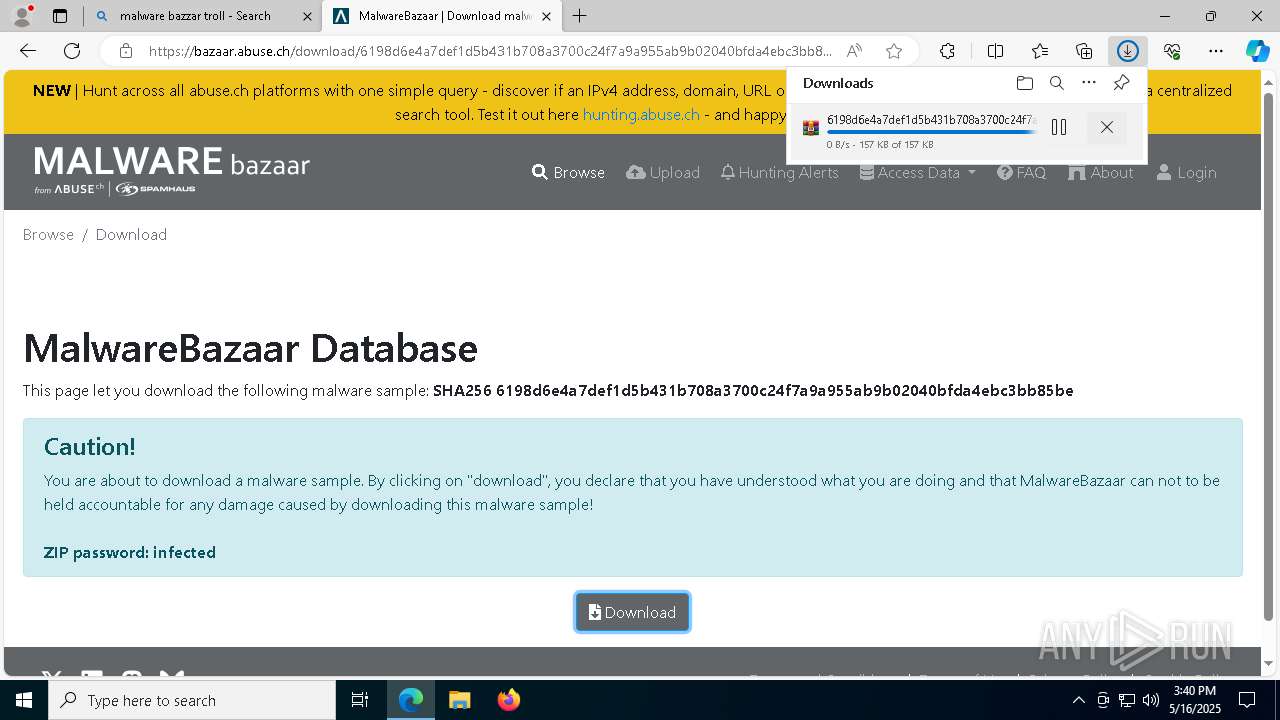
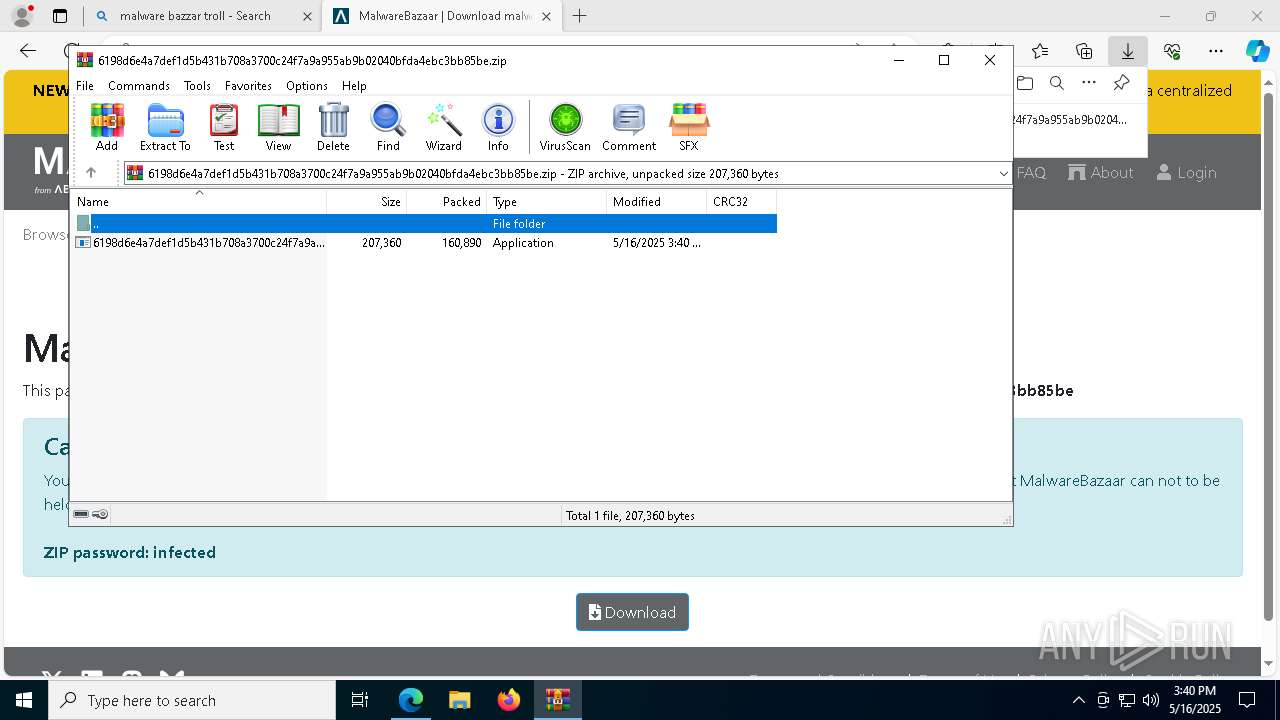
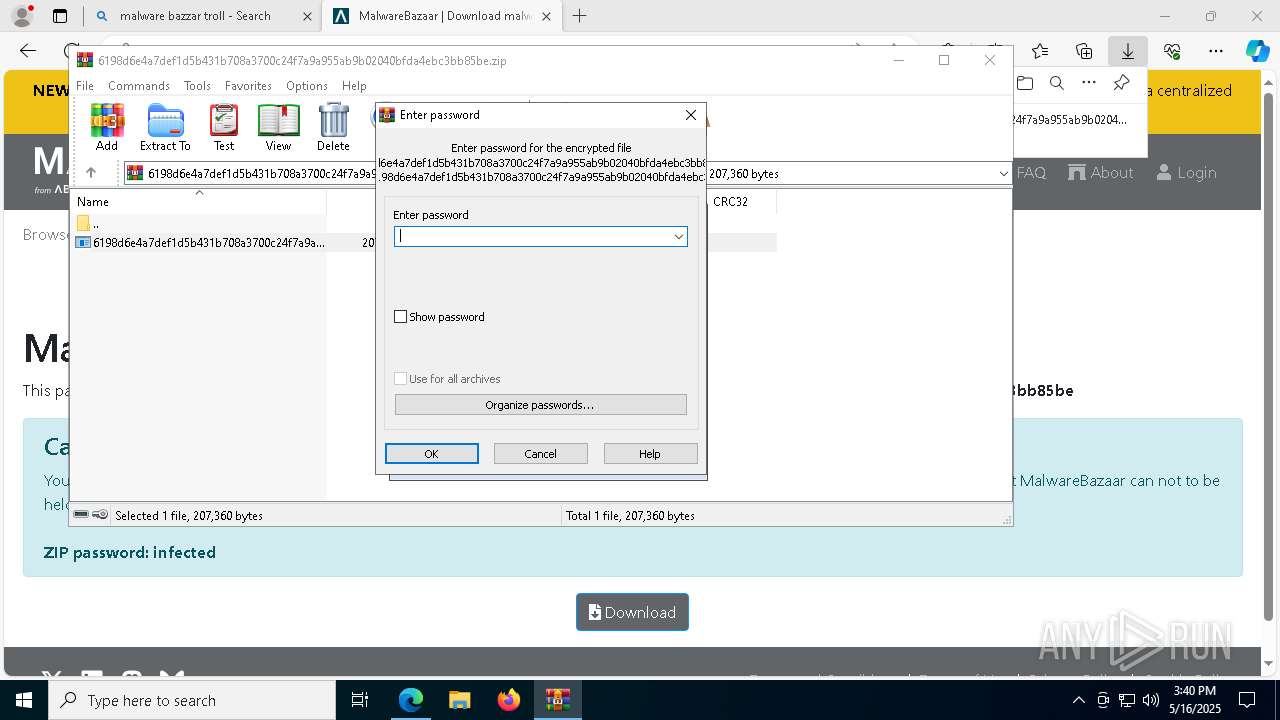
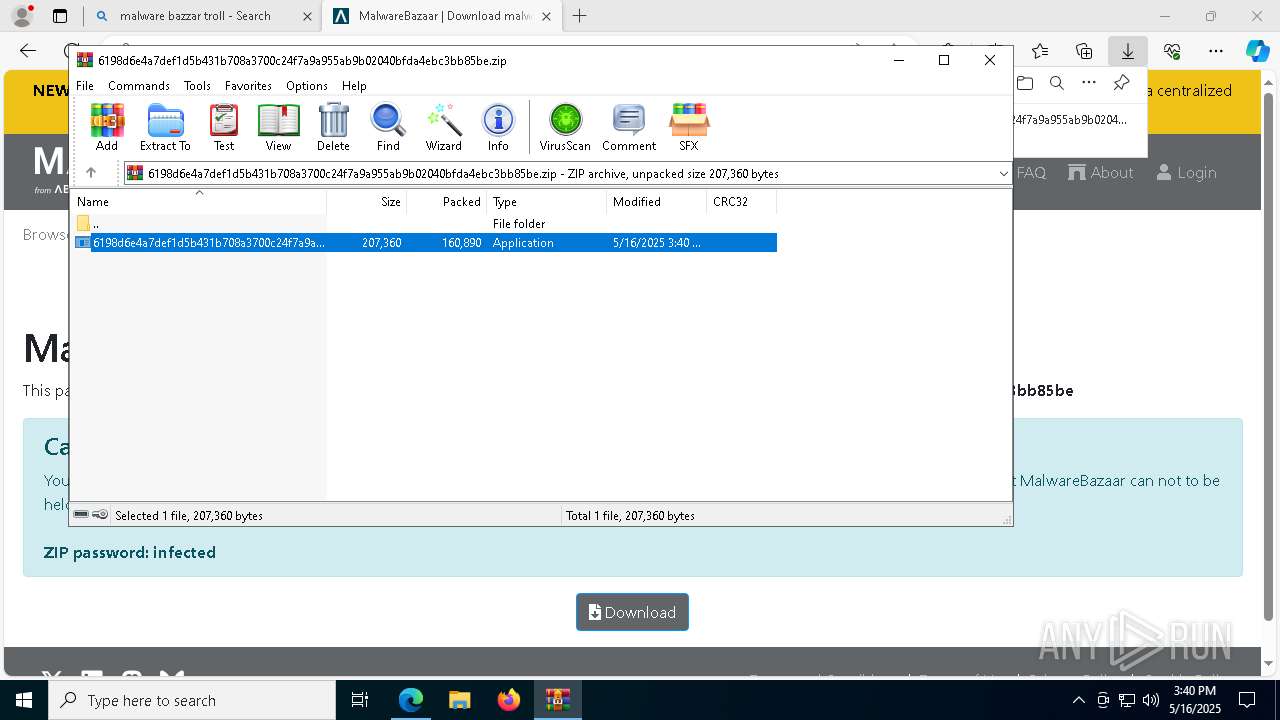
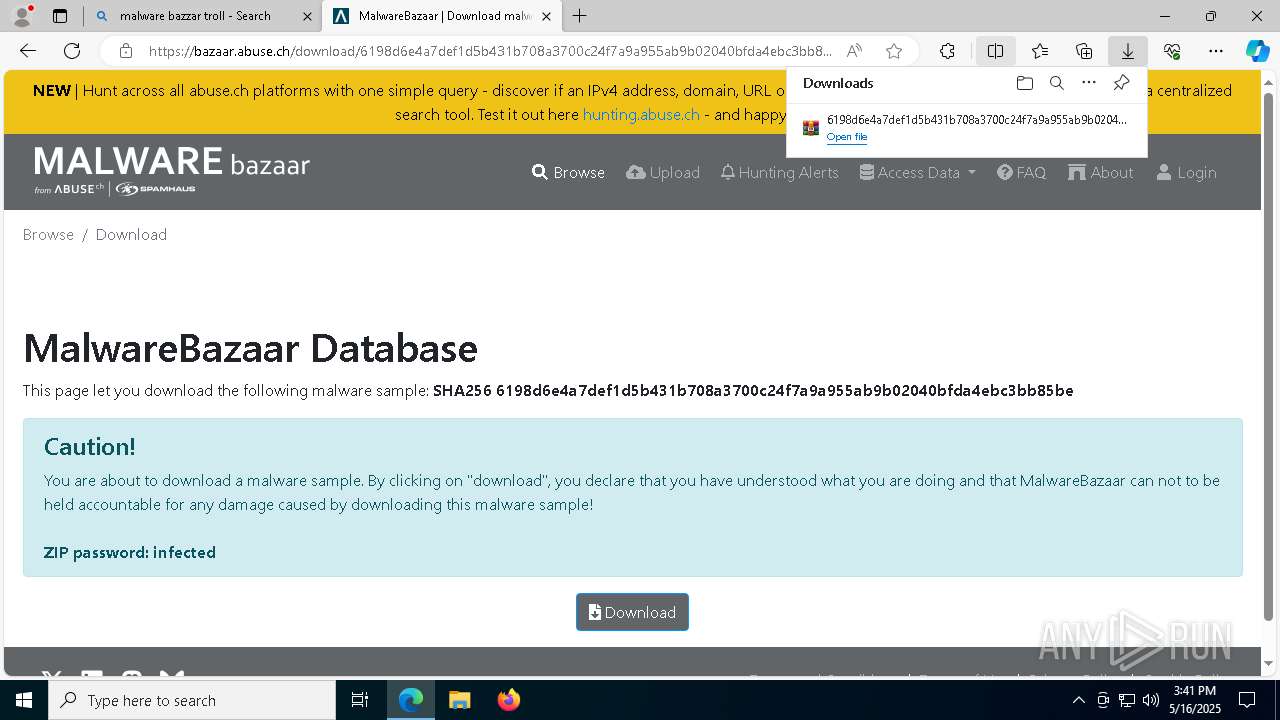
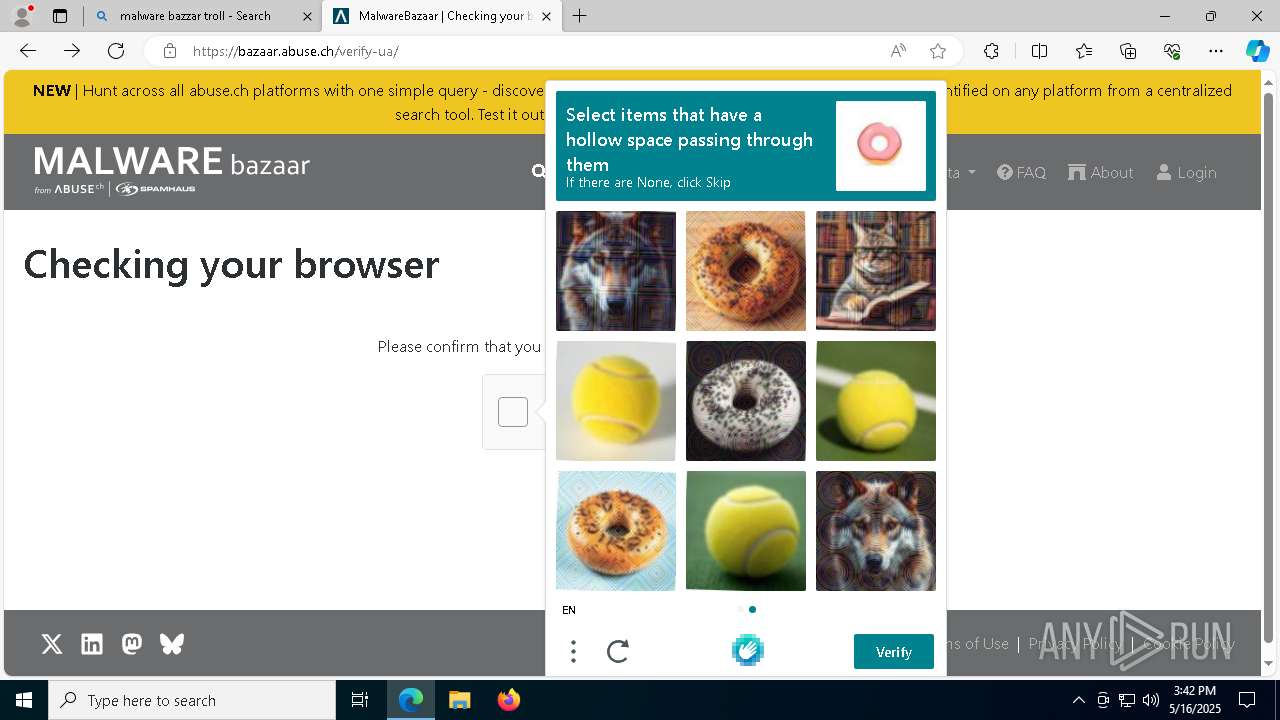
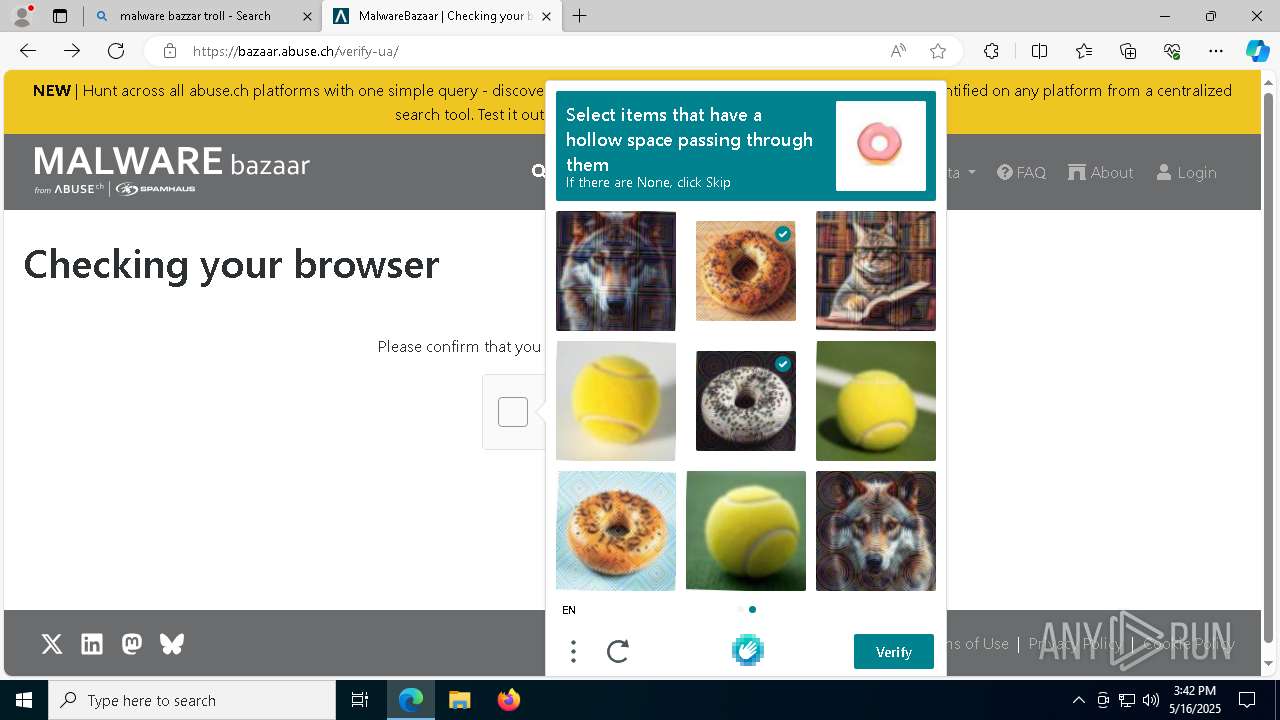
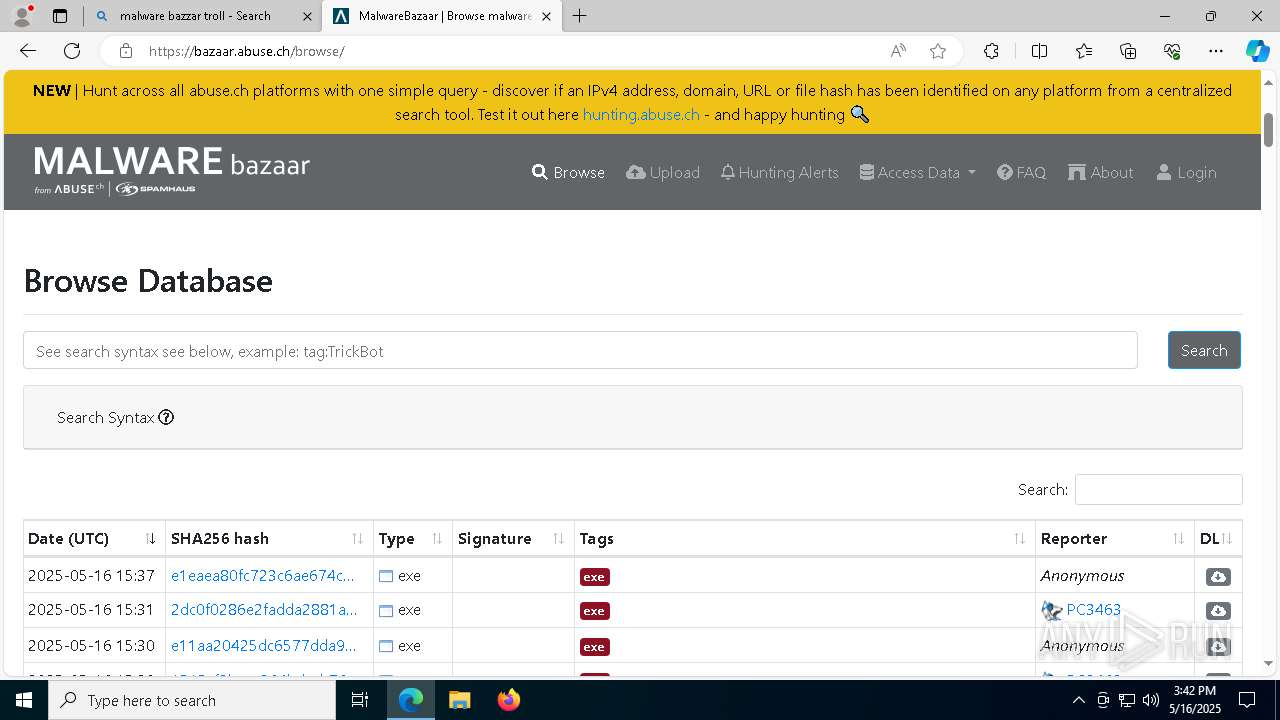
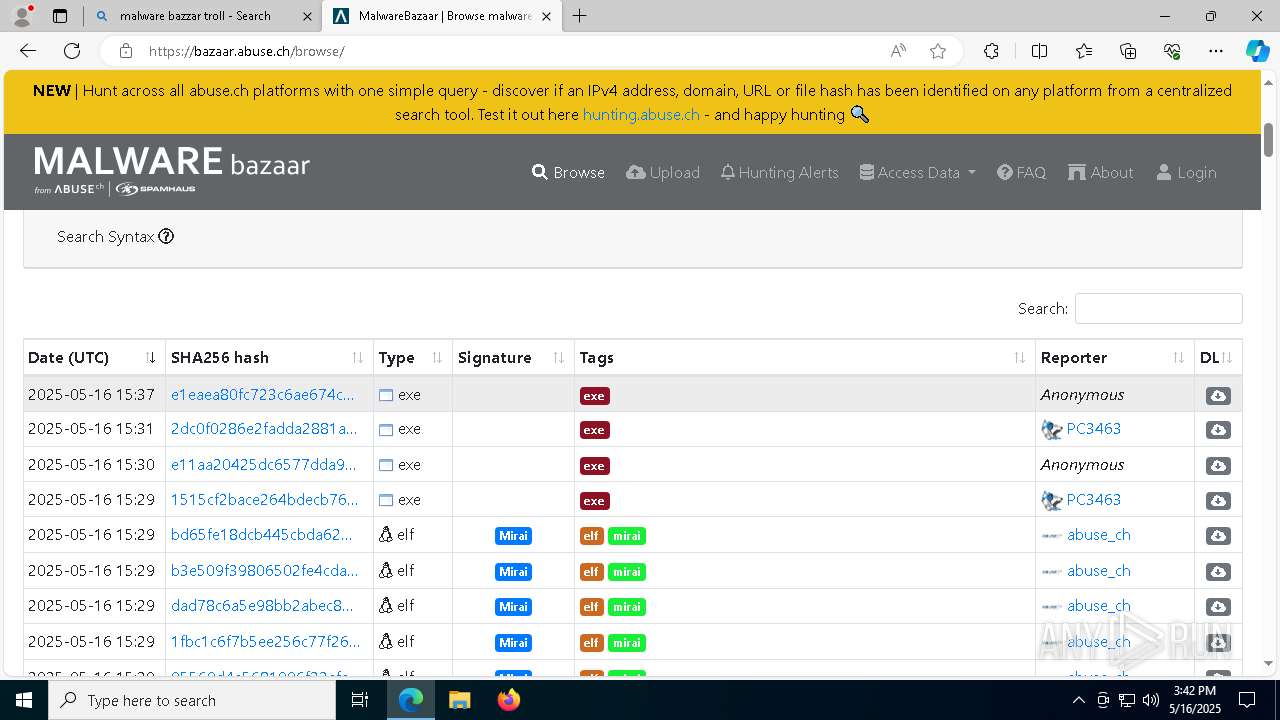
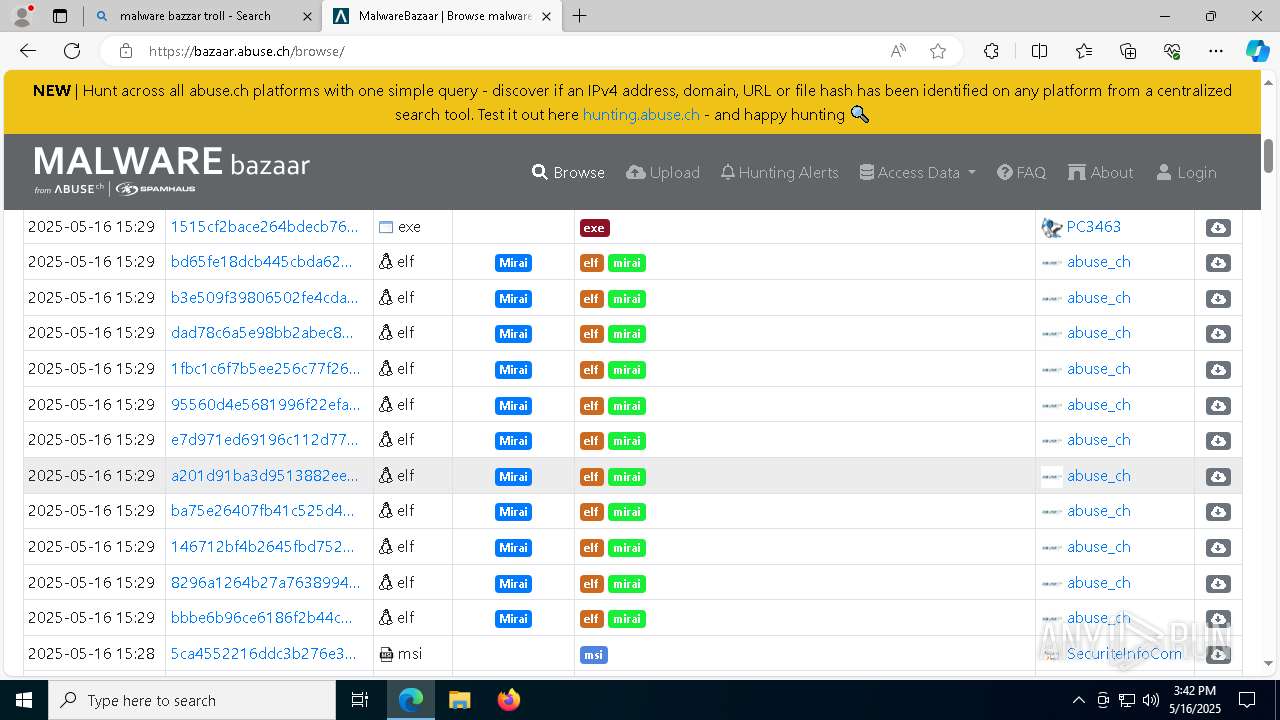
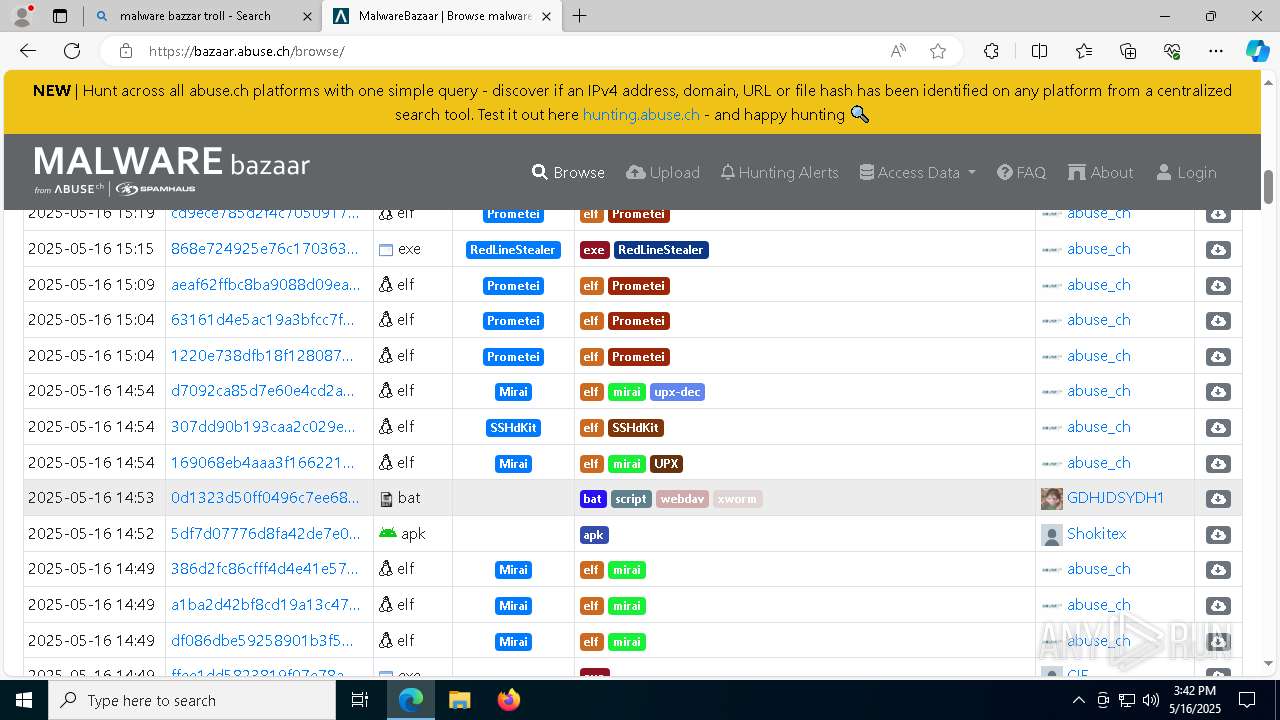
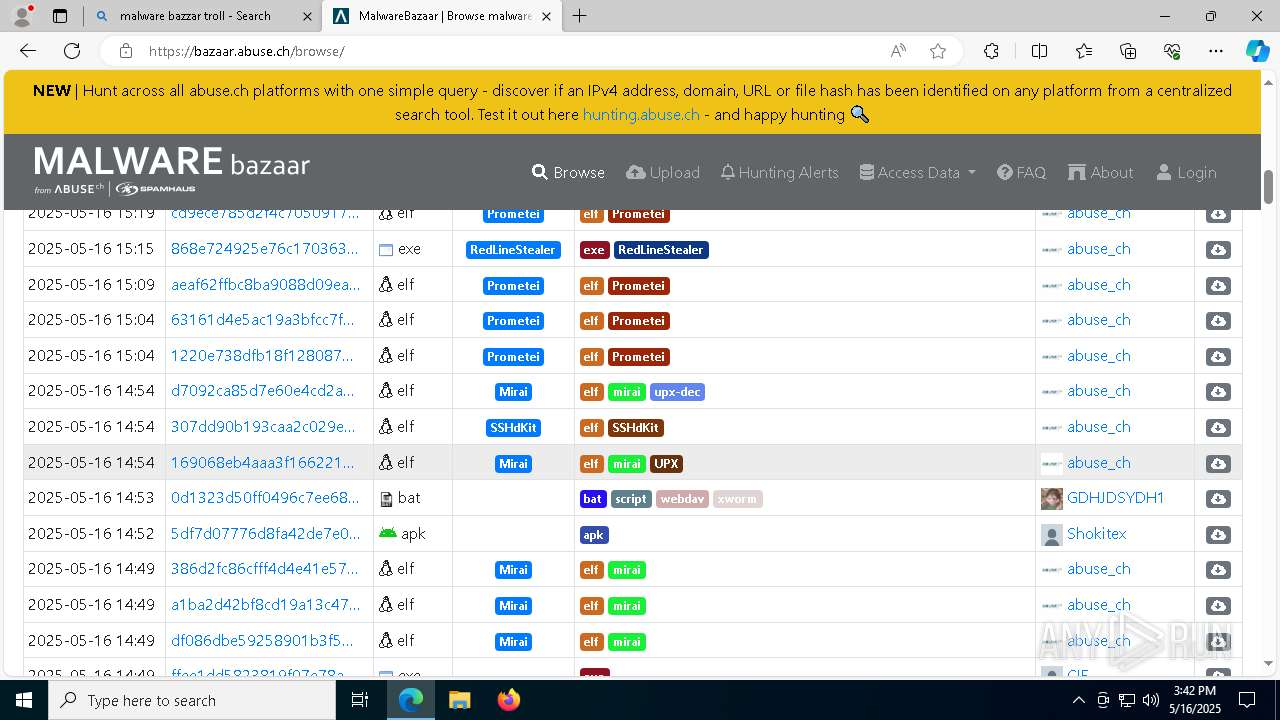
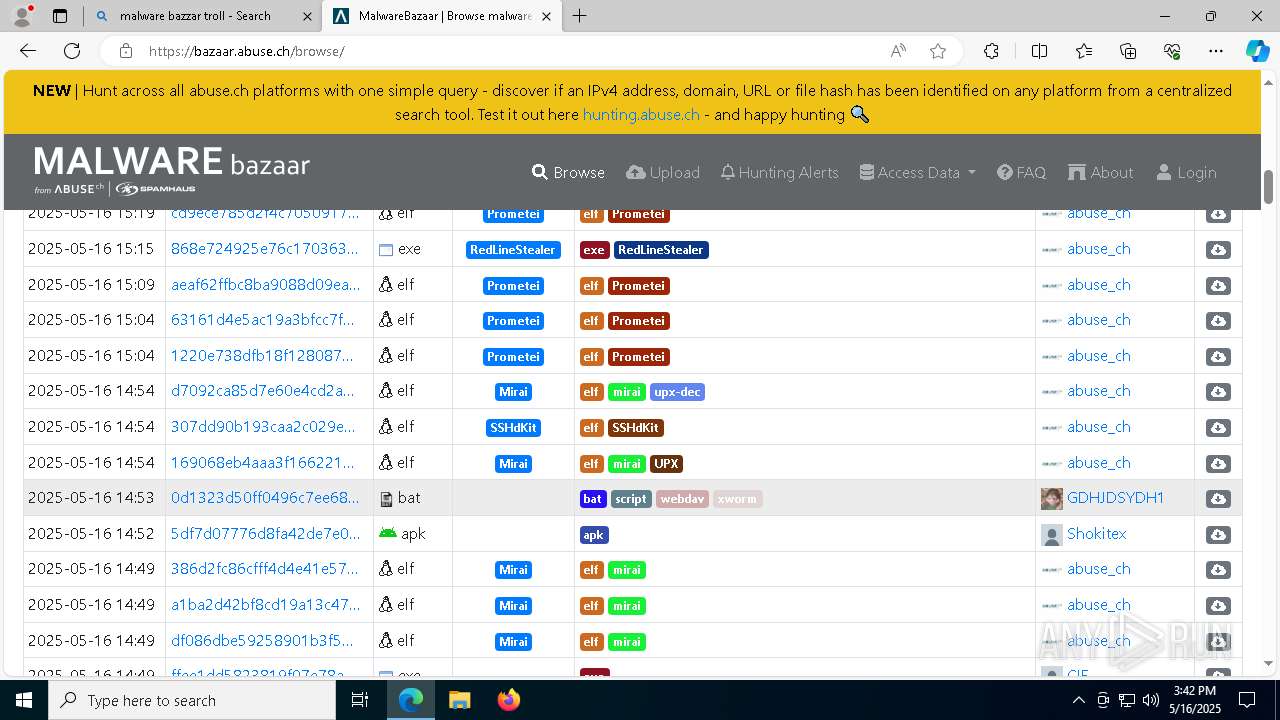
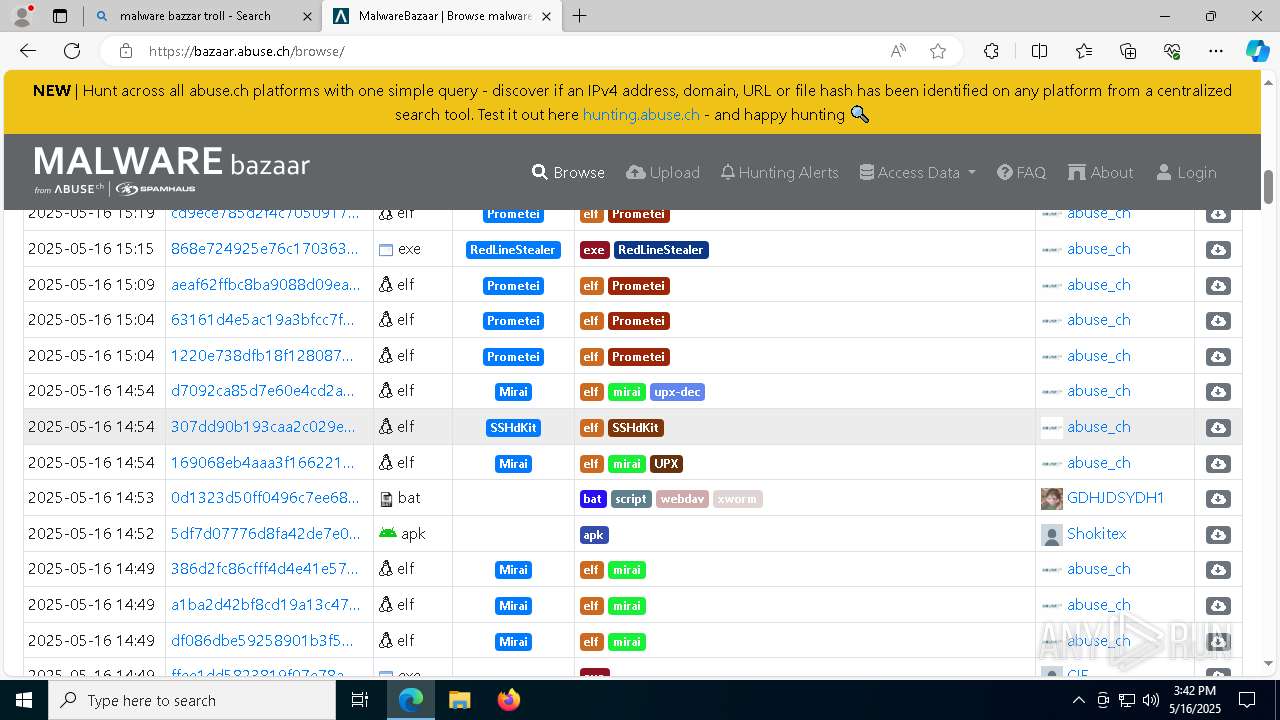
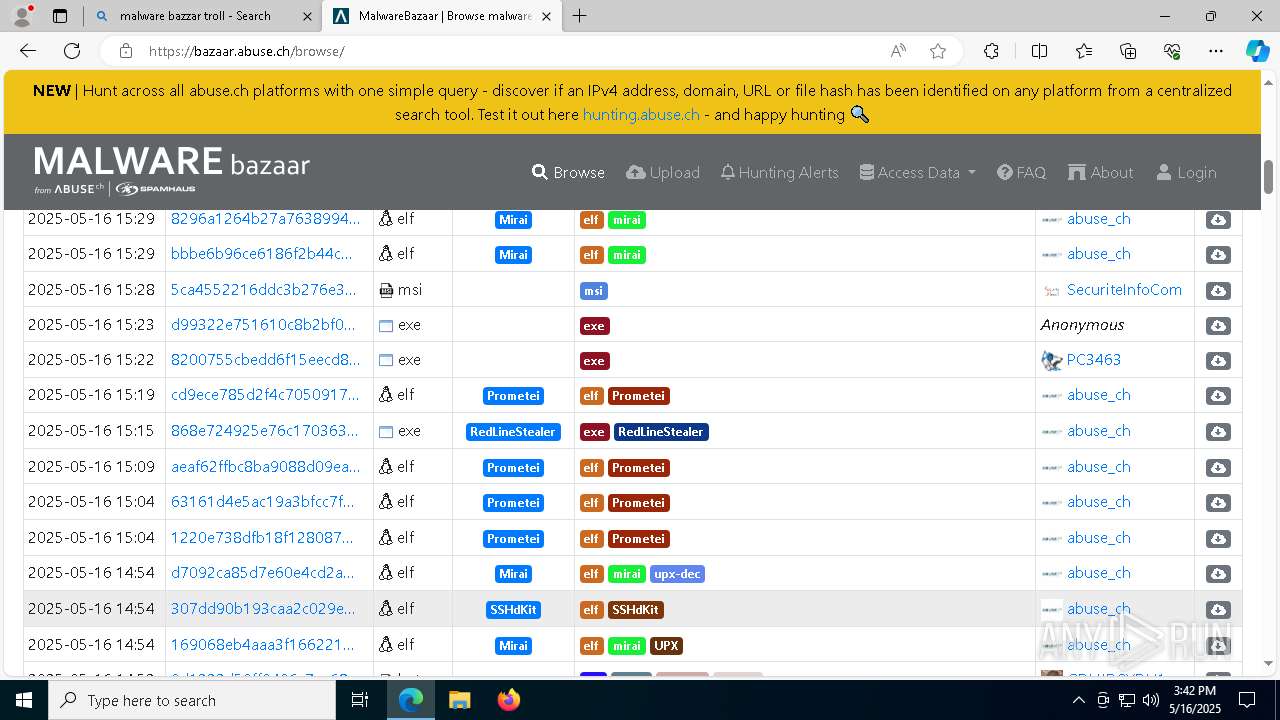
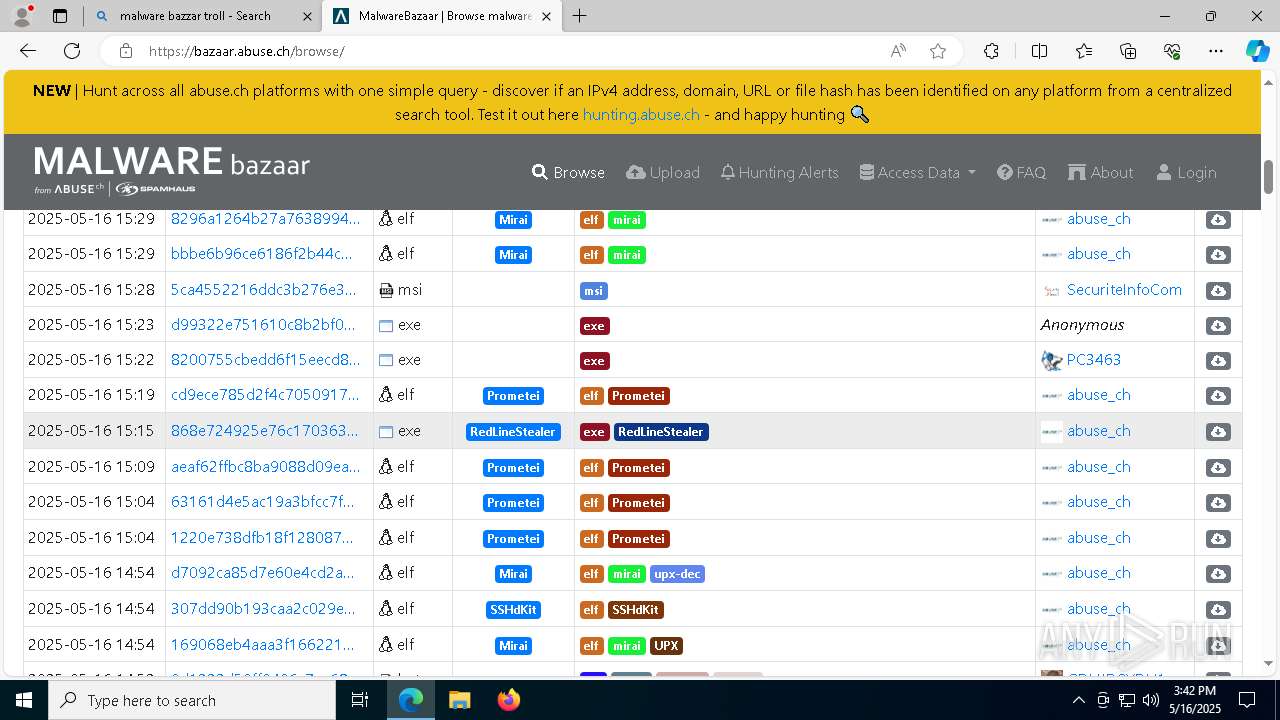
| Title: | MalwareBazaar | Checking your browser |
Total processes
341
Monitored processes
196
Malicious processes
23
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | powercfg /change monitor-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2376 --field-trial-handle=2416,i,9703871103128090224,5833574625988306183,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9408 --field-trial-handle=2300,i,11660474127249787899,11333086169785161928,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=5400 --field-trial-handle=2300,i,11660474127249787899,11333086169785161928,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6048 --field-trial-handle=2300,i,11660474127249787899,11333086169785161928,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --mojo-platform-channel-handle=9516 --field-trial-handle=2300,i,11660474127249787899,11333086169785161928,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
76 602
Read events
76 229
Write events
300
Delete events
73
Modification events
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5116) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (5972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
65
Suspicious files
674
Text files
199
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c0d1.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c0f0.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c0f0.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c0f0.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c100.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
104
TCP/UDP connections
154
DNS requests
326
Threats
240
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1280 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1280 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7792 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
7792 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
7792 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
7792 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
7792 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747697097&P2=404&P3=2&P4=jjl48ozJDOXT5iwADHDjnRx5fOJPFvAHFaX3PaRiltlt8Z5D6FHMr2MhuJrx8NMrpuW4wE0LM1WB%2fh1rMrdNrw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.16:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5972 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7292 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7292 | msedge.exe | 104.19.229.21:443 | js.hcaptcha.com | — | — | whitelisted |
7292 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
js.hcaptcha.com |
| whitelisted |
newassets.hcaptcha.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
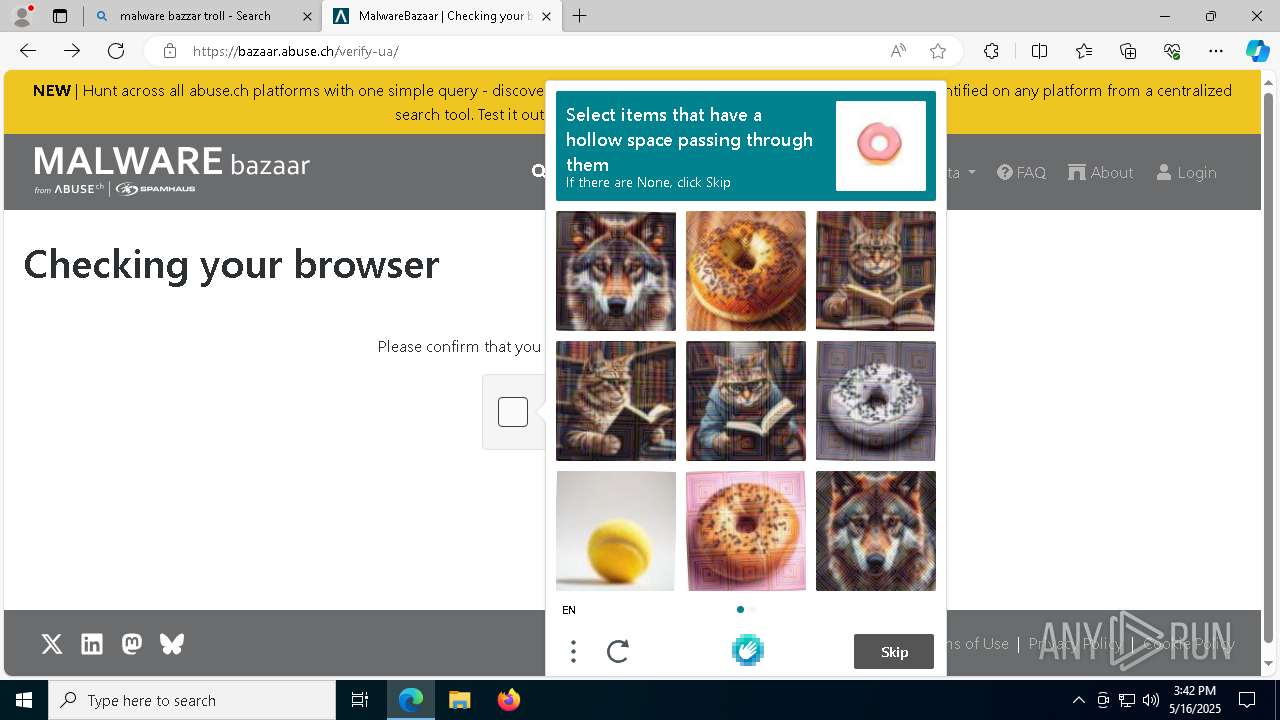
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |