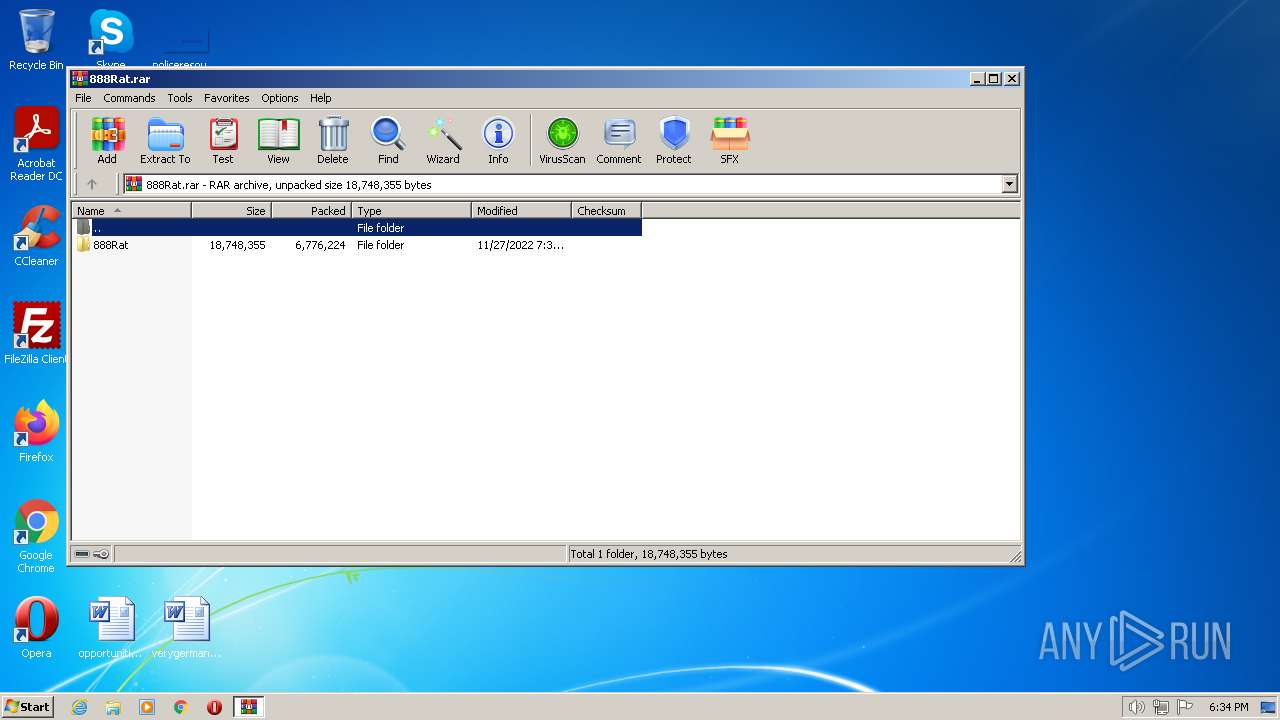
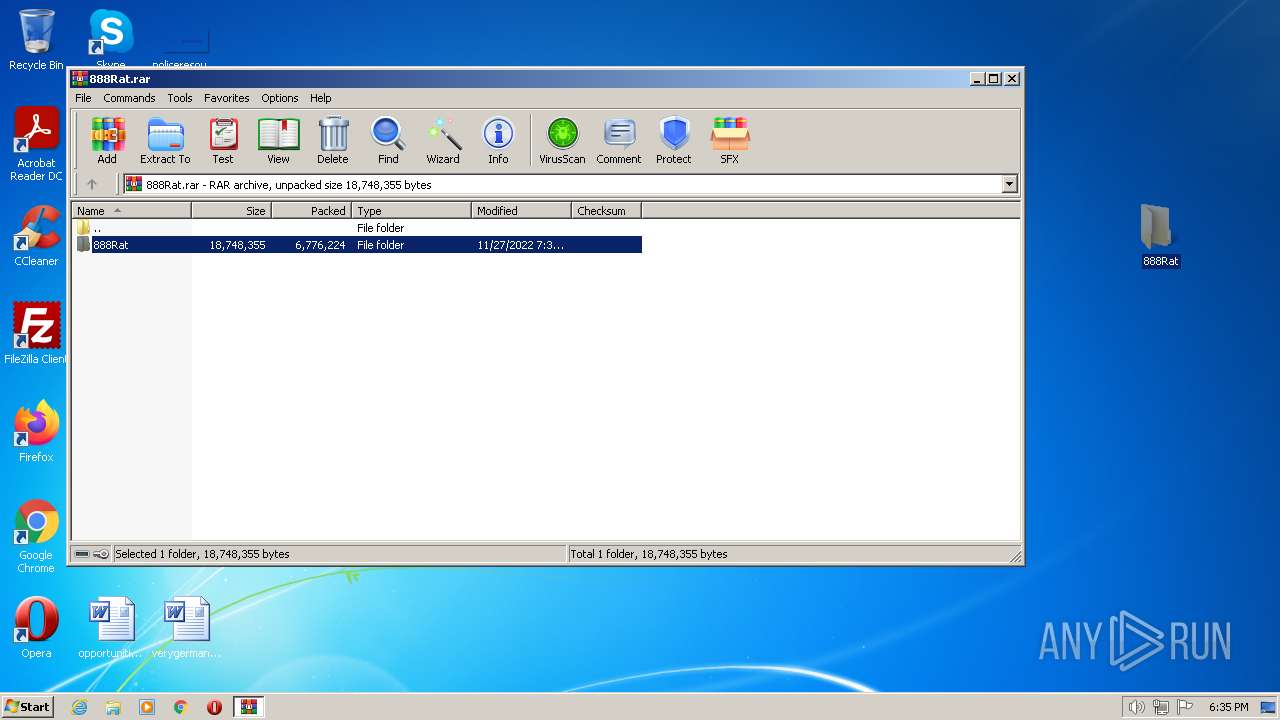
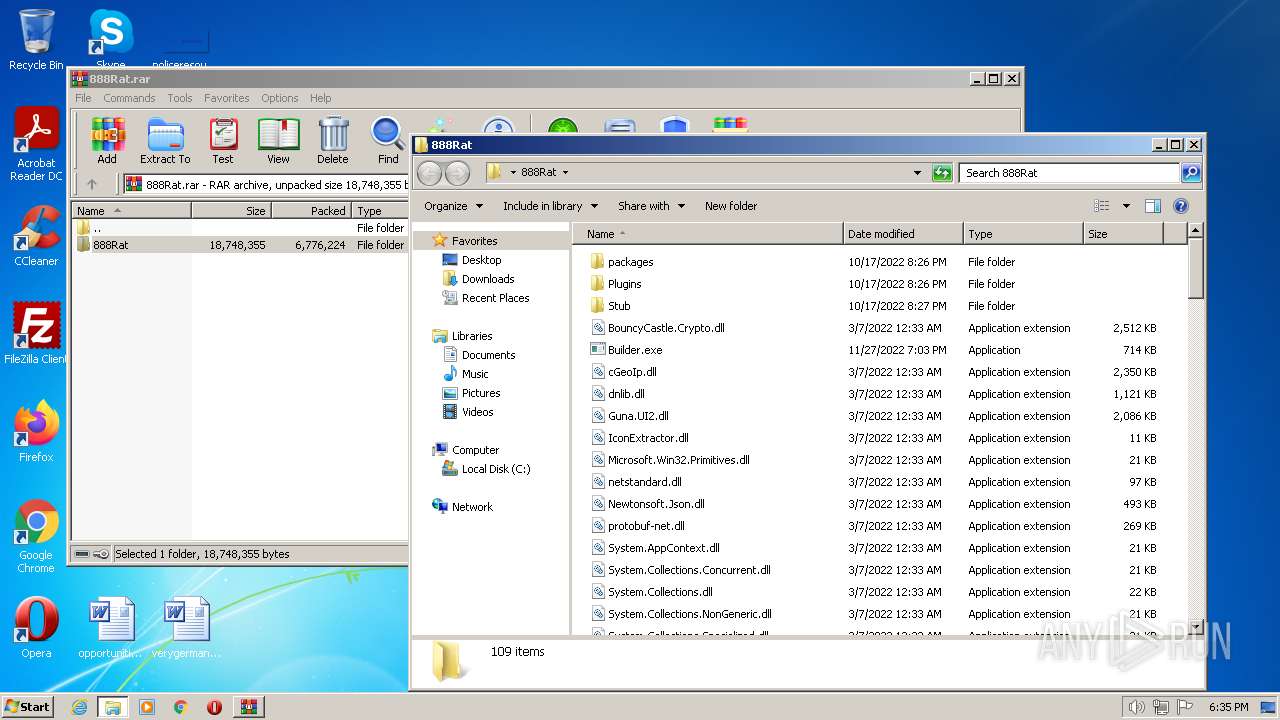
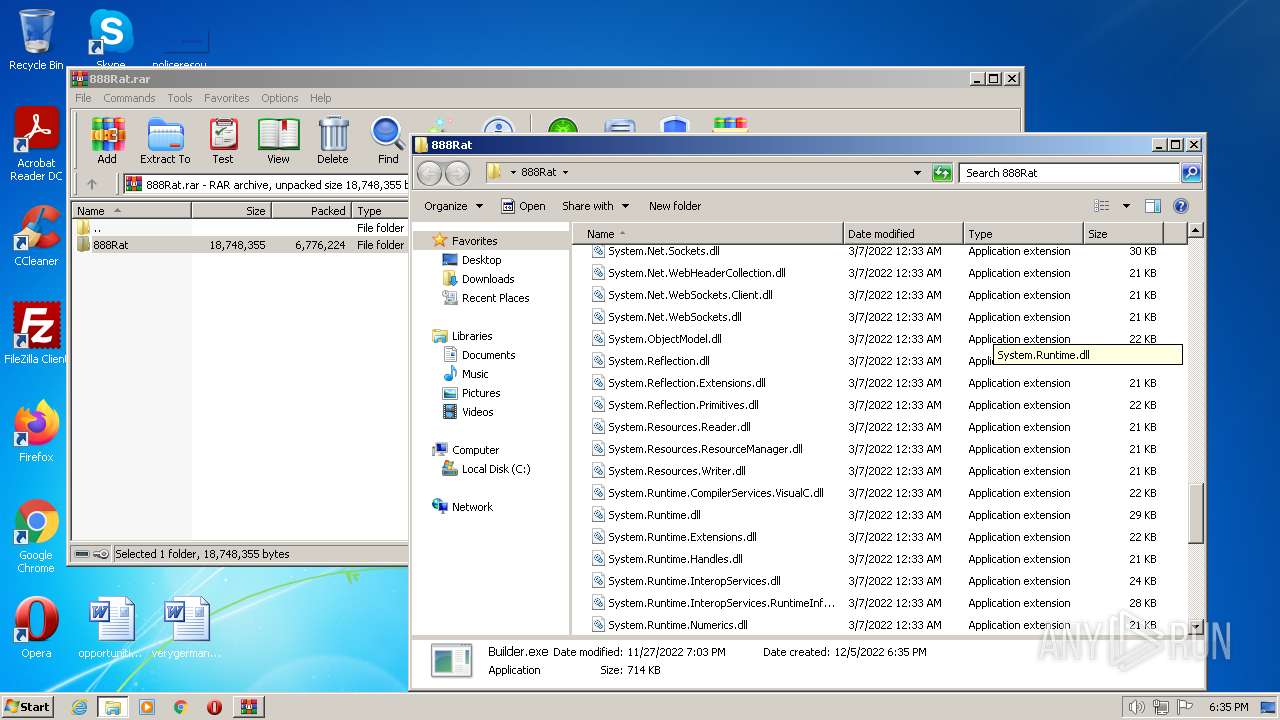
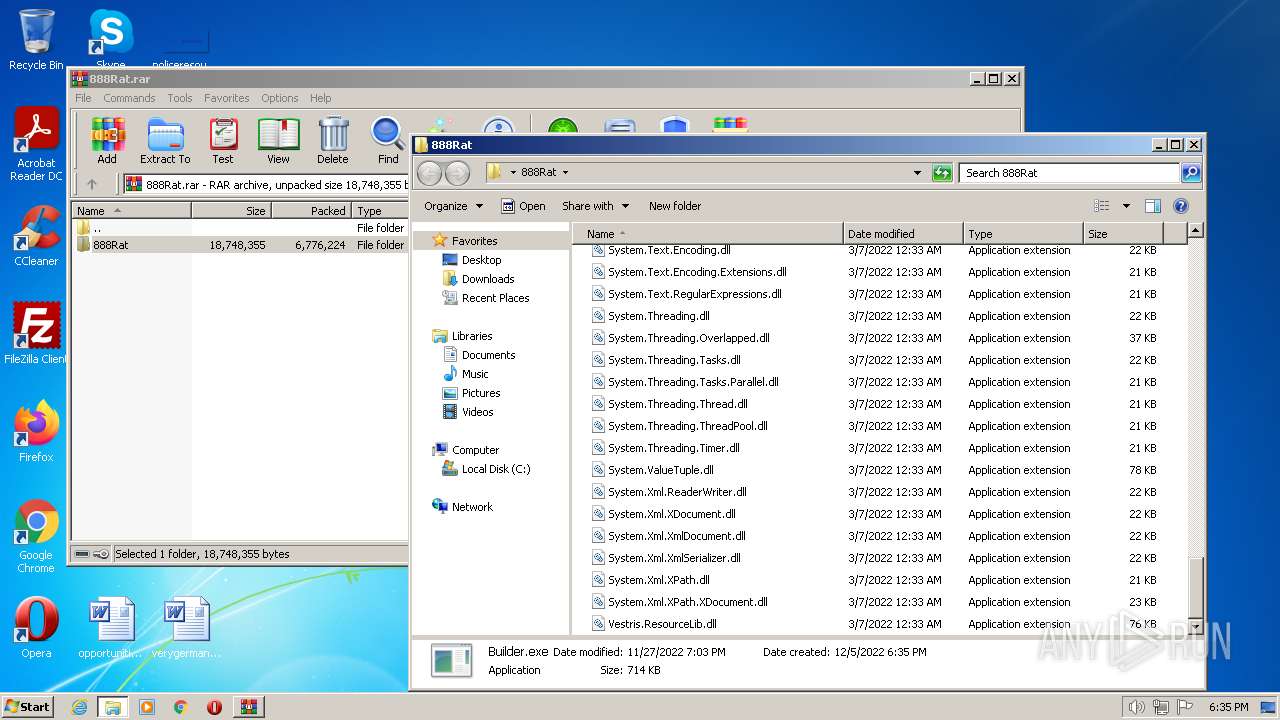
| download: | 888Rat.rar |
| Full analysis: | https://app.any.run/tasks/5fbb8fa8-fc50-4405-b88d-9fe62ff8f01c |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | December 05, 2022, 18:34:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7BB36AB2853723342AC8EFE0E93DFA27 |
| SHA1: | 3D9D42E380791FCDB9AE08A9ED90995FE8213210 |
| SHA256: | 5D7BE86004111956B4060AACD95D7ED2259F6A763EFC68A57D547A857B10794D |
| SSDEEP: | 196608:8+D6hO/ZBzQegRw1FKUmCltRWgrlUae/M2v0WJKdnCql6:8SxBEC1QE4E0M2MEKdCk6 |
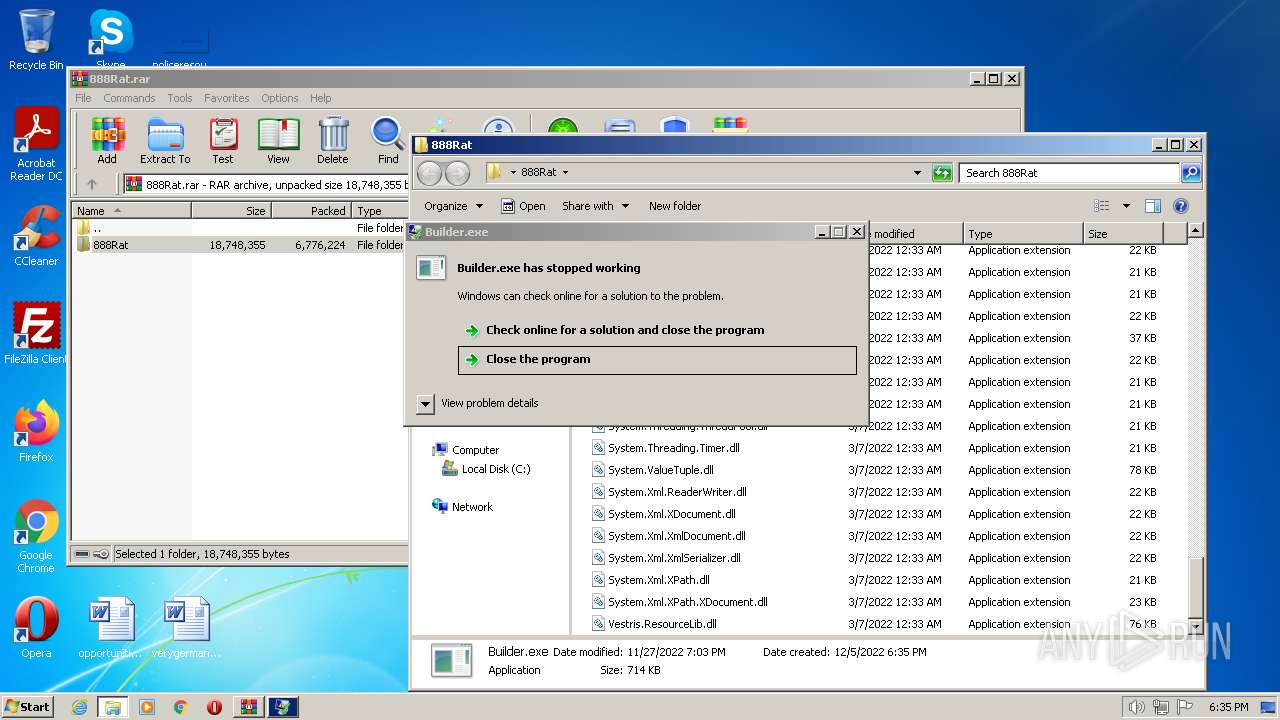
MALICIOUS
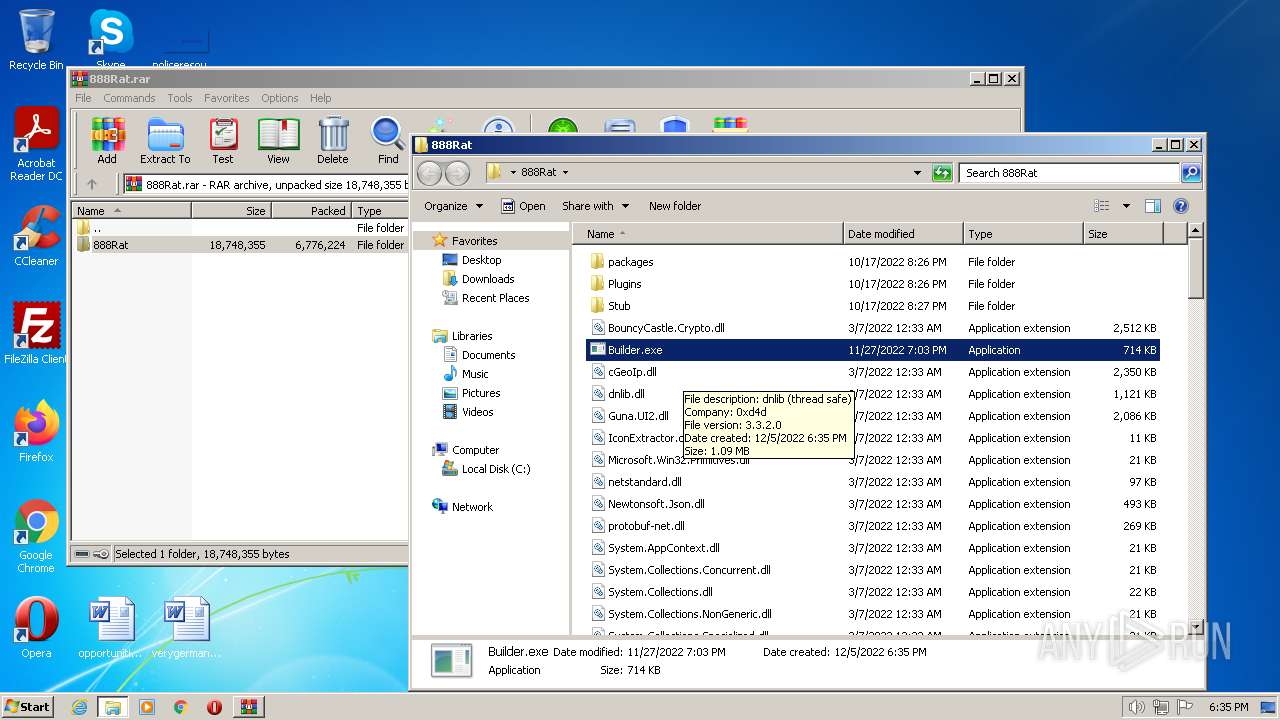
Application was dropped or rewritten from another process
- Builder.exe (PID: 2084)
Loads dropped or rewritten executable
- Explorer.EXE (PID: 1084)
- SearchProtocolHost.exe (PID: 2492)
REDLINE detected by memory dumps
- vbc.exe (PID: 2632)
- Builder.exe (PID: 2084)
SUSPICIOUS
Connects to unusual port
- vbc.exe (PID: 2632)
INFO
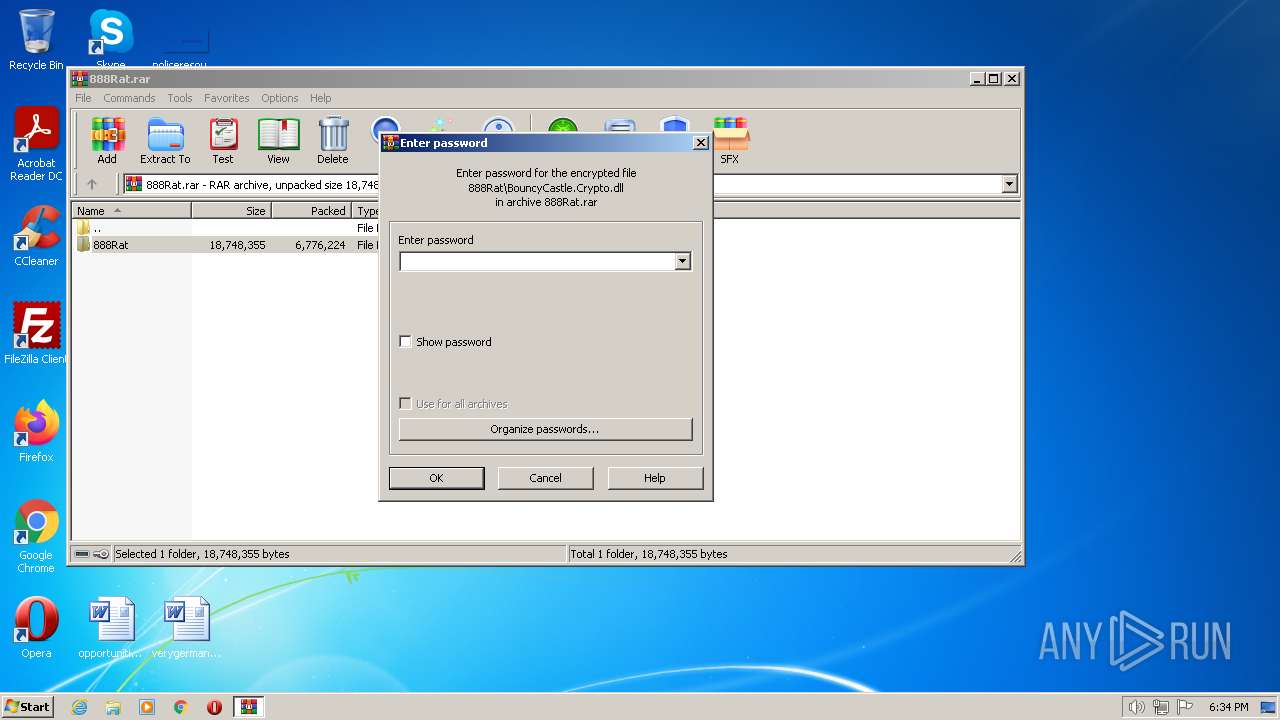
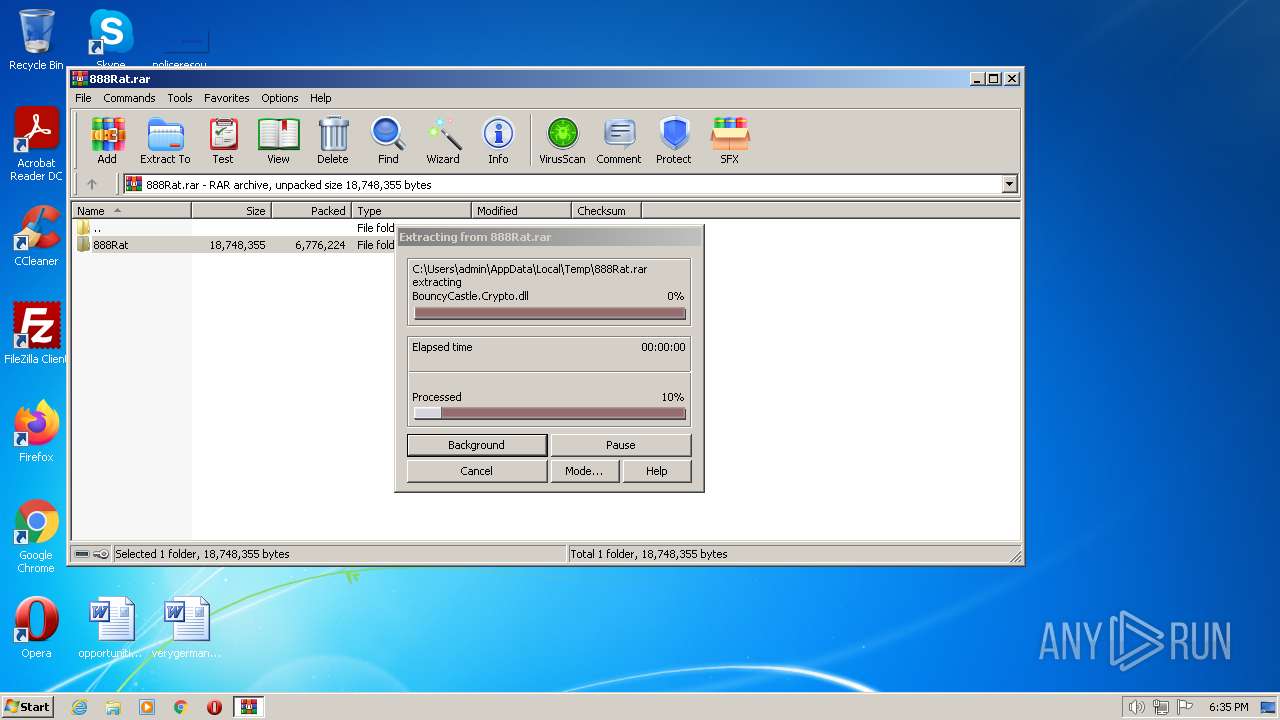
Executable content was dropped or overwritten
- WinRAR.exe (PID: 856)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 856)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2084) Builder.exe
C2 (1)82.115.223.135:2734
Botnet@fondnesssw
Err_msg
Auth_valuee26fd3a6dafd251d055a64ac67f72836
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
GetDirectories
Entity12
EnumerateDirectories
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrhKeyyptDeshKeytroyKhKeyey
hKey
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
e26fd3a6dafd251d055a64ac67f72836
Authorization
ns1
UNKNWON
CikrBzQ7AFwuGDAWCBRWCjQVEFsvGBoVCyxfTw==
@fondnesssw
Embryo
Yandex\YaAddon
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
.
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
1
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
Name
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
System.Text.RegularExpressions
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
The entered value cannot be less than 1 or greater than 20.
#F25D59
Segoe UI
#FFFFFF
#323A3D
Tahoma
#696969
#A0A0A0
−
Marlett
2
#C75050
⨉
#72767F
#FAFAFA
#DE5954
#F46662
#F68F84
#292C3D
#3C3F50
#747881
#2B3043
#7F838C
#AAABB0
Microsoft Sans Serif
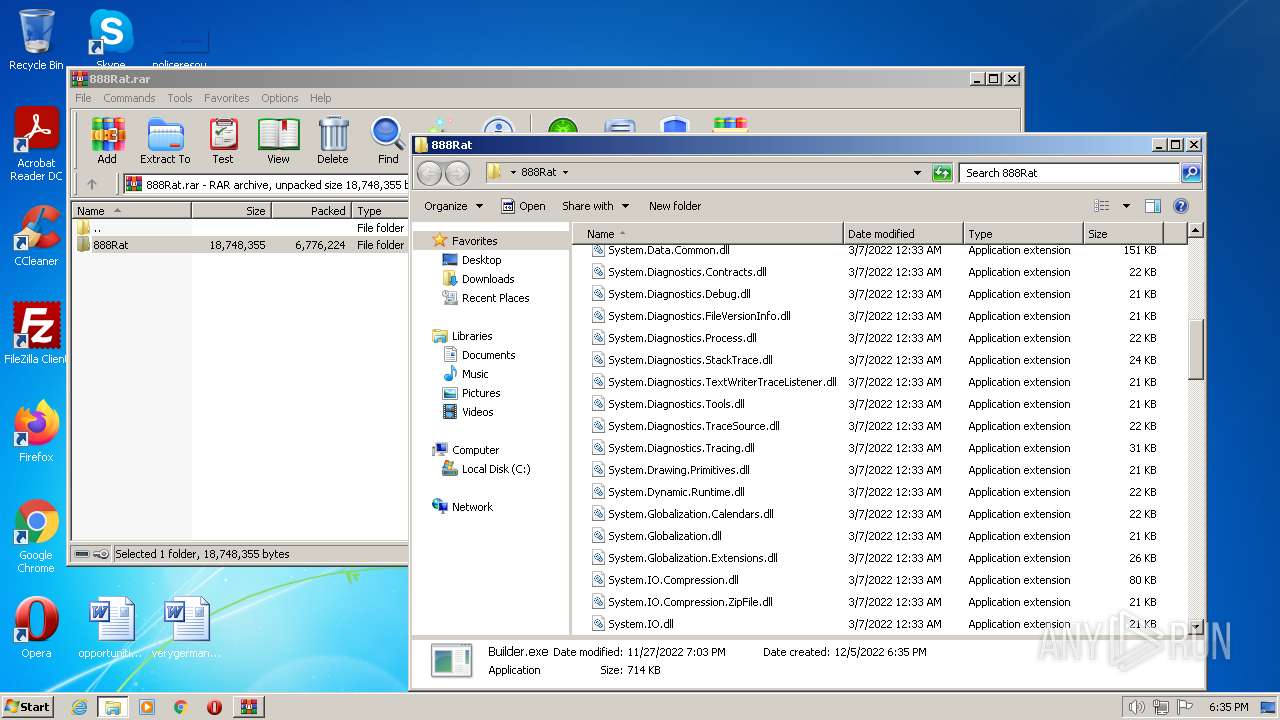
(PID) Process(2632) vbc.exe
C2 (1)82.115.223.135:2734
Botnet@fondnesssw
Err_msg
Auth_valuee26fd3a6dafd251d055a64ac67f72836
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
GetDirectories
Entity12
EnumerateDirectories
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrhKeyyptDeshKeytroyKhKeyey
hKey
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
e26fd3a6dafd251d055a64ac67f72836
Authorization
ns1
UNKNWON
CikrBzQ7AFwuGDAWCBRWCjQVEFsvGBoVCyxfTw==
@fondnesssw
Embryo
Yandex\YaAddon
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
.
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
1
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
Name
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
System.Text.RegularExpressions
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
The entered value cannot be less than 1 or greater than 20.
#F25D59
Segoe UI
#FFFFFF
#323A3D
Tahoma
#696969
#A0A0A0
−
Marlett
2
#C75050
⨉
#72767F
#FAFAFA
#DE5954
#F46662
#F68F84
#292C3D
#3C3F50
#747881
#2B3043
#7F838C
#AAABB0
Microsoft Sans Serif
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\888Rat.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1084 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\Desktop\888Rat\Builder.exe" | C:\Users\admin\Desktop\888Rat\Builder.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
RedLine(PID) Process(2084) Builder.exe C2 (1)82.115.223.135:2734 Botnet@fondnesssw Err_msg Auth_valuee26fd3a6dafd251d055a64ac67f72836 US (183) LEnvironmentogiEnvironmentn DatEnvironmenta Environment WSystem.Texteb DatSystem.Texta System.Text CoCryptographyokieCryptographys Cryptography ExtGenericension CooGenerickies Generic OFileInfopeFileInfora GFileInfoX StabFileInfole FileInfo OpLinqera GLinqX Linq ApGenericpDaGenericta\RGenericoamiGenericng\ Network Extension UNKNOWN cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ Network\ Host Port : User Pass cookies.sqlite GetDirectories Entity12 EnumerateDirectories String.Replace String.Remove bcrFileStream.IOypt.dFileStream.IOll FileStream.IO BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder string.Empty BCruintyptCloseAlgorituinthmProvuintider uint BCrUnmanagedTypeyptDecrUnmanagedTypeypt UnmanagedType BCrhKeyyptDeshKeytroyKhKeyey hKey BCpszPropertyryptGepszPropertytPropepszPropertyrty pszProperty BCEncodingryptSEncodingetPrEncodingoperEncodingty Encoding BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey bMasterKey windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob - {0} net.tcp:// / localhost e26fd3a6dafd251d055a64ac67f72836 Authorization ns1 UNKNWON CikrBzQ7AFwuGDAWCBRWCjQVEFsvGBoVCyxfTw== @fondnesssw Embryo Yandex\YaAddon asf *wallet* ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu... _ T e l gr am . ex \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata 1 String Replace string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections ( UNIQUE cstringmstringd string /ProcessC Process Process | " Armenia Azerbaijan Belarus Kazakhstan Kyrgyzstan Moldova Tajikistan Uzbekistan Ukraine Russia https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM Name SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' System.Text.RegularExpressions ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ The entered value cannot be less than 1 or greater than 20. #F25D59 Segoe UI #FFFFFF #323A3D Tahoma #696969 #A0A0A0 − Marlett 2 #C75050 ⨉ #72767F #FAFAFA #DE5954 #F46662 #F68F84 #292C3D #3C3F50 #747881 #2B3043 #7F838C #AAABB0 Microsoft Sans Serif | |||||||||||||||
| 2492 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2632 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | Builder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 12.0.51209.34209 Modules
RedLine(PID) Process(2632) vbc.exe C2 (1)82.115.223.135:2734 Botnet@fondnesssw Err_msg Auth_valuee26fd3a6dafd251d055a64ac67f72836 US (183) LEnvironmentogiEnvironmentn DatEnvironmenta Environment WSystem.Texteb DatSystem.Texta System.Text CoCryptographyokieCryptographys Cryptography ExtGenericension CooGenerickies Generic OFileInfopeFileInfora GFileInfoX StabFileInfole FileInfo OpLinqera GLinqX Linq ApGenericpDaGenericta\RGenericoamiGenericng\ Network Extension UNKNOWN cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ Network\ Host Port : User Pass cookies.sqlite GetDirectories Entity12 EnumerateDirectories String.Replace String.Remove bcrFileStream.IOypt.dFileStream.IOll FileStream.IO BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder string.Empty BCruintyptCloseAlgorituinthmProvuintider uint BCrUnmanagedTypeyptDecrUnmanagedTypeypt UnmanagedType BCrhKeyyptDeshKeytroyKhKeyey hKey BCpszPropertyryptGepszPropertytPropepszPropertyrty pszProperty BCEncodingryptSEncodingetPrEncodingoperEncodingty Encoding BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey bMasterKey windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob - {0} net.tcp:// / localhost e26fd3a6dafd251d055a64ac67f72836 Authorization ns1 UNKNWON CikrBzQ7AFwuGDAWCBRWCjQVEFsvGBoVCyxfTw== @fondnesssw Embryo Yandex\YaAddon asf *wallet* ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu... _ T e l gr am . ex \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata 1 String Replace string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections ( UNIQUE cstringmstringd string /ProcessC Process Process | " Armenia Azerbaijan Belarus Kazakhstan Kyrgyzstan Moldova Tajikistan Uzbekistan Ukraine Russia https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM Name SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' System.Text.RegularExpressions ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ The entered value cannot be less than 1 or greater than 20. #F25D59 Segoe UI #FFFFFF #323A3D Tahoma #696969 #A0A0A0 − Marlett 2 #C75050 ⨉ #72767F #FAFAFA #DE5954 #F46662 #F68F84 #292C3D #3C3F50 #747881 #2B3043 #7F838C #AAABB0 Microsoft Sans Serif | |||||||||||||||
Total events
4 440
Read events
4 388
Write events
52
Delete events
0
Modification events
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\888Rat.rar | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
135
Suspicious files
1
Text files
5
Unknown types
2
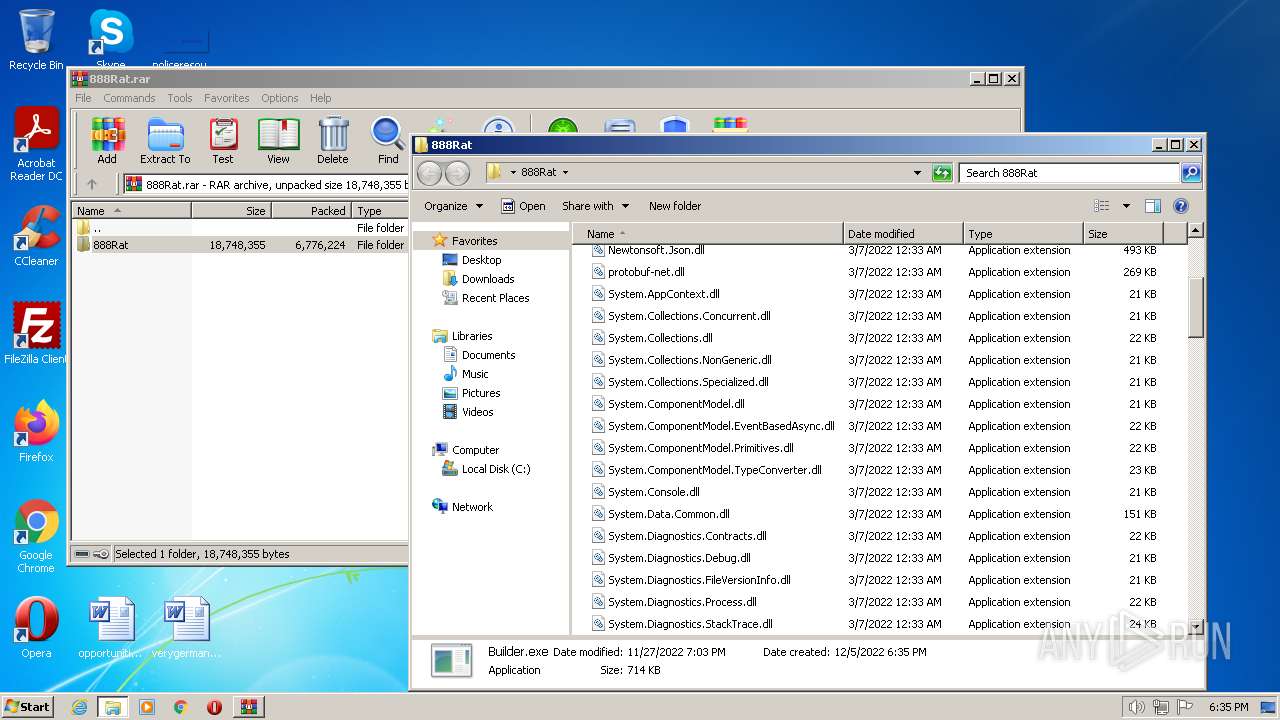
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\Builder.exe | executable | |
MD5:— | SHA256:— | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\packages\Vestris.ResourceLib.2.2.0-beta0004\lib\net40\Vestris.ResourceLib.dll | executable | |
MD5:1D4AC765C46E8474583B3BBEBA088F74 | SHA256:3B3C0BE681D7603CC1C5E3C5F1D8614A582DD82B2465F7F42D79C5AE57F7F642 | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\packages\Vestris.ResourceLib.2.2.0-beta0004\lib\net20\Vestris.ResourceLib.dll | executable | |
MD5:2E565B9ECC88100E5815D3FEC51311A1 | SHA256:6861251DF743827AAD59AF9DBC68B4F43B191C2A0857D222D28A82A9E3AA944A | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\IconExtractor.dll | executable | |
MD5:7BCF61E29E5CBCD1B81D9AB72CBFED93 | SHA256:2C359CE857982F45B09AF49DBCCFB2AE302839ACF1956E8325E7F854B339A8C9 | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\dnlib.dll | executable | |
MD5:4D0B771879DE85137EE7E5F0D4BB4B16 | SHA256:962332E8C8CB459FB2F7DACEC5D7A618CC53B1B49BC1740156398C89742F43FD | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\packages\Vestris.ResourceLib.2.2.0-beta0004\.signature.p7s | der | |
MD5:008690EFA5DCB142F17BF7F97461DF25 | SHA256:96070F8DC2B0FF9BF0D4AE6B78FBA4576CA91EB463EC82587BF2A7D933607104 | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\Microsoft.Win32.Primitives.dll | executable | |
MD5:76B8D417C2F6416FA81EACC45977CEA2 | SHA256:5EAA2E82A26B0B302280D08F54DC9DA25165DD0E286BE52440A271285D63F695 | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\netstandard.dll | executable | |
MD5:0ADF6F32F4D14F9B0BE9AA94F7EFB279 | SHA256:8BE4A2270F8B2BEA40F33F79869FDCCA34E07BB764E63B81DED49D90D2B720DD | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\packages\Vestris.ResourceLib.2.2.0-beta0004\lib\net35\Vestris.ResourceLib.dll | executable | |
MD5:4AA661EFCBAE2AEA7050ADBEEC022D46 | SHA256:21E08E7CF51FBE7952F8CF88B924947FD12B01B1CE3405CE2BF6914479F72FC9 | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb856.27050\888Rat\packages\Vestris.ResourceLib.2.2.0-beta0004\lib\net20\Vestris.ResourceLib.xml | xml | |
MD5:5D2DEE455B4003B6624B6DD890EDB279 | SHA256:02B4FD6D46FFC9411E4688A5B088FBC7D34062024E1C93637535E093319C35B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | vbc.exe | 82.115.223.135:2734 | — | Partner LLC | RU | malicious |