| File name: | ESFXCreator.exe |
| Full analysis: | https://app.any.run/tasks/84b246a2-17a5-4b62-98d2-531c9348bc11 |
| Verdict: | Malicious activity |
| Threats: | First identified in 2024, Emmenhtal operates by embedding itself within modified legitimate Windows binaries, often using HTA (HTML Application) files to execute malicious scripts. It has been linked to the distribution of malware such as CryptBot and Lumma Stealer. Emmenhtal is typically disseminated through phishing campaigns, including fake video downloads and deceptive email attachments. |
| Analysis date: | August 01, 2025, 02:54:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | DA17623F70DA83A98F7ECF8390550EA4 |
| SHA1: | D0C91542AE48EC2E02E669A85006F9831F62600E |
| SHA256: | 5D6284D388386800AC17C2BD04C5F62E8B33577AC02E8C5E5A51D260640A50C9 |
| SSDEEP: | 12288:SaSk5uceHAmCMoJ7s+hESUaSk5uceHAmlMoJ7snlu:ok5uceHAr6k5uceHAllu |
MALICIOUS
EMMENHTAL has been detected (YARA)
- mshta.exe (PID: 2596)
SUSPICIOUS
Reads security settings of Internet Explorer
- ESFXCreator.exe (PID: 2976)
There is functionality for taking screenshot (YARA)
- ESFXCreator.exe (PID: 2976)
Executes application which crashes
- mshta.exe (PID: 2596)
INFO
Checks supported languages
- ESFXCreator.exe (PID: 2976)
Create files in a temporary directory
- ESFXCreator.exe (PID: 2976)
Reads the computer name
- ESFXCreator.exe (PID: 2976)
Reads Internet Explorer settings
- mshta.exe (PID: 2596)
Checks proxy server information
- mshta.exe (PID: 2596)
- WerFault.exe (PID: 6748)
Reads security settings of Internet Explorer
- WerFault.exe (PID: 6748)
Process checks computer location settings
- ESFXCreator.exe (PID: 2976)
Creates files or folders in the user directory
- WerFault.exe (PID: 6748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 00:38:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 89600 |
| InitializedDataSize: | 467968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1638f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.0.2712 |
| ProductVersionNumber: | 1.6.0.2712 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Djengineer14 |
| FileDescription: | Create SFX/Exe Files |
| FileVersion: | 1.6.0.2712 |
| InternalName: | 7ZSfxMod |
| LegalCopyright: | Copyright © 2005-2012 Oleg N. Scherbakov |
| OriginalFileName: | 7ZSfxMod_x86.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 7-Zip SFX |
| ProductVersion: | 1.6.0.2712 |
Total processes
138
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
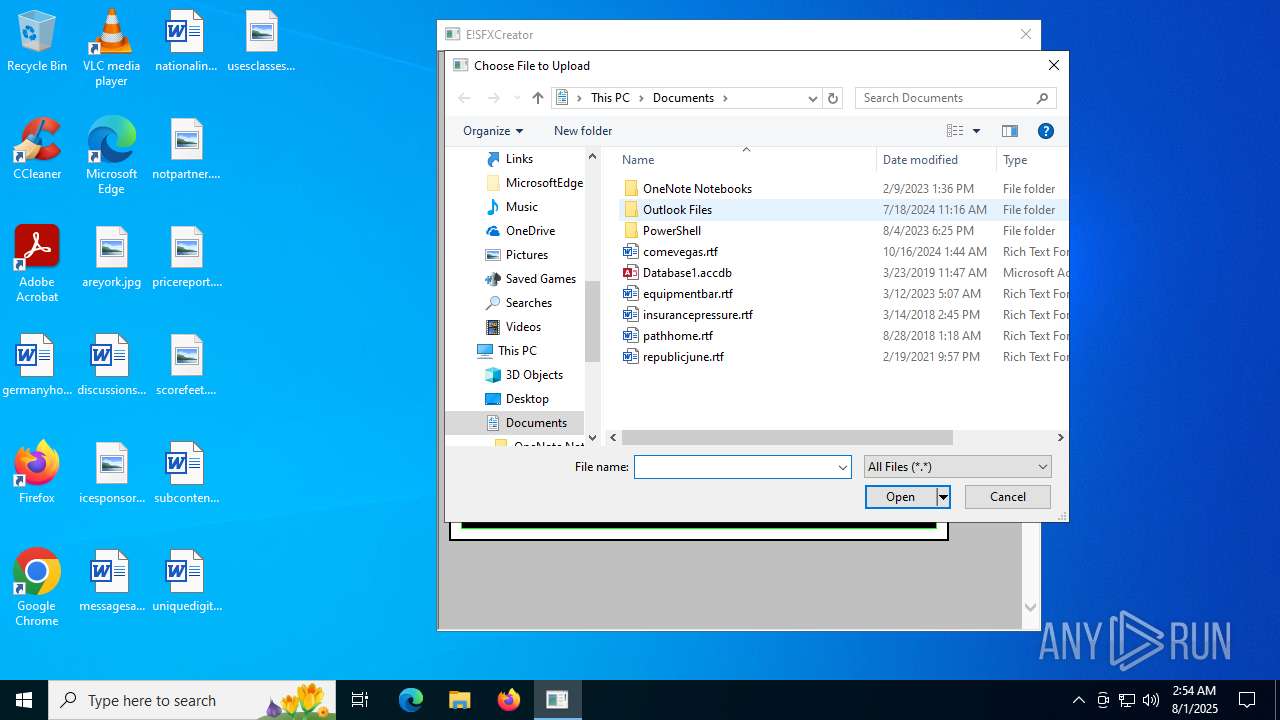
| 2596 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ESFXCreator.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | ESFXCreator.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
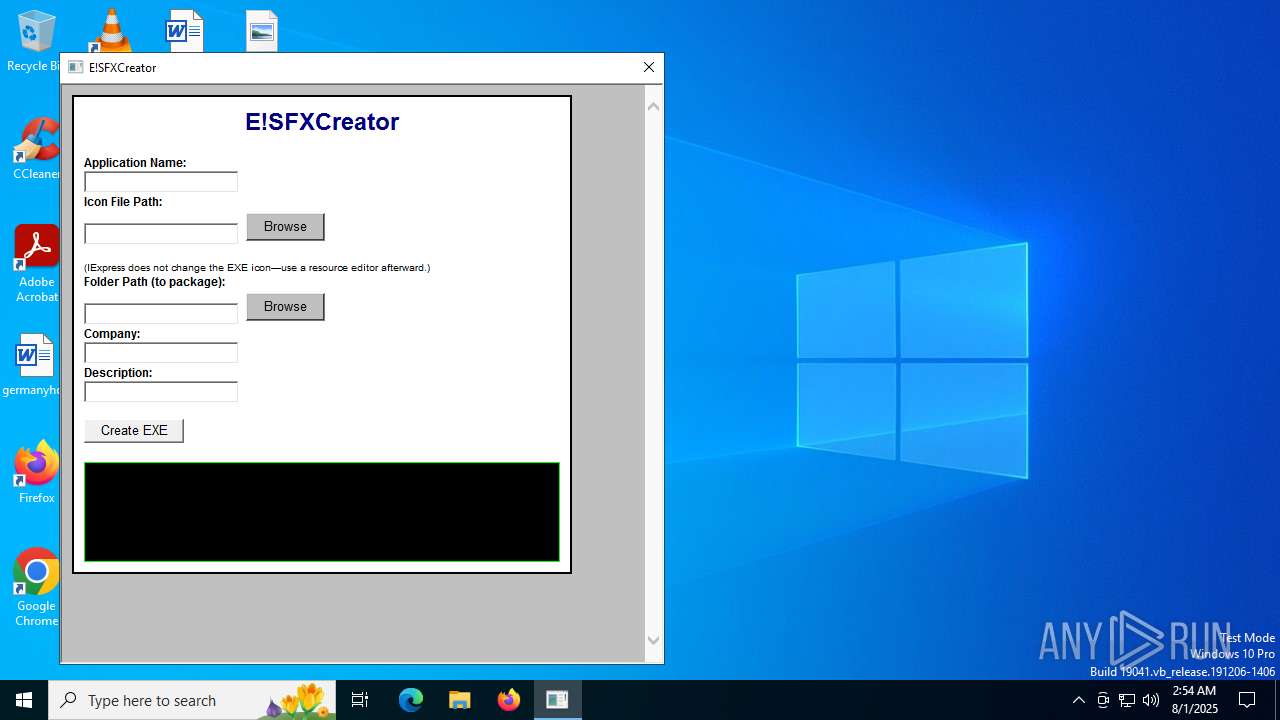
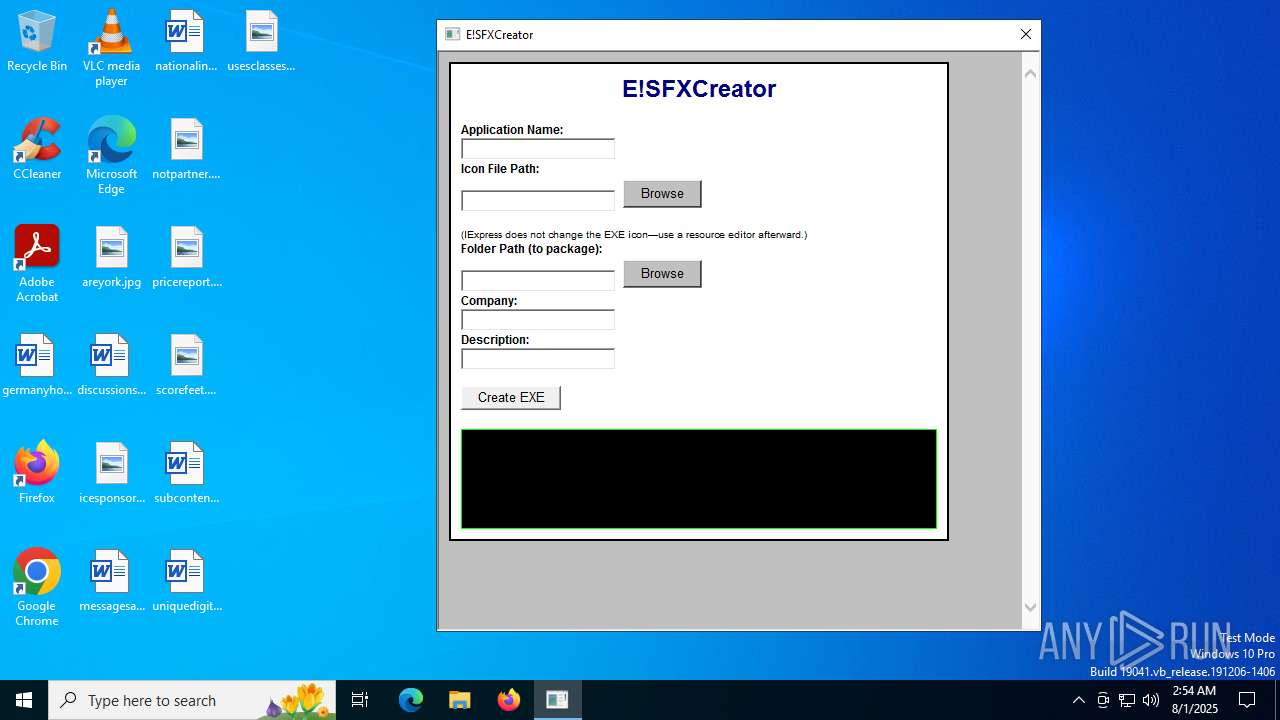
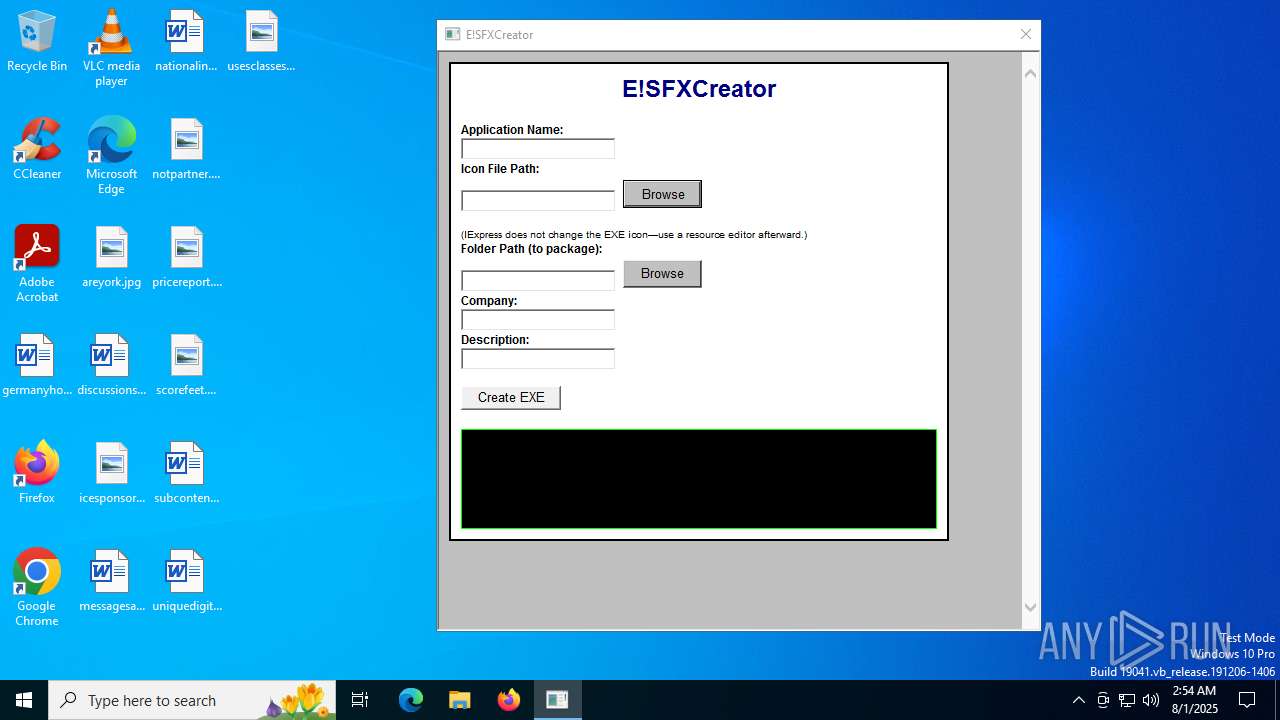
| 2976 | "C:\Users\admin\AppData\Local\Temp\ESFXCreator.exe" | C:\Users\admin\AppData\Local\Temp\ESFXCreator.exe | — | explorer.exe | |||||||||||
User: admin Company: Djengineer14 Integrity Level: MEDIUM Description: Create SFX/Exe Files Exit code: 0 Version: 1.6.0.2712 Modules
| |||||||||||||||
| 6748 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2596 -s 4608 | C:\Windows\SysWOW64\WerFault.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 252
Read events
10 071
Write events
172
Delete events
9
Modification events
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) ESFXCreator.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.hta\OpenWithProgids |
| Operation: | write | Name: | htafile |
Value: | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000050000000200000001000000FFFFFFFF | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 121 | |||
| (PID) Process: | (2596) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 642C8C6800000000 | |||
Executable files
0
Suspicious files
3
Text files
4
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6748 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_mshta.exe_1456b662b7911e7956fd7245c3cbee08940652_07a62b6c_32a4ce51-9b51-4b2e-a857-73c3aeff1cb7\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | der | |
MD5:F2A7A6D8C2D143C4E63CAD20647AC166 | SHA256:DA2ACF6F9CA54051CEFD0C6DE9D83AF5C717522BE8209BF9D319D2D821736538 | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\tumblr_ce50029b59099bbd35ee97380a74210f_7feb2f0e_540[1].png | image | |
MD5:846200917511DB5E257EEE5A951B89F8 | SHA256:53A8CECC35F40854DFBE687C5B74A20F121AD6D63B78116F2CCCD656FFD0EDE6 | |||
| 6748 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER93F.tmp.xml | xml | |
MD5:9D258393CC0ECB241C8E89D5B43A340D | SHA256:81CE35EA910937BF0E1623CA2287AB3A1D0E9C24C438F1C2FBF5E94FAE6D2820 | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4A0E35806347FEC05C6A09191AE5B7A2 | der | |
MD5:A9AA9E3A151E7CF9A86C99A3177CCAC1 | SHA256:C724A29260D1A37812C71B6C2508A4932C9D722E44CF614F0A7CE427B70E183D | |||
| 6748 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8F0.tmp.WERInternalMetadata.xml | xml | |
MD5:45F0E6A00063DA6DACA04C95DA5C8FAC | SHA256:D0C76E63F22E00B9C51D2B7787ABB356B856AEDCE7653DF025100A9445EB386A | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:42077132515F6812792EF9198E7FB55A | SHA256:70913BD0639E552CAFD7A30130E75D885050632978678C50169E63C90C750694 | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | der | |
MD5:0D6B2F6550791138E2C93EADAC4C5CC2 | SHA256:65A9A277F4D1C3FFE6BBD1DBF9CCD2A999981E6E8B28AABC682DD5361365245A | |||
| 2976 | ESFXCreator.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ESFXCreator.hta | html | |
MD5:1516B1A94E1D66E3BC4035D119EABD49 | SHA256:BA895A4FB0B9637CFED510E8EFCED88D20DFB486E2858C5C98E8D5E6A5BA6D73 | |||
| 2596 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:F9BA829389EF4401FB178464B485FA71 | SHA256:2D277CB5ABFBB900B609D8181163E5AABB40503DDD77AAACC052D8C3B086A810 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2596 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
2596 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
2596 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCRtIGhqxv2nGcM1oL8kmb%2F | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5032 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2596 | mshta.exe | 192.0.77.3:443 | 64.media.tumblr.com | AUTOMATTIC | US | whitelisted |
2596 | mshta.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
2596 | mshta.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2064 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2064 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
64.media.tumblr.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |