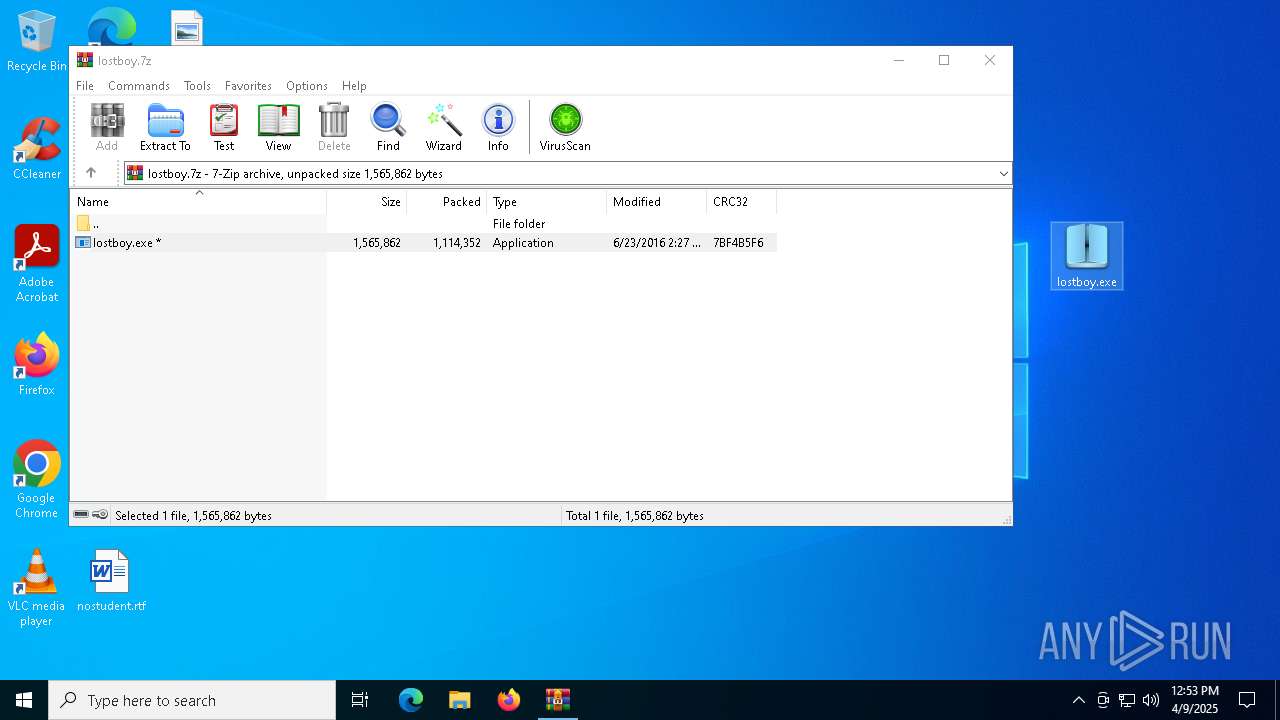
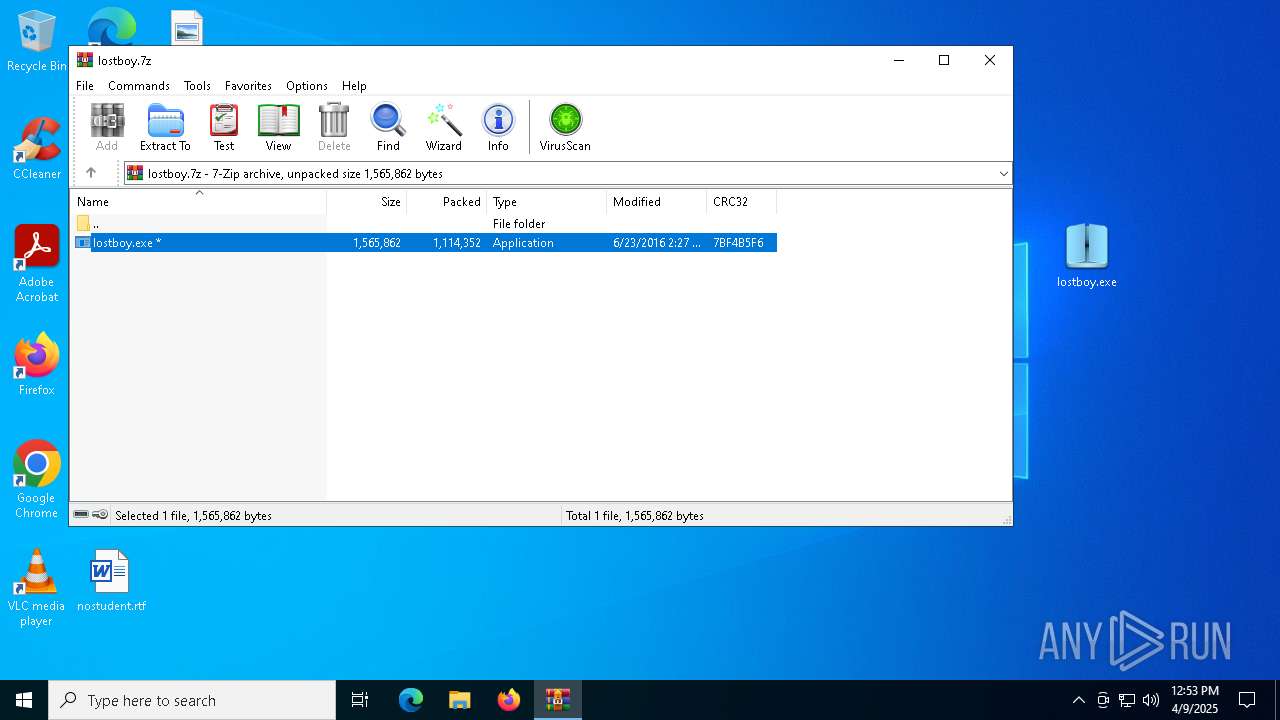
| File name: | lostboy.7z |
| Full analysis: | https://app.any.run/tasks/1ea74073-9164-434d-9e7c-24afda9e9762 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | April 09, 2025, 12:53:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
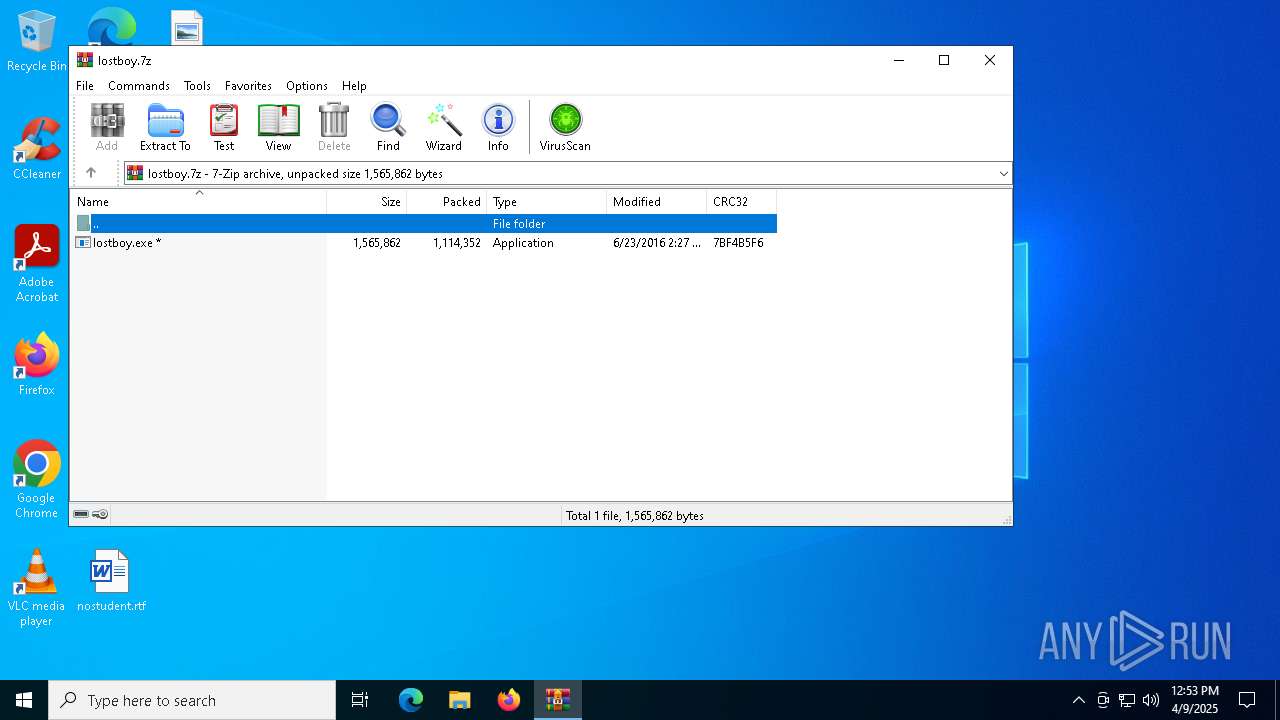
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | E580AFFFA8087DE328DAAFCADE244307 |
| SHA1: | 6001981457923AE070268ECA21268B9A7F2ECD87 |
| SHA256: | 5D578C61B65C04DD57B46CAF1FDC84943B925F4D9EB90303102CA10A00EB127E |
| SSDEEP: | 49152:Ldqz1wqoXVBv98wEuqa6BNgBtiri5jYBPbc0cplGpGygt7Q8NbYo8NgQIhE2Hn6C:vqoF998wDqTTqi2NJEgt7Q8NbYAlh1HV |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2152)
Changes the autorun value in the registry
- lostboy.exe (PID: 2616)
- msdcsc.exe (PID: 3132)
- lostboy.exe (PID: 1312)
- msdcsc.exe (PID: 4844)
DARKCOMET mutex has been found
- notepad.exe (PID: 1388)
- msdcsc.exe (PID: 4844)
SUSPICIOUS
Application launched itself
- lostboy.exe (PID: 2616)
- msdcsc.exe (PID: 3132)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6944)
- cmd.exe (PID: 4776)
Starts itself from another location
- lostboy.exe (PID: 1312)
Executable content was dropped or overwritten
- lostboy.exe (PID: 1312)
Starts CMD.EXE for commands execution
- lostboy.exe (PID: 1312)
Reads security settings of Internet Explorer
- lostboy.exe (PID: 1312)
Start notepad (likely ransomware note)
- msdcsc.exe (PID: 4844)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2152)
- lostboy.exe (PID: 1312)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2152)
Reads mouse settings
- lostboy.exe (PID: 2616)
- msdcsc.exe (PID: 3132)
Create files in a temporary directory
- lostboy.exe (PID: 2616)
- lostboy.exe (PID: 1312)
- msdcsc.exe (PID: 3132)
Checks supported languages
- lostboy.exe (PID: 2616)
- lostboy.exe (PID: 1312)
- msdcsc.exe (PID: 3132)
- msdcsc.exe (PID: 4844)
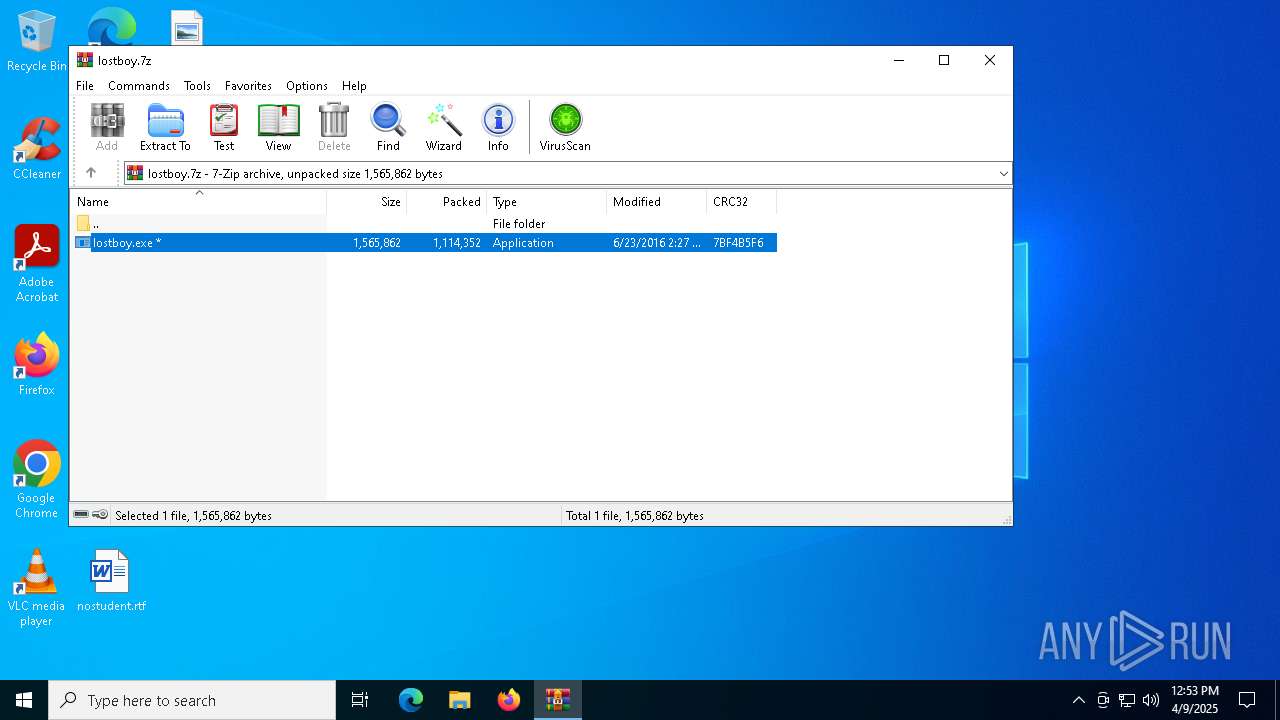
Manual execution by a user
- lostboy.exe (PID: 2616)
Creates files or folders in the user directory
- lostboy.exe (PID: 2616)
- msdcsc.exe (PID: 3132)
Reads the machine GUID from the registry
- lostboy.exe (PID: 2616)
- msdcsc.exe (PID: 3132)
Reads the computer name
- lostboy.exe (PID: 1312)
- msdcsc.exe (PID: 4844)
Process checks computer location settings
- lostboy.exe (PID: 1312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2016:06:23 14:27:45+00:00 |
| ArchivedFileName: | lostboy.exe |
Total processes
141
Monitored processes
15
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | C:\WINDOWS\SysWOW64\notepad.exe | C:\Users\admin\Desktop\lostboy.exe | lostboy.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | notepad | C:\Windows\SysWOW64\notepad.exe | msdcsc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\lostboy.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\Desktop\lostboy.exe" | C:\Users\admin\Desktop\lostboy.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe" | C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | lostboy.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 4200 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 142
Read events
2 131
Write events
11
Delete events
0
Modification events
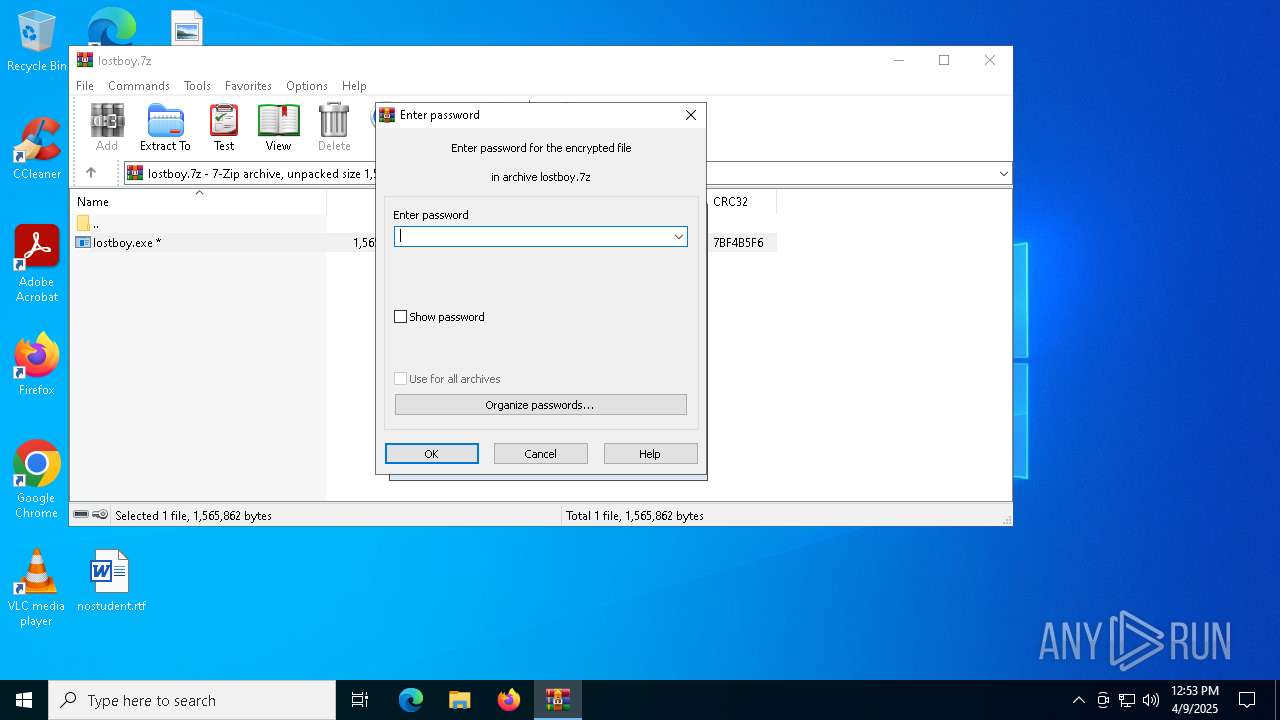
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2616) lostboy.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | lostboy.exe |
Value: C:\Users\admin\Desktop\lostboy.exe | |||
| (PID) Process: | (1312) lostboy.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (1312) lostboy.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A7803901000060B81DB4E48ED2119906E49FADC173CA7D000000 | |||
| (PID) Process: | (3132) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | msdcsc.exe |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (4844) msdcsc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
Executable files
2
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | lostboy.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2152.228\lostboy.exe | executable | |
MD5:F5B12F5F6625413BB87C228282C53F9B | SHA256:3891281145B998066D1C906CDB0DB4C2185257DEC45F459F17D4AFCBA17A50C9 | |||
| 3132 | msdcsc.exe | C:\Users\admin\AppData\Local\Temp\autFB0B.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 1312 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | executable | |
MD5:F5B12F5F6625413BB87C228282C53F9B | SHA256:3891281145B998066D1C906CDB0DB4C2185257DEC45F459F17D4AFCBA17A50C9 | |||
| 2616 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\autDB8D.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3132 | msdcsc.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6080 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6080 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6080 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6080 | SIHClient.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ajensen.no-ip.biz |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a Suspicious no-ip Domain |