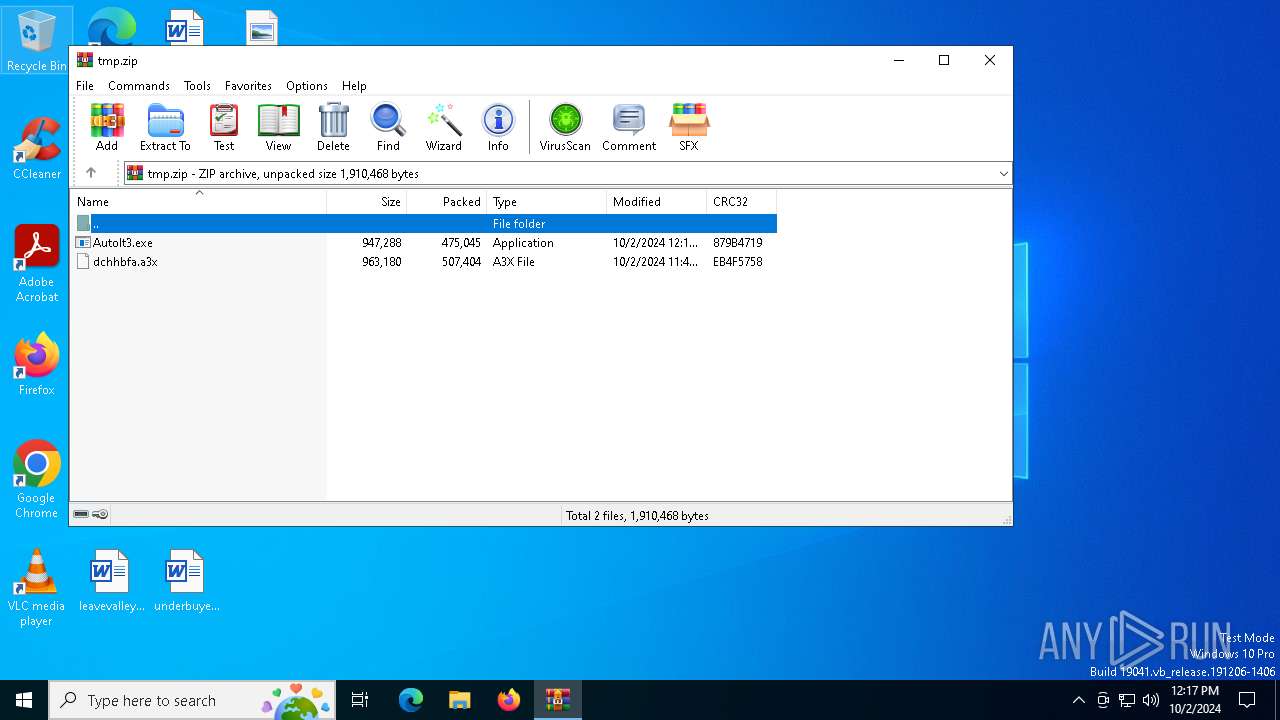
| File name: | tmp.zip |
| Full analysis: | https://app.any.run/tasks/5830aacd-6ee7-4b4e-8a35-5c20998791d7 |
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | October 02, 2024, 12:17:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
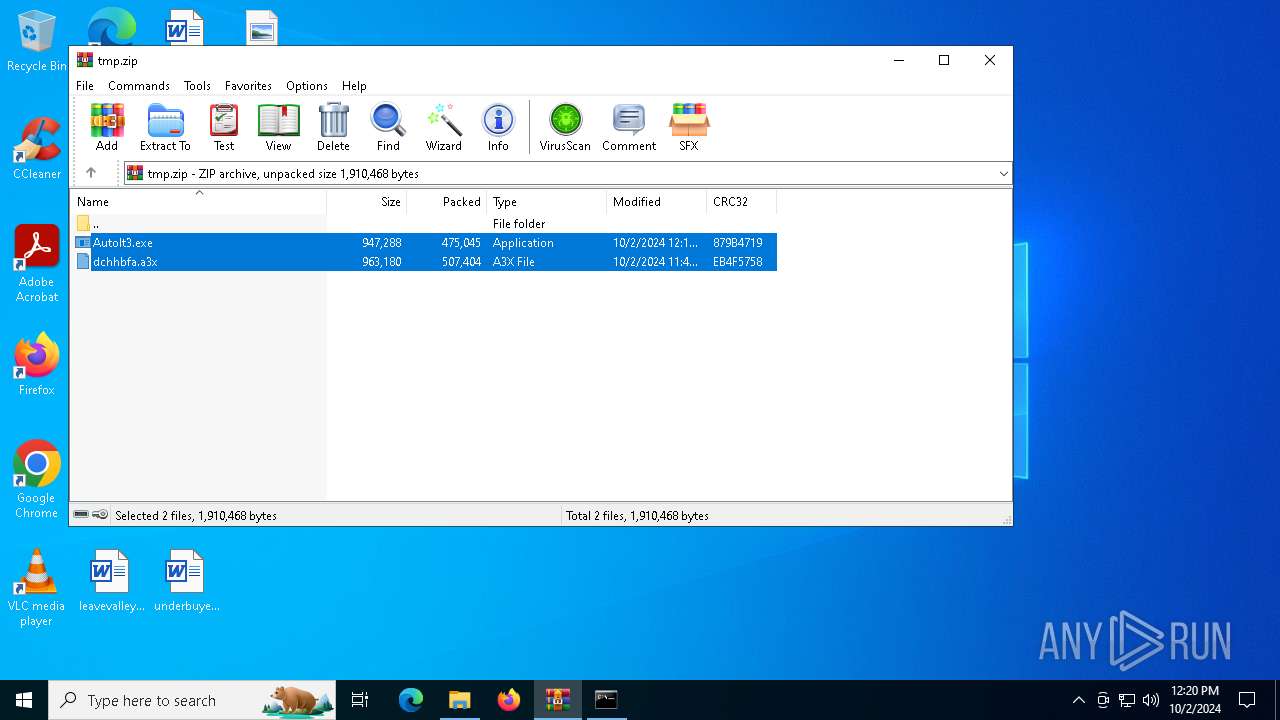
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 76AE0DB80E1B7907ECB1674F42625B8D |
| SHA1: | 2E5578D70BEC5969D6820A9B445E2AF0DA1A03CF |
| SHA256: | 5D54B99ED38527E7D79FB88D612DA2347CFA5E69A88F1B6516B80E40A16D8F1C |
| SSDEEP: | 49152:xwo1WwDXzhhShSE9rzuXxxG0ai3aa2CYhIMXKyUId15IiIkPuTIYJN3LYsT4/ywz:CoAwT8SEH0Xqa2CIIvociSI83LYA4/ae |
MALICIOUS
ARECHCLIENT2 has been detected (SURICATA)
- InstallUtil.exe (PID: 5732)
Connects to the CnC server
- InstallUtil.exe (PID: 5732)
XORed URL has been found (YARA)
- InstallUtil.exe (PID: 5732)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 5732)
Connects to unusual port
- InstallUtil.exe (PID: 5732)
INFO
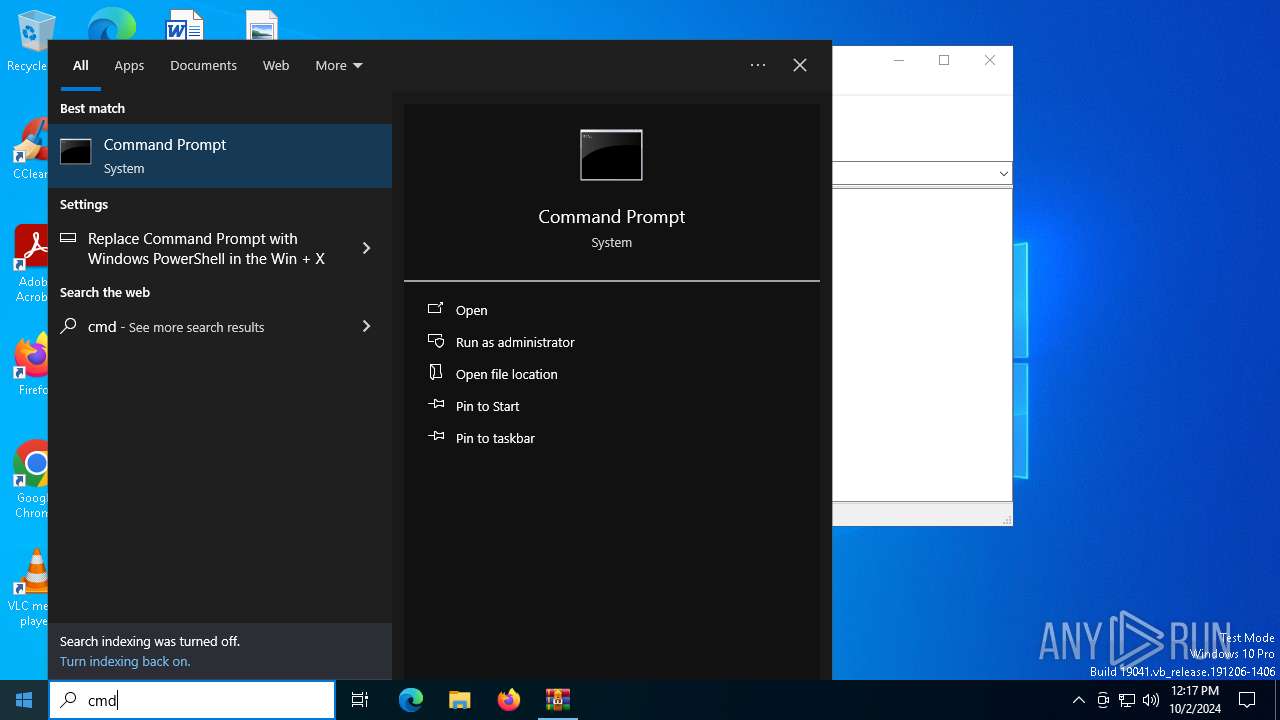
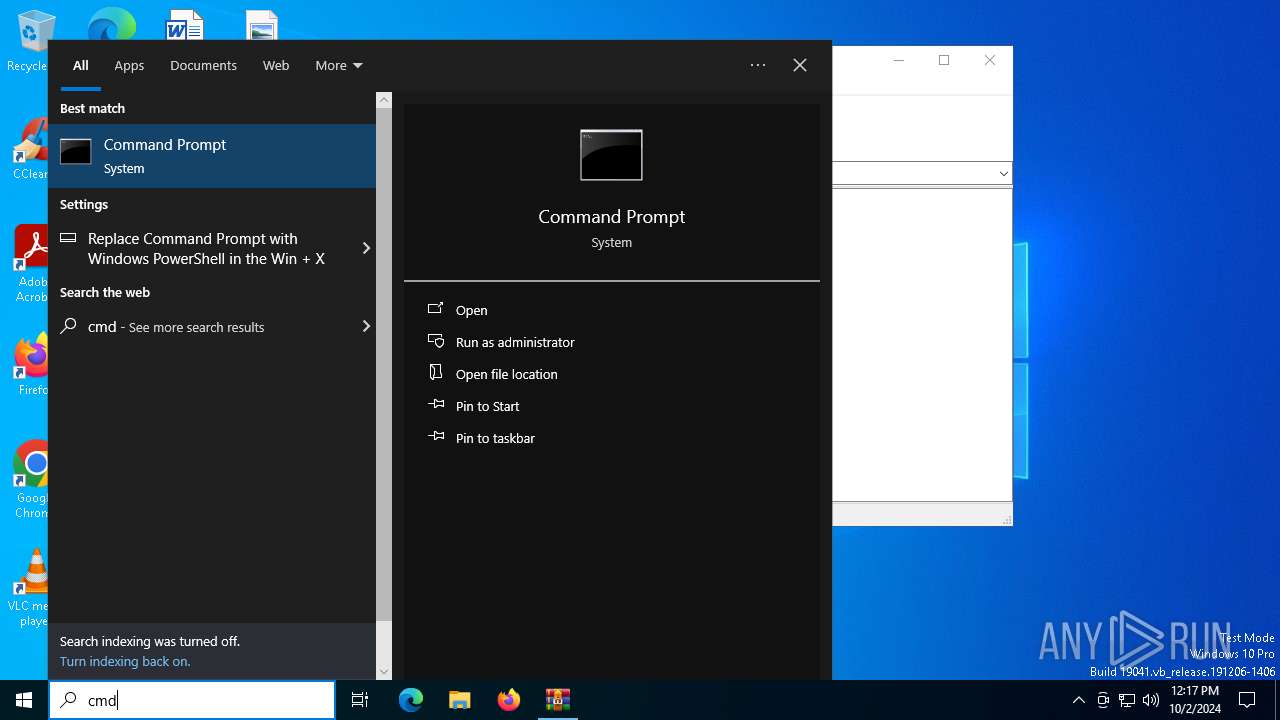
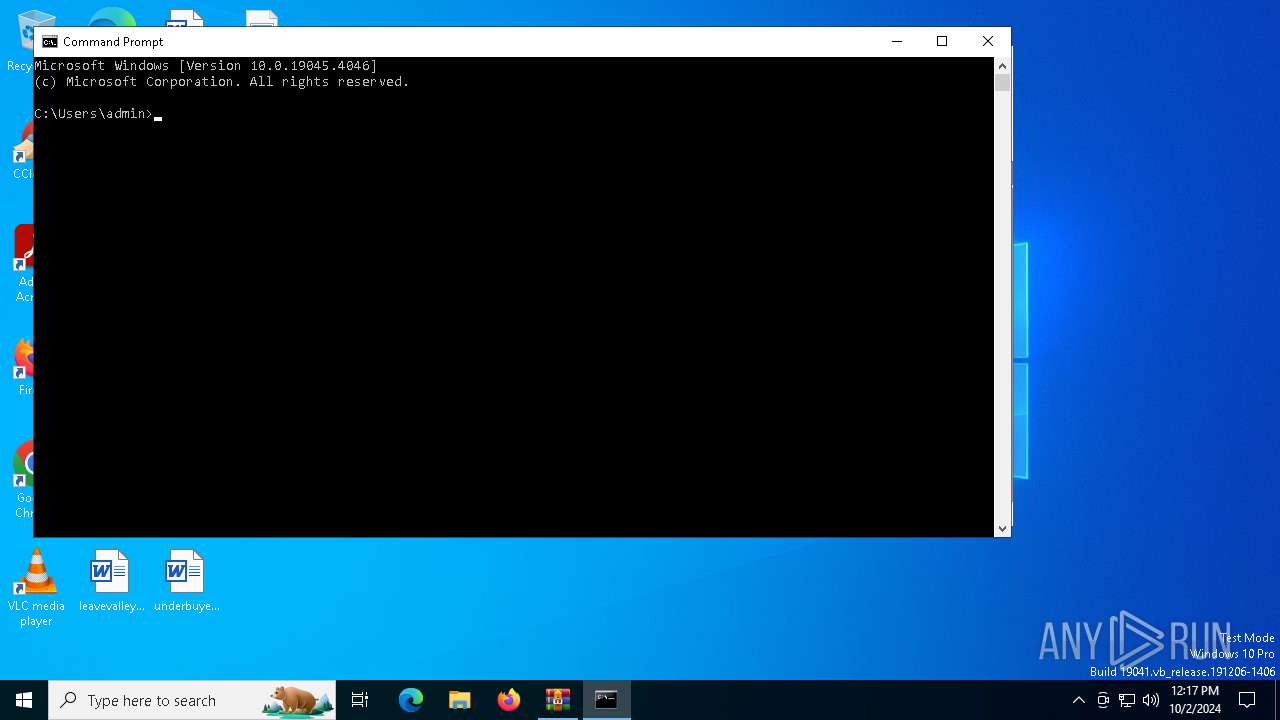
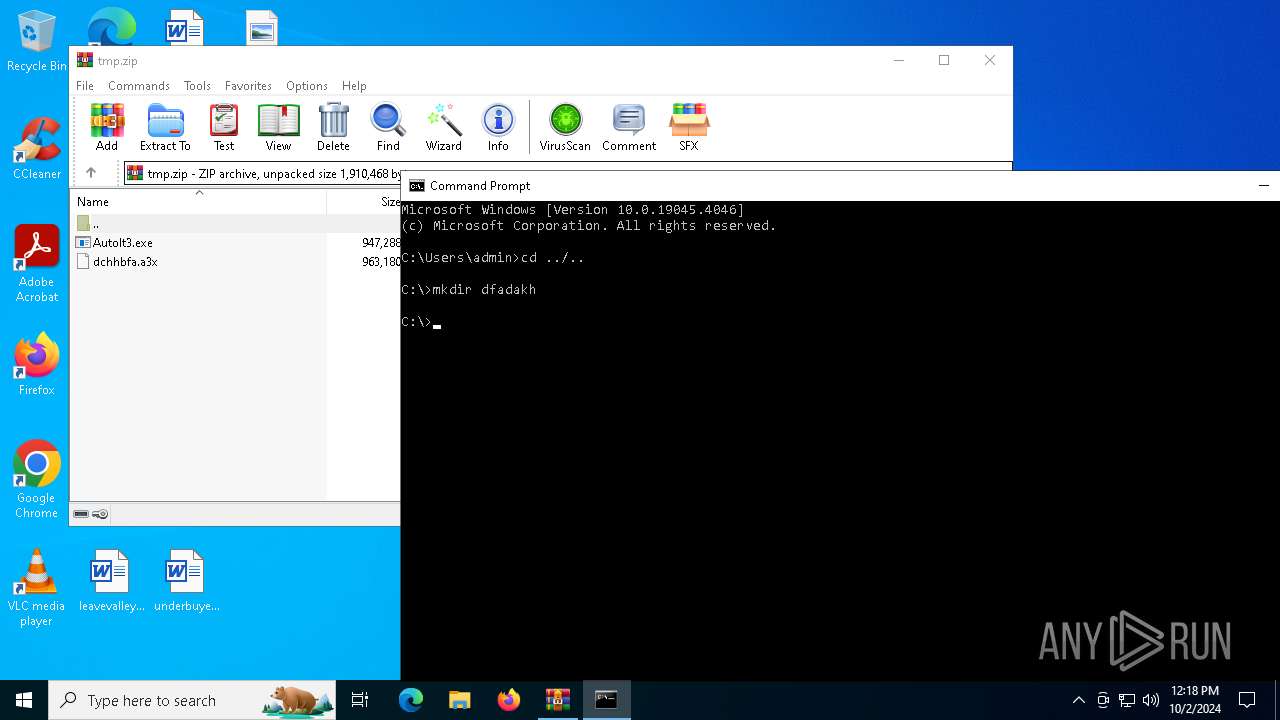
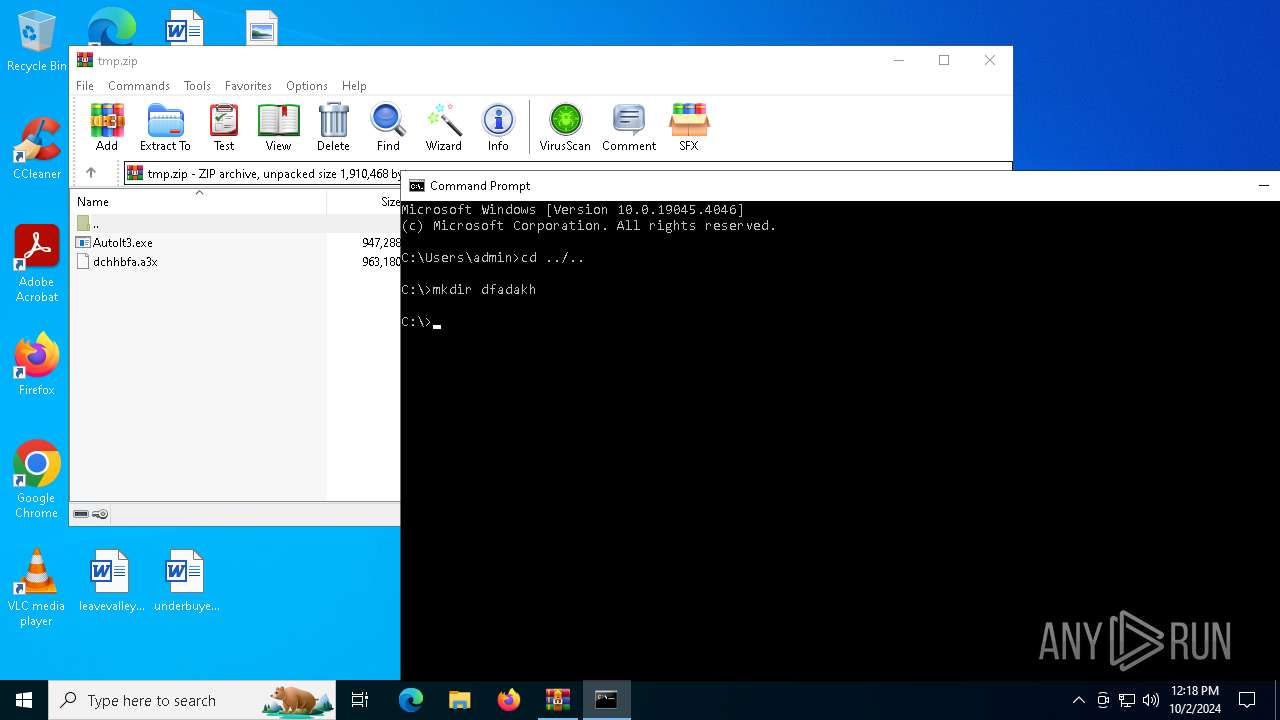
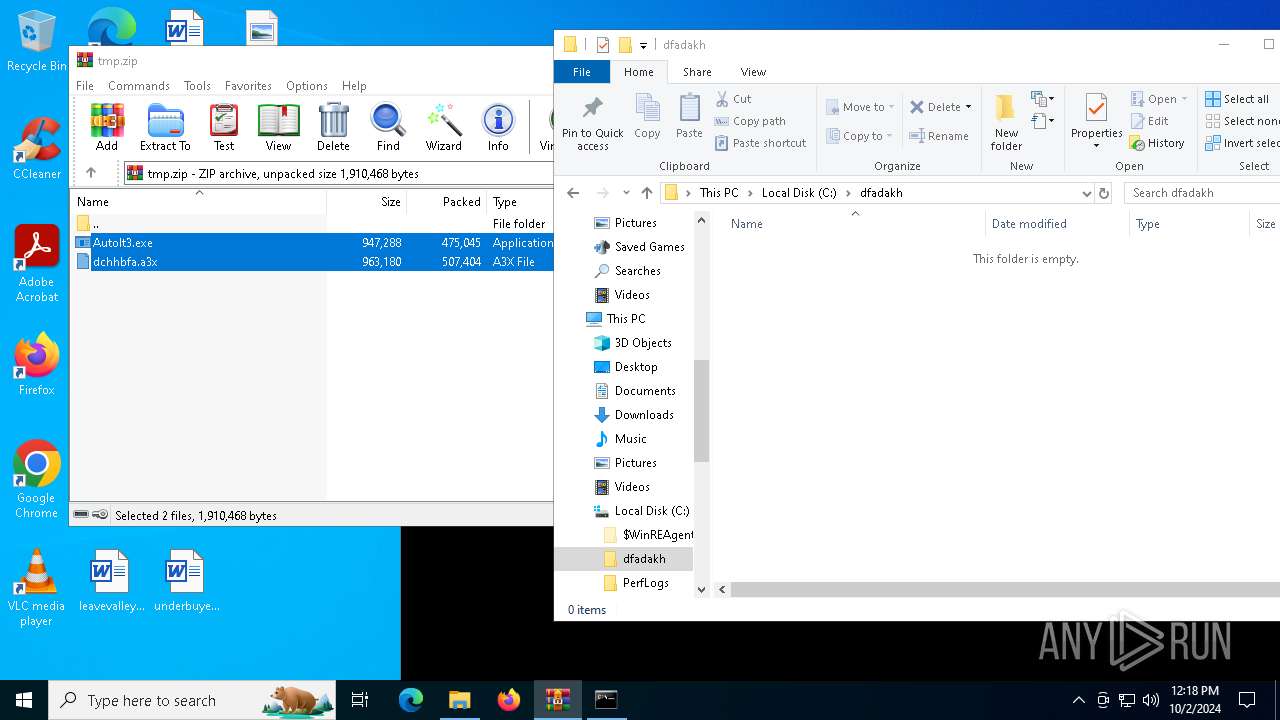
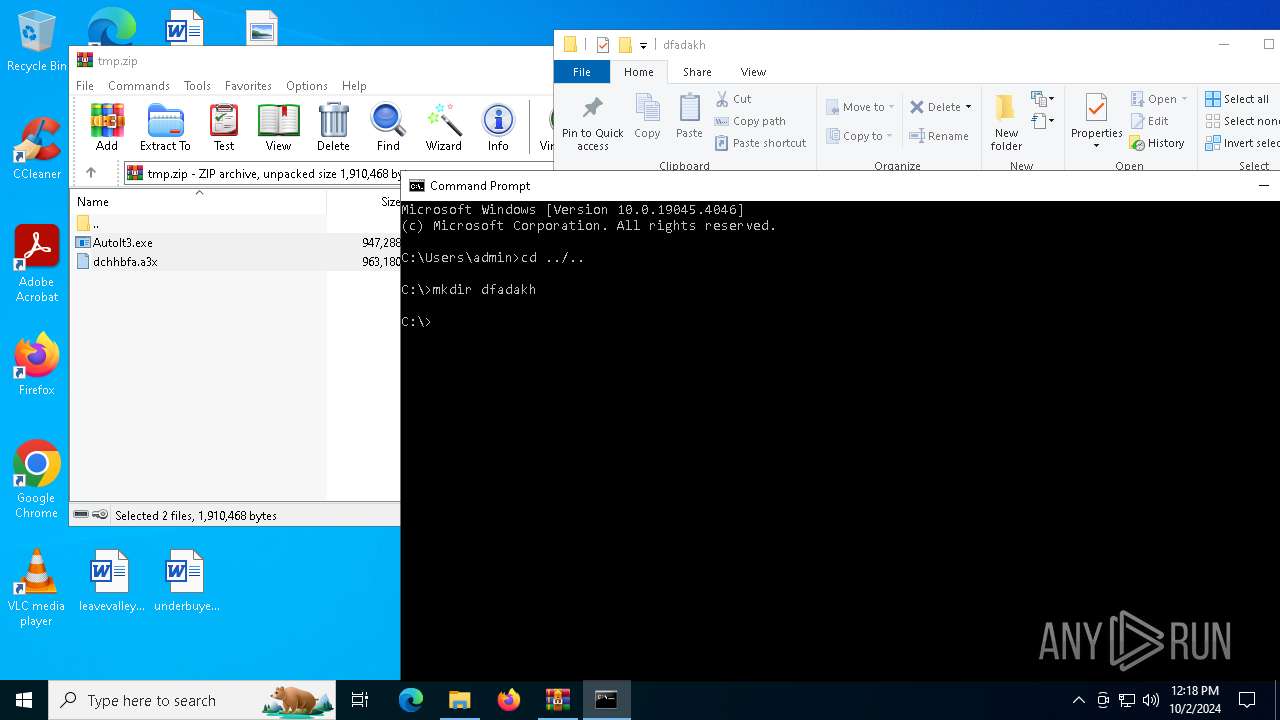
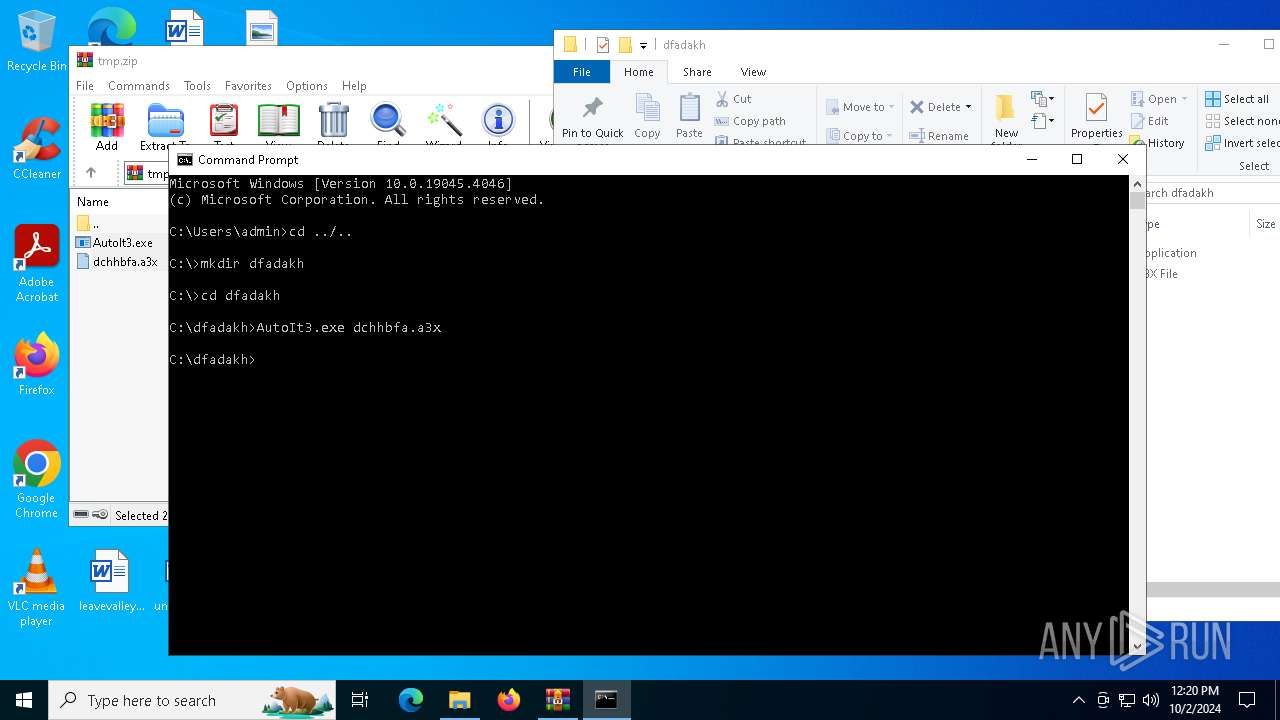
Manual execution by a user
- cmd.exe (PID: 5084)
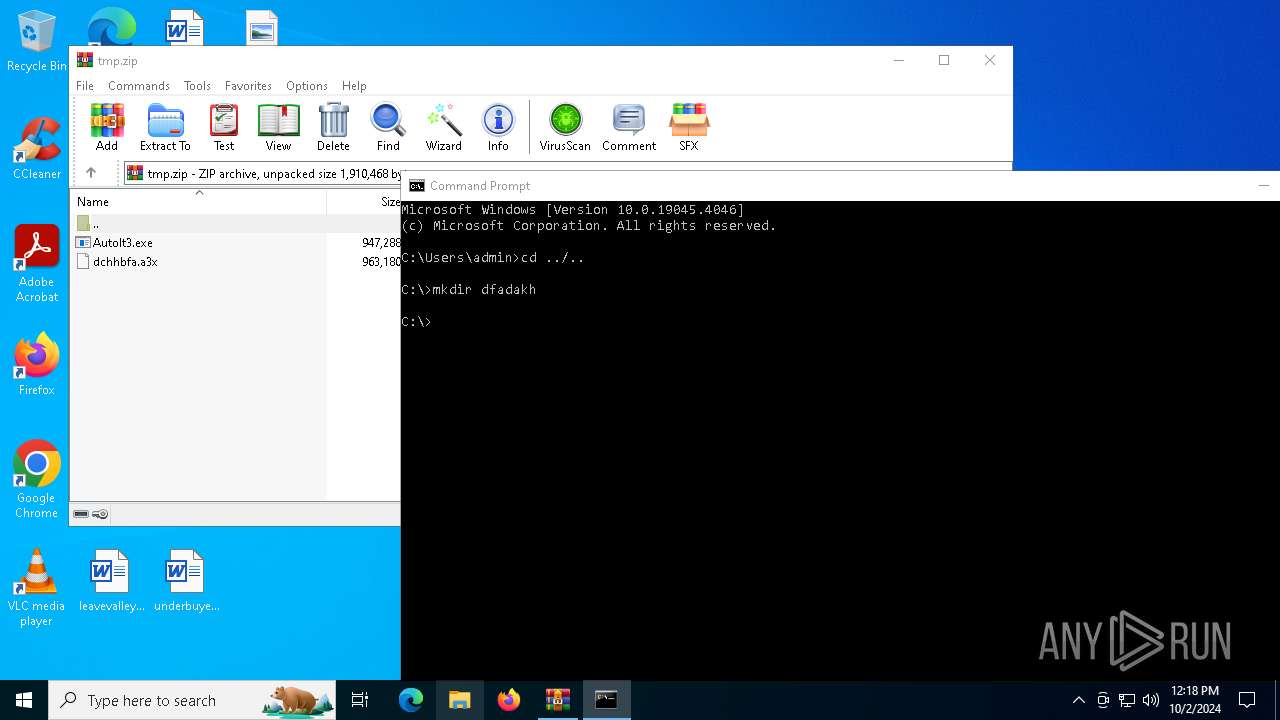
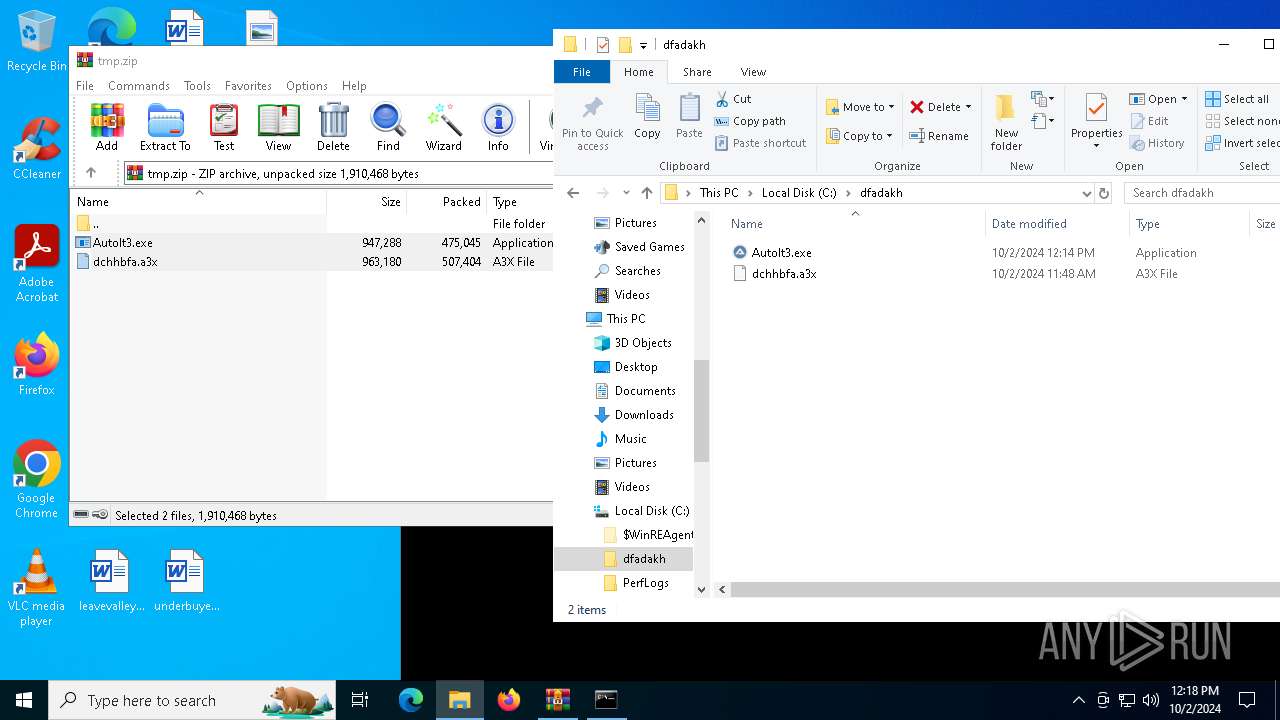
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5732) InstallUtil.exe
Decrypted-URLs (3)http://dl.google.com/chrome/install/375.126/chrome_installer.exe
https://github.com
https://pastebin.com/raw/eB8bmiVA
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:02 09:44:22 |
| ZipCRC: | 0x879b4719 |
| ZipCompressedSize: | 475045 |
| ZipUncompressedSize: | 947288 |
| ZipFileName: | AutoIt3.exe |
Total processes
134
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5084 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
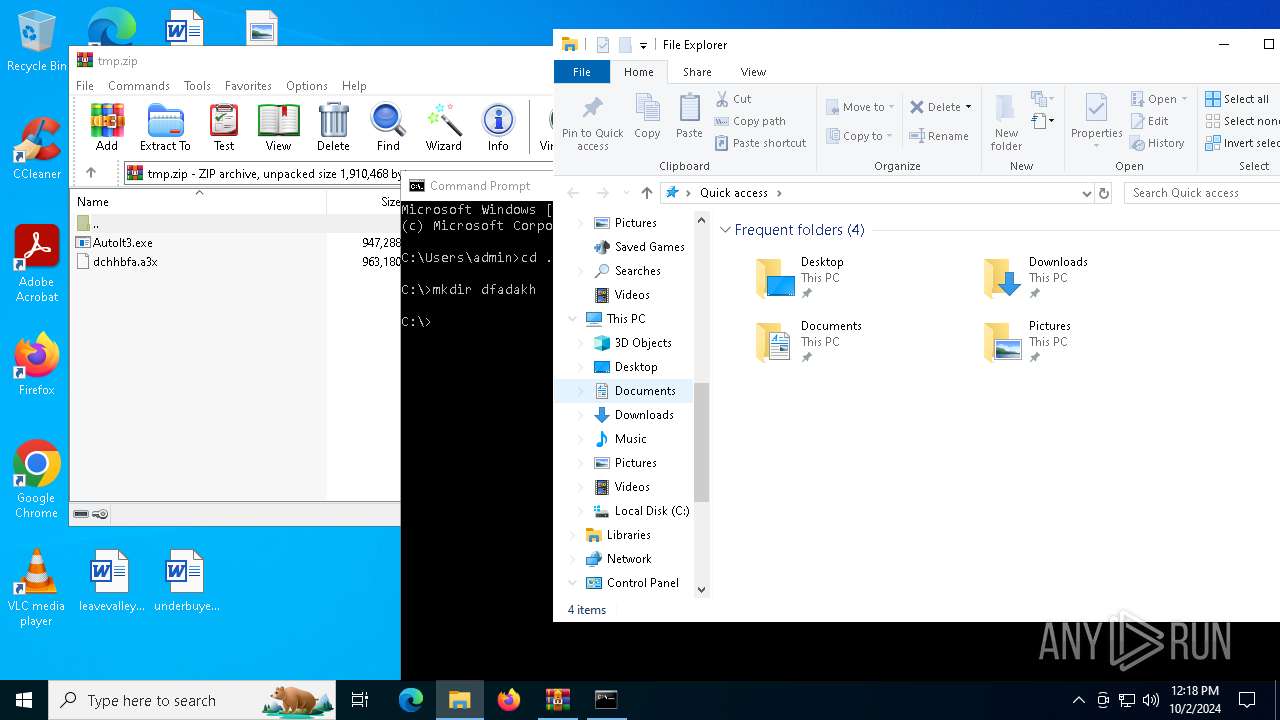
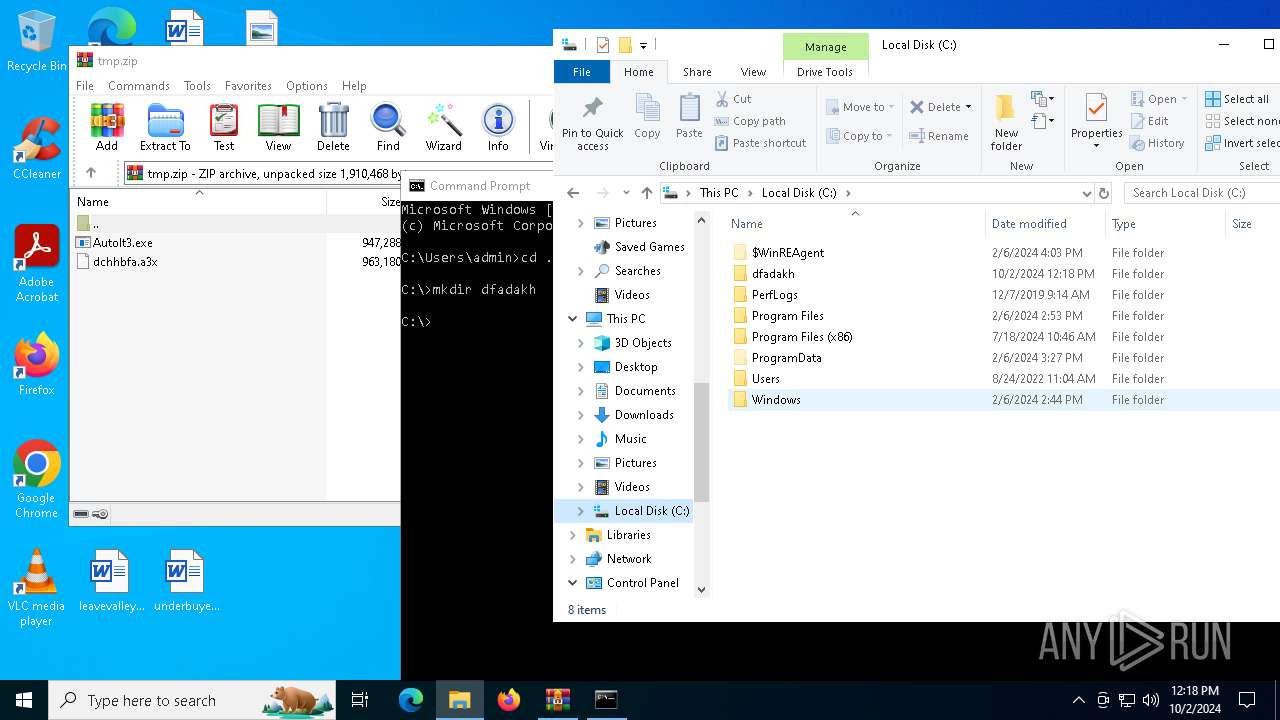
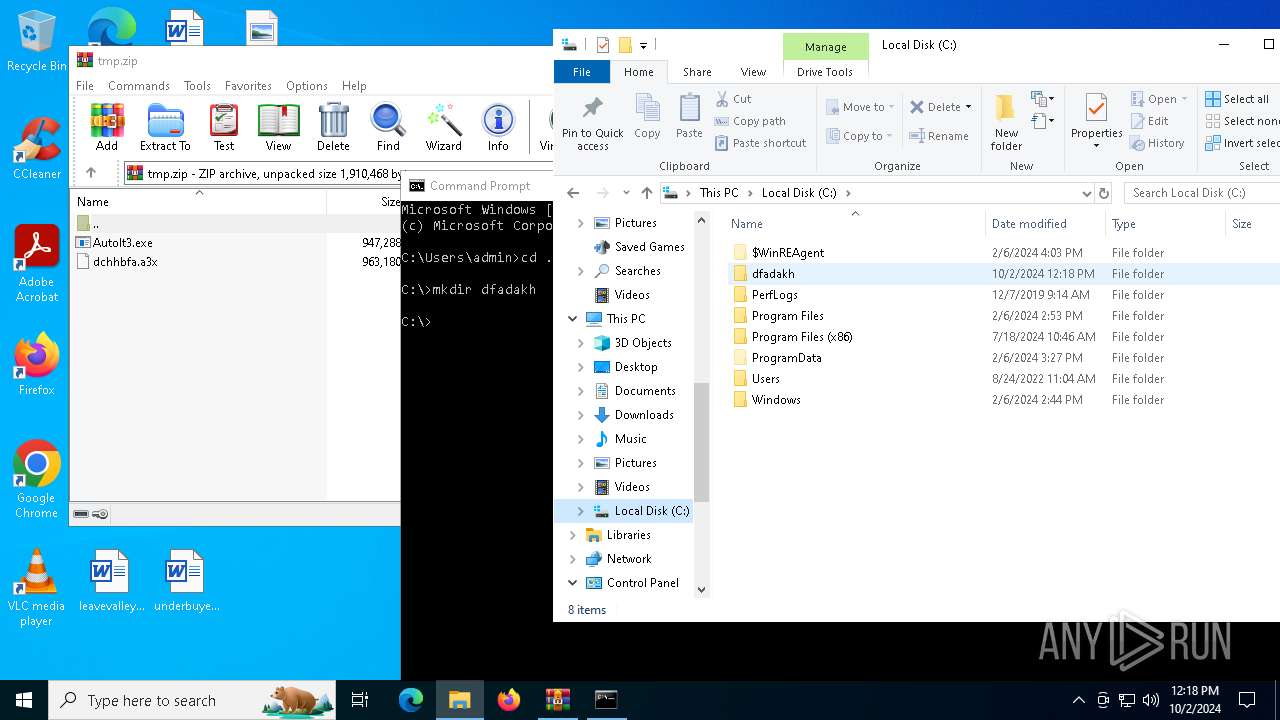
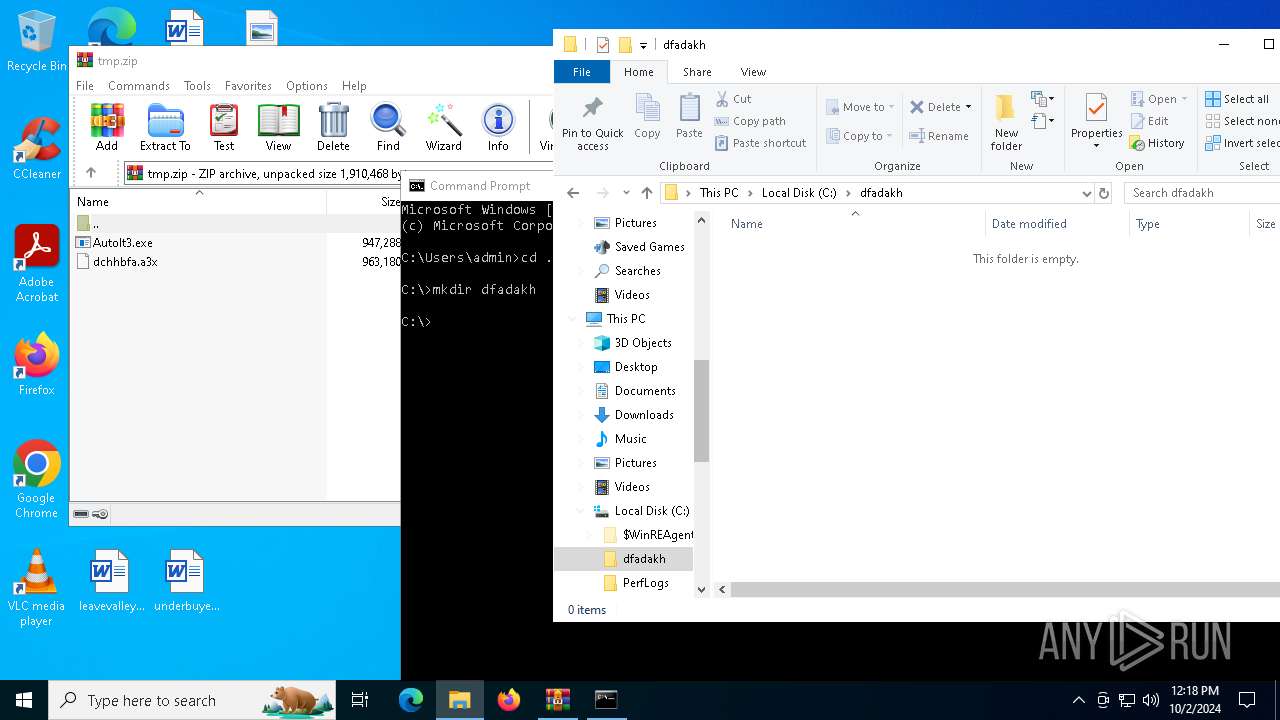
| 5220 | AutoIt3.exe dchhbfa.a3x | C:\dfadakh\AutoIt3.exe | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
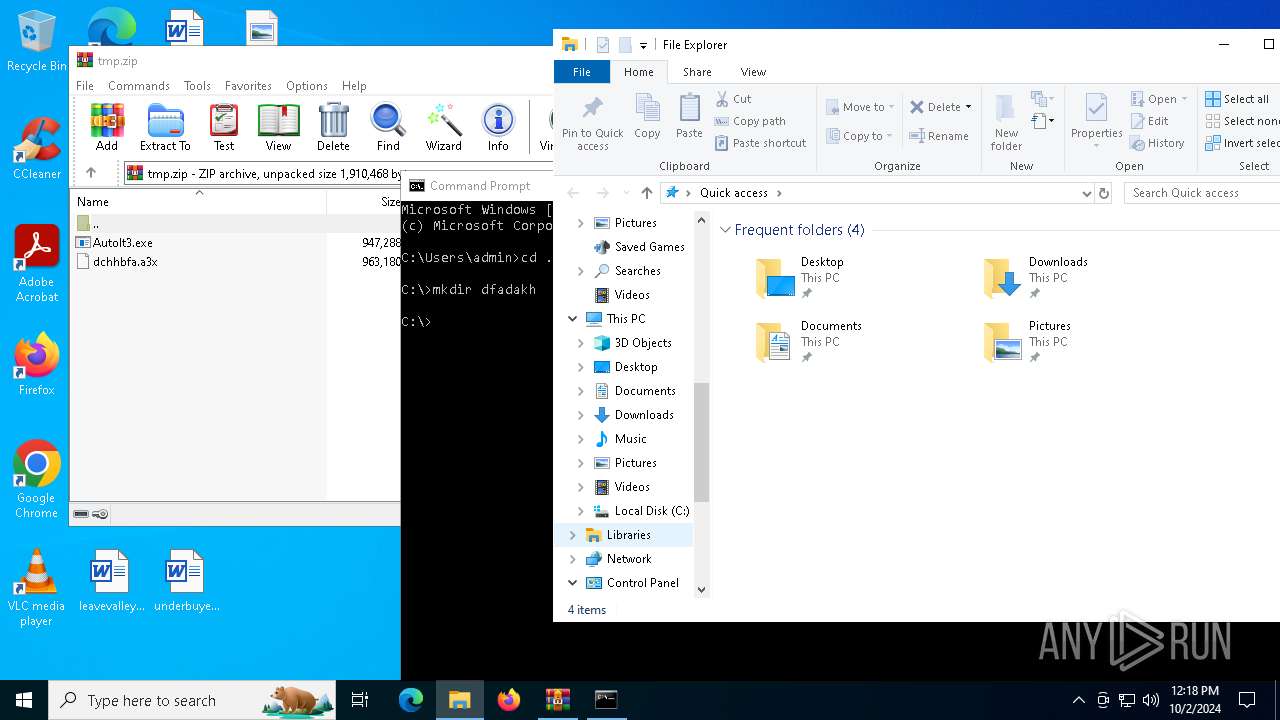
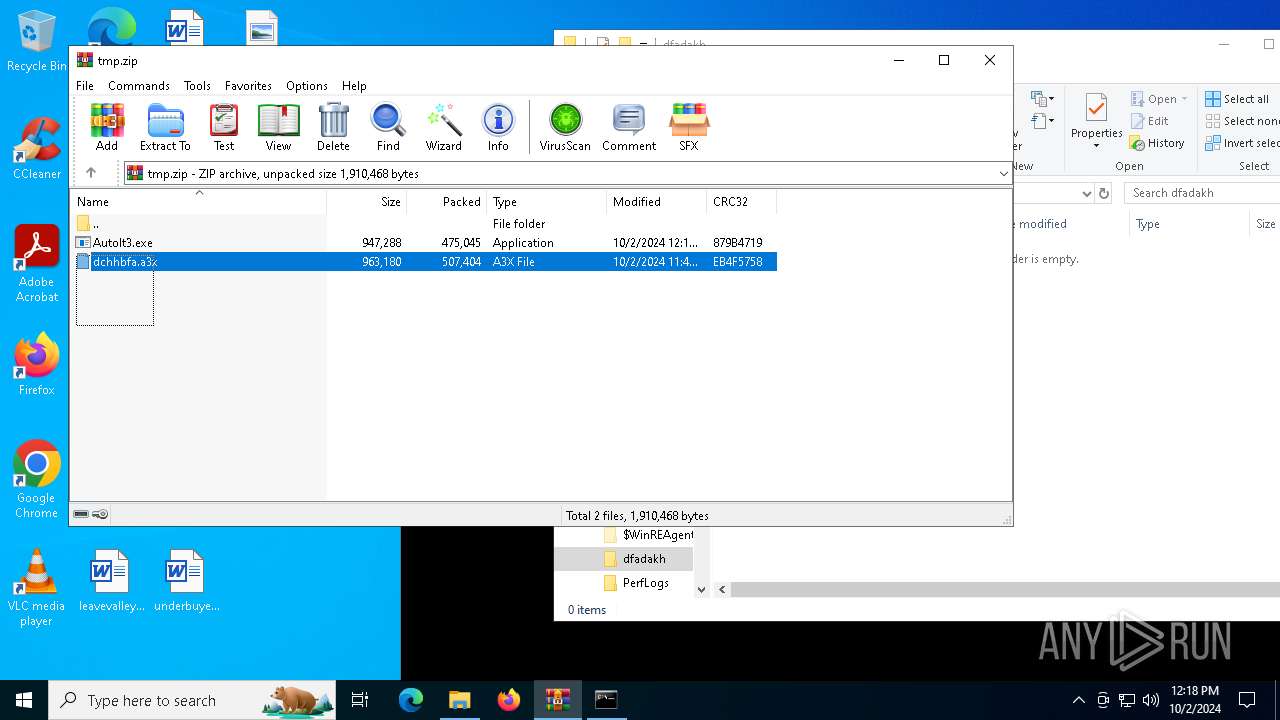
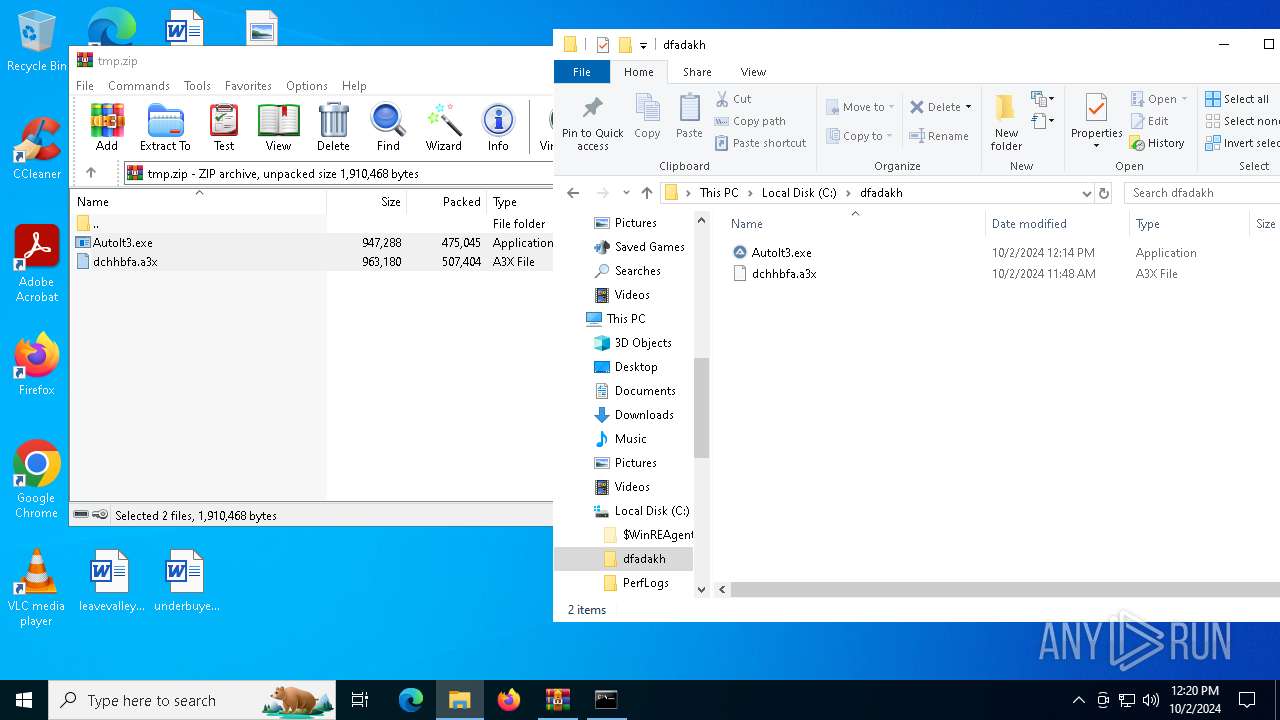
| 5508 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\tmp.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5732 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | AutoIt3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
xor-url(PID) Process(5732) InstallUtil.exe Decrypted-URLs (3)http://dl.google.com/chrome/install/375.126/chrome_installer.exe https://github.com https://pastebin.com/raw/eB8bmiVA | |||||||||||||||
Total events
4 157
Read events
4 126
Write events
31
Delete events
0
Modification events
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\tmp.zip | |||
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5220) AutoIt3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | dchhbfa |
Value: "C:\dfadakh\AutoIt3.exe" C:\dfadakh\dchhbfa.a3x | |||
| (PID) Process: | (5732) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5732) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5732) InstallUtil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\InstallUtil_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
10
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5508.31189\AutoIt3.exe | executable | |
MD5:0ADB9B817F1DF7807576C2D7068DD931 | SHA256:98E4F904F7DE1644E519D09371B8AFCBBF40FF3BD56D76CE4DF48479A4AB884B | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\nimda\llg\jquery.js | text | |
MD5:3C9137D88A00B1AE0B41FF6A70571615 | SHA256:24262BAAFEF17092927C3DAFE764AAA52A2A371B83ED2249CCA7E414DF99FAC1 | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\nimda\llg\icon.png | image | |
MD5:2C905A6E4A21A3FA14ADC1D99B7CBC03 | SHA256:CC3631CED23F21AE095C1397770E685F12F6AD788C8FA2F15487835A77A380FB | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\tmp4D21.tmp | sqlite | |
MD5:46D9FCA6032297F8AEE08D73418312BA | SHA256:865856FA4C33C4AEE52E15FBB370B6611468FE947E76E197F0E50D0AD62CB1B4 | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\nimda\llg\background.js | text | |
MD5:AA0E77EC6B92F58452BB5577B9980E6F | SHA256:AAD1C9BE17F64D7700FEB2D38DF7DC7446A48BF001AE42095B59B11FD24DFCDE | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\tmpD551.tmp | sqlite | |
MD5:46D9FCA6032297F8AEE08D73418312BA | SHA256:865856FA4C33C4AEE52E15FBB370B6611468FE947E76E197F0E50D0AD62CB1B4 | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\tmp4CE2.tmp | sqlite | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\tmpD511.tmp | sqlite | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 5732 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\tmp4CD1.tmp | sqlite | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 5508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5508.31189\dchhbfa.a3x | binary | |
MD5:54A4AE586596C6C4F02F454E20DA2F15 | SHA256:1231833EA78A813B8FCCDCF14D1A8D28EE7AA50ED5ECB4716D4B5328EE3FE8DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
73
DNS requests
24
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5732 | InstallUtil.exe | GET | 200 | 45.141.87.50:9000 | http://45.141.87.50:9000/wbinjget?q=EF680CC9EFE0A8BCEC05D07897760CE8 | unknown | — | — | unknown |
1232 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5388 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5388 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5880 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5880 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5732 | InstallUtil.exe | Malware Command and Control Activity Detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT CnC Init |
5732 | InstallUtil.exe | A Network Trojan was detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT Related Activity |
5732 | InstallUtil.exe | A Network Trojan was detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT Related Activity M2 (GET) |