| File name: | Piggy Mod.exe |
| Full analysis: | https://app.any.run/tasks/a1f94a34-1939-4c4c-809d-6c9bbf06a662 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 30, 2023, 20:00:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | BDF2688D7A74913A7B390B794C0DCA99 |
| SHA1: | CD7363AF2468C299D5BAC450D06AF0DEDE4823FF |
| SHA256: | 5D32695EE620F6DC72B9F6FA0502958FB73F3B147264925FEF4E5BDDB38B2776 |
| SSDEEP: | 49152:I0EcsT90z2NkvSCmRf7uY1+DVlYZ+hHjGmt/3DgX0nK1kltCb429nQQfHZxw/Y7m:h2NkKCmRf7uY1+DVlYZ+hHaIDgGnLfj |
MALICIOUS
Changes the autorun value in the registry
- MSAntivirus.exe (PID: 1308)
QUASAR has been detected (YARA)
- MSAntivirus.exe (PID: 1308)
Actions looks like stealing of personal data
- MSAntivirus.exe (PID: 1308)
Steals credentials from Web Browsers
- MSAntivirus.exe (PID: 1308)
SUSPICIOUS
Reads settings of System Certificates
- MSAntivirus.exe (PID: 1308)
Reads the Internet Settings
- MSAntivirus.exe (PID: 1308)
Loads DLL from Mozilla Firefox
- MSAntivirus.exe (PID: 1308)
INFO
Reads Environment values
- Piggy Mod.exe (PID: 128)
- MSAntivirus.exe (PID: 1308)
Drops the executable file immediately after the start
- Piggy Mod.exe (PID: 128)
Reads the computer name
- Piggy Mod.exe (PID: 128)
- MSAntivirus.exe (PID: 1308)
Checks supported languages
- Piggy Mod.exe (PID: 128)
- MSAntivirus.exe (PID: 1308)
Reads the machine GUID from the registry
- MSAntivirus.exe (PID: 1308)
- Piggy Mod.exe (PID: 128)
Creates files or folders in the user directory
- Piggy Mod.exe (PID: 128)
- MSAntivirus.exe (PID: 1308)
Starts itself from another location
- Piggy Mod.exe (PID: 128)
Connects to unusual port
- MSAntivirus.exe (PID: 1308)
ASYNCRAT has been detected (SURICATA)
- MSAntivirus.exe (PID: 1308)
QUASAR has been detected (SURICATA)
- MSAntivirus.exe (PID: 1308)
Connects to the CnC server
- MSAntivirus.exe (PID: 1308)
Create files in a temporary directory
- MSAntivirus.exe (PID: 1308)
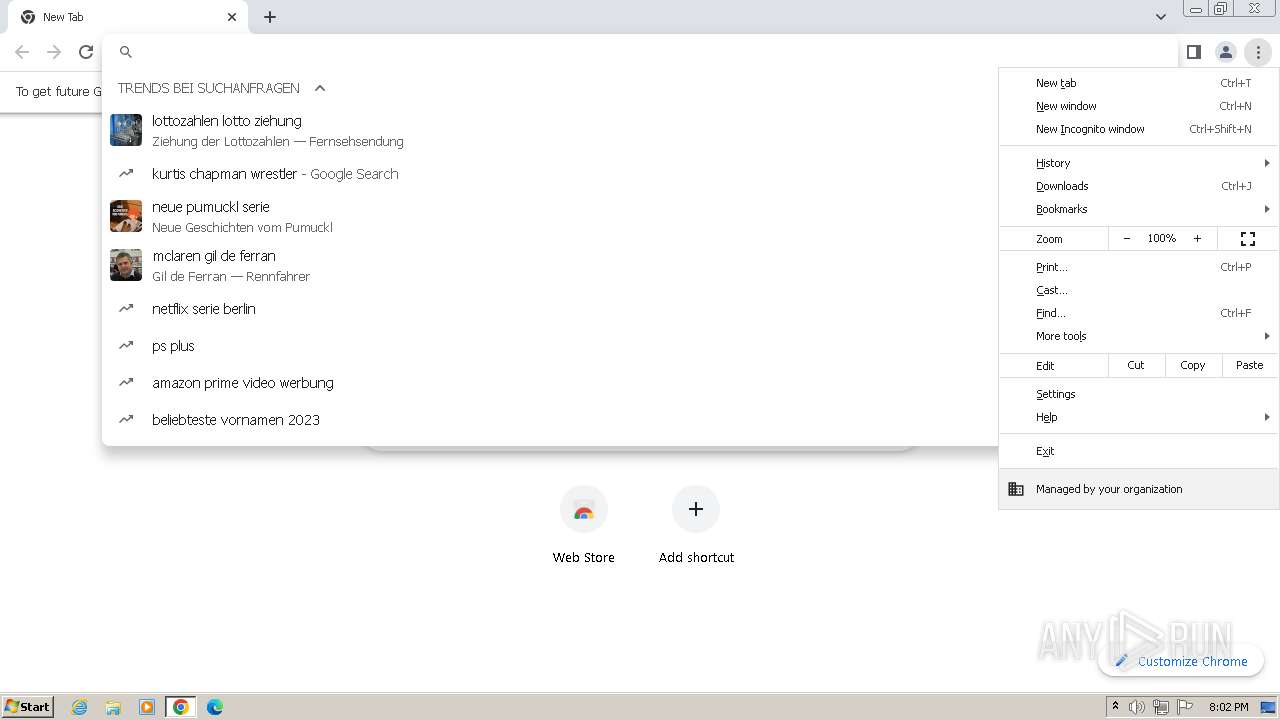
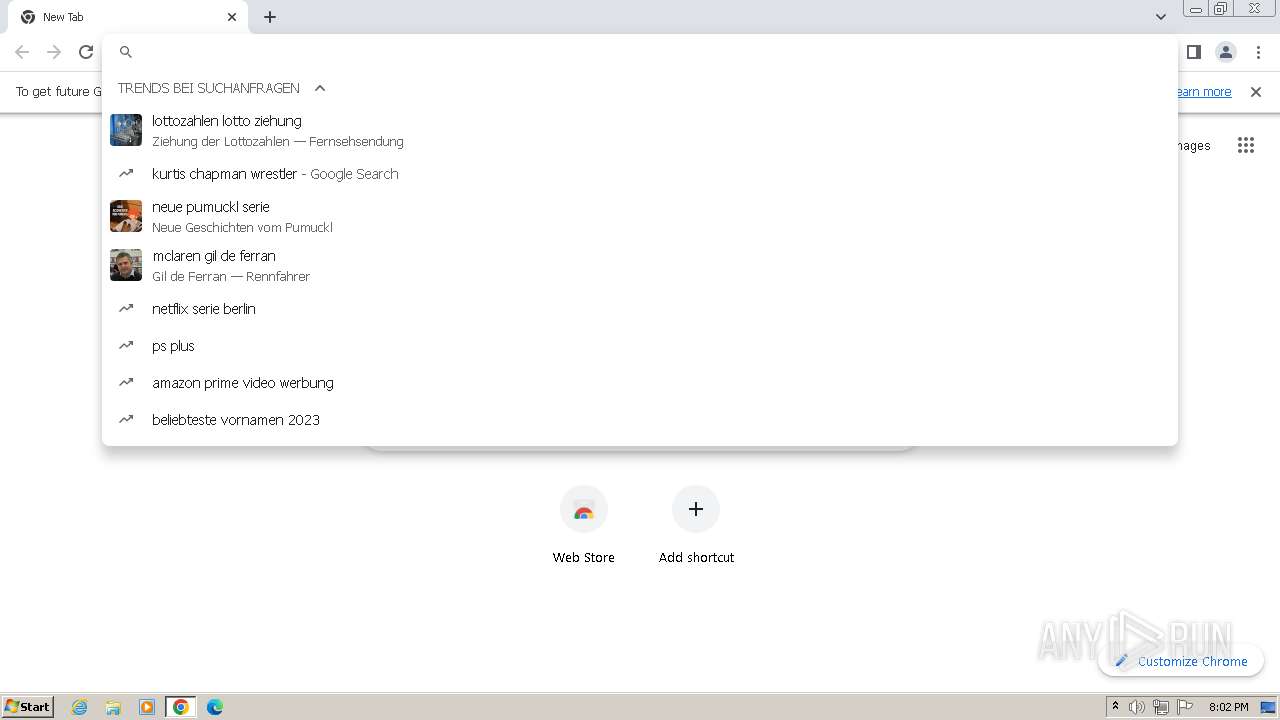
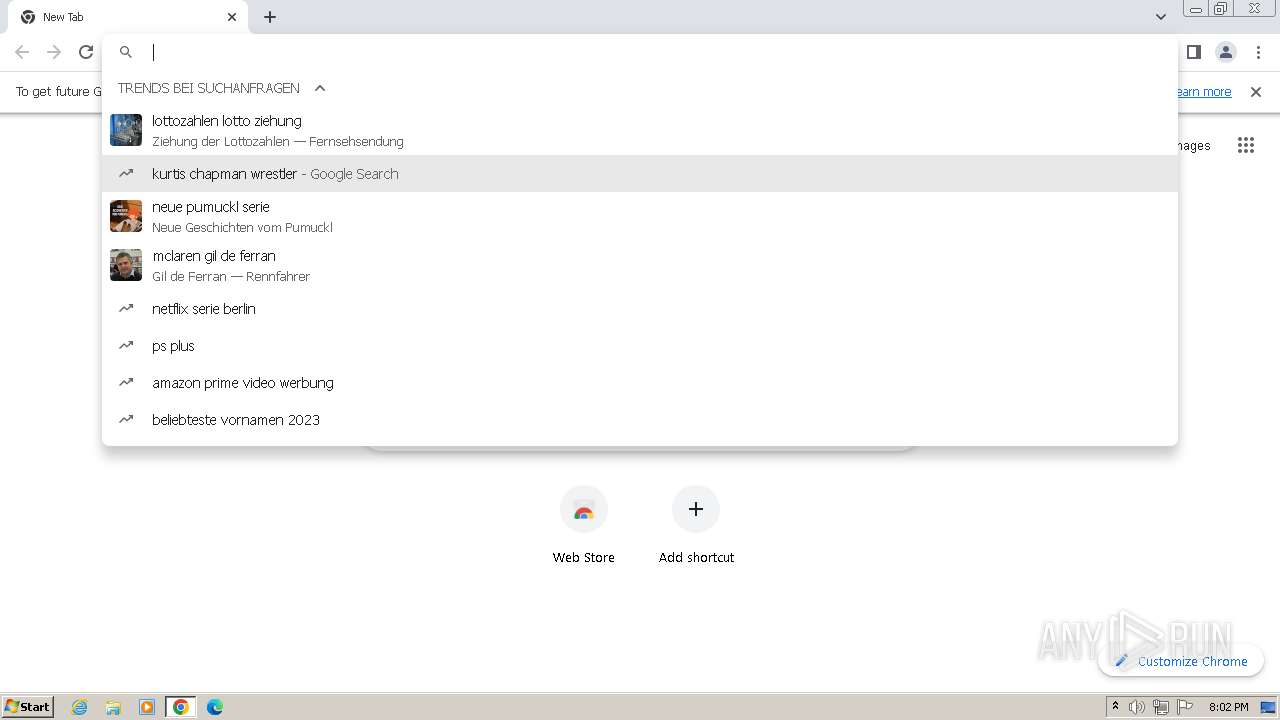
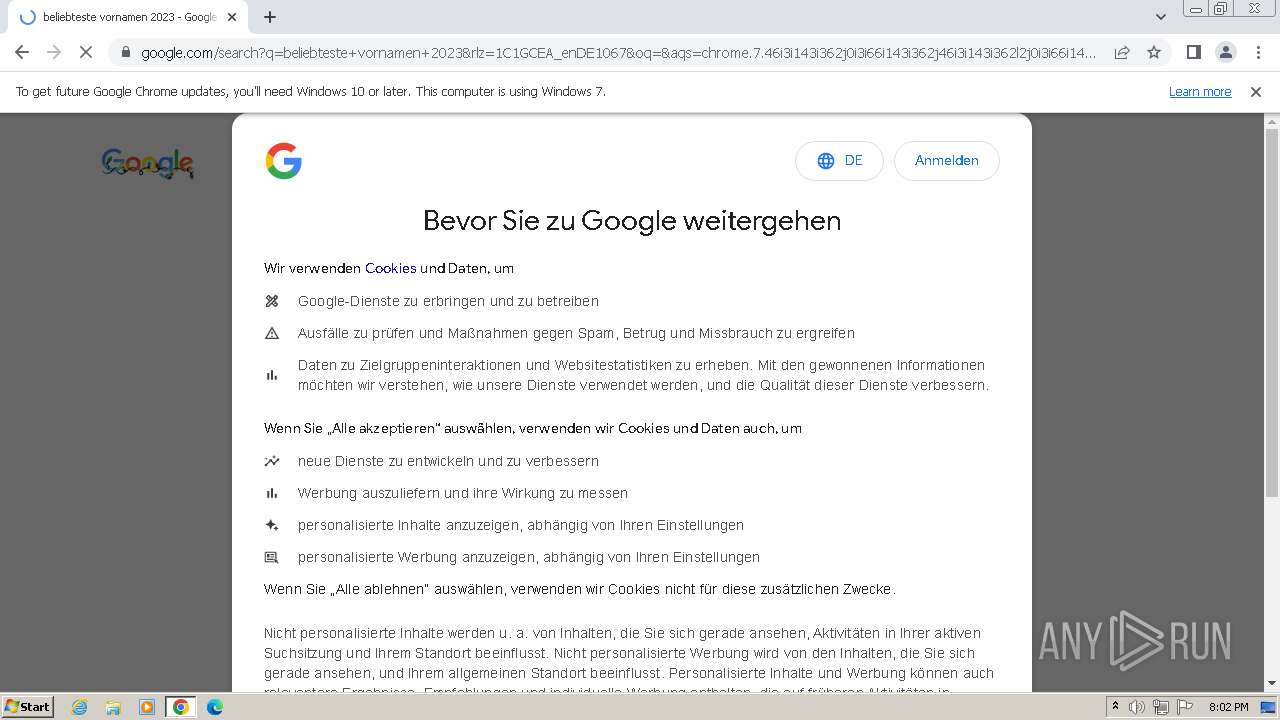
Application launched itself
- chrome.exe (PID: 1732)
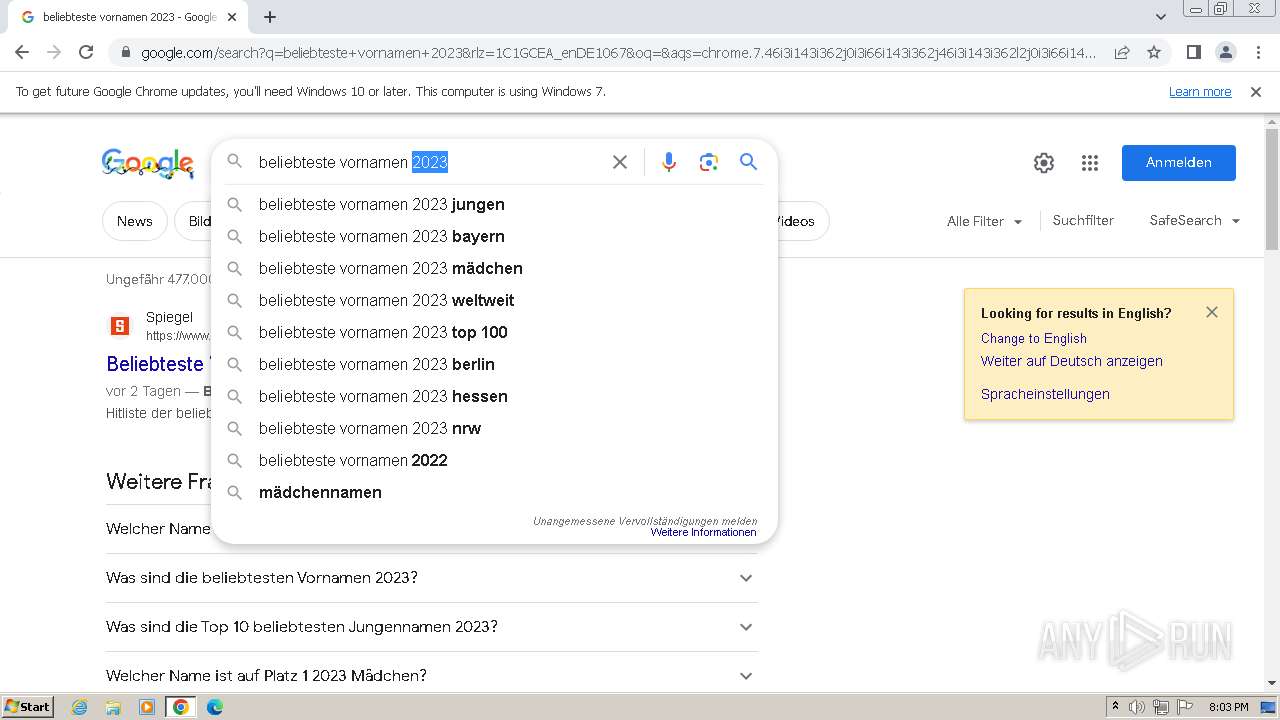
Manual execution by a user
- chrome.exe (PID: 1732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(1308) MSAntivirus.exe
Version1.4.1
C2 (2)7.tcp.eu.ngrok.io:14907
Sub_DirSubDir
Install_NameMSAntivirus.exe
Mutexe2c26705-9f97-4332-b21a-f2a908bcd5f4
StartupMicrosoft Antivirus
TagOffice04
LogDirLogs
Signaturev+hVKKZ1dRzqWGwjND4wnEevcbUeRY9v4VrbNwloeVmLRDQd4N/yqBrmI4gCMuId9hnsJto0qFQw0KUg9GuP6DOLyDtuOQll0RGzv+WKEPxIErEQjgEXqzfriYmeGGnMYj7ahr0kVJNecYTeZ2gKjiOm/rhp12nQIuYz7tLHrW8VDkMC+G7T+zUQesdtyvyd0g9nOcCuho36QVf0sJt3DuU6OGEkUOuE4Kd1sfrr8BdE3yQ439c7MqRKOpVct7zecerysqS+mE2oJXsK8kQ40gMPUHwsWHIQPMbESh8GOqY+...
CertificateMIIE9DCCAtygAwIBAgIQAIdU14NfTFZRM9UOLDUwBTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTIyODE3NDUyOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA+1M1Drz5qpSbwsfb/30Sun/bLQr6aK9NTlBkkj04LZpm4X9beIFd/CQFHTdyN194ByoXgVRI...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 17:16:39+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261440 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e3de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
51
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\Piggy Mod.exe" | C:\Users\admin\AppData\Local\Temp\Piggy Mod.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3492 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3104 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\AppData\Roaming\SubDir\MSAntivirus.exe" | C:\Users\admin\AppData\Roaming\SubDir\MSAntivirus.exe | Piggy Mod.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 0 Version: 1.4.1 Modules
Quasar(PID) Process(1308) MSAntivirus.exe Version1.4.1 C2 (2)7.tcp.eu.ngrok.io:14907 Sub_DirSubDir Install_NameMSAntivirus.exe Mutexe2c26705-9f97-4332-b21a-f2a908bcd5f4 StartupMicrosoft Antivirus TagOffice04 LogDirLogs Signaturev+hVKKZ1dRzqWGwjND4wnEevcbUeRY9v4VrbNwloeVmLRDQd4N/yqBrmI4gCMuId9hnsJto0qFQw0KUg9GuP6DOLyDtuOQll0RGzv+WKEPxIErEQjgEXqzfriYmeGGnMYj7ahr0kVJNecYTeZ2gKjiOm/rhp12nQIuYz7tLHrW8VDkMC+G7T+zUQesdtyvyd0g9nOcCuho36QVf0sJt3DuU6OGEkUOuE4Kd1sfrr8BdE3yQ439c7MqRKOpVct7zecerysqS+mE2oJXsK8kQ40gMPUHwsWHIQPMbESh8GOqY+... CertificateMIIE9DCCAtygAwIBAgIQAIdU14NfTFZRM9UOLDUwBTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTIyODE3NDUyOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA+1M1Drz5qpSbwsfb/30Sun/bLQr6aK9NTlBkkj04LZpm4X9beIFd/CQFHTdyN194ByoXgVRI... | |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x65988b38,0x65988b48,0x65988b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1080 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2272 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3620 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3376 --field-trial-handle=1196,i,8398770996080964943,18358412390974897982,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
7 156
Read events
7 092
Write events
64
Delete events
0
Modification events
| (PID) Process: | (128) Piggy Mod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1308) MSAntivirus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1308) MSAntivirus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Antivirus |
Value: "C:\Users\admin\AppData\Roaming\SubDir\MSAntivirus.exe" | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
1
Suspicious files
106
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF101afc.TMP | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1308 | MSAntivirus.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 128 | Piggy Mod.exe | C:\Users\admin\AppData\Roaming\SubDir\MSAntivirus.exe | executable | |
MD5:BDF2688D7A74913A7B390B794C0DCA99 | SHA256:5D32695EE620F6DC72B9F6FA0502958FB73F3B147264925FEF4E5BDDB38B2776 | |||
| 1308 | MSAntivirus.exe | C:\Users\admin\AppData\Local\Temp\Cab4472.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF101e09.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
40
DNS requests
30
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1308 | MSAntivirus.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9fad641487cb815d | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1308 | MSAntivirus.exe | 3.124.67.191:14907 | 7.tcp.eu.ngrok.io | AMAZON-02 | DE | malicious |
1308 | MSAntivirus.exe | 3.67.15.169:14907 | 7.tcp.eu.ngrok.io | AMAZON-02 | DE | unknown |
1308 | MSAntivirus.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
1308 | MSAntivirus.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | unknown |
1732 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2636 | chrome.exe | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2636 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
7.tcp.eu.ngrok.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ipwho.is |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
1080 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
1308 | MSAntivirus.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
1308 | MSAntivirus.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
1308 | MSAntivirus.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |