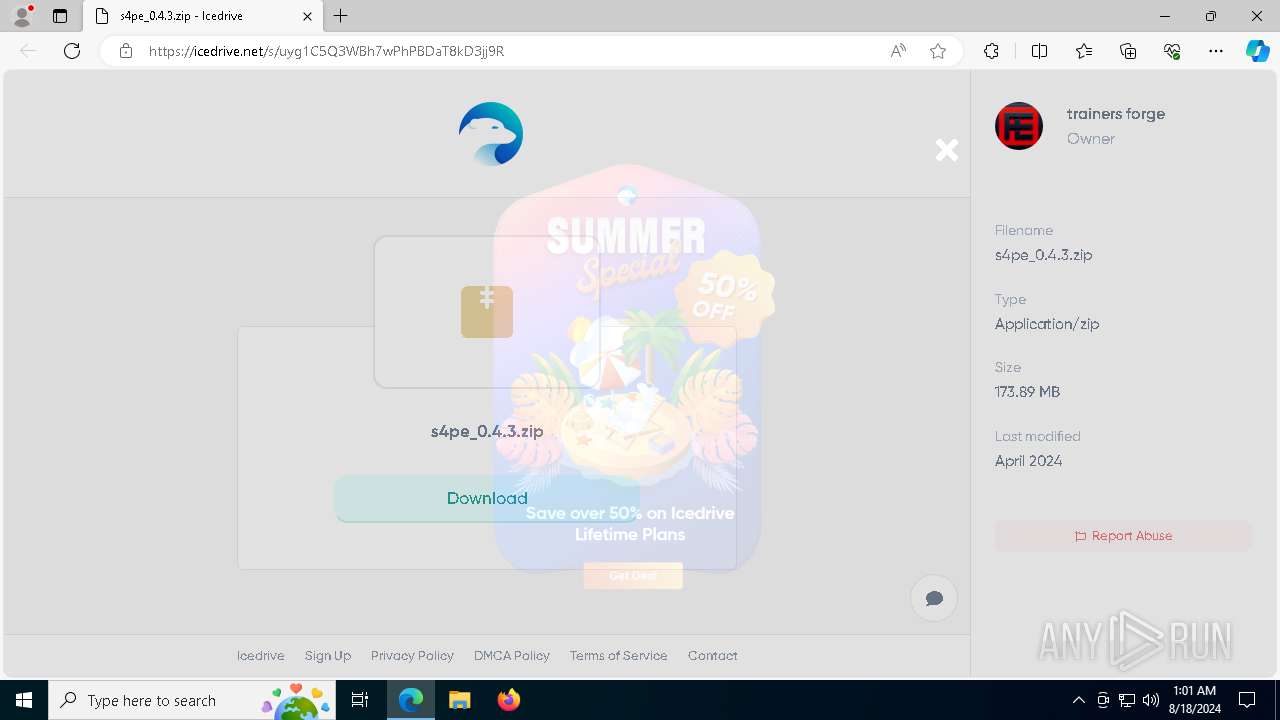
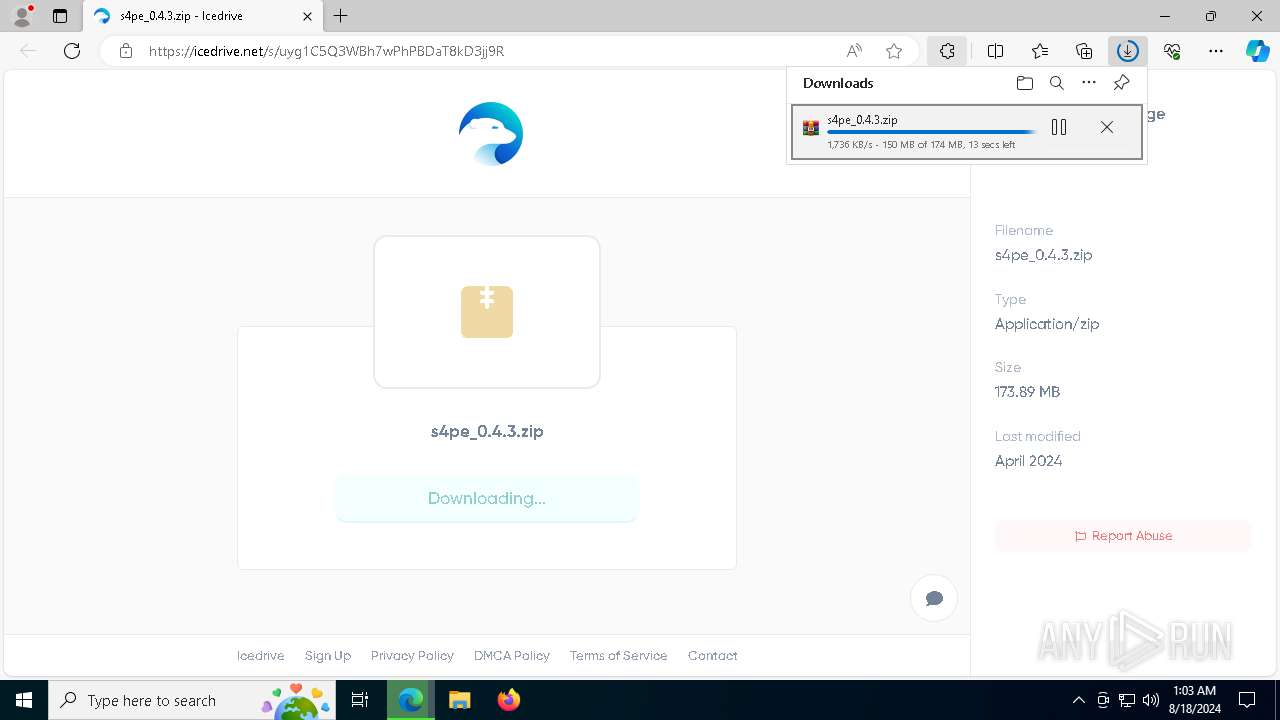
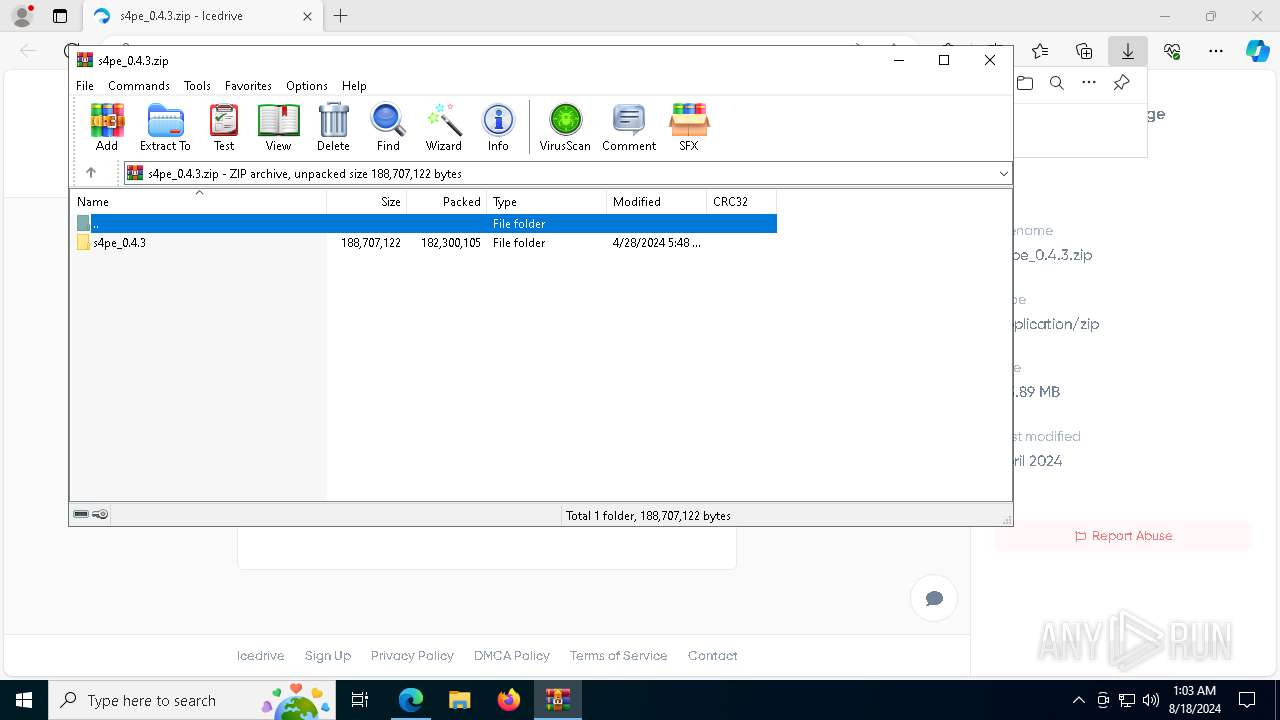
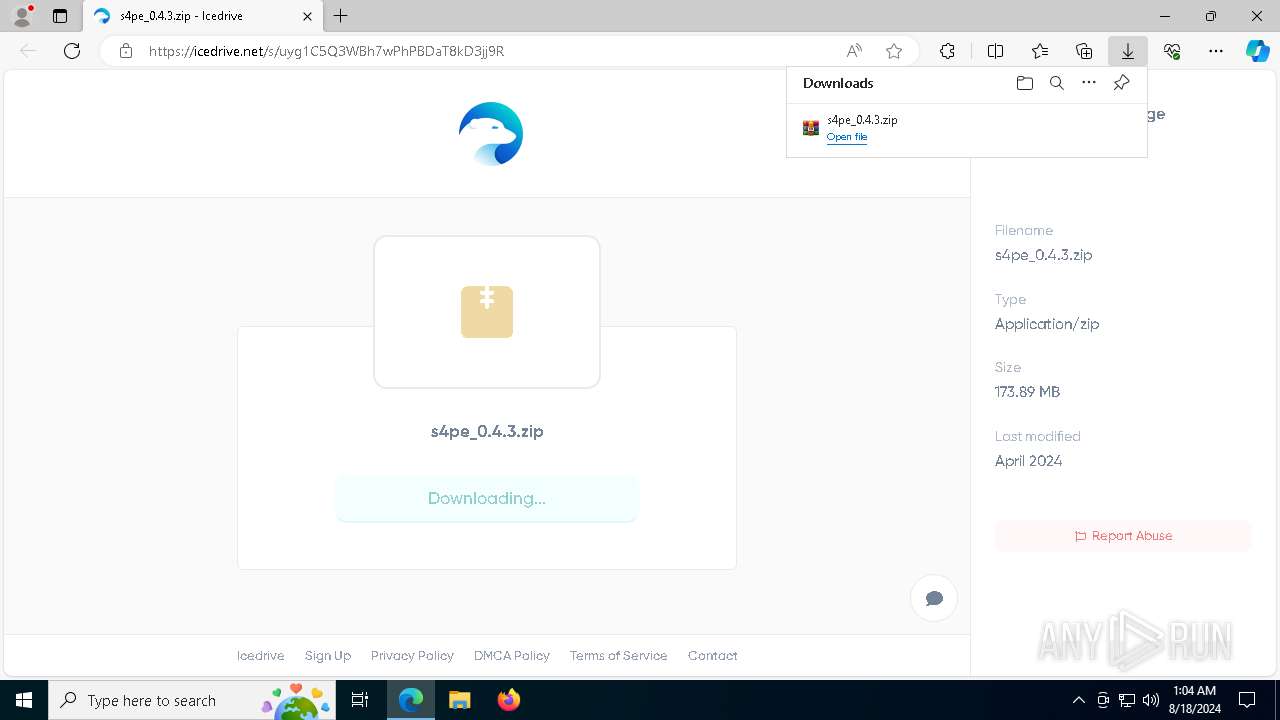
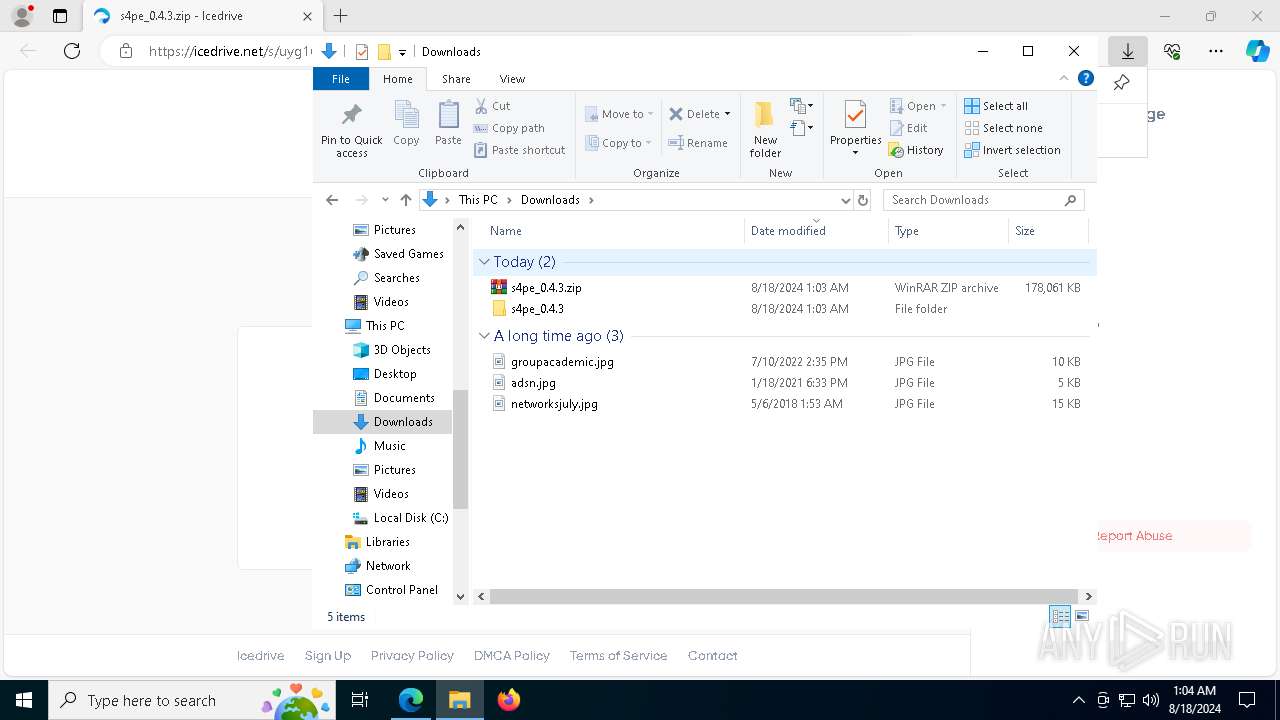
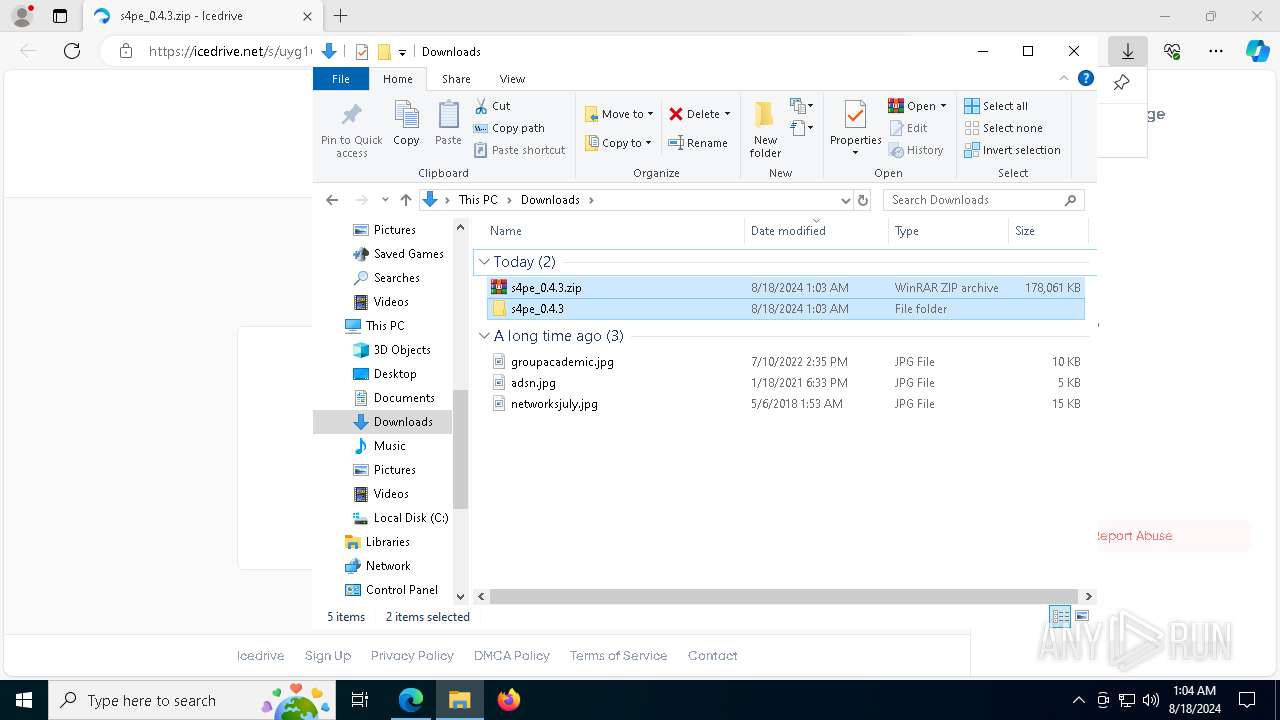
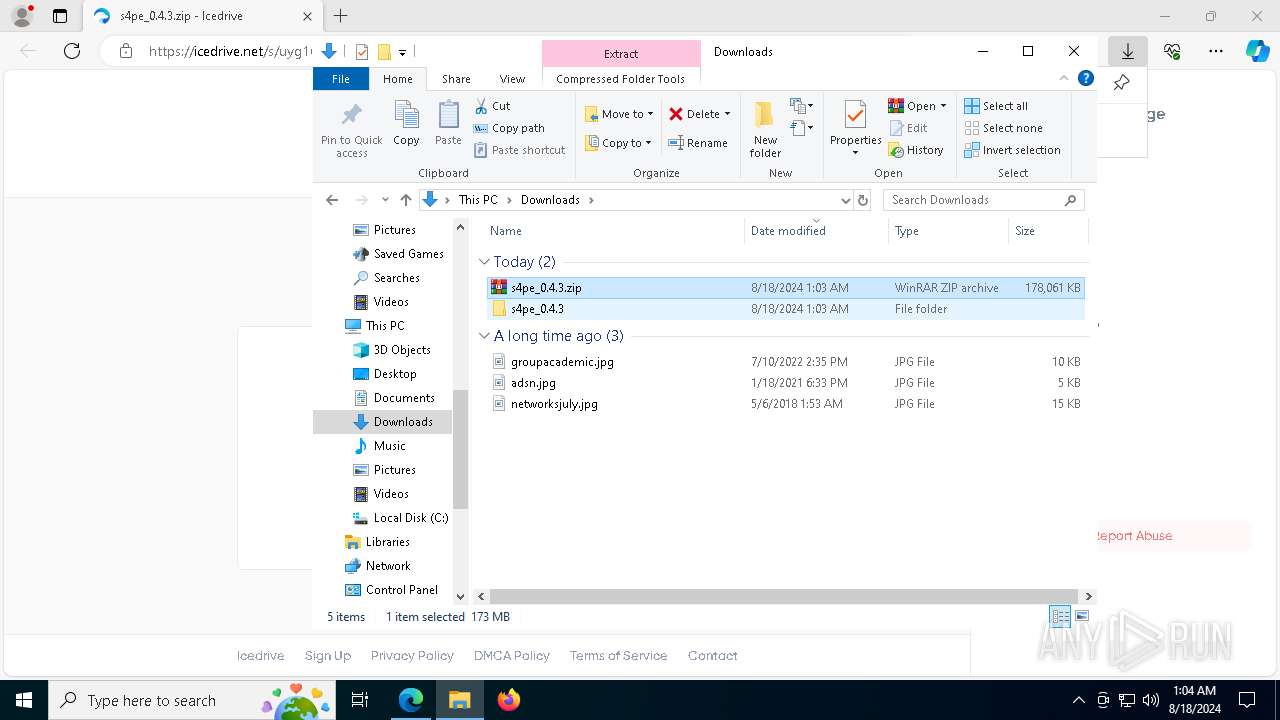
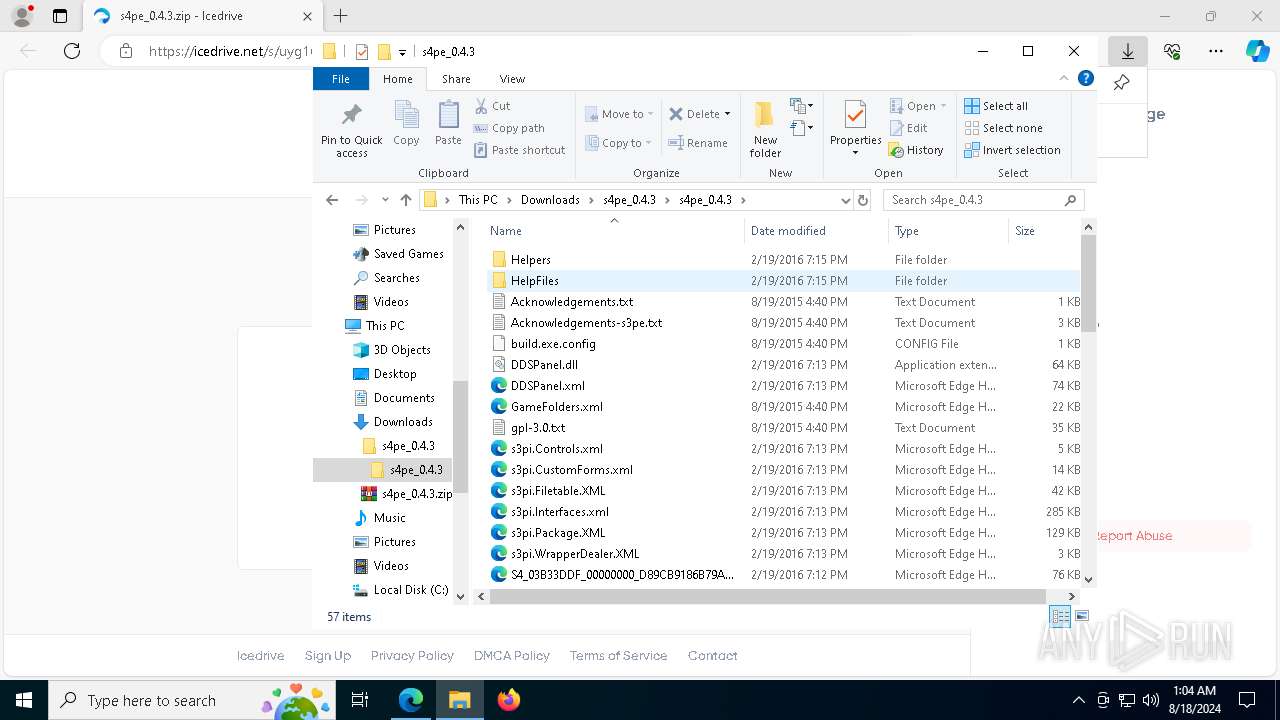
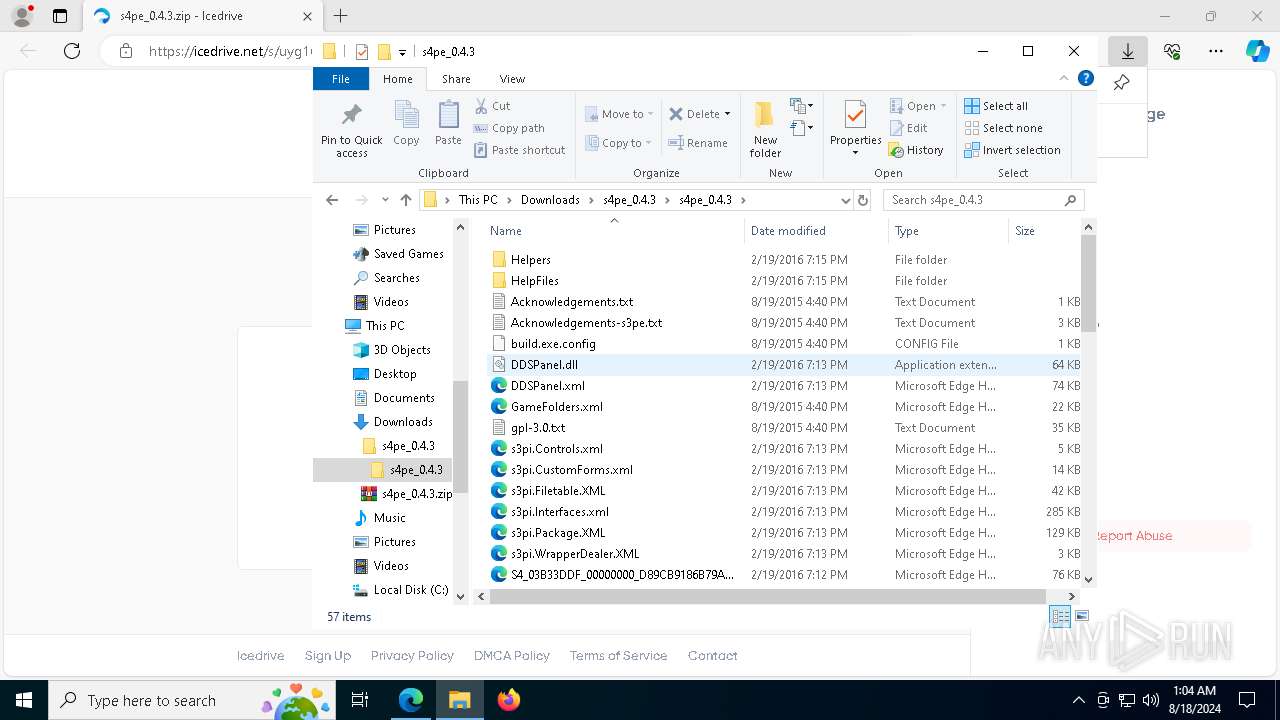
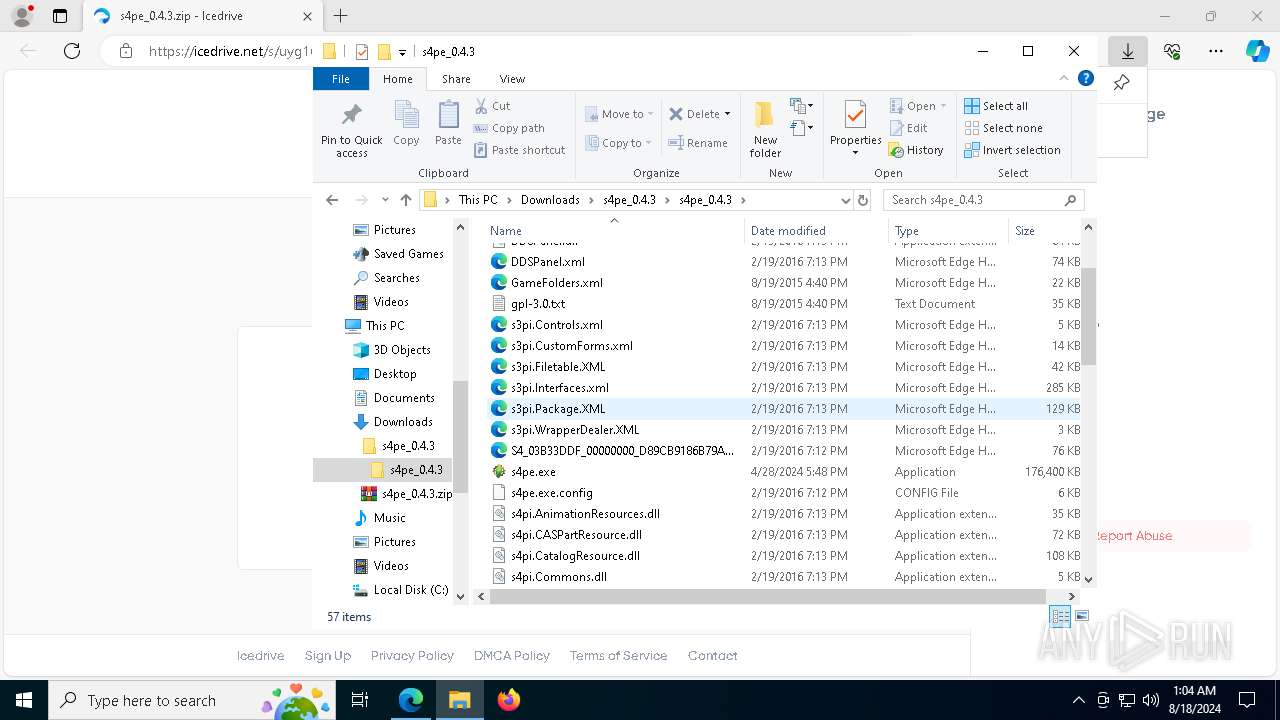
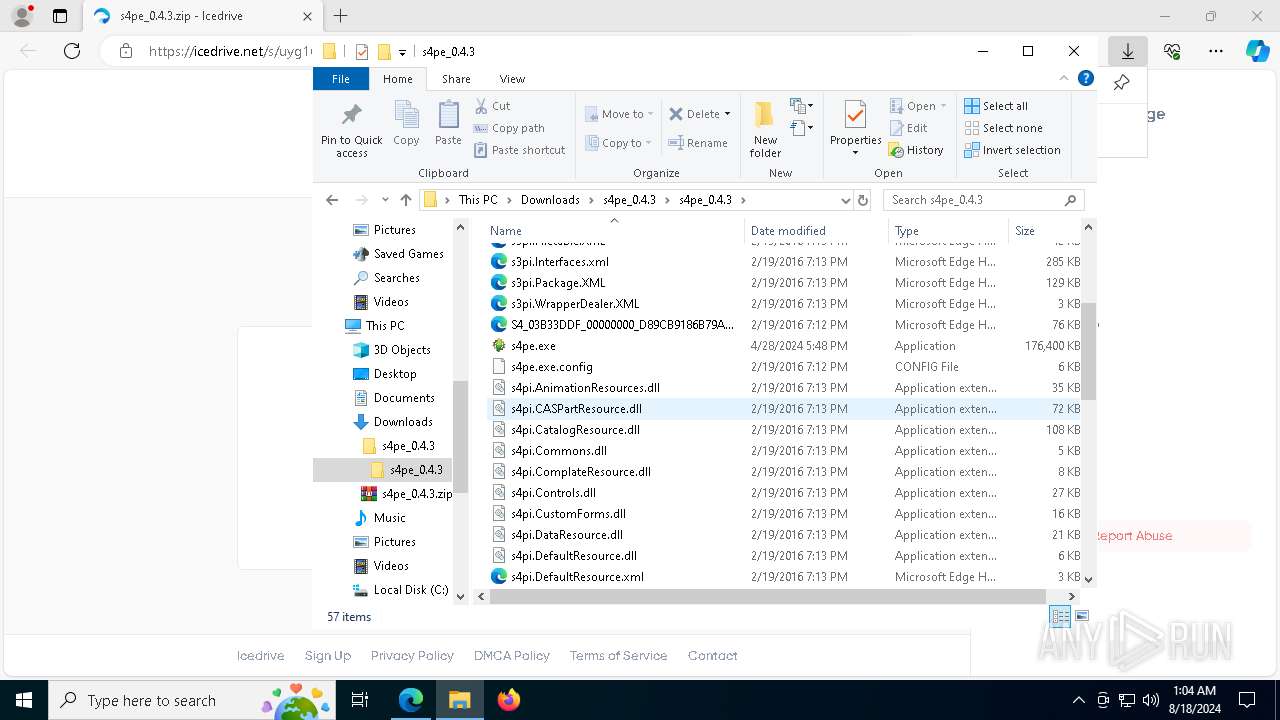
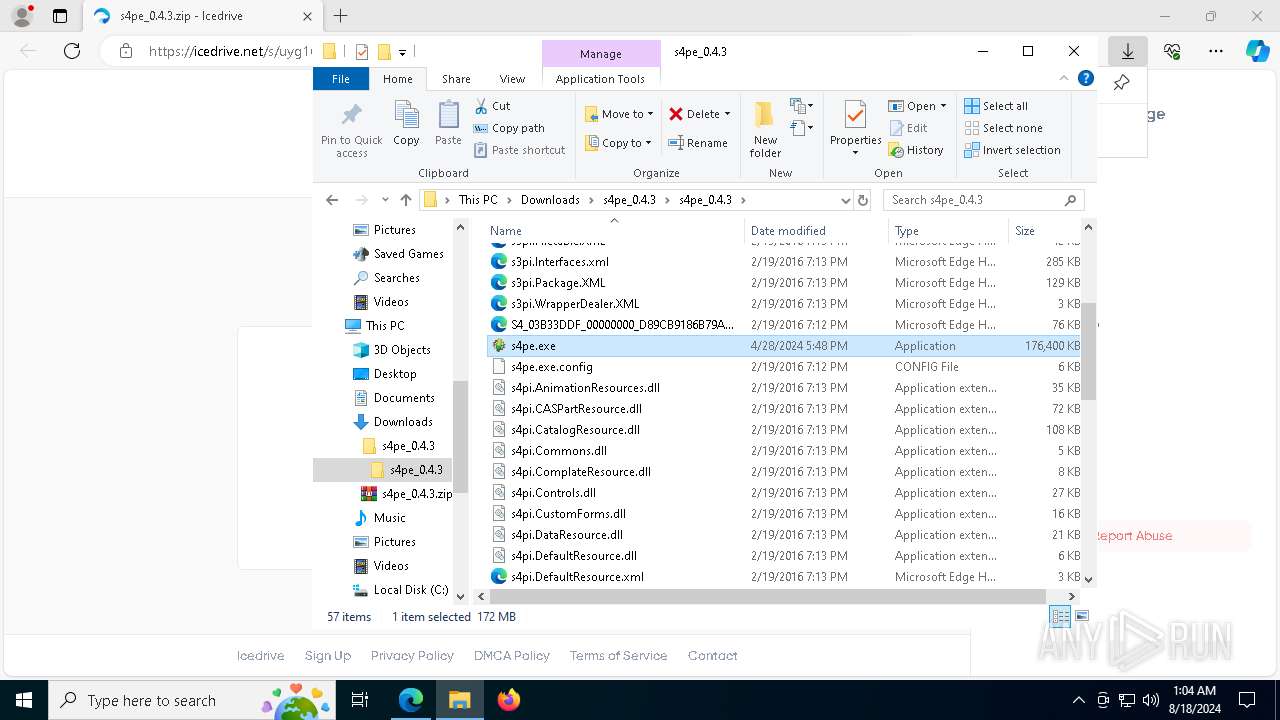
| URL: | https://icedrive.net/s/uyg1C5Q3WBh7wPhPBDaT8kD3jj9R |
| Full analysis: | https://app.any.run/tasks/75944081-abbb-4cb8-a5a3-8f890395b202 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
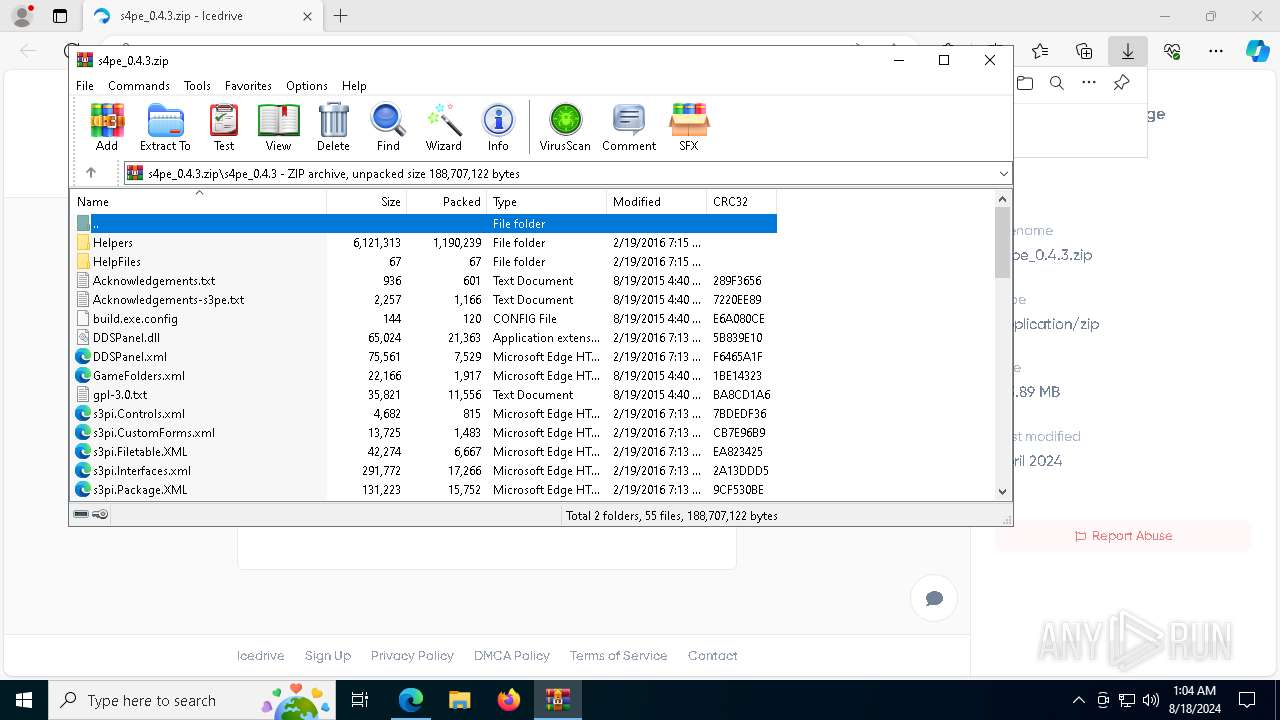
| Analysis date: | August 18, 2024, 01:01:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
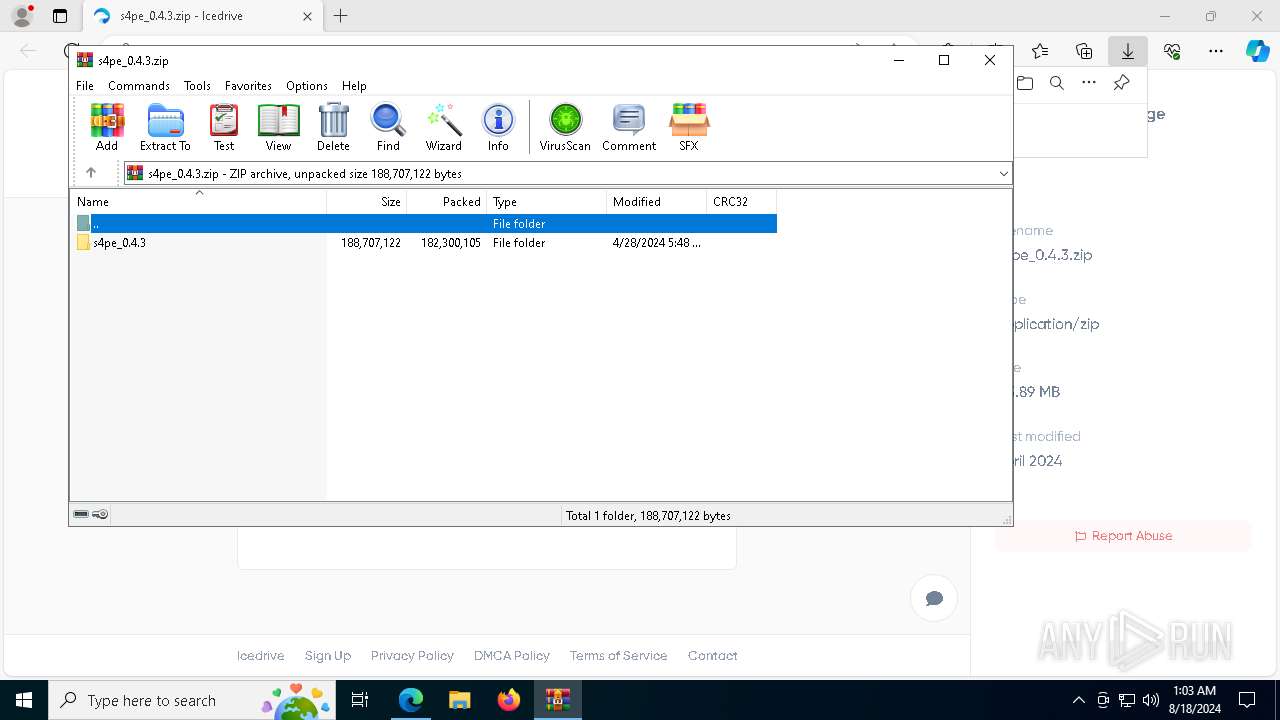
| MD5: | 31C953A25F5E4E858FBBC9DC22A6C3EC |
| SHA1: | 286B2F84BDE94B492AD08E3A373B8A96B73D9B3D |
| SHA256: | 5CB911164613221FA41C6E0AD5DAD7E385D49196F39FFECEC0571190B3A2AEF4 |
| SSDEEP: | 3:N82LHGV:2bV |
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 7884)
- net.exe (PID: 5028)
- net.exe (PID: 8184)
- net.exe (PID: 7228)
- net.exe (PID: 7520)
- net.exe (PID: 1748)
- net.exe (PID: 7856)
- net.exe (PID: 5624)
- net.exe (PID: 4192)
- net.exe (PID: 3876)
- net.exe (PID: 5408)
- net.exe (PID: 7672)
- net.exe (PID: 7400)
- net.exe (PID: 4280)
- net.exe (PID: 8096)
- net.exe (PID: 2136)
- net.exe (PID: 1116)
- cmd.exe (PID: 6012)
- net.exe (PID: 5172)
- net.exe (PID: 6124)
- net.exe (PID: 8184)
- net.exe (PID: 5484)
- net.exe (PID: 7720)
- net.exe (PID: 4316)
- net.exe (PID: 7740)
- net.exe (PID: 6608)
- net.exe (PID: 7872)
- net.exe (PID: 2572)
- net.exe (PID: 5992)
- net.exe (PID: 7884)
- net.exe (PID: 7988)
- net.exe (PID: 5028)
- net.exe (PID: 3164)
- net.exe (PID: 7096)
- net.exe (PID: 188)
- net.exe (PID: 3672)
- net.exe (PID: 7060)
- net.exe (PID: 7172)
- net.exe (PID: 5152)
- net.exe (PID: 876)
- net.exe (PID: 1692)
- net.exe (PID: 8124)
- net.exe (PID: 5744)
- net.exe (PID: 5988)
- net.exe (PID: 2628)
- net.exe (PID: 6080)
- net.exe (PID: 7332)
- net.exe (PID: 6276)
- net.exe (PID: 4316)
- net.exe (PID: 2080)
- net.exe (PID: 360)
- net.exe (PID: 3864)
- net.exe (PID: 2152)
- net.exe (PID: 2632)
- net.exe (PID: 7396)
- net.exe (PID: 6156)
- net.exe (PID: 8008)
- net.exe (PID: 4192)
- net.exe (PID: 7064)
- net.exe (PID: 3660)
- net.exe (PID: 2960)
- net.exe (PID: 5060)
- net.exe (PID: 2088)
- net.exe (PID: 4064)
- net.exe (PID: 1692)
- net.exe (PID: 8124)
- net.exe (PID: 4088)
- net.exe (PID: 6224)
- net.exe (PID: 2872)
- net.exe (PID: 7512)
- net.exe (PID: 2720)
- net.exe (PID: 1116)
- net.exe (PID: 7756)
- net.exe (PID: 1344)
- net.exe (PID: 7960)
- net.exe (PID: 7368)
- net.exe (PID: 2272)
- net.exe (PID: 7924)
- net.exe (PID: 5924)
- net.exe (PID: 7896)
- net.exe (PID: 1488)
- net.exe (PID: 6260)
- net.exe (PID: 6188)
- net.exe (PID: 7228)
- net.exe (PID: 6372)
- net.exe (PID: 7212)
- net.exe (PID: 7712)
- net.exe (PID: 1128)
- net.exe (PID: 2064)
- net.exe (PID: 7904)
- net.exe (PID: 208)
- net.exe (PID: 2272)
- net.exe (PID: 7608)
- net.exe (PID: 8016)
- net.exe (PID: 5284)
- net.exe (PID: 4280)
- net.exe (PID: 2472)
- net.exe (PID: 7828)
- net.exe (PID: 5116)
- net.exe (PID: 8124)
- net.exe (PID: 7512)
- net.exe (PID: 2872)
- net.exe (PID: 7948)
- net.exe (PID: 2340)
- net.exe (PID: 6180)
- net.exe (PID: 6224)
- net.exe (PID: 5172)
- net.exe (PID: 6176)
- net.exe (PID: 7232)
- net.exe (PID: 5052)
- net.exe (PID: 5140)
- net.exe (PID: 4308)
- net.exe (PID: 7440)
- net.exe (PID: 2572)
- net.exe (PID: 7692)
- net.exe (PID: 2472)
- net.exe (PID: 7632)
- net.exe (PID: 6936)
- net.exe (PID: 1108)
- net.exe (PID: 2080)
- net.exe (PID: 5060)
- net.exe (PID: 1608)
- net.exe (PID: 2872)
- net.exe (PID: 7312)
- net.exe (PID: 7512)
- net.exe (PID: 2768)
- net.exe (PID: 7908)
- net.exe (PID: 2136)
- net.exe (PID: 8020)
- net.exe (PID: 1132)
- net.exe (PID: 1184)
- net.exe (PID: 3372)
- net.exe (PID: 2396)
- net.exe (PID: 4692)
- net.exe (PID: 7556)
- net.exe (PID: 2400)
- net.exe (PID: 7876)
- net.exe (PID: 4784)
- net.exe (PID: 936)
- net.exe (PID: 3844)
- net.exe (PID: 4788)
- net.exe (PID: 4308)
- net.exe (PID: 460)
- net.exe (PID: 7548)
- net.exe (PID: 7064)
- net.exe (PID: 3880)
- net.exe (PID: 7328)
- net.exe (PID: 7156)
- net.exe (PID: 7608)
- net.exe (PID: 2136)
- net.exe (PID: 7480)
- net.exe (PID: 7148)
- net.exe (PID: 5552)
- net.exe (PID: 4544)
- net.exe (PID: 5304)
- net.exe (PID: 752)
- net.exe (PID: 7196)
- net.exe (PID: 1108)
- net.exe (PID: 5084)
- net.exe (PID: 6332)
- net.exe (PID: 2580)
- net.exe (PID: 7368)
- net.exe (PID: 7228)
- net.exe (PID: 3540)
- net.exe (PID: 2132)
- net.exe (PID: 7564)
- net.exe (PID: 1128)
- net.exe (PID: 3876)
- net.exe (PID: 6948)
- net.exe (PID: 7836)
- net.exe (PID: 1716)
- net.exe (PID: 1168)
- net.exe (PID: 7956)
- net.exe (PID: 4088)
- net.exe (PID: 2796)
- net.exe (PID: 2128)
- net.exe (PID: 7320)
- net.exe (PID: 4544)
- net.exe (PID: 7600)
- net.exe (PID: 7904)
- net.exe (PID: 7248)
- net.exe (PID: 1716)
- net.exe (PID: 7556)
- net.exe (PID: 7304)
- net.exe (PID: 7224)
- net.exe (PID: 2632)
- net.exe (PID: 1048)
- net.exe (PID: 5032)
- net.exe (PID: 6372)
- net.exe (PID: 6516)
- net.exe (PID: 6316)
- net.exe (PID: 400)
- net.exe (PID: 5904)
- net.exe (PID: 1656)
- net.exe (PID: 3256)
- net.exe (PID: 1884)
- net.exe (PID: 7656)
- net.exe (PID: 7368)
- net.exe (PID: 7532)
- net.exe (PID: 7520)
- net.exe (PID: 6948)
- net.exe (PID: 5904)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 6012)
- net.exe (PID: 5028)
Uses NET.EXE to stop Windows Defender service
- cmd.exe (PID: 6012)
- net.exe (PID: 8184)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 6012)
- net.exe (PID: 7228)
Uses Task Scheduler to run other applications
- clipper.exe (PID: 7644)
Create files in the Startup directory
- clipper.exe (PID: 7644)
Adds extension to the Windows Defender exclusion list
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Modifies hosts file to block updates
- BidenSucks.exe (PID: 7236)
Application was injected by another process
- svchost.exe (PID: 1272)
- svchost.exe (PID: 476)
- svchost.exe (PID: 1036)
- lsass.exe (PID: 768)
- winlogon.exe (PID: 684)
- dwm.exe (PID: 852)
- svchost.exe (PID: 1364)
- svchost.exe (PID: 1316)
- svchost.exe (PID: 1200)
- svchost.exe (PID: 1408)
- svchost.exe (PID: 1208)
- svchost.exe (PID: 1620)
- svchost.exe (PID: 1508)
- svchost.exe (PID: 1472)
- svchost.exe (PID: 1628)
- svchost.exe (PID: 1872)
- svchost.exe (PID: 1816)
- svchost.exe (PID: 2072)
- svchost.exe (PID: 1864)
- svchost.exe (PID: 2000)
- svchost.exe (PID: 2344)
- svchost.exe (PID: 2412)
- svchost.exe (PID: 2304)
- svchost.exe (PID: 2312)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 1588)
- svchost.exe (PID: 1796)
- svchost.exe (PID: 1600)
- svchost.exe (PID: 2996)
- spoolsv.exe (PID: 2592)
- svchost.exe (PID: 2496)
- svchost.exe (PID: 2692)
- svchost.exe (PID: 2788)
- OfficeClickToRun.exe (PID: 2656)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 3012)
- svchost.exe (PID: 2968)
- svchost.exe (PID: 3084)
- svchost.exe (PID: 3220)
- svchost.exe (PID: 3340)
- svchost.exe (PID: 3496)
- svchost.exe (PID: 3260)
- svchost.exe (PID: 3200)
- svchost.exe (PID: 3304)
- svchost.exe (PID: 2184)
- svchost.exe (PID: 2160)
- svchost.exe (PID: 3020)
- svchost.exe (PID: 4184)
- explorer.exe (PID: 4552)
- sihost.exe (PID: 4112)
- svchost.exe (PID: 4140)
- svchost.exe (PID: 3408)
- svchost.exe (PID: 5416)
- svchost.exe (PID: 4808)
- ctfmon.exe (PID: 4356)
- RuntimeBroker.exe (PID: 5560)
- svchost.exe (PID: 4332)
- svchost.exe (PID: 4532)
- MoUsoCoreWorker.exe (PID: 2120)
- svchost.exe (PID: 4324)
- RuntimeBroker.exe (PID: 4244)
- RuntimeBroker.exe (PID: 776)
- dllhost.exe (PID: 5568)
- svchost.exe (PID: 3888)
- svchost.exe (PID: 4300)
- dllhost.exe (PID: 3312)
- svchost.exe (PID: 5036)
- uhssvc.exe (PID: 536)
- svchost.exe (PID: 1824)
- svchost.exe (PID: 5236)
- svchost.exe (PID: 5256)
- svchost.exe (PID: 4000)
- UserOOBEBroker.exe (PID: 2744)
- svchost.exe (PID: 2096)
- svchost.exe (PID: 3276)
- svchost.exe (PID: 3376)
- WmiPrvSE.exe (PID: 3980)
- ApplicationFrameHost.exe (PID: 4052)
- svchost.exe (PID: 2092)
- svchost.exe (PID: 7864)
- WmiPrvSE.exe (PID: 8048)
Runs injected code in another process
- dialer.exe (PID: 3864)
- dialer.exe (PID: 872)
Antivirus name has been found in the command line (generic signature)
- taskkill.exe (PID: 8032)
- taskkill.exe (PID: 7632)
- taskkill.exe (PID: 3116)
- taskkill.exe (PID: 3900)
- taskkill.exe (PID: 7320)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2256)
SUSPICIOUS
Reads the date of Windows installation
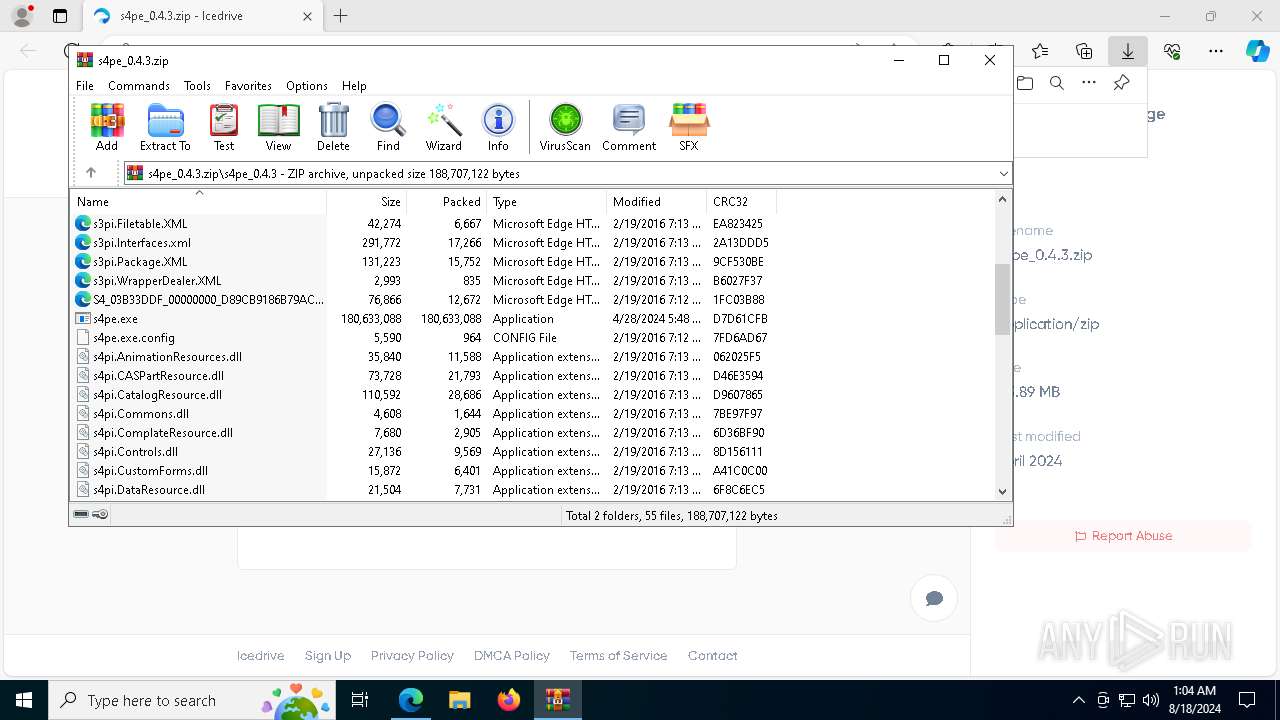
- s4pe.exe (PID: 4772)
- SystemAnalysis.exe (PID: 4080)
- clipper.exe (PID: 7644)
BASE64 encoded PowerShell command has been detected
- s4pe.exe (PID: 4772)
Base64-obfuscated command line is found
- s4pe.exe (PID: 4772)
Starts POWERSHELL.EXE for commands execution
- s4pe.exe (PID: 4772)
- BidenSucks.exe (PID: 7328)
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Executable content was dropped or overwritten
- s4pe.exe (PID: 4772)
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Drops the executable file immediately after the start
- s4pe.exe (PID: 4772)
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Drops a system driver (possible attempt to evade defenses)
- s4pe.exe (PID: 4772)
- lrxaytgrgkta.exe (PID: 5144)
Reads security settings of Internet Explorer
- SystemAnalysis.exe (PID: 4080)
- s4pe.exe (PID: 4772)
- clipper.exe (PID: 7644)
Starts CMD.EXE for commands execution
- SystemAnalysis.exe (PID: 4080)
- clipper.exe (PID: 7644)
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Executing commands from a ".bat" file
- SystemAnalysis.exe (PID: 4080)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6012)
Modifies existing scheduled task
- schtasks.exe (PID: 8124)
- schtasks.exe (PID: 8100)
- schtasks.exe (PID: 1356)
- schtasks.exe (PID: 5600)
- schtasks.exe (PID: 3028)
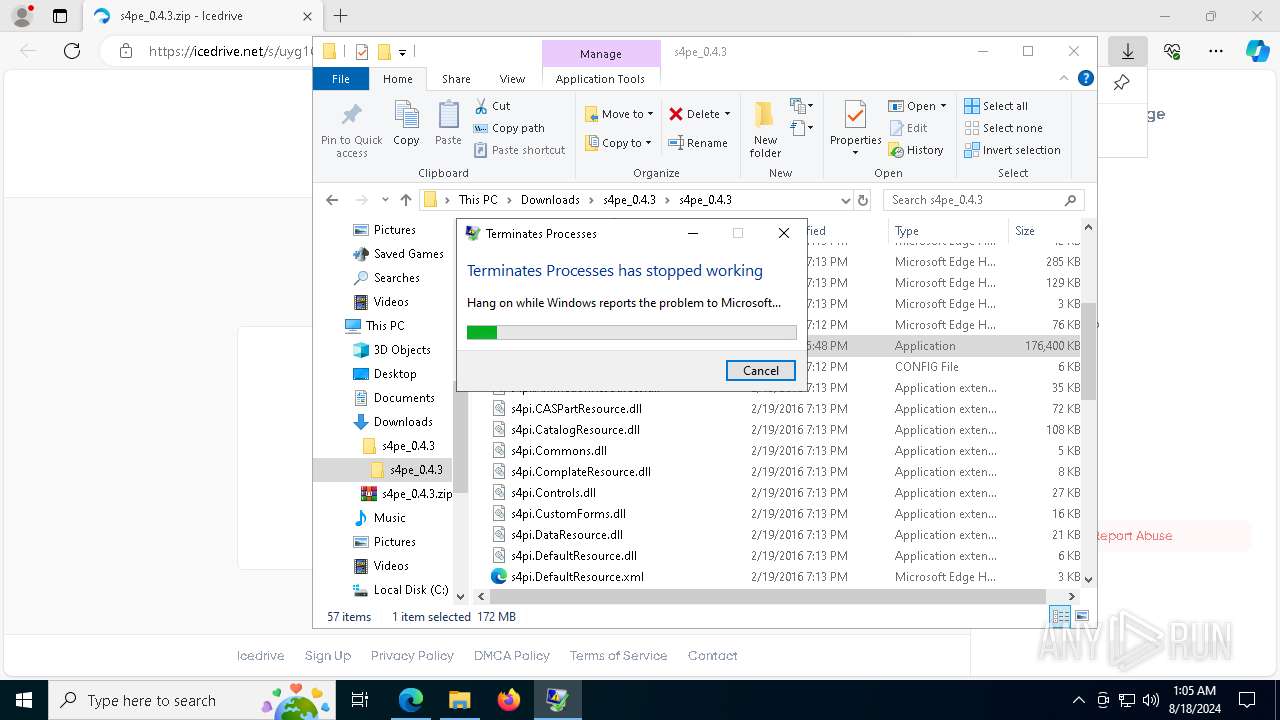
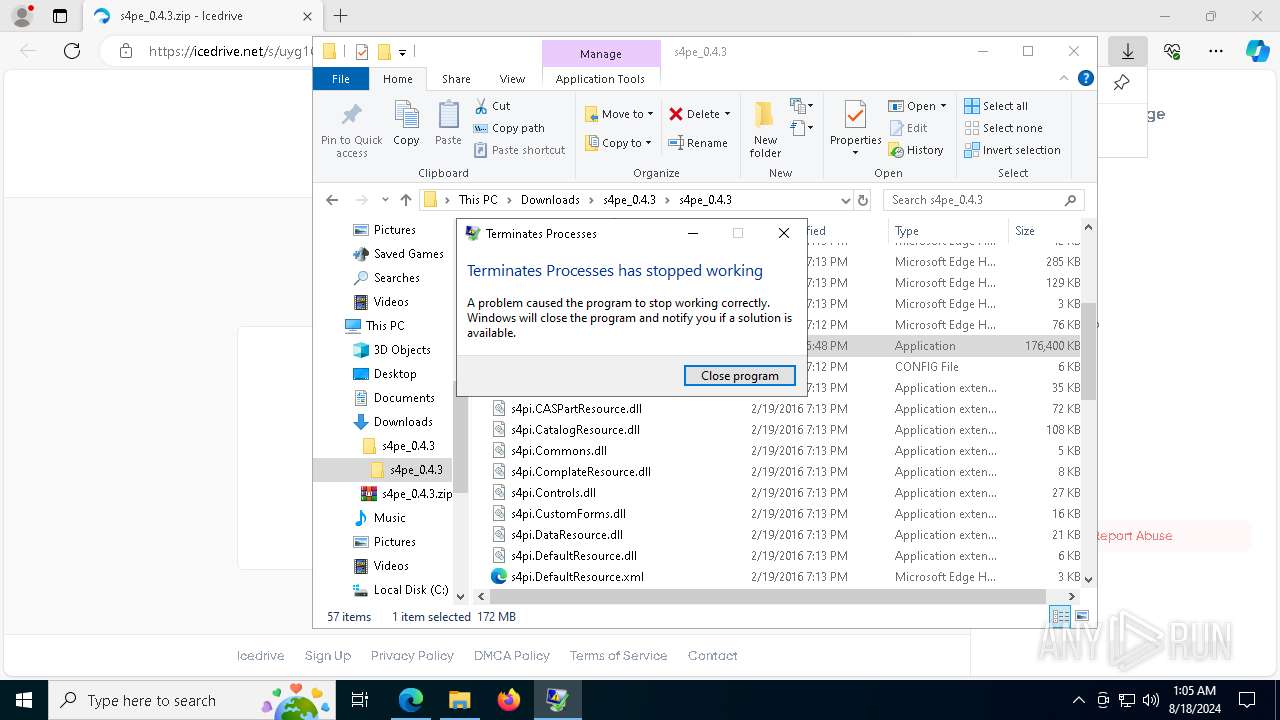
Executes application which crashes
- s4pe.exe (PID: 4692)
- taskkill.exe (PID: 2204)
Process drops python dynamic module
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
Powershell scripting: start process
- BidenSucks.exe (PID: 7328)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7344)
Process drops legitimate windows executable
- Rflower.exe (PID: 7952)
- s4pe.exe (PID: 4772)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
- svchost.exe (PID: 5236)
The process drops C-runtime libraries
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 6012)
Starts a Microsoft application from unusual location
- clipper.exe (PID: 7644)
The process creates files with name similar to system file names
- clipper.exe (PID: 7644)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6012)
Starts itself from another location
- clipper.exe (PID: 7644)
Executing commands from ".cmd" file
- clipper.exe (PID: 7644)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7736)
Script adds exclusion path to Windows Defender
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Script adds exclusion extension to Windows Defender
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 6012)
Process uninstalls Windows update
- wusa.exe (PID: 1784)
- wusa.exe (PID: 7840)
Executes as Windows Service
- lrxaytgrgkta.exe (PID: 5144)
Starts SC.EXE for service management
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Uses powercfg.exe to modify the power settings
- BidenSucks.exe (PID: 7236)
- lrxaytgrgkta.exe (PID: 5144)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2256)
Found regular expressions for crypto-addresses (YARA)
- Usermode Font Driver Host.exe (PID: 1104)
INFO
Checks supported languages
- identity_helper.exe (PID: 5484)
- SystemAnalysis.exe (PID: 4080)
- s4pe.exe (PID: 4772)
- Terminator.exe (PID: 5084)
- Rflower.exe (PID: 7952)
- s4pe.exe (PID: 4692)
- BidenSucks.exe (PID: 7328)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
- BidenSucks.exe (PID: 7236)
- Usermode Font Driver Host.exe (PID: 1104)
- lrxaytgrgkta.exe (PID: 5144)
Application launched itself
- msedge.exe (PID: 6376)
Reads Environment values
- identity_helper.exe (PID: 5484)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2304)
- explorer.exe (PID: 4552)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6376)
- OfficeClickToRun.exe (PID: 2656)
Creates files in the program directory
- MoUsoCoreWorker.exe (PID: 2120)
- svchost.exe (PID: 3376)
- BidenSucks.exe (PID: 7236)
Reads the time zone
- svchost.exe (PID: 2692)
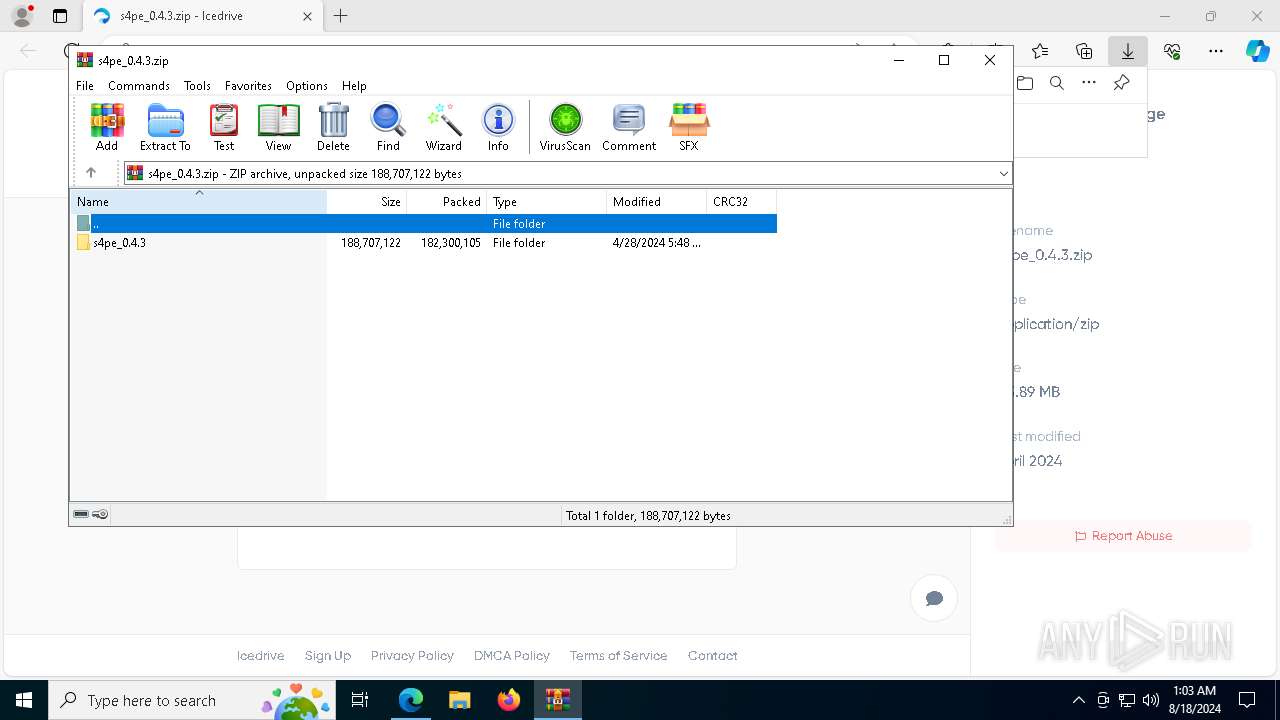
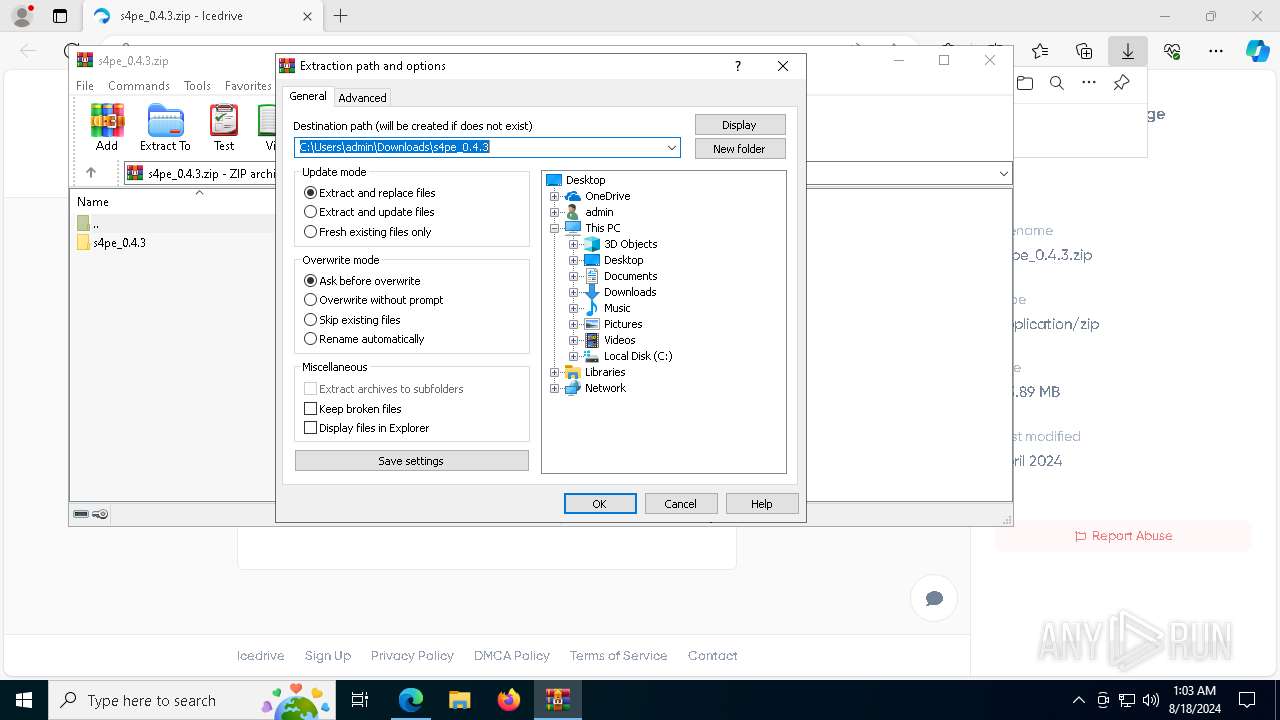
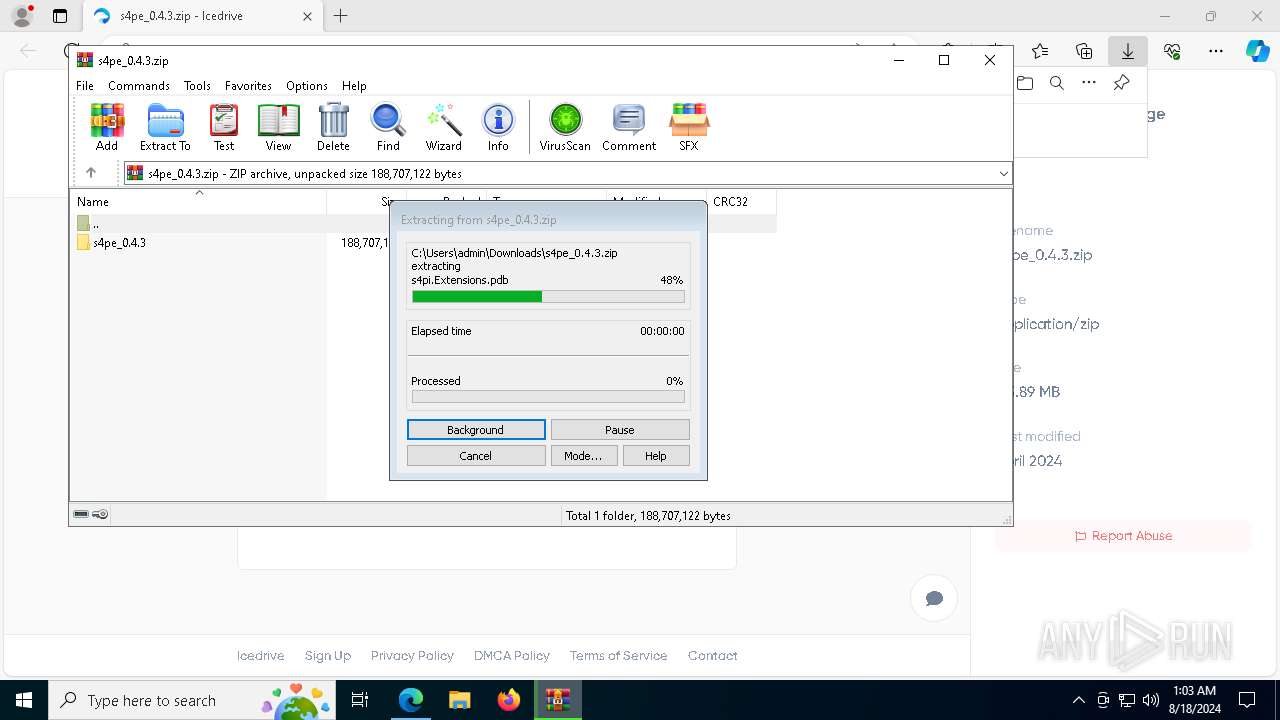
The process uses the downloaded file
- WinRAR.exe (PID: 7968)
- msedge.exe (PID: 7844)
- msedge.exe (PID: 6376)
Reads the computer name
- identity_helper.exe (PID: 5484)
- SystemAnalysis.exe (PID: 4080)
- s4pe.exe (PID: 4772)
- s4pe.exe (PID: 4692)
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
- Usermode Font Driver Host.exe (PID: 1104)
Reads the software policy settings
- OfficeClickToRun.exe (PID: 2656)
- lsass.exe (PID: 768)
- WerFault.exe (PID: 7396)
- WerFault.exe (PID: 8028)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7968)
Process checks computer location settings
- s4pe.exe (PID: 4772)
- SystemAnalysis.exe (PID: 4080)
- clipper.exe (PID: 7644)
Create files in a temporary directory
- s4pe.exe (PID: 4772)
- SystemAnalysis.exe (PID: 4080)
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
- clipper.exe (PID: 7644)
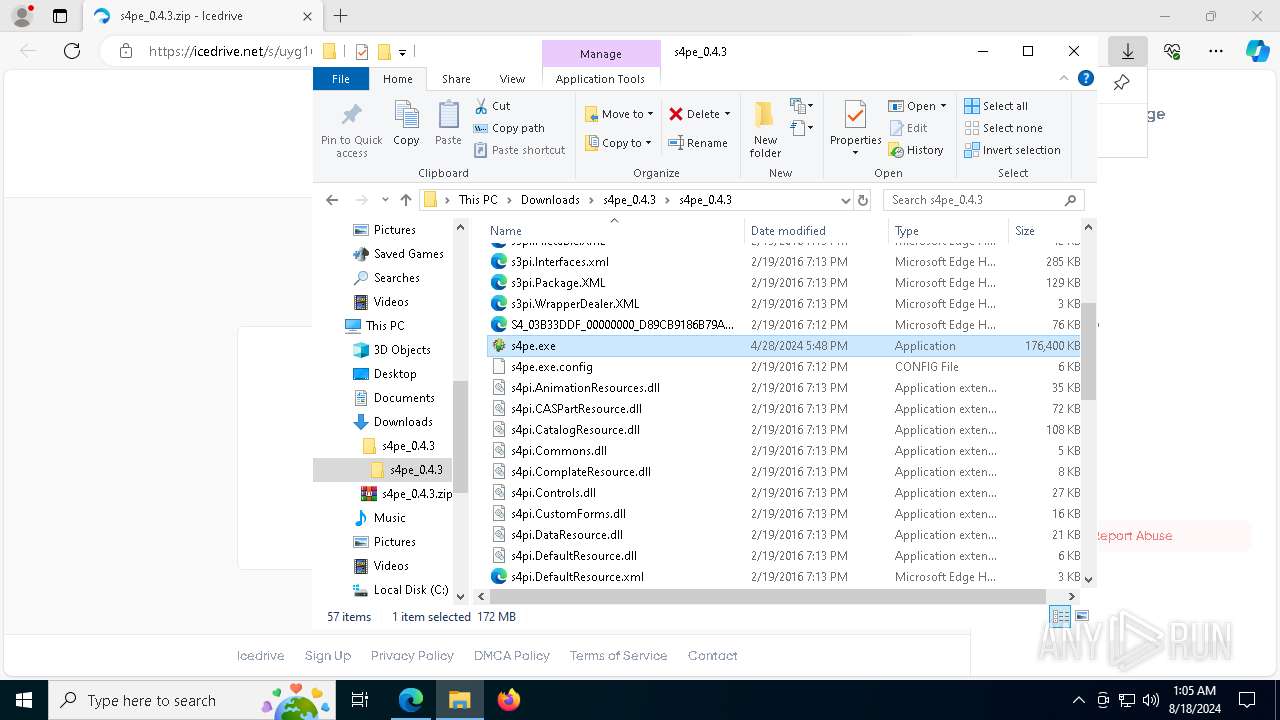
Manual execution by a user
- s4pe.exe (PID: 4772)
Checks proxy server information
- WerFault.exe (PID: 7396)
- WerFault.exe (PID: 8028)
Creates files or folders in the user directory
- WerFault.exe (PID: 7396)
- clipper.exe (PID: 7644)
- explorer.exe (PID: 4552)
- WerFault.exe (PID: 8028)
The executable file from the user directory is run by the Powershell process
- BidenSucks.exe (PID: 7236)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6636)
- powershell.exe (PID: 7984)
- powershell.exe (PID: 5388)
Reads the machine GUID from the registry
- Usermode Font Driver Host.exe (PID: 1104)
Checks transactions between databases Windows and Oracle
- WmiPrvSE.exe (PID: 8048)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6636)
- powershell.exe (PID: 7984)
- powershell.exe (PID: 5388)
PyInstaller has been detected (YARA)
- Rflower.exe (PID: 7952)
- source_prepared.exe (PID: 7604)
UPX packer has been detected
- Rflower.exe (PID: 7952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
913
Monitored processes
853
Malicious processes
93
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | net stop Avsched32 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | taskkill /f /t /im Agnitum Outpost Firewall | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | net stop IOMON98 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\net1 stop NAVAPW32 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | taskkill /f /t /im Cleaner3.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4336 --field-trial-handle=2536,i,13784421013167060299,530461526640120548,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 360 | net stop CLEANER3 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | C:\WINDOWS\system32\net1 stop ICSUPP95 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5216 --field-trial-handle=2536,i,13784421013167060299,530461526640120548,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
196 676
Read events
195 487
Write events
839
Delete events
350
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502C6 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6376) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
705
Suspicious files
463
Text files
1 902
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe5494.TMP | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe5494.TMP | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe54a3.TMP | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe54a3.TMP | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe5494.TMP | — | |
MD5:— | SHA256:— | |||
| 6376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
75
DNS requests
72
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8032 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | binary | 1.09 Kb | whitelisted |
7720 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
8032 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | binary | 1.80 Kb | whitelisted |
7228 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
8032 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | binary | 2.49 Kb | whitelisted |
8032 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | binary | 4.99 Kb | whitelisted |
8032 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | binary | 10.9 Kb | whitelisted |
8032 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b794342e-59ba-4ce6-87da-b8bc5e6ce532?P1=1724486467&P2=404&P3=2&P4=M2xYqR8Mm5sMxOcrYm2B6ZoKX8JjYWWy0c4%2bcutw2zclU3%2bQq9zoF7Jtc5S1IiQufm5NaHg6agZuxjHqmXpIow%3d%3d | DE | — | — | whitelisted |
3276 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8032 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68fecda8-3692-48b1-92f7-722862b2bb34?P1=1724352206&P2=404&P3=2&P4=aWTK5CrTSfcYG%2fQrL6mGOzhRE4FrDYD3naiFDVI89PqH6haql2%2b0xzzXQGDTyUSLA%2faE9FSb4ZKqfo59i6okTw%3d%3d | DE | binary | 9.98 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4084 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6376 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6712 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6712 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6712 | msedge.exe | 104.22.4.172:443 | icedrive.net | CLOUDFLARENET | — | unknown |
6712 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
icedrive.net |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
cdn.icedrive.net |
| unknown |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |