| File name: | SecuriteInfo.com.Win32.Malware-gen.24050.20684 |
| Full analysis: | https://app.any.run/tasks/74d456e0-4d84-4994-87a5-b03a59fe5c60 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 19, 2025, 02:08:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
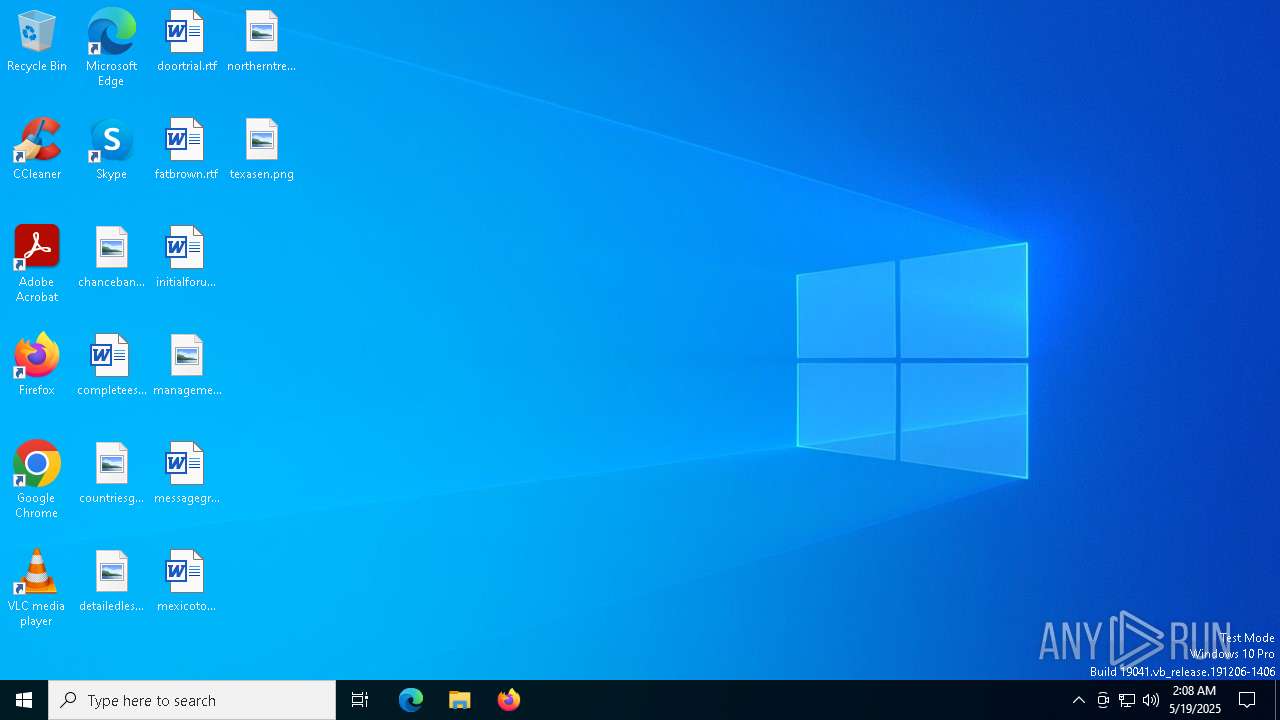
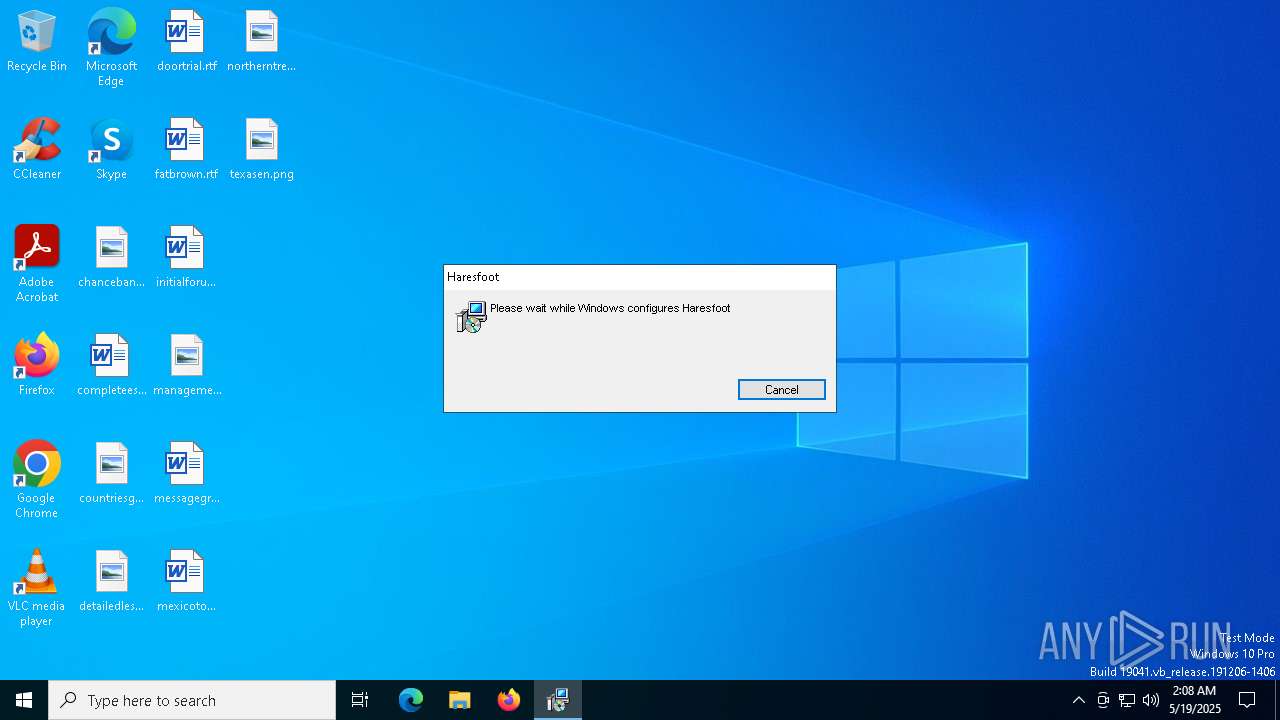
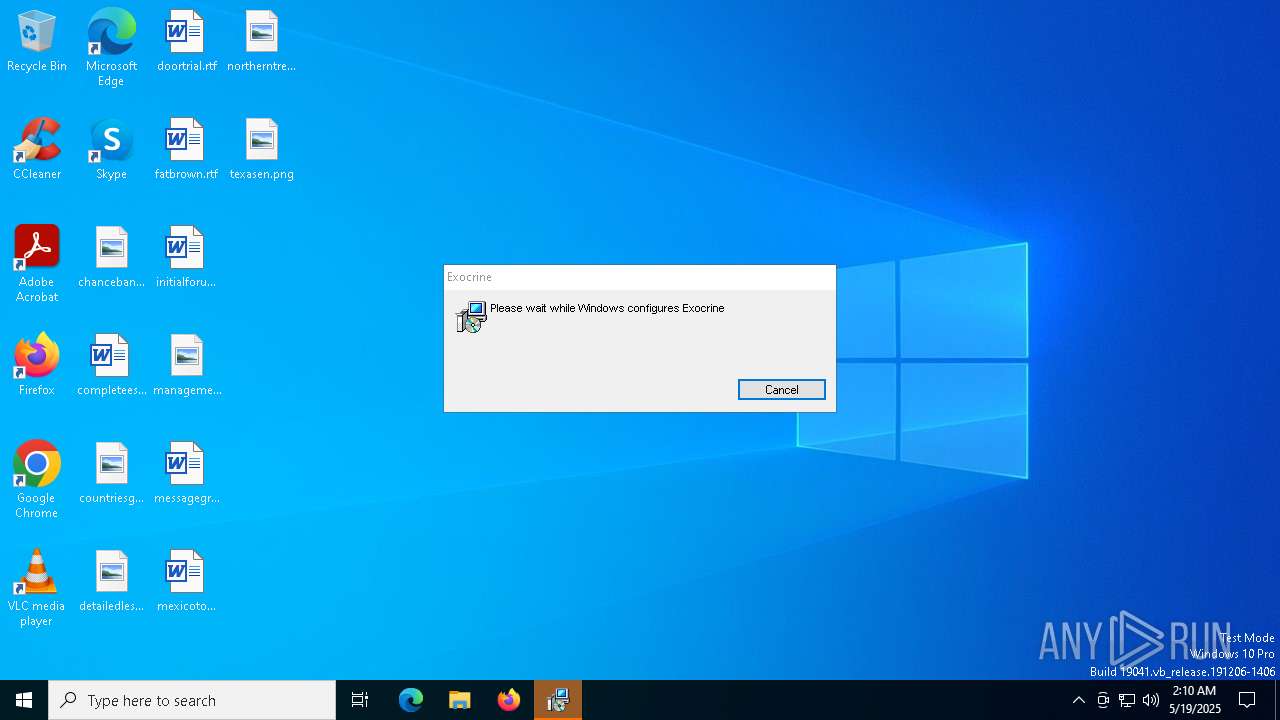
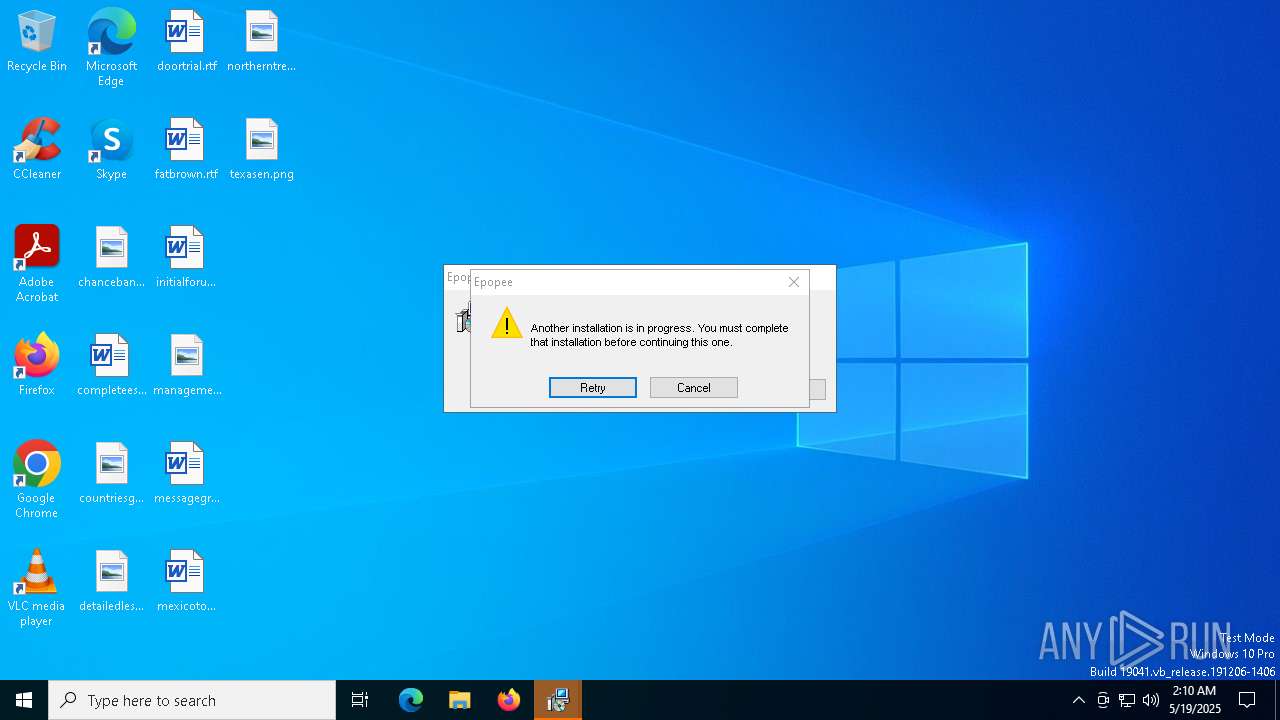
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Haresfoot, Author: Royal Sago, Keywords: Installer, Comments: This installer database contains the logic and data required to install Haresfoot., Template: Intel;1033, Revision Number: {71B4DCC1-8B49-48FD-91C3-056E1BABEE03}, Create Time/Date: Tue May 13 07:23:28 2025, Last Saved Time/Date: Tue May 13 07:23:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | E84DB67F8F30CD4BA03A0C9E6952628B |
| SHA1: | C24C01CC464DB661EC5F5910411B7049793FC1E6 |
| SHA256: | 5CA4552216DDC3B276E3CF2684CC5041B31931181A54D5CB62113BF6AABA1575 |
| SSDEEP: | 98304:t7KltuUF/1KdhUj+Rt2URMTUOyV59Avpj31mvrBvSSRkYhYYzjOMrdBg5HJKxqi3:tu3aAt6twV7WIps |
MALICIOUS
Executing a file with an untrusted certificate
- SF32.exe (PID: 8124)
- SF32.exe (PID: 8180)
- SF32.exe (PID: 6272)
- ISBEW64.exe (PID: 5324)
- ISBEW64.exe (PID: 1328)
- ISBEW64.exe (PID: 3176)
- ISBEW64.exe (PID: 3240)
- ISBEW64.exe (PID: 1532)
- ISBEW64.exe (PID: 680)
- Hashrate_Vorte.exe (PID: 300)
- Hashrate_Vorte.exe (PID: 7528)
- Hashrate_Vorte.exe (PID: 1168)
- Hashrate_Vorte.exe (PID: 7936)
- ByteS.exe (PID: 1748)
Known privilege escalation attack
- dllhost.exe (PID: 5608)
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 7484)
Stealers network behavior
- svchost.exe (PID: 7484)
Run PowerShell with an invisible window
- powershell.exe (PID: 7744)
PURECRYPTER has been detected (SURICATA)
- ByteS.exe (PID: 1748)
Bypass execution policy to execute commands
- powershell.exe (PID: 7744)
Connects to the CnC server
- AddInProcess.exe (PID: 7596)
- ThrIndex.exe (PID: 2596)
AMADEY has been detected (SURICATA)
- ThrIndex.exe (PID: 2596)
MINER has been detected (SURICATA)
- AddInProcess.exe (PID: 7596)
Starts NET.EXE for service management
- ThrIndex.exe (PID: 2596)
- net.exe (PID: 6228)
SUSPICIOUS
Starts itself from another location
- SF32.exe (PID: 8124)
- 5T~.exe (PID: 5216)
- Hashrate_Vorte.exe (PID: 300)
- Hashrate_Vorte.exe (PID: 1168)
Executable content was dropped or overwritten
- SF32.exe (PID: 8124)
- SF32.exe (PID: 6272)
- svchost.exe (PID: 7484)
- 5T~.exe (PID: 5216)
- 5T~.exe (PID: 4784)
- Hashrate_Vorte.exe (PID: 300)
- Hashrate_Vorte.exe (PID: 1168)
- Hashrate_Vorte.exe (PID: 7528)
- Hashrate_Vorte.exe (PID: 7936)
Starts CMD.EXE for commands execution
- SF32.exe (PID: 8180)
- SF32.exe (PID: 6272)
- Hashrate_Vorte.exe (PID: 7936)
- Hashrate_Vorte.exe (PID: 7528)
Connects to unusual port
- svchost.exe (PID: 736)
- svchost.exe (PID: 7484)
- ByteS.exe (PID: 1748)
- AddInProcess.exe (PID: 7596)
The process drops C-runtime libraries
- 5T~.exe (PID: 4784)
- Hashrate_Vorte.exe (PID: 300)
- Hashrate_Vorte.exe (PID: 1168)
- msiexec.exe (PID: 5936)
Process drops legitimate windows executable
- 5T~.exe (PID: 4784)
- Hashrate_Vorte.exe (PID: 300)
- msiexec.exe (PID: 5936)
- Hashrate_Vorte.exe (PID: 1168)
Starts a Microsoft application from unusual location
- Hashrate_Vorte.exe (PID: 300)
Contacting a server suspected of hosting an CnC
- ByteS.exe (PID: 1748)
- ThrIndex.exe (PID: 2596)
The process executes via Task Scheduler
- powershell.exe (PID: 7744)
Potential Corporate Privacy Violation
- AddInProcess.exe (PID: 7596)
Connects to the server without a host name
- ThrIndex.exe (PID: 2596)
Uses NETSH.EXE to change the status of the firewall
- ThrIndex.exe (PID: 2596)
Sets the service to start on system boot
- sc.exe (PID: 3008)
Starts SC.EXE for service management
- ThrIndex.exe (PID: 2596)
Executes as Windows Service
- VSSVC.exe (PID: 6708)
INFO
An automatically generated document
- msiexec.exe (PID: 6964)
Manages system restore points
- SrTasks.exe (PID: 7992)
- SrTasks.exe (PID: 7868)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5936)
The sample compiled with english language support
- SF32.exe (PID: 8124)
- SF32.exe (PID: 6272)
- svchost.exe (PID: 7484)
- 5T~.exe (PID: 5216)
- 5T~.exe (PID: 4784)
- Hashrate_Vorte.exe (PID: 300)
- Hashrate_Vorte.exe (PID: 7528)
- Hashrate_Vorte.exe (PID: 1168)
- msiexec.exe (PID: 5936)
Application launched itself
- chrome.exe (PID: 7684)
- msedge.exe (PID: 2344)
- msedge.exe (PID: 1164)
- msedge.exe (PID: 2064)
Manual execution by a user
- msedge.exe (PID: 2064)
- AddInProcess.exe (PID: 7596)
Checks supported languages
- msiexec.exe (PID: 5936)
Reads the computer name
- msiexec.exe (PID: 5936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Haresfoot |
| Author: | Royal Sago |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Haresfoot. |
| Template: | Intel;1033 |
| RevisionNumber: | {71B4DCC1-8B49-48FD-91C3-056E1BABEE03} |
| CreateDate: | 2025:05:13 07:23:28 |
| ModifyDate: | 2025:05:13 07:23:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
244
Monitored processes
98
Malicious processes
16
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Users\admin\AppData\Local\Temp\{E8135466-157F-49F2-BE3C-44D065774E07}\{E02EEFBE-0BA0-4A6B-A29F-9D745D25DC19}\Hashrate_Vorte.exe | C:\Users\admin\AppData\Local\Temp\{E8135466-157F-49F2-BE3C-44D065774E07}\{E02EEFBE-0BA0-4A6B-A29F-9D745D25DC19}\Hashrate_Vorte.exe | 5T~.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft OneNote Exit code: 0 Version: 14.0.4763.1000 Modules
| |||||||||||||||
| 300 | C:\WINDOWS\system32\net1 start termservice | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chr2F27.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chr2F27.tmp\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x288,0x28c,0x290,0x280,0x298,0x7ffc87aa5fd8,0x7ffc87aa5fe4,0x7ffc87aa5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | C:\Users\admin\AppData\Local\Temp\{E8135466-157F-49F2-BE3C-44D065774E07}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{95749809-5AB5-480F-B4C0-8A8377D09AFF} | C:\Users\admin\AppData\Local\Temp\{E8135466-157F-49F2-BE3C-44D065774E07}\ISBEW64.exe | — | 5T~.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.58 Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2584 --field-trial-handle=2420,i,10407675014433805836,17900930530976624411,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3580 --field-trial-handle=1888,i,15671742074733676458,9668807729503252384,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3772 --field-trial-handle=1888,i,15671742074733676458,9668807729503252384,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1168 | "C:\Users\admin\AppData\Local\Traipse\Hashrate_Vorte.exe" | C:\Users\admin\AppData\Local\Traipse\Hashrate_Vorte.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft OneNote Exit code: 0 Version: 14.0.4763.1000 Modules
| |||||||||||||||
Total events
25 485
Read events
24 903
Write events
542
Delete events
40
Modification events
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000B97DADED62C8DB013017000074170000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000B97DADED62C8DB013017000074170000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000B1BF05EE62C8DB013017000074170000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000007E2308EE62C8DB013017000074170000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000098730AEE62C8DB013017000074170000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A43C0FEE62C8DB013017000074170000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5936) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6708) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000027D404EF62C8DB01341A000004150000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006B3707EF62C8DB01341A00007C1C0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006B3707EF62C8DB01341A0000F0010000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
53
Suspicious files
267
Text files
93
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5936 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5936 | msiexec.exe | C:\Windows\Installer\111838.msi | — | |
MD5:— | SHA256:— | |||
| 5936 | msiexec.exe | C:\Windows\Installer\11183a.msi | — | |
MD5:— | SHA256:— | |||
| 5936 | msiexec.exe | C:\Windows\Installer\MSI1B07.tmp | binary | |
MD5:8A0D20A72958B829DB5CEA7316150241 | SHA256:26D72092649E1ADC80F2DADD07158EBA00F522504DA67A1B5B83094B8F5599C2 | |||
| 5936 | msiexec.exe | C:\Windows\Temp\~DF12C868421643A2B7.TMP | binary | |
MD5:5FB9DC3B5C2E467C7F79D52D4168A3E8 | SHA256:AD0D280D74E1E16CE7F77A002B0158D3CE765F0F77543676E92156F69B49A526 | |||
| 5936 | msiexec.exe | C:\Windows\Temp\~DF89D7E7E8DAECDCF8.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 5936 | msiexec.exe | C:\Users\admin\AppData\Local\Diphtheria\SF32.exe | executable | |
MD5:1F166F5C76EB155D44DD1BF160F37A6A | SHA256:2D13424B09BA004135A26CCD60B64CDD6917D80CE43070CBC114569EAE608588 | |||
| 5936 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:5FB9DC3B5C2E467C7F79D52D4168A3E8 | SHA256:AD0D280D74E1E16CE7F77A002B0158D3CE765F0F77543676E92156F69B49A526 | |||
| 5936 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{756f26c7-fc6d-4802-85ce-b706c7e5b406}_OnDiskSnapshotProp | binary | |
MD5:820C7BD6EF7A7400821E261822FB72B4 | SHA256:AD1D8FC4AFE9B6755F6747B3A915D3986ECC2ADDF35FF12D0C59EB484ADE0F82 | |||
| 5936 | msiexec.exe | C:\Users\admin\AppData\Local\Diphtheria\sqlite3.dll | executable | |
MD5:90ED24DFD07D01E63F0E78F2B3F5AB54 | SHA256:38042B5C4CD510F35E5D619FC8DE11B687C5ED935FFA209426937F47CD84E7D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
81
DNS requests
60
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2596 | ThrIndex.exe | POST | 200 | 196.251.89.67:80 | http://196.251.89.67/Di0Her478/index.php | unknown | — | — | unknown |
7148 | svchost.exe | HEAD | 200 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747701582&P2=404&P3=2&P4=cp7pe6%2f5JSYgB9%2fr6NEOfZewgQBQGucGj6nhOqsoixbixbXz1csyEYqYuCh9cHYUOmGGwOirXmFQruJ%2feft6tw%3d%3d | unknown | — | — | whitelisted |
2596 | ThrIndex.exe | POST | 200 | 196.251.89.67:80 | http://196.251.89.67/Di0Her478/index.php | unknown | — | — | unknown |
2596 | ThrIndex.exe | POST | 200 | 196.251.89.67:80 | http://196.251.89.67/Di0Her478/index.php | unknown | — | — | unknown |
7148 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747701582&P2=404&P3=2&P4=cp7pe6%2f5JSYgB9%2fr6NEOfZewgQBQGucGj6nhOqsoixbixbXz1csyEYqYuCh9cHYUOmGGwOirXmFQruJ%2feft6tw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
736 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
7484 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
7484 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
1748 | ByteS.exe | Malware Command and Control Activity Detected | LOADER [ANY.RUN] PureLoader Download Attempt (LOAD) |
2596 | ThrIndex.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 41 |
2596 | ThrIndex.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
7596 | AddInProcess.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
2596 | ThrIndex.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2596 | ThrIndex.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
2596 | ThrIndex.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |