| File name: | fresh.msi |
| Full analysis: | https://app.any.run/tasks/e93b005f-fce7-4a2b-9967-2bce3c5a4df6 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 11, 2019, 12:01:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Title: Exe to msi converter free, Author: www.exetomsi.com, Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0 |
| MD5: | 0FD934C1C2A35B2B685D1E23285C9AB1 |
| SHA1: | 879A0CF167ED1E78B87BED754BAD7DE29848AD90 |
| SHA256: | 5C9C882A4D2160978378B5FC431873EFE9560C309C0AA7EC42ECE982B17669CD |
| SSDEEP: | 6144:iEKC6urtW9MRPnCRRQ48Cm8dBouHk0jQuKkyh3v39AQflcVv39Fh1x0TqI6:iEKbMBtv8dtfsv9AQdW3Tfx+ |
MALICIOUS
Changes the autorun value in the registry
- NETSTAT.EXE (PID: 2224)
Actions looks like stealing of personal data
- NETSTAT.EXE (PID: 2224)
FORMBOOK was detected
- explorer.exe (PID: 276)
- NETSTAT.EXE (PID: 2224)
- Firefox.exe (PID: 3112)
Connects to CnC server
- explorer.exe (PID: 276)
Stealing of credential data
- NETSTAT.EXE (PID: 2224)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 2868)
Executed via COM
- DrvInst.exe (PID: 3968)
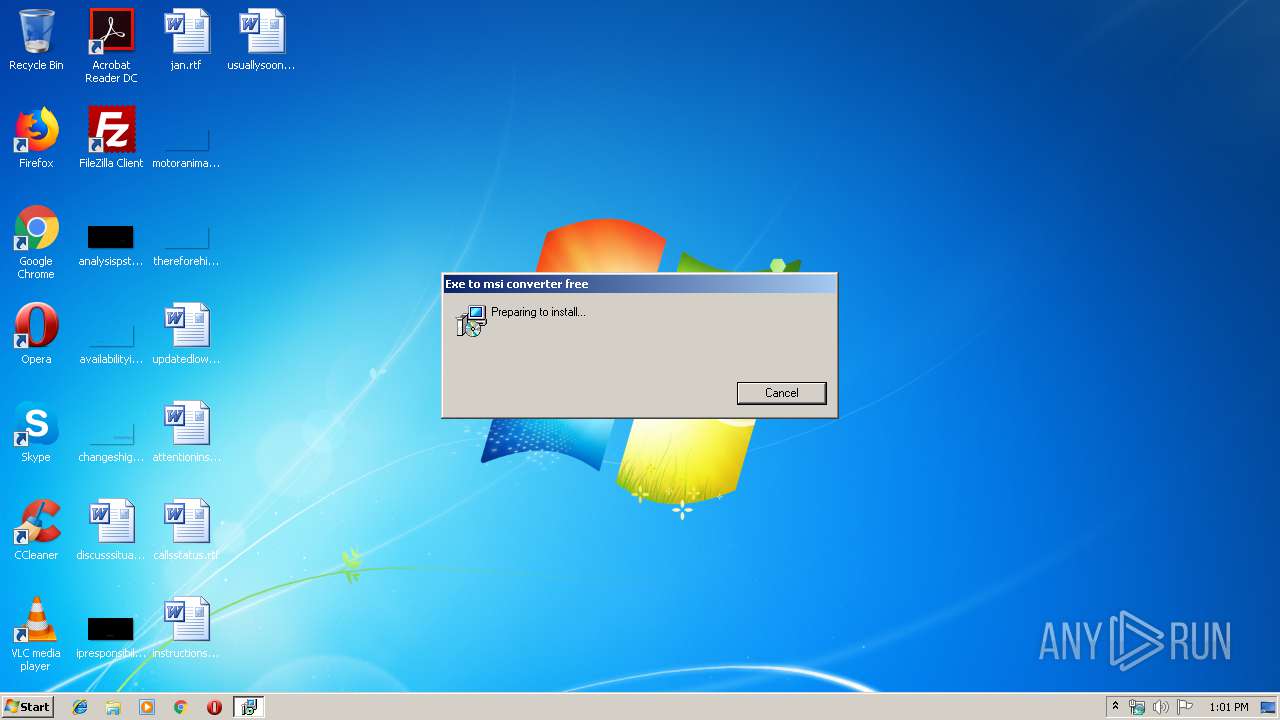
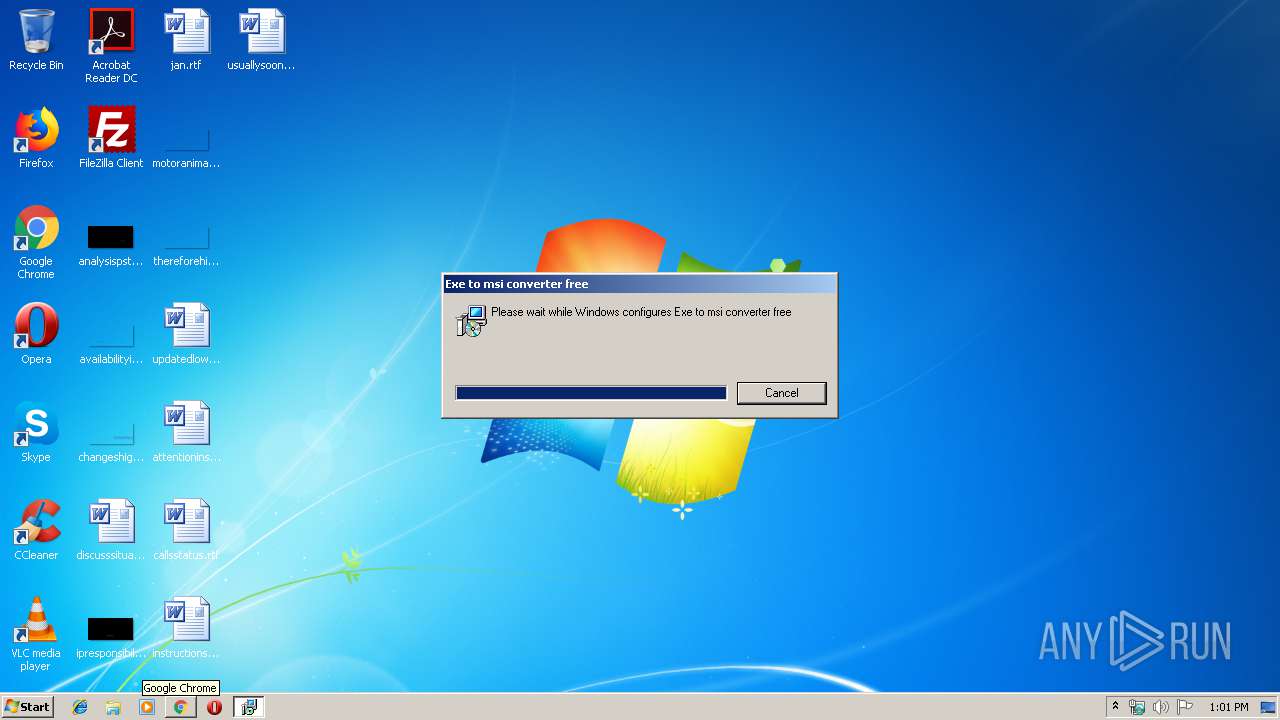
Starts Microsoft Installer
- explorer.exe (PID: 276)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3012)
Drop ExeToMSI Application
- msiexec.exe (PID: 3012)
Loads DLL from Mozilla Firefox
- NETSTAT.EXE (PID: 2224)
Starts CMD.EXE for commands execution
- NETSTAT.EXE (PID: 2224)
Uses NETSTAT.EXE to discover network connections
- explorer.exe (PID: 276)
Creates files in the user directory
- NETSTAT.EXE (PID: 2224)
INFO
Searches for installed software
- msiexec.exe (PID: 3012)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2868)
Application was dropped or rewritten from another process
- MSID836.tmp (PID: 2776)
- MSID836.tmp (PID: 2364)
Starts application with an unusual extension
- msiexec.exe (PID: 3012)
- MSID836.tmp (PID: 2776)
Application launched itself
- MSID836.tmp (PID: 2776)
Manual execution by user
- NETSTAT.EXE (PID: 2224)
Reads the hosts file
- NETSTAT.EXE (PID: 2224)
Creates files in the user directory
- Firefox.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Title: | Exe to msi converter free |
| Subject: | - |
| Author: | www.exetomsi.com |
| Keywords: | - |
| Comments: | - |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
Total processes
45
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Windows\System32\NETSTAT.EXE" | C:\Windows\System32\NETSTAT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\Installer\MSID836.tmp" | C:\Windows\Installer\MSID836.tmp | MSID836.tmp | ||||||||||||
User: SYSTEM Company: TRANSPLANT4HADES8 Integrity Level: SYSTEM Description: TRANSPLANT4Woolstock3 Exit code: 0 Version: 1.05.0006 Modules
| |||||||||||||||
| 2776 | "C:\Windows\Installer\MSID836.tmp" | C:\Windows\Installer\MSID836.tmp | — | msiexec.exe | |||||||||||
User: admin Company: TRANSPLANT4HADES8 Integrity Level: MEDIUM Description: TRANSPLANT4Woolstock3 Exit code: 0 Version: 1.05.0006 Modules
| |||||||||||||||
| 2868 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | /c del "C:\Windows\Installer\MSID836.tmp" | C:\Windows\System32\cmd.exe | — | NETSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | NETSTAT.EXE | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3424 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\fresh.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000005B8" "000002D4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
511
Read events
330
Write events
169
Delete events
12
Modification events
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3012) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000442671A19868D501C40B00006C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3012) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000442671A19868D501C40B00006C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3012) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (3012) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000DED3BFA19868D501C40B00006C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3012) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000DED3BFA19868D501C40B000044090000E8030000010000000000000000000000D890AEBEF5D04E4FB4E57F4F03263EB20000000000000000 | |||
| (PID) Process: | (2868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FA21CEA19868D501340B0000B8090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FA21CEA19868D501340B0000900D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FA21CEA19868D501340B0000880D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FA21CEA19868D501340B0000AC090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
88
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFAC5415D6356CA344.TMP | — | |
MD5:— | SHA256:— | |||
| 2868 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\Config.Msi\16d1cf.rbs | — | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFBDADD2061C7517BB.TMP | — | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\Windows\Installer\16d1ce.ipi | binary | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{beae90d8-d0f5-4f4e-b4e5-7f4f03263eb2}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3968 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 3012 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2224 | NETSTAT.EXE | C:\Users\admin\AppData\Roaming\7K93541E\7K9logrc.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
13
DNS requests
9
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
276 | explorer.exe | GET | — | 162.241.253.144:80 | http://www.sunnyandfree.com/do/?T8wXJlW=28oisobrpnp4gzKjm/boXKBSHoGcFzk4SjUKa11vZDD0tae8IjxWygsnTuOyZ7e+d+DFlw==&-ZBXn=1bvHF&sql=1 | US | — | — | malicious |
276 | explorer.exe | GET | — | 50.63.202.41:80 | http://www.rudyglez.com/do/?T8wXJlW=NUZflwQlIgwvsGdabocXY66awDa+UhvvRcnXrd95V9Re/eAN77dEtzEu8Kw2JipIWKvMQg==&-ZBXn=1bvHF&sql=1 | US | — | — | malicious |
276 | explorer.exe | POST | — | 52.1.217.30:80 | http://www.steveshydrationinfo.us/do/ | US | — | — | malicious |
276 | explorer.exe | GET | 302 | 199.34.228.176:80 | http://www.luxzurybeauty.com/do/?T8wXJlW=J04Wm4XAgNqxU/f2fTNxULpSFQma1vU1ns2/SuCcwDgYu9DDVg+gEbFp+DcYAFa2tbtO8w==&-ZBXn=1bvHF | US | html | 372 b | malicious |
276 | explorer.exe | GET | 404 | 52.1.217.30:80 | http://www.steveshydrationinfo.us/do/?T8wXJlW=tUQy/CN+oh/pJdgHdZybN09IuGYN30K0D+zl0Y11kMtDopqGKOP6t705t7QRc/PC8D4T2g==&-ZBXn=1bvHF&sql=1 | US | html | 2.53 Kb | malicious |
276 | explorer.exe | POST | — | 52.1.217.30:80 | http://www.steveshydrationinfo.us/do/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 52.1.217.30:80 | http://www.steveshydrationinfo.us/do/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 162.241.253.144:80 | http://www.sunnyandfree.com/do/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 162.241.253.144:80 | http://www.sunnyandfree.com/do/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 162.241.253.144:80 | http://www.sunnyandfree.com/do/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
276 | explorer.exe | 52.1.217.30:80 | www.steveshydrationinfo.us | Amazon.com, Inc. | US | malicious |
276 | explorer.exe | 199.34.228.176:80 | www.luxzurybeauty.com | Weebly, Inc. | US | malicious |
276 | explorer.exe | 162.241.253.144:80 | www.sunnyandfree.com | CyrusOne LLC | US | malicious |
276 | explorer.exe | 50.63.202.41:80 | www.rudyglez.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.luxzurybeauty.com |
| malicious |
www.xn--5brp51b2jpe3i.com |
| unknown |
www.lupayiwu33.party |
| unknown |
www.steveshydrationinfo.us |
| malicious |
www.ggexp.info |
| unknown |
www.basantstudiojodhpur.com |
| unknown |
www.sunnyandfree.com |
| malicious |
www.rudyglez.com |
| malicious |
www.kitchencastle.win |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
9 ETPRO signatures available at the full report