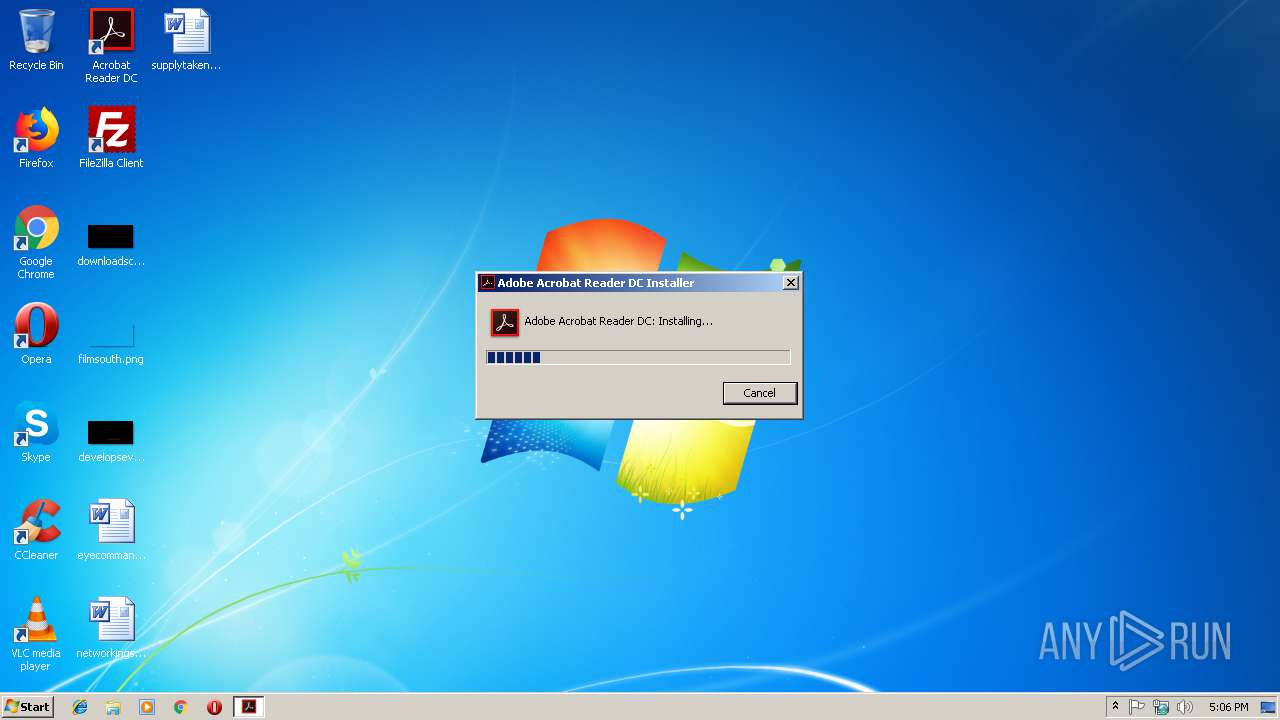
| File name: | readerdc_en_la_cra_install.exe |
| Full analysis: | https://app.any.run/tasks/24fc8da1-9f68-4269-9b7f-7aba834c3ad6 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | December 14, 2018, 17:06:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 90CAC3D16BC59B3DB6C46DF15A7F42A0 |
| SHA1: | F375D77CCDDD65FEFD08EBB8834434FCCDDB0D6A |
| SHA256: | 5C23EB19DB84A7FC1755040C6CDFEC6D2DC83920385C340B95217DD7752C7C6B |
| SSDEEP: | 98304:2ZKRLLDsklIABTcZhlvvIgxmgaRJUxkm7uq1whNFLOAkGkzdnEVomFHKnPj:5/I9h/km7uq6FLOyomFHKnPj |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:13 02:19:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1483776 |
| InitializedDataSize: | 2650624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1366dd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.96.32 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.160 |
| ProductName: | Adobe Download Manager |
| ProductVersion: | 2.0.0.160s |
| LegalCopyright: | Copyright 2015 Adobe Systems Incorporated |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Dec-2018 01:19:54 |
| Detected languages: |
|
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.160 |
| ProductName: | Adobe Download Manager |
| ProductVersion: | 2.0.0.160s |
| LegalCopyright: | Copyright 2015 Adobe Systems Incorporated |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 13-Dec-2018 01:19:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0016A34D | 0x0016A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53442 |
.rdata | 0x0016C000 | 0x00052BEC | 0x00052C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22293 |
.data | 0x001BF000 | 0x0000C5B0 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77621 |
.tls | 0x001CC000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x001CD000 | 0x00208CF8 | 0x00208E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.47364 |
.reloc | 0x003D6000 | 0x0001EEE4 | 0x0001F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.48008 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09453 | 1214 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.96764 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 5.19833 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.1197 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.63736 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.74274 | 180 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.34038 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.34004 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 2.51649 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
0
Monitored processes
0
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.106.215.179:80 | http://statistic.data-akamai.com/eYVU | US | binary | 191 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.106.215.179:80 | statistic.data-akamai.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
-sPEzZc.vortex-update.com |
| unknown |
statistic.data-akamai.com |
| malicious |
28993.pnt.data-akamai.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN [PTsecurity] Possible Cobalt Strike payload |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike payload |