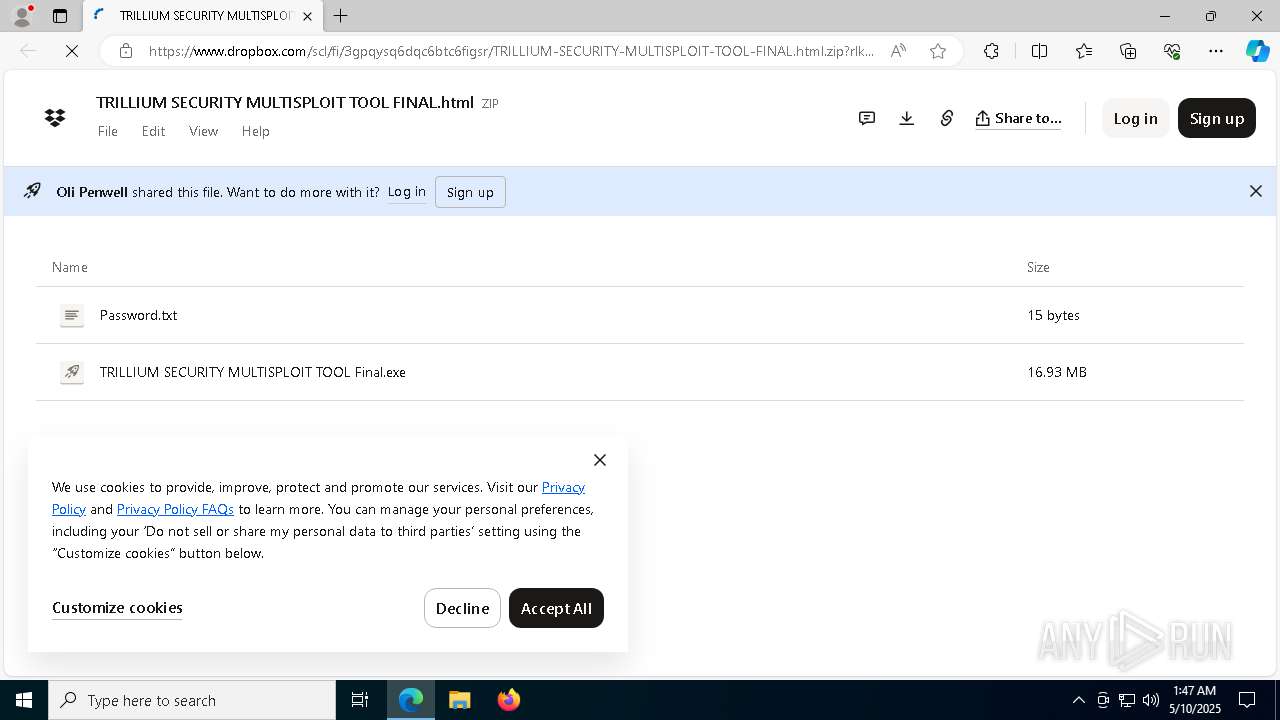
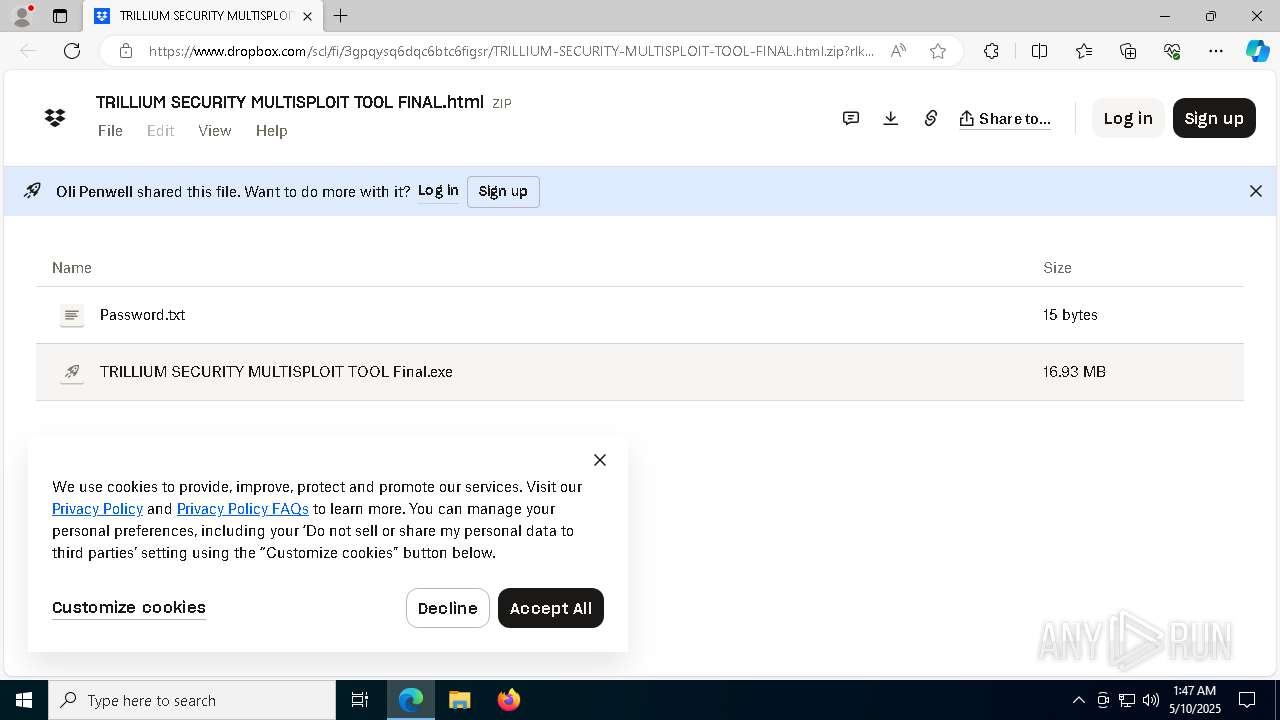
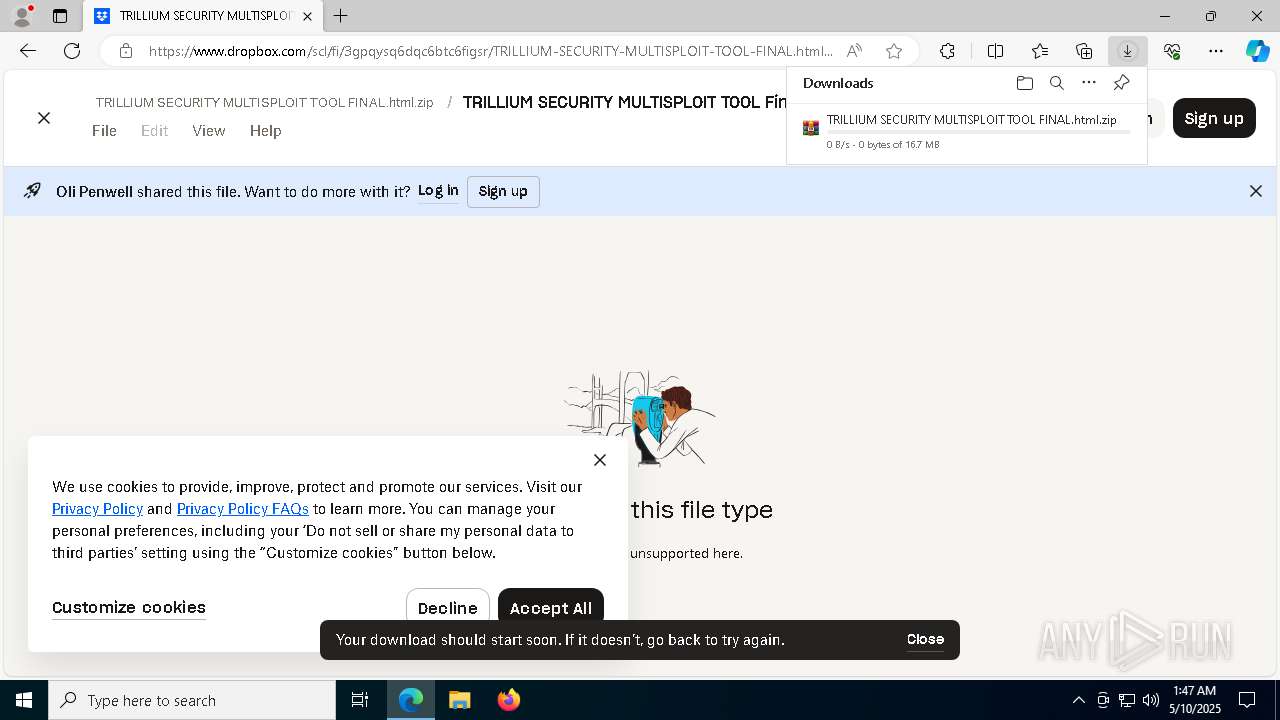
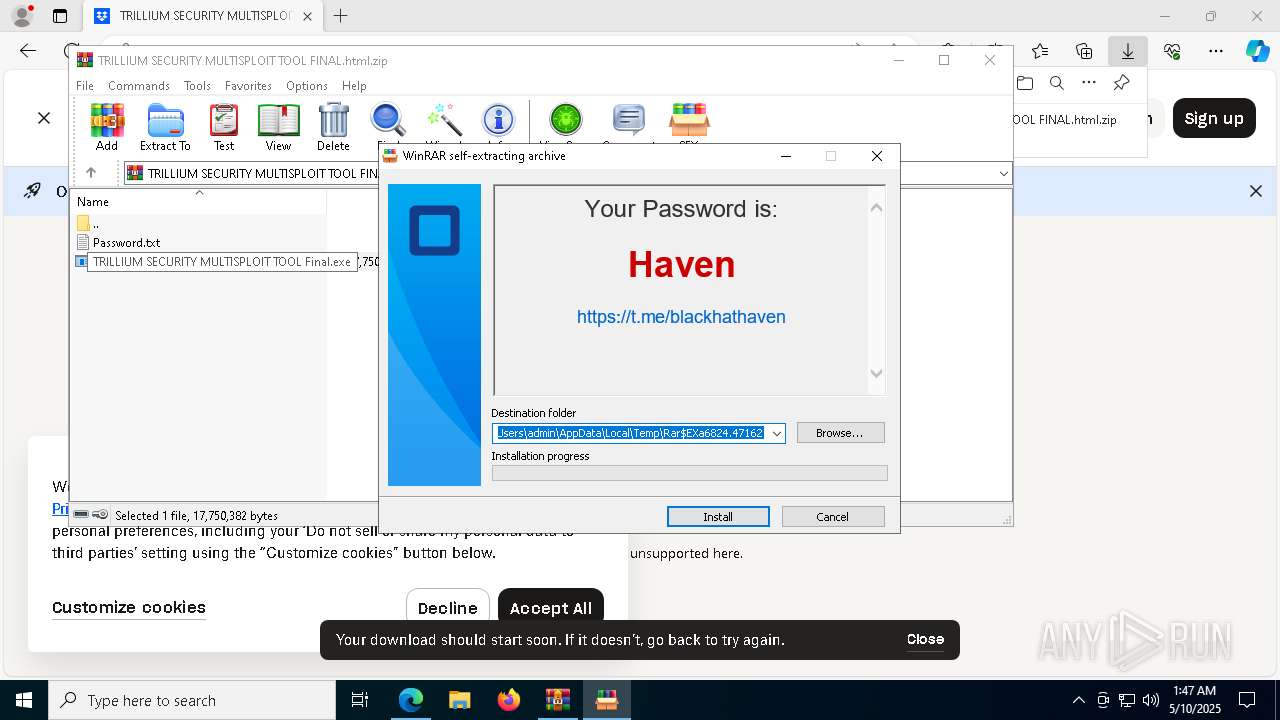
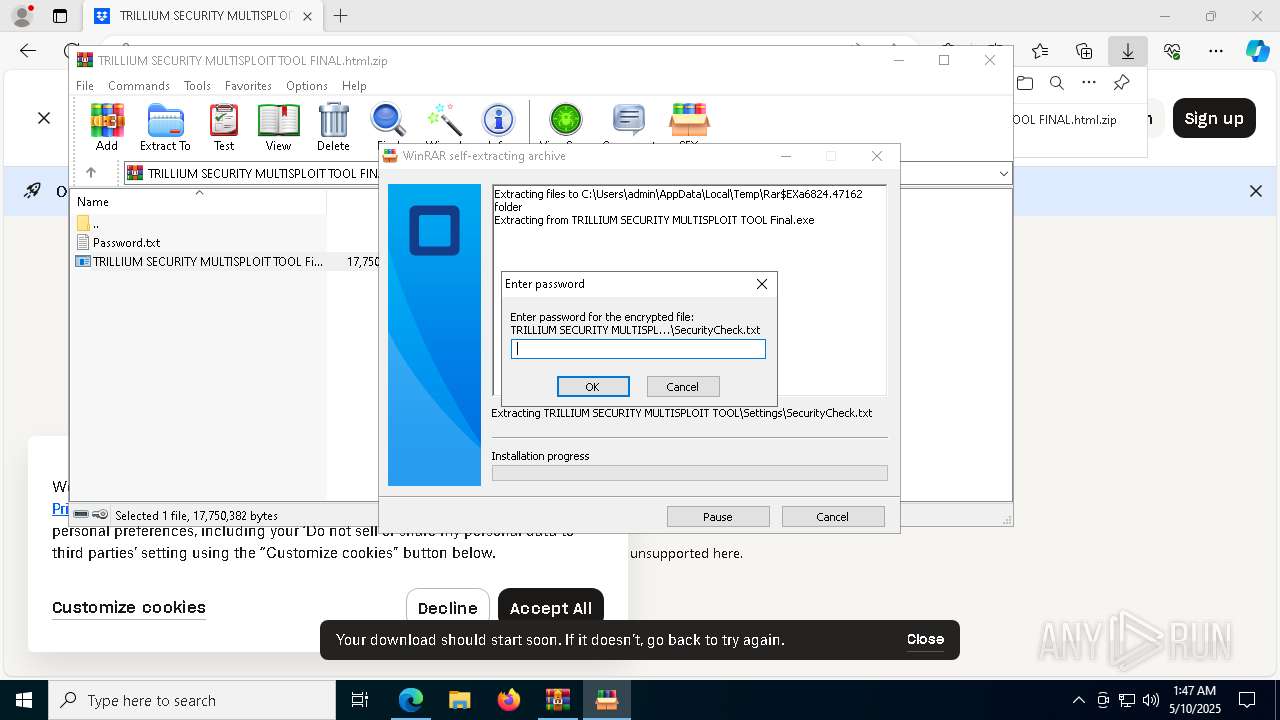
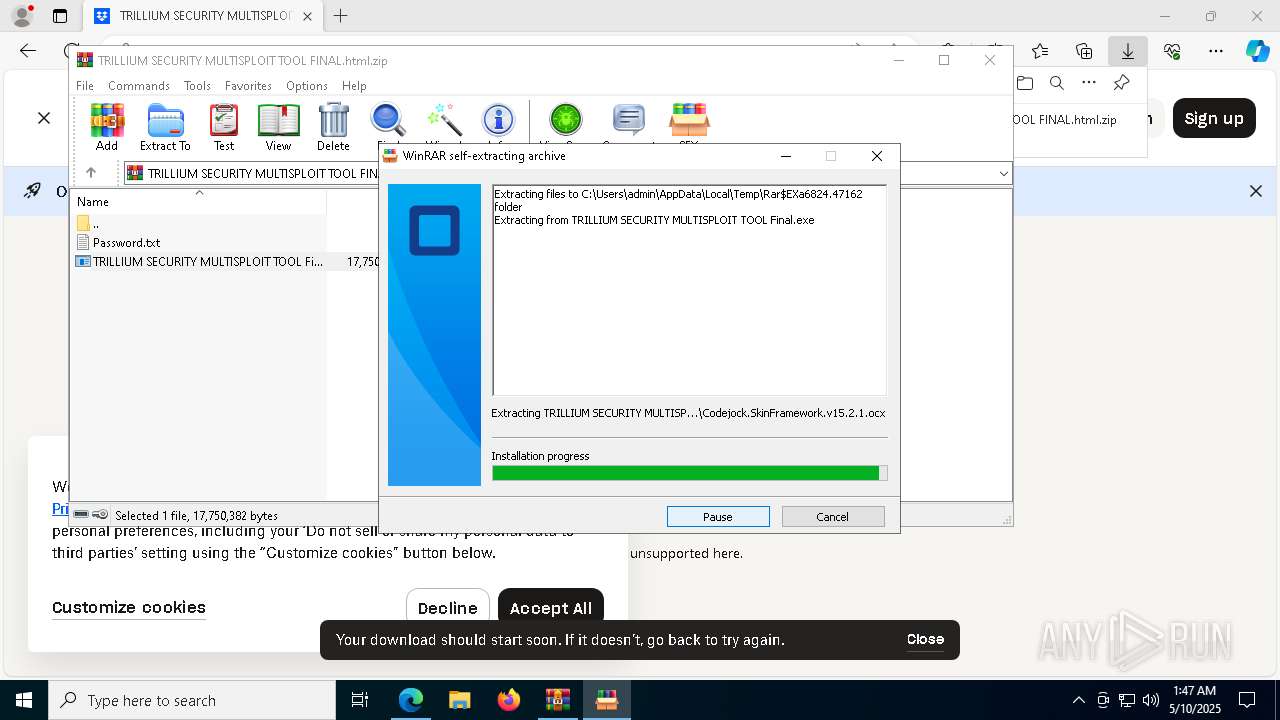
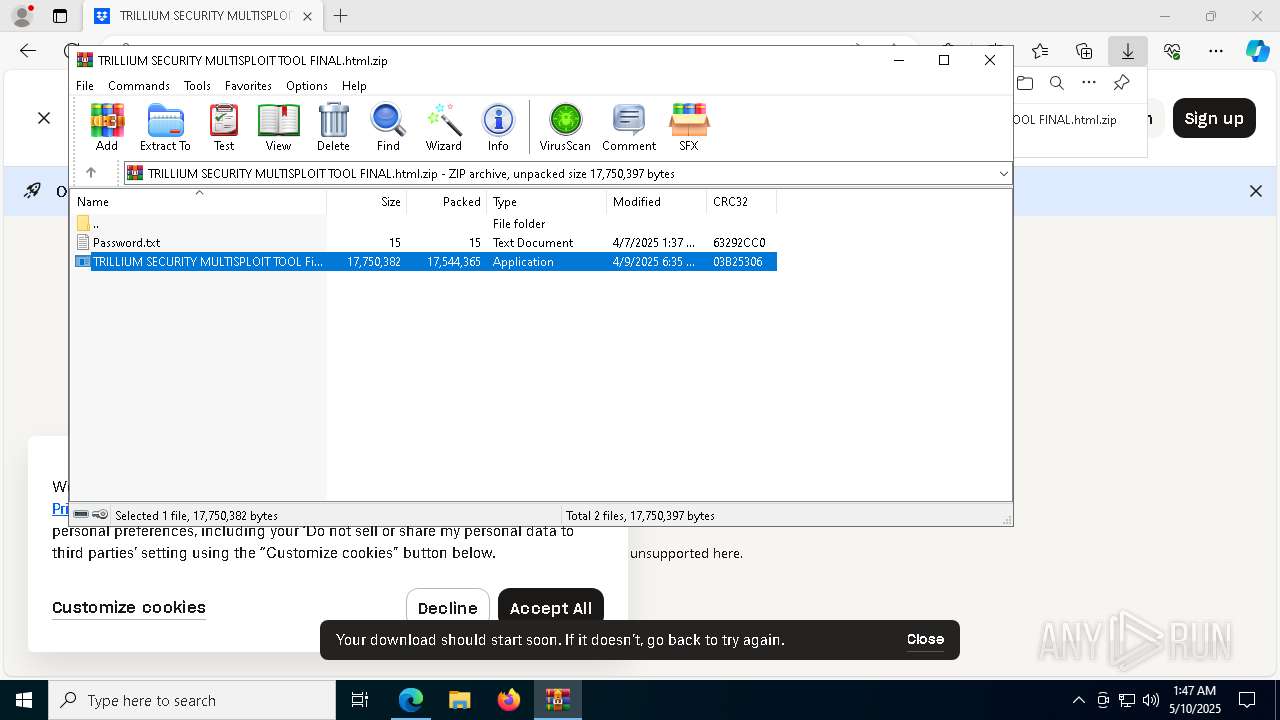
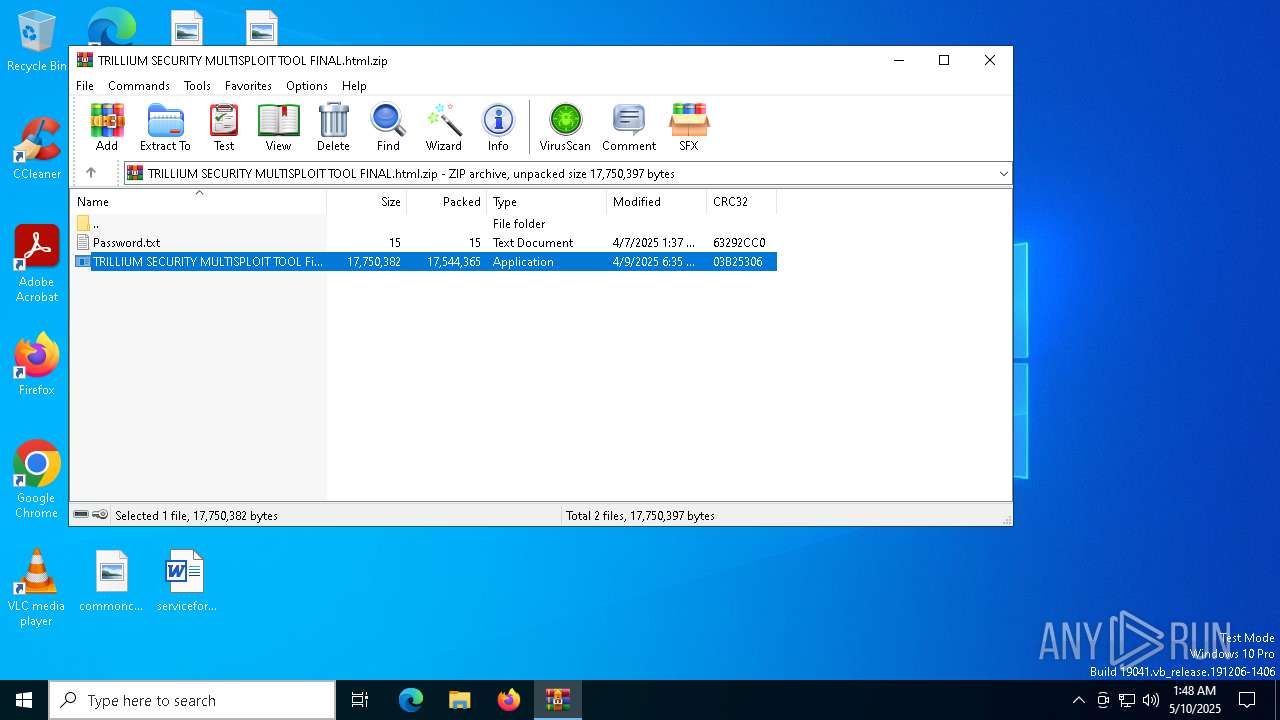
| URL: | https://www.dropbox.com/scl/fi/3gpqysq6dqc6btc6figsr/TRILLIUM-SECURITY-MULTISPLOIT-TOOL-FINAL.html.zip?rlkey=qmwyvlojz0fvmbzpx3zoku06s&st=f0ukusb2&dl=0 |
| Full analysis: | https://app.any.run/tasks/9fd7895f-827d-4331-9f45-0bc8fa36b466 |
| Verdict: | Malicious activity |
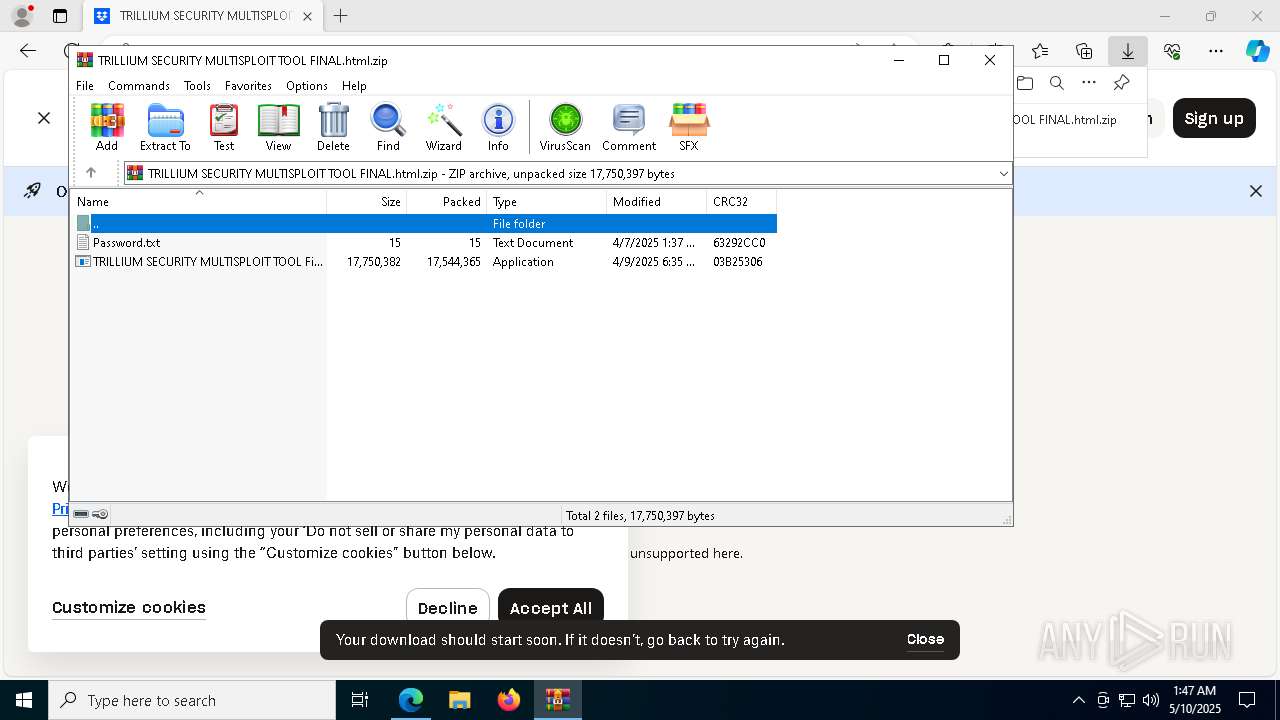
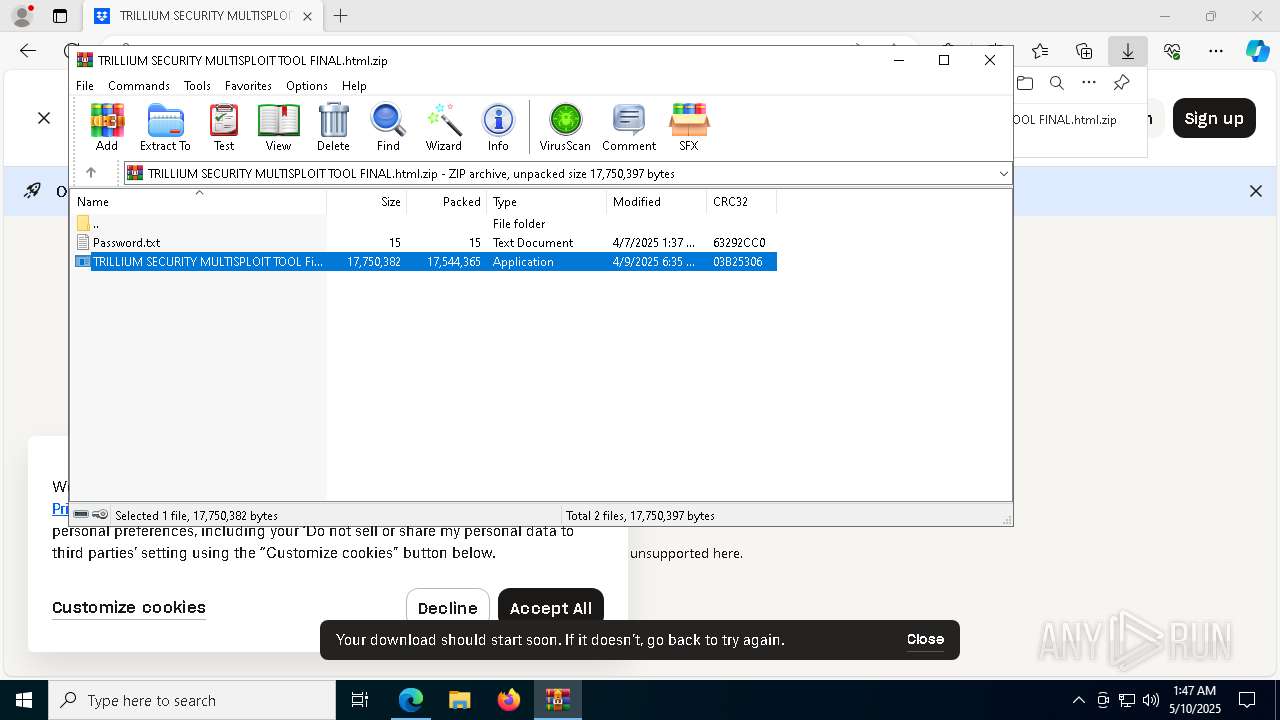
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | May 10, 2025, 01:47:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 70A669455A9F6607D5CC917BE1D6B292 |
| SHA1: | 57BE3A500A944B807EAF99FB49B97ABADCDD3747 |
| SHA256: | 5BC5F353AA6B3B9526A7A26EEB39922CE8847C0383F1130422D9A50C8686BC6B |
| SSDEEP: | 3:N8DSLcVHGkG6WCiTvqphHmpW41gwjPuJpOAcYJE2WtQ5ZYJQO3YV:2OLHkHphAvtyg5YJE32me4YV |
MALICIOUS
Executing a file with an untrusted certificate
- crack.exe (PID: 6760)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
BlankGrabber has been detected
- crack.exe (PID: 6760)
- crack.exe (PID: 2084)
Adds path to the Windows Defender exclusion list
- crack.exe (PID: 1616)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 6668)
Create files in the Startup directory
- crack.exe (PID: 1616)
- cryp.exe (PID: 8256)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 4892)
Changes Windows Defender settings
- cmd.exe (PID: 5968)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 6668)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7412)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7412)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7412)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7412)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7412)
Changes settings for real-time protection
- powershell.exe (PID: 7412)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7412)
Actions looks like stealing of personal data
- crack.exe (PID: 1616)
Steals credentials from Web Browsers
- crack.exe (PID: 1616)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8880)
Bypass execution policy to execute commands
- powershell.exe (PID: 9196)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8644)
Attempting to use instant messaging service
- Update.exe (PID: 6028)
Stealers network behavior
- Update.exe (PID: 6028)
SUSPICIOUS
Reads Microsoft Outlook installation path
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
Reads security settings of Internet Explorer
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- WinRAR.exe (PID: 6824)
- crack.exe (PID: 5304)
Reads Internet Explorer settings
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
Executable content was dropped or overwritten
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- cracker.exe (PID: 1180)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
- powershell.exe (PID: 5740)
- cryp.exe (PID: 8256)
- csc.exe (PID: 8168)
Process drops legitimate windows executable
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
Reads the date of Windows installation
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 5304)
Starts a Microsoft application from unusual location
- crack.exe (PID: 6760)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
Process drops python dynamic module
- crack.exe (PID: 6760)
- crack.exe (PID: 2084)
The process drops C-runtime libraries
- crack.exe (PID: 6760)
- crack.exe (PID: 2084)
The process executes VB scripts
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
Malware-specific behavior: drops SQLite library (may be used to steal credentials)
- cracker.exe (PID: 1180)
Application launched itself
- crack.exe (PID: 6760)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
Executing commands from a ".bat" file
- wscript.exe (PID: 1812)
- wscript.exe (PID: 1096)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1812)
- wscript.exe (PID: 1096)
- crack.exe (PID: 1616)
- setup.exe (PID: 7584)
- Update.exe (PID: 6028)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1096)
- wscript.exe (PID: 1812)
Downloads file from URI via Powershell
- powershell.exe (PID: 5740)
- powershell.exe (PID: 6488)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8880)
Checks for external IP
- svchost.exe (PID: 2196)
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
- Update.exe (PID: 6028)
The process creates files with name similar to system file names
- setup.exe (PID: 7584)
Found strings related to reading or modifying Windows Defender settings
- crack.exe (PID: 1616)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 4892)
Script disables Windows Defender's IPS
- cmd.exe (PID: 4892)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5968)
- cmd.exe (PID: 6668)
Get information on the list of running processes
- crack.exe (PID: 1616)
- cmd.exe (PID: 8332)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 8552)
The executable file from the user directory is run by the CMD process
- cryp.exe (PID: 8256)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8624)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 8372)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8484)
Starts application with an unusual extension
- cmd.exe (PID: 8876)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 8420)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 8840)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8880)
Base64-obfuscated command line is found
- cmd.exe (PID: 8880)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8880)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- setup.exe (PID: 7584)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8168)
Starts itself from another location
- cracker.exe (PID: 1180)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 9128)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8216)
- cmd.exe (PID: 8292)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8900)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 7964)
The process connected to a server suspected of theft
- Update.exe (PID: 6028)
MS Edge headless start
- msedge.exe (PID: 7764)
- msedge.exe (PID: 8876)
INFO
Checks supported languages
- identity_helper.exe (PID: 6476)
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- setup.exe (PID: 7584)
- cracker.exe (PID: 1180)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
- cryp.exe (PID: 8256)
Reads the computer name
- identity_helper.exe (PID: 6476)
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- setup.exe (PID: 7584)
- cracker.exe (PID: 1180)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
- cryp.exe (PID: 8256)
Reads Environment values
- identity_helper.exe (PID: 6476)
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
Application launched itself
- msedge.exe (PID: 7476)
- chrome.exe (PID: 8548)
- msedge.exe (PID: 7764)
Connects to unusual port
- msedge.exe (PID: 7768)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7476)
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6824)
Checks proxy server information
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 5740)
Create files in a temporary directory
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- cracker.exe (PID: 1180)
- crack.exe (PID: 5304)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
The sample compiled with english language support
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 6760)
- cracker.exe (PID: 1180)
- crack.exe (PID: 2084)
- crack.exe (PID: 1616)
Process checks computer location settings
- TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe (PID: 6048)
- crack.exe (PID: 5304)
Disables trace logs
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 6488)
Reads the machine GUID from the registry
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
Reads the software policy settings
- cracker.exe (PID: 1180)
- setup.exe (PID: 7584)
Creates files or folders in the user directory
- setup.exe (PID: 7584)
- cryp.exe (PID: 8256)
Creates files in the program directory
- crack.exe (PID: 1616)
The Powershell gets current clipboard
- powershell.exe (PID: 8948)
Checks the directory tree
- tree.com (PID: 8944)
- tree.com (PID: 9016)
- tree.com (PID: 3396)
- tree.com (PID: 5064)
- tree.com (PID: 8716)
- tree.com (PID: 7320)
Changes the display of characters in the console
- cmd.exe (PID: 8372)
- cmd.exe (PID: 9128)
Attempting to use instant messaging service
- setup.exe (PID: 7584)
- Update.exe (PID: 6028)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 6324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
318
Monitored processes
185
Malicious processes
14
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | netsh wlan show networks mode=bssid | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5252 --field-trial-handle=2308,i,2673068094952930277,2110829855050810485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-appcompat-clear --disable-logging --mojo-platform-channel-handle=4424 --field-trial-handle=2360,i,12251821002694127388,9775146487113792629,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6340 --field-trial-handle=2308,i,2673068094952930277,2110829855050810485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$EXa6824.47162\min.vbs" | C:\Windows\System32\wscript.exe | — | TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6824.47162\cracker.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6824.47162\cracker.exe | TRILLIUM SECURITY MULTISPLOIT TOOL Final.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: conhost Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6532 --field-trial-handle=2308,i,2673068094952930277,2110829855050810485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 521
Read events
70 423
Write events
95
Delete events
3
Modification events
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2BBA8D8B54932F00 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C142978B54932F00 | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394060 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5C7A96F2-D459-4B63-8380-E51CD2C22B2A} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394060 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4E823E6E-CD4F-496B-BC57-7FAB9B38DC05} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394060 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B01A8C88-CC5B-437D-89F5-539326FD5B4B} | |||
| (PID) Process: | (7476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394060 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5E2B781C-A5AA-41F5-810E-C2FB35C0C3AC} | |||
Executable files
62
Suspicious files
542
Text files
158
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b5e4.TMP | — | |
MD5:— | SHA256:— | |||
| 7476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
92
DNS requests
93
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.4:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
4736 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
1180 | cracker.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | whitelisted |
4736 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
7584 | setup.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | text | 15 b | whitelisted |
6028 | Update.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.4:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7768 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7476 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7768 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7768 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.dropbox.com |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1180 | cracker.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7584 | setup.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7584 | setup.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |