| File name: | Statement.exe |
| Full analysis: | https://app.any.run/tasks/4d91794c-2999-4fb6-9eb7-06db503fa936 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | May 24, 2019, 01:58:40 |
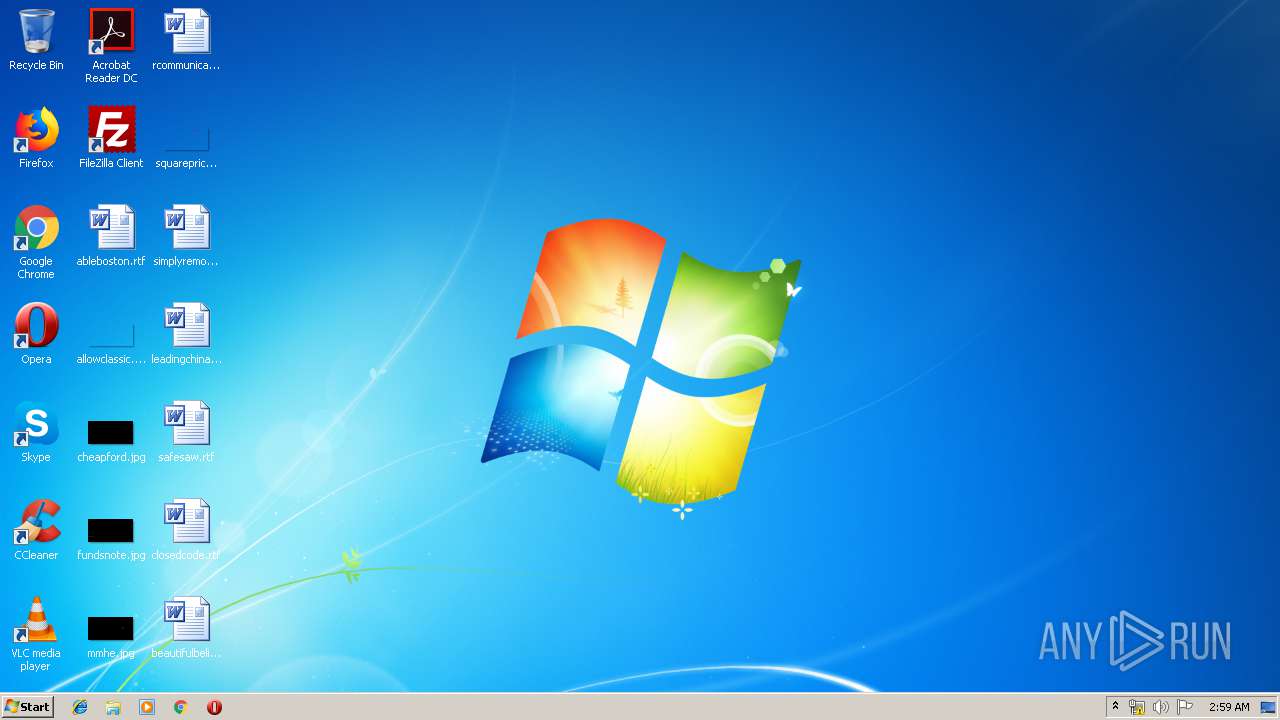
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 467D70FABE3EFB18F367C9858A60FC14 |
| SHA1: | 06F3AEE1A79328881D3C7FB8B491429D4A847071 |
| SHA256: | 5BBE32C809EBDA0CA8B19011487915FA1A1013FA53B5C687F2F63DE45C55236B |
| SSDEEP: | 12288:uraGhLYyapgY9LNAYDzgsMMLSvEm/l4lkY38aGVQlnfVchU6Q/Bp9/r7kaVQtD0Z:QergmVYsFqYAVk/3Br/Z |
MALICIOUS
Writes to a start menu file
- simos.exe (PID: 2384)
Detected Hawkeye Keylogger
- simos.exe (PID: 2152)
Actions looks like stealing of personal data
- vbc.exe (PID: 1028)
SUSPICIOUS
Executable content was dropped or overwritten
- Statement.exe (PID: 3208)
Creates files in the user directory
- Statement.exe (PID: 3208)
- simos.exe (PID: 2384)
- simos.exe (PID: 2152)
Starts itself from another location
- Statement.exe (PID: 3208)
Application launched itself
- simos.exe (PID: 2384)
Checks for external IP
- simos.exe (PID: 2152)
Executes scripts
- simos.exe (PID: 2152)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2612)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:02:09 09:33:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 358400 |
| InitializedDataSize: | 474112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x58698 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Feb-1992 08:33:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 09-Feb-1992 08:33:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000576E0 | 0x00057800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5299 |
DATA | 0x00059000 | 0x0000CBFC | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.87696 |
BSS | 0x00066000 | 0x00000C15 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00067000 | 0x00002090 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88829 |
.tls | 0x0006A000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0006B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x0006C000 | 0x0000672C | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65505 |
.rsrc | 0x00073000 | 0x0005E214 | 0x0005E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.37539 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.67432 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
1000 | 4.84751 | 974 | Latin 1 / Western European | English - United States | RT_DLGINCLUDE |
1058 | 7.56853 | 10202 | Latin 1 / Western European | English - United States | RT_BITMAP |
1059 | 7.63622 | 10202 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
37
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | simos.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Roaming\simom\simos.exe" | C:\Users\admin\AppData\Roaming\simom\simos.exe | simos.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Roaming\simom\simos.exe" | C:\Users\admin\AppData\Roaming\simom\simos.exe | Statement.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2612 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | simos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\AppData\Local\Temp\Statement.exe" | C:\Users\admin\AppData\Local\Temp\Statement.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
97
Read events
84
Write events
13
Delete events
0
Modification events
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2152) simos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\simos_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | Statement.exe | C:\Users\admin\AppData\Roaming\simom\simos.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 1028 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 2612 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 3208 | Statement.exe | C:\Users\admin\AppData\Roaming\simom\simos.exe | executable | |
MD5:— | SHA256:— | |||
| 2152 | simos.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
| 2384 | simos.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\simom.vbs | text | |
MD5:— | SHA256:— | |||
| 2152 | simos.exe | C:\Users\admin\AppData\Roaming\pid.txt | text | |
MD5:A486CD07E4AC3D270571622F4F316EC5 | SHA256:7E8250DFC4ECB8399D6B28E63AA883E53151B004AE4F8DB06F0BC1CE52FFF899 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | simos.exe | GET | 403 | 104.16.154.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | simos.exe | 104.16.154.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
2152 | simos.exe | 208.91.198.143:587 | smtp.baka-ltb.com | PDR | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.baka-ltb.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2152 | simos.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
2152 | simos.exe | A Network Trojan was detected | ET TROJAN HawkEye Keylogger Report SMTP |
2152 | simos.exe | A Network Trojan was detected | ET TROJAN HawkEye Keylogger Report SMTP |
2 ETPRO signatures available at the full report