| File name: | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a |
| Full analysis: | https://app.any.run/tasks/65867488-0955-4846-8179-1ab27eae002d |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
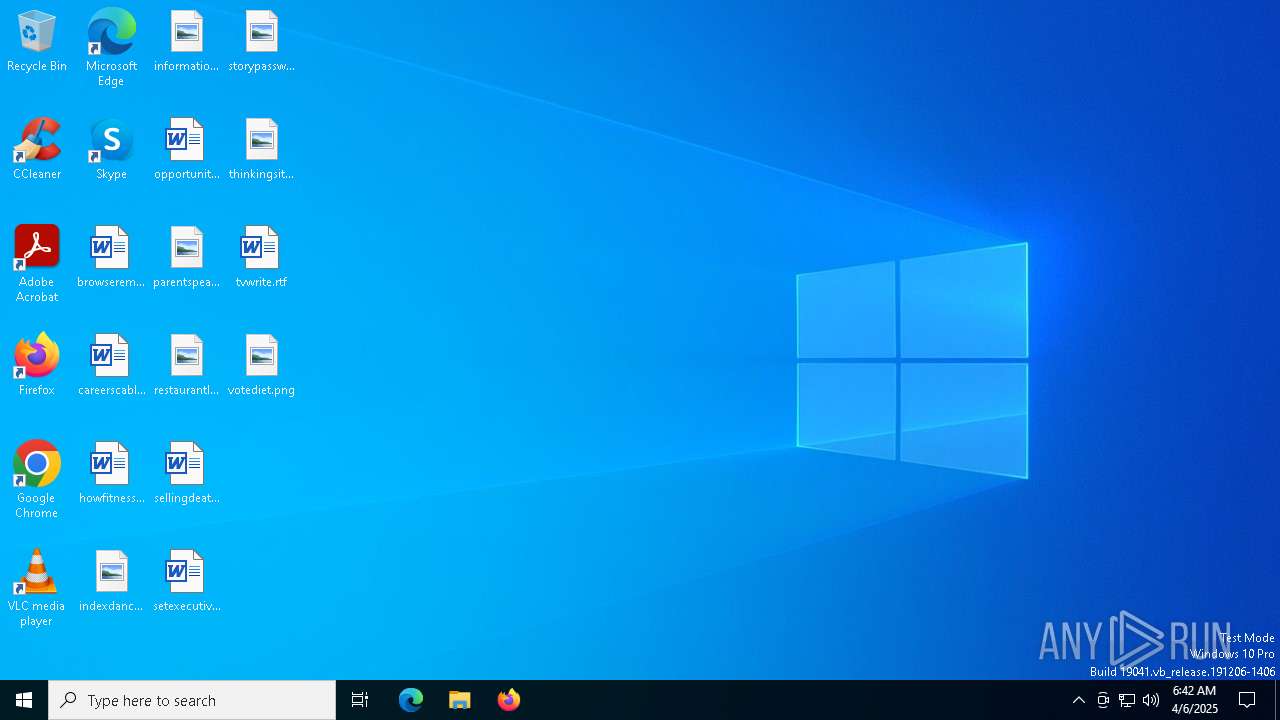
| Analysis date: | April 06, 2025, 06:42:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 3D0156E1F7FABBC3AF8A0063D86AE4D4 |
| SHA1: | 179047B99C4DBE290DE325A98995ADF485725EEB |
| SHA256: | 5B73EFE60CE4A31E0D4BE12C608A08CE685EB11A6901B5A37E6A856DD21BCC7A |
| SSDEEP: | 98304:WX5UXVxdjtPSVSg58bEvnB3H/eyJHEAsc3G1fC5RHxQUneevbG1AfhnxcANsZb7Z:AM |
MALICIOUS
SAINBOX has been detected
- TXPlatforn.exe (PID: 2284)
- TXPlatforn.exe (PID: 4692)
GH0ST mutex has been found
- TXPlatforn.exe (PID: 2284)
- TXPlatforn.exe (PID: 4692)
Starts CMD.EXE for self-deleting
- svchost.exe (PID: 6700)
GH0ST has been detected
- svchost.exe (PID: 6700)
ZEGOST has been detected
- svchos.exe (PID: 5556)
SUSPICIOUS
The process creates files with name similar to system file names
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
Executable content was dropped or overwritten
- svchost.exe (PID: 6700)
- svchos.exe (PID: 5556)
- TXPlatforn.exe (PID: 4692)
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
Executes as Windows Service
- TXPlatforn.exe (PID: 2284)
Hides command output
- cmd.exe (PID: 6944)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 6700)
Application launched itself
- TXPlatforn.exe (PID: 2284)
Mutex name with non-standard characters
- svchos.exe (PID: 5556)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6944)
Executes application which crashes
- svchos.exe (PID: 5556)
Creates or modifies Windows services
- TXPlatforn.exe (PID: 4692)
Creates files in the driver directory
- TXPlatforn.exe (PID: 4692)
Drops a system driver (possible attempt to evade defenses)
- TXPlatforn.exe (PID: 4692)
There is functionality for taking screenshot (YARA)
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
- TXPlatforn.exe (PID: 4692)
INFO
Create files in a temporary directory
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
The sample compiled with chinese language support
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
Checks supported languages
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
- svchost.exe (PID: 6700)
- TXPlatforn.exe (PID: 2284)
- TXPlatforn.exe (PID: 4692)
- HD_5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5772)
- svchos.exe (PID: 5556)
Reads the computer name
- svchost.exe (PID: 6700)
- TXPlatforn.exe (PID: 2284)
- TXPlatforn.exe (PID: 4692)
The sample compiled with english language support
- 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe (PID: 5972)
Creates files or folders in the user directory
- WerFault.exe (PID: 4488)
- WerFault.exe (PID: 4120)
Checks proxy server information
- slui.exe (PID: 1184)
Reads the software policy settings
- slui.exe (PID: 1184)
UPX packer has been detected
- TXPlatforn.exe (PID: 4692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:10 15:16:58+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 520192 |
| InitializedDataSize: | 1175552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x60e35 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.9.8.9 |
| ProductVersionNumber: | 8.9.8.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 8.9.8.9 |
| FileDescription: | 应用程序 |
| ProductName: | 应用程序 |
| ProductVersion: | 8.9.8.9 |
| CompanyName: | Osama bin Mohammed bin Awad bin Laden |
| LegalCopyright: | Osama bin Mohammed bin Awad bin Laden |
| Comments: | 应用程序 |
Total processes
139
Monitored processes
13
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\SysWOW64\TXPlatforn.exe -auto | C:\Windows\SysWOW64\TXPlatforn.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 4120 | "C:\Users\admin\Desktop\5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe" | C:\Users\admin\Desktop\5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | — | explorer.exe | |||||||||||
User: admin Company: Osama bin Mohammed bin Awad bin Laden Integrity Level: MEDIUM Description: 应用程序 Exit code: 3221226540 Version: 8.9.8.9 Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5556 -s 468 | C:\Windows\SysWOW64\WerFault.exe | — | svchos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5556 -s 500 | C:\Windows\SysWOW64\WerFault.exe | — | svchos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | C:\WINDOWS\SysWOW64\TXPlatforn.exe -acsi | C:\Windows\SysWOW64\TXPlatforn.exe | TXPlatforn.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 5556 | C:\Users\admin\AppData\Local\Temp\\svchos.exe | C:\Users\admin\AppData\Local\Temp\svchos.exe | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | ||||||||||||
User: admin Company: FEIM Studios Integrity Level: HIGH Description: A Free Enterprise Instant Messenger Exit code: 3221225477 Version: 3, 5, 0, 1 Modules
| |||||||||||||||
| 5772 | C:\Users\admin\Desktop\HD_5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | C:\Users\admin\Desktop\HD_5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | — | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 5868 | ping -n 2 127.0.0.1 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 527
Read events
7 482
Write events
39
Delete events
6
Modification events
| (PID) Process: | (6700) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Select |
| Operation: | write | Name: | MarkTime |
Value: 2025-04-06 06:43 | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | Type |
Value: 2 | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | ErrorControl |
Value: 0 | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\QAssist.sys | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | DisplayName |
Value: QAssist | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | Group |
Value: FSFilter Activity Monitor | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | DebugFlags |
Value: 0 | |||
| (PID) Process: | (4692) TXPlatforn.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\QAssist |
| Operation: | write | Name: | SupportedFeatures |
Value: 3 | |||
Executable files
18
Suspicious files
6
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4488 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_svchos.exe_95345e27e37364fea753b9e974c85f747b416d_efb276f5_0b9f0935-9b4a-4198-ba1b-39f84373ebdf\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4120 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_svchos.exe_c7c228458ceec88fff268b845fe1698aecd56ab_efb276f5_411f3031-3fd0-4d71-ba6b-276aa04bad09\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5972 | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | C:\Program Files\CCleaner\CCleaner64.exe | — | |
MD5:— | SHA256:— | |||
| 5972 | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | — | ||
MD5:— | SHA256:— | |||
| 6700 | svchost.exe | C:\Windows\SysWOW64\TXPlatforn.exe | executable | |
MD5:A4329177954D4104005BCE3020E5EF59 | SHA256:6156D003D54DCF2EE92F21BD6E7A6A7F91730BD2804381260BCABE465ABE6DDD | |||
| 4488 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:7893FC0BAD94DD15F11A22C53F67EC45 | SHA256:C60A93FDE5A130246931C8965ABCB91E90DA4E87675570B5ED77D6D7EADE851F | |||
| 5972 | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe | — | |
MD5:— | SHA256:— | |||
| 5972 | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | C:\Users\admin\AppData\Local\Temp\svchos.exe | executable | |
MD5:3B377AD877A942EC9F60EA285F7119A2 | SHA256:62954FDF65E629B39A29F539619D20691332184C6B6BE5A826128A8E759BFA84 | |||
| 4488 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCA86.tmp.WERInternalMetadata.xml | binary | |
MD5:88007AE3776F9AC9CC30578B6A1BA58D | SHA256:092BB33B614B435560462F121A530296C5E17024A52DCC00D351BE689B3FEDD8 | |||
| 5972 | 5b73efe60ce4a31e0d4be12c608a08ce685eb11a6901b5a37e6a856dd21bcc7a.exe | C:\Users\admin\AppData\Local\Temp\svchost.exe | executable | |
MD5:A4329177954D4104005BCE3020E5EF59 | SHA256:6156D003D54DCF2EE92F21BD6E7A6A7F91730BD2804381260BCABE465ABE6DDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
21
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4996 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | — | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4996 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4996 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3284 | svchost.exe | 13.89.179.12:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
900 | slui.exe | 13.77.207.86:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1184 | slui.exe | 13.77.207.86:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
hackerinvasion.f3322.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |