| File name: | LB3.exe |
| Full analysis: | https://app.any.run/tasks/17a6a25a-ae2c-460f-8da8-f43b896deac9 |
| Verdict: | Malicious activity |
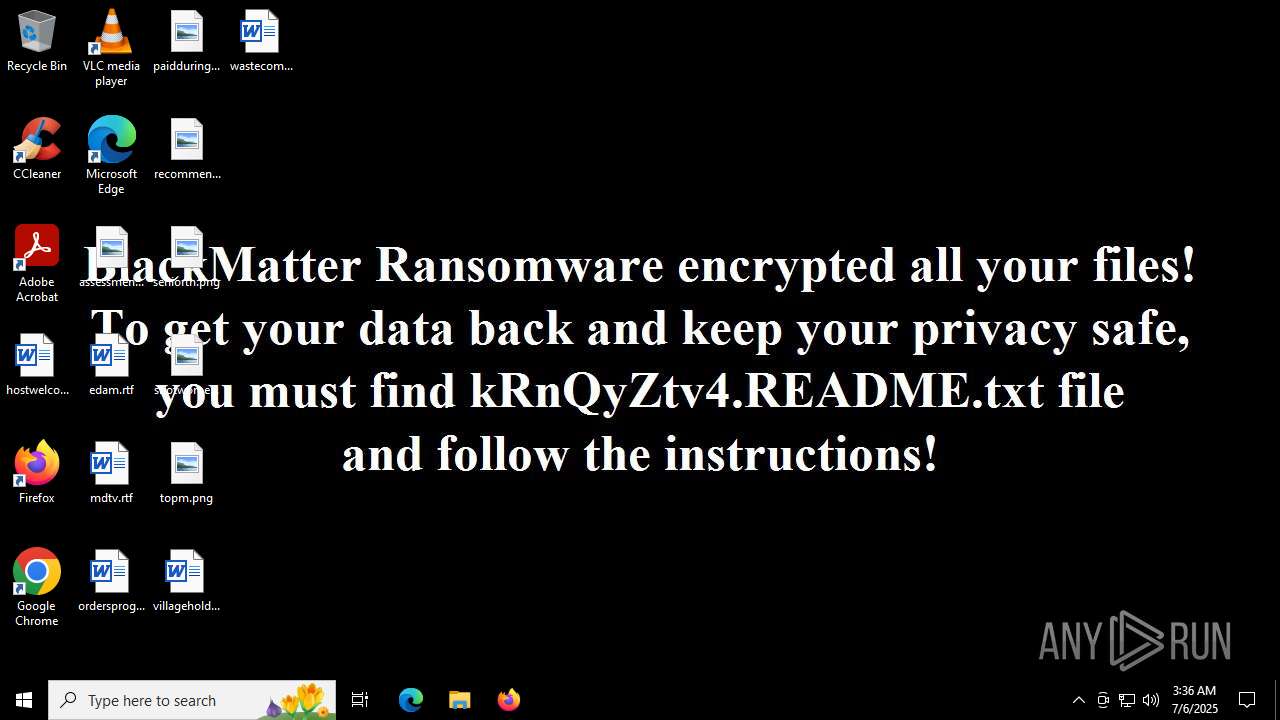
| Threats: | BlackMatter is a ransomware strain operating as a Ransomware-as-a-Service (RaaS), designed to encrypt files, remove recovery options, and extort victims across critical industries. Emerging in 2021, it quickly became a major concern due to its ability to evade defenses, spread across networks, and cause large-scale operational disruption, forcing security teams to act against a highly destructive and persistent threat. |
| Analysis date: | July 06, 2025, 03:35:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 5DFAE5C2170FB41EE8EDF3D87BD6852D |
| SHA1: | B2E15B65854A3BD5DAE27A4F8250B9AD550FDF9E |
| SHA256: | 5B48EE4D804EA8CF505CF4A12F7F2E8F887C724AE6F4B282AC7E4B85AA668020 |
| SSDEEP: | 3072:bRXn9S+eOp8wT3mymg7/UvxNUh39qWCJqGb8SnD:bnnDmG/UvxW39q7 |
MALICIOUS
BLACKMATTER mutex has been found
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
CONTI mutex has been found
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Bypass User Account Control (Modify registry)
- svchost.exe (PID: 7136)
Changes the autorun value in the registry
- svchost.exe (PID: 7136)
BLACKMATTER has been detected (SURICATA)
- svchost.exe (PID: 2200)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 6732)
LOCKBIT3 has been detected
- svchost.exe (PID: 7136)
Connects to the CnC server
- svchost.exe (PID: 2200)
Deletes shadow copies
- svchost.exe (PID: 7136)
- cmd.exe (PID: 6732)
[YARA] LockBit is detected
- svchost.exe (PID: 7136)
DARKSIDE has been detected (SURICATA)
- svchost.exe (PID: 7136)
Renames files like ransomware
- svchost.exe (PID: 7136)
Modifies files in the Chrome extension folder
- svchost.exe (PID: 7136)
Starts NET.EXE for service management
- svchost.exe (PID: 7136)
- net.exe (PID: 5540)
- net.exe (PID: 5528)
- net.exe (PID: 4444)
- net.exe (PID: 6172)
- net.exe (PID: 5368)
- net.exe (PID: 5720)
- net.exe (PID: 5712)
- net.exe (PID: 5876)
- net.exe (PID: 768)
- net.exe (PID: 3148)
- net.exe (PID: 3788)
- net.exe (PID: 7060)
- net.exe (PID: 6520)
- net.exe (PID: 4132)
- net.exe (PID: 1612)
- net.exe (PID: 4836)
- net.exe (PID: 6240)
- net.exe (PID: 5352)
- net.exe (PID: 7032)
- net.exe (PID: 1512)
- net.exe (PID: 5252)
- net.exe (PID: 6364)
- net.exe (PID: 6868)
- net.exe (PID: 5460)
- net.exe (PID: 6664)
- net.exe (PID: 6940)
- net.exe (PID: 6828)
- net.exe (PID: 856)
- net.exe (PID: 2528)
- net.exe (PID: 6380)
- net.exe (PID: 4868)
- net.exe (PID: 2032)
- net.exe (PID: 2596)
- net.exe (PID: 6284)
- net.exe (PID: 4080)
- net.exe (PID: 4868)
- net.exe (PID: 4752)
- net.exe (PID: 1080)
- net.exe (PID: 6648)
- net.exe (PID: 7160)
- net.exe (PID: 3392)
- net.exe (PID: 3476)
- net.exe (PID: 5188)
- net.exe (PID: 7092)
- net.exe (PID: 5628)
- net.exe (PID: 6536)
- net.exe (PID: 2216)
- net.exe (PID: 4312)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 4236)
- net.exe (PID: 5564)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 984)
- cmd.exe (PID: 2324)
BLACKMATTER has been detected (YARA)
- svchost.exe (PID: 7136)
SUSPICIOUS
Executing commands from a ".bat" file
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Starts CMD.EXE for commands execution
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4968)
- cmd.exe (PID: 4500)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 4888)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 1156)
The process creates files with name similar to system file names
- LB3.exe (PID: 3976)
Executable content was dropped or overwritten
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Reads security settings of Internet Explorer
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Reads the date of Windows installation
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Starts itself from another location
- LB3.exe (PID: 3976)
Changes default file association
- svchost.exe (PID: 7136)
Hides command output
- cmd.exe (PID: 864)
- cmd.exe (PID: 3780)
- cmd.exe (PID: 1612)
- cmd.exe (PID: 6512)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- svchost.exe (PID: 7136)
There is functionality for taking screenshot (YARA)
- svchost.exe (PID: 7136)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 4412)
Starts NET.EXE for network exploration
- svchost.exe (PID: 7136)
Connects to the server without a host name
- svchost.exe (PID: 7136)
Starts SC.EXE for service management
- svchost.exe (PID: 7136)
Windows service management via SC.EXE
- sc.exe (PID: 2536)
- sc.exe (PID: 1328)
- sc.exe (PID: 2664)
- sc.exe (PID: 5496)
- sc.exe (PID: 2596)
- sc.exe (PID: 4844)
- sc.exe (PID: 4100)
- sc.exe (PID: 7016)
- sc.exe (PID: 6900)
- sc.exe (PID: 5600)
- sc.exe (PID: 4864)
- sc.exe (PID: 4312)
- sc.exe (PID: 6756)
- sc.exe (PID: 6980)
- sc.exe (PID: 6492)
- sc.exe (PID: 4192)
- sc.exe (PID: 6368)
- sc.exe (PID: 5244)
- sc.exe (PID: 2696)
- sc.exe (PID: 2428)
- sc.exe (PID: 3820)
- sc.exe (PID: 5496)
- sc.exe (PID: 4084)
- sc.exe (PID: 2708)
- sc.exe (PID: 3948)
- sc.exe (PID: 1984)
- sc.exe (PID: 4400)
- sc.exe (PID: 2276)
- sc.exe (PID: 2604)
- sc.exe (PID: 5884)
- sc.exe (PID: 7092)
- sc.exe (PID: 6868)
- sc.exe (PID: 3564)
- sc.exe (PID: 3648)
- sc.exe (PID: 3000)
- sc.exe (PID: 1052)
- sc.exe (PID: 4960)
- sc.exe (PID: 6520)
- sc.exe (PID: 6732)
- sc.exe (PID: 5576)
- sc.exe (PID: 6828)
- sc.exe (PID: 7072)
- sc.exe (PID: 4700)
- sc.exe (PID: 6512)
- sc.exe (PID: 3392)
- sc.exe (PID: 5244)
- sc.exe (PID: 4864)
- sc.exe (PID: 1212)
- sc.exe (PID: 6172)
- sc.exe (PID: 6236)
- sc.exe (PID: 6776)
- sc.exe (PID: 5884)
- sc.exe (PID: 4216)
- sc.exe (PID: 1336)
- sc.exe (PID: 3736)
- sc.exe (PID: 2992)
- sc.exe (PID: 2072)
- sc.exe (PID: 6756)
- sc.exe (PID: 5352)
- sc.exe (PID: 424)
- sc.exe (PID: 4040)
- sc.exe (PID: 2880)
- sc.exe (PID: 4236)
- sc.exe (PID: 7100)
- sc.exe (PID: 6408)
- sc.exe (PID: 856)
- sc.exe (PID: 6368)
- sc.exe (PID: 4816)
- sc.exe (PID: 5008)
- sc.exe (PID: 5400)
- sc.exe (PID: 1052)
- sc.exe (PID: 7020)
- sc.exe (PID: 5548)
- sc.exe (PID: 2380)
- sc.exe (PID: 2032)
- sc.exe (PID: 4844)
- sc.exe (PID: 6776)
- sc.exe (PID: 5368)
- sc.exe (PID: 4932)
- sc.exe (PID: 4864)
- sc.exe (PID: 3936)
- sc.exe (PID: 2696)
- sc.exe (PID: 6540)
- sc.exe (PID: 5340)
- sc.exe (PID: 2324)
- sc.exe (PID: 5352)
- sc.exe (PID: 5924)
- sc.exe (PID: 4968)
- sc.exe (PID: 5020)
- sc.exe (PID: 3588)
- sc.exe (PID: 2992)
- sc.exe (PID: 2536)
- sc.exe (PID: 4868)
- sc.exe (PID: 1328)
- sc.exe (PID: 2800)
- sc.exe (PID: 3932)
INFO
Checks supported languages
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Reads the machine GUID from the registry
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Reads the computer name
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Create files in a temporary directory
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Creates files or folders in the user directory
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Process checks computer location settings
- LB3.exe (PID: 3976)
- svchost.exe (PID: 7136)
Launching a file from a Registry key
- svchost.exe (PID: 7136)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- svchost.exe (PID: 7136)
Reads Environment values
- svchost.exe (PID: 7136)
Disables trace logs
- svchost.exe (PID: 7136)
Checks proxy server information
- svchost.exe (PID: 7136)
Reads the software policy settings
- svchost.exe (PID: 7136)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5824)
Creates files in the program directory
- svchost.exe (PID: 7136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:06 03:34:54+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 138240 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x23a8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | LB3.exe |
| LegalCopyright: | |
| OriginalFileName: | LB3.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
546
Monitored processes
412
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | C:\WINDOWS\system32\net1 stop vss | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | C:\WINDOWS\system32\net1 user svc_4s5ZRS4Q niiQcxOGCptP /add /active:yes | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "sc.exe" delete backup | C:\Windows\System32\sc.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Windows\System32\cmd.exe" /C /c wevtutil cl security | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 264
Read events
11 253
Write events
11
Delete events
0
Modification events
| (PID) Process: | (7136) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | UpdateLEkfGc |
Value: C:\Users\admin\AppData\Local\svchost.exe | |||
| (PID) Process: | (7136) svchost.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell\Open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (7136) svchost.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{3D8B0590-F691-11D2-8EA9-006008039E37} |
| Operation: | write | Name: | LocalizedResourceName |
Value: UACBypass | |||
| (PID) Process: | (7136) svchost.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{3D8B0590-F691-11D2-8EA9-006008039E37}\Elevation |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (7136) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\eventvwr.exe |
| Operation: | write | Name: | Path |
Value: C:\PROGRA~3 | |||
Executable files
6
Suspicious files
216
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | LB3.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_ntshK1sQ.bat | text | |
MD5:98EC0893542F27D9CB66F211A8623F74 | SHA256:682C08D1E8363272024133D9C0F84BEC7F153847B3738887C801DCA692CA5A6E | |||
| 3976 | LB3.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_FHPVUOCt.bat | text | |
MD5:98EC0893542F27D9CB66F211A8623F74 | SHA256:682C08D1E8363272024133D9C0F84BEC7F153847B3738887C801DCA692CA5A6E | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_LT0ZW9Tu.bat | text | |
MD5:80384AC2A6120ACBE512303AEBC66A1D | SHA256:169674D683BE5127DF6B0817287779B6292835BD97B12785ED9243543B823505 | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_ckEnO044.bat | text | |
MD5:80384AC2A6120ACBE512303AEBC66A1D | SHA256:169674D683BE5127DF6B0817287779B6292835BD97B12785ED9243543B823505 | |||
| 3976 | LB3.exe | C:\Users\admin\AppData\Local\svchost.exe | executable | |
MD5:5DFAE5C2170FB41EE8EDF3D87BD6852D | SHA256:5B48EE4D804EA8CF505CF4A12F7F2E8F887C724AE6F4B282AC7E4B85AA668020 | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\update_MCjFR6.exe | executable | |
MD5:5DFAE5C2170FB41EE8EDF3D87BD6852D | SHA256:5B48EE4D804EA8CF505CF4A12F7F2E8F887C724AE6F4B282AC7E4B85AA668020 | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_XEc7ldUB.bat | text | |
MD5:80384AC2A6120ACBE512303AEBC66A1D | SHA256:169674D683BE5127DF6B0817287779B6292835BD97B12785ED9243543B823505 | |||
| 3976 | LB3.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_EkJpepqm.bat | text | |
MD5:98EC0893542F27D9CB66F211A8623F74 | SHA256:682C08D1E8363272024133D9C0F84BEC7F153847B3738887C801DCA692CA5A6E | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\selfdestruct_eMtQSb02.bat | text | |
MD5:80384AC2A6120ACBE512303AEBC66A1D | SHA256:169674D683BE5127DF6B0817287779B6292835BD97B12785ED9243543B823505 | |||
| 7136 | svchost.exe | C:\Users\admin\AppData\Local\Temp\update_MEFsCg.exe | executable | |
MD5:5DFAE5C2170FB41EE8EDF3D87BD6852D | SHA256:5B48EE4D804EA8CF505CF4A12F7F2E8F887C724AE6F4B282AC7E4B85AA668020 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
28
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2876 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7136 | svchost.exe | GET | 200 | 3.33.130.190:80 | http://mojobiden.com/ | unknown | — | — | malicious |
7136 | svchost.exe | GET | 200 | 5.255.108.35:80 | http://5.255.108.35/ | unknown | — | — | unknown |
7136 | svchost.exe | GET | 200 | 162.210.195.122:80 | http://baroquetees.com/ | unknown | — | — | malicious |
7136 | svchost.exe | GET | 200 | 199.59.243.228:80 | http://survey-smiles.com/ | unknown | — | — | whitelisted |
7136 | svchost.exe | GET | 200 | 199.59.243.228:80 | http://survey-smiles.com/ | unknown | — | — | whitelisted |
6764 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7136 | svchost.exe | POST | 405 | 3.33.130.190:80 | http://mojobiden.com/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7136 | svchost.exe | 3.33.130.190:443 | mojobiden.com | AMAZON-02 | US | malicious |
2876 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2876 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mojobiden.com |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
paymenthacks.com |
| malicious |
securebestapp20.com |
| malicious |
temisleyes.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE BlackMatter CnC Domain in DNS Lookup (mojobiden .com) |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE BlackMatter CnC Domain in DNS Lookup (paymenthacks .com) |
7136 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |